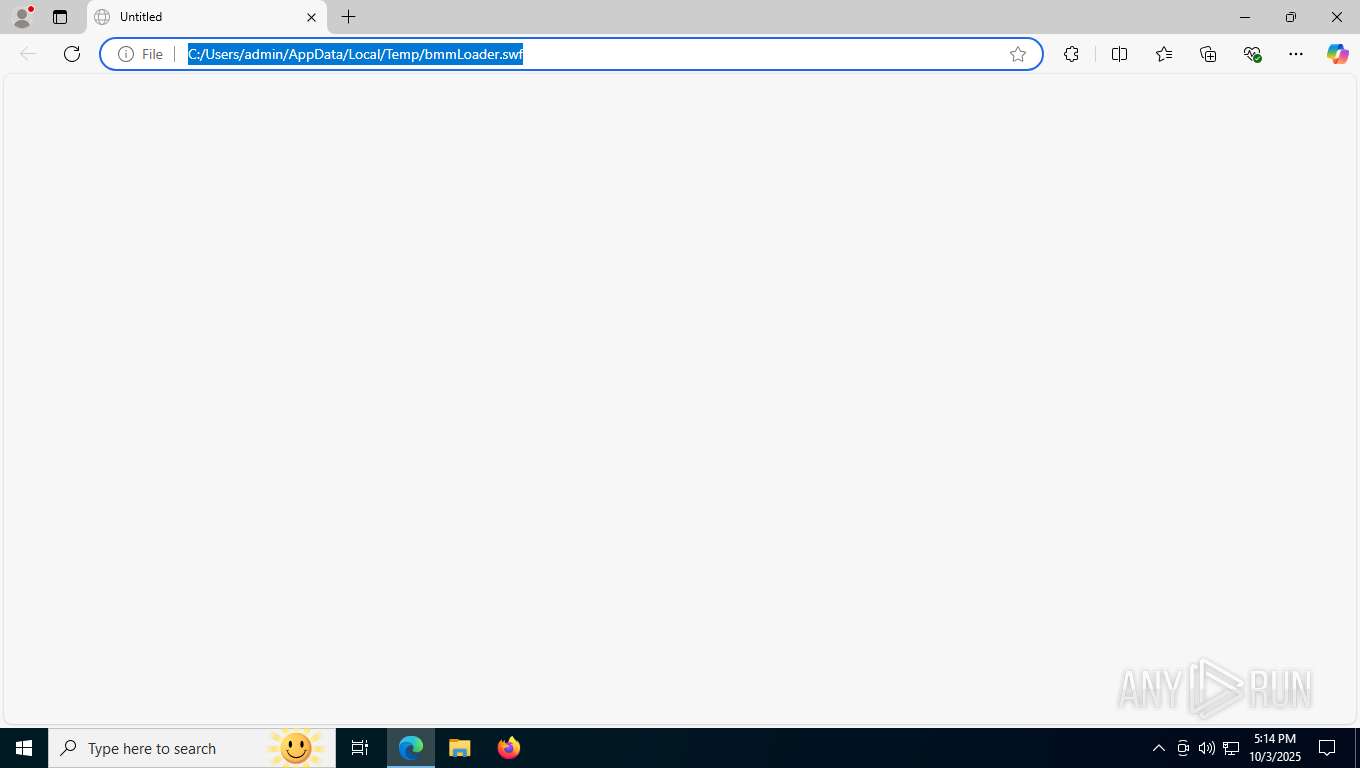
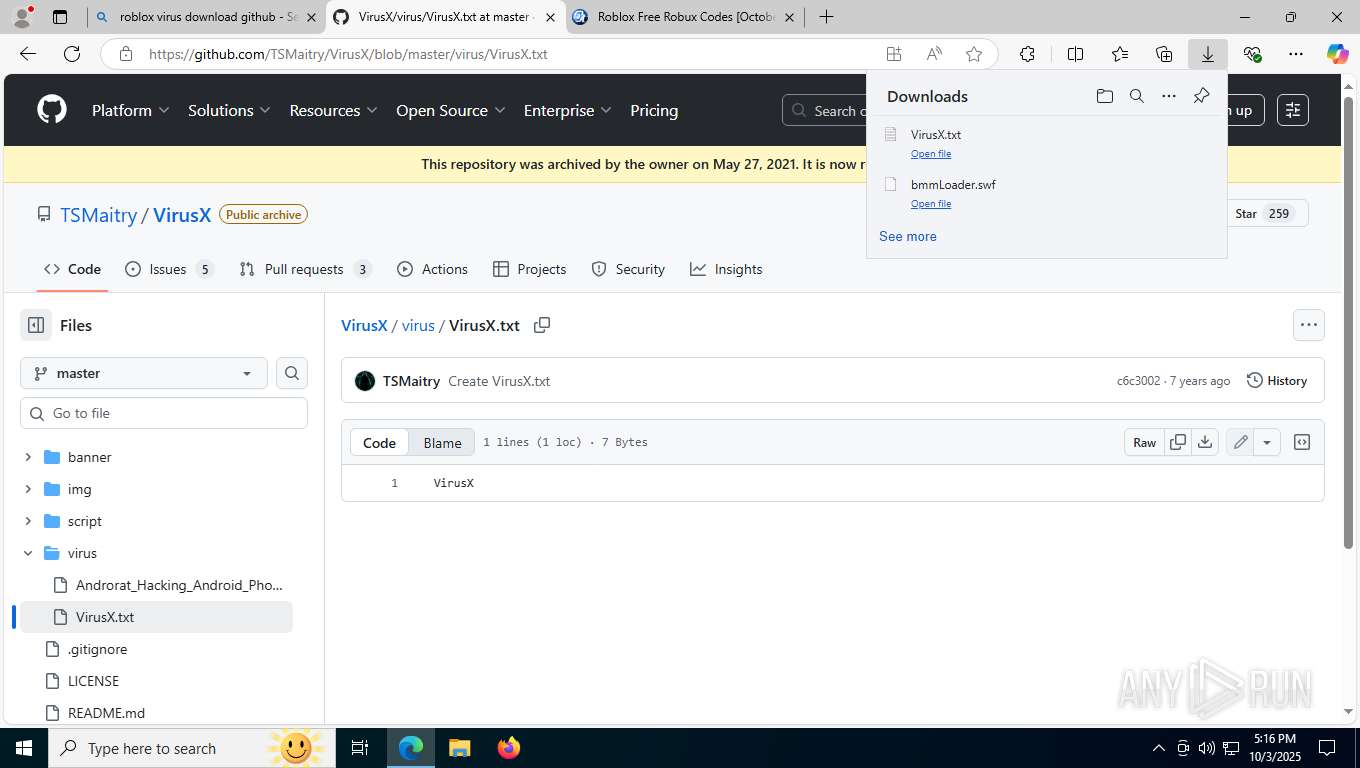
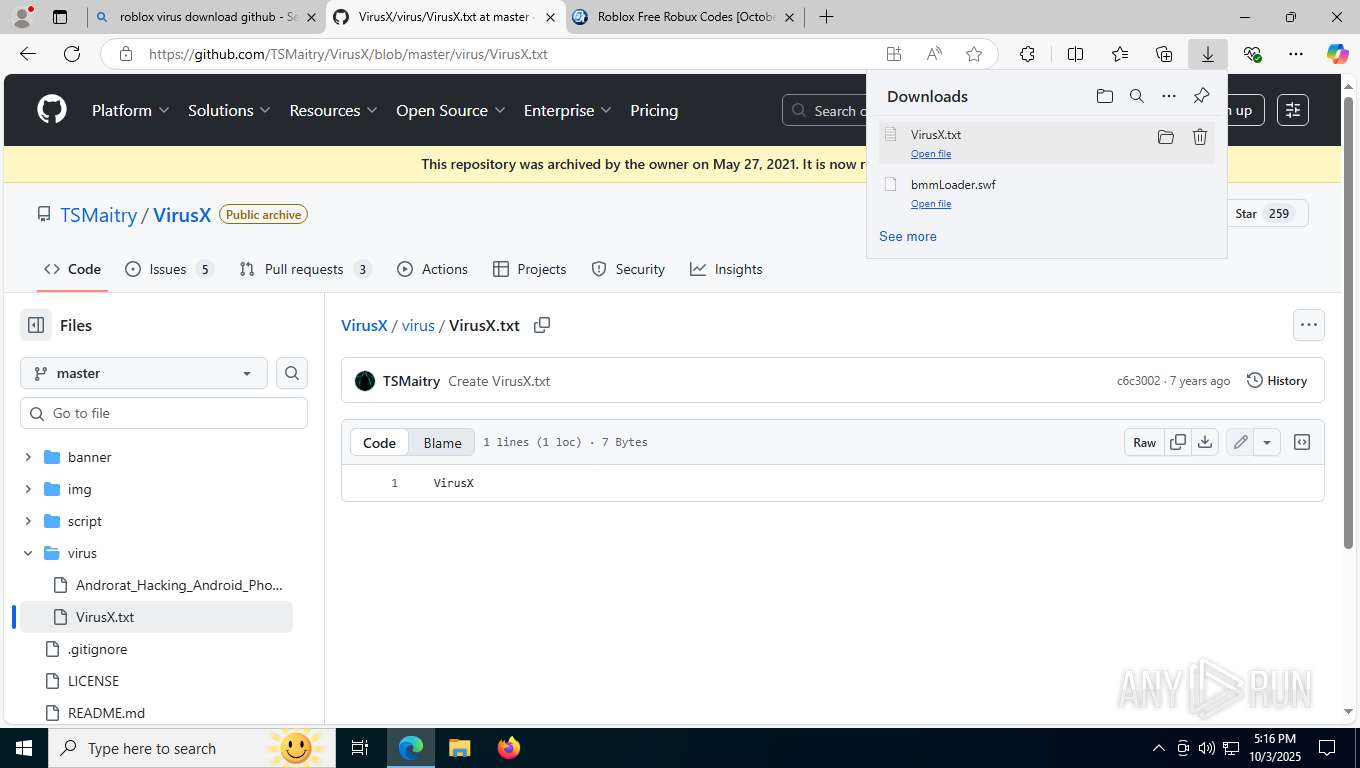
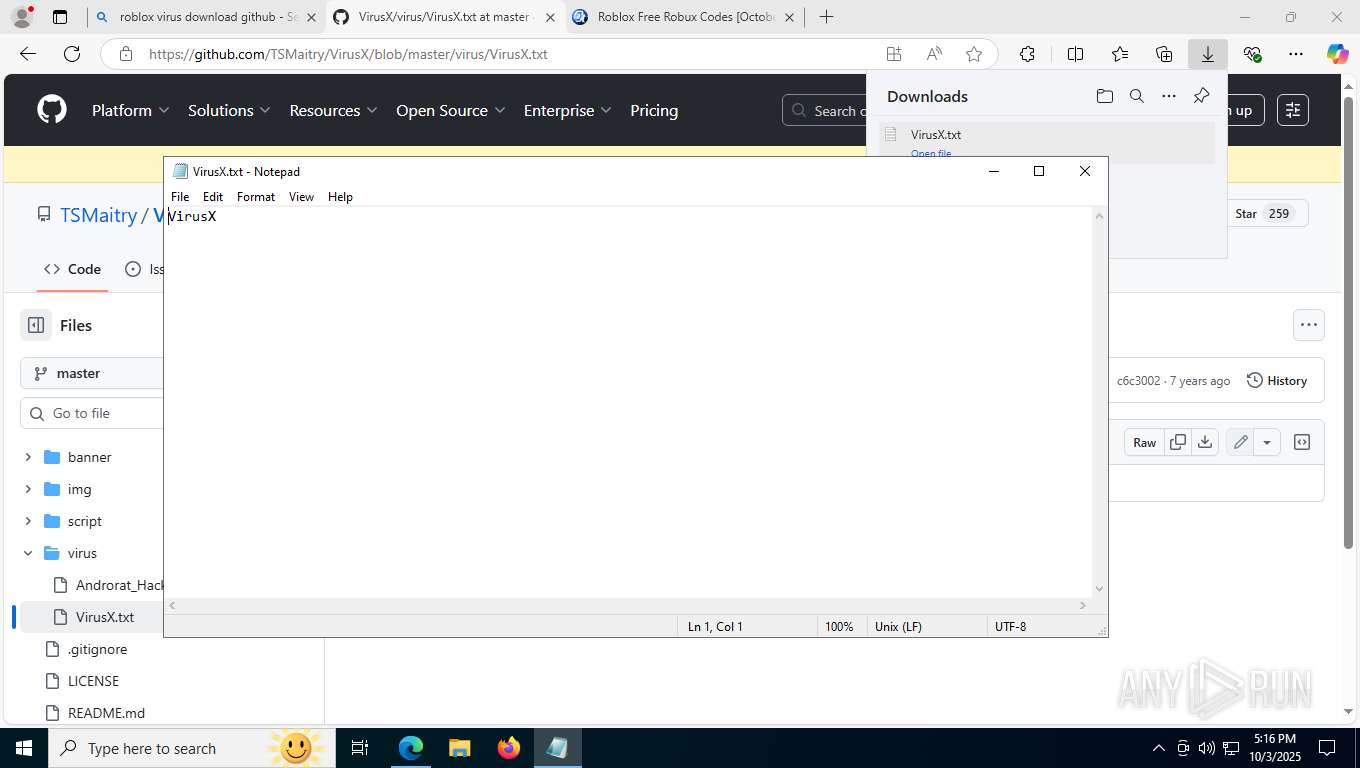
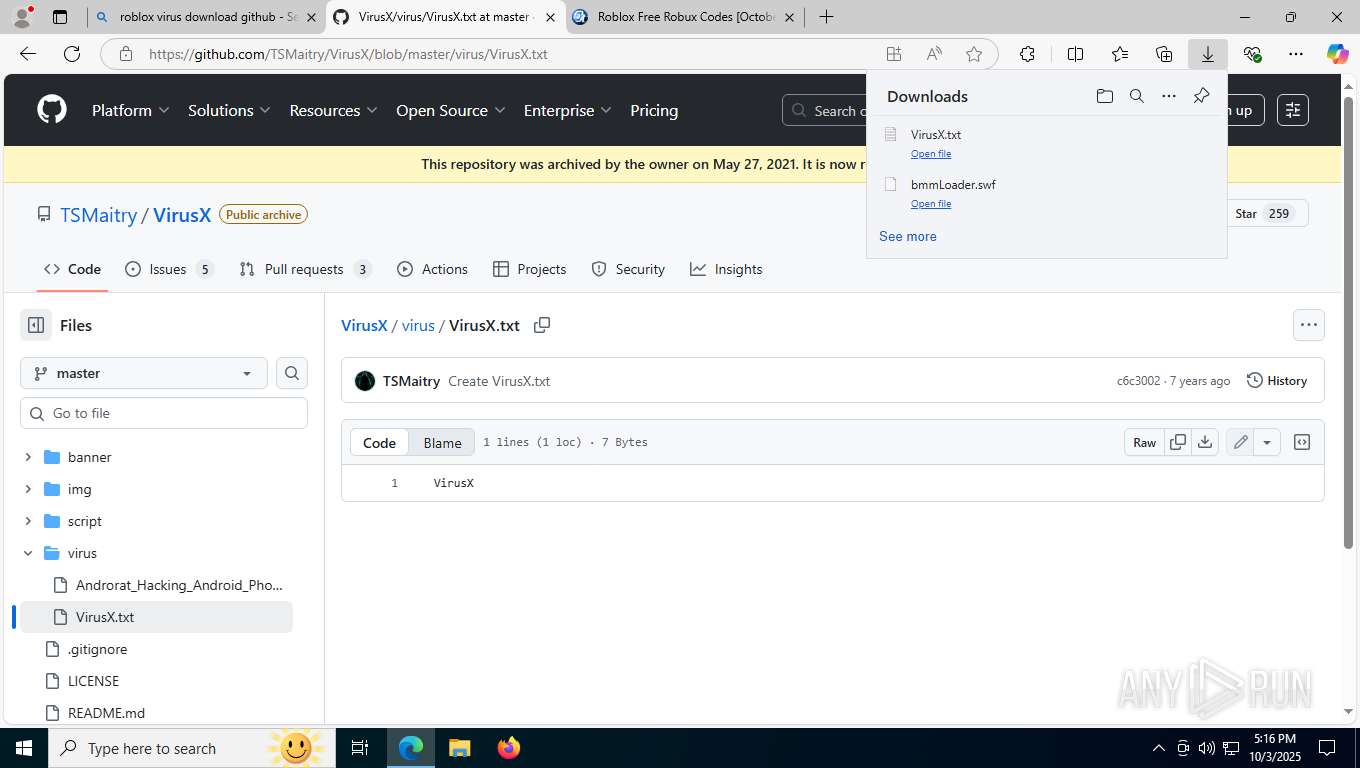
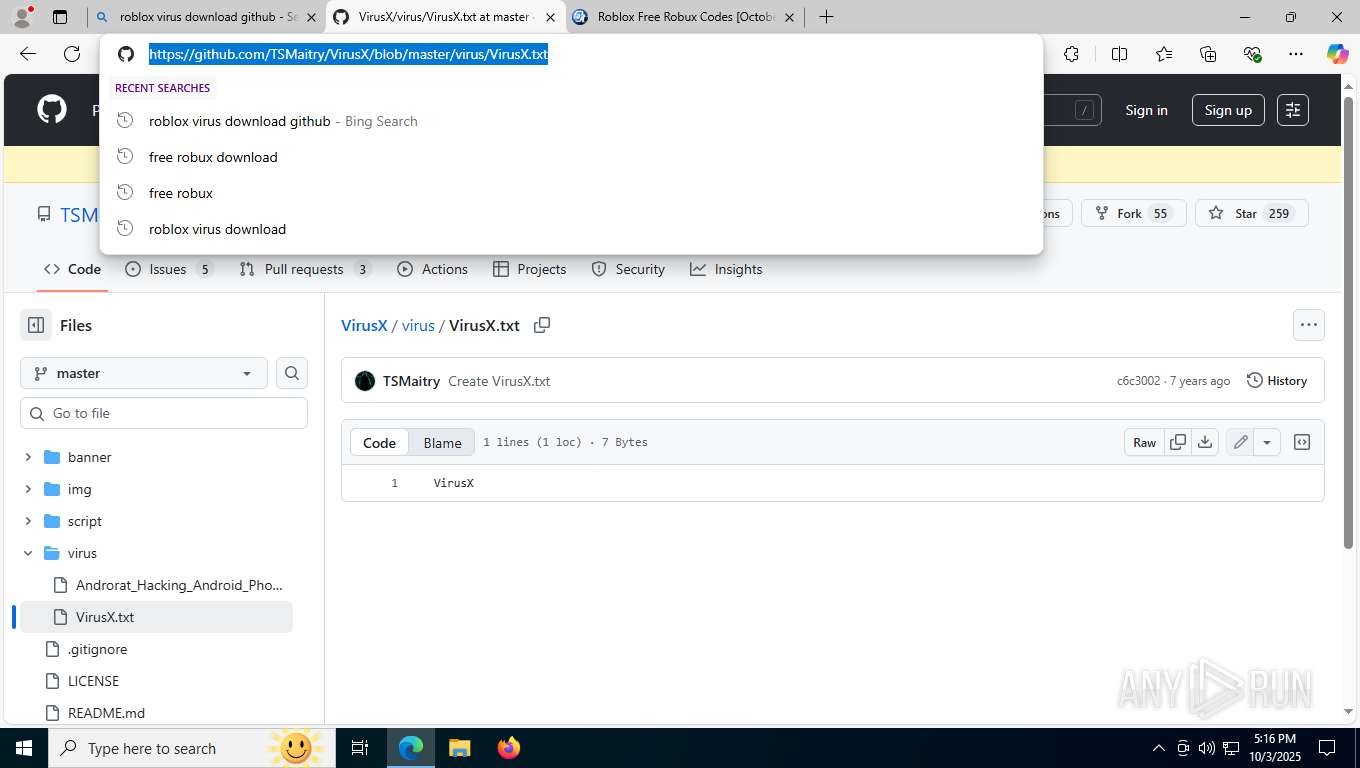
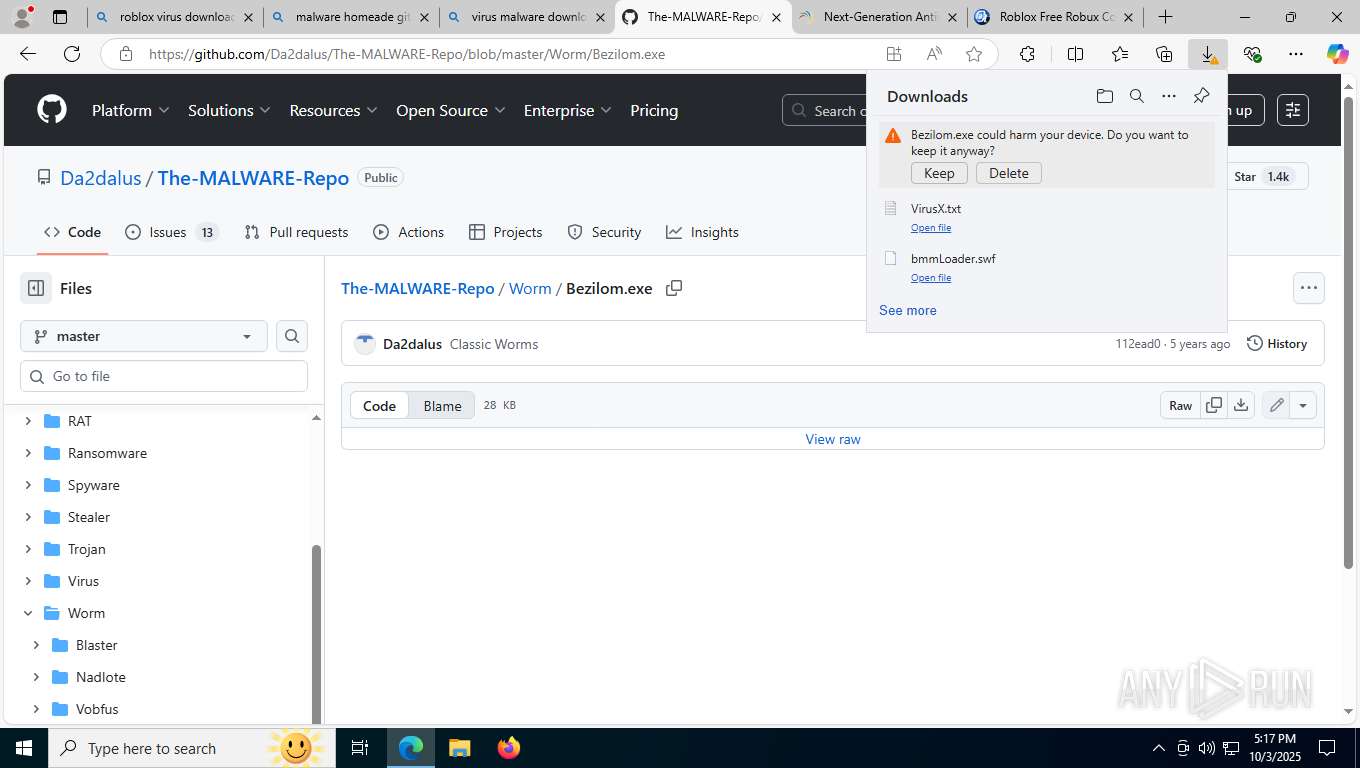
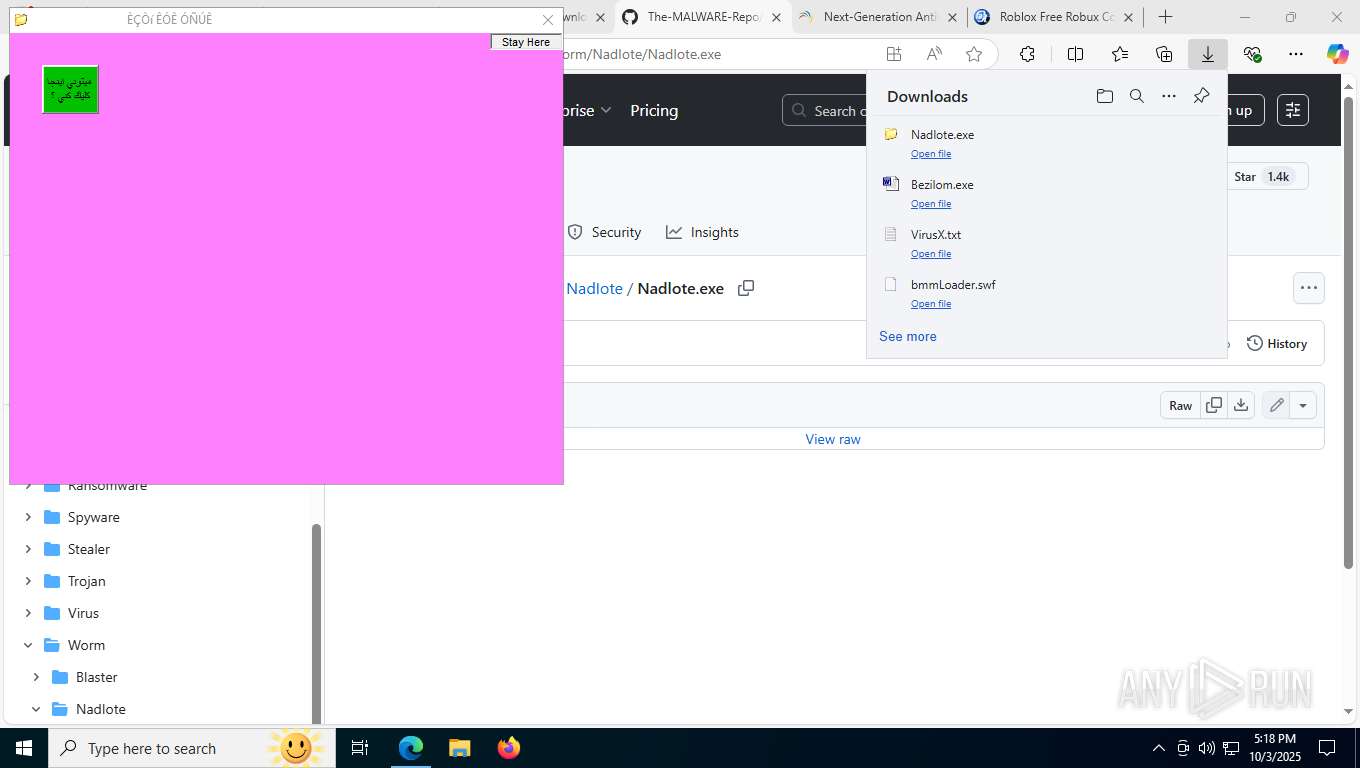
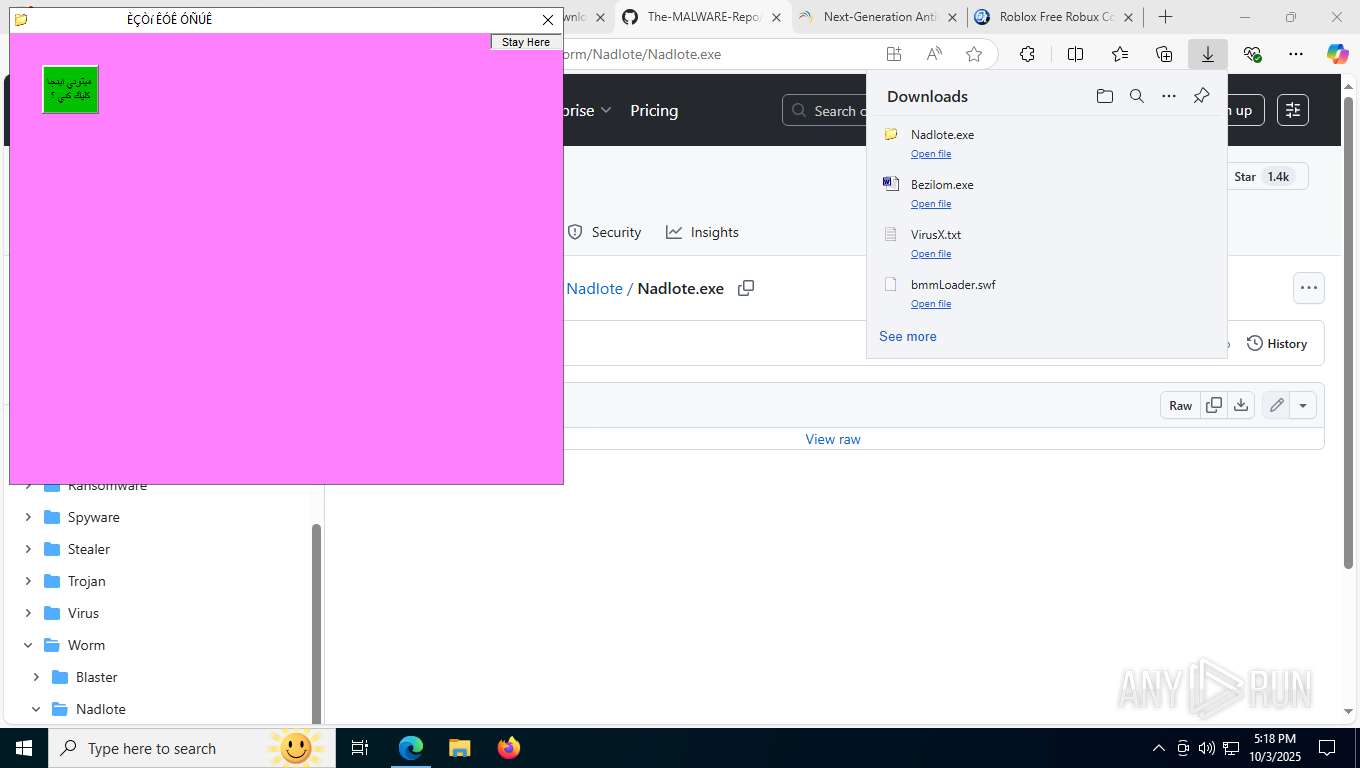
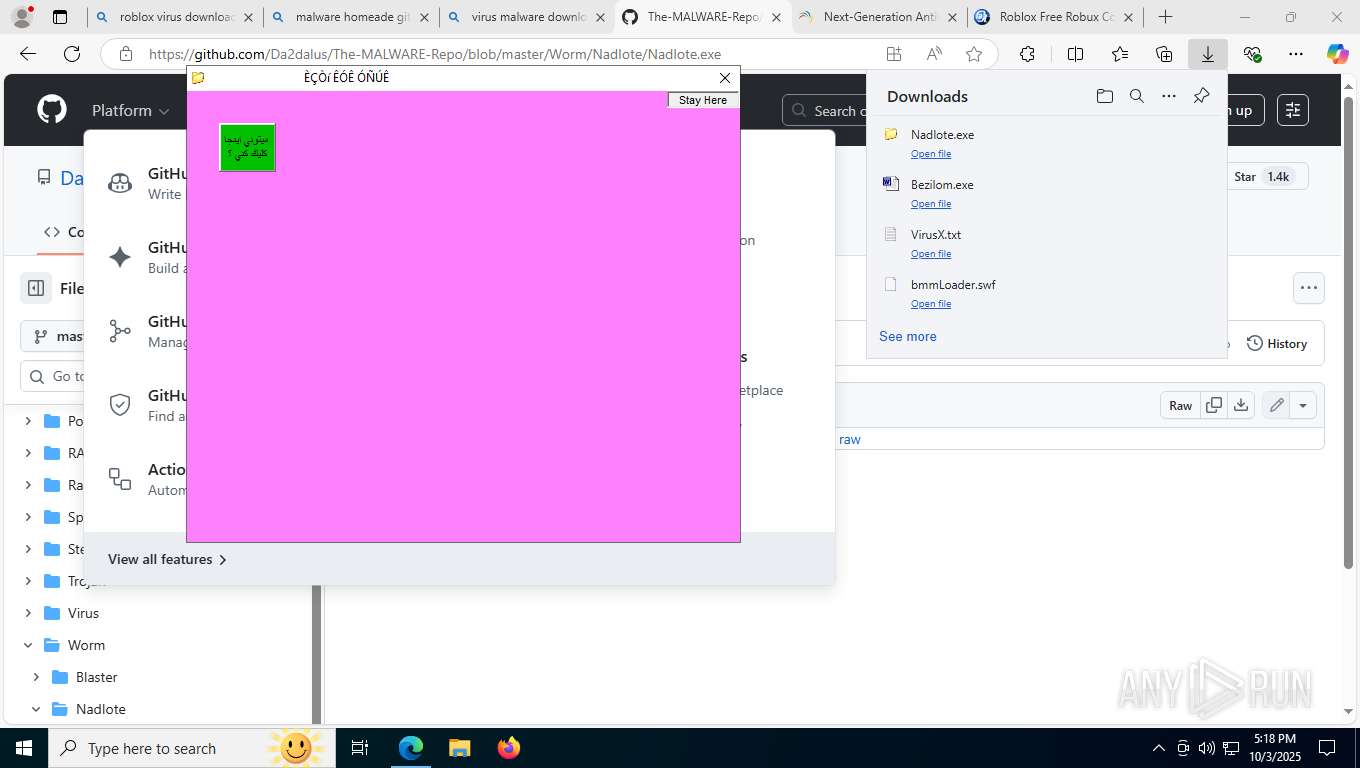
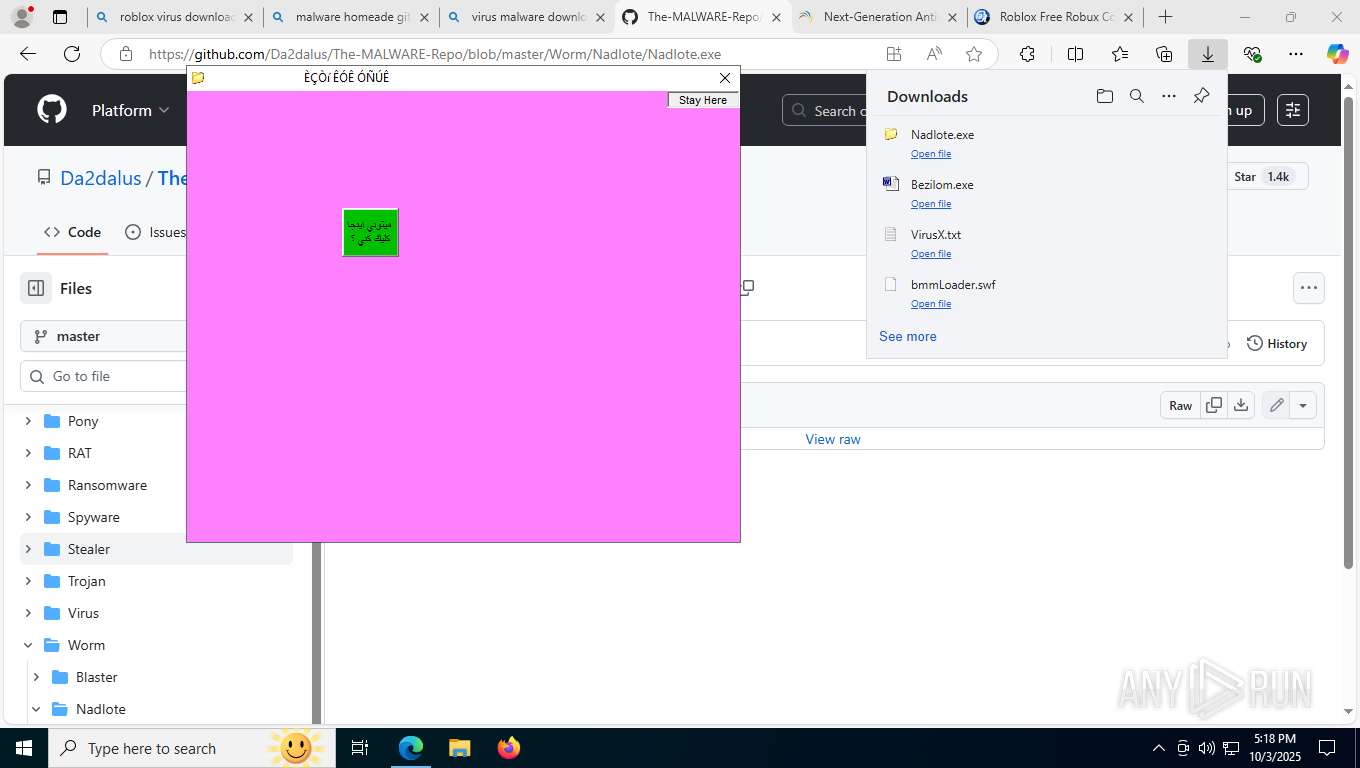
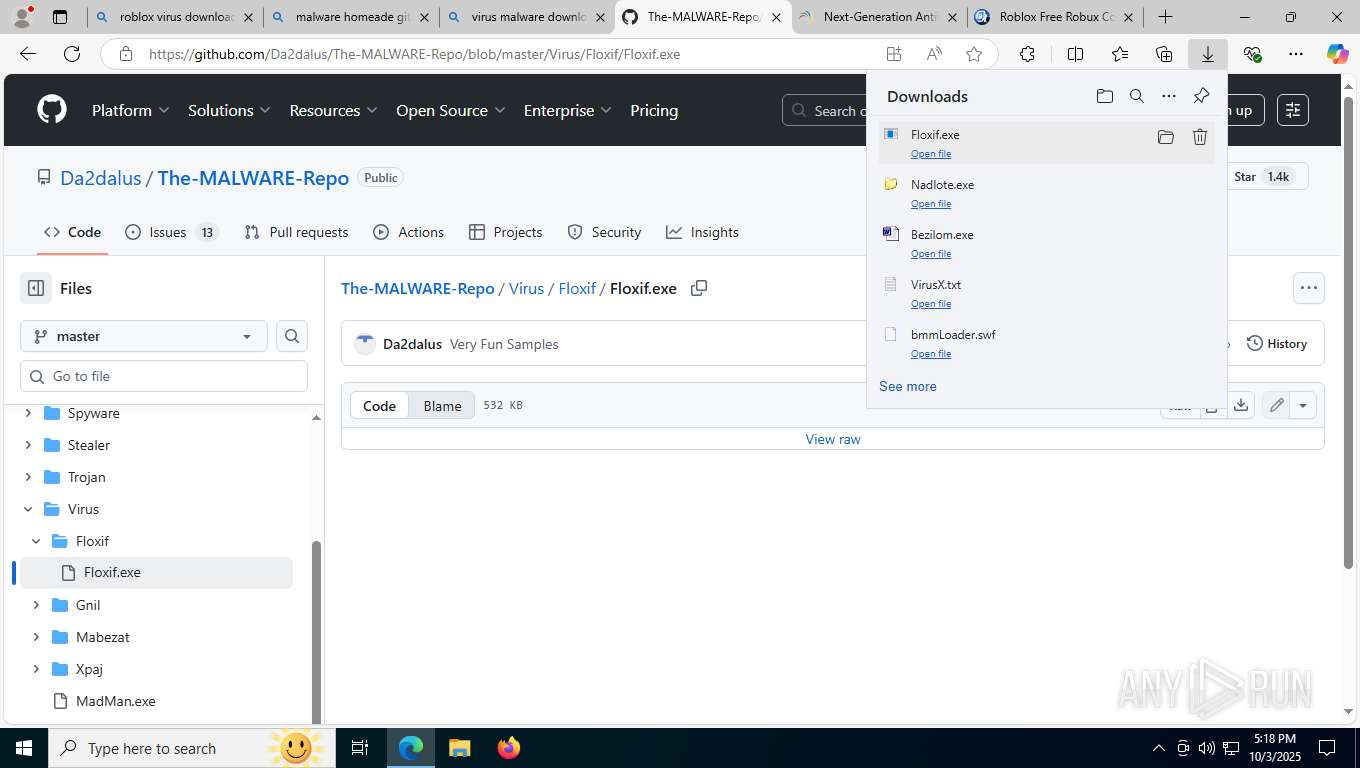
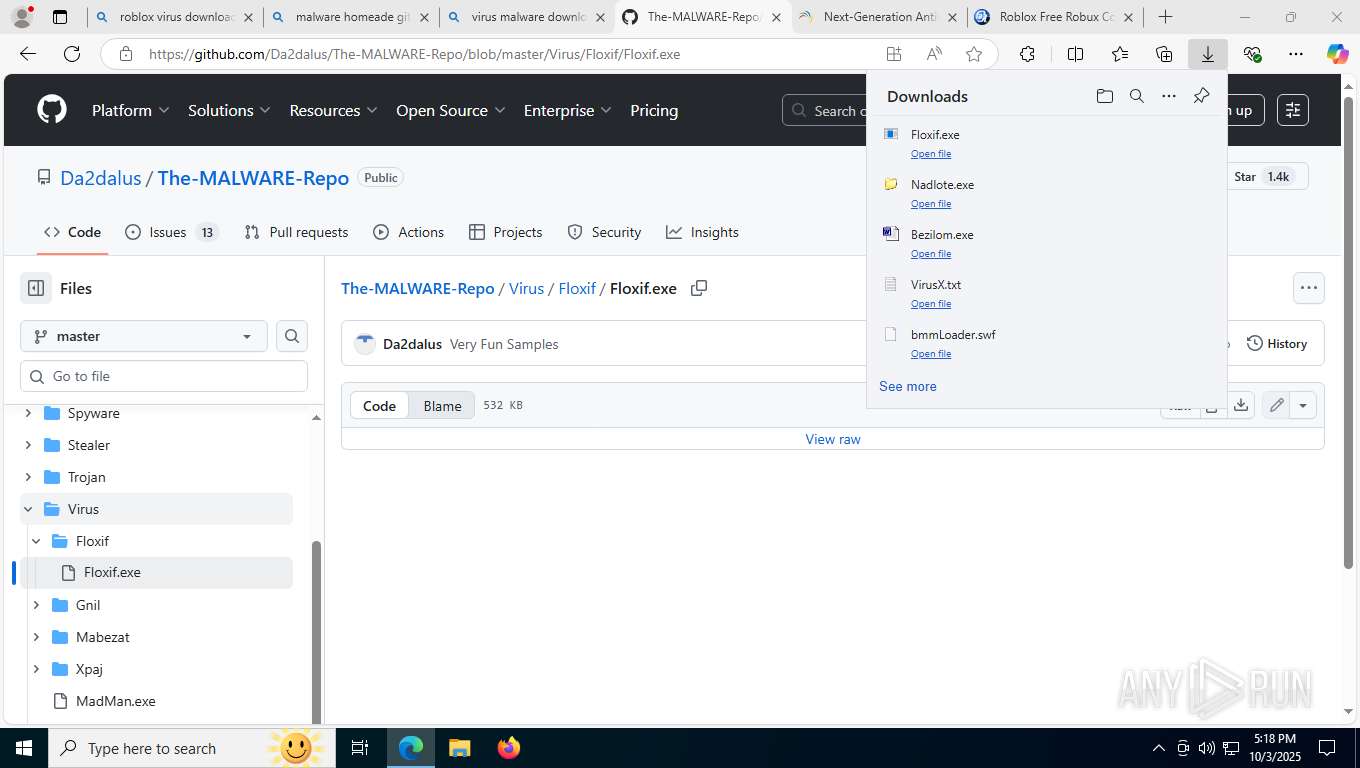
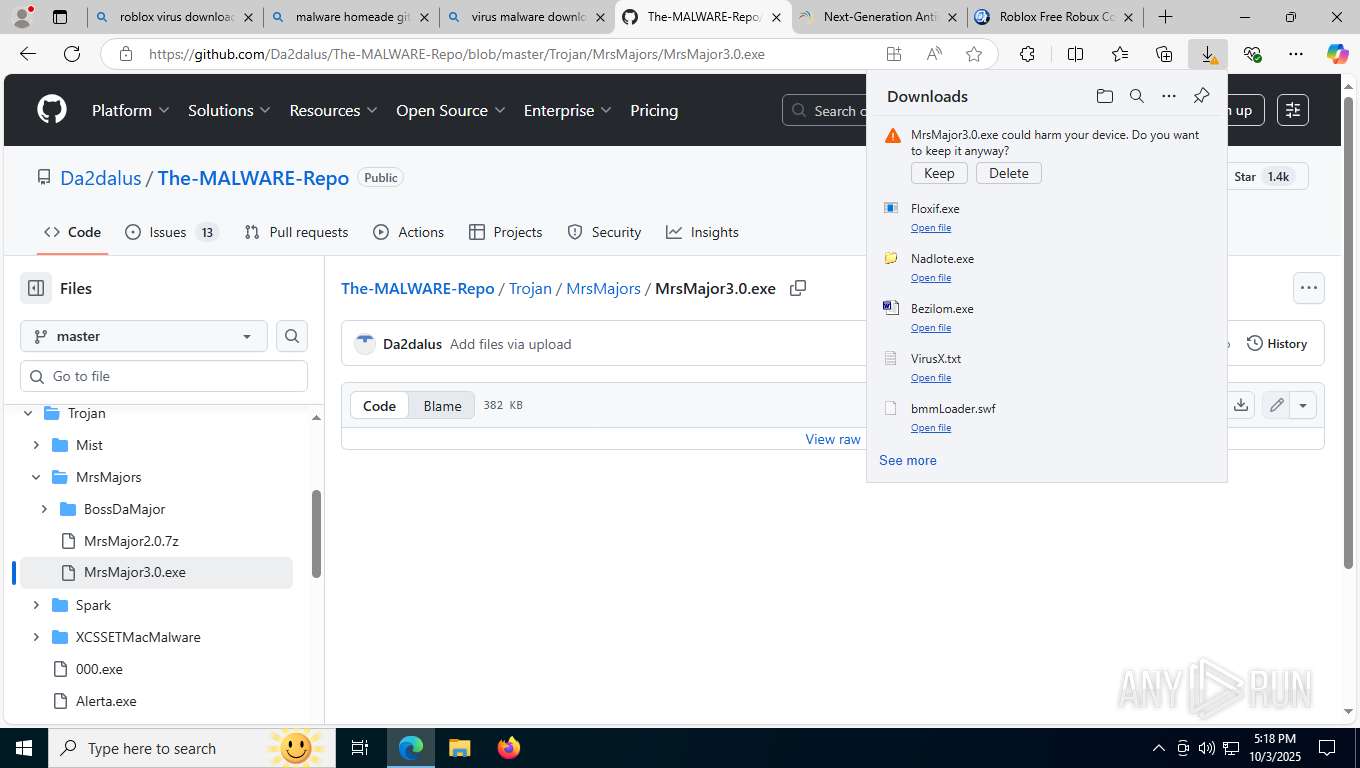
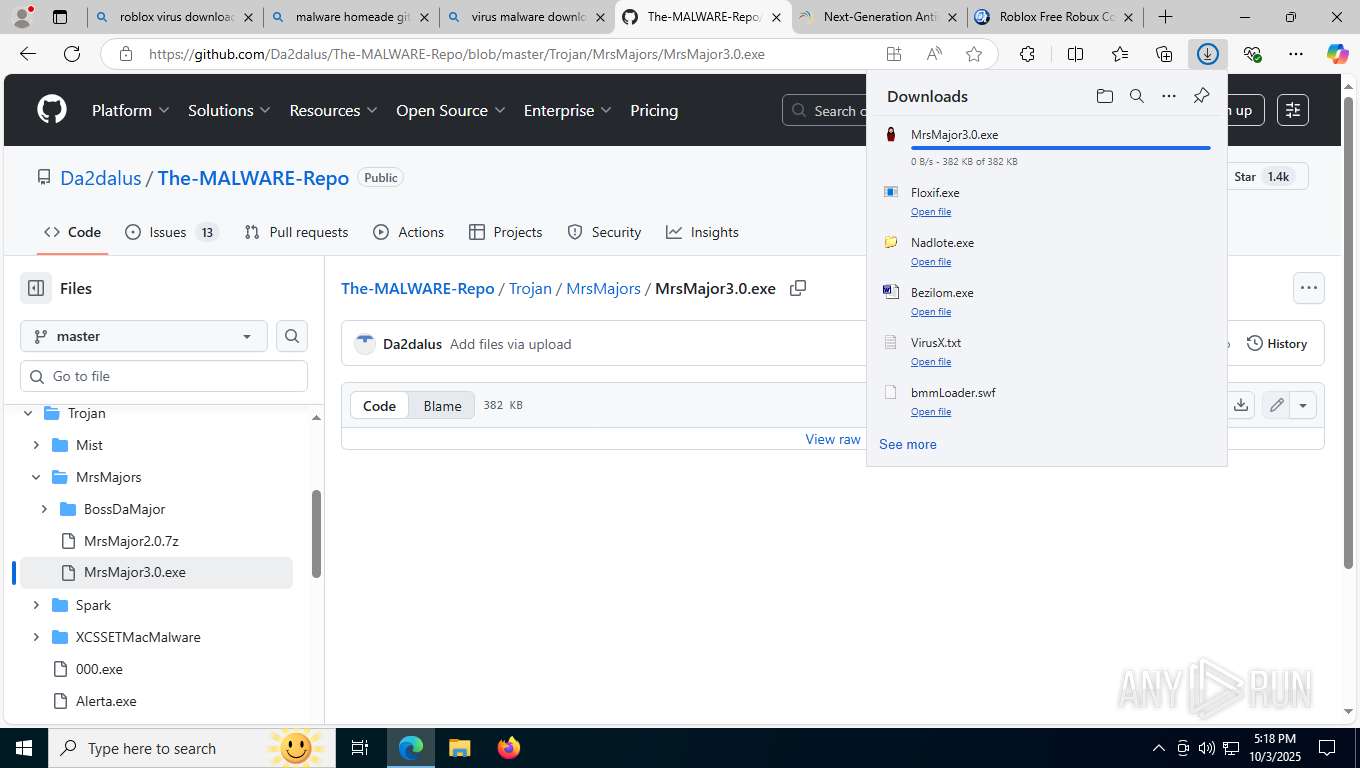
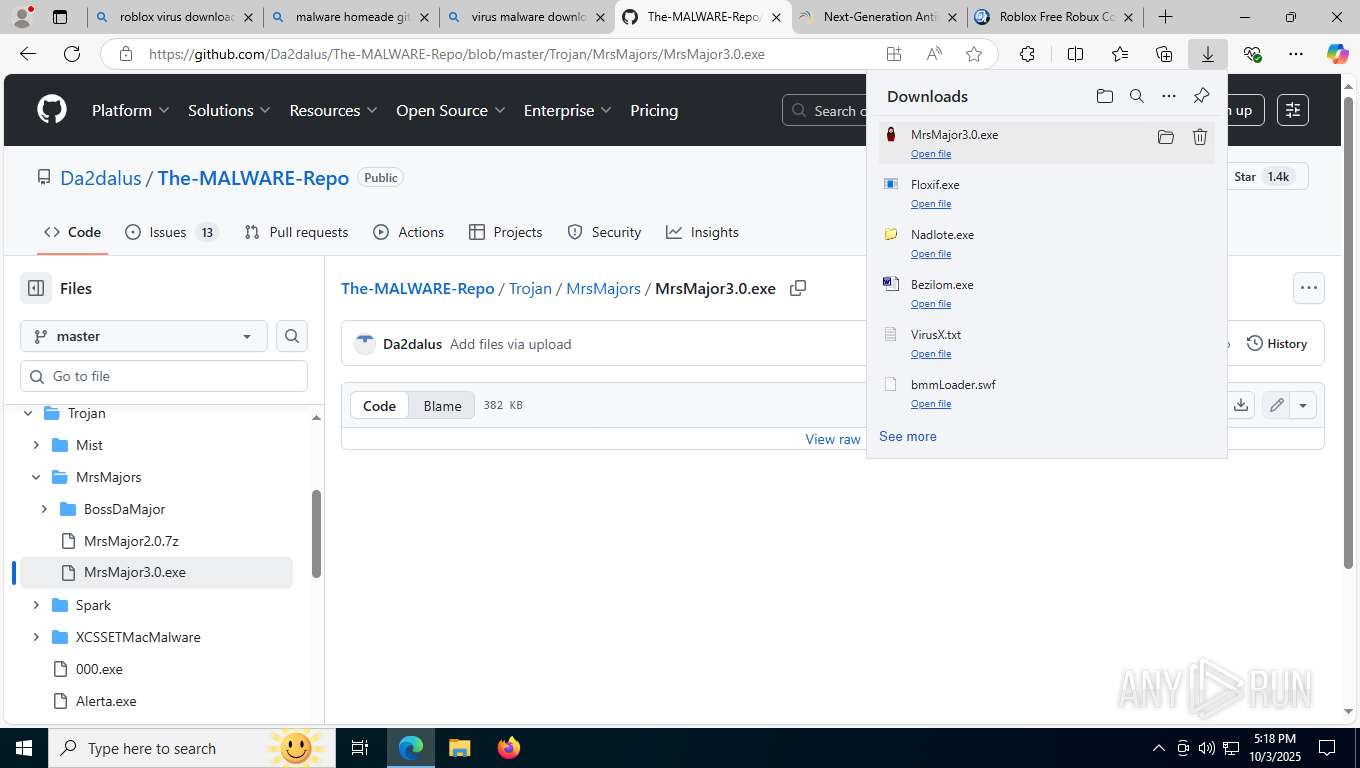
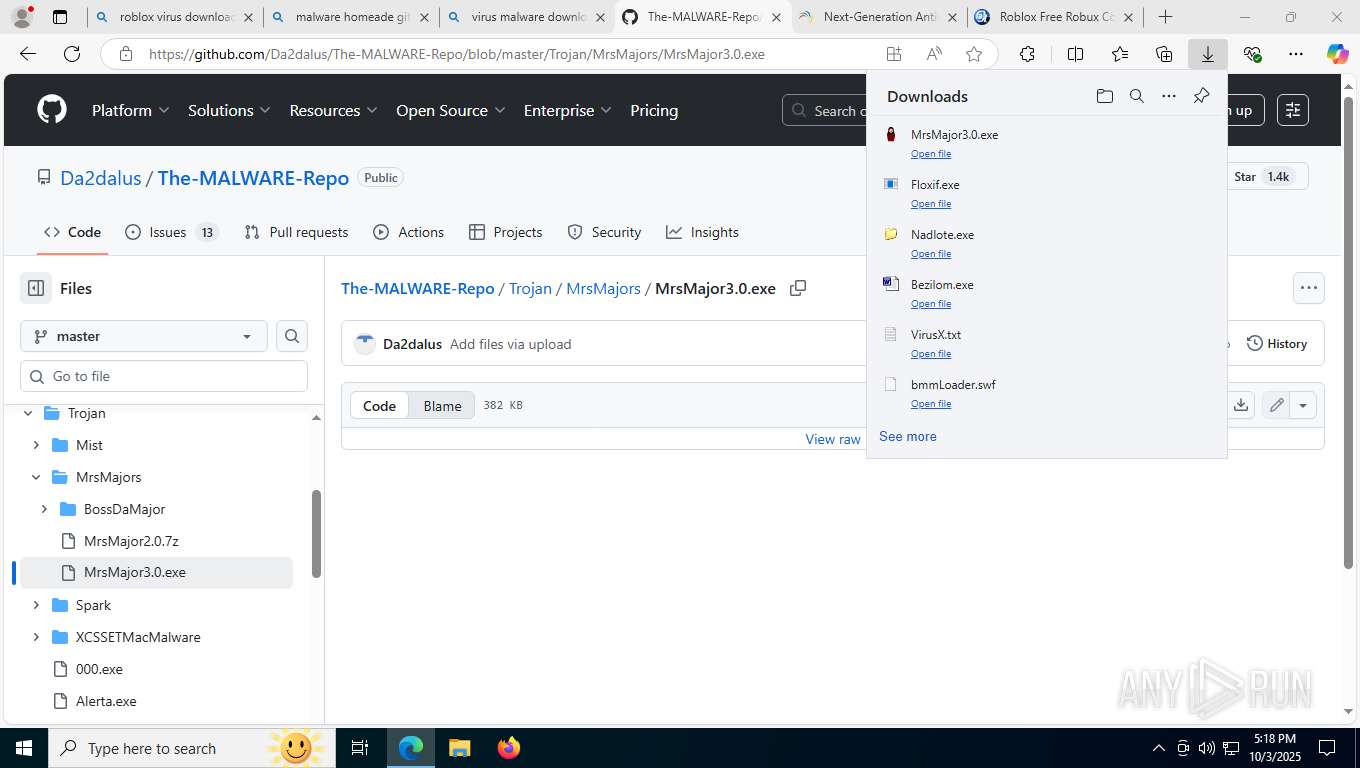
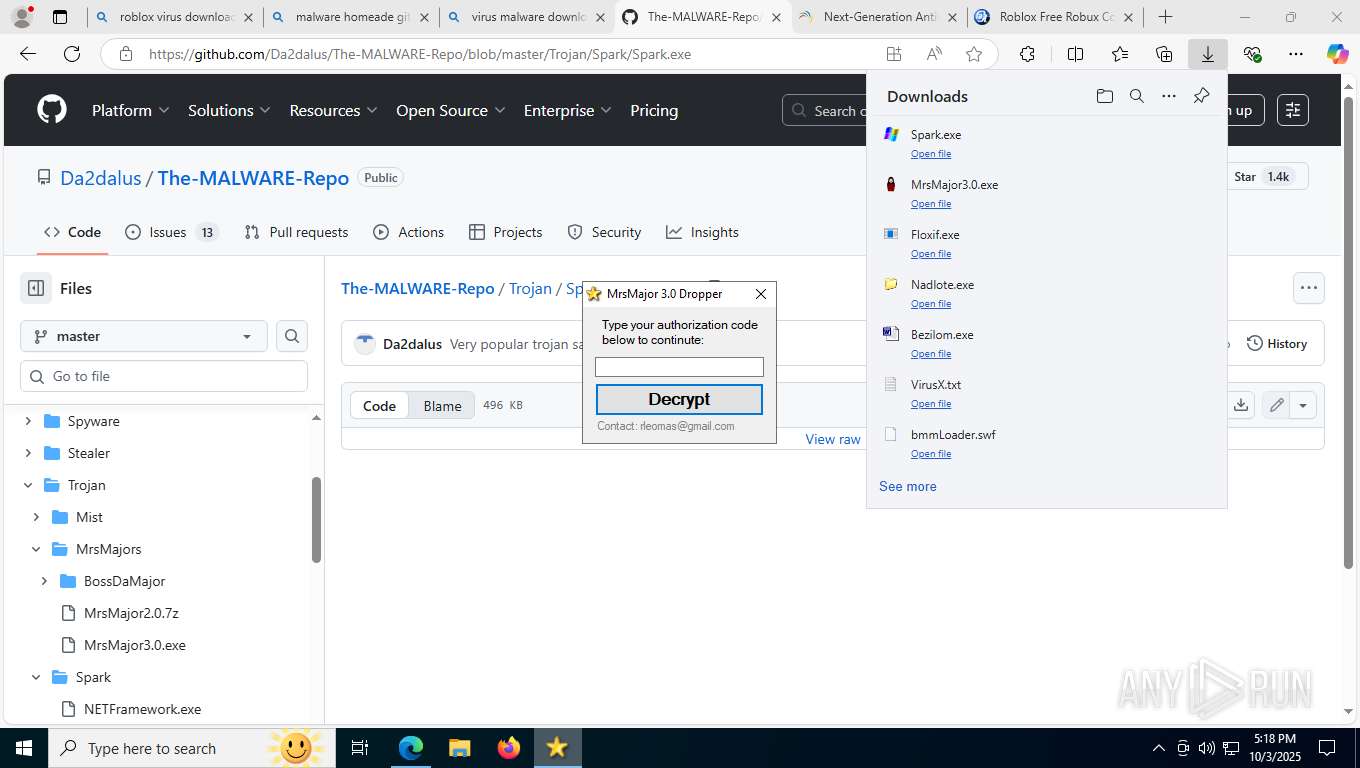
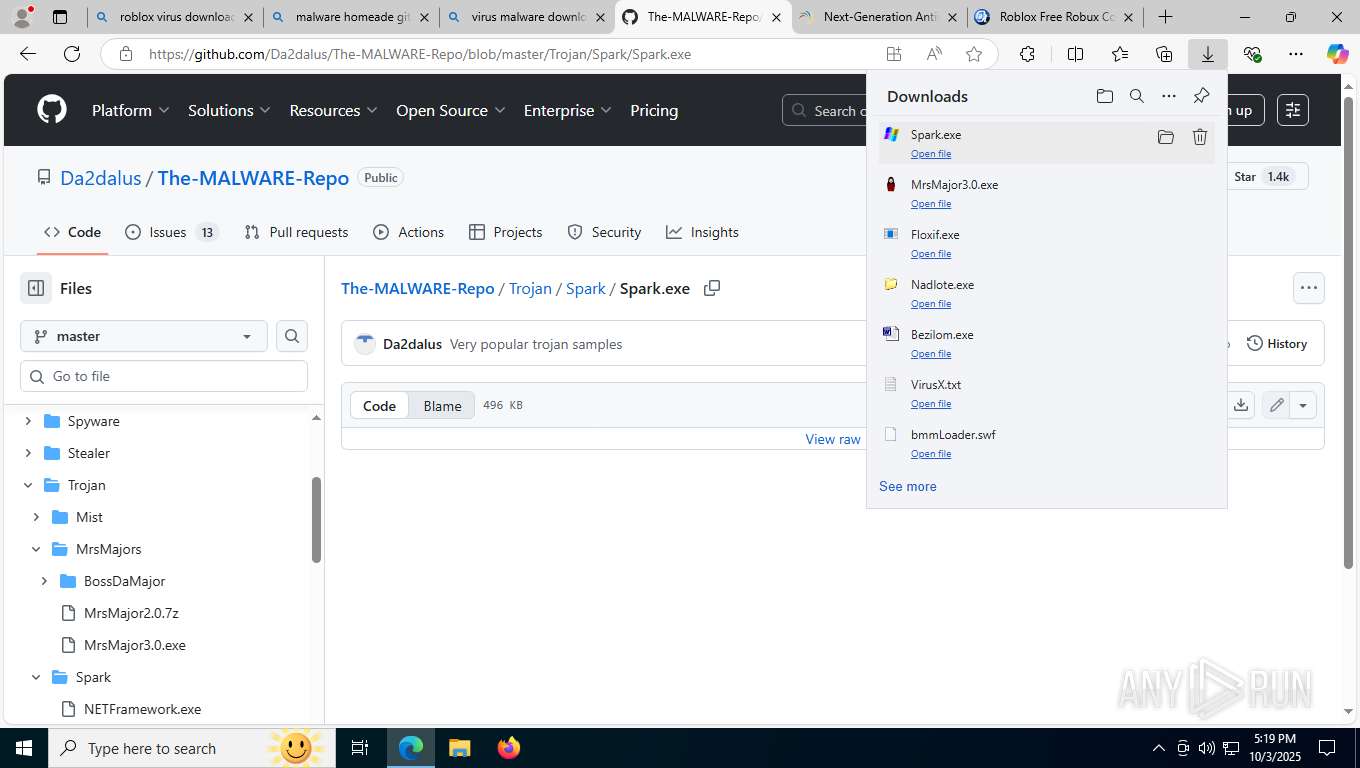
| File name: | bmmLoader.swf |
| Full analysis: | https://app.any.run/tasks/4b9b3cfb-bbf5-4291-9236-2225c890cc3e |
| Verdict: | Malicious activity |
| Analysis date: | October 03, 2025, 17:14:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-shockwave-flash |
| File info: | Macromedia Flash data (compressed), version 34 |
| MD5: | 596FE91D1A3A502C6977D49103D18C0B |
| SHA1: | 014D8CA61DBAE4B9FF05E1F362F14F4AC2E54A16 |
| SHA256: | 75D95776924DDE30B89F026EC452AA114F21EAF583A27AC235F84D9C0627A4D3 |
| SSDEEP: | 98304:+pAbN6/cL5tfKhwkCWk8MPIczEeSNGQhnla+Dmd04iXNYgOJVEO7QZ8eLDHxyHI2:/PKvQn |
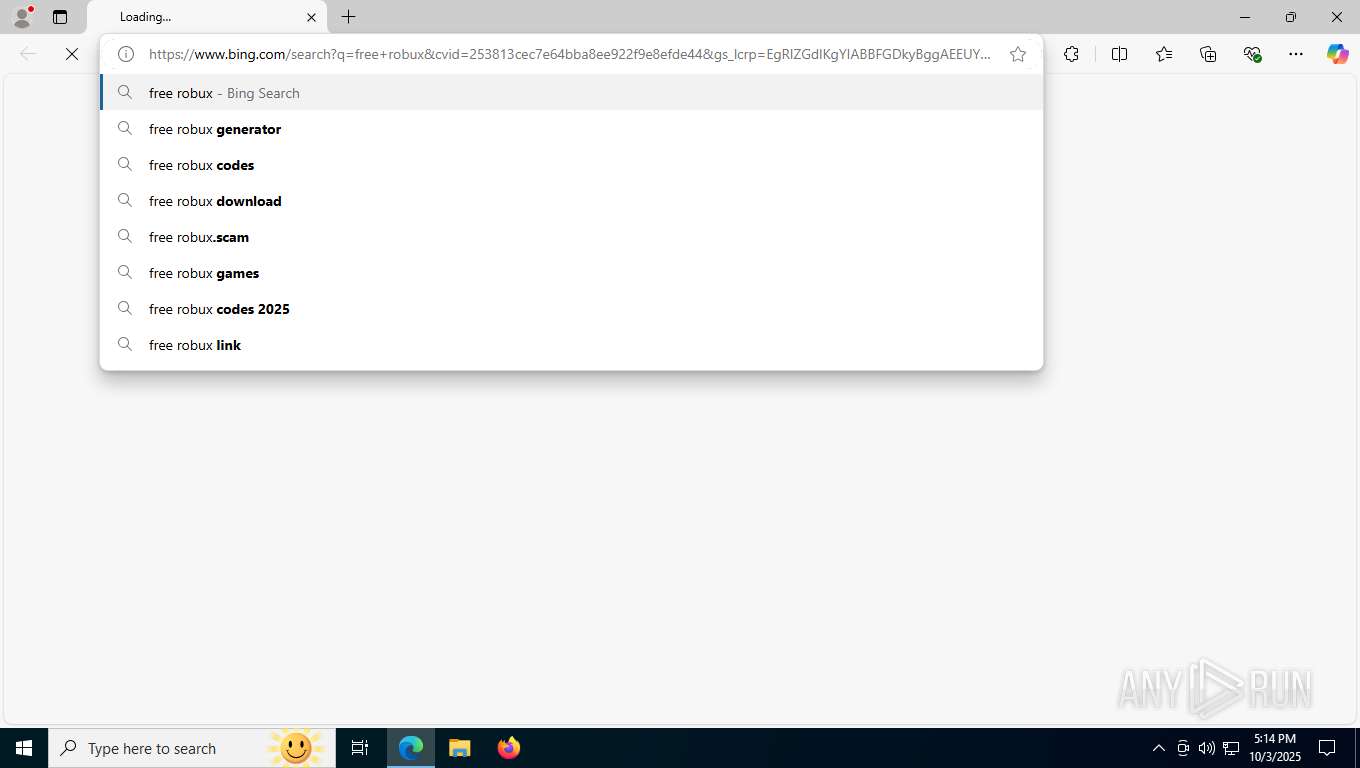
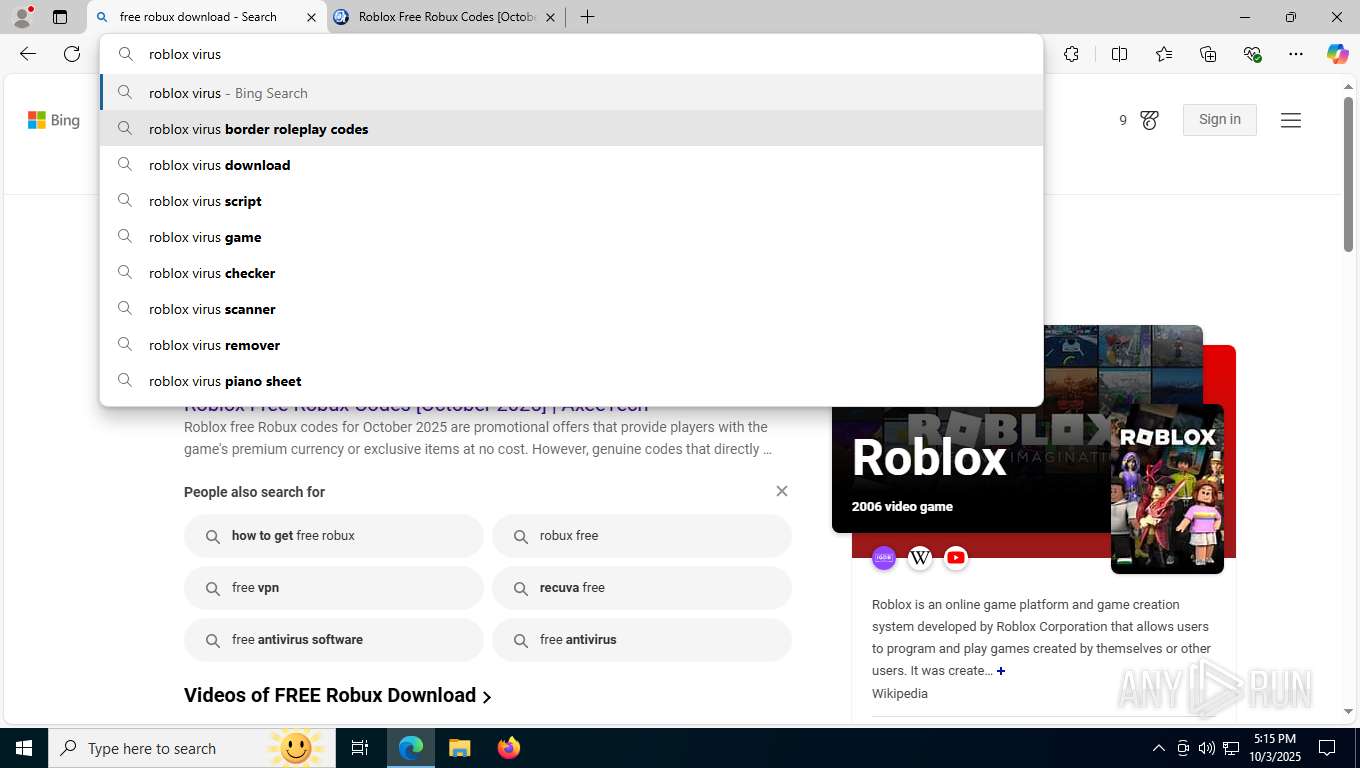
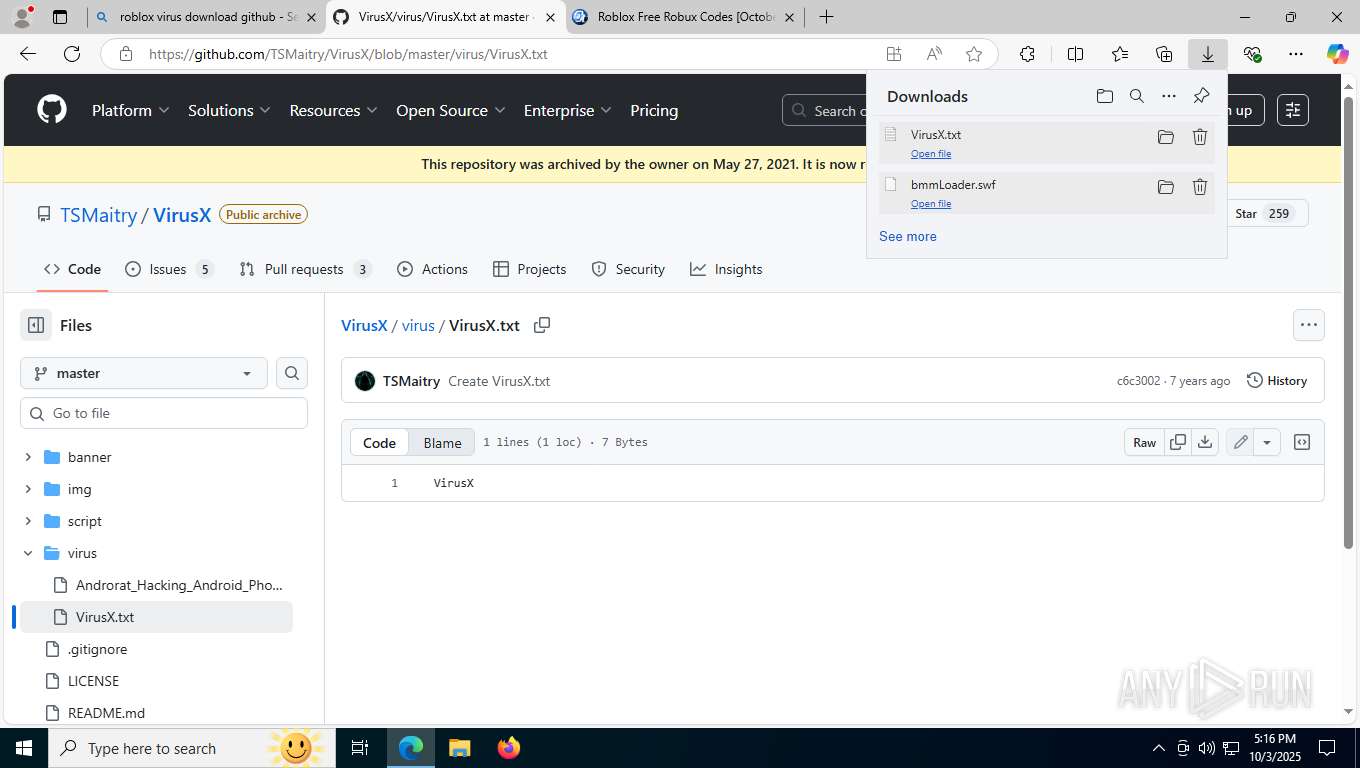
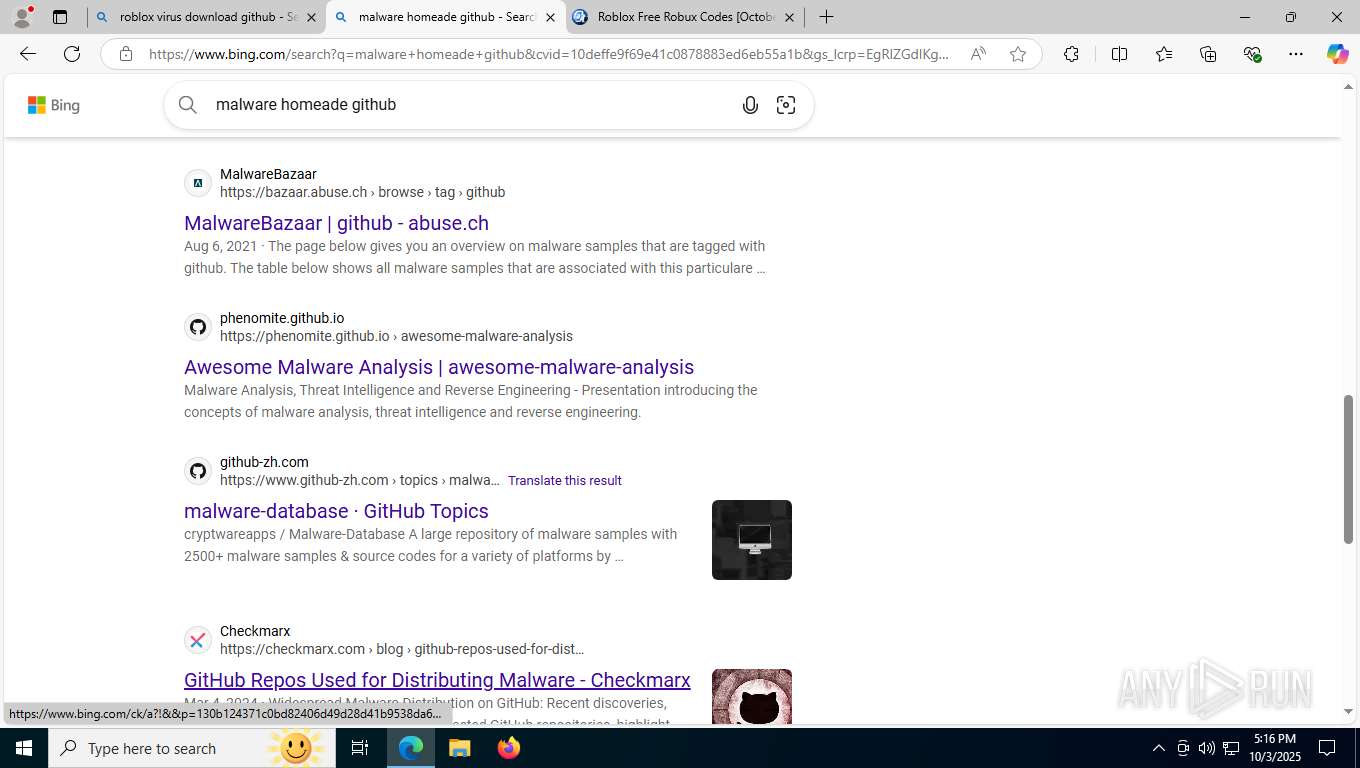
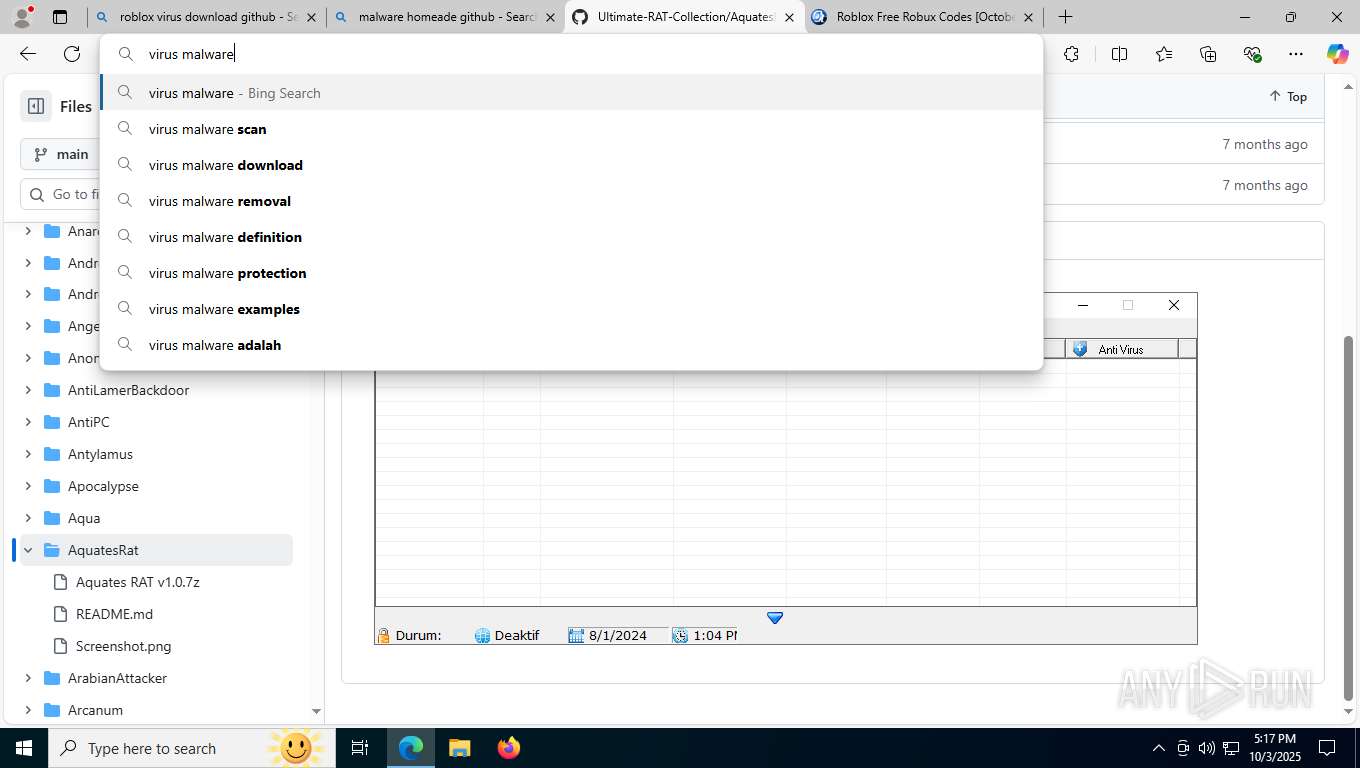
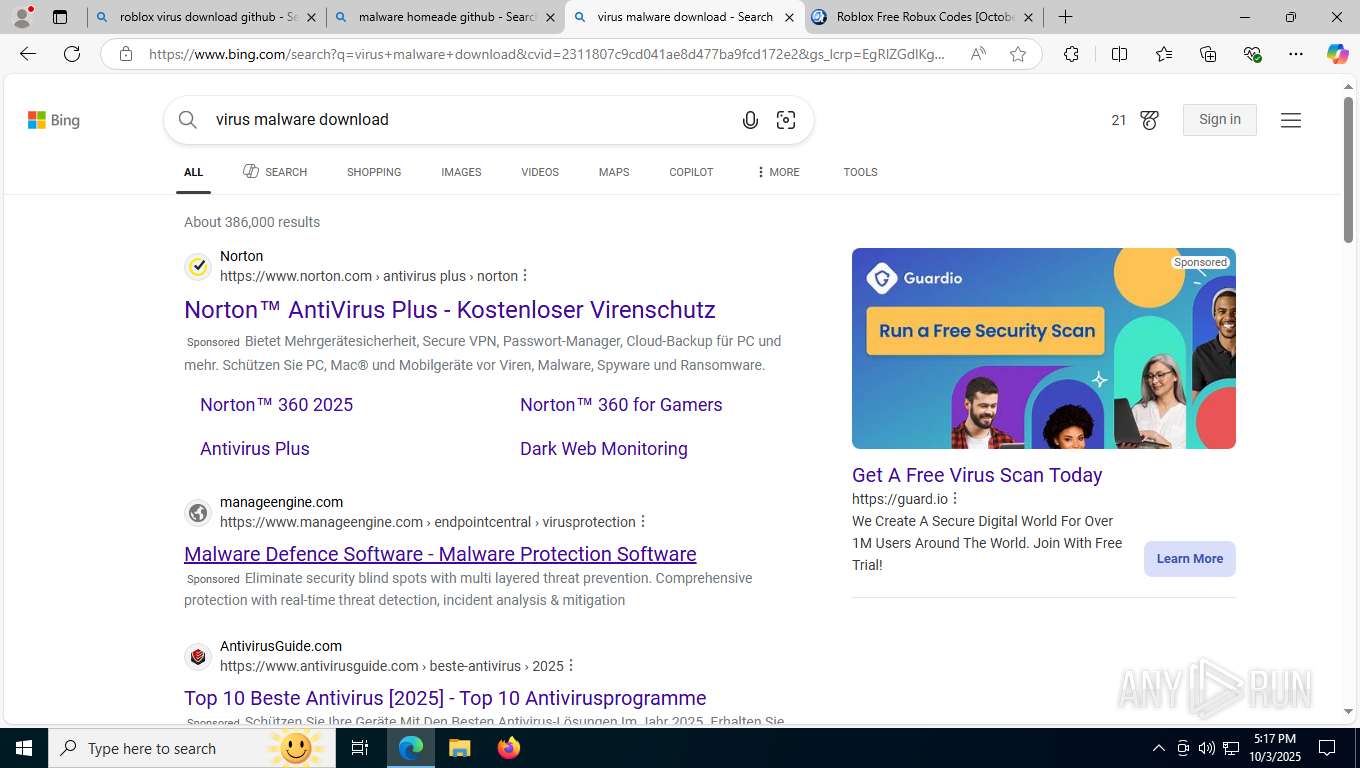
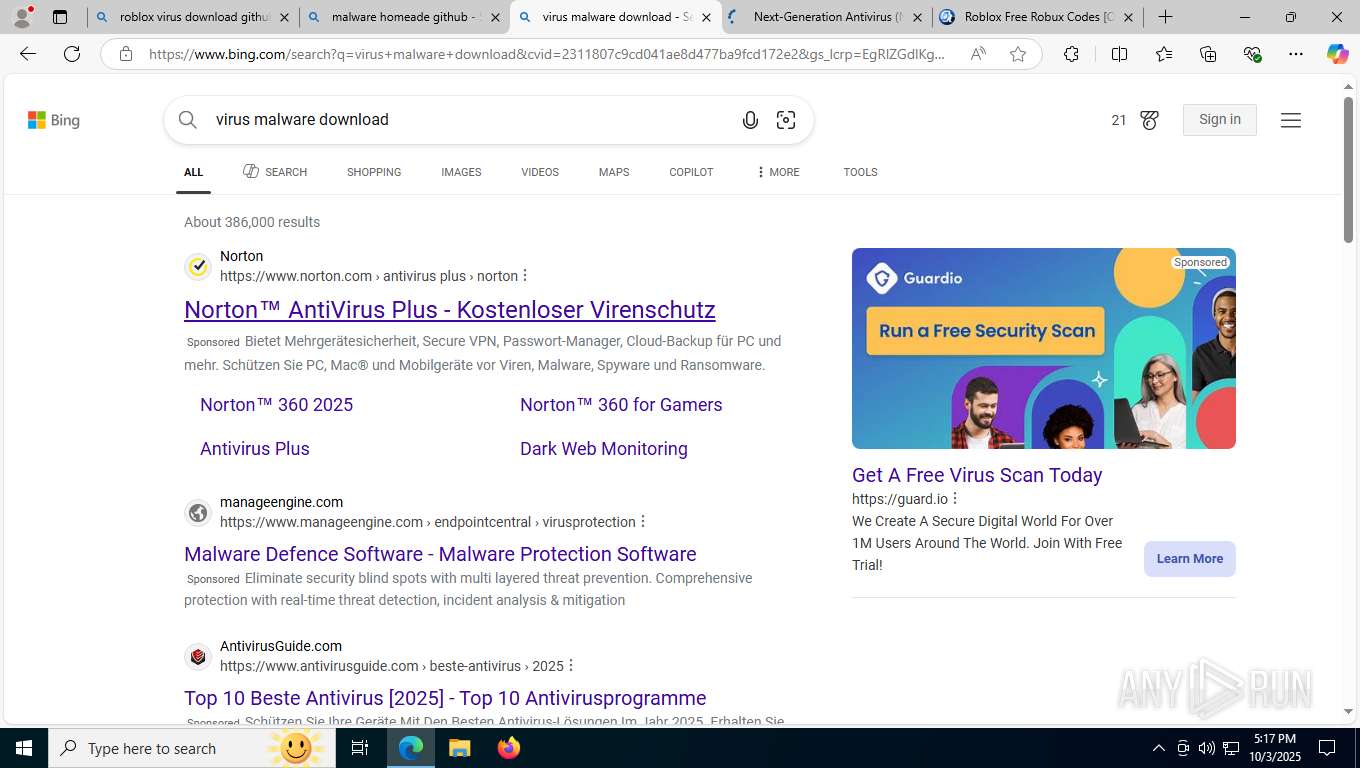
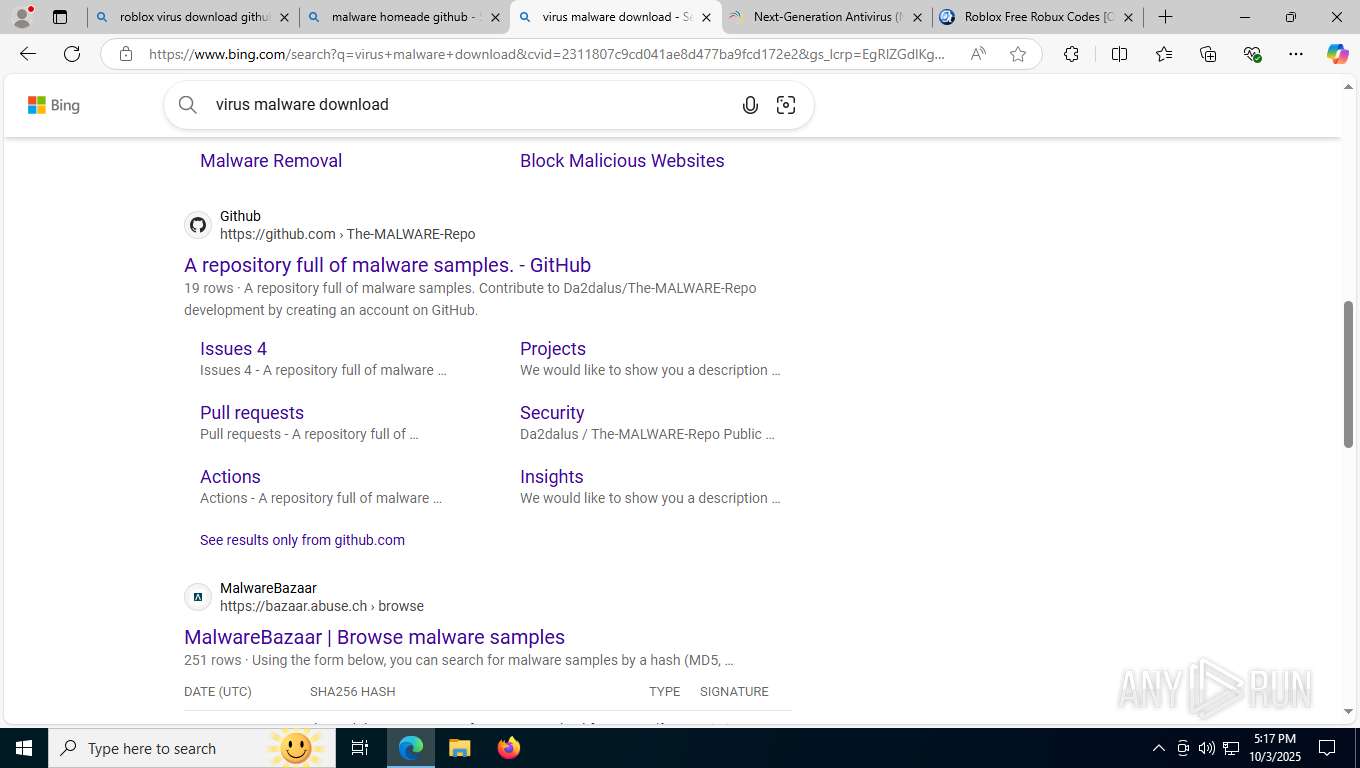
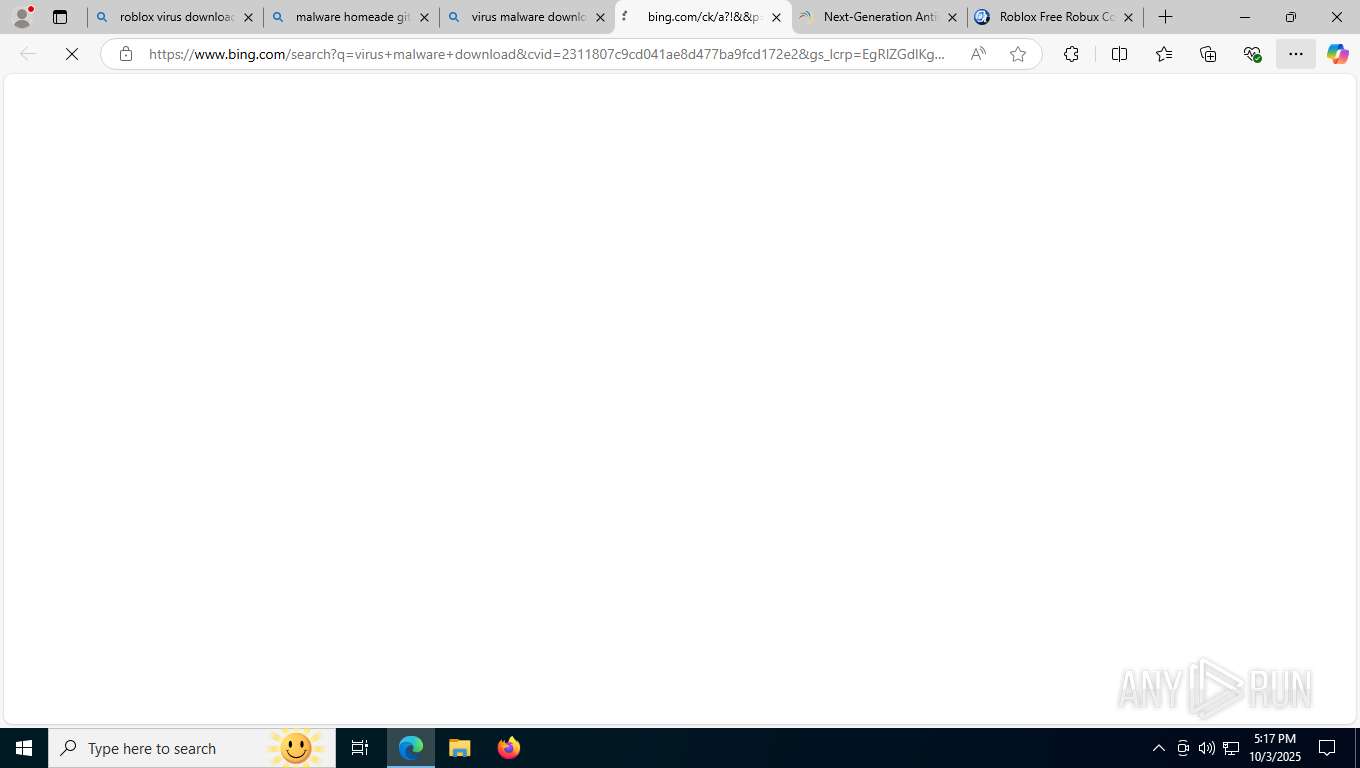
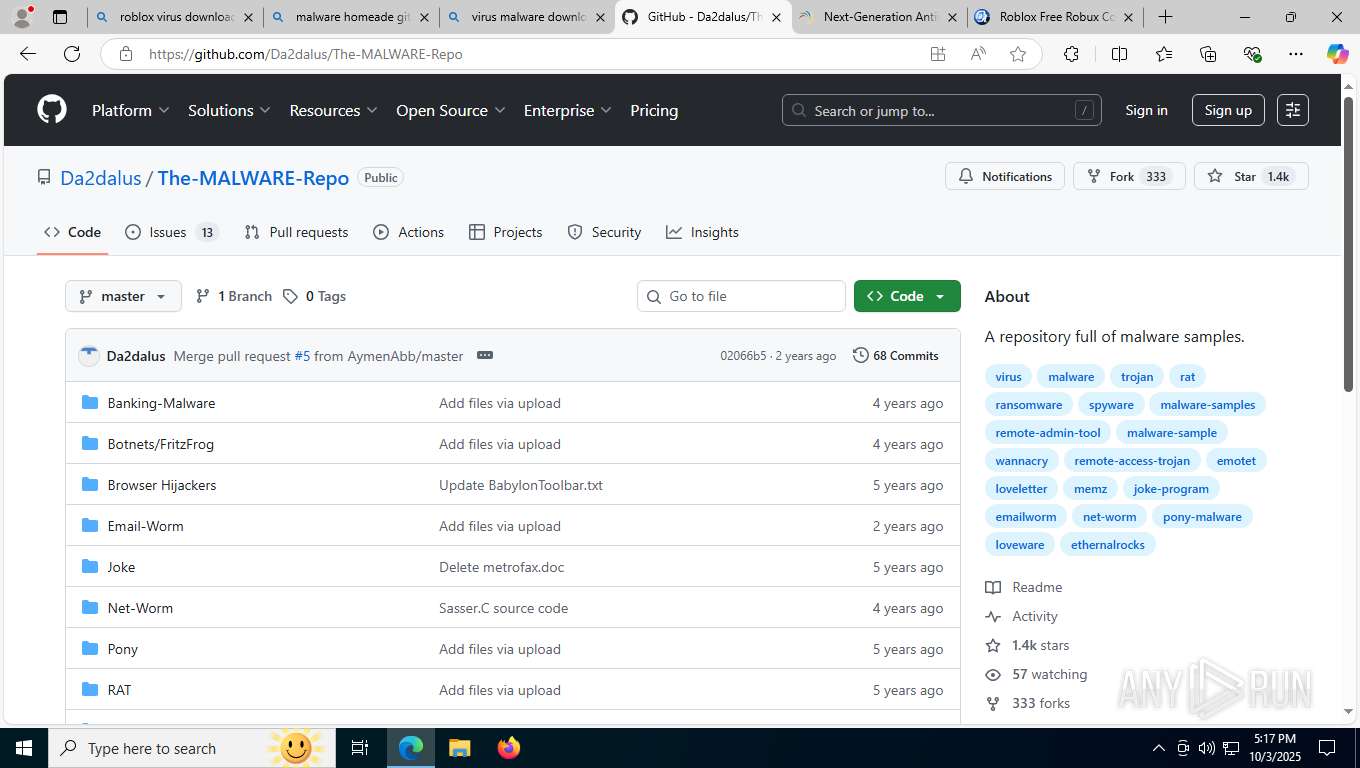
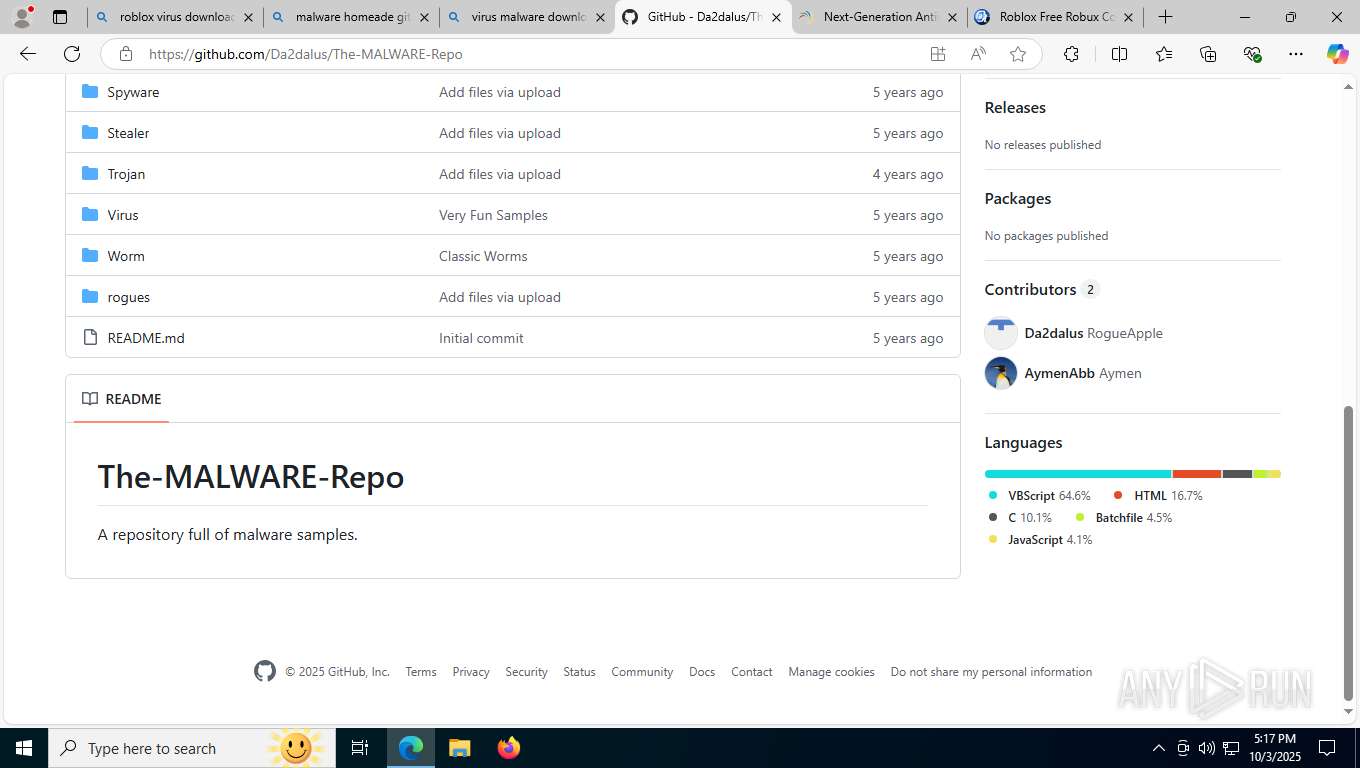
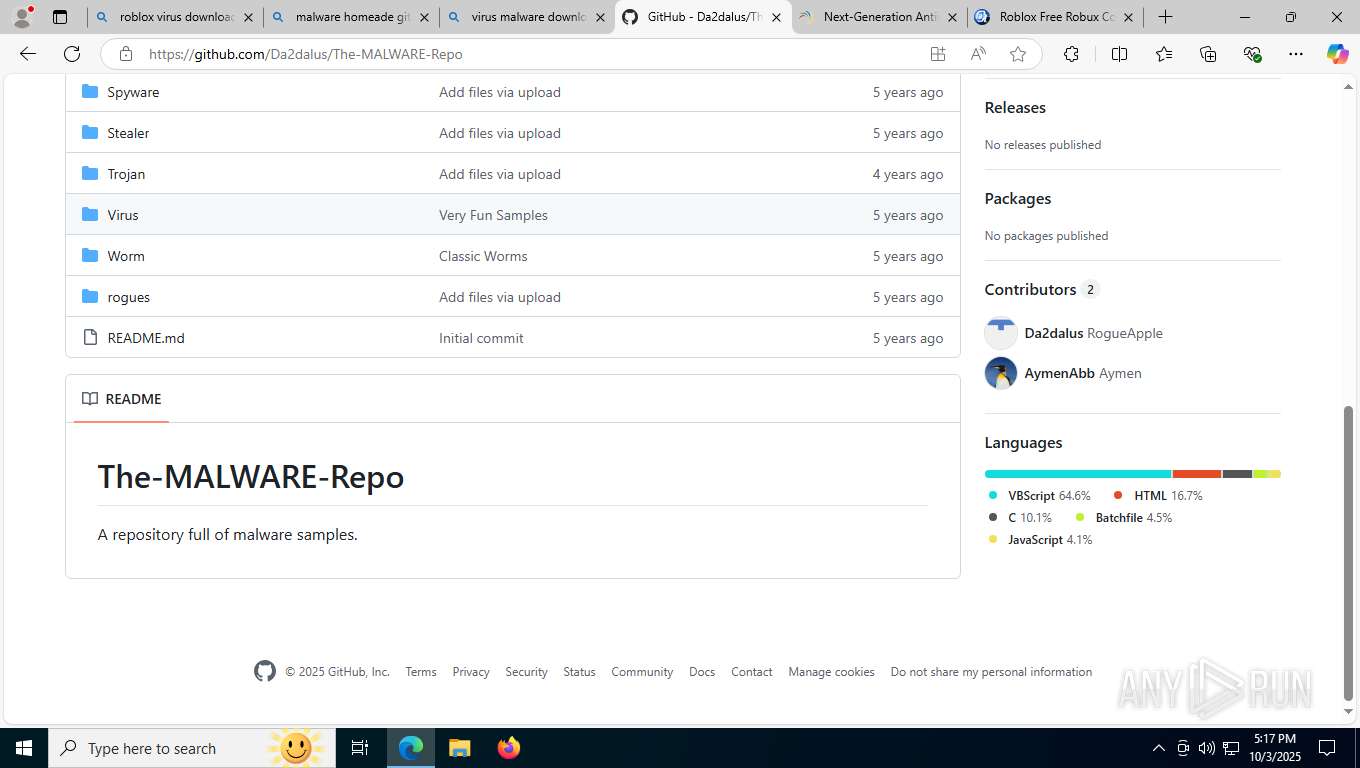
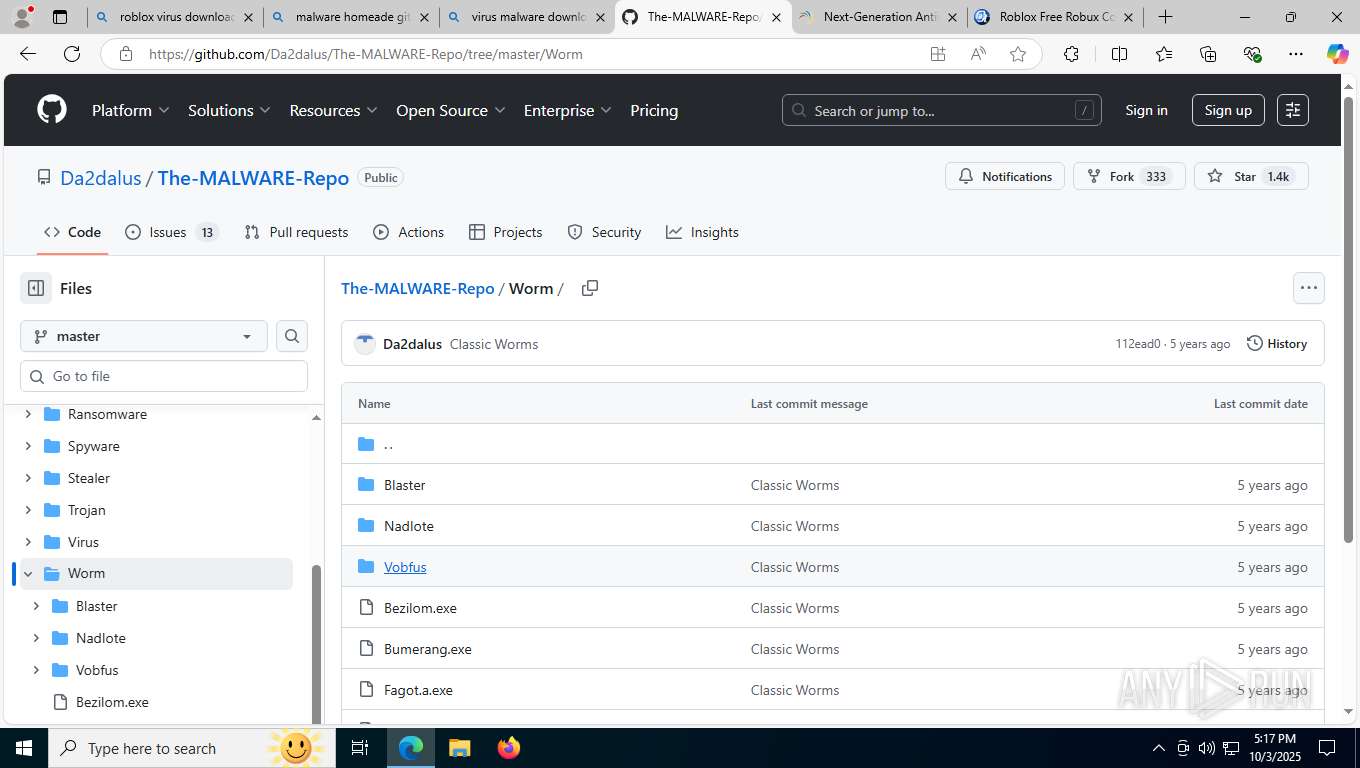
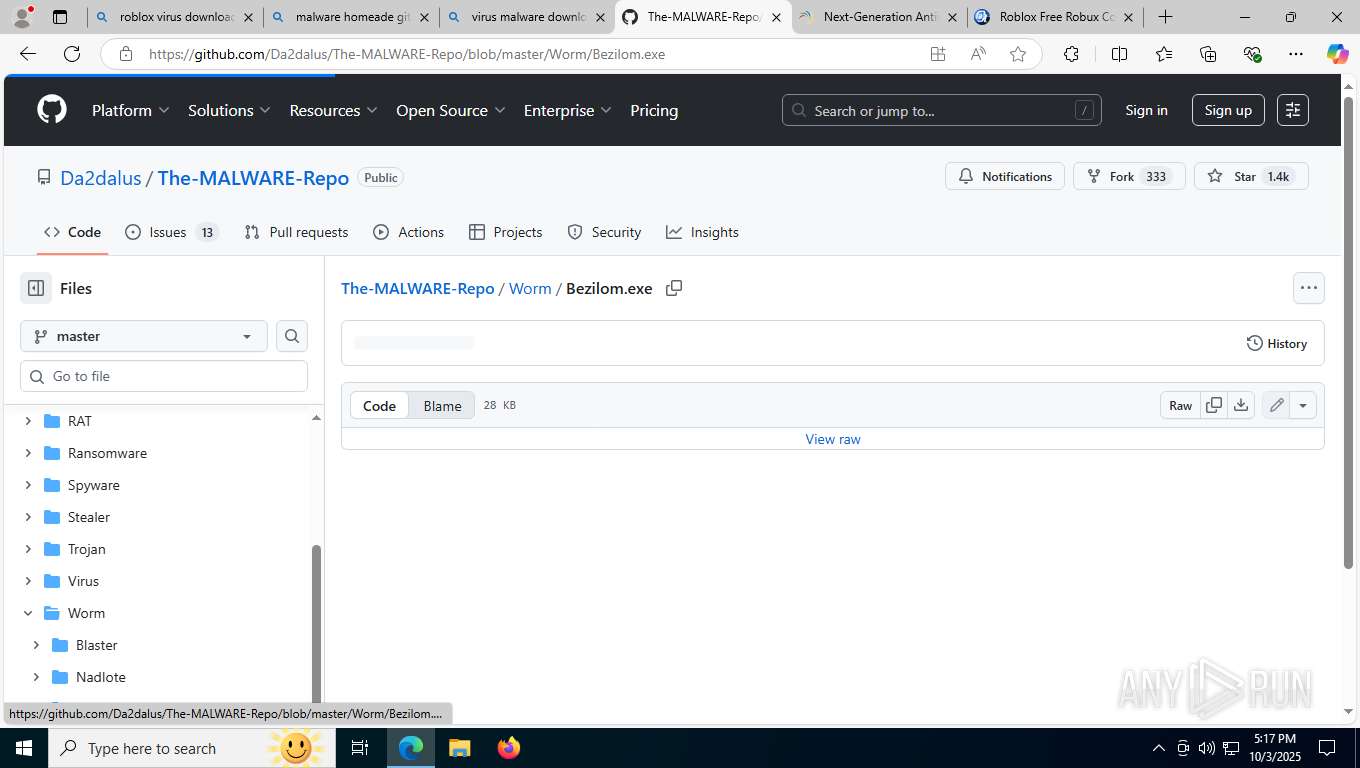
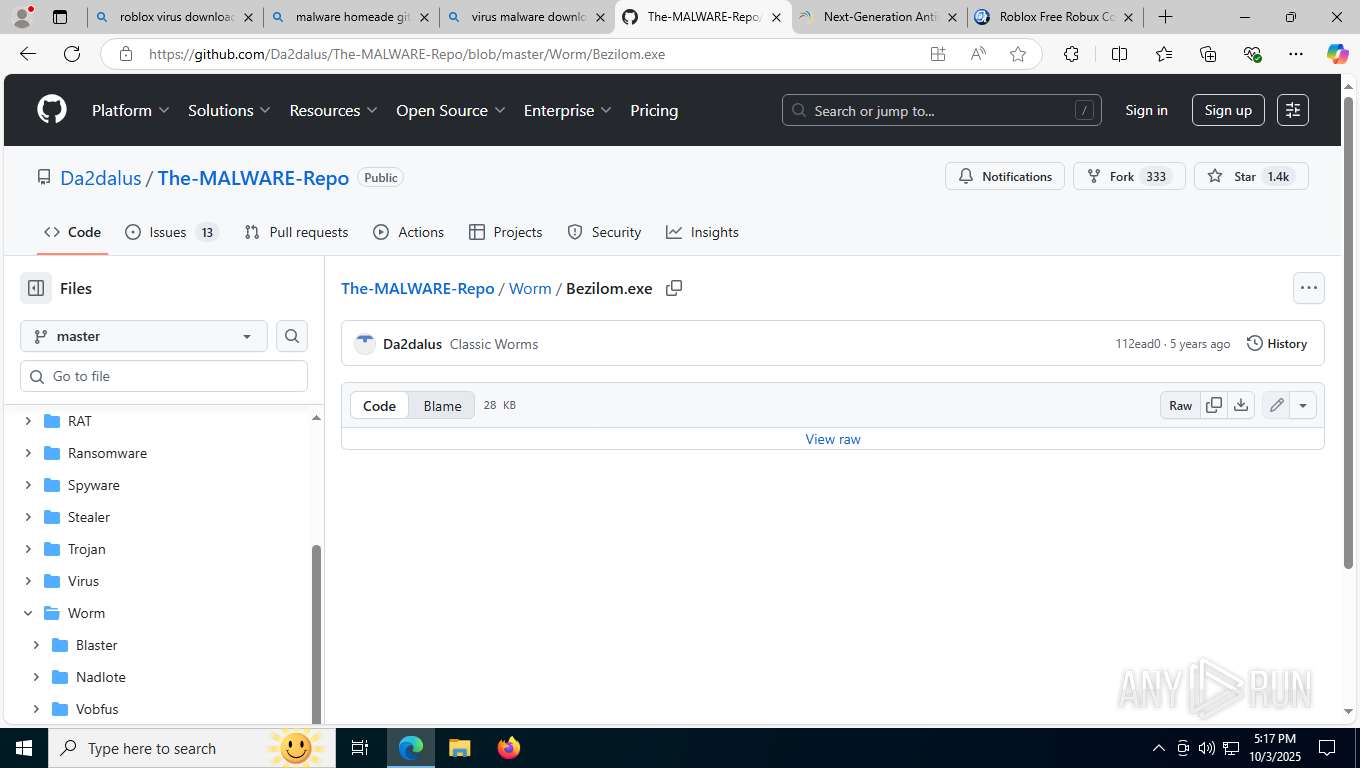
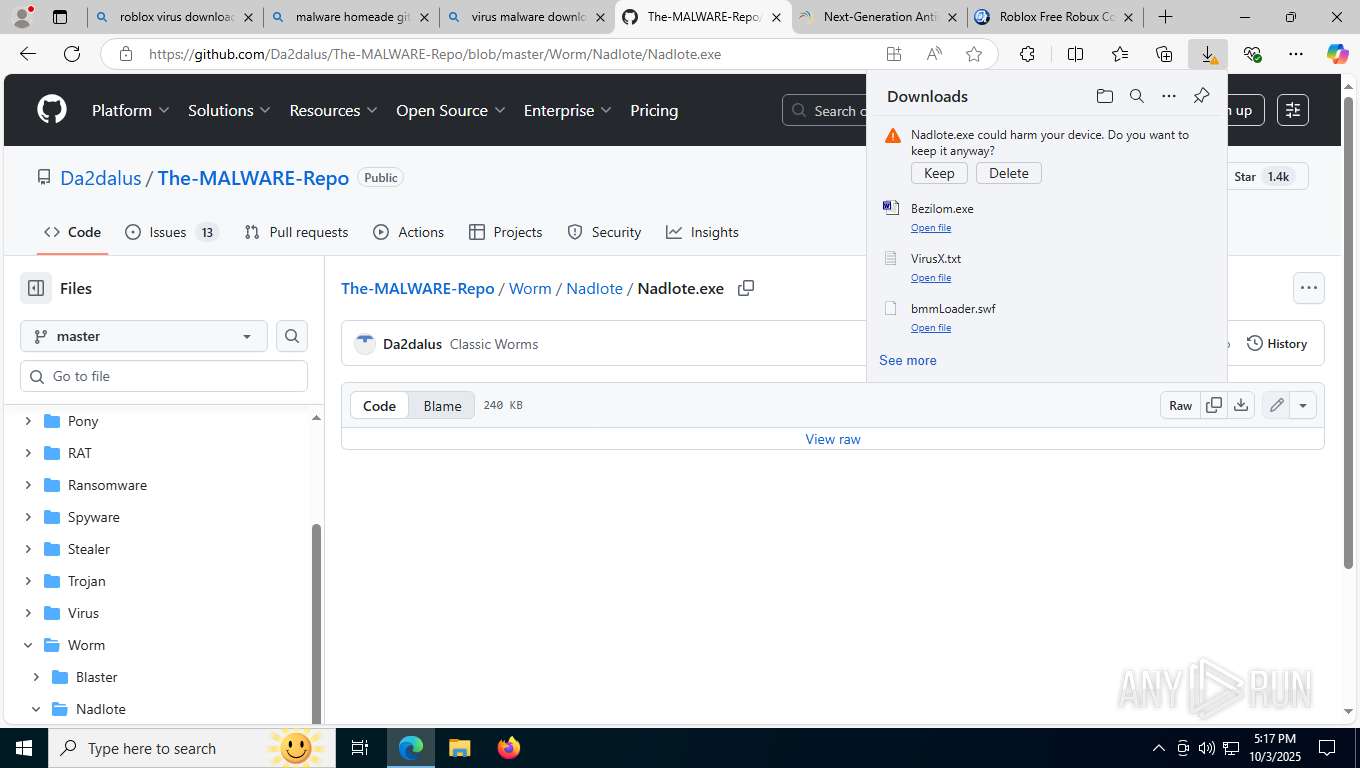
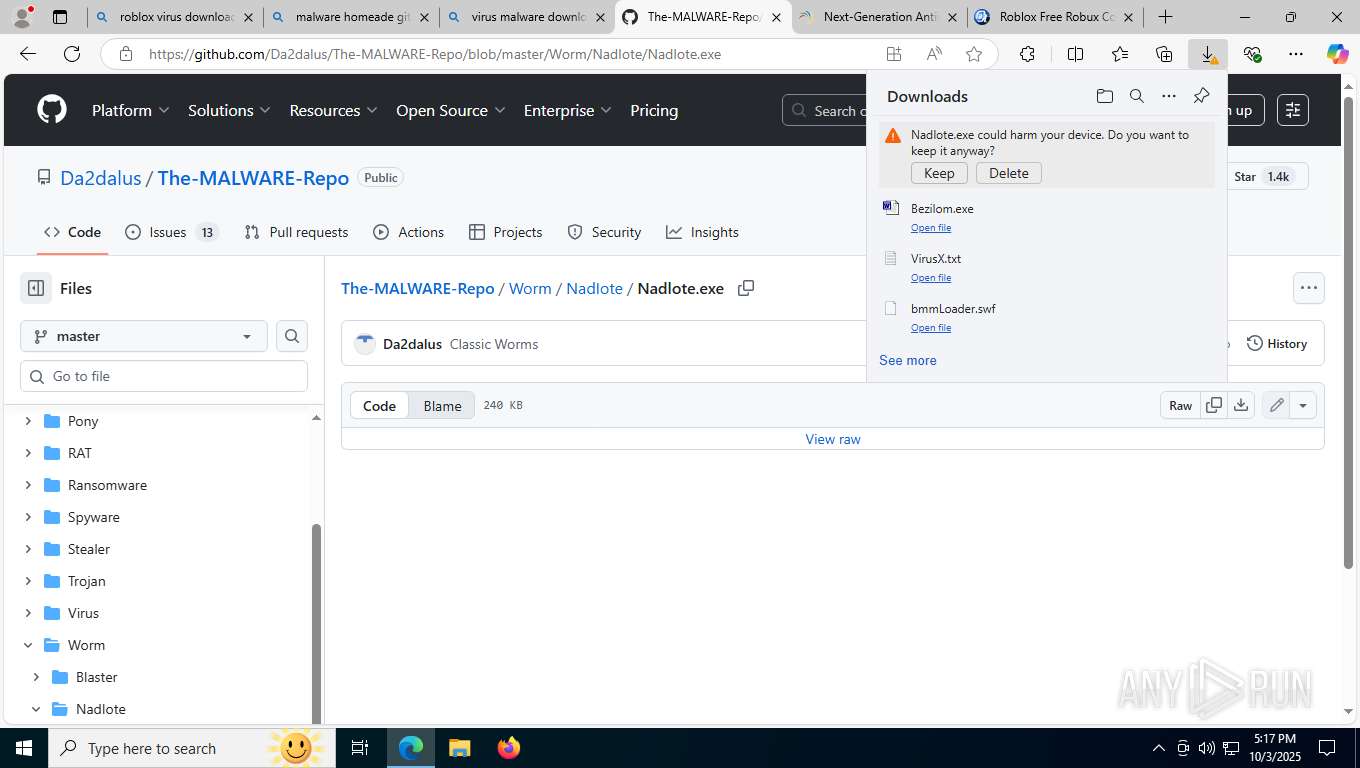
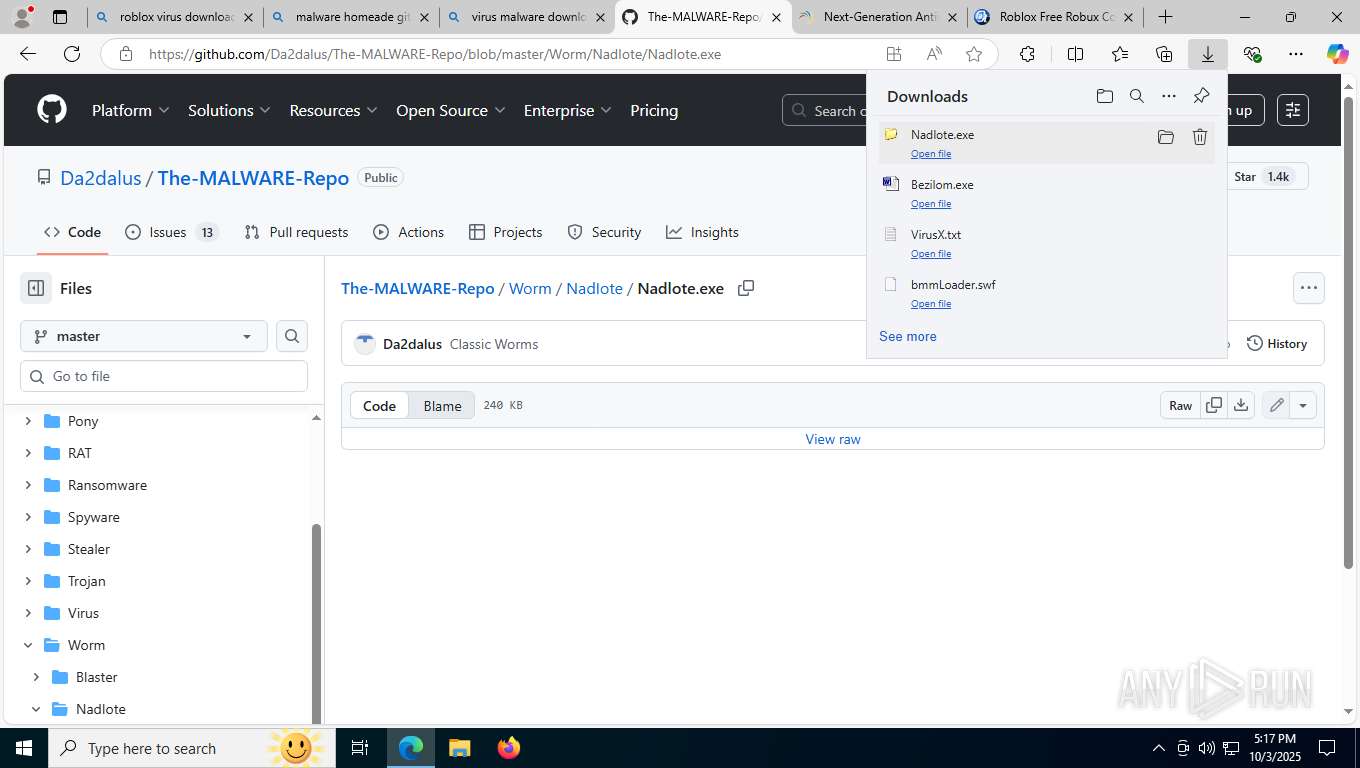
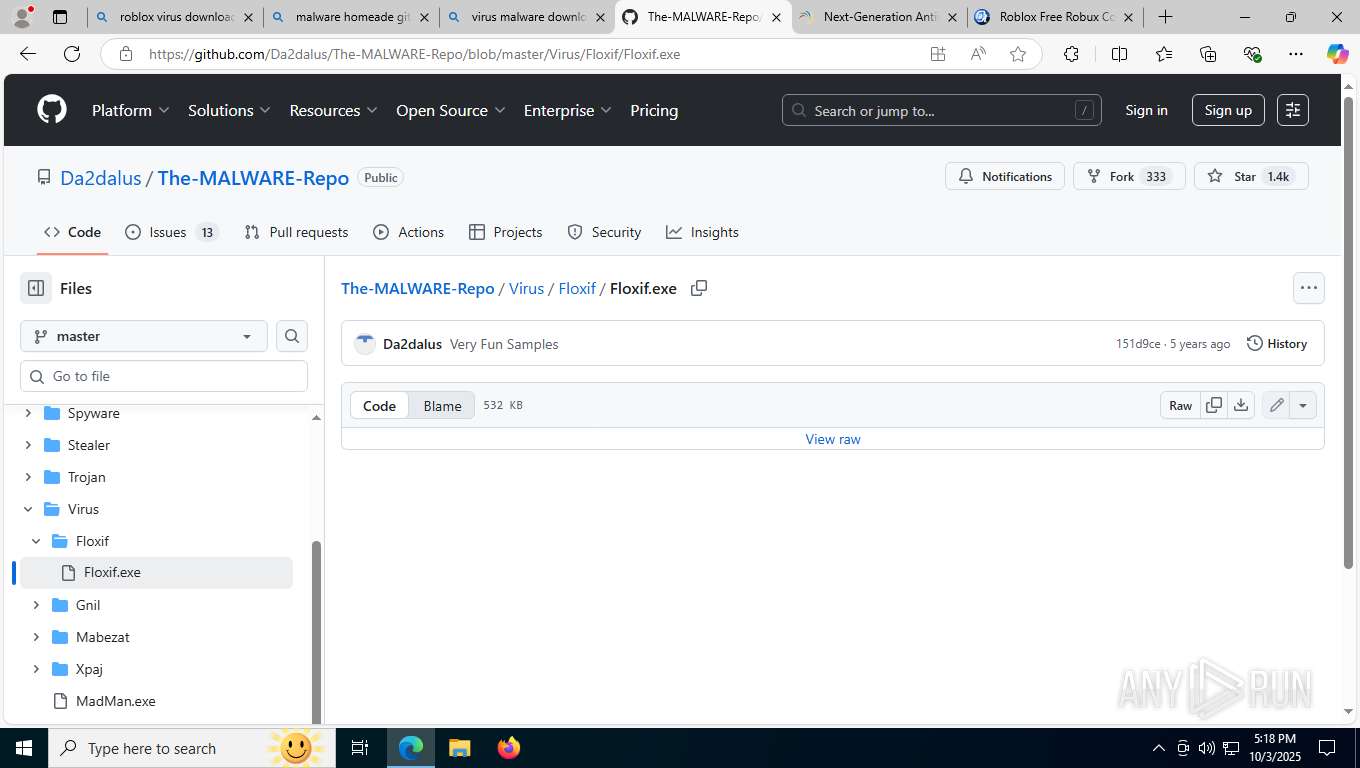
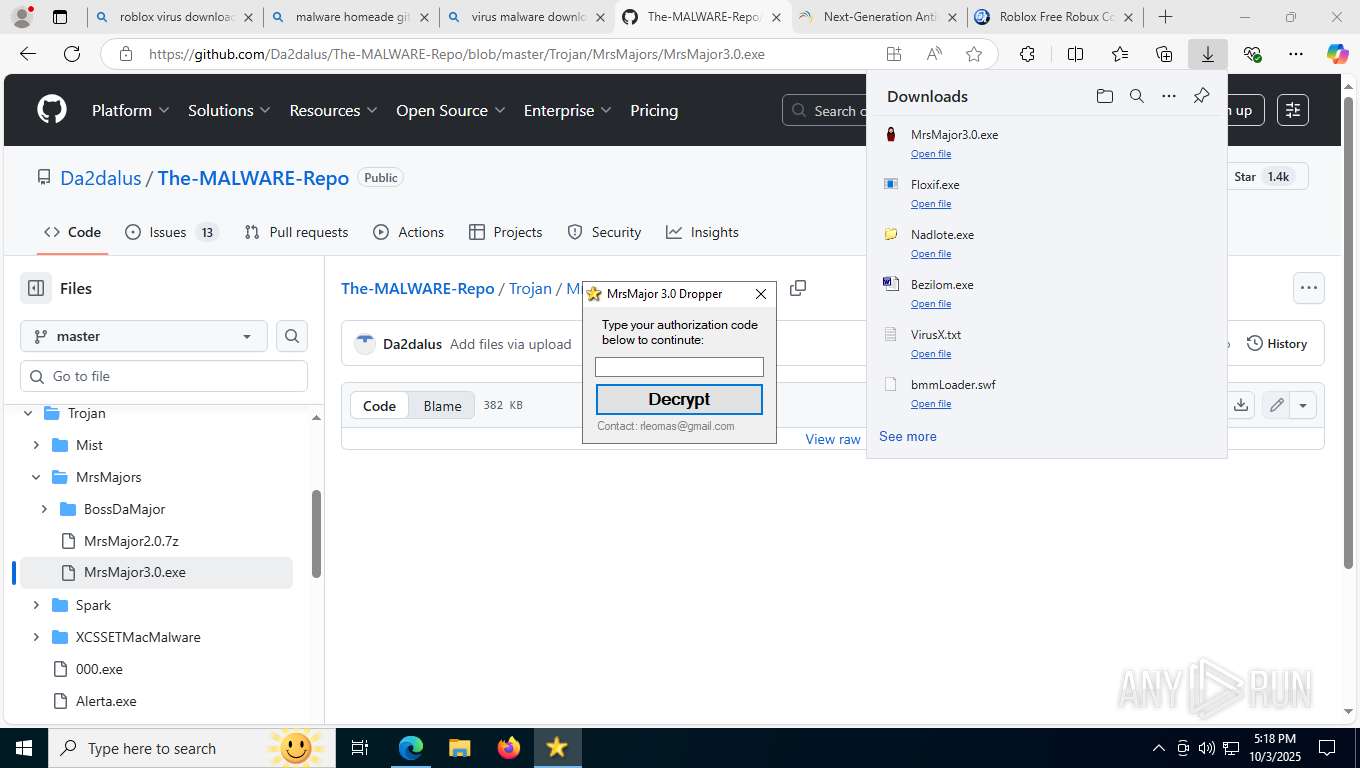
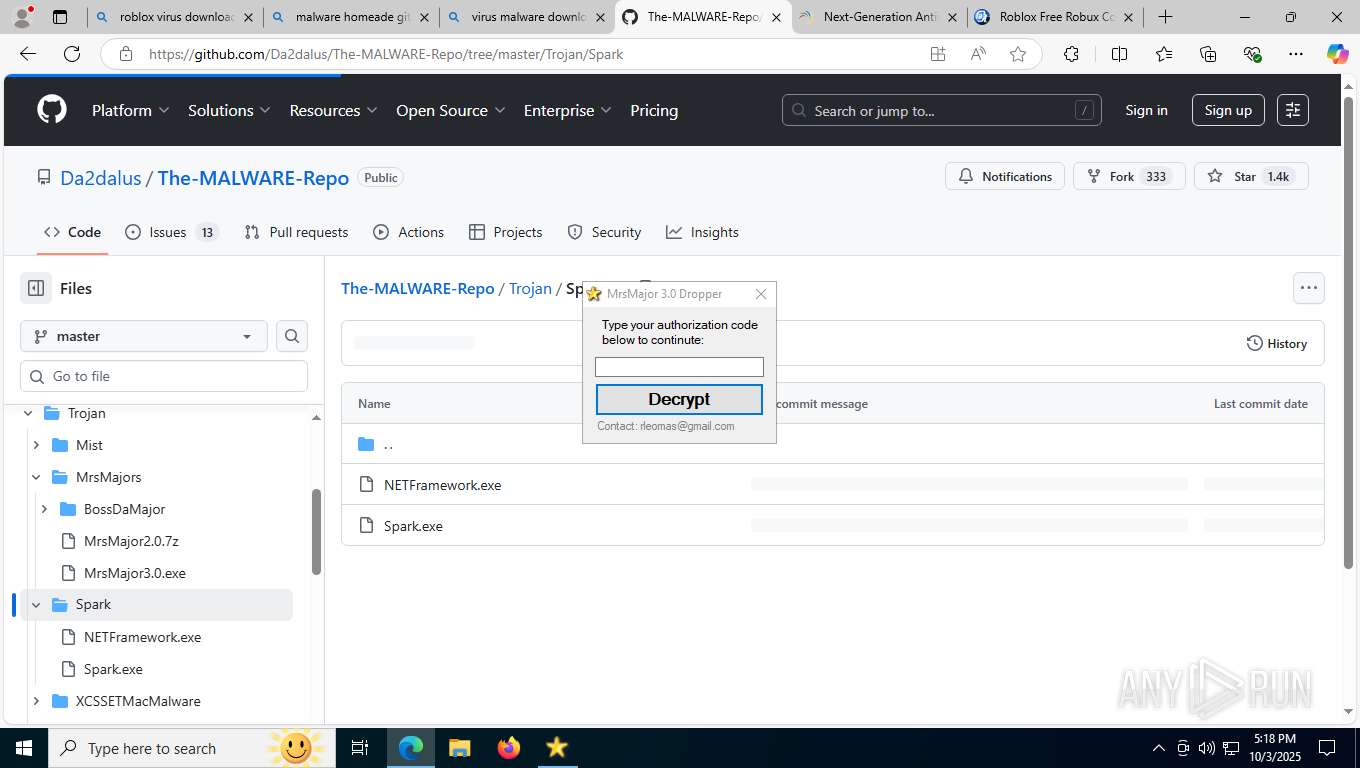
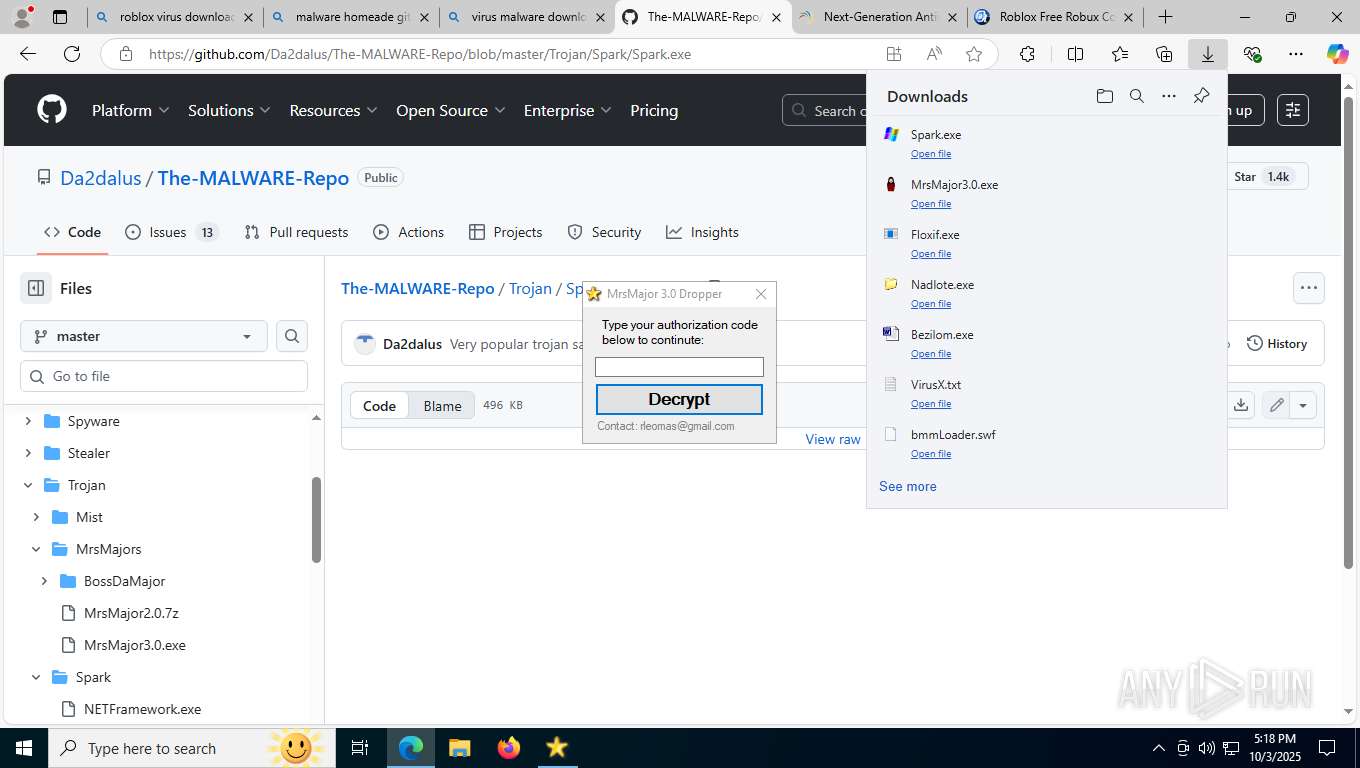
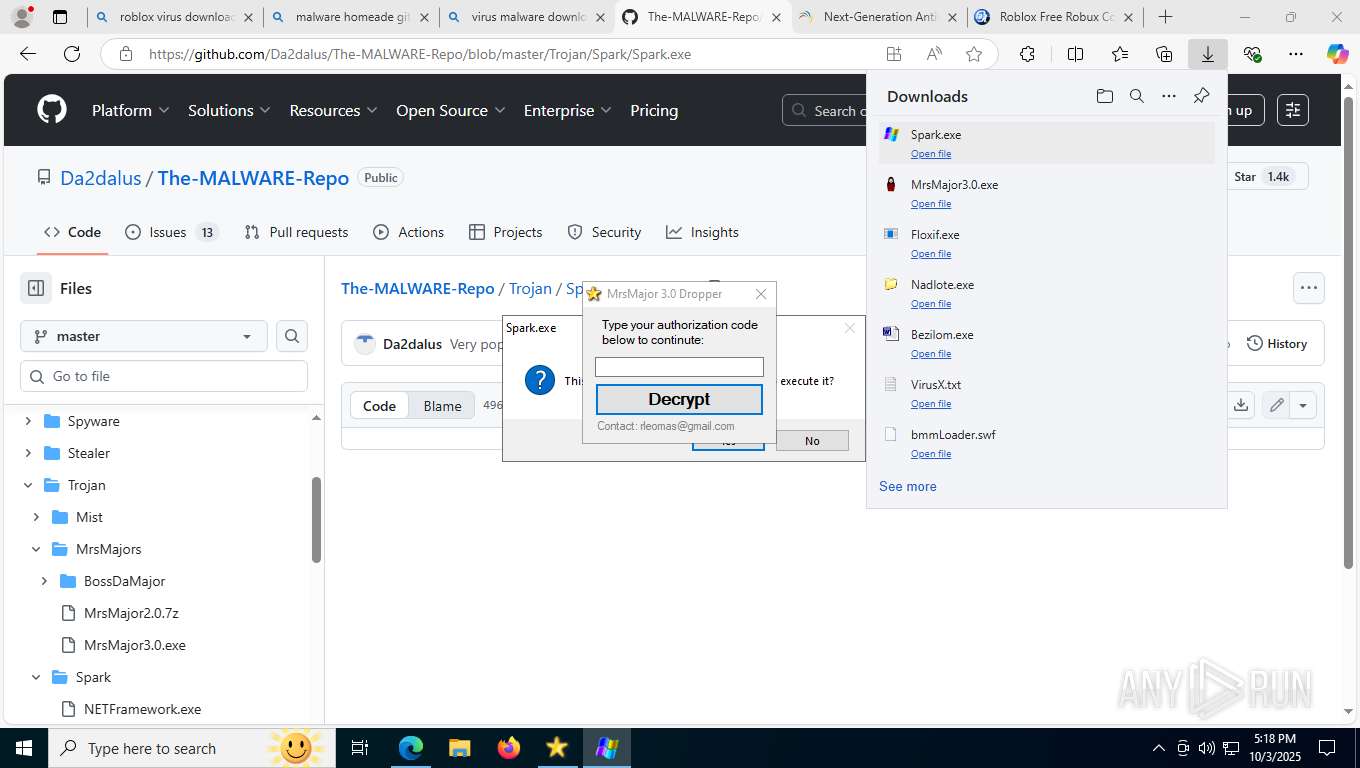
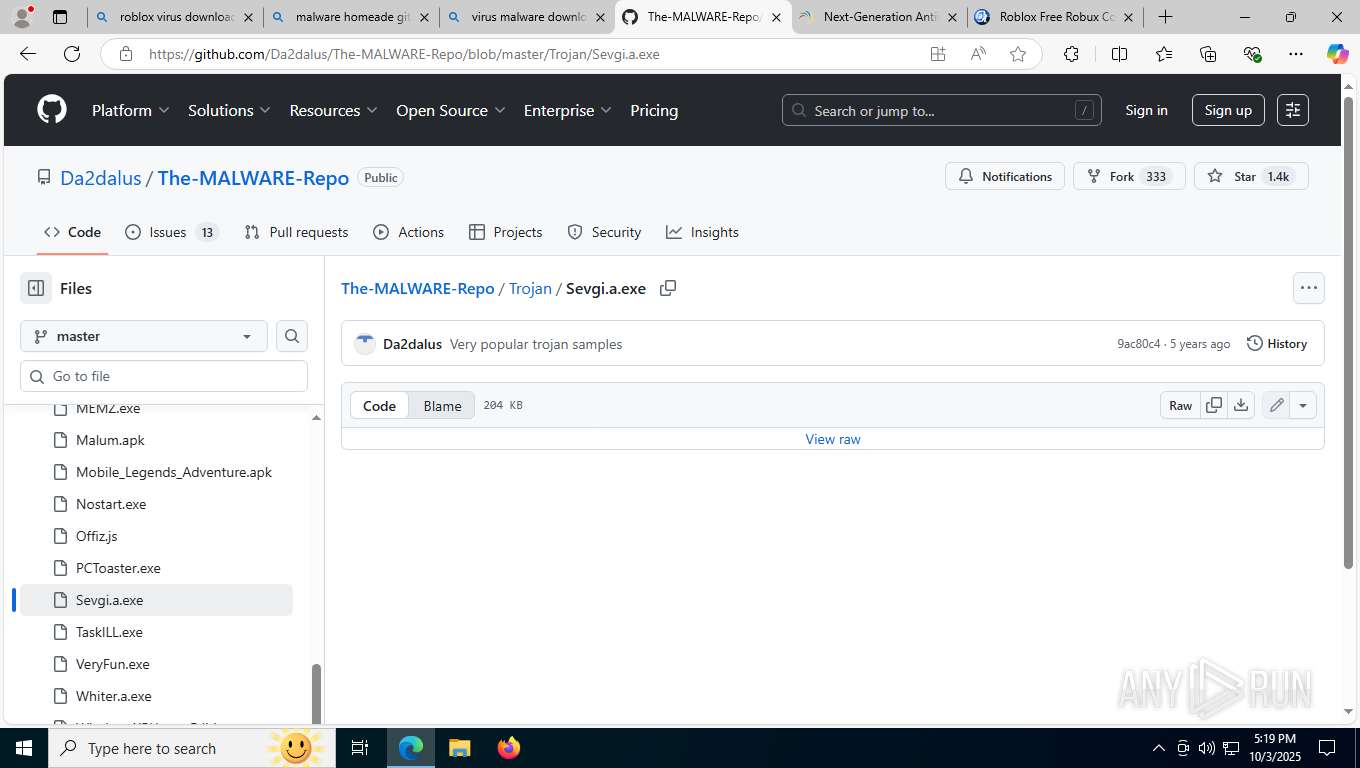
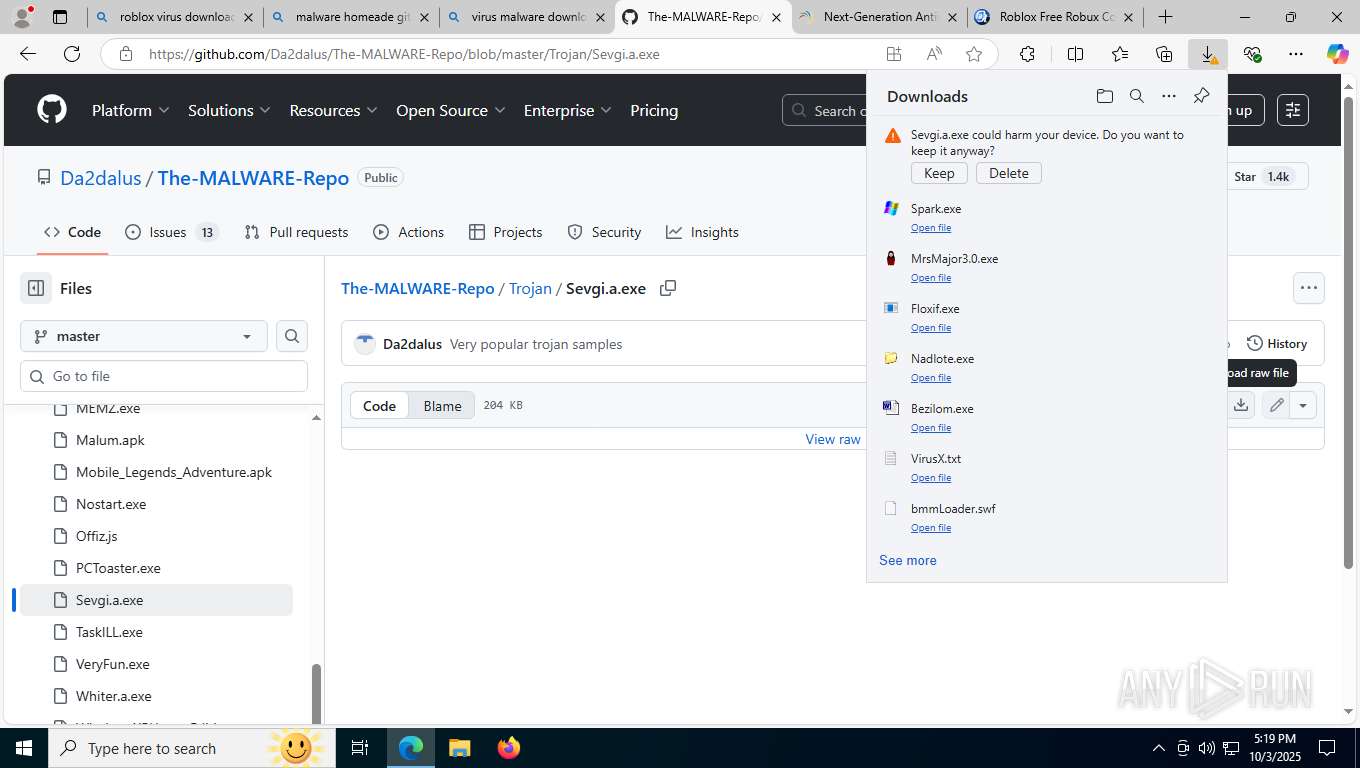
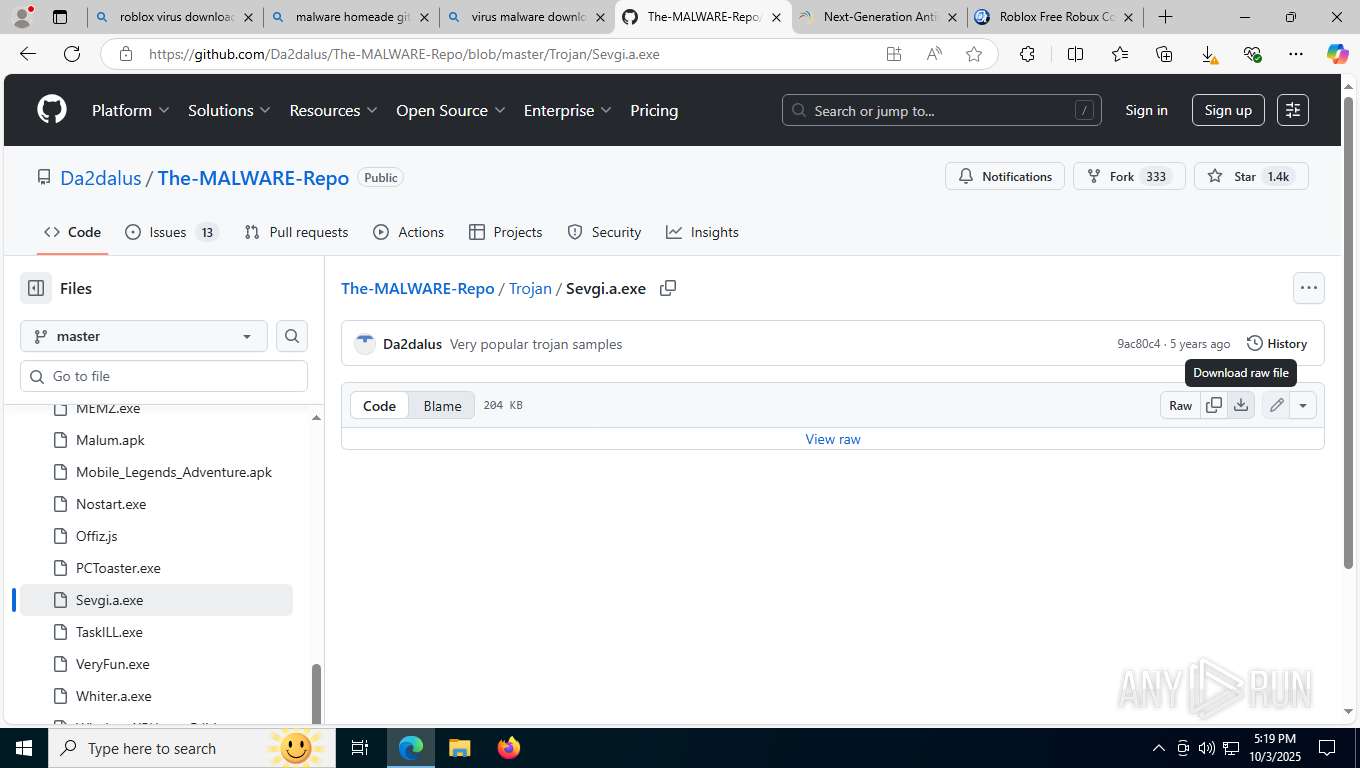
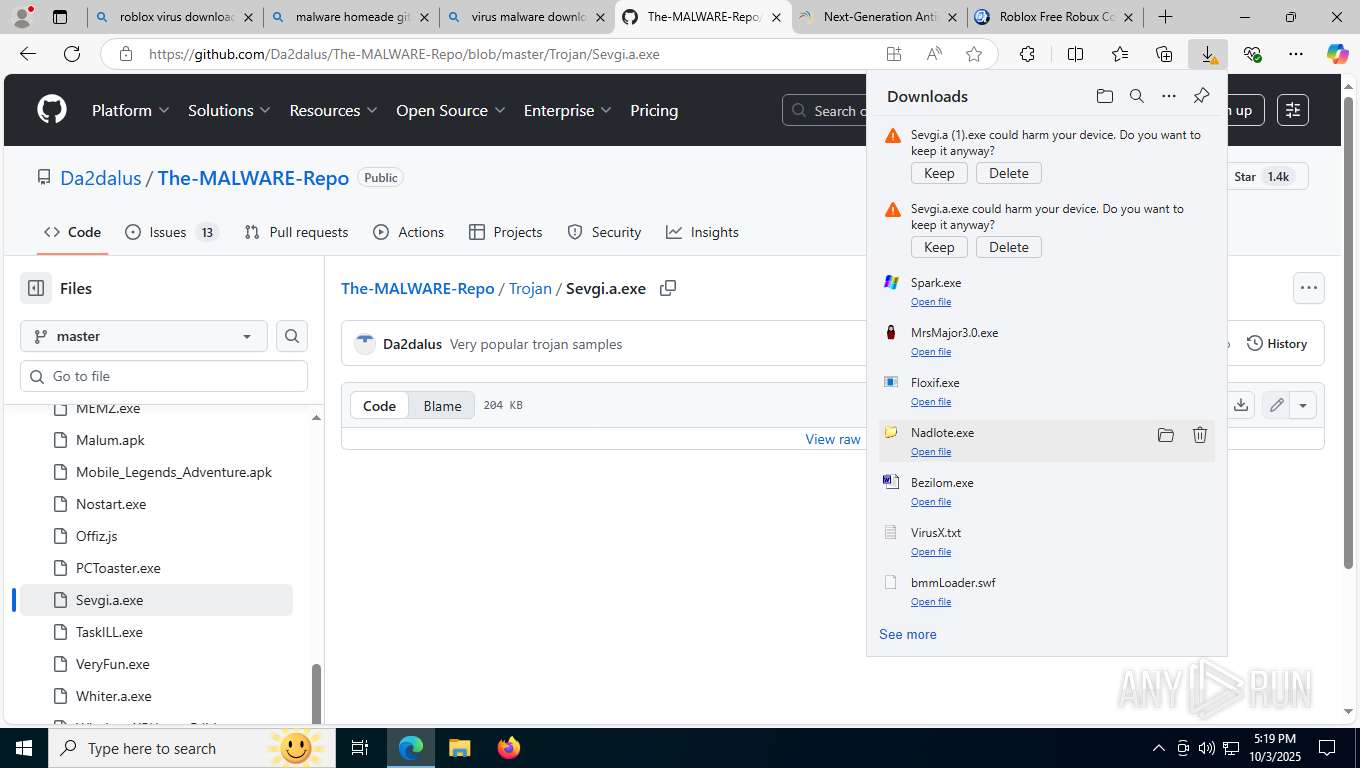
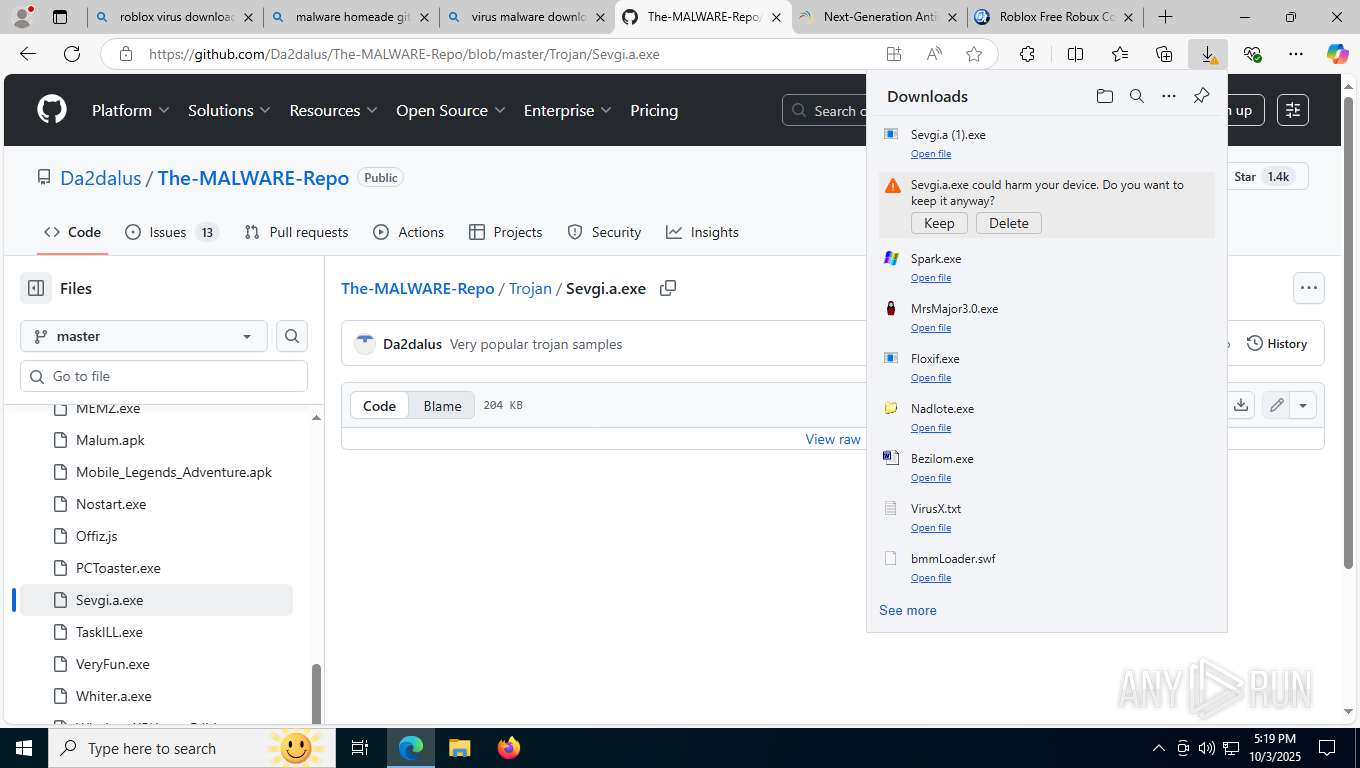
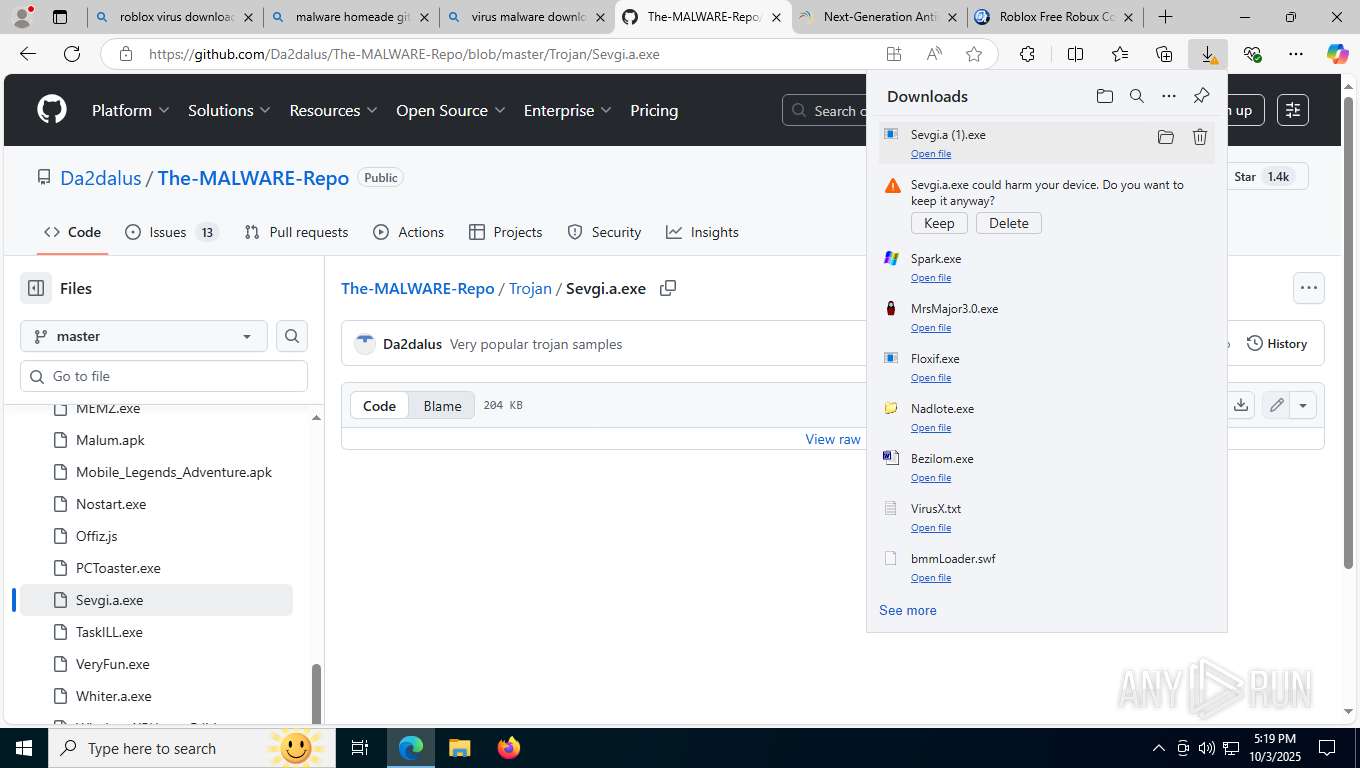
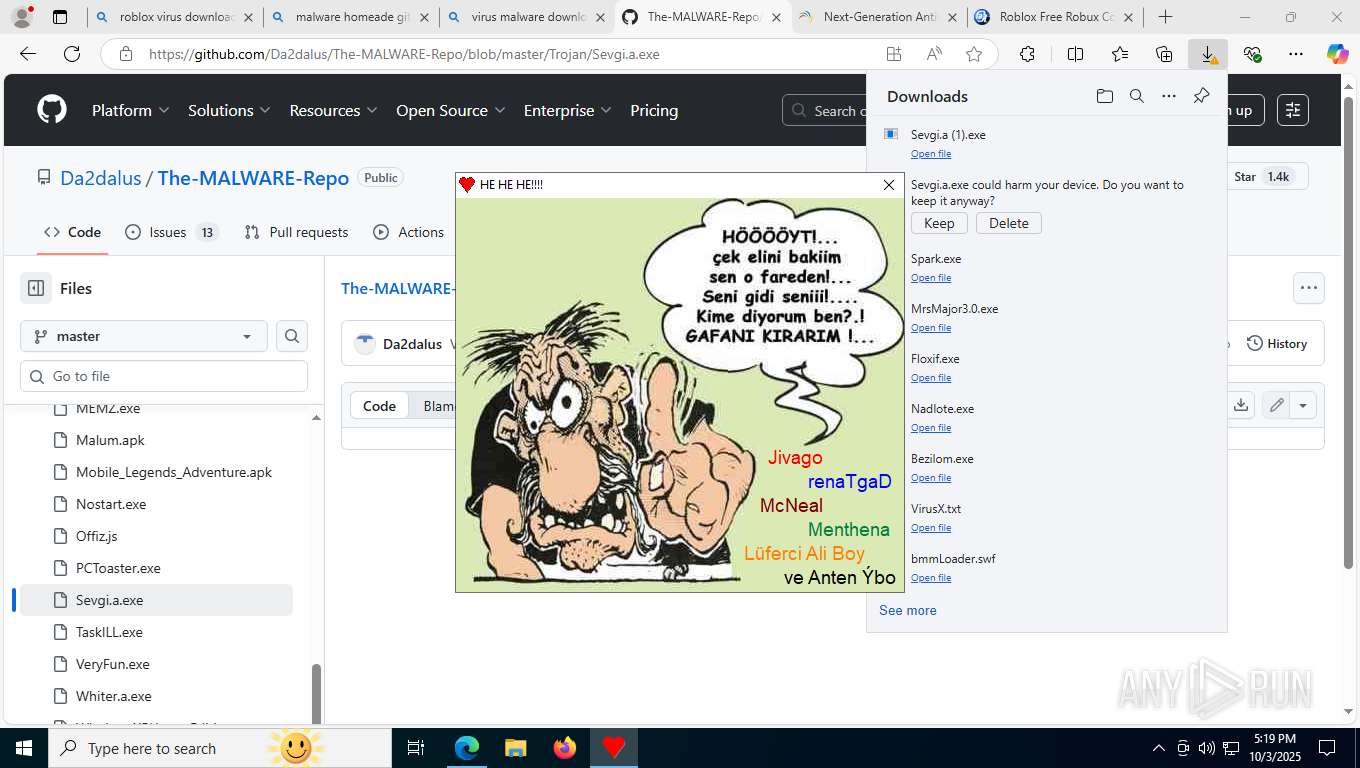
MALICIOUS
GENERIC has been found (auto)
- msedge.exe (PID: 8020)
- msedge.exe (PID: 4608)
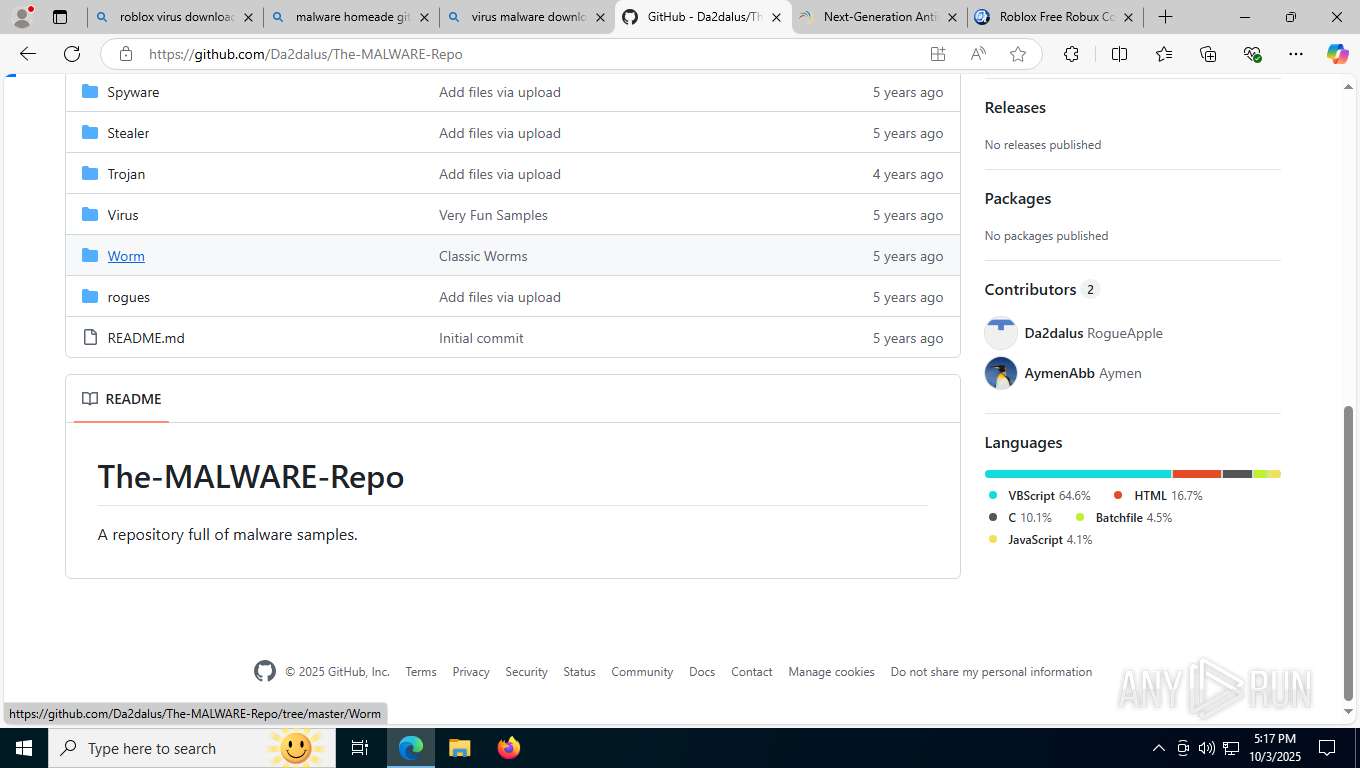
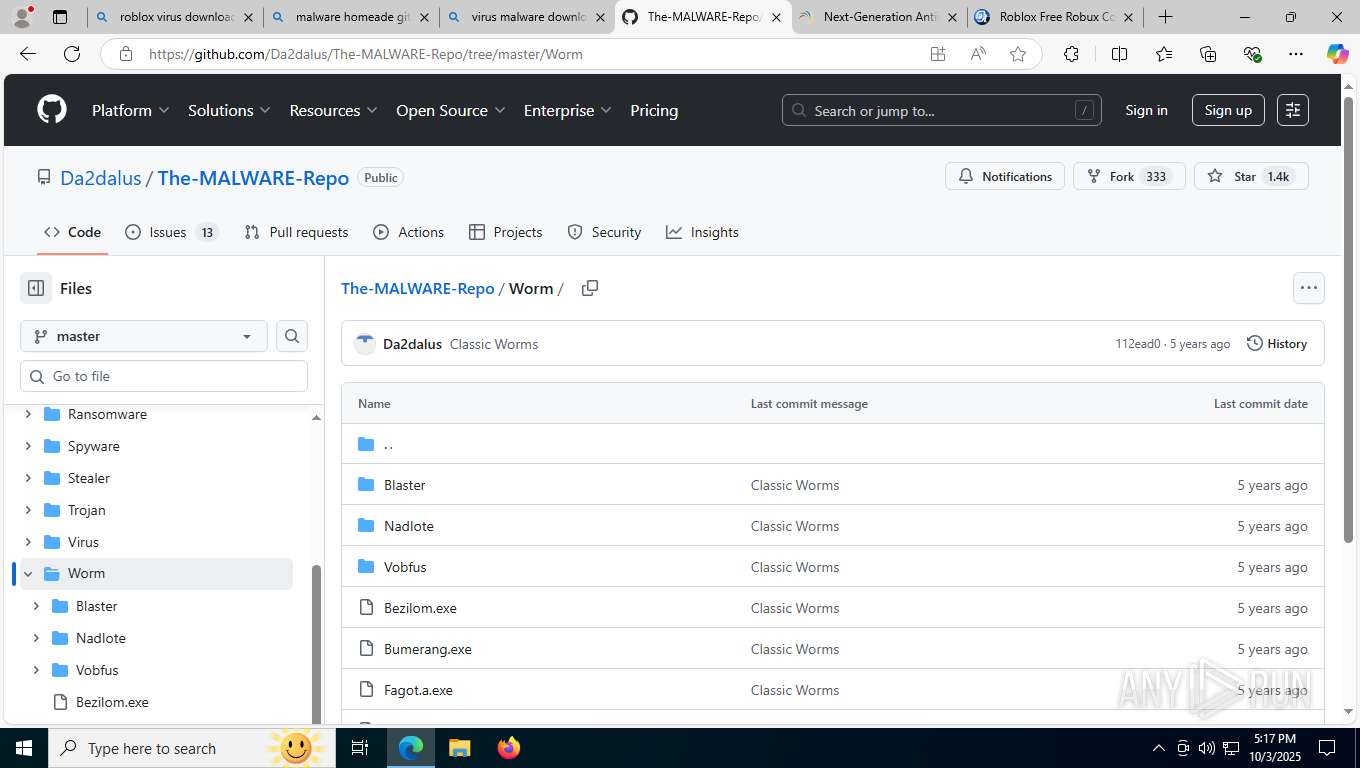
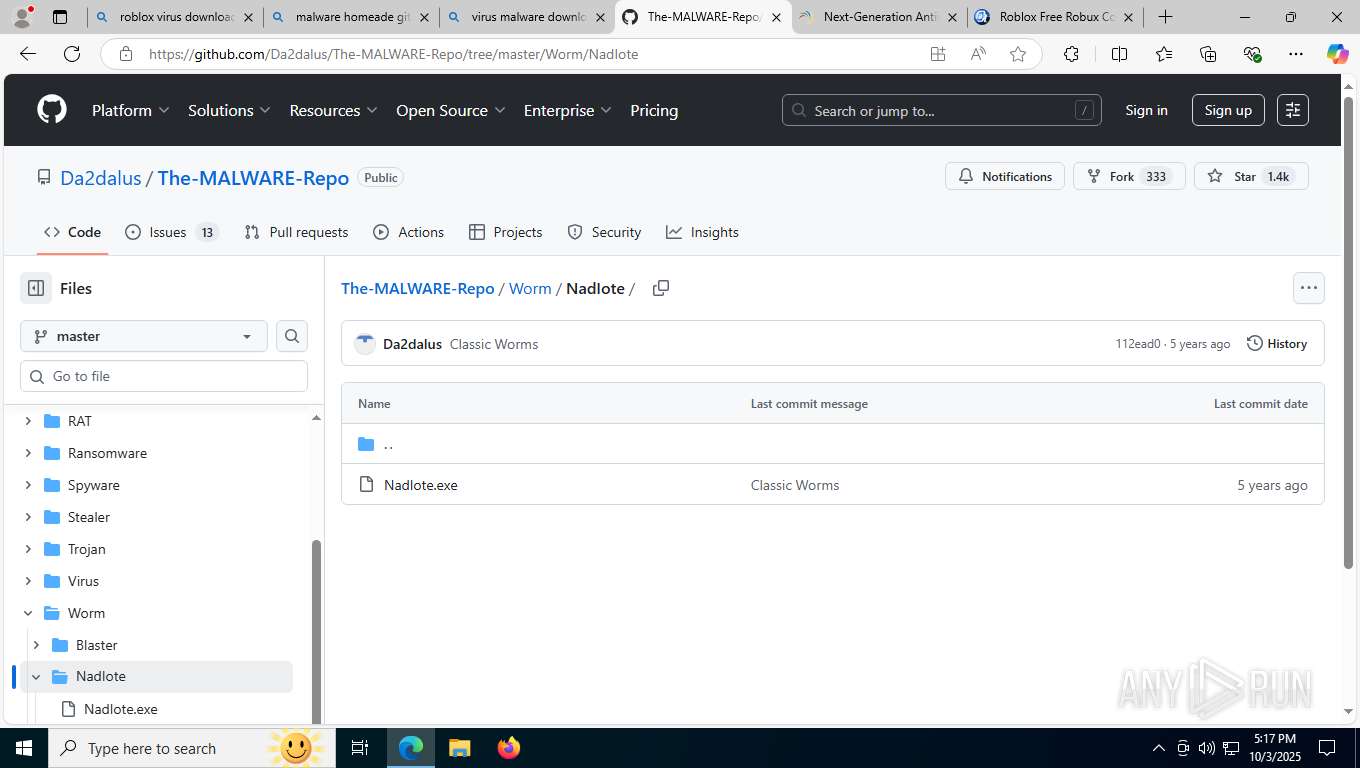
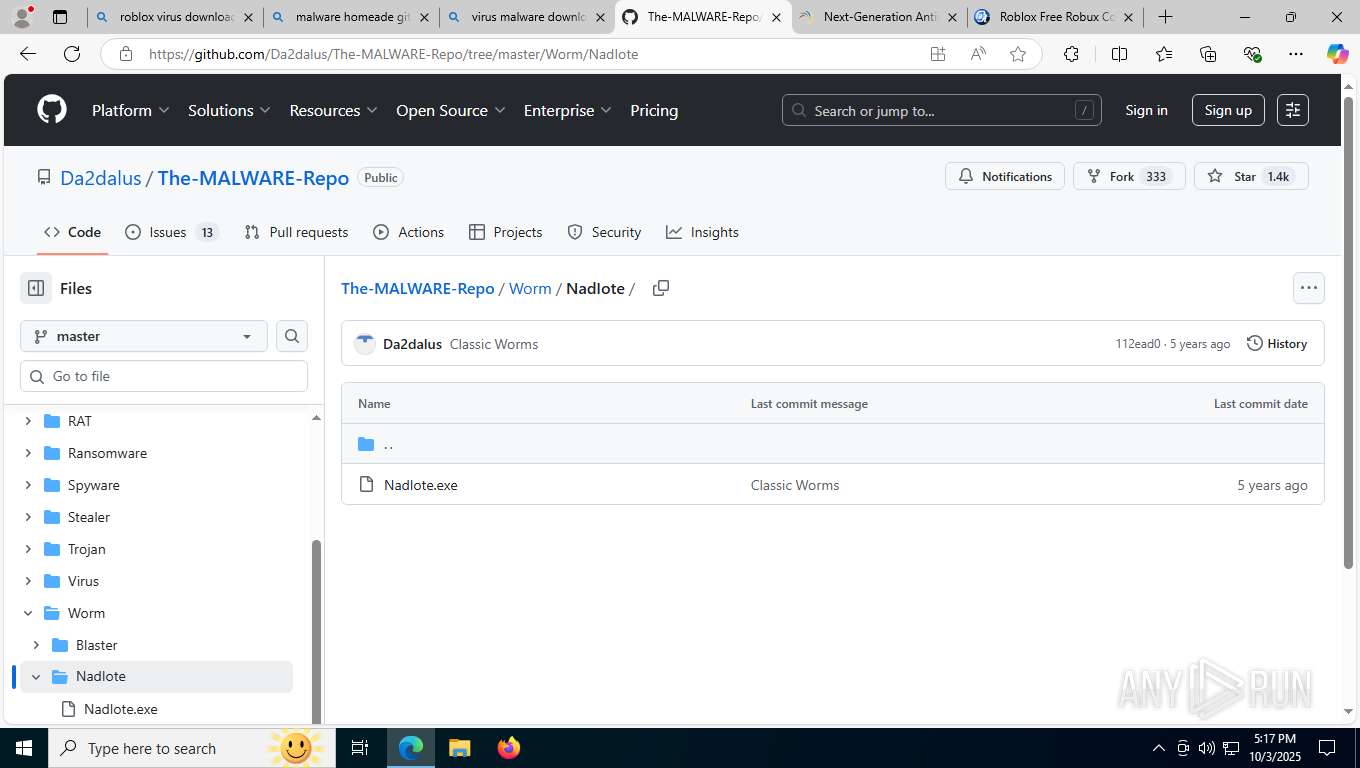
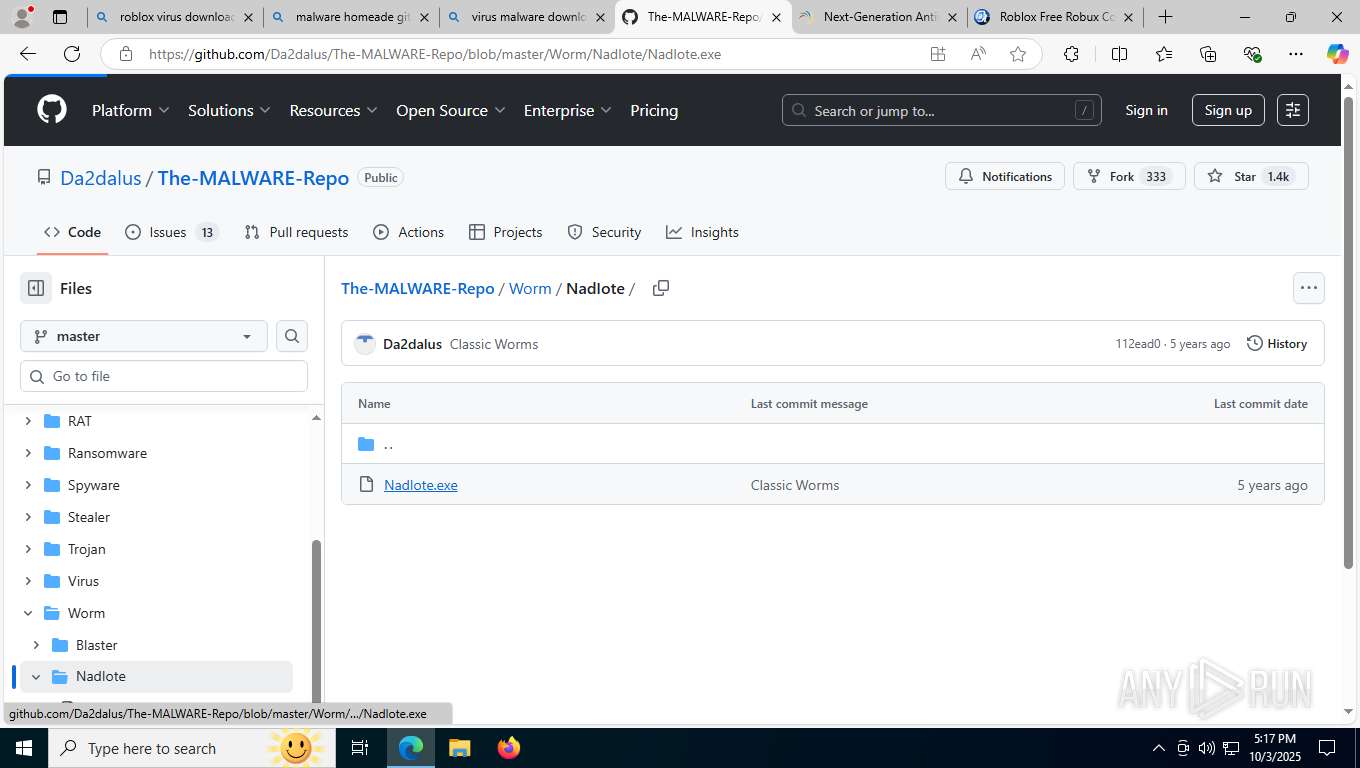
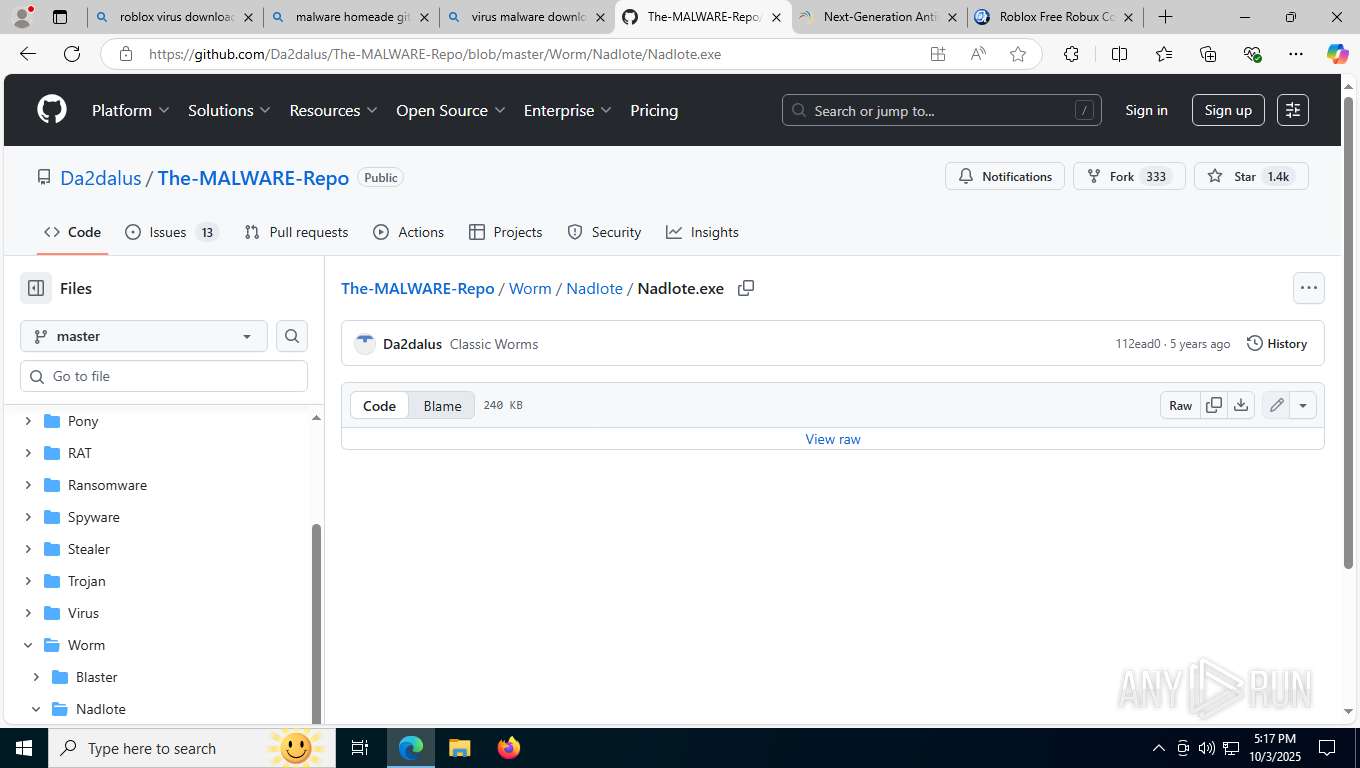
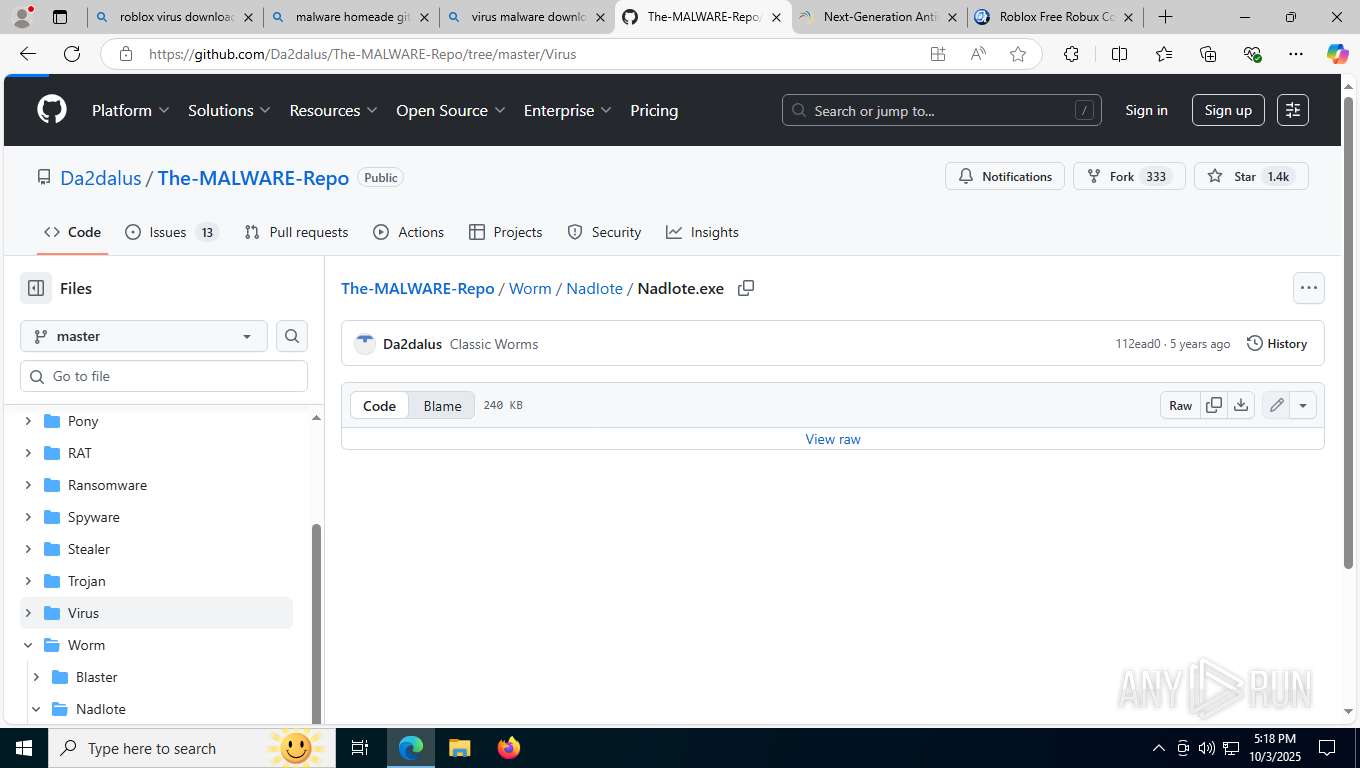
- Nadlote.exe (PID: 7740)
Changes the autorun value in the registry
- reg.exe (PID: 9408)
- Bezilom.exe (PID: 9388)
- reg.exe (PID: 9320)
- reg.exe (PID: 704)
- reg.exe (PID: 9536)
- reg.exe (PID: 9576)
- reg.exe (PID: 7220)
- reg.exe (PID: 2836)
- reg.exe (PID: 9448)
- reg.exe (PID: 9472)
- reg.exe (PID: 1308)
- reg.exe (PID: 9760)
- reg.exe (PID: 9528)
- reg.exe (PID: 9160)
- reg.exe (PID: 9376)
- reg.exe (PID: 9384)
- reg.exe (PID: 7208)
- reg.exe (PID: 9580)
- reg.exe (PID: 9812)
- reg.exe (PID: 9764)
Starts NET.EXE to view/change shared resources
- cmd.exe (PID: 9472)
- net.exe (PID: 6064)
- net.exe (PID: 8232)
- net.exe (PID: 9188)
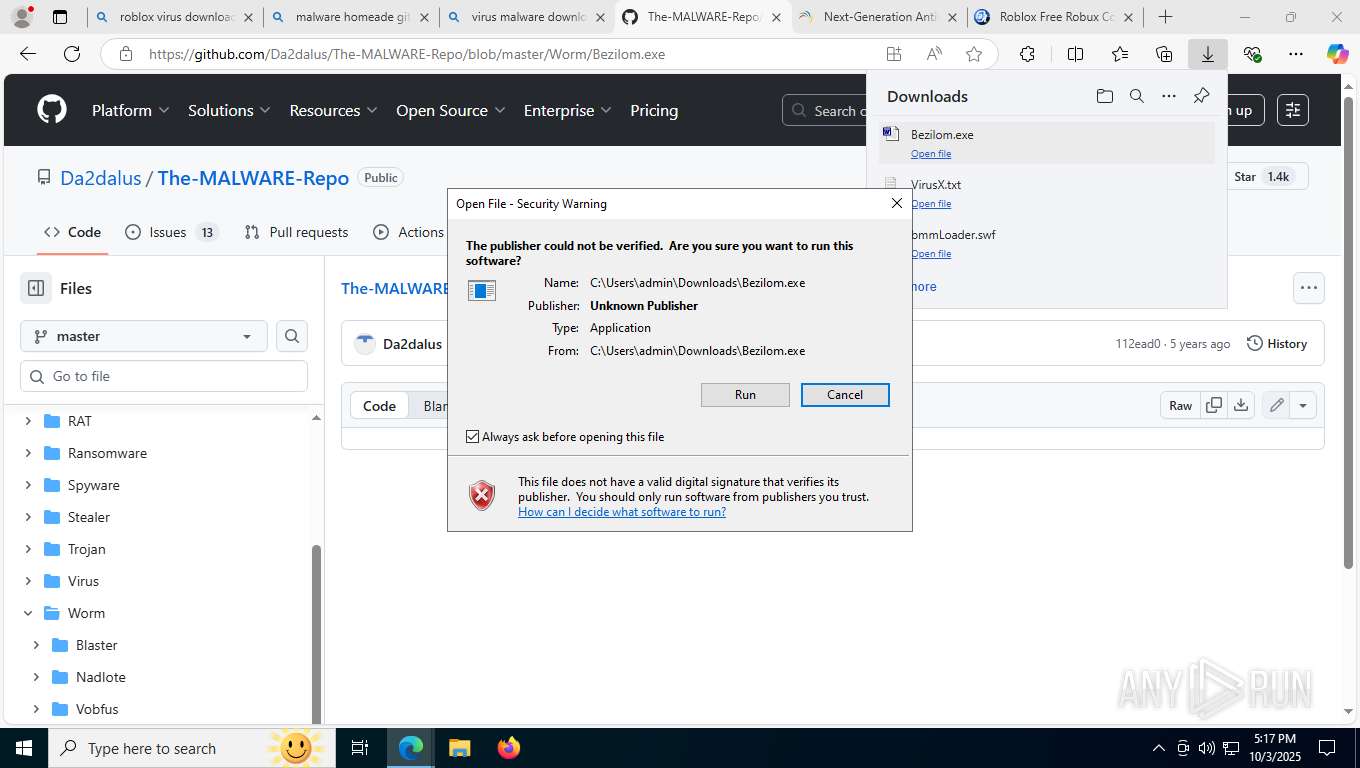
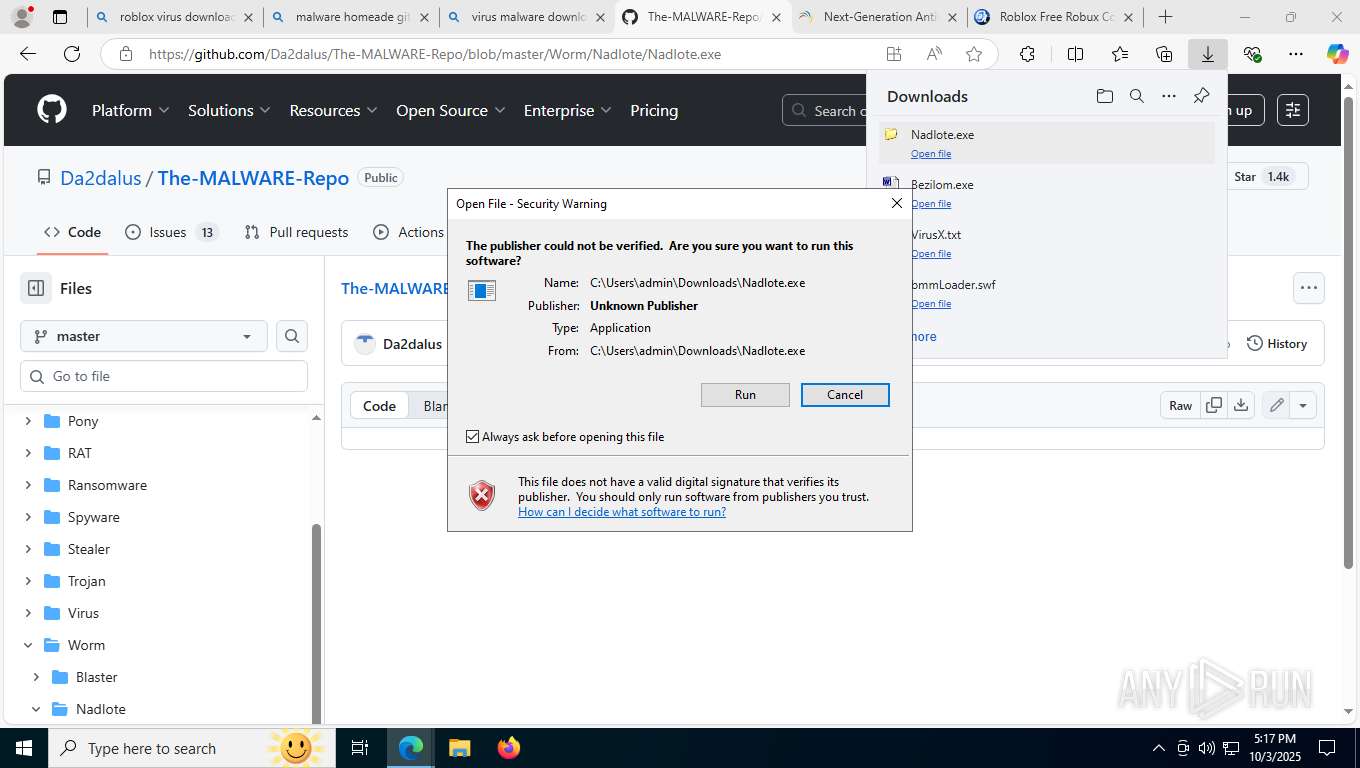
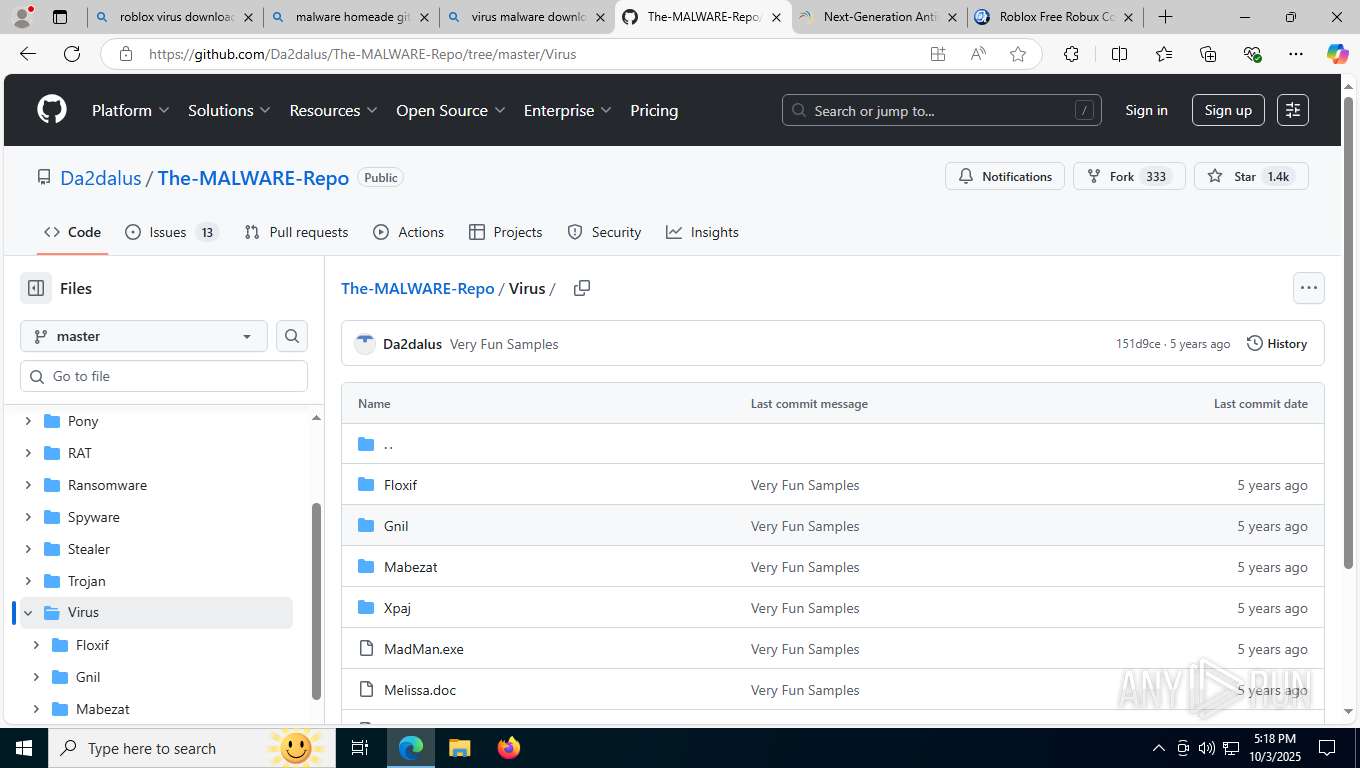
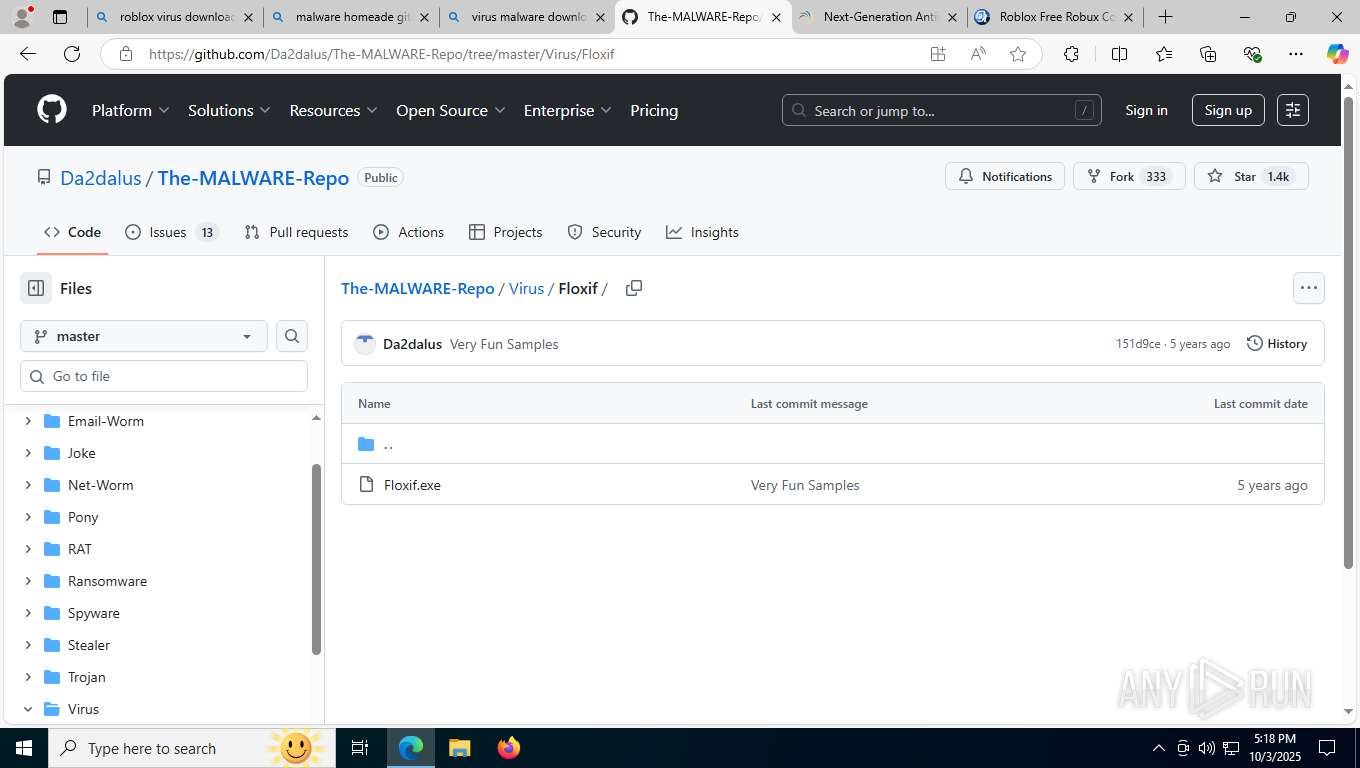
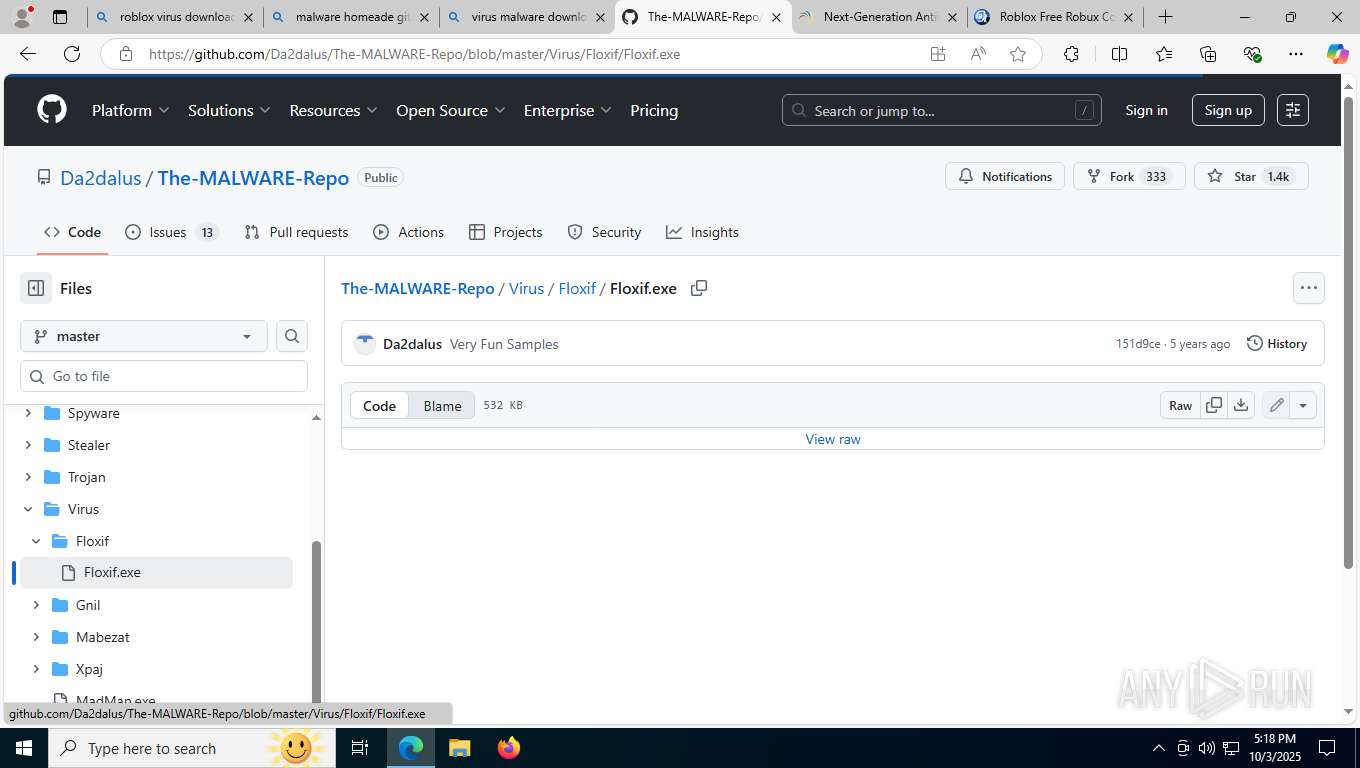
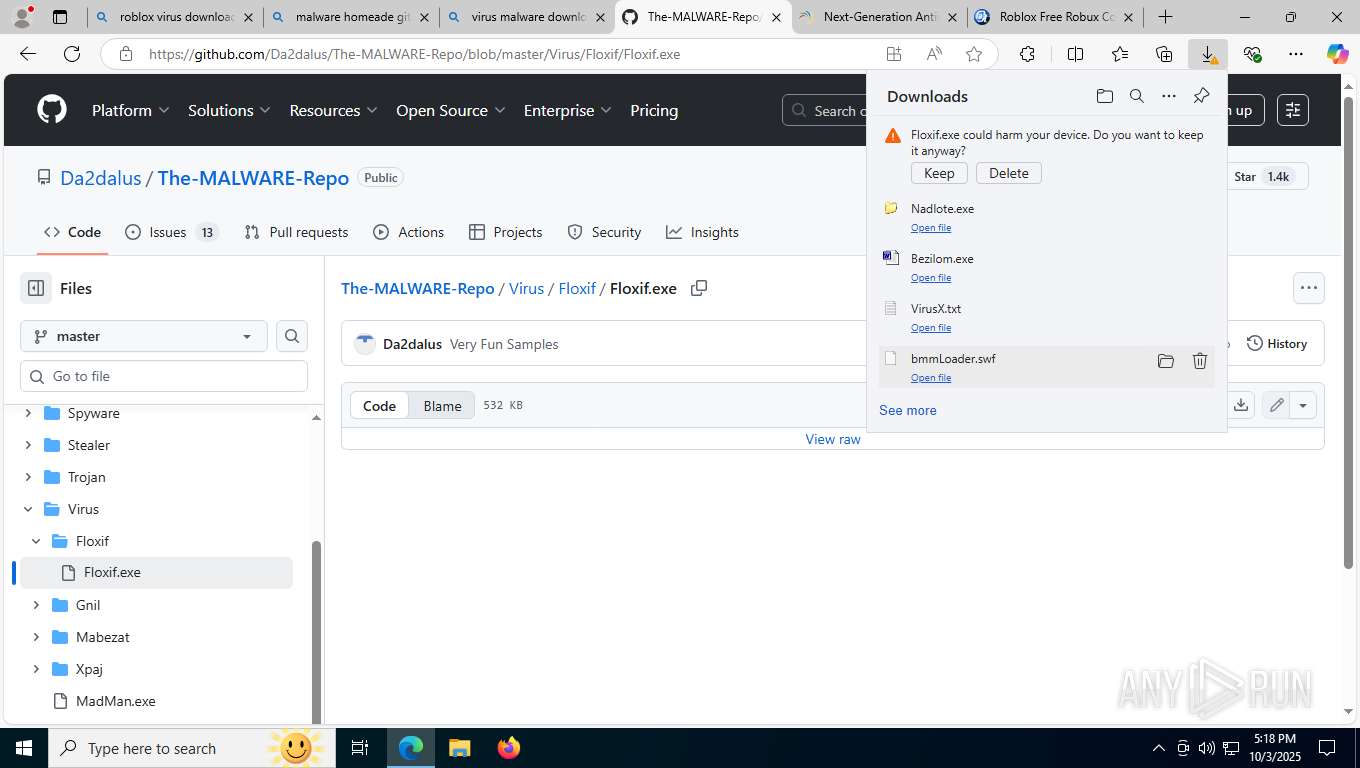
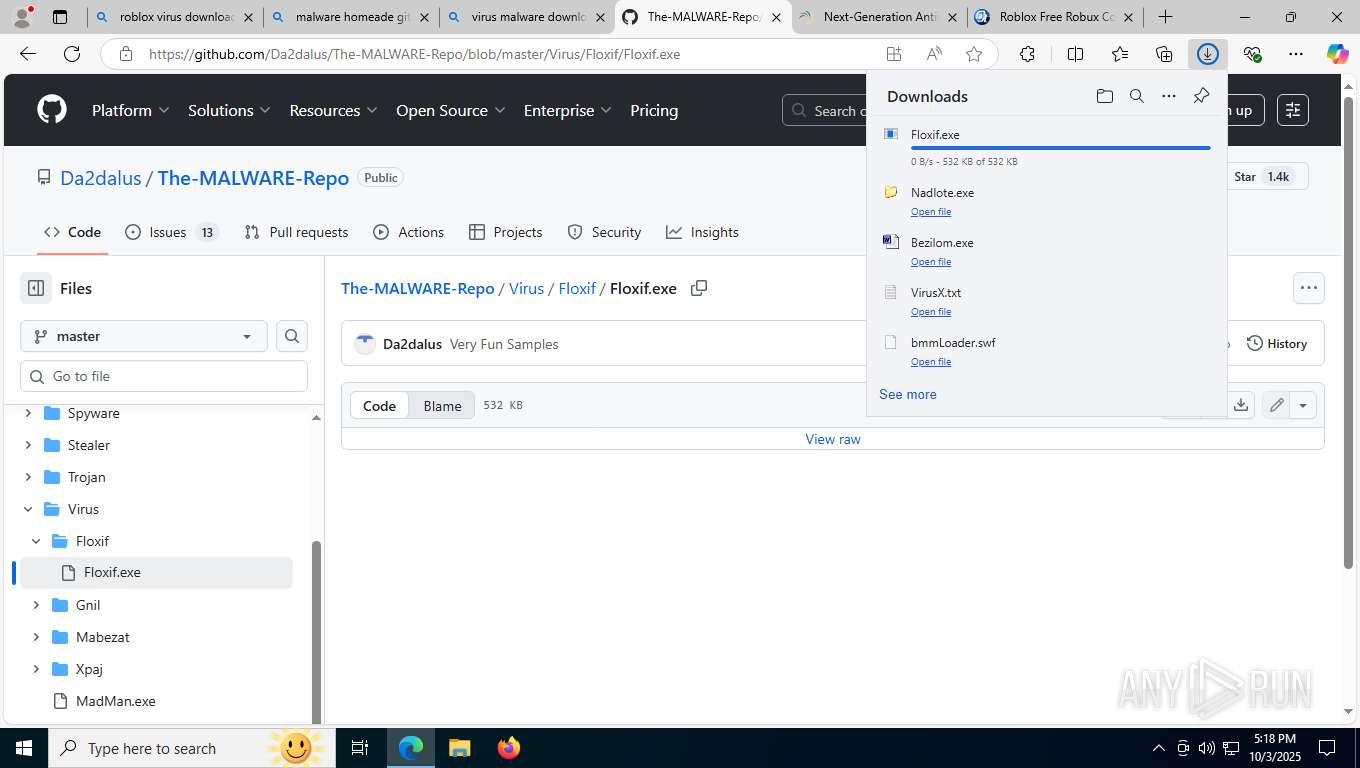
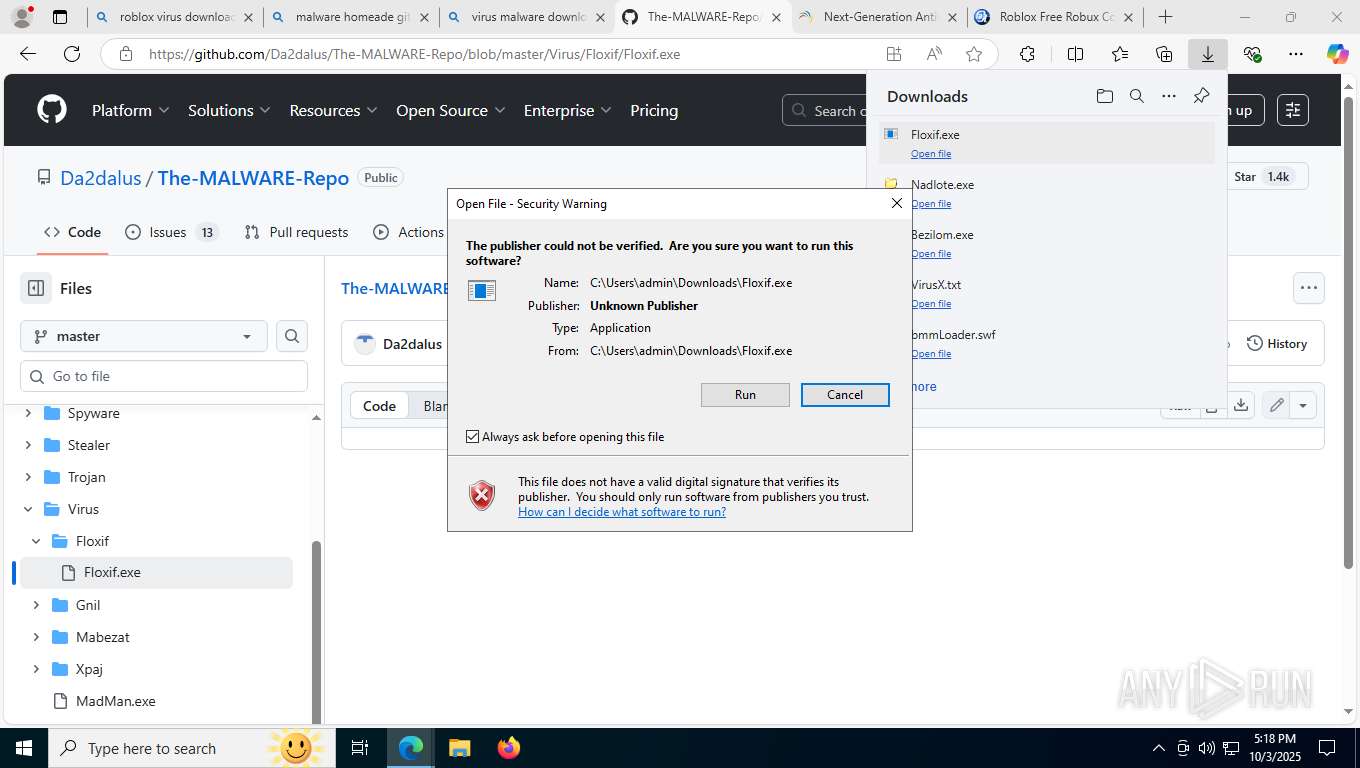
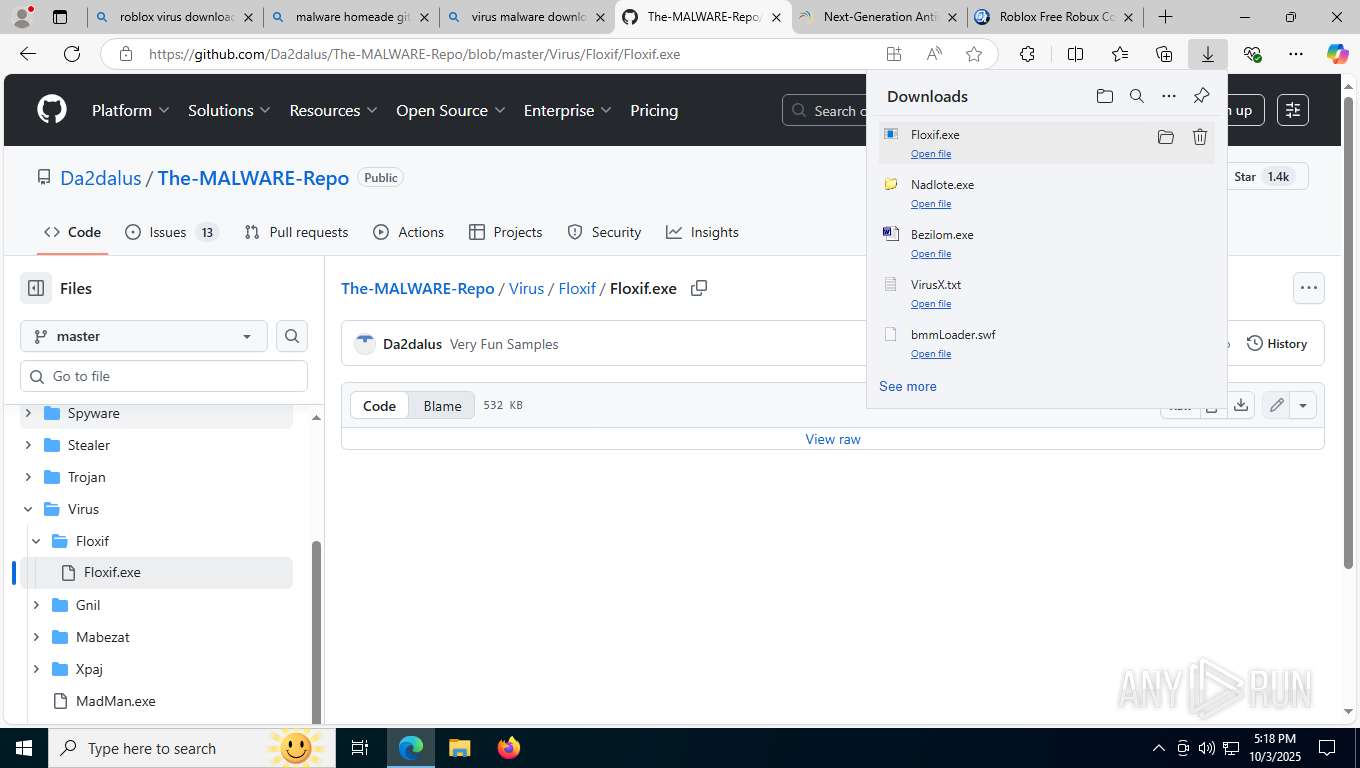
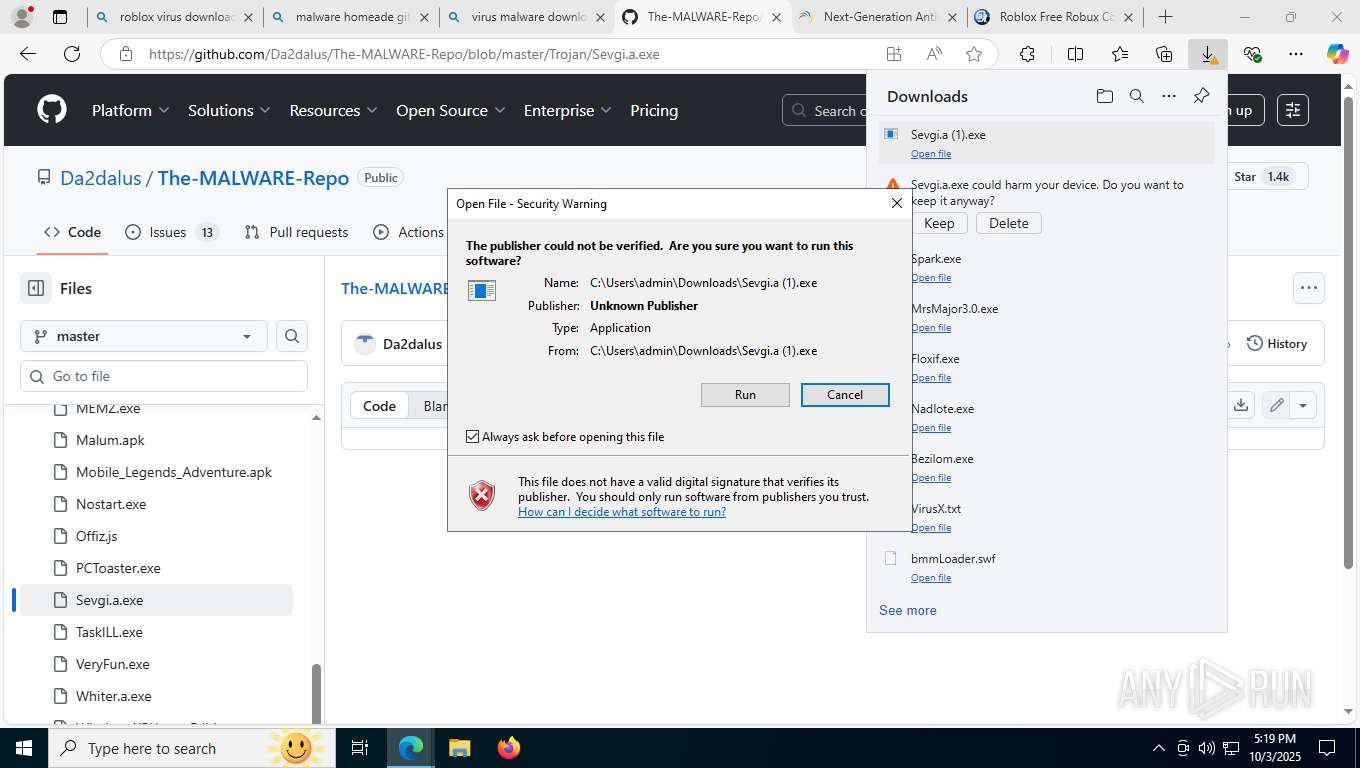
Executing a file with an untrusted certificate
- Floxif.exe (PID: 4748)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 9932)
SUSPICIOUS
Creates file in the systems drive root
- Bezilom.exe (PID: 9388)
- Nadlote.exe (PID: 7740)
- smss.exe (PID: 788)
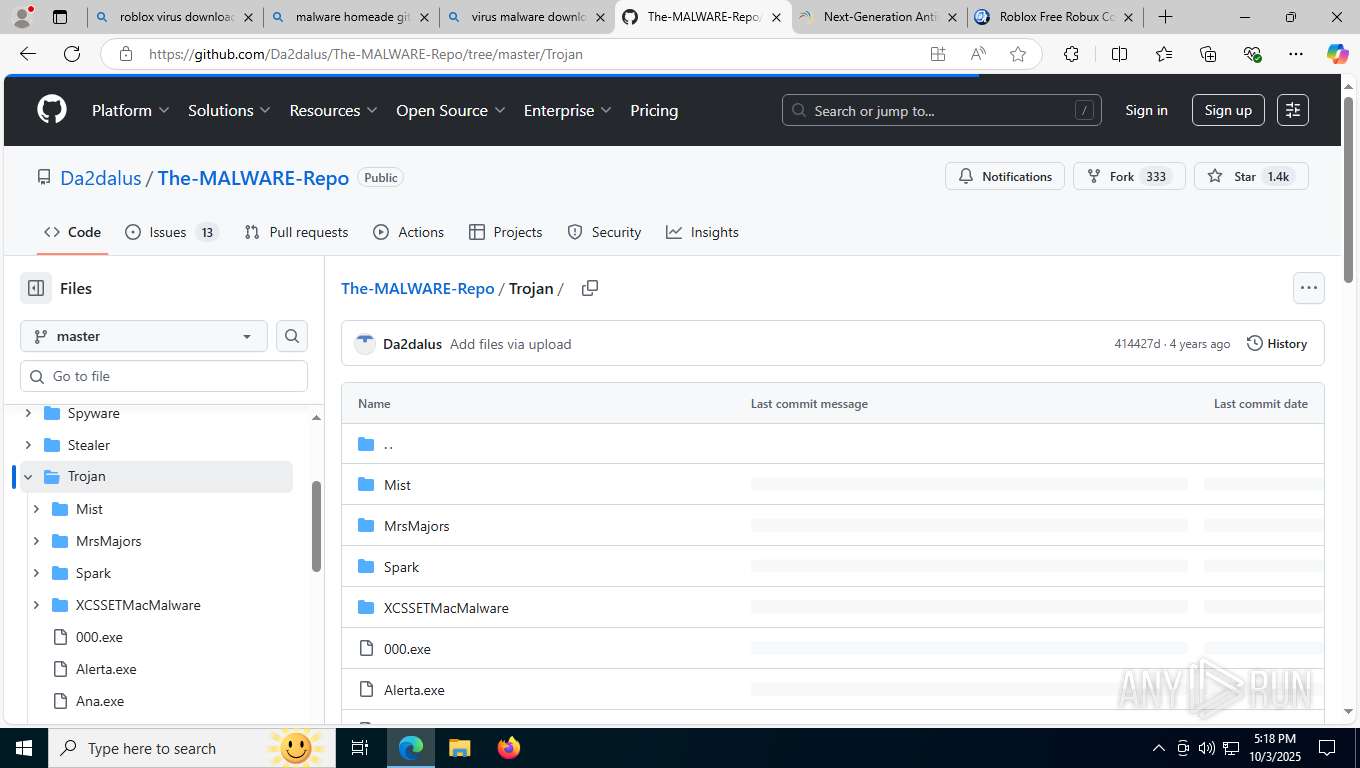
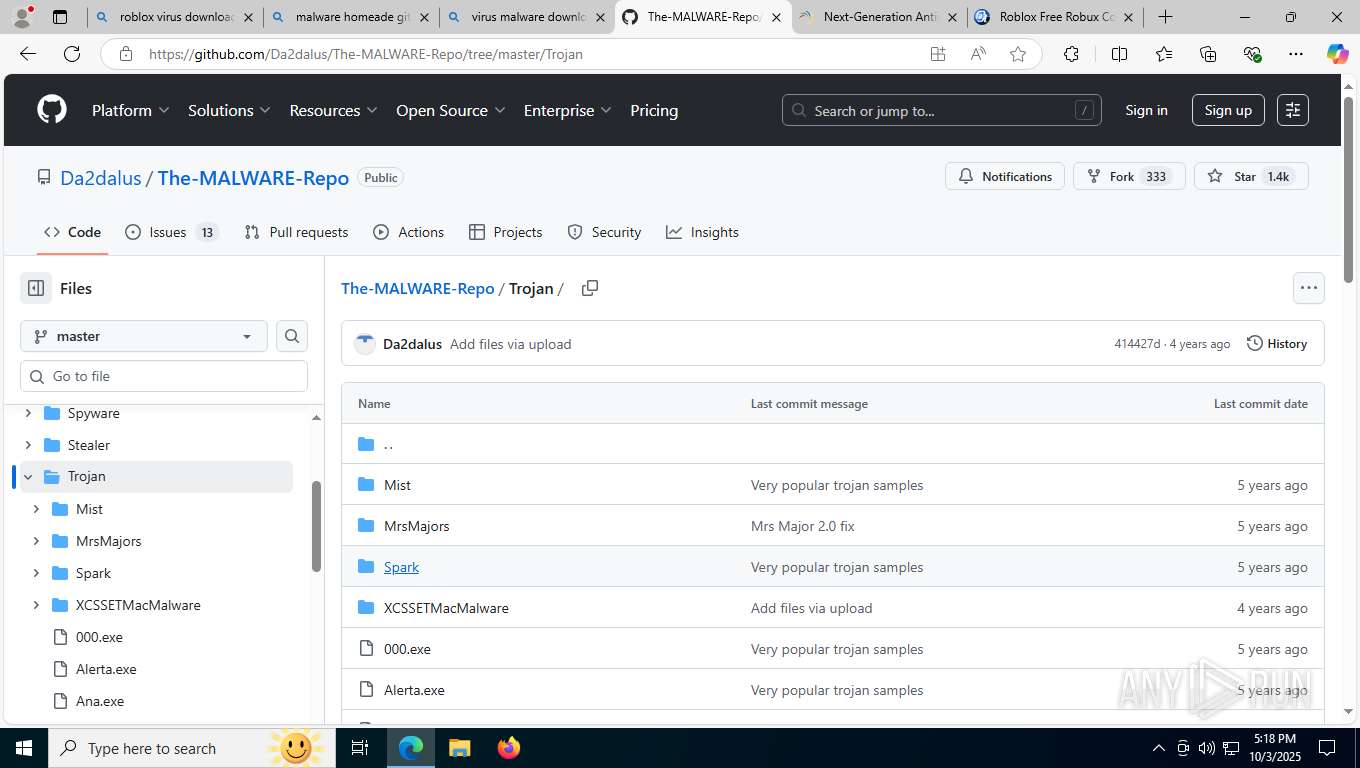
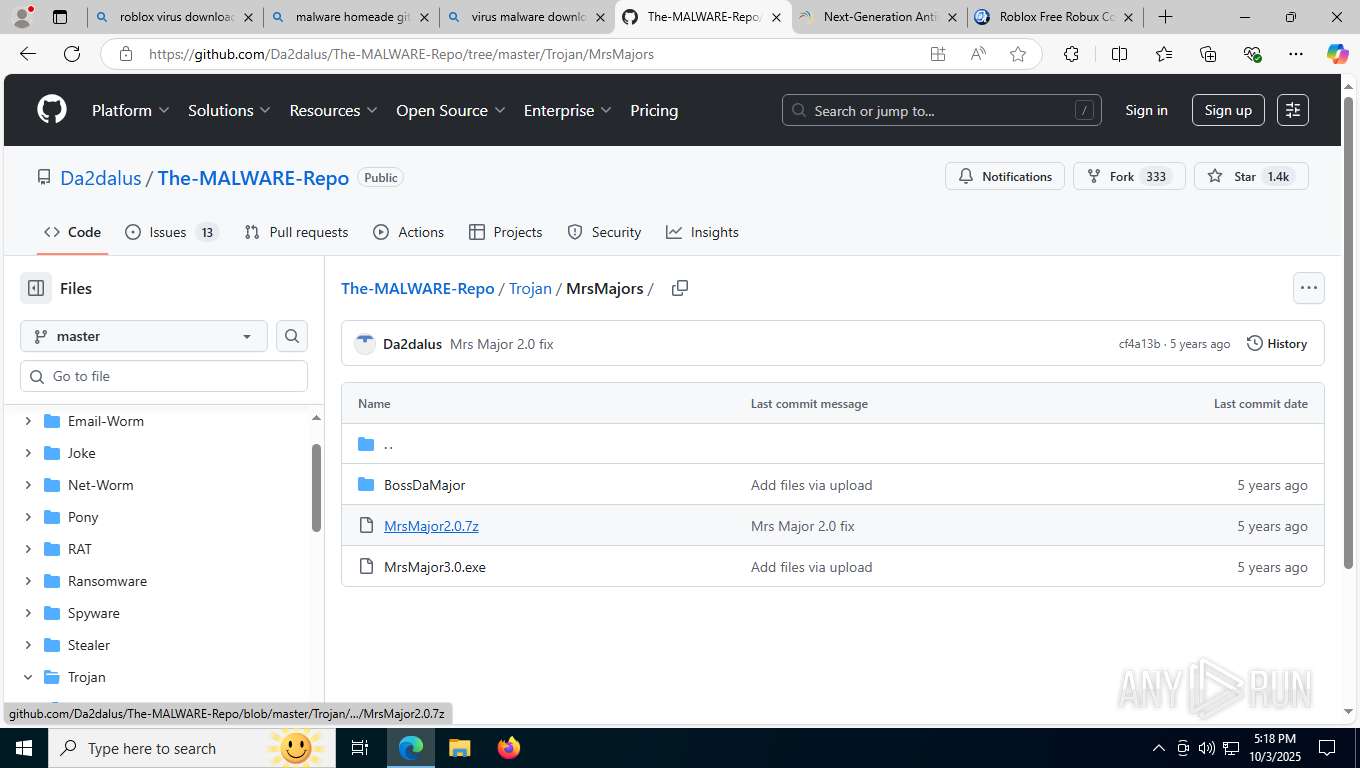
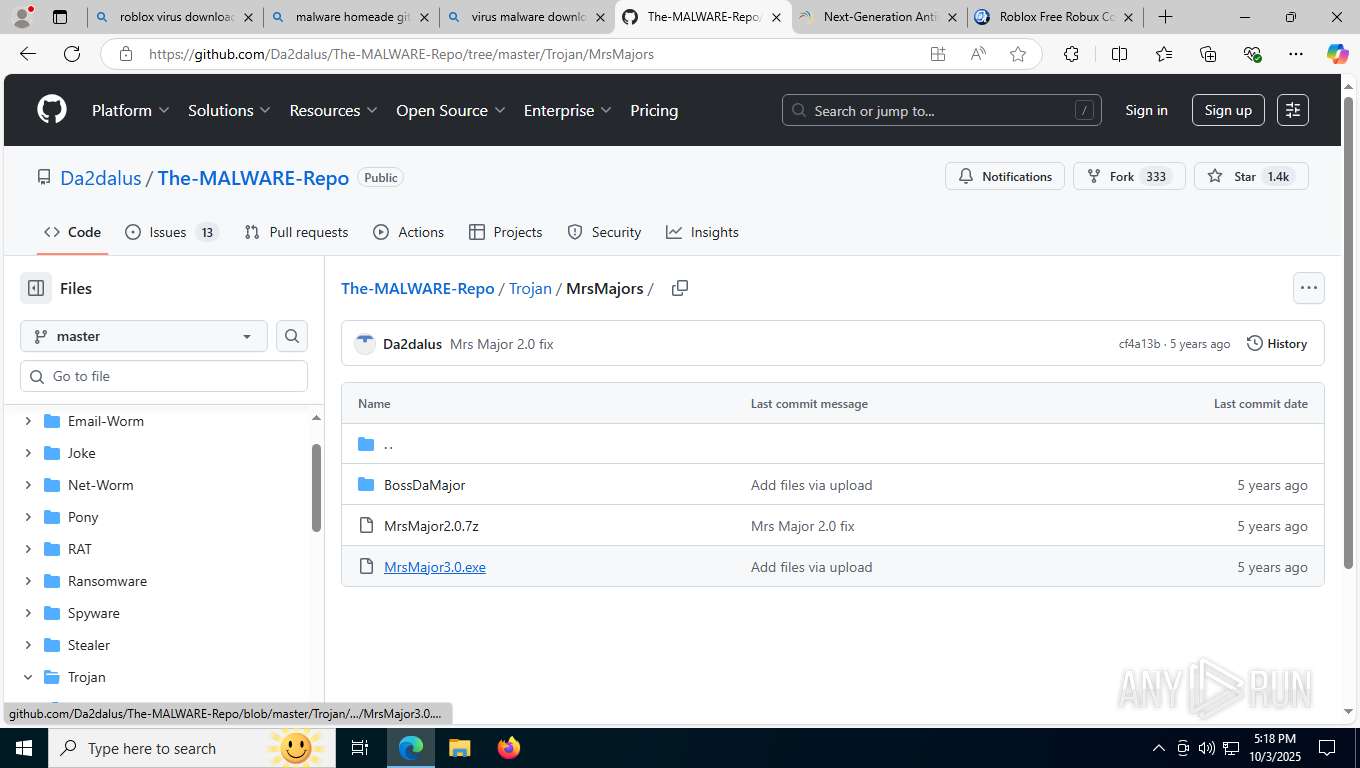
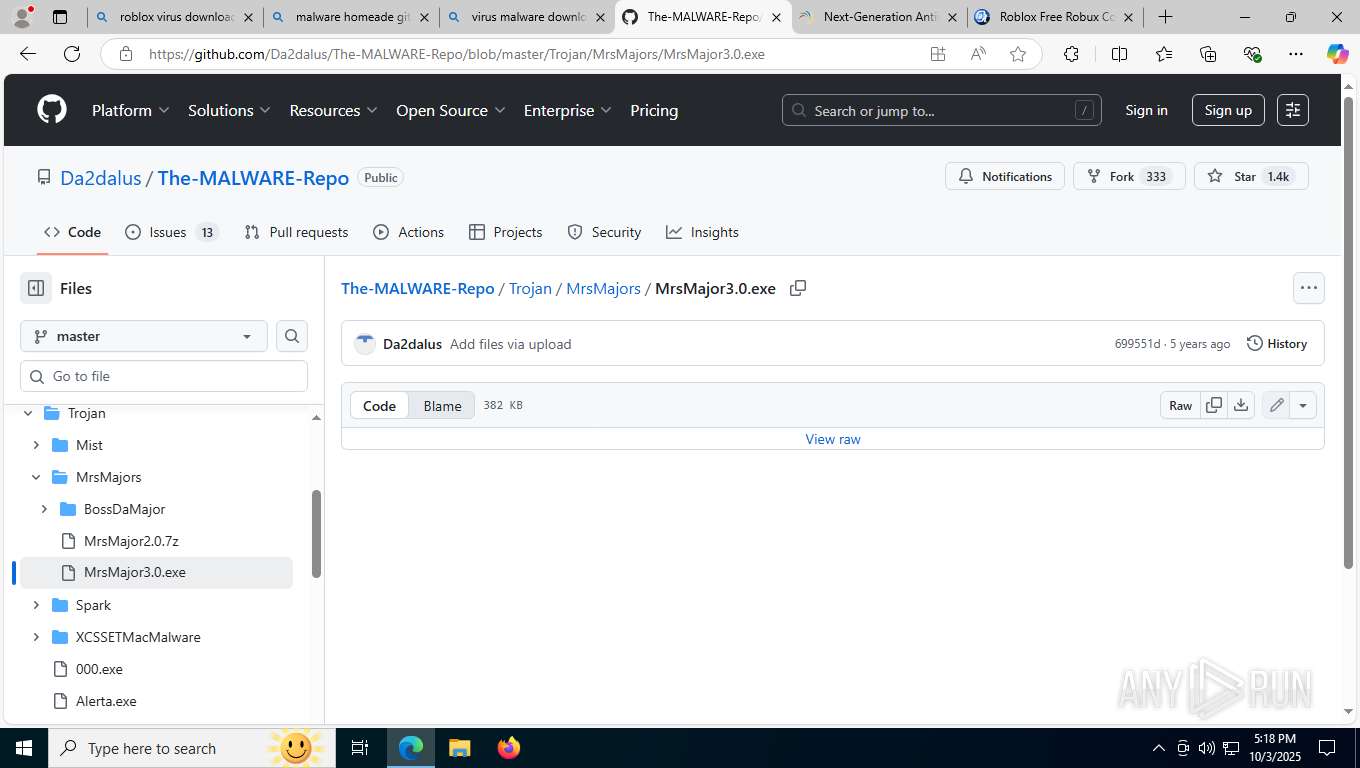
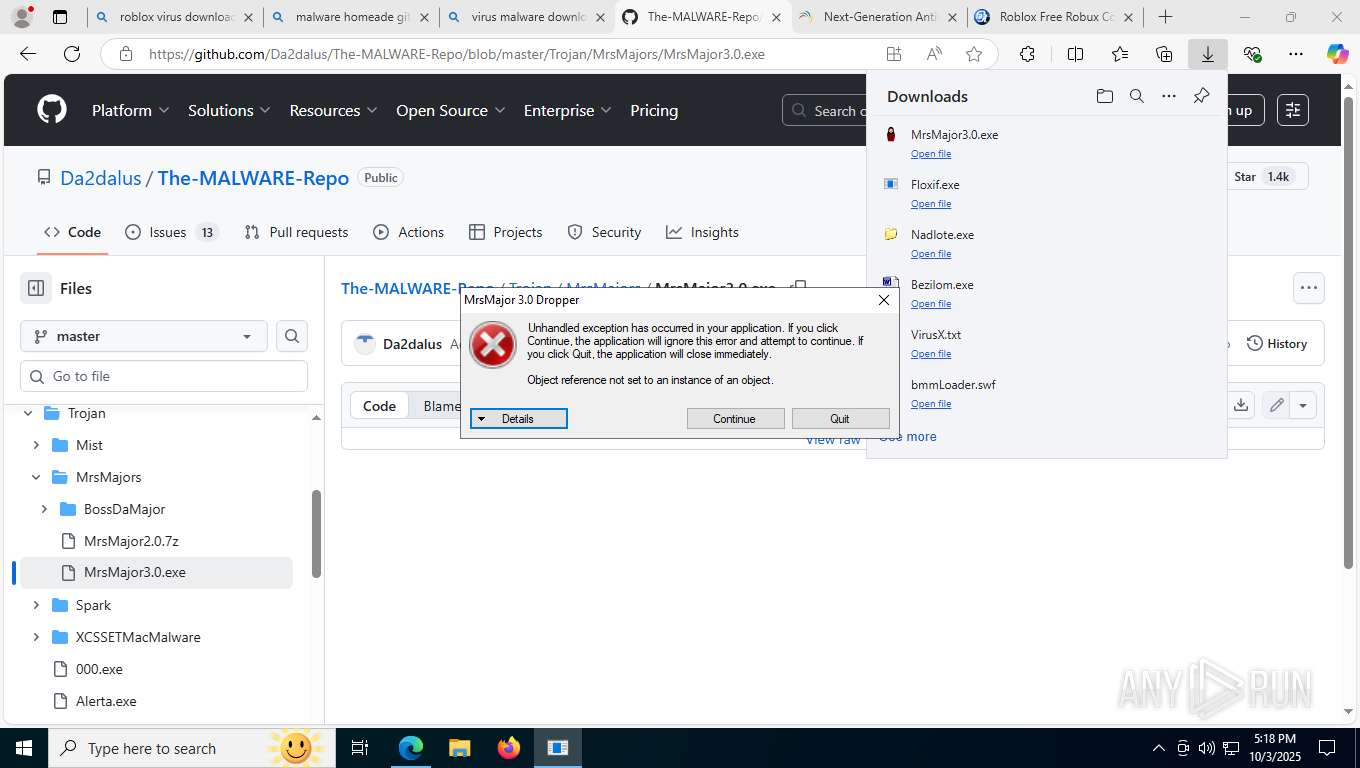
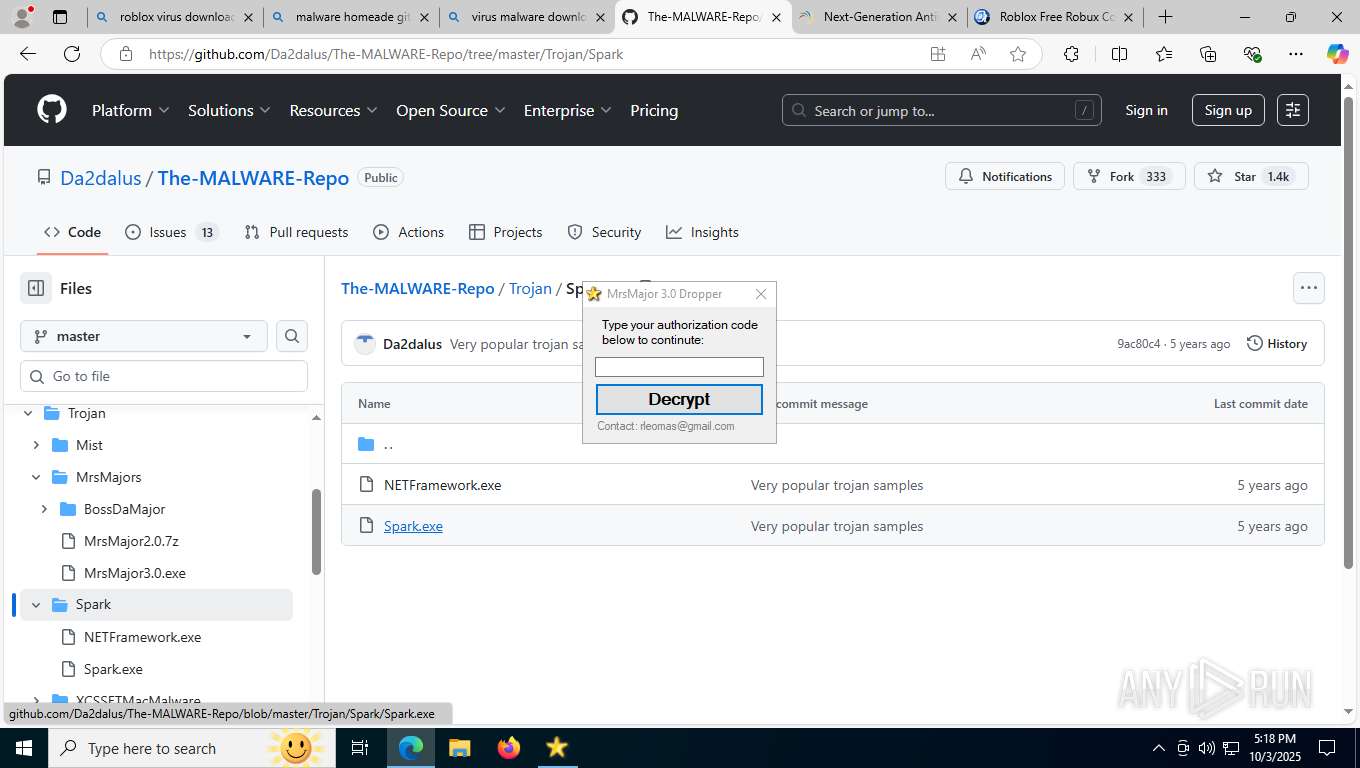
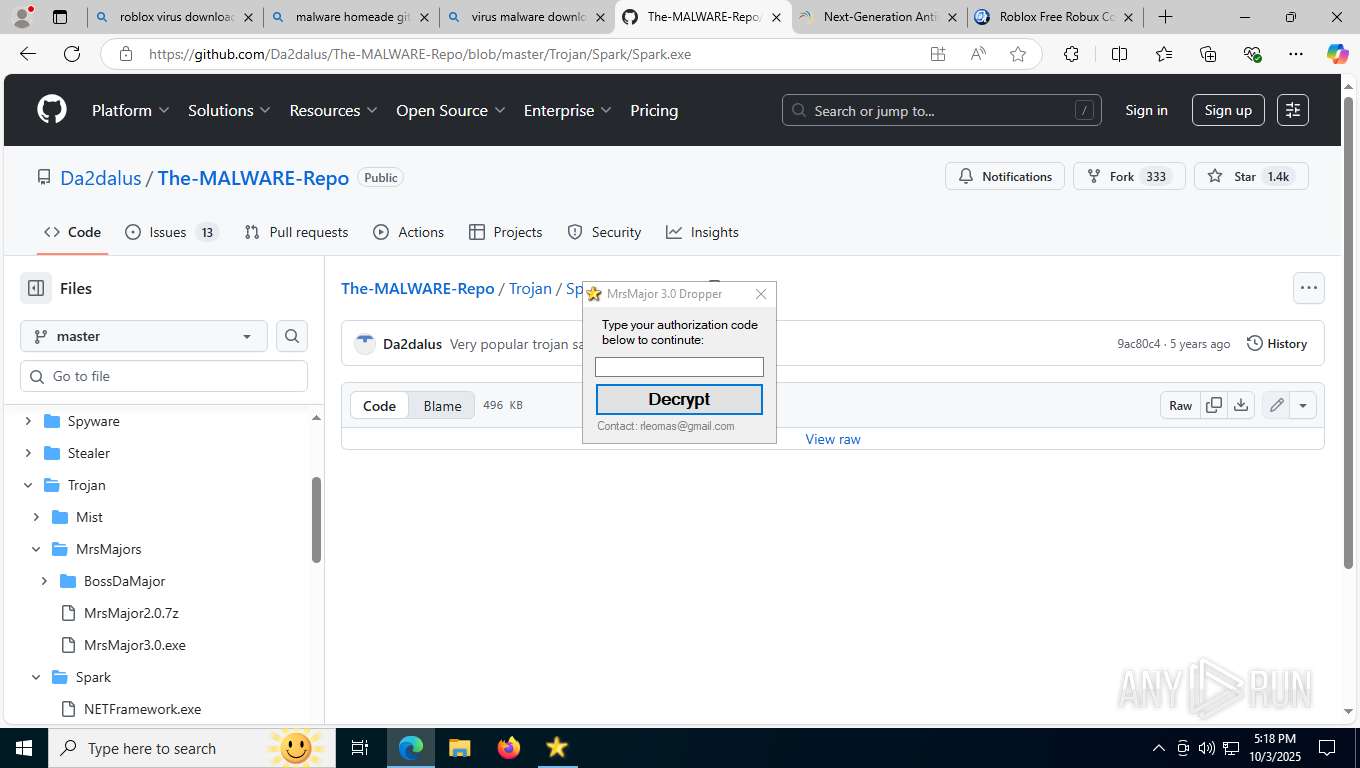
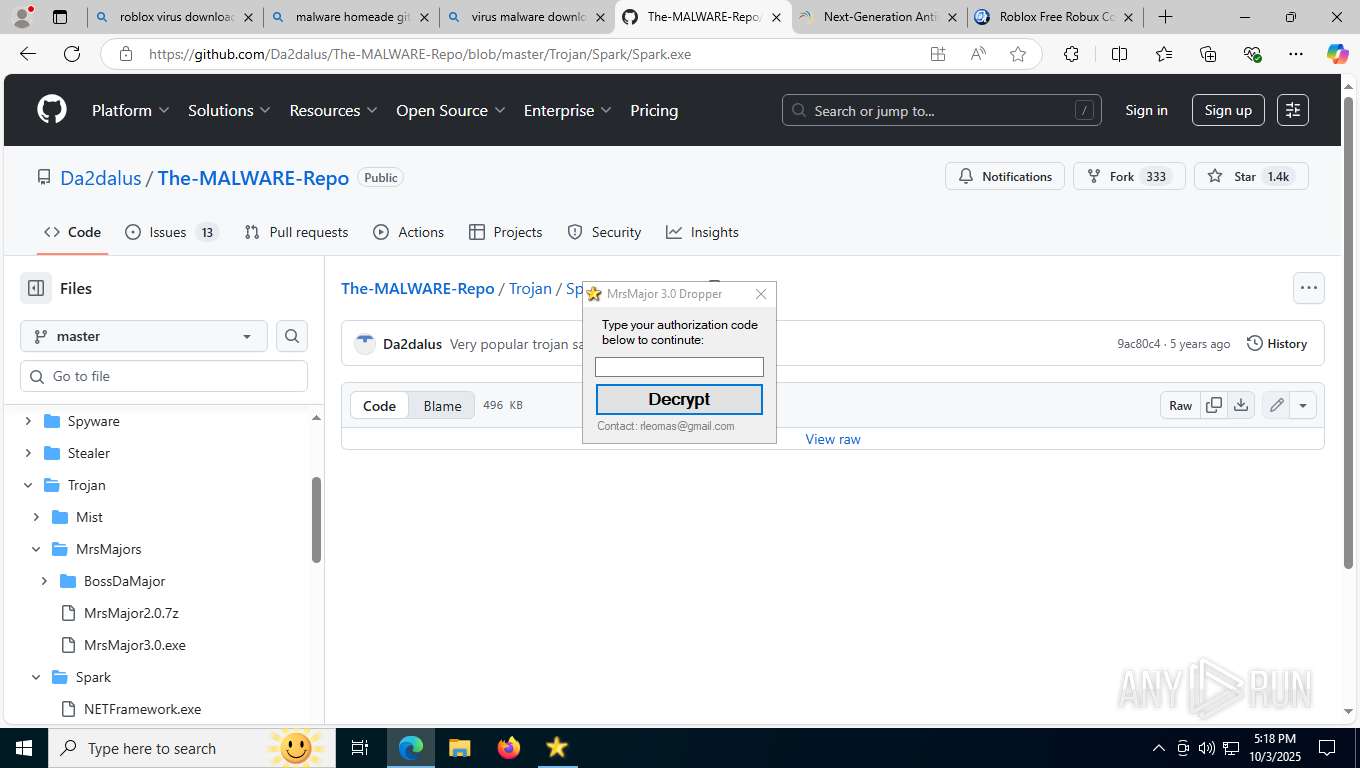
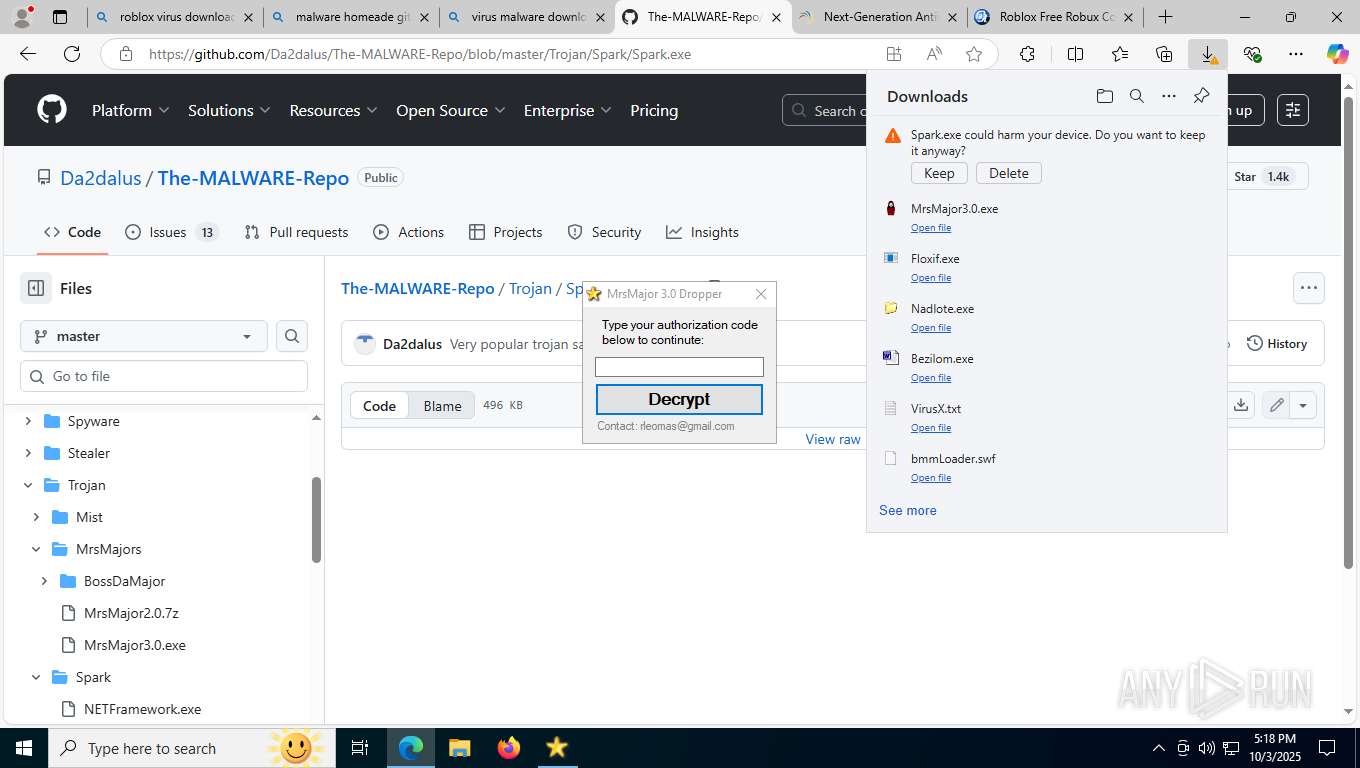
Executable content was dropped or overwritten
- Nadlote.exe (PID: 7740)
- MrsMajor3.0.exe (PID: 2400)
- Floxif.exe (PID: 4748)
- eulascr.exe (PID: 8952)
- Spark.exe (PID: 9012)
Starts application from unusual location
- Nadlote.exe (PID: 7740)
- cmd.exe (PID: 7372)
- smss.exe (PID: 788)
- ipconfig.exe (PID: 828)
- cmd.exe (PID: 8952)
- cmd.exe (PID: 7808)
- PING.EXE (PID: 9016)
- cmd.exe (PID: 8312)
- PING.EXE (PID: 2004)
- cmd.exe (PID: 10136)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7196)
- cmd.exe (PID: 9820)
- cmd.exe (PID: 9884)
- cmd.exe (PID: 4956)
- cmd.exe (PID: 592)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 7316)
- cmd.exe (PID: 7804)
- cmd.exe (PID: 4180)
- cmd.exe (PID: 8872)
- cmd.exe (PID: 6368)
- cmd.exe (PID: 9272)
- cmd.exe (PID: 8308)
- cmd.exe (PID: 6804)
- cmd.exe (PID: 4228)
- cmd.exe (PID: 9964)
- cmd.exe (PID: 9508)
- cmd.exe (PID: 9756)
- cmd.exe (PID: 592)
- cmd.exe (PID: 10132)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 3984)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 9728)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 8592)
- cmd.exe (PID: 9476)
- cmd.exe (PID: 3592)
- cmd.exe (PID: 8888)
- cmd.exe (PID: 9868)
- cmd.exe (PID: 9372)
Starts CMD.EXE for commands execution
- Nadlote.exe (PID: 7740)
- smss.exe (PID: 788)
Process uses IPCONFIG to get network configuration information
- cmd.exe (PID: 8952)
Detected use of alternative data streams (AltDS)
- smss.exe (PID: 788)
Process drops legitimate windows executable
- Floxif.exe (PID: 4748)
Executes application which crashes
- Floxif.exe (PID: 4748)
Reads security settings of Internet Explorer
- MrsMajor3.0.exe (PID: 2400)
Runs WScript without displaying logo
- wscript.exe (PID: 9932)
Runs shell command (SCRIPT)
- wscript.exe (PID: 9932)
Reads the date of Windows installation
- MrsMajor3.0.exe (PID: 2400)
The process executes VB scripts
- MrsMajor3.0.exe (PID: 2400)
Drops a system driver (possible attempt to evade defenses)
- Spark.exe (PID: 9012)
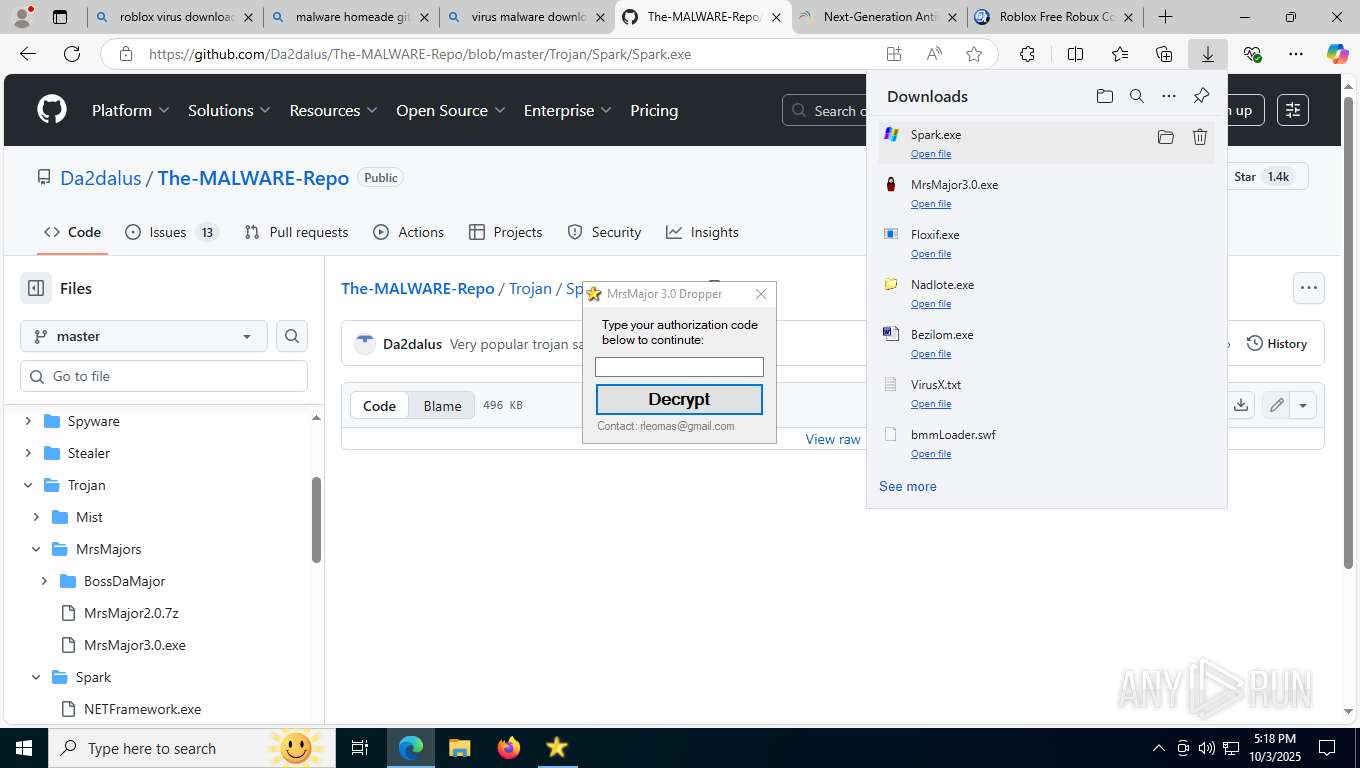
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 4608)
Checks supported languages
- identity_helper.exe (PID: 8816)
- Bezilom.exe (PID: 9388)
- Nadlote.exe (PID: 7740)
- smss.exe (PID: 788)
- Floxif.exe (PID: 4748)
- MrsMajor3.0.exe (PID: 2400)
- eulascr.exe (PID: 8952)
- Spark.exe (PID: 9012)
- Sevgi.a (1).exe (PID: 2344)
Reads the computer name
- identity_helper.exe (PID: 8816)
- Bezilom.exe (PID: 9388)
- Nadlote.exe (PID: 7740)
- smss.exe (PID: 788)
- Floxif.exe (PID: 4748)
- MrsMajor3.0.exe (PID: 2400)
- eulascr.exe (PID: 8952)
- Spark.exe (PID: 9012)
Reads Environment values
- identity_helper.exe (PID: 8816)
Reads the software policy settings
- slui.exe (PID: 9100)
- WerFault.exe (PID: 8920)
Checks proxy server information
- slui.exe (PID: 9100)
- WerFault.exe (PID: 8920)
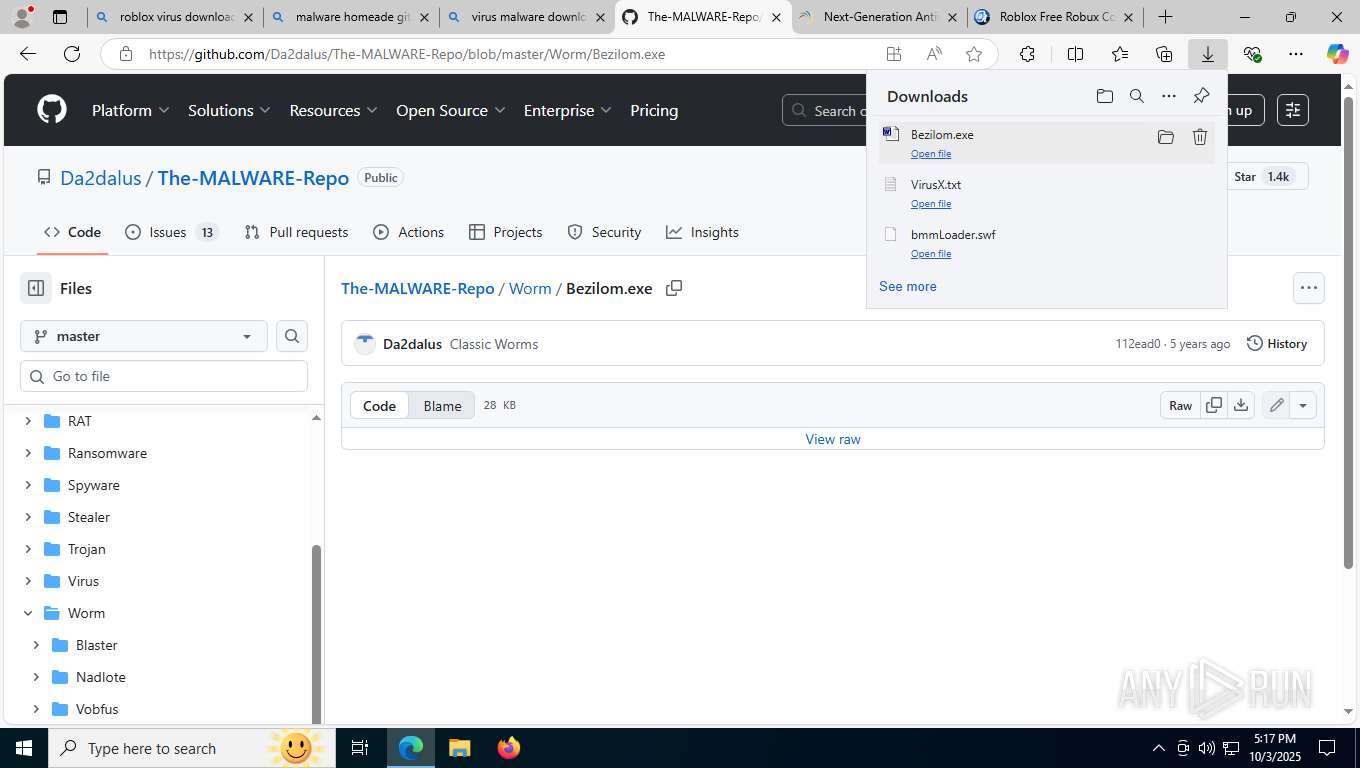
Launching a file from the Downloads directory
- msedge.exe (PID: 4608)
Application launched itself
- msedge.exe (PID: 4608)
Reads security settings of Internet Explorer
- notepad.exe (PID: 10192)
The sample compiled with english language support
- msedge.exe (PID: 8020)
- msedge.exe (PID: 4608)
- Nadlote.exe (PID: 7740)
- Floxif.exe (PID: 4748)
Create files in a temporary directory
- Bezilom.exe (PID: 9388)
- Nadlote.exe (PID: 7740)
- smss.exe (PID: 788)
- Floxif.exe (PID: 4748)
- MrsMajor3.0.exe (PID: 2400)
- eulascr.exe (PID: 8952)
Executable content was dropped or overwritten
- msedge.exe (PID: 8020)
- msedge.exe (PID: 4608)
Failed to create an executable file in Windows directory
- Bezilom.exe (PID: 9388)
- Nadlote.exe (PID: 7740)
- smss.exe (PID: 788)
- Floxif.exe (PID: 4748)
Launching a file from a Registry key
- Bezilom.exe (PID: 9388)
The sample compiled with chinese language support
- msedge.exe (PID: 4608)
- msedge.exe (PID: 8020)
Creates files or folders in the user directory
- WerFault.exe (PID: 8920)
Process checks computer location settings
- MrsMajor3.0.exe (PID: 2400)
Reads the machine GUID from the registry
- eulascr.exe (PID: 8952)
- Spark.exe (PID: 9012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
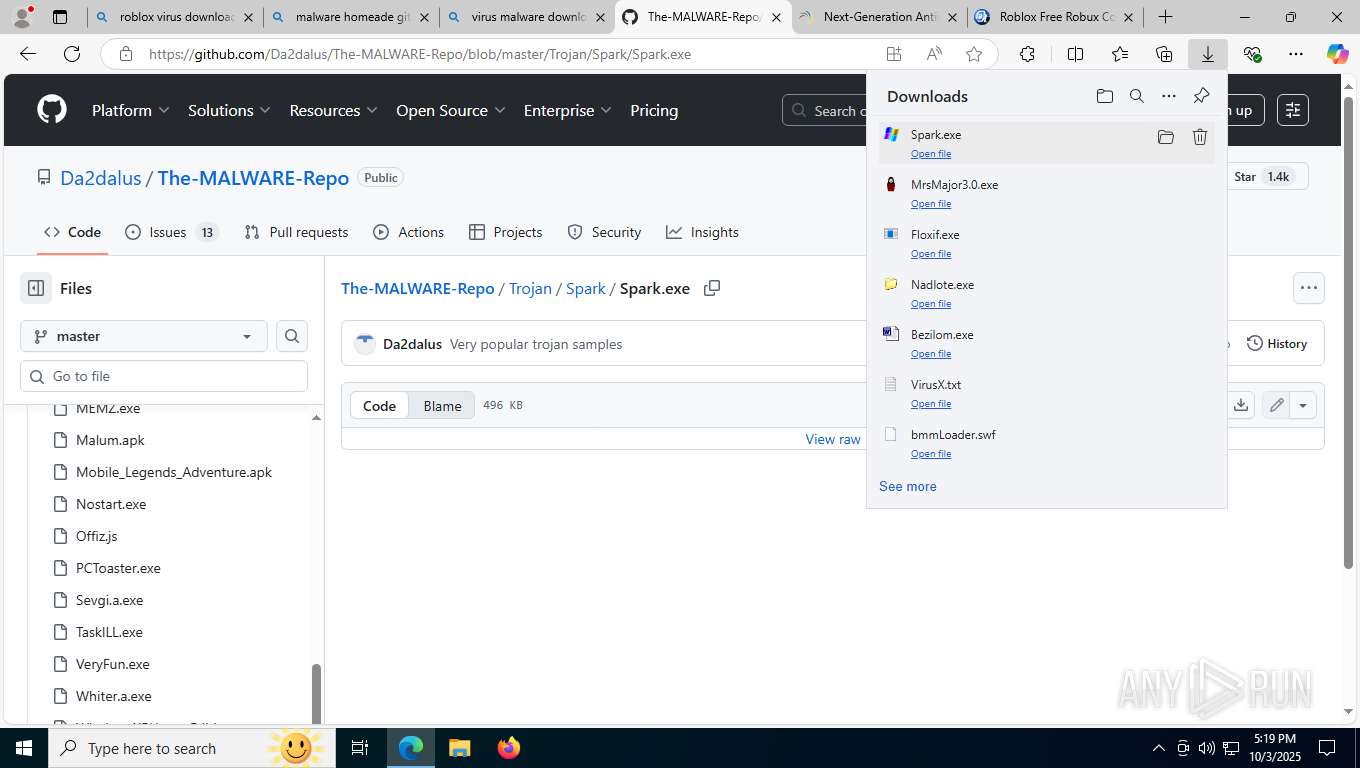
TRiD
| .swf | | | Macromedia Flash Player Compressed Movie (100) |
|---|
EXIF
Flash
| FlashVersion: | 34 |
|---|---|
| Compressed: | |
| ImageWidth: | 800 |
| ImageHeight: | 480 |
| FrameRate: | 30 |
| FrameCount: | 1 |
| Duration: | 0.03 s |
| FlashAttributes: | ActionScript3, [6] |
Composite
| ImageSize: | 800x480 |
|---|---|
| Megapixels: | 0.384 |
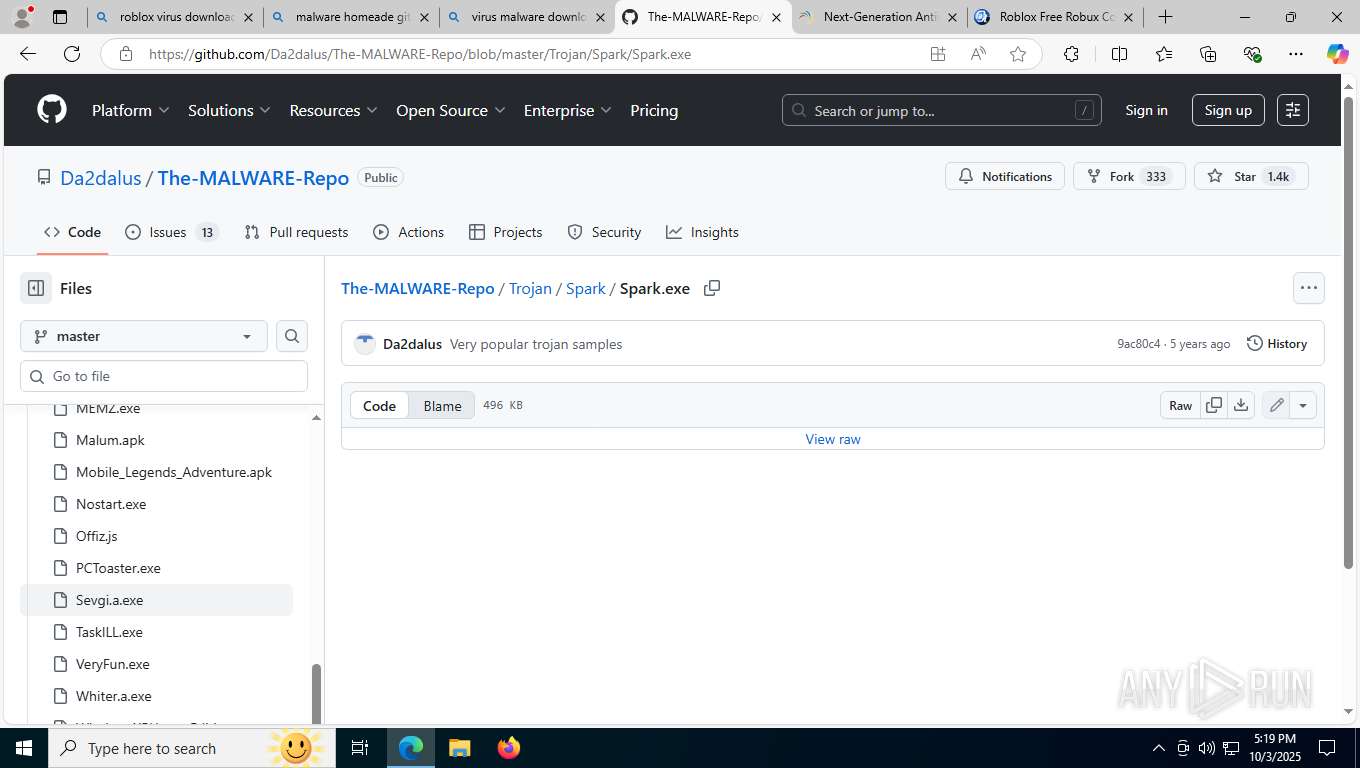
Total processes
394
Monitored processes
215
Malicious processes
9
Suspicious processes
20
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=28 --always-read-main-dll --field-trial-handle=8112,i,15432077384381568754,10268371136871221858,262144 --variations-seed-version --mojo-platform-channel-handle=8120 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 592 | cmd /c REG ADD HKLM\Software\MICROSOFT\WINDOWS\CURRENTVERSION\RUN /V smss /t REG_SZ /d "smss\smss.exe " /f | C:\Windows\SysWOW64\cmd.exe | — | smss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 592 | cmd /c REG ADD HKCU\Software\MICROSOFT\WINDOWS\CURRENTVERSION\RUN /V Csrss /t REG_SZ /d "c:\RECYCLER\smss.exe " /f | C:\Windows\SysWOW64\cmd.exe | — | smss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 704 | REG ADD HKCU\Software\MICROSOFT\WINDOWS\CURRENTVERSION\RUN /V Csrss /t REG_SZ /d "c:\RECYCLER\smss.exe " /f | C:\Windows\SysWOW64\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 788 | c:\RECYCLER\smss.exe | C:\RECYCLER\smss.exe | — | cmd.exe | |||||||||||
User: admin Company: Free Microsoft Games Integrity Level: MEDIUM Version: 5.05 Modules
| |||||||||||||||
| 828 | ipconfig | C:\Windows\SysWOW64\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1308 | REG ADD HKCU\Software\MICROSOFT\WINDOWS\CURRENTVERSION\RUN /V Csrss /t REG_SZ /d "c:\RECYCLER\smss.exe " /f | C:\Windows\SysWOW64\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1320 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1380 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
28 468
Read events
26 838
Write events
1 624
Delete events
6
Modification events
| (PID) Process: | (4608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (4608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Defaults |
| Operation: | write | Name: | is_dse_recommended |
Value: 1 | |||
| (PID) Process: | (4608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Defaults |
| Operation: | write | Name: | is_startup_page_recommended |
Value: 1 | |||
| (PID) Process: | (4608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | lastrun |
Value: 13403985264097432 | |||
| (PID) Process: | (4608) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262780 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {70C11B59-3CFD-4B4E-A817-CAEEB2BB3586} | |||
| (PID) Process: | (6752) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (6752) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (6752) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (6752) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (6752) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
Executable files
53
Suspicious files
977
Text files
103
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17100d.TMP | — | |
MD5:— | SHA256:— | |||
| 4608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17101d.TMP | — | |
MD5:— | SHA256:— | |||
| 4608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF17104c.TMP | — | |
MD5:— | SHA256:— | |||
| 4608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17104c.TMP | — | |
MD5:— | SHA256:— | |||
| 4608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17104c.TMP | — | |
MD5:— | SHA256:— | |||
| 4608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
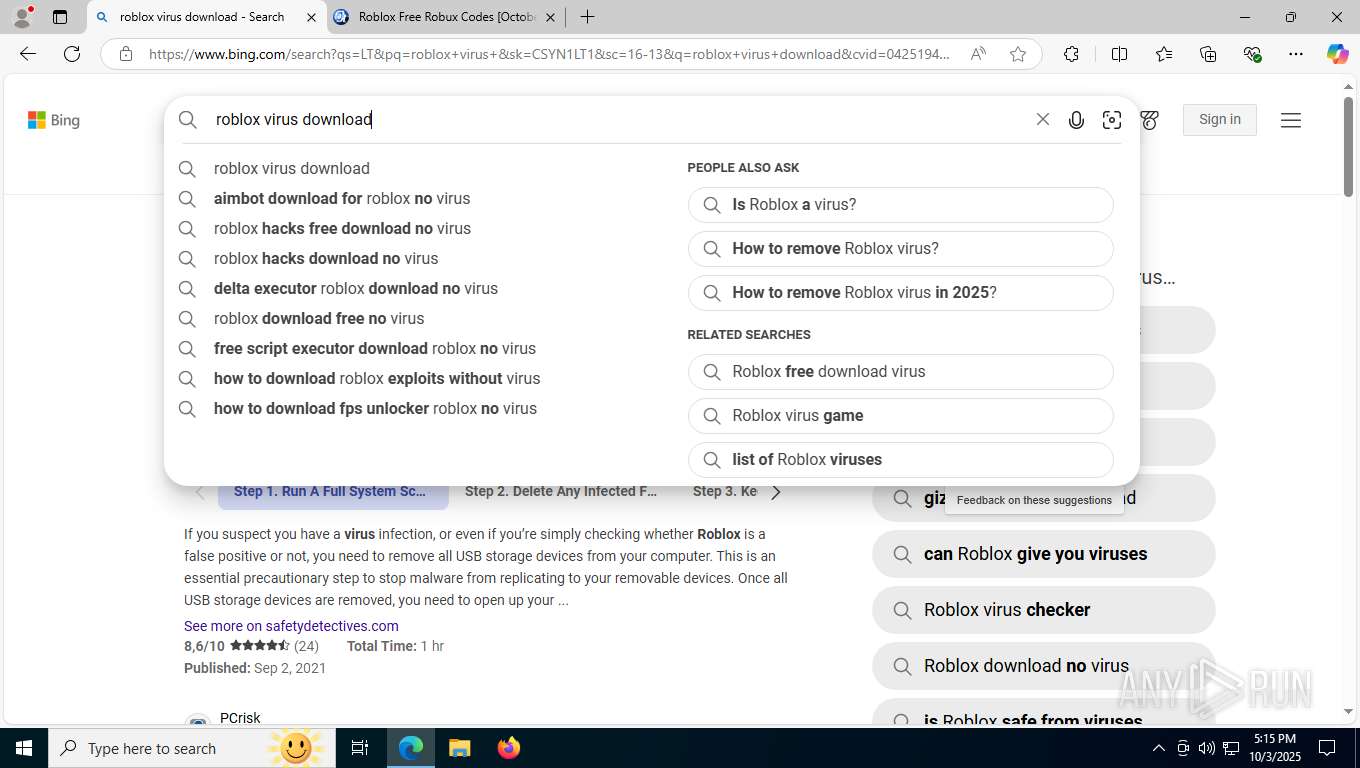
HTTP(S) requests
27
TCP/UDP connections
289
DNS requests
383
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8020 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:dkjNpcLeEBY7sPjRX9Nj53xp6fXY0ZJt9_LI6sLBdf8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 96 b | whitelisted |
7988 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7988 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
8776 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
9052 | svchost.exe | HEAD | 200 | 2.16.10.177:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1759855200&P2=404&P3=2&P4=iGq4RStsYLHPp2GLlSbG%2bcjoaAWDolrP0npYTI7CppuYQPoVGhile7o5XapVNhIOvkDsUaddr%2fquY%2bFnpcve6w%3d%3d | AT | — | — | whitelisted |
8792 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
8652 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
9052 | svchost.exe | GET | 206 | 2.16.10.177:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1759855200&P2=404&P3=2&P4=iGq4RStsYLHPp2GLlSbG%2bcjoaAWDolrP0npYTI7CppuYQPoVGhile7o5XapVNhIOvkDsUaddr%2fquY%2bFnpcve6w%3d%3d | AT | binary | 1.09 Kb | whitelisted |
9052 | svchost.exe | HEAD | 200 | 2.16.10.177:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1759855202&P2=404&P3=2&P4=BqyXmff%2btDkl5SFdJRJZi%2fis7Ff4RXjFkJ1RtmRgxns1jQ1rD9qEVN4zI2how8djhRw8zt2GENgs9R2gPY7ERw%3d%3d | AT | compressed | 770 b | whitelisted |
9052 | svchost.exe | GET | 206 | 2.16.10.177:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1759855200&P2=404&P3=2&P4=iGq4RStsYLHPp2GLlSbG%2bcjoaAWDolrP0npYTI7CppuYQPoVGhile7o5XapVNhIOvkDsUaddr%2fquY%2bFnpcve6w%3d%3d | AT | compressed | 770 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6016 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
8108 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
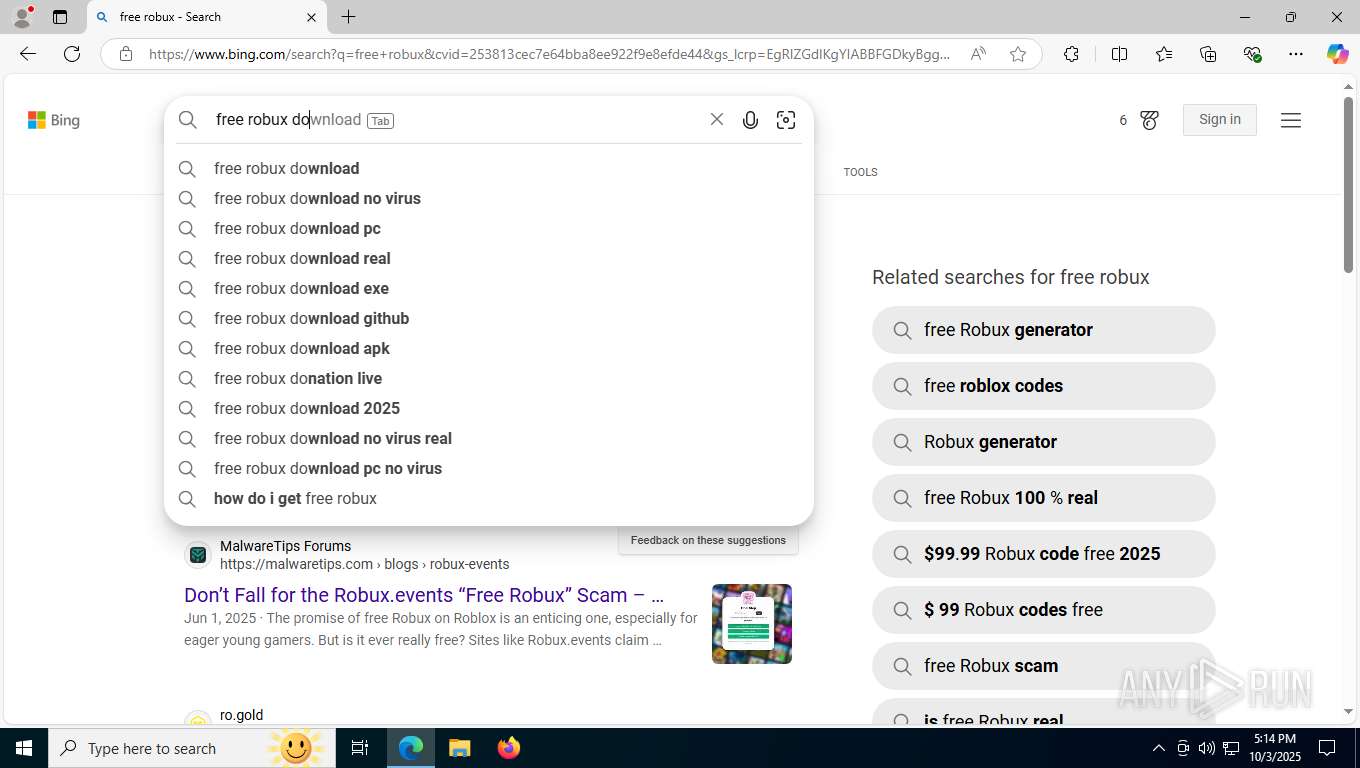
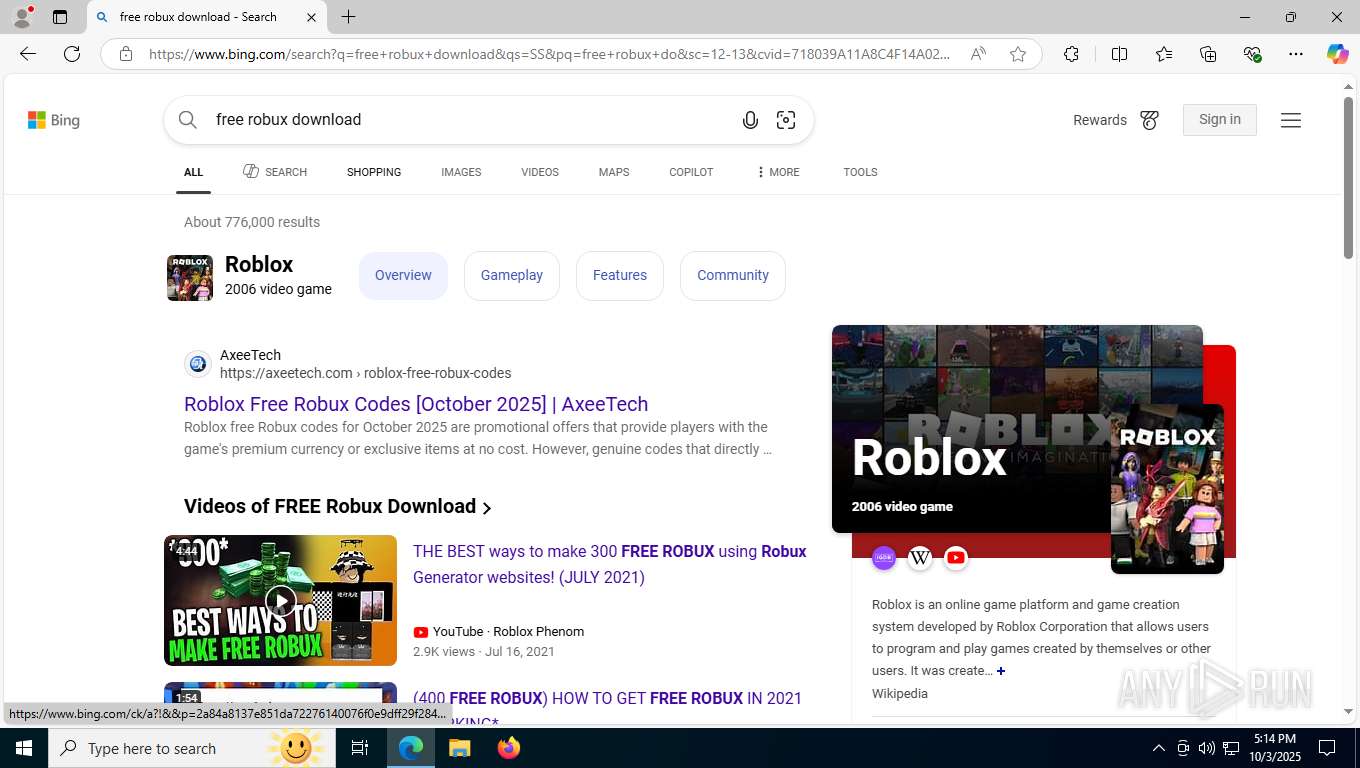
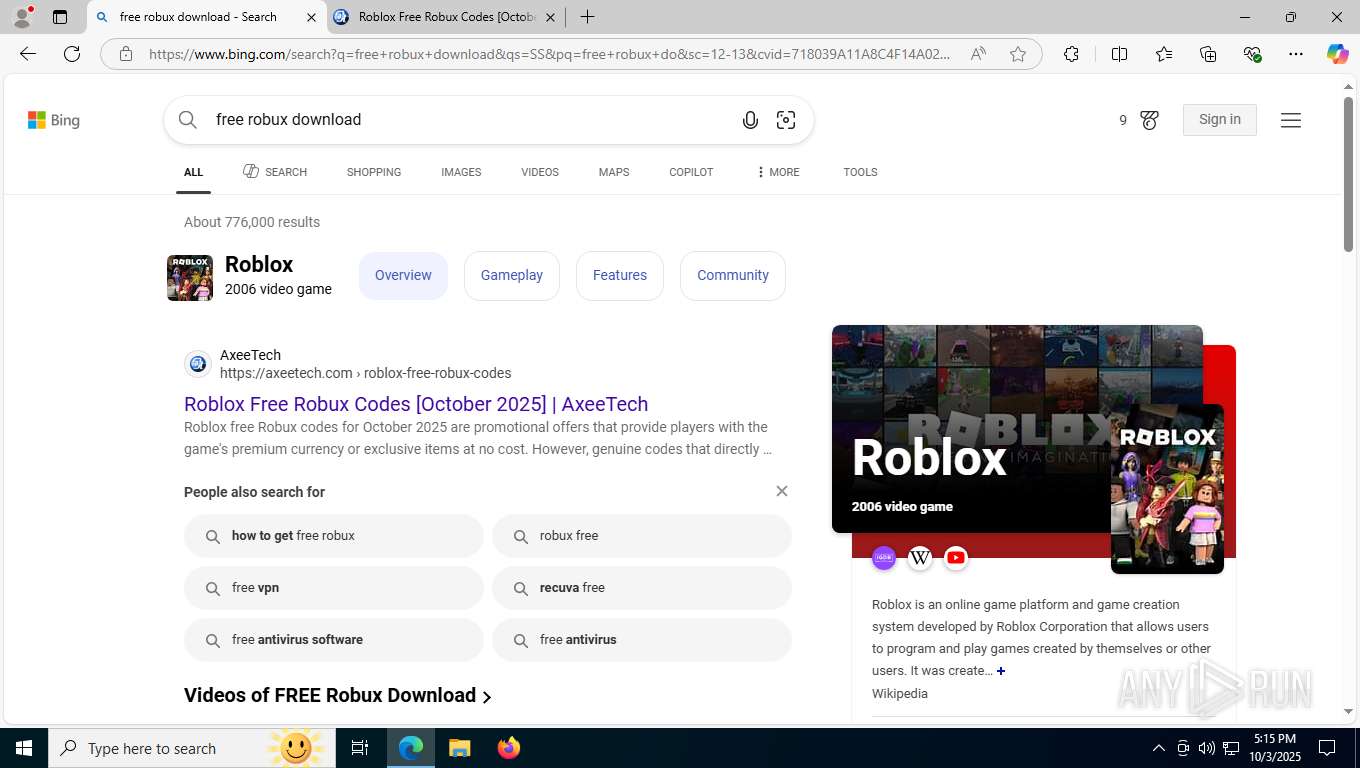
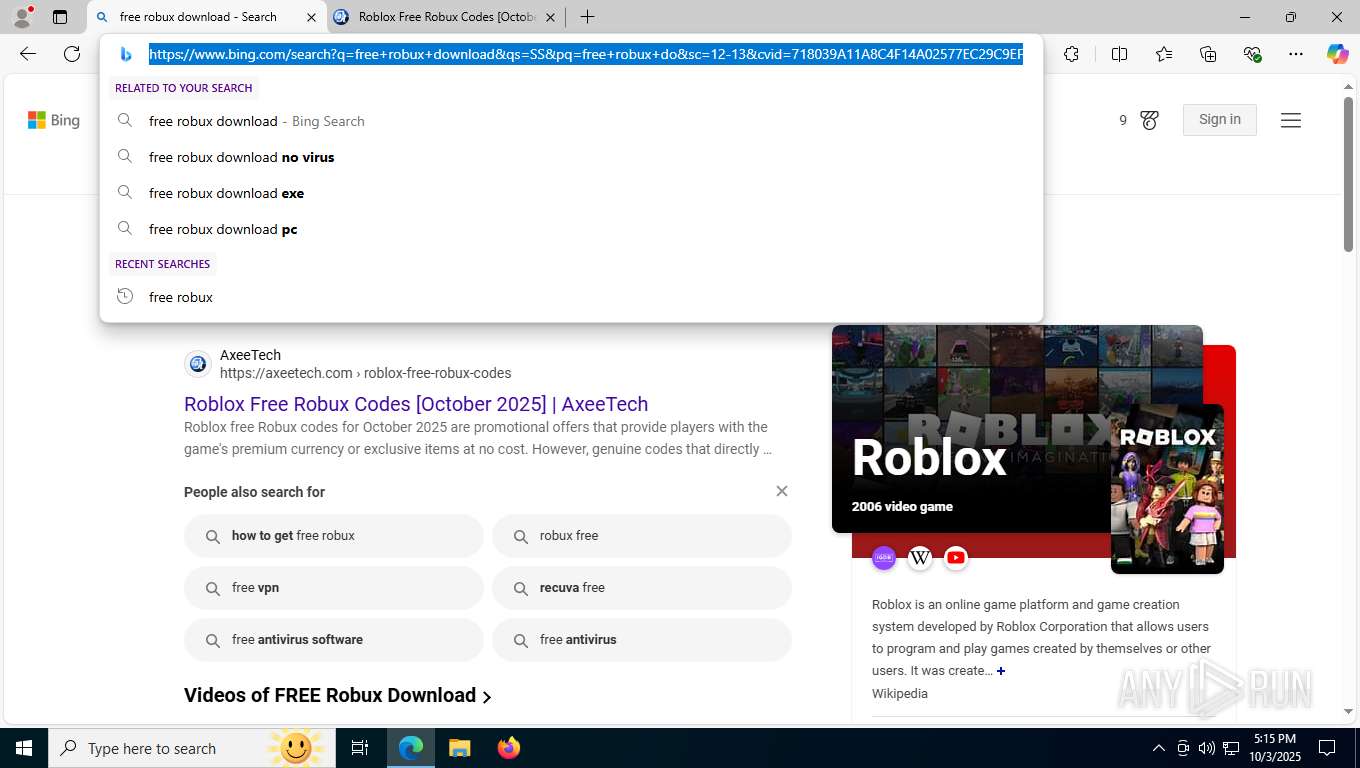
5224 | SearchApp.exe | 2.16.241.201:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
8020 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8020 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8020 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8020 | msedge.exe | 172.217.18.3:443 | update.googleapis.com | GOOGLE | US | whitelisted |
8020 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
8020 | msedge.exe | 2.16.241.201:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
www.googleapis.com |
| whitelisted |
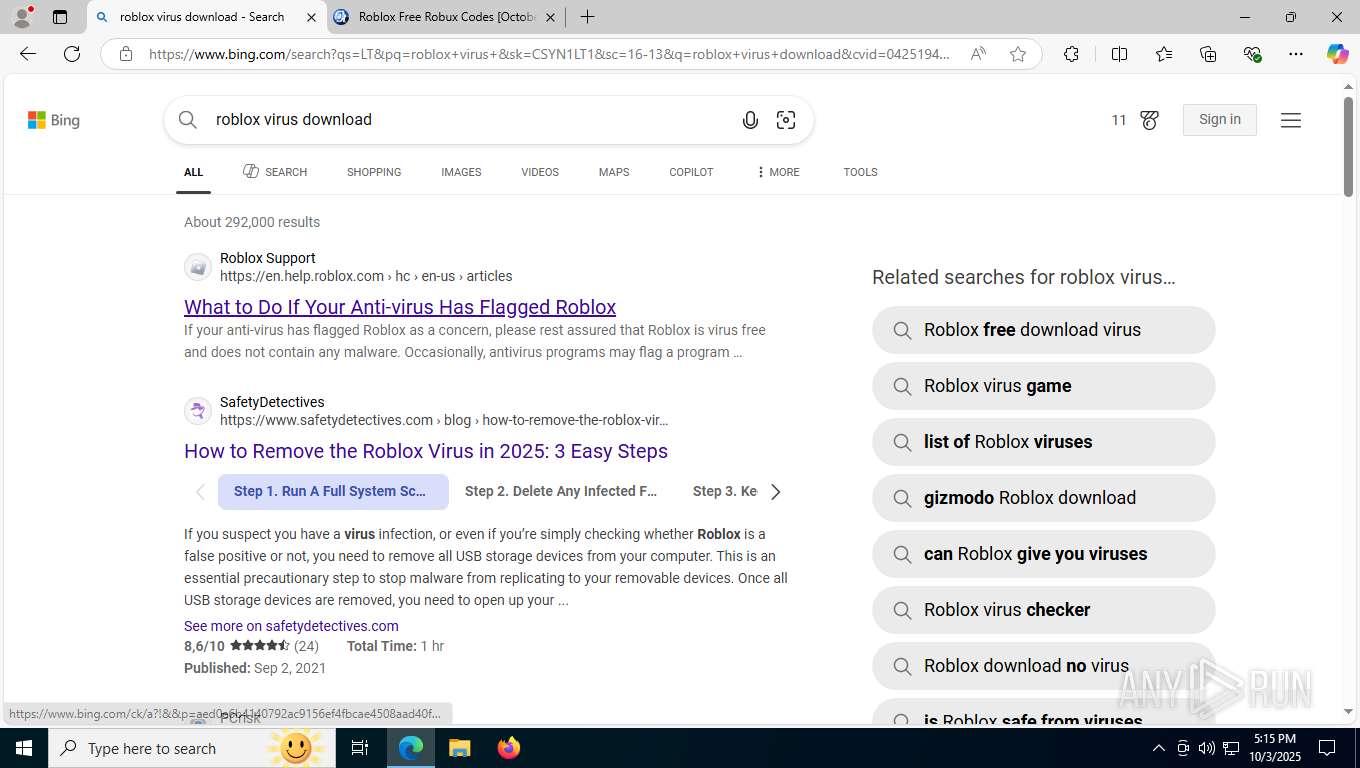
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
8020 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
8020 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
8020 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
8020 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
8020 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
8020 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
8020 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
8020 | msedge.exe | Misc activity | INFO [ANY.RUN] .cc TLD domain request |