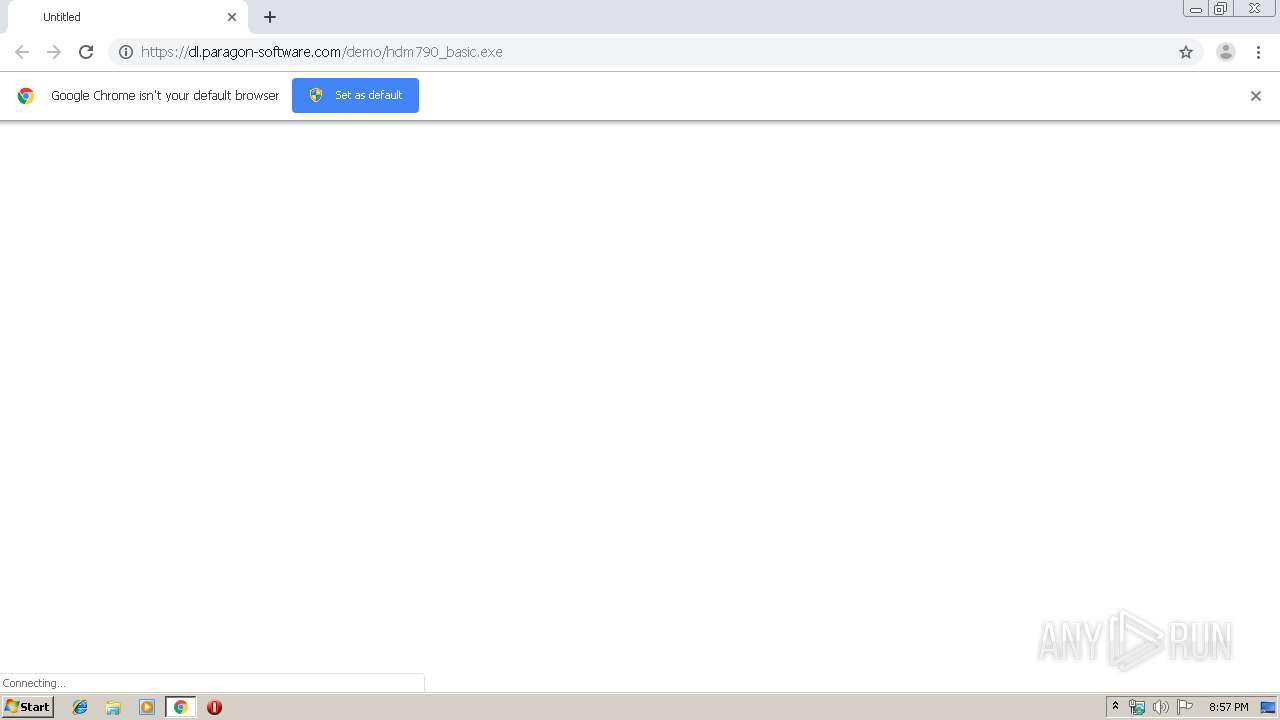
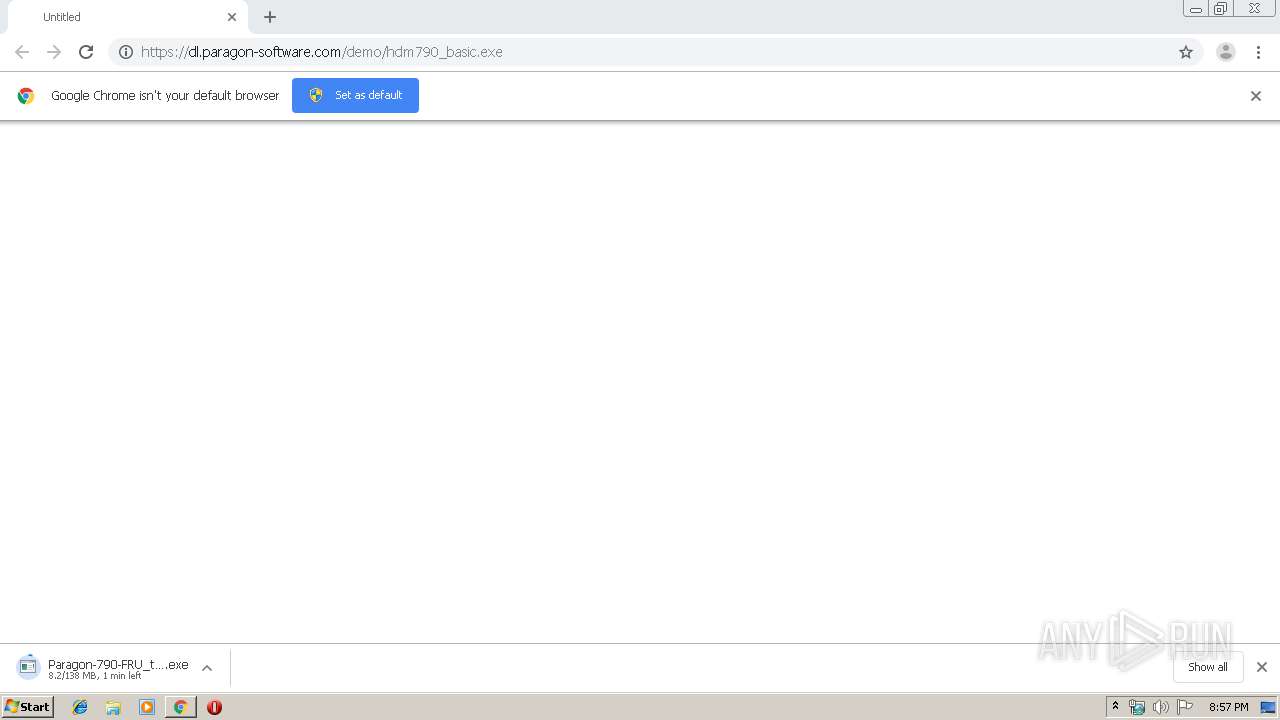
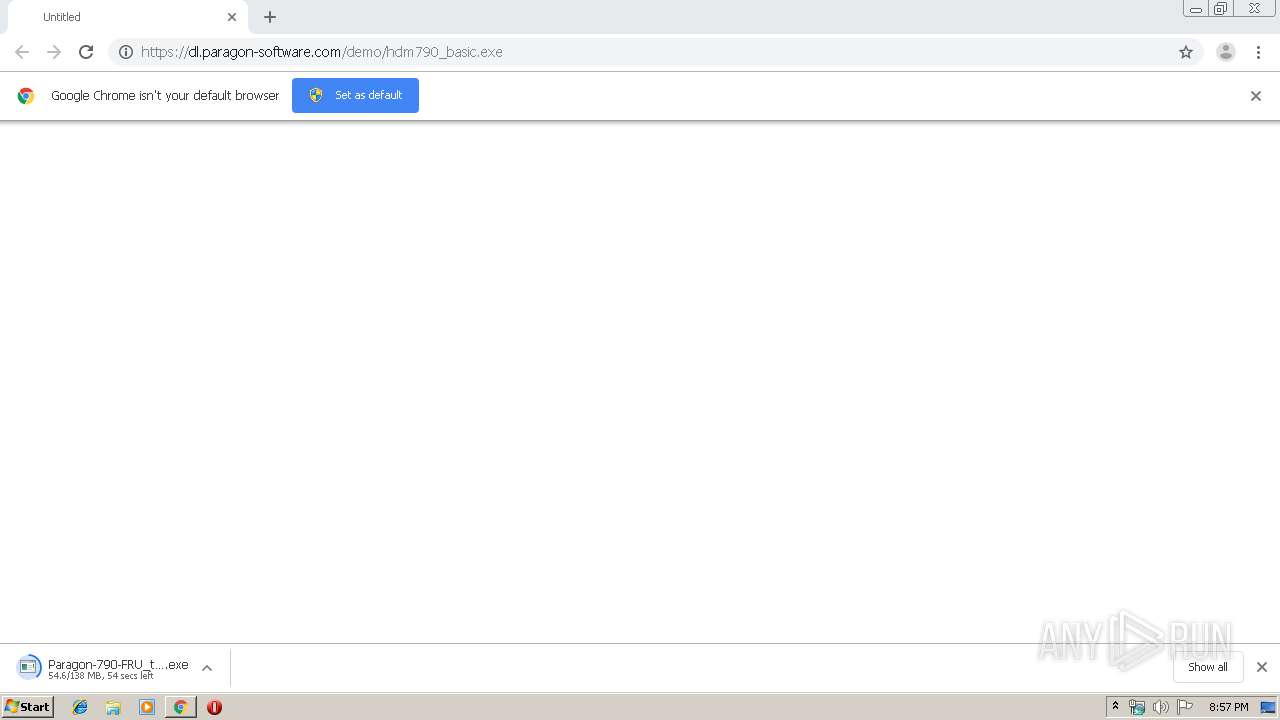
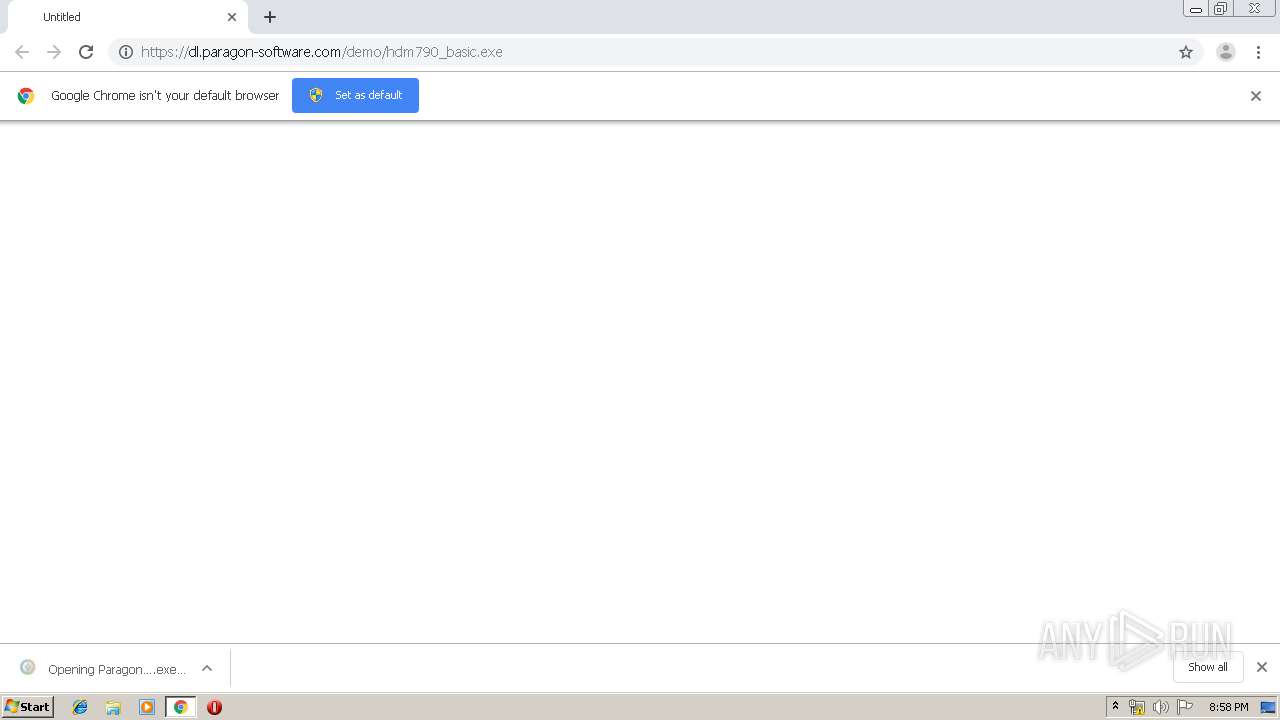
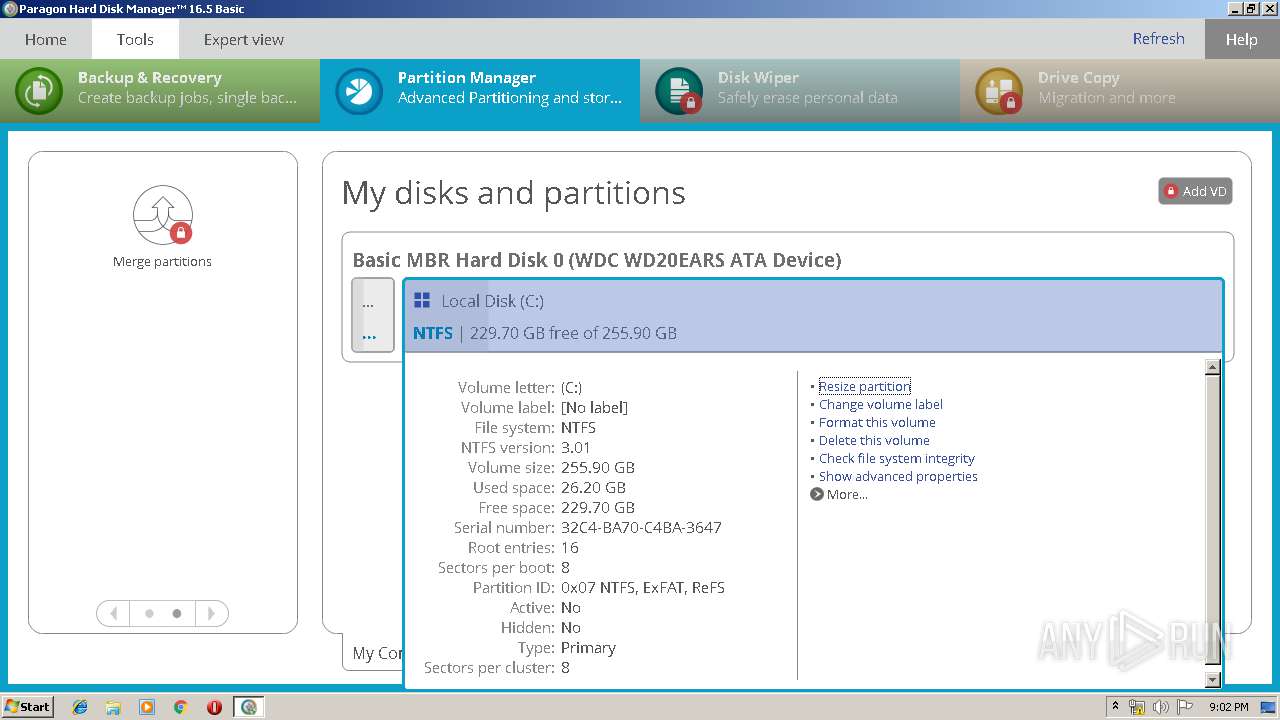
| URL: | https://dl.paragon-software.com/demo/hdm790_basic.exe |
| Full analysis: | https://app.any.run/tasks/7115380b-35c0-4a80-b0b7-3280569297c1 |
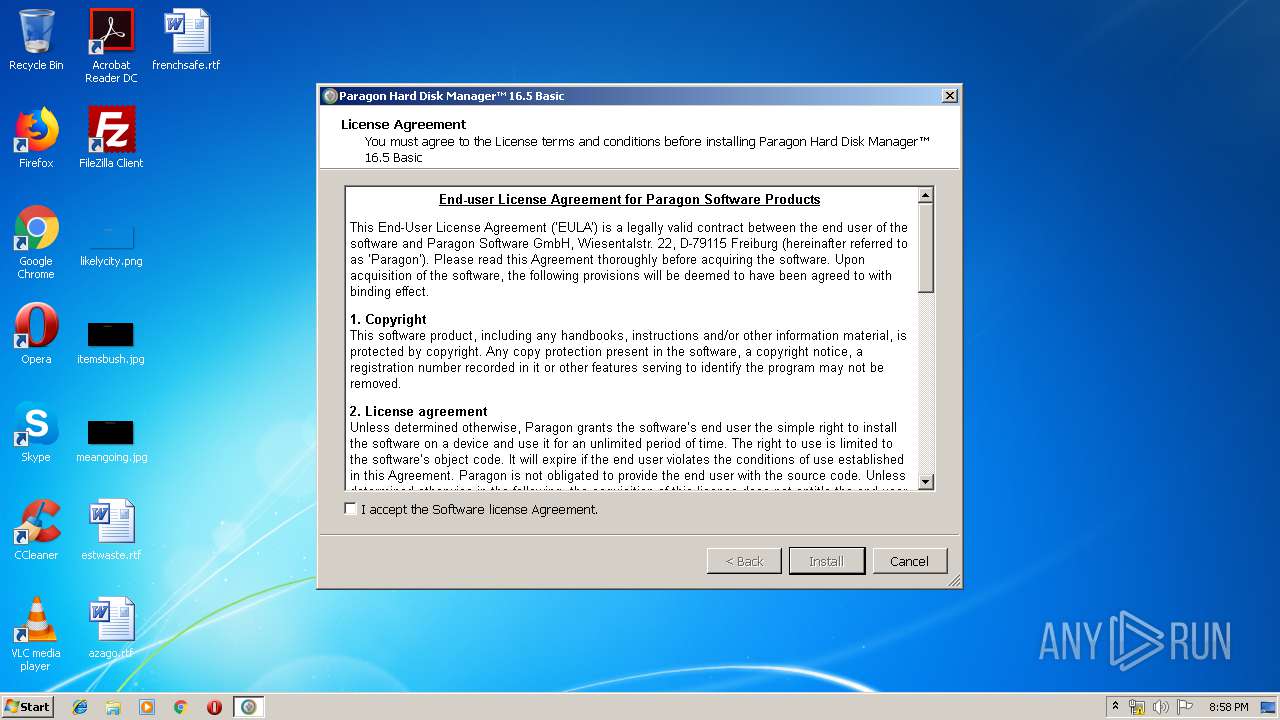
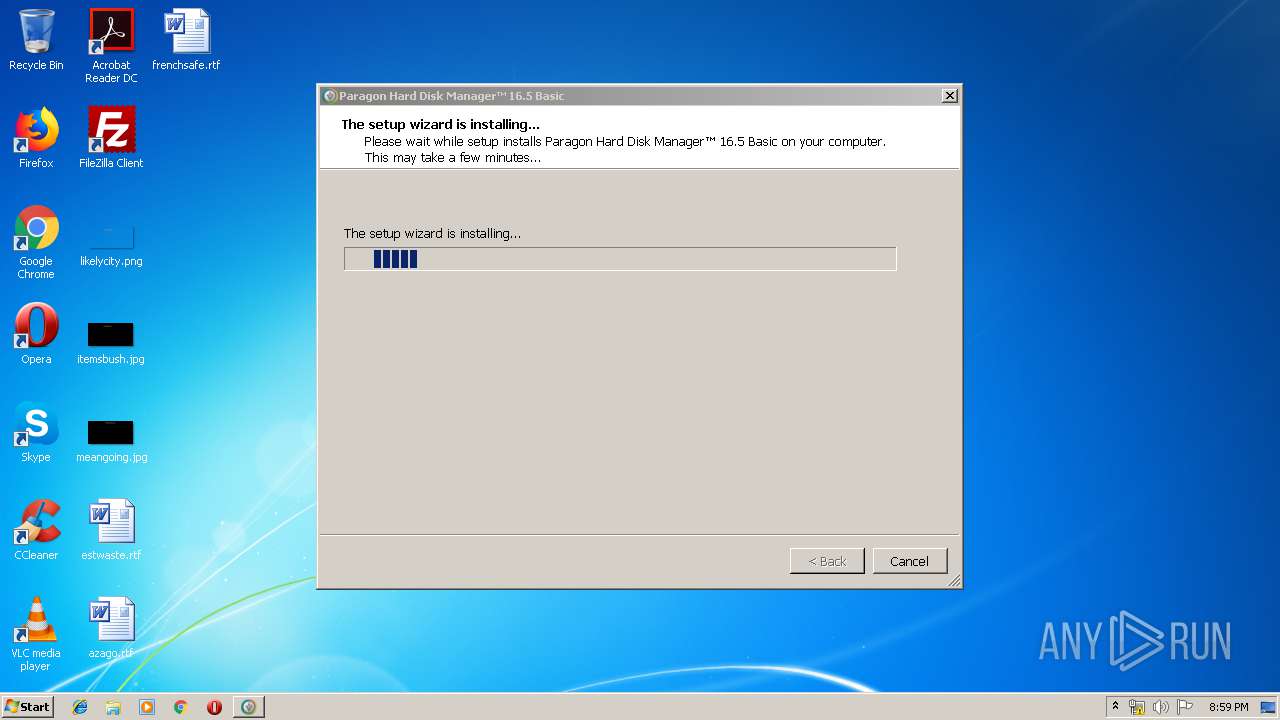
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2019, 19:57:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0148C27D3DC5345082477F8DBE3EC2FD |
| SHA1: | 505698A649CBF7F16246D5754A082561F1102B34 |
| SHA256: | 7599D71F43F1BC97093D8BD5A814BEFBA96293F595161D41166FEDECCFFB8210 |
| SSDEEP: | 3:N8RSXeHFxAIK3VsEbA:2+v33ScA |
MALICIOUS
Application was dropped or rewritten from another process
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 3264)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 2336)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 3048)
- hdm16basic_x86.exe (PID: 2628)
- winfuse_uimsetup.exe (PID: 3744)
- advlauncher.exe (PID: 2996)
- advlauncher.exe (PID: 2636)
- QtWebEngineProcess.exe (PID: 3684)
- QtWebEngineProcess.exe (PID: 3764)
- QtWebEngineProcess.exe (PID: 2740)
Loads dropped or rewritten executable
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 3048)
- winfuse_uimsetup.exe (PID: 3744)
- DrvInst.exe (PID: 3392)
- WUDFHost.exe (PID: 2416)
- advlauncher.exe (PID: 2636)
- QtWebEngineProcess.exe (PID: 3684)
- QtWebEngineProcess.exe (PID: 3764)
- QtWebEngineProcess.exe (PID: 2740)
Changes the autorun value in the registry
- hdm16basic_x86.exe (PID: 2628)
Changes settings of System certificates
- MsiExec.exe (PID: 3124)
- winfuse_uimsetup.exe (PID: 3744)
Loads the Task Scheduler COM API
- advlauncher.exe (PID: 2636)
SUSPICIOUS
Executable content was dropped or overwritten
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 2336)
- hdm16basic_x86.exe (PID: 2628)
- chrome.exe (PID: 3556)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 3048)
- DrvInst.exe (PID: 2836)
- msiexec.exe (PID: 3164)
- winfuse_uimsetup.exe (PID: 3744)
- DrvInst.exe (PID: 3392)
- DrvInst.exe (PID: 888)
- DrvInst.exe (PID: 3196)
- DrvInst.exe (PID: 2644)
- DrvInst.exe (PID: 3484)
Creates files in the Windows directory
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 3048)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 2336)
- msiexec.exe (PID: 3164)
- DrvInst.exe (PID: 2836)
- winfuse_uimsetup.exe (PID: 3744)
- DrvInst.exe (PID: 3392)
- WUDFHost.exe (PID: 2416)
- DrvInst.exe (PID: 888)
- DrvInst.exe (PID: 3196)
- DrvInst.exe (PID: 2644)
- DrvInst.exe (PID: 3484)
- advlauncher.exe (PID: 2636)
Creates files in the program directory
- hdm16basic_x86.exe (PID: 2628)
- advlauncher.exe (PID: 2636)
Starts itself from another location
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 3048)
Creates a software uninstall entry
- hdm16basic_x86.exe (PID: 2628)
Adds / modifies Windows certificates
- MsiExec.exe (PID: 3124)
- winfuse_uimsetup.exe (PID: 3744)
Creates files in the driver directory
- DrvInst.exe (PID: 2836)
- DrvInst.exe (PID: 888)
- DrvInst.exe (PID: 3392)
- DrvInst.exe (PID: 3196)
- DrvInst.exe (PID: 2644)
- DrvInst.exe (PID: 3484)
Removes files from Windows directory
- DrvInst.exe (PID: 2836)
- DrvInst.exe (PID: 3392)
- DrvInst.exe (PID: 888)
- DrvInst.exe (PID: 3196)
- DrvInst.exe (PID: 2644)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 3048)
- DrvInst.exe (PID: 3484)
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 2336)
- advlauncher.exe (PID: 2636)
Executed via COM
- DrvInst.exe (PID: 3392)
- DrvInst.exe (PID: 2956)
- DrvInst.exe (PID: 888)
- DrvInst.exe (PID: 1188)
- DrvInst.exe (PID: 3196)
- DrvInst.exe (PID: 2644)
- DrvInst.exe (PID: 3484)
- DrvInst.exe (PID: 1860)
- DrvInst.exe (PID: 2836)
- vdsldr.exe (PID: 2428)
Low-level read access rights to disk partition
- advlauncher.exe (PID: 2636)
- vds.exe (PID: 2648)
Executed as Windows Service
- vds.exe (PID: 2648)
- vssvc.exe (PID: 3584)
Changes IE settings (feature browser emulation)
- msiexec.exe (PID: 3164)
INFO
Reads the hosts file
- chrome.exe (PID: 2920)
- chrome.exe (PID: 3556)
- advlauncher.exe (PID: 2636)
Dropped object may contain Bitcoin addresses
- Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe (PID: 3048)
- msiexec.exe (PID: 3164)
Reads Internet Cache Settings
- chrome.exe (PID: 3556)
Application launched itself
- chrome.exe (PID: 3556)
- msiexec.exe (PID: 3164)
Creates a software uninstall entry
- msiexec.exe (PID: 3164)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3584)
Creates files in the program directory
- msiexec.exe (PID: 3164)
Searches for installed software
- DrvInst.exe (PID: 888)
- DrvInst.exe (PID: 2644)
- DrvInst.exe (PID: 2836)
Manual execution by user
- advlauncher.exe (PID: 2636)
- advlauncher.exe (PID: 2996)
Reads settings of System Certificates
- advlauncher.exe (PID: 2636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
39
Malicious processes
16
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{0f5bcafd-82ce-2da0-366e-2b0af7b98b6b}\uimbus.inf" "0" "648d7e42b" "000005C4" "WinSta0\Default" "000004D8" "208" "c:\program files\paragon software\universal image mounter" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1188 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot23" "" "" "631c88d3b" "00000000" "000003C8" "000005EC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1860 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot24" "" "" "6cdcd25f3" "00000000" "0000060C" "000005EC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fe6a9d0,0x6fe6a9e0,0x6fe6a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1541630968800692453 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2336 | "C:\Users\admin\Downloads\Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe" | C:\Users\admin\Downloads\Paragon-790-FRU_trial_WinInstall_16.23.0_000.exe | chrome.exe | ||||||||||||
User: admin Company: Paragon Software GmbH Integrity Level: HIGH Description: A Part Paragon Software Utility Exit code: 0 Version: 10.12.0.3337 Modules
| |||||||||||||||
| 2416 | "C:\Windows\system32\WUDFHost.exe" -HostGUID:{193a1820-d9ac-4997-8c55-be817523f6aa} -IoEventPortName:HostProcess-d4b0a906-008e-4f8e-90d6-0954af2806cc -SystemEventPortName:HostProcess-ee439018-50af-4277-9fdf-c1f760fd5cdc -IoCancelEventPortName:HostProcess-eb78884c-78b9-4295-a613-3d17c8c07338 -NonStateChangingEventPortName:HostProcess-bb1b4706-b6b1-4e8f-81f7-07100c264165 -ServiceSID:S-1-5-80-2652678385-582572993-1835434367-1344795993-749280709 -LifetimeId:ea40b5f2-efc6-4f33-b47f-fadc4d4316d4 | C:\Windows\system32\WUDFHost.exe | — | svchost.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Driver Foundation - User-mode Driver Framework Host Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2428 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4433066904441282798 --mojo-platform-channel-handle=3508 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11636698304020267501 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 542
Read events
1 798
Write events
1 715
Delete events
29
Modification events
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3556-13213051045467500 |
Value: 259 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
188
Suspicious files
94
Text files
879
Unknown types
139
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f0f0b9da-749f-4d28-8333-5934aa0a3f88.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169ca2.TMP | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF169cd1.TMP | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169c64.TMP | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF169d1f.TMP | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
17
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3164 | msiexec.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2920 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
3164 | msiexec.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
2920 | chrome.exe | 13.35.253.93:443 | dl.paragon-software.com | — | US | suspicious |
2636 | advlauncher.exe | 62.159.194.50:443 | my.paragon-software.com | Deutsche Telekom AG | DE | unknown |
2920 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2920 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2920 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2920 | chrome.exe | 13.35.253.35:443 | dl.paragon-software.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.paragon-software.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
my.paragon-software.com |
| unknown |
a.root-servers.net |
| unknown |
Threats
Process | Message |
|---|---|
DrvInst.exe | WudfUpdate: installing version (1,9,0,7600).
|
DrvInst.exe | WudfUpdate: Checking for presence of previous UMDF installation.
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\drivers\wudfrd.sys version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\drivers\wudfpf.sys version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfhost.exe version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfsvc.dll version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfx.dll version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfplatform.dll version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: Found binary %WINDIR%\system32\wudfcoinstaller.dll version (1.9.0.7601)
|
DrvInst.exe | WudfUpdate: UMDF installation is newer than update.
|