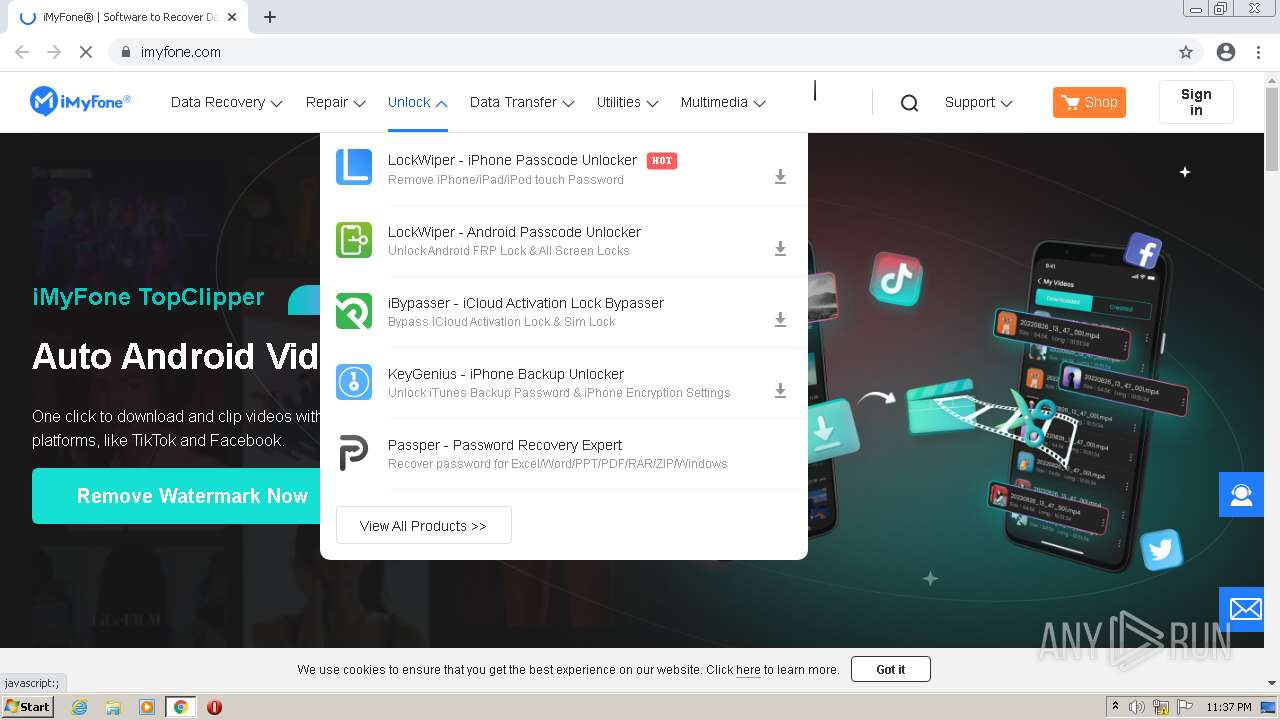
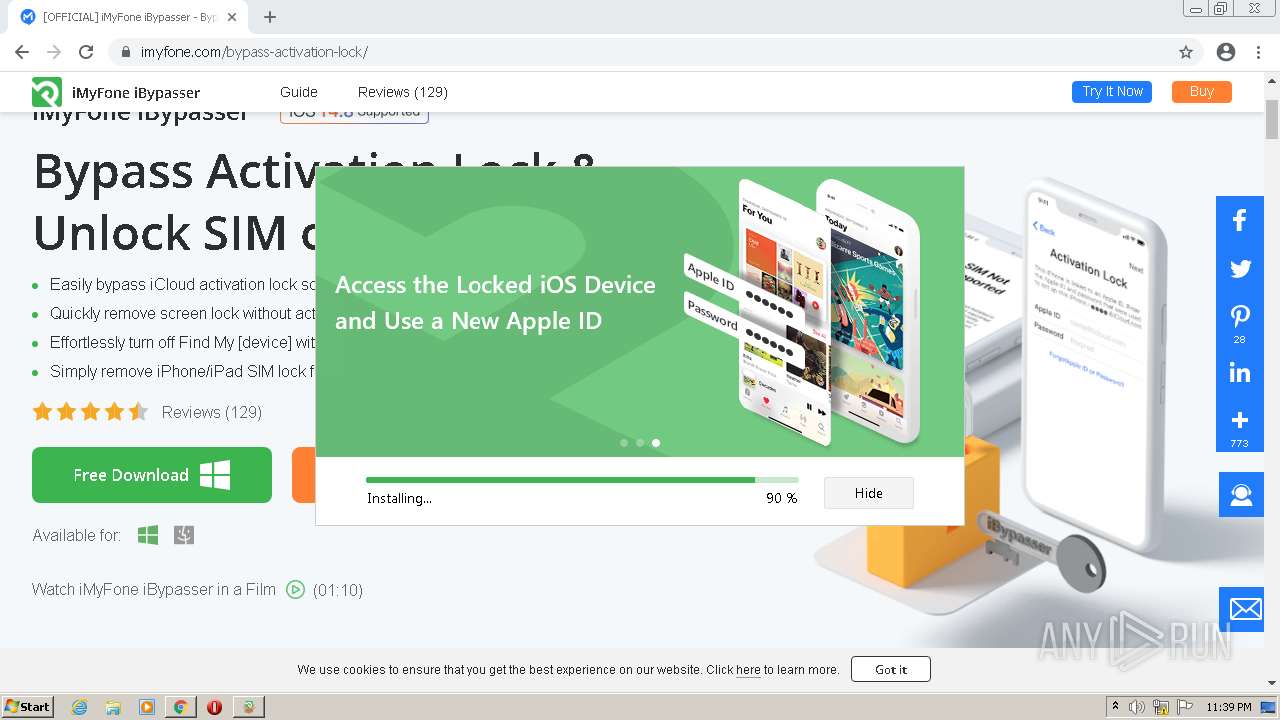
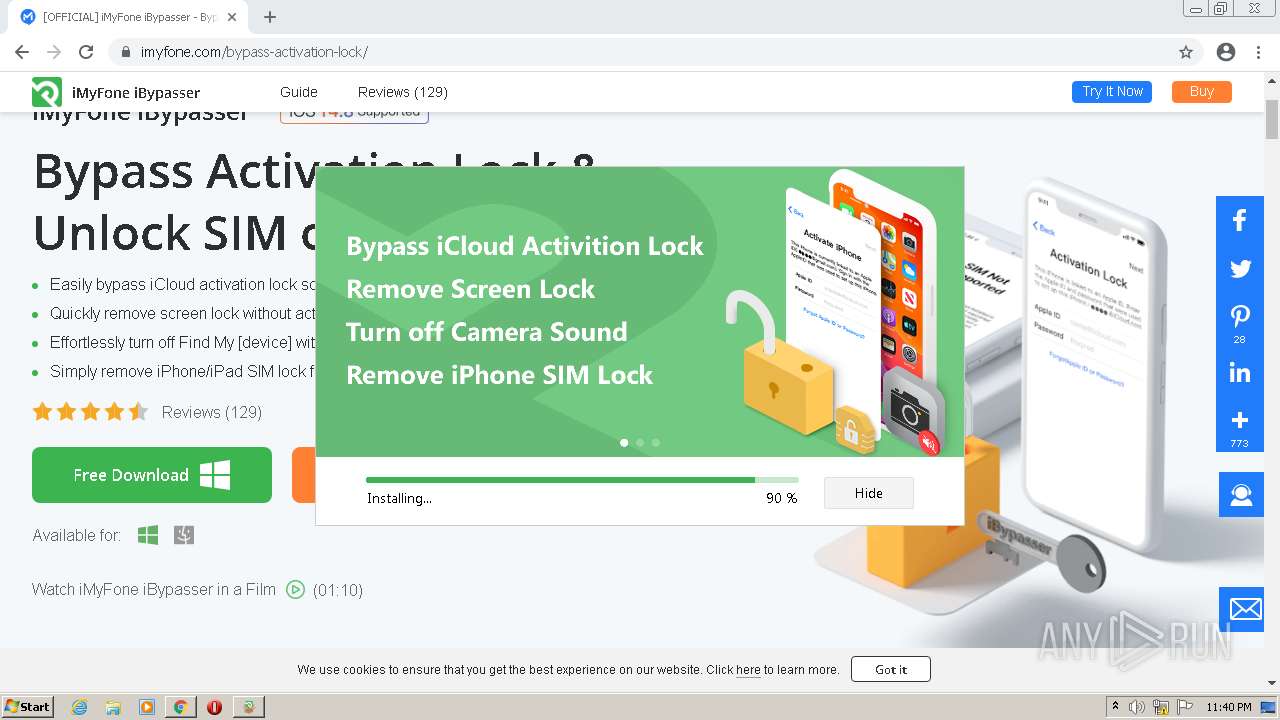
| URL: | https://www.imyfone.com |
| Full analysis: | https://app.any.run/tasks/fae68670-956a-422c-902a-60a15fd96d7d |
| Verdict: | Malicious activity |
| Analysis date: | November 22, 2022, 23:36:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4393C131D430E998E6CE8BB4741C4A13 |
| SHA1: | 81EC6B870290AAAAA5E3953A9F734633A8CE3D96 |
| SHA256: | 76171478D3D586421045FB080C340687D9C11779C9756B98AB80EF3F5490823D |
| SSDEEP: | 3:N8DSLwVZI:2OLwg |
MALICIOUS
Application was dropped or rewritten from another process
- iMyfone-bypass-activation-lock_setup.exe (PID: 3400)
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
- 7z.exe (PID: 3908)
- 7z.exe (PID: 3764)
- MFResident.exe (PID: 872)
- ResidentAutoUpdate.exe (PID: 3768)
- LocalService.exe (PID: 1296)
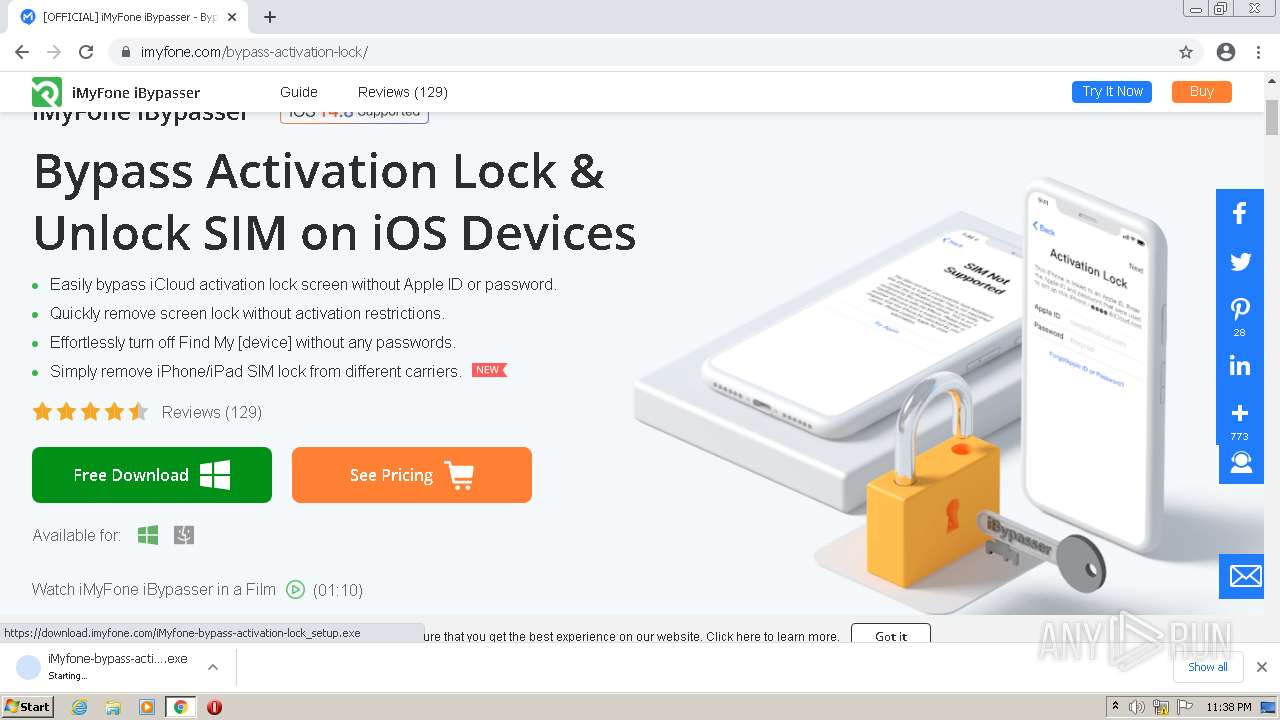
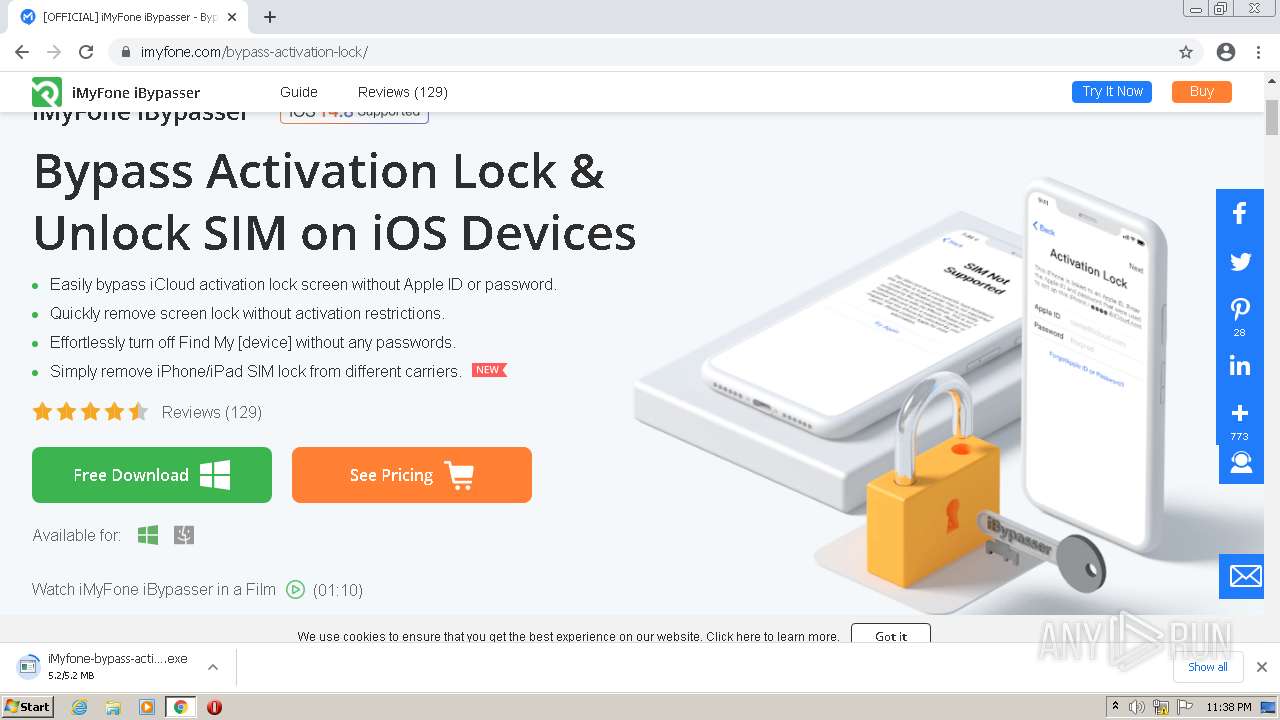
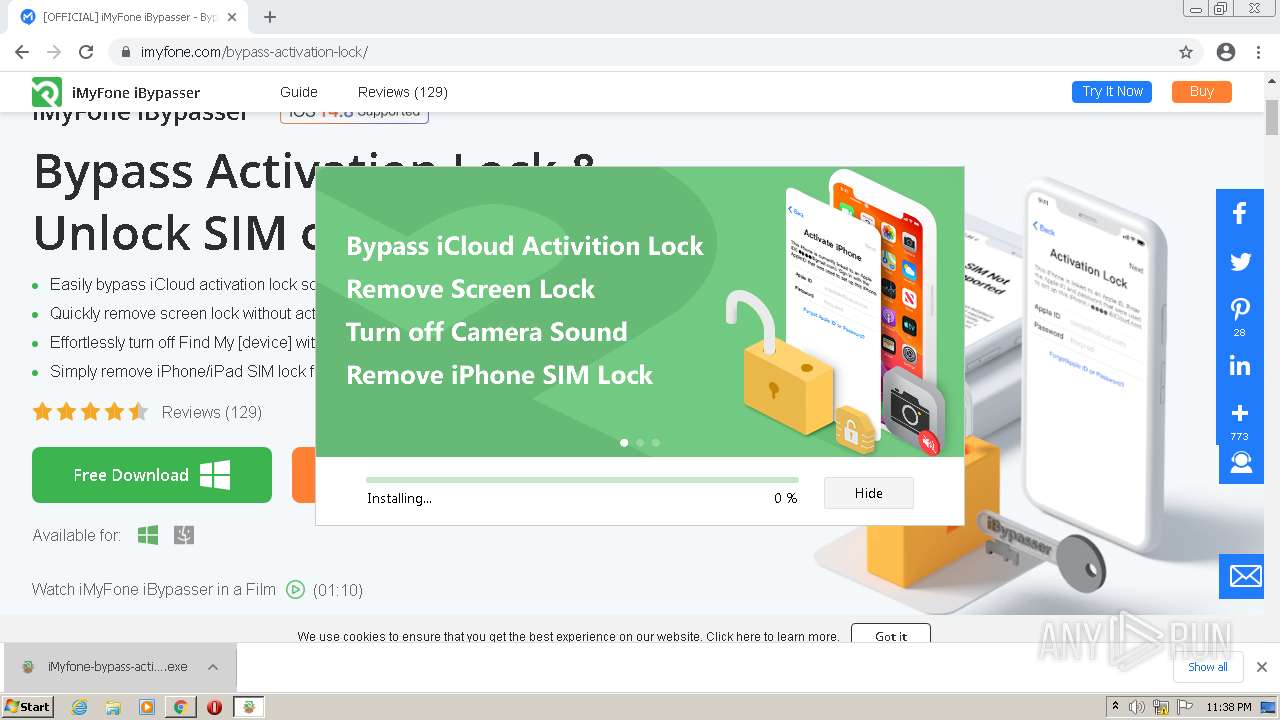
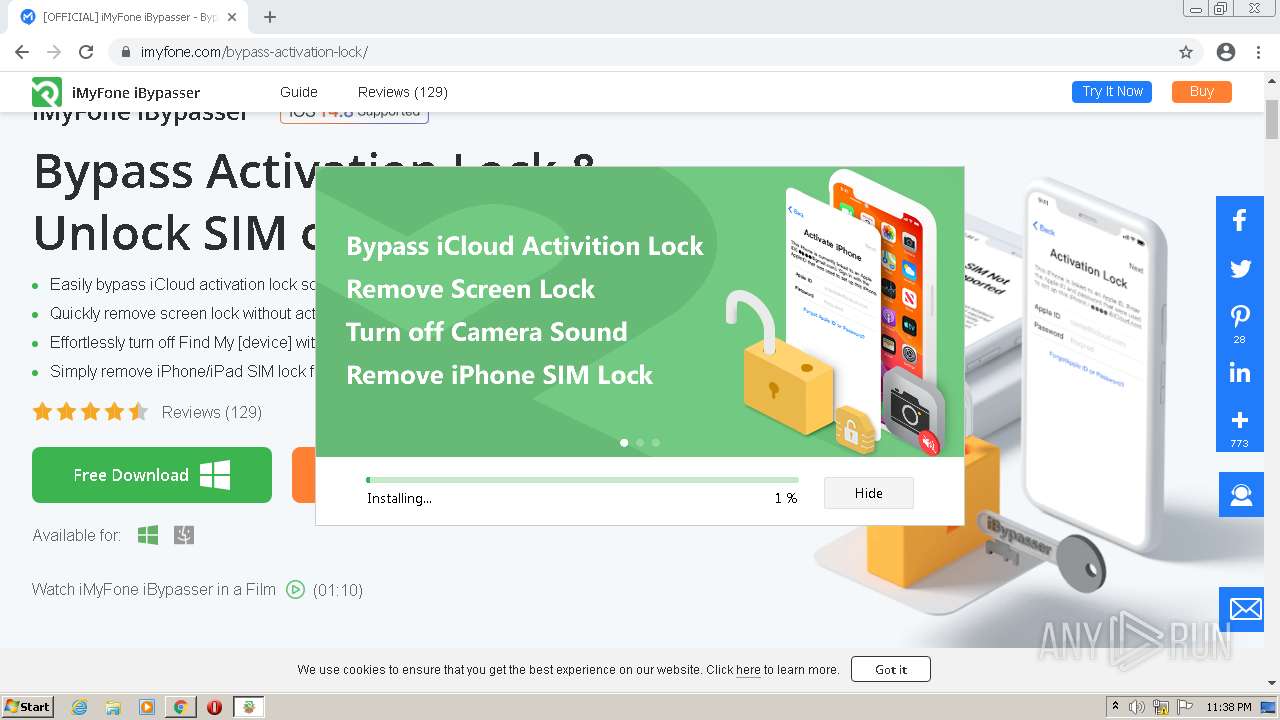
Drops the executable file immediately after the start
- imyfone-download.exe (PID: 2820)
- 7z.exe (PID: 3908)
- imyfone-download.tmp (PID: 3564)
- 7z.exe (PID: 3764)
Loads dropped or rewritten executable
- 7z.exe (PID: 3908)
- LocalService.exe (PID: 1296)
- MFResident.exe (PID: 872)
- ResidentAutoUpdate.exe (PID: 3768)
SUSPICIOUS
Reads settings of System Certificates
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
- ResidentAutoUpdate.exe (PID: 3768)
Process requests binary or script from the Internet
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
Adds/modifies Windows certificates
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
Creates a directory in Program Files
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
- imyfone-download.tmp (PID: 3564)
- 7z.exe (PID: 3908)
- 7z.exe (PID: 3764)
Reads Internet Settings
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
Executable content was dropped or overwritten
- imyfone-download.exe (PID: 2820)
- 7z.exe (PID: 3908)
- imyfone-download.tmp (PID: 3564)
- 7z.exe (PID: 3764)
Reads the Windows owner or organization settings
- imyfone-download.tmp (PID: 3564)
Drops a file with too old compile date
- imyfone-download.tmp (PID: 3564)
Executes as Windows Service
- LocalService.exe (PID: 1296)
INFO
Application launched itself
- chrome.exe (PID: 2408)
- iexplore.exe (PID: 2468)
Process checks LSA protection
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
- imyfone-download.tmp (PID: 3564)
- ResidentAutoUpdate.exe (PID: 3768)
Drops the executable file immediately after the start
- chrome.exe (PID: 2408)
- chrome.exe (PID: 3908)
Reads Environment values
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
Reads product name
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
Checks supported languages
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
- imyfone-download.exe (PID: 2820)
- imyfone-download.tmp (PID: 3564)
- 7z.exe (PID: 3908)
- 7z.exe (PID: 3764)
- MFResident.exe (PID: 872)
- ResidentAutoUpdate.exe (PID: 3768)
- LocalService.exe (PID: 1296)
Executable content was dropped or overwritten
- chrome.exe (PID: 2408)
- chrome.exe (PID: 3908)
Reads the computer name
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
- imyfone-download.tmp (PID: 3564)
- 7z.exe (PID: 3908)
- 7z.exe (PID: 3764)
- LocalService.exe (PID: 1296)
- ResidentAutoUpdate.exe (PID: 3768)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3908)
- imyfone-download.tmp (PID: 3564)
- 7z.exe (PID: 3908)
Reads the machine GUID from the registry
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
- imyfone-download.tmp (PID: 3564)
- ResidentAutoUpdate.exe (PID: 3768)
Creates a file in a temporary directory
- imyfone-download.exe (PID: 2820)
- imyfone-download.tmp (PID: 3564)
- MFResident.exe (PID: 872)
- ResidentAutoUpdate.exe (PID: 3768)
Creates files in the program directory
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
- 7z.exe (PID: 3908)
- 7z.exe (PID: 3764)
- MFResident.exe (PID: 872)
- imyfone-download.tmp (PID: 3564)
- ResidentAutoUpdate.exe (PID: 3768)
Loads dropped or rewritten executable
- imyfone-download.tmp (PID: 3564)
Dropped object may contain Bitcoin addresses
- imyfone-download.tmp (PID: 3564)
- 7z.exe (PID: 3908)
- 7z.exe (PID: 3764)
Application was dropped or rewritten from another process
- imyfone-download.tmp (PID: 3564)
Creates files in the user directory
- imyfone-download.tmp (PID: 3564)
Creates a software uninstall entry
- imyfone-download.tmp (PID: 3564)
Process checks SAM and SYSTEM backups
- LocalService.exe (PID: 1296)
Dropped object may contain TOR URL's
- chrome.exe (PID: 3008)
- chrome.exe (PID: 2408)
Starts Internet Explorer
- iMyfone-bypass-activation-lock_setup.exe (PID: 4004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
44
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,5416007988676206802,12724560090667458018,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3888 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,5416007988676206802,12724560090667458018,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,5416007988676206802,12724560090667458018,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2152 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,5416007988676206802,12724560090667458018,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,5416007988676206802,12724560090667458018,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2364 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:/Program Files (x86)/Common Files/iMyFone/Components/Resident/MFResident.exe" | C:\Program Files (x86)\Common Files\iMyFone\Components\Resident\MFResident.exe | LocalService.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: MFResident.exe Exit code: 0 Version: 1.1.0.1 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,5416007988676206802,12724560090667458018,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1144 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,5416007988676206802,12724560090667458018,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=512 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,5416007988676206802,12724560090667458018,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4124 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1056,5416007988676206802,12724560090667458018,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3800 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
31 218
Read events
30 899
Write events
308
Delete events
11
Modification events
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
397
Suspicious files
78
Text files
1 324
Unknown types
145
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-637D5CFF-968.pma | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:D435EC39EAF201C40FD0AFA51667D783 | SHA256:E045B87095A285F7FEAAB11EDC84B624AFE6AE6CFC073DFE3702B688F1F11EA7 | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\56b86bff-3367-45e0-8ef0-fcfb8b1c5686.tmp | text | |
MD5:D435EC39EAF201C40FD0AFA51667D783 | SHA256:E045B87095A285F7FEAAB11EDC84B624AFE6AE6CFC073DFE3702B688F1F11EA7 | |||
| 3288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFd9710.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RFd9914.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFd9720.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
123
DNS requests
87
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4004 | iMyfone-bypass-activation-lock_setup.exe | HEAD | 200 | 13.32.99.7:80 | http://download.imyfone.com/ibypasser/imyfone-ibypasser.exe | US | — | — | whitelisted |
4004 | iMyfone-bypass-activation-lock_setup.exe | GET | — | 13.32.99.7:80 | http://download.imyfone.com/ibypasser/imyfone-ibypasser.exe | US | — | — | whitelisted |
4004 | iMyfone-bypass-activation-lock_setup.exe | GET | — | 13.32.99.35:80 | http://download.imyfone.com/ibypasser/imyfone-ibypasser.exe | US | — | — | whitelisted |
4004 | iMyfone-bypass-activation-lock_setup.exe | GET | — | 13.32.99.7:80 | http://download.imyfone.com/ibypasser/imyfone-ibypasser.exe | US | — | — | whitelisted |
4004 | iMyfone-bypass-activation-lock_setup.exe | GET | — | 13.32.99.29:80 | http://download.imyfone.com/ibypasser/imyfone-ibypasser.exe | US | — | — | whitelisted |
880 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 53.9 Kb | whitelisted |
880 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | crx | 49.6 Kb | whitelisted |
880 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gd6jdte4vib27q2ihmxeviicra_2891/jflookgnkcckhobaglndicnbbgbonegd_2891_all_i4ipsjhoqtj3lm33rd3y6rdk7a.crx3 | US | crx | 49.6 Kb | whitelisted |
4004 | iMyfone-bypass-activation-lock_setup.exe | GET | — | 13.32.99.29:80 | http://download.imyfone.com/ibypasser/imyfone-ibypasser.exe | US | — | — | whitelisted |
880 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gd6jdte4vib27q2ihmxeviicra_2891/jflookgnkcckhobaglndicnbbgbonegd_2891_all_i4ipsjhoqtj3lm33rd3y6rdk7a.crx3 | US | binary | 53.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3748 | chrome.exe | 142.250.185.173:443 | accounts.google.com | GOOGLE | US | suspicious |
3748 | chrome.exe | 142.250.186.78:443 | clients2.google.com | GOOGLE | US | whitelisted |
3748 | chrome.exe | 142.250.186.131:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
3748 | chrome.exe | 99.86.4.119:443 | www.imyfone.com | AMAZON-02 | US | suspicious |
3748 | chrome.exe | 79.133.177.217:443 | static.imyfone.com | Zhejiang Taobao Network Co.,Ltd | RU | suspicious |
3748 | chrome.exe | 142.250.186.72:443 | www.googletagmanager.com | GOOGLE | US | suspicious |
3748 | chrome.exe | 79.133.177.232:443 | static.ifonelab.com | Zhejiang Taobao Network Co.,Ltd | RU | malicious |
3748 | chrome.exe | 163.181.92.227:443 | images.imyfone.com | Zhejiang Taobao Network Co.,Ltd | DE | malicious |
3748 | chrome.exe | 65.9.95.85:443 | widget.trustpilot.com | AMAZON-02 | US | suspicious |
3748 | chrome.exe | 79.133.177.227:443 | static.ifonelab.com | Zhejiang Taobao Network Co.,Ltd | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.imyfone.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
static.imyfone.com |
| malicious |
static.ifonelab.com |
| malicious |
www.googletagmanager.com |
| whitelisted |
images.imyfone.com |
| malicious |
public.imyfone.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4004 | iMyfone-bypass-activation-lock_setup.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
4004 | iMyfone-bypass-activation-lock_setup.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
4004 | iMyfone-bypass-activation-lock_setup.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
4004 | iMyfone-bypass-activation-lock_setup.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
4004 | iMyfone-bypass-activation-lock_setup.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
4004 | iMyfone-bypass-activation-lock_setup.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
4004 | iMyfone-bypass-activation-lock_setup.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
4004 | iMyfone-bypass-activation-lock_setup.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
4004 | iMyfone-bypass-activation-lock_setup.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
4004 | iMyfone-bypass-activation-lock_setup.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
Process | Message |
|---|---|
iMyfone-bypass-activation-lock_setup.exe | [0] 0 ~ 14182805,length = 14182806
|
iMyfone-bypass-activation-lock_setup.exe | [1] 14182806 ~ 28365611,length = 14182806
|
iMyfone-bypass-activation-lock_setup.exe | [2] 28365612 ~ 42548417,length = 14182806
|
iMyfone-bypass-activation-lock_setup.exe | [3] 42548418 ~ 56731223,length = 14182806
|
iMyfone-bypass-activation-lock_setup.exe | [4] 56731224 ~ 70914031,length = 14182808
|
LocalService.exe | QObject::startTimer: Timers can only be used with threads started with QThread
|
MFResident.exe | MFResident CControlManager::checkUpdate 179 true "C:\\Program Files (x86)\\Common Files\\iMyFone\\Components\\Resident\\ResidentAutoUpdate.exe" ("--silent=true", "--alwaysHide=true")
|
ResidentAutoUpdate.exe | set QT_SCALE_FACTOR= "1.000000"
|
ResidentAutoUpdate.exe | libpng warning: iCCP: known incorrect sRGB profile
|
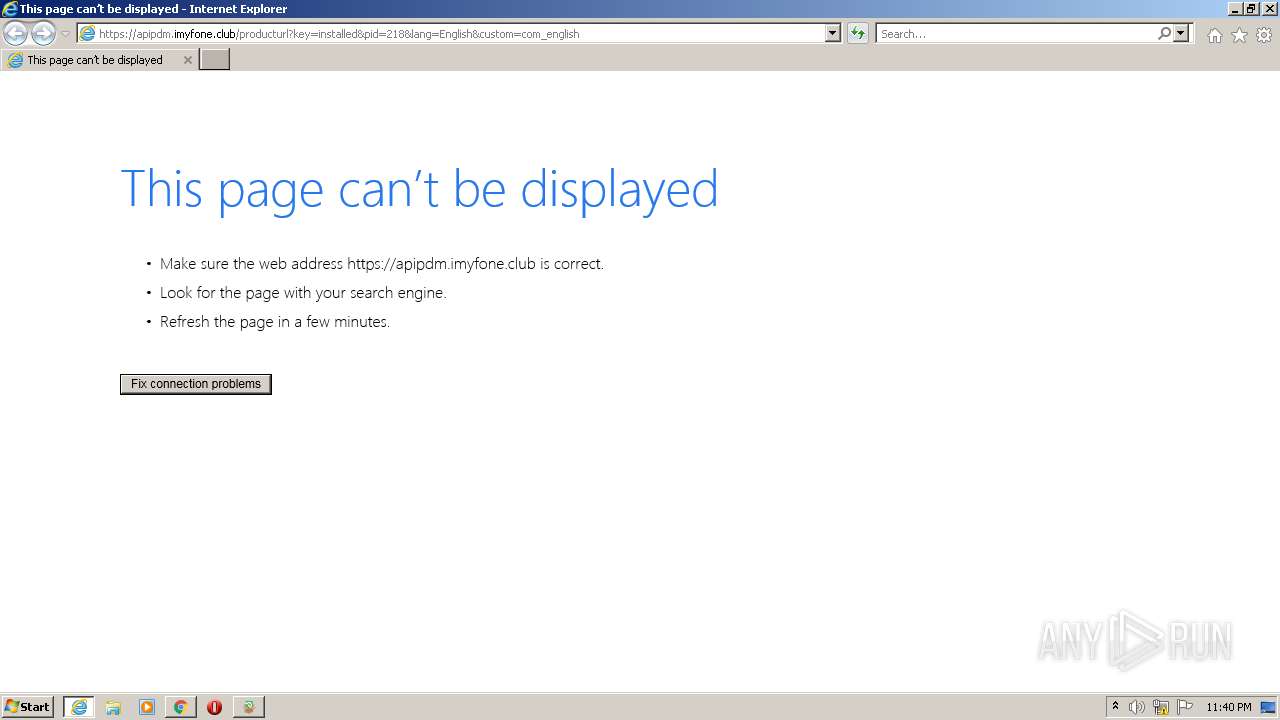
ResidentAutoUpdate.exe | resident_updater AutoUpdateV2::fetchConfig 95 patchUrl: "https://apipdm.imyfone.club/v2/appUpdate?pid=001&lang=English&bit=1&updatetype=2&patchVer=MFResident-20220630-55"
|