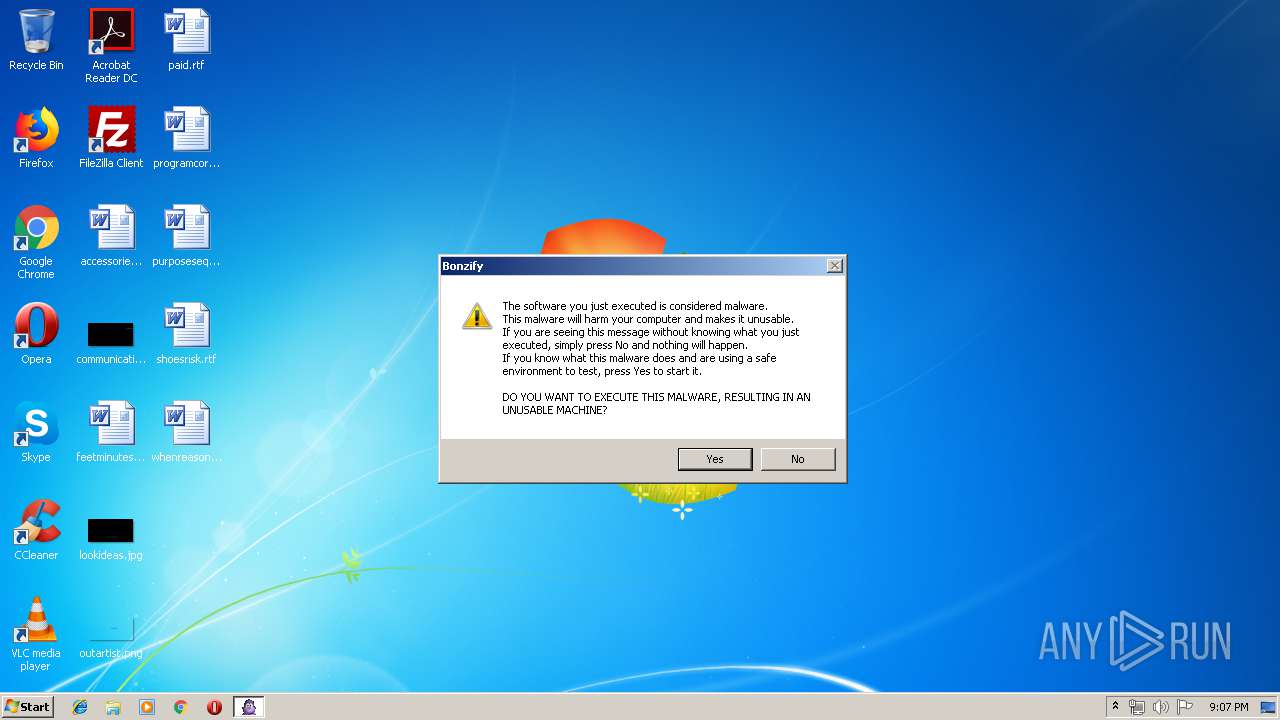
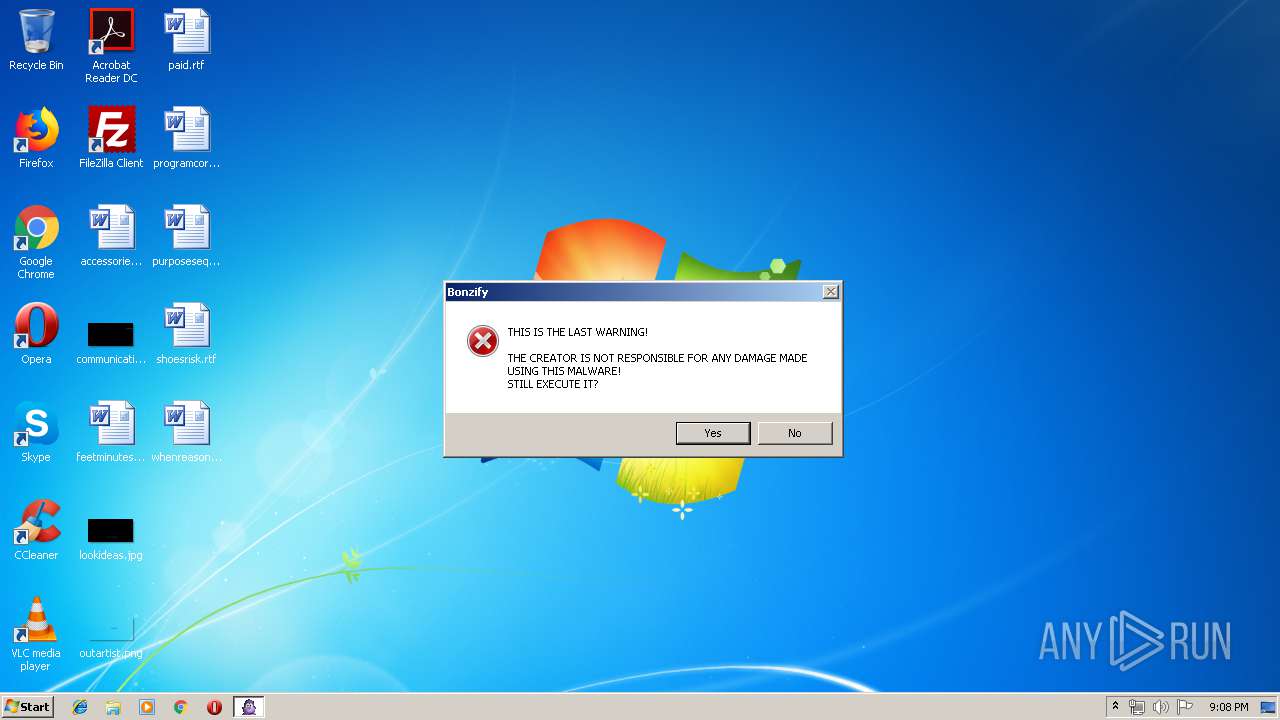
| File name: | Bonzify.exe |
| Full analysis: | https://app.any.run/tasks/47b21a57-2886-461d-9d26-b006b4fb191a |
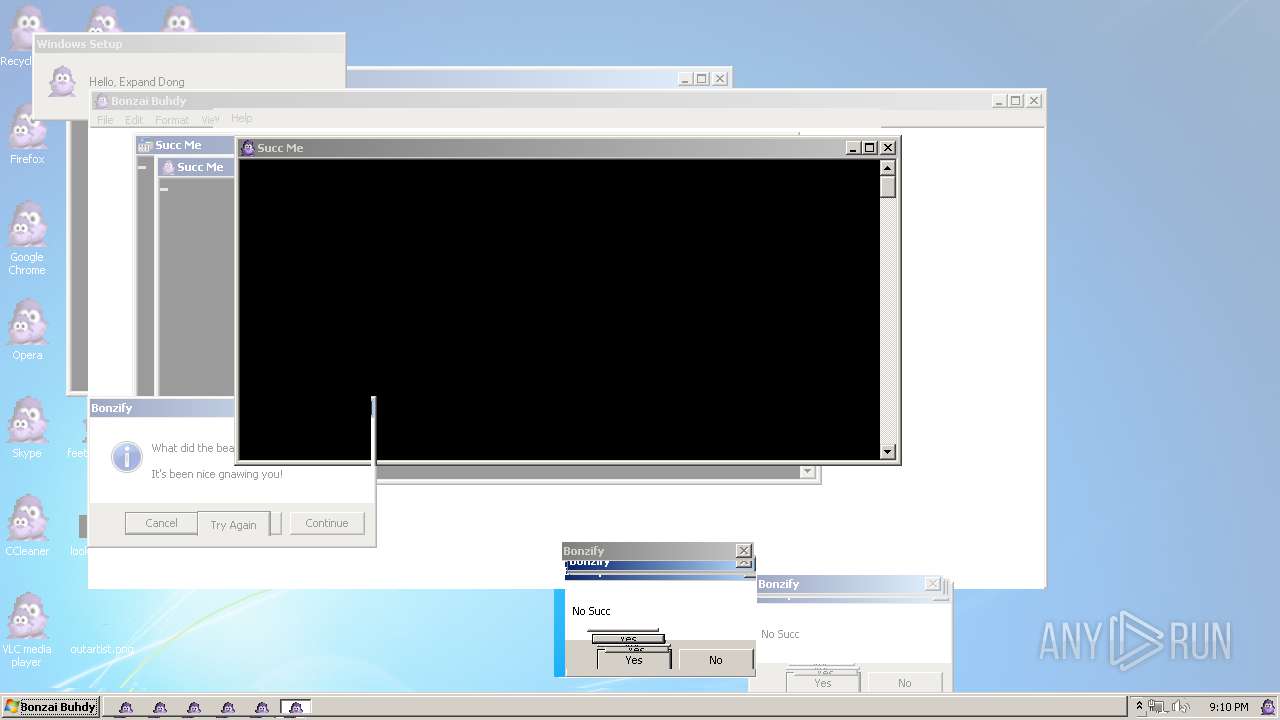
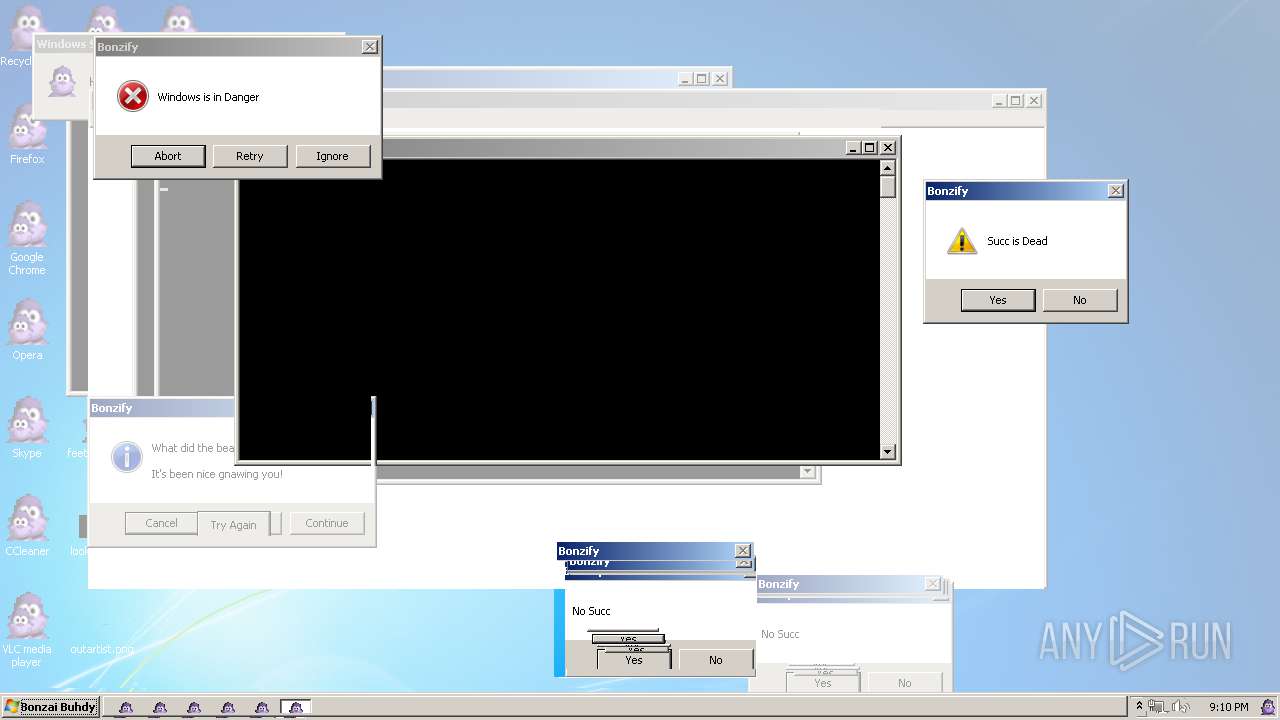
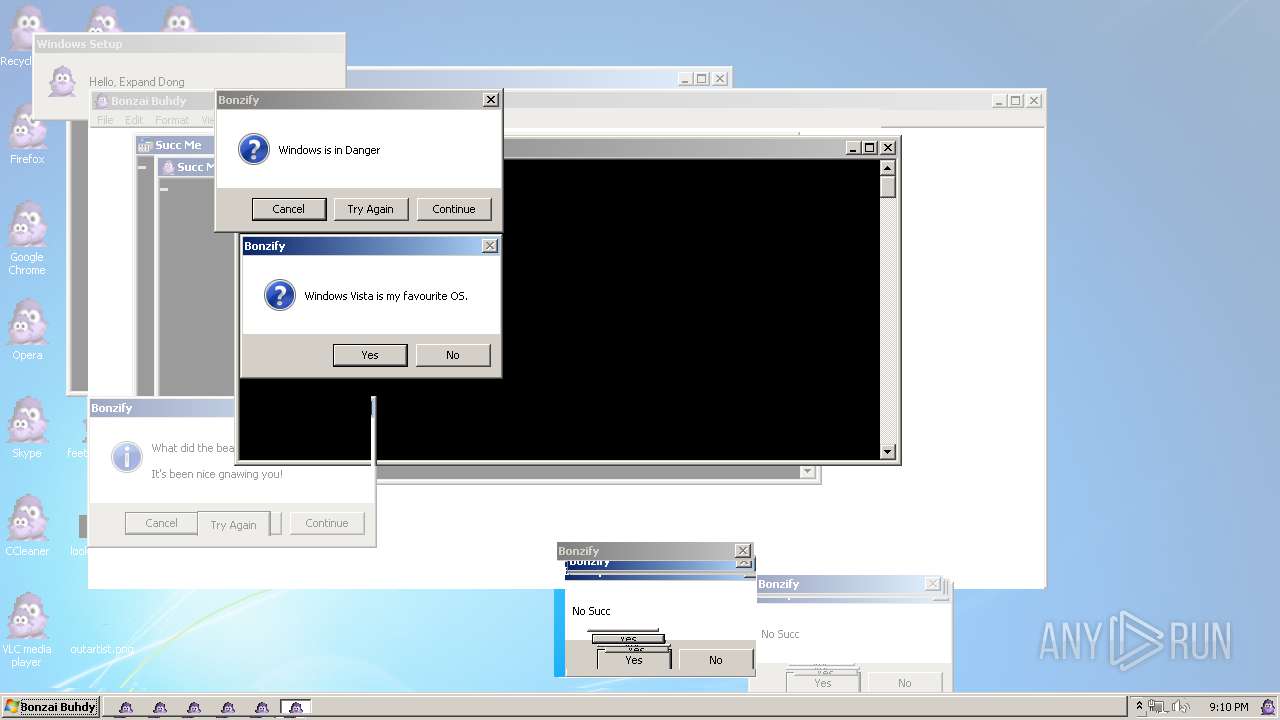
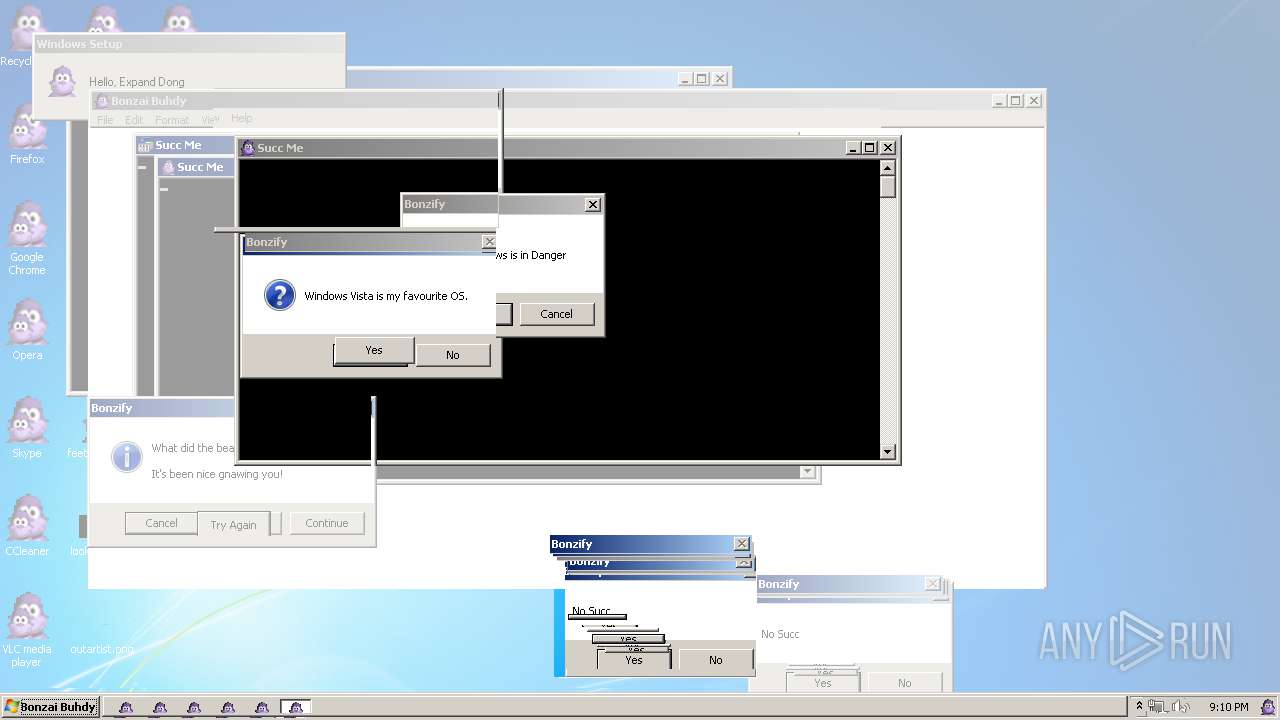
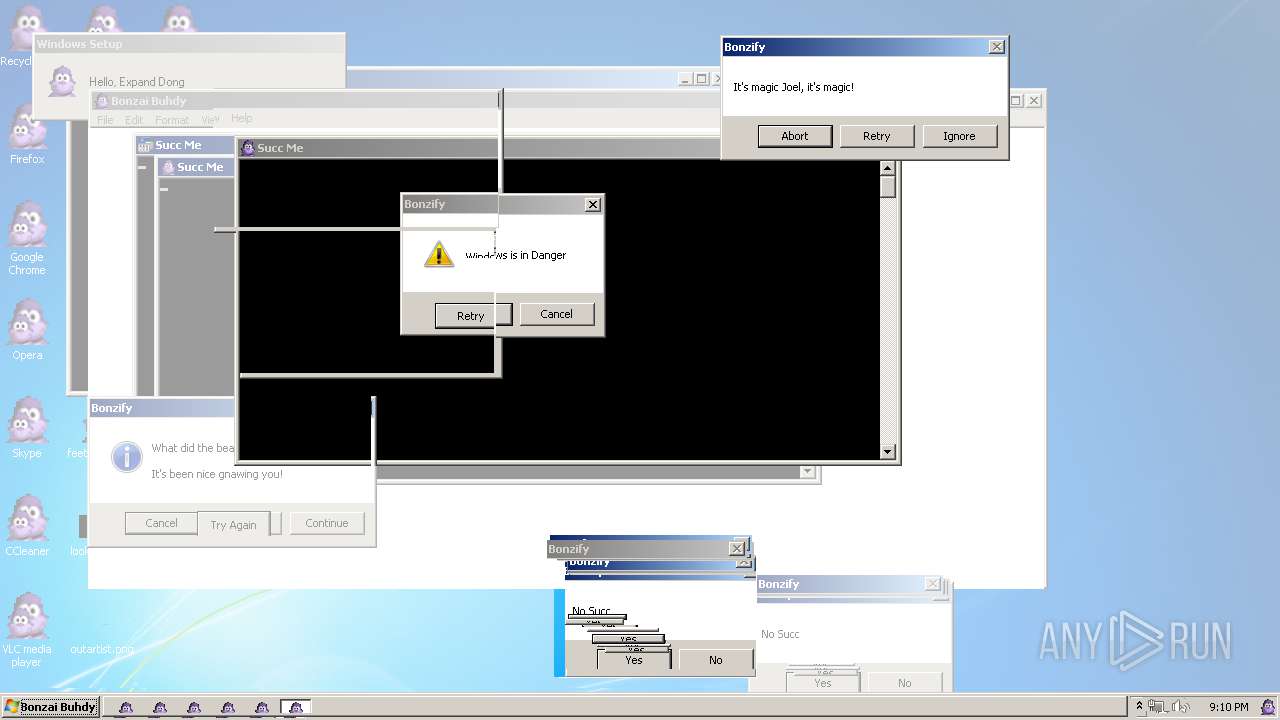
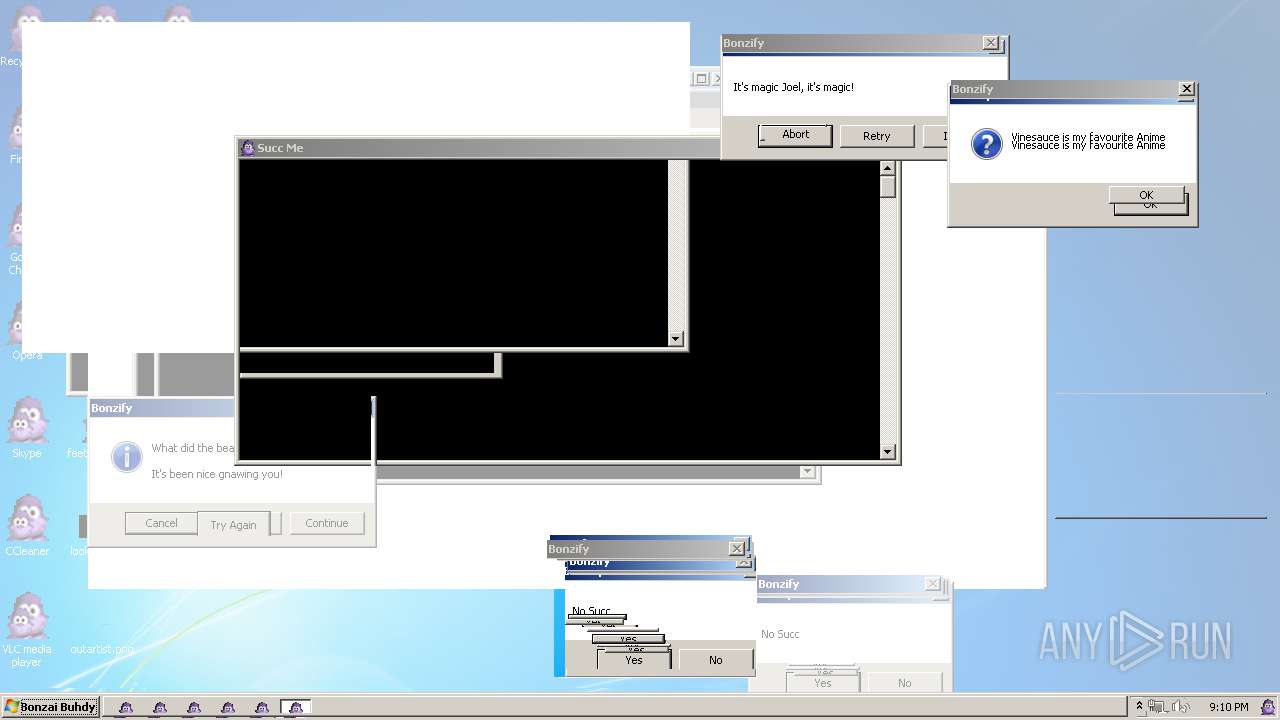
| Verdict: | Malicious activity |
| Analysis date: | May 08, 2019, 20:07:24 |
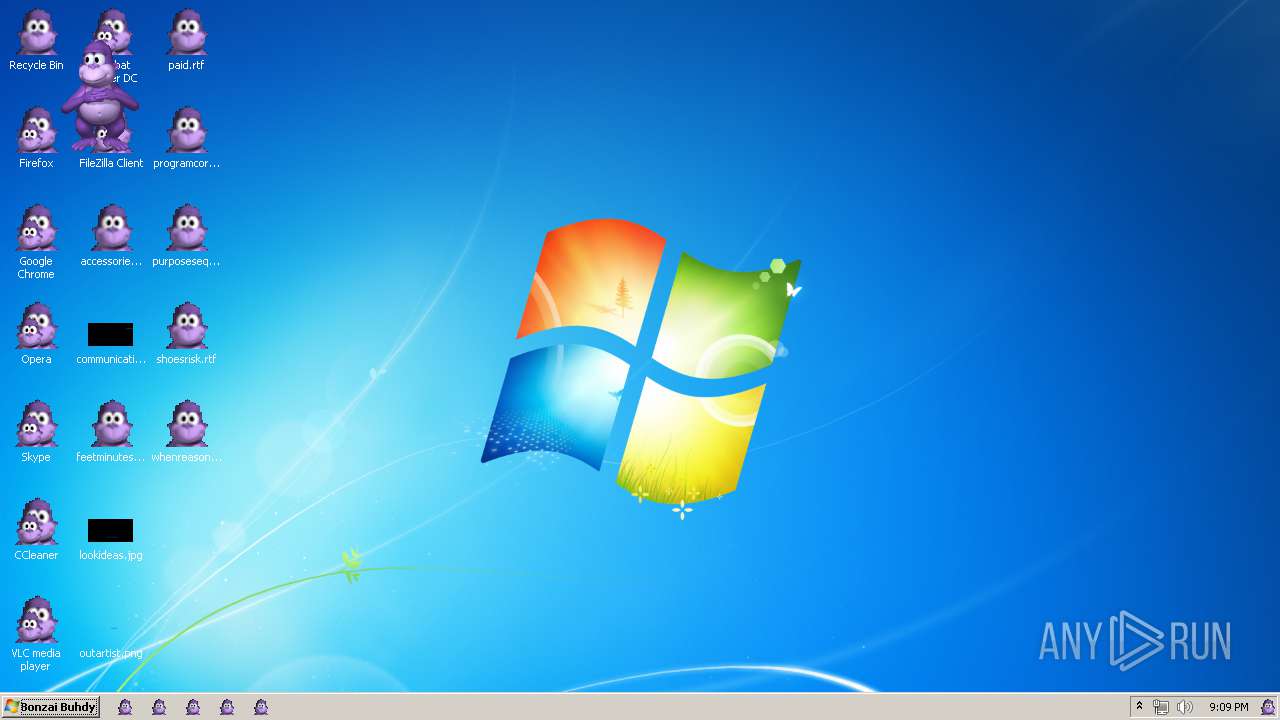
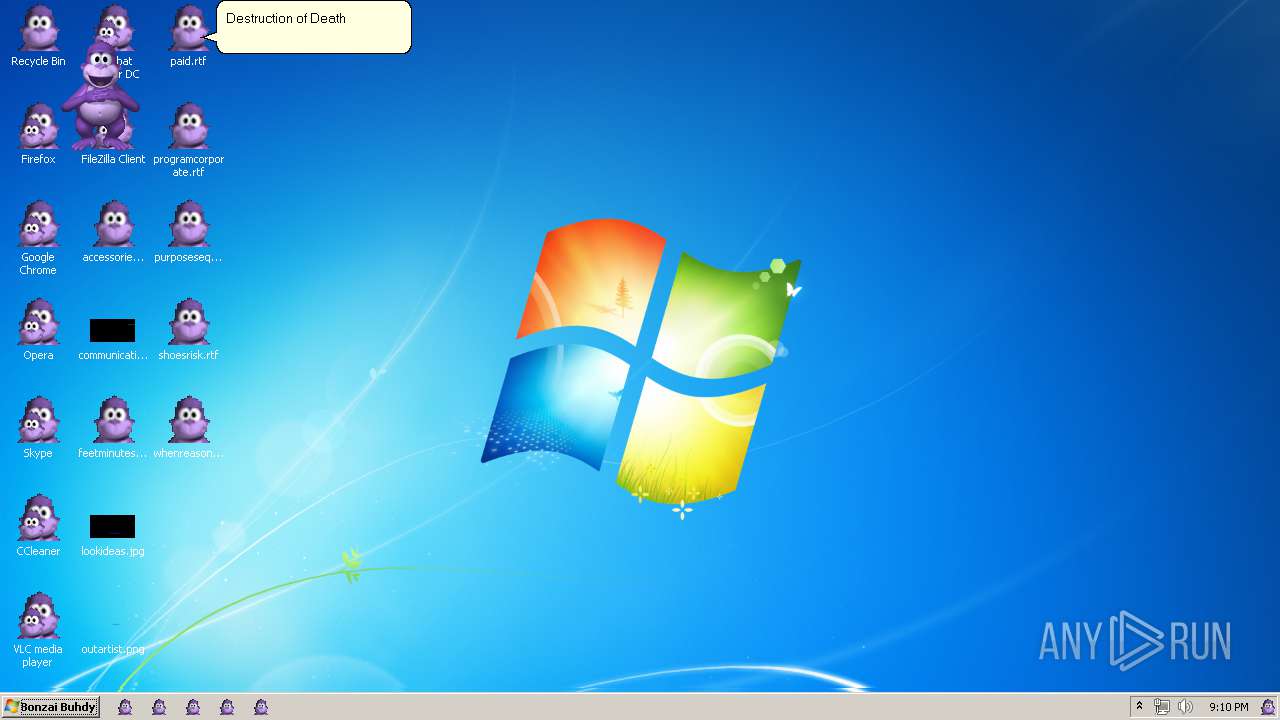
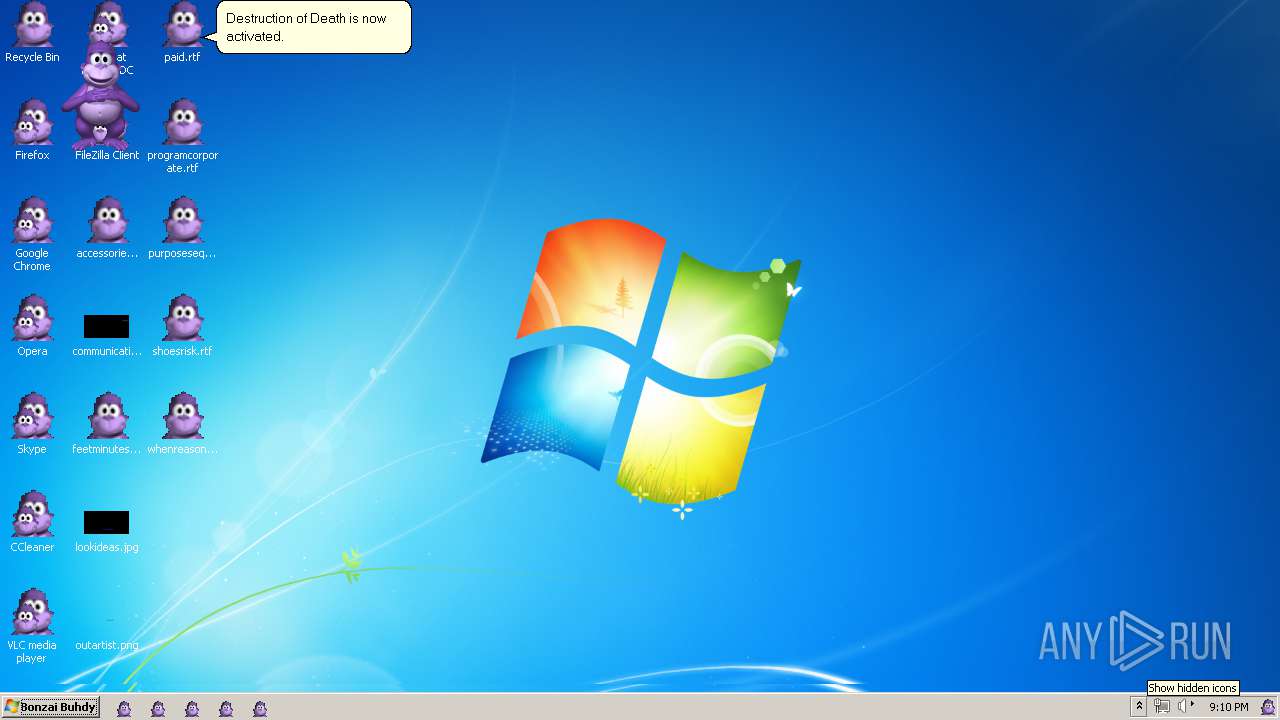
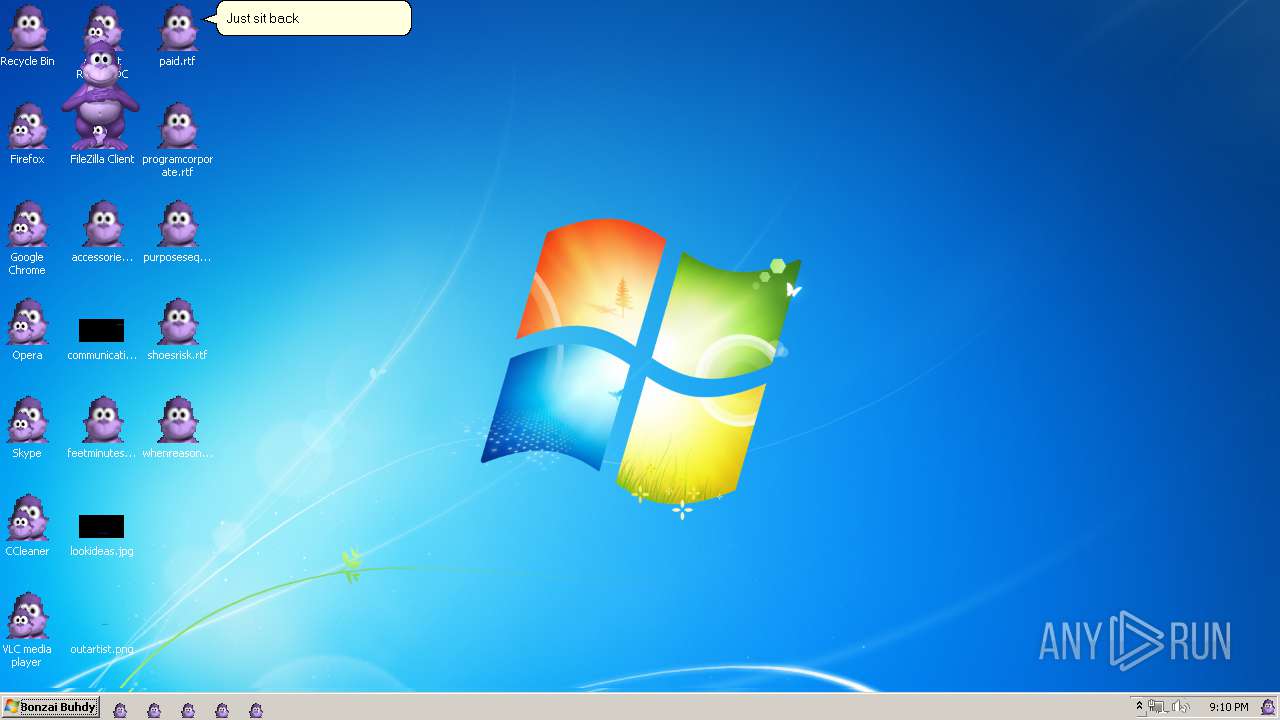
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BF5036B29D933F358D89584A97FC1F9F |
| SHA1: | AE286CF55C22ECEEBCEE02ACDA226787FBE5B44D |
| SHA256: | 761260840091E08192BE749FF8231788E6E59A47382841EEB791D48057A54750 |
| SSDEEP: | 196608:7dAMaWetTeAkLIdx751qFTkub//73lc6u7b5VJ2Yx5xIdk3:baWedh+Idx75QYub//73lc6u7bLMYxD |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- INSTALLER.exe (PID: 3696)
- INSTALLER.exe (PID: 2376)
Application was dropped or rewritten from another process
- INSTALLER.exe (PID: 3696)
- INSTALLER.exe (PID: 2376)
Changes the autorun value in the registry
- INSTALLER.exe (PID: 2376)
- SearchProtocolHost.exe (PID: 1548)
- conhost.exe (PID: 1144)
- Bonzify.exe (PID: 3404)
- svchost.exe (PID: 2628)
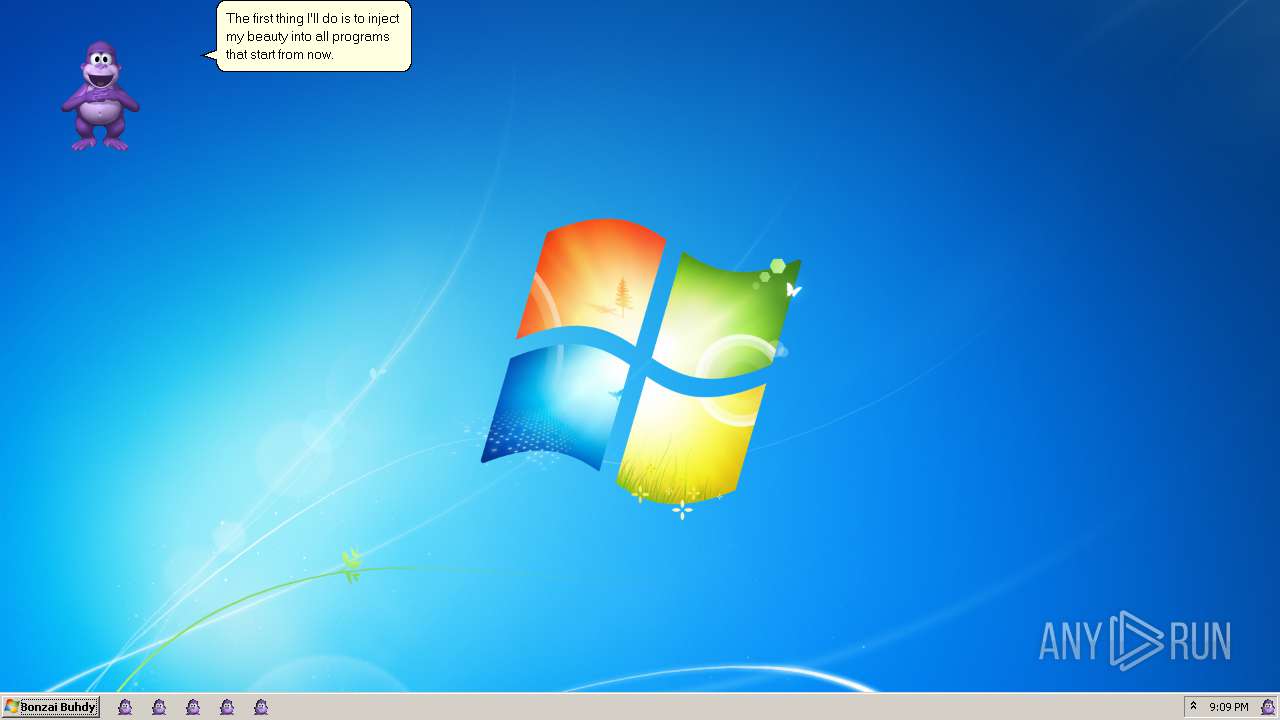
Loads dropped or rewritten executable
- INSTALLER.exe (PID: 3696)
- regsvr32.exe (PID: 3580)
- regsvr32.exe (PID: 1772)
- INSTALLER.exe (PID: 2376)
- AgentSvr.exe (PID: 344)
- conhost.exe (PID: 1144)
- RMActivate.exe (PID: 2164)
- notepad.exe (PID: 664)
- runonce.exe (PID: 3952)
- ehexthost.exe (PID: 3088)
- explorer.exe (PID: 536)
- DllHost.exe (PID: 948)
- SearchProtocolHost.exe (PID: 1548)
- SearchFilterHost.exe (PID: 3988)
- powershell_ise.exe (PID: 4056)
- conhost.exe (PID: 920)
- WerFault.exe (PID: 724)
- conhost.exe (PID: 2812)
- taskhost.exe (PID: 3260)
- WerFault.exe (PID: 3660)
- eventcreate.exe (PID: 1692)
- resmon.exe (PID: 3996)
- svchost.exe (PID: 1884)
- iexplore.exe (PID: 2620)
- WerFault.exe (PID: 3856)
- werfault.exe (PID: 2316)
- consent.exe (PID: 1704)
- svchost.exe (PID: 704)
- McxTask.exe (PID: 1220)
- WerFault.exe (PID: 3868)
- dllhst3g.exe (PID: 3024)
- conhost.exe (PID: 408)
- conhost.exe (PID: 1684)
- svchost.exe (PID: 2628)
- WerFault.exe (PID: 1652)
- IMSCPROP.exe (PID: 3384)
- CISVC.EXE (PID: 2116)
- DllHost.exe (PID: 2848)
- spoolsv.exe (PID: 1464)
Changes AppInit_DLLs value (autorun option)
- Bonzify.exe (PID: 3404)
Changes internet zones settings
- explorer.exe (PID: 536)
- SearchProtocolHost.exe (PID: 1548)
- conhost.exe (PID: 1144)
- WerFault.exe (PID: 724)
- resmon.exe (PID: 3996)
- svchost.exe (PID: 704)
- iexplore.exe (PID: 2620)
- consent.exe (PID: 1704)
- svchost.exe (PID: 2628)
Loads the Task Scheduler COM API
- explorer.exe (PID: 536)
Changes the Startup folder
- resmon.exe (PID: 3996)
SUSPICIOUS
Creates files in the Windows directory
- Bonzify.exe (PID: 3404)
- INSTALLER.exe (PID: 3696)
- INSTALLER.exe (PID: 2376)
Executable content was dropped or overwritten
- INSTALLER.exe (PID: 3696)
- Bonzify.exe (PID: 3404)
- INSTALLER.exe (PID: 2376)
- consent.exe (PID: 1704)
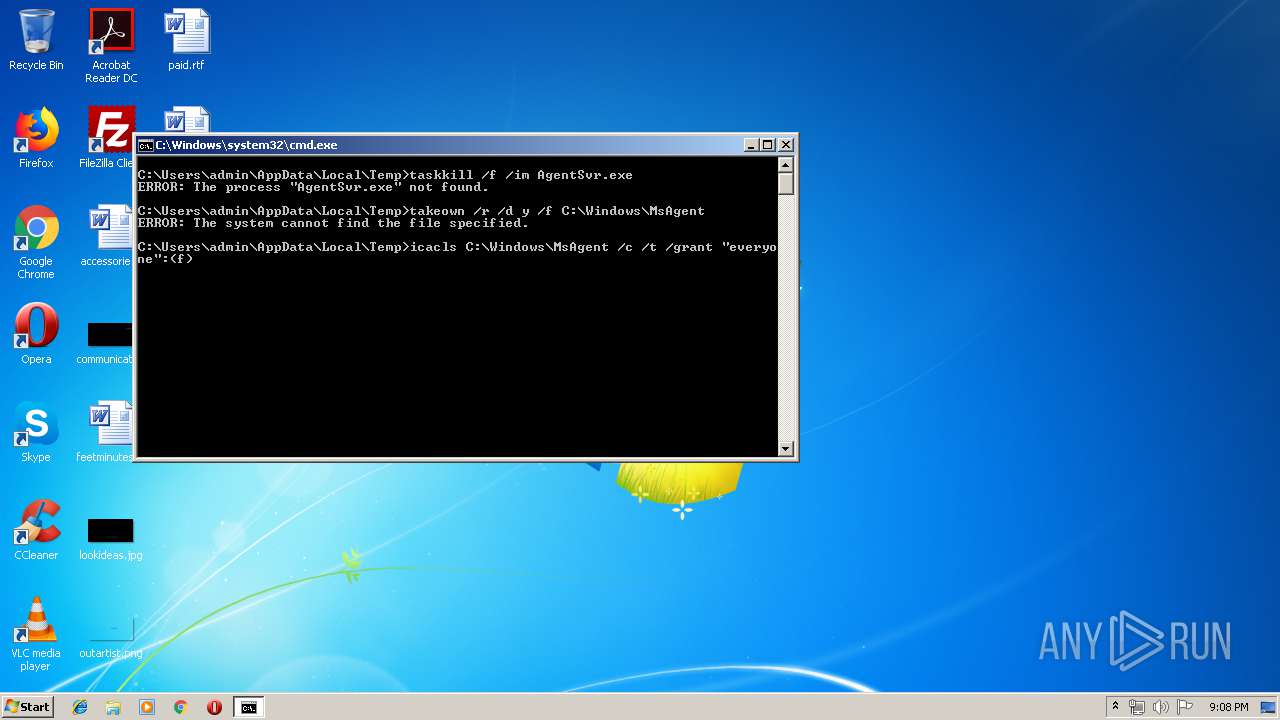
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2852)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 2852)
Creates COM task schedule object
- regsvr32.exe (PID: 2496)
- regsvr32.exe (PID: 3464)
- regsvr32.exe (PID: 2744)
- regsvr32.exe (PID: 1556)
- regsvr32.exe (PID: 1496)
- regsvr32.exe (PID: 3292)
- regsvr32.exe (PID: 1864)
- regsvr32.exe (PID: 1772)
- regsvr32.exe (PID: 3580)
- explorer.exe (PID: 536)
- WerFault.exe (PID: 724)
- conhost.exe (PID: 1144)
- svchost.exe (PID: 704)
- iexplore.exe (PID: 2620)
- consent.exe (PID: 1704)
- svchost.exe (PID: 2628)
- resmon.exe (PID: 3996)
Removes files from Windows directory
- INSTALLER.exe (PID: 2376)
- INSTALLER.exe (PID: 3696)
Creates a software uninstall entry
- INSTALLER.exe (PID: 2376)
Changes the desktop background image
- conhost.exe (PID: 1144)
Executes application which crashes
- powershell_ise.exe (PID: 4056)
Modifies the open verb of a shell class
- iexplore.exe (PID: 2620)
Executes PowerShell scripts
- consent.exe (PID: 1704)
Starts CMD.EXE for commands execution
- Bonzify.exe (PID: 3404)
INFO
Dropped object may contain Bitcoin addresses
- Bonzify.exe (PID: 3404)
Application was crashed
- explorer.exe (PID: 536)
- WerFault.exe (PID: 724)
- WerFault.exe (PID: 3660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (80.4) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.2) |
| .exe | | | Win64 Executable (generic) (7.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.7) |
| .exe | | | Win32 Executable (generic) (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:16 04:19:10+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 4096 |
| InitializedDataSize: | 6695936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16b0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Dec-2018 03:19:10 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Dec-2018 03:19:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000E46 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.30794 |
.rdata | 0x00002000 | 0x000012E4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41988 |
.data | 0x00004000 | 0x00000020 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00005000 | 0x00661228 | 0x00661400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.85029 |
.reloc | 0x00667000 | 0x0000018C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.54097 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
100 | 7.82633 | 5249795 | UNKNOWN | UNKNOWN | DATA |
101 | 7.78087 | 400536 | UNKNOWN | UNKNOWN | DATA |
102 | 7.93147 | 1021232 | UNKNOWN | UNKNOWN | DATA |
103 | 4.86014 | 158 | UNKNOWN | UNKNOWN | DATA |
104 | 4.44475 | 45 | UNKNOWN | UNKNOWN | DATA |
110 | 5.62084 | 14336 | UNKNOWN | UNKNOWN | DATA |
IDI_BONZI | 1.91924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
135
Monitored processes
59
Malicious processes
14
Suspicious processes
0
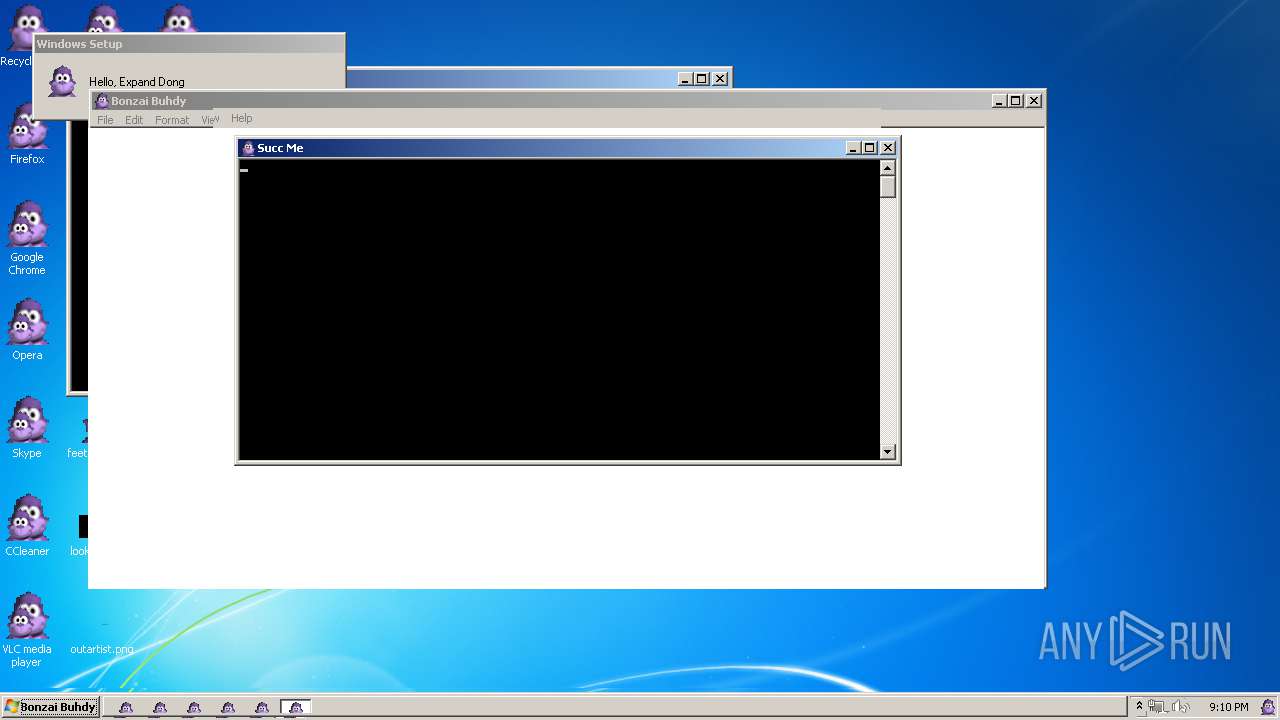
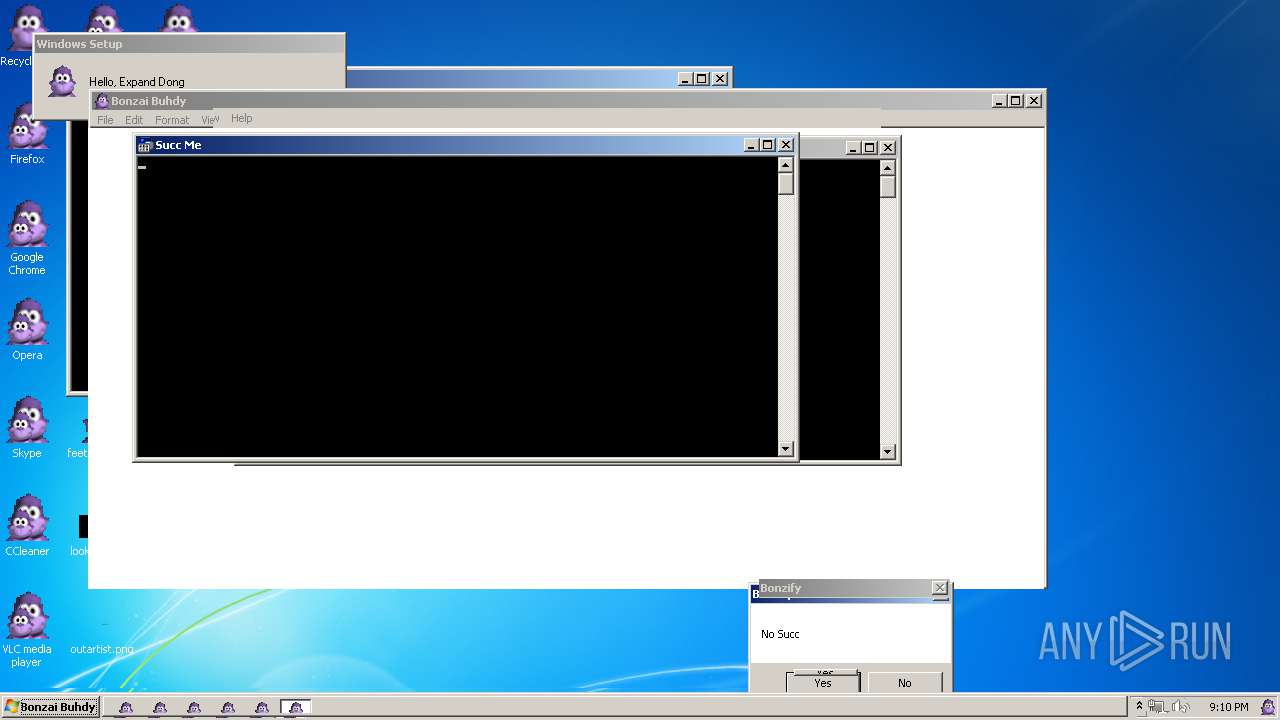
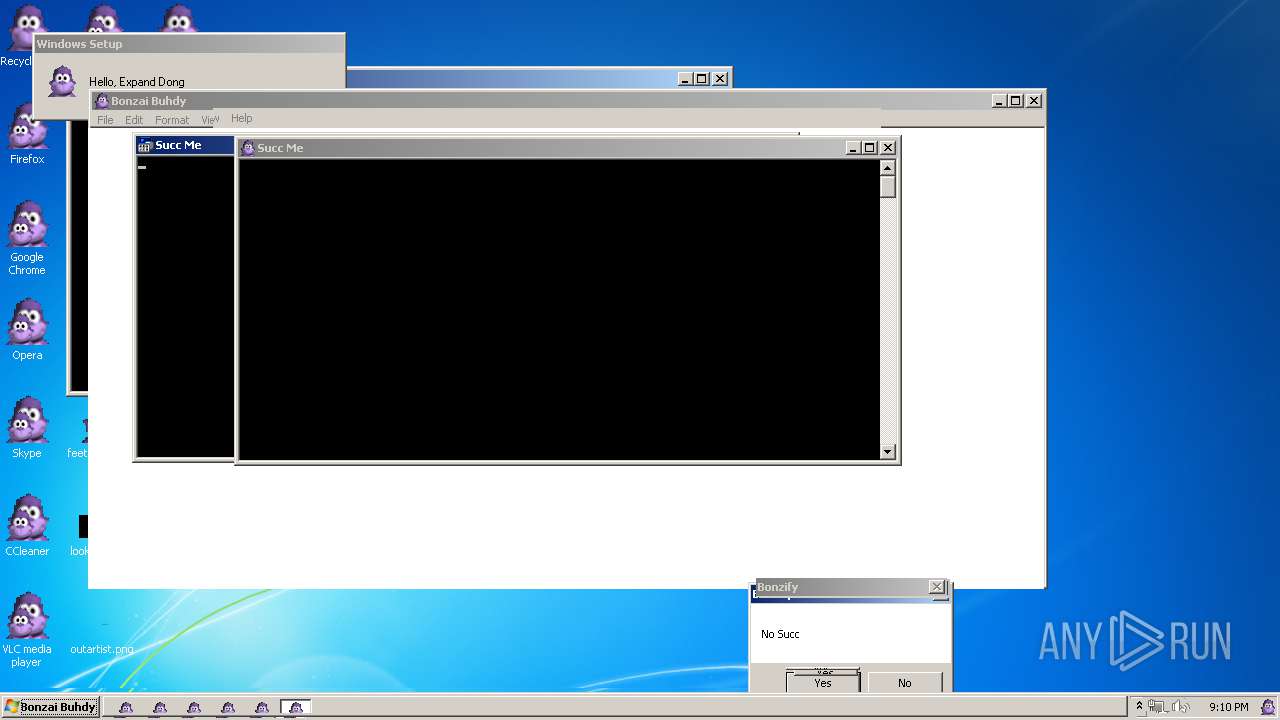
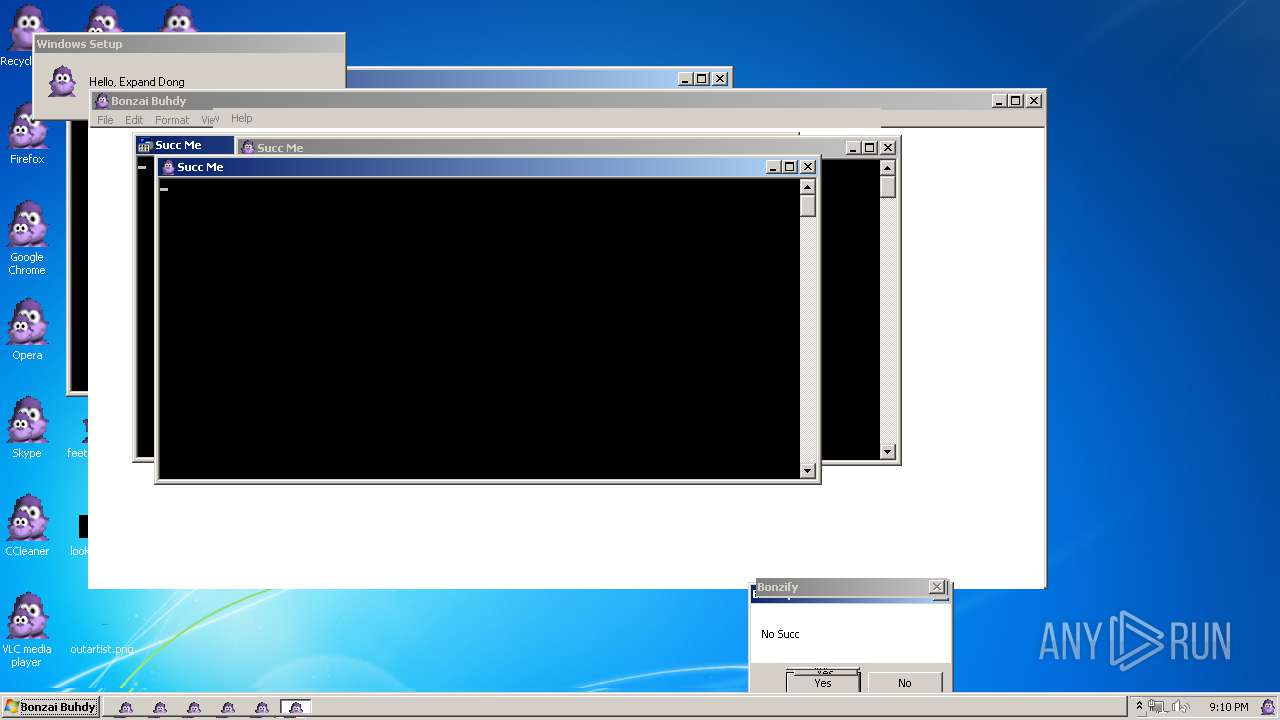
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | C:\Windows\msagent\AgentSvr.exe -Embeddingg | C:\Windows\msagent\AgentSvr.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: UNTRUSTED Description: Microsoft Agent Server Exit code: 0 Version: 2.00.0.2202 Modules
| |||||||||||||||
| 408 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 536 | explorer.exe | C:\Windows\explorer.exe | winlogon.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 588 | takeown /r /d y /f C:\Windows\MsAgent | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 664 | "C:\Windows\notepad.exe" | C:\Windows\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 704 | C:\Windows\System32\svchost.exe -k WerSvcGroup | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 3221226356 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 724 | C:\Windows\system32\WerFault.exe -u -p 536 -s 1208 | C:\Windows\system32\WerFault.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | icacls C:\Windows\MsAgent /c /t /grant "everyone":(f) | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 920 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 391
Read events
1 516
Write events
3 857
Delete events
18
Modification events
| (PID) Process: | (3696) INSTALLER.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (1496) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.1 |
| Operation: | write | Name: | |
Value: Microsoft Agent Control 1.5 | |||
| (PID) Process: | (1496) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.1\CLSID |
| Operation: | write | Name: | |
Value: {F5BE8BD2-7DE6-11D0-91FE-00C04FD701A5} | |||
| (PID) Process: | (1496) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.2 |
| Operation: | write | Name: | |
Value: Microsoft Agent Control 2.0 | |||
| (PID) Process: | (1496) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.2\CLSID |
| Operation: | write | Name: | |
Value: {D45FD31B-5C6E-11D1-9EC1-00C04FD7081F} | |||
| (PID) Process: | (1496) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control |
| Operation: | write | Name: | |
Value: Microsoft Agent Control 2.0 | |||
| (PID) Process: | (1496) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control\CurVer |
| Operation: | write | Name: | |
Value: Agent.Control.2 | |||
| (PID) Process: | (1496) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F} |
| Operation: | write | Name: | |
Value: Microsoft Agent Control 2.0 | |||
| (PID) Process: | (1496) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\ProgID |
| Operation: | write | Name: | |
Value: Agent.Control.2 | |||
| (PID) Process: | (1496) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\VersionIndependentProgID |
| Operation: | write | Name: | |
Value: Agent.Control | |||
Executable files
16
Suspicious files
3
Text files
43
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3696 | INSTALLER.exe | C:\Windows\msagent\intl\SET2790.tmp | — | |
MD5:— | SHA256:— | |||
| 3696 | INSTALLER.exe | C:\Windows\msagent\SET27A1.tmp | — | |
MD5:— | SHA256:— | |||
| 2376 | INSTALLER.exe | C:\Windows\lhsp\tv\SET33AB.tmp | — | |
MD5:— | SHA256:— | |||
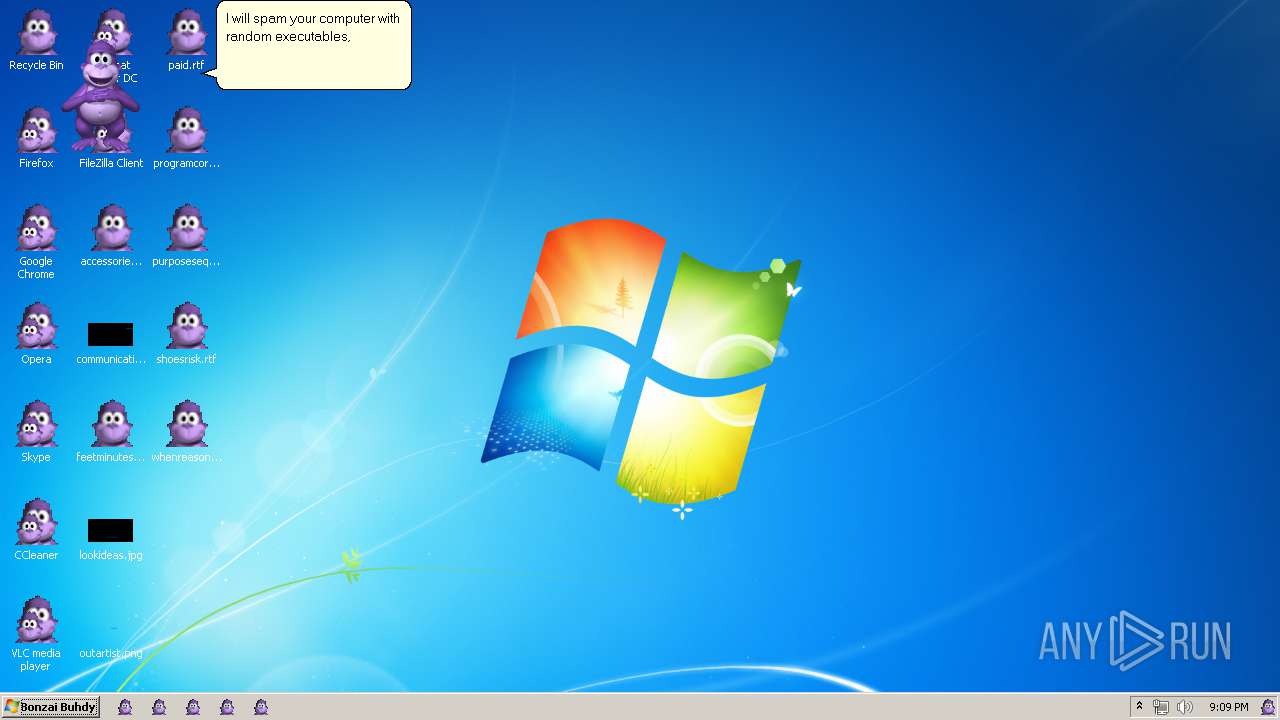
| 3404 | Bonzify.exe | C:\Windows\executables.bin | binary | |
MD5:— | SHA256:— | |||
| 2376 | INSTALLER.exe | C:\Windows\lhsp\tv\SET33CB.tmp | — | |
MD5:— | SHA256:— | |||
| 3696 | INSTALLER.exe | C:\Windows\INF\setupapi.app.log | text | |
MD5:— | SHA256:— | |||
| 2376 | INSTALLER.exe | C:\Windows\lhsp\help\SET33DB.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | Bonzify.exe | C:\Users\admin\AppData\Local\Temp\TakeOwn.bat | text | |
MD5:E5F461B27469D58FCFFDAEA1BA1E0172 | SHA256:8EA7E9F2130A1B1ACA020740E8F81623761EFAA3F5FE0D34C730F4641480250D | |||
| 2376 | INSTALLER.exe | C:\Windows\fonts\SET33DC.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | Bonzify.exe | C:\Users\admin\AppData\Local\Temp\KillAgent.bat | text | |
MD5:6EA65B32F50D5B71FBB6557CDBBFDA10 | SHA256:66E35917FAFA086C45BBABC1D22AC08DB935952F7026DBD5E9CC9EC1673F19AB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
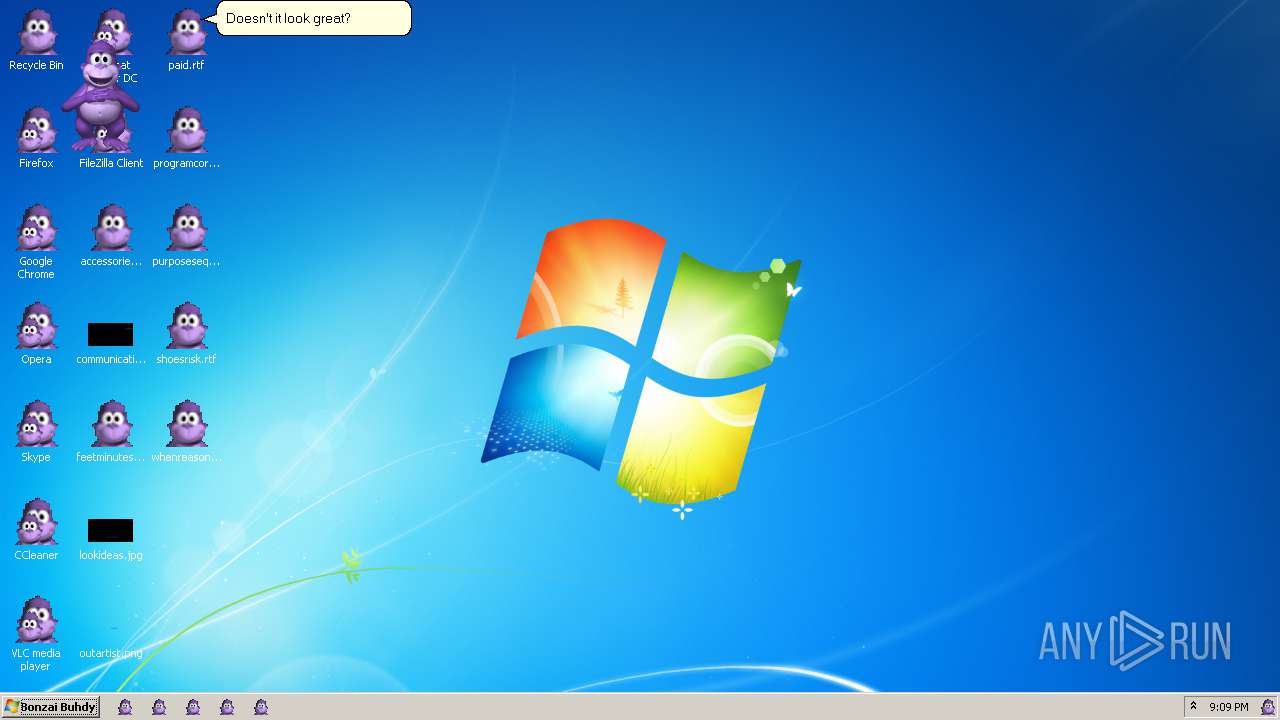
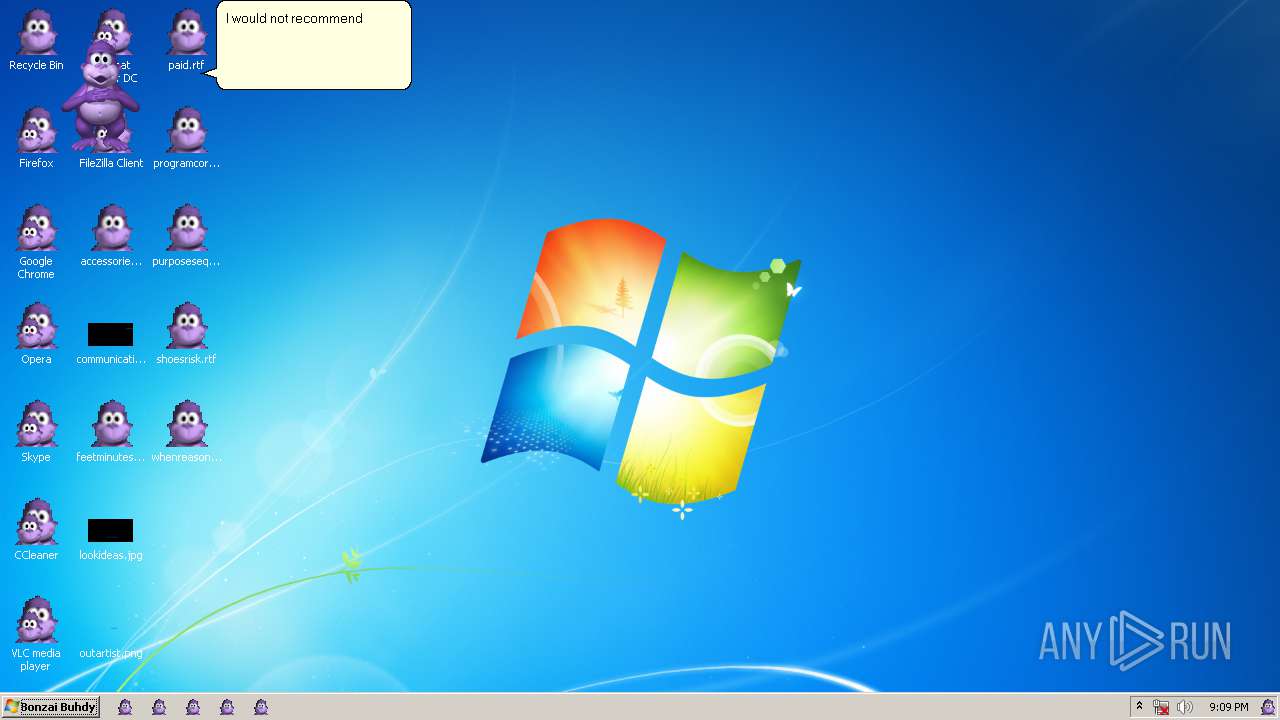
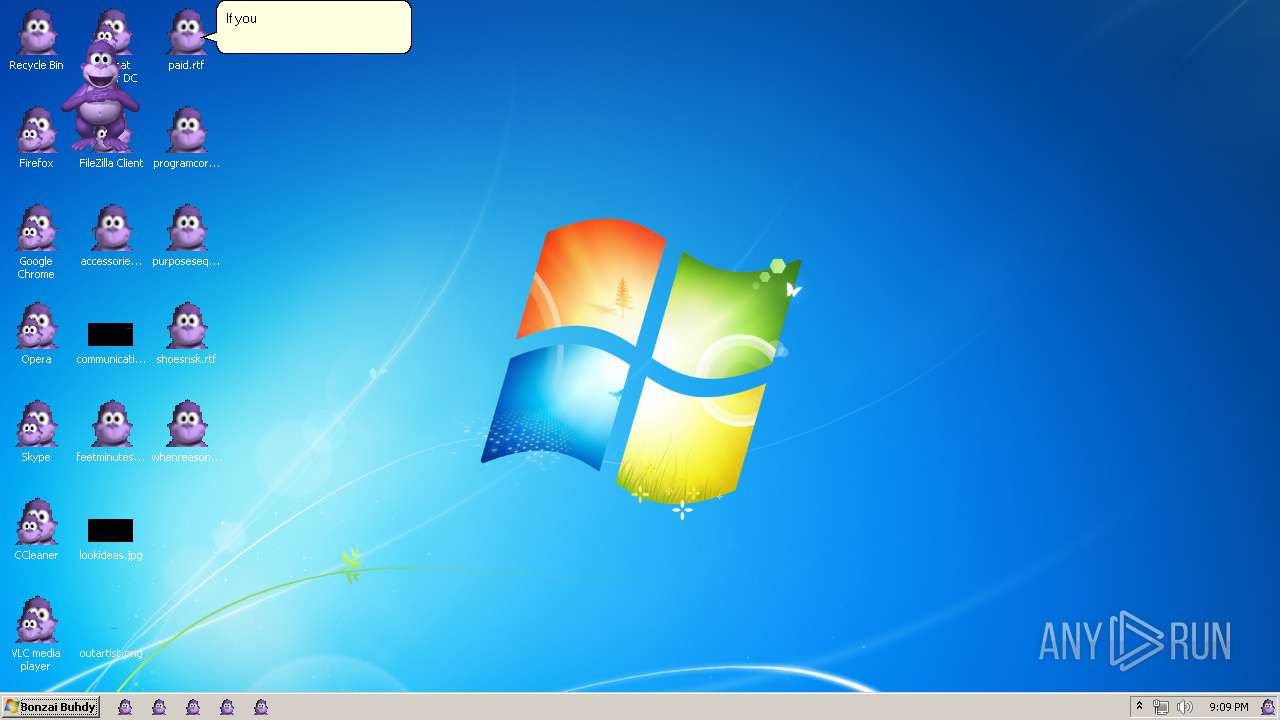
Process | Message |
|---|---|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|