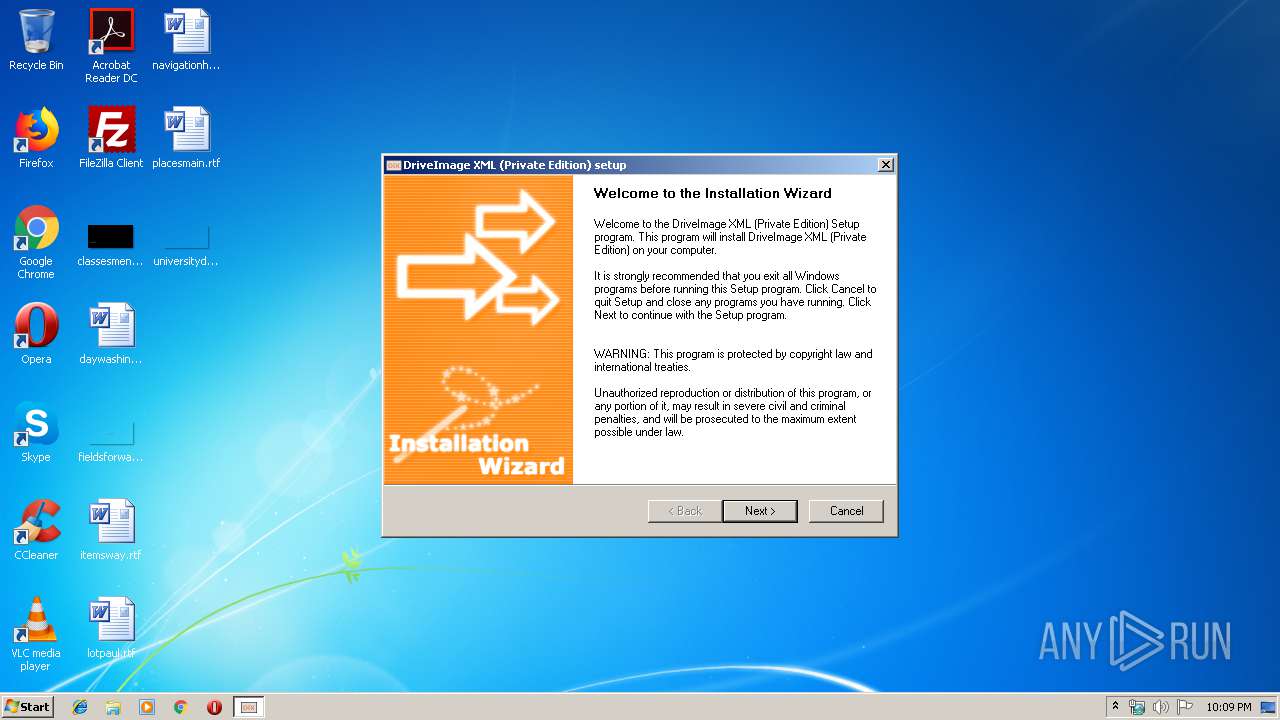
| File name: | dixmlsetup.exe |
| Full analysis: | https://app.any.run/tasks/50fe5711-4f95-428c-b1af-645b50c86b79 |
| Verdict: | Malicious activity |
| Analysis date: | October 11, 2019, 21:08:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 6C1FDAFC87373626693A76917F0294AE |
| SHA1: | 3CAD51549C20F775848617C18336DA9486016A2B |
| SHA256: | 75B37C7C2BD3B7ED6E852CF89505CC841F2929371672178A4E1AB5D6549F5BD8 |
| SSDEEP: | 49152:o2nEqFJHW8qRKx/Py44PQqL89H+lW656S:o2EqXHKQx/Ptw89H+ljIS |
MALICIOUS
Loads dropped or rewritten executable
- dixmlsetup.exe (PID: 1524)
Application was dropped or rewritten from another process
- dixml.exe (PID: 1316)
- dixml.exe (PID: 2576)
SUSPICIOUS
Executable content was dropped or overwritten
- dixmlsetup.exe (PID: 1524)
Creates files in the user directory
- dixmlsetup.exe (PID: 1524)
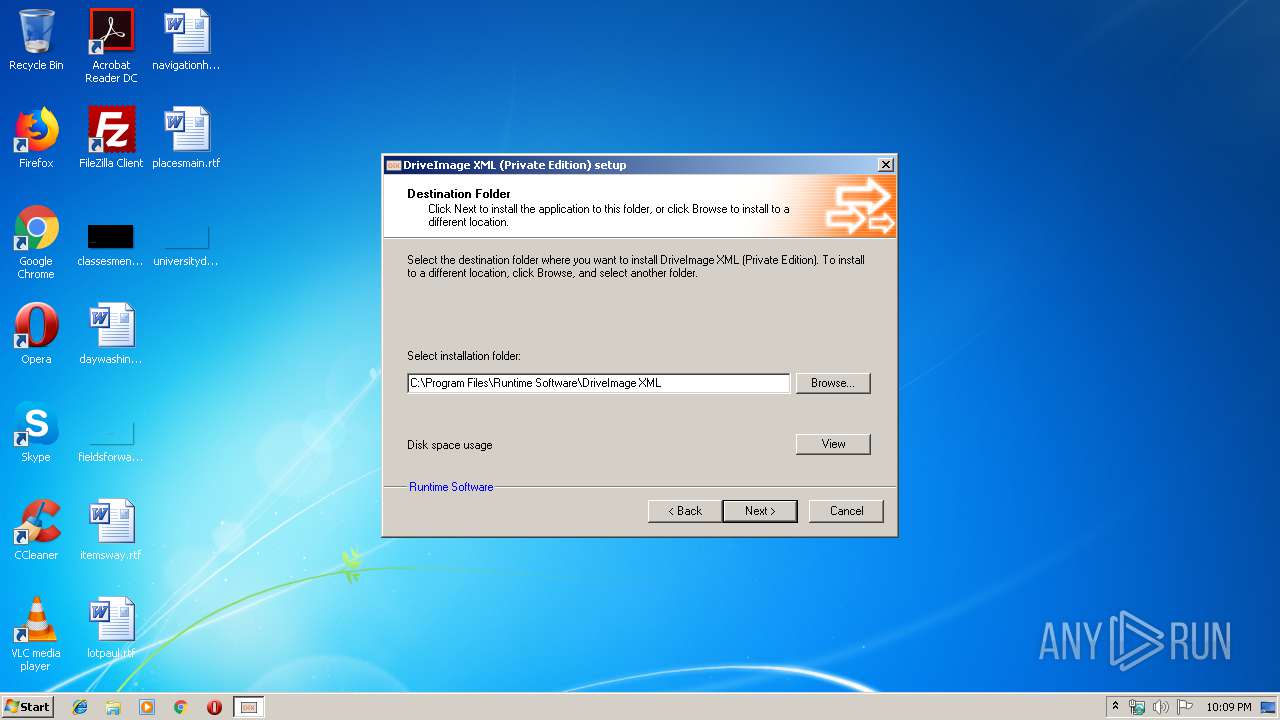
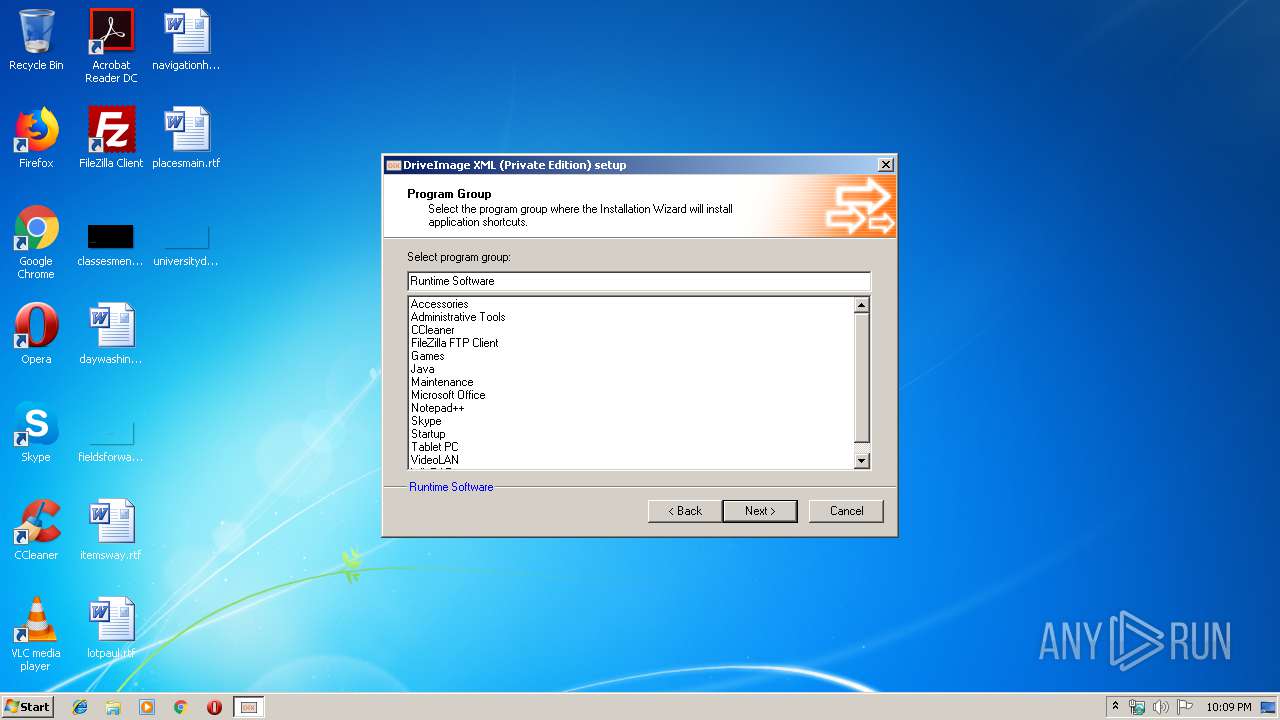
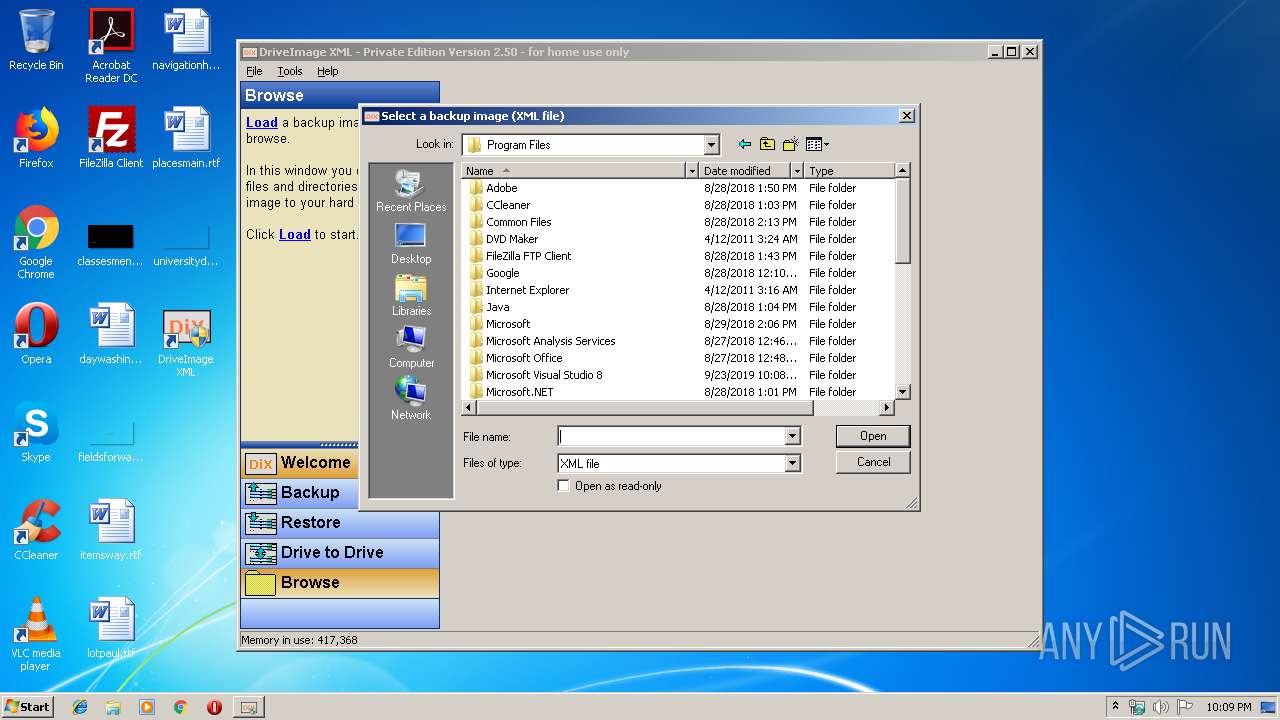
Creates files in the program directory
- dixml.exe (PID: 2576)
- dixmlsetup.exe (PID: 1524)
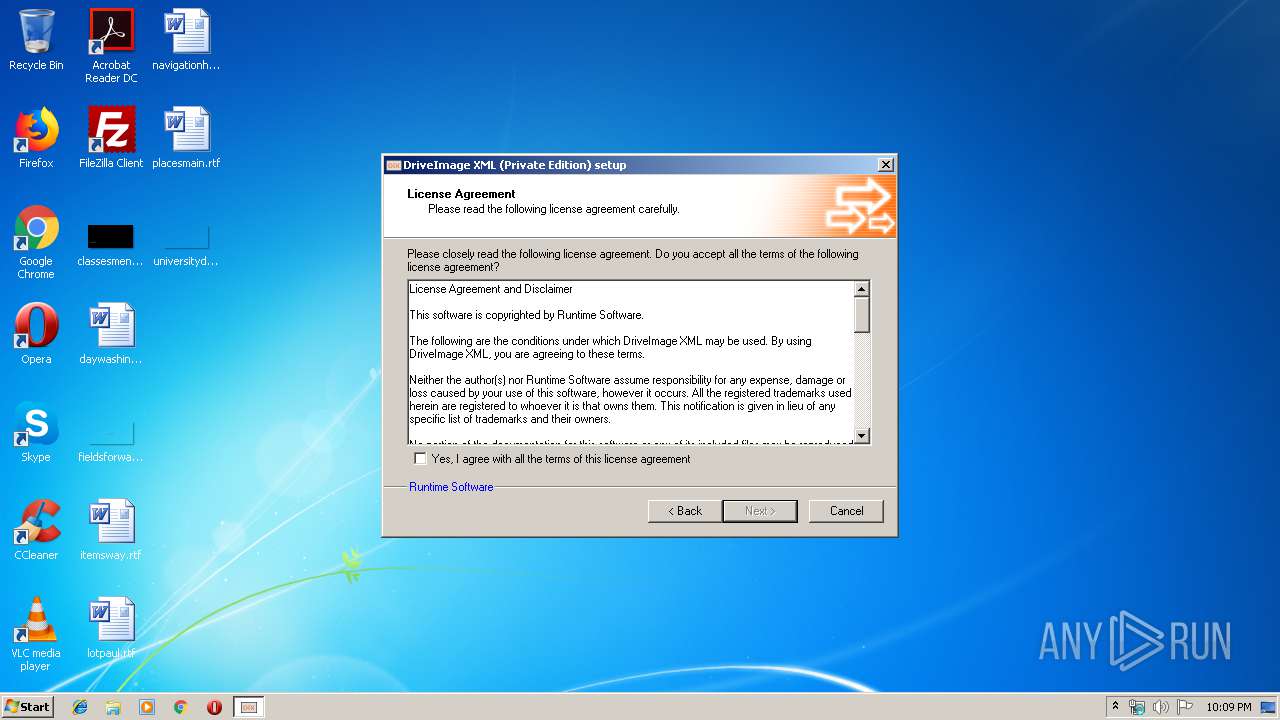
Creates a software uninstall entry
- dixmlsetup.exe (PID: 1524)
Reads Internet Cache Settings
- dixml.exe (PID: 2576)
INFO
Manual execution by user
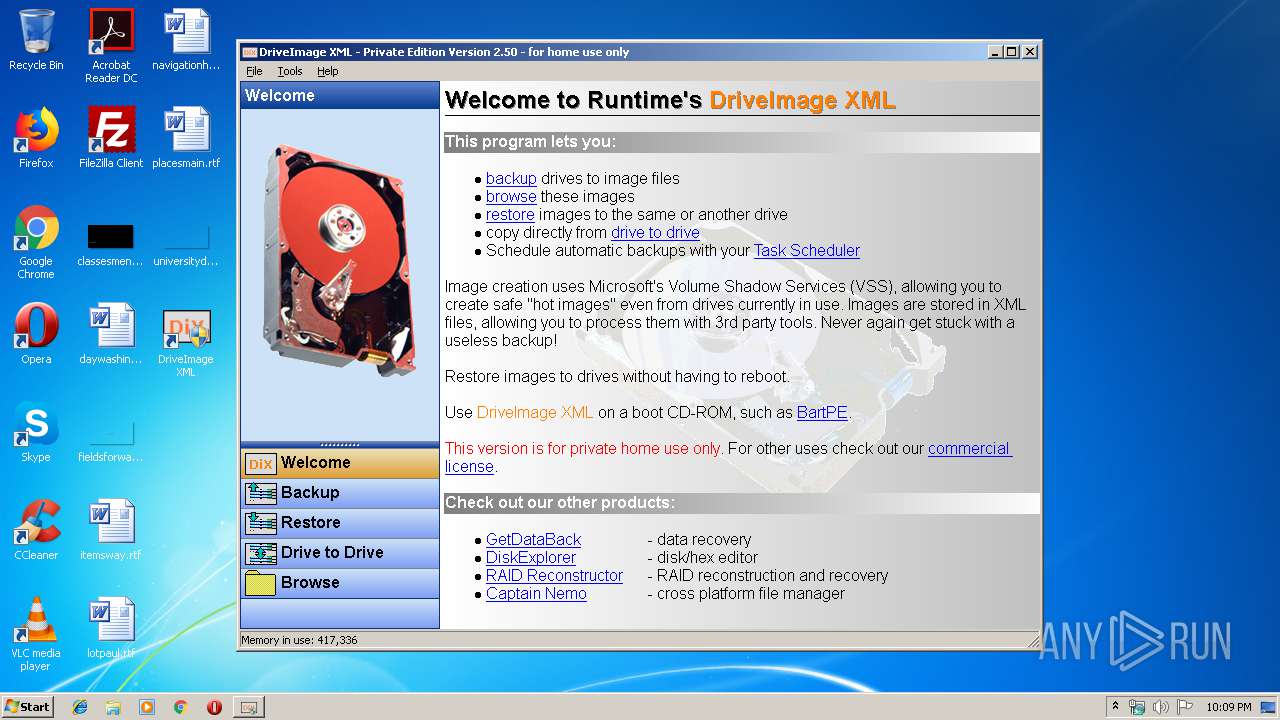
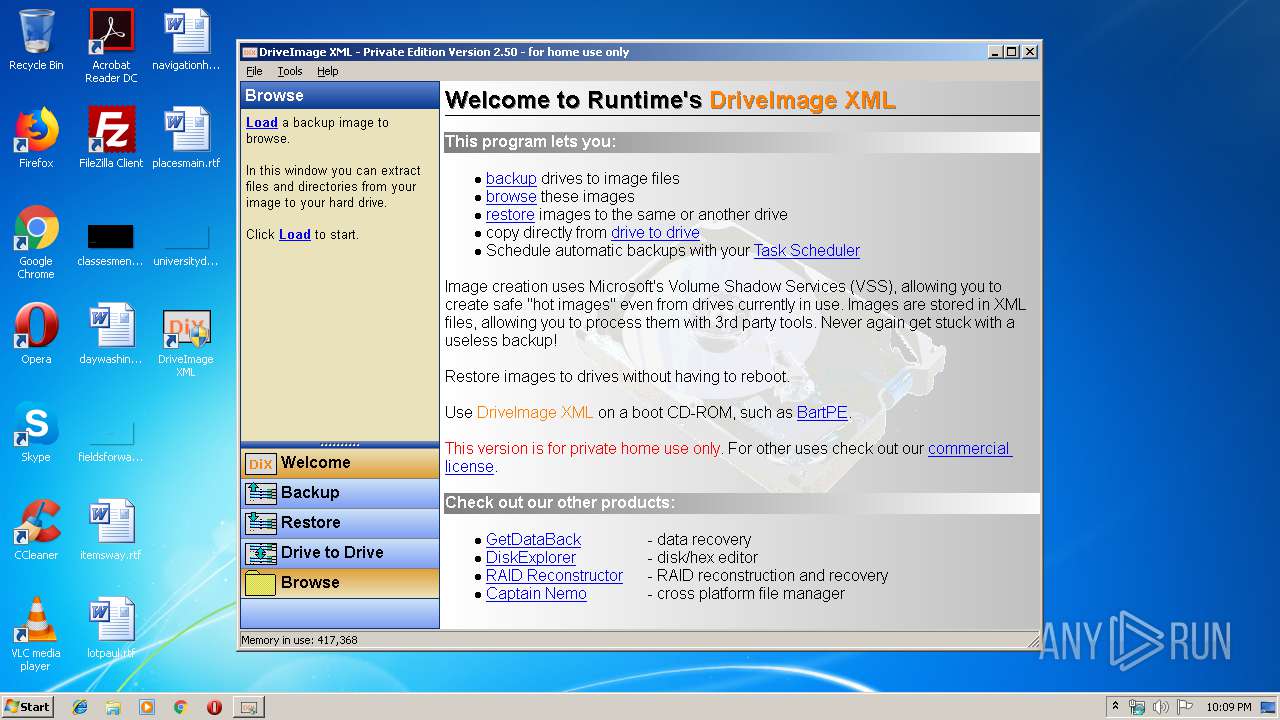
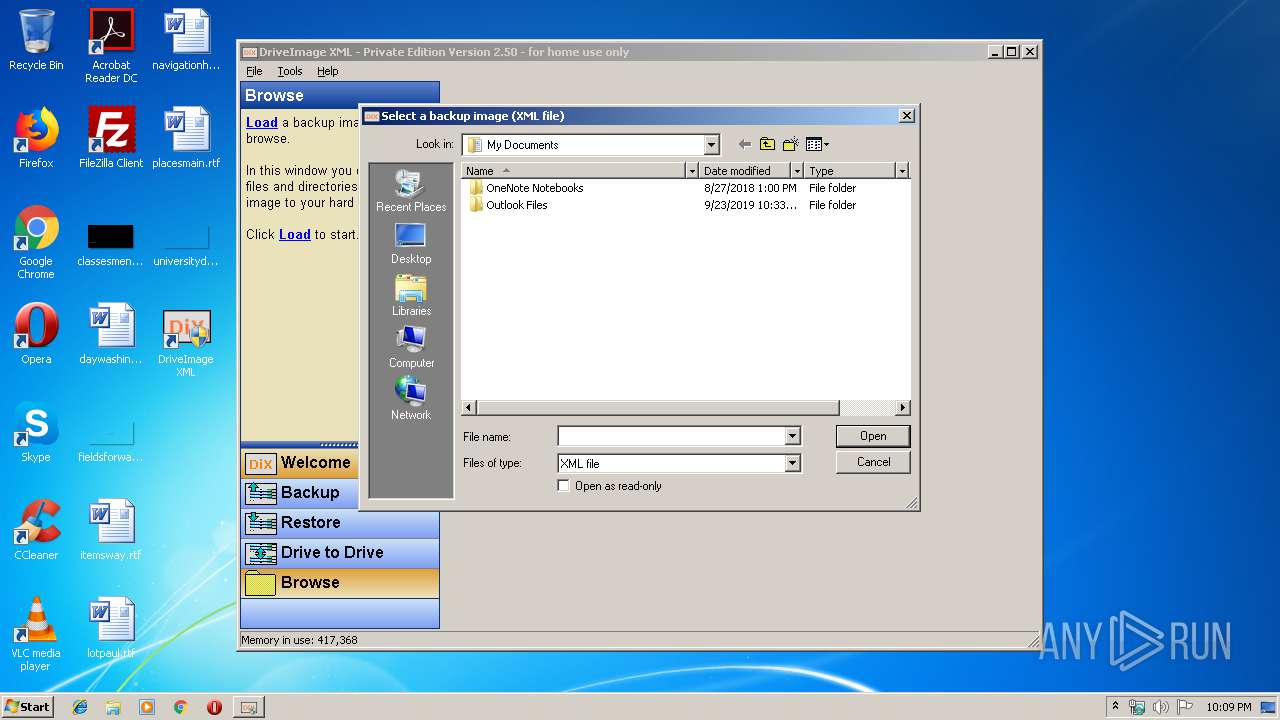
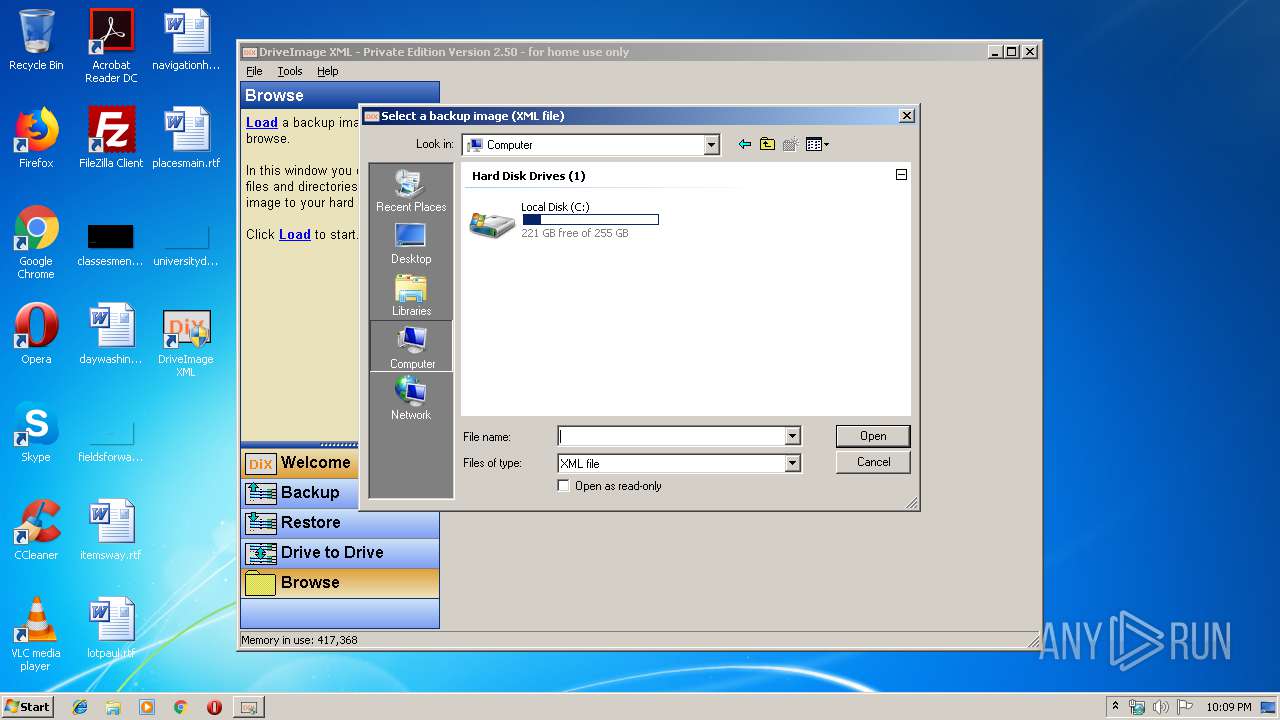
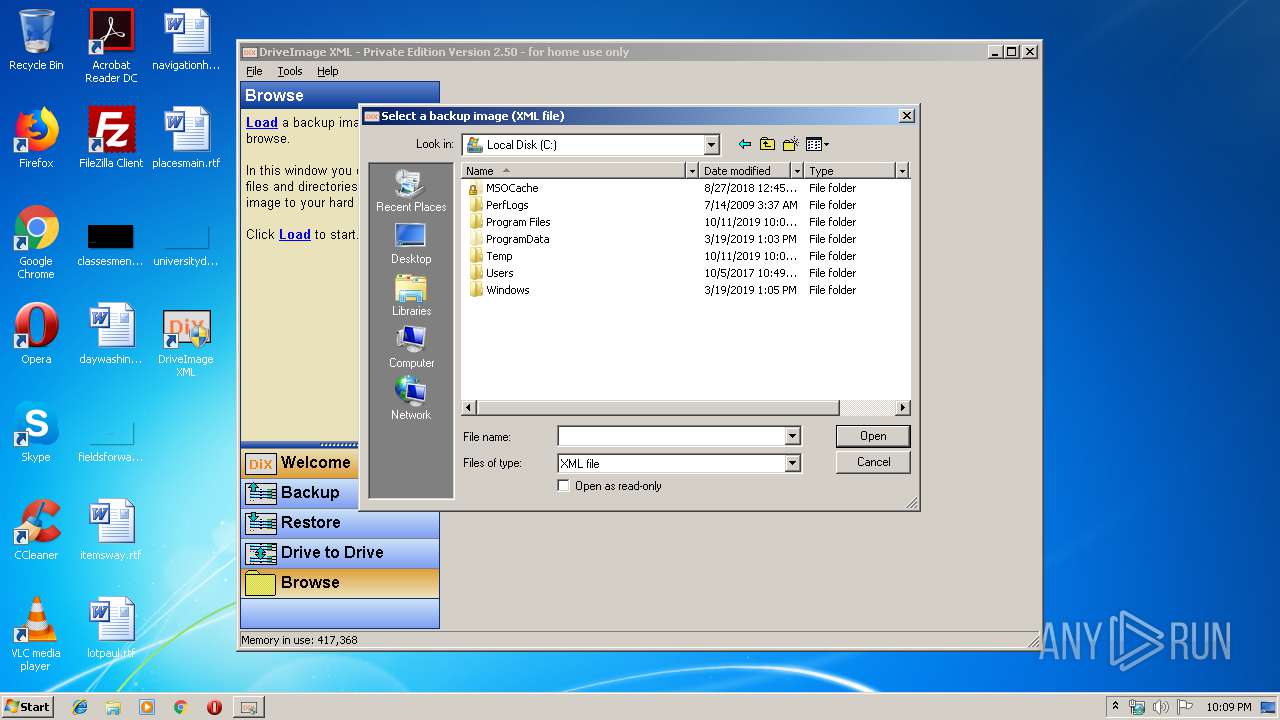
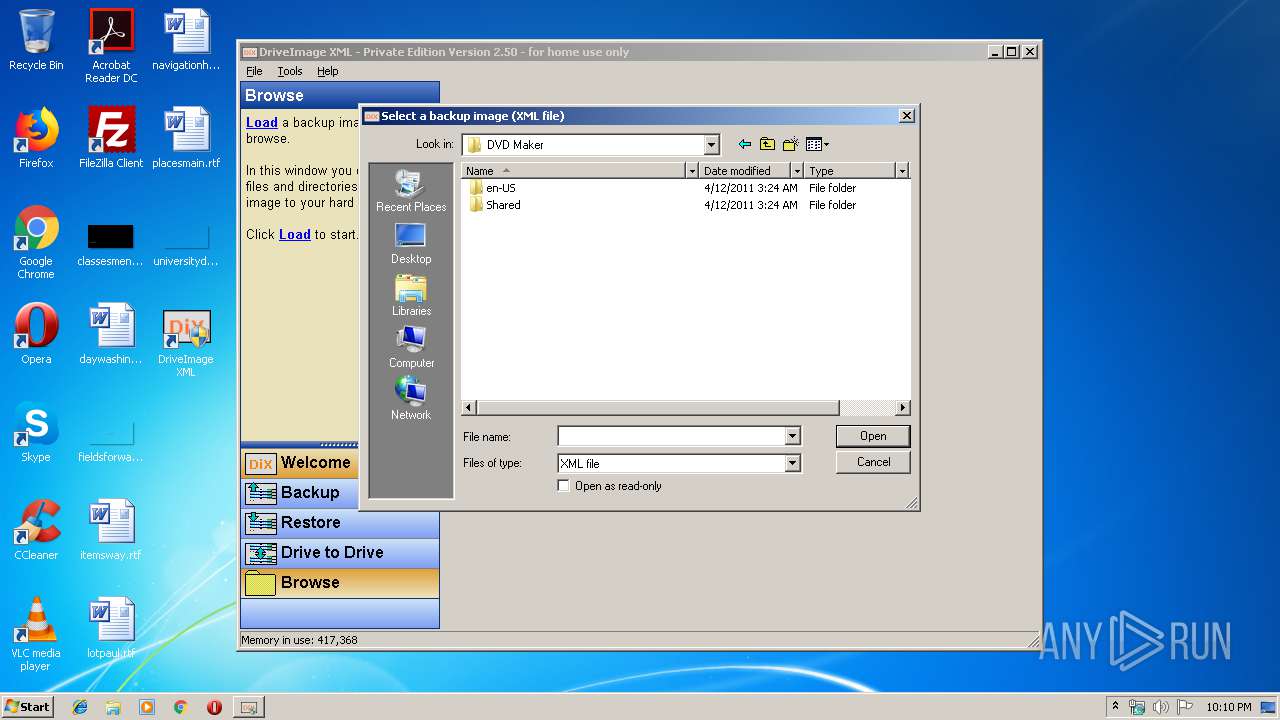
- dixml.exe (PID: 2576)
- dixml.exe (PID: 1316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (38.2) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (37.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.2) |
| .exe | | | Win32 Executable (generic) (6.3) |
| .exe | | | Win16/32 Executable Delphi generic (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 135168 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | 278528 |
| EntryPoint: | 0x65da0 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00044000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00045000 | 0x00021000 | 0x00021000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.91774 |
.rsrc | 0x00066000 | 0x00003000 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.26033 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05797 | 522 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.47151 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.91708 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.91366 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.13639 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4089 | 7.64472 | 956 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 7.68747 | 1248 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 7.64996 | 756 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 6.94829 | 228 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 6.84161 | 188 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
45
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1028 | "C:\Users\admin\AppData\Local\Temp\dixmlsetup.exe" | C:\Users\admin\AppData\Local\Temp\dixmlsetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Runtime Software\DriveImage XML\dixml.exe" | C:\Program Files\Runtime Software\DriveImage XML\dixml.exe | — | explorer.exe | |||||||||||
User: admin Company: Runtime Software Integrity Level: MEDIUM Description: DriveImage XML - Private Edition Exit code: 3221226540 Version: 2.5.0.0 Modules
| |||||||||||||||
| 1524 | "C:\Users\admin\AppData\Local\Temp\dixmlsetup.exe" | C:\Users\admin\AppData\Local\Temp\dixmlsetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Runtime Software\DriveImage XML\dixml.exe" | C:\Program Files\Runtime Software\DriveImage XML\dixml.exe | explorer.exe | ||||||||||||
User: admin Company: Runtime Software Integrity Level: HIGH Description: DriveImage XML - Private Edition Exit code: 0 Version: 2.5.0.0 Modules
| |||||||||||||||
Total events
1 060
Read events
823
Write events
236
Delete events
1
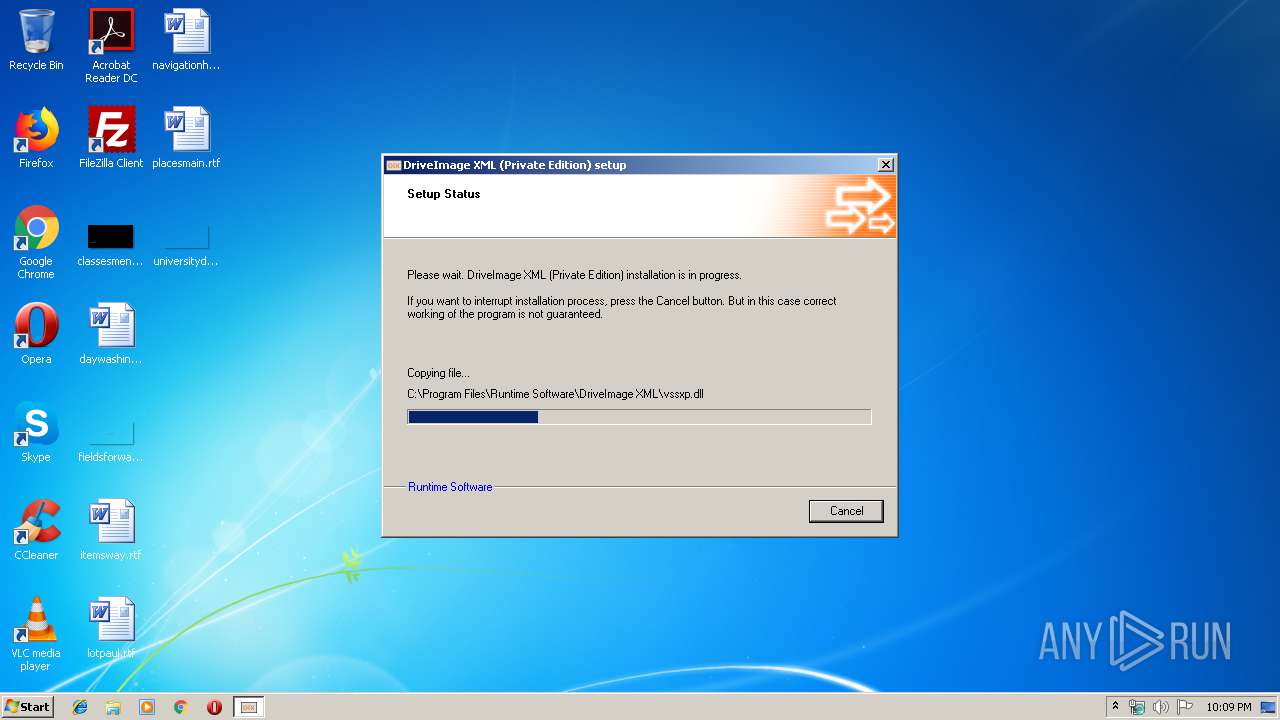
Modification events
| (PID) Process: | (1524) dixmlsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Runtime Software\DIXML |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files\Runtime Software\DriveImage XML | |||
| (PID) Process: | (1524) dixmlsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Runtime Software\DIXML |
| Operation: | write | Name: | Version |
Value: 2.50.000 | |||
| (PID) Process: | (1524) dixmlsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F7E1CA14-B39D-452A-960B-39423DDDD933} |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (1524) dixmlsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F7E1CA14-B39D-452A-960B-39423DDDD933} |
| Operation: | write | Name: | DisplayName |
Value: DriveImage XML (Private Edition) | |||
| (PID) Process: | (1524) dixmlsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F7E1CA14-B39D-452A-960B-39423DDDD933} |
| Operation: | write | Name: | ModifyPath |
Value: "C:\Program Files\Runtime Software\DriveImage XML\Uninstall.exe" "C:\Program Files\Runtime Software\DriveImage XML\install.log" | |||
| (PID) Process: | (1524) dixmlsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F7E1CA14-B39D-452A-960B-39423DDDD933} |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Runtime Software\DriveImage XML\Uninstall.exe" "C:\Program Files\Runtime Software\DriveImage XML\install.log" -u | |||
| (PID) Process: | (1524) dixmlsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F7E1CA14-B39D-452A-960B-39423DDDD933} |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Runtime Software\DriveImage XML | |||
| (PID) Process: | (1524) dixmlsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F7E1CA14-B39D-452A-960B-39423DDDD933} |
| Operation: | write | Name: | InstallSource |
Value: C:\Users\admin\AppData\Local\Temp | |||
| (PID) Process: | (1524) dixmlsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F7E1CA14-B39D-452A-960B-39423DDDD933} |
| Operation: | write | Name: | InstallSourceFile |
Value: C:\Users\admin\AppData\Local\Temp\dixmlsetup.exe | |||
| (PID) Process: | (1524) dixmlsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F7E1CA14-B39D-452A-960B-39423DDDD933} |
| Operation: | write | Name: | InstallDate |
Value: 10/11/2019 | |||
Executable files
11
Suspicious files
3
Text files
15
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1524 | dixmlsetup.exe | C:\Temp\3FP7JCCO\Resume.exe | executable | |
MD5:— | SHA256:— | |||
| 1524 | dixmlsetup.exe | C:\Temp\3FP7JCCO\dixmlsetup\maindb | binary | |
MD5:— | SHA256:— | |||
| 1524 | dixmlsetup.exe | C:\Temp\3FP7JCCO\dixmlsetup\packagedb | binary | |
MD5:— | SHA256:— | |||
| 1524 | dixmlsetup.exe | C:\Temp\3FP7JCCO\dixmlsetup\presetup\butt_cancel.bmp | image | |
MD5:610790880AF04A61D92C552145F295FB | SHA256:54E304DBF6BAF2C212C3138134A1FCF7C4BAC0CD89778EA4E395A6D319D2381C | |||
| 1524 | dixmlsetup.exe | C:\Temp\3FP7JCCO\dixmlsetup\plugins\0\CustomUI.dll | executable | |
MD5:5112C614BC619F7645DC8CC59566E650 | SHA256:EDE6693D4BD8A795E51CCA3C526FF4F419CB4BA3101CC738ED9417001E70412E | |||
| 1524 | dixmlsetup.exe | C:\Temp\3FP7JCCO\dixmlsetup\presetup\maintenance.bmp | image | |
MD5:D424965D5F4D233DE84F3F7611382469 | SHA256:429816608E9BED397AAB109C33526D12795694A69AA20A8A8F37E97C5B516039 | |||
| 1524 | dixmlsetup.exe | C:\Temp\3FP7JCCO\dixmlsetup\presetup.rgn | binary | |
MD5:4C53358F3DDDADFCCBA8DFD0C91F8DED | SHA256:4A2BFE0977756DD8ED38EF1A67365BE130E431C3CDFE4A3127D9AD9D7AD438B2 | |||
| 1524 | dixmlsetup.exe | C:\Temp\3FP7JCCO\dixmlsetup\presetup\watermark.bmp | image | |
MD5:34BD68C6829AB933F4E030F7D79269AE | SHA256:C3CA47C1EB6E1F96B4D8FFA77EF7BA46737FF5D73221380C3E3E041E96689D8C | |||
| 1524 | dixmlsetup.exe | C:\Temp\3FP7JCCO\dixmlsetup\presetup\unwatermark.bmp | image | |
MD5:B5882C2B639BD0F42EED8C615624DFF0 | SHA256:E6071E398839AE49D67837A256D245AC977F5FD6033CBB63CB3E694AB377054C | |||
| 1524 | dixmlsetup.exe | C:\Temp\3FP7JCCO\dixmlsetup\presetup\disclaimer.txt | text | |
MD5:348565BCC04545CE4E2FEF41CE6E6E5B | SHA256:9D6ECBC94CD84FA5EA1B90B33CAC659E012E2102CBDDB23587E7D9D4726FF6D6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
dixml.exe | loaded |