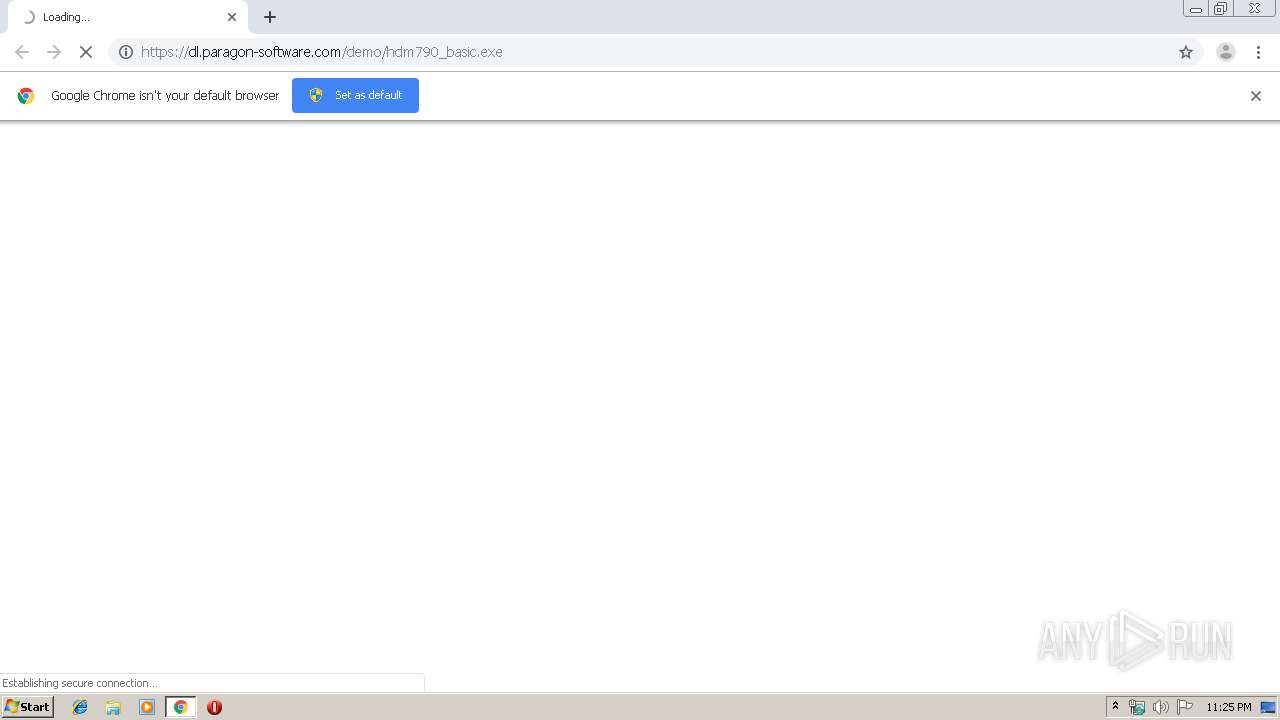
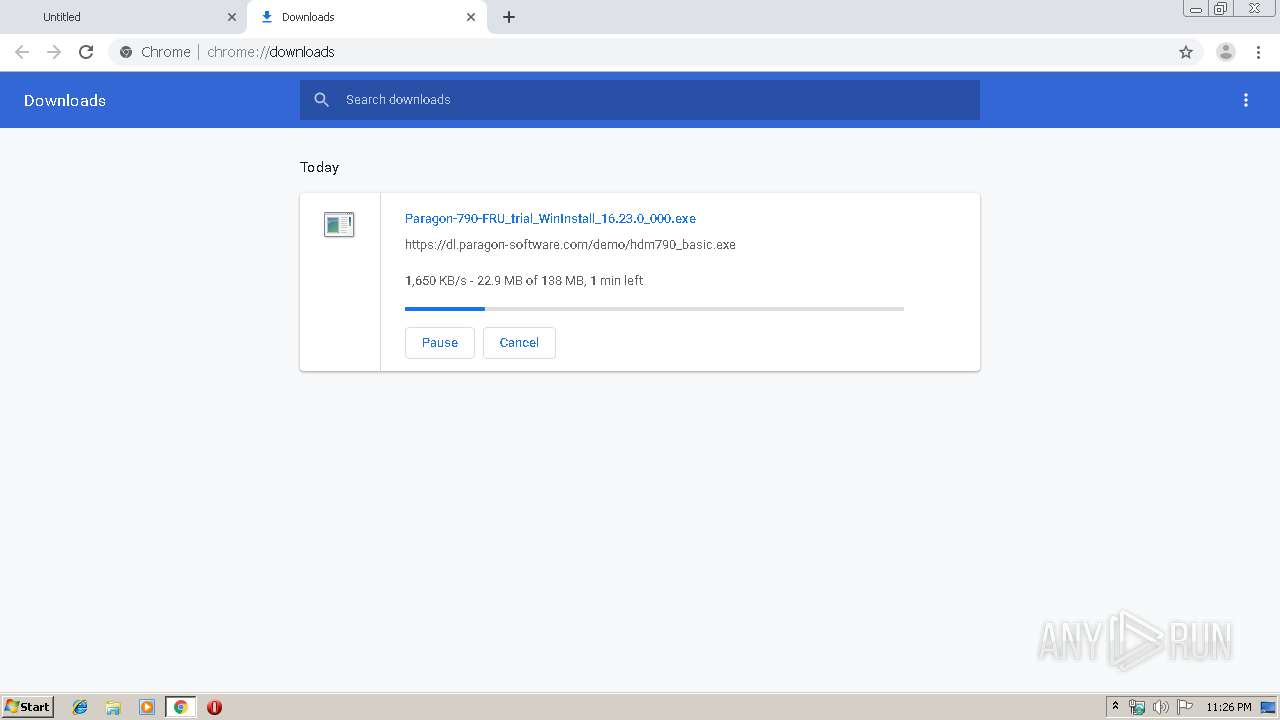
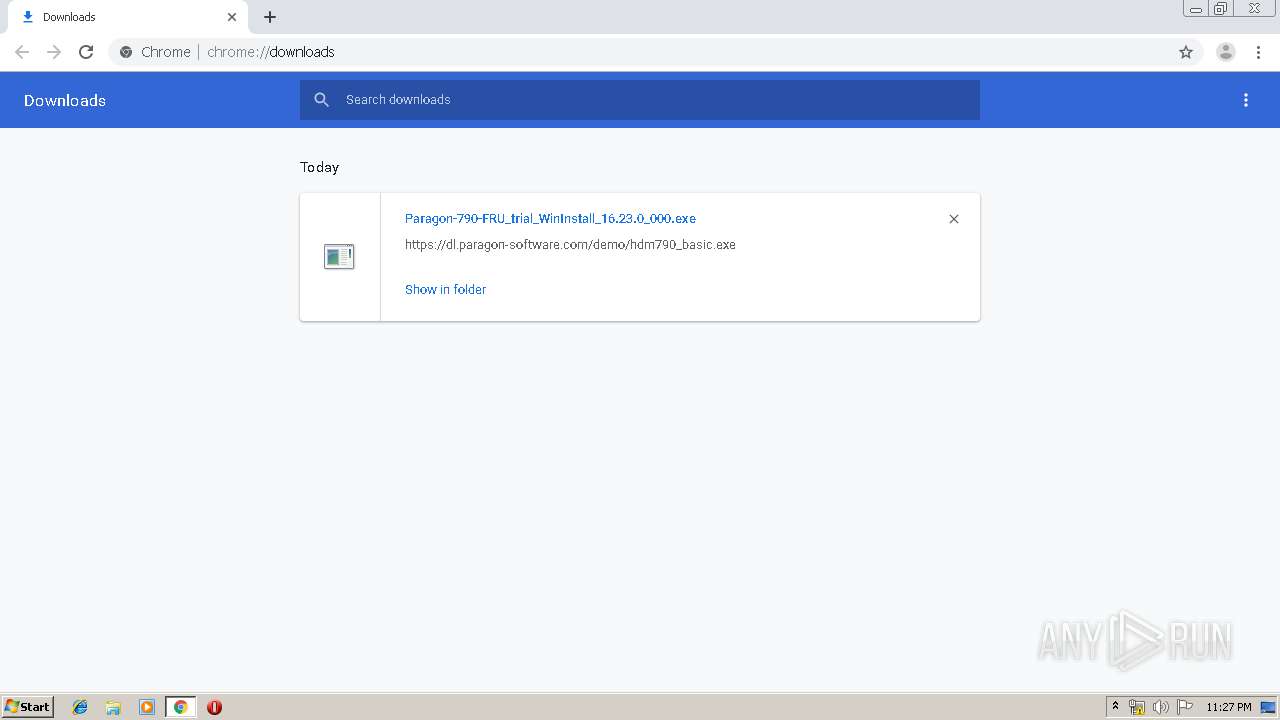
| URL: | https://dl.paragon-software.com/demo/hdm790_basic.exe |
| Full analysis: | https://app.any.run/tasks/b7ed5142-978f-41a5-9c10-30eac9cdb3a1 |
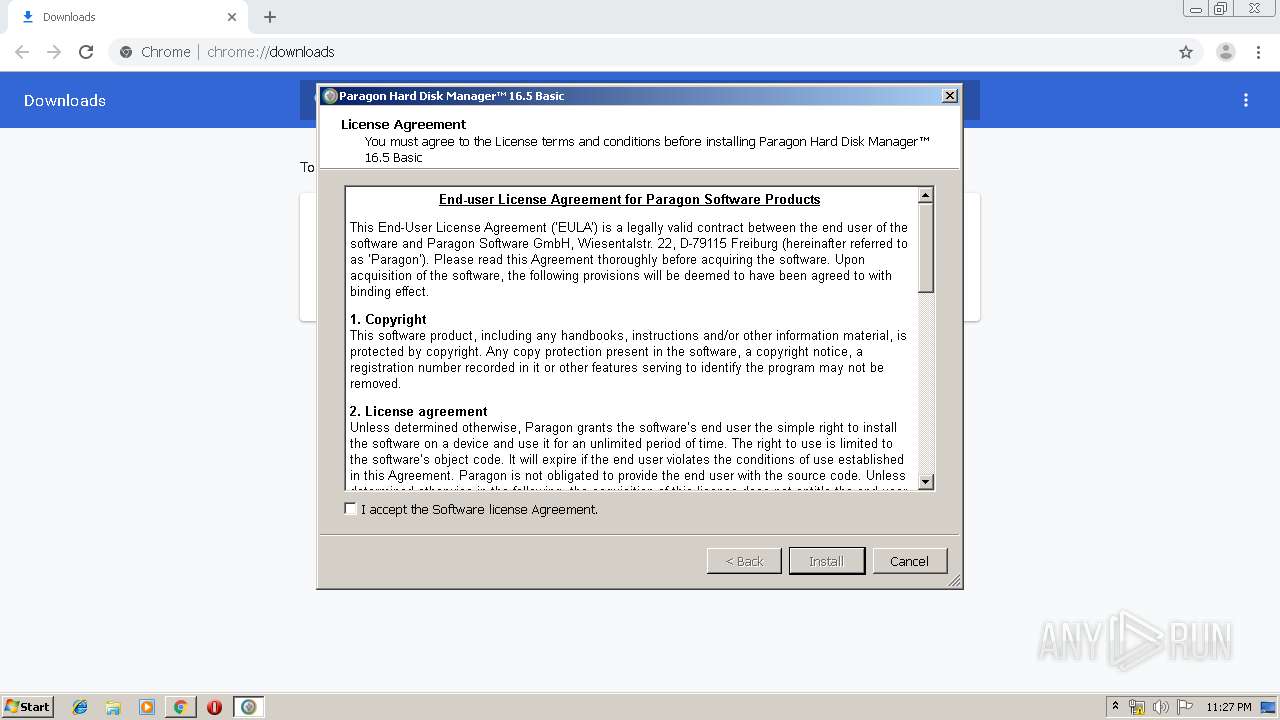
| Verdict: | Malicious activity |
| Analysis date: | December 25, 2019, 23:25:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0148C27D3DC5345082477F8DBE3EC2FD |
| SHA1: | 505698A649CBF7F16246D5754A082561F1102B34 |
| SHA256: | 7599D71F43F1BC97093D8BD5A814BEFBA96293F595161D41166FEDECCFFB8210 |
| SSDEEP: | 3:N8RSXeHFxAIK3VsEbA:2+v33ScA |
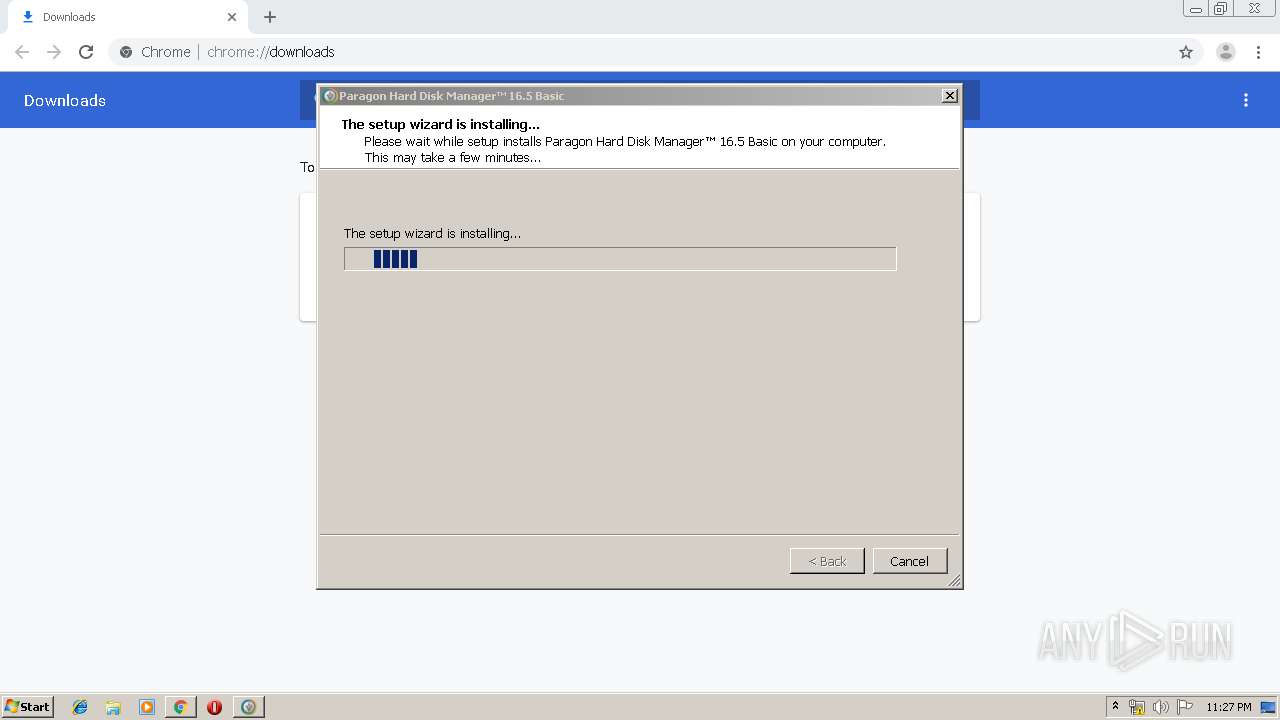
MALICIOUS
Application was dropped or rewritten from another process
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 1764)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 1028)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 1252)
- hdm16basic_x86.exe (PID: 2504)
- winfuse_uimsetup.exe (PID: 3156)
- advlauncher.exe (PID: 2196)
- QtWebEngineProcess.exe (PID: 2356)
- advlauncher.exe (PID: 1712)
- QtWebEngineProcess.exe (PID: 3332)
Loads dropped or rewritten executable
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 1252)
- WUDFHost.exe (PID: 720)
- winfuse_uimsetup.exe (PID: 3156)
- DrvInst.exe (PID: 328)
- advlauncher.exe (PID: 1712)
- QtWebEngineProcess.exe (PID: 2356)
- QtWebEngineProcess.exe (PID: 3332)
Changes settings of System certificates
- MsiExec.exe (PID: 3732)
- winfuse_uimsetup.exe (PID: 3156)
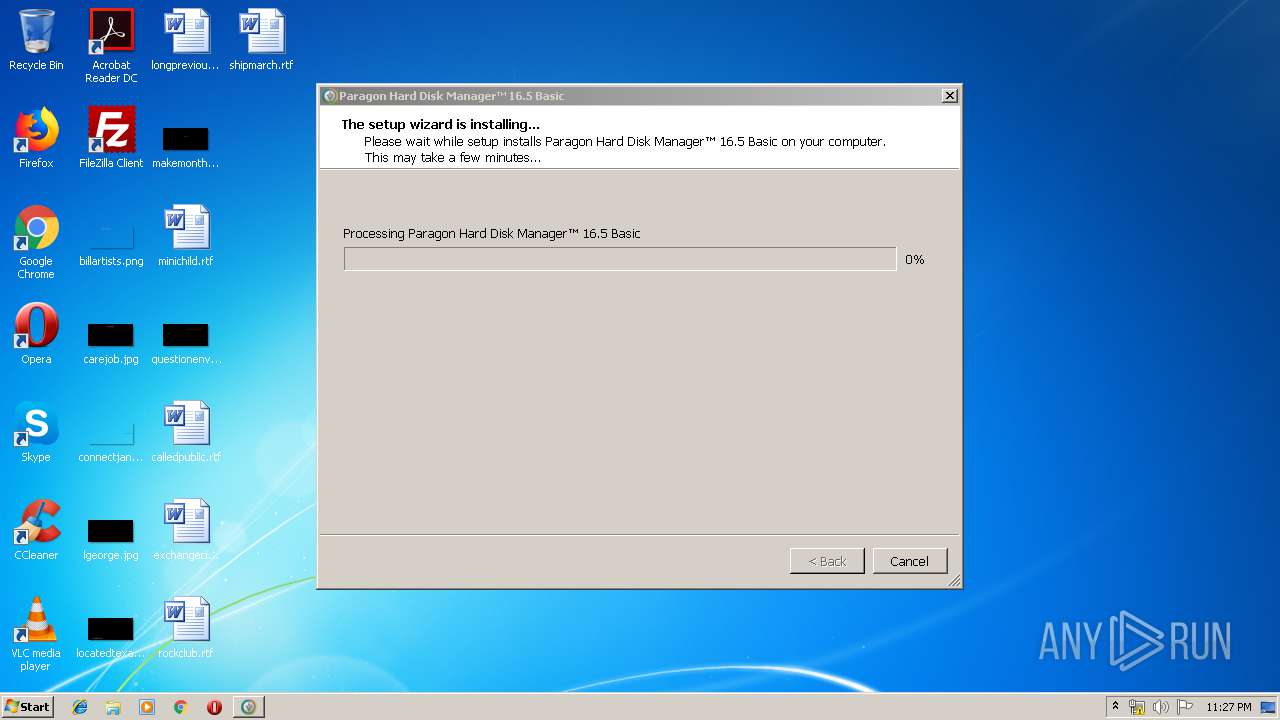
Changes the autorun value in the registry
- hdm16basic_x86.exe (PID: 2504)
Loads the Task Scheduler COM API
- advlauncher.exe (PID: 1712)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2556)
Executable content was dropped or overwritten
- chrome.exe (PID: 2556)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 1028)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 1252)
- hdm16basic_x86.exe (PID: 2504)
- winfuse_uimsetup.exe (PID: 3156)
- DrvInst.exe (PID: 1956)
- DrvInst.exe (PID: 328)
- DrvInst.exe (PID: 2860)
- DrvInst.exe (PID: 3696)
- DrvInst.exe (PID: 4048)
- DrvInst.exe (PID: 2712)
- msiexec.exe (PID: 392)
Creates files in the Windows directory
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 1028)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 1252)
- msiexec.exe (PID: 392)
- winfuse_uimsetup.exe (PID: 3156)
- DrvInst.exe (PID: 1956)
- DrvInst.exe (PID: 328)
- WUDFHost.exe (PID: 720)
- DrvInst.exe (PID: 2860)
- DrvInst.exe (PID: 3696)
- DrvInst.exe (PID: 4048)
- DrvInst.exe (PID: 2712)
- advlauncher.exe (PID: 1712)
Starts itself from another location
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 1252)
Creates files in the program directory
- hdm16basic_x86.exe (PID: 2504)
- advlauncher.exe (PID: 1712)
Creates a software uninstall entry
- hdm16basic_x86.exe (PID: 2504)
Changes IE settings (feature browser emulation)
- msiexec.exe (PID: 392)
Adds / modifies Windows certificates
- MsiExec.exe (PID: 3732)
- winfuse_uimsetup.exe (PID: 3156)
Executed via COM
- DrvInst.exe (PID: 1956)
- DrvInst.exe (PID: 328)
- DrvInst.exe (PID: 2860)
- DrvInst.exe (PID: 3696)
- DrvInst.exe (PID: 4048)
- DrvInst.exe (PID: 2712)
- vdsldr.exe (PID: 3480)
Removes files from Windows directory
- DrvInst.exe (PID: 1956)
- DrvInst.exe (PID: 328)
- DrvInst.exe (PID: 2860)
- DrvInst.exe (PID: 3696)
- DrvInst.exe (PID: 4048)
- DrvInst.exe (PID: 2712)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 1252)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 1028)
- advlauncher.exe (PID: 1712)
Creates files in the driver directory
- DrvInst.exe (PID: 1956)
- DrvInst.exe (PID: 328)
- DrvInst.exe (PID: 2860)
- DrvInst.exe (PID: 4048)
- DrvInst.exe (PID: 3696)
- DrvInst.exe (PID: 2712)
Executed as Windows Service
- vssvc.exe (PID: 2996)
- vds.exe (PID: 1740)
Low-level read access rights to disk partition
- advlauncher.exe (PID: 1712)
- vds.exe (PID: 1740)
INFO
Application launched itself
- chrome.exe (PID: 2556)
- msiexec.exe (PID: 392)
Reads the hosts file
- chrome.exe (PID: 2556)
- chrome.exe (PID: 2372)
- advlauncher.exe (PID: 1712)
Reads Internet Cache Settings
- chrome.exe (PID: 2556)
Dropped object may contain Bitcoin addresses
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 1252)
- msiexec.exe (PID: 392)
Reads settings of System Certificates
- chrome.exe (PID: 2372)
- advlauncher.exe (PID: 1712)
Creates a software uninstall entry
- msiexec.exe (PID: 392)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2996)
Searches for installed software
- DrvInst.exe (PID: 1956)
- DrvInst.exe (PID: 2860)
- DrvInst.exe (PID: 4048)
Creates files in the program directory
- msiexec.exe (PID: 392)
Manual execution by user
- advlauncher.exe (PID: 2196)
- advlauncher.exe (PID: 1712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
97
Monitored processes
52
Malicious processes
14
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | DrvInst.exe "2" "211" "ROOT\PARAGONBLOCKDEVICE\0000" "C:\Windows\INF\oem4.inf" "winfuse_blockmounter.inf:Paragon.NTx86:blockmounter:24.17.0.0:wudf\paragonblockdev" "67370f437" "000002F0" "000005DC" "000005E0" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3207724735020144132,8011526629135158438,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3570252270298855004 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 392 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3207724735020144132,8011526629135158438,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18262292478170222673 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4308 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 720 | "C:\Windows\system32\WUDFHost.exe" -HostGUID:{193a1820-d9ac-4997-8c55-be817523f6aa} -IoEventPortName:HostProcess-7cb70948-8181-4af5-b1ca-1a2ae7fe0cf9 -SystemEventPortName:HostProcess-5ac93cc0-812b-4c90-8ccf-87d10255c181 -IoCancelEventPortName:HostProcess-af4f0057-a5f4-4bae-9641-83ce0b8a3f8c -NonStateChangingEventPortName:HostProcess-83e86c08-8383-44b4-b0a1-5df18cfe1f2e -ServiceSID:S-1-5-80-2652678385-582572993-1835434367-1344795993-749280709 -LifetimeId:e981bab5-c7cd-4dbe-98fd-3b9f58378483 | C:\Windows\system32\WUDFHost.exe | — | svchost.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Driver Foundation - User-mode Driver Framework Host Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3207724735020144132,8011526629135158438,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16041088835199823217 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Users\admin\Downloads\Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe" | C:\Users\admin\Downloads\Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe | chrome.exe | ||||||||||||
User: admin Company: Paragon Software GmbH Integrity Level: HIGH Description: A Part Paragon Software Utility Exit code: 0 Version: 10.12.0.3337 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,3207724735020144132,8011526629135158438,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16034437985504667007 --mojo-platform-channel-handle=2896 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Windows\Temp\{CE5781BE-AC74-4250-AD22-F43CFB0B948F}\.cr\Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe" -burn.clean.room="C:\Users\admin\Downloads\Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Windows\Temp\{CE5781BE-AC74-4250-AD22-F43CFB0B948F}\.cr\Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe | Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe | ||||||||||||
User: admin Company: Paragon Software GmbH Integrity Level: HIGH Description: A Part Paragon Software Utility Exit code: 0 Version: 10.12.0.3337 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,3207724735020144132,8011526629135158438,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18240073623543946342 --mojo-platform-channel-handle=4024 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 876
Read events
2 113
Write events
1 732
Delete events
31
Modification events
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2556-13221789950214250 |
Value: 259 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2556-13221789950214250 |
Value: 259 | |||
Executable files
187
Suspicious files
95
Text files
980
Unknown types
146
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a93b.TMP | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cf12ae3c-9fe6-48b1-8a05-752fb23efbba.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a969.TMP | text | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
21
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2372 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
2372 | chrome.exe | GET | 200 | 172.217.130.199:80 | http://r2---sn-hgn7rn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.183.105.219&mm=28&mn=sn-hgn7rn7k&ms=nvh&mt=1577316314&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
392 | msiexec.exe | GET | 200 | 92.122.213.217:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.4 Kb | whitelisted |
2372 | chrome.exe | GET | 200 | 74.125.11.138:80 | http://r5---sn-hgn7yn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.183.105.219&mm=28&mn=sn-hgn7yn7e&ms=nvh&mt=1577316314&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2372 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 511 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2372 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 216.58.210.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 216.58.206.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 172.217.130.199:80 | r2---sn-hgn7rn7k.gvt1.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 172.217.16.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 74.125.11.138:80 | r5---sn-hgn7yn7e.gvt1.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
dl.paragon-software.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-hgn7rn7k.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
r5---sn-hgn7yn7e.gvt1.com |
| whitelisted |
Threats
Process | Message |
|---|---|
DrvInst.exe | WudfUpdate: installing version (1,9,0,7600).
|
DrvInst.exe | WudfUpdate: Checking for presence of previous UMDF installation.
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfplatform.dll version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\drivers\wudfrd.sys version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfhost.exe version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\drivers\wudfpf.sys version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Loading configuration coinstaller from C:\Windows\system32\wudfcoinstaller.dll.
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfx.dll version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfcoinstaller.dll version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: UMDF installation is newer than update.
|