| File name: | Clyraze+.exe |
| Full analysis: | https://app.any.run/tasks/ad382221-9f0d-40c6-83ba-12a739e1a8a6 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 12:30:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 8B15CBD51CA58E0C3909032A65D82AD4 |
| SHA1: | ACD5419E49864C72A3B362A48BFD577CAB749315 |
| SHA256: | 765C22C0062FB660B8AC20FEC2825630E11119DC62EEB8E02C6A937BC37DE883 |
| SSDEEP: | 24576:F0RKAPCwk4+eF8kekipkrXnDIv8kU8as8VL5iYTaSEcm:F0Rxawk4+eF8kekip4XDIv8kjas8V1iV |
MALICIOUS
No malicious indicators.SUSPICIOUS
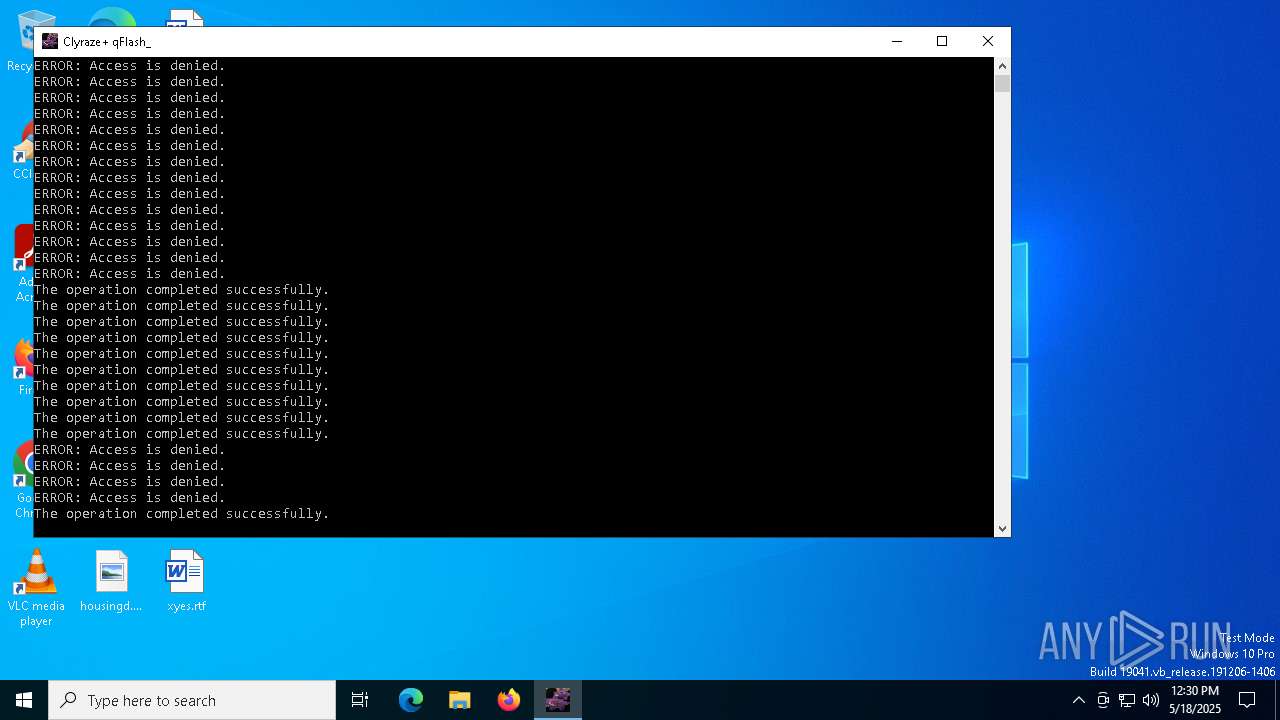
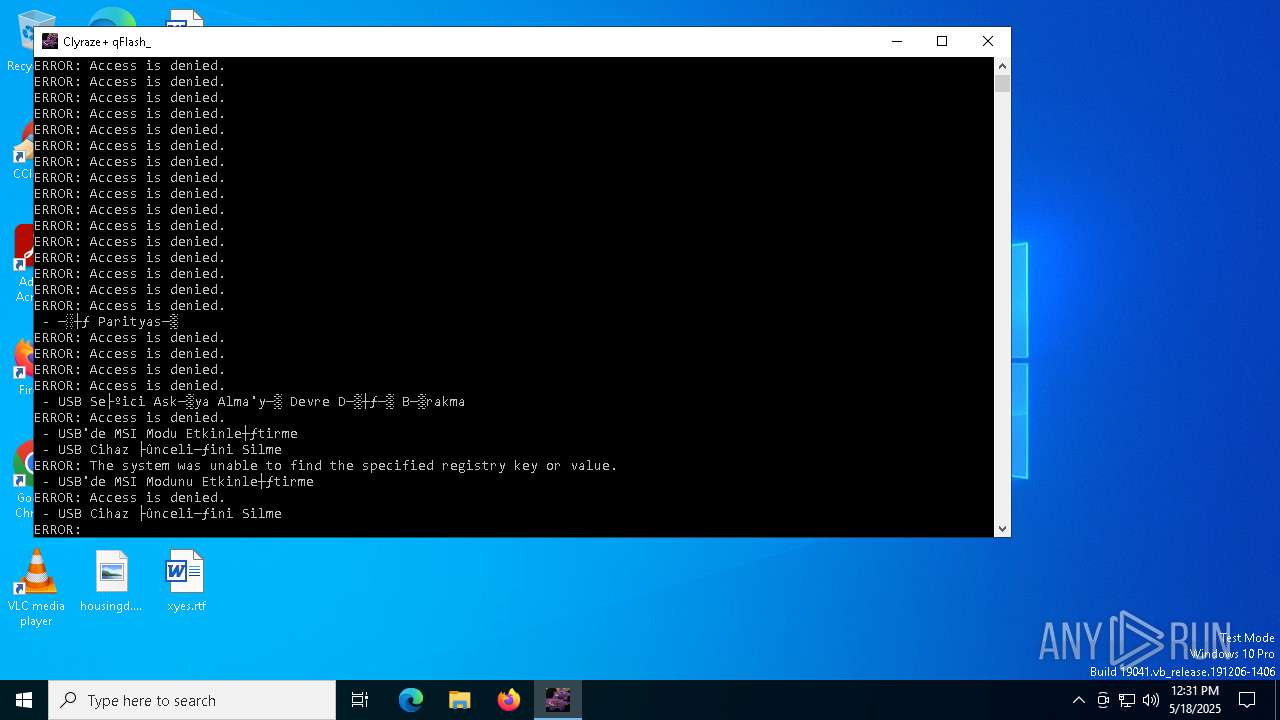
Executing commands from a ".bat" file
- Clyraze+.exe (PID: 2284)
Accesses computer name via WMI (SCRIPT)
- WMIC.exe (PID: 2852)
- WMIC.exe (PID: 7020)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6572)
- Clyraze+.exe (PID: 2284)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6572)
Uses WMIC.EXE
- cmd.exe (PID: 2692)
- cmd.exe (PID: 4408)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4408)
- cmd.exe (PID: 5936)
Application launched itself
- cmd.exe (PID: 6572)
INFO
Checks supported languages
- Clyraze+.exe (PID: 2284)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2852)
- WMIC.exe (PID: 7020)
Reads mouse settings
- reg.exe (PID: 6028)
- reg.exe (PID: 2152)
- reg.exe (PID: 3300)
- reg.exe (PID: 1244)
- reg.exe (PID: 6652)
- reg.exe (PID: 6476)
- reg.exe (PID: 1228)
- reg.exe (PID: 976)
- reg.exe (PID: 5892)
- reg.exe (PID: 5800)
- reg.exe (PID: 2148)
- reg.exe (PID: 5008)
- reg.exe (PID: 6740)
- reg.exe (PID: 3900)
- reg.exe (PID: 2096)
- reg.exe (PID: 2340)
- reg.exe (PID: 516)
- reg.exe (PID: 1052)
- reg.exe (PID: 4000)
- reg.exe (PID: 6268)
- reg.exe (PID: 7052)
- reg.exe (PID: 1180)
Create files in a temporary directory
- Clyraze+.exe (PID: 2284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.2) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:07:30 08:52:08+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.5 |
| CodeSize: | 92672 |
| InitializedDataSize: | 401408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
289
Monitored processes
163
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | Reg.exe add "HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management" /v "UseNtfsMemoryMapping" /t REG_SZ /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | Reg.exe add "HKLM\System\CurrentControlSet\Enum\PCI\VEN_8086&DEV_2934&SUBSYS_11001AF4&REV_03\3&13C0B0C5&0&20\Device Parameters\Interrupt Management\MessageSignaledInterruptProperties" /v "MSISupported" /t REG_DWORD /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | REG ADD "HKEY_CURRENT_USER\Control Panel\Mouse" /v SnapToDefaultButton /t REG_SZ /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Input\Settings\ControllerProcessor\CursorSpeed" /v CursorUpdateInterval /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | Reg.exe add "HKCU\Control Panel\Accessibility\MouseKeys" /v "Flags" /t REG_SZ /d "0" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | Reg.exe add "HKCU\Control Panel\Accessibility\Keyboard Response" /v "AutoRepeatRate" /t REG_SZ /d "15" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | Reg.exe add "HKLM\SYSTEM\CurrentControlSet\Enum\PCI\VEN_8086&DEV_293A&SUBSYS_11001AF4&REV_03\3&13C0B0C5&0&27\Device Parameters" /v "EnableSelectiveSuspend" /t REG_DWORD /d "0" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | Reg.exe add "HKLM\System\CurrentControlSet\Enum\PCI\VEN_8086&DEV_2936&SUBSYS_11001AF4&REV_03\3&13C0B0C5&0&22\Device Parameters\Interrupt Management\MessageSignaledInterruptProperties" /v "MSISupported" /t REG_DWORD /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | Reg.exe add "HKLM\SYSTEM\CurrentControlSet\Control\Nsi{eb004a03-9b1a-11d4-9123-0050047759bc}\0" /v "0200" /t REG_BINARY /d "0000000000000000000000000000000000000000000000000000000002000000000000000000000000000000000000000000ff000000000000000000000000000000000000000000ff000000000000000000000000000000" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | Reg.exe add "HKLM\SYSTEM\ControlSet001\Services\Tcpip\Parameters" /v "DataBasePath" /t REG_EXPAND_SZ /d "%SystemRoot%\System32\drivers\etc" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 387
Read events
2 334
Write events
51
Delete events
2
Modification events
| (PID) Process: | (6028) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Accessibility\Keyboard Response |
| Operation: | write | Name: | BounceTime |
Value: 0 | |||
| (PID) Process: | (6244) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Accessibility\Keyboard Response |
| Operation: | write | Name: | Flags |
Value: 59 | |||
| (PID) Process: | (6700) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Accessibility\Keyboard Response |
| Operation: | write | Name: | Last BounceKey Setting |
Value: 0 | |||
| (PID) Process: | (4040) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Accessibility\Keyboard Response |
| Operation: | write | Name: | Last Valid Wait |
Value: 1000 | |||
| (PID) Process: | (1272) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Accessibility\Keyboard Response |
| Operation: | write | Name: | AutoRepeatDelay |
Value: 200 | |||
| (PID) Process: | (672) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Accessibility\Keyboard Response |
| Operation: | write | Name: | AutoRepeatRate |
Value: 15 | |||
| (PID) Process: | (4920) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Accessibility\Keyboard Response |
| Operation: | write | Name: | DelayBeforeAcceptance |
Value: 0 | |||
| (PID) Process: | (3240) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Accessibility\Keyboard Response |
| Operation: | write | Name: | Last Valid Repeat |
Value: 0 | |||
| (PID) Process: | (5256) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | VisualFXSetting |
Value: 2 | |||
| (PID) Process: | (4000) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Mouse |
| Operation: | write | Name: | MouseSensitivity |
Value: 10 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2284 | Clyraze+.exe | C:\Users\admin\AppData\Local\Temp\B99D.tmp\B99E.tmp\B99F.bat | text | |
MD5:C1CF1E35EB557AFE5538E7E2F6402F77 | SHA256:BFE65C9085940CAEE2F70DB2AB3CB04F1E90207E9C5433C23B8ABC7770B5E1EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
18
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6652 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.52.56.216:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6652 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
6544 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.52.56.216:80 | ocsp.digicert.com | AKAMAI-AS | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6652 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |