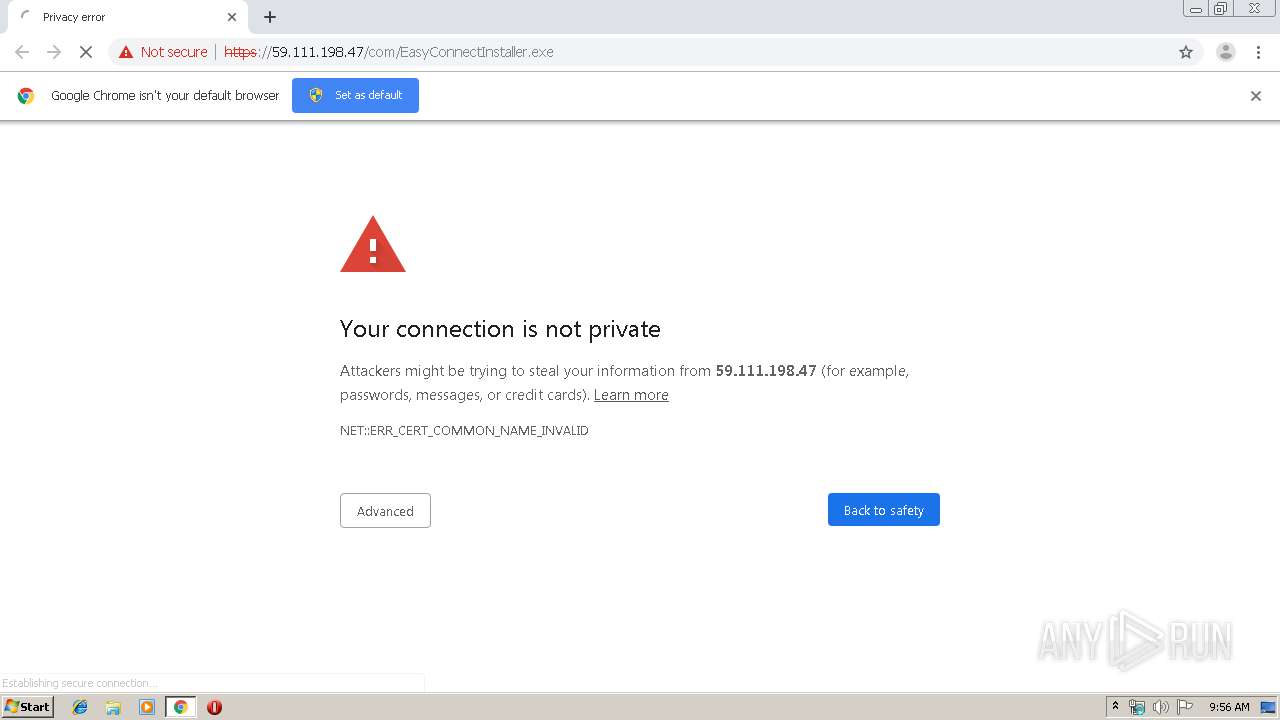
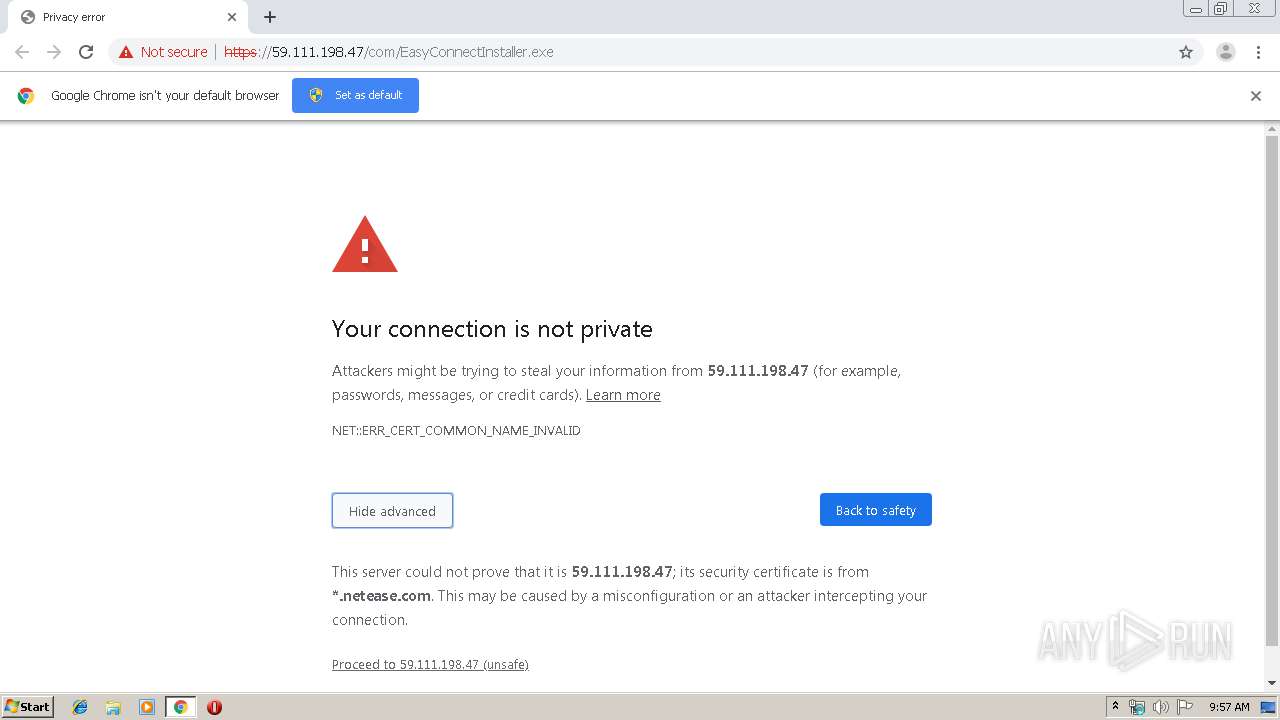
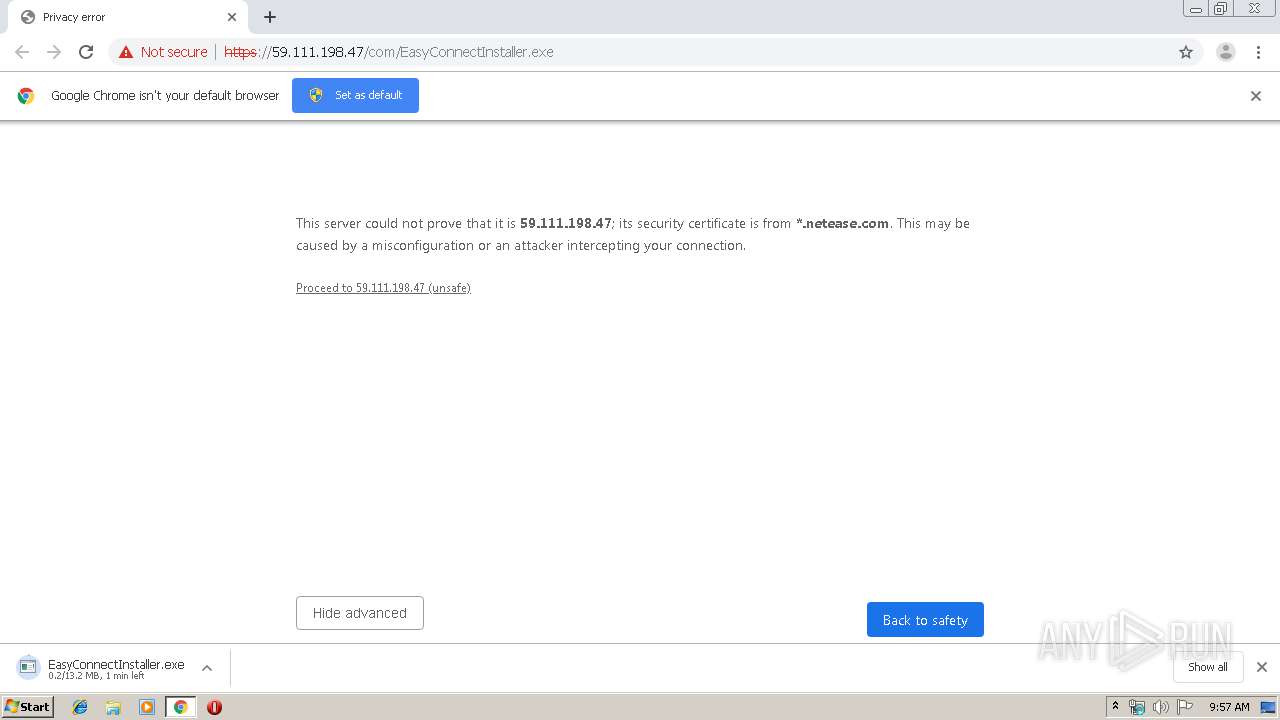
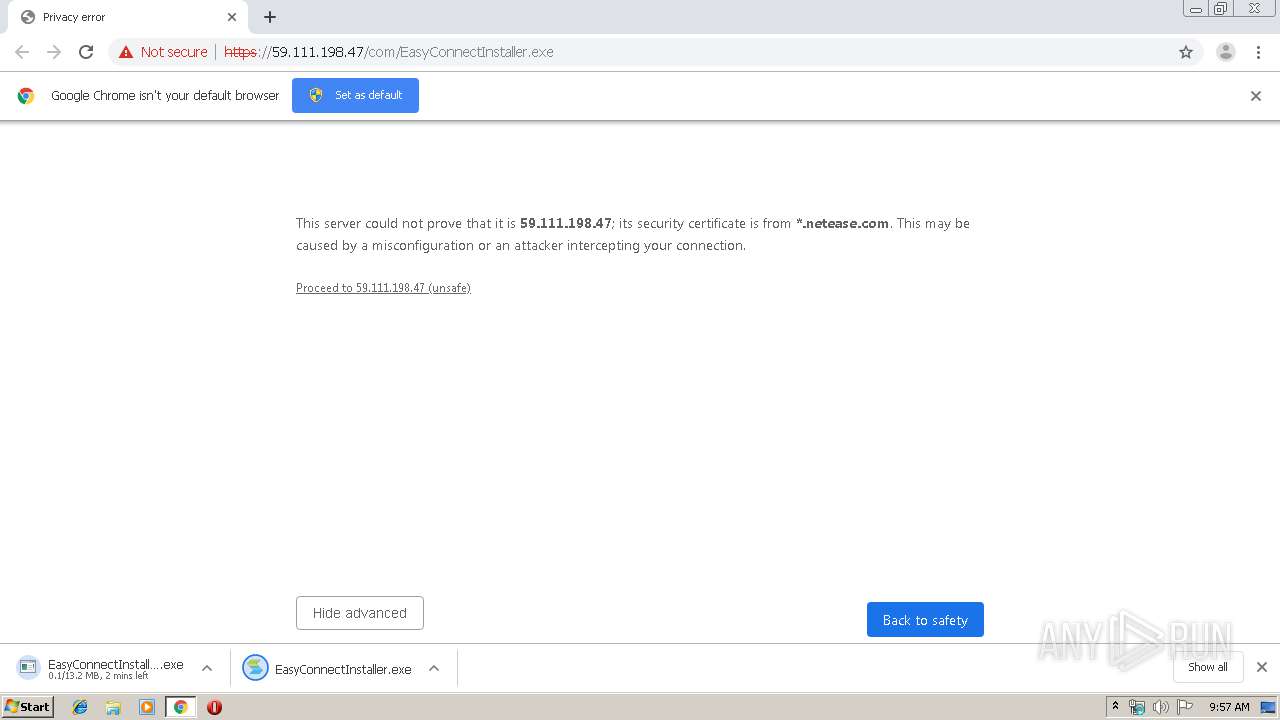
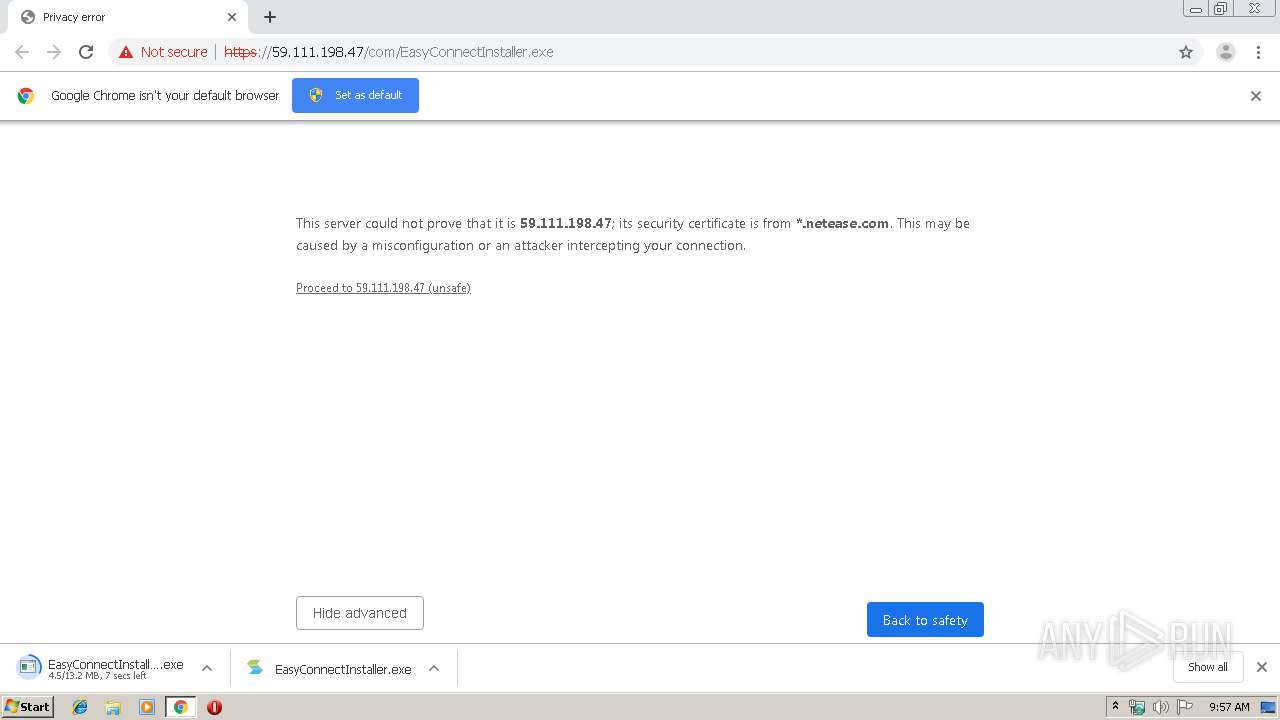
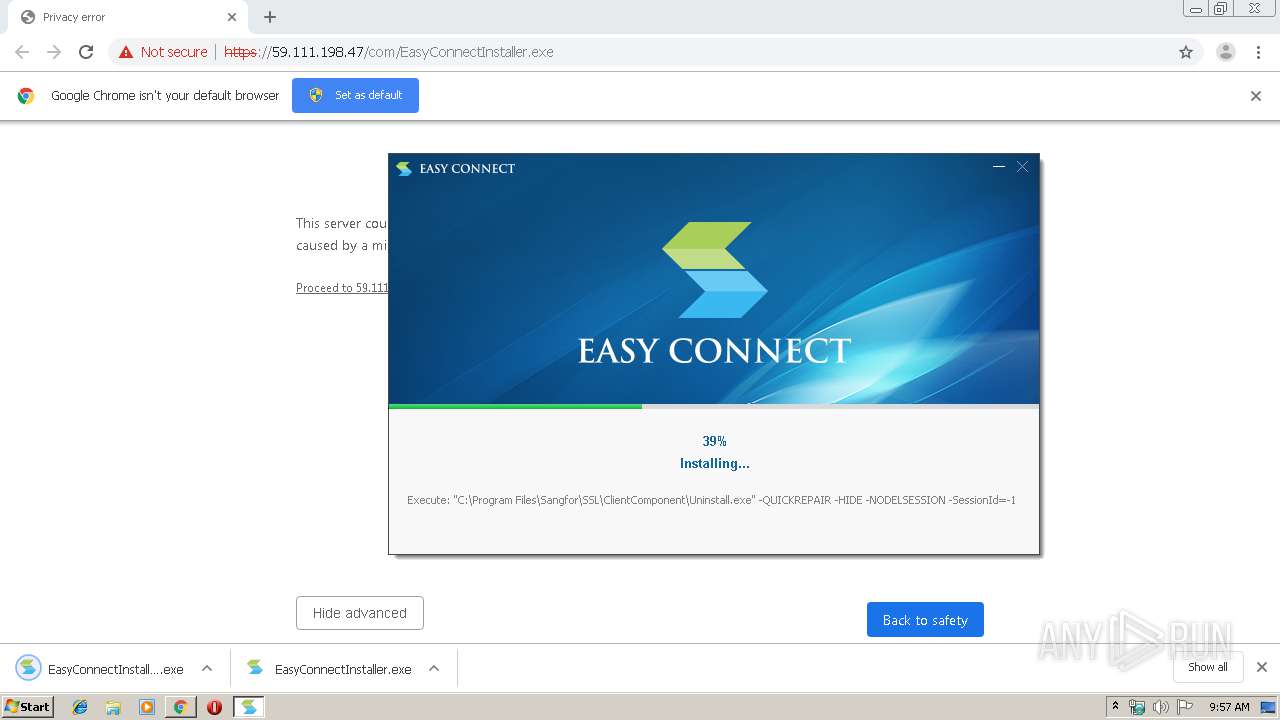
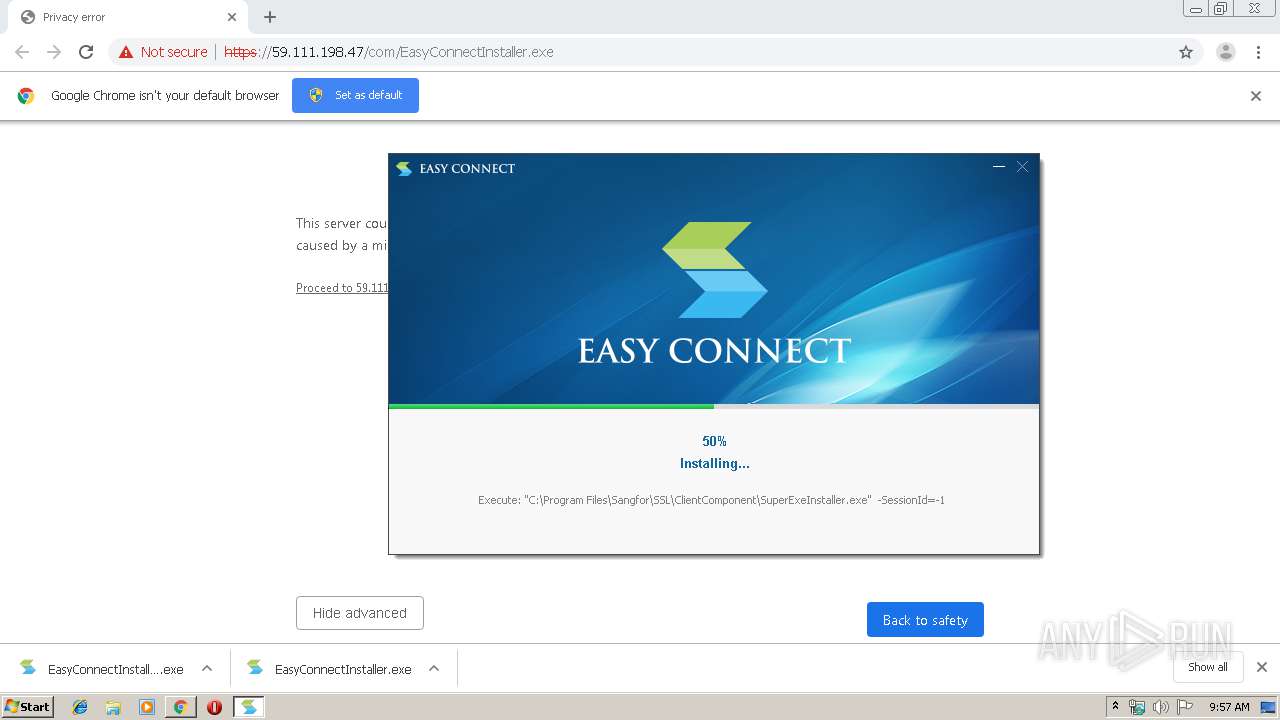
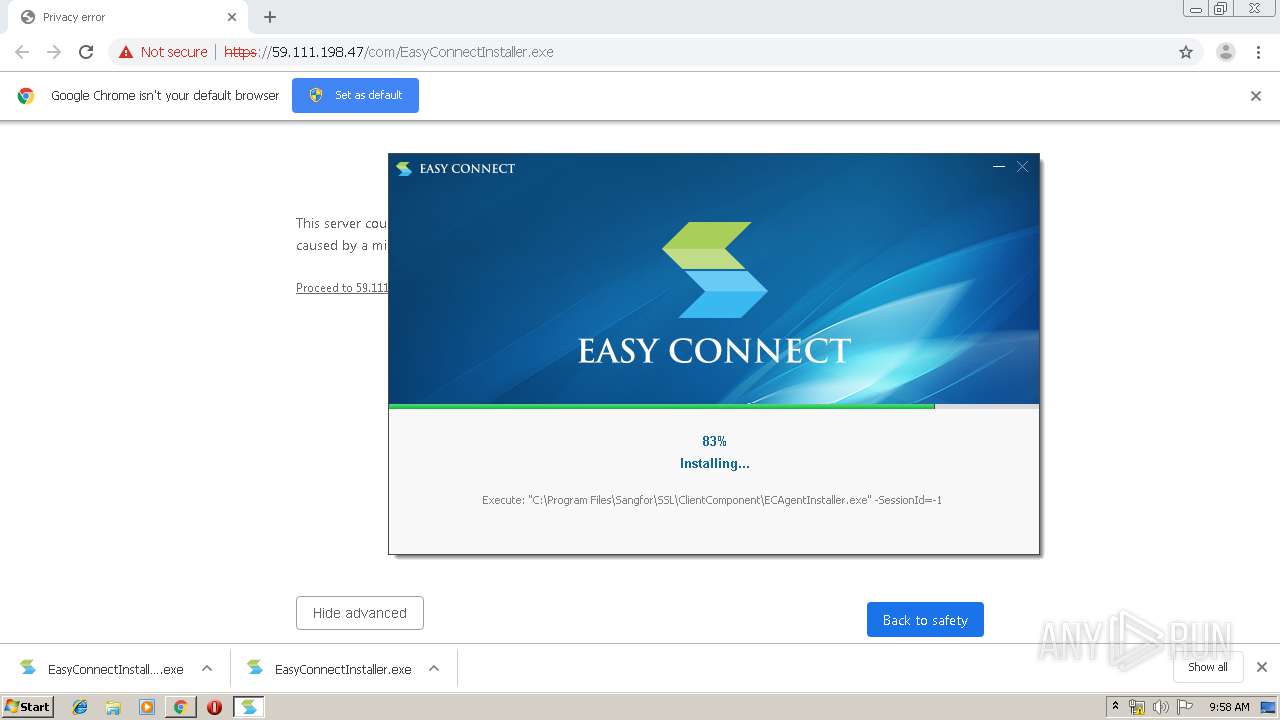
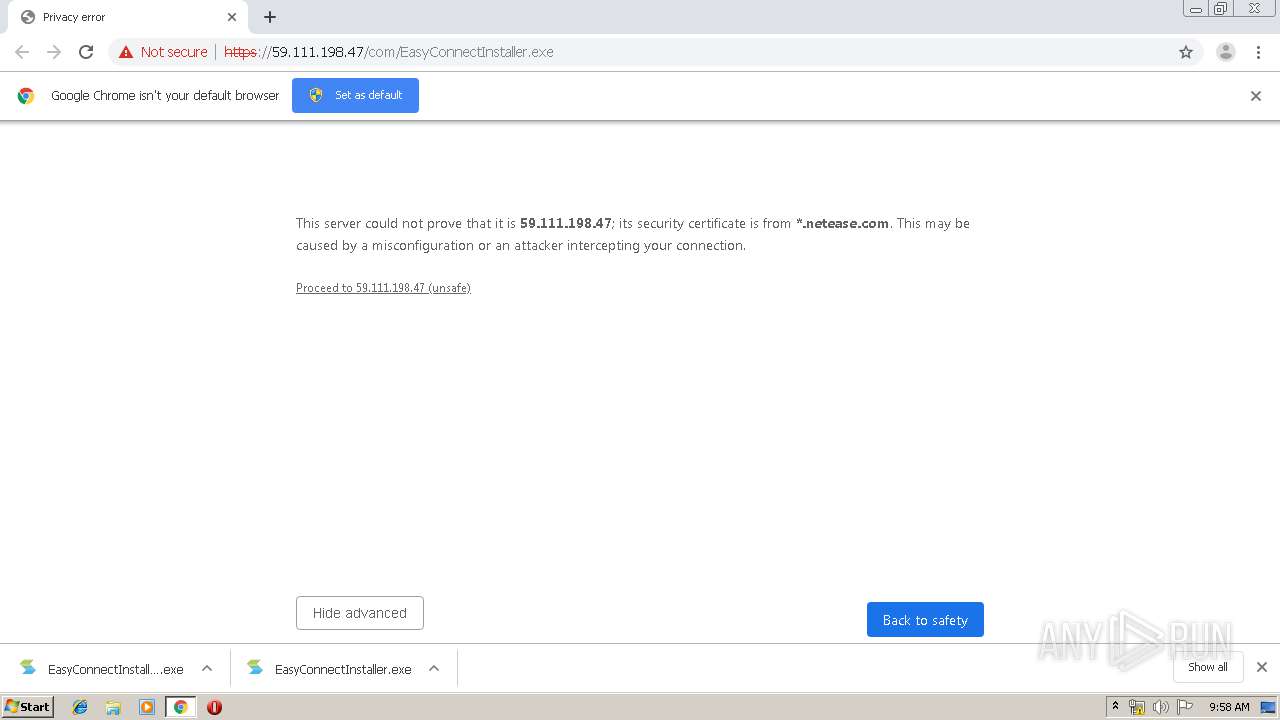
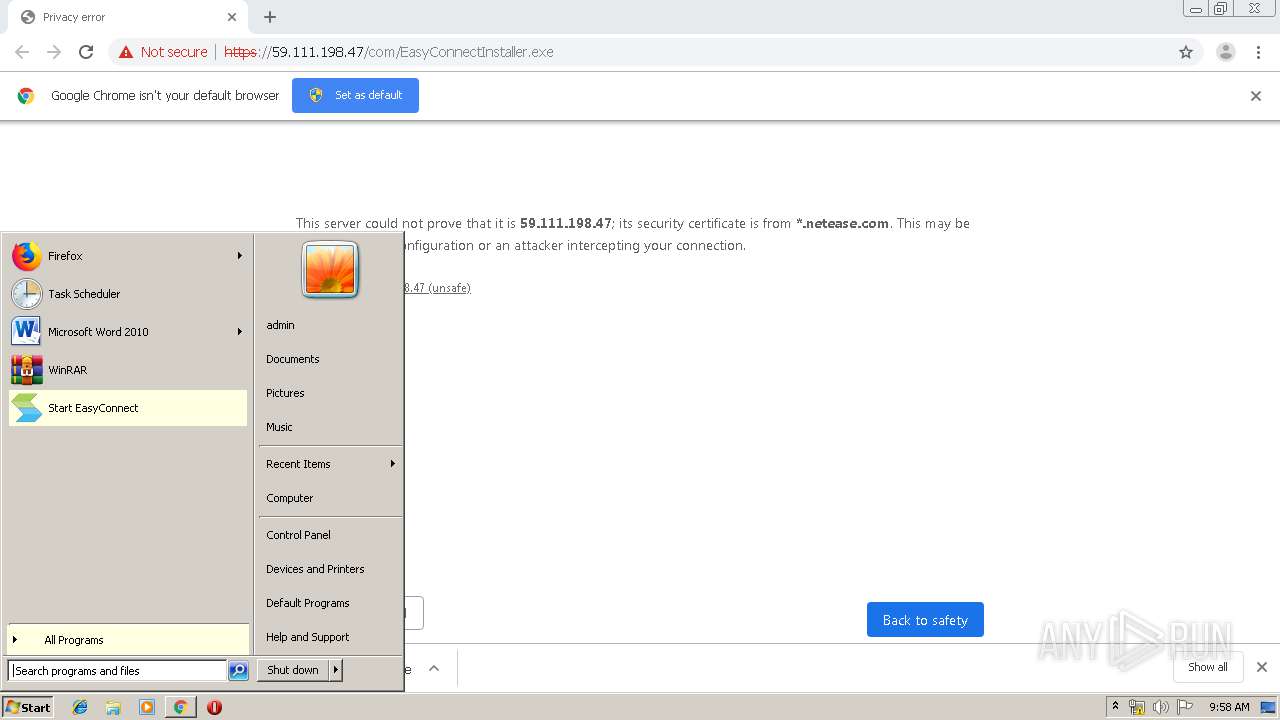
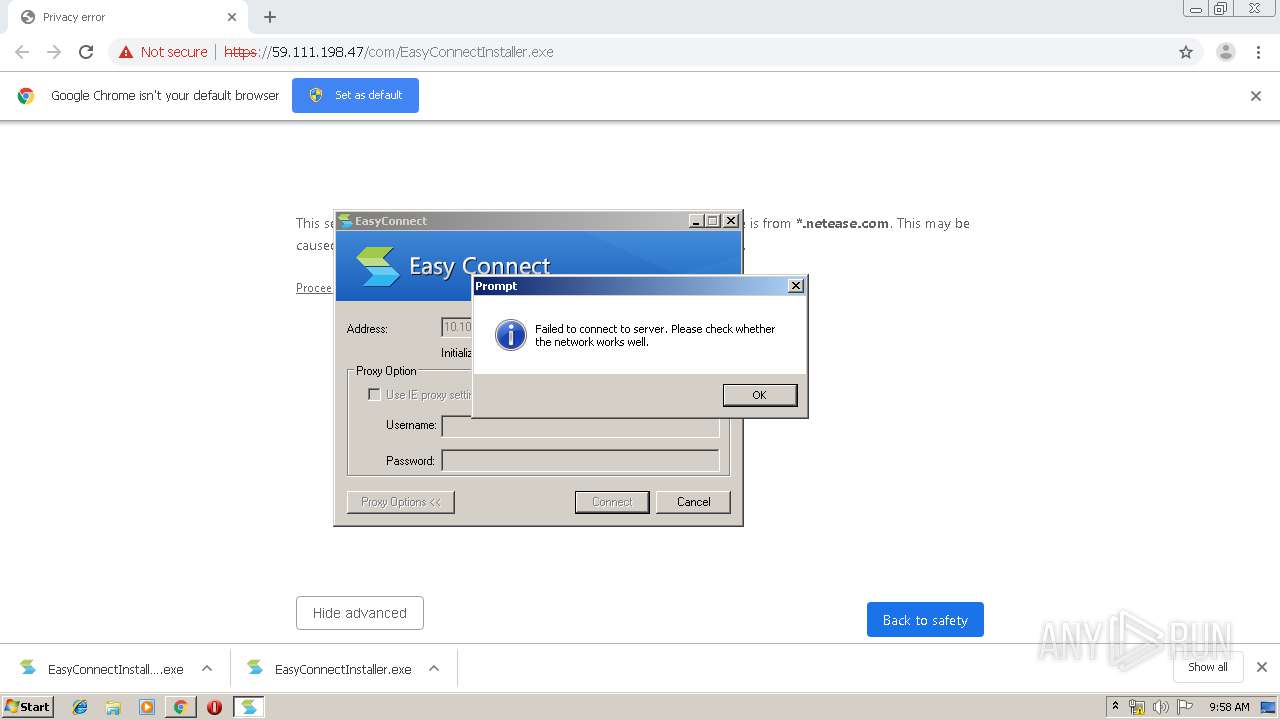
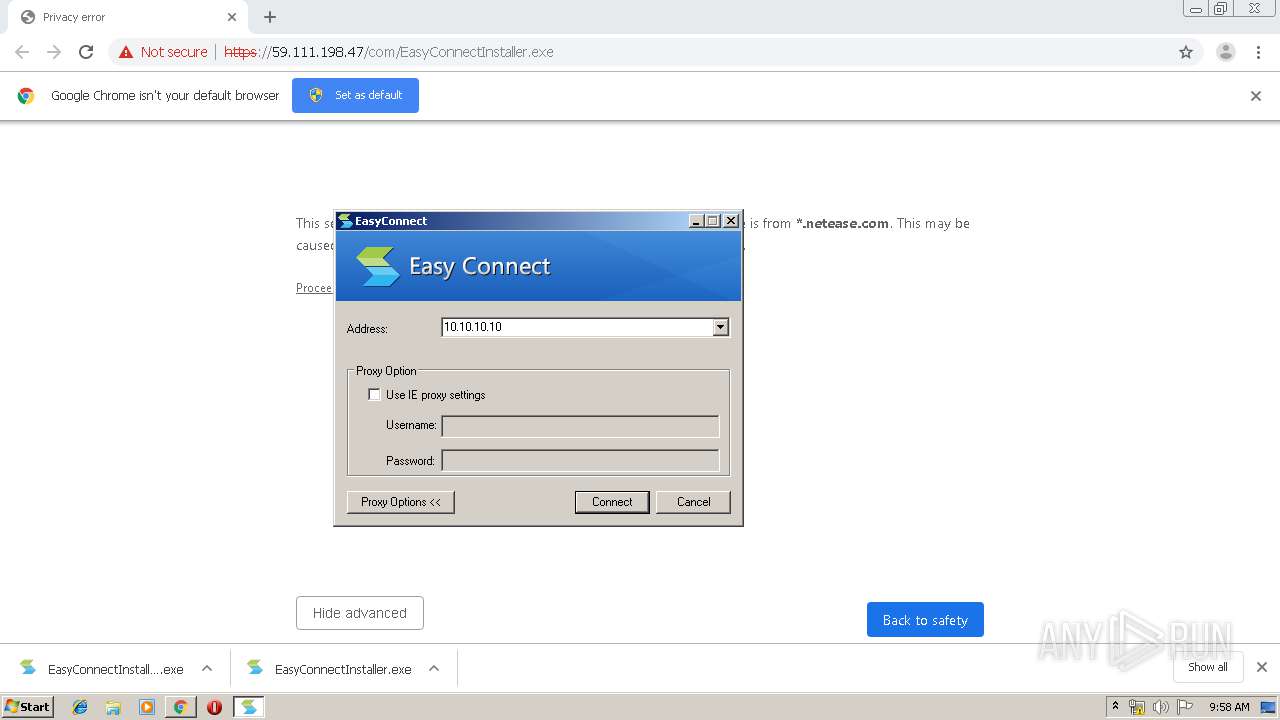
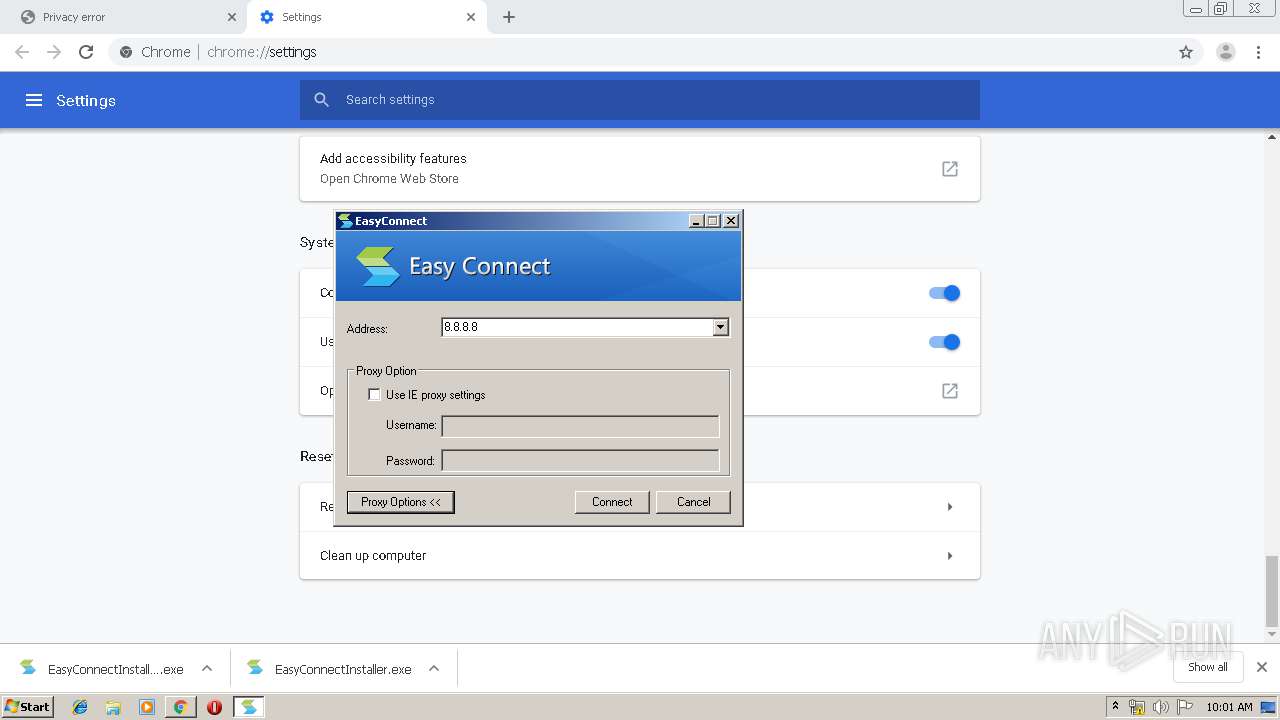
| URL: | https://59.111.198.47/com/EasyConnectInstaller.exe |
| Full analysis: | https://app.any.run/tasks/6a908859-4167-4e32-a737-0b6b1033ec39 |
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2020, 09:56:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DF2E5D5053DF630DE4465804709F3441 |
| SHA1: | 23FDB6F32245E77A3ECCA6B637D789DDDD2431BC |
| SHA256: | 75E1A6692D8C527E018860608E8F70695CDBFA05D18D53110CB2CFC52735D3ED |
| SSDEEP: | 3:N8jgNLFJzGTwmfGRjEgXLNn:2kNL3KrGNEgXLN |
MALICIOUS
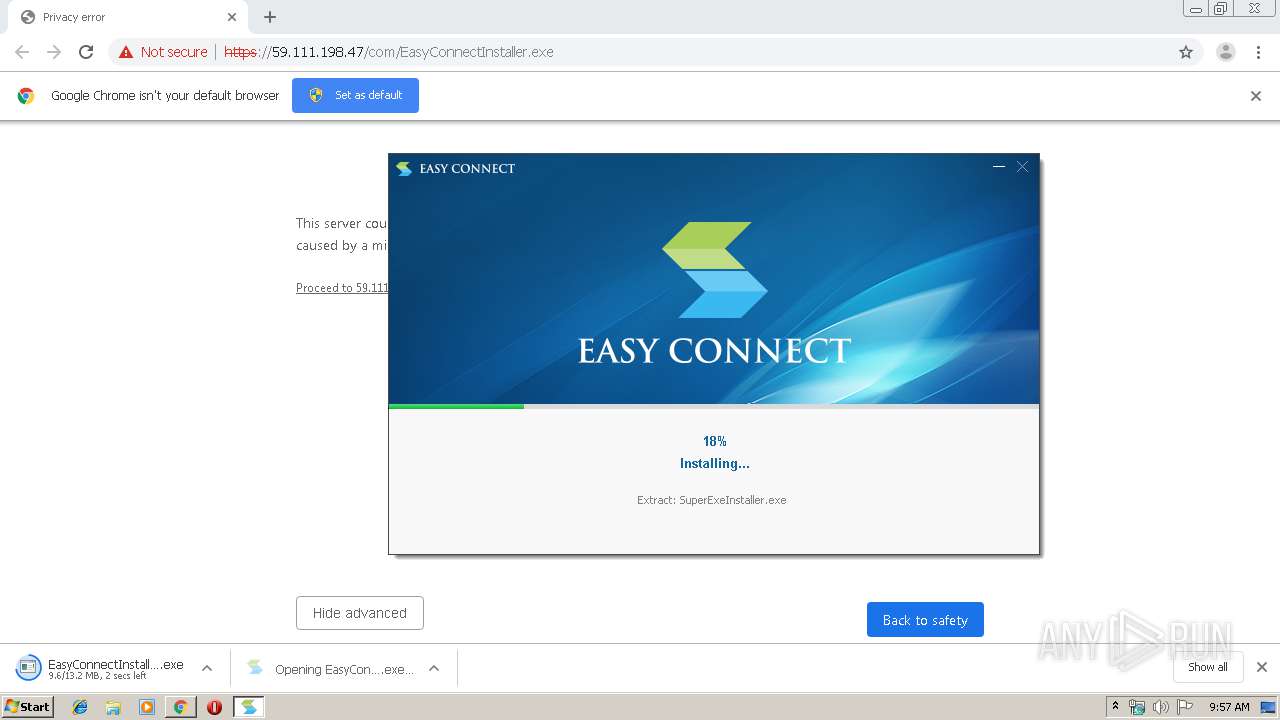
Application was dropped or rewritten from another process
- EasyConnectInstaller.exe (PID: 3412)
- EasyConnectInstaller.exe (PID: 3084)
- Uninstall.exe (PID: 3868)
- SangforCSClientInstaller.exe (PID: 2832)
- TcpDriverInstaller.exe (PID: 3400)
- Remove.exe (PID: 3084)
- DnsDriverInstaller.exe (PID: 928)
- Install.exe (PID: 1740)
- SuperExeInstaller.exe (PID: 496)
- Install.exe (PID: 504)
- Remove.exe (PID: 1488)
- SangforServiceClientInstaller.exe (PID: 1740)
- VC2010RedistX86UInstaller.exe (PID: 4044)
- SJobberInstaller.exe (PID: 3848)
- SangforUpdateInstaller.exe (PID: 3968)
- InstallControl.exe (PID: 776)
- SangforRAppInstaller.exe (PID: 1248)
- VNICInstaller.exe (PID: 3860)
- ndiscleanup.x86.exe (PID: 3976)
- ns50C8.tmp (PID: 1852)
- ns5240.tmp (PID: 1244)
- ns9A27.tmp (PID: 1024)
- SetIPTime.exe (PID: 1780)
- ECBaseInstaller.exe (PID: 2212)
- vacon.exe (PID: 3752)
- SuperServiceInstaller.exe (PID: 2848)
- ECAgent.exe (PID: 3896)
- ECAgentInstaller.exe (PID: 3244)
- ECAgent.exe (PID: 2668)
- ECAgent.exe (PID: 3324)
- SangforPromoteService.exe (PID: 1732)
- SangforPromoteService.exe (PID: 516)
- SangforPromoteService.exe (PID: 2692)
- ECAgent.exe (PID: 600)
- ECAgent.exe (PID: 816)
- ECAgent.exe (PID: 532)
- ECAgent.exe (PID: 1756)
- SangforCSClient.exe (PID: 3748)
- SangforPromote.exe (PID: 1772)
- ECAgent.exe (PID: 3584)
- ECAgent.exe (PID: 2944)
Loads dropped or rewritten executable
- EasyConnectInstaller.exe (PID: 3412)
- SangforCSClientInstaller.exe (PID: 2832)
- TcpDriverInstaller.exe (PID: 3400)
- DnsDriverInstaller.exe (PID: 928)
- SuperExeInstaller.exe (PID: 496)
- SangforServiceClientInstaller.exe (PID: 1740)
- InstallControl.exe (PID: 776)
- VNICInstaller.exe (PID: 3860)
- svchost.exe (PID: 1232)
- chrome.exe (PID: 2180)
- svchost.exe (PID: 864)
- svchost.exe (PID: 1000)
- ECBaseInstaller.exe (PID: 2212)
- ECAgent.exe (PID: 3896)
- ECAgent.exe (PID: 2668)
- chrome.exe (PID: 2064)
- ECAgent.exe (PID: 3324)
- SangforPromoteService.exe (PID: 2692)
- ECAgent.exe (PID: 816)
- ECAgent.exe (PID: 600)
- ECAgent.exe (PID: 532)
- ECAgent.exe (PID: 1756)
- SangforCSClient.exe (PID: 3748)
- SangforPromote.exe (PID: 1772)
- ECAgent.exe (PID: 3584)
- ECAgent.exe (PID: 2944)
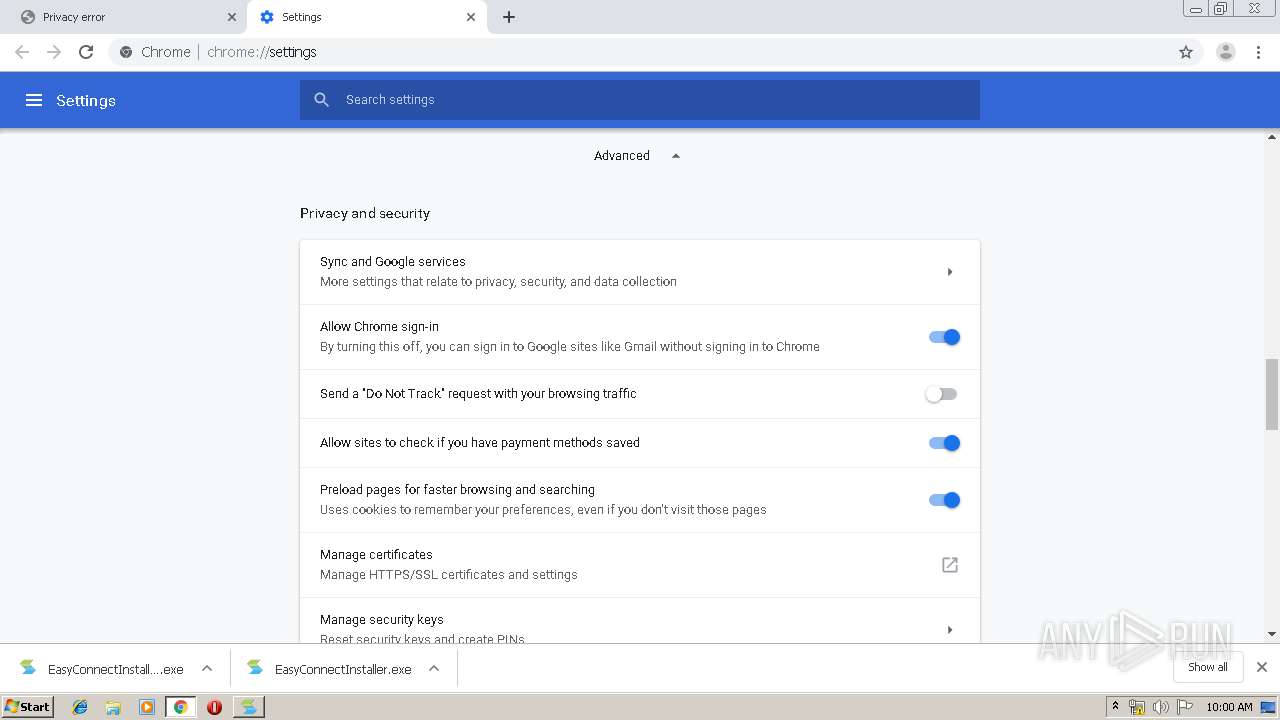
Changes settings of System certificates
- vacon.exe (PID: 3752)
- ECAgent.exe (PID: 3324)
- ECAgent.exe (PID: 816)
- ECAgent.exe (PID: 1756)
- SangforPromoteService.exe (PID: 2692)
- ECAgent.exe (PID: 2944)
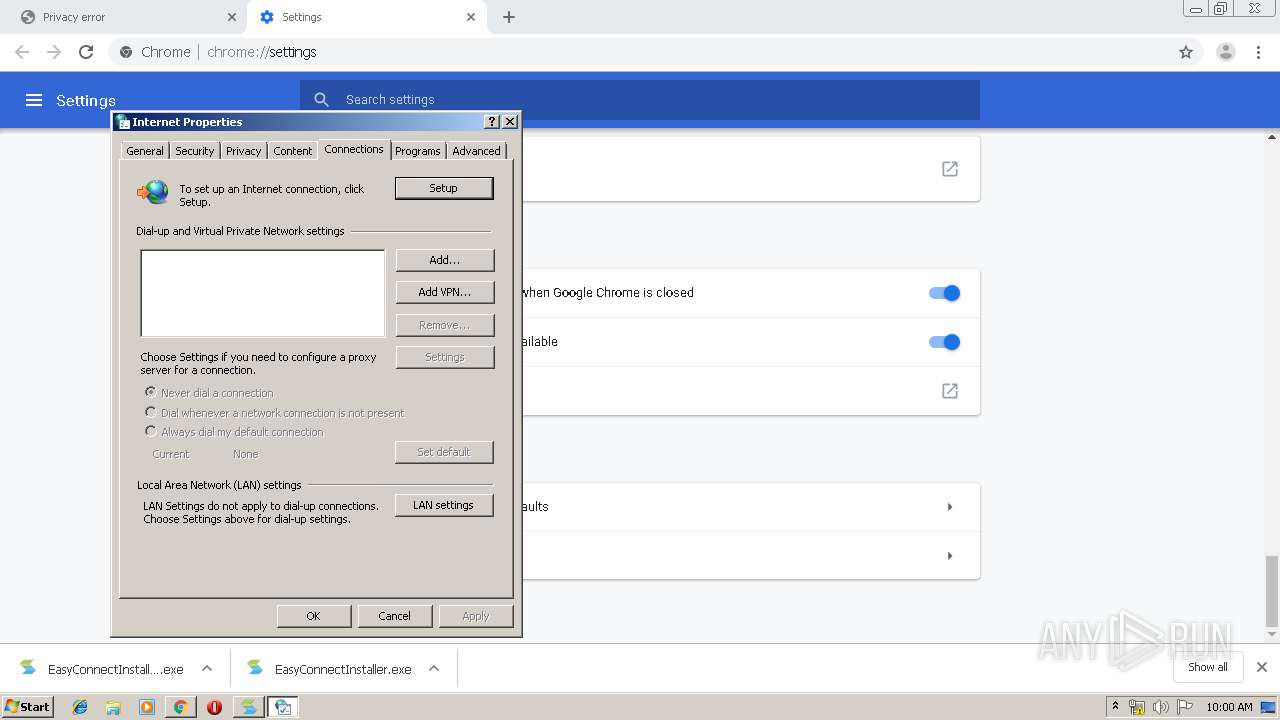
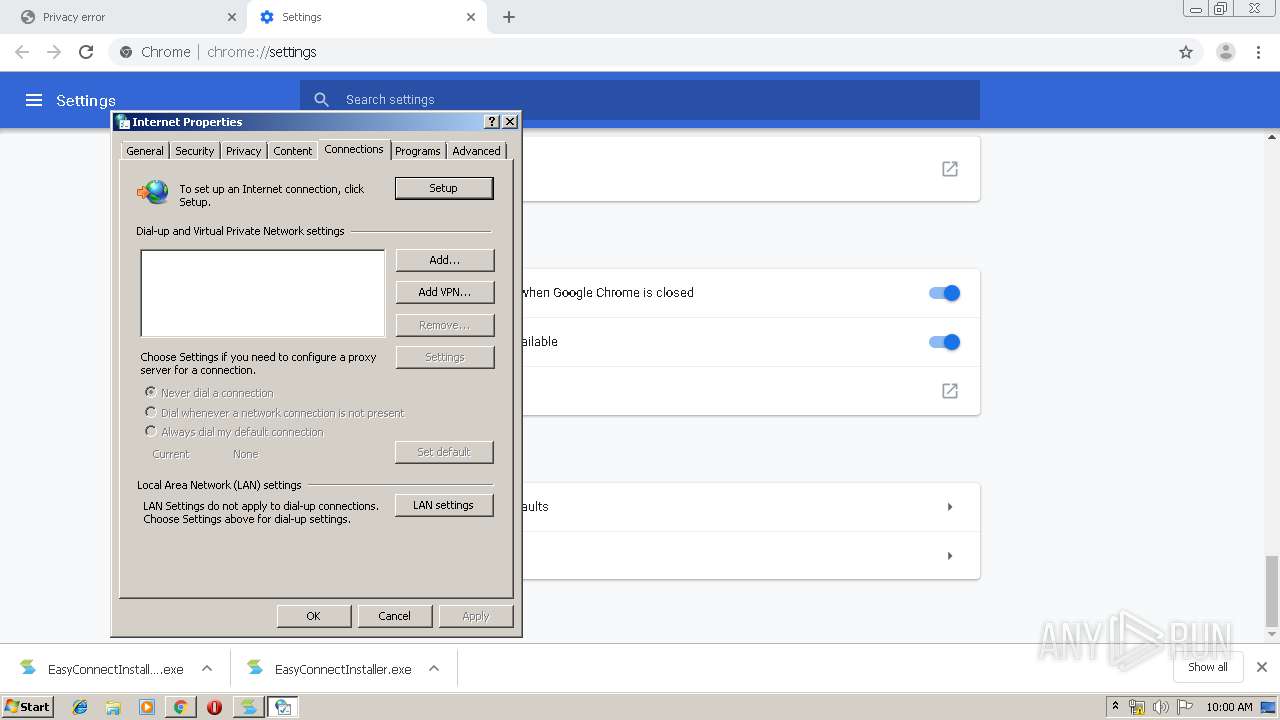
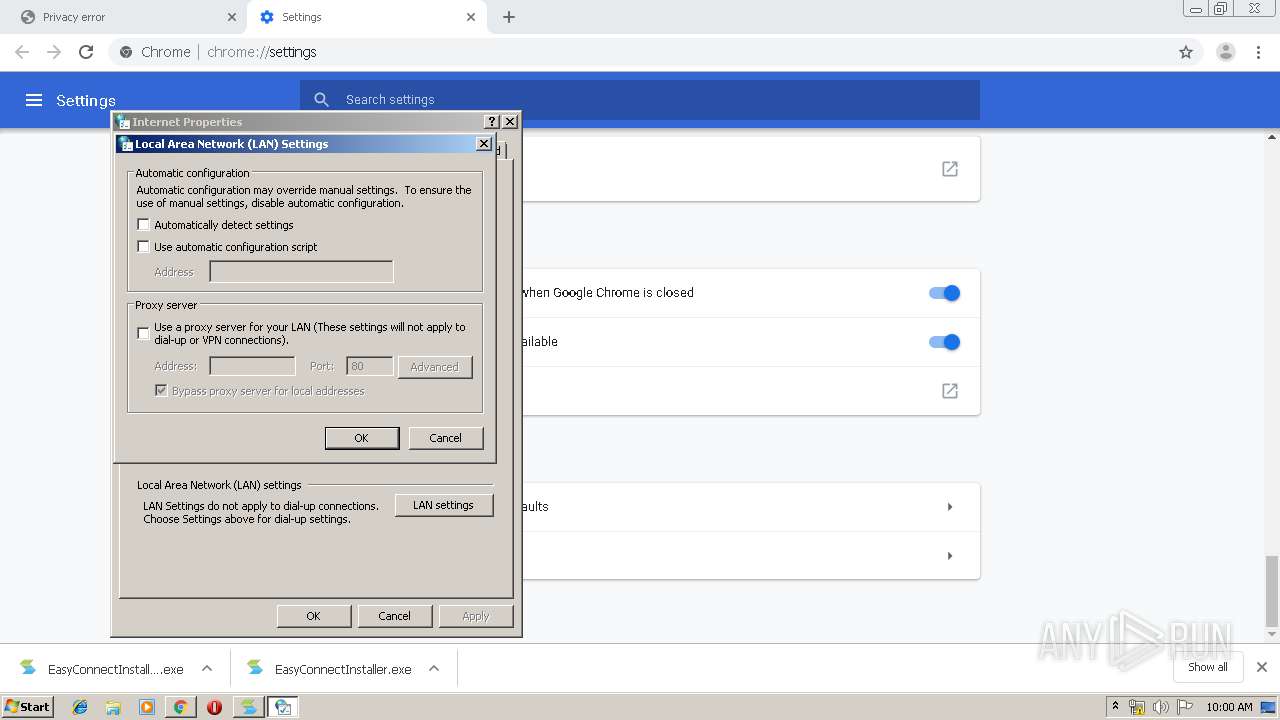
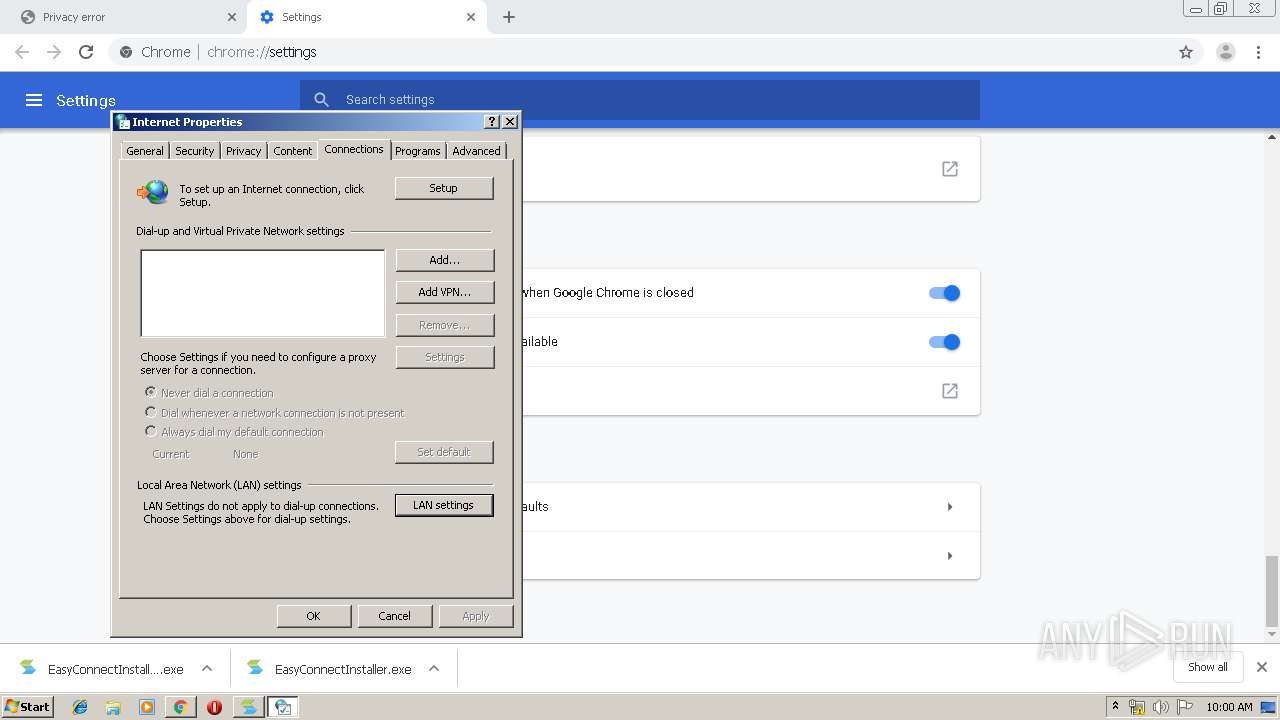
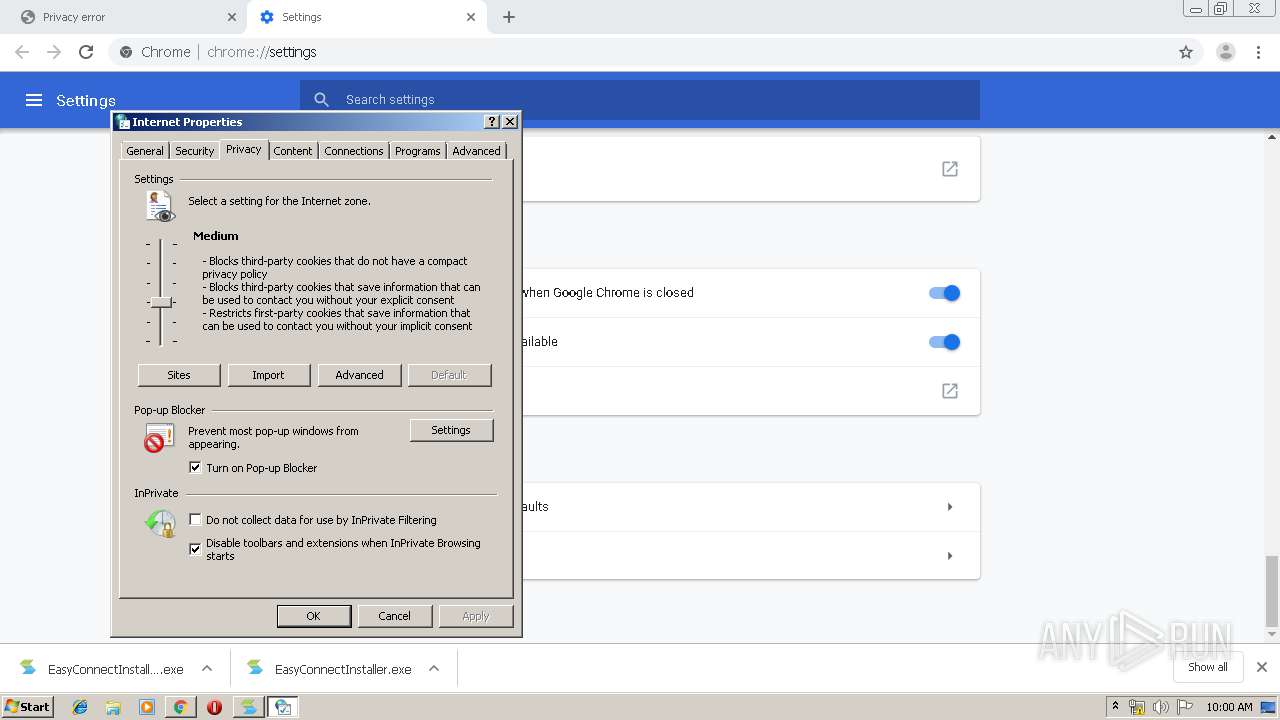
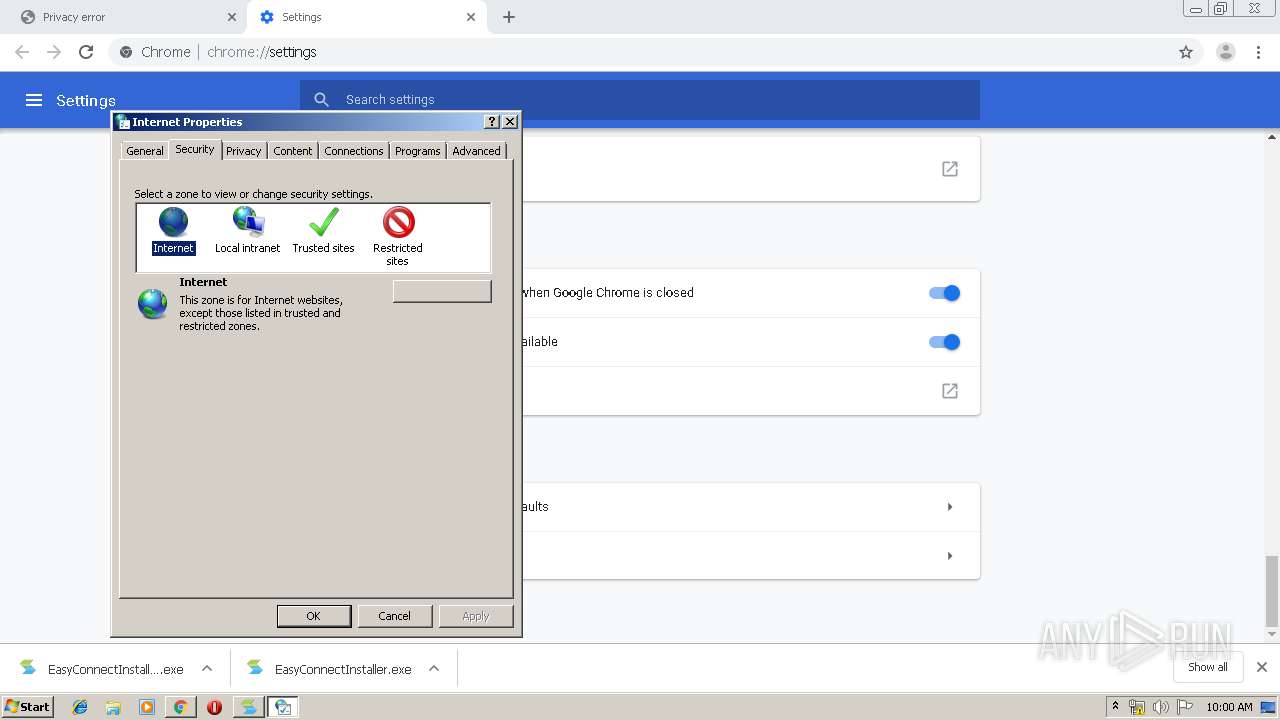
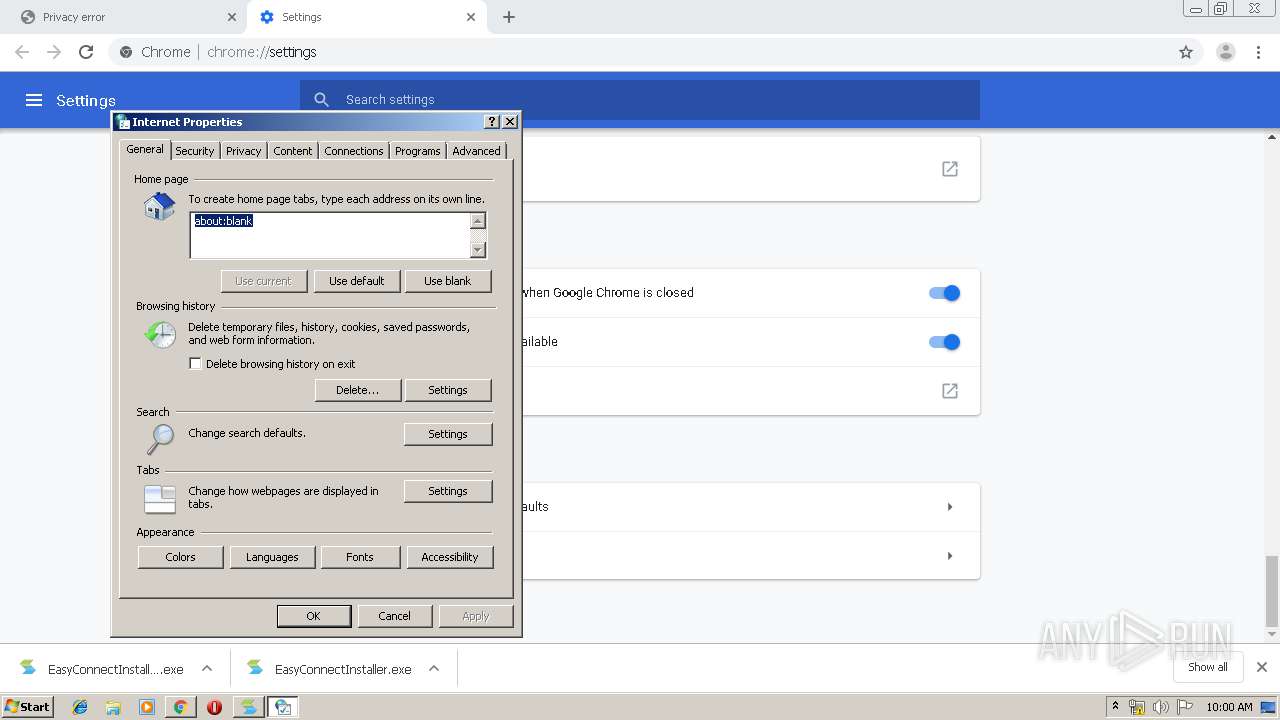
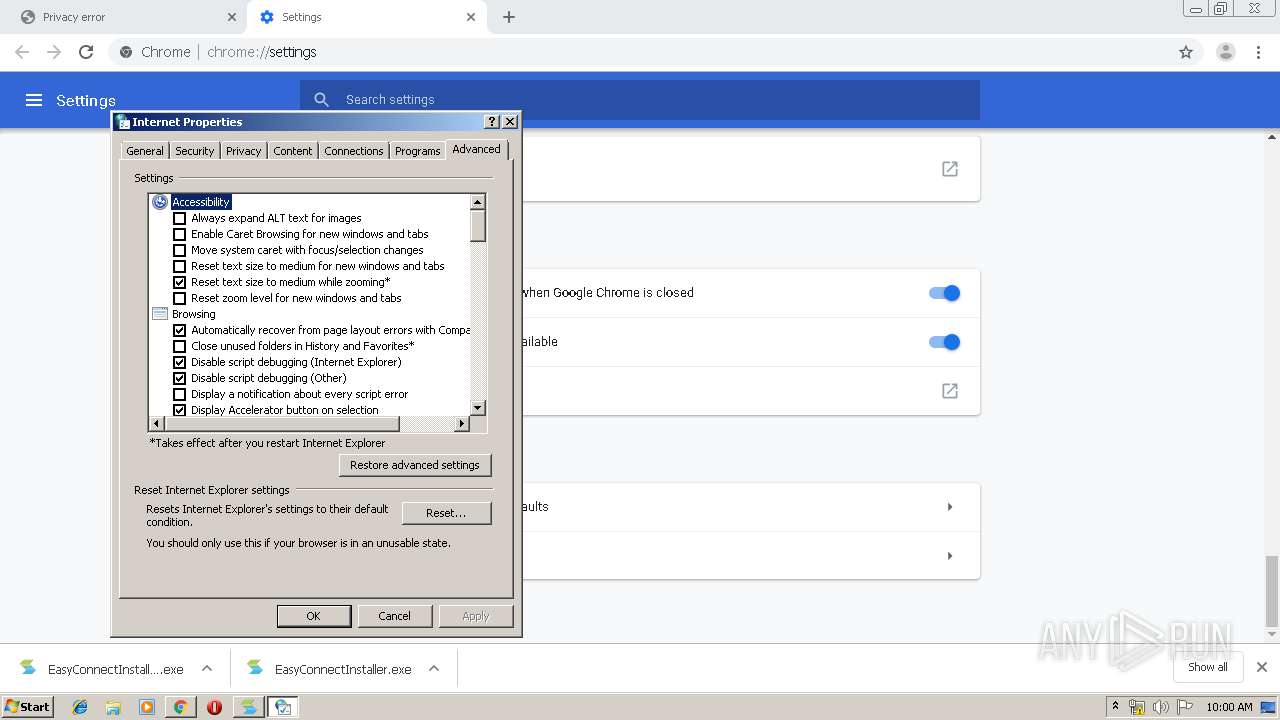
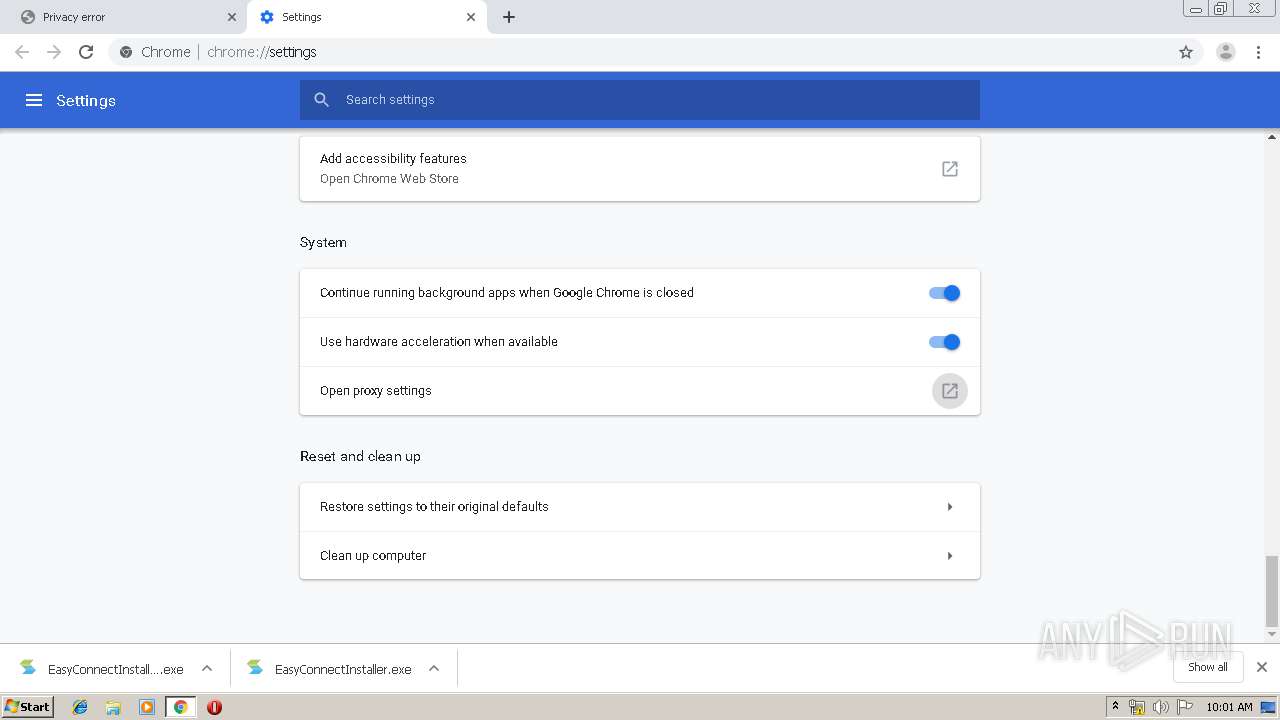
Changes internet zones settings
- ECAgent.exe (PID: 600)
- ECAgent.exe (PID: 3584)
- ECAgent.exe (PID: 532)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2064)
- EasyConnectInstaller.exe (PID: 3412)
- SangforCSClientInstaller.exe (PID: 2832)
- DnsDriverInstaller.exe (PID: 928)
- TcpDriverInstaller.exe (PID: 3400)
- SuperExeInstaller.exe (PID: 496)
- expand.exe (PID: 2364)
- expand.exe (PID: 3276)
- SJobberInstaller.exe (PID: 3848)
- SangforServiceClientInstaller.exe (PID: 1740)
- VC2010RedistX86UInstaller.exe (PID: 4044)
- SangforUpdateInstaller.exe (PID: 3968)
- SangforRAppInstaller.exe (PID: 1248)
- InstallControl.exe (PID: 776)
- VNICInstaller.exe (PID: 3860)
- vacon.exe (PID: 3752)
- DrvInst.exe (PID: 2476)
- DrvInst.exe (PID: 2168)
- ECBaseInstaller.exe (PID: 2212)
- ECAgentInstaller.exe (PID: 3244)
- SuperServiceInstaller.exe (PID: 2848)
Creates files in the Windows directory
- EasyConnectInstaller.exe (PID: 3412)
- SangforCSClientInstaller.exe (PID: 2832)
- expand.exe (PID: 2364)
- DrvInst.exe (PID: 2476)
- DrvInst.exe (PID: 2168)
- ECAgent.exe (PID: 3324)
- ECAgent.exe (PID: 816)
- ECAgent.exe (PID: 1756)
- ECAgent.exe (PID: 2944)
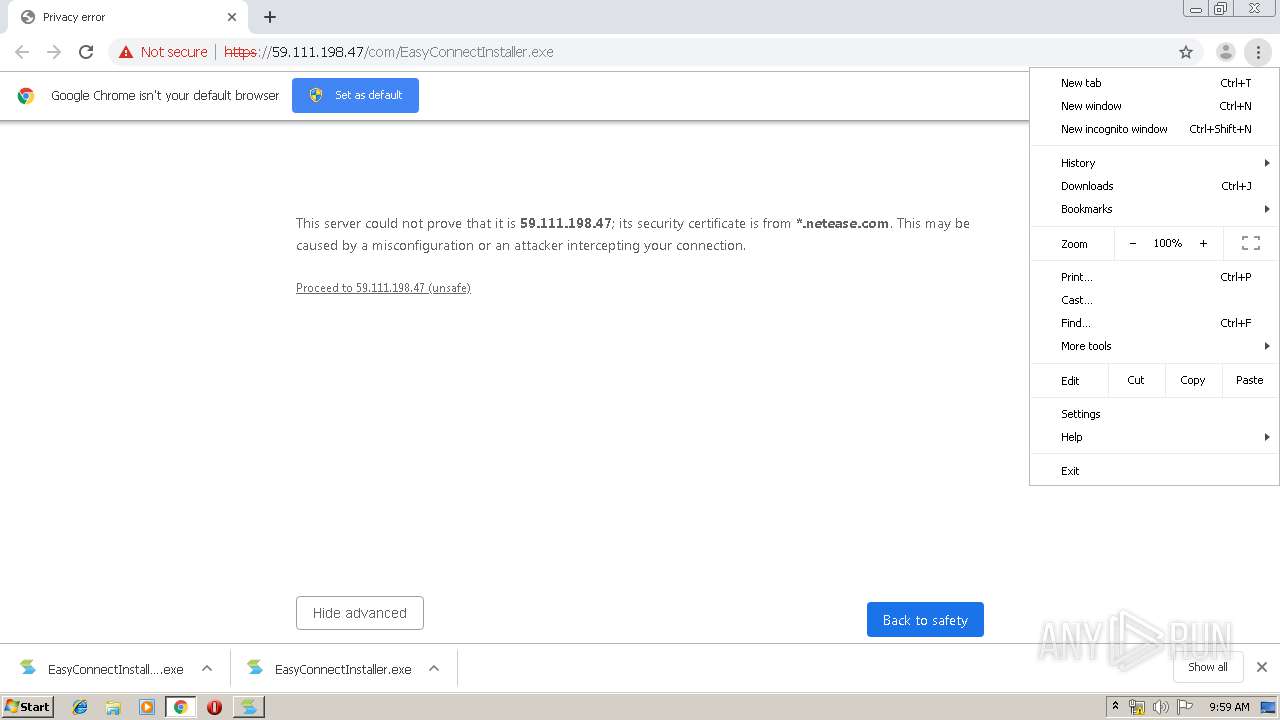
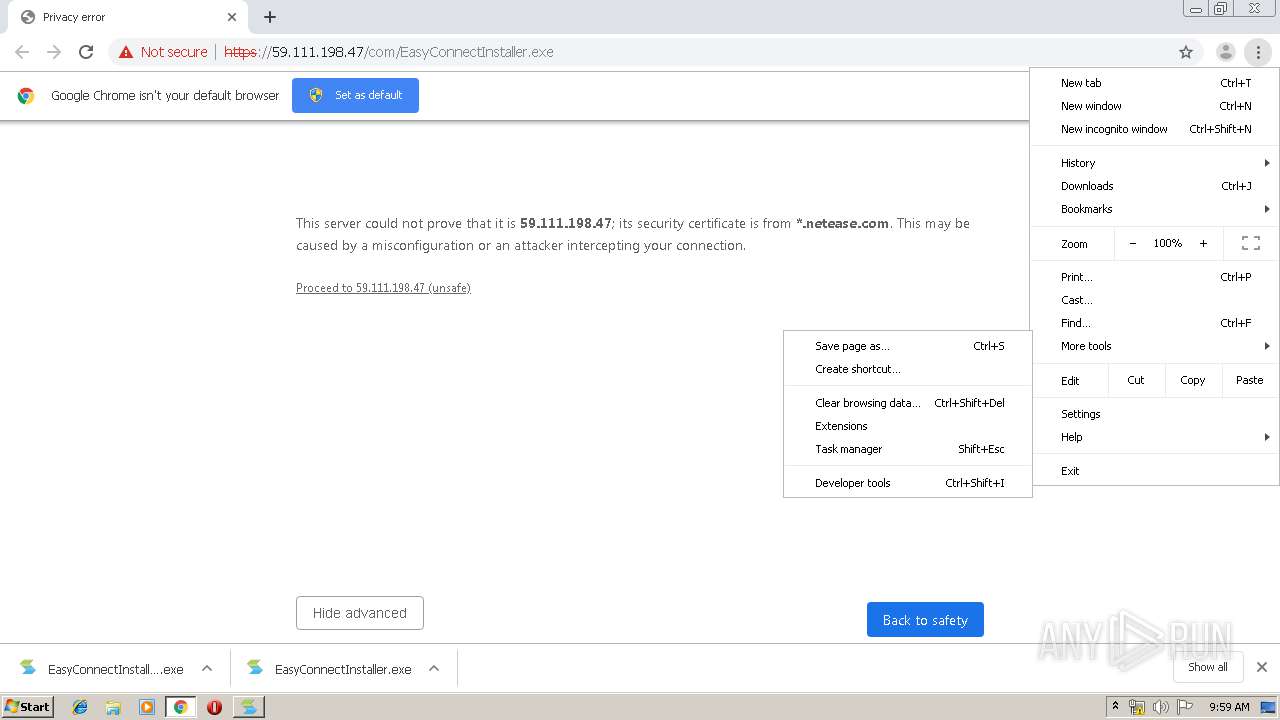
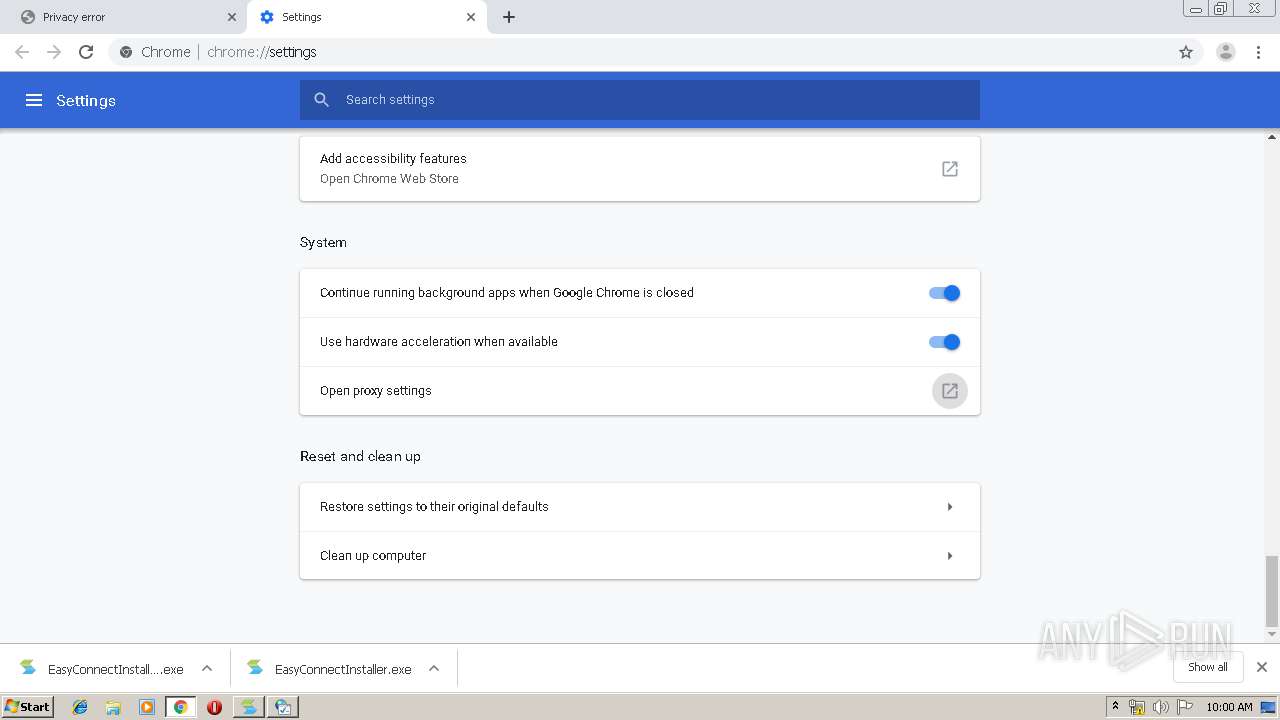
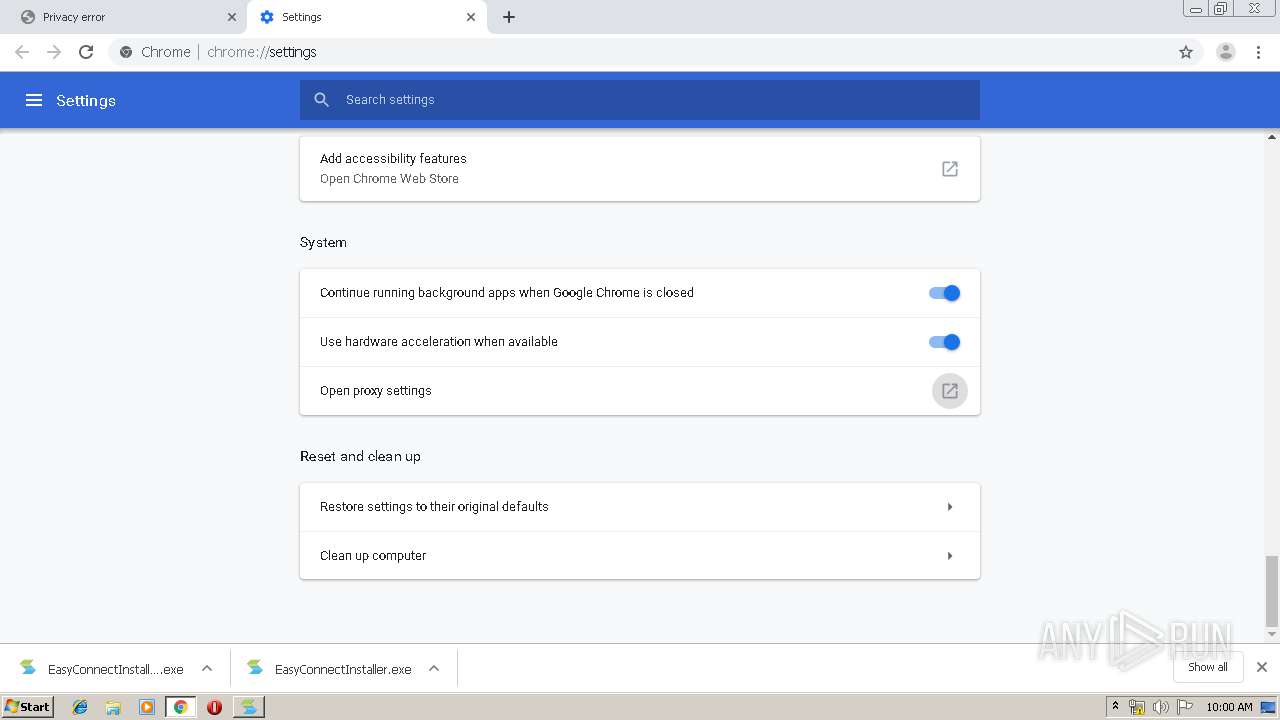
Modifies files in Chrome extension folder
- chrome.exe (PID: 2064)
Creates files in the program directory
- EasyConnectInstaller.exe (PID: 3412)
- SangforCSClientInstaller.exe (PID: 2832)
- TcpDriverInstaller.exe (PID: 3400)
- expand.exe (PID: 2364)
- SuperExeInstaller.exe (PID: 496)
- DnsDriverInstaller.exe (PID: 928)
- SangforServiceClientInstaller.exe (PID: 1740)
- expand.exe (PID: 3276)
- SJobberInstaller.exe (PID: 3848)
- SangforUpdateInstaller.exe (PID: 3968)
- SangforRAppInstaller.exe (PID: 1248)
- InstallControl.exe (PID: 776)
- VNICInstaller.exe (PID: 3860)
- ECBaseInstaller.exe (PID: 2212)
- SuperServiceInstaller.exe (PID: 2848)
- ECAgentInstaller.exe (PID: 3244)
Creates COM task schedule object
- EasyConnectInstaller.exe (PID: 3412)
- InstallControl.exe (PID: 776)
Modifies the open verb of a shell class
- SangforCSClientInstaller.exe (PID: 2832)
Creates a software uninstall entry
- SangforCSClientInstaller.exe (PID: 2832)
- VNICInstaller.exe (PID: 3860)
Starts application with an unusual extension
- SuperExeInstaller.exe (PID: 496)
- SangforServiceClientInstaller.exe (PID: 1740)
- VNICInstaller.exe (PID: 3860)
Removes files from Windows directory
- DrvInst.exe (PID: 2476)
- DrvInst.exe (PID: 2168)
- EasyConnectInstaller.exe (PID: 3412)
- ECAgent.exe (PID: 3324)
- ECAgent.exe (PID: 816)
- ECAgent.exe (PID: 1756)
- ECAgent.exe (PID: 2944)
Adds / modifies Windows certificates
- vacon.exe (PID: 3752)
Executed via COM
- DrvInst.exe (PID: 2476)
- rundll32.exe (PID: 1784)
- DrvInst.exe (PID: 2168)
Creates files in the driver directory
- DrvInst.exe (PID: 2476)
- DrvInst.exe (PID: 2168)
Executed as Windows Service
- vssvc.exe (PID: 2144)
- SangforPromoteService.exe (PID: 2692)
Uses NETSH.EXE for network configuration
- SetIPTime.exe (PID: 1780)
Creates files in the user directory
- ECAgent.exe (PID: 3896)
- ECAgent.exe (PID: 2668)
- SangforCSClient.exe (PID: 3748)
Uses RUNDLL32.EXE to load library
- chrome.exe (PID: 2064)
- rundll32.exe (PID: 3960)
Application launched itself
- rundll32.exe (PID: 3960)
Reads Internet Cache Settings
- rundll32.exe (PID: 1104)
INFO
Application launched itself
- chrome.exe (PID: 2064)
Reads the hosts file
- chrome.exe (PID: 2180)
- chrome.exe (PID: 2064)
Reads Internet Cache Settings
- chrome.exe (PID: 2064)
Searches for installed software
- DrvInst.exe (PID: 2476)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2144)
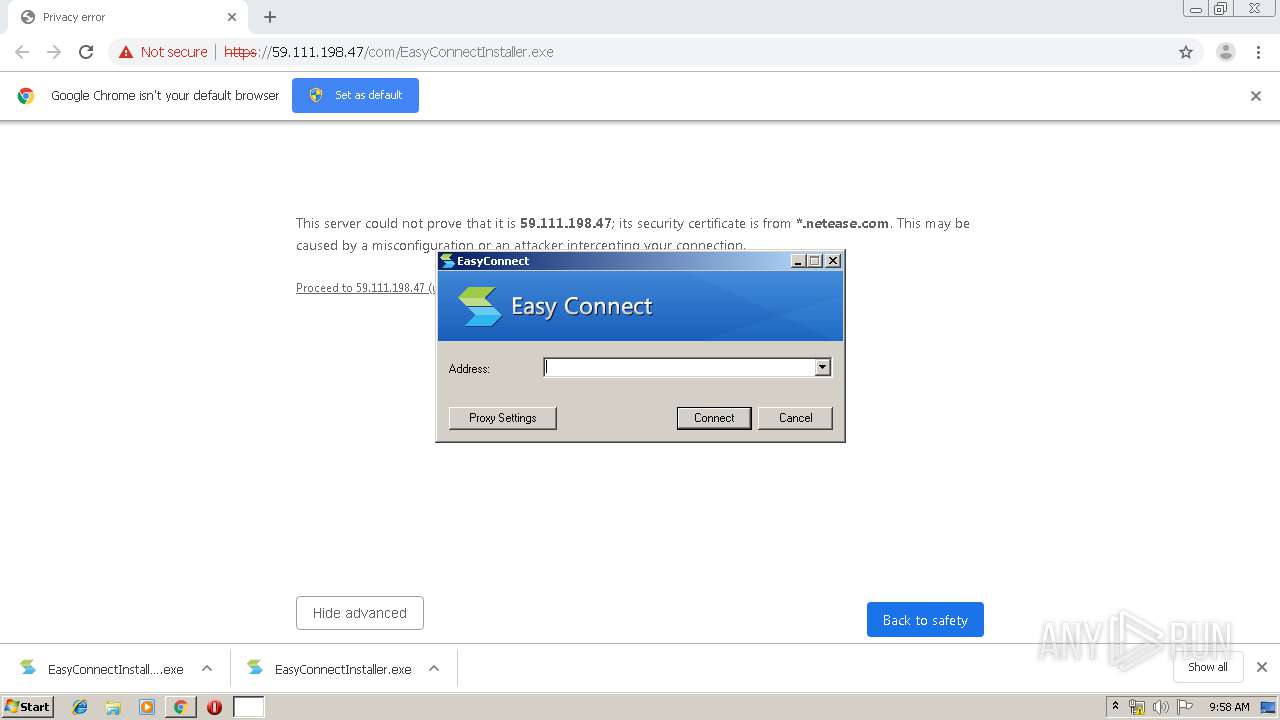
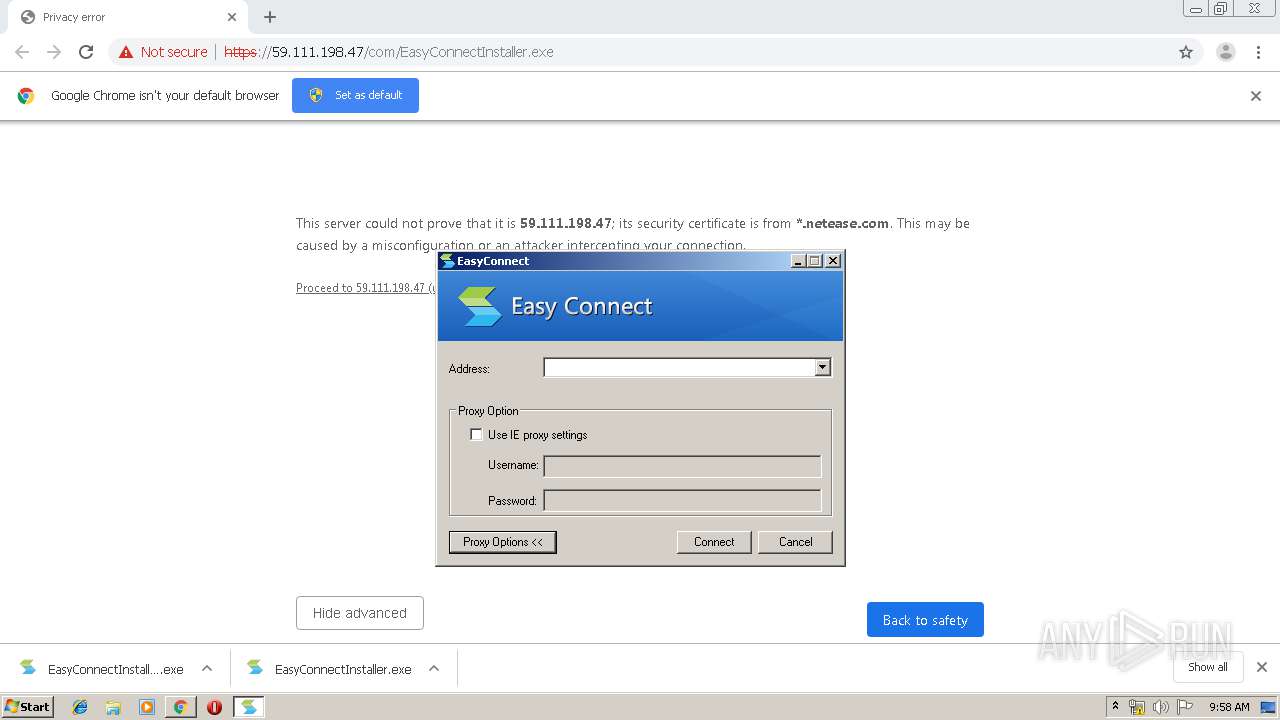
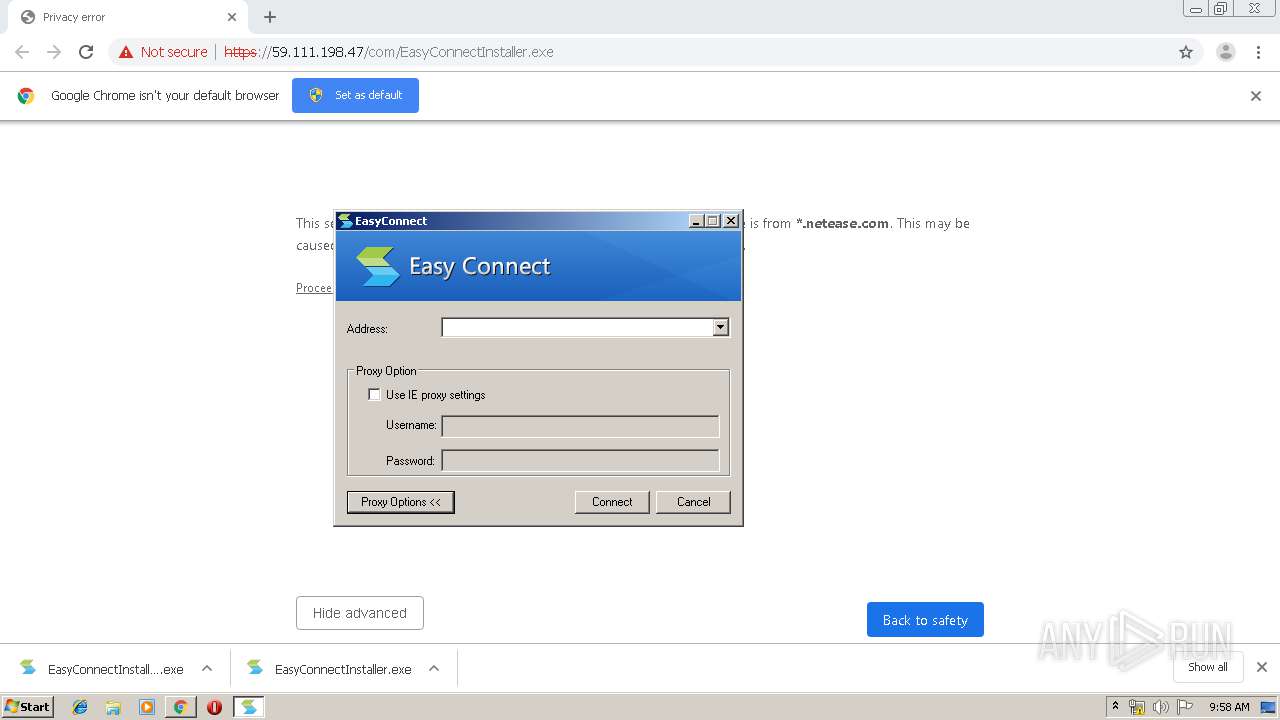
Manual execution by user
- SangforCSClient.exe (PID: 3748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
134
Monitored processes
90
Malicious processes
24
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Users\admin\AppData\Local\Temp\nsg482C.tmp\ns483D.tmp" "expand.exe" -r "C:\Program Files\Sangfor\SSL\SangforServiceClient\SangforServiceClient.CAB" "C:\Program Files\Sangfor\SSL\SangforServiceClient" | C:\Users\admin\AppData\Local\Temp\nsg482C.tmp\ns483D.tmp | — | SangforServiceClientInstaller.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,14334341205312465070,6870145229510633206,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4157694731616851094 --mojo-platform-channel-handle=1028 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 496 | "C:\Program Files\Sangfor\SSL\ClientComponent\SuperExeInstaller.exe" -SessionId=-1 | C:\Program Files\Sangfor\SSL\ClientComponent\SuperExeInstaller.exe | EasyConnectInstaller.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Sangfor\SSL\DnsDriver\Install.exe" | C:\Program Files\Sangfor\SSL\DnsDriver\Install.exe | DnsDriverInstaller.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Sangfor\SSL\Promote\SangforPromoteService.exe" -/StartServer | C:\Program Files\Sangfor\SSL\Promote\SangforPromoteService.exe | SuperServiceInstaller.exe | ||||||||||||
User: admin Company: Sangfor Technologies Inc. Integrity Level: HIGH Description: Promote Service Exit code: 1 Version: 7, 6, 3, 0 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Sangfor\SSL\ECAgent\ECAgent.exe" --import-nss --enable-ie-loopback | C:\Program Files\Sangfor\SSL\ECAgent\ECAgent.exe | SangforPromoteService.exe | ||||||||||||
User: admin Company: Sangfor Technologies Inc. Integrity Level: MEDIUM Description: Agent for EasyConnect Exit code: 0 Version: 7,6,3,0 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Sangfor\SSL\ECAgent\ECAgent.exe" --import-nss --enable-ie-loopback | C:\Program Files\Sangfor\SSL\ECAgent\ECAgent.exe | SangforPromoteService.exe | ||||||||||||
User: admin Company: Sangfor Technologies Inc. Integrity Level: MEDIUM Description: Agent for EasyConnect Exit code: 0 Version: 7,6,3,0 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Sangfor\SSL\ClientComponent\InstallControl.exe" -SessionId=-1 | C:\Program Files\Sangfor\SSL\ClientComponent\InstallControl.exe | EasyConnectInstaller.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 816 | "C:\Program Files\Sangfor\SSL\ECAgent\ECAgent.exe" --import-sys --enable-loopback | C:\Program Files\Sangfor\SSL\ECAgent\ECAgent.exe | SangforPromoteService.exe | ||||||||||||
User: SYSTEM Company: Sangfor Technologies Inc. Integrity Level: SYSTEM Description: Agent for EasyConnect Exit code: 0 Version: 7,6,3,0 Modules
| |||||||||||||||
| 864 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 538
Read events
2 534
Write events
1 719
Delete events
285
Modification events
| (PID) Process: | (964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2064-13223037417367125 |
Value: 259 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
119
Suspicious files
60
Text files
400
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a87f.TMP | — | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e6c2abcc-f4de-4980-ba9e-4aa432c6103b.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a87f.TMP | text | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 864 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
31
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2180 | chrome.exe | GET | 204 | 172.217.18.163:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
2180 | chrome.exe | GET | 204 | 172.217.18.163:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
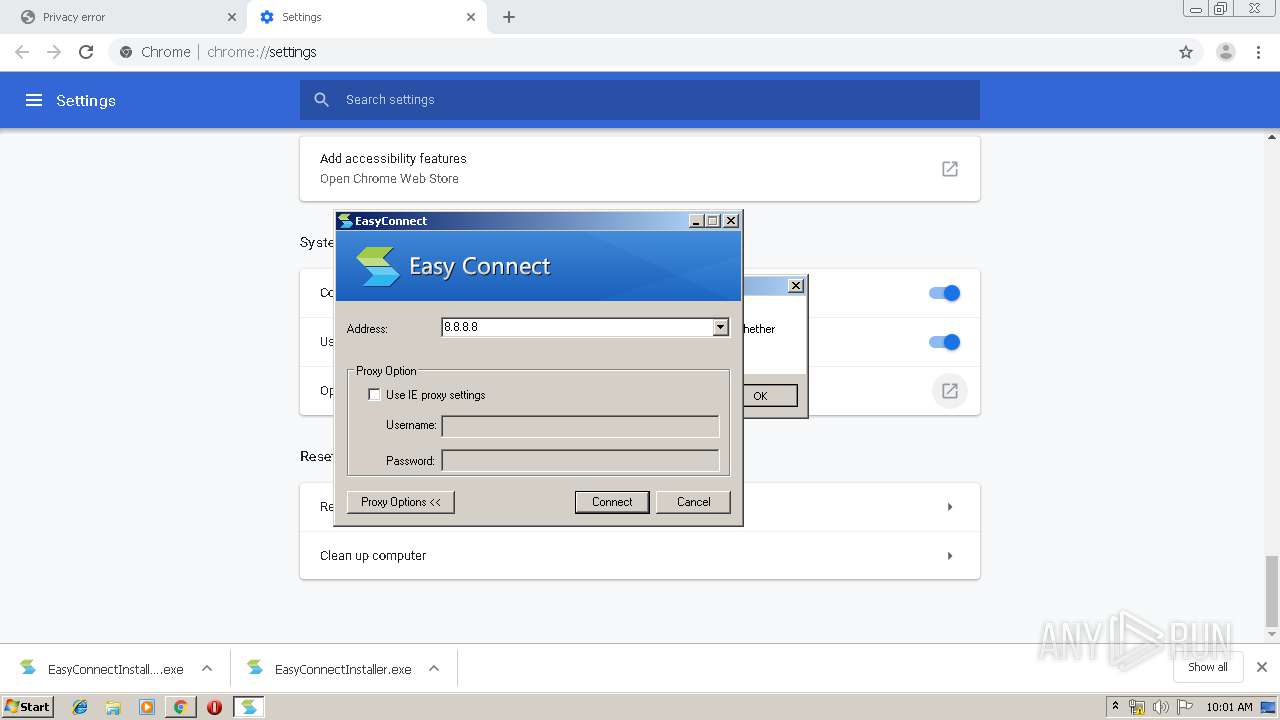
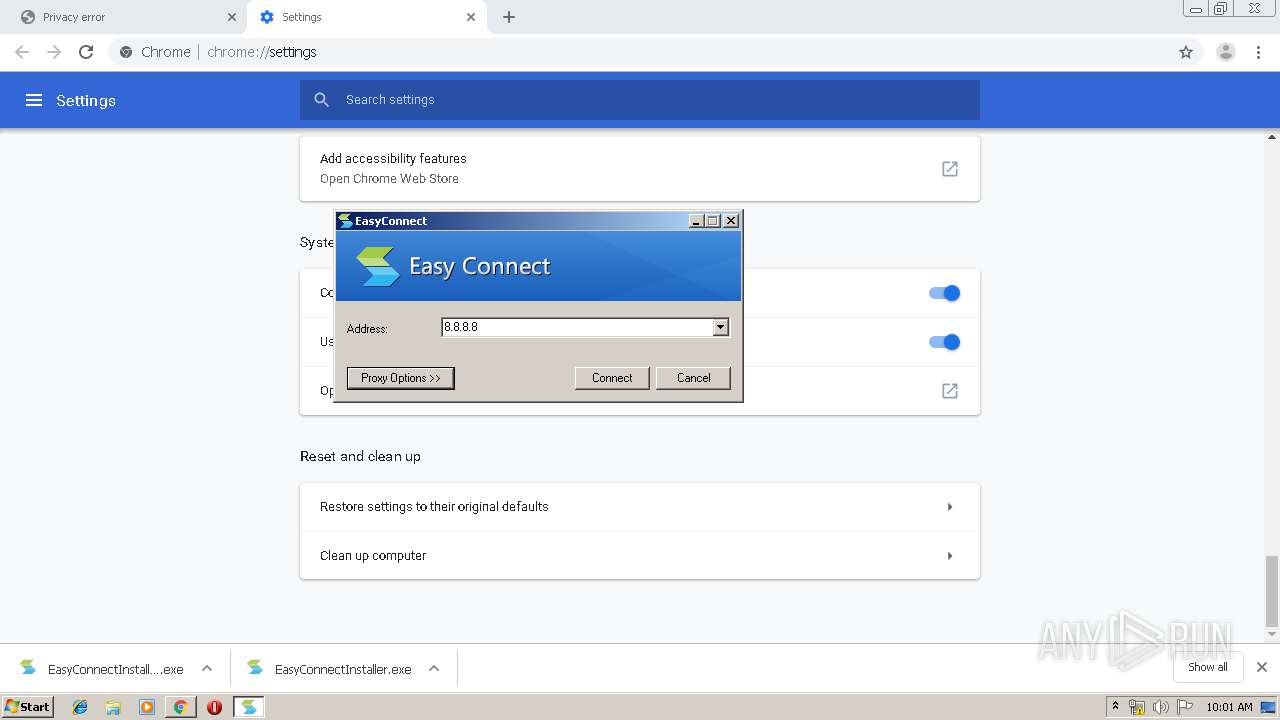
3748 | SangforCSClient.exe | GET | — | 10.10.10.10:80 | http://10.10.10.10/ | unknown | — | — | malicious |
3748 | SangforCSClient.exe | GET | — | 8.8.8.8:80 | http://8.8.8.8/ | US | — | — | malicious |
2180 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
2180 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
2180 | chrome.exe | GET | 200 | 74.125.100.7:80 | http://r2---sn-5hnekn7l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=37.48.118.41&mm=28&mn=sn-5hnekn7l&ms=nvh&mt=1578563777&mv=m&mvi=1&pl=27&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2180 | chrome.exe | GET | 200 | 74.125.100.137:80 | http://r3---sn-5hnedn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=37.48.118.41&mm=28&mn=sn-5hnedn7e&ms=nvh&mt=1578563718&mv=m&mvi=2&pl=27&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2180 | chrome.exe | 59.111.198.47:443 | — | Guangzhou NetEase Computer System Co., Ltd. | CN | unknown |
2180 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 172.217.18.163:80 | www.gstatic.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 74.125.100.7:80 | r2---sn-5hnekn7l.gvt1.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 172.217.21.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 216.58.210.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2180 | chrome.exe | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-5hnedn7e.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
r2---sn-5hnekn7l.gvt1.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
EasyConnectInstaller.exe | registry(SOFTWARE\Sangfor\SSL\VPN\Sessions\IDTable) not found |
EasyConnectInstaller.exe | open registry(SOFTWARE\Sangfor\SSL\VPN\Sessions\IDTable) failed, errcode = 2 |
EasyConnectInstaller.exe | open registry(SOFTWARE\Sangfor\SSL\SangforCSClient) failed, errcode = 2 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is HTHMAC.HTHMACCtrl.1 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is EnumFile.EnumPathFile.1 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is ProxyIE.CSProxy.1 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is NOWIN.NowinCtrl.1 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is Epnd.Epassnd.1 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is CSClientManagerPrj.CSClientManager.1 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is SangforBHO.SangforHelper.1 |