| URL: | http://tiobiter.gq/ |
| Full analysis: | https://app.any.run/tasks/fd5d08a0-f518-437c-bea7-903441c58d8d |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 04:54:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C2670B36D8AE9ECCD5DAFADA32CFCD54 |
| SHA1: | 3A5228BE50BF56BB6773D6025AC429CF54F7840B |
| SHA256: | 75B774DFA62B79D9C9A110DA3084CB4EF1FF418F6D91CCB99949E68D5DC59AAC |
| SSDEEP: | 3:N1KKMc9LXK:CKpm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3468)
INFO
Application launched itself
- chrome.exe (PID: 3468)
Reads the hosts file
- chrome.exe (PID: 3468)
- chrome.exe (PID: 2988)
Reads settings of System Certificates
- chrome.exe (PID: 2988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,4756398656555230842,14661670697041074113,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17262561892125268918 --mojo-platform-channel-handle=3812 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,4756398656555230842,14661670697041074113,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12853182744522272502 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2388 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3472 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fdea9d0,0x6fdea9e0,0x6fdea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,4756398656555230842,14661670697041074113,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4035619526260346703 --mojo-platform-channel-handle=3060 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,4756398656555230842,14661670697041074113,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2513178830353506066 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,4756398656555230842,14661670697041074113,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8928750433229029032 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,4756398656555230842,14661670697041074113,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17762293038053905223 --mojo-platform-channel-handle=3836 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,4756398656555230842,14661670697041074113,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11328104735956328048 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,4756398656555230842,14661670697041074113,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7222293325316343298 --mojo-platform-channel-handle=964 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
630
Read events
539
Write events
86
Delete events
5
Modification events
| (PID) Process: | (3468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3468-13212651272604500 |
Value: 259 | |||
| (PID) Process: | (3468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3468) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
47
Text files
158
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b6d8d19b-a9fe-4794-b80a-a0dcaa955b35.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169ea6.TMP | text | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169eb5.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
43
DNS requests
30
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
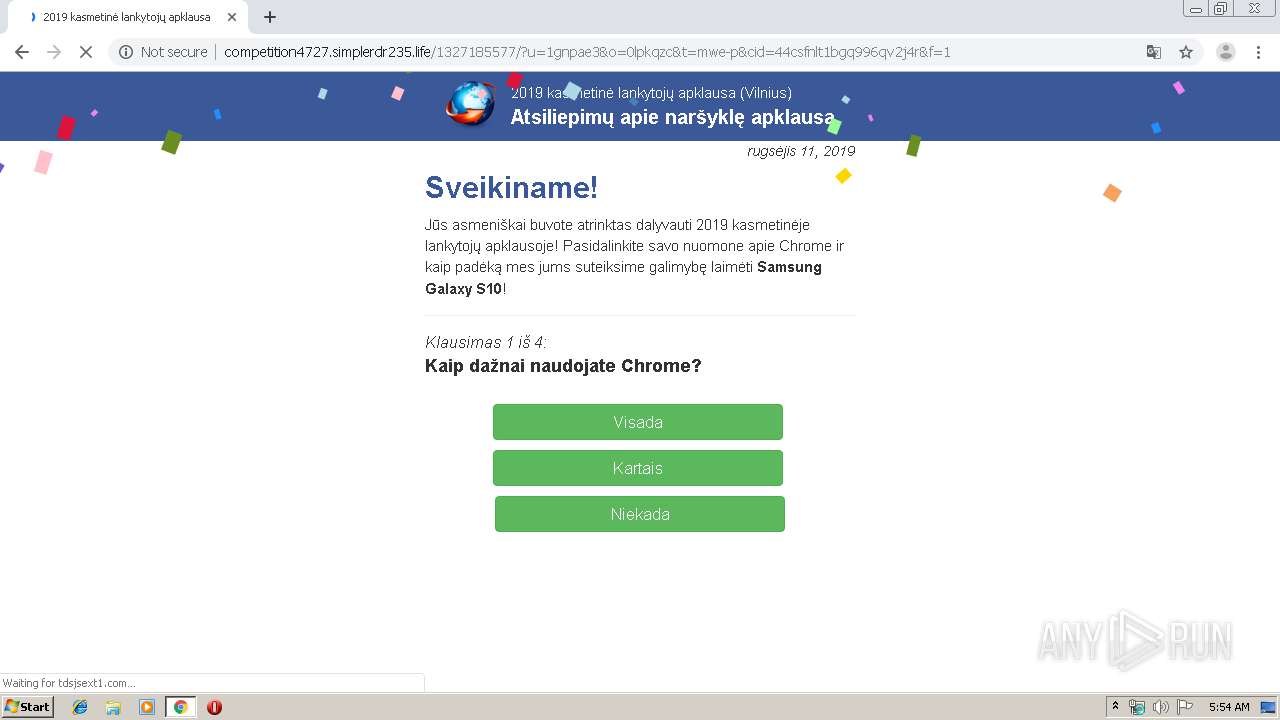
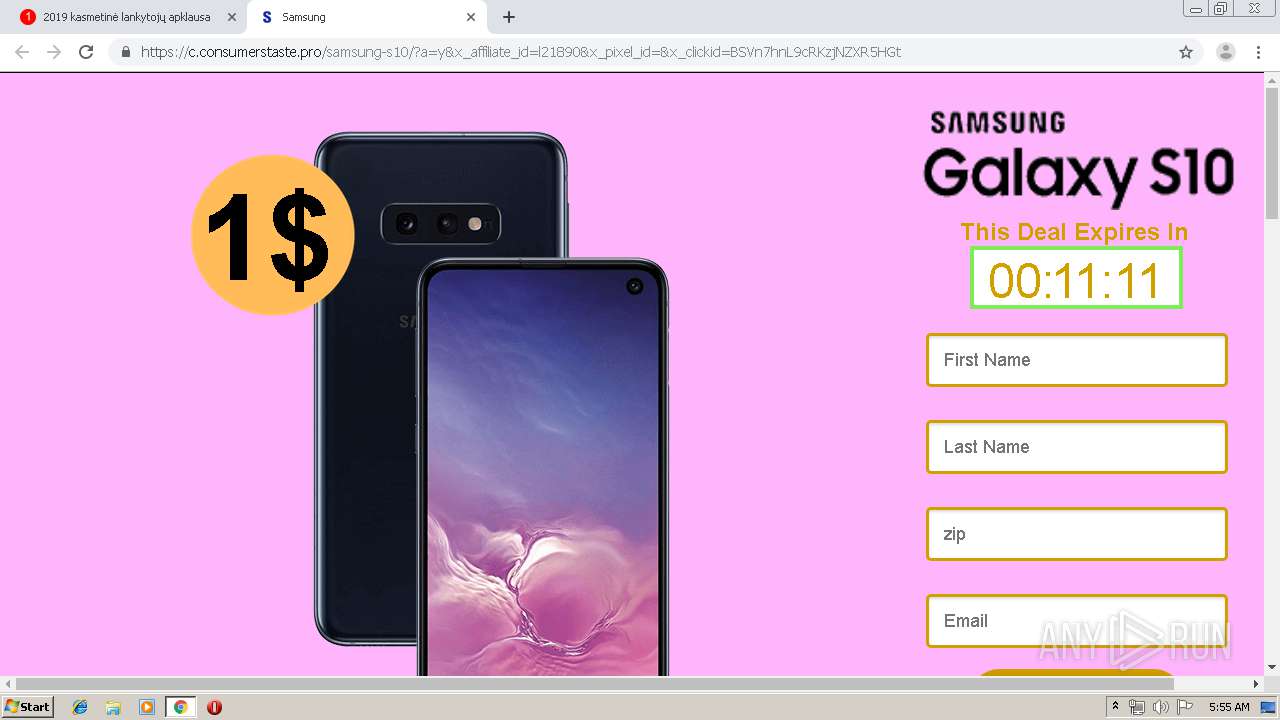
2988 | chrome.exe | GET | 301 | 104.28.31.130:80 | http://tiobiter.gq/ | US | — | — | suspicious |
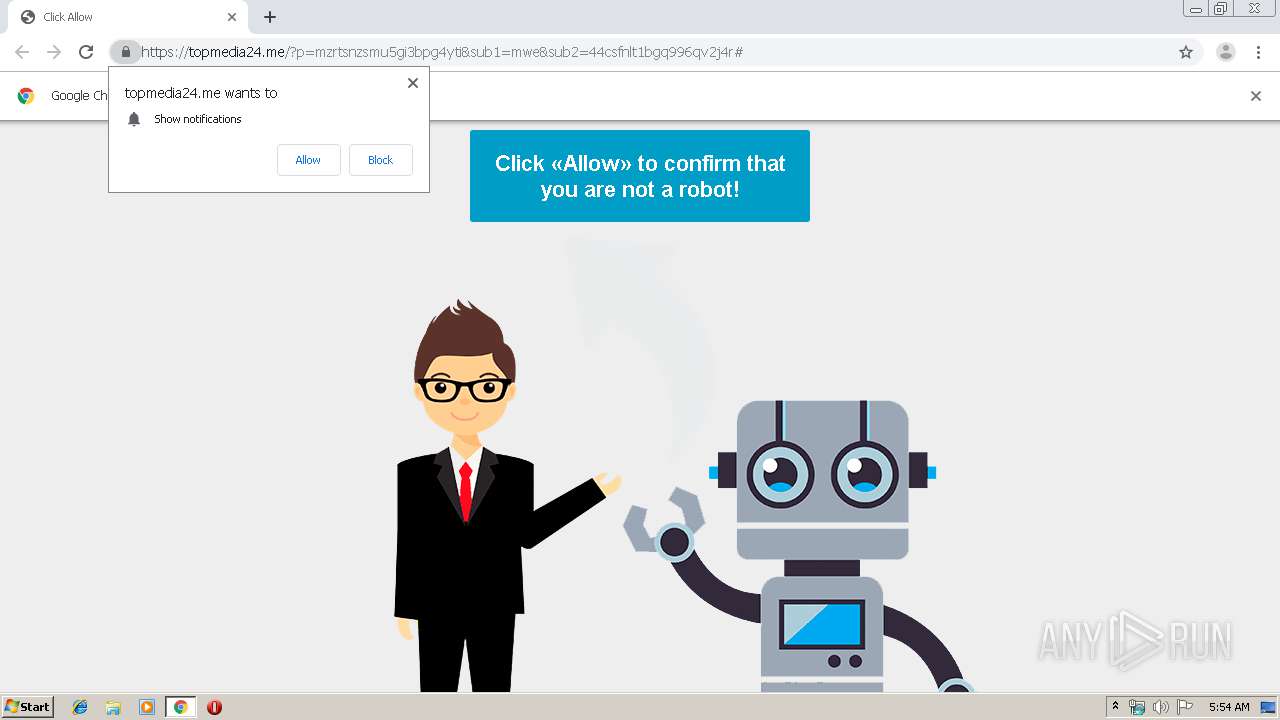
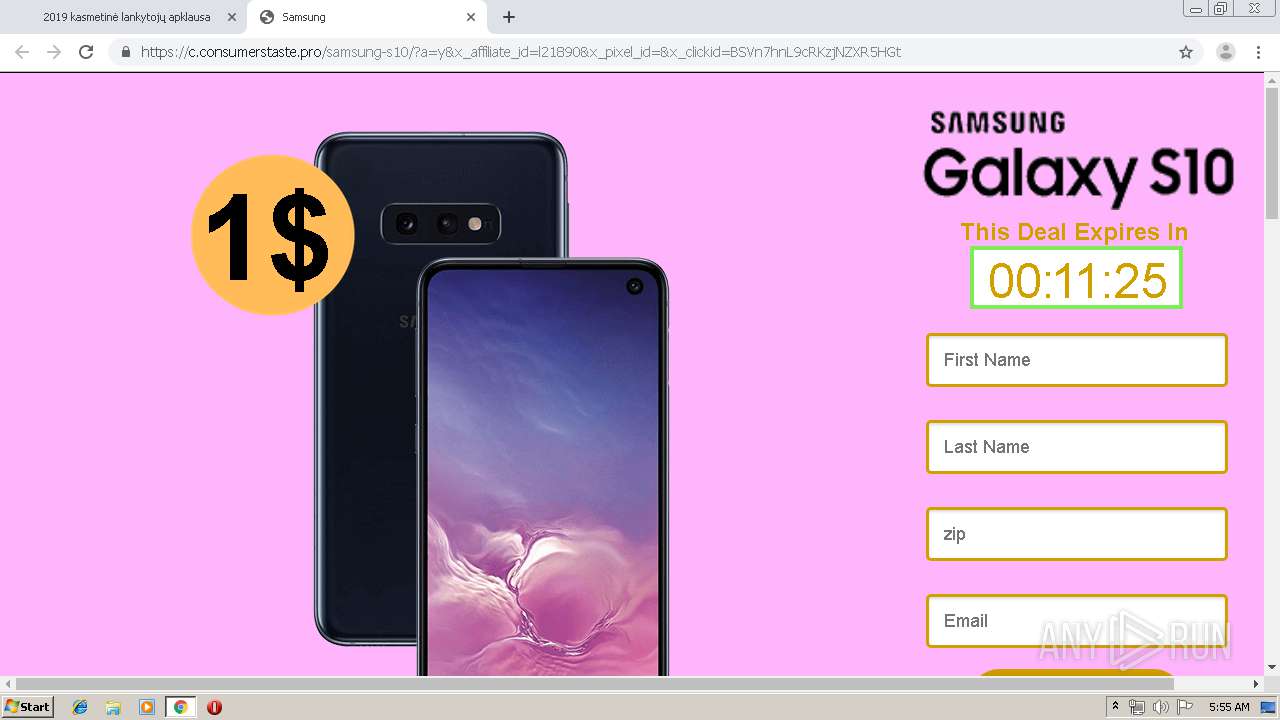
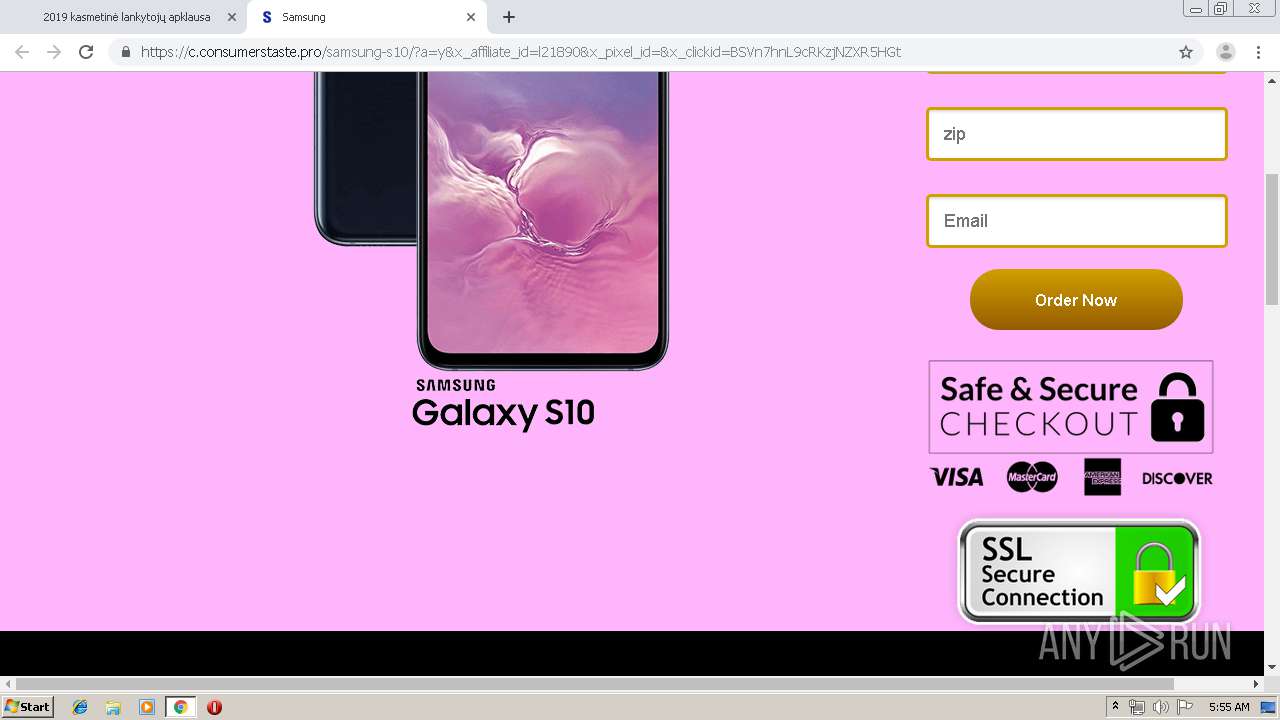
2988 | chrome.exe | GET | 302 | 104.18.39.82:80 | http://earthbonus.host/?u=1gnpae3&o=0lpkqzc&t=mwe-p&cid=44csfnlt1bgq996qv2j4r | US | html | 243 b | suspicious |
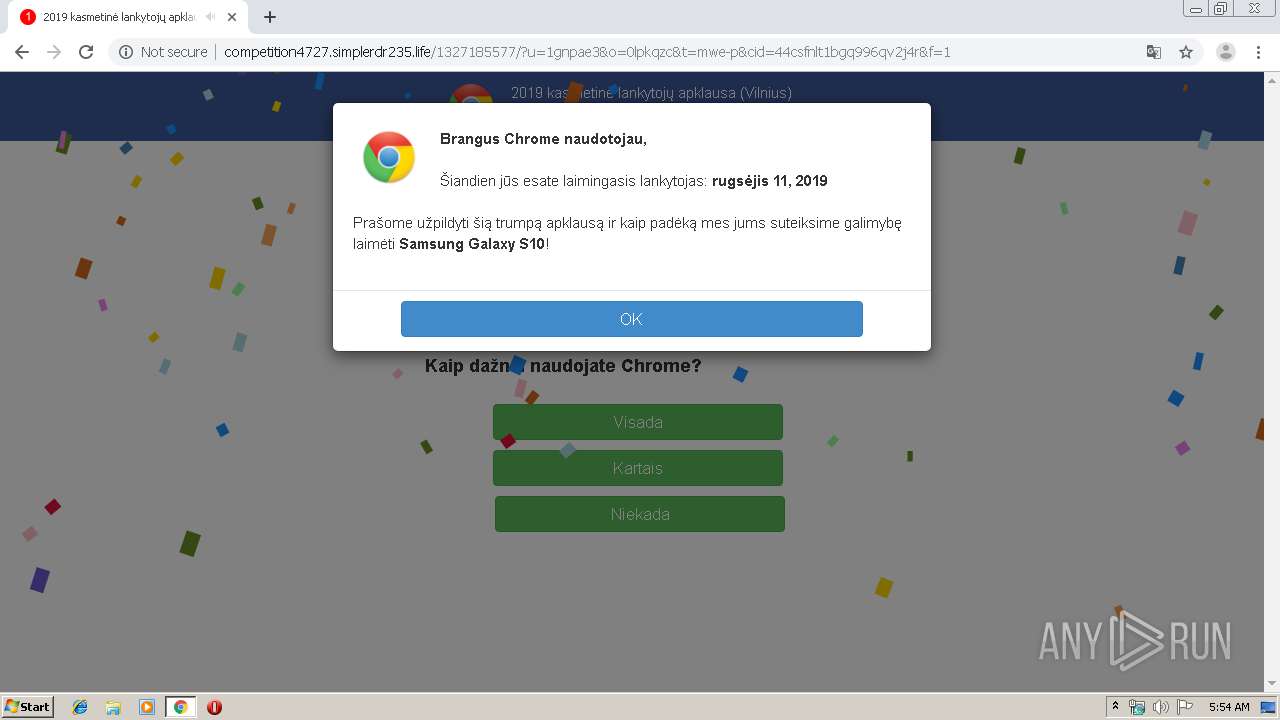
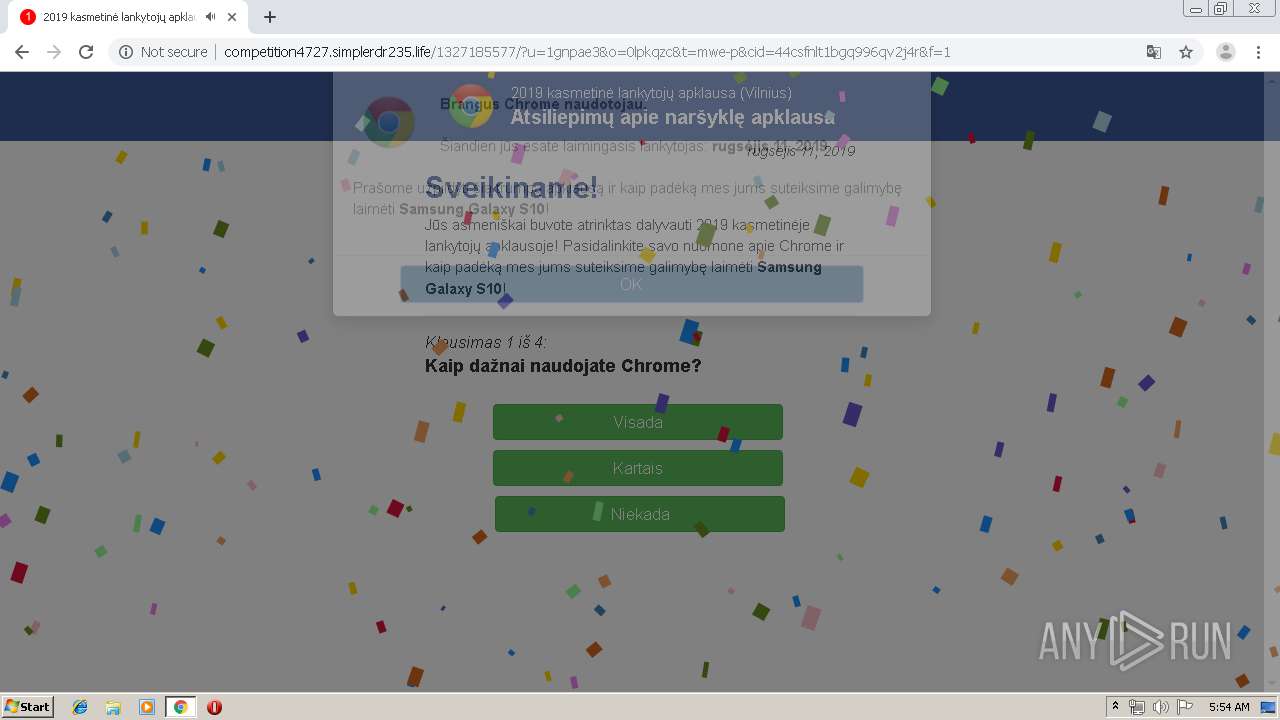
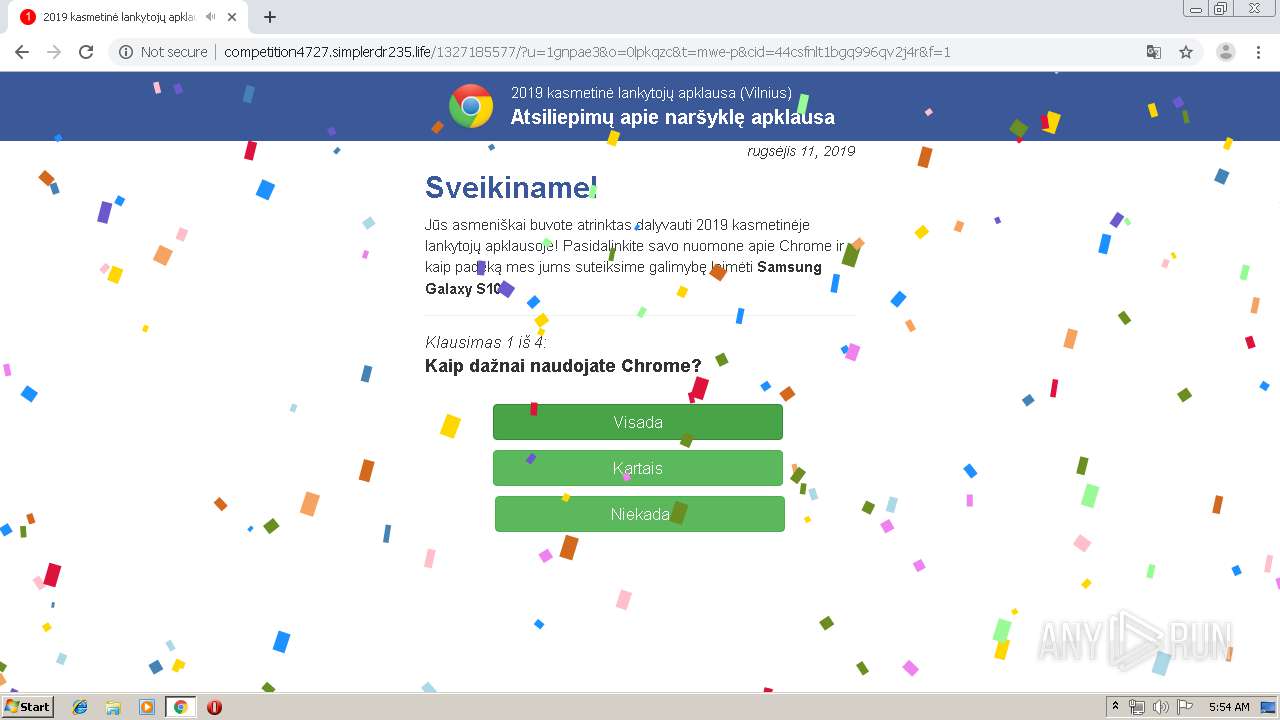
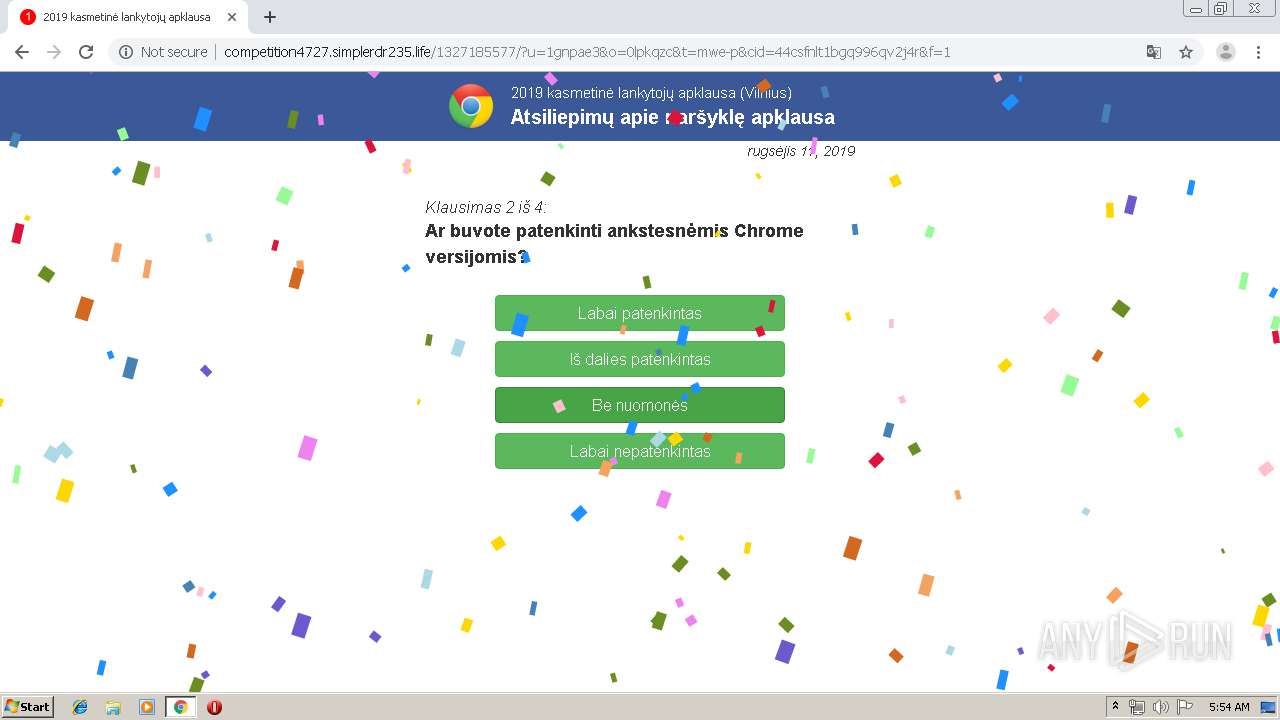
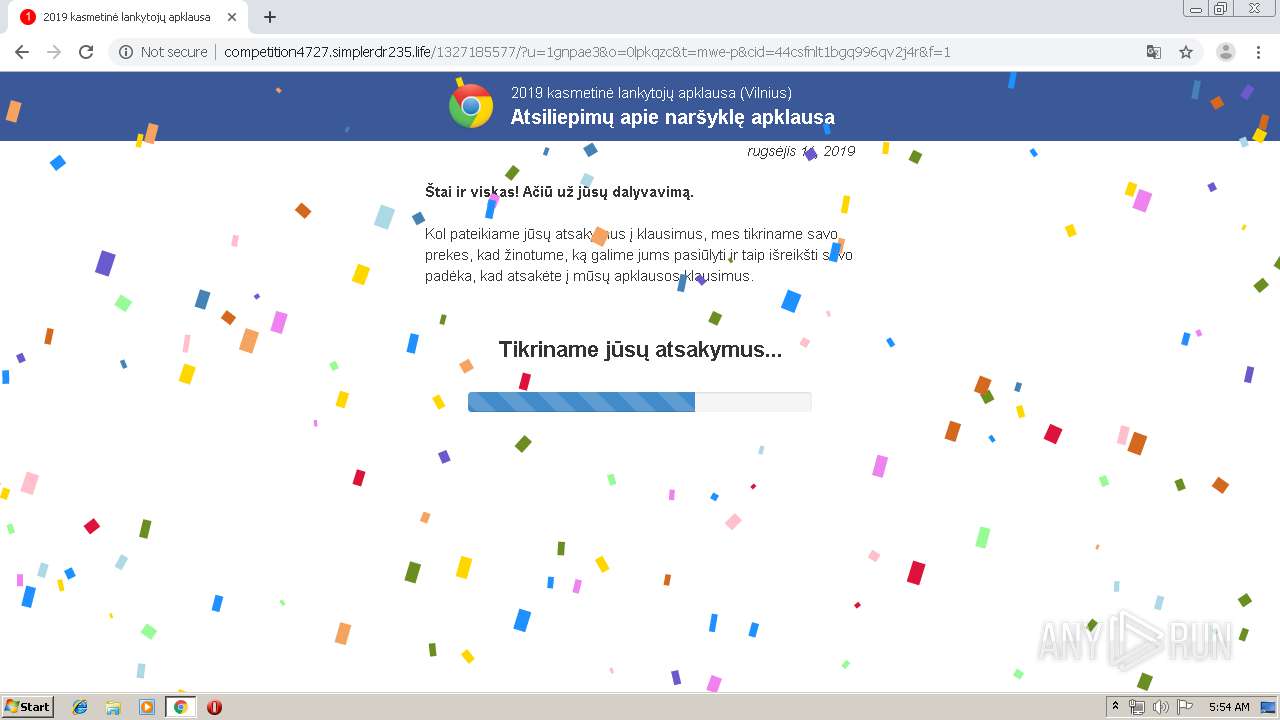
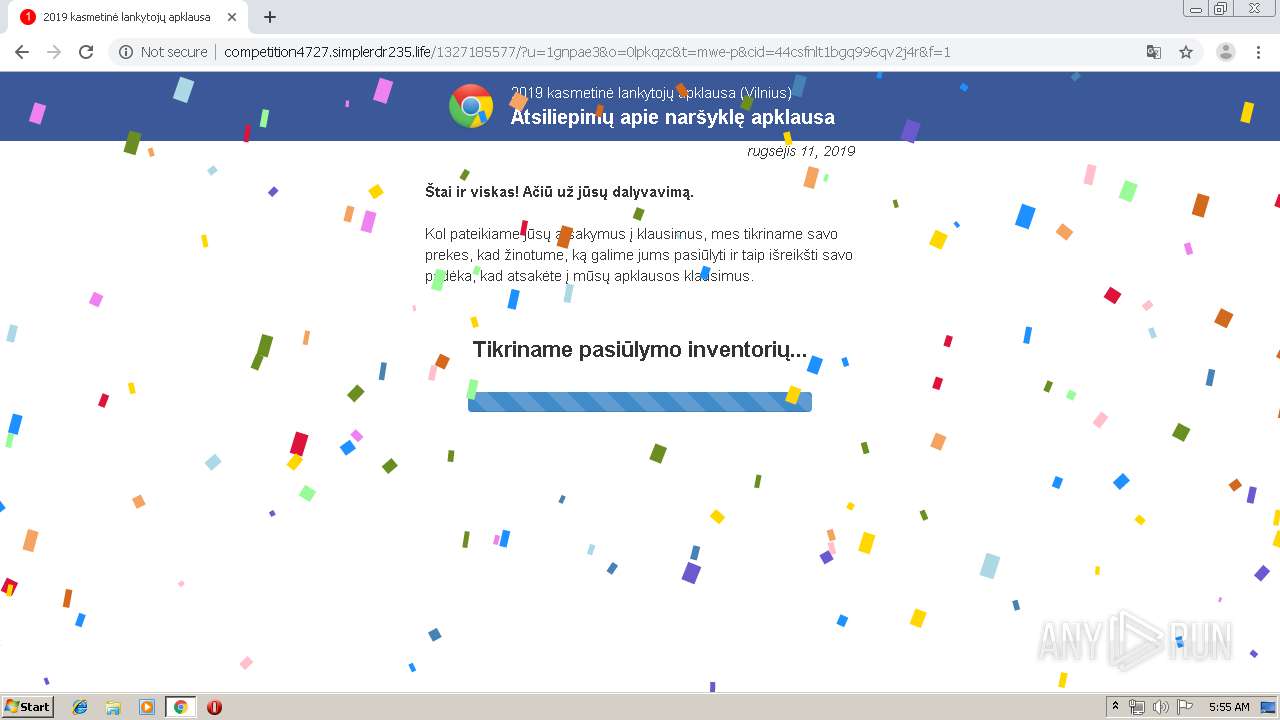
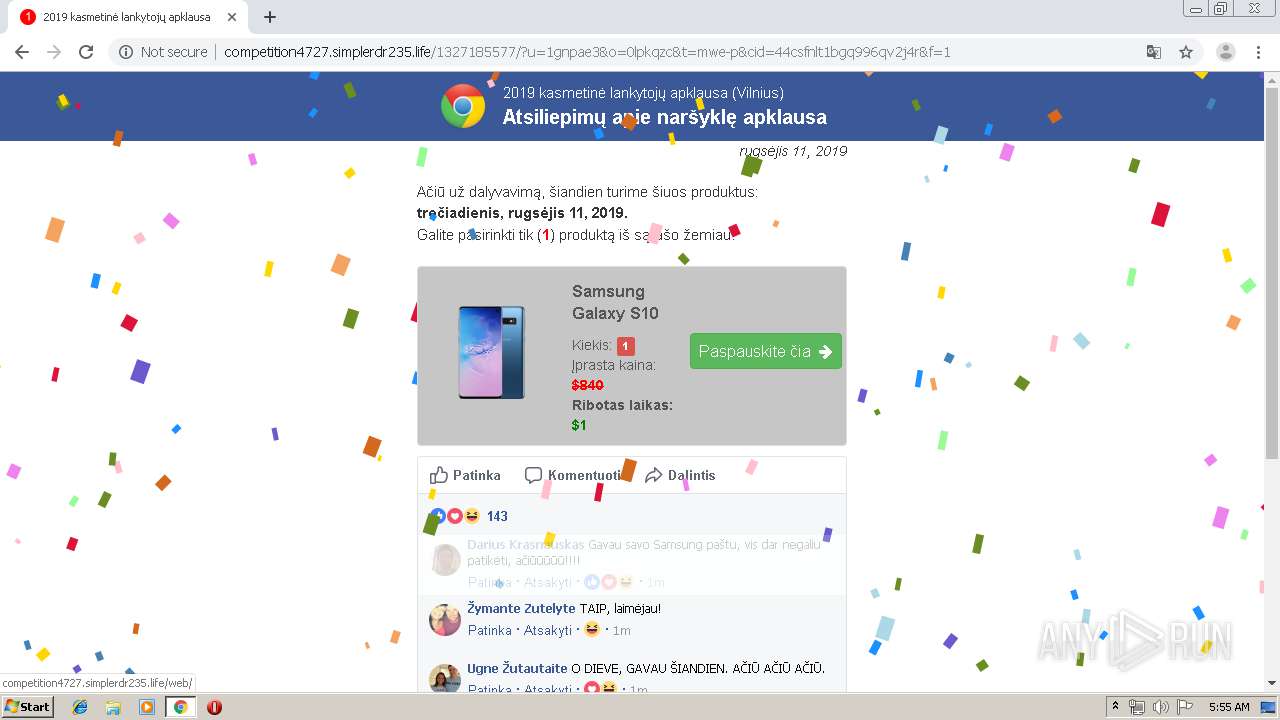
2988 | chrome.exe | GET | 200 | 185.89.102.128:80 | http://competition4727.simplerdr235.life/1327185577/?u=1gnpae3&o=0lpkqzc&t=mwe-p&cid=44csfnlt1bgq996qv2j4r&f=1 | UA | html | 17.2 Kb | suspicious |
2988 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 520 b | whitelisted |
2988 | chrome.exe | GET | 200 | 185.89.102.128:80 | http://competition4727.simplerdr235.life/media/mainstream/us/wap/mobsurvey/comment.js | UA | text | 2.77 Kb | suspicious |
2988 | chrome.exe | GET | 200 | 185.89.102.128:80 | http://competition4727.simplerdr235.life/util/utils-ms.js | UA | html | 17.8 Kb | suspicious |
2988 | chrome.exe | GET | 200 | 185.89.102.128:80 | http://competition4727.simplerdr235.life/media/mainstream/lt/wap/mobsurvey/font-awesome.css | UA | text | 17.2 Kb | suspicious |
2988 | chrome.exe | GET | 200 | 185.89.102.128:80 | http://competition4727.simplerdr235.life/media/mainstream/lt/wap/mobsurvey/modernizr-2.6.2-respond-1.1.0.min.js | UA | html | 17.8 Kb | suspicious |
2988 | chrome.exe | GET | 200 | 185.89.102.128:80 | http://competition4727.simplerdr235.life/media/mainstream/lt/wap/mobsurvey/main.css | UA | text | 7.03 Kb | suspicious |
2988 | chrome.exe | GET | 200 | 185.89.102.128:80 | http://competition4727.simplerdr235.life/media/mainstream/lt/wap/mobsurvey/returnDate.lt.js | UA | text | 590 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2988 | chrome.exe | 104.19.196.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
2988 | chrome.exe | 104.31.73.148:443 | crowdmind.host | Cloudflare Inc | US | shared |
2988 | chrome.exe | 178.128.141.43:443 | newscode.me | Forthnet | GR | unknown |
— | — | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
— | — | 216.58.205.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 87.245.196.12:80 | r1---sn-gxuog0-bvwe.gvt1.com | RETN Limited | RU | whitelisted |
2988 | chrome.exe | 108.177.15.188:5228 | mtalk.google.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 104.28.31.130:443 | tiobiter.gq | Cloudflare Inc | US | shared |
2988 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tiobiter.gq |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cdnjs.cloudflare.com |
| whitelisted |
crowdmind.host |
| unknown |
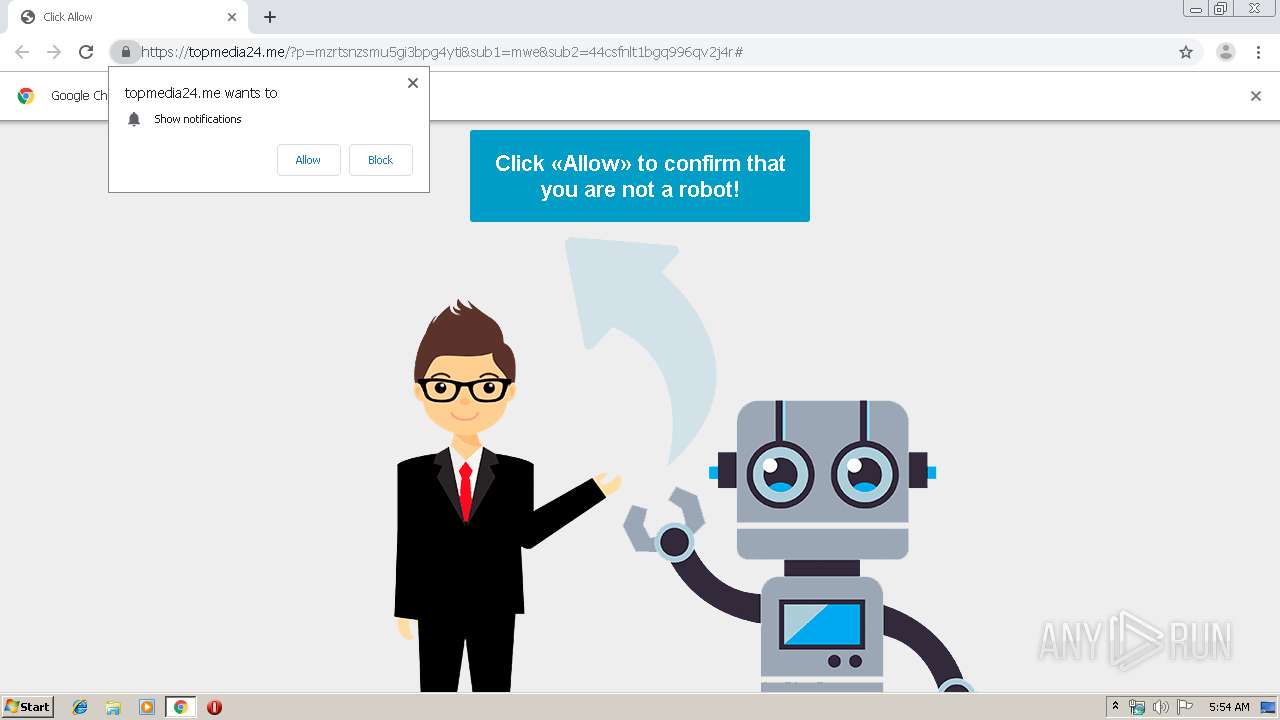
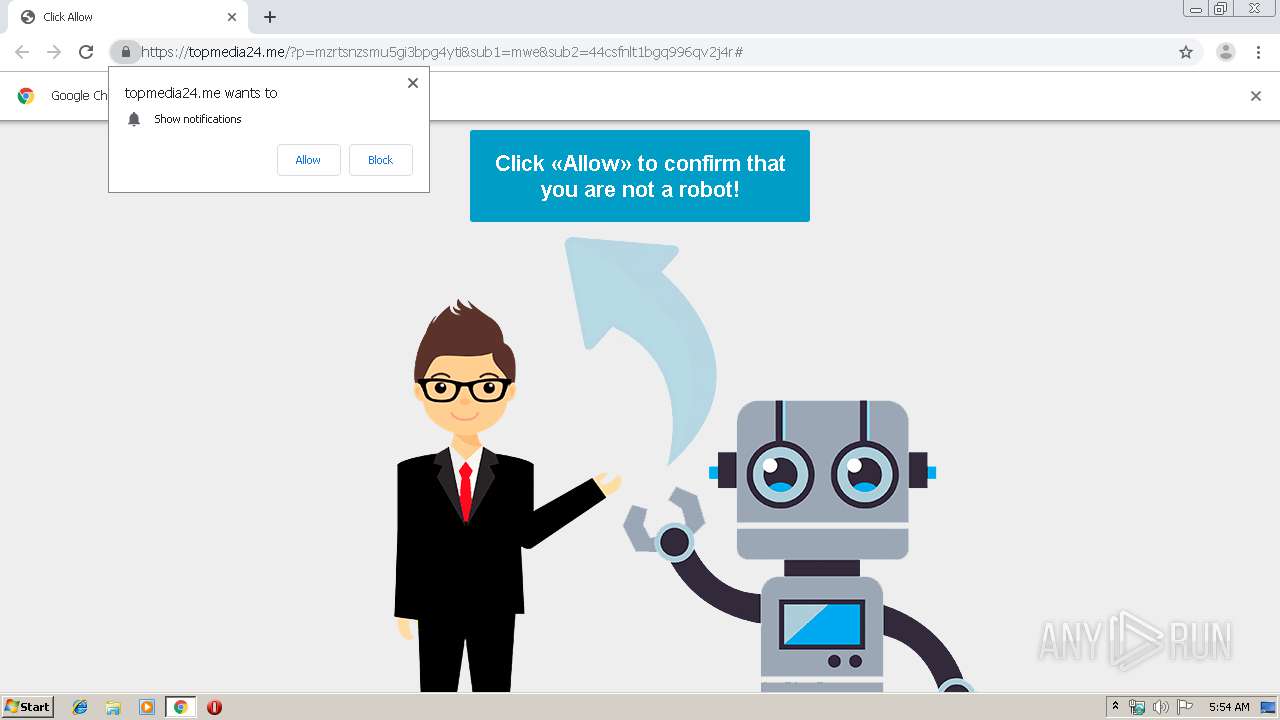
topmedia24.me |
| malicious |
clients2.google.com |
| whitelisted |
newscode.me |
| suspicious |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
2988 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.gq) in TLS SNI |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
2988 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2988 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2988 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2988 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2988 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2988 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2988 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2 ETPRO signatures available at the full report