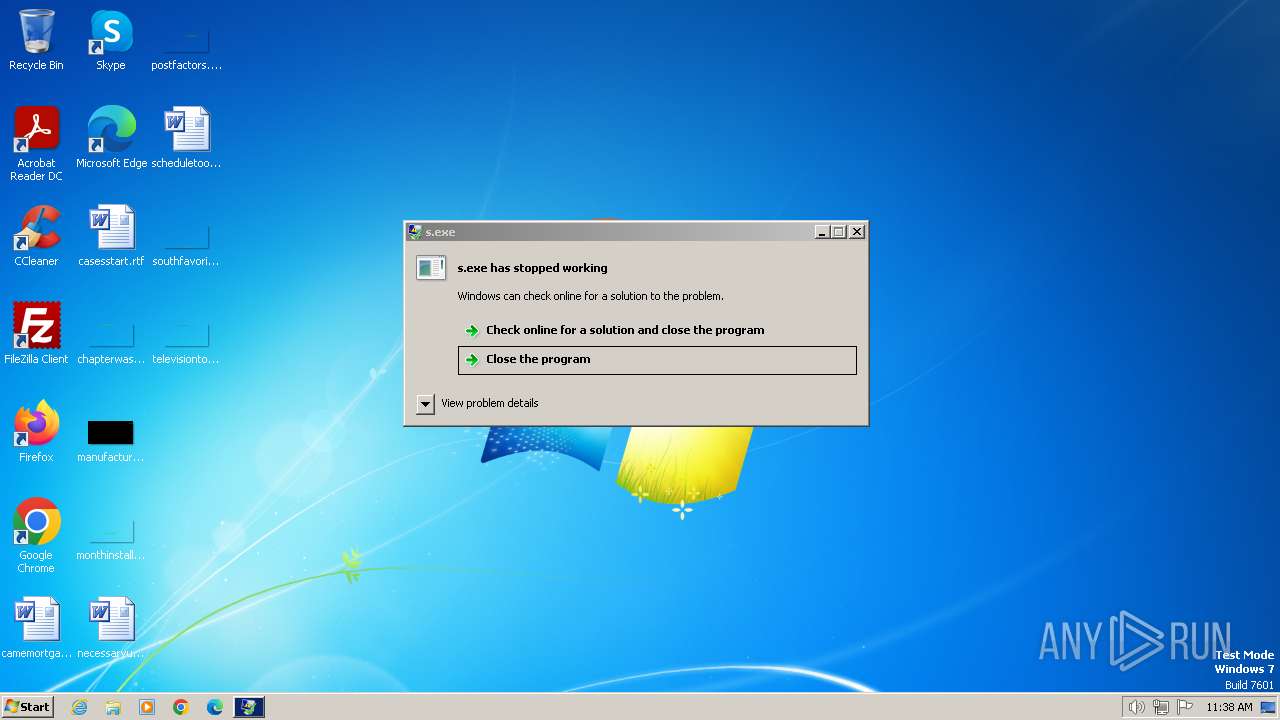
| File name: | s.exe |
| Full analysis: | https://app.any.run/tasks/587b1b79-fcd2-4fa4-a5a5-35c903a95231 |
| Verdict: | Malicious activity |
| Analysis date: | January 02, 2024, 11:38:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 167E3E8482B1B210846370C10F07D4F1 |
| SHA1: | 177B86293F50021BBF3C386882DCB30A42FB1951 |
| SHA256: | 75FEEC5EAFCD190F23892EB994D5F1DF5A3D9E7D77FA936AD28C832C94E868B8 |
| SSDEEP: | 24576:7dSRK8cPgnnhWnlXhYzoqNDeyxuU2kCJYcHYQYRE:7dS48cPgnnhWnlxYzoqNDeyxuU2kCJY6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads settings of System Certificates
- s.exe (PID: 116)
Reads the Internet Settings
- s.exe (PID: 116)
INFO
Drops the executable file immediately after the start
- s.exe (PID: 116)
Checks supported languages
- dcd.exe (PID: 2032)
- s.exe (PID: 116)
Reads the computer name
- s.exe (PID: 116)
Create files in a temporary directory
- s.exe (PID: 116)
Reads the machine GUID from the registry
- s.exe (PID: 116)
Reads Environment values
- s.exe (PID: 116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:01:02 11:58:06+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 272384 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x446fe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | s.exe |
| LegalCopyright: | |
| OriginalFileName: | s.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\AppData\Local\Temp\s.exe" | C:\Users\admin\AppData\Local\Temp\s.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2032 | "C:\Users\admin\AppData\Local\Temp\dcd.exe" -path="" | C:\Users\admin\AppData\Local\Temp\dcd.exe | — | s.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 333
Read events
3 319
Write events
14
Delete events
0
Modification events
| (PID) Process: | (116) s.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 116 | s.exe | C:\Users\admin\AppData\Local\Temp\dcd.exe | executable | |
MD5:B5AC46E446CEAD89892628F30A253A06 | SHA256:DEF7AFCB65126C4B04A7CBF08C693F357A707AA99858CAC09A8D5E65F3177669 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | s.exe | GET | 204 | 172.217.18.14:80 | http://google.com/generate_204 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
116 | s.exe | 172.217.18.14:80 | google.com | GOOGLE | US | whitelisted |
116 | s.exe | 172.67.194.181:443 | eterprx.net | CLOUDFLARENET | US | unknown |
116 | s.exe | 104.21.21.142:443 | eternitypr.net | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
eterprx.net |
| malicious |
eternitypr.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Eternity Stealer CnC Domain in DNS Lookup (eterprx .net) |
116 | s.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Eternity Stealer Domain (eterprx .net in TLS SNI) |
1080 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Eternity Stealer CnC Domain in DNS Lookup (eternitypr .net) |
116 | s.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Eternity Stealer Domain (eternitypr .net in TLS SNI) |