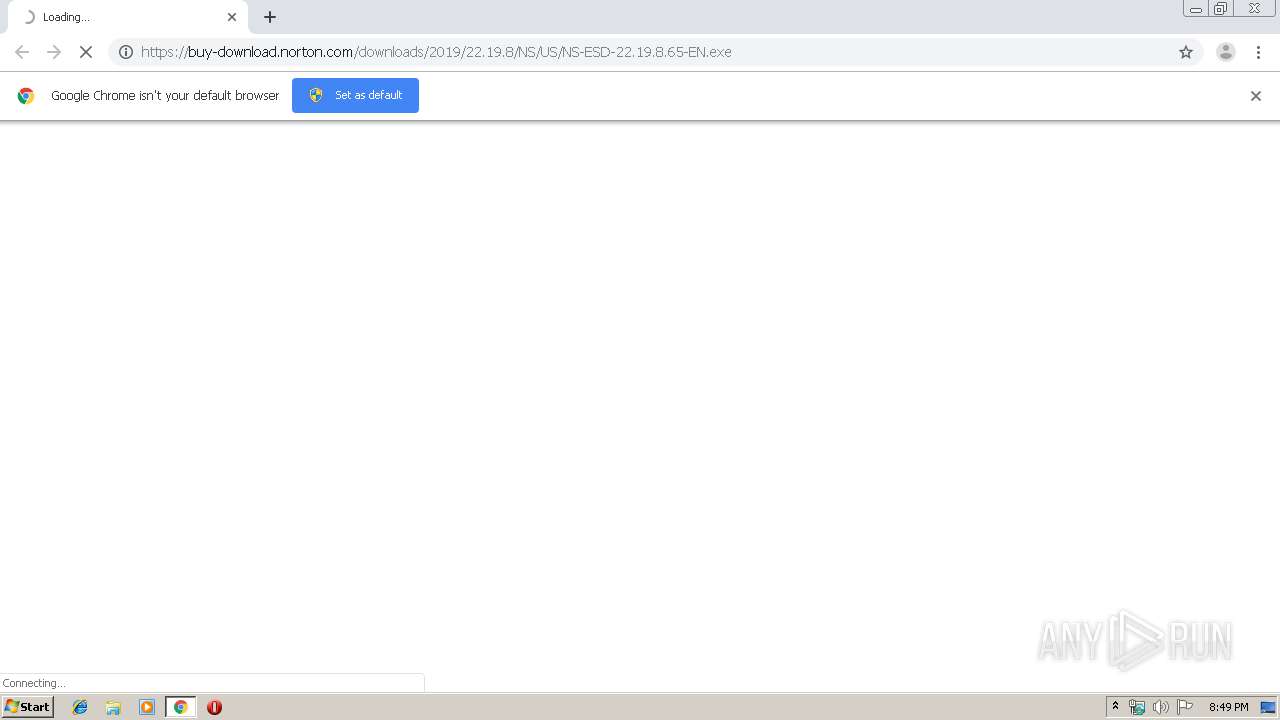
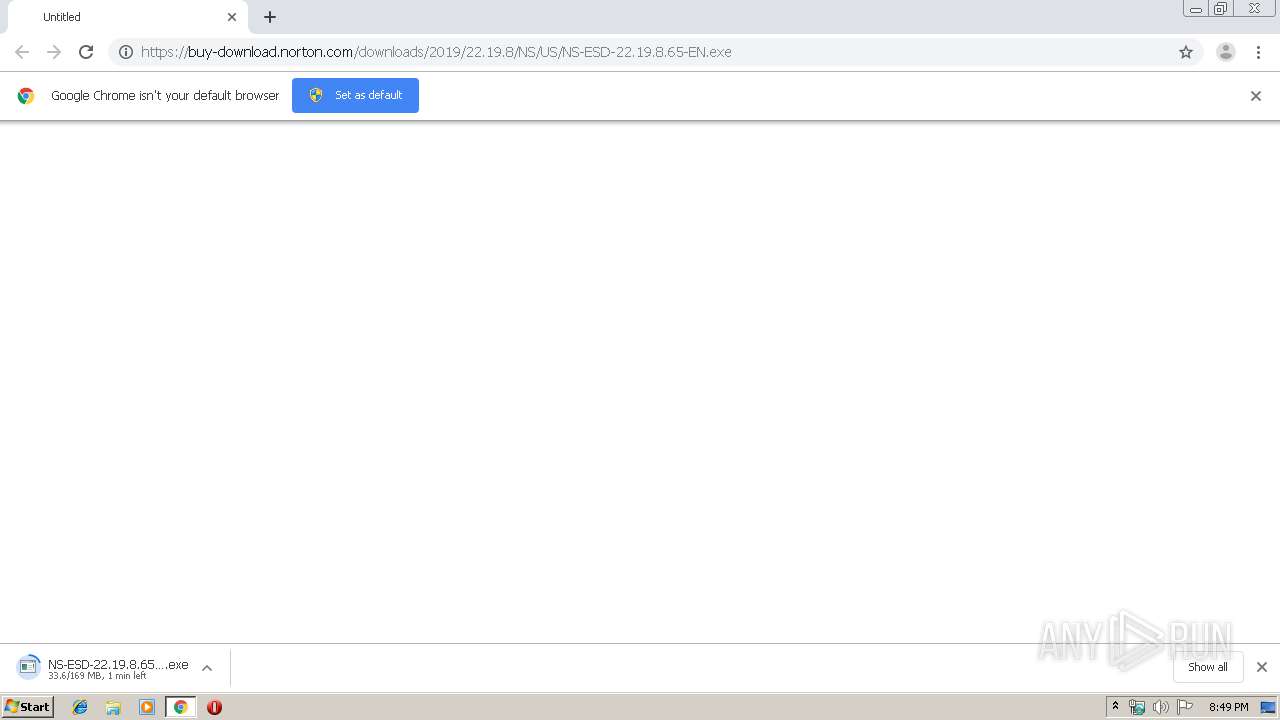
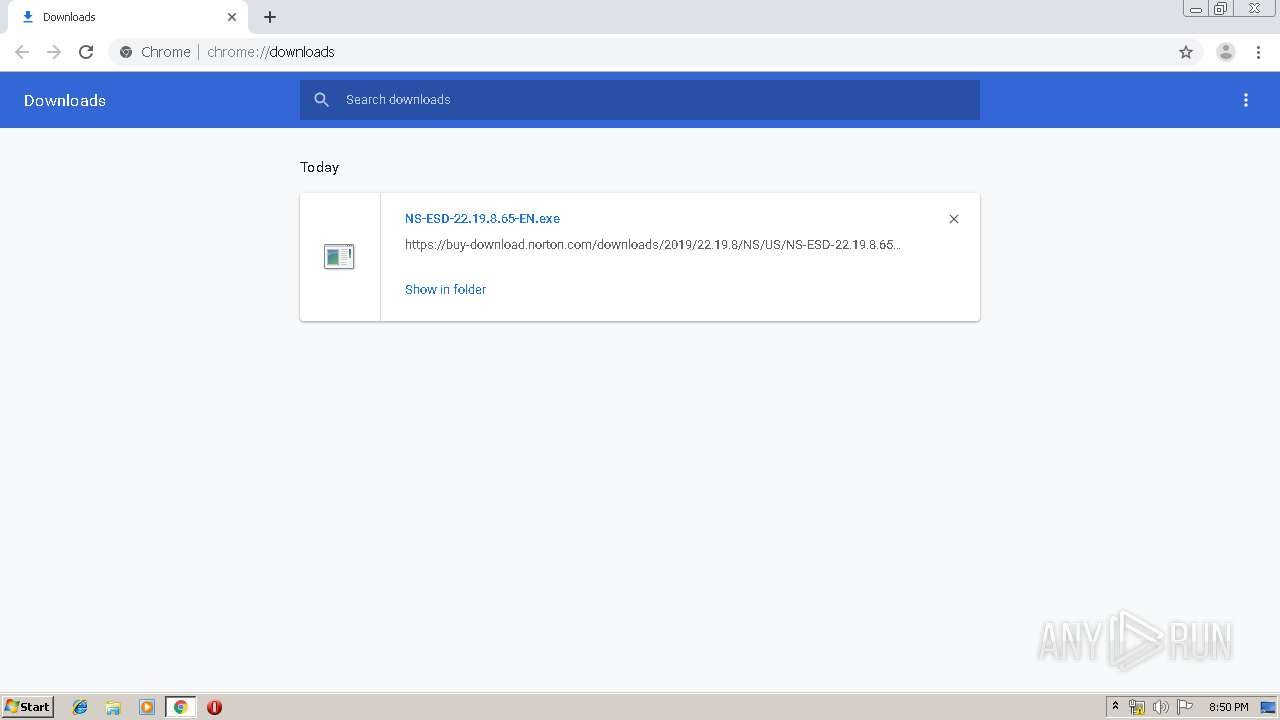
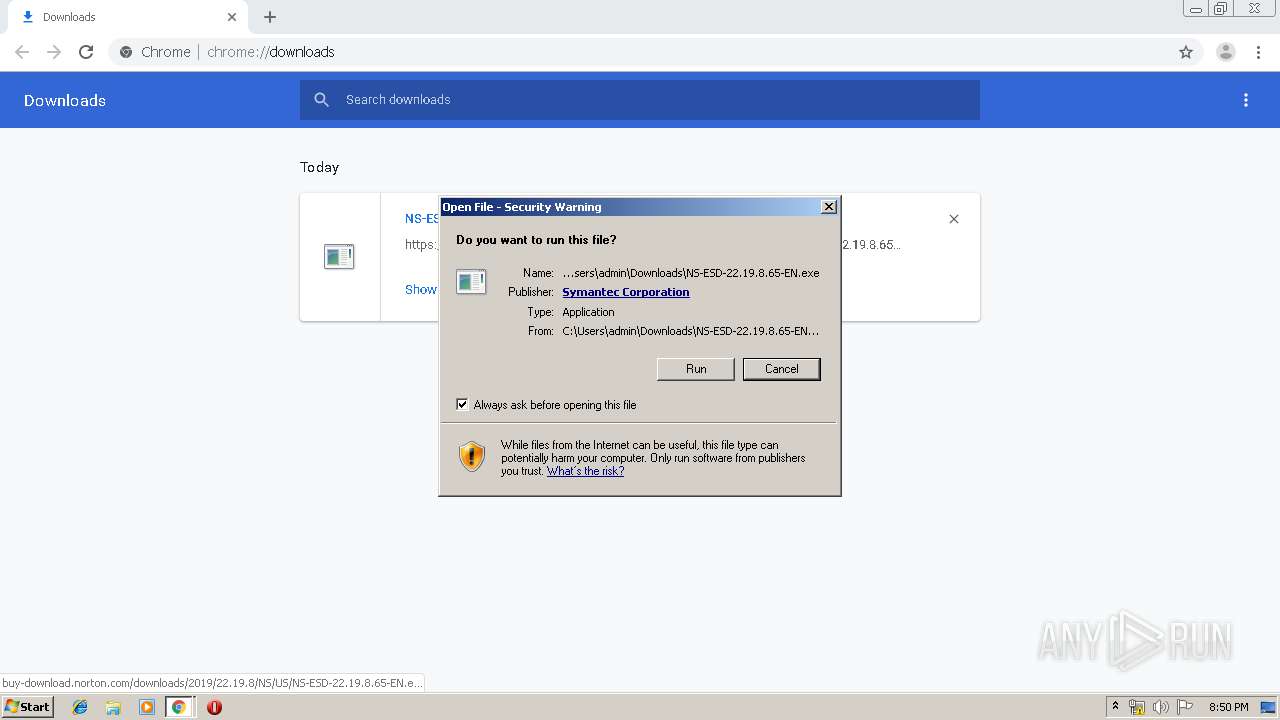
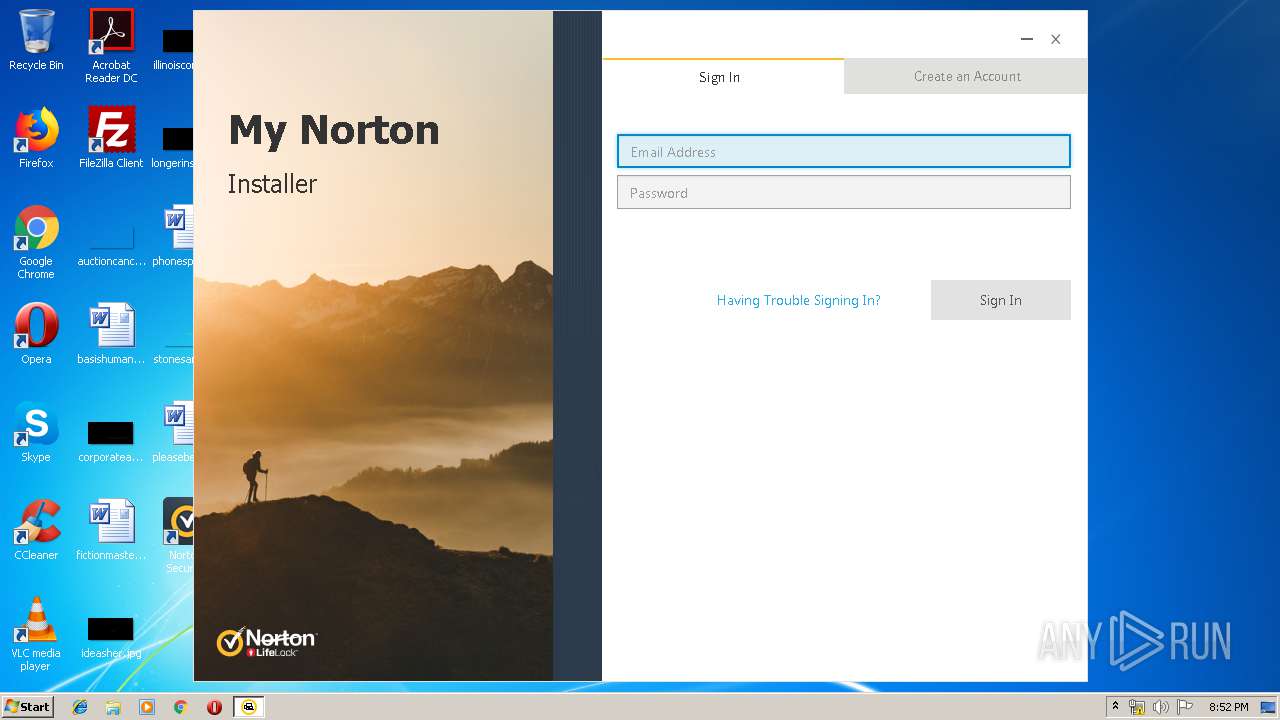
| URL: | https://buy-download.norton.com/downloads/2019/22.19.8/NS/US/NS-ESD-22.19.8.65-EN.exe |
| Full analysis: | https://app.any.run/tasks/135ddcbc-6244-490a-a6b8-3ab0306a4e16 |
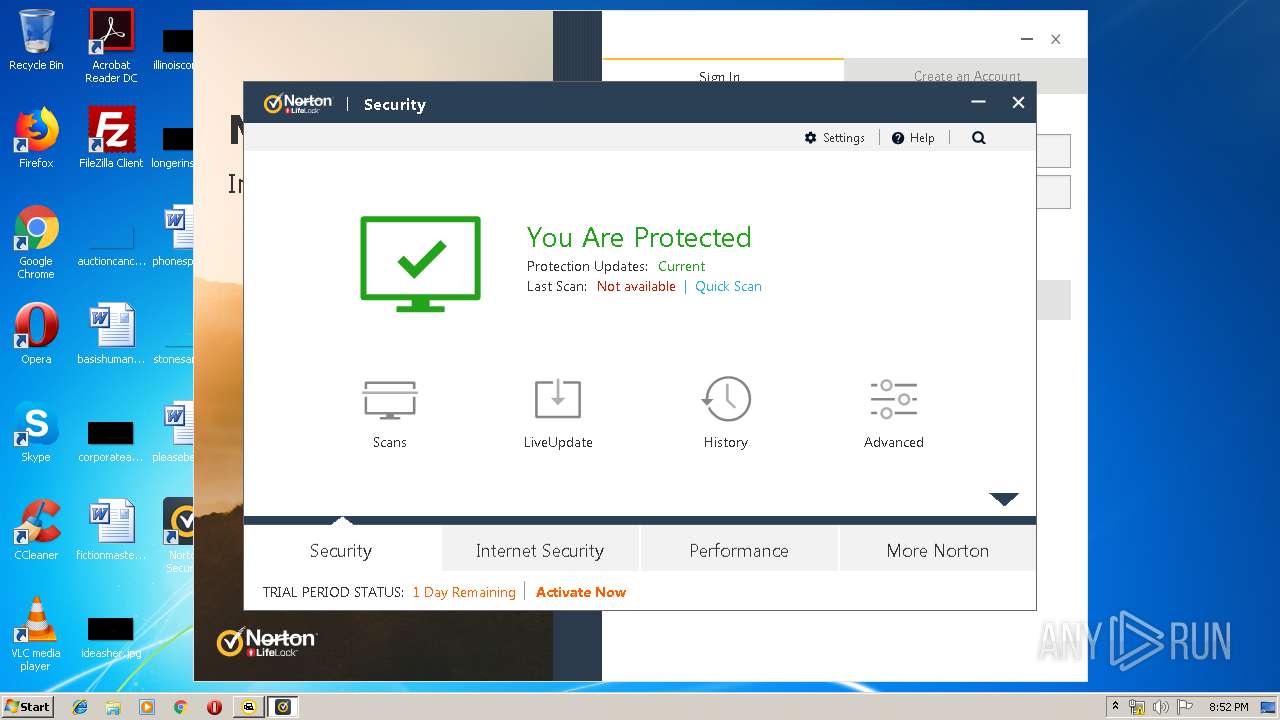
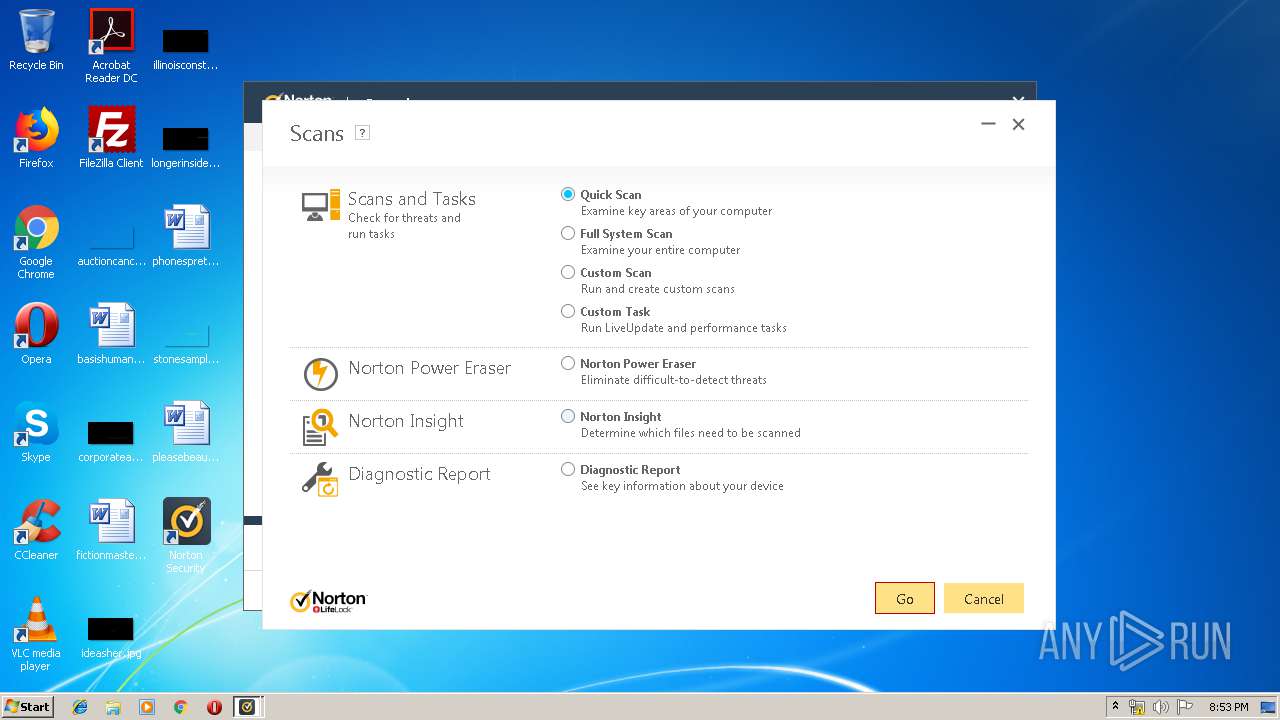
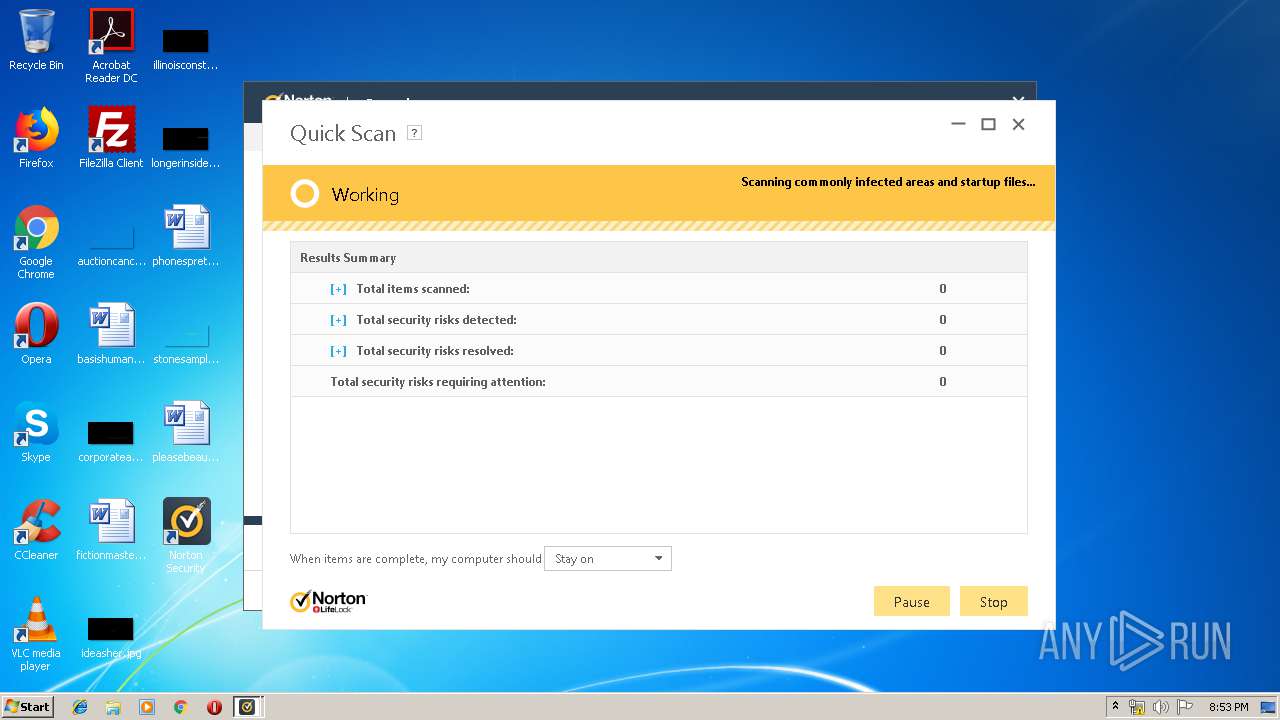
| Verdict: | Malicious activity |
| Analysis date: | September 28, 2019, 19:48:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2B26E5726D5B70CB6724DC8C28E46F1D |
| SHA1: | 4282EB4A13BE479BA9D3549ADABDD081D3534640 |
| SHA256: | 765D2C502DAFF7FA6904BCFEB12AC98A75C89E4564B110F9A47594C3A11ED910 |
| SSDEEP: | 3:N8084Jl+BQyWKXKX2HLFkiarvcIzA:203/maGHZa7G |
MALICIOUS
Application was dropped or rewritten from another process
- NS-ESD-22.19.8.65-EN.exe (PID: 1744)
- NS-ESD-22.19.8.65-EN.exe (PID: 1424)
- EFAInst.exe (PID: 1412)
- SymVTCatalogDB.exe (PID: 1360)
- Sevinst.exe (PID: 2312)
- NortonSecurity.exe (PID: 3312)
- InstCA.exe (PID: 3408)
- coInst.exe (PID: 2664)
- cltLMH.exe (PID: 504)
- NortonSecurity.exe (PID: 3652)
- WSCStub.exe (PID: 2332)
- WSCStub.exe (PID: 304)
- WSCStub.exe (PID: 1512)
- WSCStub.exe (PID: 2656)
- WSCStub.exe (PID: 3148)
- WSCStub.exe (PID: 2520)
- SymIMIns.exe (PID: 2360)
- WSCStub.exe (PID: 3872)
- SRTSP_CA.exe (PID: 1040)
- symerr.exe (PID: 3712)
- symerr.exe (PID: 3192)
- NSc.exe (PID: 2716)
- WSCStub.exe (PID: 3264)
- WSCStub.exe (PID: 3168)
- WSCStub.exe (PID: 3600)
- NSc.exe (PID: 1900)
- tuIH.exe (PID: 3784)
- WSCStub.exe (PID: 1920)
- WSCStub.exe (PID: 4020)
- NSc.exe (PID: 4024)
- WSCStub.exe (PID: 2504)
- WSCStub.exe (PID: 548)
- WSCStub.exe (PID: 2912)
- WSCStub.exe (PID: 3996)
- WSCStub.exe (PID: 1492)
- uiStub.exe (PID: 2944)
- WSCStub.exe (PID: 3088)
- intiupdater.exe (PID: 2508)
- uiStub.exe (PID: 2168)
- WSCStub.exe (PID: 1524)
- WSCStub.exe (PID: 3924)
- WSCStub.exe (PID: 3320)
- WSCStub.exe (PID: 4072)
- RuleUp.exe (PID: 1648)
Changes the autorun value in the registry
- NS-ESD-22.19.8.65-EN.exe (PID: 1424)
Loads dropped or rewritten executable
- NS-ESD-22.19.8.65-EN.exe (PID: 1424)
- explorer.exe (PID: 236)
- SearchProtocolHost.exe (PID: 1008)
- EFAInst.exe (PID: 1412)
- coInst.exe (PID: 2664)
- SymIMIns.exe (PID: 2360)
- symerr.exe (PID: 3192)
- RuleUp.exe (PID: 1648)
- tuIH.exe (PID: 3784)
- InstCA.exe (PID: 3408)
- NortonSecurity.exe (PID: 3312)
- cltLMH.exe (PID: 504)
- NortonSecurity.exe (PID: 3652)
- WSCStub.exe (PID: 2332)
- symerr.exe (PID: 3712)
- WSCStub.exe (PID: 304)
- WSCStub.exe (PID: 1512)
- WSCStub.exe (PID: 2520)
- WSCStub.exe (PID: 3872)
- NSc.exe (PID: 2716)
- WSCStub.exe (PID: 3168)
- WSCStub.exe (PID: 3600)
- WSCStub.exe (PID: 4020)
- NSc.exe (PID: 1900)
- NSc.exe (PID: 4024)
- WSCStub.exe (PID: 3996)
- WSCStub.exe (PID: 1920)
- WSCStub.exe (PID: 548)
- WSCStub.exe (PID: 2504)
- WSCStub.exe (PID: 3088)
- WSCStub.exe (PID: 1492)
- uiStub.exe (PID: 2944)
- intiupdater.exe (PID: 2508)
- uiStub.exe (PID: 2168)
- WSCStub.exe (PID: 1524)
- WSCStub.exe (PID: 3924)
- WSCStub.exe (PID: 4072)
- WSCStub.exe (PID: 3320)
- WSCStub.exe (PID: 2656)
- WSCStub.exe (PID: 3264)
- WSCStub.exe (PID: 3148)
- WSCStub.exe (PID: 2912)
Loads the Task Scheduler COM API
- symerr.exe (PID: 3192)
- tuIH.exe (PID: 3784)
- InstCA.exe (PID: 3408)
- NortonSecurity.exe (PID: 3312)
SUSPICIOUS
Cleans NTFS data-stream (Zone Identifier)
- chrome.exe (PID: 2980)
Executable content was dropped or overwritten
- chrome.exe (PID: 2980)
- Sevinst.exe (PID: 2312)
- NS-ESD-22.19.8.65-EN.exe (PID: 1424)
- NortonSecurity.exe (PID: 3312)
- symcdefsv5i32.exe (PID: 2348)
- intiupdater.exe (PID: 2508)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2980)
Creates a software uninstall entry
- NS-ESD-22.19.8.65-EN.exe (PID: 1424)
- Sevinst.exe (PID: 2312)
Creates or modifies windows services
- NS-ESD-22.19.8.65-EN.exe (PID: 1424)
- NortonSecurity.exe (PID: 3312)
Application launched itself
- NS-ESD-22.19.8.65-EN.exe (PID: 1744)
- NortonSecurity.exe (PID: 3312)
- NSc.exe (PID: 2716)
Creates files in the Windows directory
- NS-ESD-22.19.8.65-EN.exe (PID: 1424)
- Sevinst.exe (PID: 2312)
- symcdefsv5i32.exe (PID: 2348)
- intiupdater.exe (PID: 2508)
Creates files in the driver directory
- NS-ESD-22.19.8.65-EN.exe (PID: 1424)
- Sevinst.exe (PID: 2312)
Creates files in the program directory
- EFAInst.exe (PID: 1412)
- Sevinst.exe (PID: 2312)
- SymIMIns.exe (PID: 2360)
- RuleUp.exe (PID: 1648)
- tuIH.exe (PID: 3784)
- InstCA.exe (PID: 3408)
- NortonSecurity.exe (PID: 3652)
- symerr.exe (PID: 3712)
- NortonSecurity.exe (PID: 3312)
- NS-ESD-22.19.8.65-EN.exe (PID: 1424)
- intiupdater.exe (PID: 2508)
Writes to a desktop.ini file (may be used to cloak folders)
- NS-ESD-22.19.8.65-EN.exe (PID: 1424)
Executed as Windows Service
- NortonSecurity.exe (PID: 3312)
Low-level read access rights to disk partition
- cltLMH.exe (PID: 504)
- NortonSecurity.exe (PID: 3312)
Creates COM task schedule object
- NS-ESD-22.19.8.65-EN.exe (PID: 1424)
Creates files in the user directory
- NortonSecurity.exe (PID: 3652)
Removes files from Windows directory
- symcdefsv5i32.exe (PID: 2348)
- NortonSecurity.exe (PID: 3312)
Uses IPCONFIG.EXE to discover IP address
- symerr.exe (PID: 3712)
INFO
Reads the hosts file
- chrome.exe (PID: 2260)
- chrome.exe (PID: 2980)
- NortonSecurity.exe (PID: 3312)
- symerr.exe (PID: 3712)
- NSc.exe (PID: 2716)
Reads Internet Cache Settings
- chrome.exe (PID: 2980)
Application launched itself
- chrome.exe (PID: 2980)
Dropped object may contain Bitcoin addresses
- NS-ESD-22.19.8.65-EN.exe (PID: 1424)
- intiupdater.exe (PID: 2508)
Reads settings of System Certificates
- NortonSecurity.exe (PID: 3312)
- explorer.exe (PID: 236)
- NSc.exe (PID: 2716)
Reads Microsoft Office registry keys
- NortonSecurity.exe (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
114
Monitored processes
71
Malicious processes
45
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | "C:\Program Files\Norton Security\Engine\22.19.8.65\WSCStub.exe" | C:\Program Files\Norton Security\Engine\22.19.8.65\WSCStub.exe | — | NortonSecurity.exe | |||||||||||
User: SYSTEM Company: Symantec Corporation Integrity Level: SYSTEM Description: WSCStub Exit code: 0 Version: 22.19.8.467 Modules
| |||||||||||||||
| 504 | scan:b-f+ onlinedefs:0 boot:"*"- file:"%SYSTEMDRIVE%\*"+"%TEMP%"-"%TMP%"- container:"*"+"dxsndb"- containerdepth:8 dataexchange:"%APPDATA%\cltLMH.dxsndb" | C:\Program Files\Norton Security\Engine\22.19.8.65\cltLMH.exe | — | NortonSecurity.exe | |||||||||||
User: SYSTEM Company: Symantec Corporation Integrity Level: SYSTEM Description: Symantec Shared Component Exit code: 2147776550 Version: 15.19.8.4 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Norton Security\Engine\22.19.8.65\WSCStub.exe" /updatewdsc | C:\Program Files\Norton Security\Engine\22.19.8.65\WSCStub.exe | — | NortonSecurity.exe | |||||||||||
User: SYSTEM Company: Symantec Corporation Integrity Level: SYSTEM Description: WSCStub Exit code: 0 Version: 22.19.8.467 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,16339687627644002753,4928640842245209266,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17642830354484467155 --mojo-platform-channel-handle=3164 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Norton Security\Engine\22.19.8.65\SRTSP_CA.exe" /install | C:\Program Files\Norton Security\Engine\22.19.8.65\SRTSP_CA.exe | — | NS-ESD-22.19.8.65-EN.exe | |||||||||||
User: admin Company: Symantec Corporation Integrity Level: HIGH Description: Symantec Real Time Storage Protection Custom Action Exit code: 0 Version: 15.7.8.14 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Norton Security\Engine\22.19.8.65\SymVTCatalogDB.exe" /d | C:\Program Files\Norton Security\Engine\22.19.8.65\SymVTCatalogDB.exe | — | NS-ESD-22.19.8.65-EN.exe | |||||||||||
User: admin Company: Symantec Corporation Integrity Level: HIGH Description: SymVT Catalog Database Application Exit code: 0 Version: 10.1.0.38 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Norton Security\Engine\22.19.8.65\EFAInst.exe" /legacydelsysvolinfo | C:\Program Files\Norton Security\Engine\22.19.8.65\EFAInst.exe | NS-ESD-22.19.8.65-EN.exe | ||||||||||||
User: admin Company: Symantec Corporation Integrity Level: HIGH Description: Symantec Extended File Attributes Exit code: 0 Version: 7.3.2.4 Modules
| |||||||||||||||
| 1424 | "C:\Users\admin\Downloads\NS-ESD-22.19.8.65-EN.exe" "C:\Users\admin\Downloads\NS-ESD-22.19.8.65-EN.exe" /ADMIN | C:\Users\admin\Downloads\NS-ESD-22.19.8.65-EN.exe | NS-ESD-22.19.8.65-EN.exe | ||||||||||||
User: admin Company: Symantec Corporation Integrity Level: HIGH Description: Norton Security Exit code: 0 Version: 22.19.8.65 Modules
| |||||||||||||||
Total events
10 589
Read events
7 188
Write events
3 273
Delete events
128
Modification events
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2980-13214173746836375 |
Value: 259 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
472
Suspicious files
525
Text files
489
Unknown types
148
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\46ea76ff-a877-47fc-ac73-6697bd0623ba.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF114f27.TMP | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF114f55.TMP | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF114f17.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
39
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2716 | NSc.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAxkn0RfEw2haHhoK09NYw0%3D | US | der | 471 b | whitelisted |
2716 | NSc.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEA7rLR6jB8oLdTlvedQtXcU%3D | US | der | 471 b | whitelisted |
1060 | svchost.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/GTSGIAG3/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCCHX2nnAAq%2F8G | US | binary | 5 b | whitelisted |
2260 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2260 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
2260 | chrome.exe | GET | 200 | 74.125.173.234:80 | http://r5---sn-4g5ednz7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.128.27.151&mm=28&mn=sn-4g5ednz7&ms=nvh&mt=1569700037&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2260 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2260 | chrome.exe | 2.20.20.197:443 | buy-download.norton.com | Akamai International B.V. | — | whitelisted |
2260 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 172.217.18.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2260 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 216.58.208.33:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 74.125.173.234:80 | r5---sn-4g5ednz7.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
buy-download.norton.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-4g5ednz7.gvt1.com |
| whitelisted |
Threats
Process | Message |
|---|---|
EFAInst.exe | 2019-09-28-20-51-38-307 : EFASIInst : 0x0584 : 0x0220 : Information : --> Starting wWinMain...
|
EFAInst.exe | 2019-09-28-20-51-38-307 : EFASIInst : 0x0584 : 0x0220 : Information : --> Starting Main...
|
EFAInst.exe | 2019-09-28-20-51-38-307 : EFASIInst : 0x0584 : 0x0220 : Information : --> Starting Main...
|
EFAInst.exe | 2019-09-28-20-51-39-275 : EFASIInst : 0x0584 : 0x0220 : Information : SymEFA 4.x style uninstall started.
|
EFAInst.exe | 2019-09-28-20-51-39-275 : EFASIInst : 0x0584 : 0x0220 : Information : Removing data from System Volume Information folders.
|
EFAInst.exe | 2019-09-28-20-51-39-275 : EFASIInst : 0x0584 : 0x0220 : Information : Getting DelSysVol actions...
|
EFAInst.exe | 2019-09-28-20-51-39-275 : EFASIInst : 0x0584 : 0x0220 : Information : --> Starting SymEFA::GetDelSysVolInfoActions...
|
EFAInst.exe | 2019-09-28-20-51-39-275 : EFASIInst : 0x0584 : 0x0220 : Information : <-- SymEFA::GetDelSysVolInfoActions ended
|
EFAInst.exe | 2019-09-28-20-51-39-275 : EFASIInst : 0x0584 : 0x0220 : Information : Acquiring privileges...
|
EFAInst.exe | 2019-09-28-20-51-39-275 : EFASIInst : 0x0584 : 0x0220 : Information : CEfaDataAction: Action will be permanently uninstalled
|