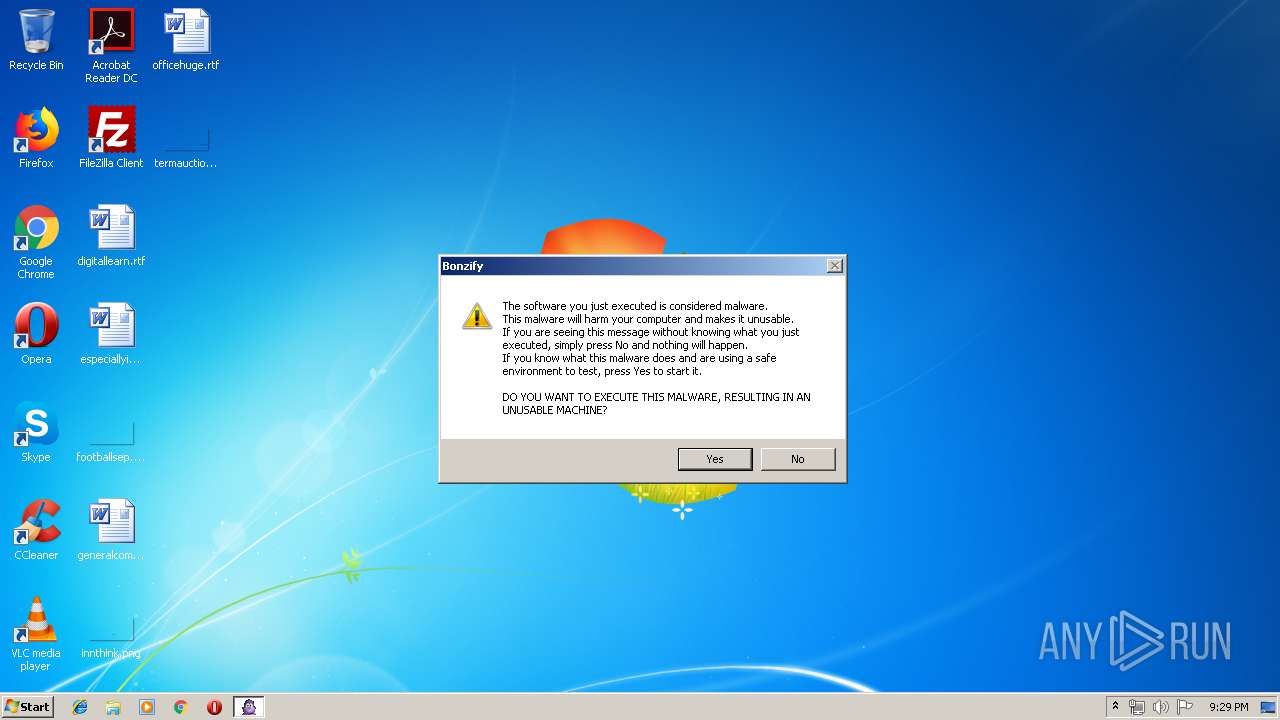
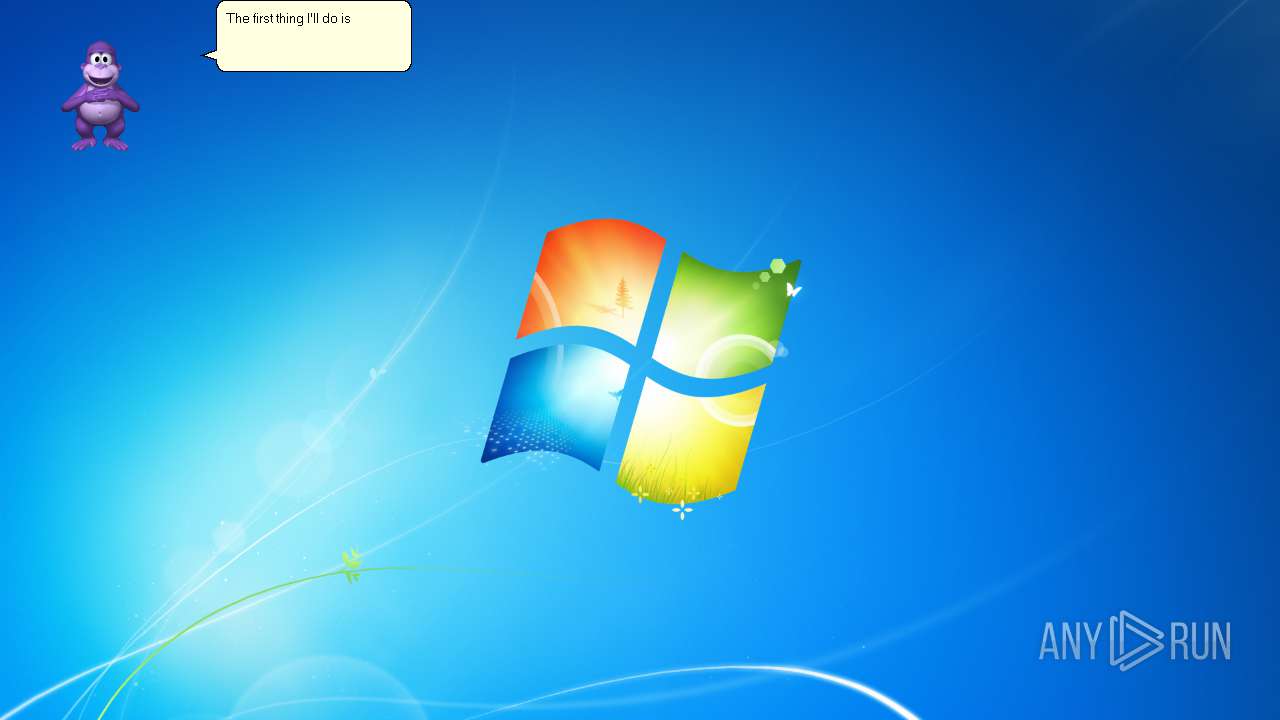
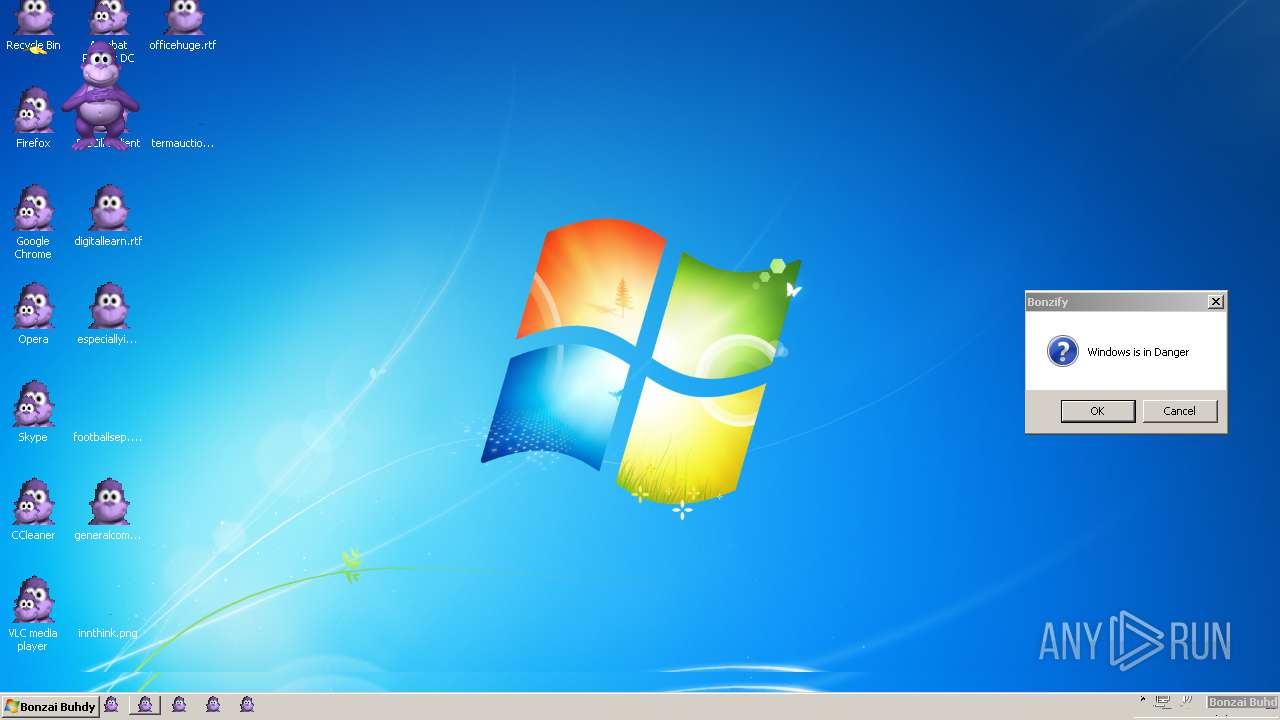
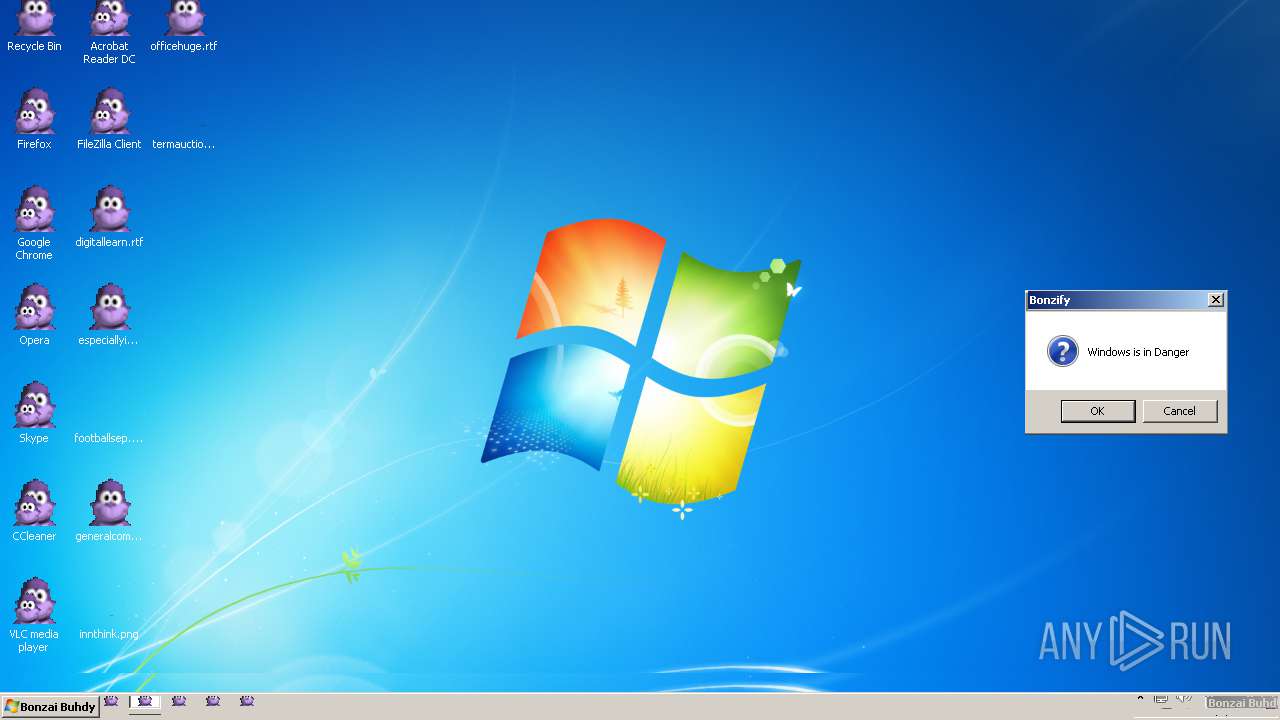
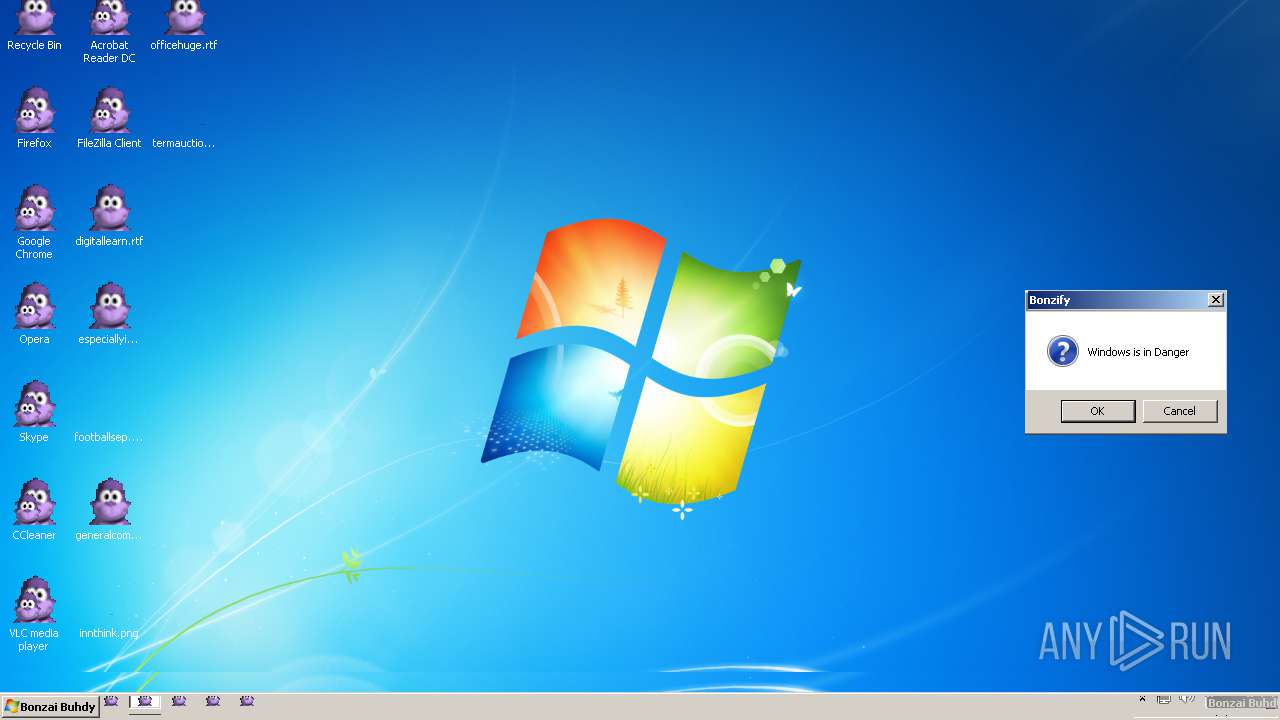
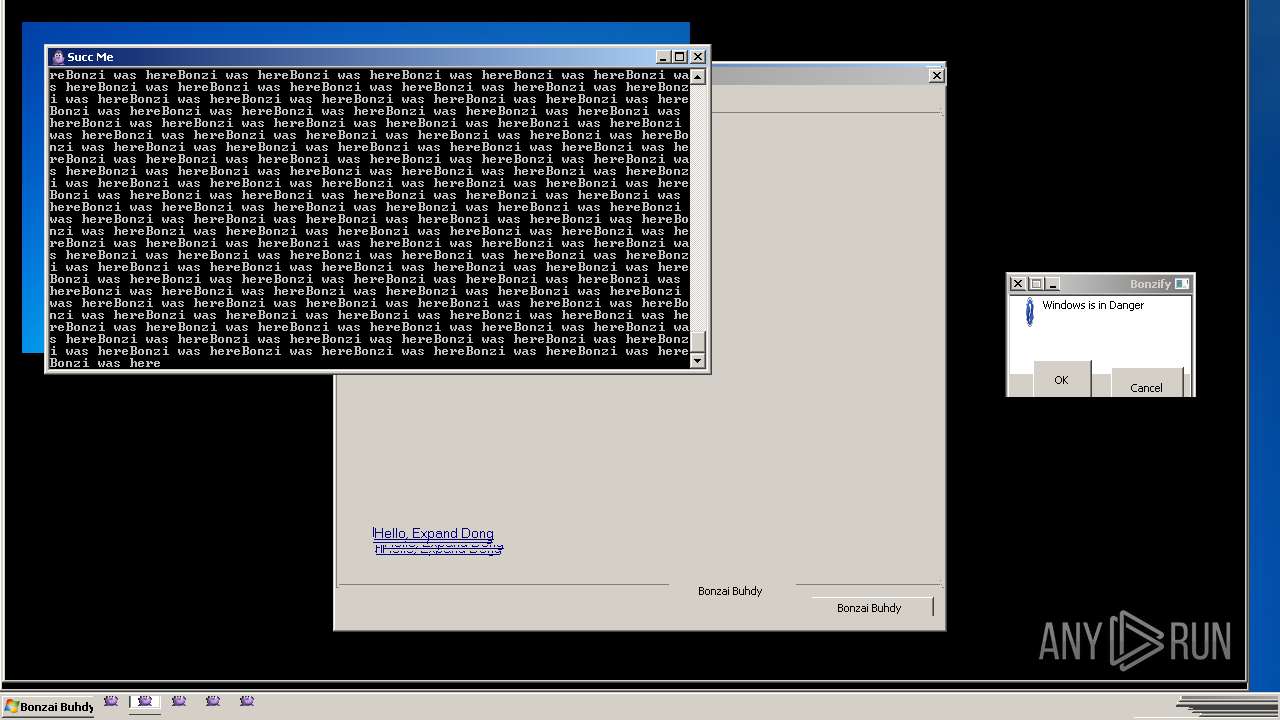
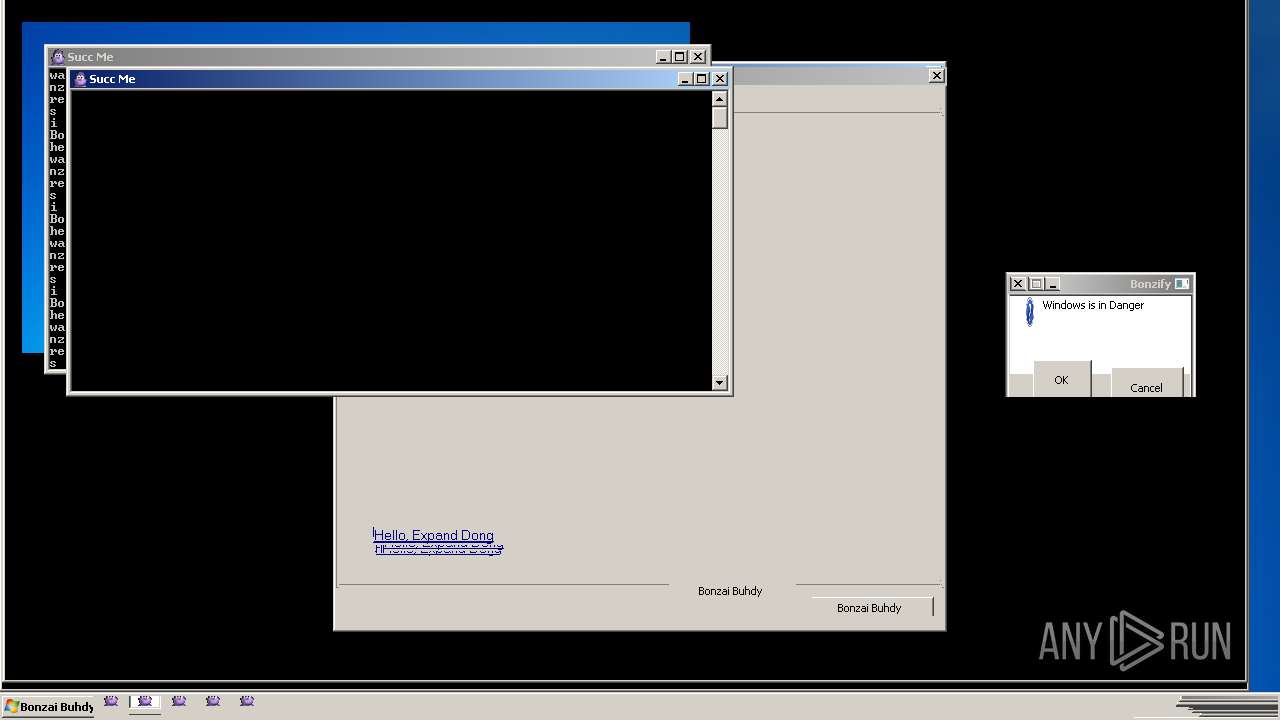
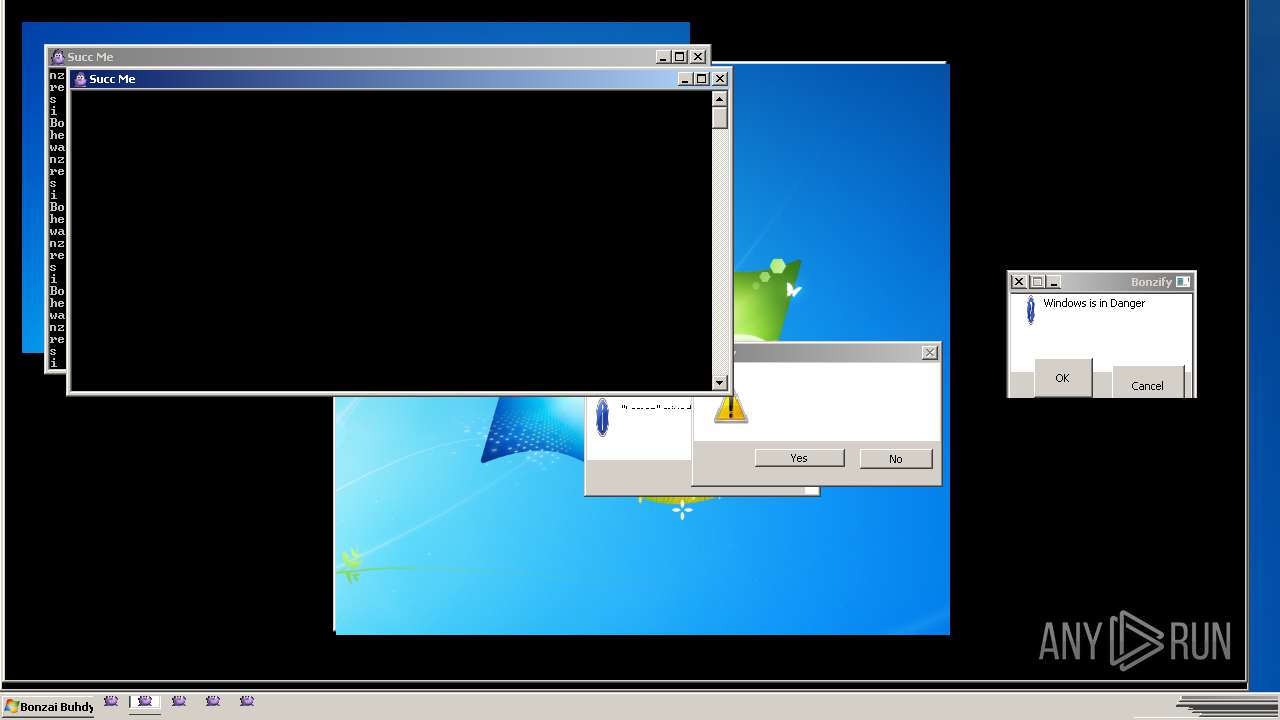
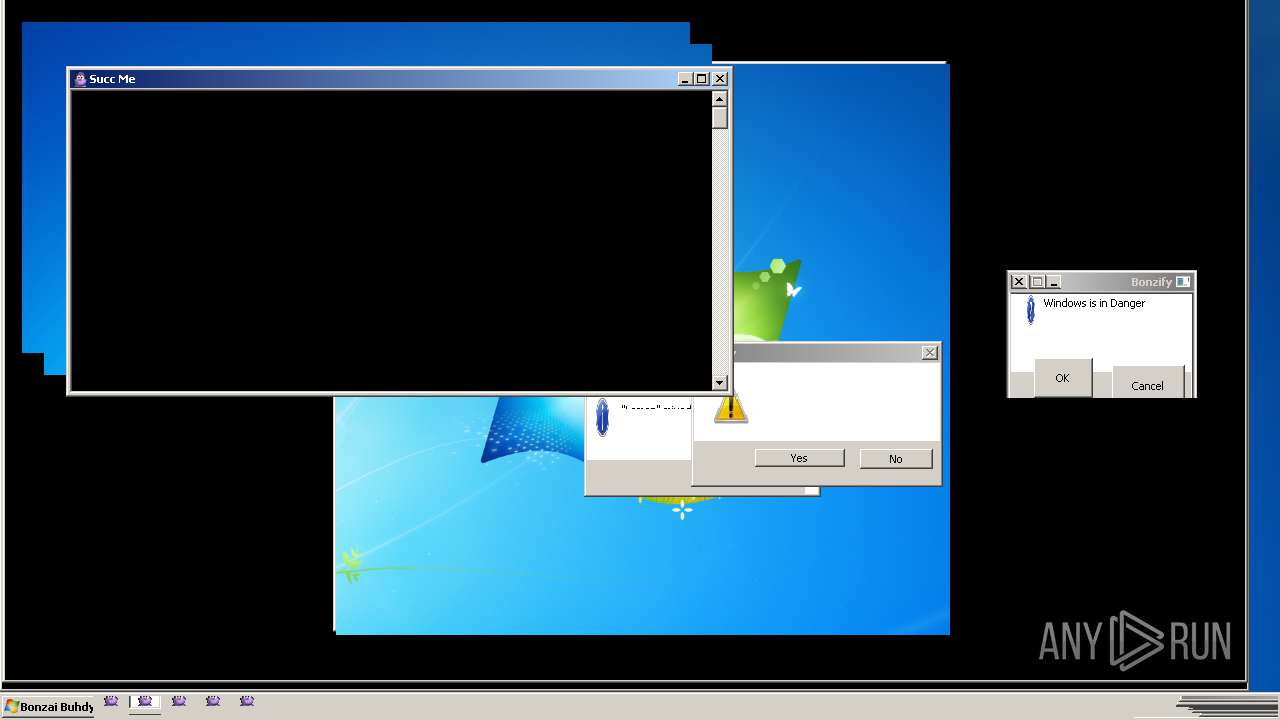
| File name: | Bonzify.exe |
| Full analysis: | https://app.any.run/tasks/a3ad0611-8976-4f40-8fc0-397c3bcd5548 |
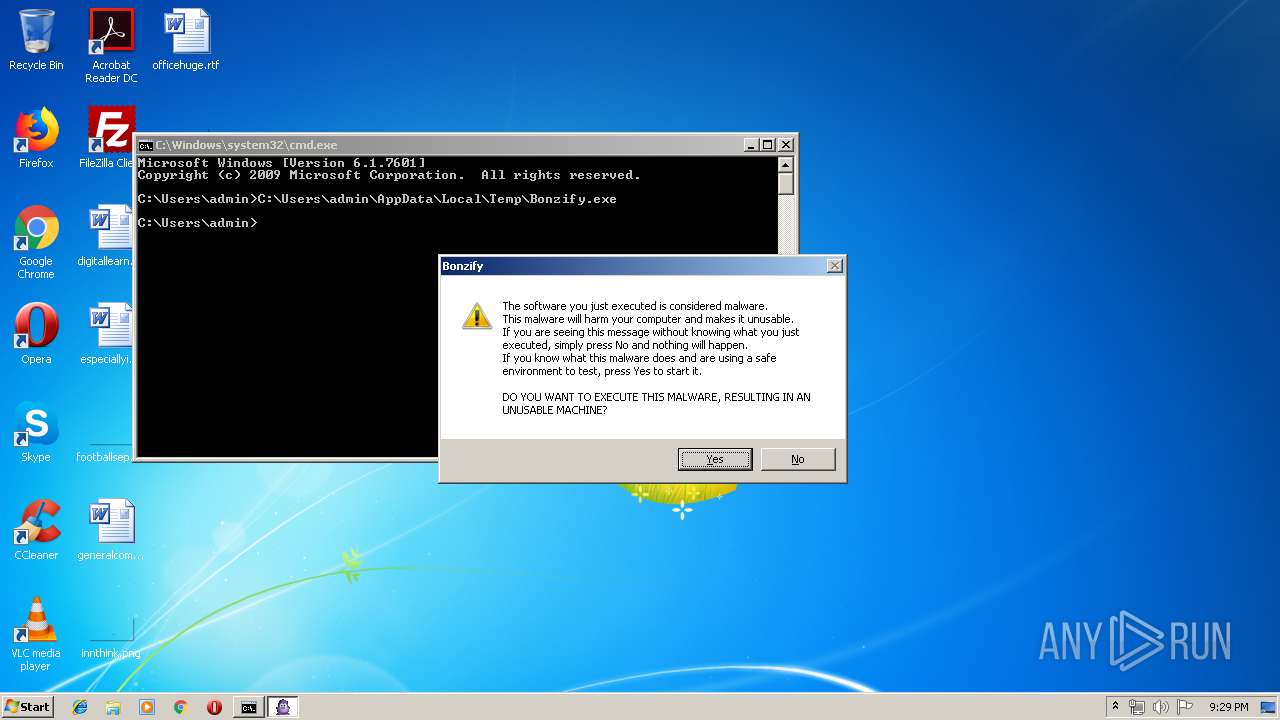
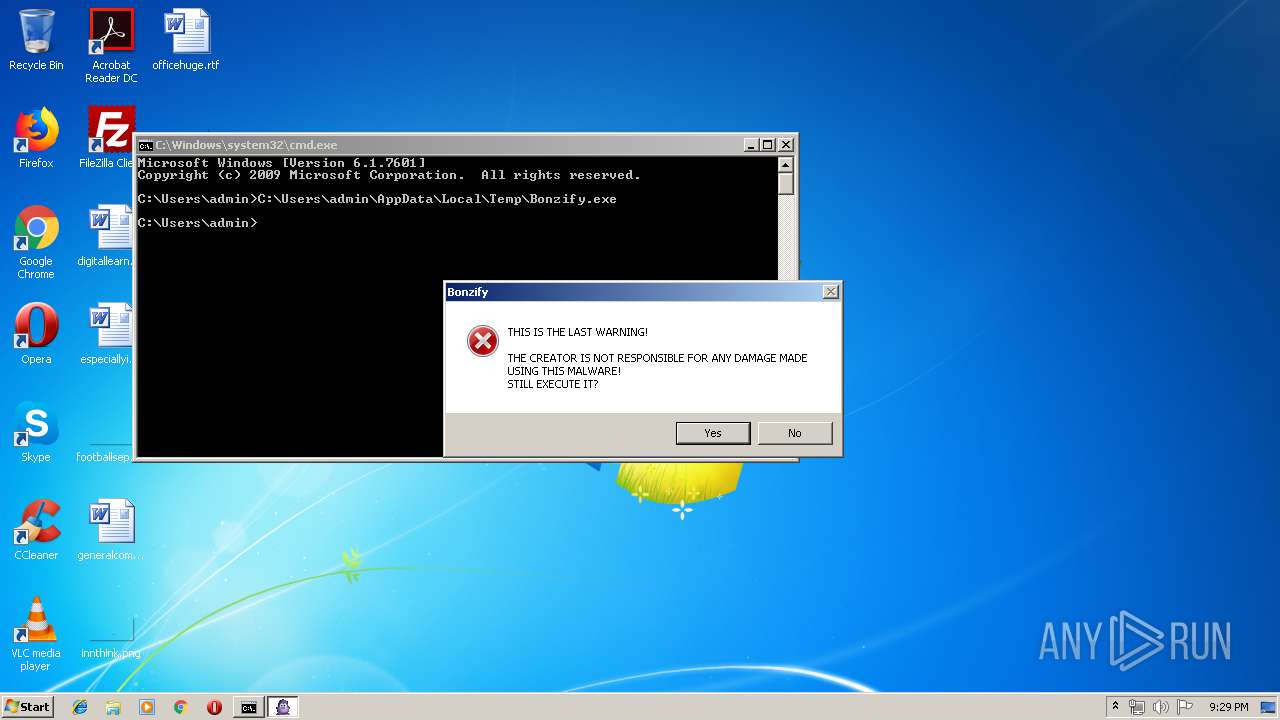
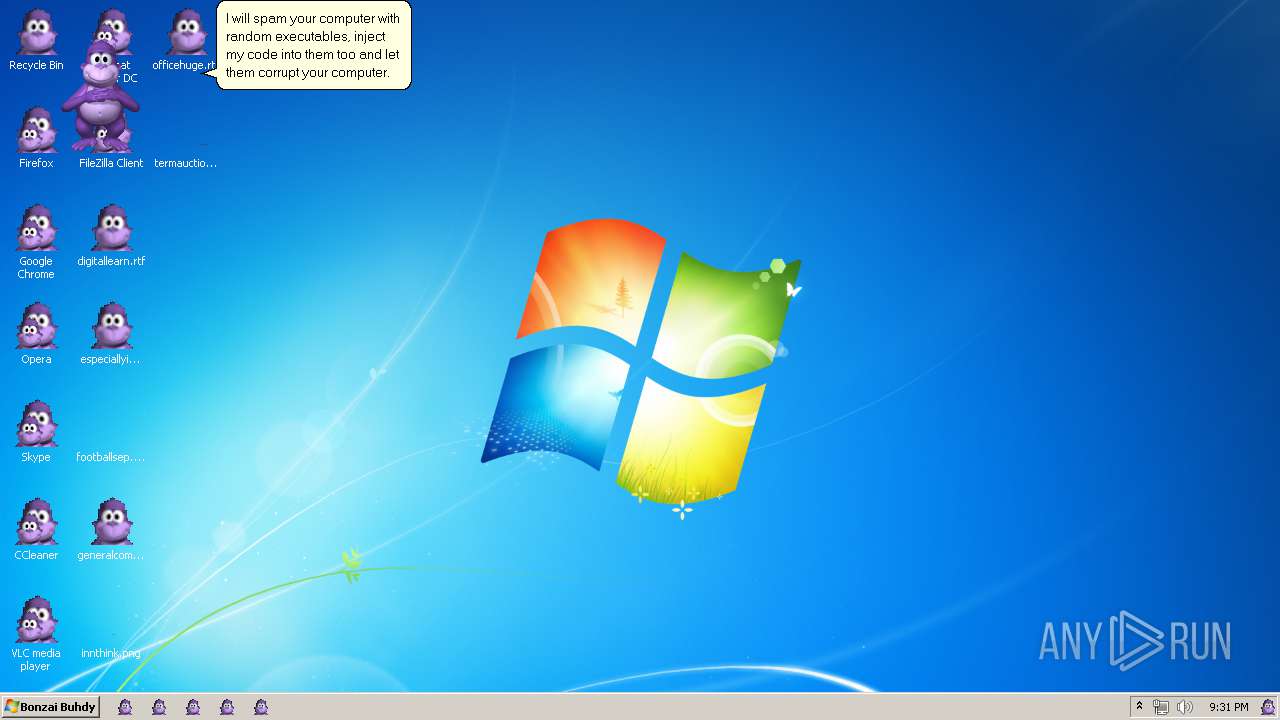
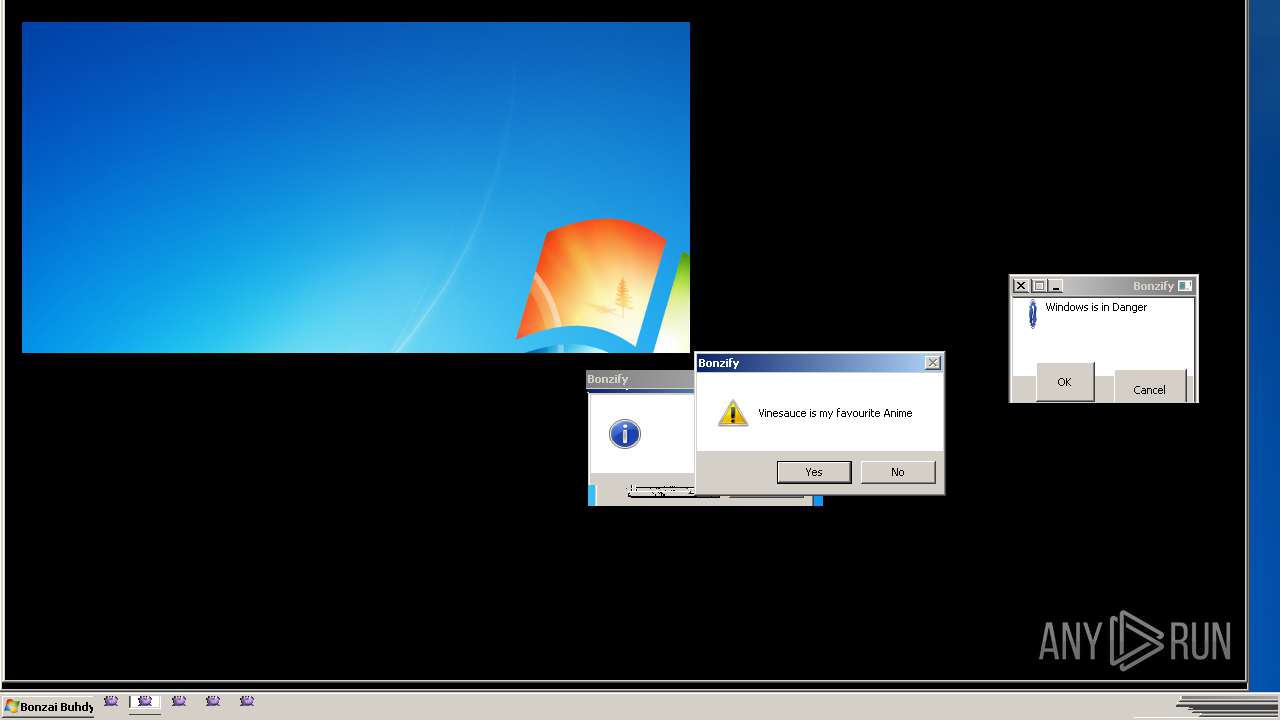
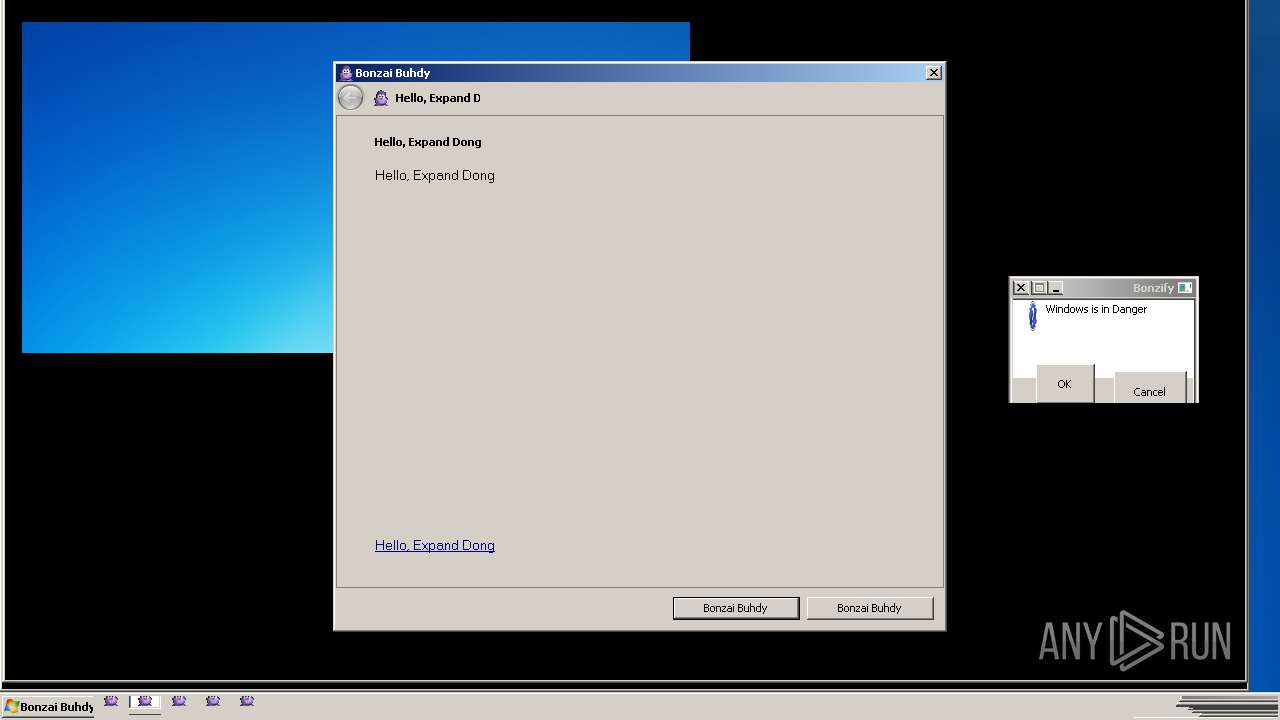
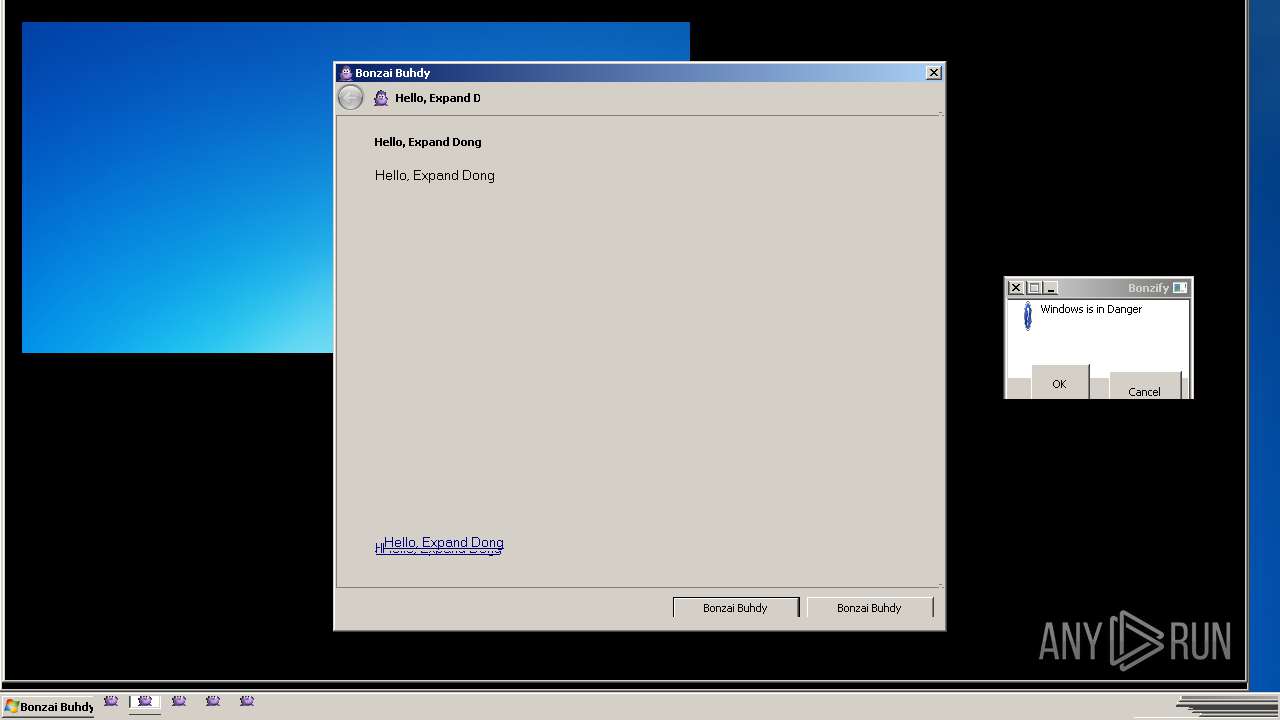
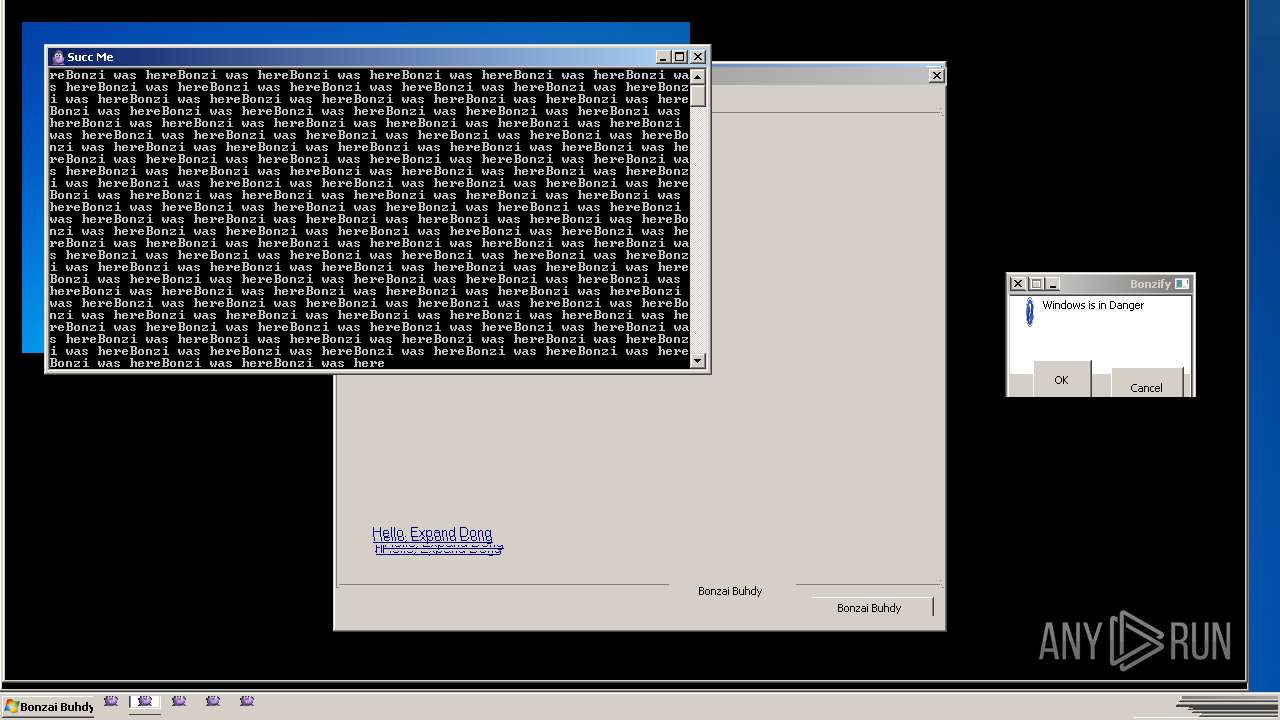
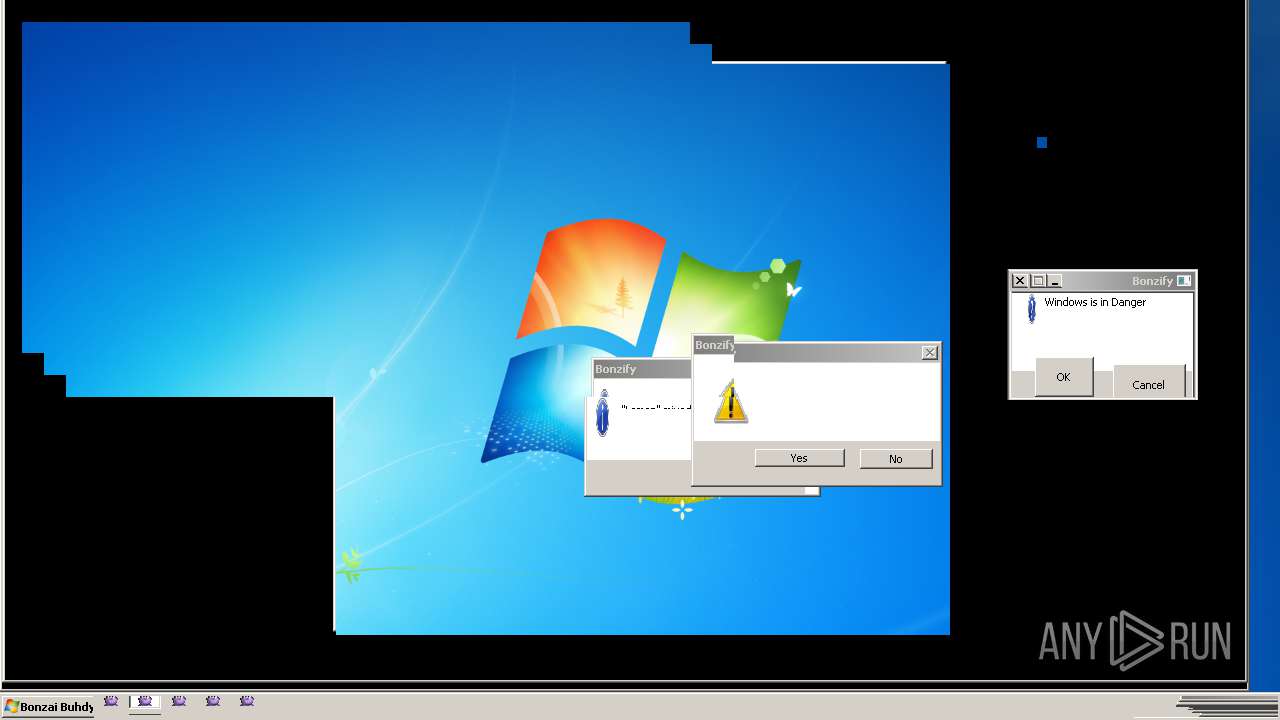
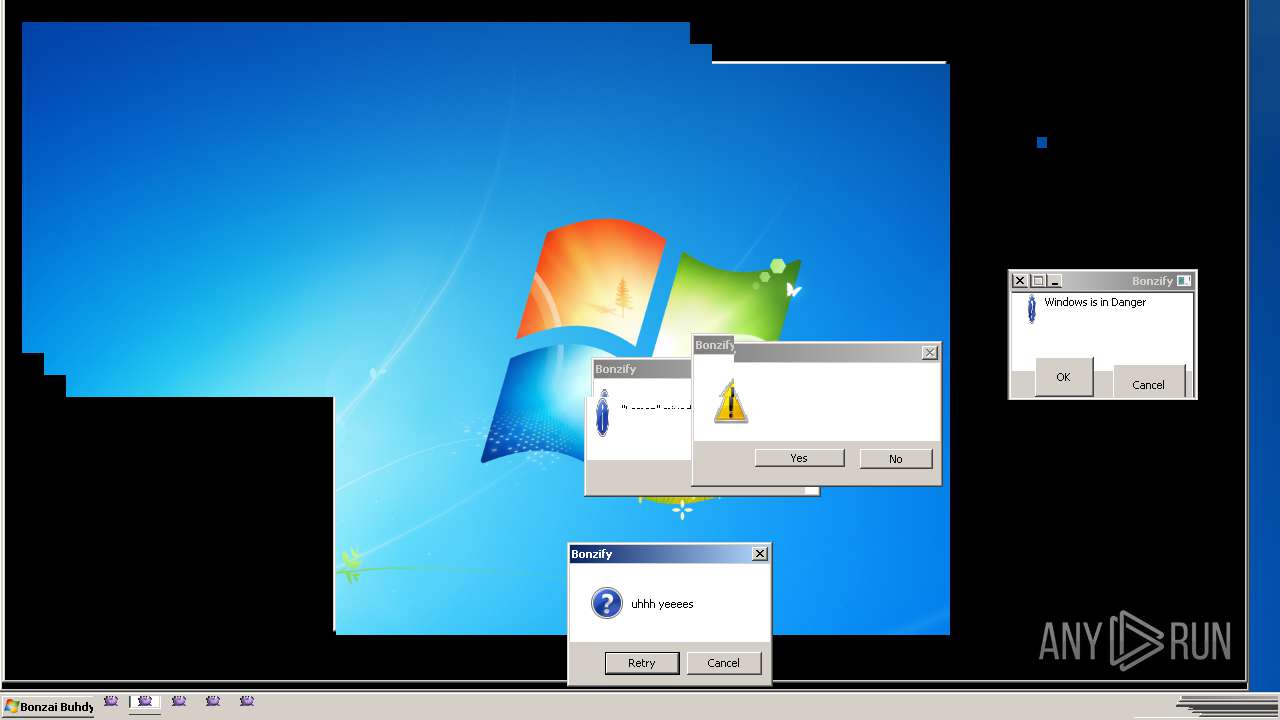
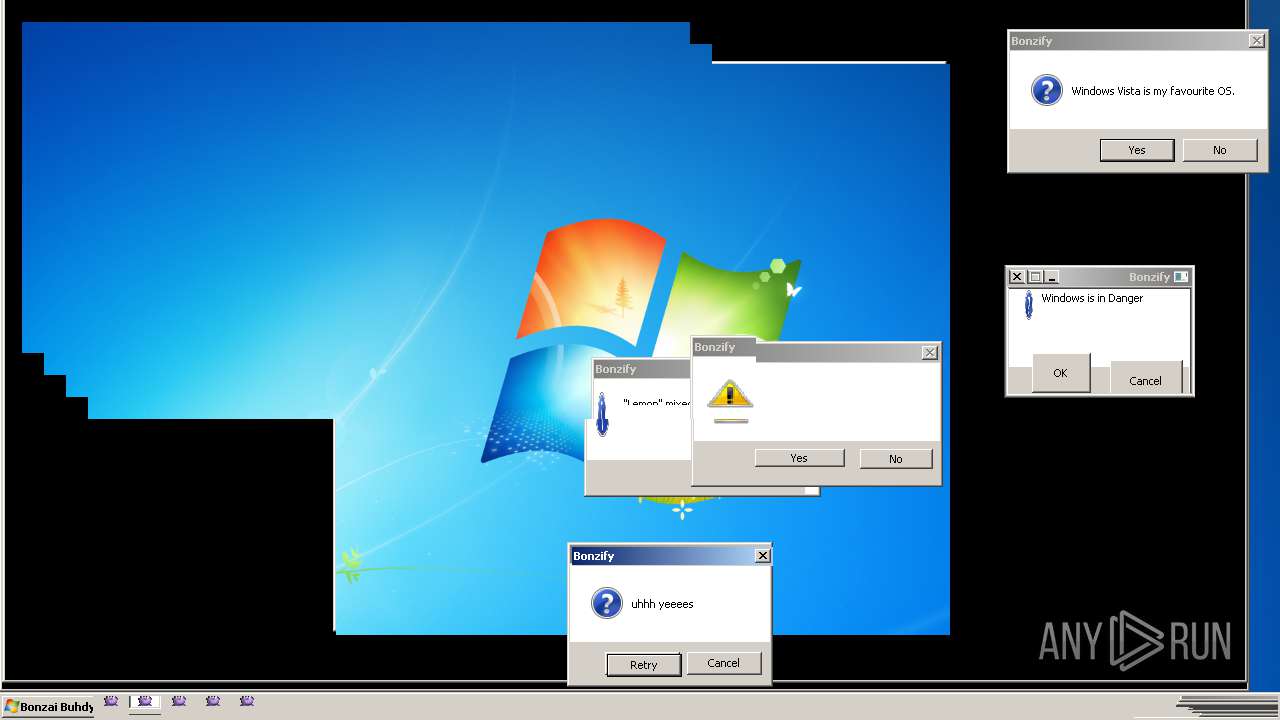
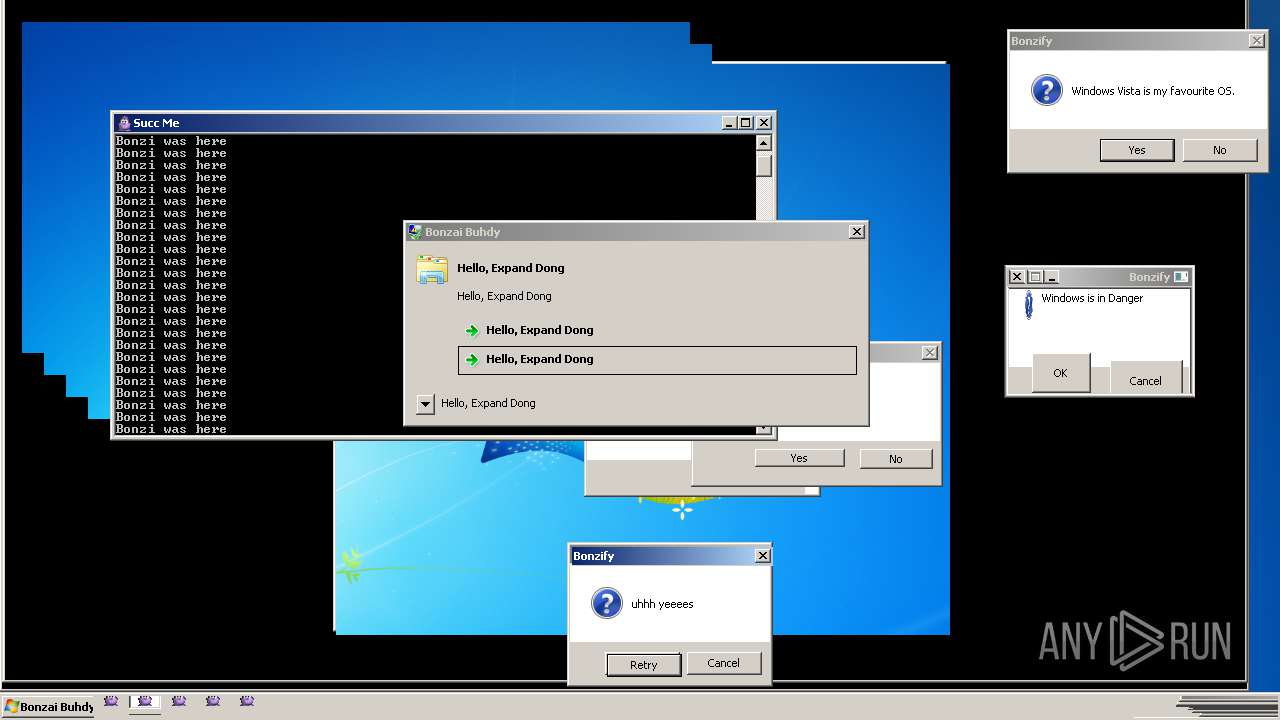
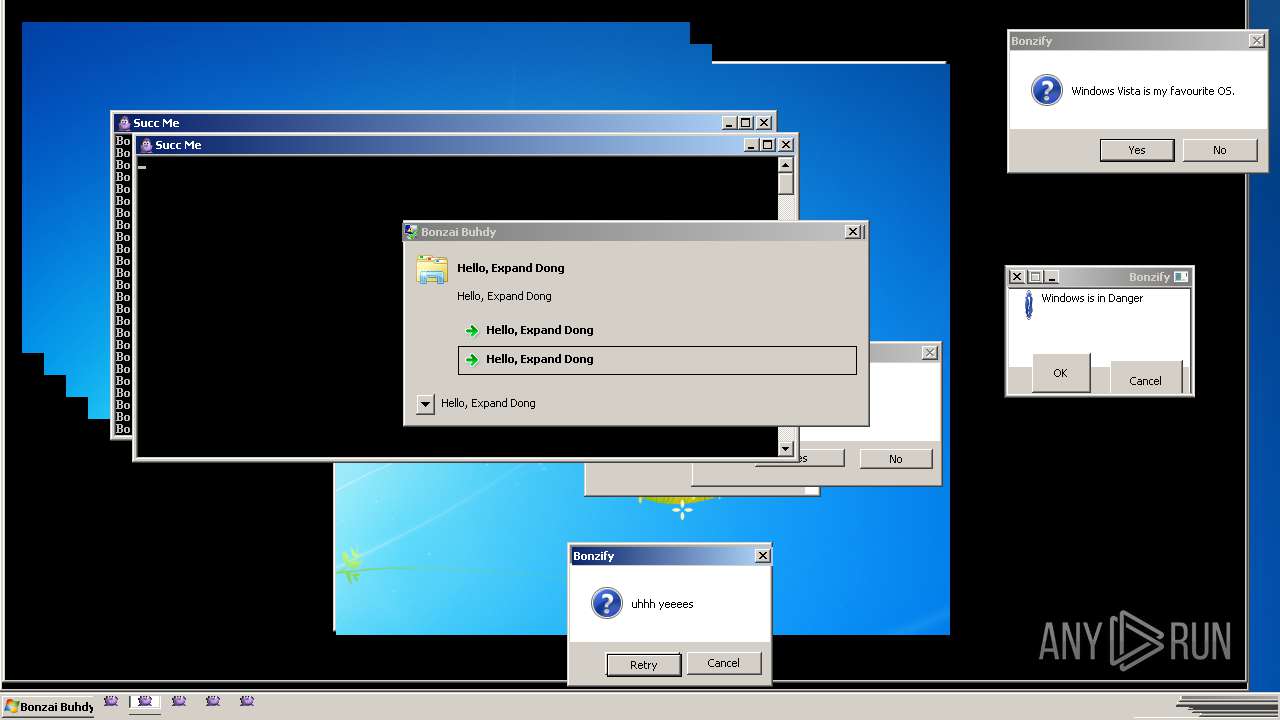
| Verdict: | Malicious activity |
| Analysis date: | May 08, 2019, 20:29:00 |
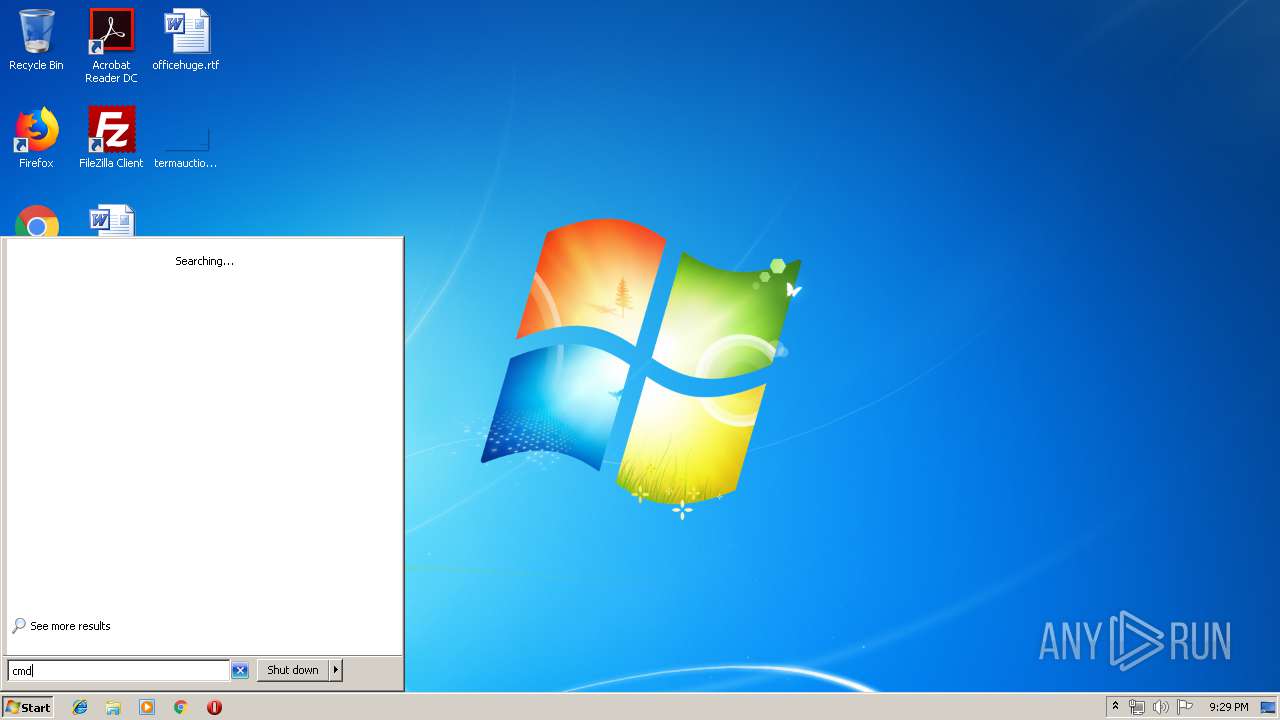
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BF5036B29D933F358D89584A97FC1F9F |
| SHA1: | AE286CF55C22ECEEBCEE02ACDA226787FBE5B44D |
| SHA256: | 761260840091E08192BE749FF8231788E6E59A47382841EEB791D48057A54750 |
| SSDEEP: | 196608:7dAMaWetTeAkLIdx751qFTkub//73lc6u7b5VJ2Yx5xIdk3:baWedh+Idx75QYub//73lc6u7bLMYxD |
MALICIOUS
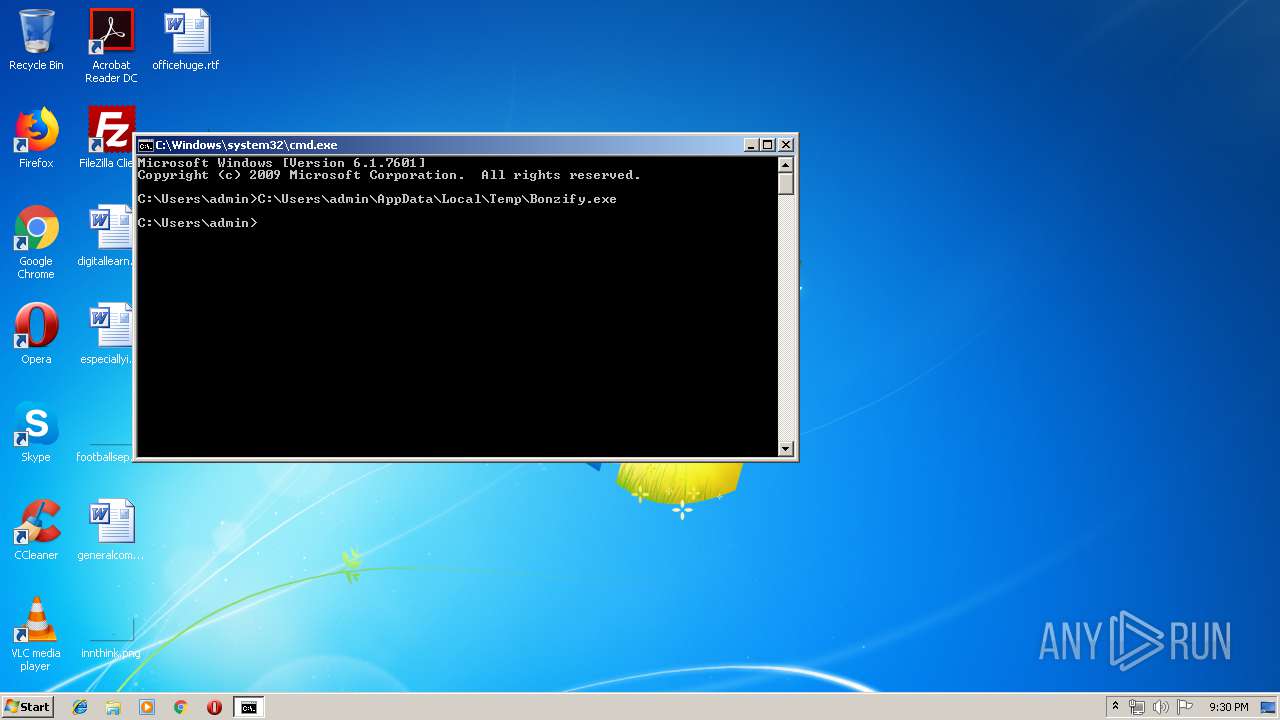
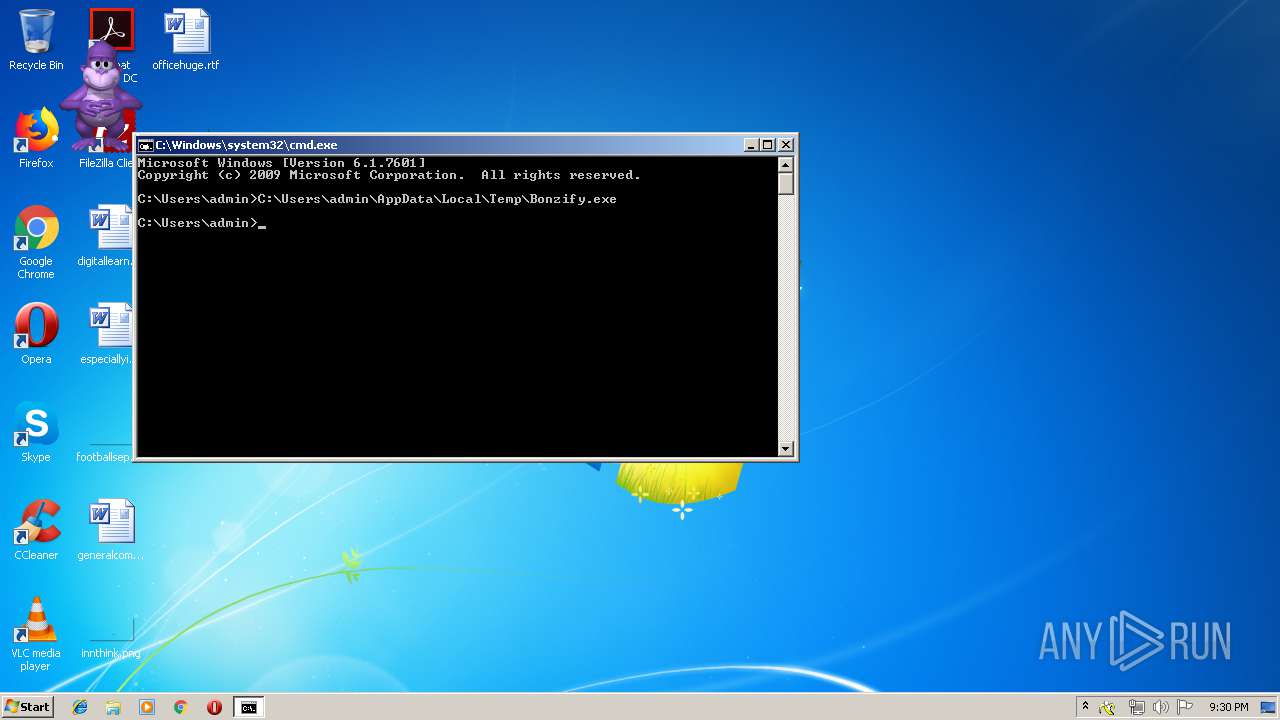
Application was dropped or rewritten from another process
- INSTALLER.exe (PID: 2664)
- INSTALLER.exe (PID: 3256)
Registers / Runs the DLL via REGSVR32.EXE
- INSTALLER.exe (PID: 2664)
- INSTALLER.exe (PID: 3256)
- Robocopy.exe (PID: 2180)
Changes the autorun value in the registry
- INSTALLER.exe (PID: 3256)
- Bonzify.exe (PID: 4056)
- WerFault.exe (PID: 2316)
- conhost.exe (PID: 2304)
- ntvdm.exe (PID: 876)
- rekeywiz.exe (PID: 2168)
- WerFault.exe (PID: 2292)
- WerFault.exe (PID: 1556)
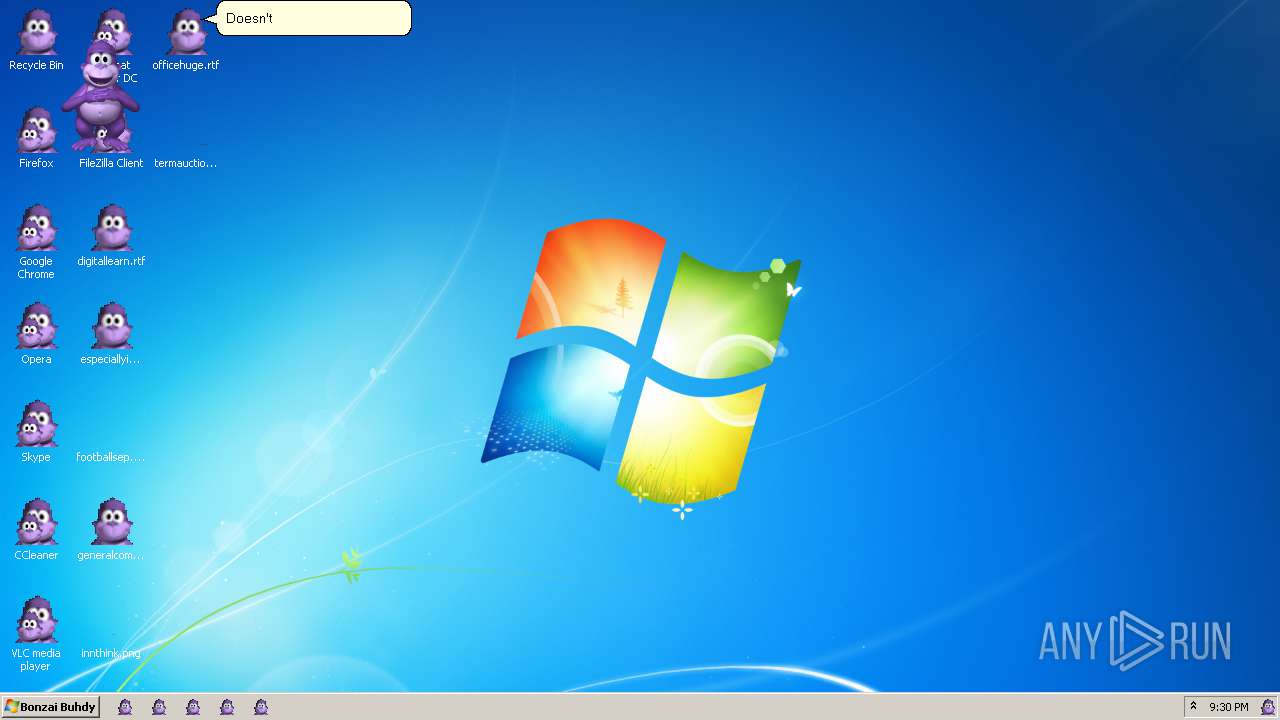
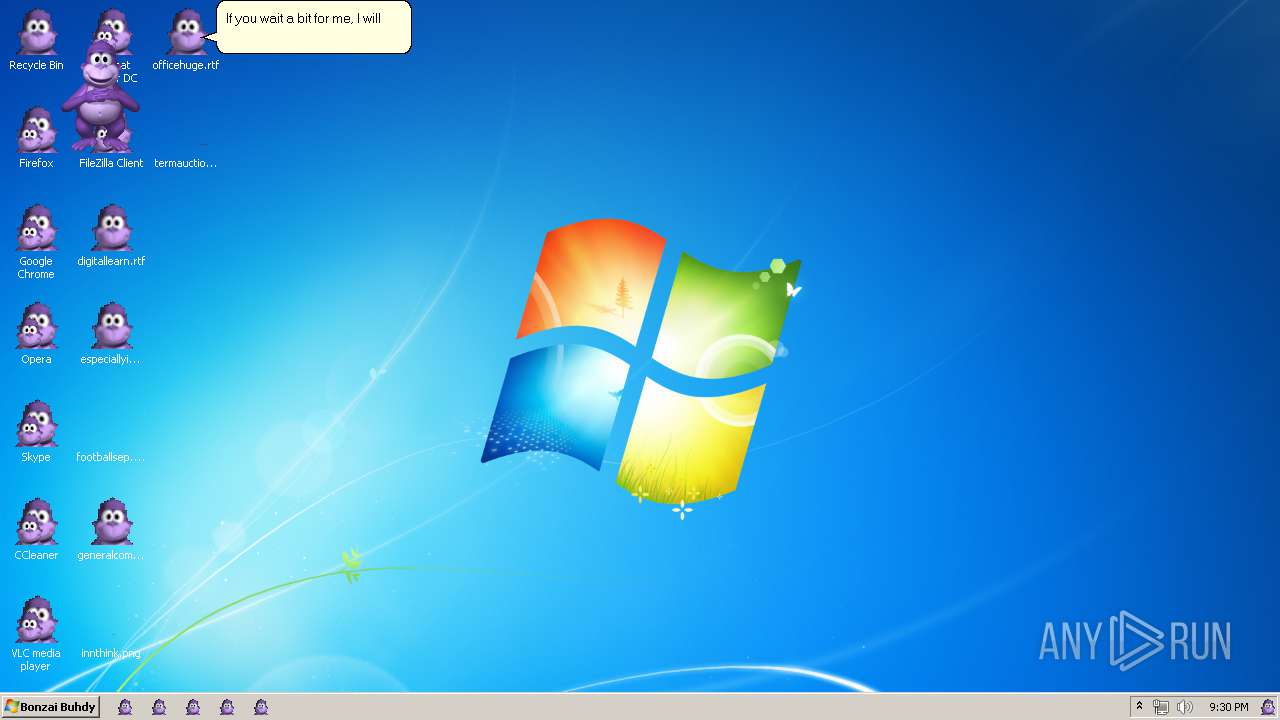
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2432)
- INSTALLER.exe (PID: 2664)
- INSTALLER.exe (PID: 3256)
- regsvr32.exe (PID: 3448)
- DllHost.exe (PID: 2904)
- AgentSvr.exe (PID: 3404)
- explorer.exe (PID: 3752)
- SearchFilterHost.exe (PID: 1644)
- SearchProtocolHost.exe (PID: 2320)
- opera.exe (PID: 3432)
- extrac32.exe (PID: 1536)
- charmap.exe (PID: 184)
- conhost.exe (PID: 592)
- MdRes.exe (PID: 3620)
- WerFault.exe (PID: 2316)
- convert.exe (PID: 1828)
- svchost.exe (PID: 2916)
- ntvdm.exe (PID: 876)
- efsui.exe (PID: 2076)
- cmmon32.exe (PID: 2448)
- WerFault.exe (PID: 3352)
- dpnsvr.exe (PID: 3520)
- conhost.exe (PID: 2548)
- nltest.exe (PID: 2524)
- conhost.exe (PID: 2832)
- conhost.exe (PID: 2304)
- conhost.exe (PID: 2056)
- netsh.exe (PID: 2852)
- conhost.exe (PID: 3808)
- change.exe (PID: 1344)
- conhost.exe (PID: 3916)
- rekeywiz.exe (PID: 2168)
- Robocopy.exe (PID: 2180)
- conhost.exe (PID: 2344)
- conhost.exe (PID: 3524)
- conhost.exe (PID: 1920)
- unlodctr.exe (PID: 2920)
- conhost.exe (PID: 3592)
- wlanext.exe (PID: 1216)
- svchost.exe (PID: 392)
- MigAutoPlay.exe (PID: 460)
- WerFault.exe (PID: 2384)
- lodctr.exe (PID: 3680)
- WerFault.exe (PID: 2292)
- conhost.exe (PID: 3364)
- WerFault.exe (PID: 1688)
- WerFault.exe (PID: 2464)
- conhost.exe (PID: 3844)
- TapiUnattend.exe (PID: 2312)
- WerFault.exe (PID: 2116)
- SearchFilterHost.exe (PID: 328)
- secinit.exe (PID: 3784)
- TrustedInstaller.exe (PID: 2192)
- sppsvc.exe (PID: 2820)
- conhost.exe (PID: 3492)
- WerFault.exe (PID: 504)
- conhost.exe (PID: 4076)
- WerFault.exe (PID: 1556)
- AdobeCollabSync.exe (PID: 3604)
- conhost.exe (PID: 1804)
- PushPrinterConnections.exe (PID: 3780)
- OptionalFeatures.exe (PID: 2684)
- CLVIEW.EXE (PID: 1012)
- conhost.exe (PID: 3092)
- conhost.exe (PID: 276)
- RunLegacyCPLElevated.exe (PID: 2092)
- explorer.exe (PID: 1680)
- klist.exe (PID: 3968)
- TrustedInstaller.exe (PID: 1140)
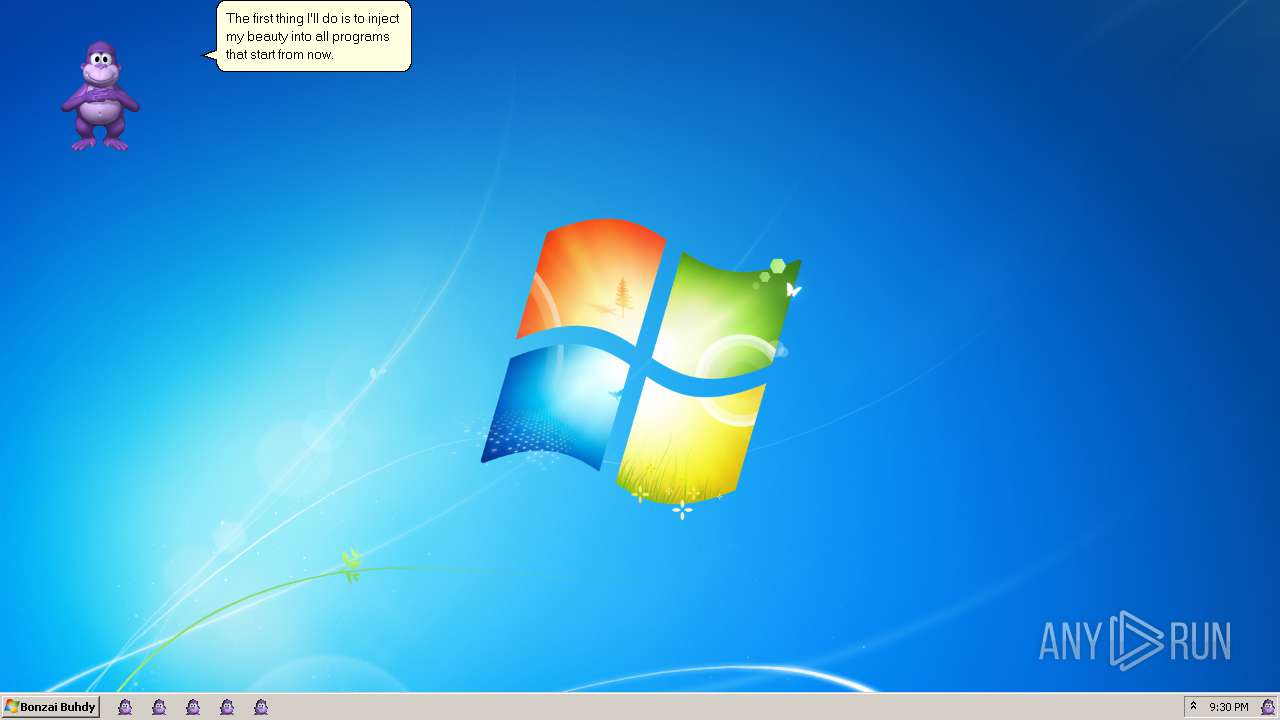
Changes AppInit_DLLs value (autorun option)
- Bonzify.exe (PID: 4056)
Loads the Task Scheduler COM API
- explorer.exe (PID: 3752)
Changes internet zones settings
- explorer.exe (PID: 3752)
- SearchProtocolHost.exe (PID: 2320)
- conhost.exe (PID: 592)
- conhost.exe (PID: 2304)
- svchost.exe (PID: 2916)
- rekeywiz.exe (PID: 2168)
- svchost.exe (PID: 392)
- conhost.exe (PID: 2344)
- TrustedInstaller.exe (PID: 2192)
- WerFault.exe (PID: 2292)
- WerFault.exe (PID: 1556)
- conhost.exe (PID: 4076)
SUSPICIOUS
Creates files in the Windows directory
- Bonzify.exe (PID: 4056)
- INSTALLER.exe (PID: 3256)
- INSTALLER.exe (PID: 2664)
- ntvdm.exe (PID: 876)
- TrustedInstaller.exe (PID: 2192)
- WerFault.exe (PID: 1556)
Creates COM task schedule object
- regsvr32.exe (PID: 2832)
- regsvr32.exe (PID: 808)
- regsvr32.exe (PID: 1868)
- regsvr32.exe (PID: 3536)
- regsvr32.exe (PID: 3904)
- regsvr32.exe (PID: 3136)
- regsvr32.exe (PID: 2432)
- regsvr32.exe (PID: 3448)
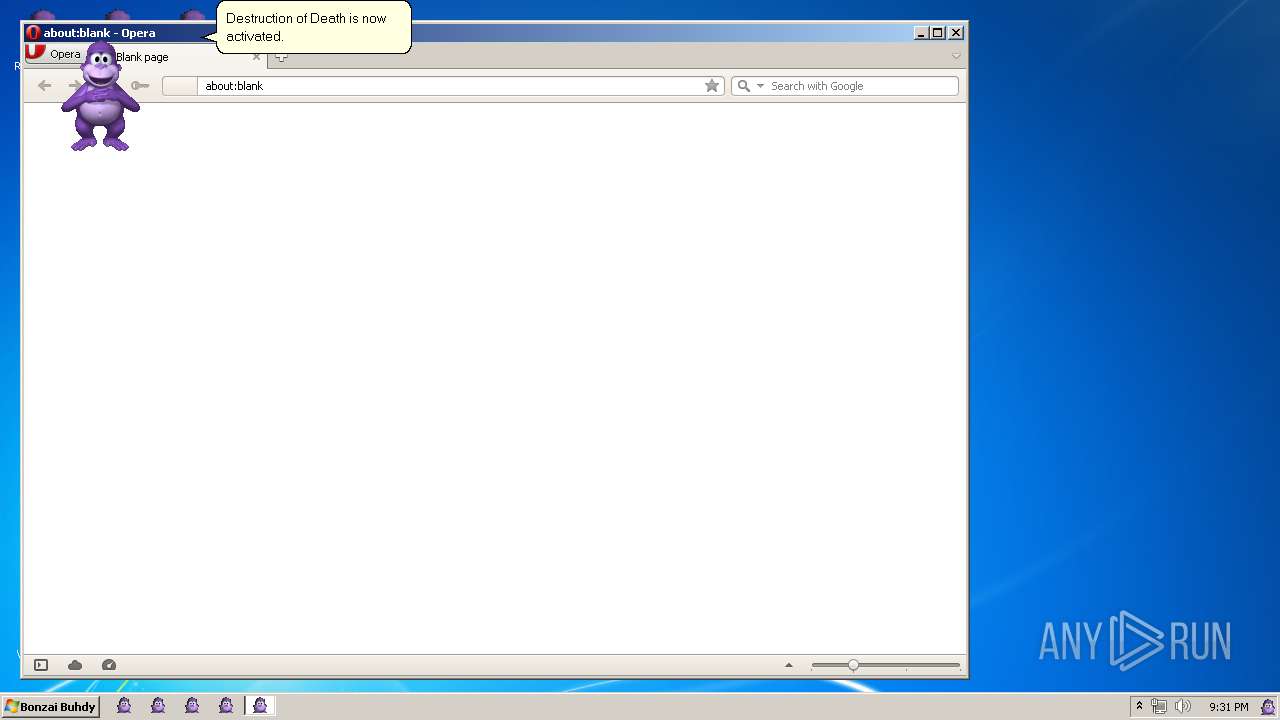
- opera.exe (PID: 3432)
- SearchProtocolHost.exe (PID: 2320)
- svchost.exe (PID: 2916)
- rekeywiz.exe (PID: 2168)
- explorer.exe (PID: 3752)
- MigAutoPlay.exe (PID: 460)
- svchost.exe (PID: 392)
- WerFault.exe (PID: 2292)
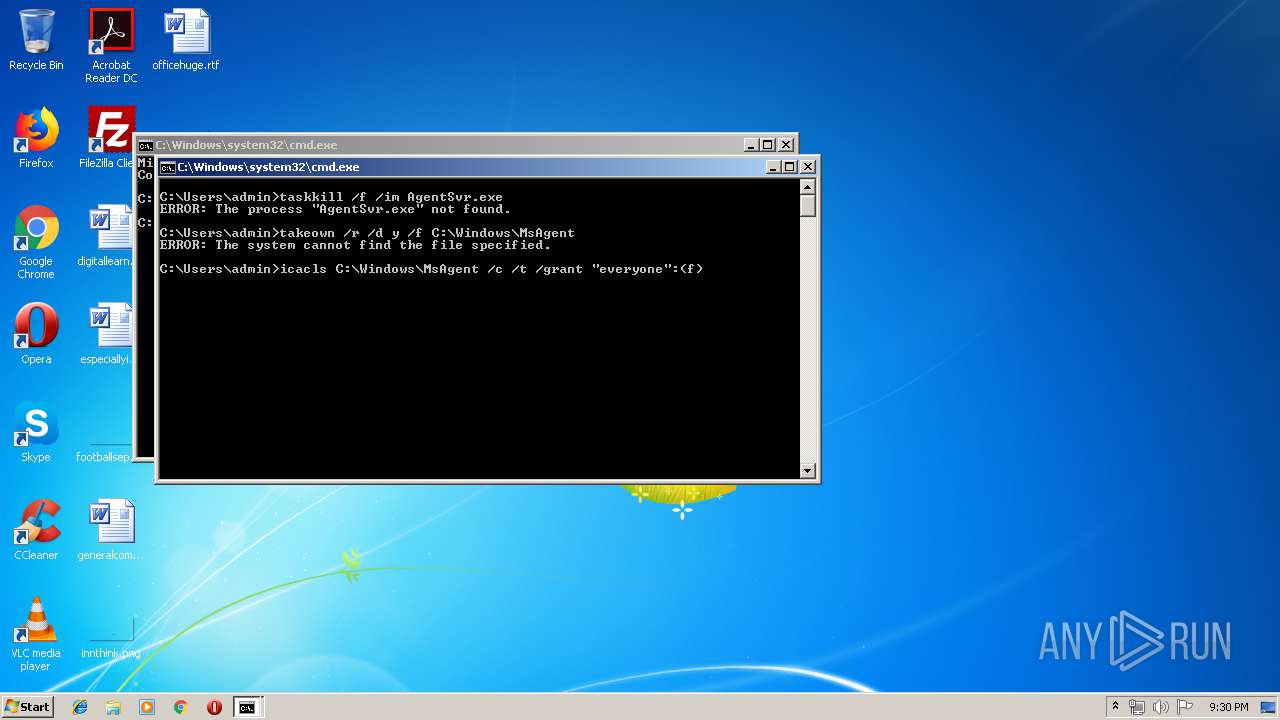
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 2900)
Executable content was dropped or overwritten
- Bonzify.exe (PID: 4056)
- INSTALLER.exe (PID: 3256)
- TrustedInstaller.exe (PID: 2192)
- WerFault.exe (PID: 1556)
Starts CMD.EXE for commands execution
- Bonzify.exe (PID: 4056)
Removes files from Windows directory
- INSTALLER.exe (PID: 2664)
- INSTALLER.exe (PID: 3256)
- ntvdm.exe (PID: 876)
- WerFault.exe (PID: 1556)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2900)
Creates a software uninstall entry
- INSTALLER.exe (PID: 3256)
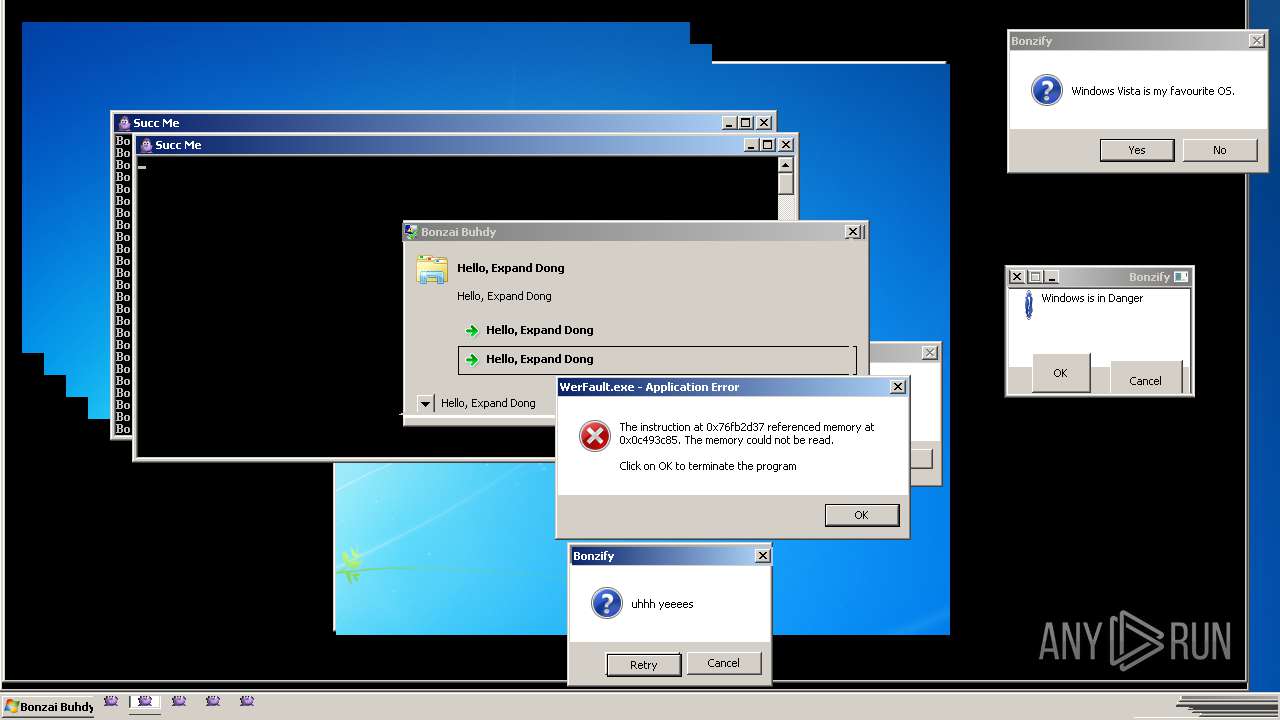
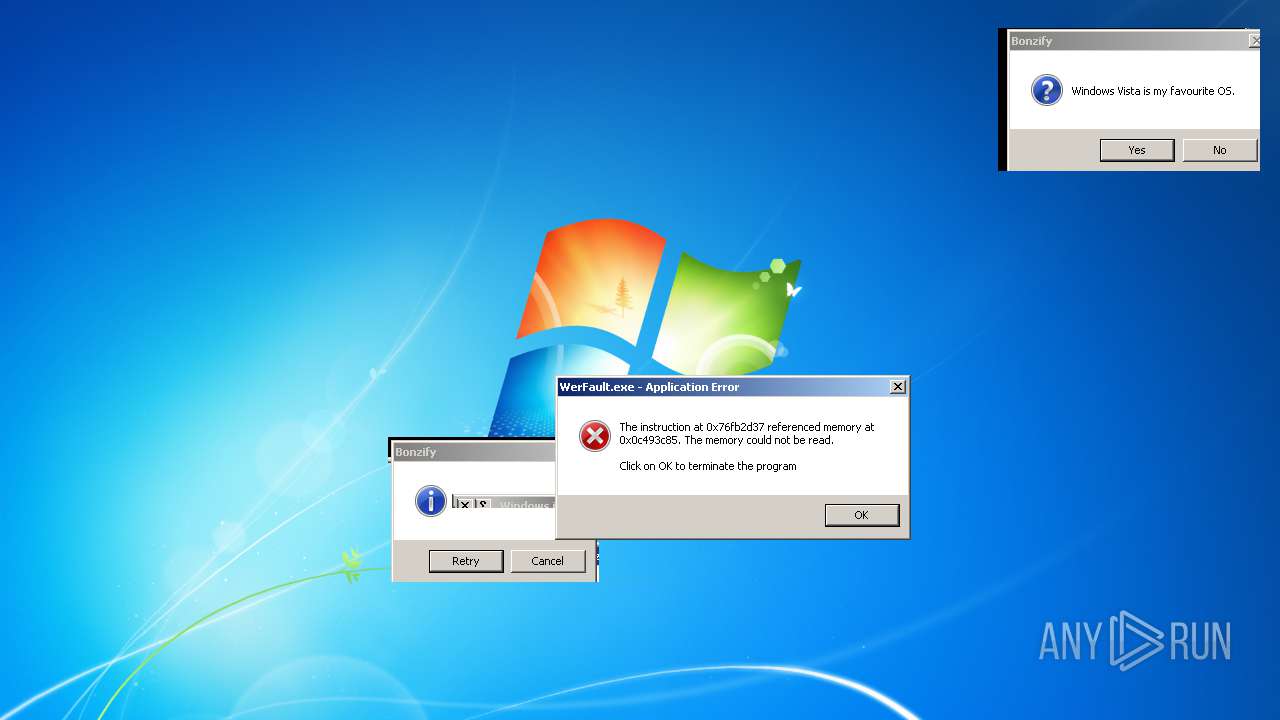
Executes application which crashes
- svchost.exe (PID: 2916)
- MigAutoPlay.exe (PID: 460)
Modifies the open verb of a shell class
- svchost.exe (PID: 2916)
- explorer.exe (PID: 3752)
- svchost.exe (PID: 392)
Uses NETSH.EXE for network configuration
- explorer.exe (PID: 3752)
INFO
Dropped object may contain Bitcoin addresses
- INSTALLER.exe (PID: 3256)
- Bonzify.exe (PID: 4056)
Creates files in the user directory
- opera.exe (PID: 3432)
Application was crashed
- SearchFilterHost.exe (PID: 1644)
- SearchProtocolHost.exe (PID: 2320)
- conhost.exe (PID: 2304)
- conhost.exe (PID: 3524)
- Robocopy.exe (PID: 2180)
- explorer.exe (PID: 3752)
- WerFault.exe (PID: 2292)
- TrustedInstaller.exe (PID: 2192)
- conhost.exe (PID: 3092)
Changes internet zones settings
- opera.exe (PID: 3432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (80.4) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.2) |
| .exe | | | Win64 Executable (generic) (7.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.7) |
| .exe | | | Win32 Executable (generic) (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:16 04:19:10+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 4096 |
| InitializedDataSize: | 6695936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16b0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Dec-2018 03:19:10 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Dec-2018 03:19:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000E46 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.30794 |
.rdata | 0x00002000 | 0x000012E4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41988 |
.data | 0x00004000 | 0x00000020 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00005000 | 0x00661228 | 0x00661400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.85029 |
.reloc | 0x00667000 | 0x0000018C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.54097 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
100 | 7.82633 | 5249795 | UNKNOWN | UNKNOWN | DATA |
101 | 7.78087 | 400536 | UNKNOWN | UNKNOWN | DATA |
102 | 7.93147 | 1021232 | UNKNOWN | UNKNOWN | DATA |
103 | 4.86014 | 158 | UNKNOWN | UNKNOWN | DATA |
104 | 4.44475 | 45 | UNKNOWN | UNKNOWN | DATA |
110 | 5.62084 | 14336 | UNKNOWN | UNKNOWN | DATA |
IDI_BONZI | 1.91924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
154
Monitored processes
101
Malicious processes
16
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Windows\System32\charmap.exe" | C:\Windows\System32\charmap.exe | — | opera.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Character Map Exit code: 0 Version: 5.2.3668.0 Modules
| |||||||||||||||
| 256 | "C:\Windows\System32\sdbinst.exe" | C:\Windows\System32\sdbinst.exe | — | MigAutoPlay.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Application Compatibility Database Installer Exit code: 0 Version: 6.0.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 276 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 328 | "C:\Windows\System32\SearchFilterHost.exe" | C:\Windows\System32\SearchFilterHost.exe | — | MigAutoPlay.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Filter Host Exit code: 2147944039 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | C:\Windows\System32\svchost.exe -k WerSvcGroup | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 460 | "C:\Windows\System32\MigAutoPlay.exe" | C:\Windows\System32\MigAutoPlay.exe | — | rekeywiz.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Easy Transfer Autoplay Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 504 | C:\Windows\system32\WerFault.exe -u -p 2292 -s 572 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 3221226356 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 672 | C:\Windows\system32\net1 | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 808 | taskkill /f /im AgentSvr.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 448
Read events
2 037
Write events
4 393
Delete events
18
Modification events
| (PID) Process: | (2996) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2996) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2664) INSTALLER.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (3536) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.1 |
| Operation: | write | Name: | |
Value: Microsoft Agent Control 1.5 | |||
| (PID) Process: | (3536) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.1\CLSID |
| Operation: | write | Name: | |
Value: {F5BE8BD2-7DE6-11D0-91FE-00C04FD701A5} | |||
| (PID) Process: | (3536) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.2 |
| Operation: | write | Name: | |
Value: Microsoft Agent Control 2.0 | |||
| (PID) Process: | (3536) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.2\CLSID |
| Operation: | write | Name: | |
Value: {D45FD31B-5C6E-11D1-9EC1-00C04FD7081F} | |||
| (PID) Process: | (3536) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control |
| Operation: | write | Name: | |
Value: Microsoft Agent Control 2.0 | |||
| (PID) Process: | (3536) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control\CurVer |
| Operation: | write | Name: | |
Value: Agent.Control.2 | |||
| (PID) Process: | (3536) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F} |
| Operation: | write | Name: | |
Value: Microsoft Agent Control 2.0 | |||
Executable files
15
Suspicious files
39
Text files
21
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3256 | INSTALLER.exe | C:\Windows\lhsp\tv\SET2524.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | INSTALLER.exe | C:\Windows\lhsp\tv\SET2534.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | INSTALLER.exe | C:\Windows\lhsp\help\SET2545.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | INSTALLER.exe | C:\Windows\fonts\SET2546.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | INSTALLER.exe | C:\Windows\INF\SET2566.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | INSTALLER.exe | C:\Windows\system32\SET2577.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | INSTALLER.exe | C:\Windows\Temp\OLD2591.tmp | — | |
MD5:— | SHA256:— | |||
| 4056 | Bonzify.exe | C:\Windows\executables.bin | binary | |
MD5:— | SHA256:— | |||
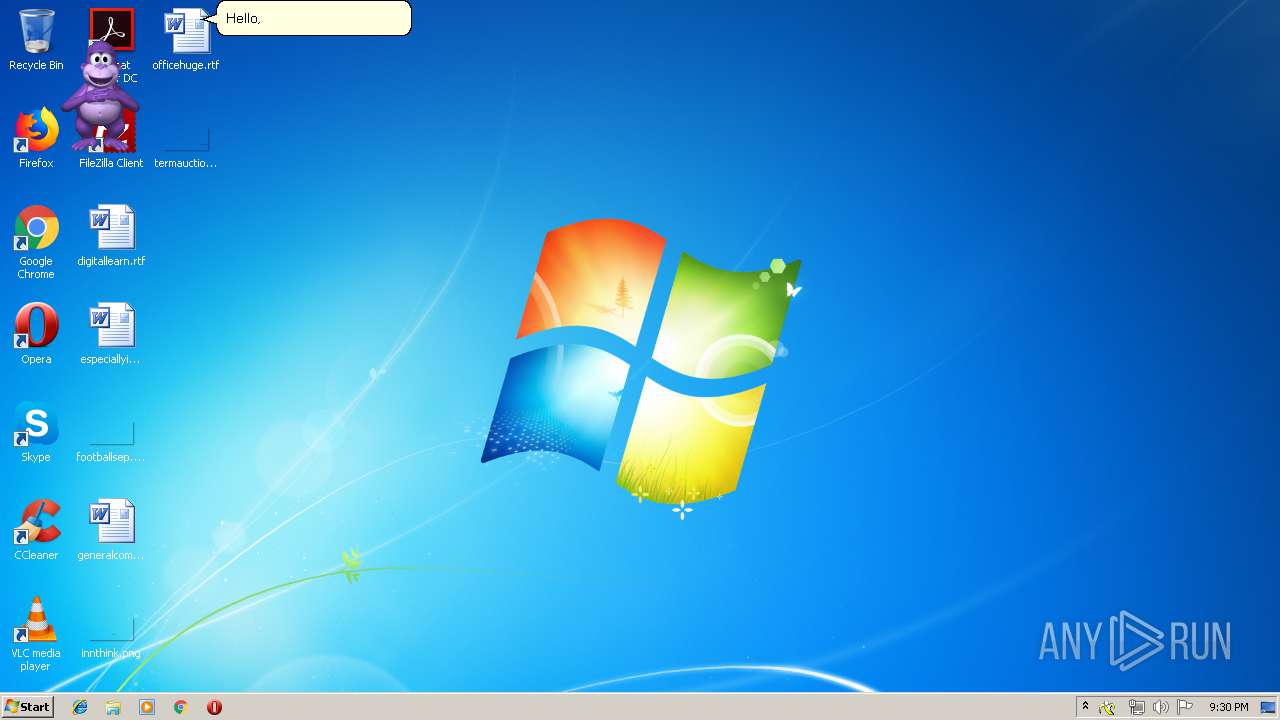
| 4056 | Bonzify.exe | C:\Windows\msagent\chars\Bonzi.acs | — | |
MD5:— | SHA256:— | |||
| 3256 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\tv_enua.dll | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3432 | opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3432 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3432 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|