| File name: | 67df6dd1fec343d8823874bd8caf9df3 |
| Full analysis: | https://app.any.run/tasks/4618246e-d38f-43c0-9ecf-a617a5b45d7d |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 14:08:59 |
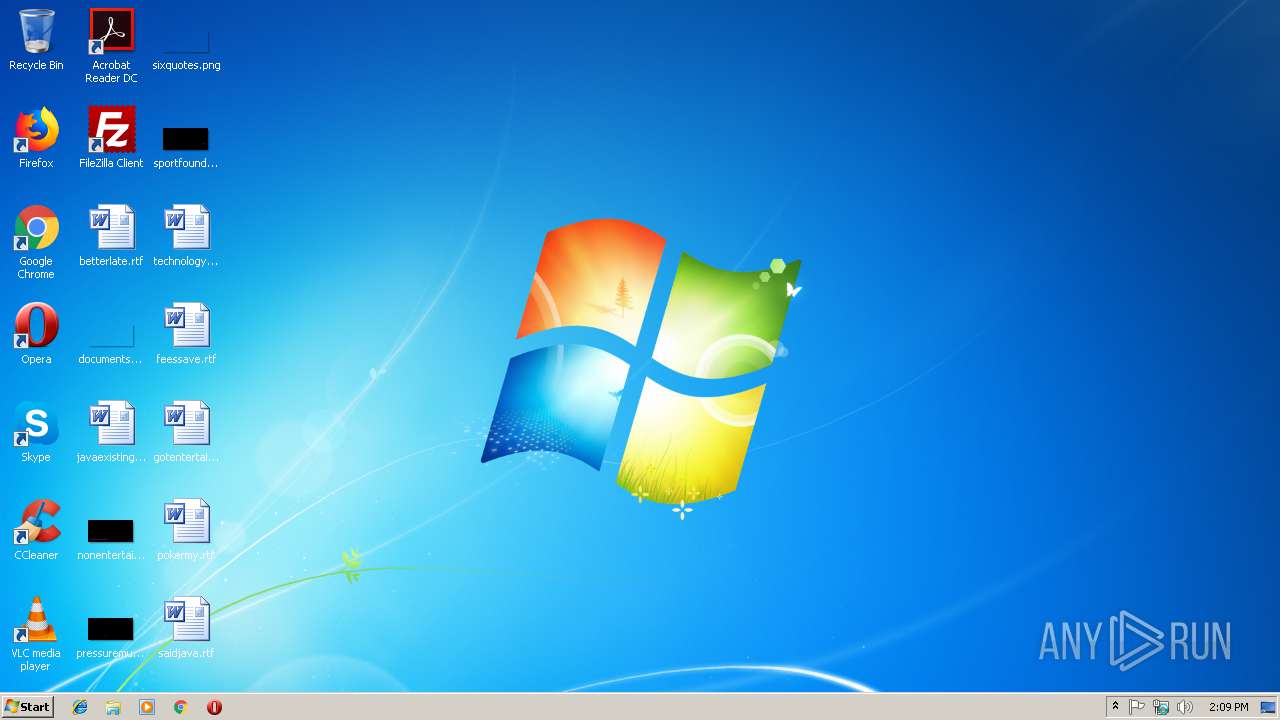
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 67DF6DD1FEC343D8823874BD8CAF9DF3 |
| SHA1: | FD43C75A44745CDF0AE40343A42B646677DC56A9 |
| SHA256: | 763AEE1EB43F82F6C9E7E5AB0EEBA3DEC619E4D45CE2EB26AFF14314E7F28EE8 |
| SSDEEP: | 49152:nX5V5bSIh5Robl+Gd6pzGg90o0TicZiZHhd:X75bSynocSQqgqZWHd |
MALICIOUS
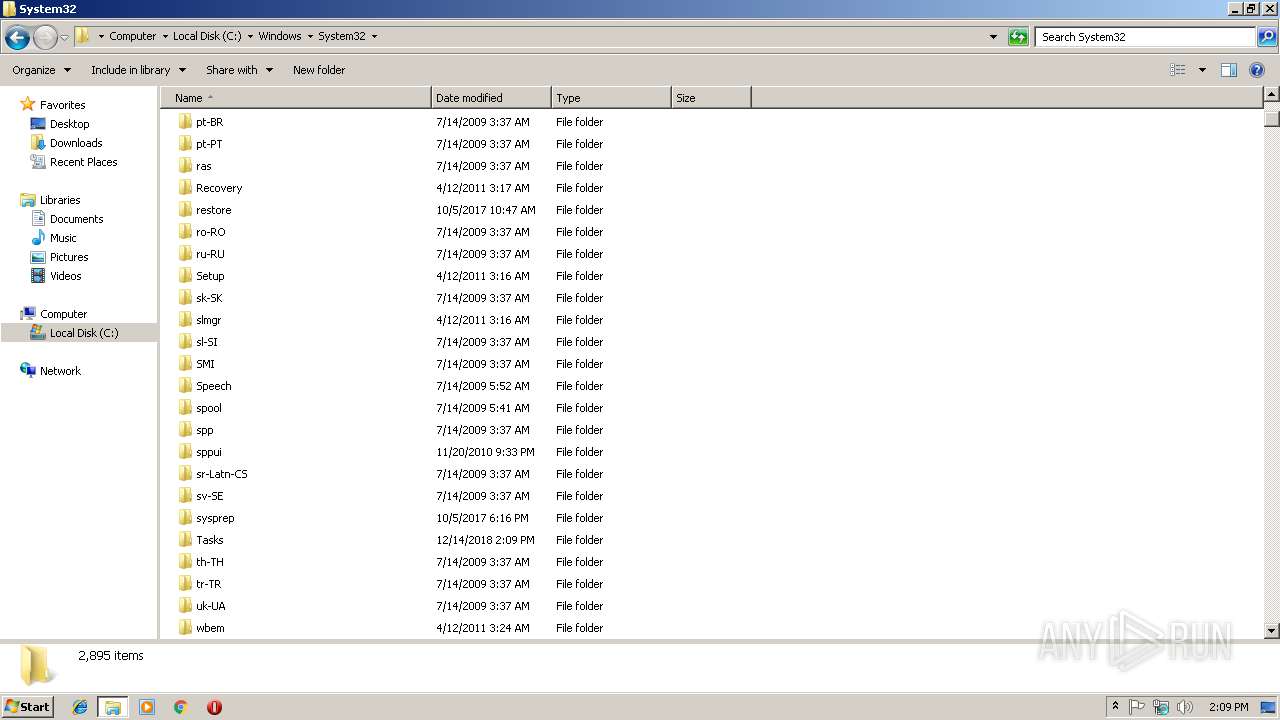
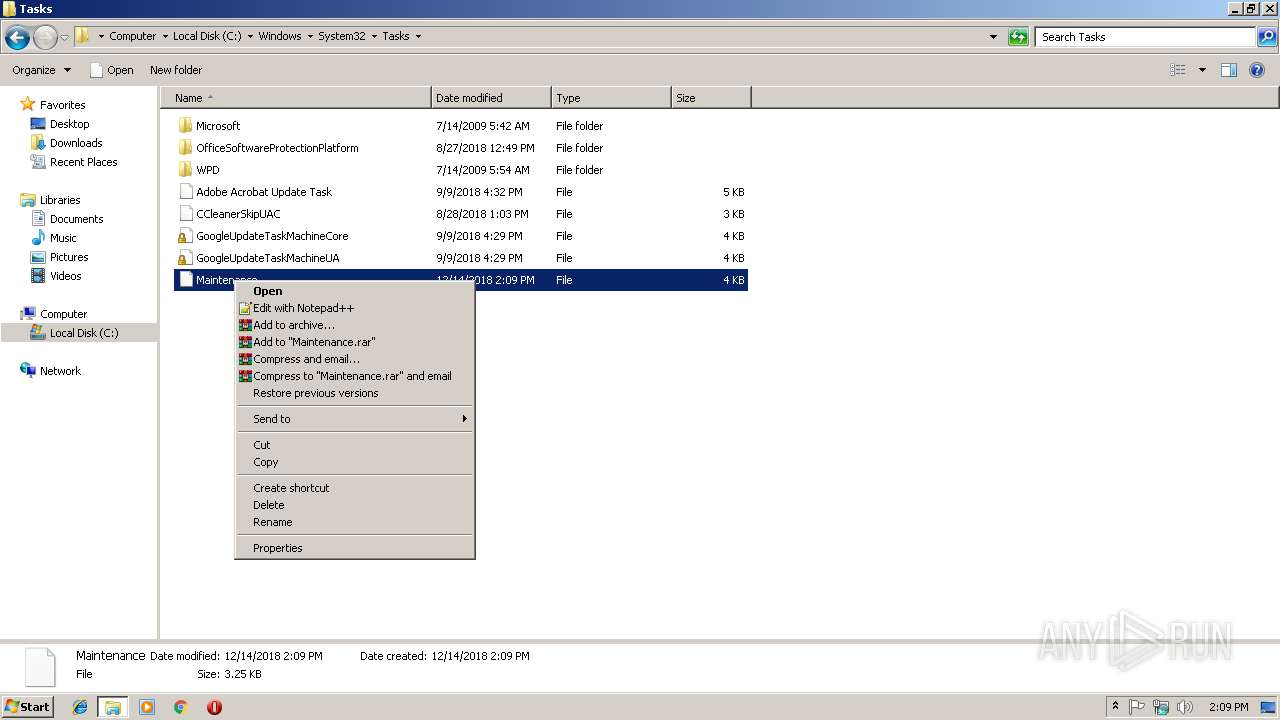
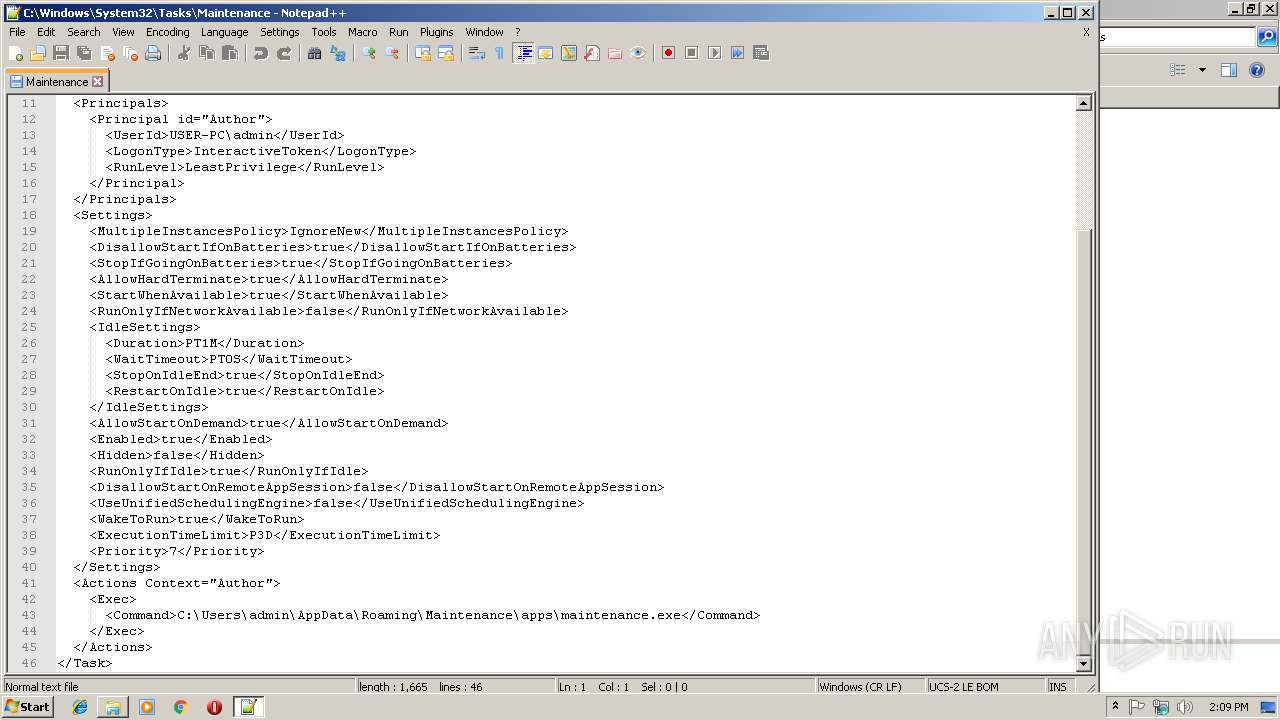
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2264)
Application was dropped or rewritten from another process
- 67df6dd1fec343d8823874bd8caf9df3.exe (PID: 3236)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1668)
- schtasks.exe (PID: 2936)
SUSPICIOUS
Creates files in the user directory
- 67df6dd1fec343d8823874bd8caf9df3.exe (PID: 3008)
- notepad++.exe (PID: 2824)
Executable content was dropped or overwritten
- 67df6dd1fec343d8823874bd8caf9df3.exe (PID: 3008)
- cmd.exe (PID: 3124)
Starts application with an unusual extension
- cmd.exe (PID: 3124)
Starts CMD.EXE for commands execution
- 67df6dd1fec343d8823874bd8caf9df3.exe (PID: 3008)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (52.6) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (20) |
| .exe | | | Win64 Executable (generic) (17.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.2) |
| .exe | | | Win32 Executable (generic) (2.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:27 16:58:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 31232 |
| InitializedDataSize: | 1563648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3ae3 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Spanish (Modern) |
| CharacterSet: | Unicode |
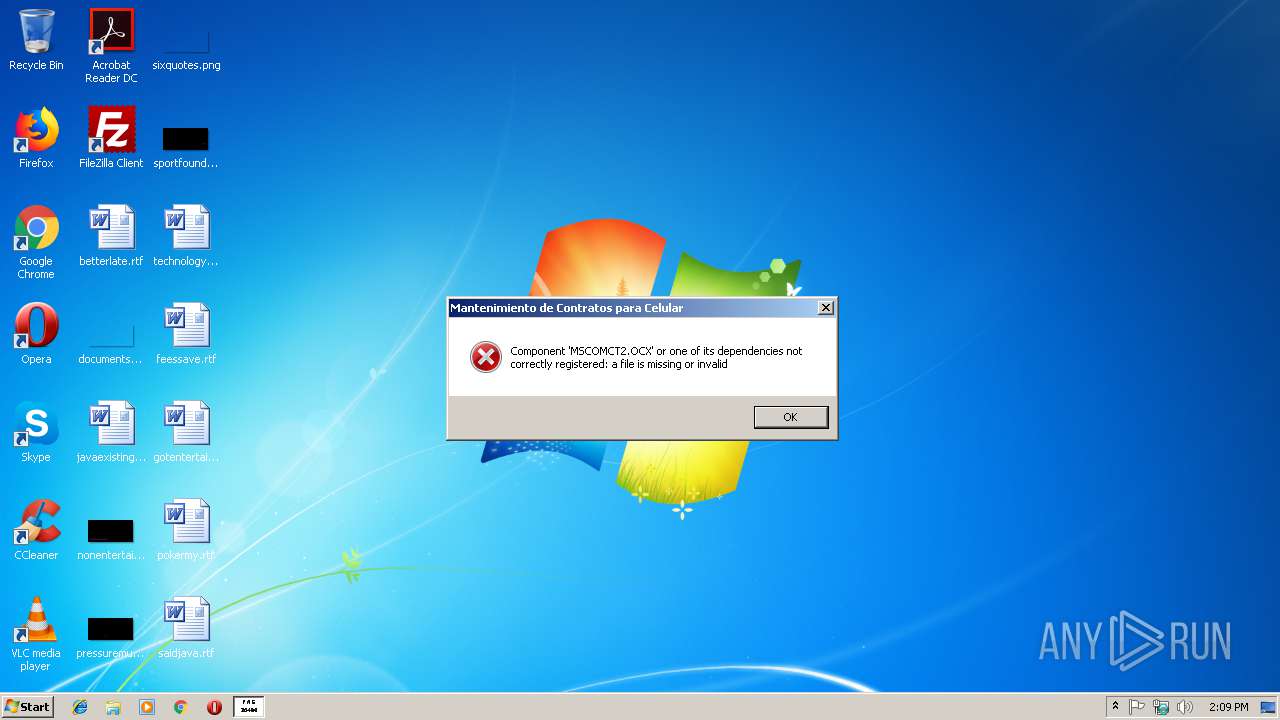
| CompanyName: | LUIS ROMAN |
| ProductName: | Mantenimiento de Contratos para Celular |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | FACPY030404 |
| OriginalFileName: | FACPY030404.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-May-2018 14:58:52 |
| Detected languages: |
|
| CompanyName: | LUIS ROMAN |
| ProductName: | Mantenimiento de Contratos para Celular |
| FileVersion: | 1.00 |
| ProductVersion: | 1.00 |
| InternalName: | FACPY030404 |
| OriginalFilename: | FACPY030404.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 27-May-2018 14:58:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000794A | 0x00007A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58937 |
.rdata | 0x00009000 | 0x000011A0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.96886 |
.data | 0x0000B000 | 0x00003158 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.48955 |
.rsrc | 0x0000F000 | 0x0017BF48 | 0x0017C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.85718 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.25616 | 608 | Latin 1 / Western European | UNKNOWN | RT_VERSION |
1001 | 3.45943 | 11 | Latin 1 / Western European | Russian - Russia | RT_RCDATA |
1002 | 7.8874 | 1579 | Latin 1 / Western European | Russian - Russia | RT_RCDATA |
1003 | 7.85622 | 1552384 | Latin 1 / Western European | Russian - Russia | RT_RCDATA |
1004 | 3.90689 | 15 | Latin 1 / Western European | Russian - Russia | RT_RCDATA |
1005 | 6.56005 | 143 | Latin 1 / Western European | Russian - Russia | RT_RCDATA |
1006 | 6.69822 | 146 | Latin 1 / Western European | Russian - Russia | RT_RCDATA |
1007 | 4.62352 | 26 | Latin 1 / Western European | Russian - Russia | RT_RCDATA |
30001 | 1.8629 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
MAINICON | 2.55772 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
47
Monitored processes
11
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
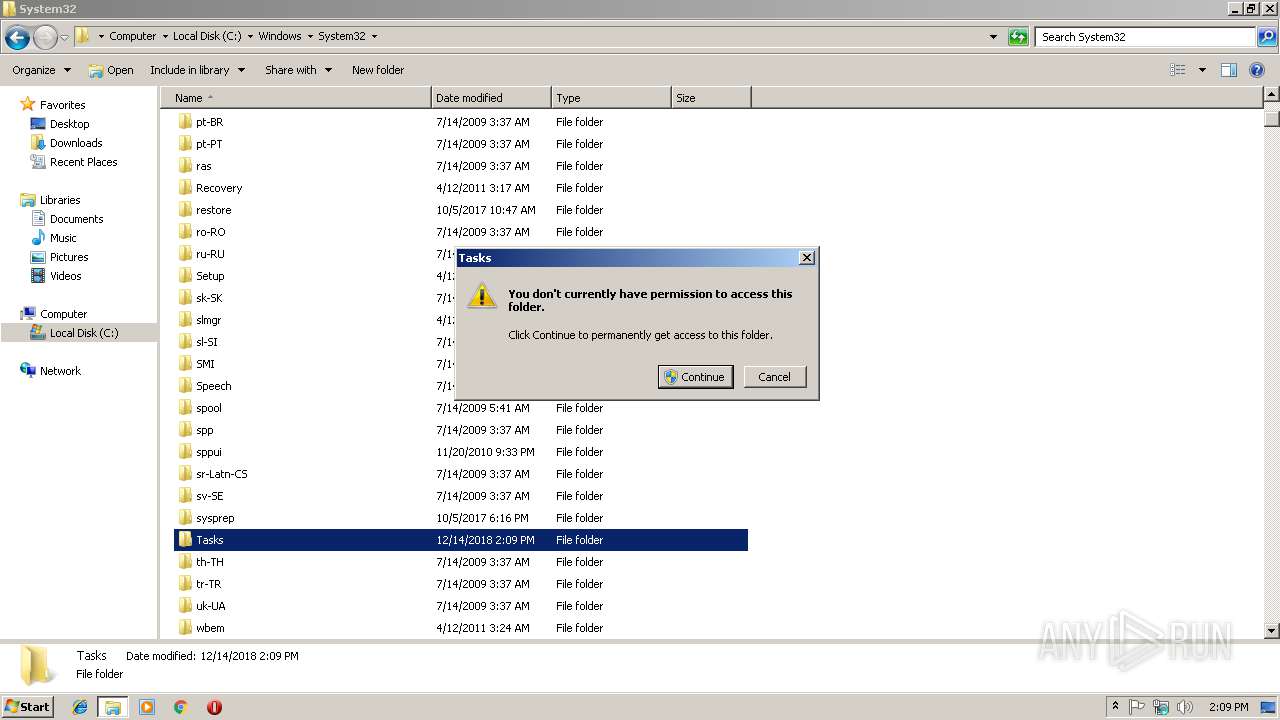
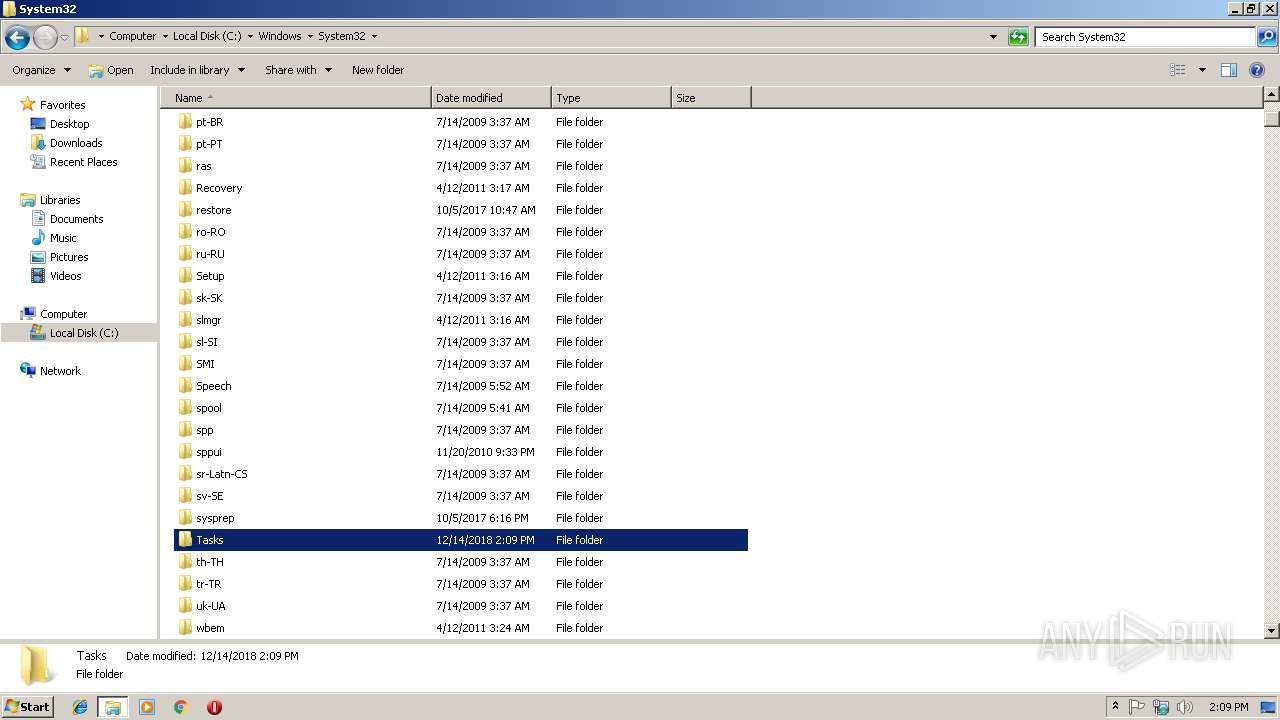
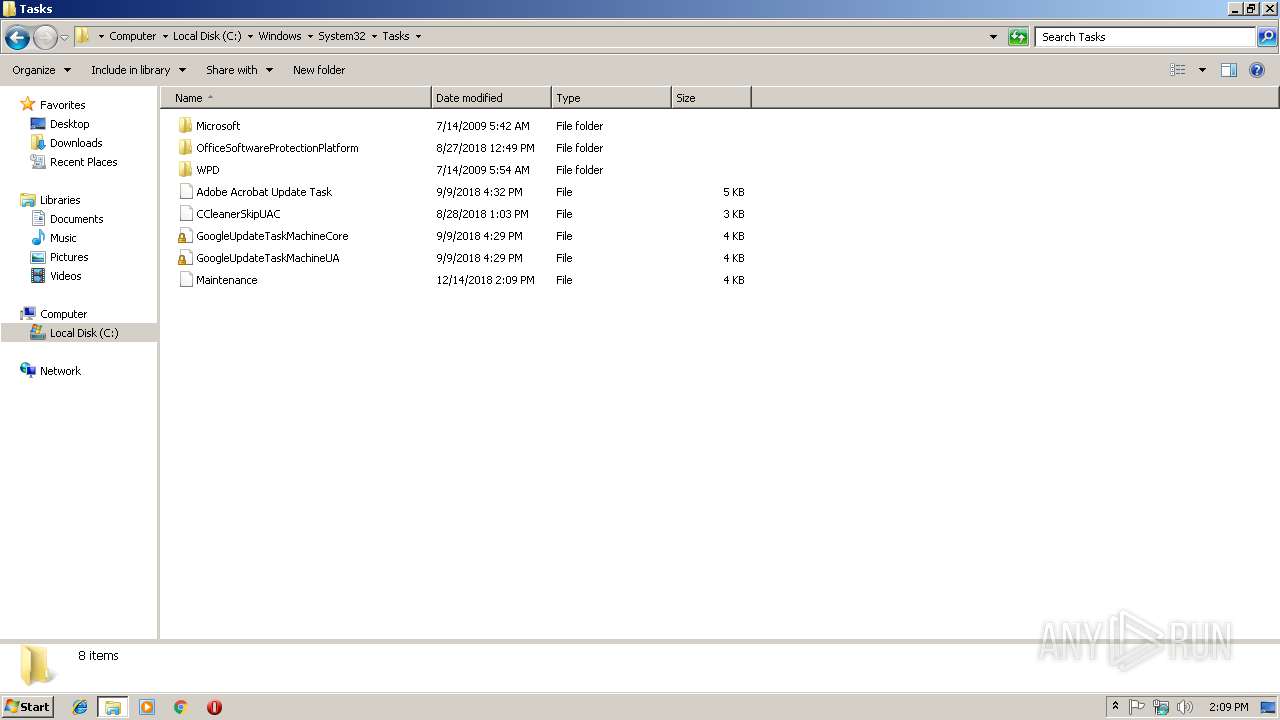
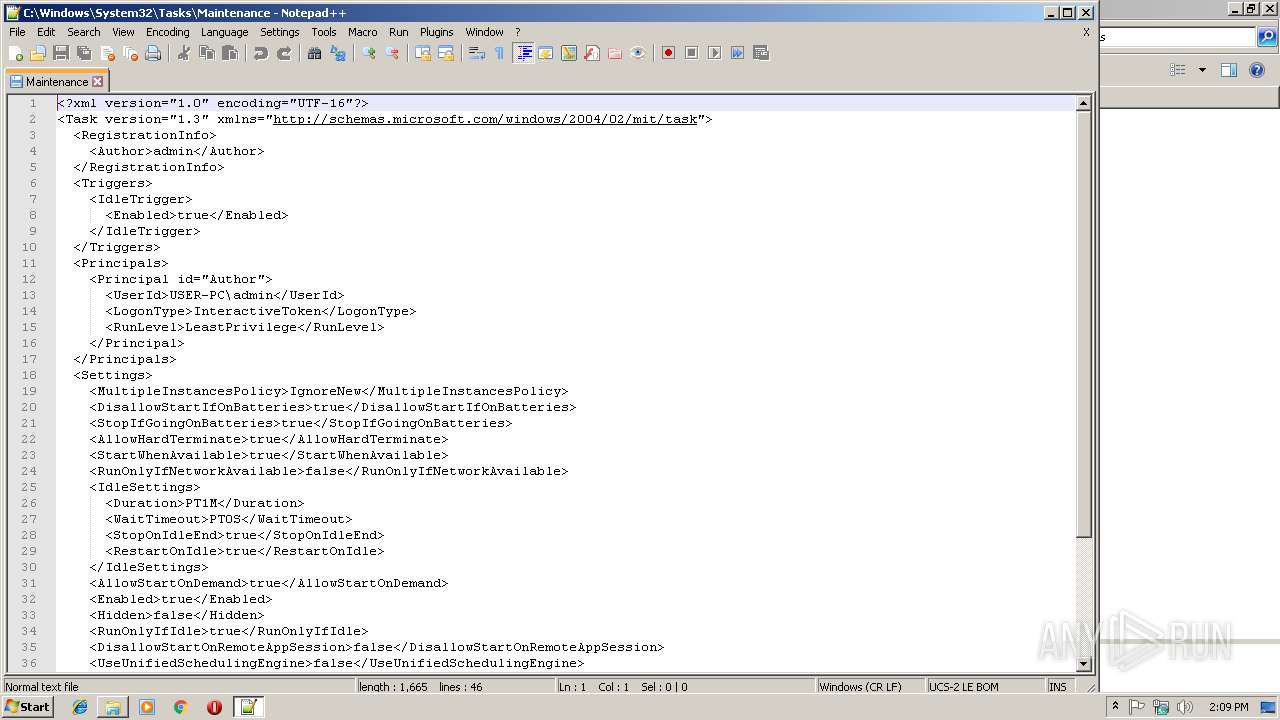
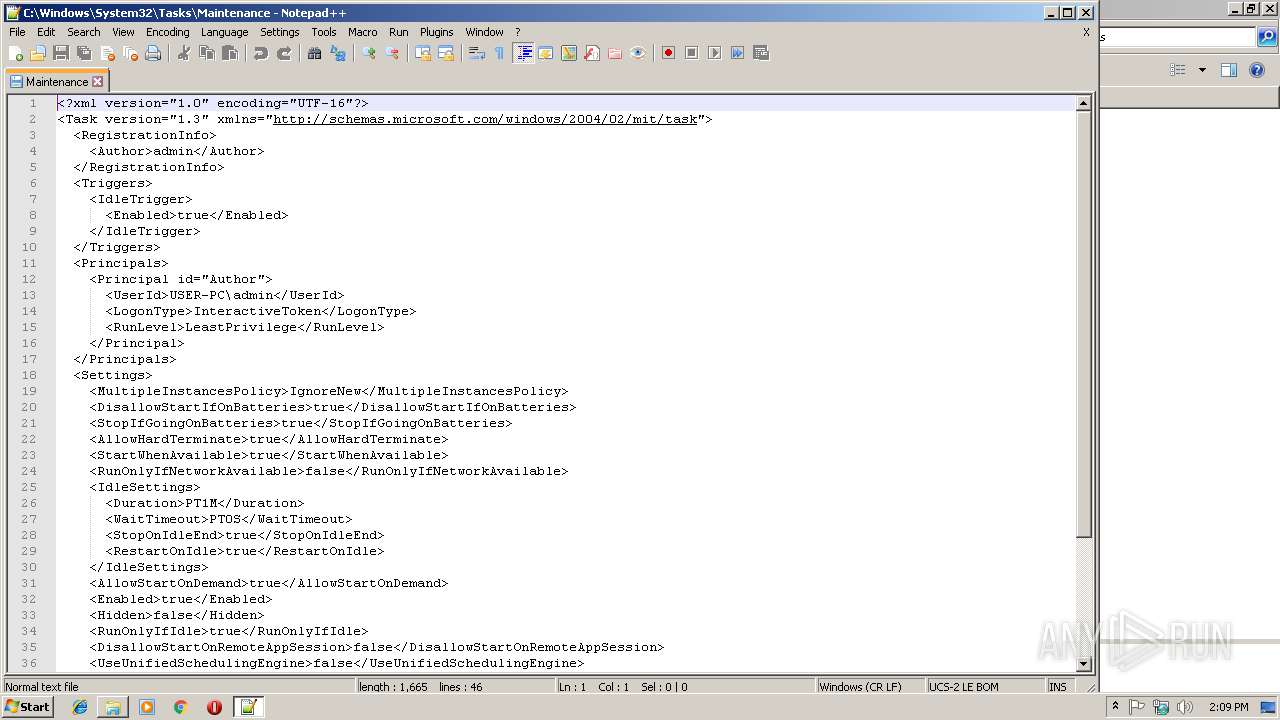
| 1668 | Schtasks.EXE /create /tn "Maintenance" /xml "C:\Users\admin\AppData\Local\Temp\zx2018121414916417.xml" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2264 | cmd /c ""C:\Users\admin\AppData\Local\Temp\zbe2018121414916417.bat" " | C:\Windows\system32\cmd.exe | — | 67df6dd1fec343d8823874bd8caf9df3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2452 | chcp 1251 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2544 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
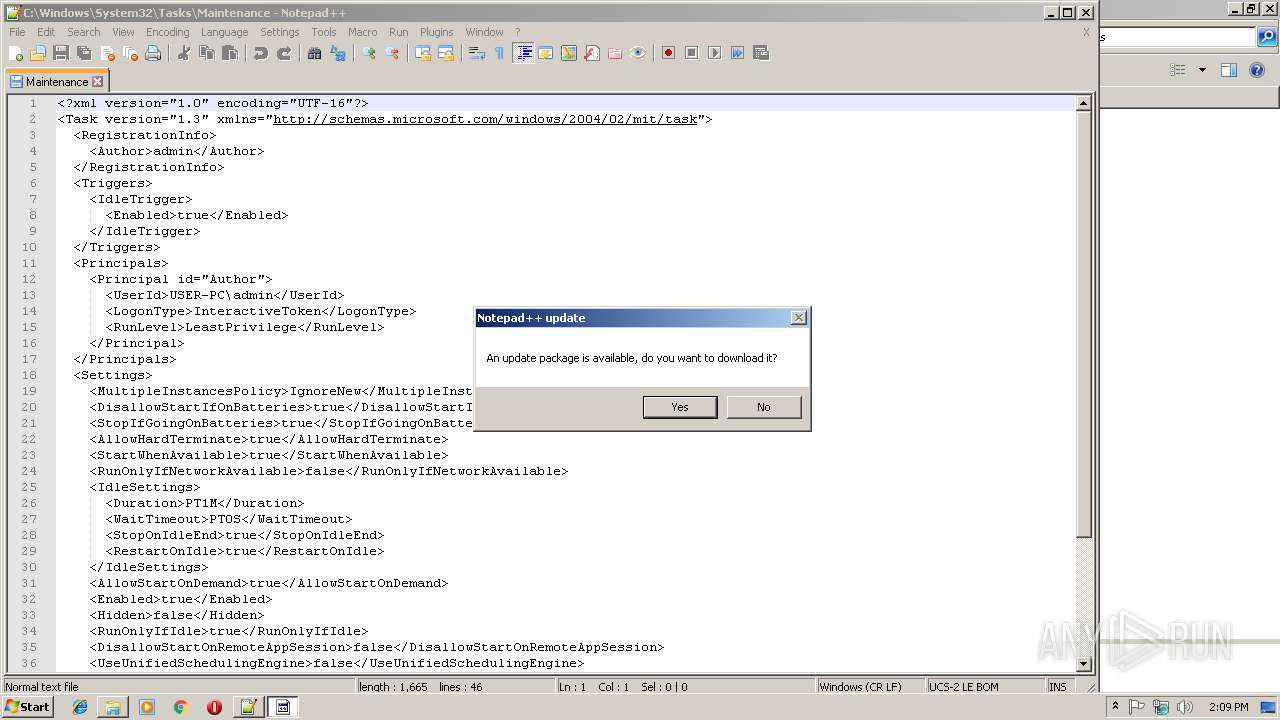
| 2824 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Windows\System32\Tasks\Maintenance" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 2936 | Schtasks.EXE /delete /tn "Maintenance" /f | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3008 | "C:\Users\admin\AppData\Local\Temp\67df6dd1fec343d8823874bd8caf9df3.exe" | C:\Users\admin\AppData\Local\Temp\67df6dd1fec343d8823874bd8caf9df3.exe | explorer.exe | ||||||||||||
User: admin Company: LUIS ROMAN Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3124 | cmd /c ""C:\Users\admin\AppData\Local\Temp\zb2018121414916417.bat" " | C:\Windows\system32\cmd.exe | 67df6dd1fec343d8823874bd8caf9df3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3236 | "C:\Users\admin\AppData\Local\Temp\67df6dd1fec343d8823874bd8caf9df3.exe" | C:\Users\admin\AppData\Local\Temp\67df6dd1fec343d8823874bd8caf9df3.exe | — | cmd.exe | |||||||||||
User: admin Company: LUIS ROMAN Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3380 | timeout /t 3 /nobreak | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
425
Read events
403
Write events
22
Delete events
0
Modification events
| (PID) Process: | (3008) 67df6dd1fec343d8823874bd8caf9df3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3008) 67df6dd1fec343d8823874bd8caf9df3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2824) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2824) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2824) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
0
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3236 | 67df6dd1fec343d8823874bd8caf9df3.exe | C:\Users\admin\AppData\Local\Temp\~DFC6F3E84D2E069F65.TMP | — | |
MD5:— | SHA256:— | |||
| 3008 | 67df6dd1fec343d8823874bd8caf9df3.exe | C:\Users\admin\AppData\Local\Temp\zbe2018121414916417.bat | text | |
MD5:— | SHA256:— | |||
| 3008 | 67df6dd1fec343d8823874bd8caf9df3.exe | C:\Users\admin\AppData\Local\Temp\zx2018121414916417.xml | xml | |
MD5:8011751D49E6A898F95A86539DEEE37E | SHA256:81FF81CE8D9F5A0422261B526B96CB4706968423FCA22DB1820F59183D01CB57 | |||
| 3124 | cmd.exe | C:\Users\admin\AppData\Local\Temp\67df6dd1fec343d8823874bd8caf9df3.exe | executable | |
MD5:— | SHA256:— | |||
| 2824 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\Config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 3008 | 67df6dd1fec343d8823874bd8caf9df3.exe | C:\Users\admin\AppData\Local\Temp\zb2018121414916417.bat | text | |
MD5:— | SHA256:— | |||
| 3008 | 67df6dd1fec343d8823874bd8caf9df3.exe | C:\Users\admin\AppData\Roaming\Maintenance\apps\maintenance.exe | executable | |
MD5:— | SHA256:— | |||
| 3008 | 67df6dd1fec343d8823874bd8caf9df3.exe | C:\Users\admin\AppData\Local\Temp\ze2018121414916417.tmp | executable | |
MD5:— | SHA256:— | |||
| 2824 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:AD21A64014891793DD9B21D835278F36 | SHA256:C24699C9D00ABDD510140FE1B2ACE97BFC70D8B21BF3462DED85AFC4F73FE52F | |||
| 2824 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:E792264BEC29005B9044A435FBA185AB | SHA256:5298FD2F119C43D04F6CF831F379EC25B4156192278E40E458EC356F9B49D624 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.186.32:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | unknown | der | 471 b | whitelisted |
— | — | GET | 200 | 2.16.186.32:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEAXk3DuUOKs7hZfLpqGYUOM%3D | unknown | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4068 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
— | — | 2.16.186.32:80 | ocsp.usertrust.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|