| File name: | dban-2.3.0_i586.iso |
| Full analysis: | https://app.any.run/tasks/cf5b85f3-91e4-41b7-96f7-c7f4c4e98df9 |
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2020, 08:10:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-iso9660-image |
| File info: | ISO 9660 CD-ROM filesystem data 'DBAN' (bootable) |
| MD5: | 33A1DF4171E649462EF9679AC207AA77 |
| SHA1: | 9C83EFEDC998B3334D48B8754A86475DE9328BF8 |
| SHA256: | 7613DAFC1CFC77054DCF5F7D01682D808BC31FAAAACFBF3263F4887580103776 |
| SSDEEP: | 393216:gy1SwNofZ9H/0YJZKBHviq//ZvQVFxVyqpbFzR:lKfZ9H/lQ//ZvStyqpbFF |
MALICIOUS
No malicious indicators.SUSPICIOUS
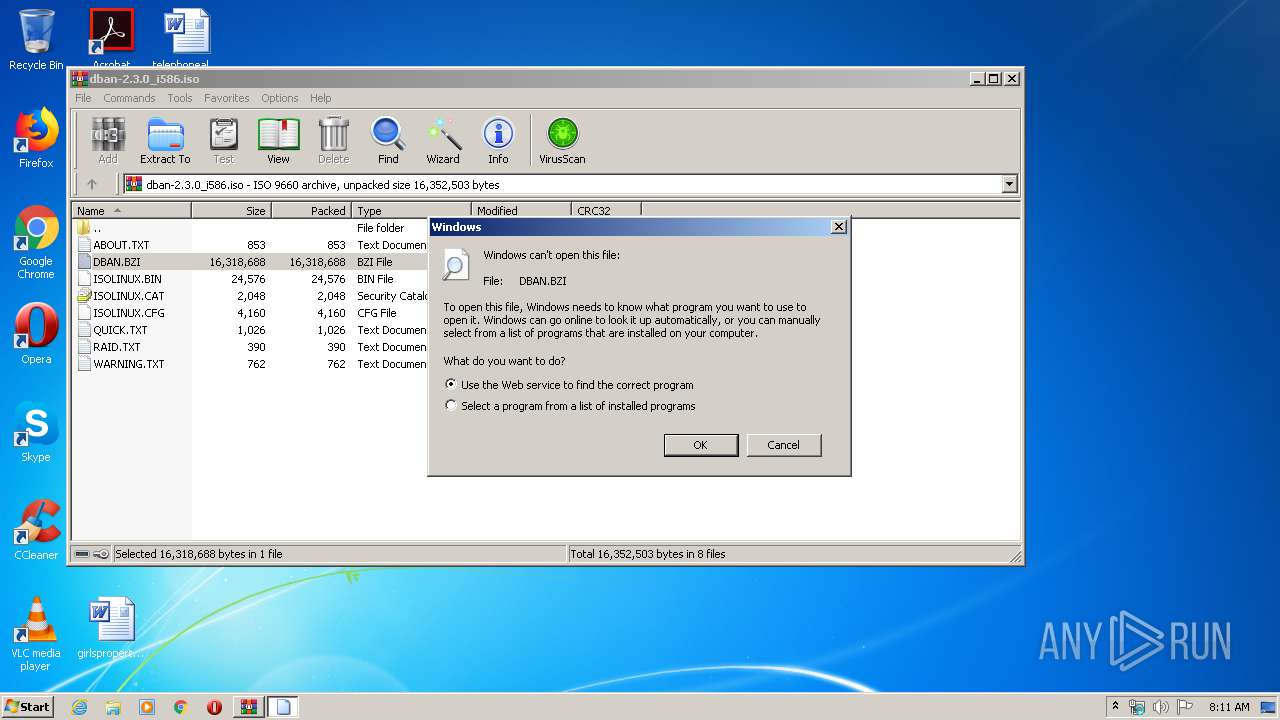
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 872)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
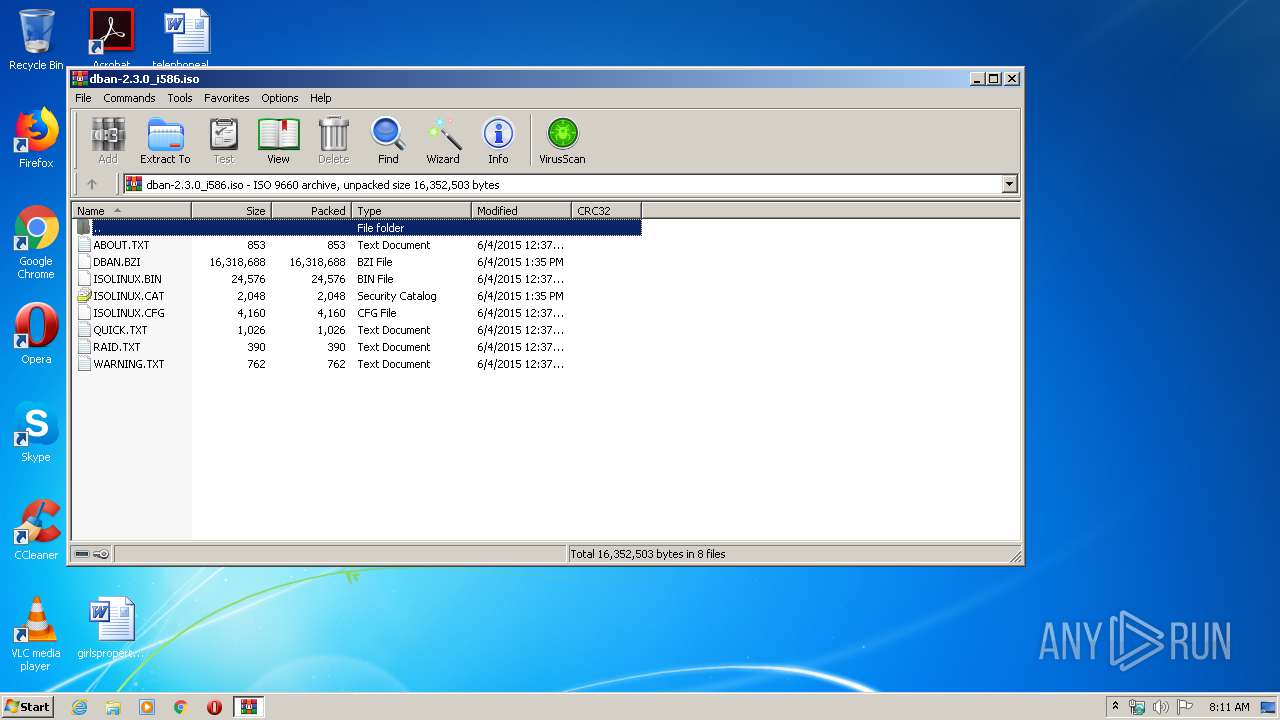
| .iso | | | ISO 9660 CD image (27.6) |
|---|---|---|
| .atn | | | Photoshop Action (27.1) |
| .gmc | | | Game Music Creator Music (6.1) |
EXIF
ISO
| System: | LINUX |
|---|---|
| VolumeName: | DBAN |
| VolumeBlockCount: | 8164 |
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 2015:06:04 15:35:23+03:00 |
| Software: | GENISOIMAGE ISO 9660/HFS FILESYSTEM CREATOR (C) 1993 E.YOUNGDALE (C) 1997-2006 J.PEARSON/J.SCHILLING (C) 2006-2007 CDRKIT TEAM |
| VolumeCreateDate: | 2015:06:04 15:35:23.00+03:00 |
| VolumeModifyDate: | 2015:06:04 15:35:23.00+03:00 |
| VolumeEffectiveDate: | 2015:06:04 15:35:23.00+03:00 |
| BootSystem: | EL TORITO SPECIFICATION |
Composite
| VolumeSize: | 16 MB |
|---|
Total processes
37
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
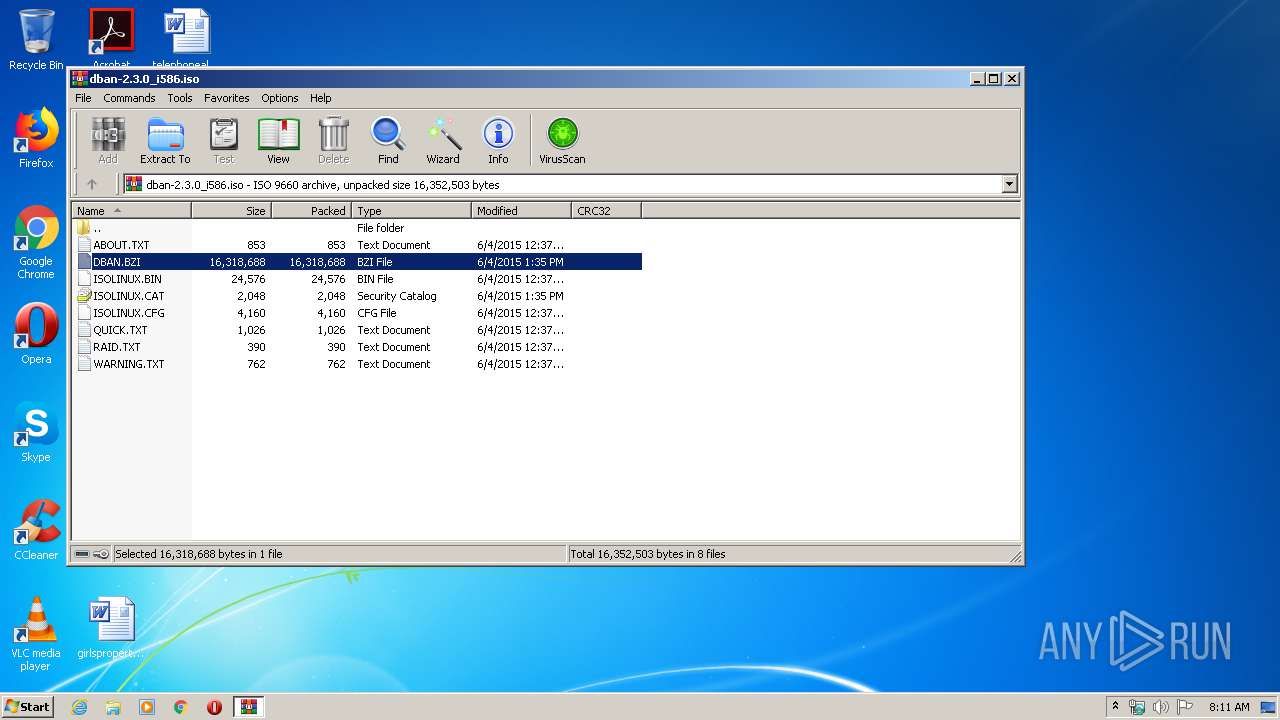
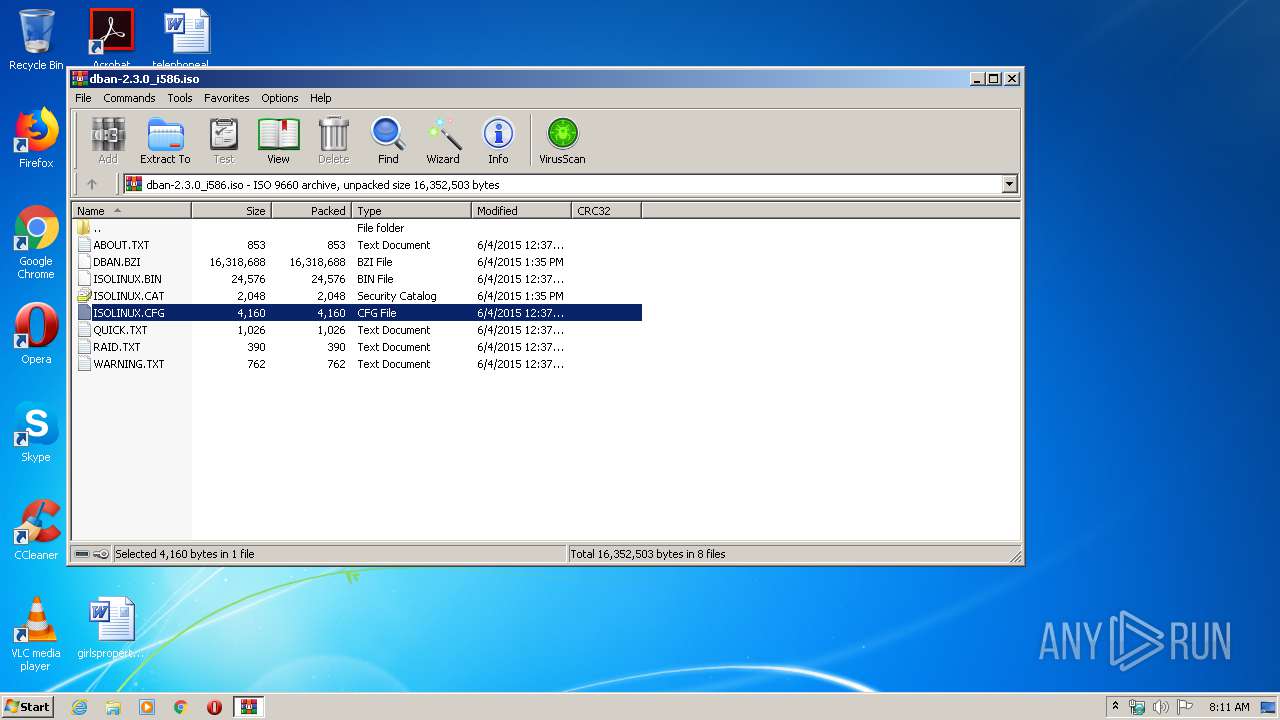
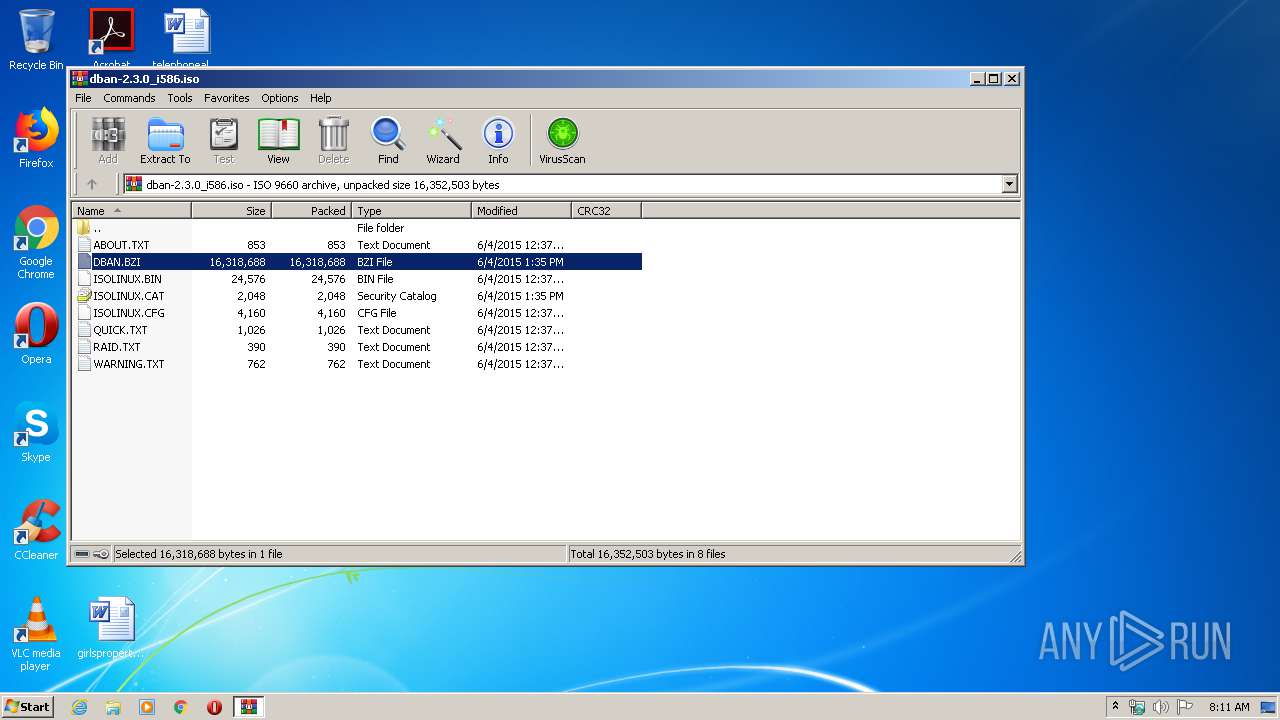
| 872 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\dban-2.3.0_i586.iso" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
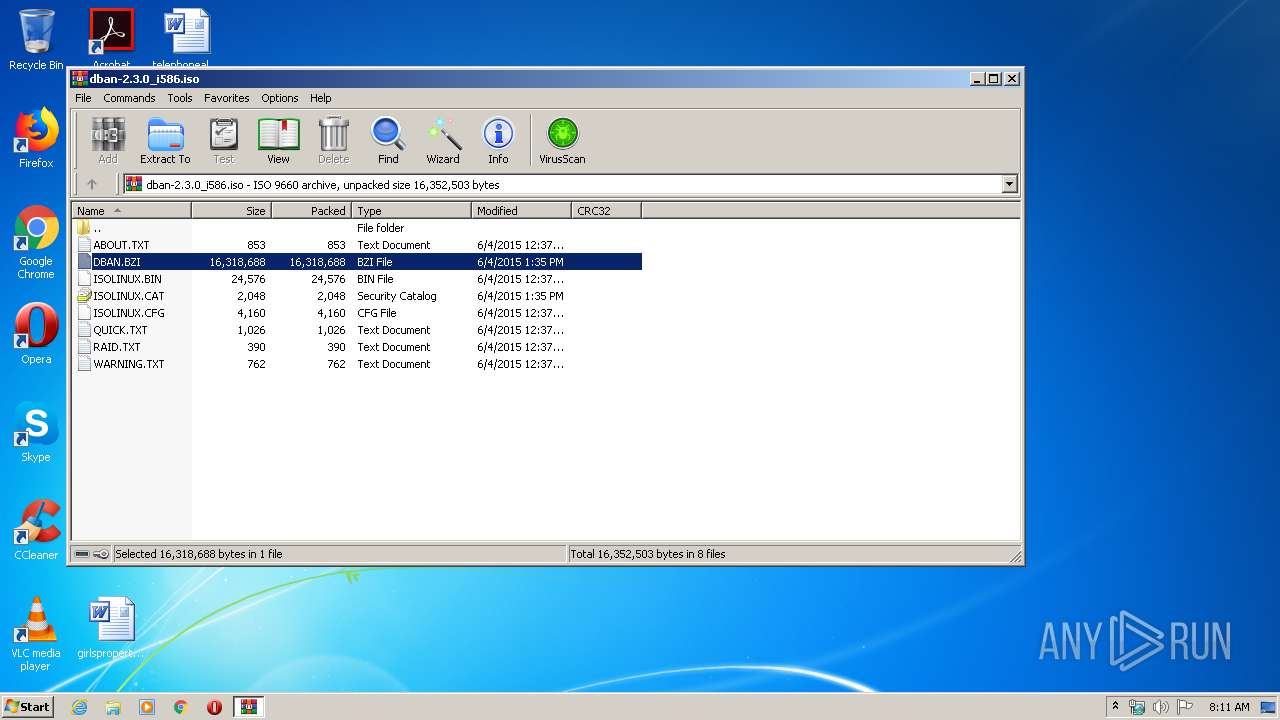
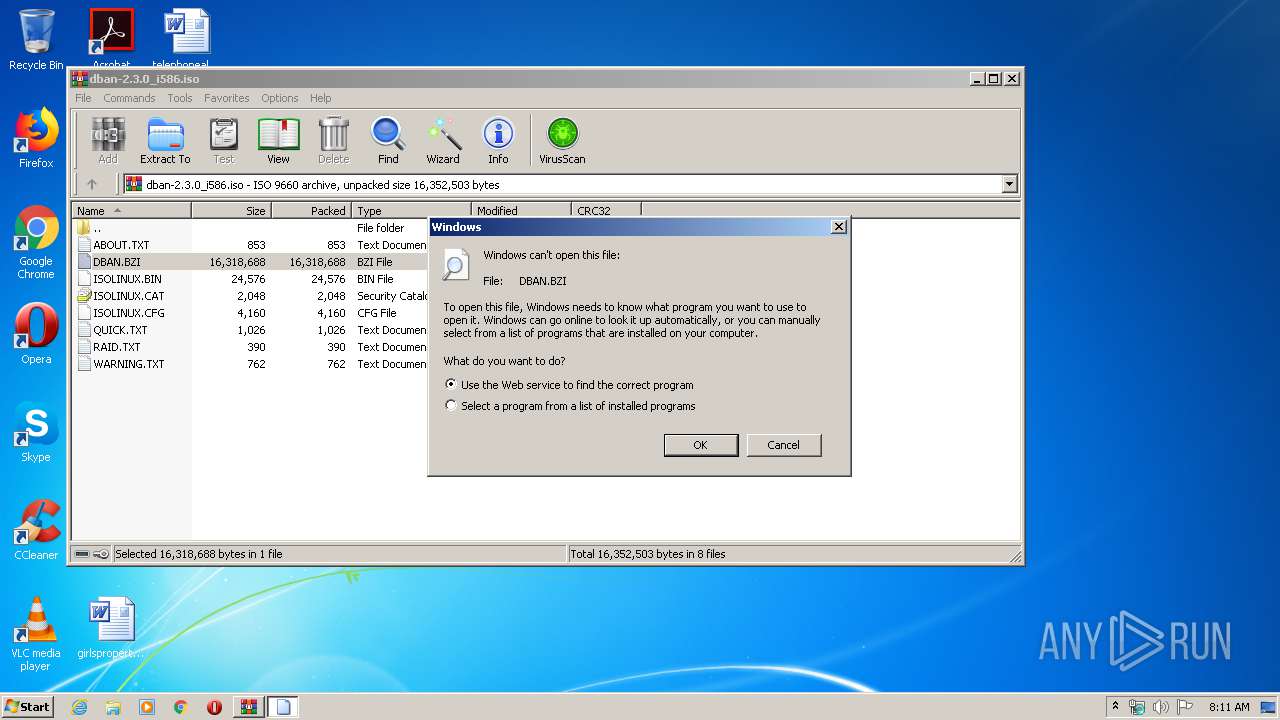
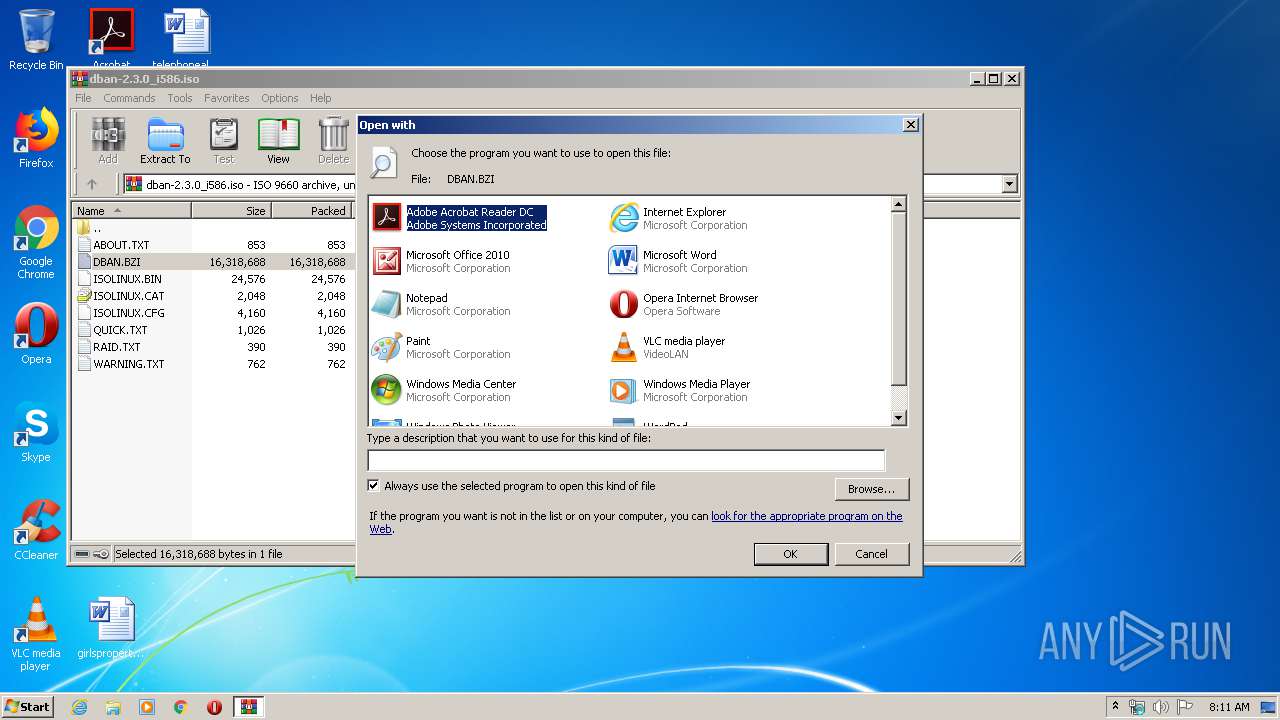
| 1812 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIa872.17212\DBAN.BZI | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIa872.18919\DBAN.BZI | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
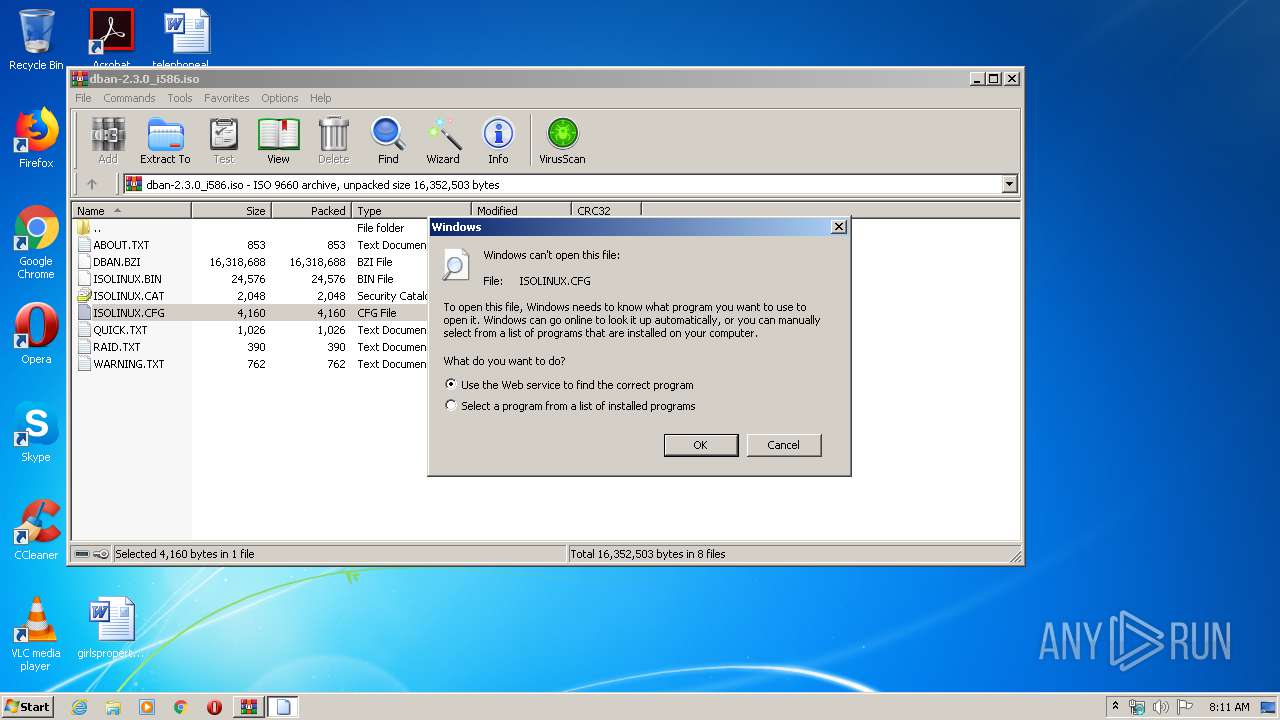
| 2852 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIa872.18151\ISOLINUX.CFG | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
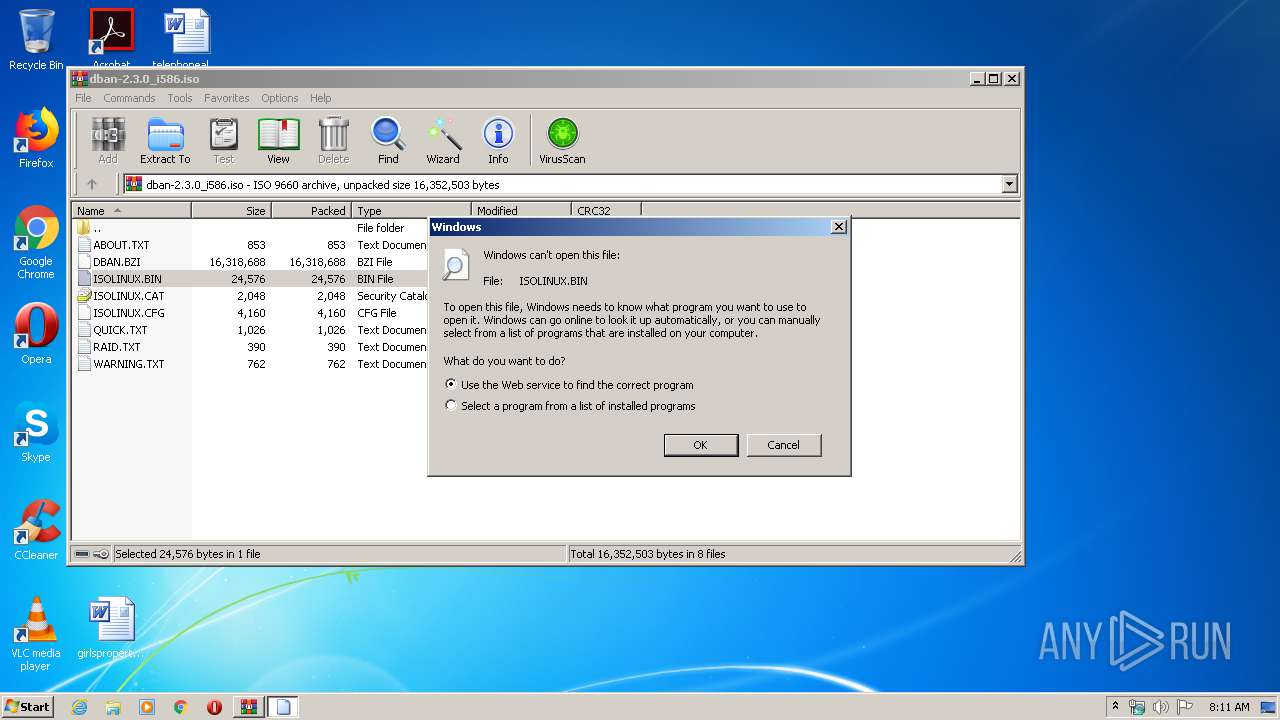
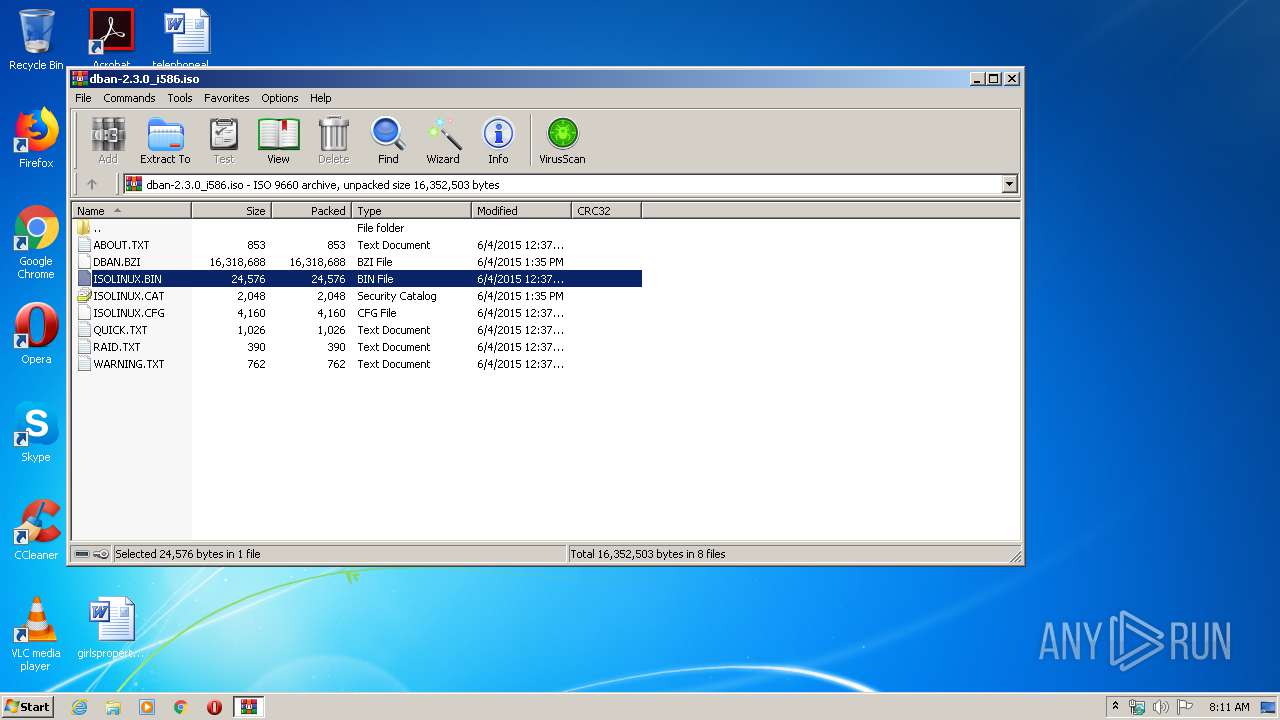
| 3624 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIa872.17691\ISOLINUX.BIN | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
524
Read events
489
Write events
35
Delete events
0
Modification events
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\dban-2.3.0_i586.iso | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (872) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @cryptext.dll,-6145 |
Value: Security Catalog | |||
| (PID) Process: | (2420) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
Executable files
0
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa872.17212\DBAN.BZI | — | |
MD5:— | SHA256:— | |||
| 872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa872.18919\DBAN.BZI | — | |
MD5:— | SHA256:— | |||
| 872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa872.17691\ISOLINUX.BIN | binary | |
MD5:539B9376A442BA303D8C724A3AC50AF8 | SHA256:53EF6D900EC8C05642830B6A190CABAF4E241F30C89EAD8E1E001DFF1B9A213E | |||
| 872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa872.18151\ISOLINUX.CFG | text | |
MD5:84EBBCE5AFB6AEE0342482CE8CBB0AAB | SHA256:B1F7C8D4D5187651B3BA9342EEF7DB2B48A080276271442C92FFD6C8E33C875B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report