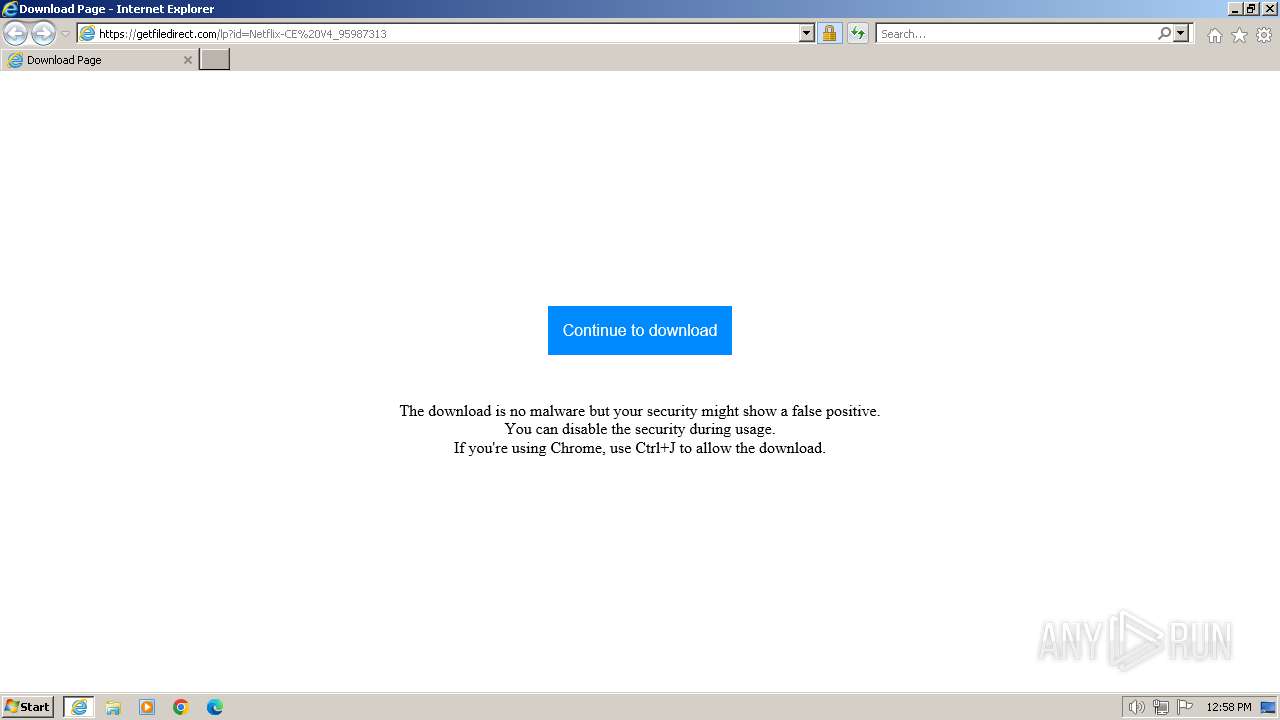
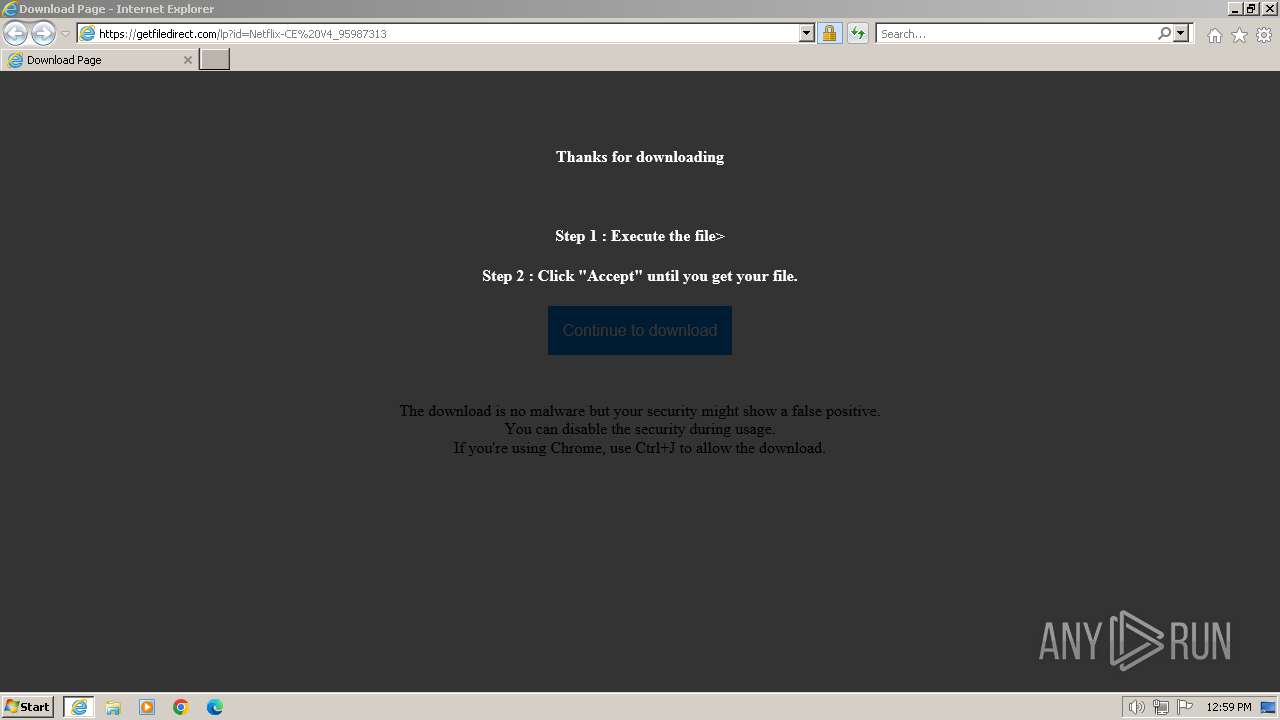
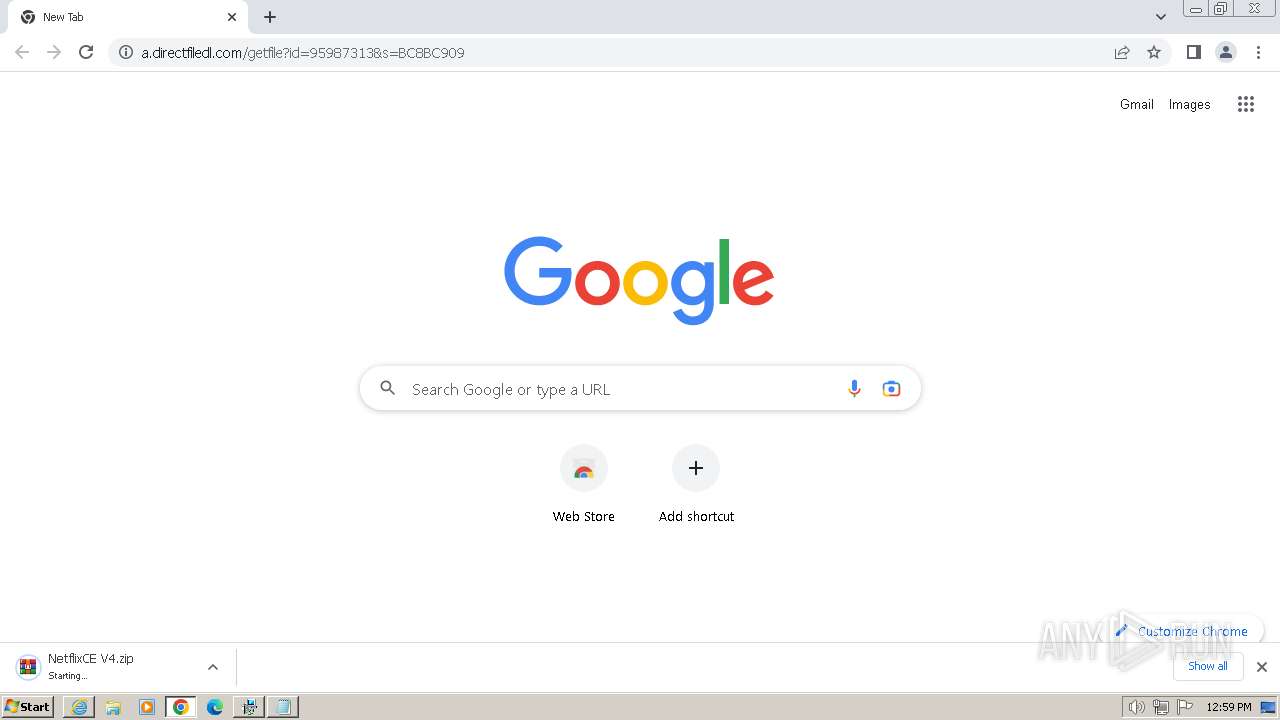
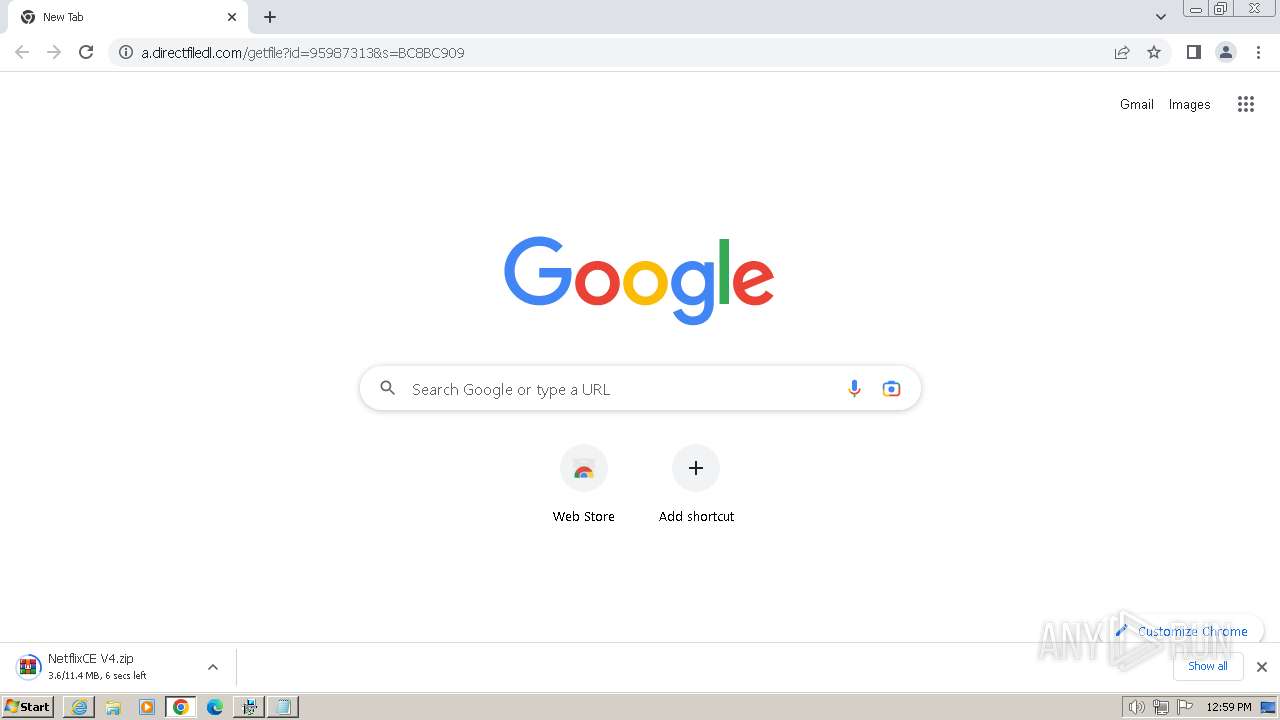
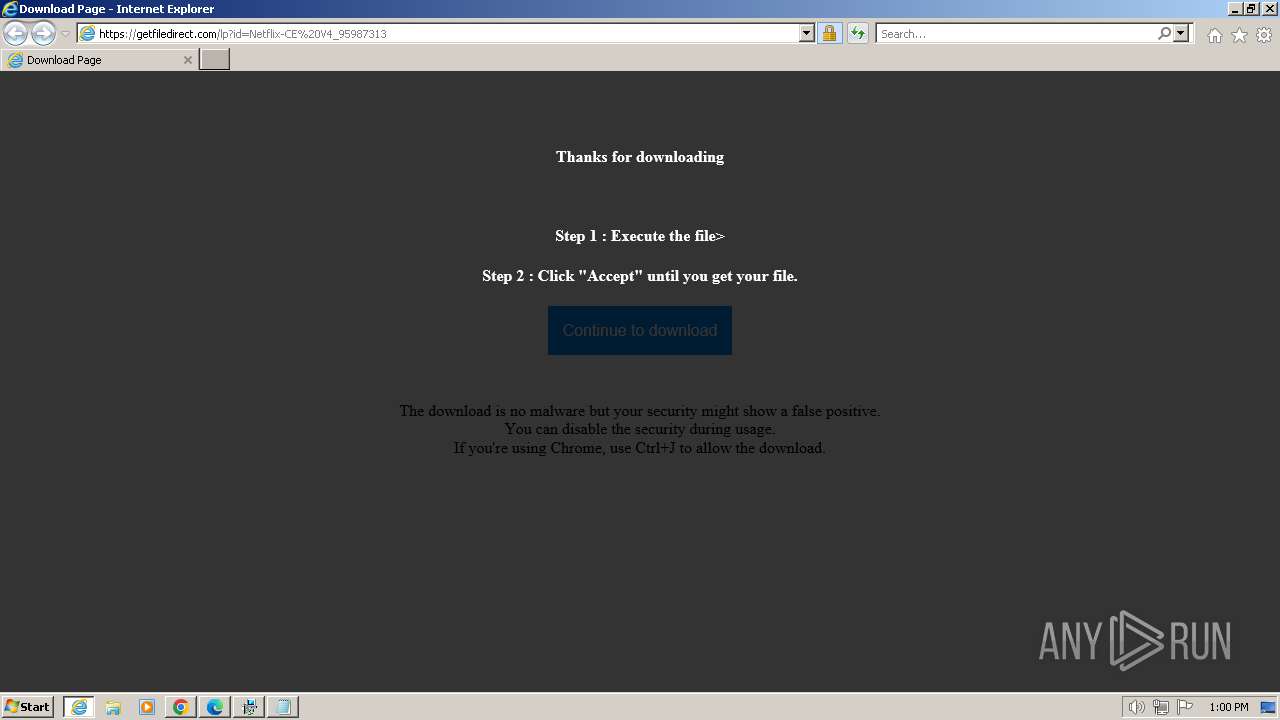
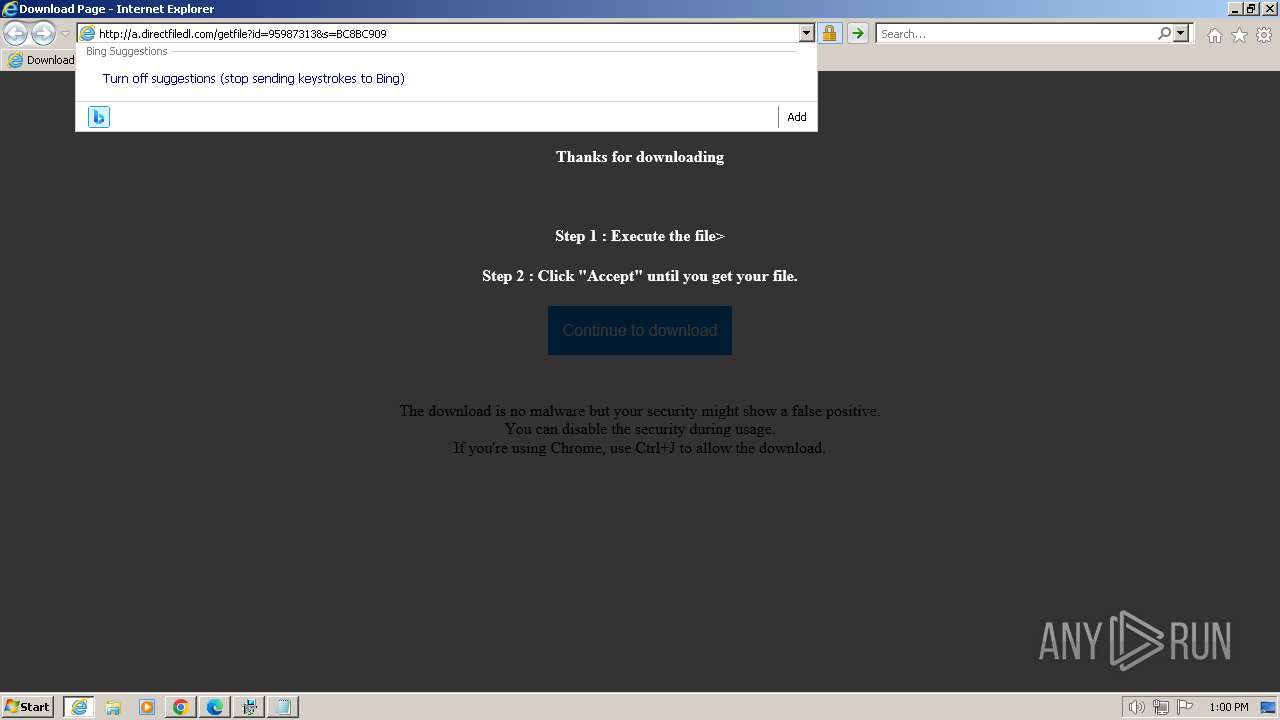
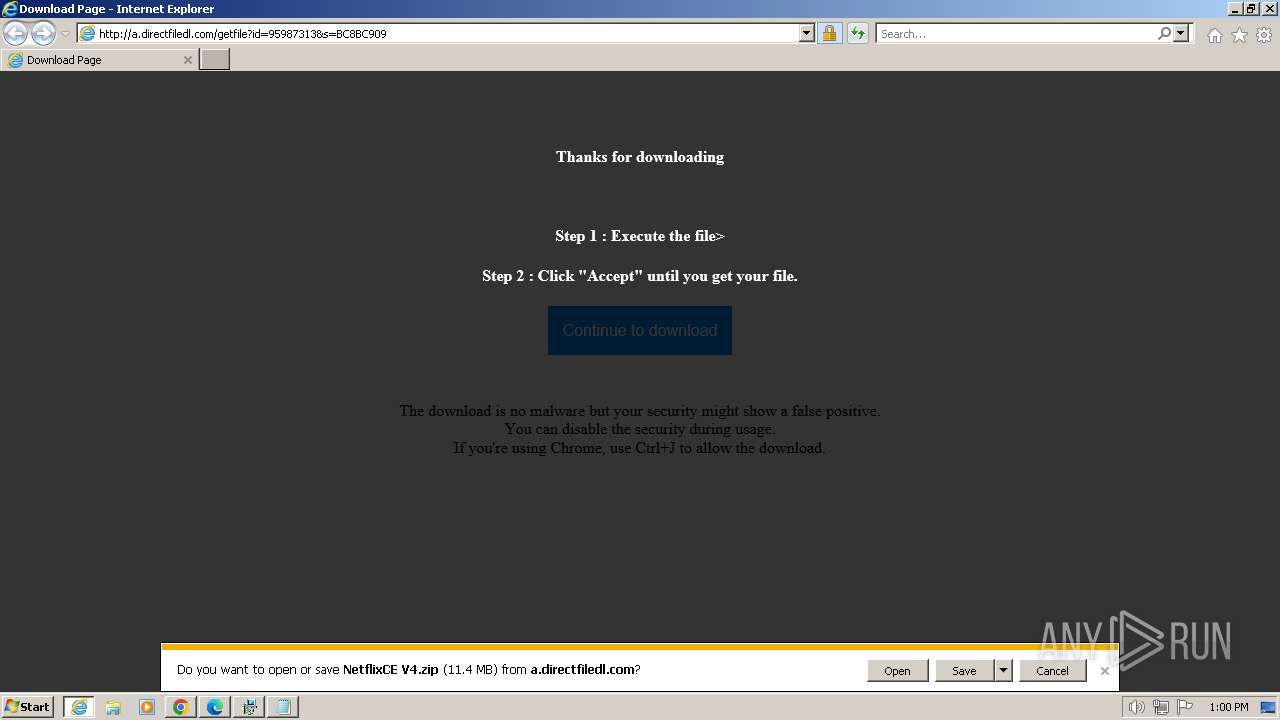
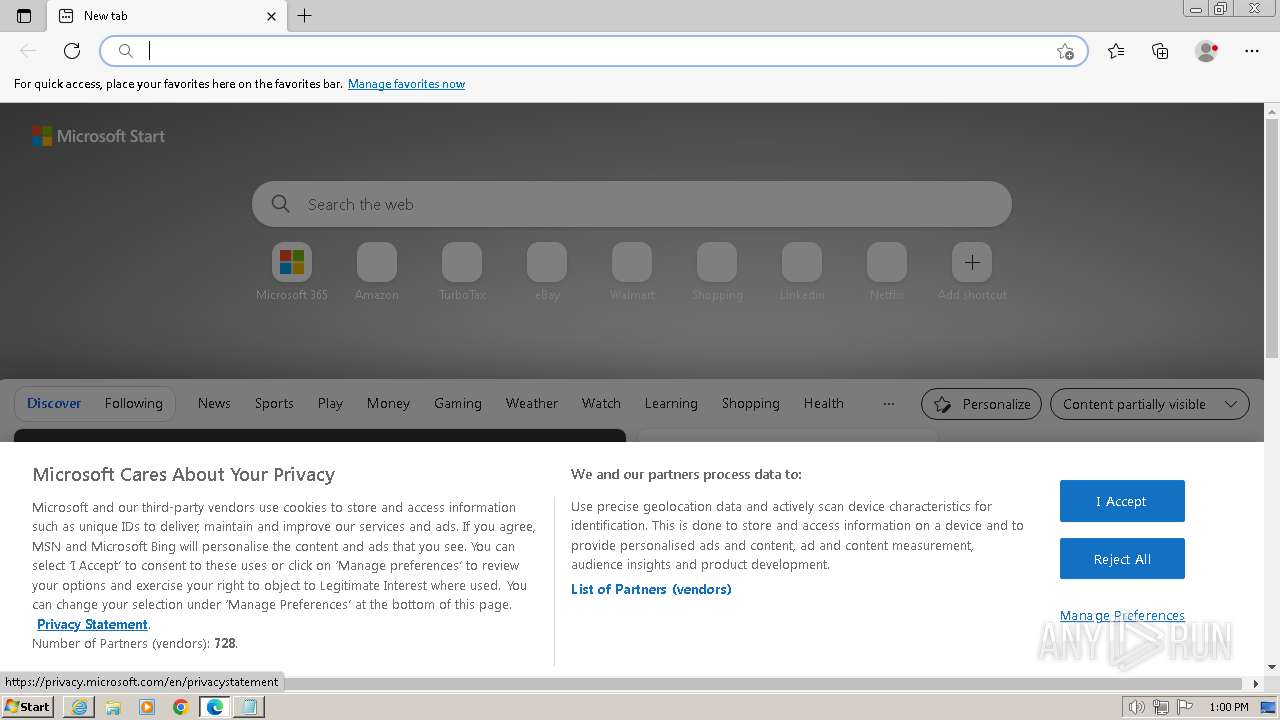
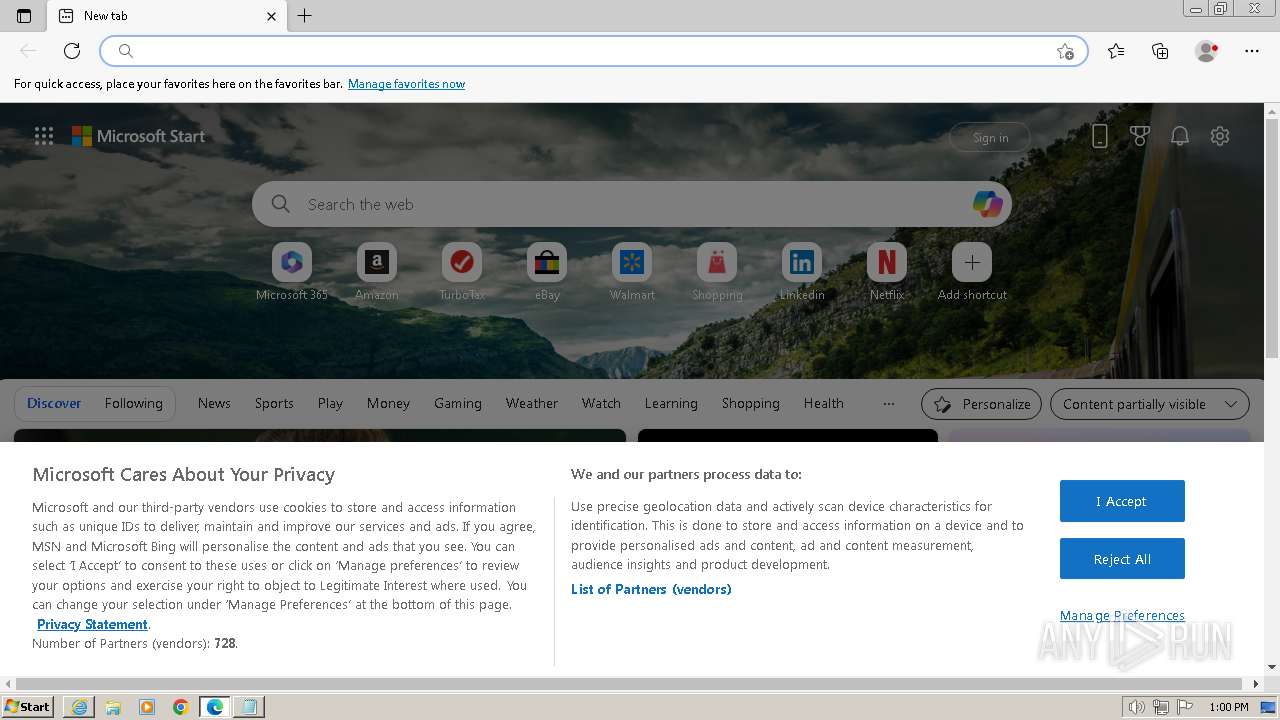
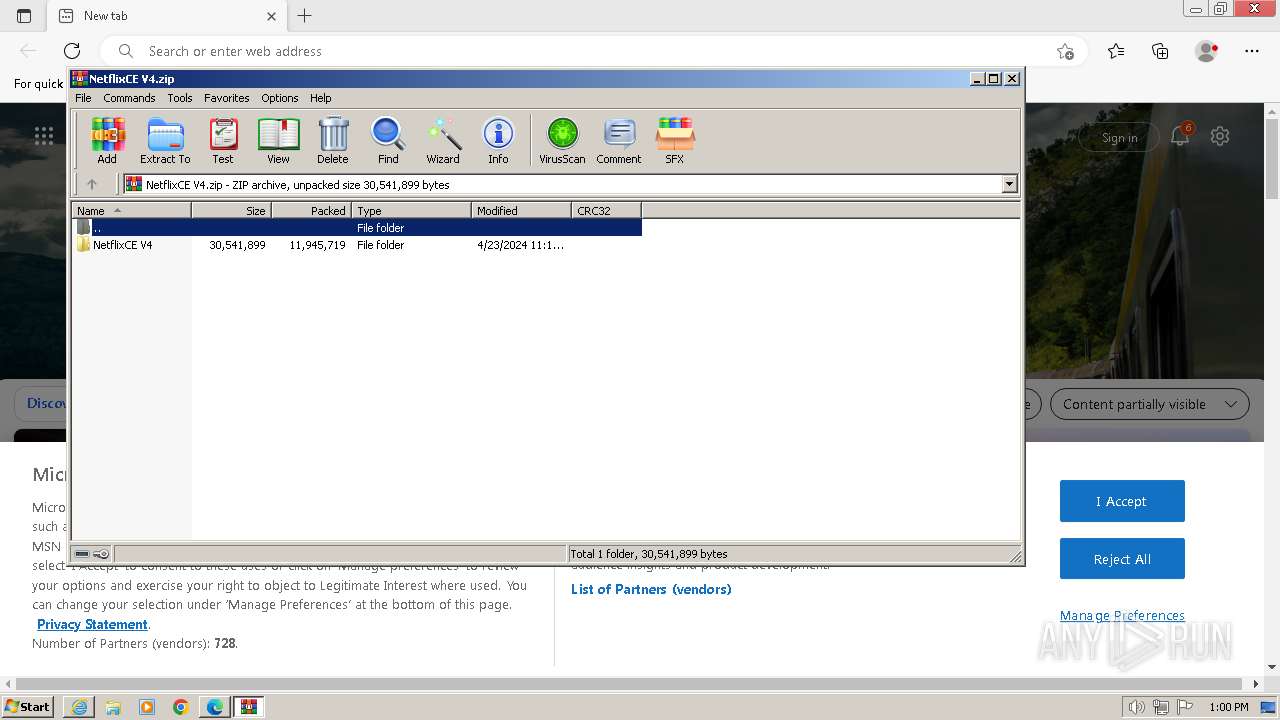
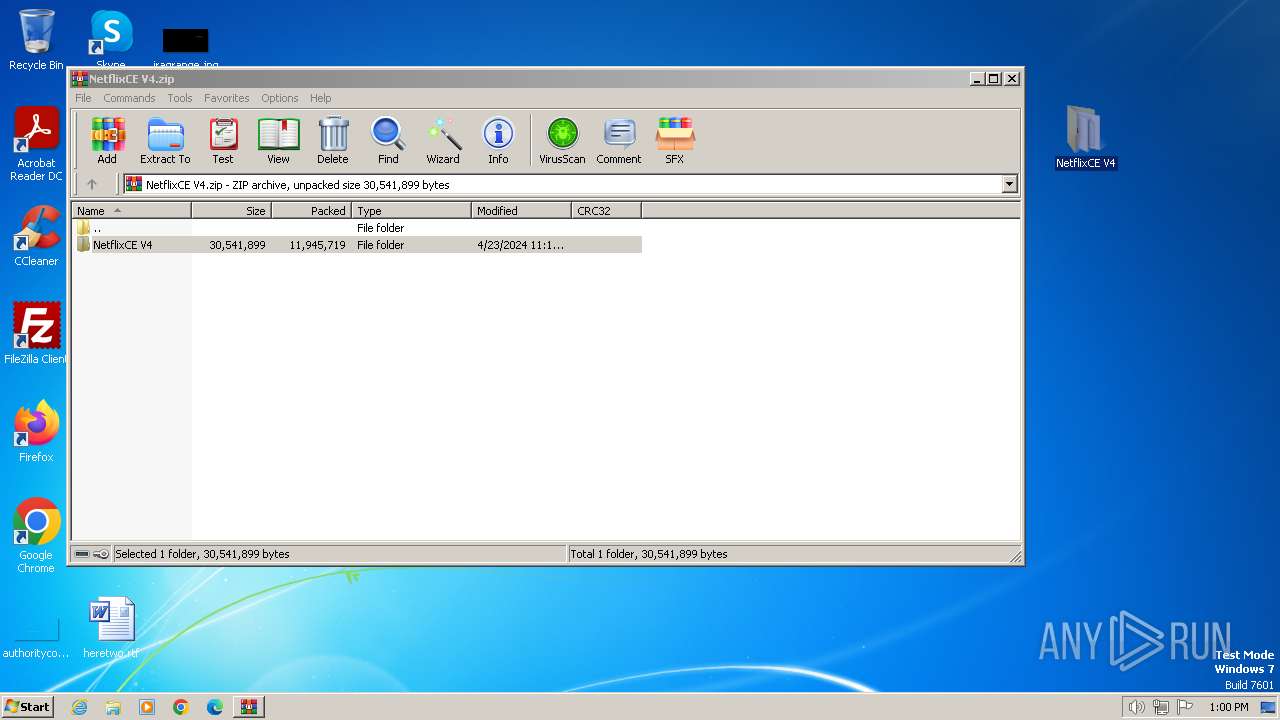
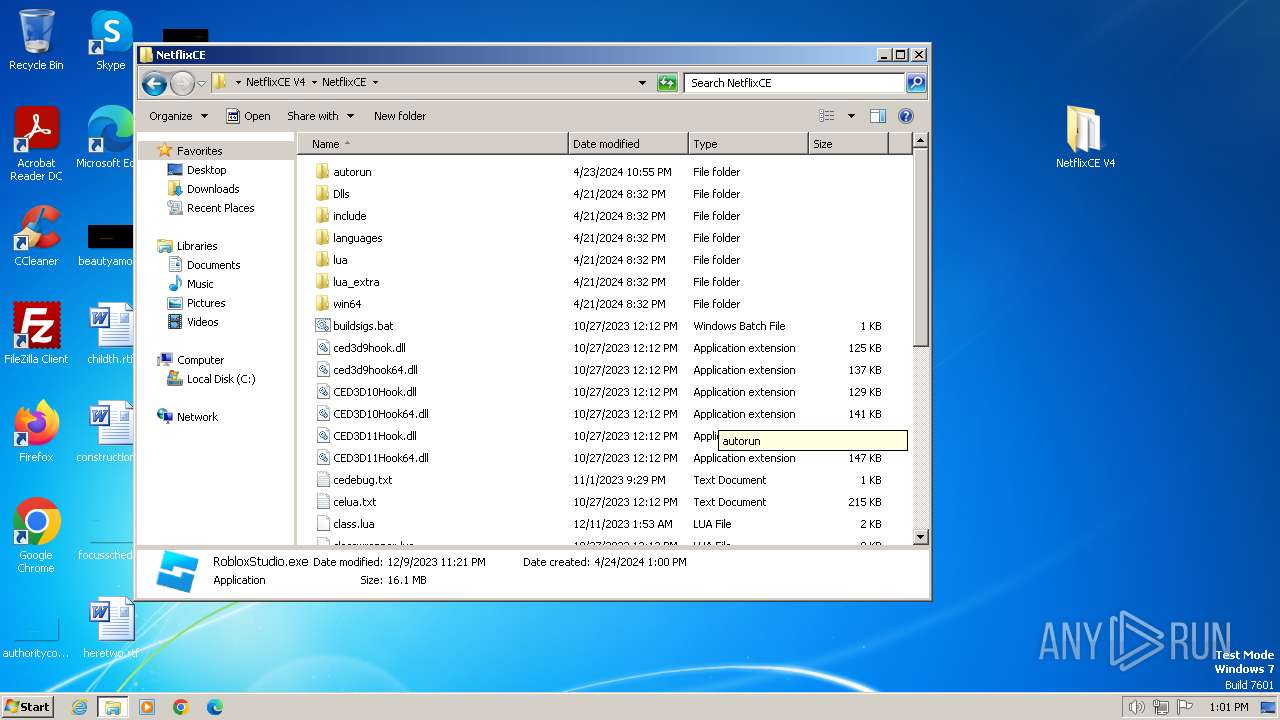
| URL: | https://getfiledirect.com/lp?id=Netflix-CE%20V4_95987313 |
| Full analysis: | https://app.any.run/tasks/dcf02caa-76c1-44a8-bf40-486bd993f679 |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2024, 11:58:49 |
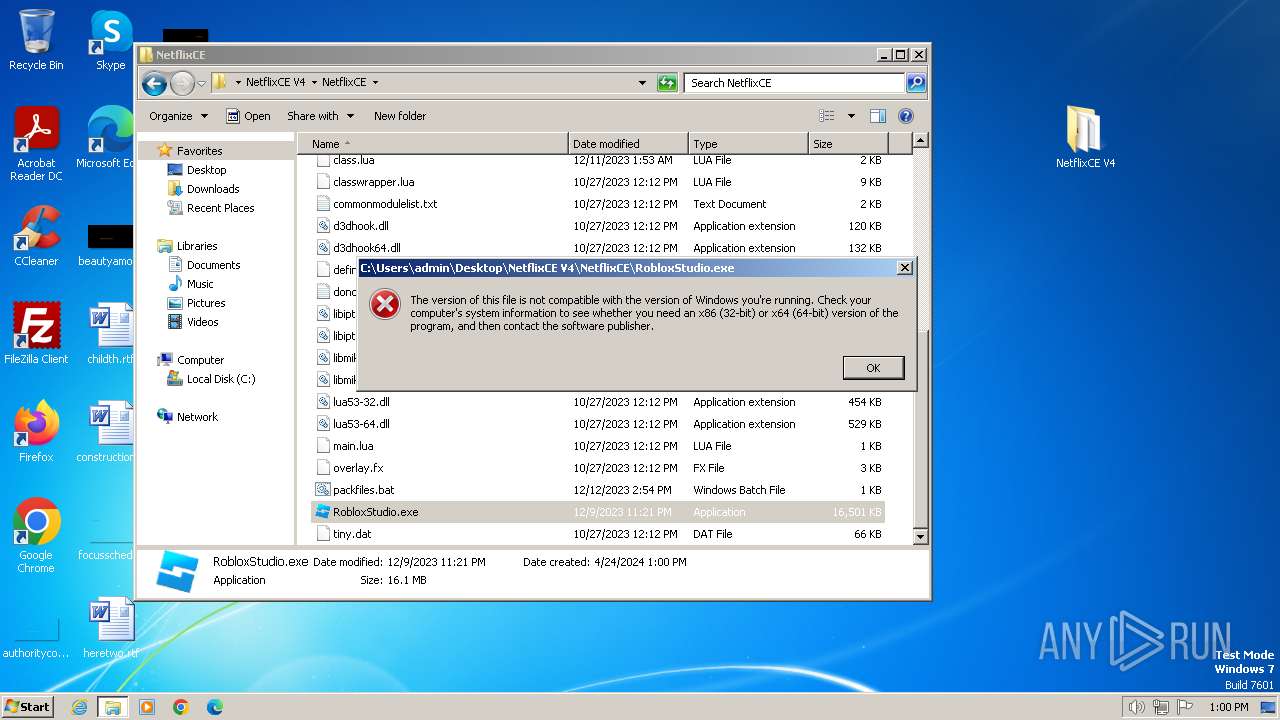
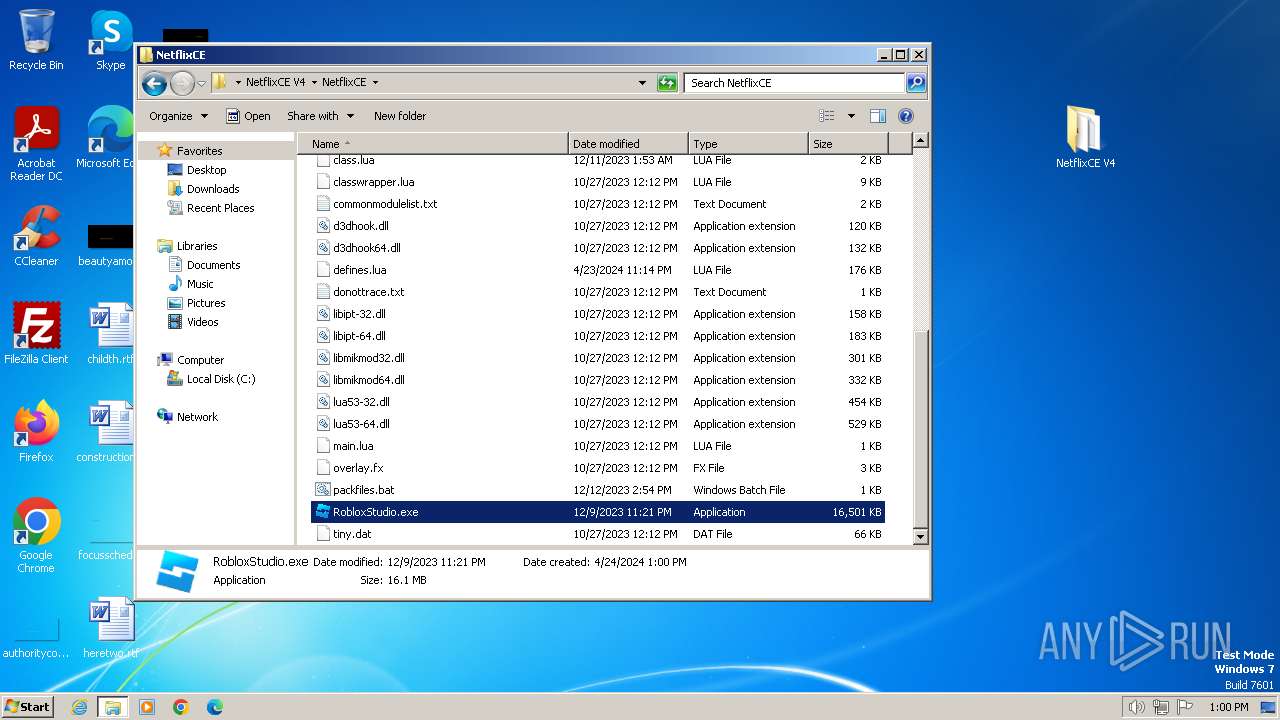
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5F51D5C393360DF4E414E5EA15F44C41 |
| SHA1: | 3C156D7D234FA9B6CDA77111BCFE7E453CD66C11 |
| SHA256: | 765BDD1D3C63A12303D1CCFB9FA501E8A4313BD8DB361F05D0CC8135B1BDB5BD |
| SSDEEP: | 3:N8hOAg0KaAGFL9jSa:2xNua |
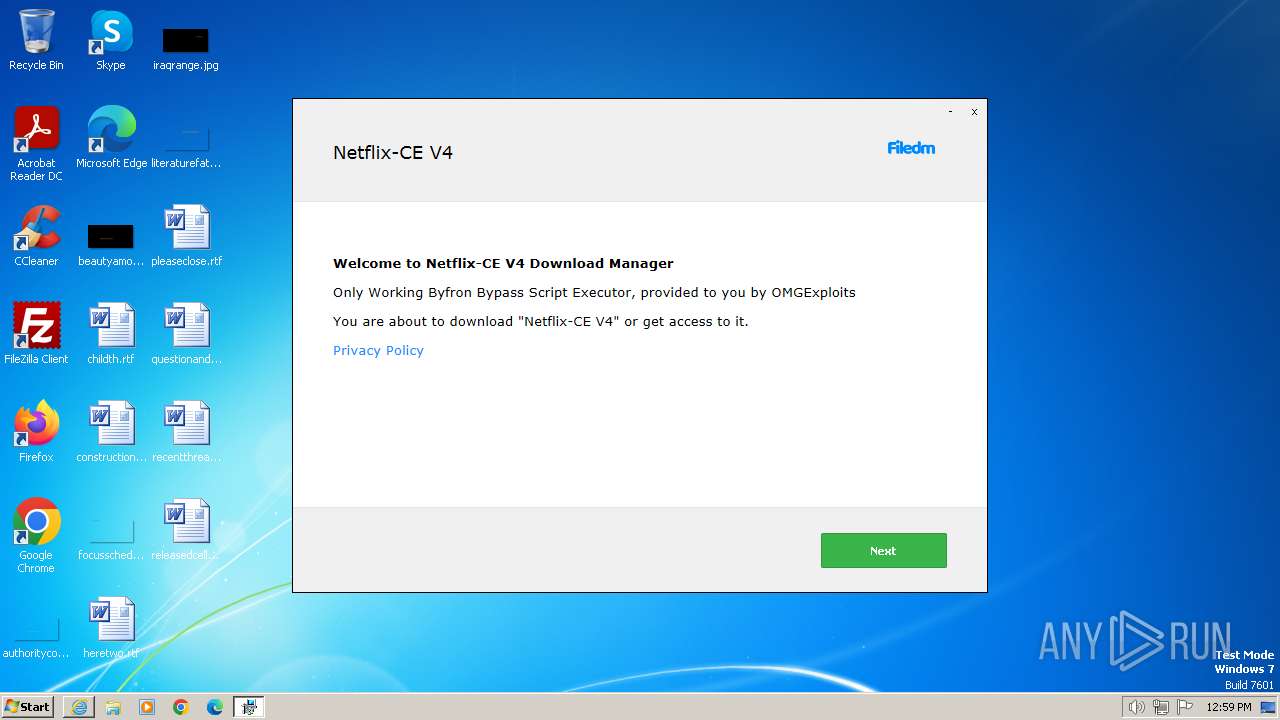
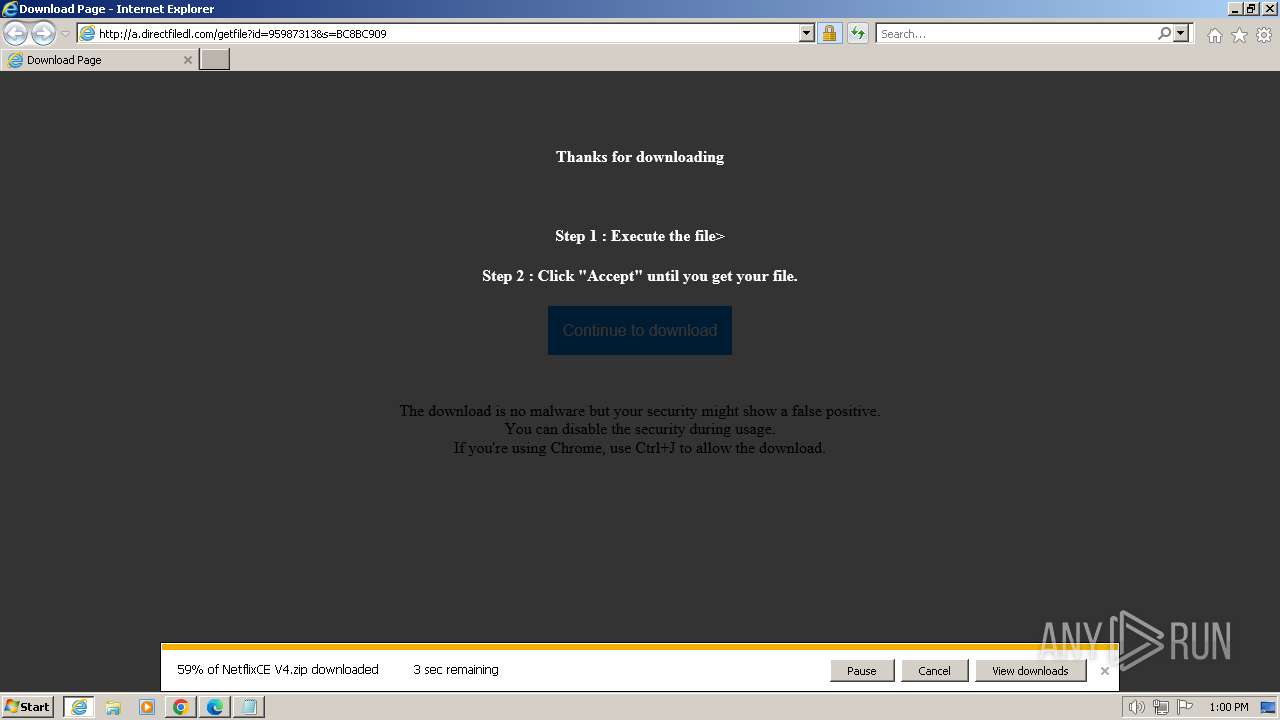
MALICIOUS
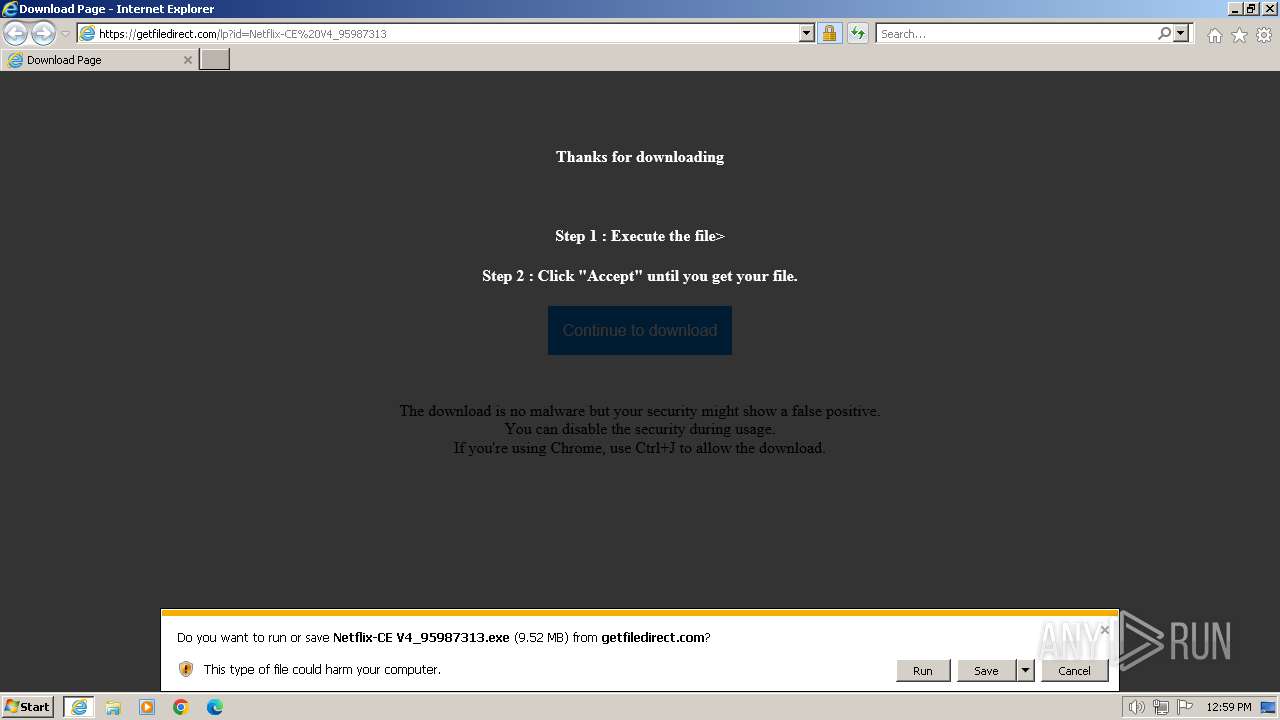
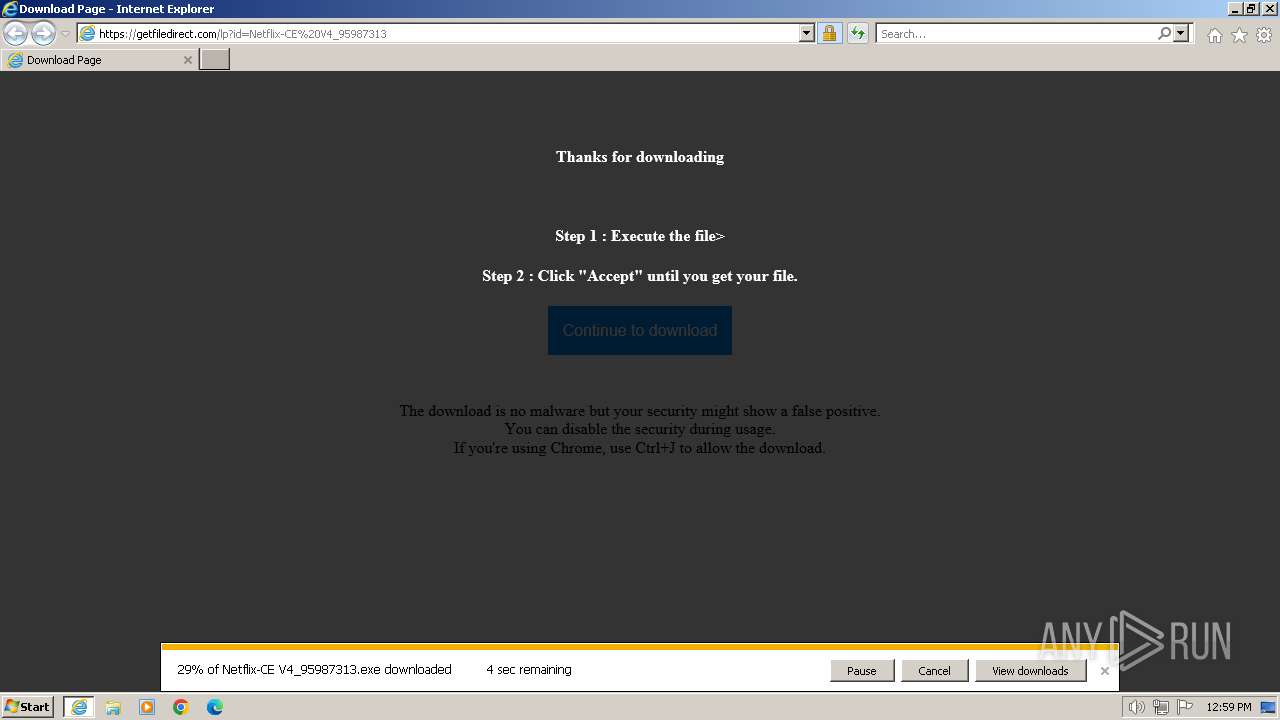
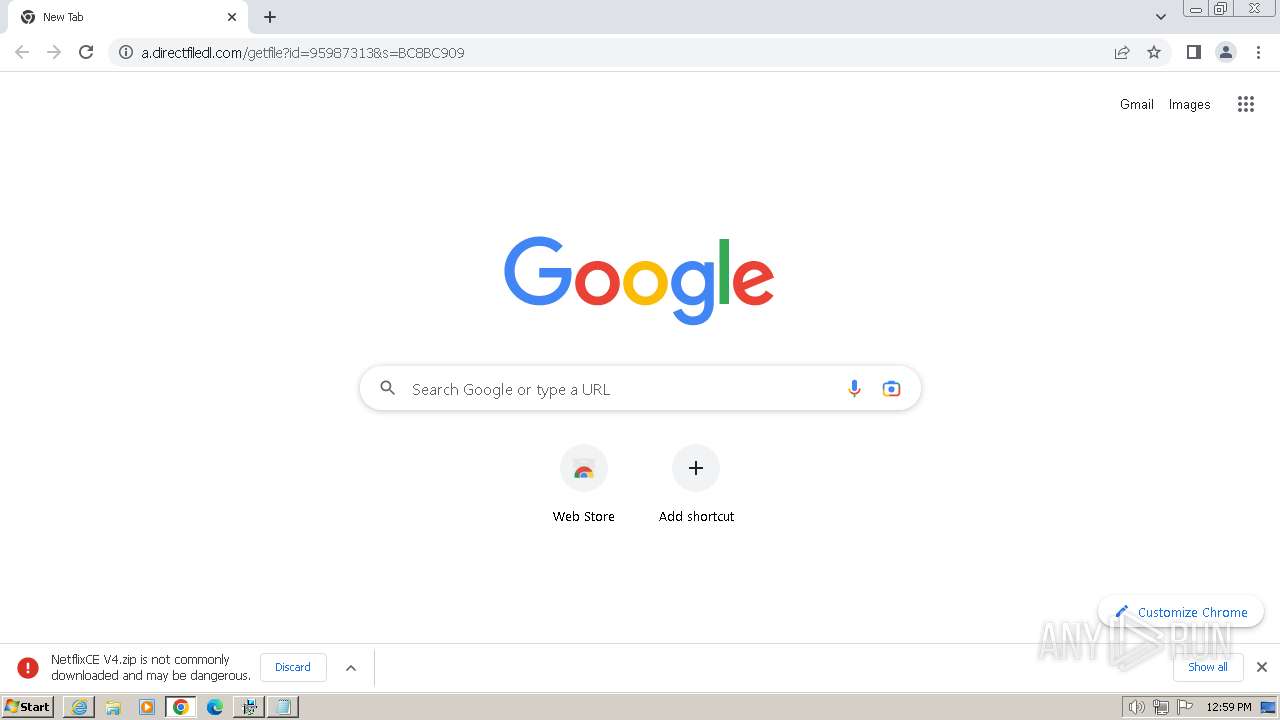
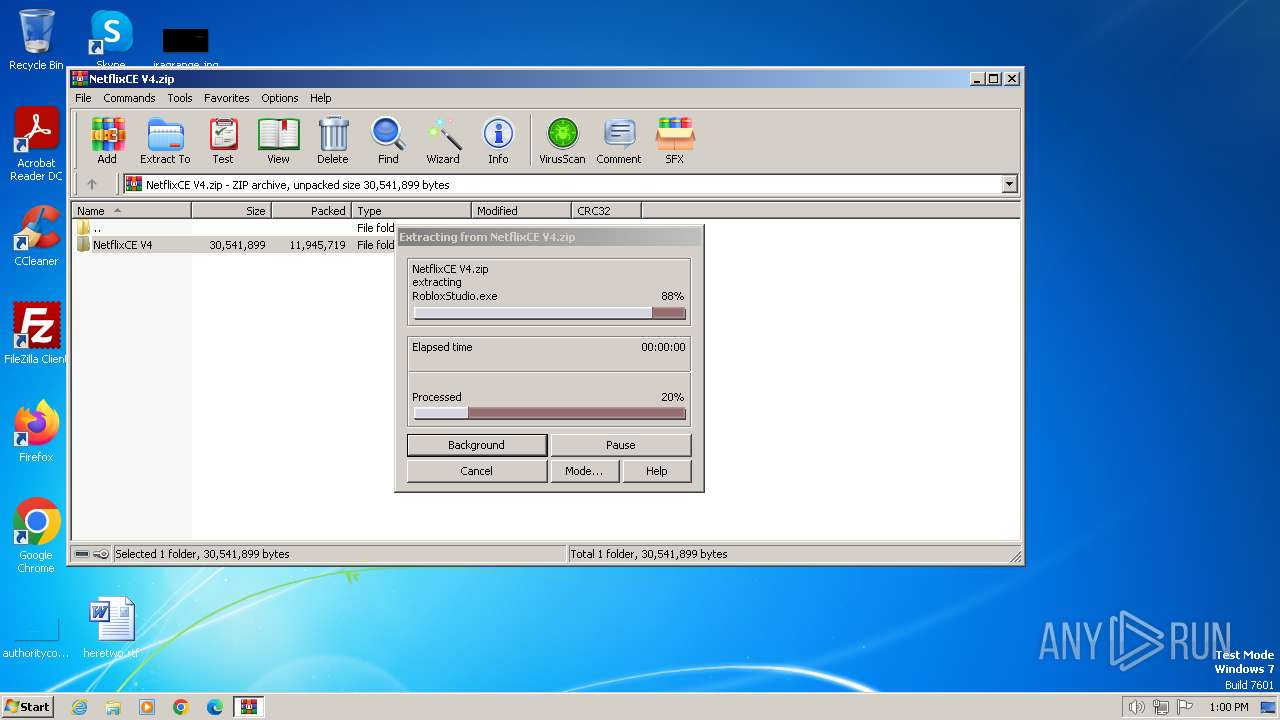
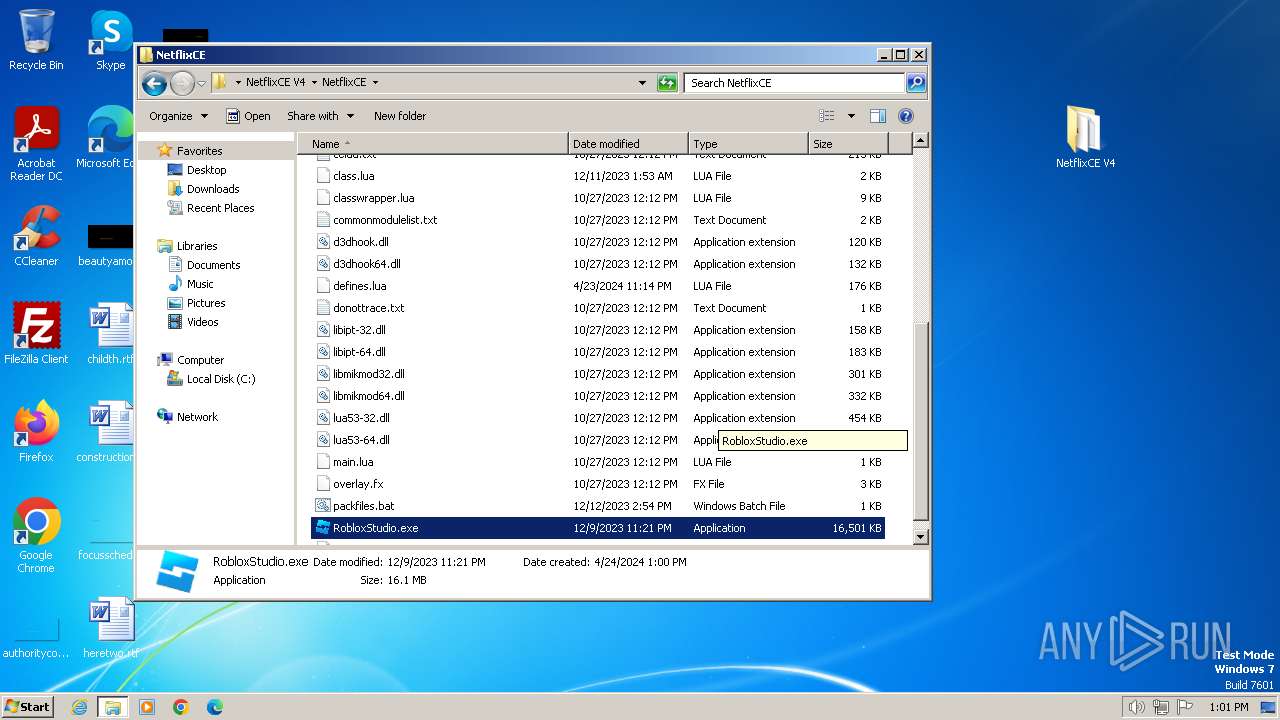
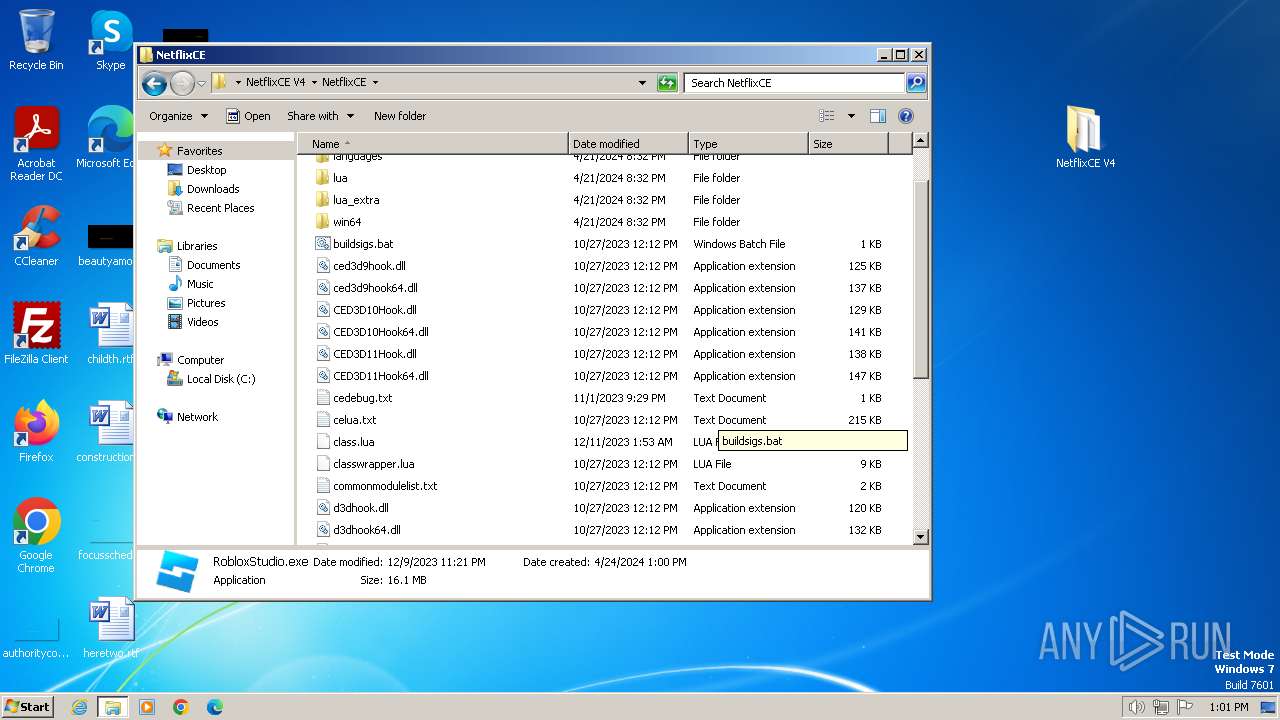
Drops the executable file immediately after the start
- Netflix-CE V4_95987313.exe (PID: 3804)
- setup95987313.exe (PID: 2564)
Actions looks like stealing of personal data
- setup95987313.exe (PID: 2564)
SUSPICIOUS
Reads the Internet Settings
- Netflix-CE V4_95987313.exe (PID: 3804)
- setup95987313.exe (PID: 2564)
- setup95987313.exe (PID: 3716)
Reads settings of System Certificates
- Netflix-CE V4_95987313.exe (PID: 3804)
- setup95987313.exe (PID: 2564)
Reads security settings of Internet Explorer
- Netflix-CE V4_95987313.exe (PID: 3804)
- setup95987313.exe (PID: 2564)
- setup95987313.exe (PID: 3716)
Executable content was dropped or overwritten
- Netflix-CE V4_95987313.exe (PID: 3804)
- setup95987313.exe (PID: 2564)
Checks Windows Trust Settings
- Netflix-CE V4_95987313.exe (PID: 3804)
- setup95987313.exe (PID: 2564)
Process drops legitimate windows executable
- setup95987313.exe (PID: 2564)
- WinRAR.exe (PID: 1768)
The process creates files with name similar to system file names
- setup95987313.exe (PID: 2564)
The process drops C-runtime libraries
- setup95987313.exe (PID: 2564)
Reads the Windows owner or organization settings
- setup95987313.exe (PID: 2564)
Adds/modifies Windows certificates
- setup95987313.exe (PID: 2564)
Searches for installed software
- setup95987313.exe (PID: 2564)
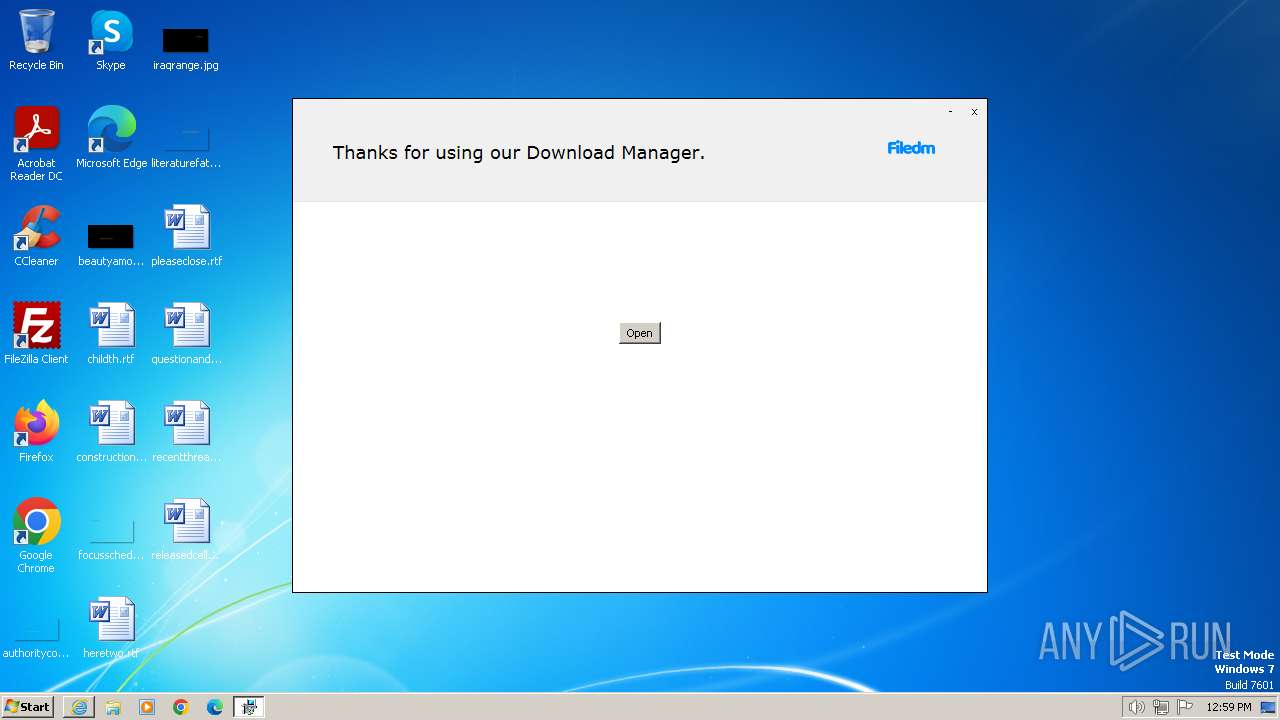
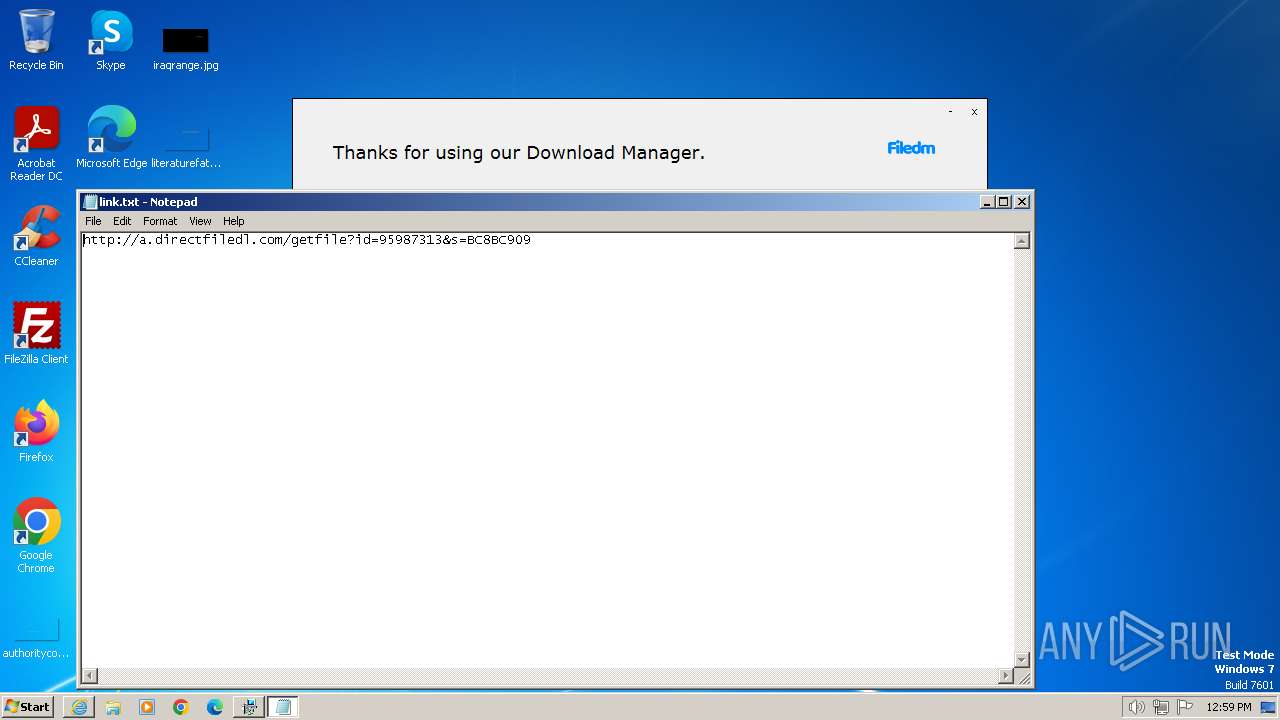
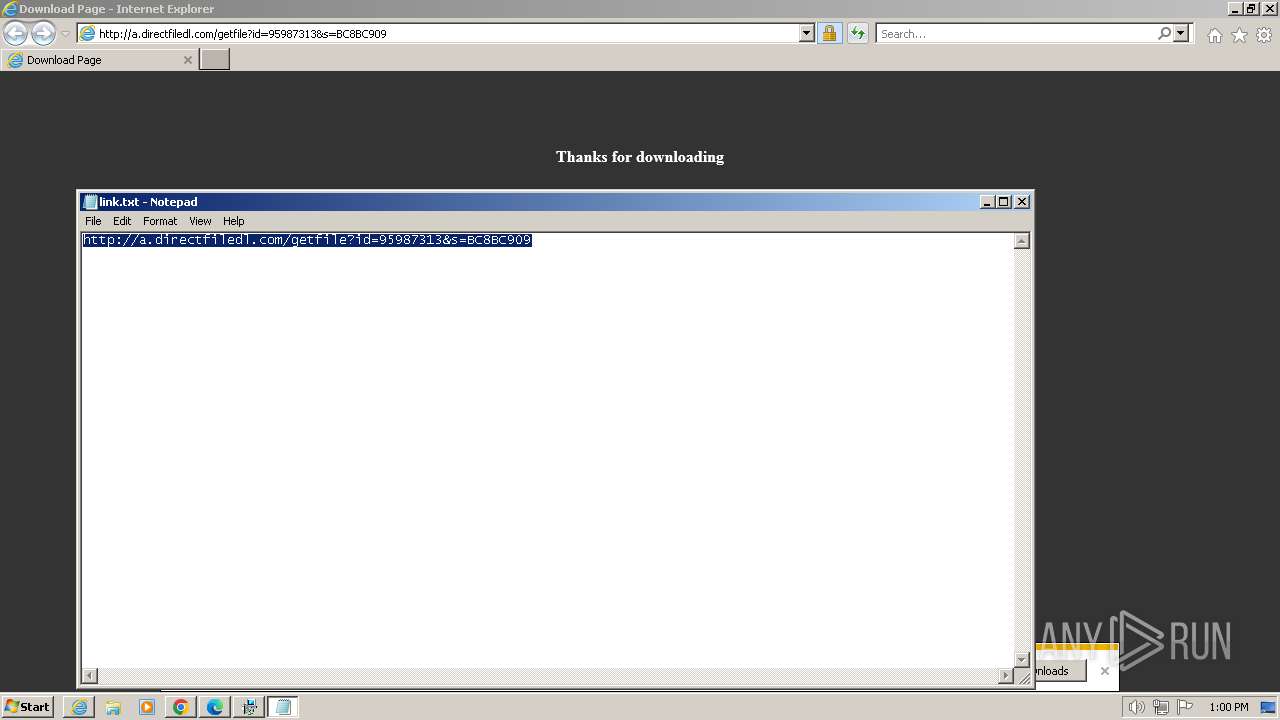
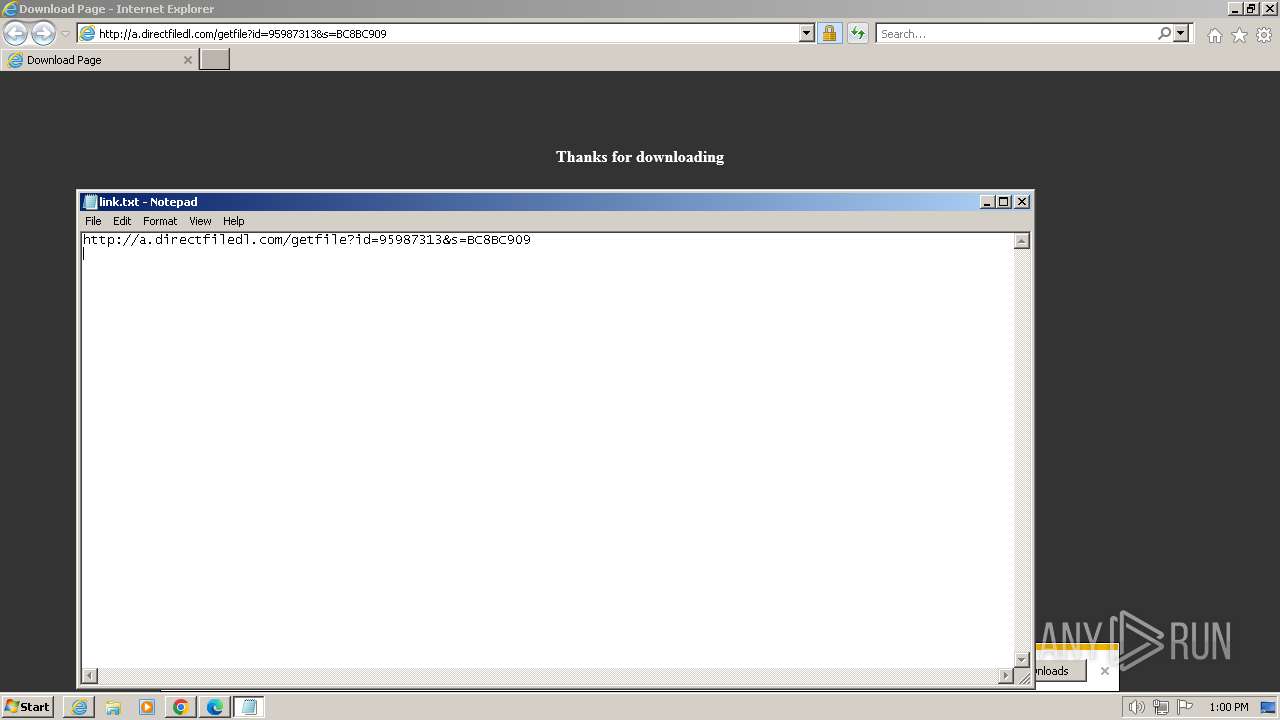
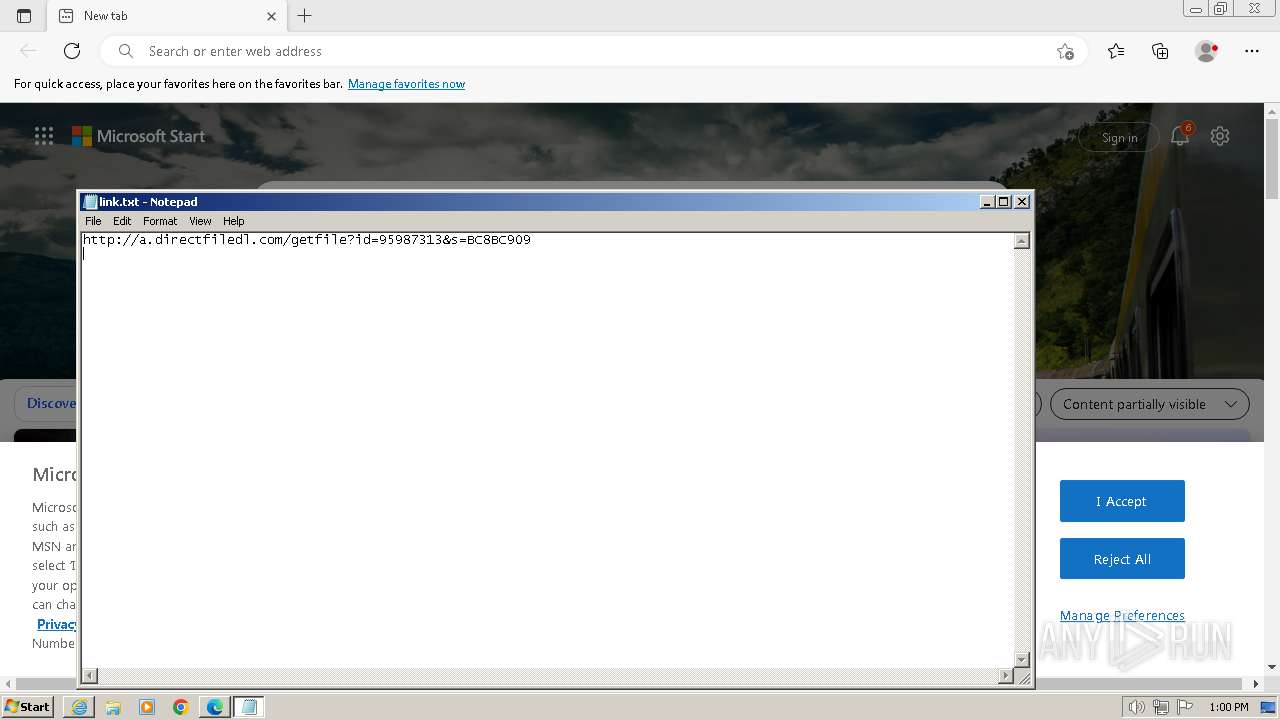
Start notepad (likely ransomware note)
- Netflix-CE V4_95987313.exe (PID: 3804)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 292)
Starts CMD.EXE for commands execution
- setup95987313.exe (PID: 2564)
Process drops SQLite DLL files
- WinRAR.exe (PID: 1768)
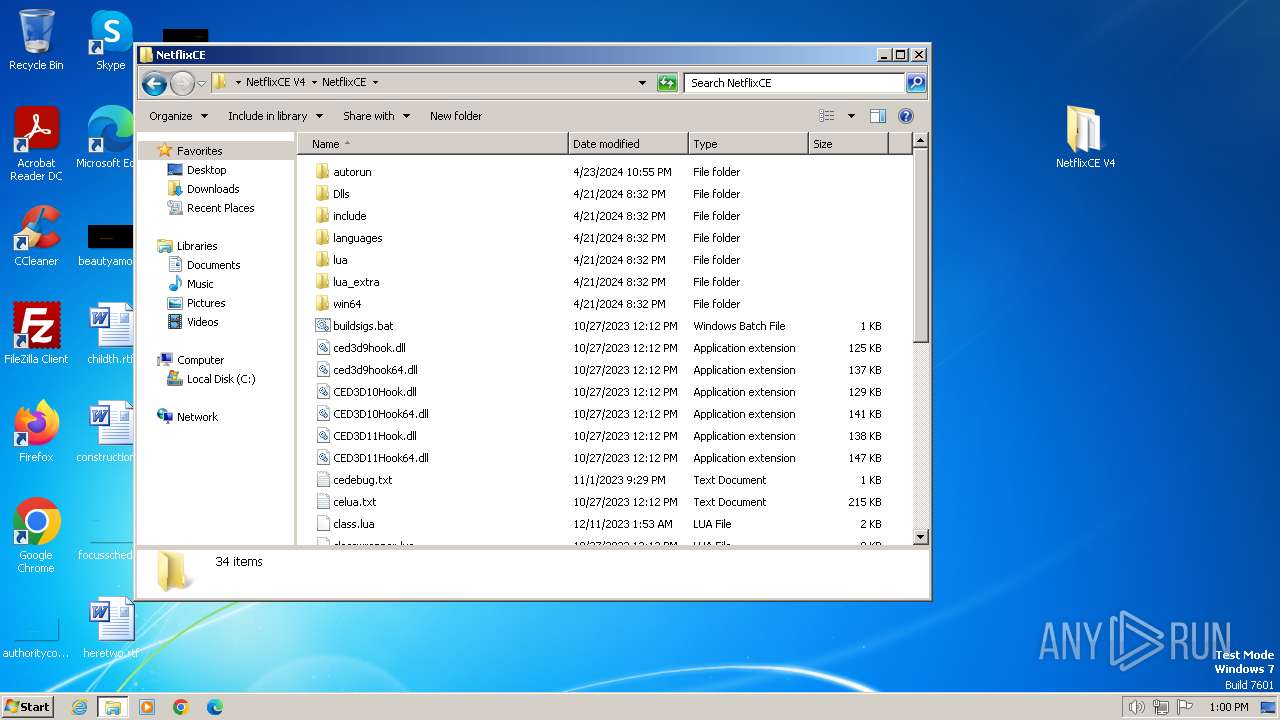
Executing commands from a ".bat" file
- setup95987313.exe (PID: 2564)
Get information on the list of running processes
- cmd.exe (PID: 292)
INFO
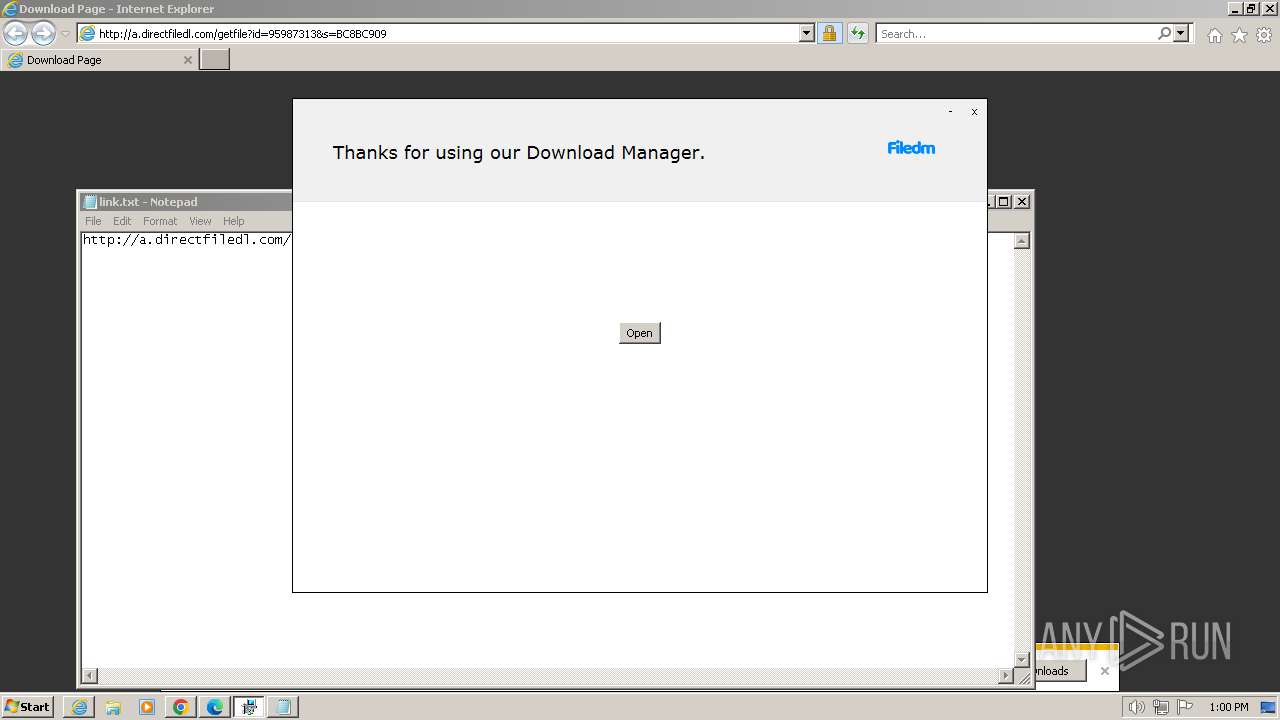
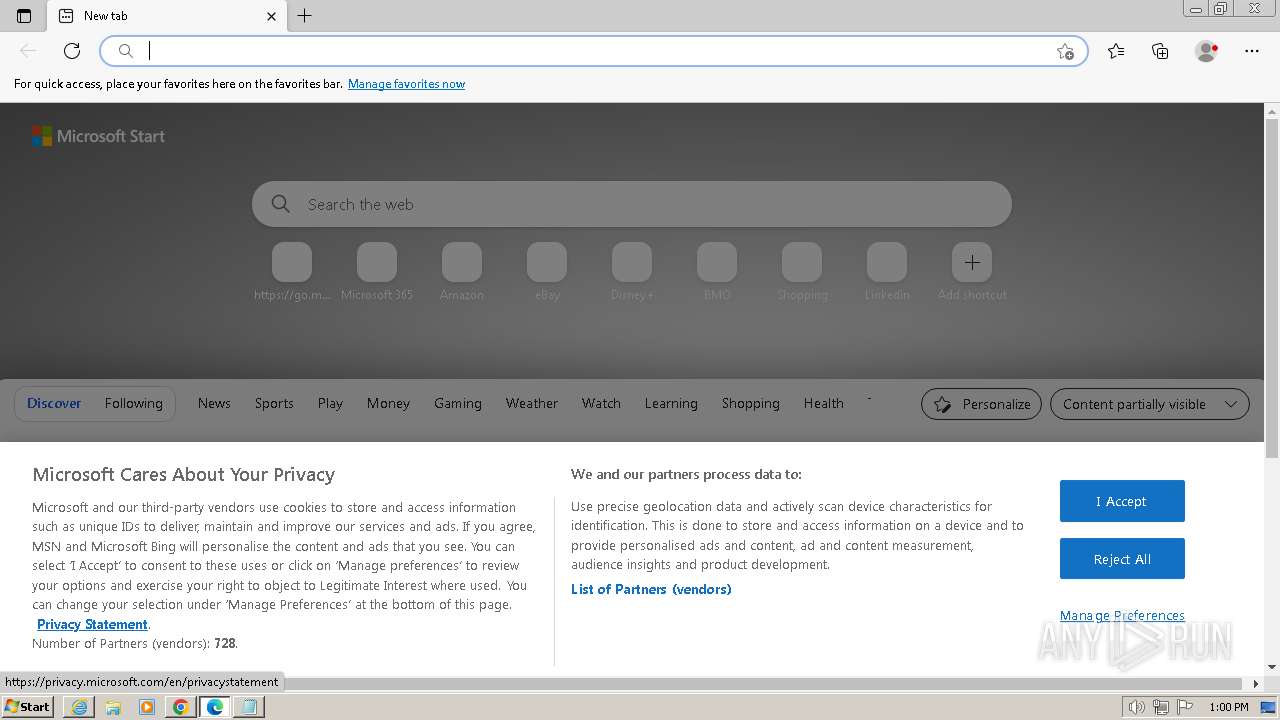
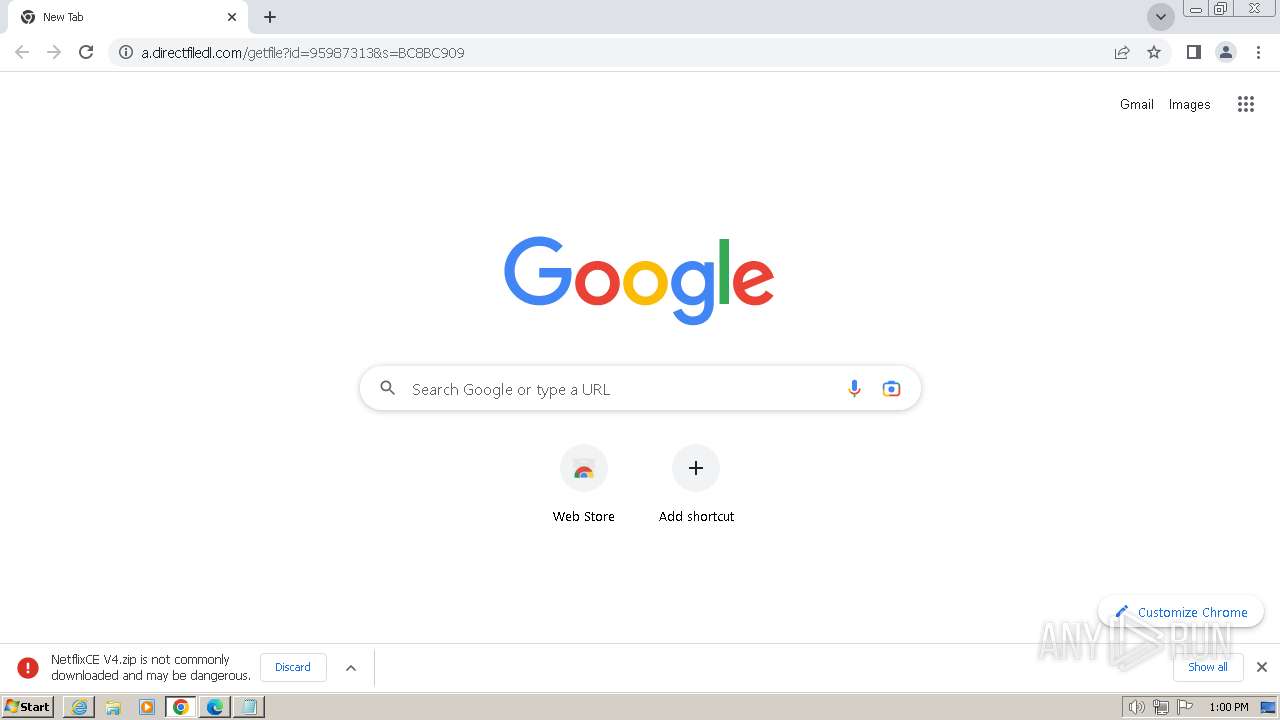
Application launched itself
- iexplore.exe (PID: 668)
- chrome.exe (PID: 3732)
- msedge.exe (PID: 3436)
Modifies the phishing filter of IE
- iexplore.exe (PID: 668)
Executable content was dropped or overwritten
- iexplore.exe (PID: 668)
- iexplore.exe (PID: 3384)
- WinRAR.exe (PID: 1768)
Reads the computer name
- Netflix-CE V4_95987313.exe (PID: 3804)
- setup95987313.exe (PID: 2564)
- setup95987313.exe (PID: 3716)
- wmpnscfg.exe (PID: 2848)
The process uses the downloaded file
- iexplore.exe (PID: 668)
- WinRAR.exe (PID: 1768)
Drops the executable file immediately after the start
- iexplore.exe (PID: 668)
- iexplore.exe (PID: 3384)
- chrome.exe (PID: 3732)
- WinRAR.exe (PID: 1768)
Checks supported languages
- Netflix-CE V4_95987313.exe (PID: 3804)
- setup95987313.exe (PID: 2564)
- setup95987313.exe (PID: 3716)
- wmpnscfg.exe (PID: 2848)
Checks proxy server information
- Netflix-CE V4_95987313.exe (PID: 3804)
Reads the software policy settings
- Netflix-CE V4_95987313.exe (PID: 3804)
- setup95987313.exe (PID: 2564)
Reads the machine GUID from the registry
- Netflix-CE V4_95987313.exe (PID: 3804)
- setup95987313.exe (PID: 2564)
- setup95987313.exe (PID: 3716)
Creates files or folders in the user directory
- Netflix-CE V4_95987313.exe (PID: 3804)
- setup95987313.exe (PID: 2564)
Create files in a temporary directory
- setup95987313.exe (PID: 2564)
- setup95987313.exe (PID: 3716)
Reads Environment values
- setup95987313.exe (PID: 2564)
Reads product name
- setup95987313.exe (PID: 2564)
Manual execution by a user
- chrome.exe (PID: 3732)
- wmpnscfg.exe (PID: 2848)
- msedge.exe (PID: 3436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
84
Monitored processes
38
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\H2OCleanup.bat"" | C:\Windows\System32\cmd.exe | — | setup95987313.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 548 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x69cbf598,0x69cbf5a8,0x69cbf5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 560 | timeout 5 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x61a18b38,0x61a18b48,0x61a18b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://getfiledirect.com/lp?id=Netflix-CE%20V4_95987313" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1448 --field-trial-handle=1100,i,10199641237083182895,8381044180024455709,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3576 --field-trial-handle=1100,i,10199641237083182895,8381044180024455709,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2136 --field-trial-handle=1100,i,10199641237083182895,8381044180024455709,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3656 --field-trial-handle=1172,i,9763427887858789502,10016502209723709351,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
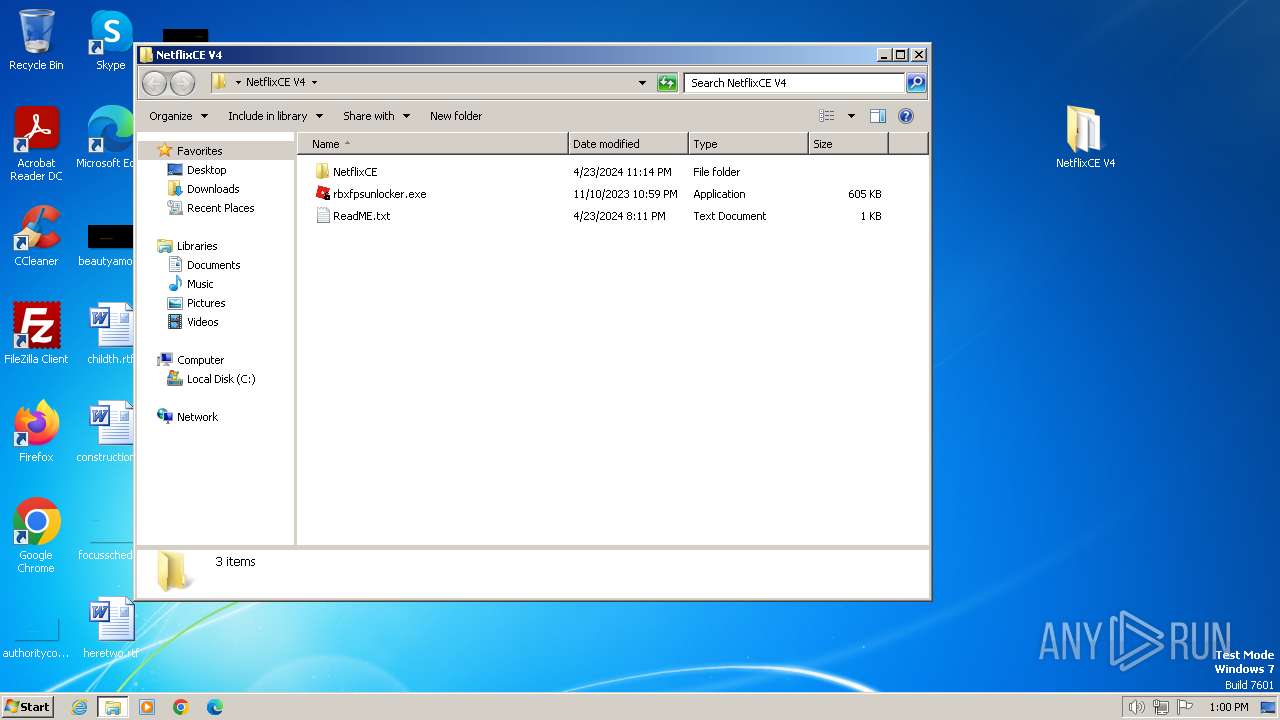
| 1768 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\NetflixCE V4.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
55 529
Read events
55 127
Write events
321
Delete events
81
Modification events
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31102526 | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31102526 | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
57
Suspicious files
202
Text files
375
Unknown types
54
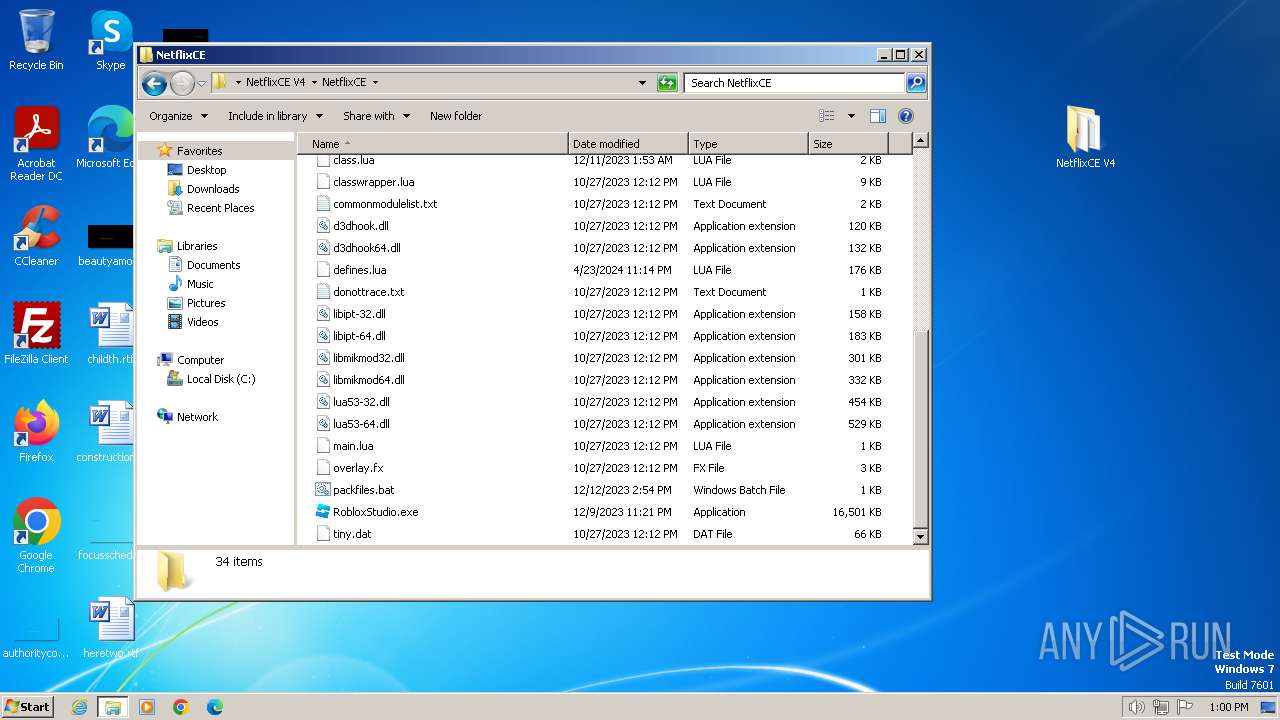
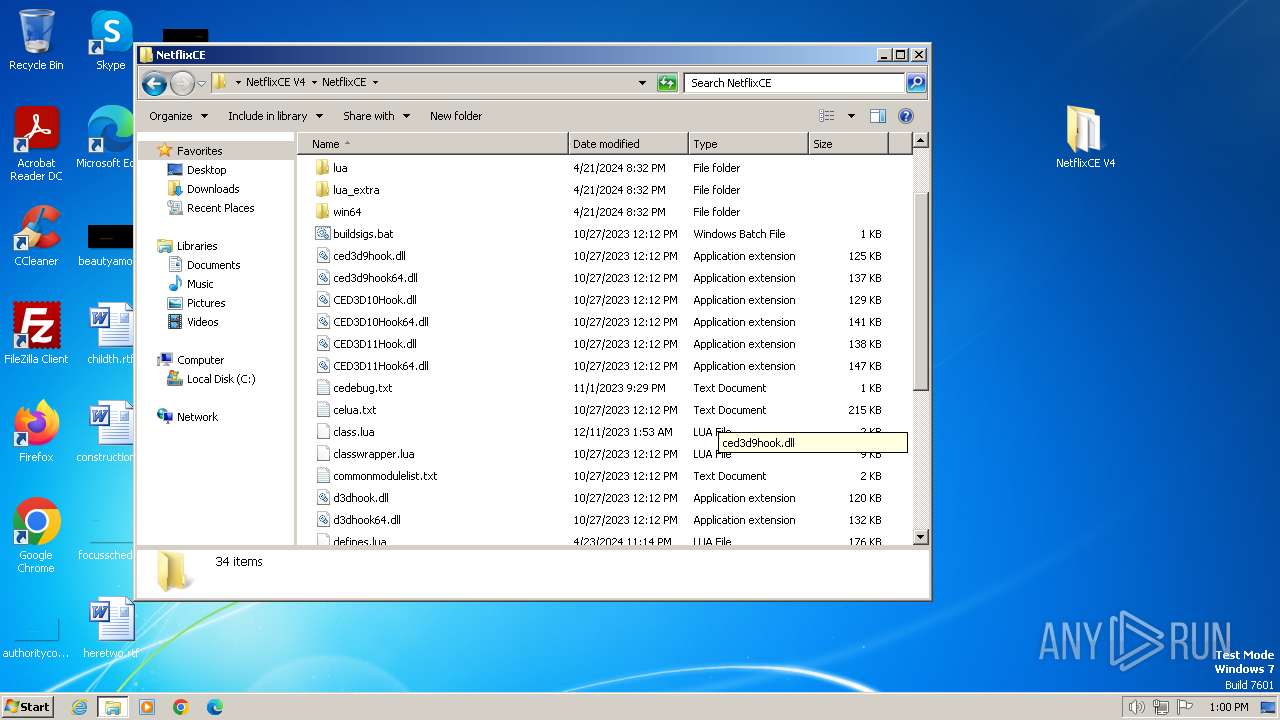
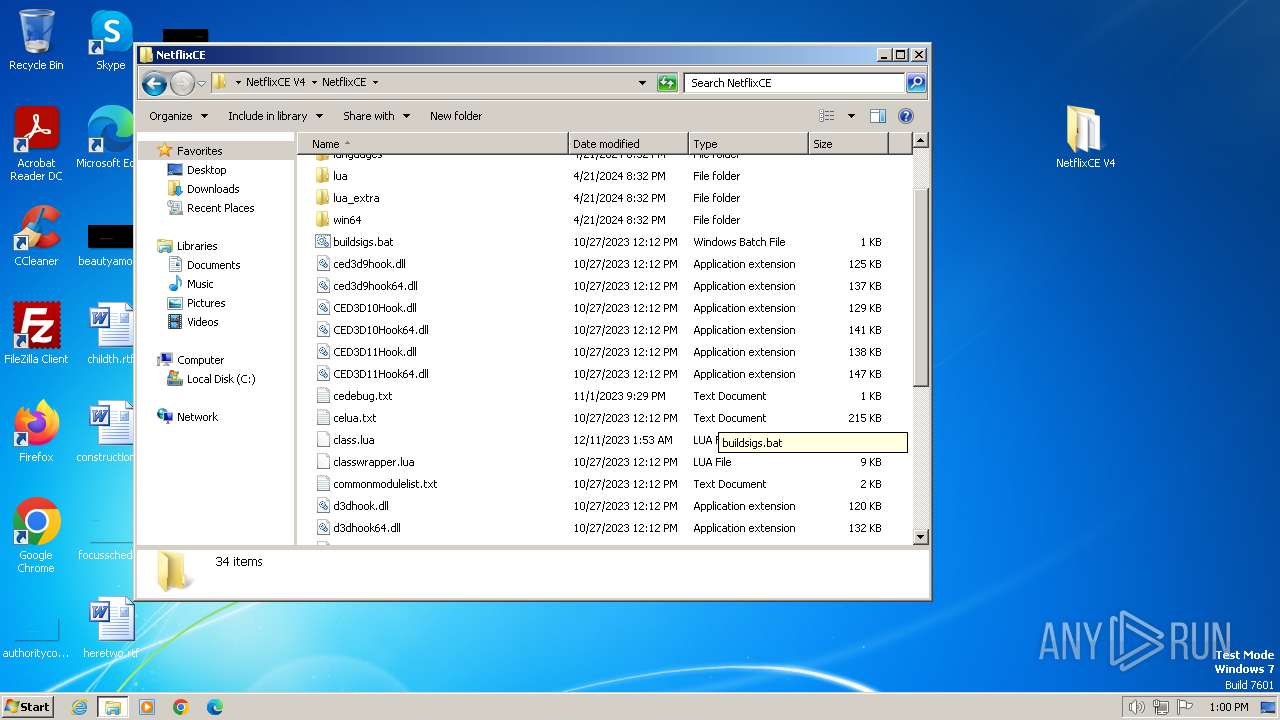
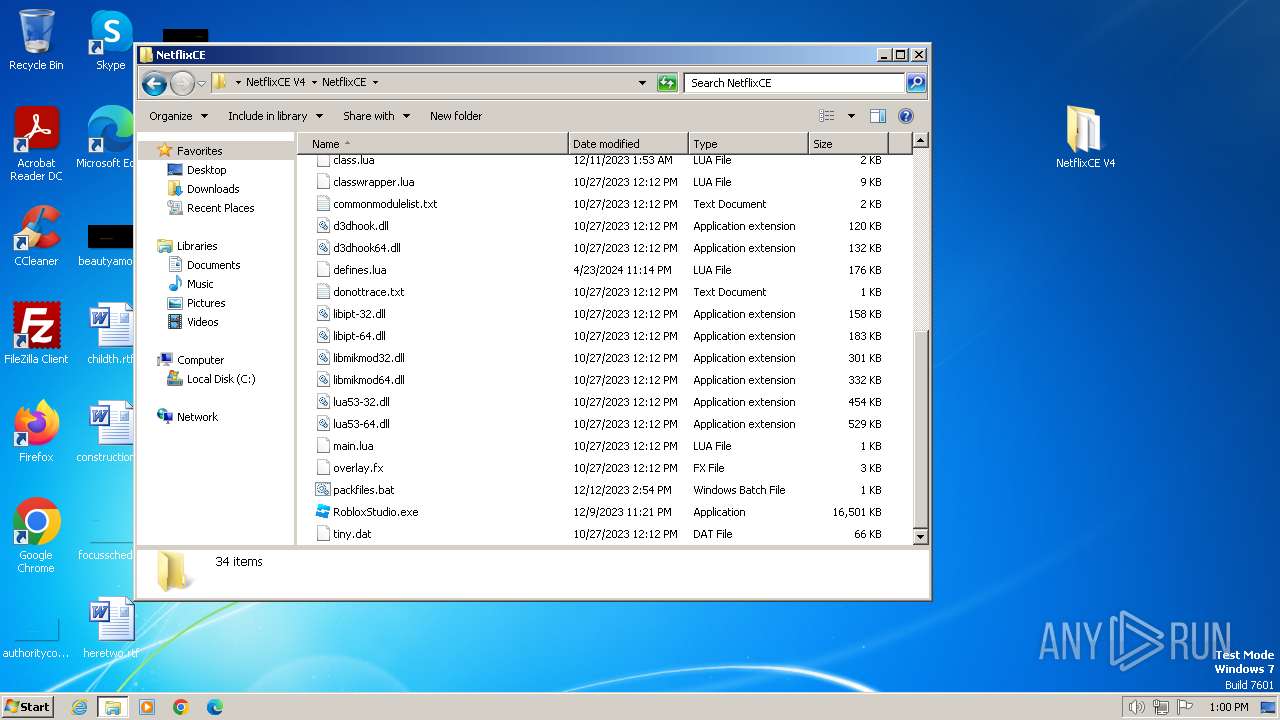
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:BC4EEDE67436F3EAC9B1A4494FC9AF20 | SHA256:AE5AC25996E73C71DF31371FDDE66BB0219B051E50AF4A2B6814F8B9DFE2A8A7 | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | der | |
MD5:5AE8478AF8DD6EEC7AD4EDF162DD3DF1 | SHA256:FE42AC92EAE3B2850370B73C3691CCF394C23AB6133DE39F1697A6EBAC4BEDCA | |||
| 668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:09DC6DE82E5E23C882CBB9110F94265F | SHA256:5F1D352111D9CE1CFCA8FD34AE9F16560DF74EFDCBB4BC7A01E01DCDBB1D68A9 | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:29F65BA8E88C063813CC50A4EA544E93 | SHA256:1ED81FA8DFB6999A9FEDC6E779138FFD99568992E22D300ACD181A6D2C8DE184 | |||
| 668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | der | |
MD5:EB6AC869DB45FDCAC124B22AC7128B56 | SHA256:BFB060F60268B5AD7FBB0D4F234465F949C9AEA069B24AE6E22C7FB3FCF037DA | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarD63B.tmp | cat | |
MD5:435A9AC180383F9FA094131B173A2F7B | SHA256:67DC37ED50B8E63272B49A254A6039EE225974F1D767BB83EB1FD80E759A7C34 | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:1FB2882807160A417F3F27FDC365EDCF | SHA256:4870A791B0FFA17EABD89A8ABAA107A29DAFB02C66220E87A911AA3B2D225172 | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarD629.tmp | cat | |
MD5:435A9AC180383F9FA094131B173A2F7B | SHA256:67DC37ED50B8E63272B49A254A6039EE225974F1D767BB83EB1FD80E759A7C34 | |||
| 668 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
91
DNS requests
111
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3384 | iexplore.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?13701d01566341eb | unknown | — | — | unknown |
3384 | iexplore.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7f68a02ba6df2d36 | unknown | — | — | unknown |
3384 | iexplore.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?645a241442c7e609 | unknown | — | — | unknown |
3384 | iexplore.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?bddd04696ddfc96b | unknown | — | — | unknown |
3384 | iexplore.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
3384 | iexplore.exe | GET | 200 | 72.246.169.163:80 | http://x2.c.lencr.org/ | unknown | — | — | unknown |
668 | iexplore.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ea3c55793538016f | unknown | — | — | unknown |
668 | iexplore.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?abc3609693924bbb | unknown | — | — | unknown |
668 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
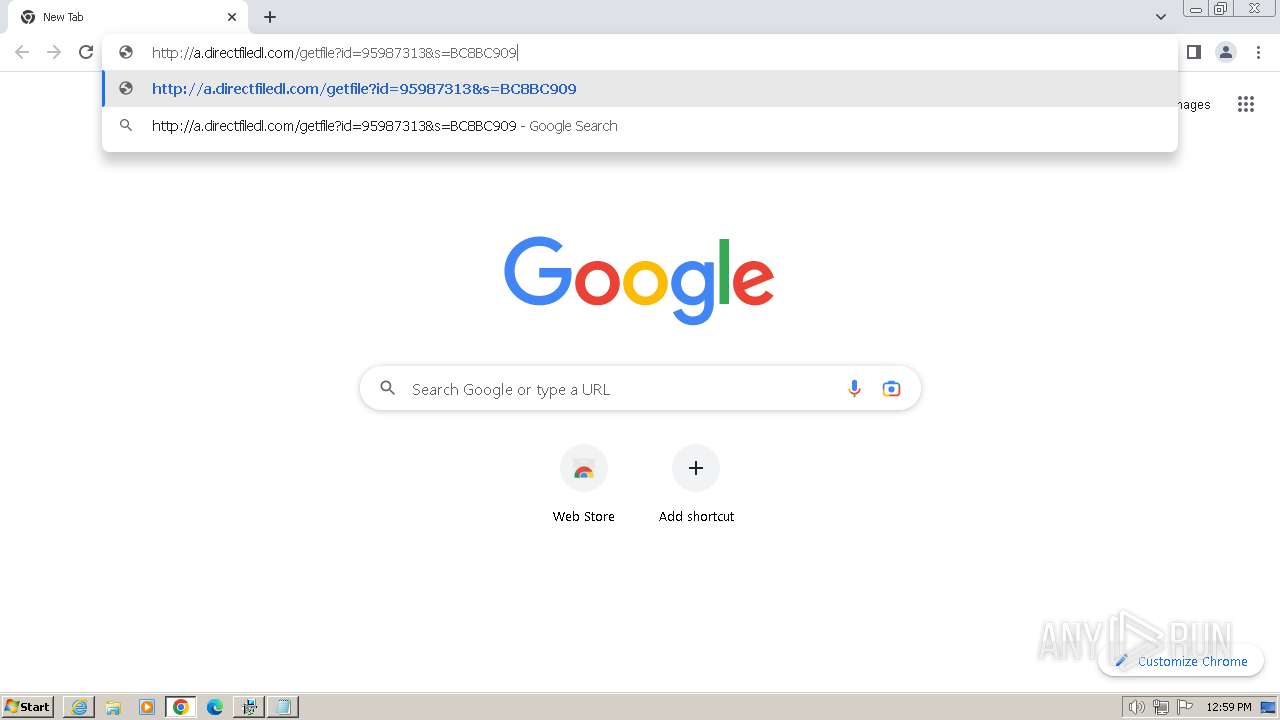
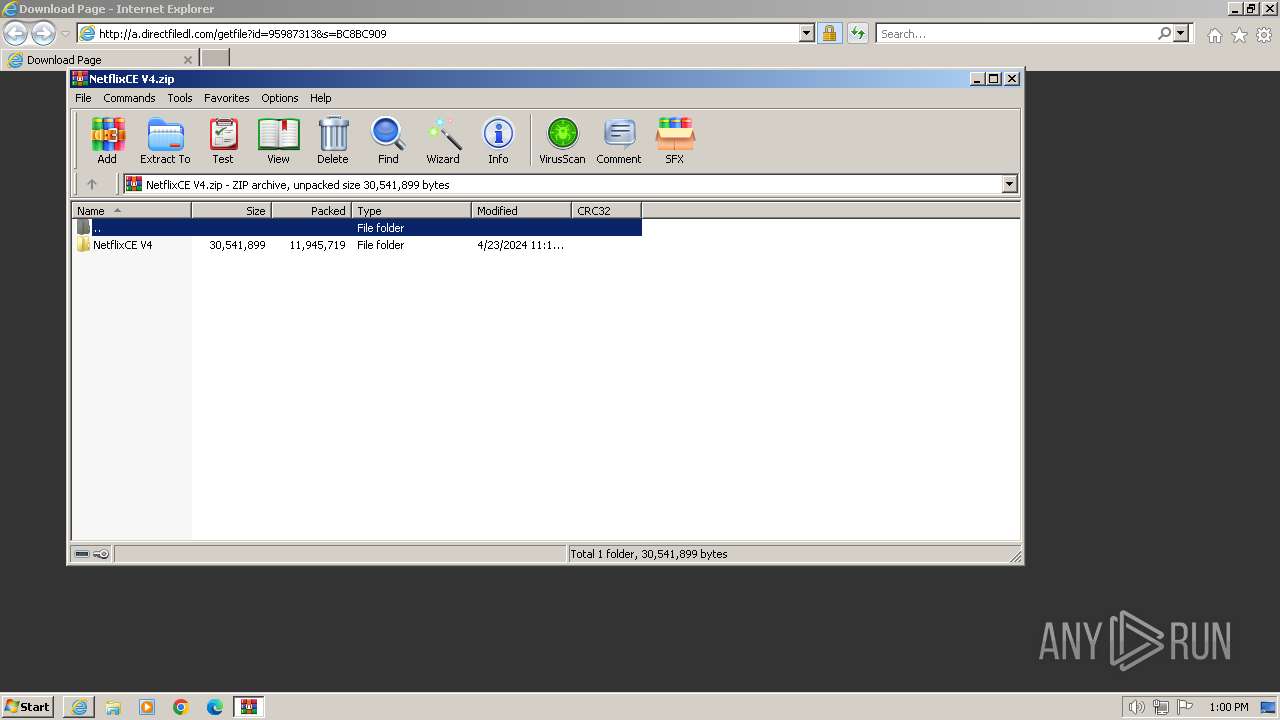
876 | chrome.exe | GET | 200 | 167.235.218.62:80 | http://a.directfiledl.com/getfile?id=95987313&s=BC8BC909 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3384 | iexplore.exe | 188.114.97.3:443 | getfiledirect.com | CLOUDFLARENET | NL | unknown |
3384 | iexplore.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
3384 | iexplore.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
3384 | iexplore.exe | 72.246.169.163:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
668 | iexplore.exe | 188.114.97.3:443 | getfiledirect.com | CLOUDFLARENET | NL | unknown |
668 | iexplore.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
668 | iexplore.exe | 184.86.251.20:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
getfiledirect.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.dlsft.com |
| unknown |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| whitelisted |
Threats
8 ETPRO signatures available at the full report
Process | Message |
|---|---|
Netflix-CE V4_95987313.exe | at initializeDynamicVariables (this://app/main.html(329))
|
Netflix-CE V4_95987313.exe | |
Netflix-CE V4_95987313.exe | |
Netflix-CE V4_95987313.exe | Error: (undefined) has no property - value
|
Netflix-CE V4_95987313.exe | at getFileInfo.@285@39 (this://app/main.html(307))
|
setup95987313.exe | Error: File not found - sciterwrapper:console.tis
|
setup95987313.exe | |
setup95987313.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|
setup95987313.exe | at sciter:init-script.tis
|
setup95987313.exe | |