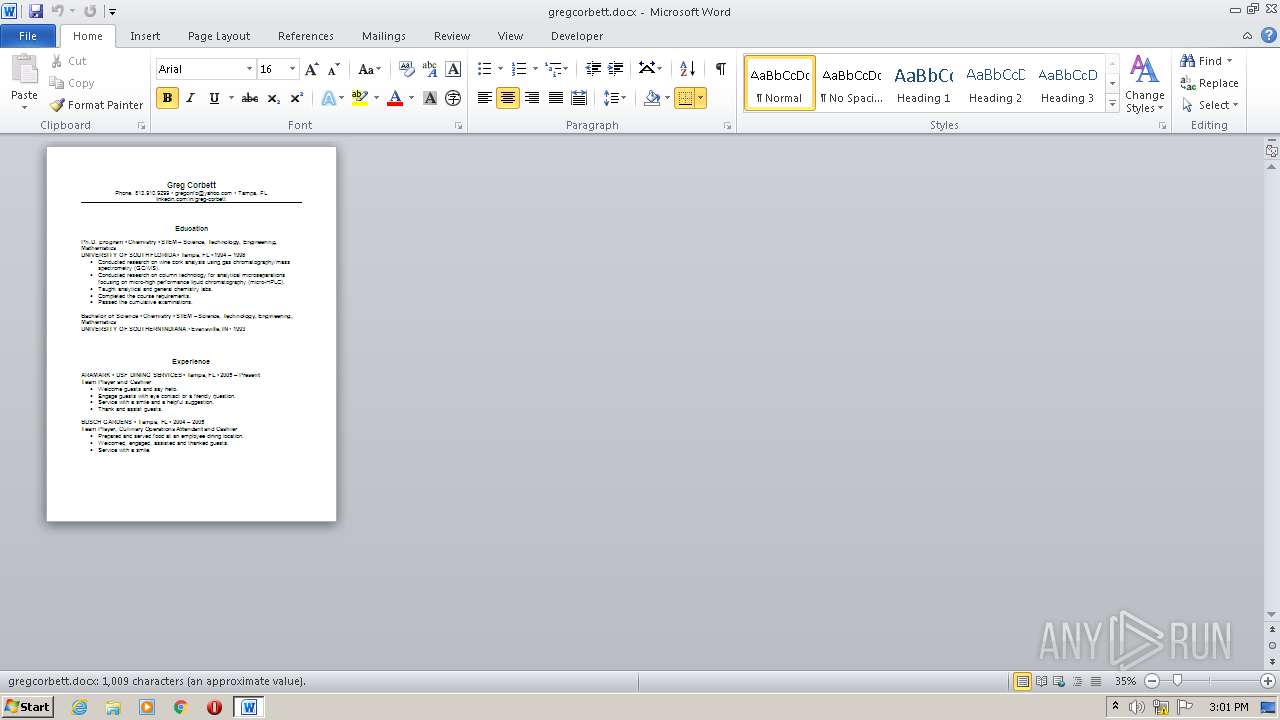
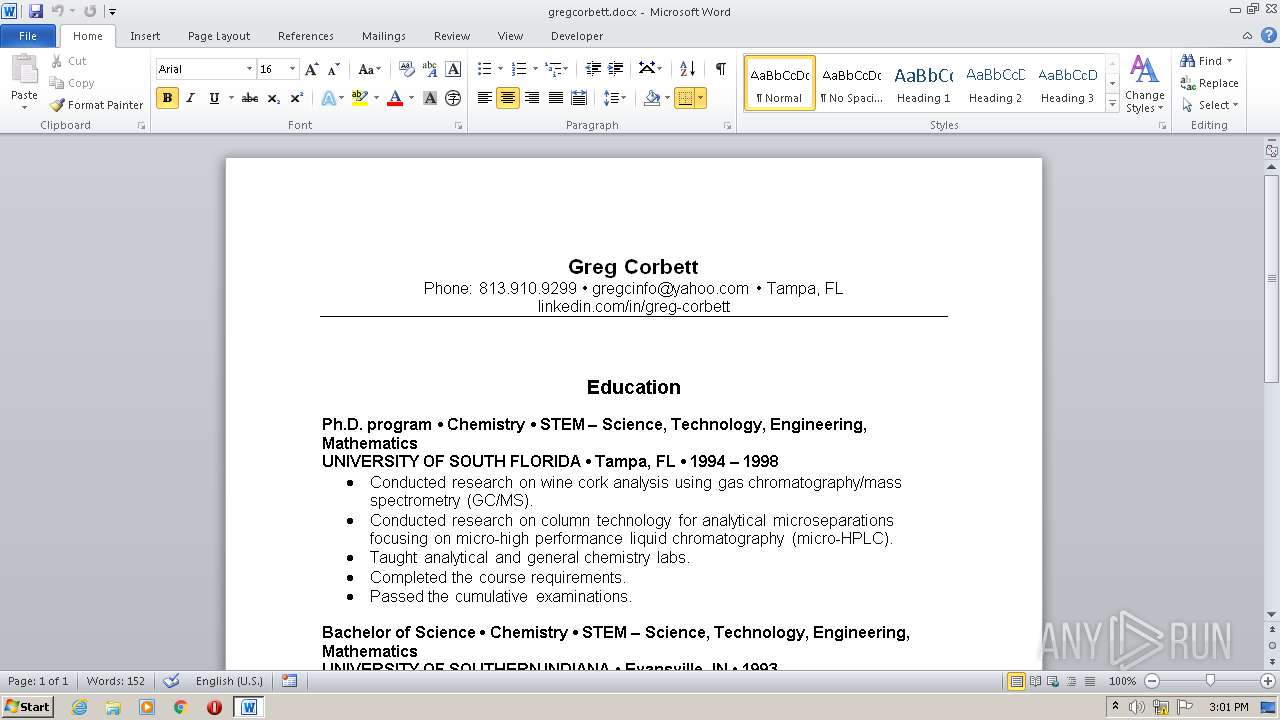
| File name: | gregcorbett.docx |
| Full analysis: | https://app.any.run/tasks/0630fcd3-c484-4d6f-8c57-e36017f470be |
| Verdict: | No threats detected |
| Analysis date: | August 24, 2020, 14:01:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 3A0FDEED15393368A17AF86012D4AB7C |
| SHA1: | AAF167011256AC324C900A212FB36FA9E0191837 |
| SHA256: | 7646799C6B3ACF68E3A92ED843D79019493AB071E9B00C2704A9A27F8C7FA4B1 |
| SSDEEP: | 768:GycEQIjPAlDKjsgS+S+ixfqMDcdtog+/PMS:0EQwAUjKt+ixfRzsS |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2248)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x393d6f2a |
| ZipCompressedSize: | 404 |
| ZipUncompressedSize: | 1981 |
| ZipFileName: | [Content_Types].xml |
XML
| InternalTags: | - |
|---|---|
| ContentTypeId: | 0x0101006EDDDB5EE6D98C44930B742096920B300400F5B6D36B3EF94B4E9A635CDF2A18F5B8 |
| FeatureTags: | - |
| LocalizationTags: | - |
| CampaignTags: | - |
| ScenarioTags: | - |
| LocLastLocAttemptVersionTypeLookup: | - |
| MarketSpecific: | - |
| ApprovalStatus: | InProgress |
| LocComments: | - |
| DirectSourceMarket: | - |
| LocPublishedLinkedAssetsLookup: | - |
| ThumbnailAssetId: | - |
| PrimaryImageGen: | 1 |
| LegacyData: | - |
| LocNewPublishedVersionLookup: | - |
| NumericId: | 102787001 |
| TPFriendlyName: | - |
| LocOverallPublishStatusLookup: | - |
| LocRecommendedHandoff: | - |
| BlockPublish: | - |
| BusinessGroup: | - |
| OpenTemplate: | 1 |
| SourceTitle: | - |
| LocOverallLocStatusLookup: | - |
| APEditor: | - |
| UALocComments: | - |
| IntlLangReviewDate: | - |
| PublishStatusLookup: | 1343188;# |
| ParentAssetId: | - |
| FeatureTagsTaxHTField0: | - |
| MachineTranslated: | - |
| Providers: | - |
| OriginalSourceMarket: | - |
| APDescription: | - |
| ContentItem: | - |
| ClipArtFilename: | - |
| TPInstallLocation: | - |
| TimesCloned: | - |
| PublishTargets: | OfficeOnlineVNext |
| AcquiredFrom: | Internal MS |
| AssetStart: | 2011-11-23T12:29:00Z |
| FriendlyTitle: | - |
| Provider: | - |
| LastHandOff: | - |
| TPClientViewer: | - |
| TemplateStatus: | Complete |
| Downloads: | - |
| OOCacheId: | - |
| IsDeleted: | - |
| LocPublishedDependentAssetsLookup: | - |
| AssetExpire: | 2029-05-12T03:00:00Z |
| CSXSubmissionMarket: | - |
| DSATActionTaken: | - |
| SubmitterId: | - |
| EditorialTags: | - |
| TPExecutable: | - |
| CSXSubmissionDate: | - |
| CSXUpdate: | - |
| AssetType: | TP |
| ApprovalLog: | - |
| BugNumber: | - |
| OriginAsset: | - |
| TPComponent: | - |
| Milestone: | - |
| RecommendationsModifier: | - |
| AssetId: | TP102787001 |
| PolicheckWords: | - |
| TPLaunchHelpLink: | - |
| IntlLocPriority: | - |
| TPApplication: | - |
| IntlLangReviewer: | - |
| HandoffToMSDN: | - |
| PlannedPubDate: | - |
| CrawlForDependencies: | - |
| LocLastLocAttemptVersionLookup: | 693888 |
| LocProcessedForHandoffsLookup: | - |
| TrustLevel: | 1 Microsoft Managed Content |
| CampaignTagsTaxHTField0: | - |
| TPNamespace: | - |
| LocOverallPreviewStatusLookup: | - |
| TaxCatchAll: | - |
| IsSearchable: | - |
| TemplateTemplateType: | Word Document Template |
| Markets: | - |
| IntlLangReview: | - |
| UAProjectedTotalWords: | - |
| OutputCachingOn: | - |
| AverageRating: | - |
| LocMarketGroupTiers2: | - |
| APAuthor: | 978;#REDMOND\v-namall |
| TPCommandLine: | - |
| LocManualTestRequired: | - |
| TPAppVersion: | - |
| EditorialStatus: | Complete |
| LocProcessedForMarketsLookup: | - |
| LastModifiedDateTime: | - |
| TPLaunchHelpLinkType: | Template |
| ScenarioTagsTaxHTField0: | - |
| OriginalRelease: | 14 |
| LocalizationTagsTaxHTField0: | - |
| Manager: | - |
| UALocRecommendation: | Localize |
| LocOverallHandbackStatusLookup: | - |
| ArtSampleDocs: | - |
| UACurrentWords: | - |
| ShowIn: | Show everywhere |
| CSXHash: | - |
| VoteCount: | - |
| InternalTagsTaxHTField0: | - |
| UANotes: | - |
| Keywords: | - |
| LastModifiedBy: | gregcinfo@yahoo.com |
| RevisionNumber: | 10 |
| CreateDate: | 2020:08:17 20:38:00Z |
| ModifyDate: | 2020:08:17 20:45:00Z |
| Template: | Single%20spaced%20(blank).dotx |
| TotalEditTime: | 7 minutes |
| Pages: | 1 |
| Words: | 182 |
| Characters: | 1042 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 8 |
| Paragraphs: | 2 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 1222 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | Singh, Akash |
| Description: | - |
Total processes
37
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2248 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\gregcorbett.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 906
Read events
882
Write events
900
Delete events
124
Modification events
| (PID) Process: | (2248) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | m)= |
Value: 6D293D00C8080000010000000000000000000000 | |||
| (PID) Process: | (2248) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2248) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2248) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2248) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2248) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2248) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2248) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2248) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2248) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE54D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\msoEC53.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$egcorbett.docx | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report