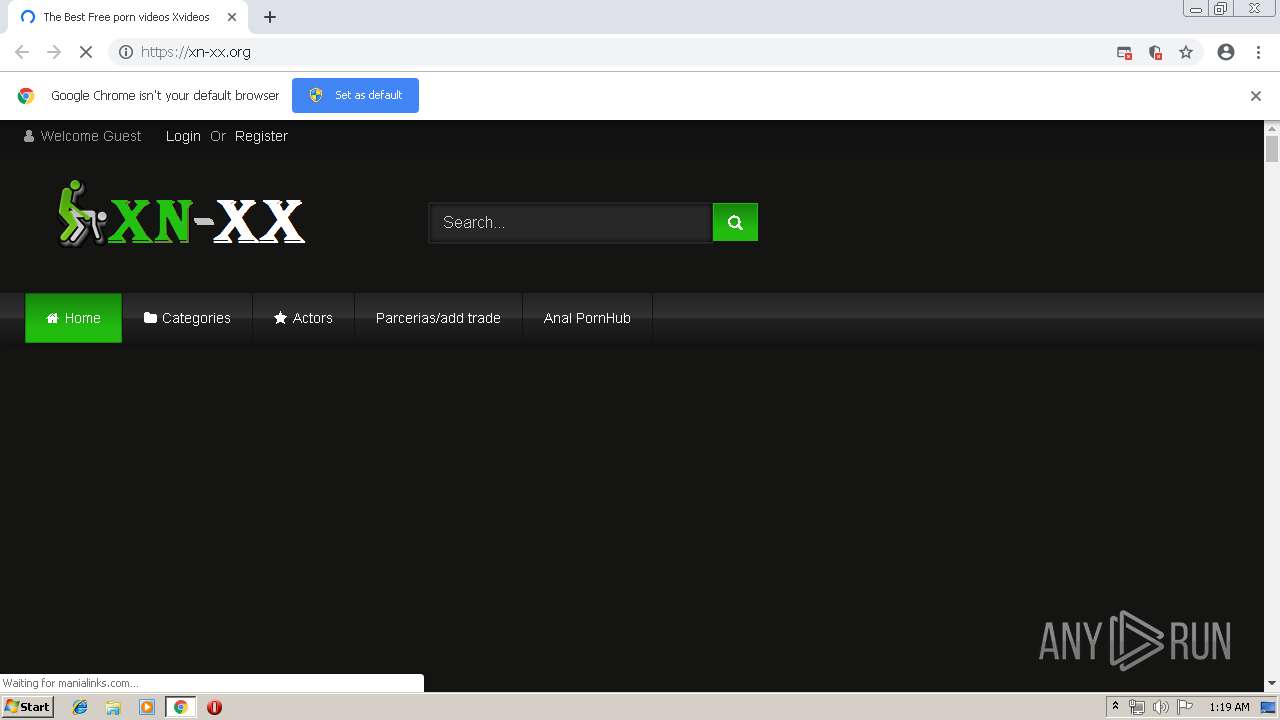
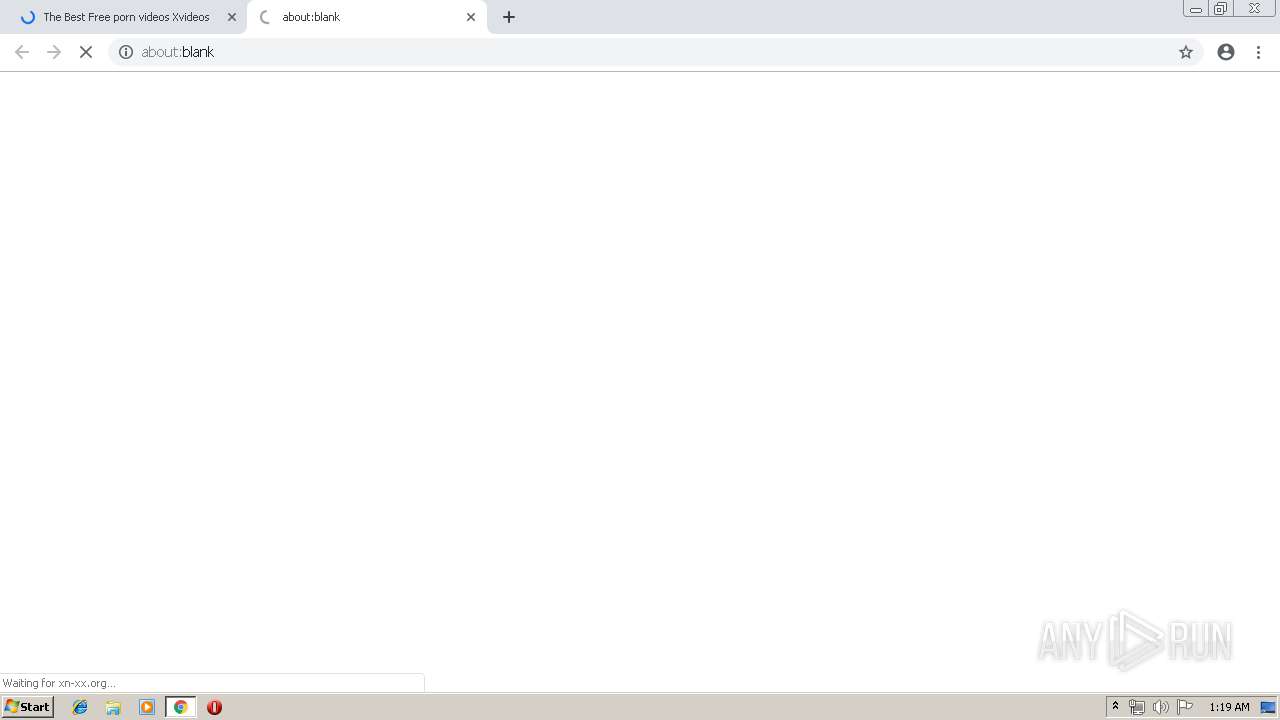
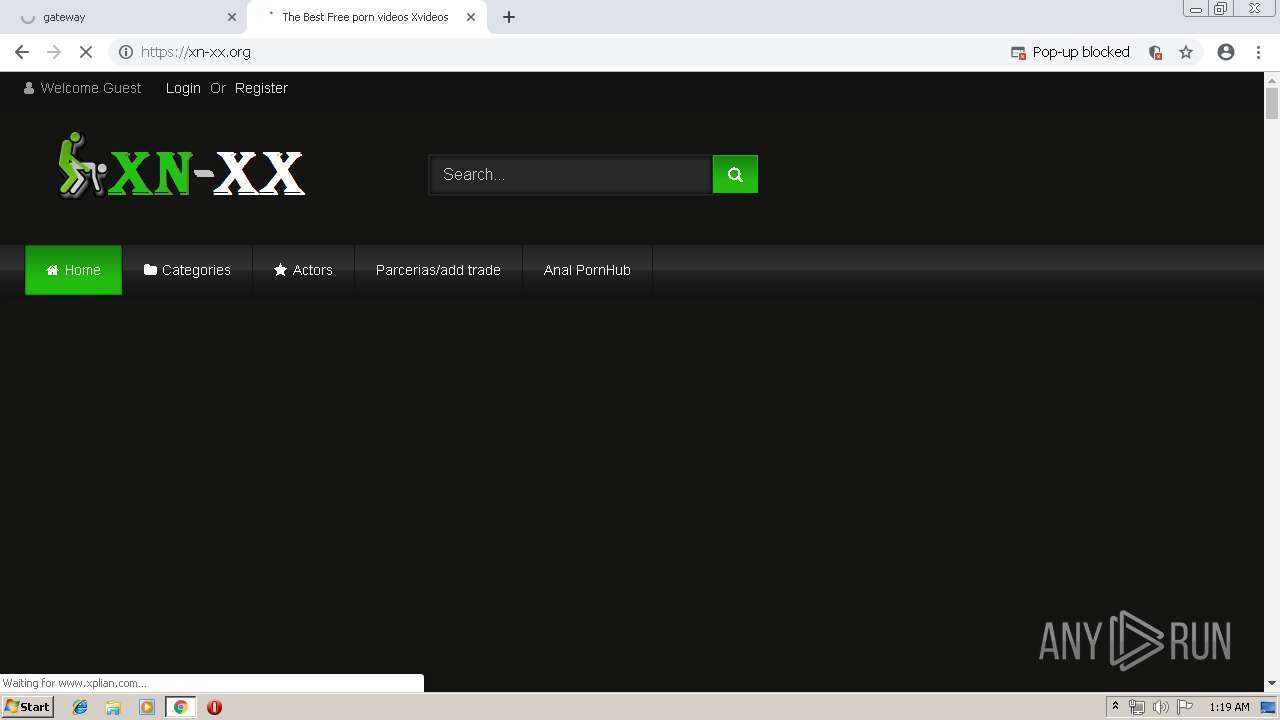
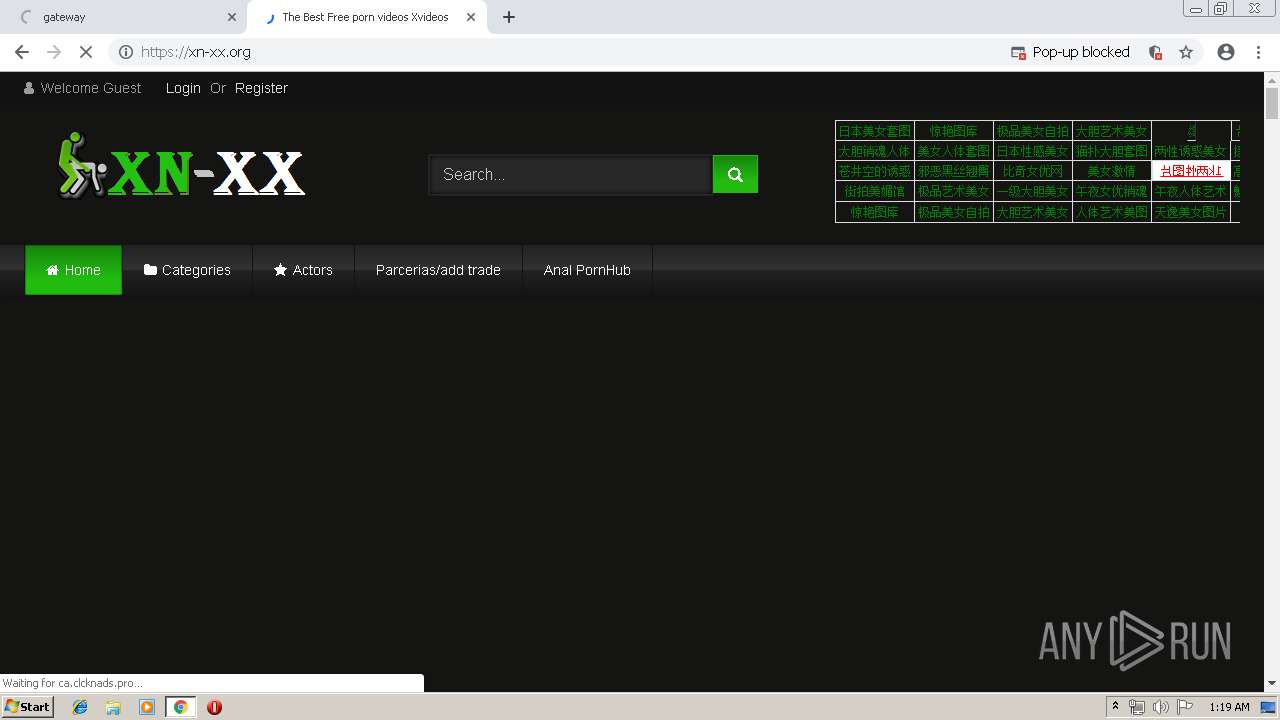
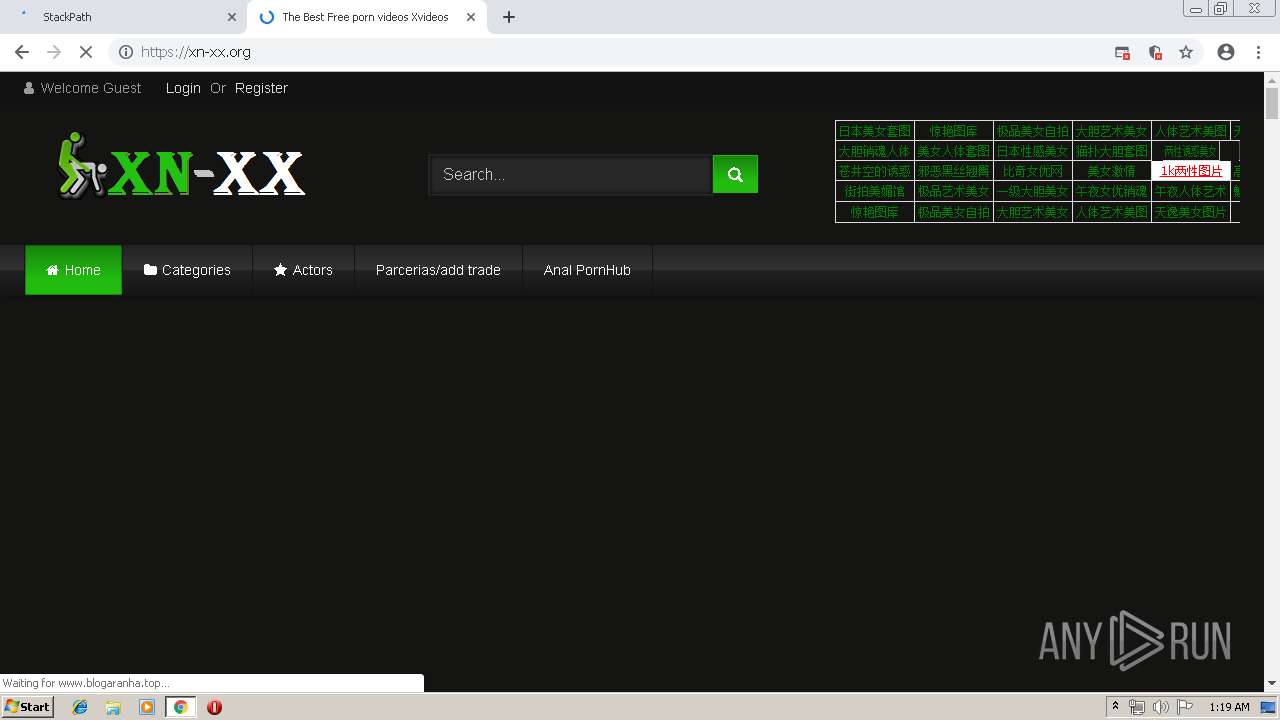
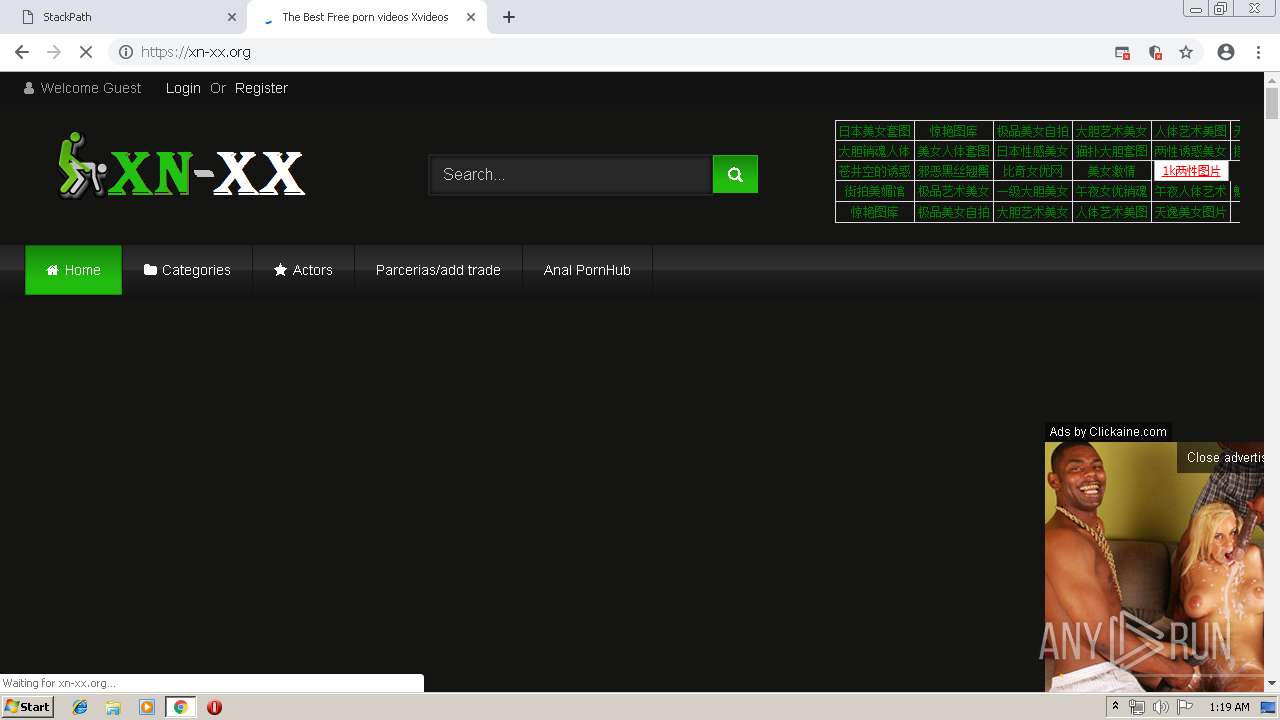
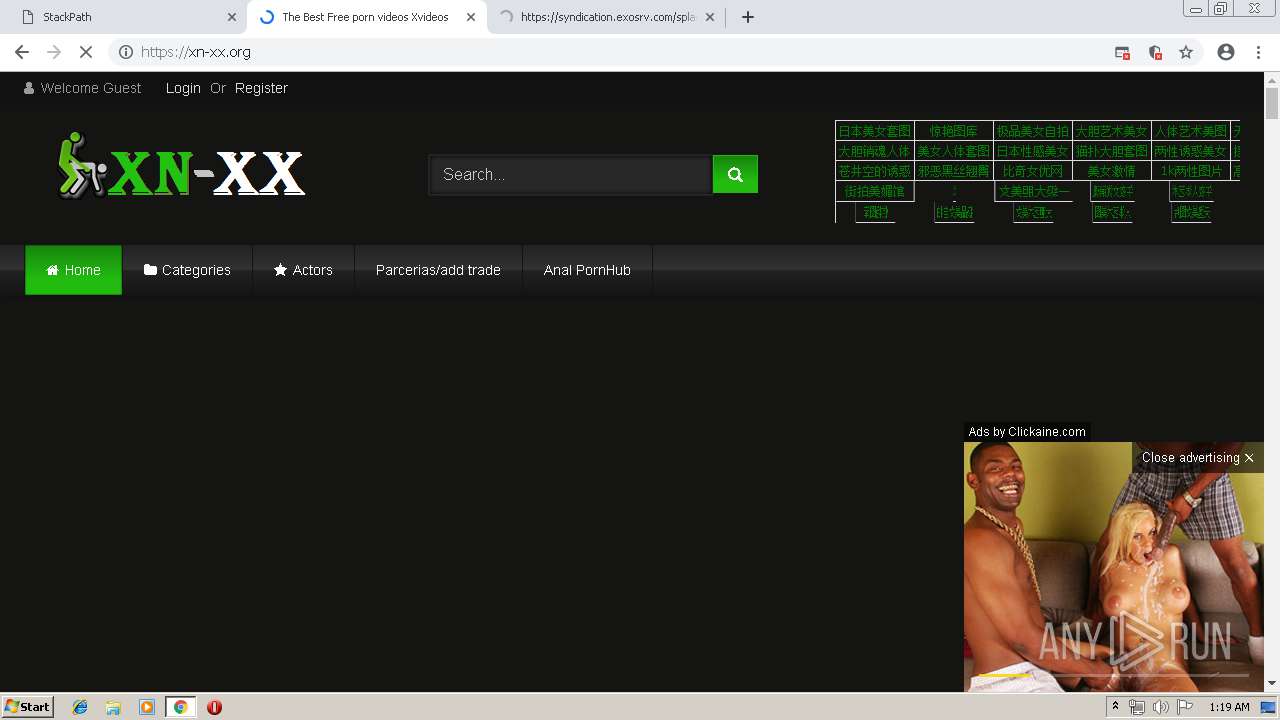
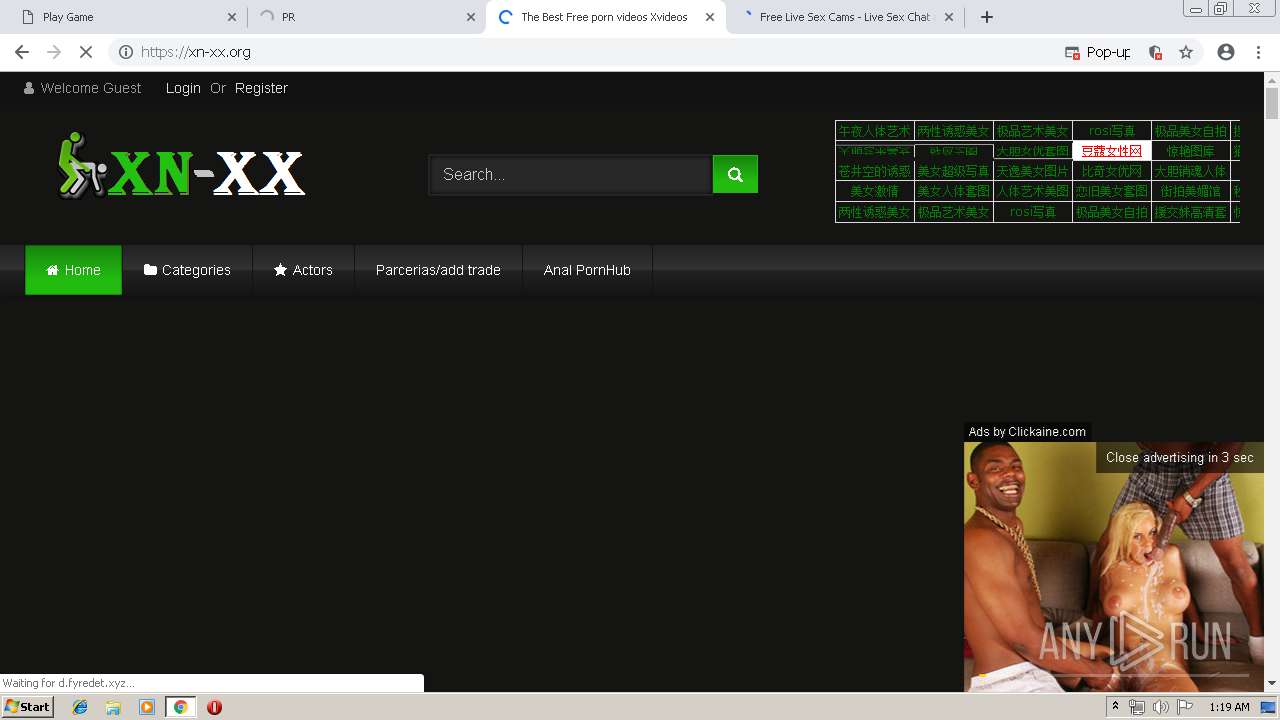
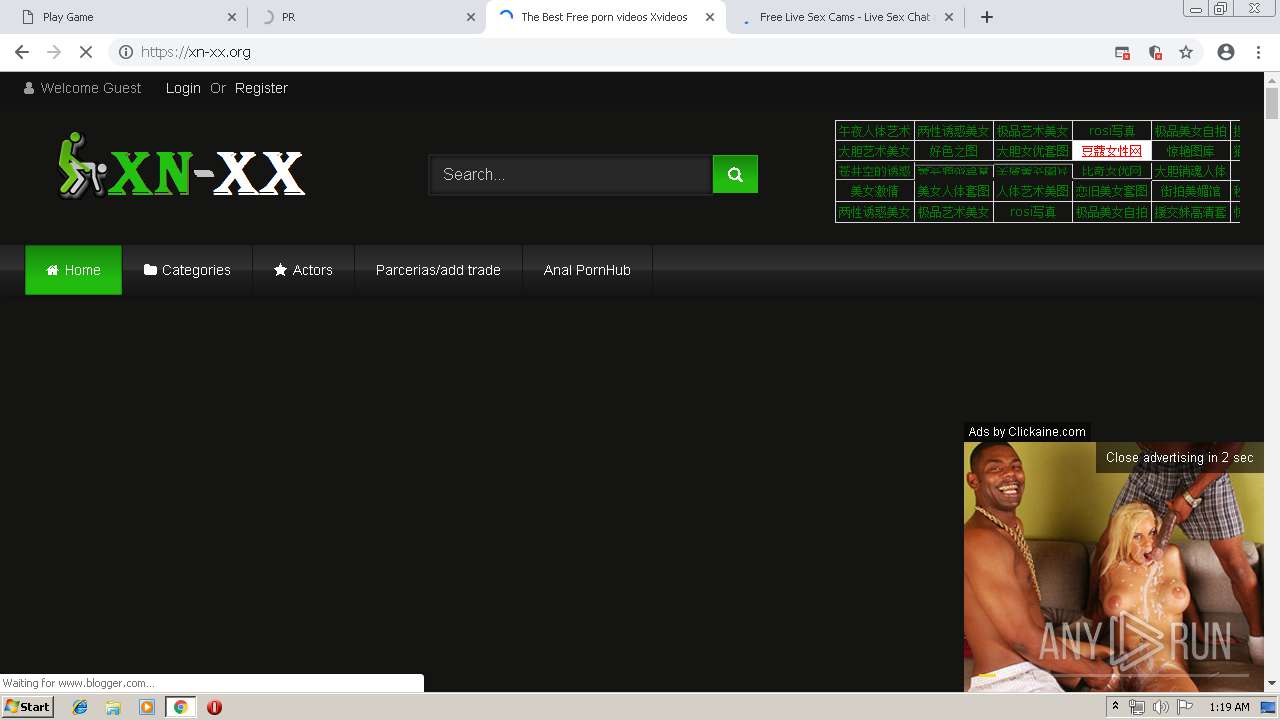
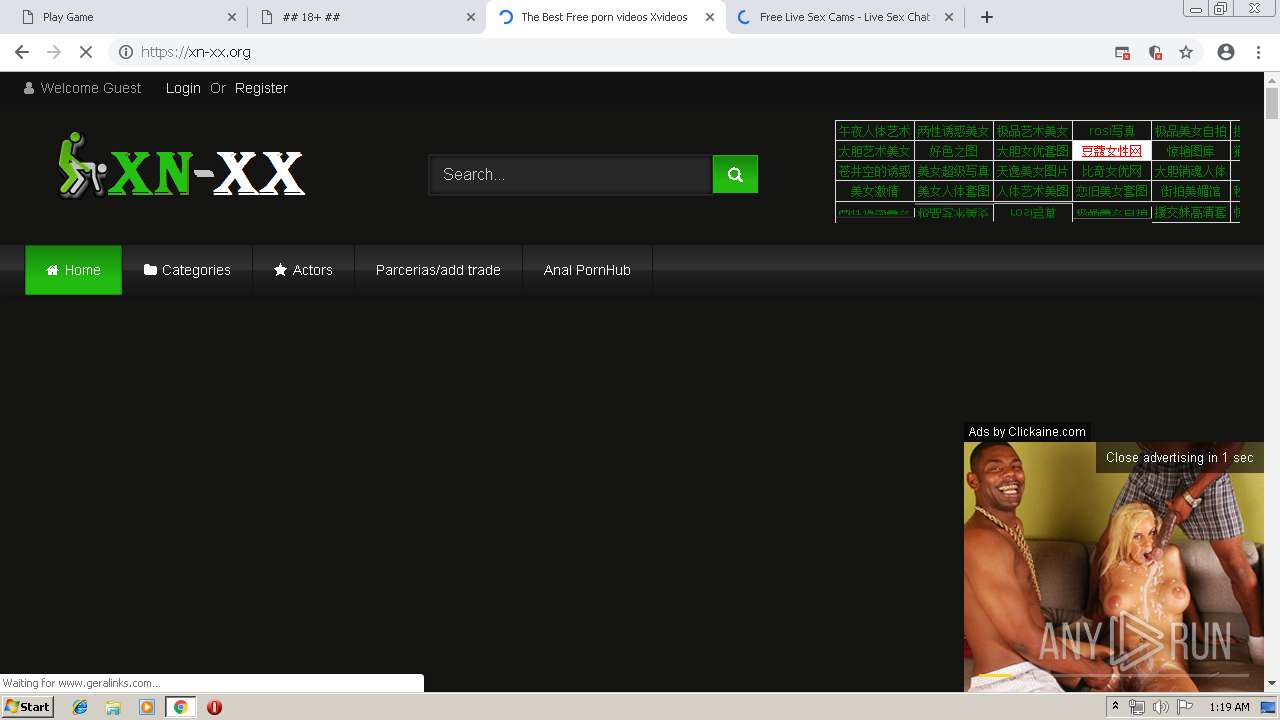
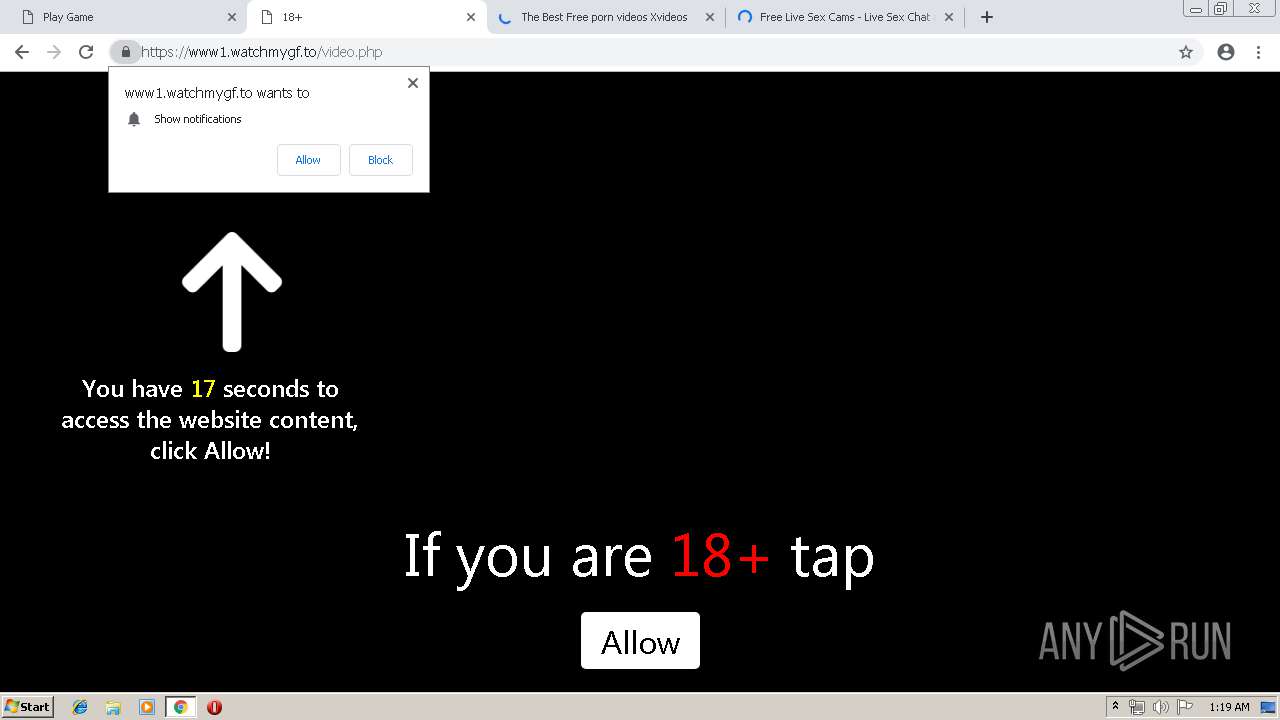
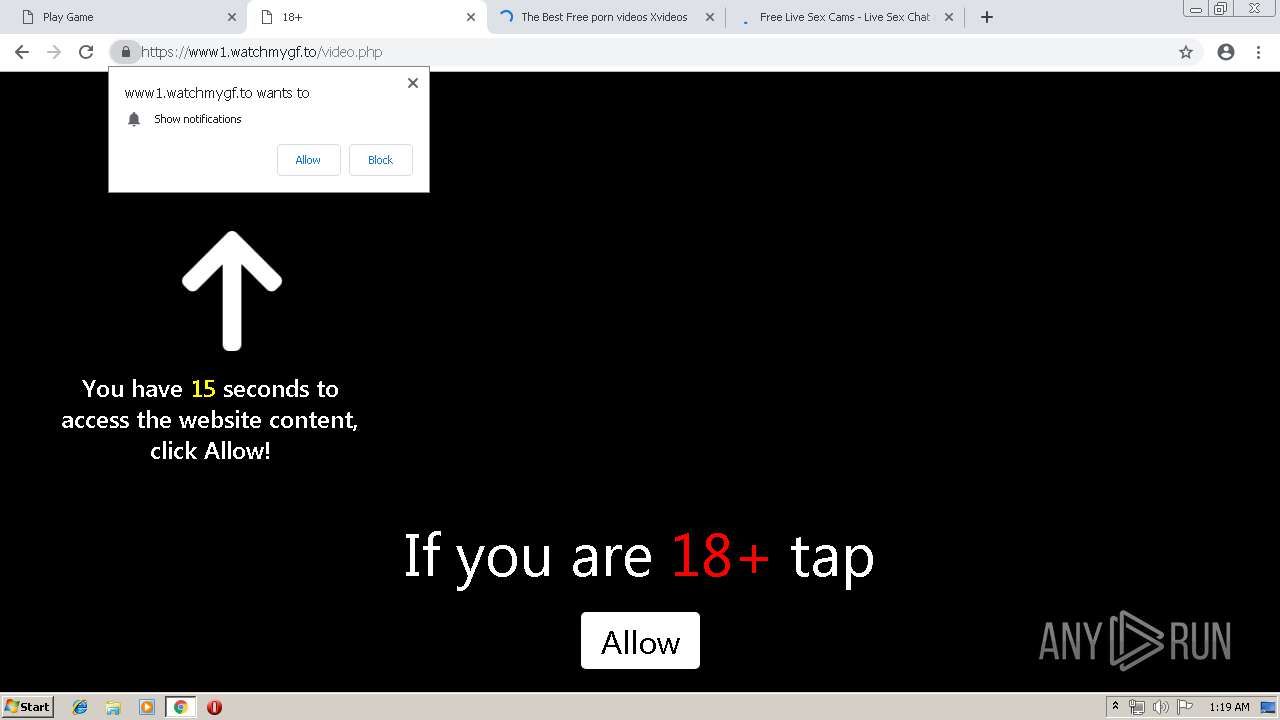
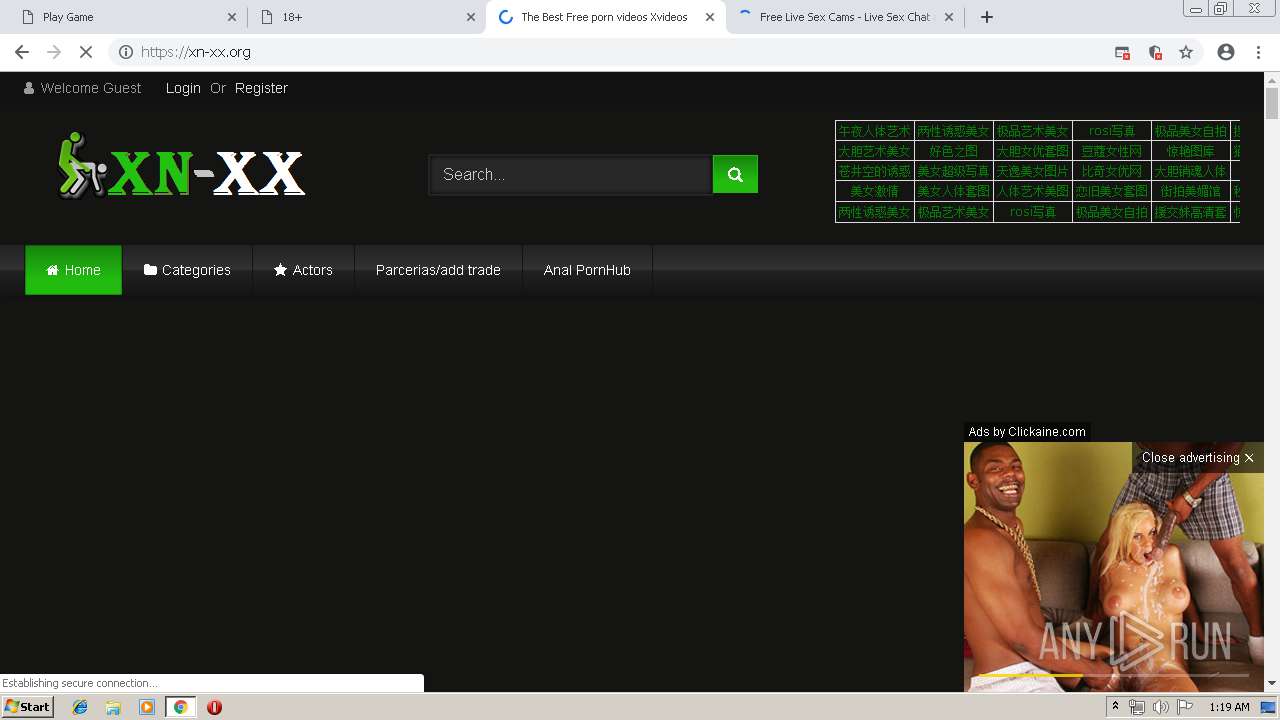
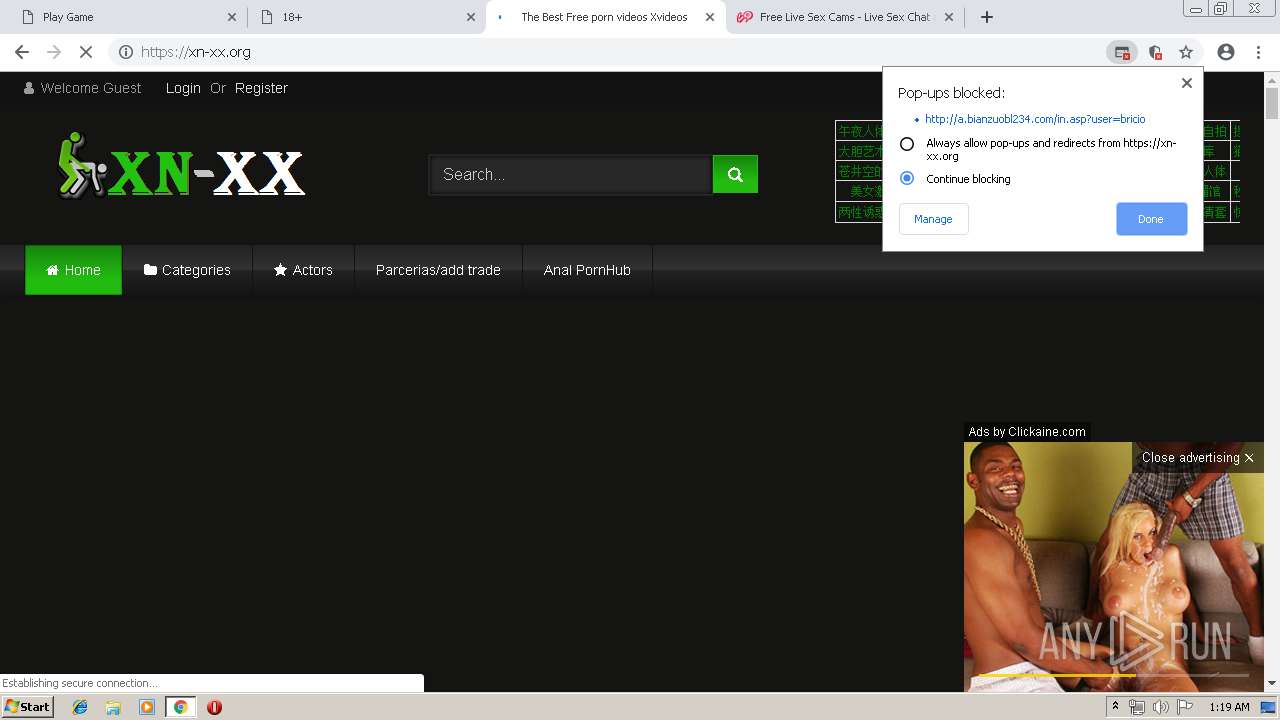
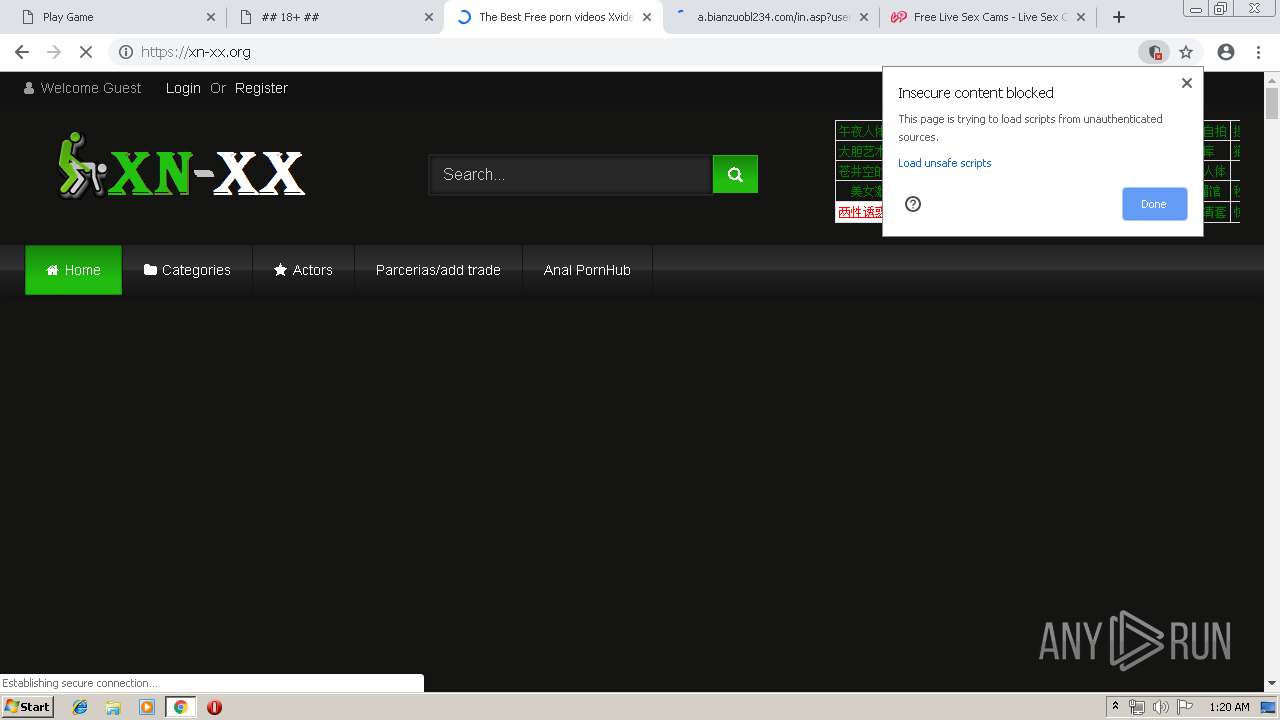
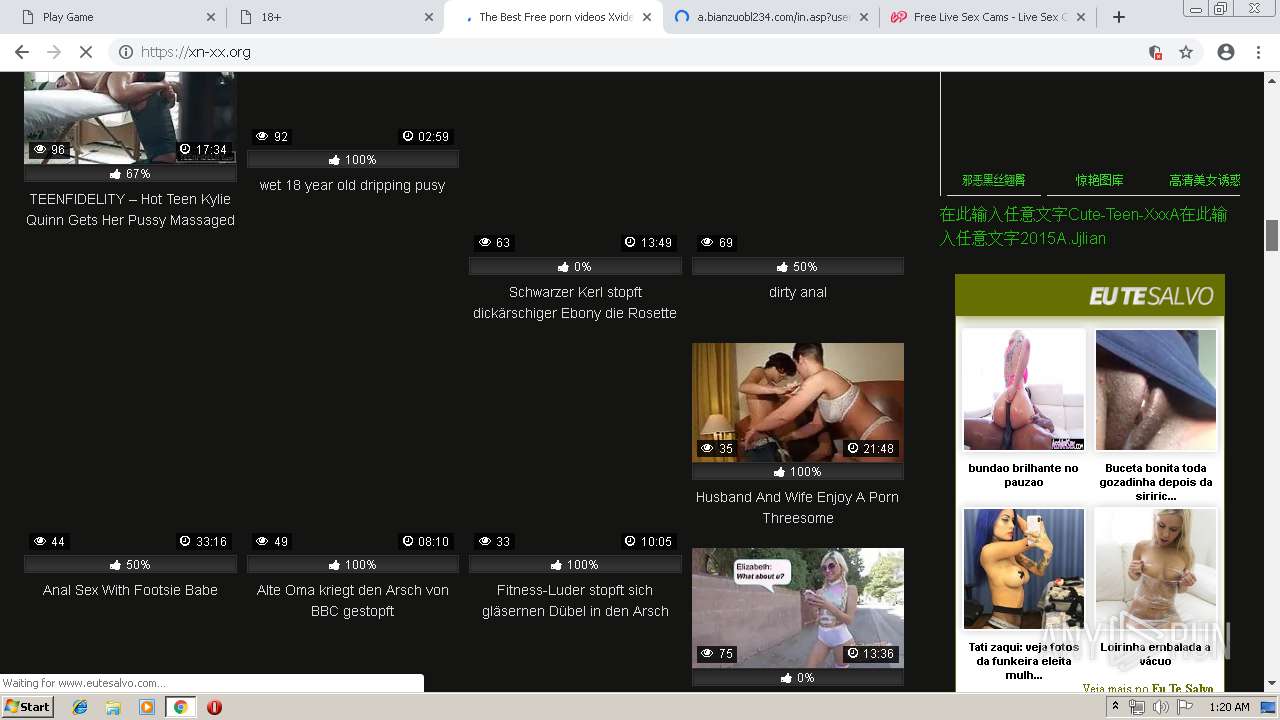
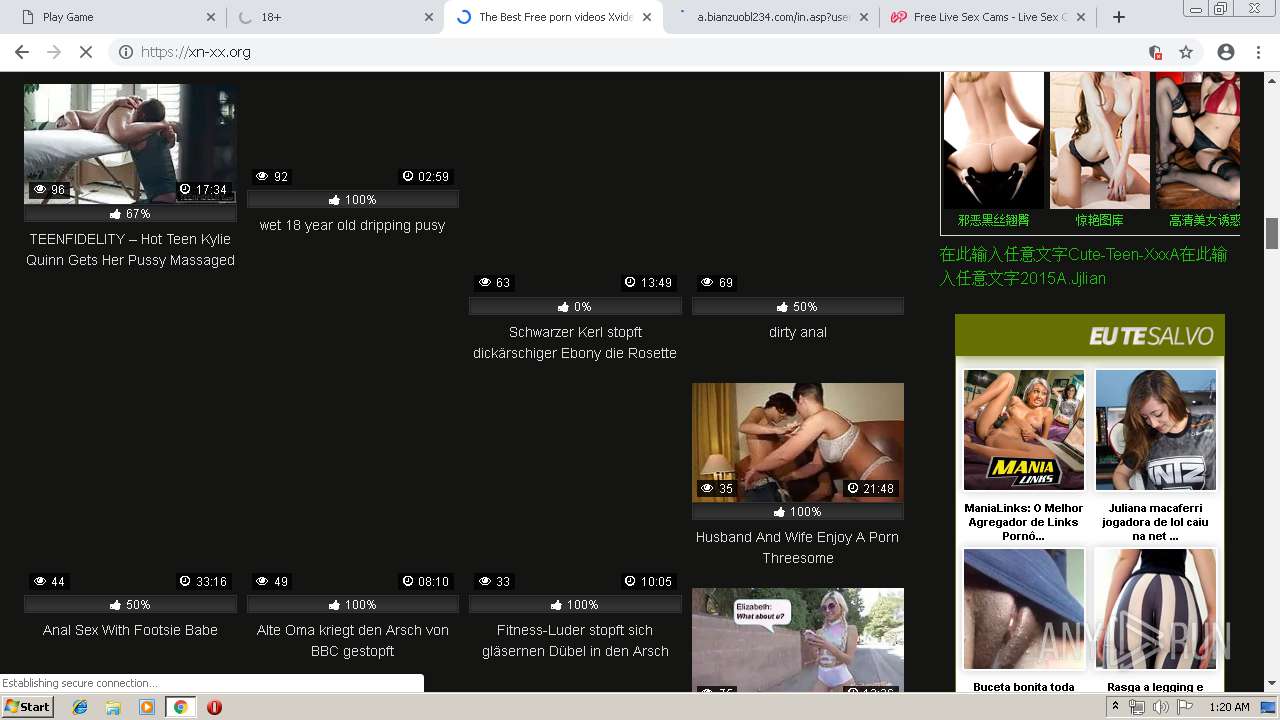
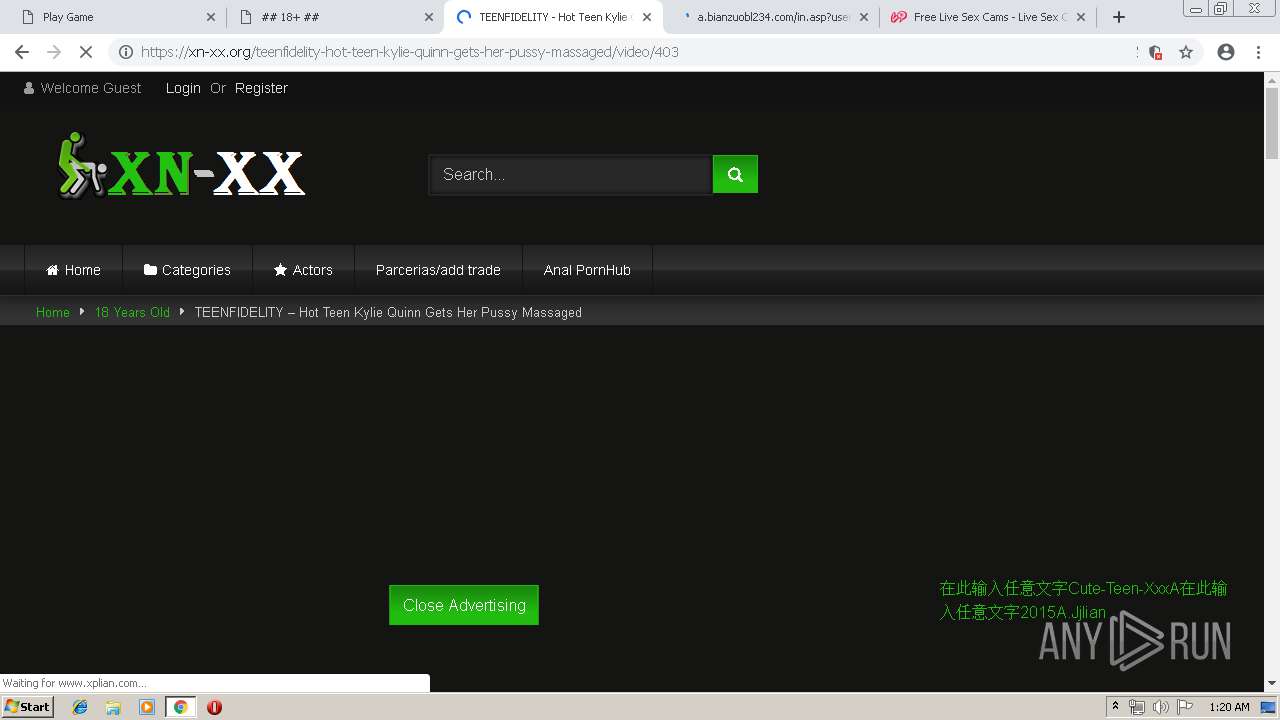
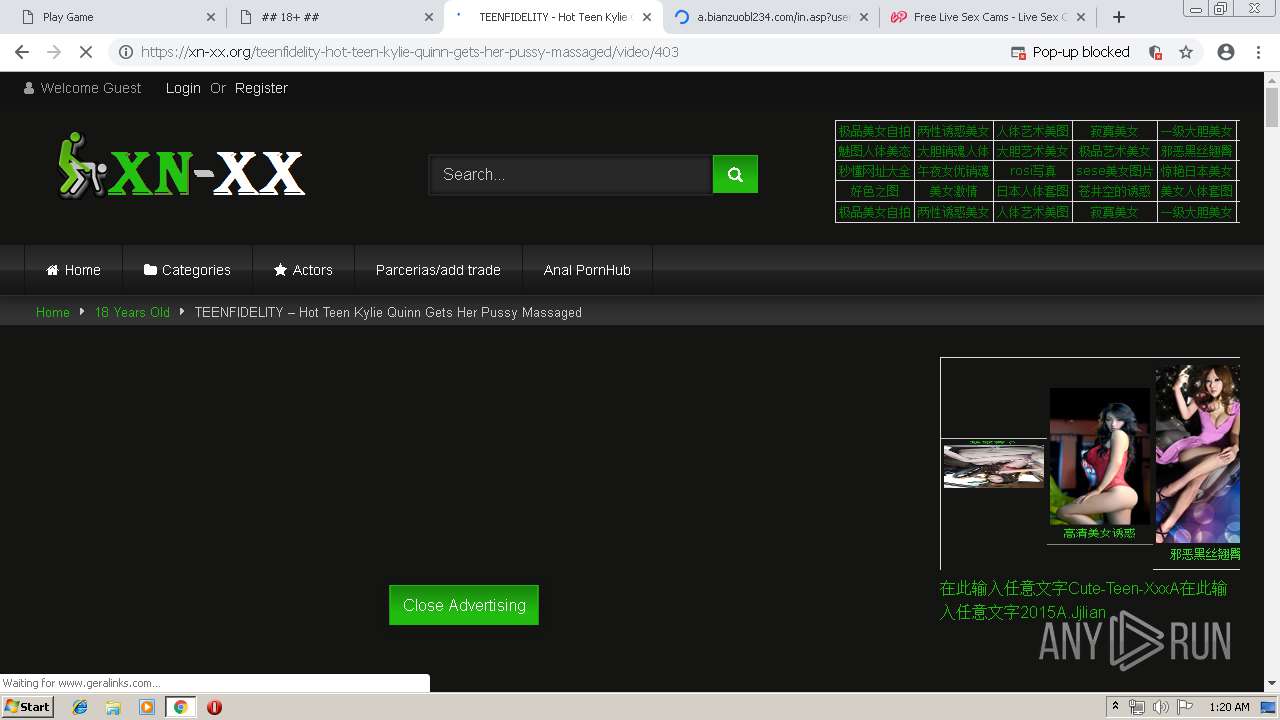
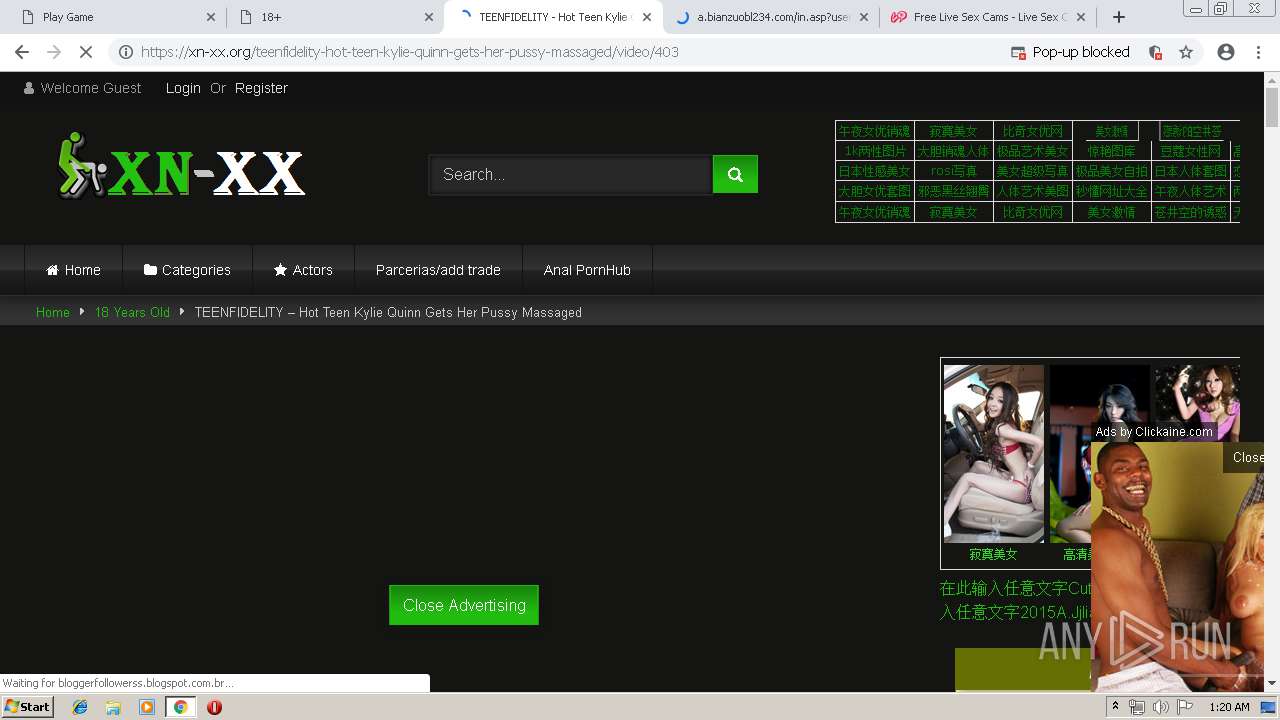
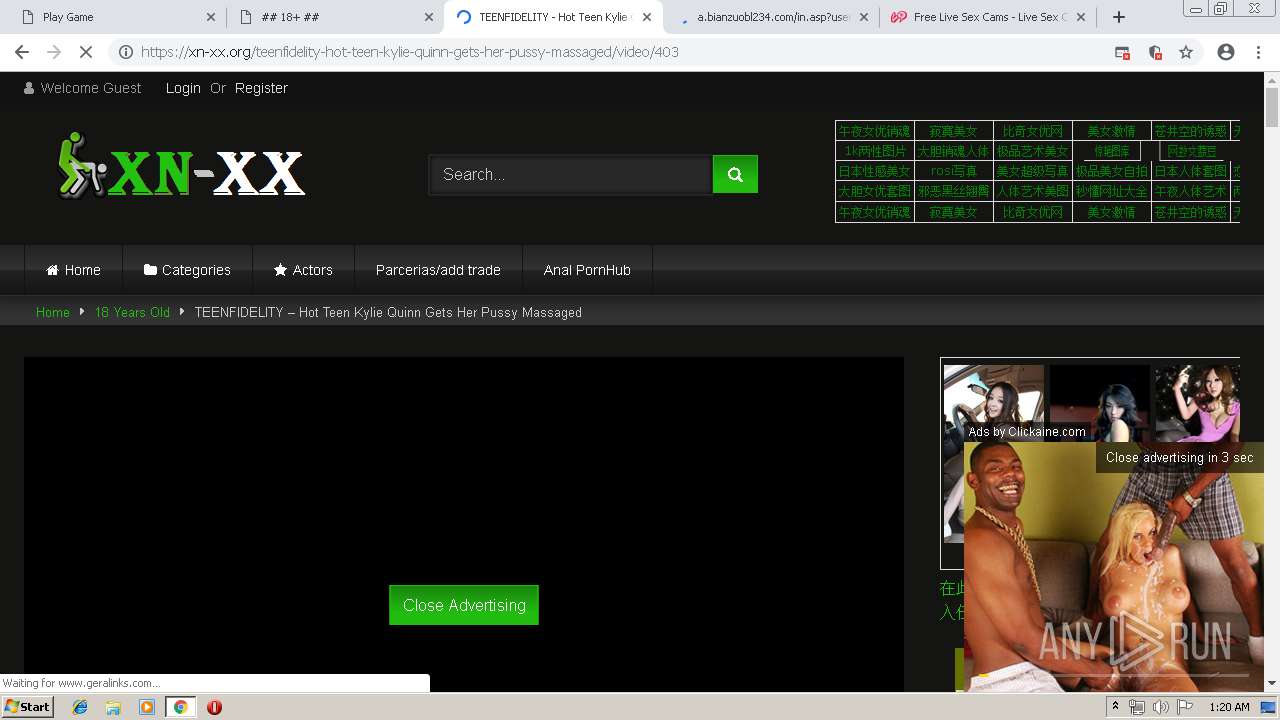
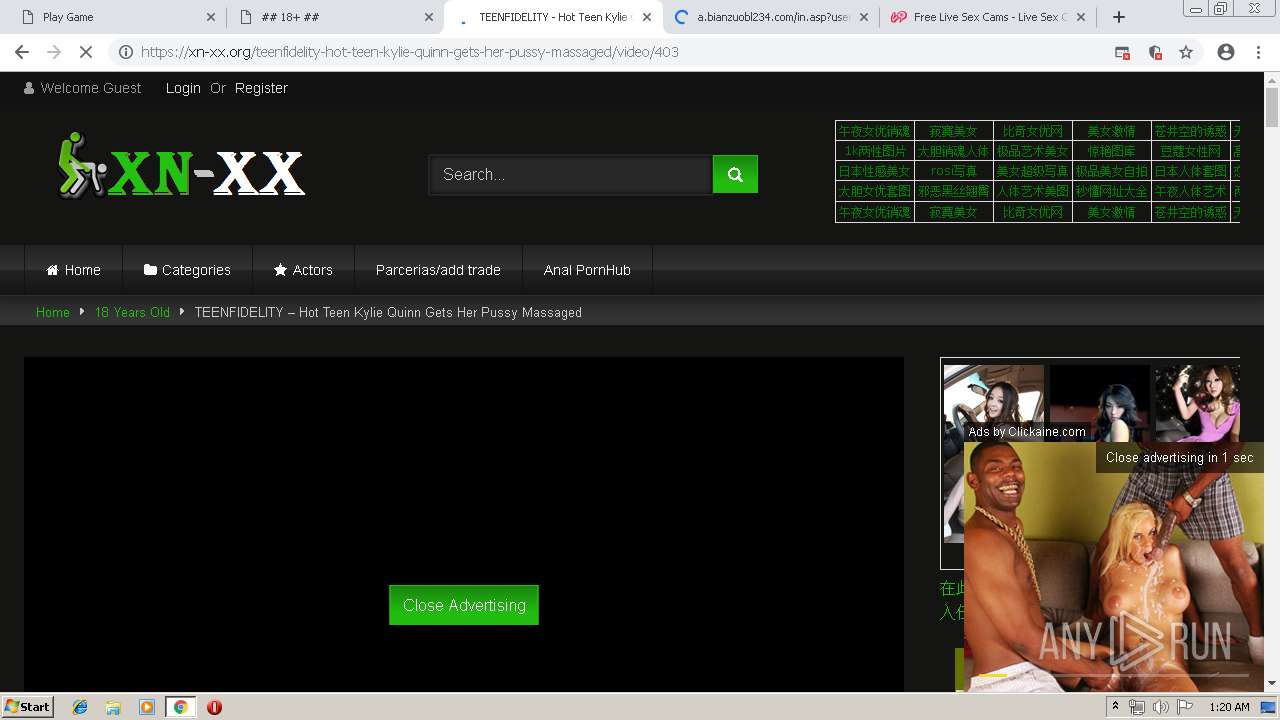
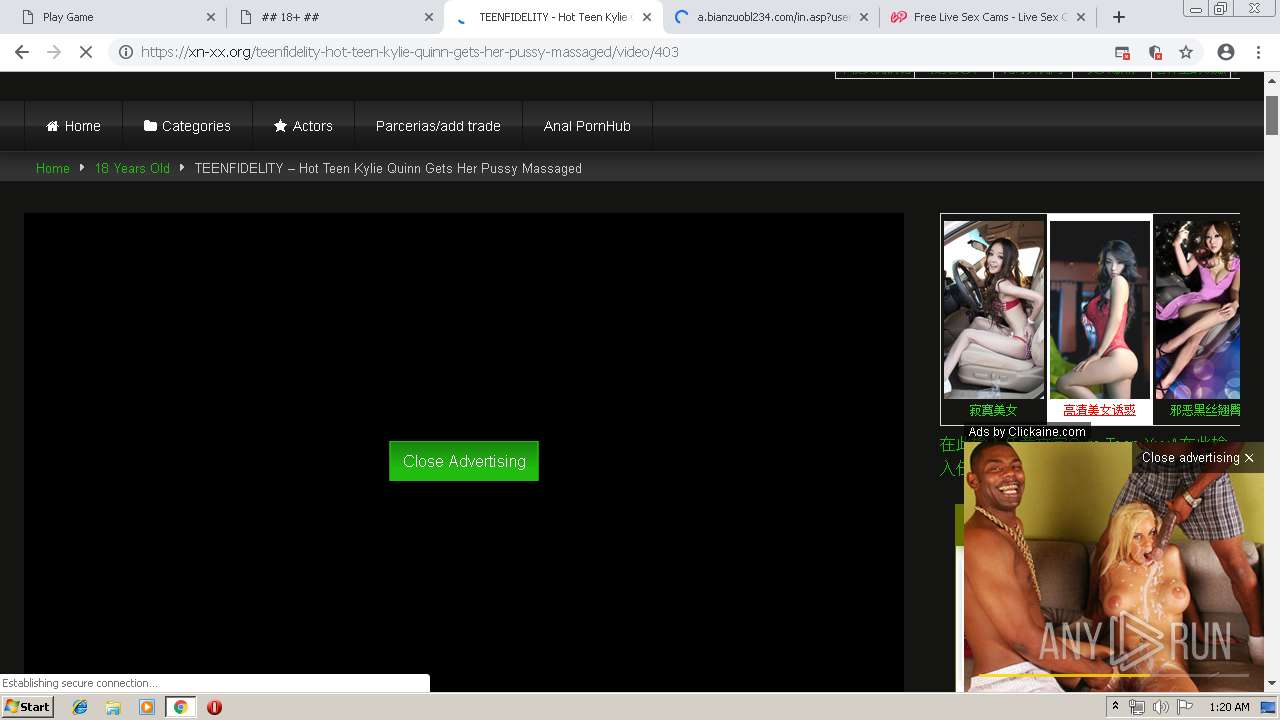
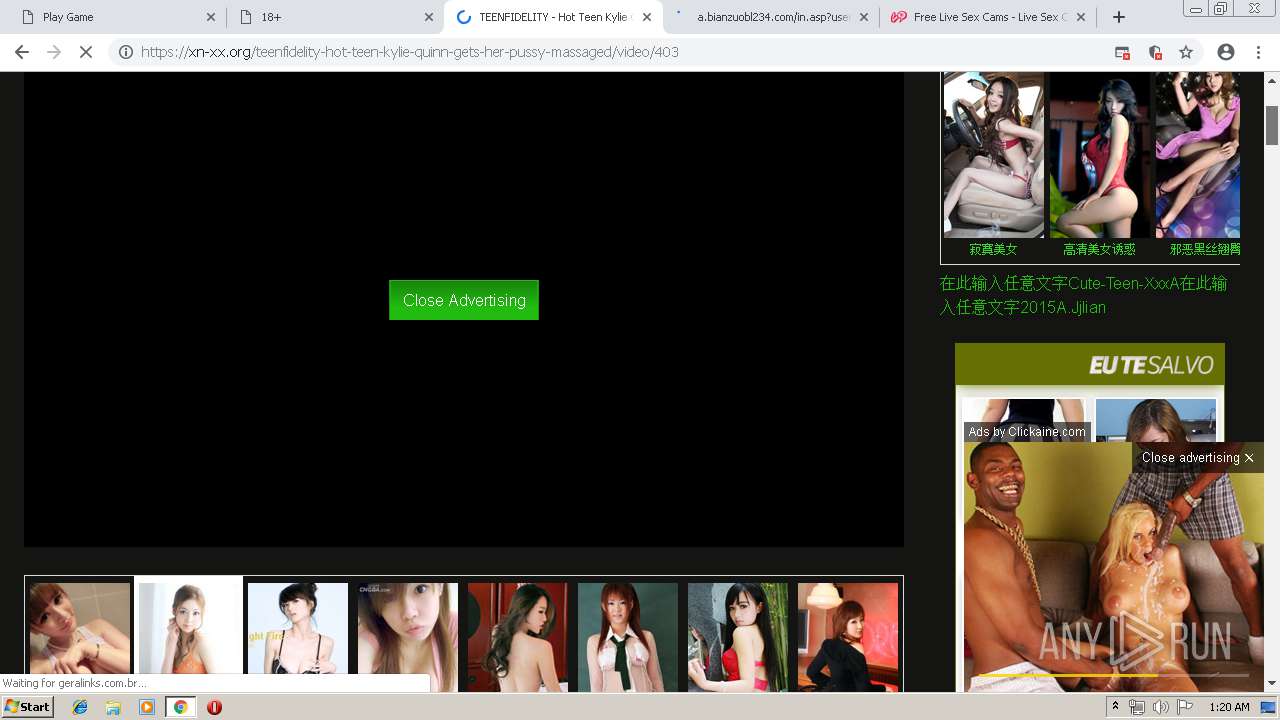
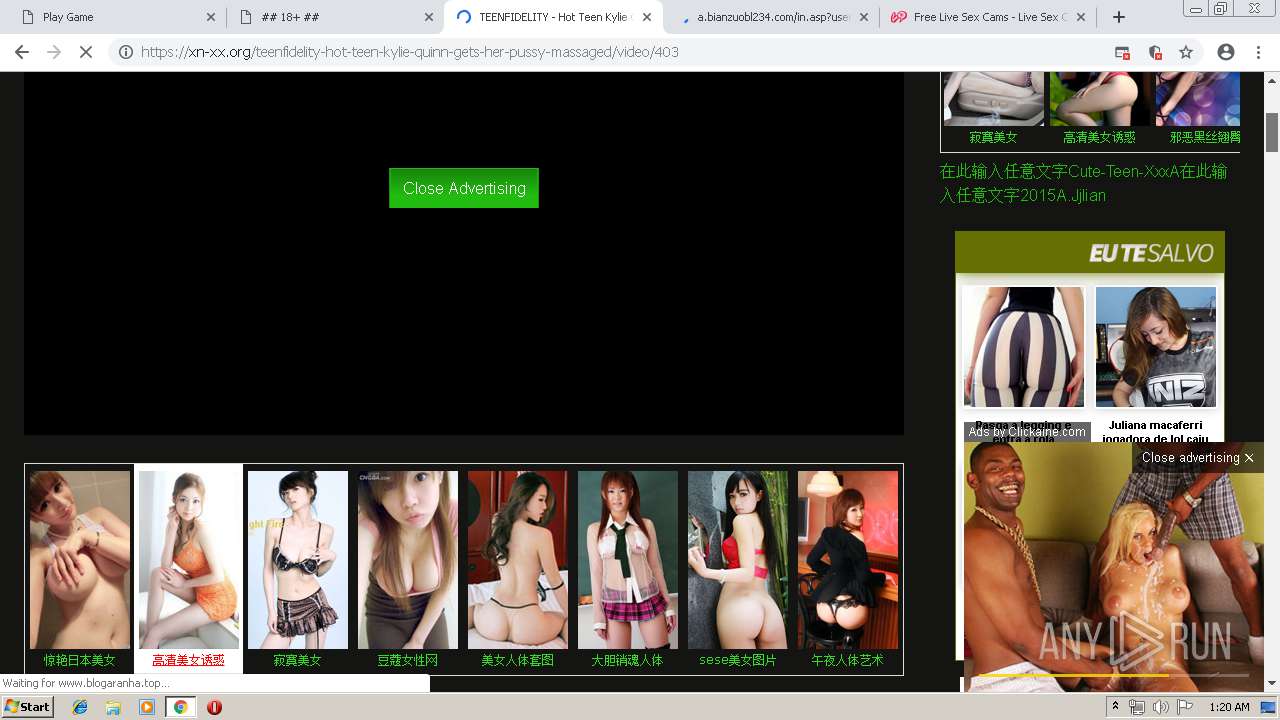
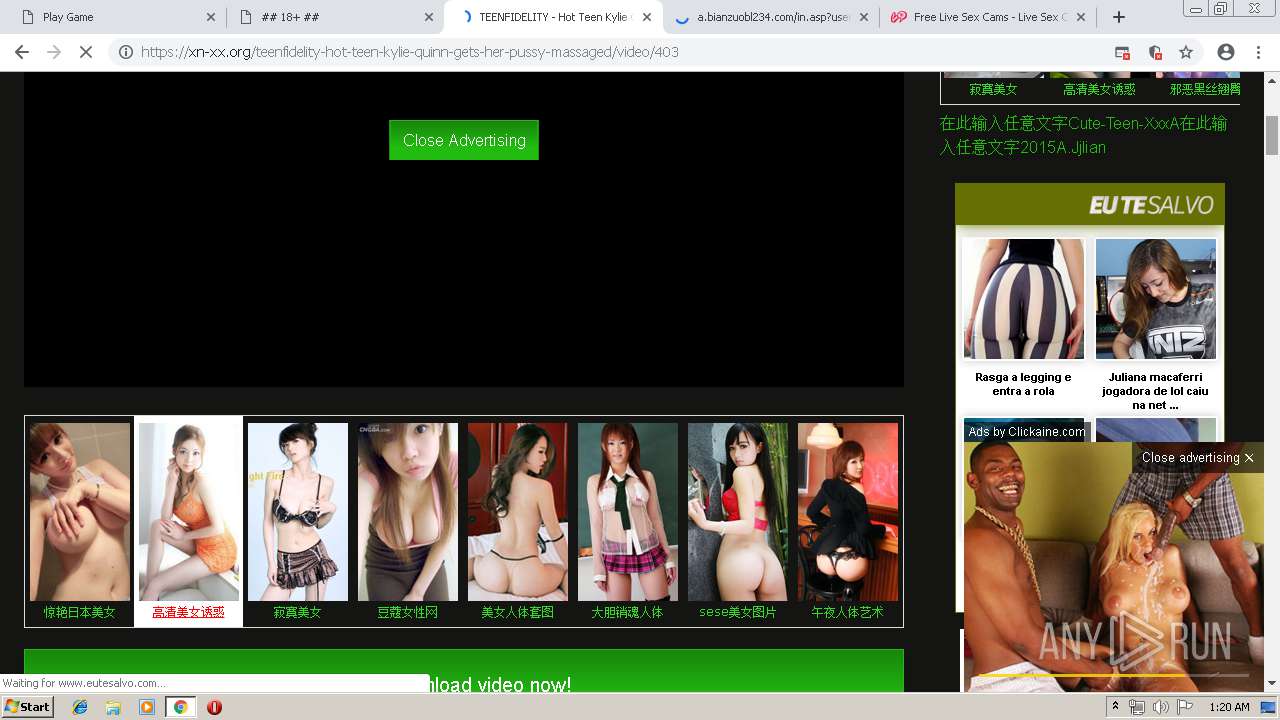
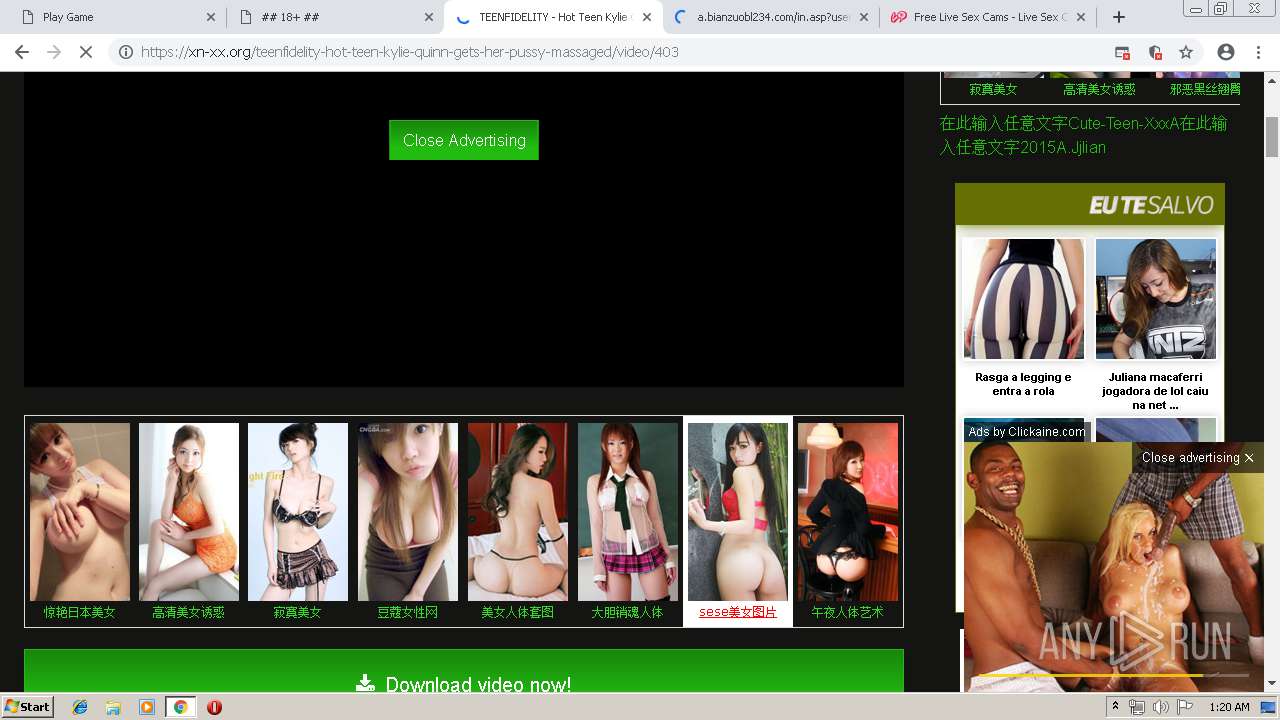
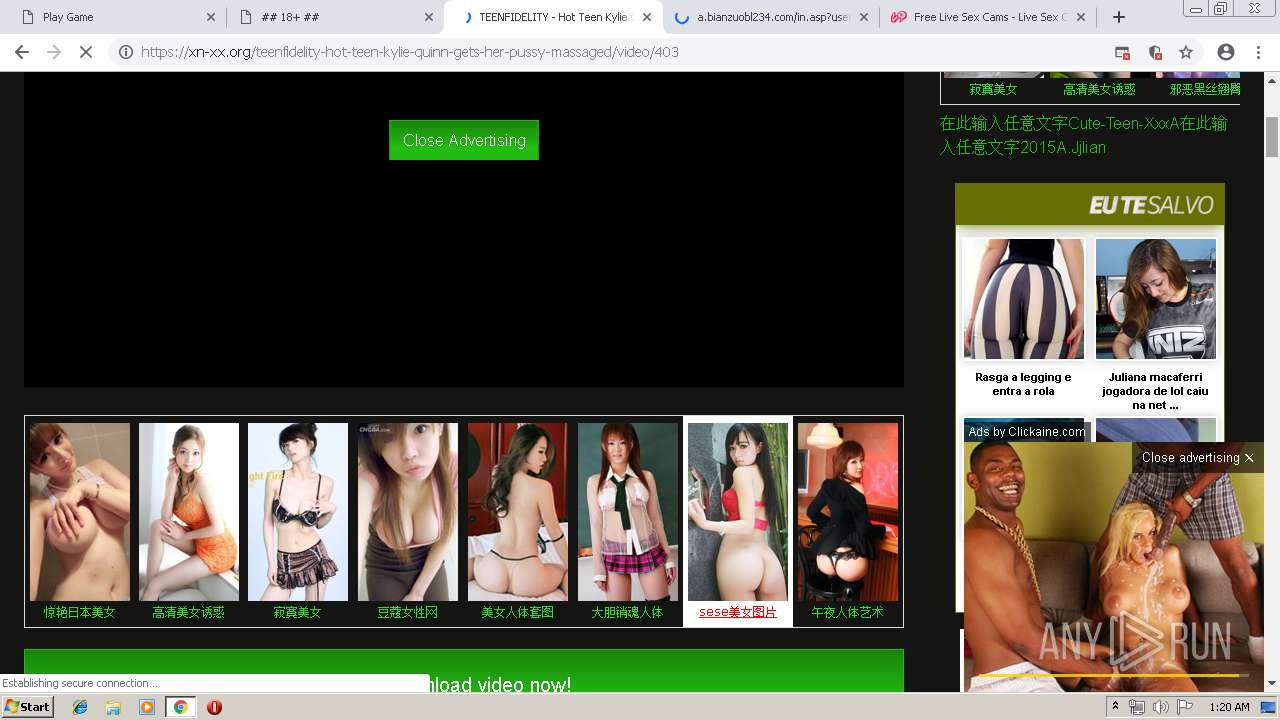
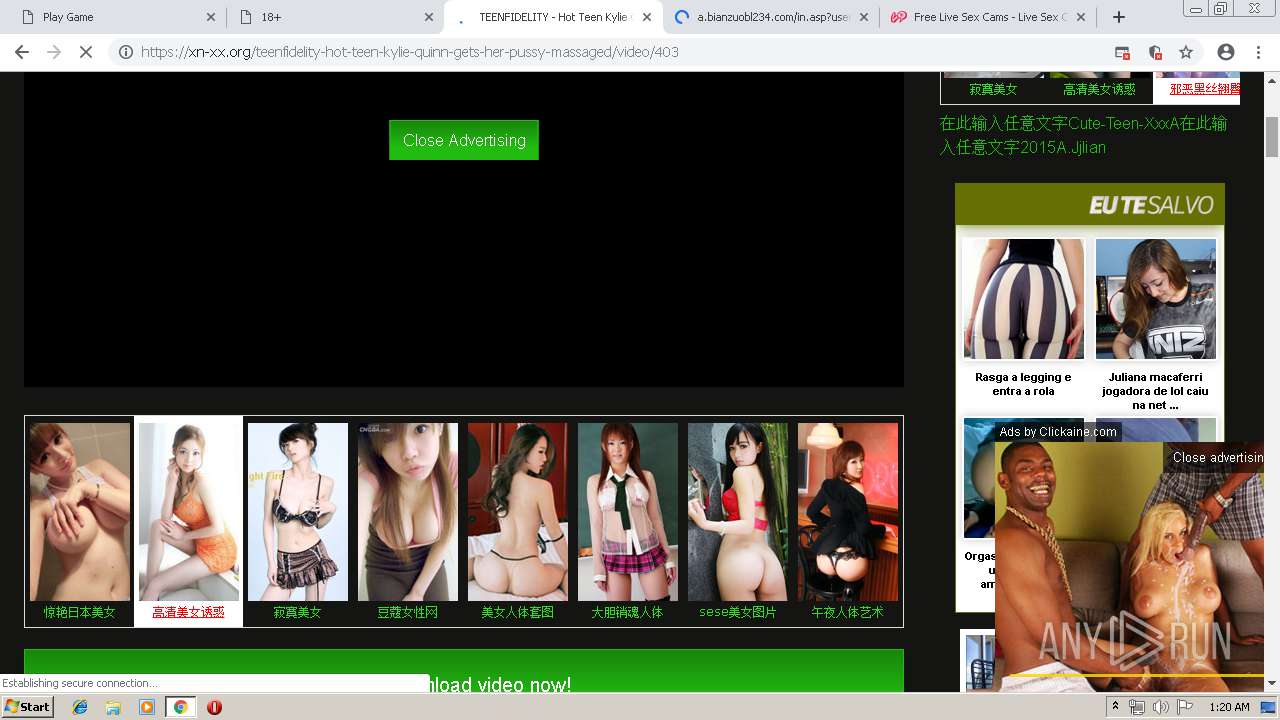
| URL: | https://xn-xx.org |
| Full analysis: | https://app.any.run/tasks/ffa7f763-6e2f-4acd-82d5-d0c7961b557f |
| Verdict: | Suspicious activity |
| Analysis date: | May 12, 2019, 00:18:57 |
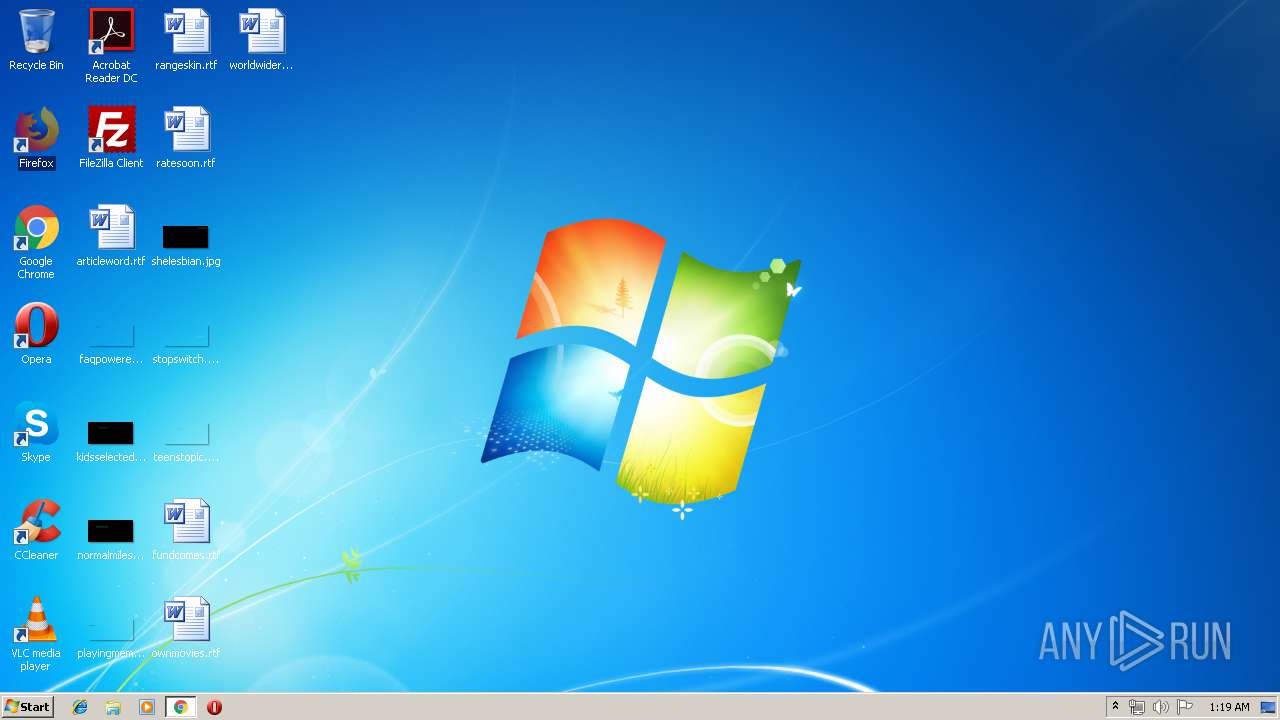
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3BEBE5651178CDF76D45541425E09977 |
| SHA1: | FBDA874F8B78B3C2C10CFA4D6E9390932D87AF4E |
| SHA256: | 75D85965125BF54BDA807EBA231D5925C2C1D49FD48F9B73E927F6D038B2ACEB |
| SSDEEP: | 3:N8n1Cn:2In |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3876)
INFO
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3876)
Application launched itself
- chrome.exe (PID: 3876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
140
Monitored processes
109
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16553902915090535603 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16553902915090535603 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4704 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=104925638847711998 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=104925638847711998 --renderer-client-id=64 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7628 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17389305665724468236 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17389305665724468236 --renderer-client-id=77 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7717323306269842767 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7717323306269842767 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6351279925140945931 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6351279925140945931 --renderer-client-id=78 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6088153910801036321 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6088153910801036321 --renderer-client-id=61 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3729894989326445479 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3729894989326445479 --renderer-client-id=91 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6088 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14242226638389550704 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14242226638389550704 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=12479734380235714017 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12479734380235714017 --renderer-client-id=57 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=8724 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14657496077651504765 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14657496077651504765 --renderer-client-id=86 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=8644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
676
Read events
497
Write events
174
Delete events
5
Modification events
| (PID) Process: | (3876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3876-13202093951401500 |
Value: 259 | |||
| (PID) Process: | (3876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3876) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
422
Text files
314
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\58f1e656-944e-4a42-9db5-b95ba99bf37e.tmp | — | |
MD5:— | SHA256:— | |||
| 3876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
279
DNS requests
181
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3876 | chrome.exe | GET | 301 | 151.139.128.10:80 | http://www.pornexpert.net/pussysaga.php?id=1900230451&type=P | US | — | — | malicious |
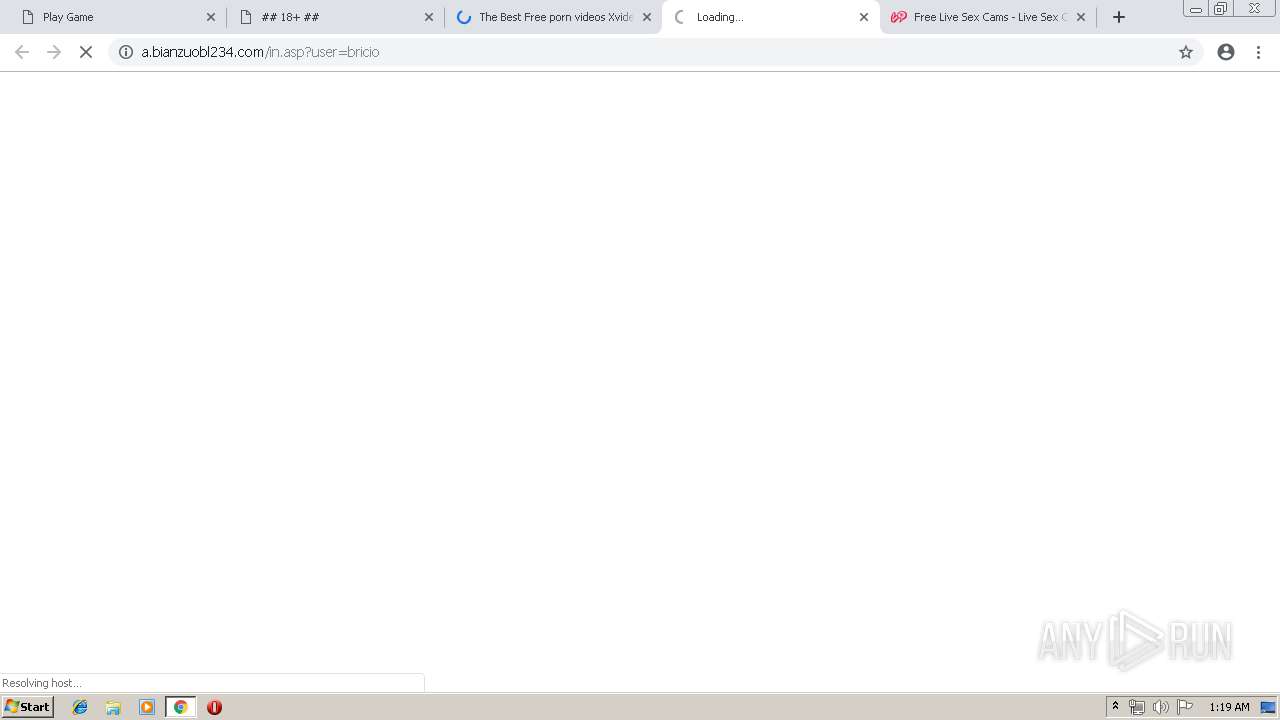
3876 | chrome.exe | GET | — | 216.18.168.180:80 | http://bongacams2.com/track?c=300777&subid=oodNbVHNLZHZLHPLO5SlOmuqqqrldRNXTXLVY6VzqpbXUzOndQ6V0rpXV2V2OldK6V0zpXSuldK6Z0rpXTOq12srrt2nuqn2njslttptqrnosrnsnouqdvtrrZtvPVrvxVLxNpLRtpbNnpTddrNVm6VygRKVGEnLpp7ZVWTyudK6V0rg.w--&subid2=1955560 | US | — | — | suspicious |
3876 | chrome.exe | GET | 302 | 31.192.116.151:80 | http://promo-bc.com/hit.php?c=300777&subid=oodNbVHNLZHZLHPLO5SlOmuqqqrldRNXTXLVY6VzqpbXUzOndQ6V0rpXV2V2OldK6V0zpXSuldK6Z0rpXTOq12srrt2nuqn2njslttptqrnosrnsnouqdvtrrZtvPVrvxVLxNpLRtpbNnpTddrNVm6VygRKVGEnLpp7ZVWTyudK6V0rg.w--&subid2=1955560 | NL | — | — | suspicious |
3876 | chrome.exe | GET | — | 114.80.187.105:80 | http://s95.cnzz.com/stat.php?id=2024340&web_id=2024340 | CN | — | — | whitelisted |
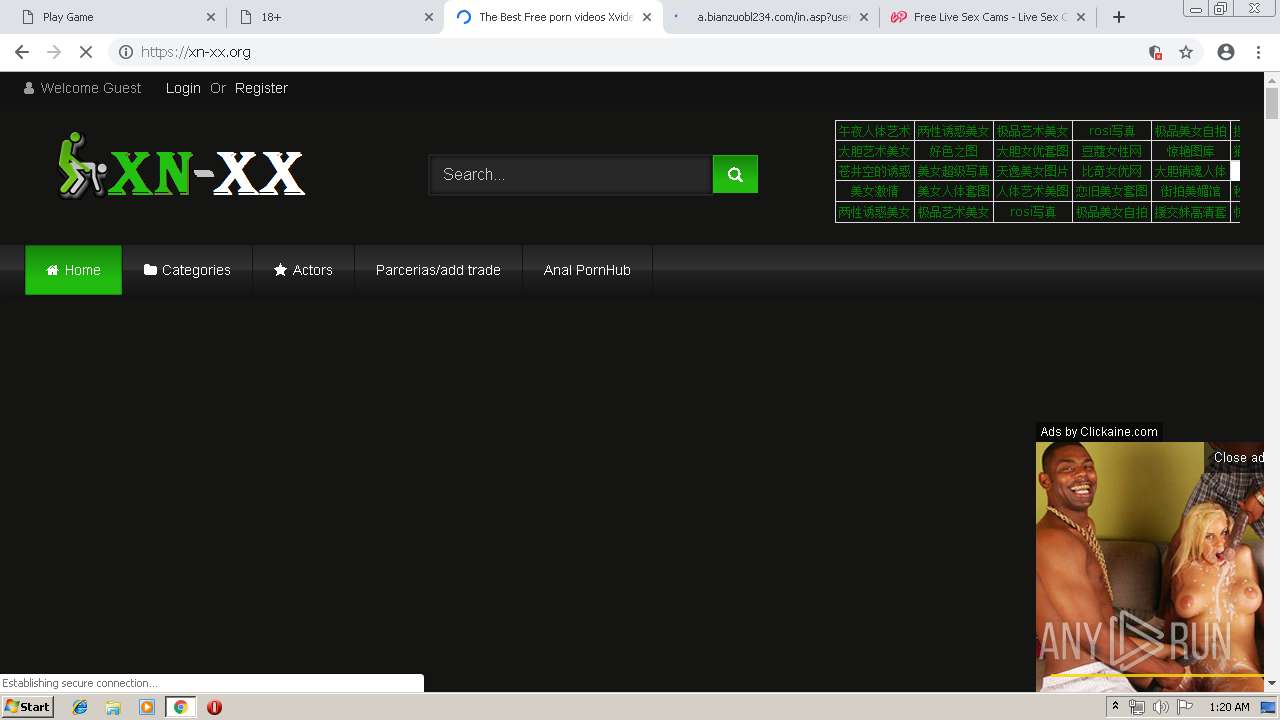
3876 | chrome.exe | GET | 301 | 104.18.32.64:80 | http://xn-xx.org/wp-content/uploads/2019/01/logo_dark.png | US | html | 266 b | malicious |
3876 | chrome.exe | GET | 301 | 104.18.32.64:80 | http://xn-xx.org/wp-content/themes/retrotube/assets/img/banners/header-mobile.jpg | US | html | 290 b | malicious |
3876 | chrome.exe | GET | 200 | 151.139.128.10:80 | http://redir.jads.co/pu_uu.php?cb=1557620361&uu=CC44D500-4147-707C-C26E-CEC6AF1988A2 | US | html | 1.72 Kb | suspicious |
3876 | chrome.exe | GET | 302 | 151.139.128.10:80 | http://redir.jads.co/pu_uu.php?cb=1557620361&uu=CC44D500-4147-707C-C26E-CEC6AF1988A2 | US | compressed | 1.72 Kb | suspicious |
3876 | chrome.exe | GET | 302 | 172.217.20.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 505 b | whitelisted |
3876 | chrome.exe | GET | 200 | 104.37.178.1:80 | http://landcdn.mysexjourney.com/content/086-1088721388/play.png | US | image | 5.79 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3876 | chrome.exe | 104.18.32.64:443 | xn-xx.org | Cloudflare Inc | US | shared |
3876 | chrome.exe | 104.18.32.64:80 | xn-xx.org | Cloudflare Inc | US | shared |
3876 | chrome.exe | 88.208.59.71:443 | arda0hylt58g4wg0.pro | DataWeb Global Group B.V. | NL | suspicious |
— | — | 88.208.59.71:443 | arda0hylt58g4wg0.pro | DataWeb Global Group B.V. | NL | suspicious |
3876 | chrome.exe | 104.18.49.140:443 | manialinks.com | Cloudflare Inc | US | shared |
3876 | chrome.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
3876 | chrome.exe | 216.58.211.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3876 | chrome.exe | 172.217.168.196:443 | www.google.com | Google Inc. | US | whitelisted |
3876 | chrome.exe | 172.217.20.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3876 | chrome.exe | 104.27.165.38:443 | www.eutesalvo.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
xn-xx.org |
| malicious |
accounts.google.com |
| shared |
c0.wp.com |
| whitelisted |
juicypop.xn-xx.org |
| unknown |
arda0hylt58g4wg0.pro |
| unknown |
c4ns.xn-xx.org |
| unknown |
ca.clcknads.pro |
| malicious |
manialinks.com |
| suspicious |
js.juicyads.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3876 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
1068 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3876 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |