| File name: | Photo.exe |
| Full analysis: | https://app.any.run/tasks/8c6371dc-1617-460d-a15c-ebc5b45b8584 |
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2024, 12:44:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | E29657ED37F6D5FA30F2E0E8486090B5 |
| SHA1: | 4922F66C8065C99C5FA6B04F4A0119426D0A8945 |
| SHA256: | 7661E4276EC82293324438ED2C541AEA4A6A758A0D720A1B7229CCED0ED8ECFD |
| SSDEEP: | 98304:RN6jxhHppN8DzBhntVWbsamEJAk0W+cqXbEPKNVOsRd4FFdmJMiIOjl3FnxN3cb1:kFqXhQabHdZ4 |
MALICIOUS
Drops the executable file immediately after the start
- Photo.exe (PID: 3996)
Changes the autorun value in the registry
- Photo.exe (PID: 3996)
SUSPICIOUS
Reads security settings of Internet Explorer
- Photo.exe (PID: 3996)
Executable content was dropped or overwritten
- Photo.exe (PID: 3996)
Detected use of alternative data streams (AltDS)
- Photo.exe (PID: 3996)
Reads the Internet Settings
- Photo.exe (PID: 3996)
INFO
Reads the computer name
- Photo.exe (PID: 3996)
Reads the machine GUID from the registry
- Photo.exe (PID: 3996)
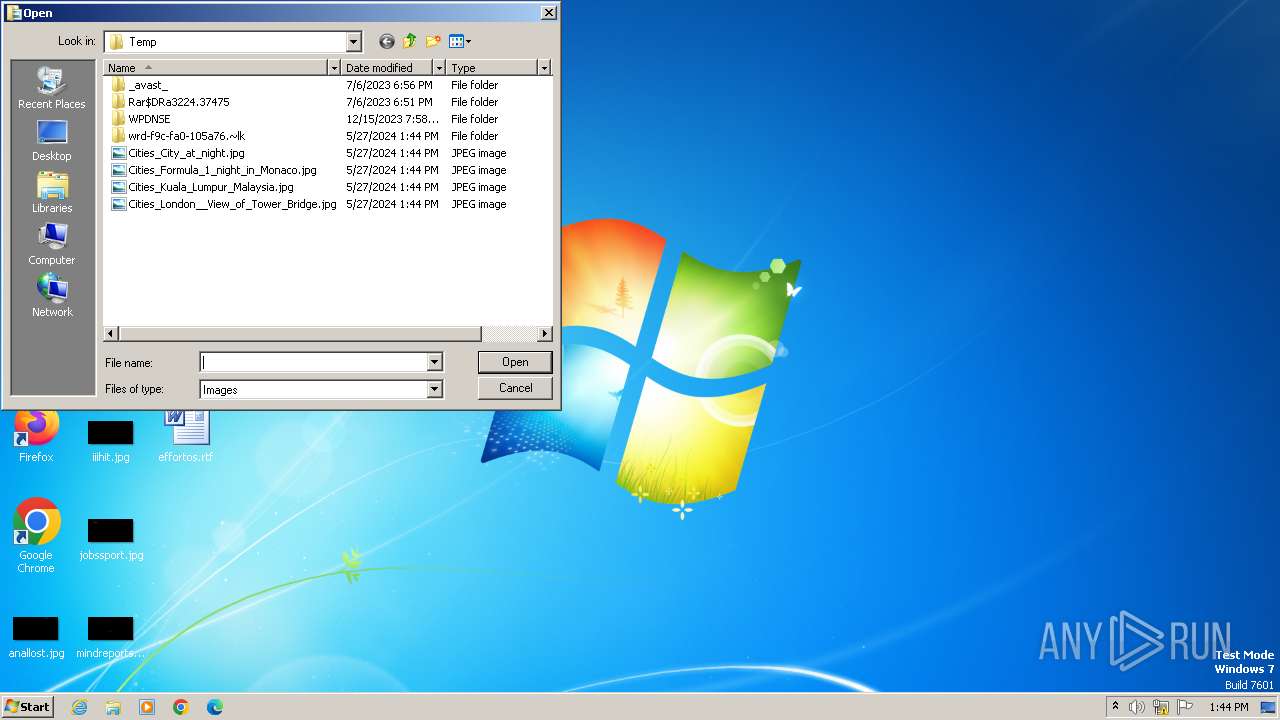
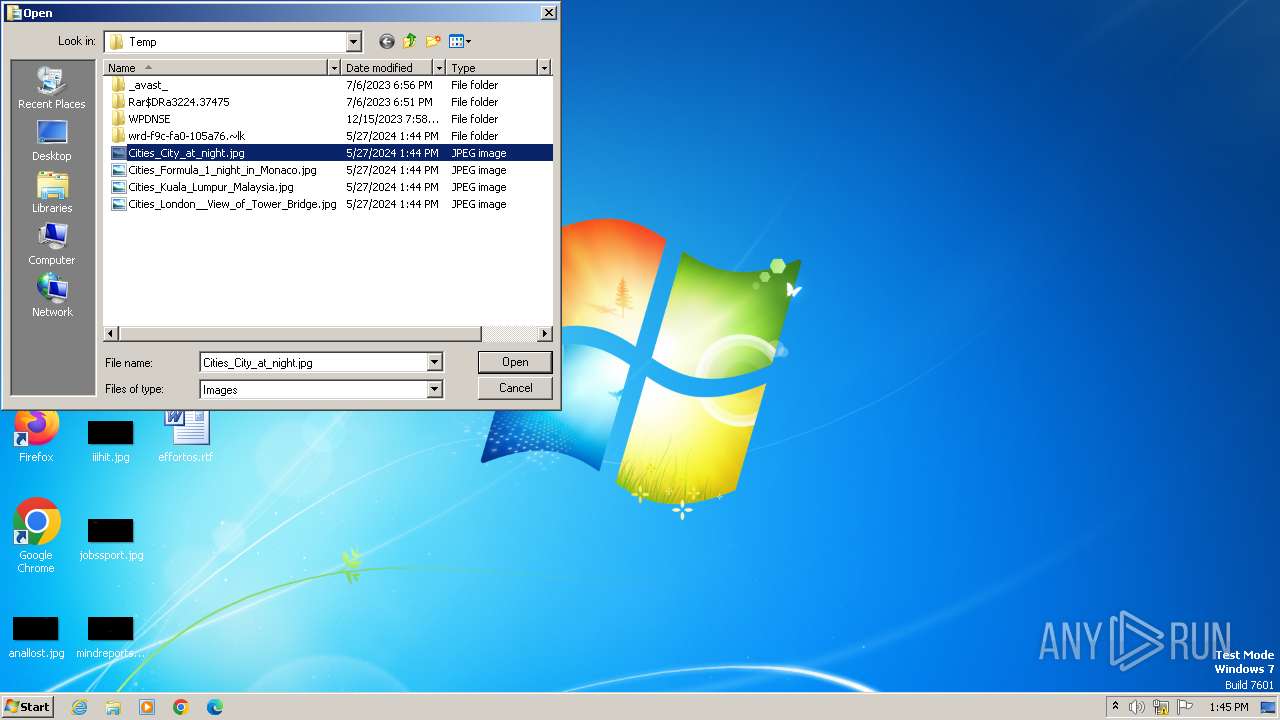
Create files in a temporary directory
- Photo.exe (PID: 3996)
Creates files or folders in the user directory
- Photo.exe (PID: 3996)
Checks supported languages
- Photo.exe (PID: 3996)
Reads CPU info
- Photo.exe (PID: 3996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (28.6) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (28) |
| .exe | | | Win32 EXE Yoda's Crypter (27.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.8) |
| .exe | | | Win32 Executable (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:04:10 11:29:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 2011136 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | 1515520 |
| EntryPoint: | 0x35cf40 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.0.7 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| CompanyName: | Soft |
| FileDescription: | Open photo |
| FileVersion: | 1.1.0.7 |
| InternalName: | Photo |
| LegalCopyright: | Soft inc. |
| LegalTrademarks: | Copyright 2012 |
| OriginalFileName: | Photo |
| ProductName: | Photo |
| ProductVersion: | 1.1.0.7 |
Total processes
33
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3996 | "C:\Users\admin\AppData\Local\Temp\Photo.exe" | C:\Users\admin\AppData\Local\Temp\Photo.exe | explorer.exe | ||||||||||||
User: admin Company: Soft Integrity Level: MEDIUM Description: Open photo Version: 1.1.0.7 Modules
| |||||||||||||||
Total events
8 501
Read events
8 474
Write events
26
Delete events
1
Modification events
| (PID) Process: | (3996) Photo.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3996) Photo.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3996) Photo.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3996) Photo.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3996) Photo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Photo.exe | |||
| (PID) Process: | (3996) Photo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: | |||
| (PID) Process: | (3996) Photo.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Find |
Value: C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Photo.exe | |||
| (PID) Process: | (3996) Photo.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (3996) Photo.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00500068006F0074006F002E00650078006500000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000000 | |||
| (PID) Process: | (3996) Photo.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
Executable files
6
Suspicious files
4
Text files
4
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | Photo.exe | C:\Users\admin\AppData\Local\Temp\wrd-f9c-fa0-105a76.~lk\4.mdd | executable | |
MD5:5379C9DA4EECAD6BD87E16FA9BF77793 | SHA256:F0466700070303202910C7E7B740D3A96750B0FA8A5B5B035D789D2815D49029 | |||
| 3996 | Photo.exe | C:\Users\admin\AppData\Local\Temp\wrd-f9c-fa0-105a76.~lk\3.mdd | executable | |
MD5:5168F1A61E75EEF60CFD9B2356B2A033 | SHA256:3D2D7161BDA781E891C8B7609C4F3C28777B6440084BE3B9DFAB4B088CB496C9 | |||
| 3996 | Photo.exe | C:\Users\admin\AppData\Local\Temp\wrd-f9c-fa0-105a76.~lk\2.mdd | executable | |
MD5:3A9FFF286CF967CFD251324C83BF4921 | SHA256:BED9643898F91E7BCC4D551CEFF435C02D71867CC5A950B0DE53489E26CB2155 | |||
| 3996 | Photo.exe | C:\Users\admin\AppData\Local\Temp\wrd-f9c-fa0-105a76.~lk\0.mdd | executable | |
MD5:9EDA6AC05D976773BEC1A5AC2FC19C3B | SHA256:47CC32F966ED28E1BD719FAA6CE6D2919C4D447EF784B866155796EBB410AE0A | |||
| 3996 | Photo.exe | C:\Users\admin\AppData\Local\Temp\wrd-f9c-fa0-105a76.~lk\~swd1.swf | swf | |
MD5:EEB736D65F89DBABDC5670F801C6D53B | SHA256:110CC62DFE0D51671099BC36E39F9C07331A1AF2CBC1265E6BCF19991268E425 | |||
| 3996 | Photo.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | sol | |
MD5:4E442C66F85325FE25C83EE8855432CA | SHA256:C1F7F9394B37899EC9EFE36DD2C26C80837F357D86F20F67DC13F6491F0CFEA9 | |||
| 3996 | Photo.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Photo.exe | executable | |
MD5:E29657ED37F6D5FA30F2E0E8486090B5 | SHA256:7661E4276EC82293324438ED2C541AEA4A6A758A0D720A1B7229CCED0ED8ECFD | |||
| 3996 | Photo.exe | C:\Users\admin\AppData\Local\Temp\Cities_City_at_night.jpg | image | |
MD5:5E01886ED947DE9C14928B976C01F618 | SHA256:086DA8BB4E7E202F2BD84C5944C3A3C0ECF3BEAB25CF9480033B128F335BEB09 | |||
| 3996 | Photo.exe | C:\Users\admin\AppData\Local\Temp\Cities_Formula_1_night_in_Monaco.jpg | image | |
MD5:034F501389CD2485D65EE7EB21F92678 | SHA256:755681CDAD1F5E4682472DD98BF978023B85031037CA4F654DBDB3CE1158B3AB | |||
| 3996 | Photo.exe | C:\Users\admin\AppData\Local\Temp\wrd-f9c-fa0-105a76.~lk\~swd1.dat | swf | |
MD5:666DCF1DF26B167B1171767CDF887943 | SHA256:3F8FBFAD9C9B3237F1782090F28A86B30F62CE09706CF082E862C3838DFB2C15 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Threats
Process | Message |
|---|---|
Photo.exe | WM_PAINT |
Photo.exe | wm_setfocus
|
Photo.exe | setfocus flash
|
Photo.exe | killfocus main form 0
|
Photo.exe | wm_killfocus
|
Photo.exe | setfocus child form 0
|
Photo.exe | setfocus flash
|
Photo.exe | setfocus main form 0
|
Photo.exe | killfocus child form 0
|
Photo.exe | setfocus child form 0
|