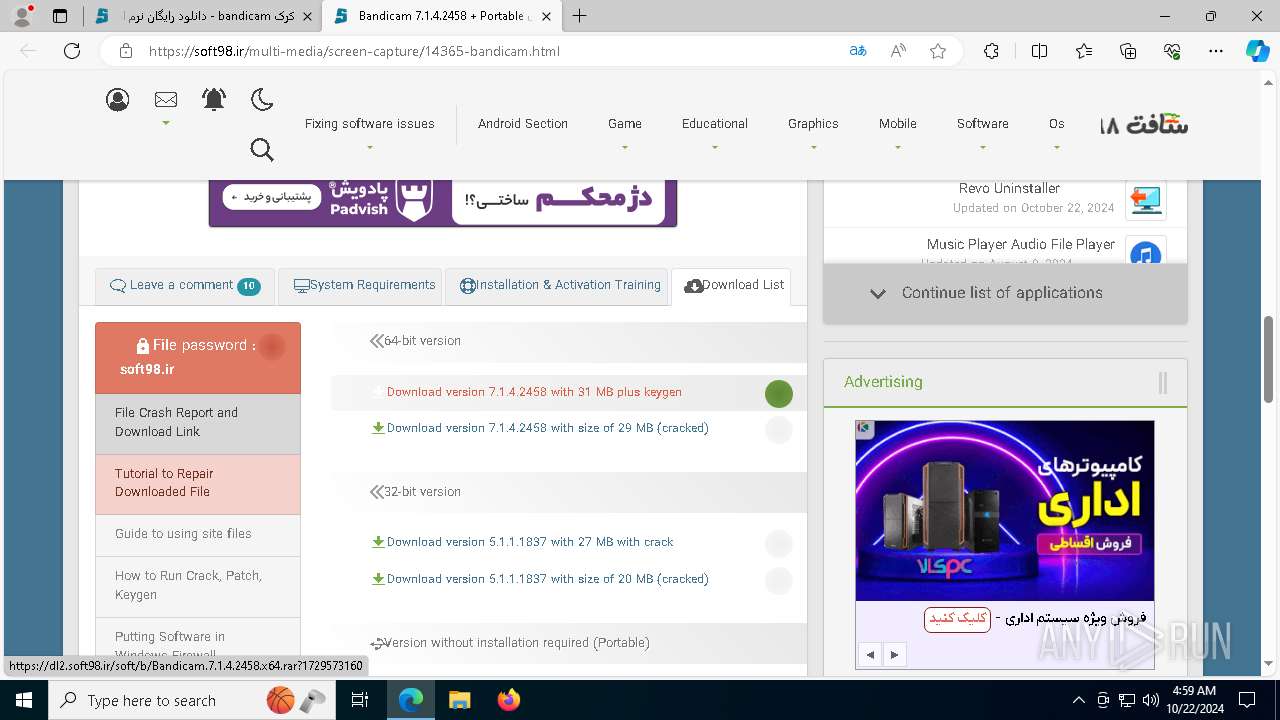
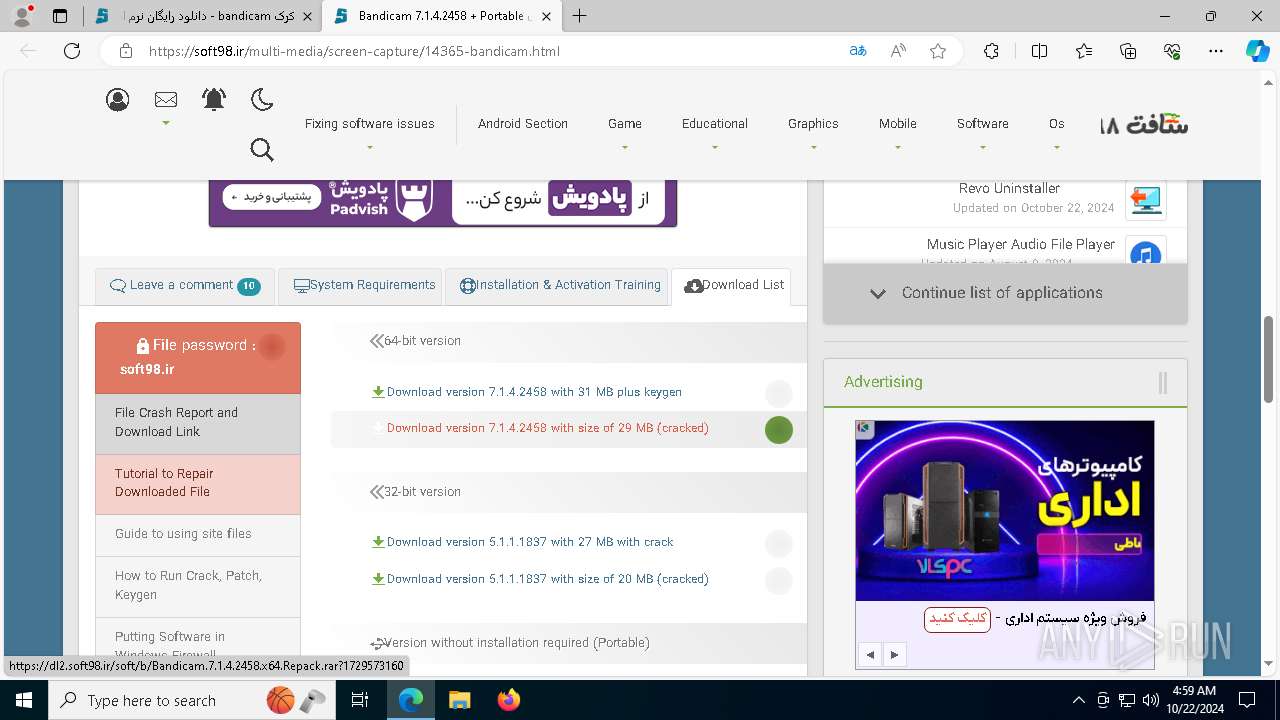
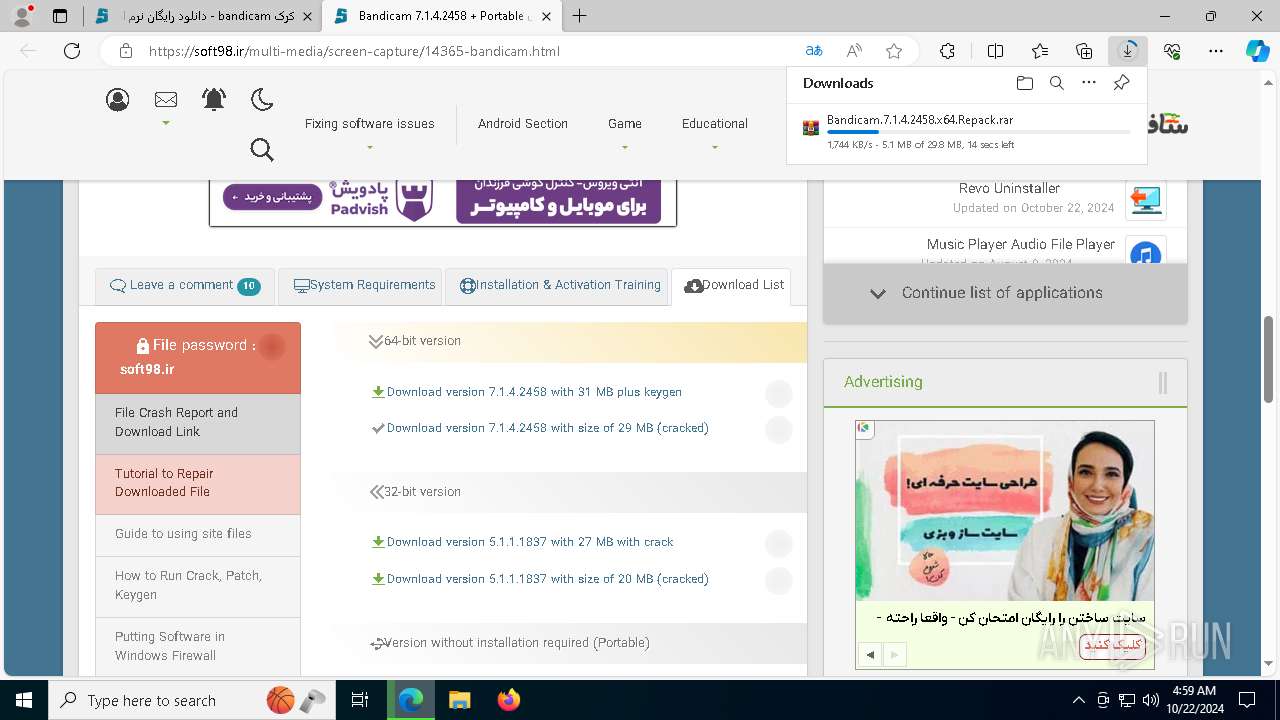
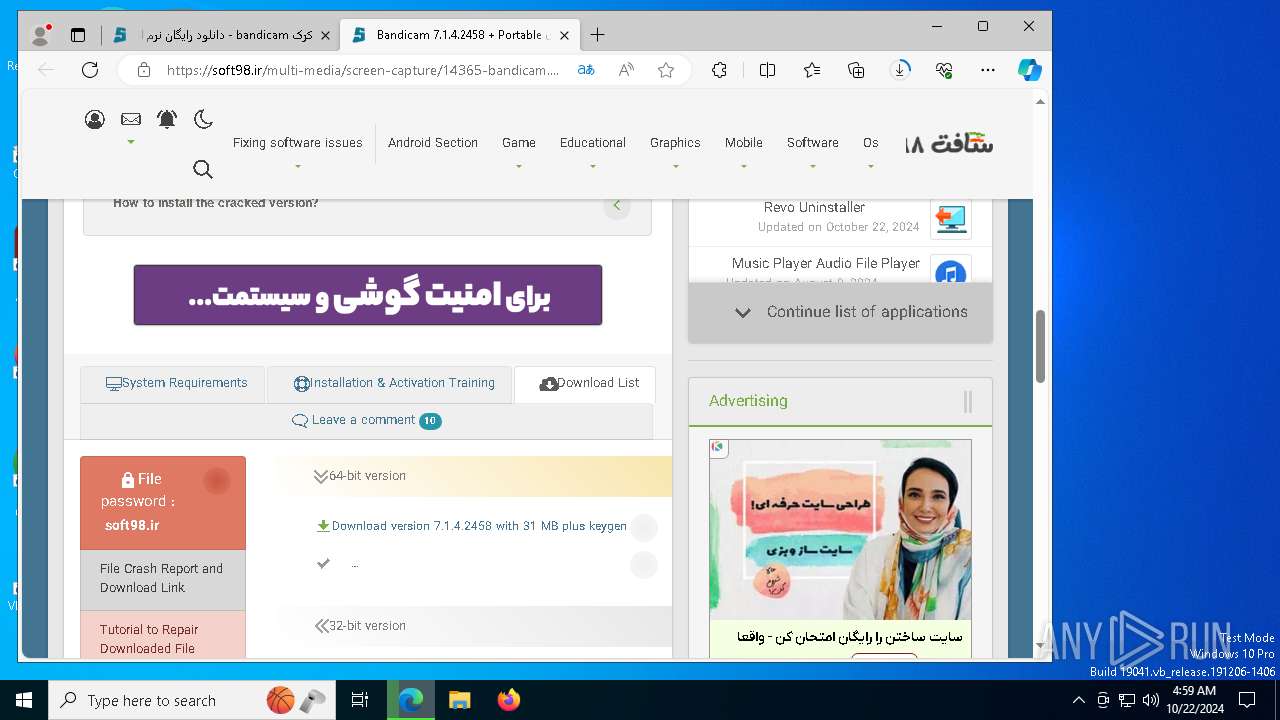
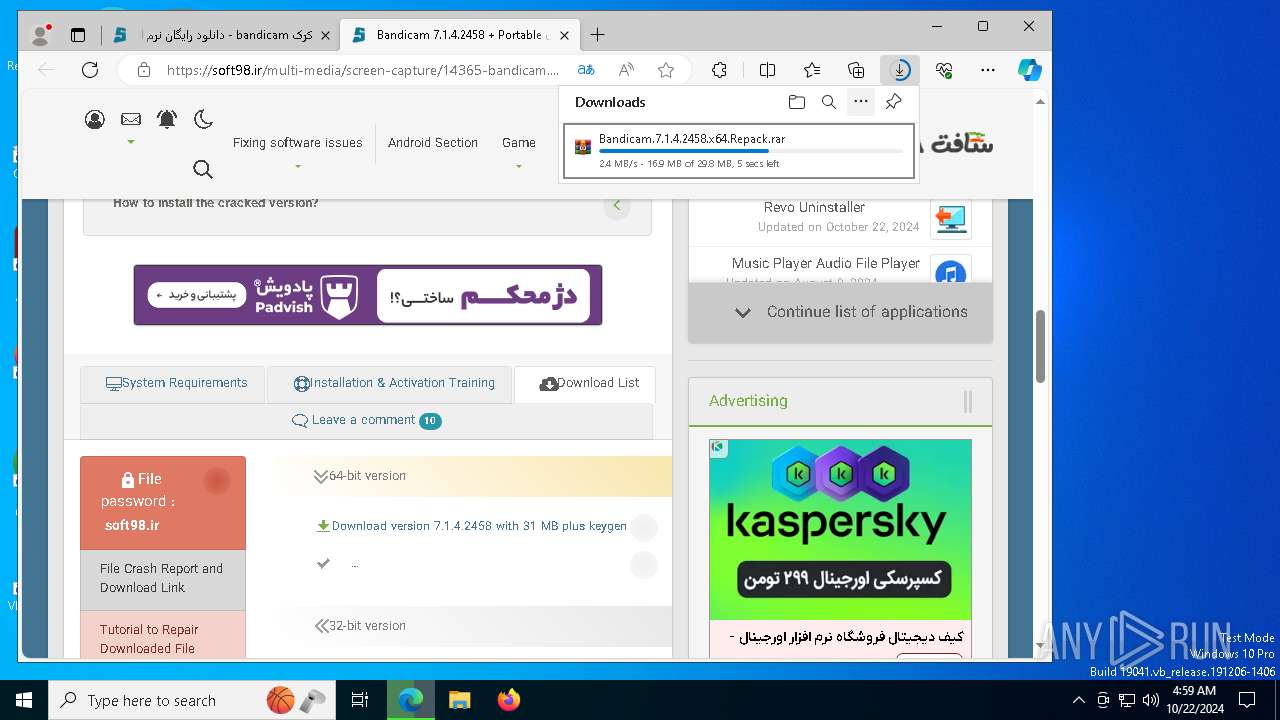
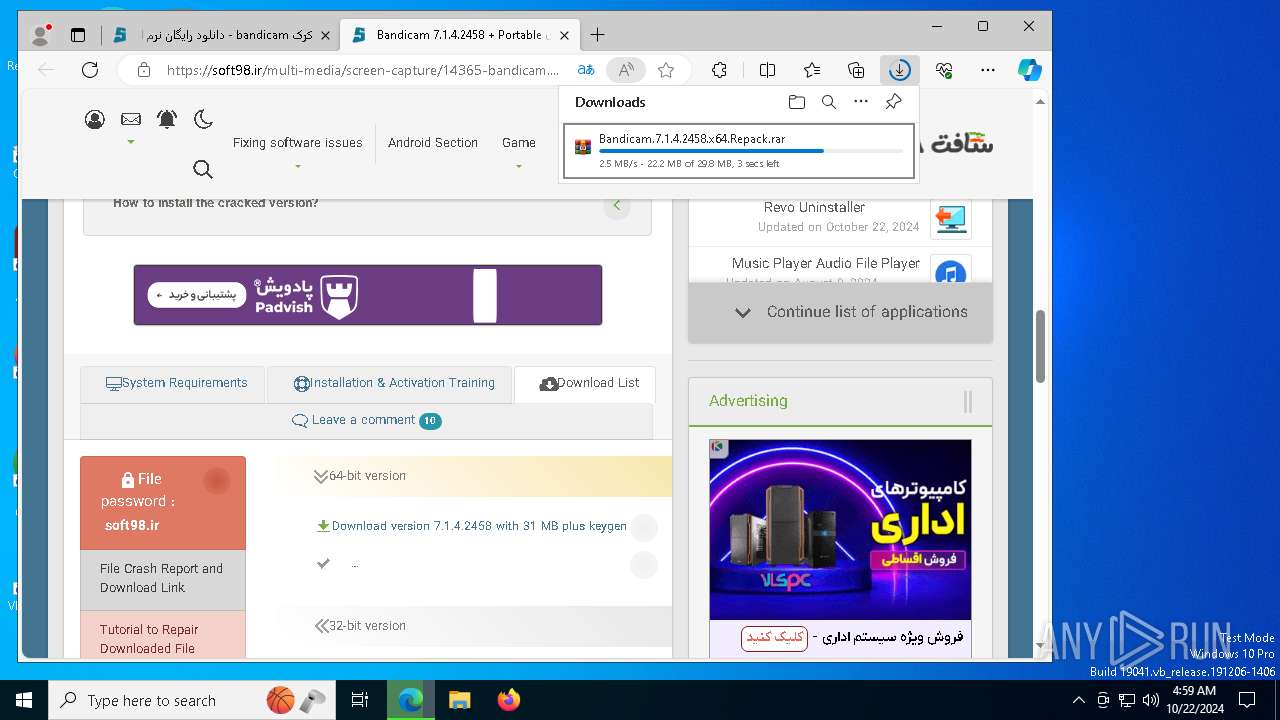
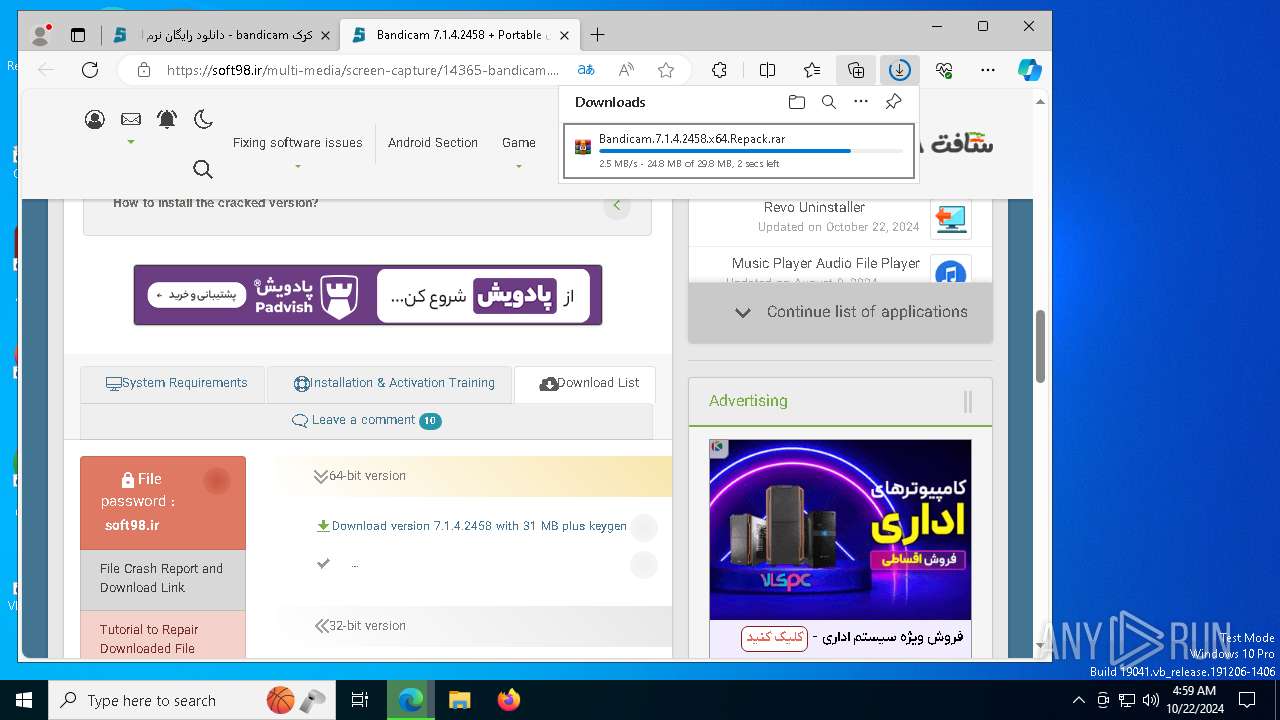
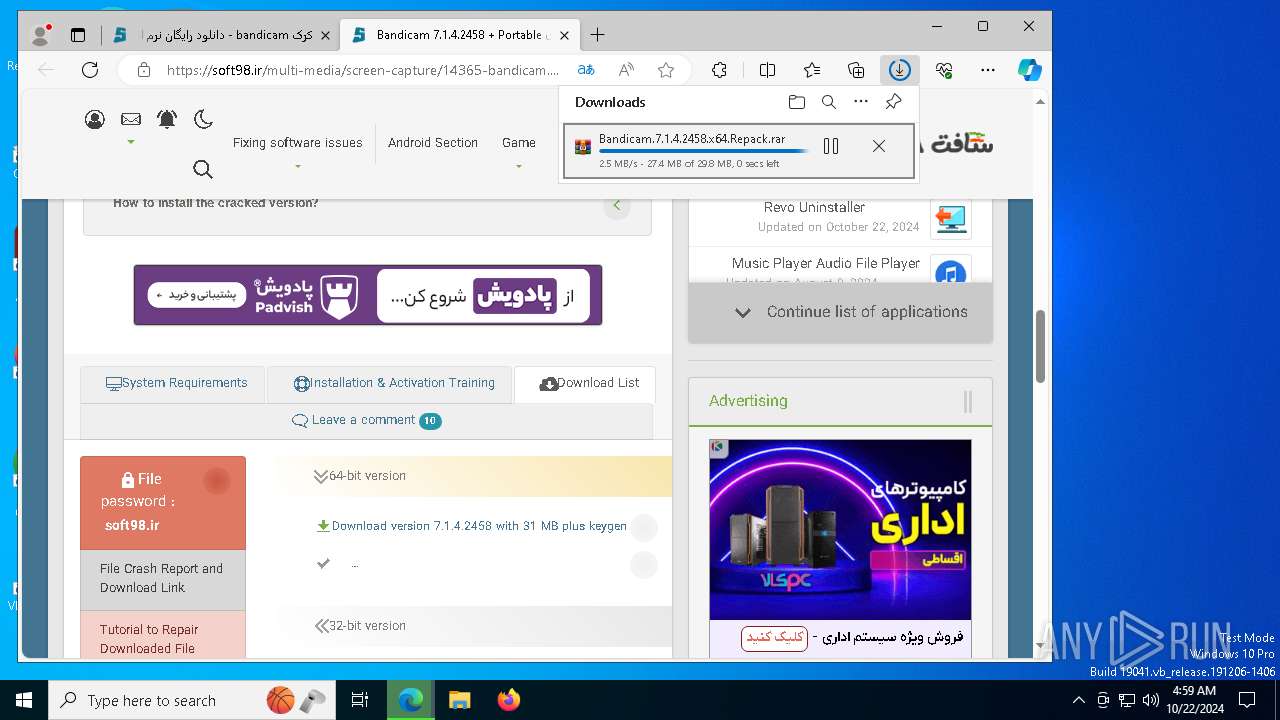
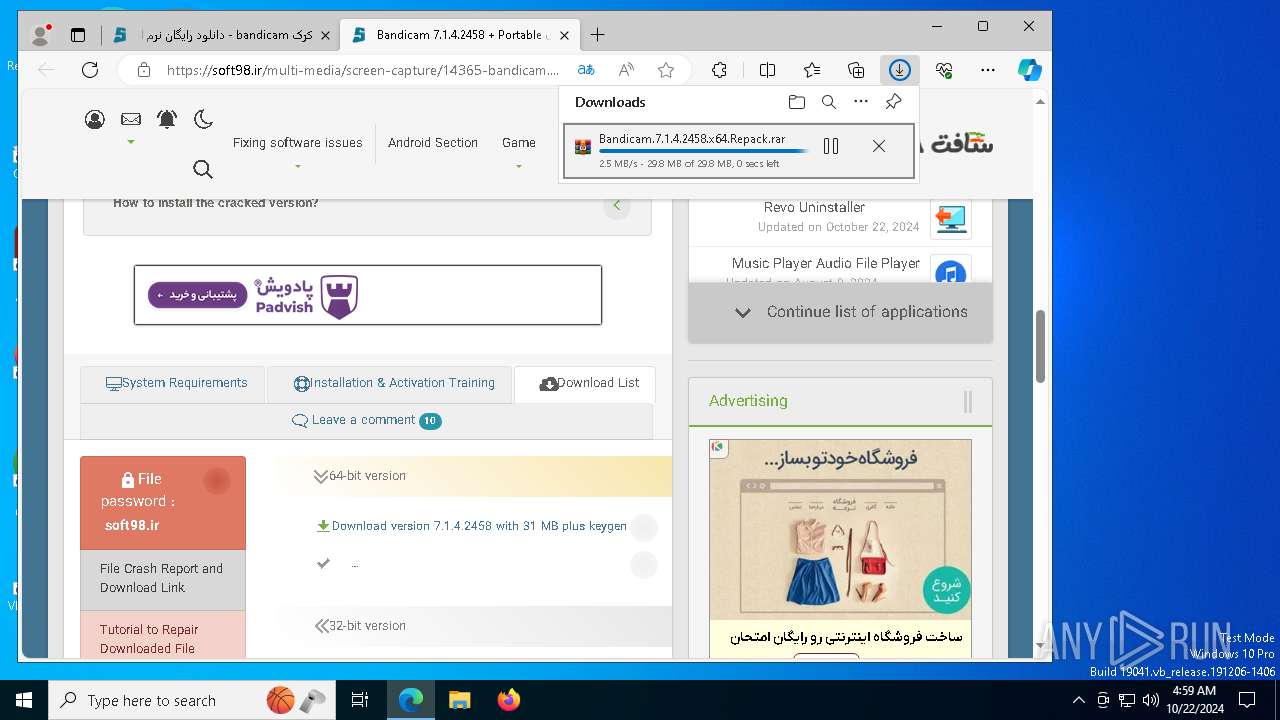
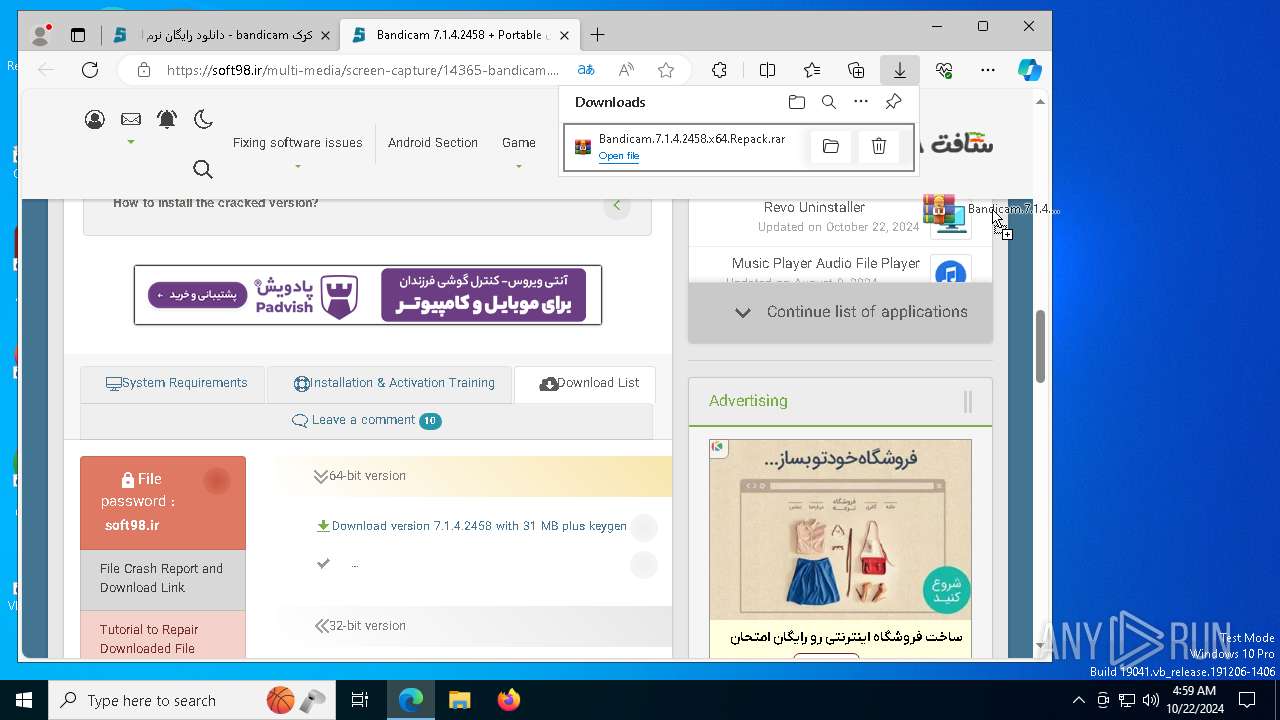
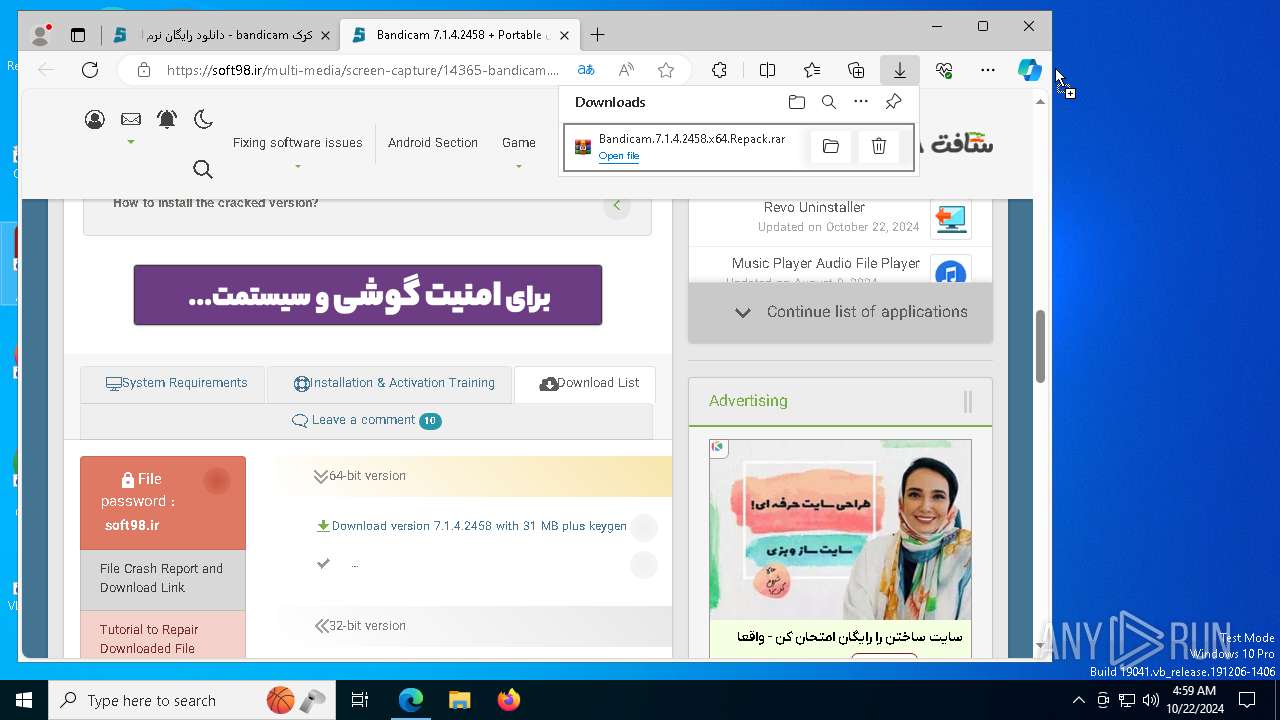
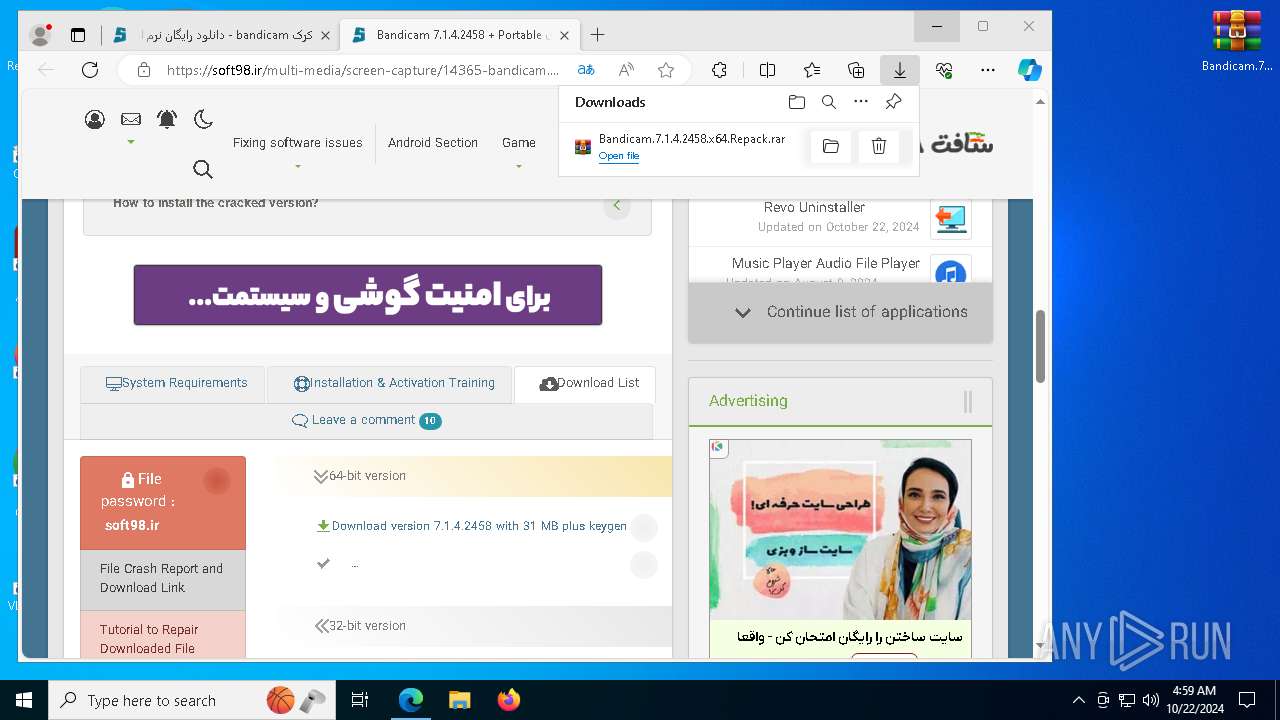
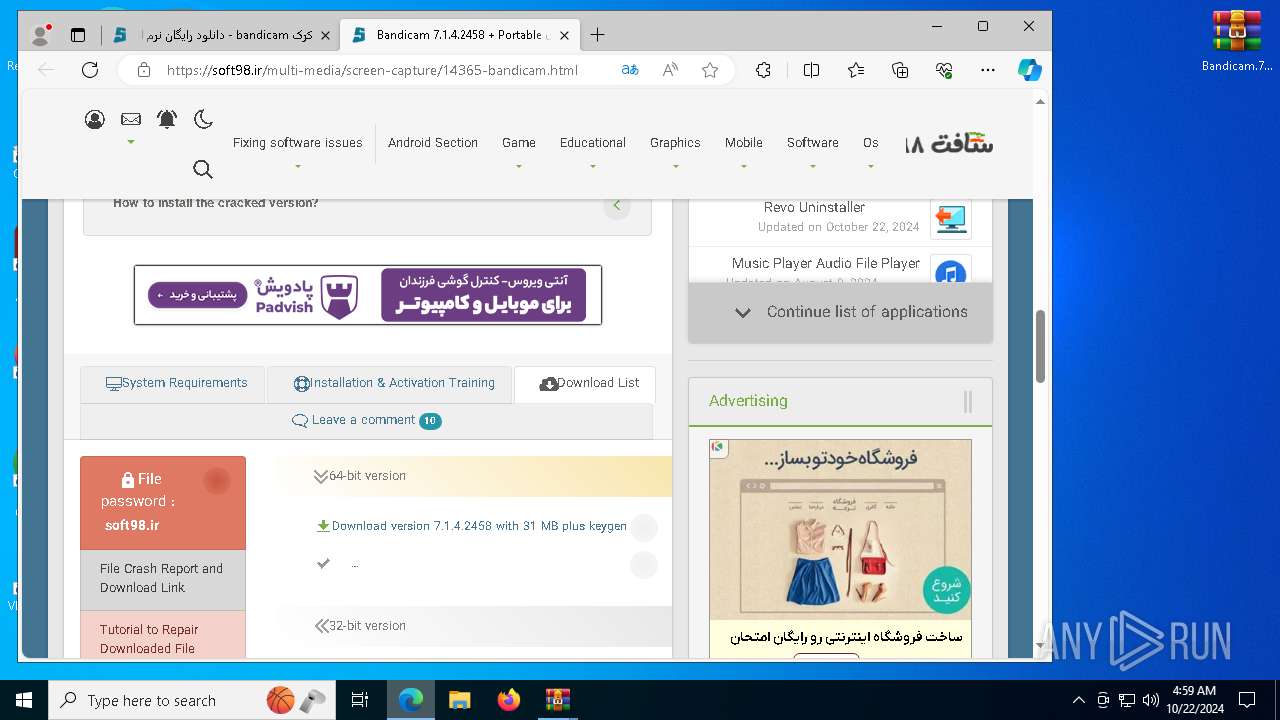
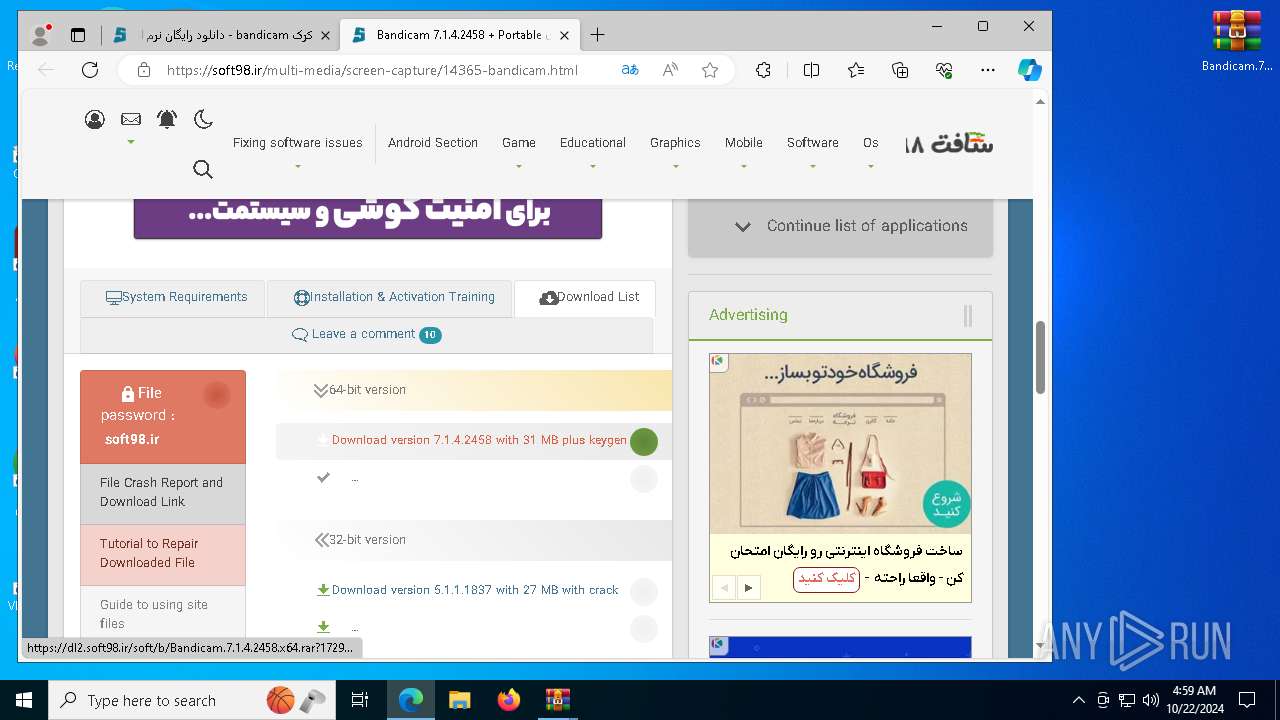
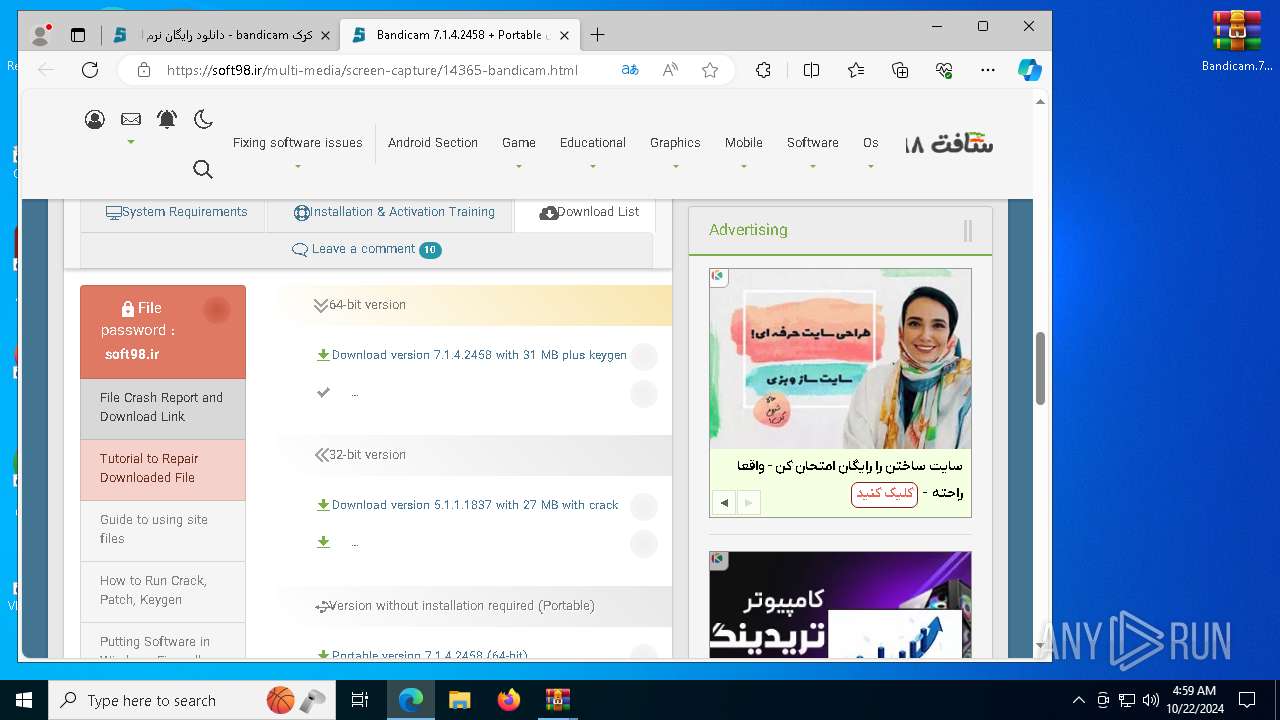
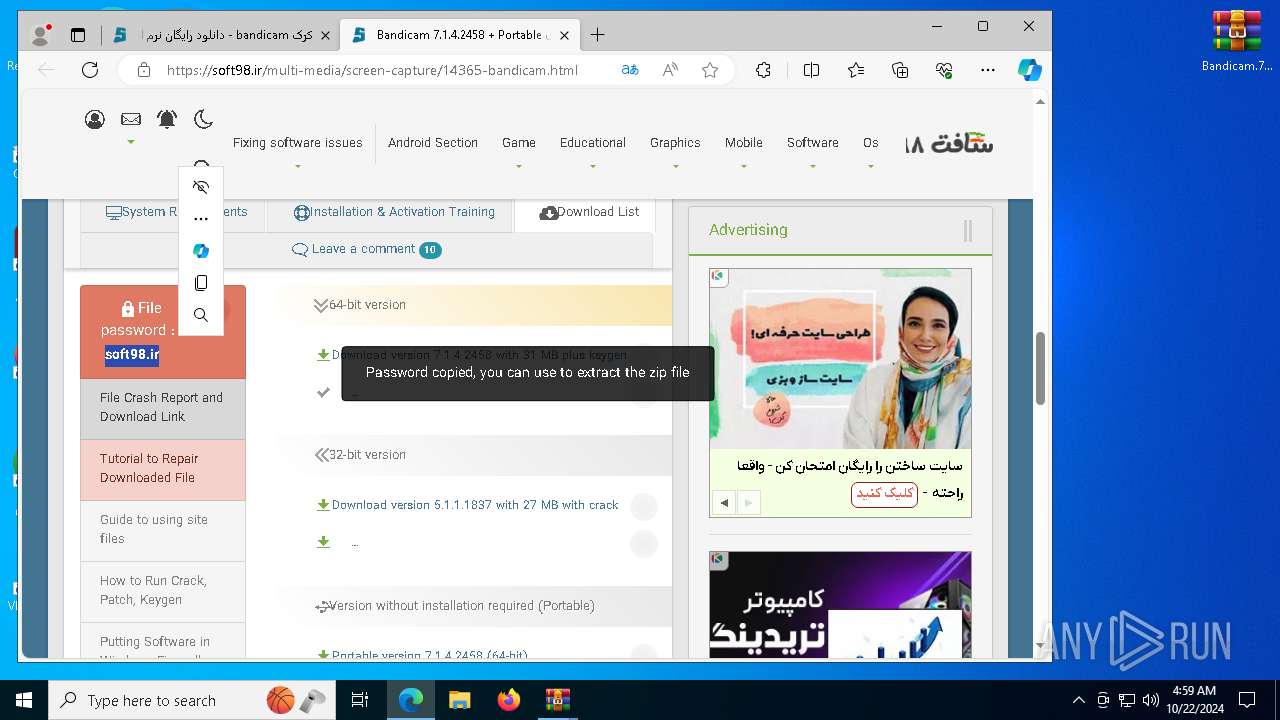
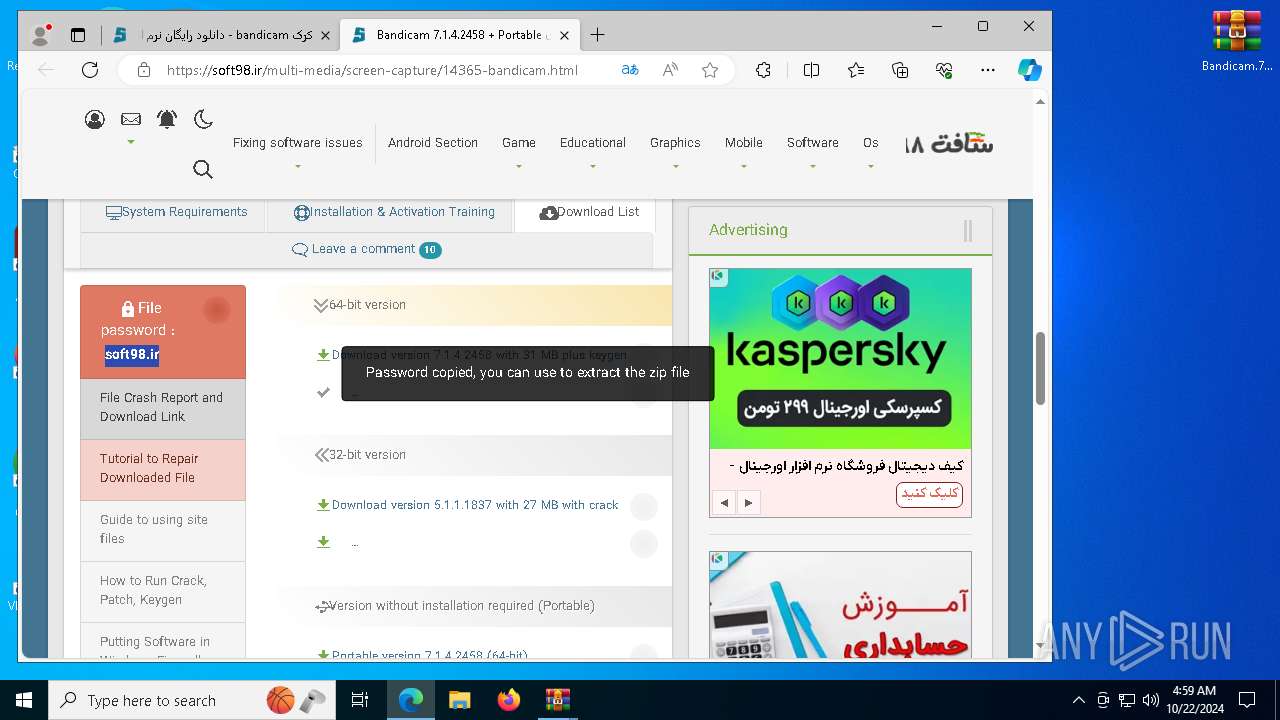
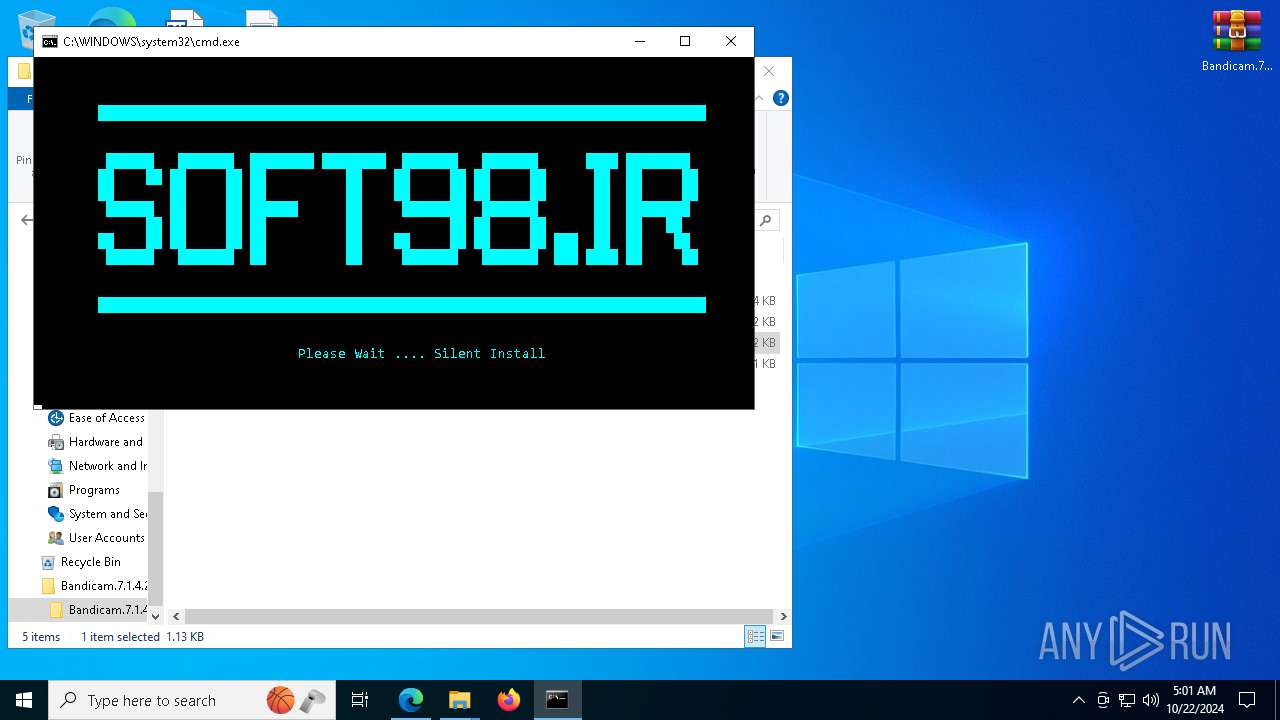
| URL: | https://soft98.ir/tags/%DA%A9%D8%B1%DA%A9%2bbandicam/ |
| Full analysis: | https://app.any.run/tasks/b81857f8-d964-4795-81fd-db307e346410 |
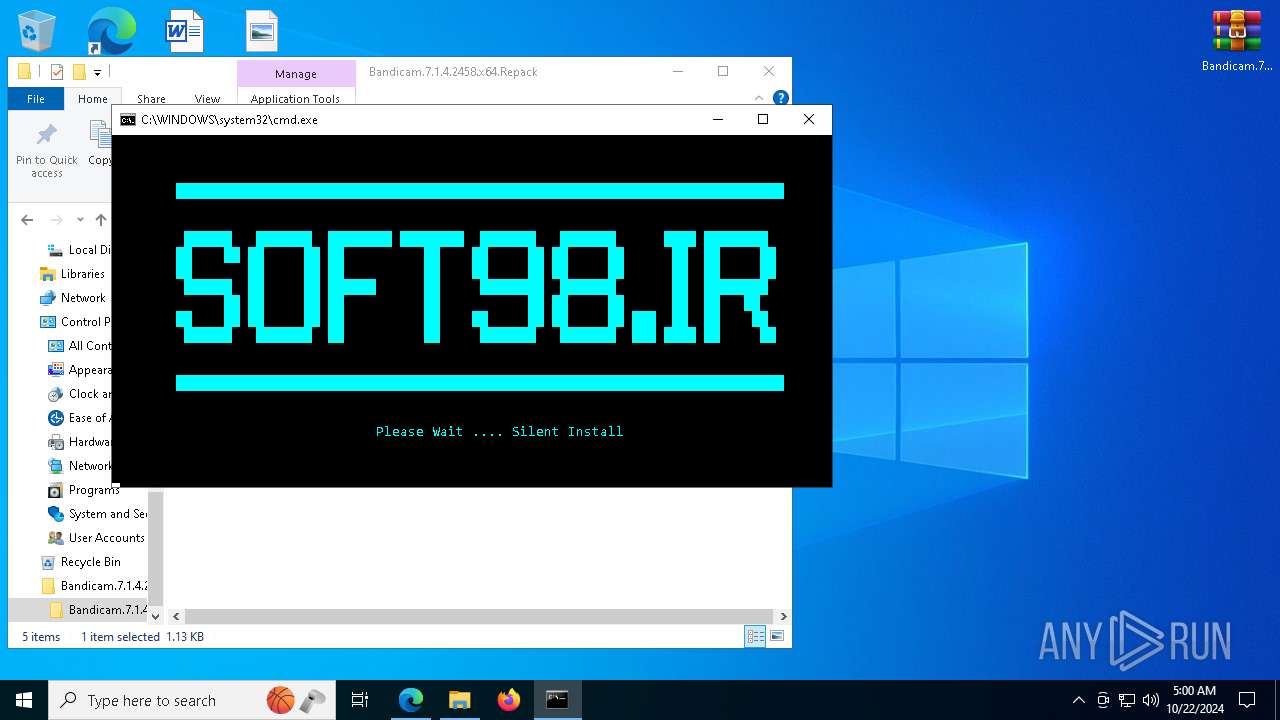
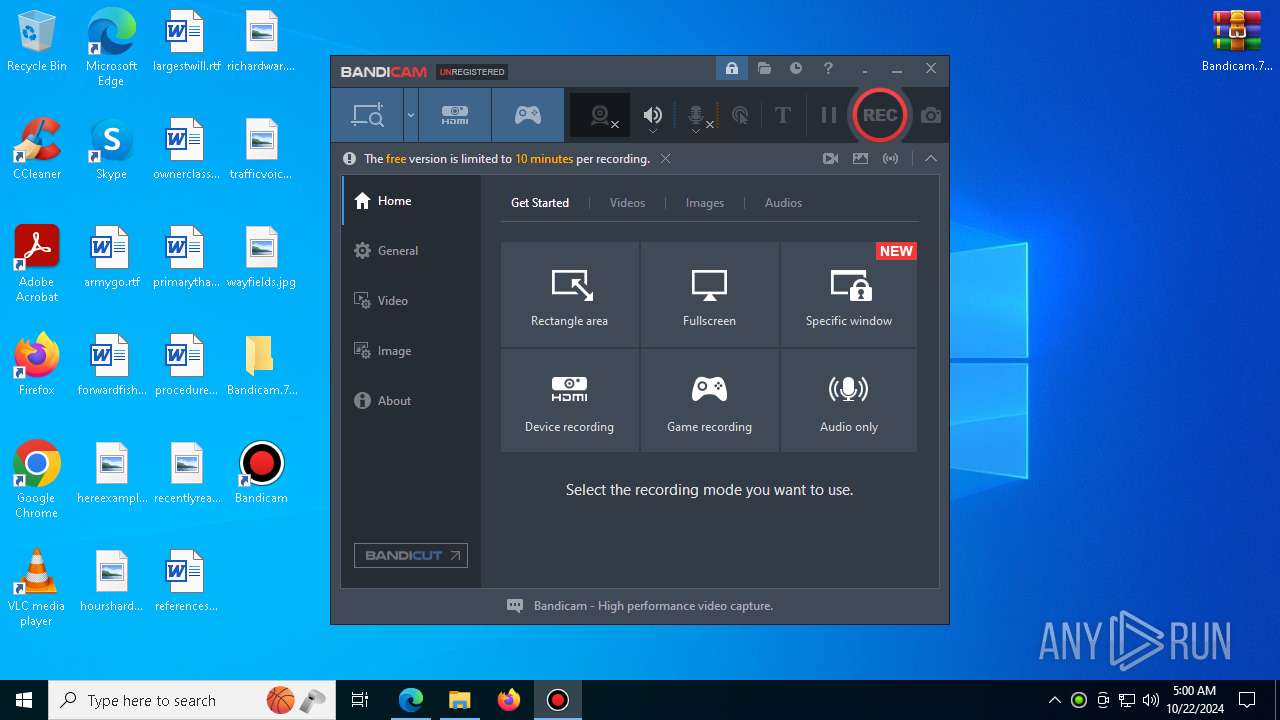
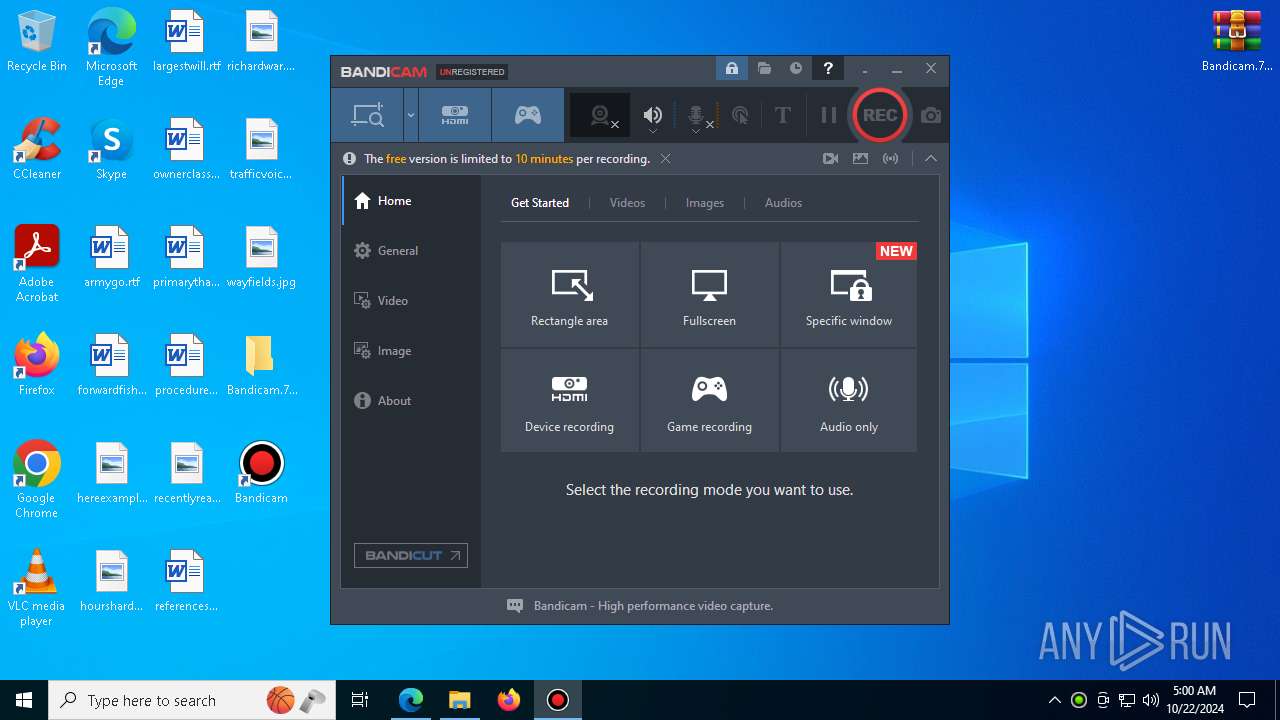
| Verdict: | Malicious activity |
| Analysis date: | October 22, 2024, 04:58:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | D70FD3E7FCE66B5495D9DC46DEC34C6C |
| SHA1: | E0F3EDFE9B5C2FBD5A23D94D8D736D98A7E1C2F2 |
| SHA256: | 75F44F5C7F995E1660DF483D679EB844C2A5E146C0E3132D51A1D28C65A200B1 |
| SSDEEP: | 3:N8HyrXlkUATVyT3:22lCT43 |
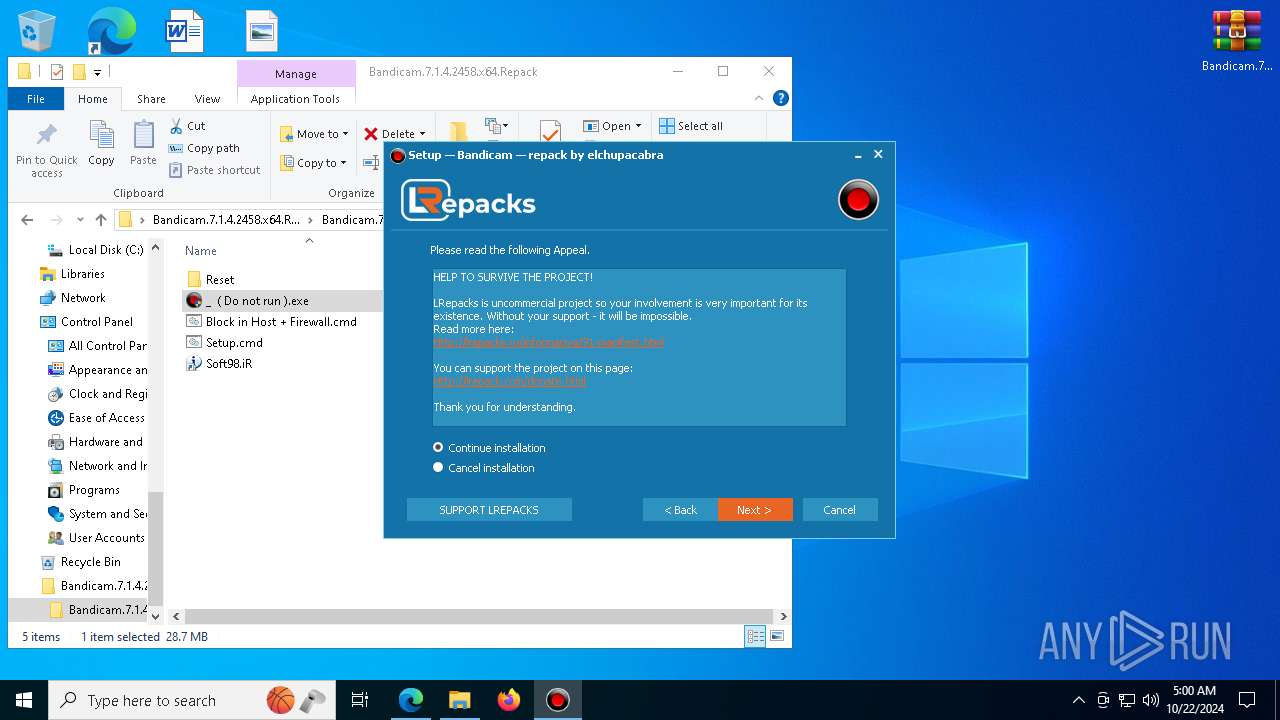
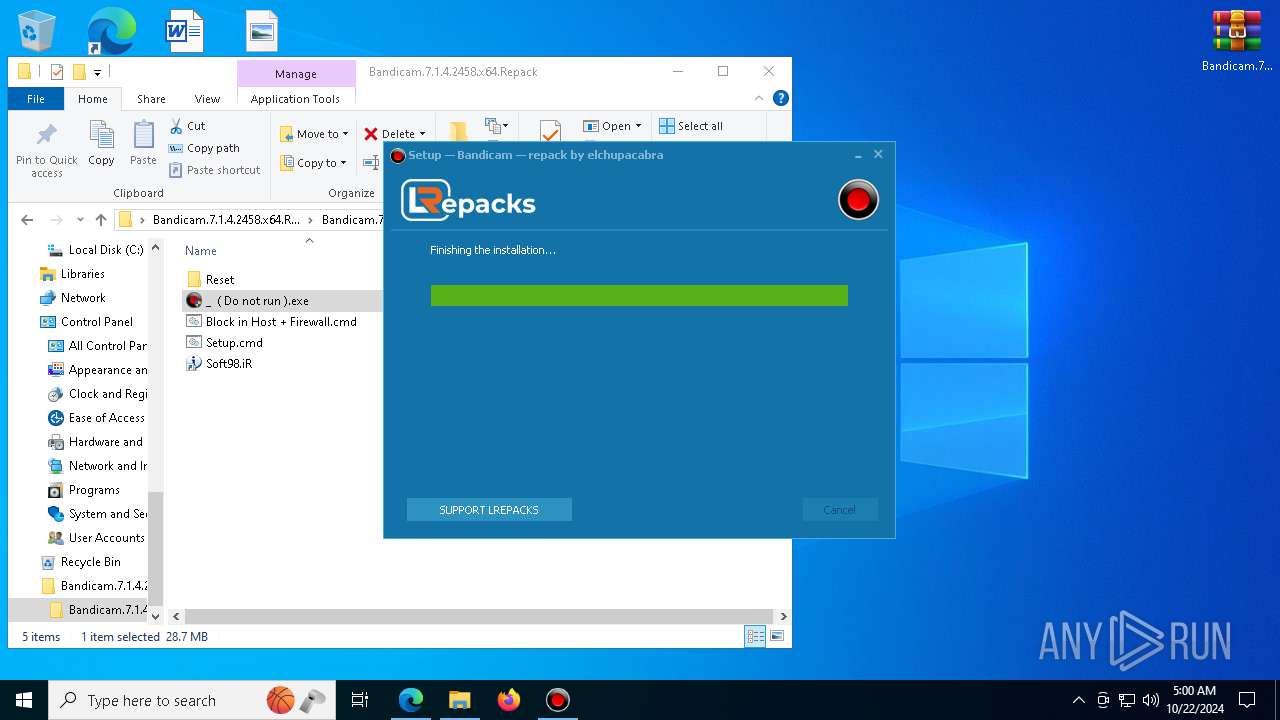
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- _ ( Do not run ).tmp (PID: 7444)
- _ ( Do not run ).tmp (PID: 7476)
- _ ( Do not run ).tmp (PID: 7624)
SUSPICIOUS
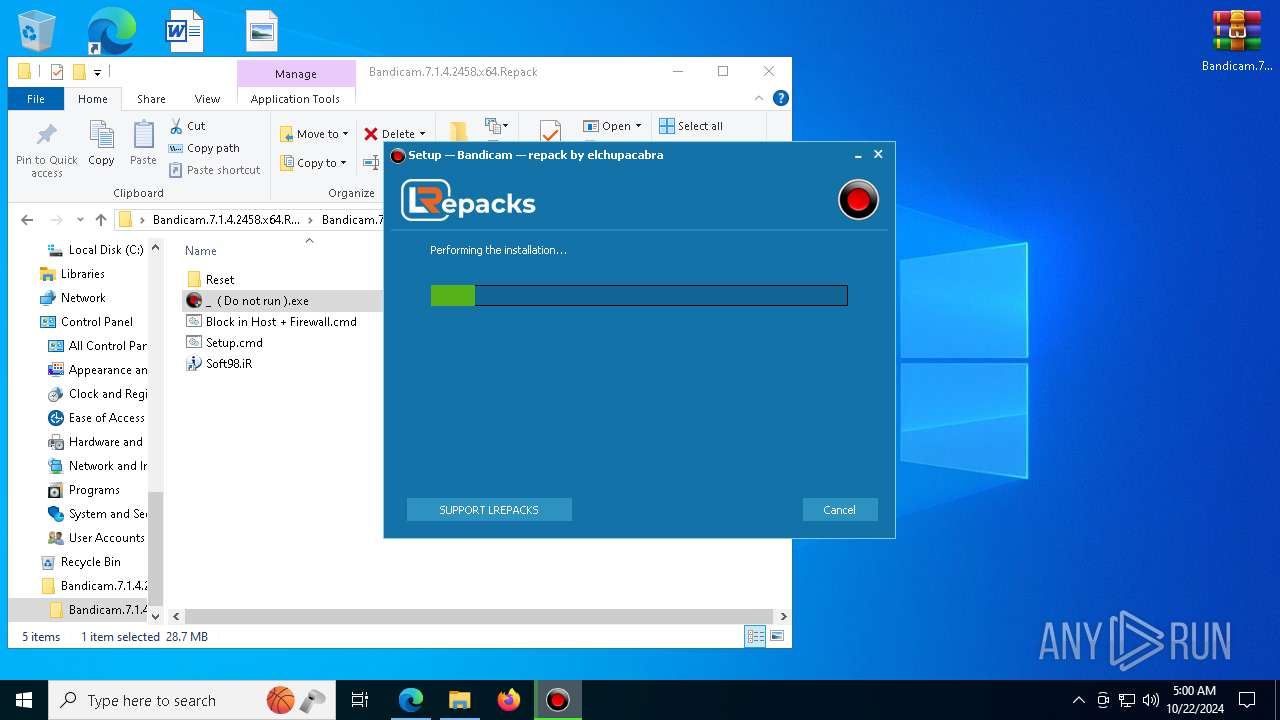
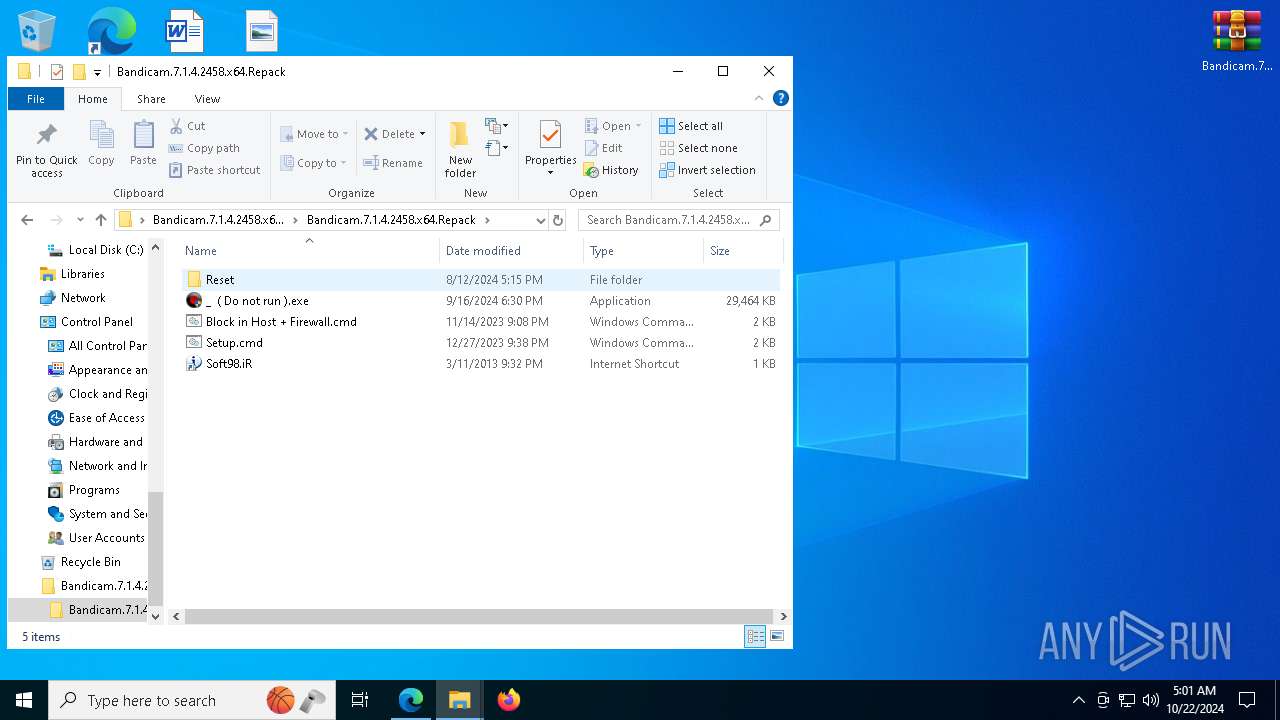
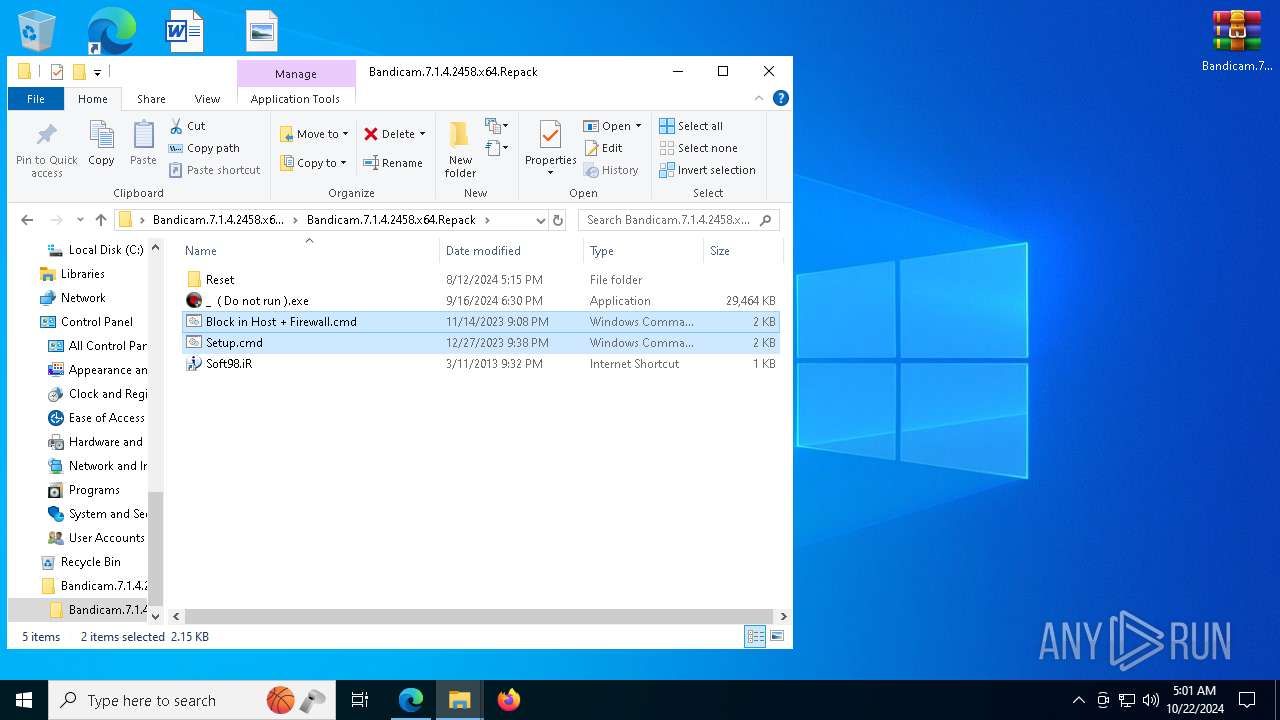
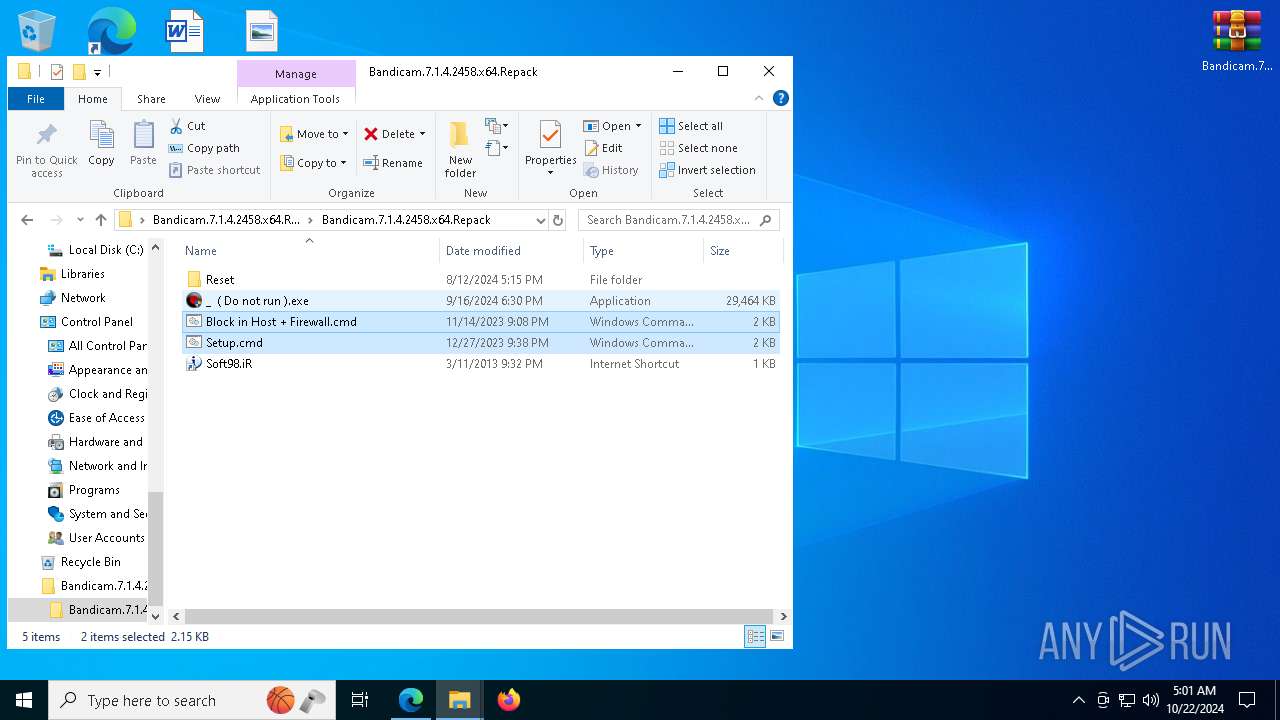
Executable content was dropped or overwritten
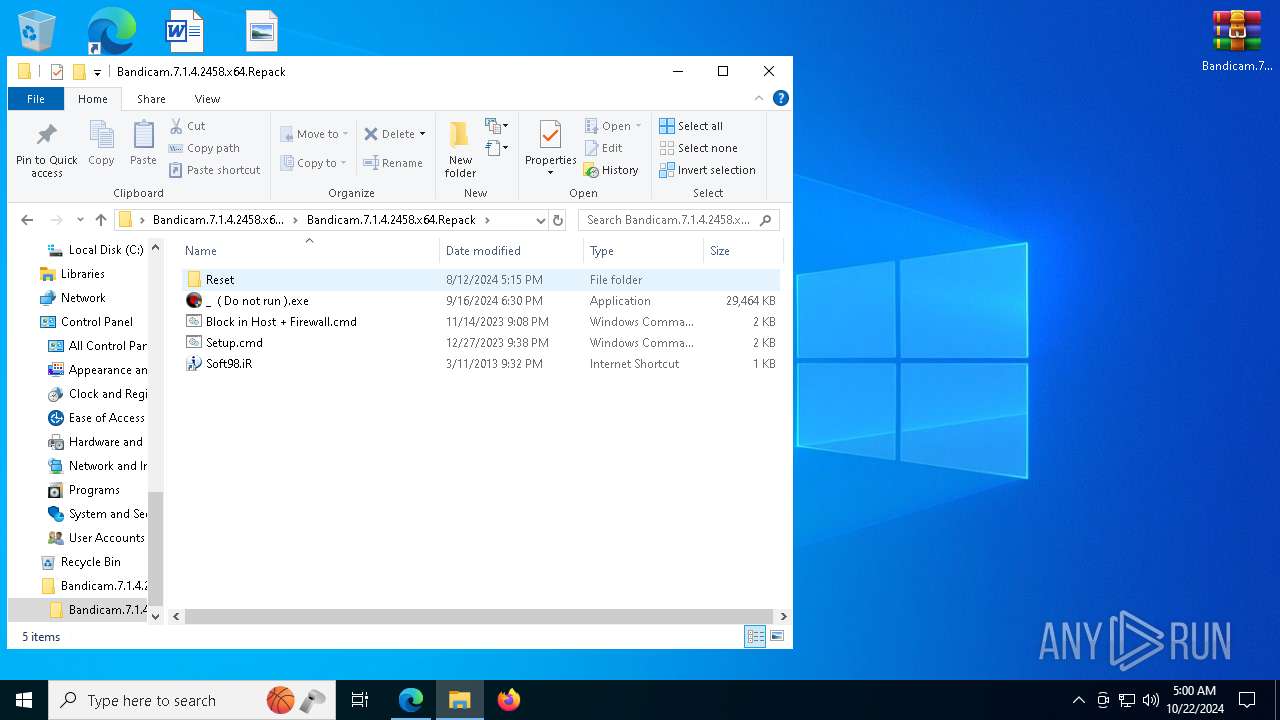
- _ ( Do not run ).exe (PID: 1580)
- _ ( Do not run ).tmp (PID: 7444)
- _ ( Do not run ).exe (PID: 7500)
- _ ( Do not run ).tmp (PID: 7476)
- _ ( Do not run ).tmp (PID: 7624)
- _ ( Do not run ).exe (PID: 7900)
Process drops legitimate windows executable
- _ ( Do not run ).tmp (PID: 7444)
- _ ( Do not run ).tmp (PID: 7476)
- _ ( Do not run ).tmp (PID: 7624)
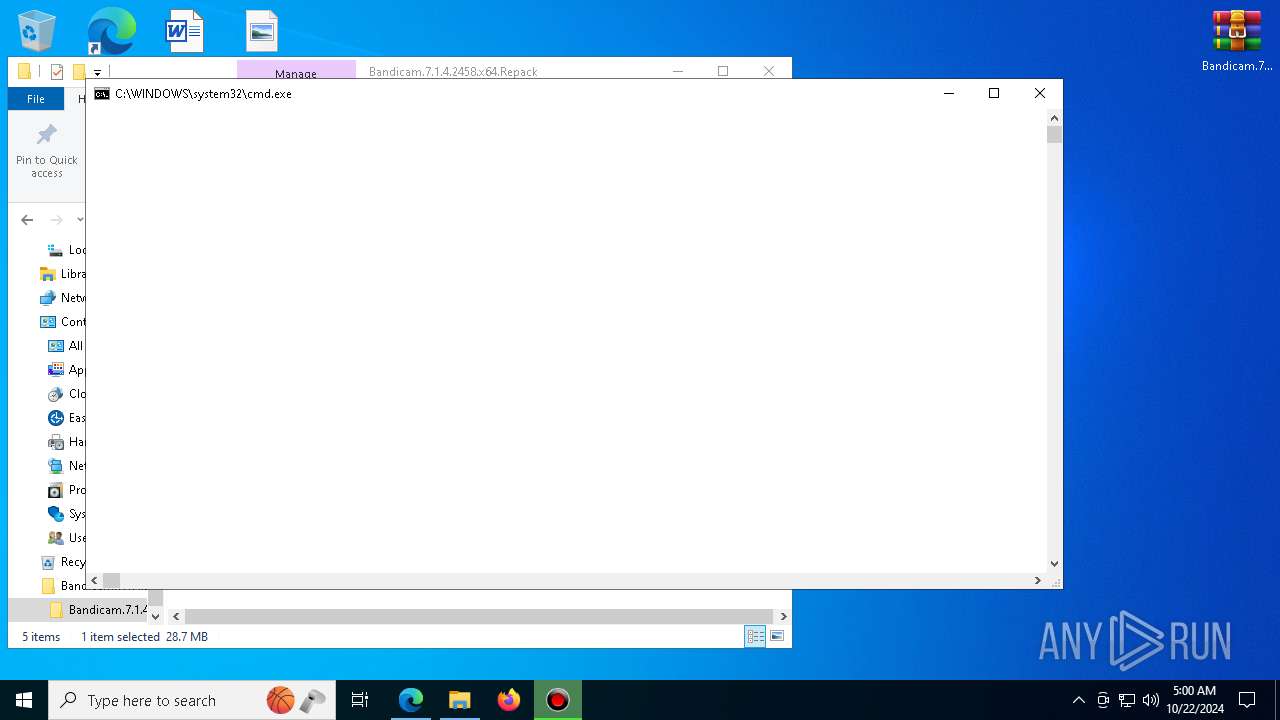
Application launched itself
- cmd.exe (PID: 6512)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 7448)
- cmd.exe (PID: 4376)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6512)
- _ ( Do not run ).tmp (PID: 7444)
- cmd.exe (PID: 8016)
- cscript.exe (PID: 7420)
- cmd.exe (PID: 7448)
- _ ( Do not run ).tmp (PID: 7476)
- _ ( Do not run ).tmp (PID: 7624)
- cmd.exe (PID: 4376)
The process executes VB scripts
- cmd.exe (PID: 6512)
Executing commands from a ".bat" file
- _ ( Do not run ).tmp (PID: 7444)
- _ ( Do not run ).tmp (PID: 7476)
- _ ( Do not run ).tmp (PID: 7624)
The executable file from the user directory is run by the CMD process
- bcact.exe (PID: 2420)
- bcact.exe (PID: 2864)
- bcact.exe (PID: 4996)
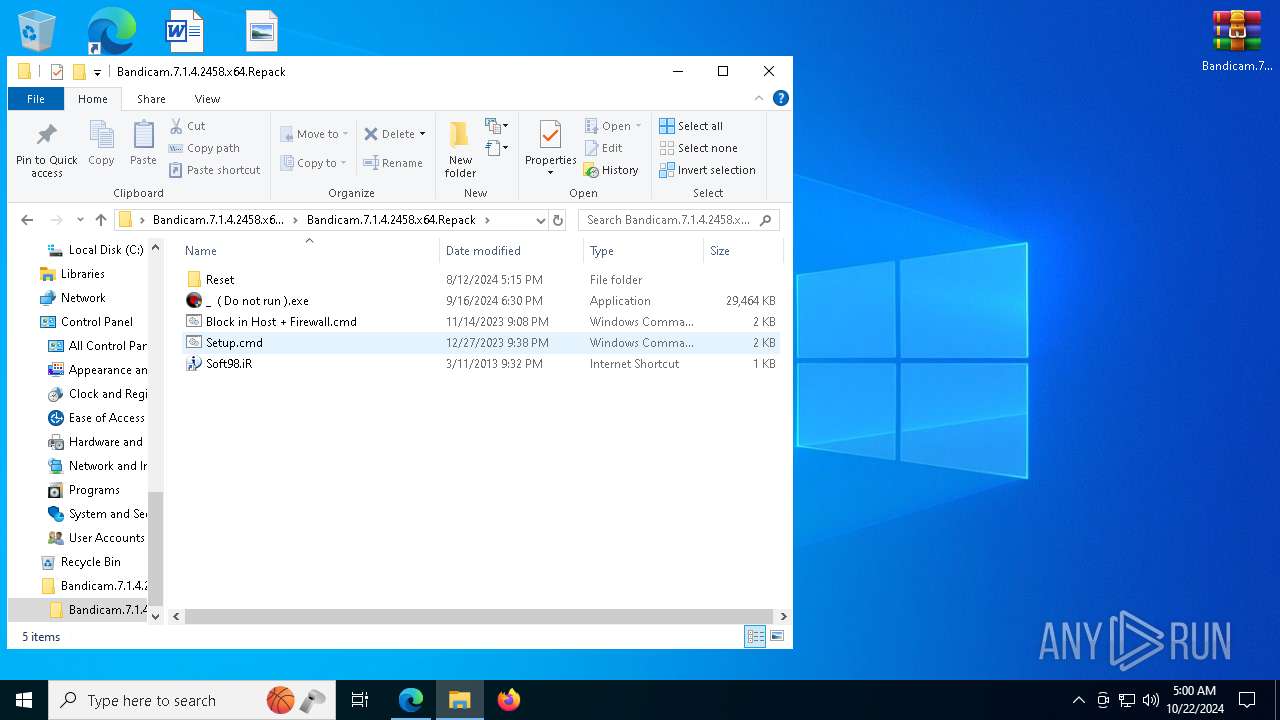
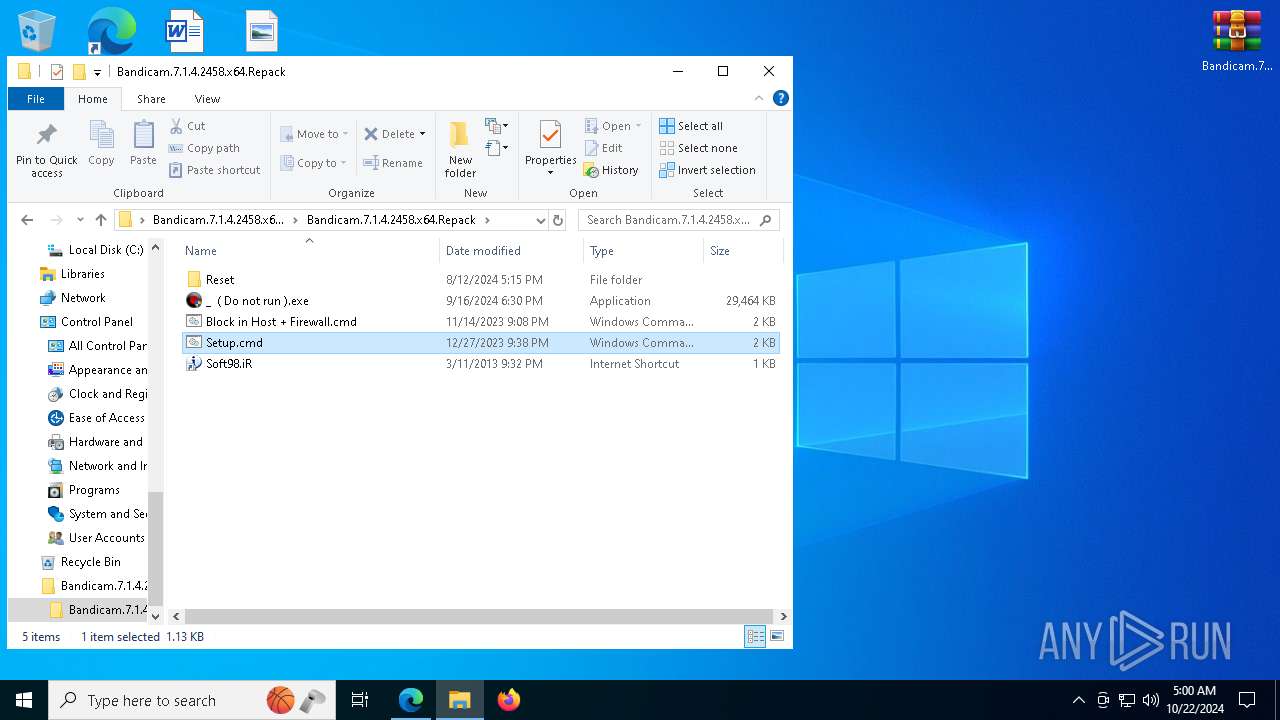
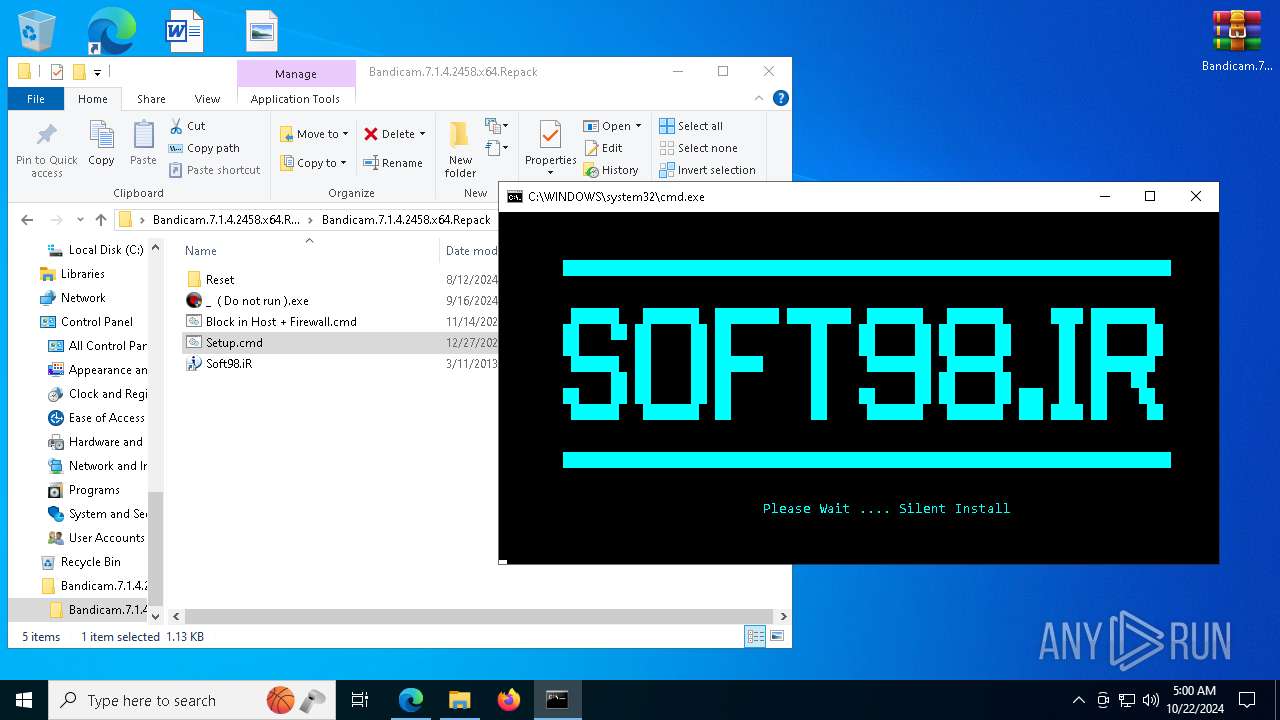
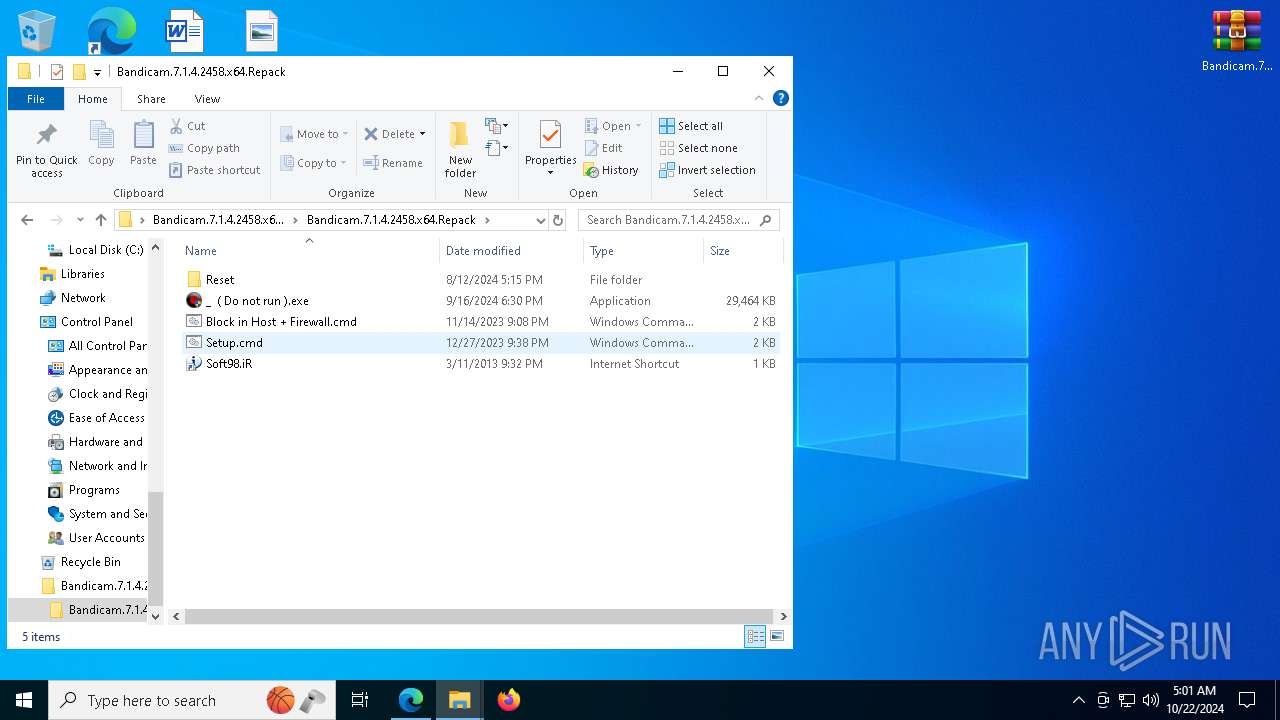
Executing commands from ".cmd" file
- cscript.exe (PID: 7420)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1200)
- cmd.exe (PID: 6460)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 6300)
- bdcam.exe (PID: 7620)
- cmd.exe (PID: 4012)
- bdcam.exe (PID: 6860)
- cmd.exe (PID: 944)
- bdcam.exe (PID: 7420)
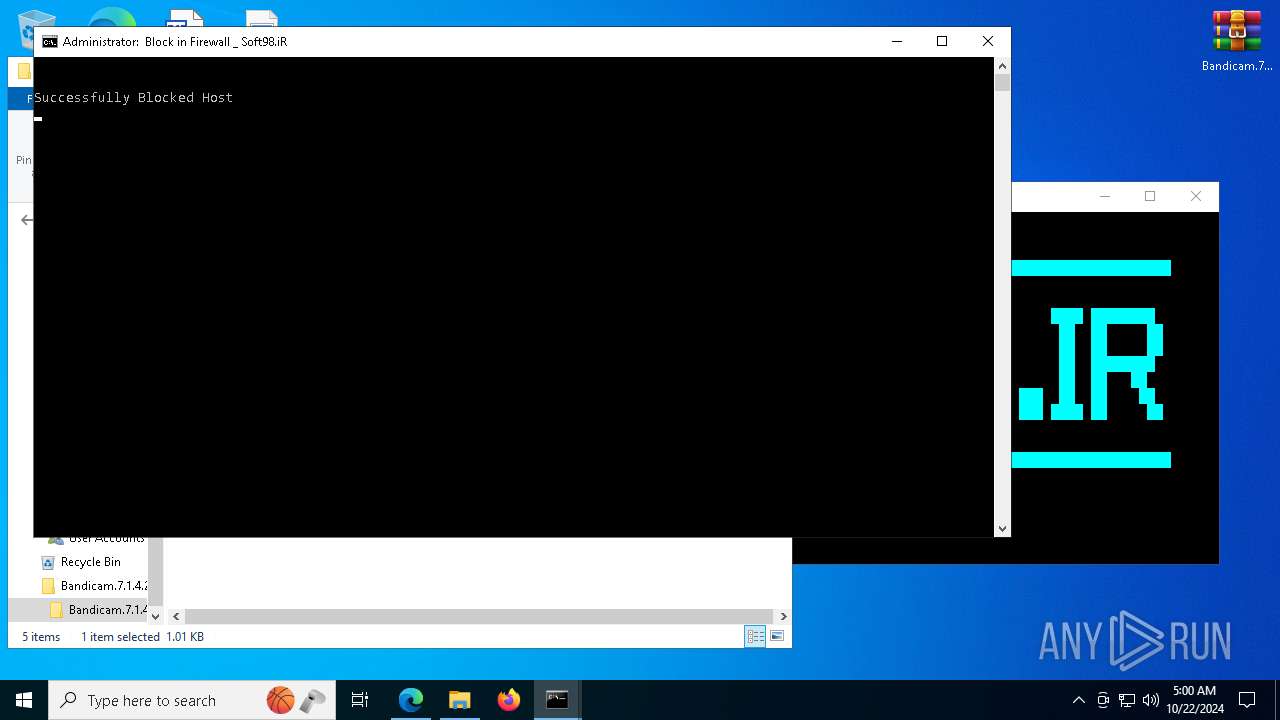
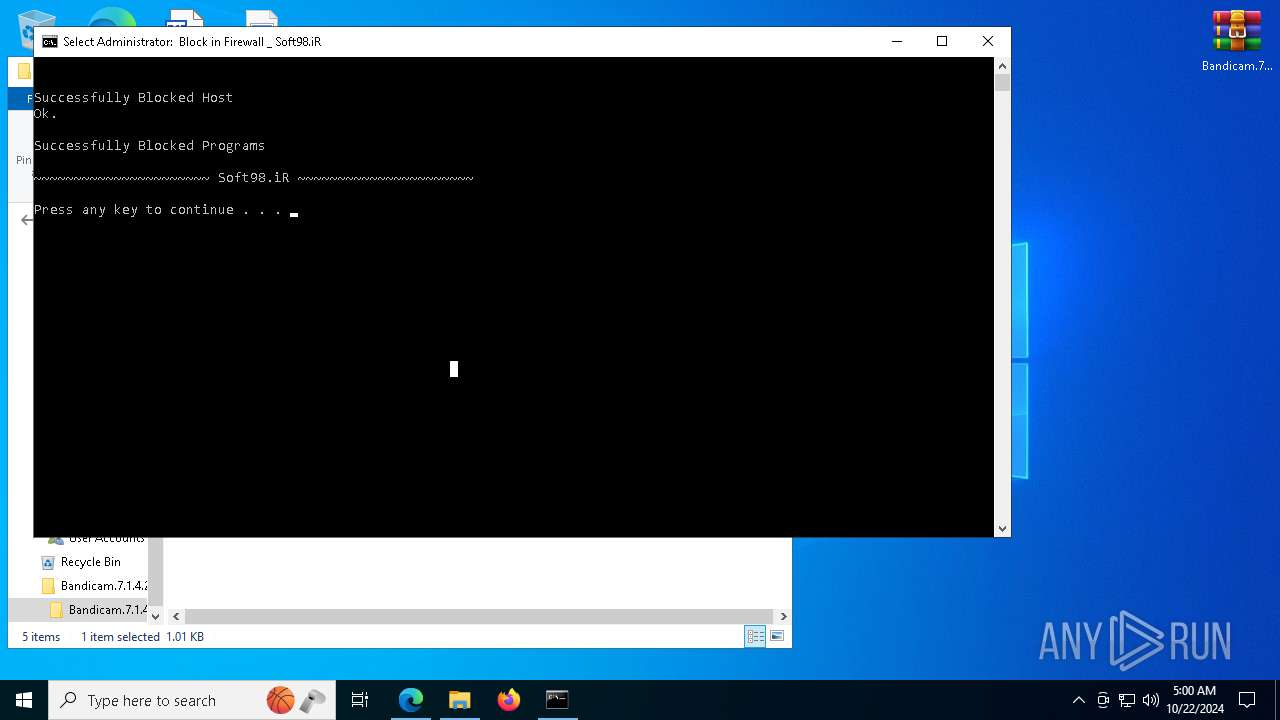
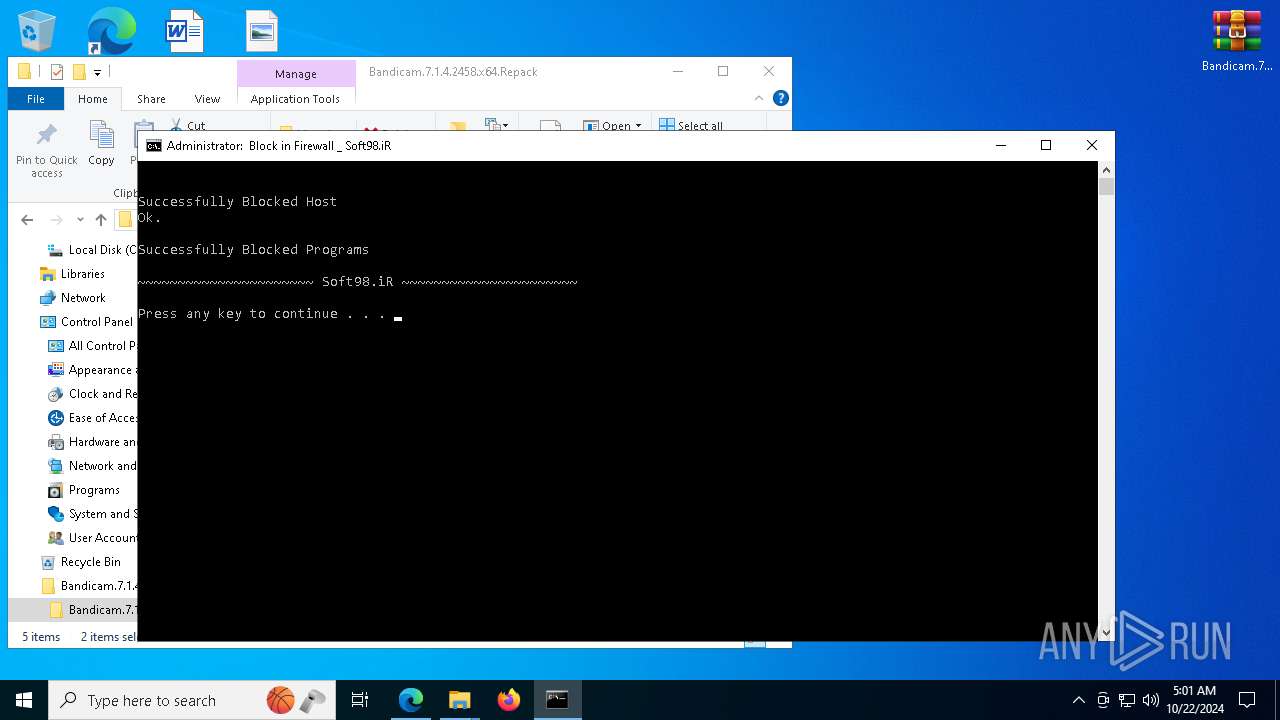
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 1200)
- cmd.exe (PID: 6460)
Uses REG/REGEDIT.EXE to modify registry
- _ ( Do not run ).tmp (PID: 7444)
- _ ( Do not run ).tmp (PID: 7476)
- _ ( Do not run ).tmp (PID: 7624)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- _ ( Do not run ).tmp (PID: 7444)
- _ ( Do not run ).tmp (PID: 7476)
- _ ( Do not run ).tmp (PID: 7624)
INFO
Application launched itself
- msedge.exe (PID: 6268)
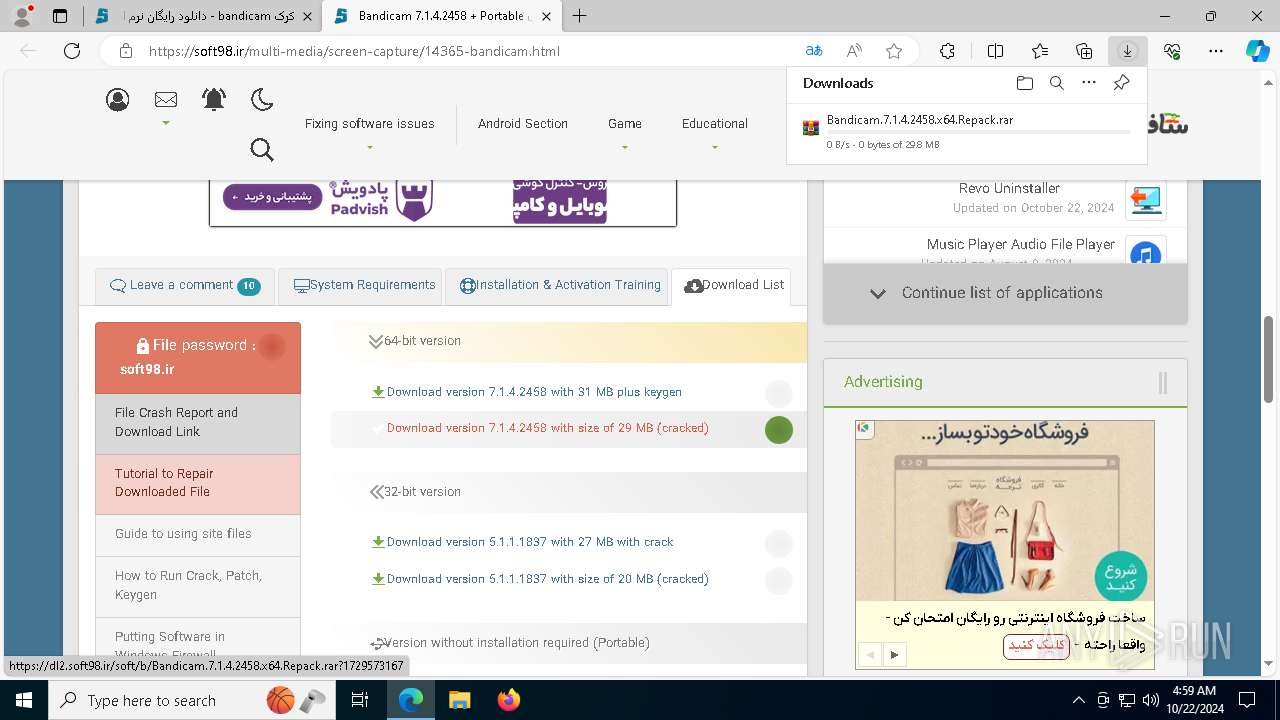
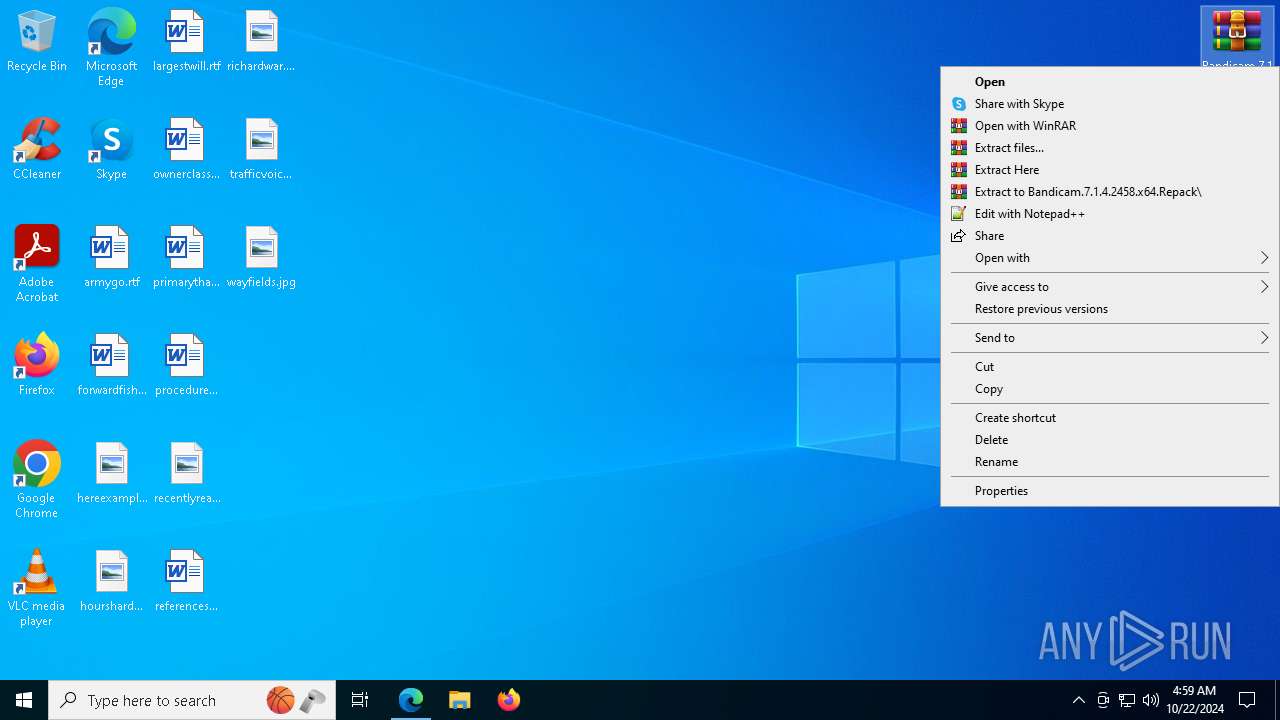
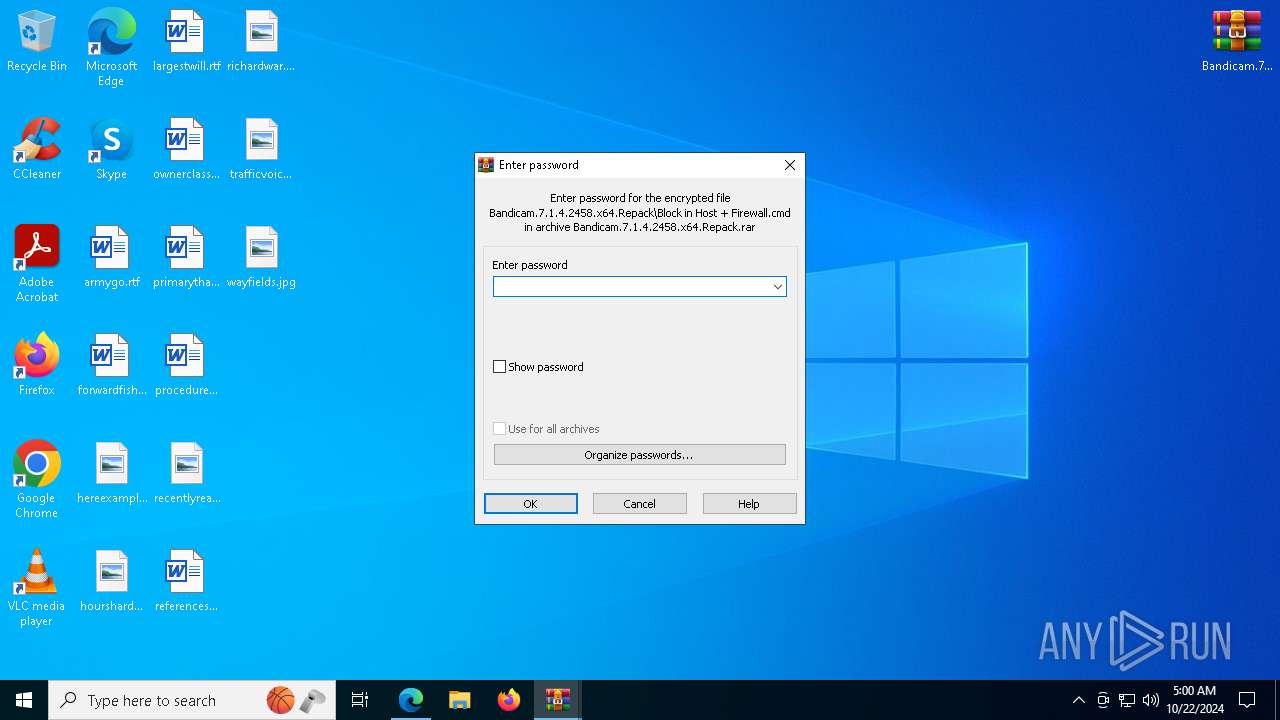
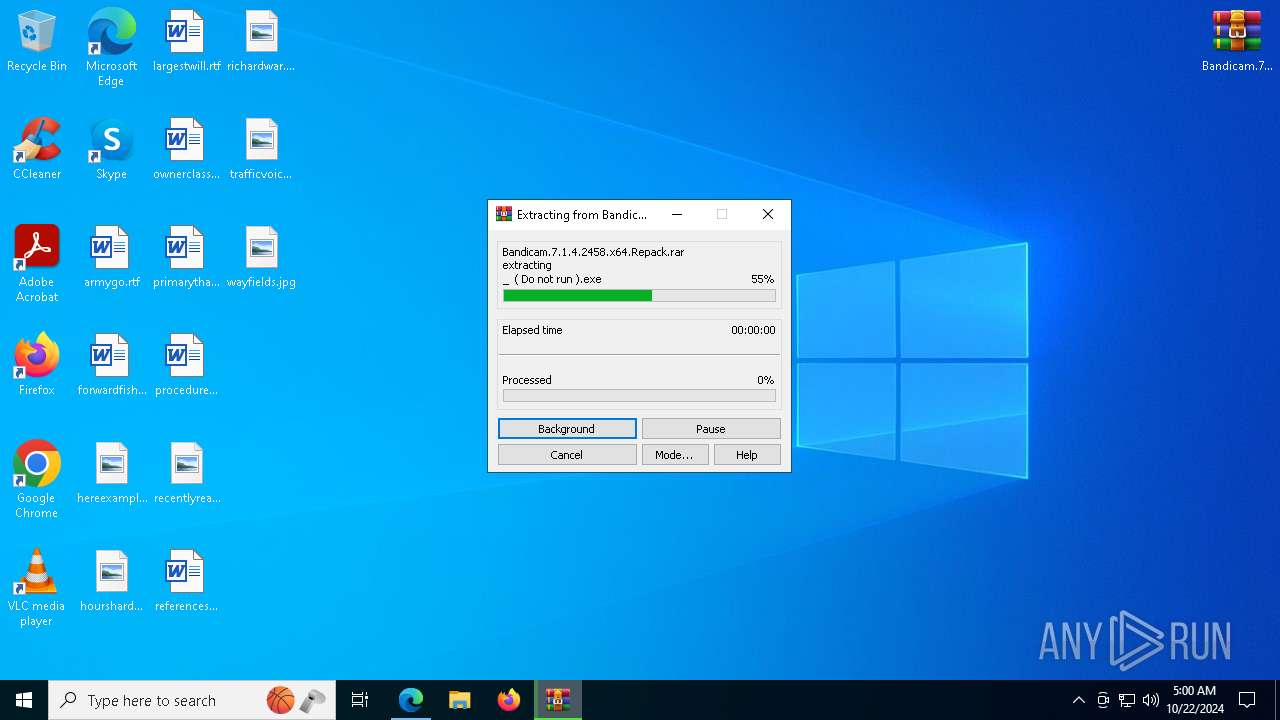
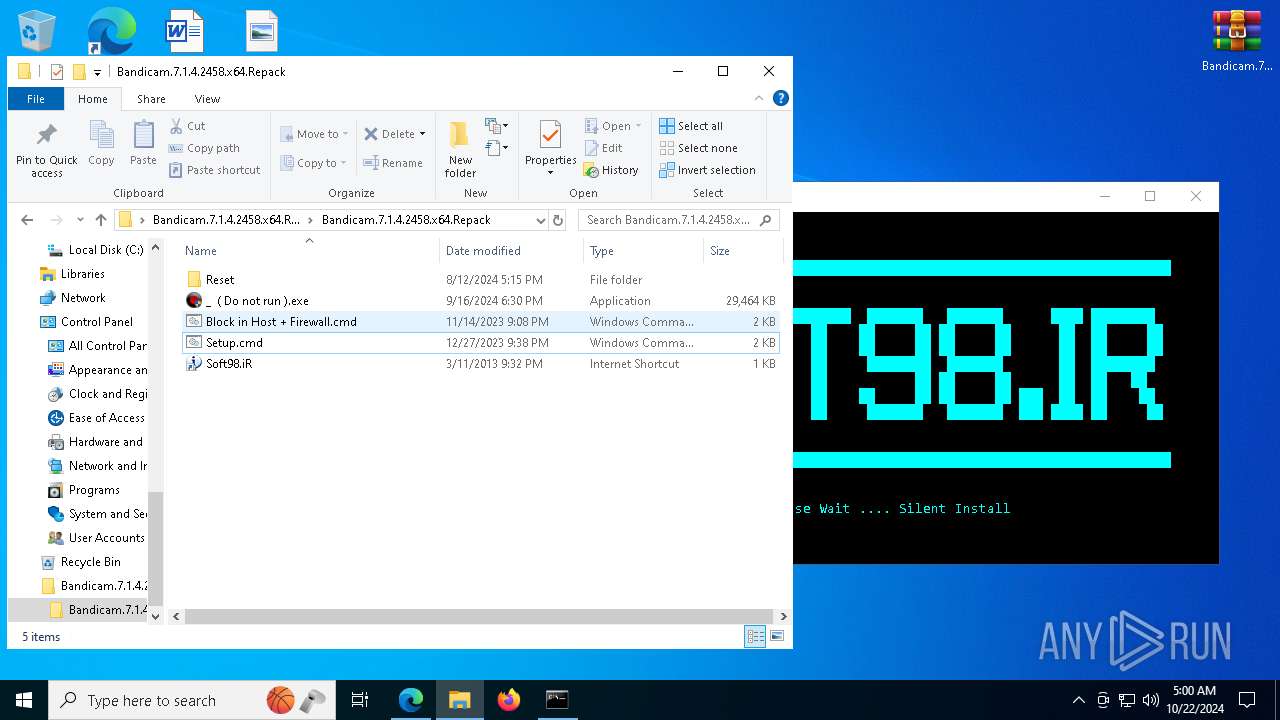
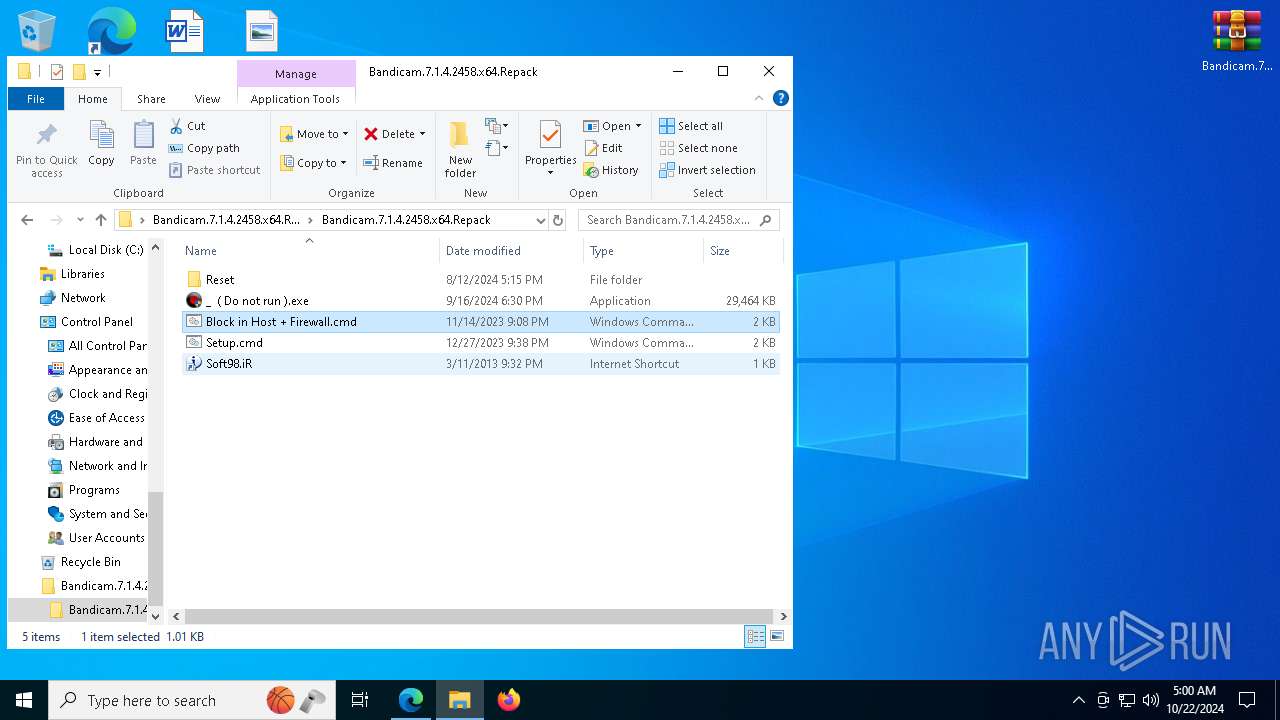
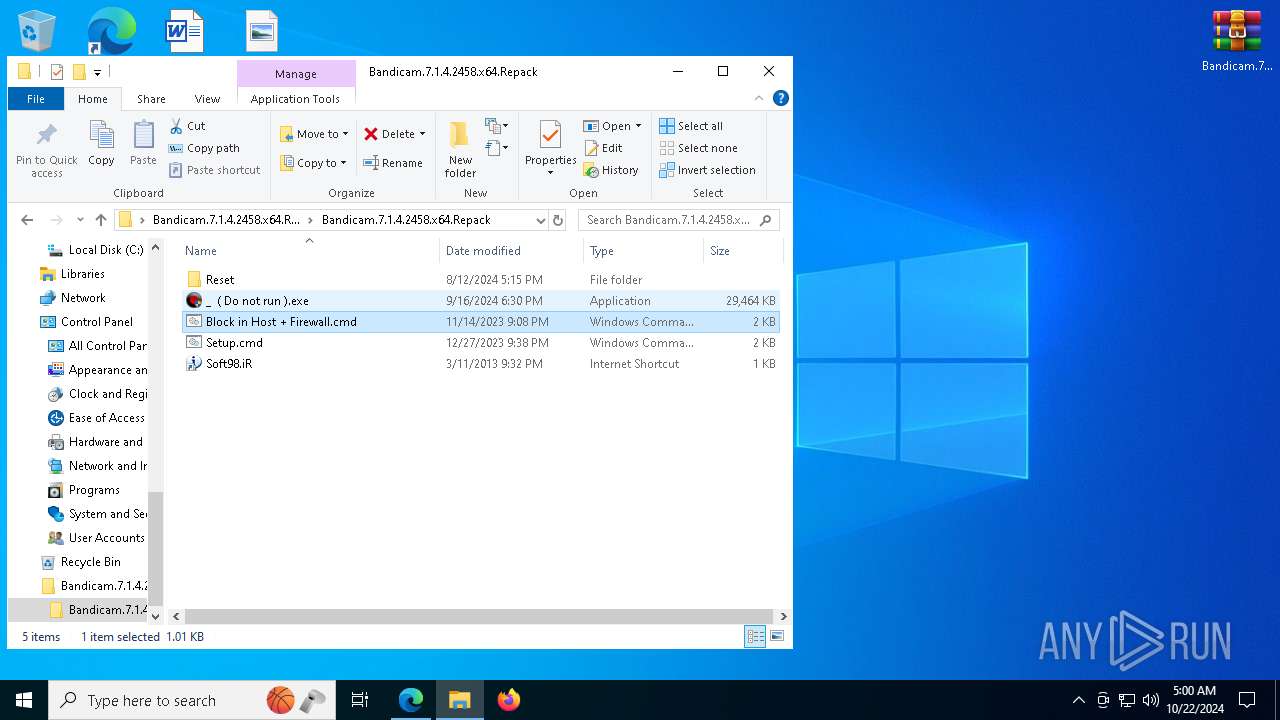
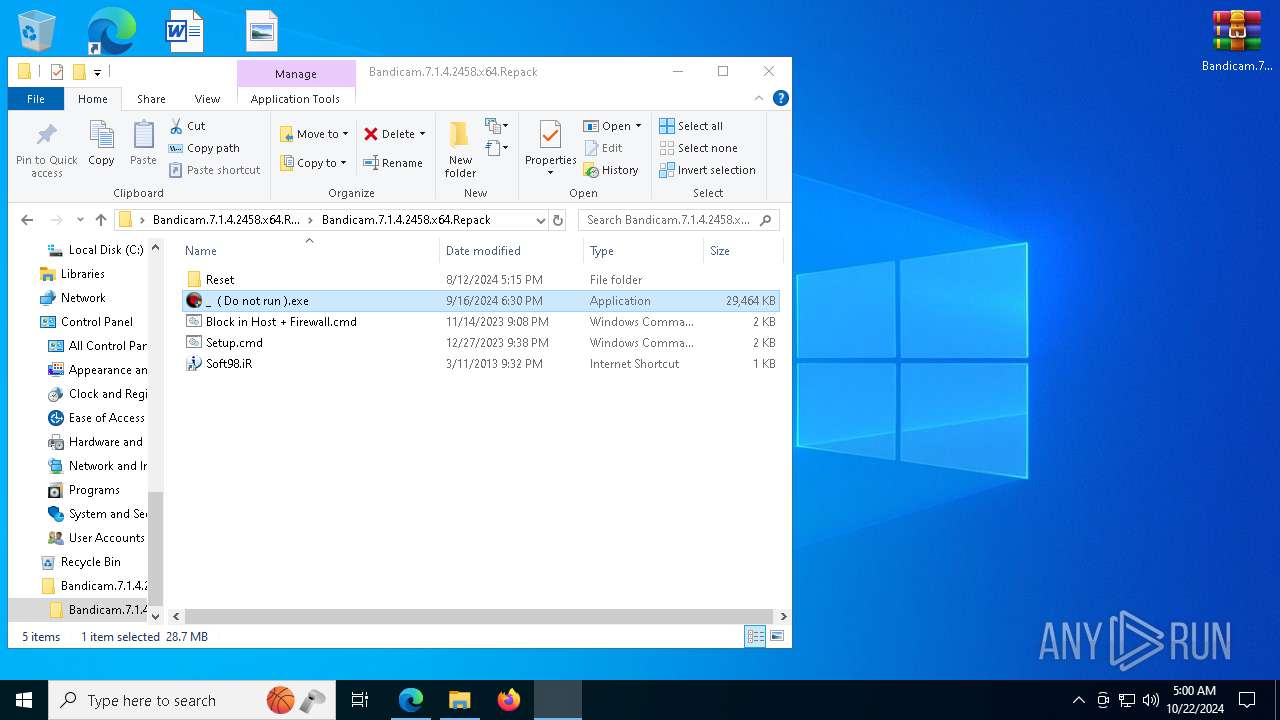
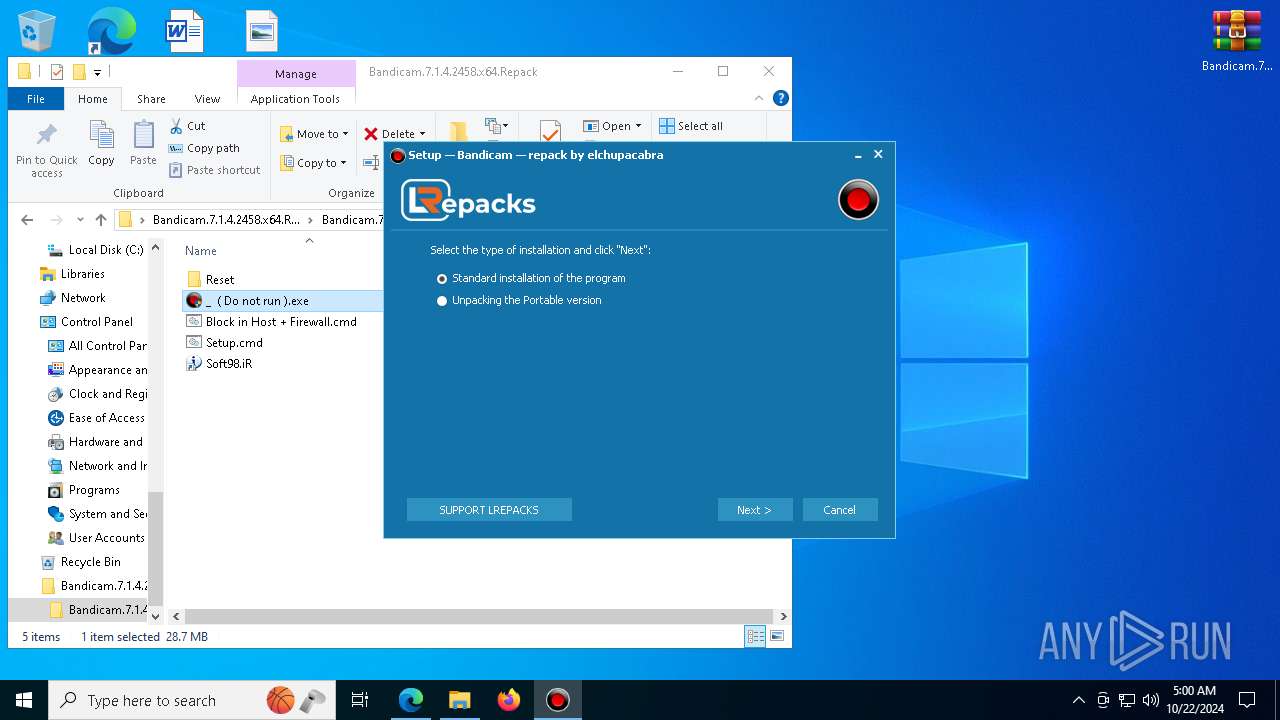
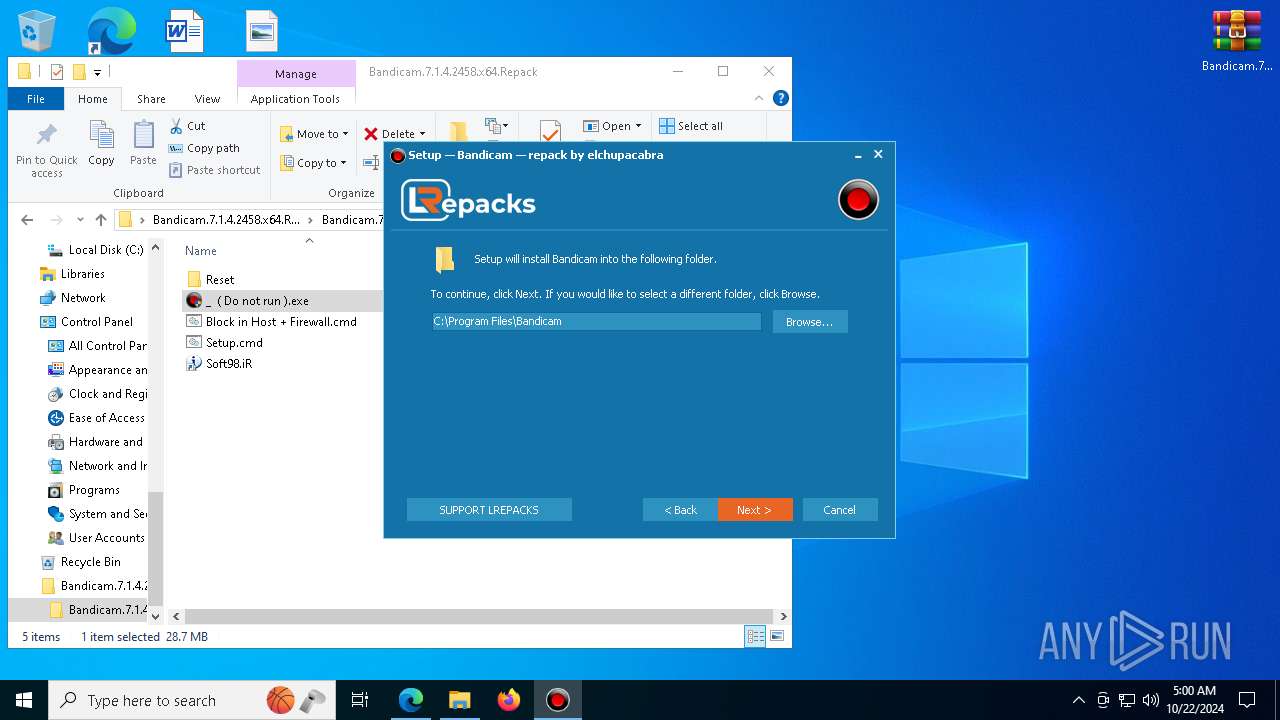
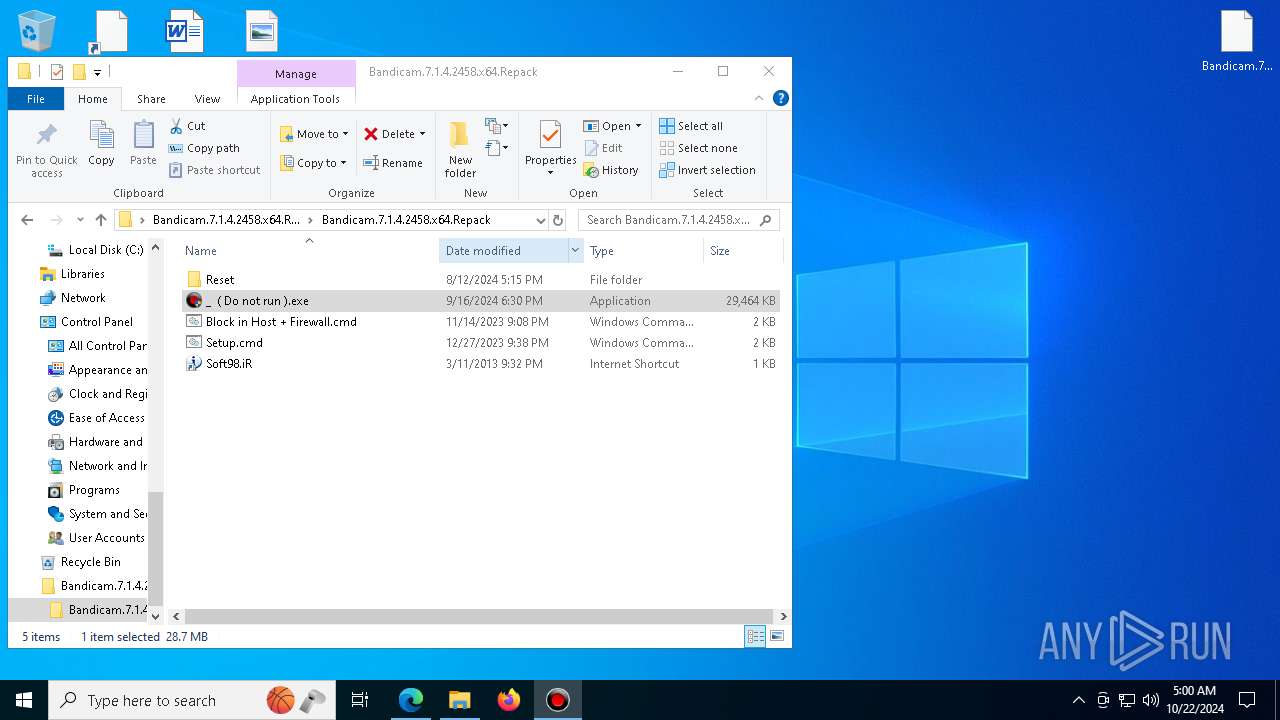
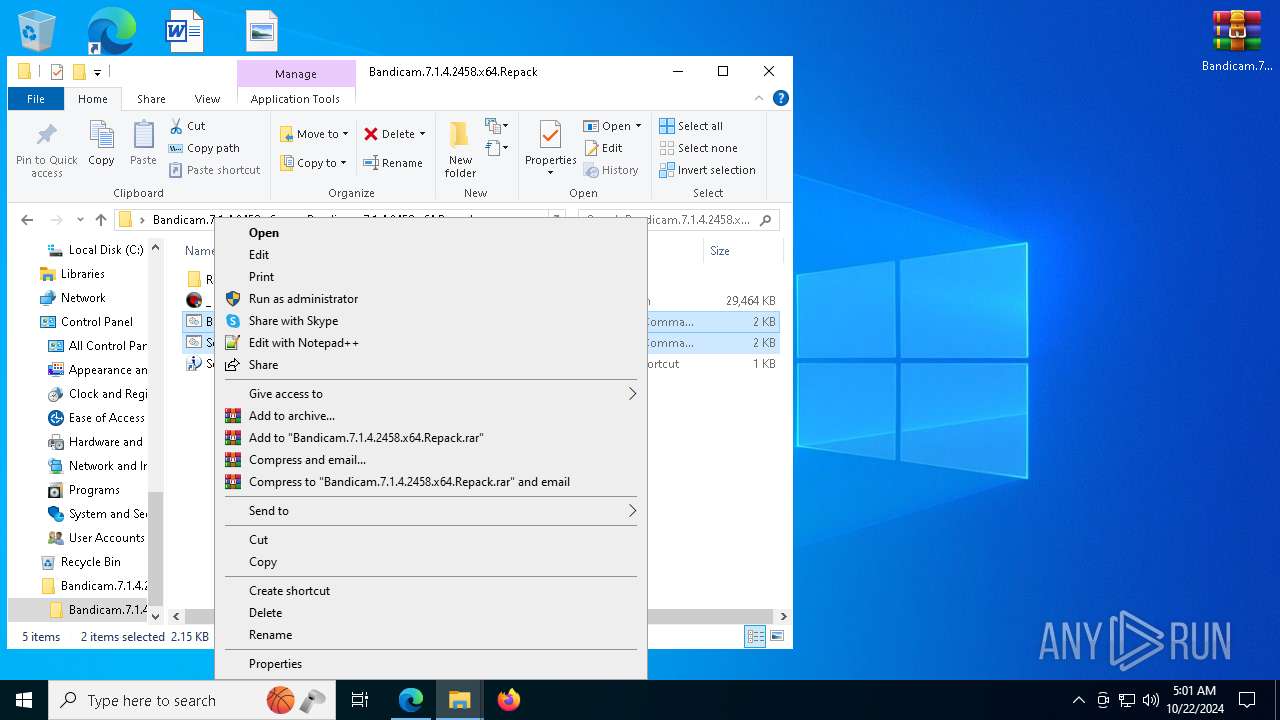
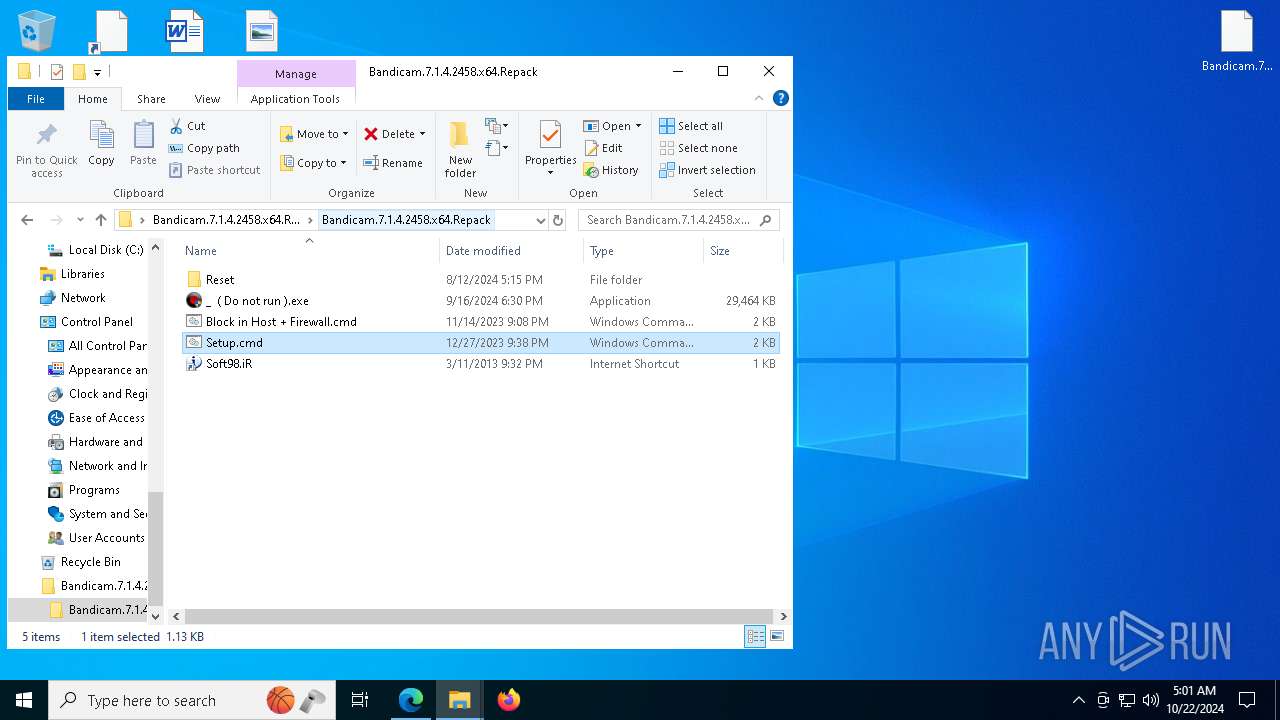
Manual execution by a user
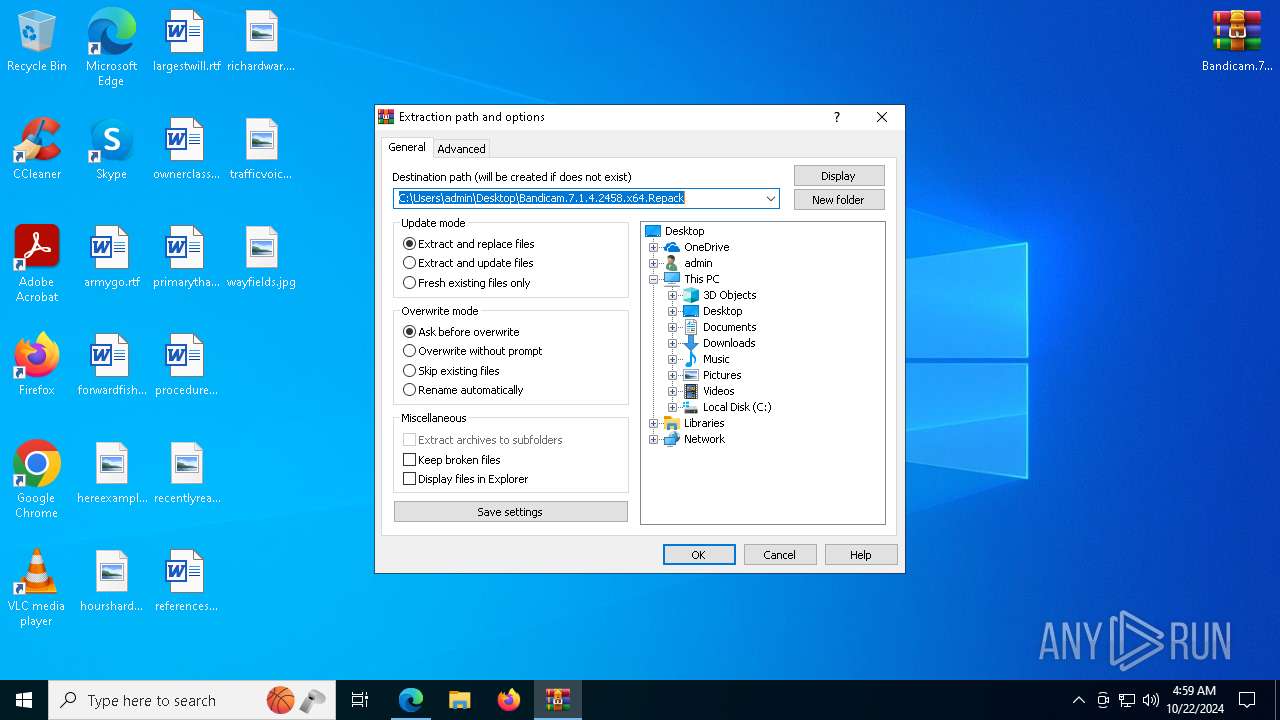
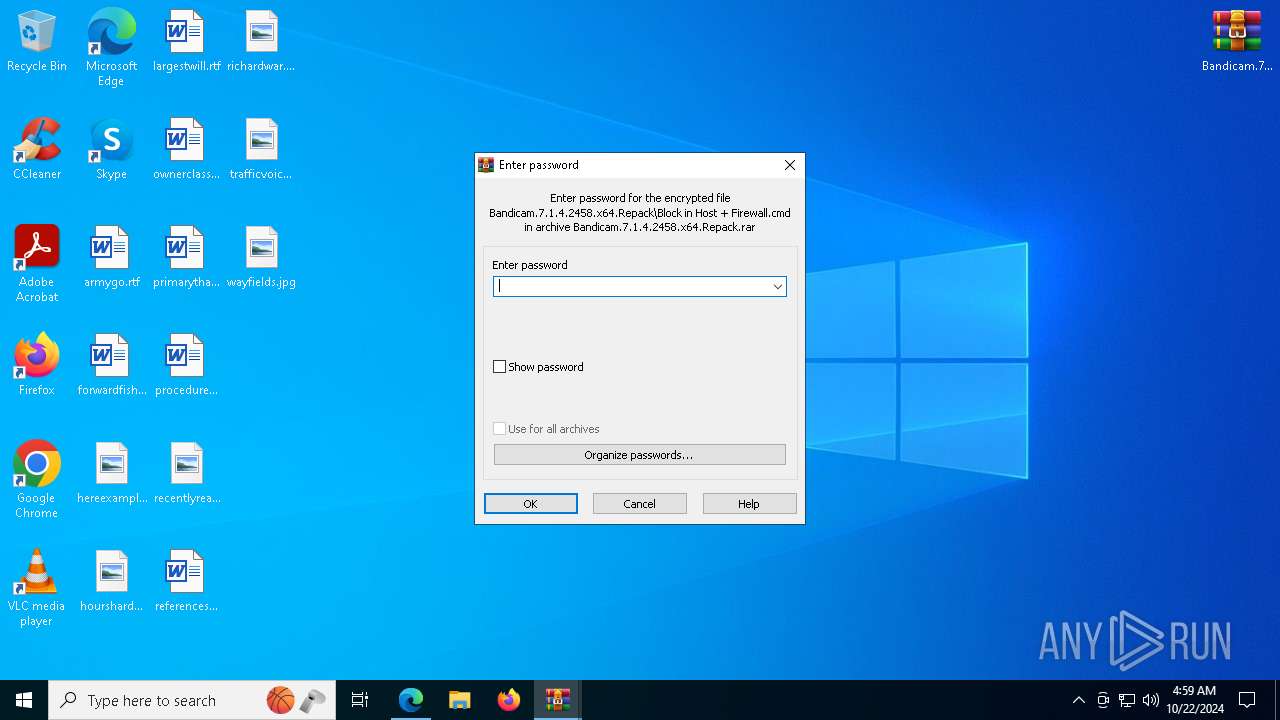
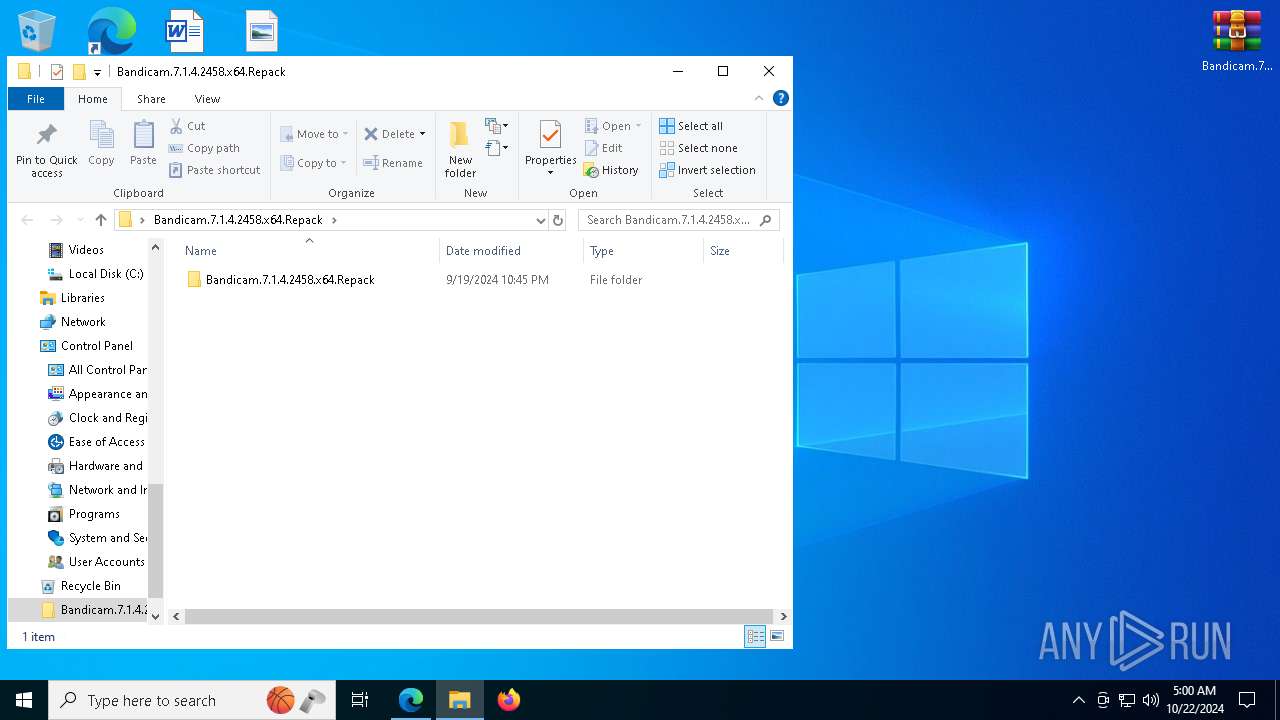
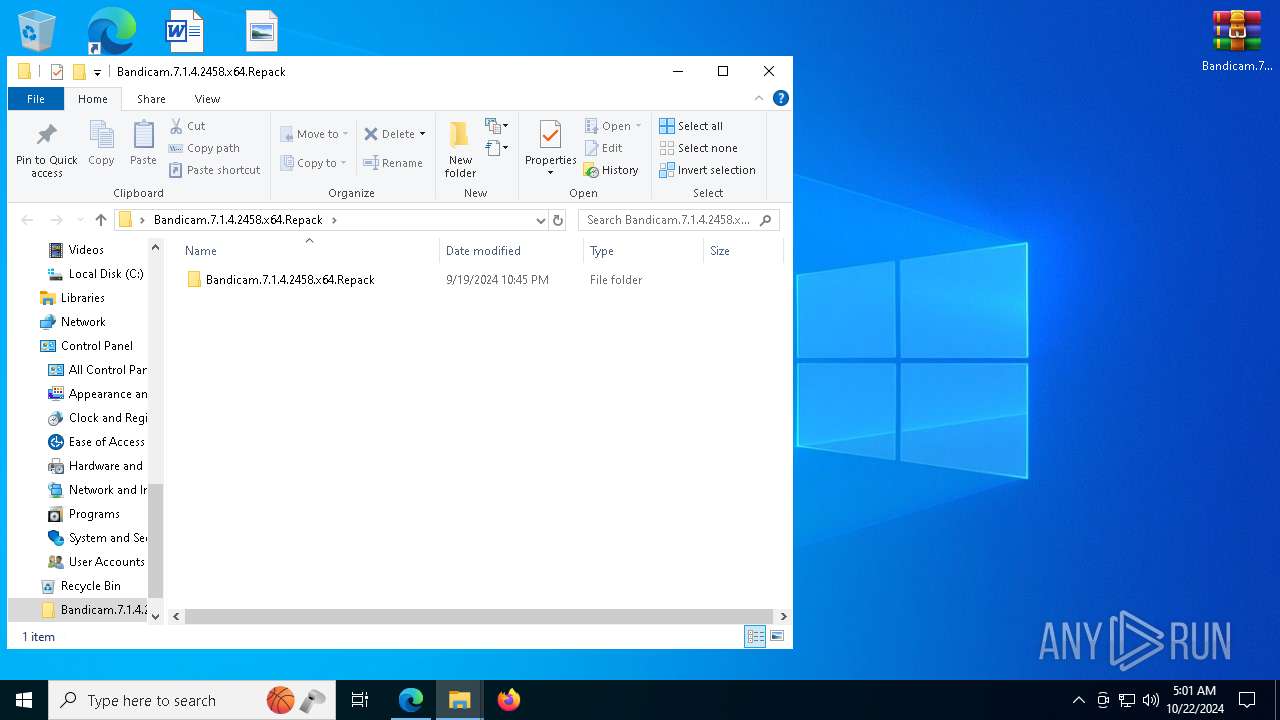
- WinRAR.exe (PID: 4432)
- cmd.exe (PID: 7048)
- cmd.exe (PID: 6512)
- _ ( Do not run ).exe (PID: 6696)
- _ ( Do not run ).exe (PID: 7500)
- bdcam.exe (PID: 6392)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 2588)
- cmd.exe (PID: 6460)
Starts MODE.COM to configure console settings
- mode.com (PID: 2808)
- mode.com (PID: 8060)
- mode.com (PID: 7504)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4432)
- msedge.exe (PID: 7564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
295
Monitored processes
149
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | attrib +r C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | cmd /u /c type "C:\Users\admin\AppData\Local\Temp\GetAdmin.vbs" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files\Bandicam\BandiMPEG1\bdfilters.dll" | C:\Windows\System32\regsvr32.exe | — | _ ( Do not run ).tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4272 --field-trial-handle=2380,i,18423988177148746401,3144020477948451108,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 944 | "C:\WINDOWS\system32\cmd.exe" /C "C:\Program Files\Bandicam\RegVulkanLayer.bat" | C:\Windows\System32\cmd.exe | — | _ ( Do not run ).tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1200 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\BANDIC~1.REP\BANDIC~1.REP\BLOCKI~1.CMD" | C:\Windows\System32\cmd.exe | cscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\WINDOWS\system32\rundll32.exe" "C:\Program Files\Bandicam\bdcamvk64.dll",RegDll | C:\Windows\System32\rundll32.exe | — | bdcam.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1580 | "C:\Users\admin\Desktop\Bandicam.7.1.4.2458.x64.Repack\Bandicam.7.1.4.2458.x64.Repack\_ ( Do not run ).exe" /VerySILENT /TASKS="activate,desktopicon" | C:\Users\admin\Desktop\Bandicam.7.1.4.2458.x64.Repack\Bandicam.7.1.4.2458.x64.Repack\_ ( Do not run ).exe | cmd.exe | ||||||||||||
User: admin Company: LR Integrity Level: HIGH Description: Bandicam Setup Exit code: 0 Version: 7.1.4.2458.0 Modules
| |||||||||||||||
| 1584 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 376
Read events
10 253
Write events
110
Delete events
13
Modification events
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 96B40CE99F832F00 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 54EB17E99F832F00 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459280 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9942ACEF-E043-4193-9861-013BE7637C75} | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459280 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {82479D4F-372A-4FB2-AF52-5D8DBE21AA8F} | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459280 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {02123C95-2BC5-4372-B528-EE2A5AD29CC4} | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459280 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F55D92B7-C078-49AF-91DE-2B34DA5EAC68} | |||
Executable files
170
Suspicious files
537
Text files
226
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8b908.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8b908.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8b908.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8b908.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8b908.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
149
DNS requests
105
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4304 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4304 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7112 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/181d62d0-8e71-4ab0-b6f0-62f746749689?P1=1729777944&P2=404&P3=2&P4=BP1MyGG2f9IES8Sp9DKsNSKd9Kb7DAb7HLWdS9QOEKxPfGdacBPxbyHRlJ3%2brhJJmoPbB5pc7ZHOLCmgnhuDww%3d%3d | unknown | — | — | whitelisted |
7112 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/181d62d0-8e71-4ab0-b6f0-62f746749689?P1=1729777944&P2=404&P3=2&P4=BP1MyGG2f9IES8Sp9DKsNSKd9Kb7DAb7HLWdS9QOEKxPfGdacBPxbyHRlJ3%2brhJJmoPbB5pc7ZHOLCmgnhuDww%3d%3d | unknown | — | — | whitelisted |
7112 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/181d62d0-8e71-4ab0-b6f0-62f746749689?P1=1729777944&P2=404&P3=2&P4=BP1MyGG2f9IES8Sp9DKsNSKd9Kb7DAb7HLWdS9QOEKxPfGdacBPxbyHRlJ3%2brhJJmoPbB5pc7ZHOLCmgnhuDww%3d%3d | unknown | — | — | whitelisted |
7112 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/181d62d0-8e71-4ab0-b6f0-62f746749689?P1=1729777944&P2=404&P3=2&P4=BP1MyGG2f9IES8Sp9DKsNSKd9Kb7DAb7HLWdS9QOEKxPfGdacBPxbyHRlJ3%2brhJJmoPbB5pc7ZHOLCmgnhuDww%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4360 | SearchApp.exe | 104.126.37.154:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6272 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
soft98.ir |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
regedit.exe | REGEDIT: CreateFile failed, GetLastError() = 2
|