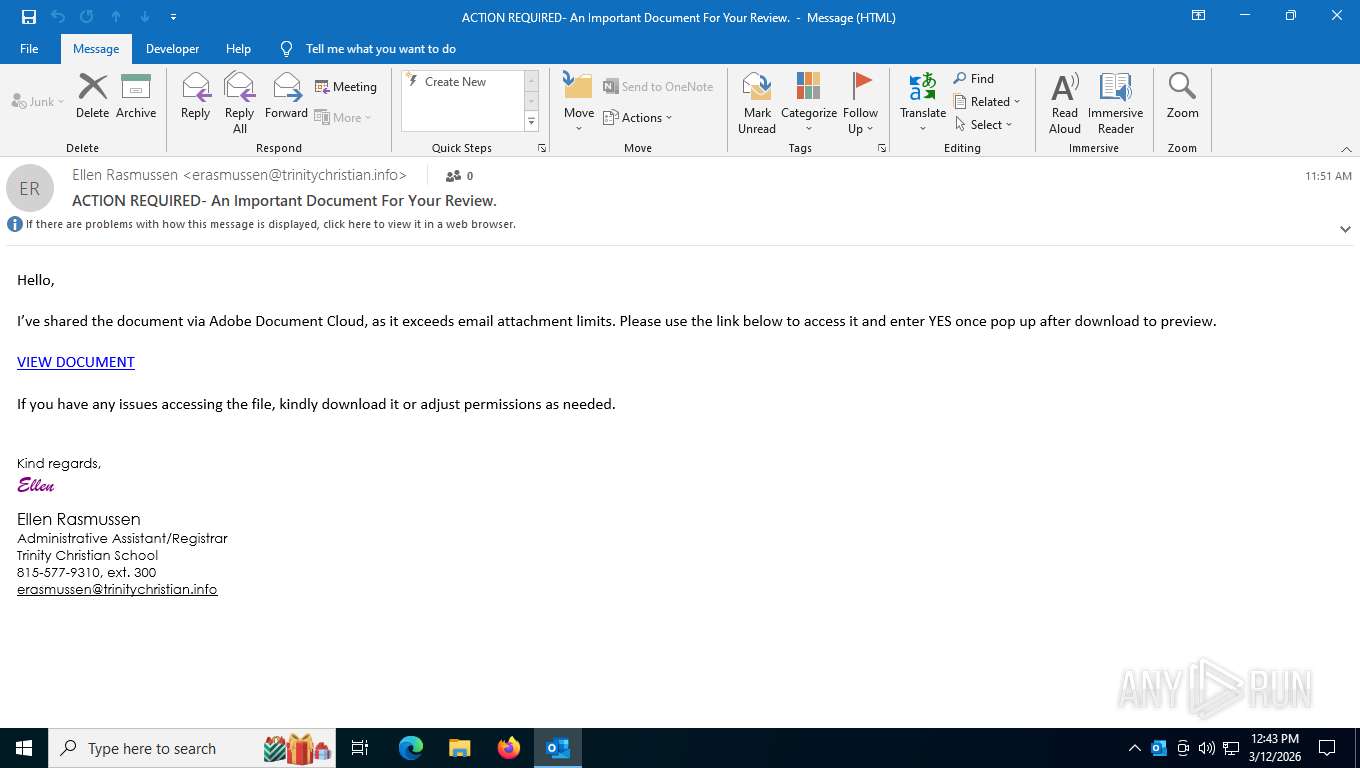
| File name: | ACTION REQUIRED- An Important Document For Your Review..eml |
| Full analysis: | https://app.any.run/tasks/8f80d503-95d7-4306-80f5-08343920ebe7 |
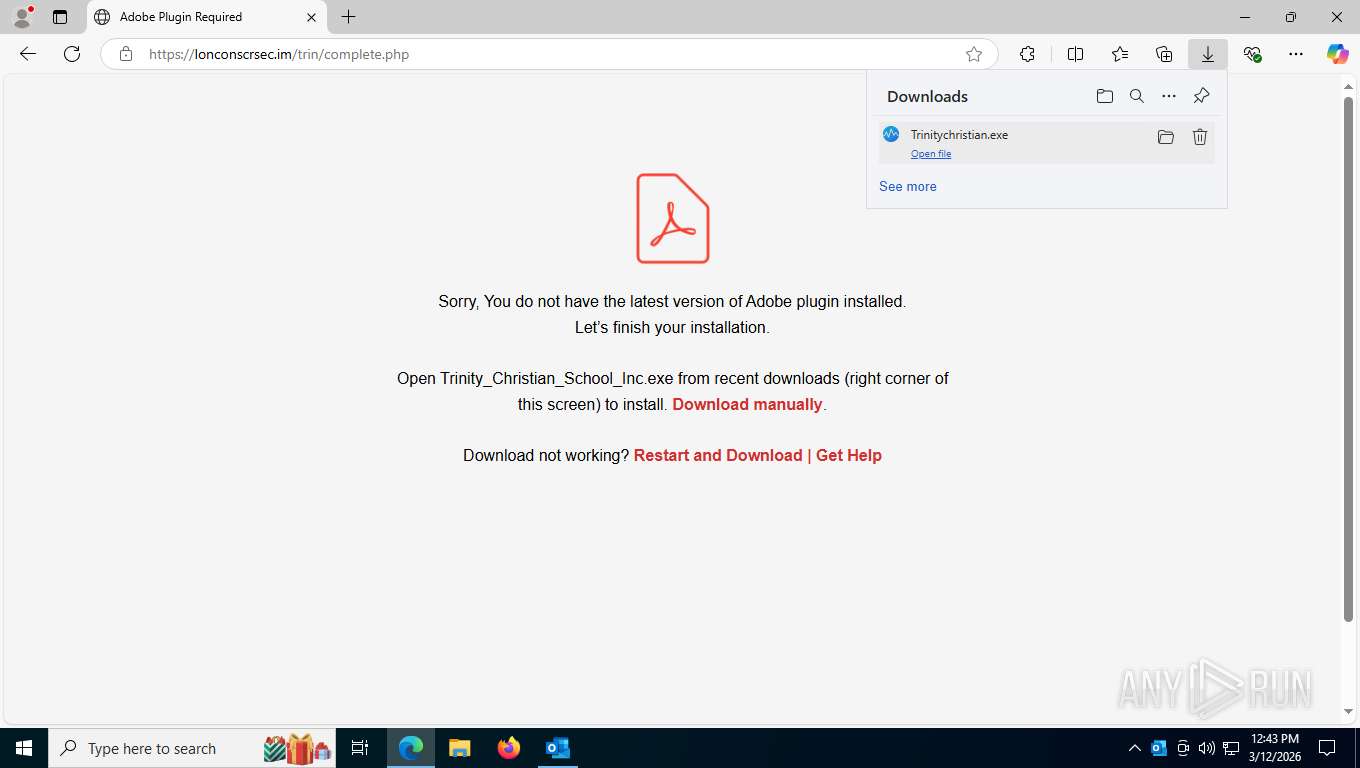
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2026, 16:43:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | SMTP mail, ASCII text, with very long lines (793), with CRLF line terminators |
| MD5: | 81781937D4BAEAA14546F06DFB6BBAF7 |
| SHA1: | F723E072423780F8C61541A3A1944AFC9515508E |
| SHA256: | 75C82313FF955479CD80FAE61146440897D328F293B15E3B8AE1D5ADB9730DF7 |
| SSDEEP: | 384:An104/v4hX4pmvRFFc4oogx4KeUt09uX06ej+Cg1zzCWQ:e104/v4hX4pERFFcVom4KZhX063rS |
MALICIOUS
Changes the autorun value in the registry
- Trinitychristian.exe (PID: 4336)
- Trinitychristian.exe (PID: 3344)
- Trinitychristian.exe (PID: 7296)
- Trinitychristian.exe (PID: 1424)
- Trinitychristian.exe (PID: 6628)
Registers / Runs the DLL via REGSVR32.EXE
- CagService.exe (PID: 1820)
DATTO has been detected
- CagService.exe (PID: 1820)
SUSPICIOUS
The process creates files with name similar to system file names
- Trinitychristian.exe (PID: 4336)
- Trinitychristian.exe (PID: 3344)
- Trinitychristian.exe (PID: 7296)
- Trinitychristian.exe (PID: 1424)
- Trinitychristian.exe (PID: 6628)
- Trinitychristian.exe (PID: 2680)
- CagService.exe (PID: 1820)
- Trinitychristian.exe (PID: 7052)
Malware-specific behavior (creating "System.dll" in Temp)
- Trinitychristian.exe (PID: 4336)
- Trinitychristian.exe (PID: 3344)
- Trinitychristian.exe (PID: 6628)
- Trinitychristian.exe (PID: 7296)
- Trinitychristian.exe (PID: 1424)
- Trinitychristian.exe (PID: 2680)
- Trinitychristian.exe (PID: 7052)
Executable content was dropped or overwritten
- Trinitychristian.exe (PID: 7296)
- Trinitychristian.exe (PID: 1424)
- Trinitychristian.exe (PID: 6628)
- Trinitychristian.exe (PID: 3344)
- Trinitychristian.exe (PID: 4336)
- CagService.exe (PID: 1820)
- Trinitychristian.exe (PID: 7052)
- Trinitychristian.exe (PID: 2680)
Executes as Windows Service
- CagService.exe (PID: 1820)
Searches for installed software
- CagService.exe (PID: 1820)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 6828)
Creates or modifies Windows services
- CagService.exe (PID: 1820)
INFO
Checks supported languages
- identity_helper.exe (PID: 8728)
- Trinitychristian.exe (PID: 4336)
- Trinitychristian.exe (PID: 3344)
- Trinitychristian.exe (PID: 1424)
- Trinitychristian.exe (PID: 6628)
- Trinitychristian.exe (PID: 7296)
- CagService.exe (PID: 1820)
- Gui.exe (PID: 6808)
- Trinitychristian.exe (PID: 2680)
- Trinitychristian.exe (PID: 7052)
- Gui.exe (PID: 6976)
- Gui.exe (PID: 7932)
- Gui.exe (PID: 5304)
- Gui.exe (PID: 8604)
- AEMAgent.exe (PID: 3180)
Reads Environment values
- identity_helper.exe (PID: 8728)
- CagService.exe (PID: 1820)
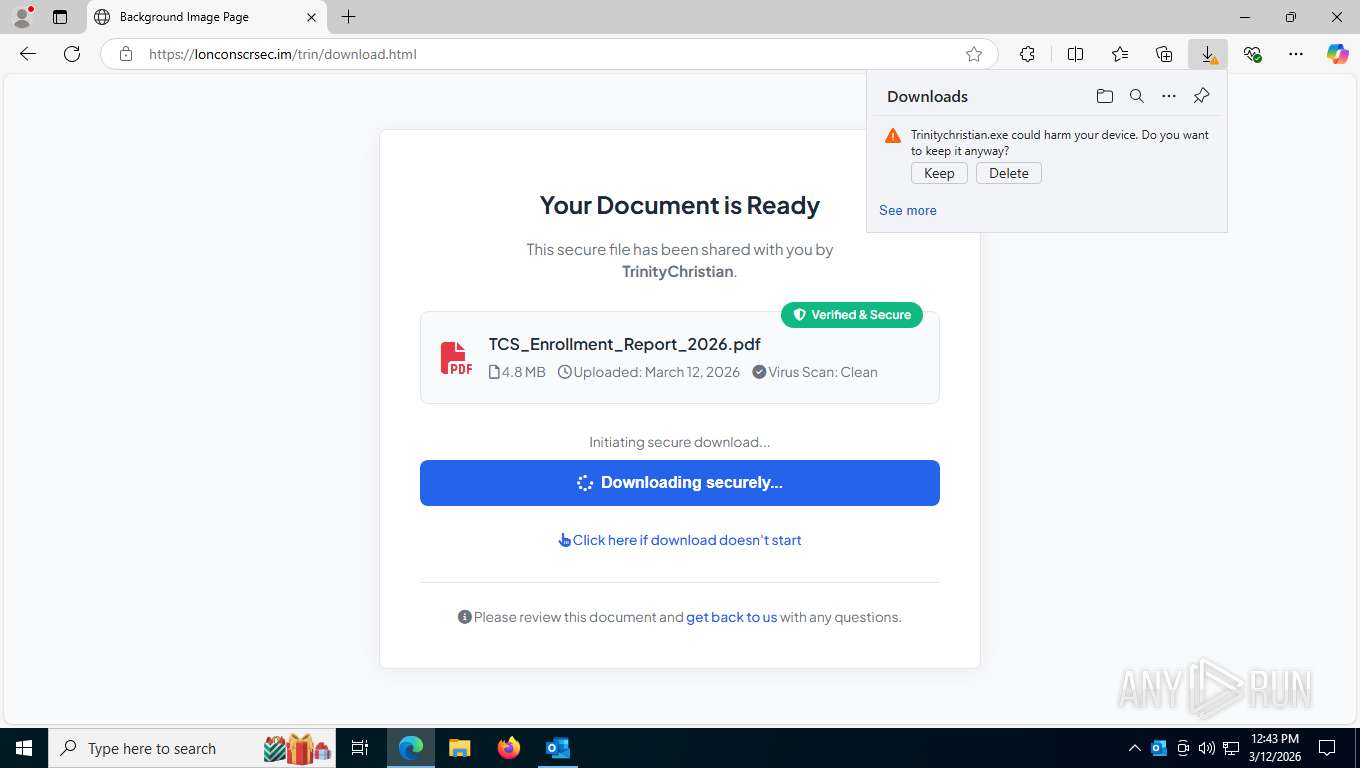
Launching a file from the Downloads directory
- msedge.exe (PID: 5464)
Executable content was dropped or overwritten
- msedge.exe (PID: 5392)
- msedge.exe (PID: 5464)
Reads the computer name
- identity_helper.exe (PID: 8728)
- Trinitychristian.exe (PID: 4336)
- CagService.exe (PID: 1820)
- Gui.exe (PID: 6808)
- Trinitychristian.exe (PID: 3344)
- Gui.exe (PID: 7932)
- Trinitychristian.exe (PID: 7296)
- Gui.exe (PID: 6976)
- Trinitychristian.exe (PID: 1424)
- Trinitychristian.exe (PID: 6628)
- Gui.exe (PID: 5304)
- Gui.exe (PID: 8604)
Application launched itself
- msedge.exe (PID: 5464)
Create files in a temporary directory
- Trinitychristian.exe (PID: 4336)
- Trinitychristian.exe (PID: 1424)
- Trinitychristian.exe (PID: 3344)
- Trinitychristian.exe (PID: 7296)
- Trinitychristian.exe (PID: 6628)
- Trinitychristian.exe (PID: 2680)
- Trinitychristian.exe (PID: 7052)
The sample compiled with english language support
- Trinitychristian.exe (PID: 4336)
- CagService.exe (PID: 1820)
Creates files in the program directory
- Trinitychristian.exe (PID: 4336)
- CagService.exe (PID: 1820)
- Gui.exe (PID: 6808)
- AEMAgent.exe (PID: 3180)
Creates a software uninstall entry
- Trinitychristian.exe (PID: 4336)
- CagService.exe (PID: 1820)
- Trinitychristian.exe (PID: 3344)
- Trinitychristian.exe (PID: 7296)
- Trinitychristian.exe (PID: 1424)
- Trinitychristian.exe (PID: 6628)
Launching a file from a Registry key
- Trinitychristian.exe (PID: 4336)
- Trinitychristian.exe (PID: 7296)
- Trinitychristian.exe (PID: 1424)
- Trinitychristian.exe (PID: 6628)
- Trinitychristian.exe (PID: 3344)
DATTO has been detected
- Trinitychristian.exe (PID: 4336)
- CagService.exe (PID: 1820)
- CagService.exe (PID: 1820)
- Gui.exe (PID: 6808)
- Trinitychristian.exe (PID: 3344)
- Gui.exe (PID: 7932)
- Trinitychristian.exe (PID: 7296)
- Gui.exe (PID: 6976)
- Trinitychristian.exe (PID: 1424)
- Trinitychristian.exe (PID: 6628)
- Gui.exe (PID: 5304)
- Gui.exe (PID: 8604)
- AEMAgent.exe (PID: 3180)
Reads the machine GUID from the registry
- CagService.exe (PID: 1820)
- Gui.exe (PID: 6808)
- Gui.exe (PID: 7932)
- Gui.exe (PID: 6976)
- Gui.exe (PID: 5304)
- Gui.exe (PID: 8604)
Reads security settings of Internet Explorer
- CagService.exe (PID: 1820)
- Gui.exe (PID: 6808)
- Gui.exe (PID: 7932)
- Gui.exe (PID: 6976)
- Gui.exe (PID: 5304)
- Gui.exe (PID: 8604)
Creates files or folders in the user directory
- Gui.exe (PID: 6808)
Disables trace logs
- CagService.exe (PID: 1820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 7) (100) |
|---|
Total processes
219
Monitored processes
55
Malicious processes
3
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7340,i,6115098338972537151,5039595791813333313,262144 --variations-seed-version --mojo-platform-channel-handle=7312 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
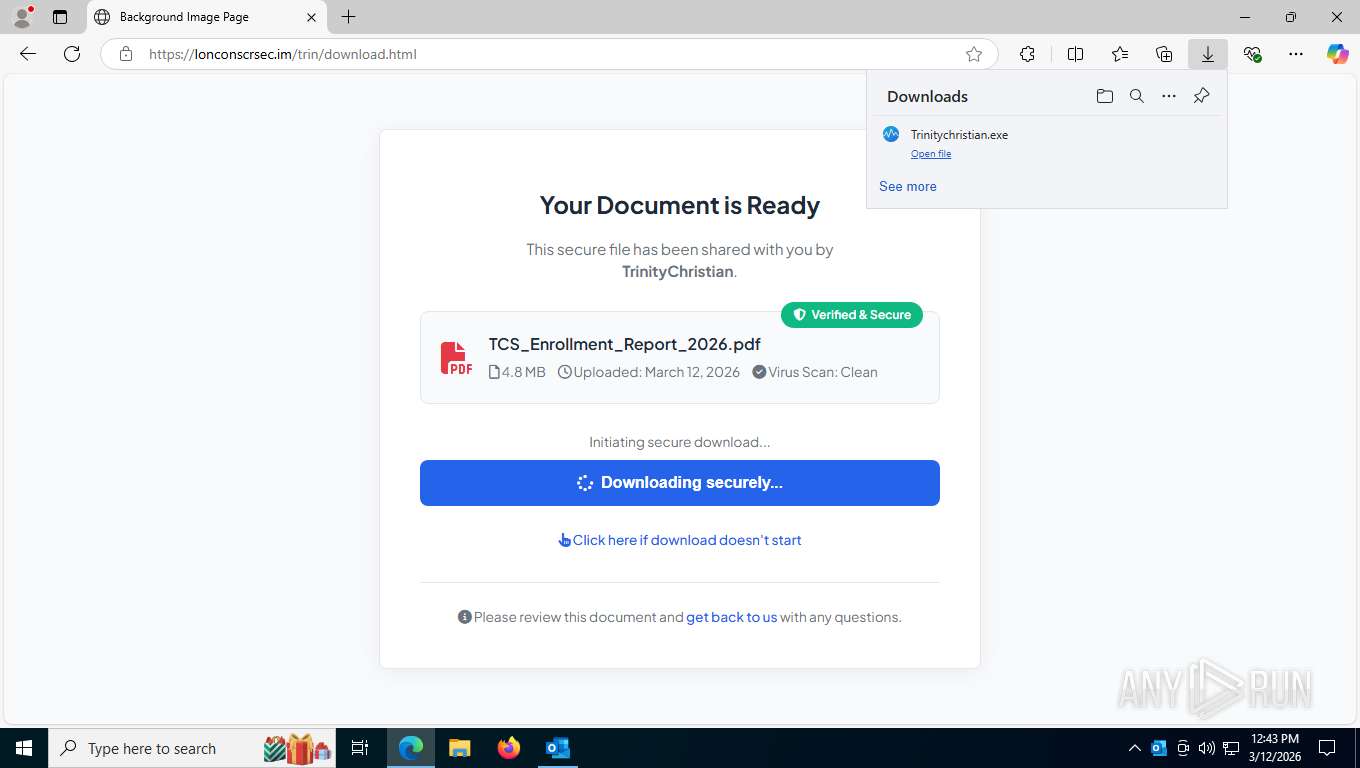
| 1424 | "C:\Users\admin\Downloads\Trinitychristian.exe" | C:\Users\admin\Downloads\Trinitychristian.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1656 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7344,i,6115098338972537151,5039595791813333313,262144 --variations-seed-version --mojo-platform-channel-handle=7304 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1820 | "C:\Program Files (x86)\CentraStage\CagService.exe" | C:\Program Files (x86)\CentraStage\CagService.exe | services.exe | ||||||||||||
User: SYSTEM Company: CentraStage Integrity Level: SYSTEM Description: CentraStage Service Version: 4.4.10748.10748 Modules
| |||||||||||||||
| 2252 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7448,i,6115098338972537151,5039595791813333313,262144 --variations-seed-version --mojo-platform-channel-handle=1496 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2368 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3620,i,6115098338972537151,5039595791813333313,262144 --variations-seed-version --mojo-platform-channel-handle=3876 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2456 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files (x86)\CentraStage\scvncctrl.dll" | C:\Windows\System32\regsvr32.exe | — | CagService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2548 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5280,i,6115098338972537151,5039595791813333313,262144 --variations-seed-version --mojo-platform-channel-handle=7356 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2680 | "C:\Users\admin\Downloads\Trinitychristian.exe" | C:\Users\admin\Downloads\Trinitychristian.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
28 802
Read events
28 361
Write events
391
Delete events
50
Modification events
| (PID) Process: | (8556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 01941A000000001000B24E9A3E06000000000000000600000000000000 | |||
| (PID) Process: | (8556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (8556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | CantBootResolution |
Value: BootSuccess | |||
| (PID) Process: | (8556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | ProfileBeingOpened |
Value: Outlook | |||
| (PID) Process: | (8556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | SessionId |
Value: C3D8E96E-C1AF-4750-8D52-F4E28119C131 | |||
| (PID) Process: | (8556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | BootDiagnosticsLogFile |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK_16_0_16026_20146-20240718T1116060318-1644.etl | |||
| (PID) Process: | (8556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | ProfileBeingOpened |
Value: | |||
| (PID) Process: | (8556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsData |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8556) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | write | Name: | OutlookBootFlag |
Value: 1 | |||
Executable files
326
Suspicious files
60
Text files
317
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8556 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 5464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e6436.TMP | — | |
MD5:— | SHA256:— | |||
| 5464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e6455.TMP | — | |
MD5:— | SHA256:— | |||
| 5464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e6455.TMP | — | |
MD5:— | SHA256:— | |||
| 5464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e6465.TMP | — | |
MD5:— | SHA256:— | |||
| 5464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e6455.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
105
TCP/UDP connections
79
DNS requests
83
Threats
43
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5392 | msedge.exe | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=uH5YXWLNsE3vtTuT9p%2FjImnAZTZoNm2gxc6f2sRNCfvJJDmzSW3e47XggxB3L2kL%2FSsClVJ5ASFGQuV5w6boECdJ%2FywXFoGoawcNaTNWIimT6DIhKUNOWdyLkgJt65lDA0k%3D | US | — | — | unknown |
8556 | OUTLOOK.EXE | GET | 200 | 52.123.129.14:443 | https://ecs.office.com/config/v2/Office/outlook/16.0.16026.20146/Production/CC?&Clientid=%7bD61AB268-C26A-439D-BB15-2A0DEDFCA6A3%7d&Application=outlook&Platform=win32&Version=16.0.16026.20146&MsoVersion=16.0.16026.20002&SDX=fa000000002.2.0.1907.31003&SDX=fa000000005.1.0.1909.30011&SDX=fa000000006.1.0.1909.13002&SDX=fa000000008.1.0.1908.16006&SDX=fa000000009.1.0.1908.6002&SDX=fa000000016.1.0.1810.13001&SDX=fa000000029.1.0.1906.25001&SDX=fa000000033.1.0.1908.24001&SDX=wa104381125.1.0.1810.9001&ProcessName=outlook.exe&Audience=Production&Build=ship&Architecture=x64&Language=en-US&SubscriptionLicense=false&PerpetualLicense=2019&LicenseCategory=6&LicenseSKU=Professional2019Retail&OsVersion=10.0&OsBuild=19045&Channel=CC&InstallType=C2R&SessionId=%7bF1F99930-9EDC-409E-8AEE-A05C91D19F31%7d&LabMachine=false | US | text | 345 Kb | unknown |
5392 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:qOT2AtlD3z9CnF_ZORtYB8m3L7jAc7fxVapJx-_djjM&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
5392 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 295 b | whitelisted |
5392 | msedge.exe | GET | 200 | 52.123.243.194:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.38 Kb | whitelisted |
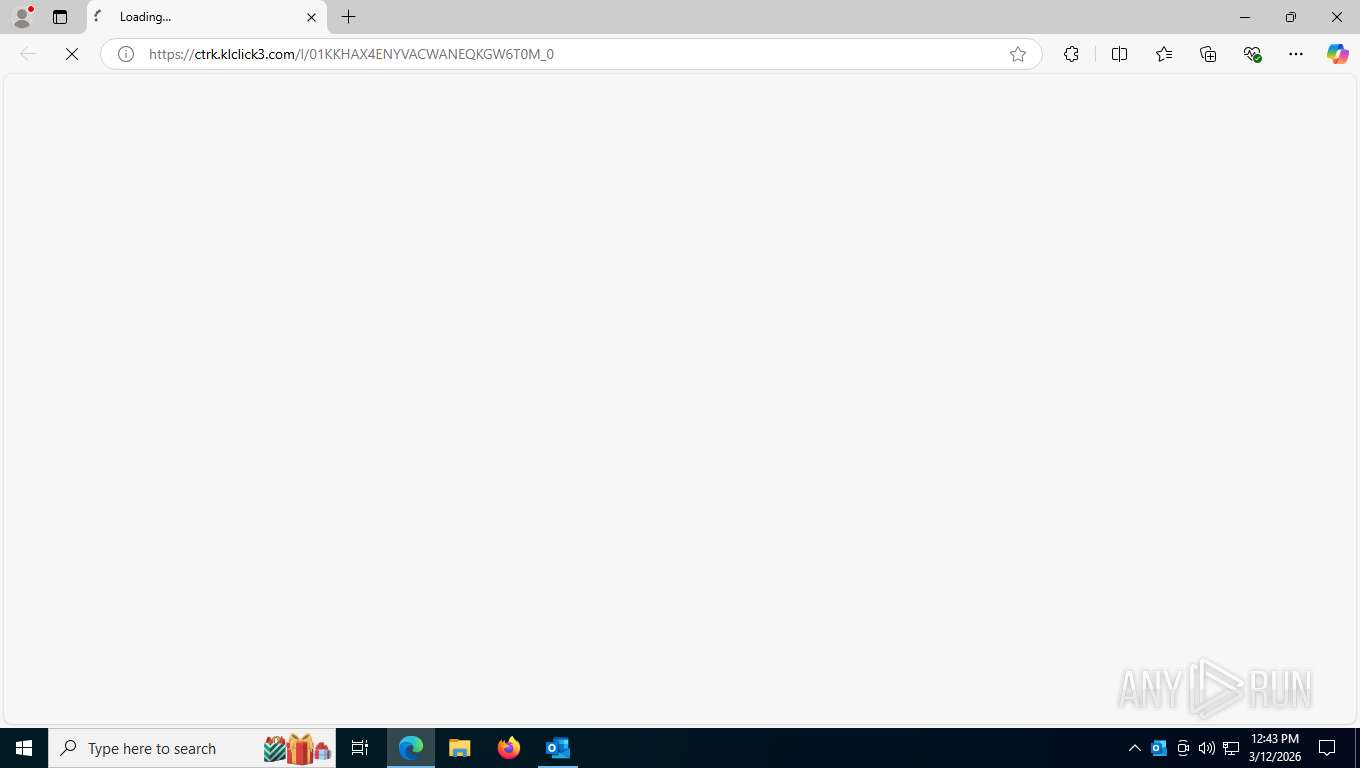
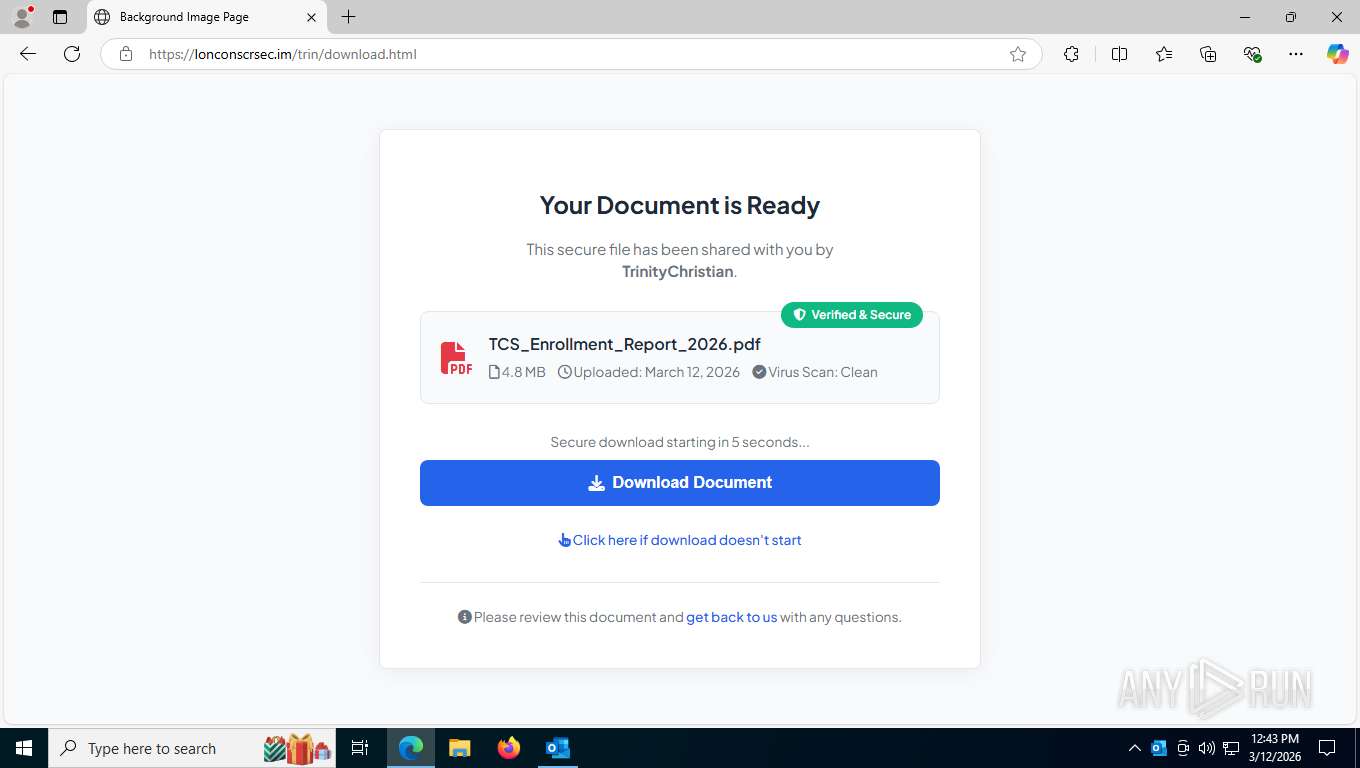
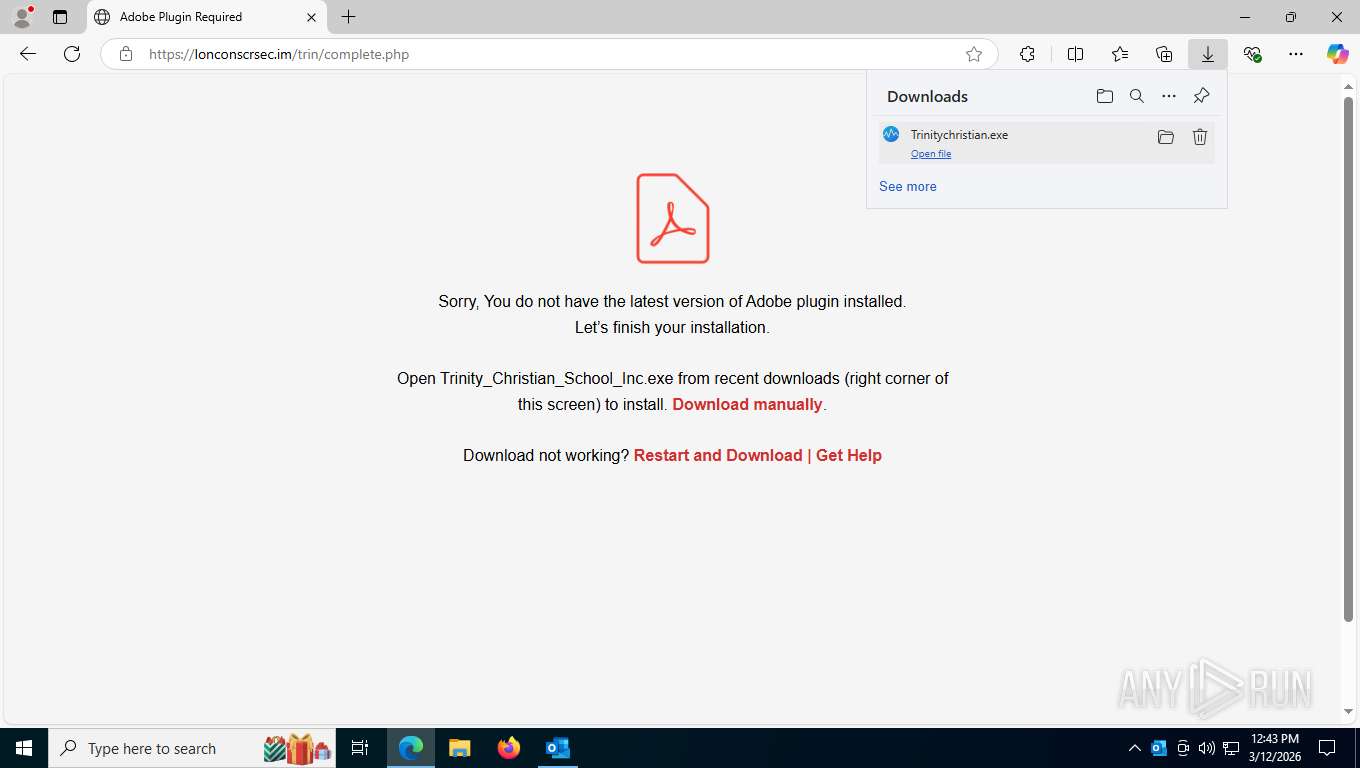
5392 | msedge.exe | GET | 302 | 104.17.94.1:443 | https://ctrk.klclick3.com/l/01KKHAX4ENYVACWANEQKGW6T0M_0 | US | html | 106 b | unknown |
5392 | msedge.exe | GET | 200 | 13.107.246.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
4936 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
4936 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
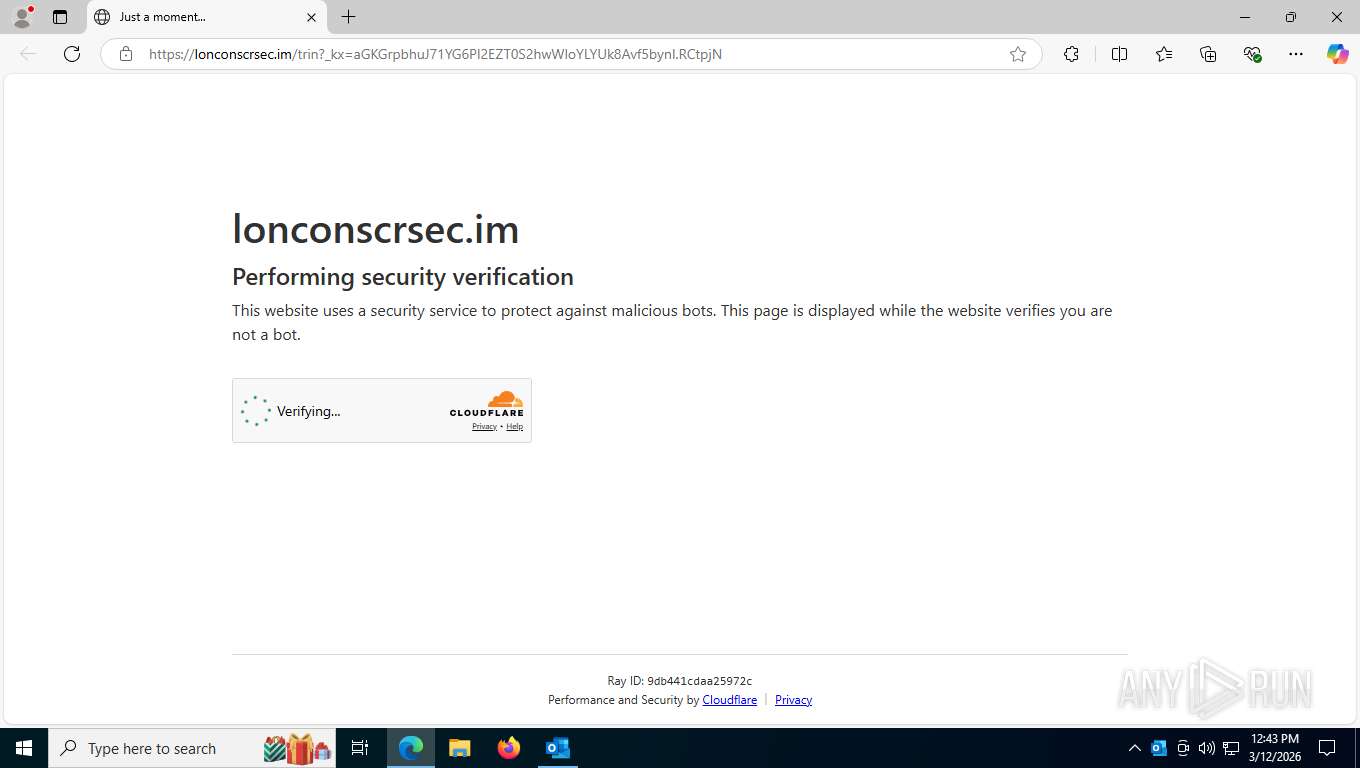
5392 | msedge.exe | GET | 403 | 172.67.131.97:443 | https://lonconscrsec.im/trin?_kx=aGKGrpbhuJ71YG6PI2EZT0S2hwWloYLYUk8Avf5bynI.RCtpjN | US | html | 9.43 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4936 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
9088 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8556 | OUTLOOK.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8556 | OUTLOOK.EXE | 2.16.164.75:443 | omex.cdn.office.net | AKAMAI-ASN1 | NL | whitelisted |
8556 | OUTLOOK.EXE | 52.111.236.4:443 | messaging.lifecycle.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5392 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5392 | msedge.exe | 52.123.243.194:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ctrk.klclick3.com |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5392 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5392 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5392 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Observed DNS Query to Frequently Abused Online Tool Domain (klclick3 .com) |
5392 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Frequently Abused Online Tool Domain (klclick3 .com in TLS SNI) |
5392 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Observed DNS Query to Frequently Abused Online Tool Domain (klclick3 .com) |
5392 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Frequently Abused Online Tool Domain (klclick3 .com in TLS SNI) |
5392 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
5392 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
5392 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
5392 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Challenge-Platform Page Request to cdn-cgi |