| File name: | 27hb7t8u |
| Full analysis: | https://app.any.run/tasks/a755f29d-eaa2-4fd6-88ec-5e02399d8777 |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2024, 00:05:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
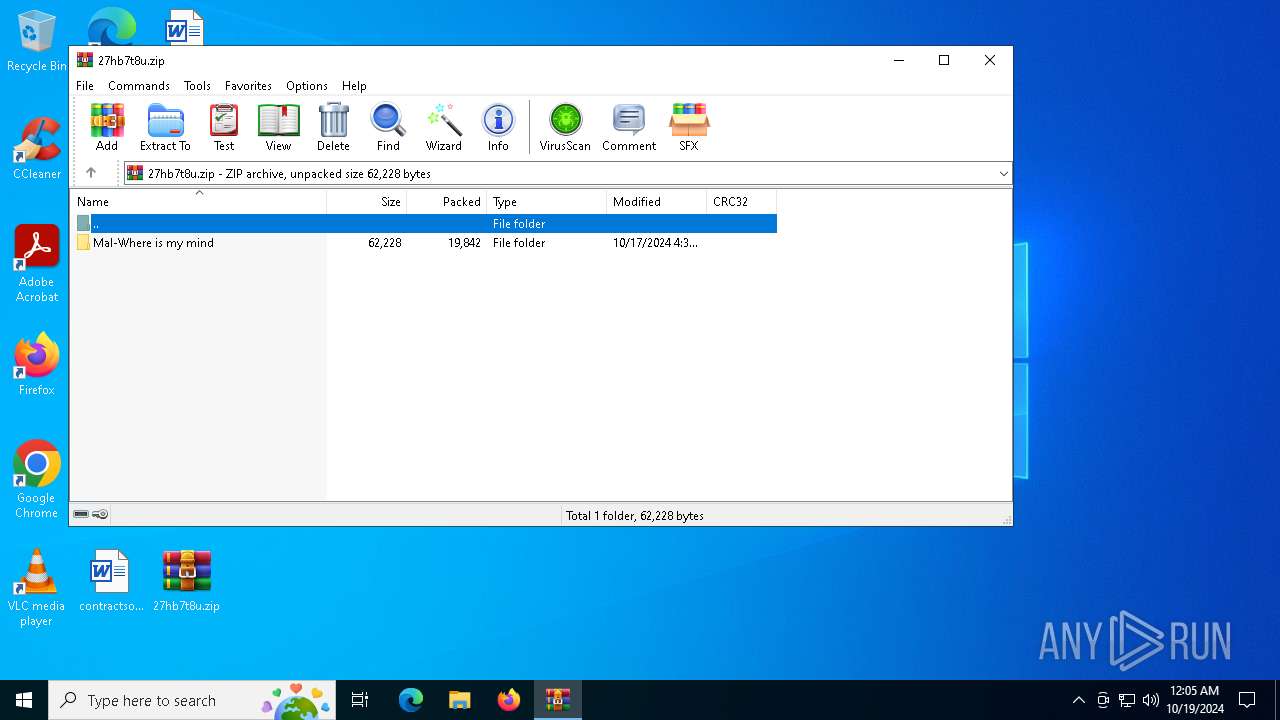
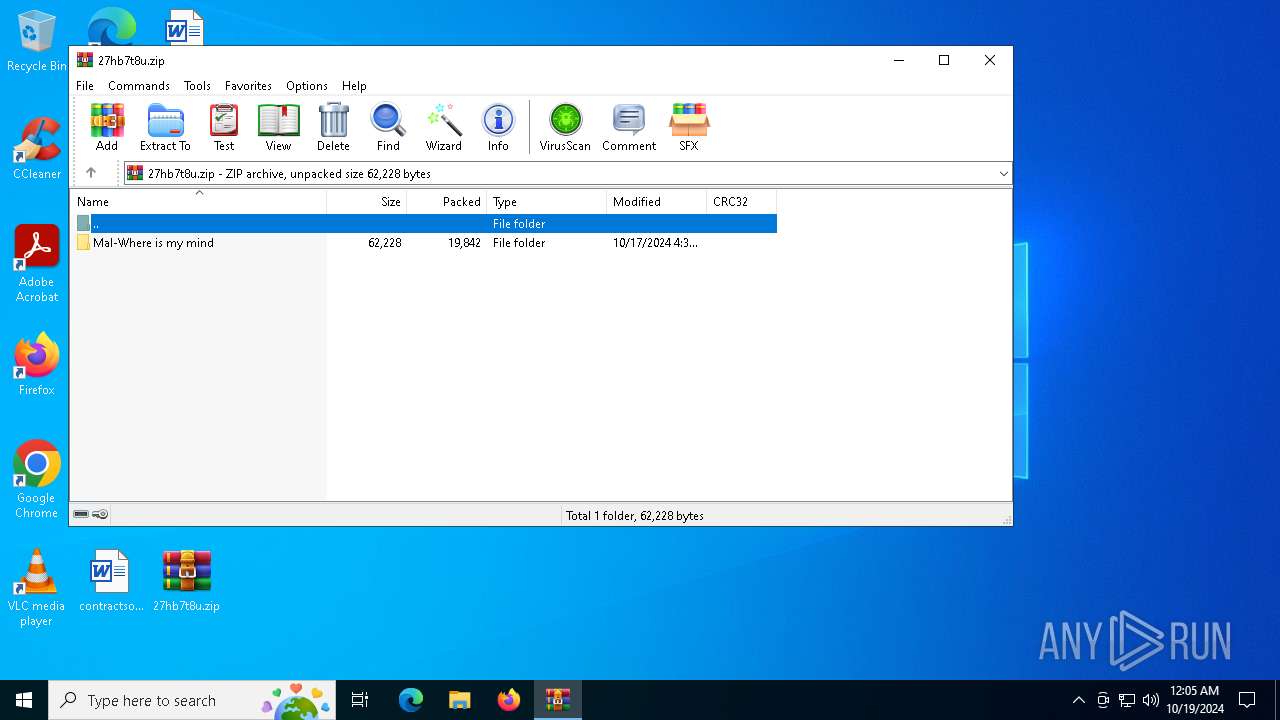
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 0FEF698C81AABBD10A2B54DFB489D6A8 |
| SHA1: | 453C474856EE2AC50E184A8FEBA5526C7736116F |
| SHA256: | 75906C5A82590DE8102514FF757FE6C2B5B161614964F222EE0AE098AC6979CF |
| SSDEEP: | 384:C0wbcF+YyXs0tDKoFLxbhHDHEpxrXCL5KMicO5d2+tmRdXjL7p635x7JxW:C0+cFhyXs6txbh8TCLNicO5wP835xts |
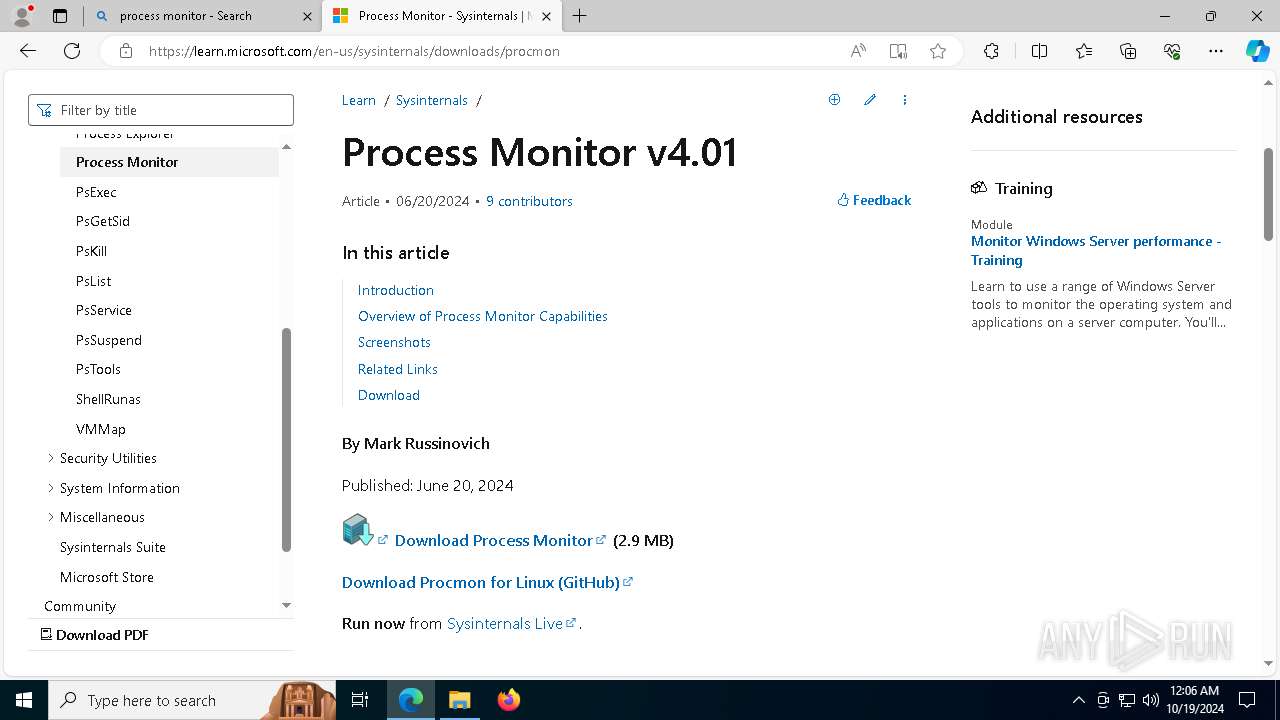
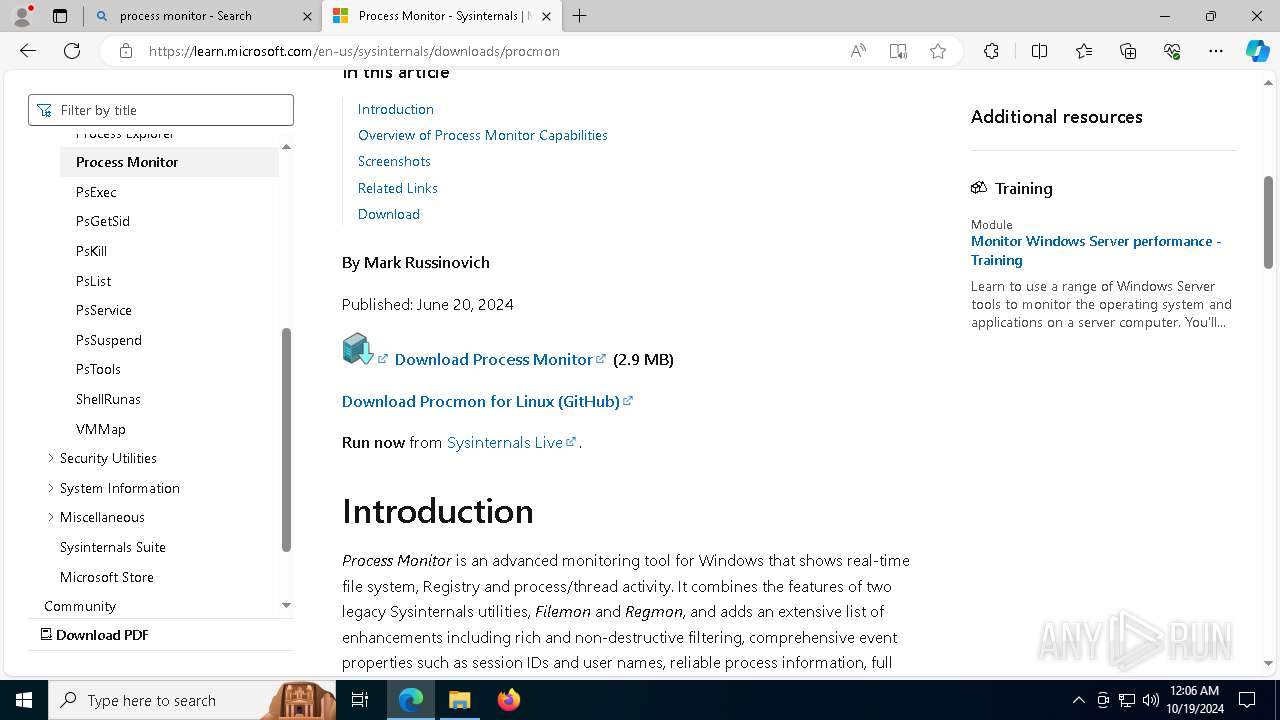
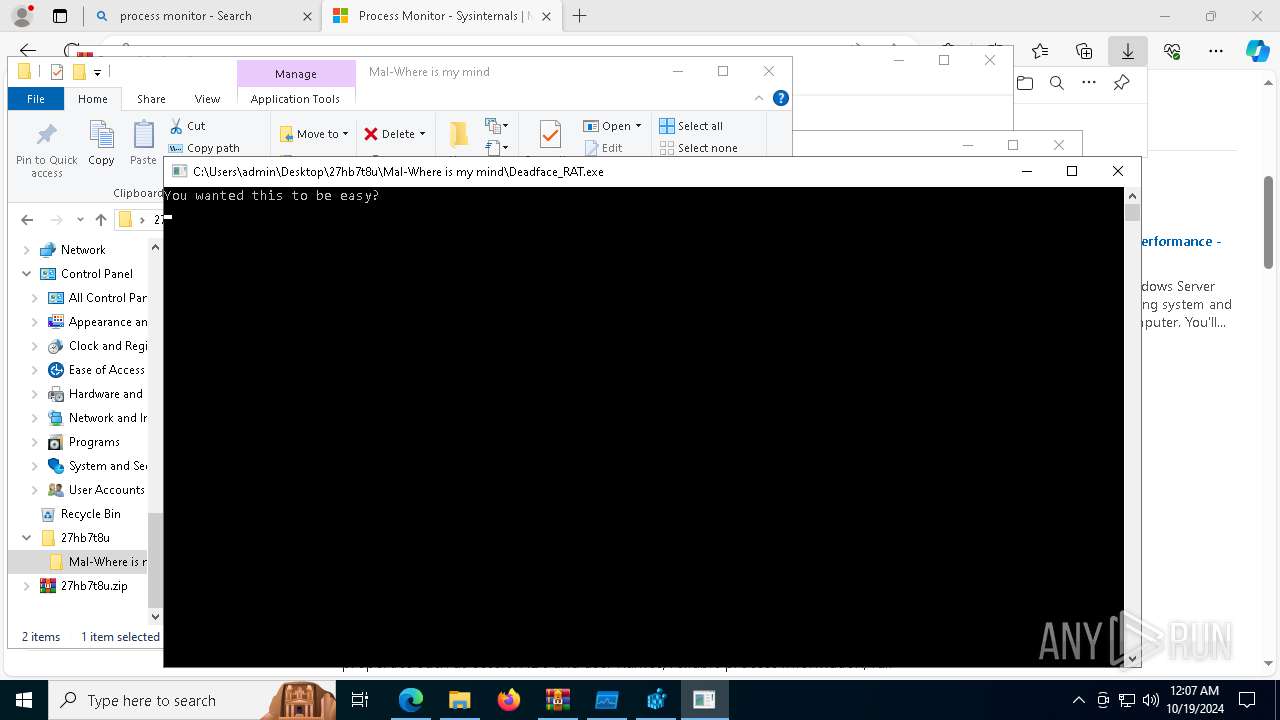
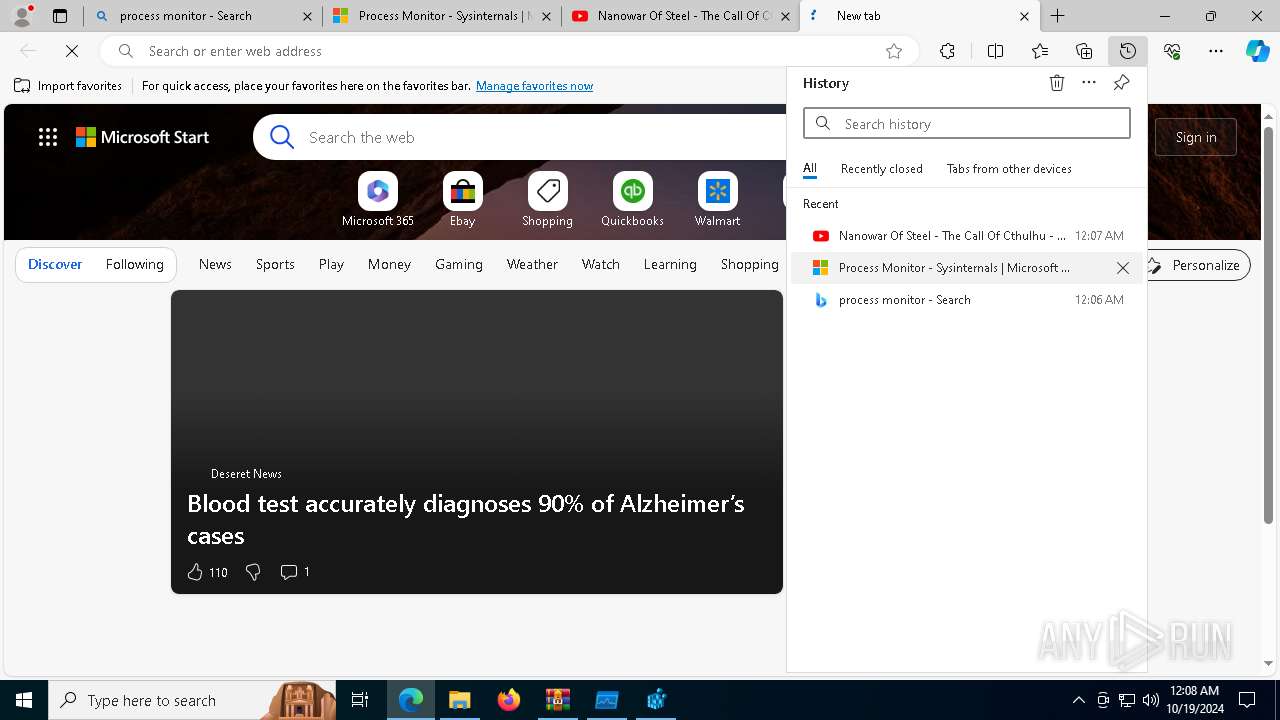
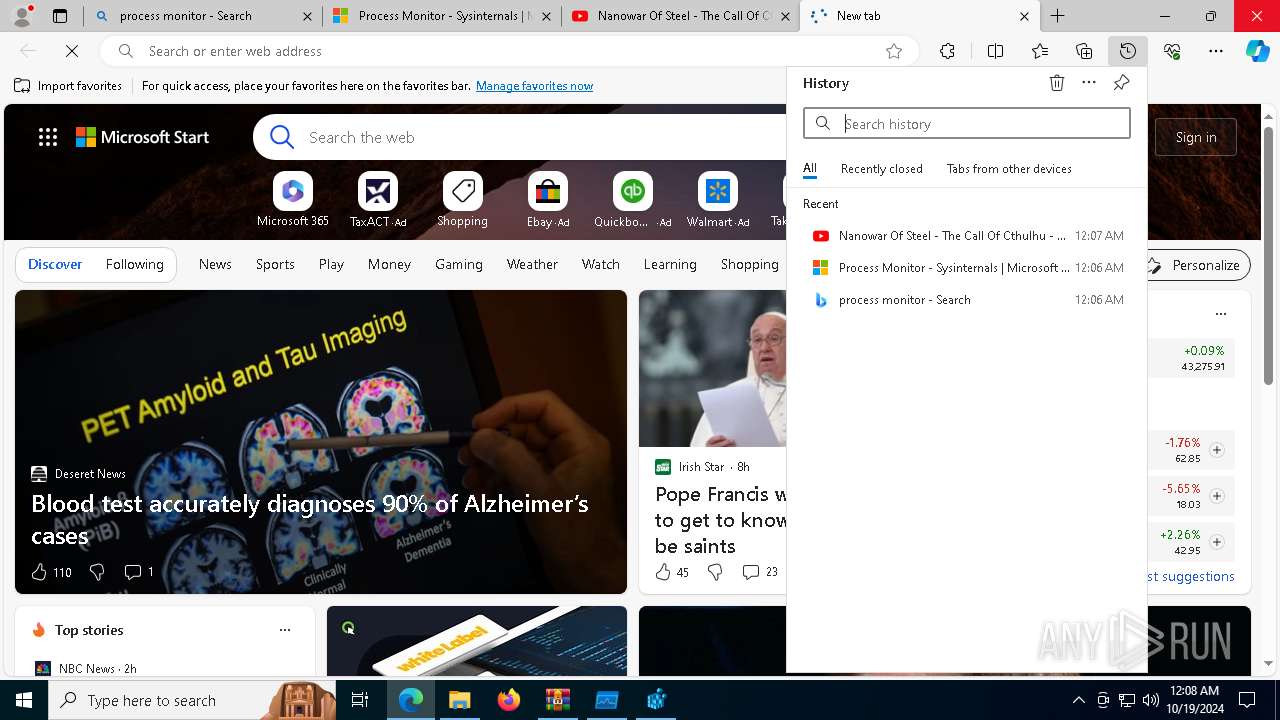
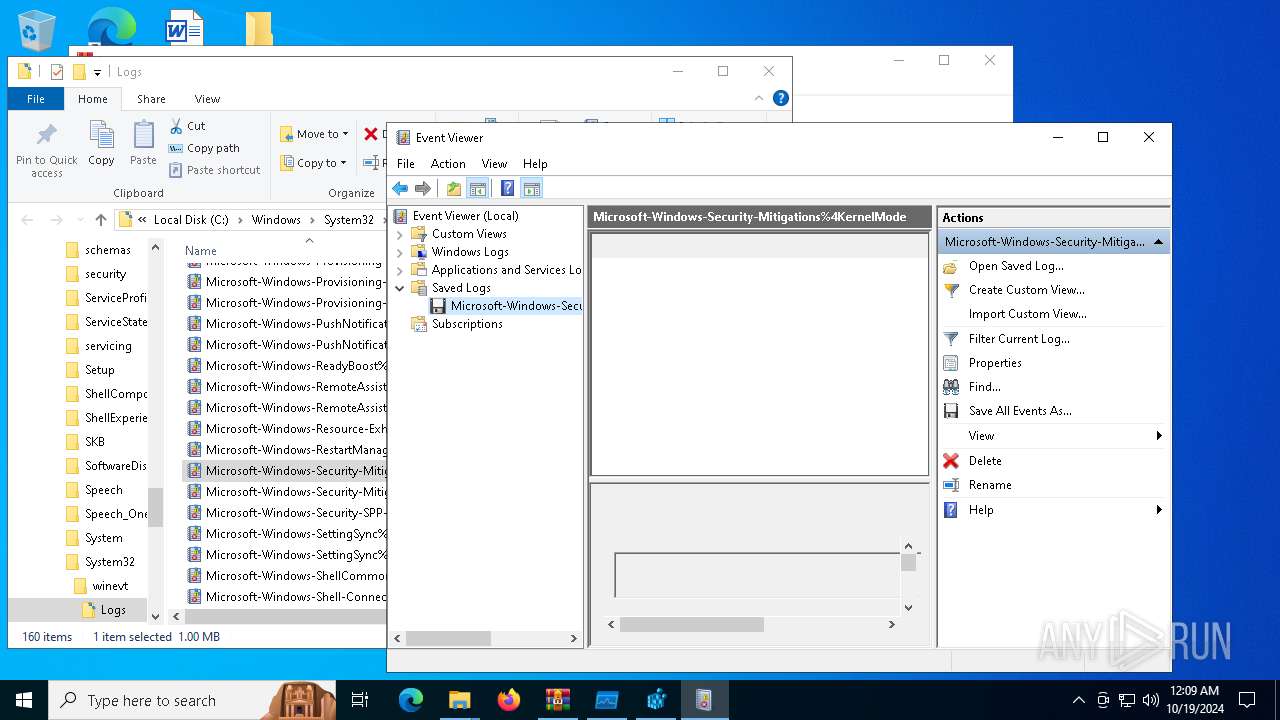
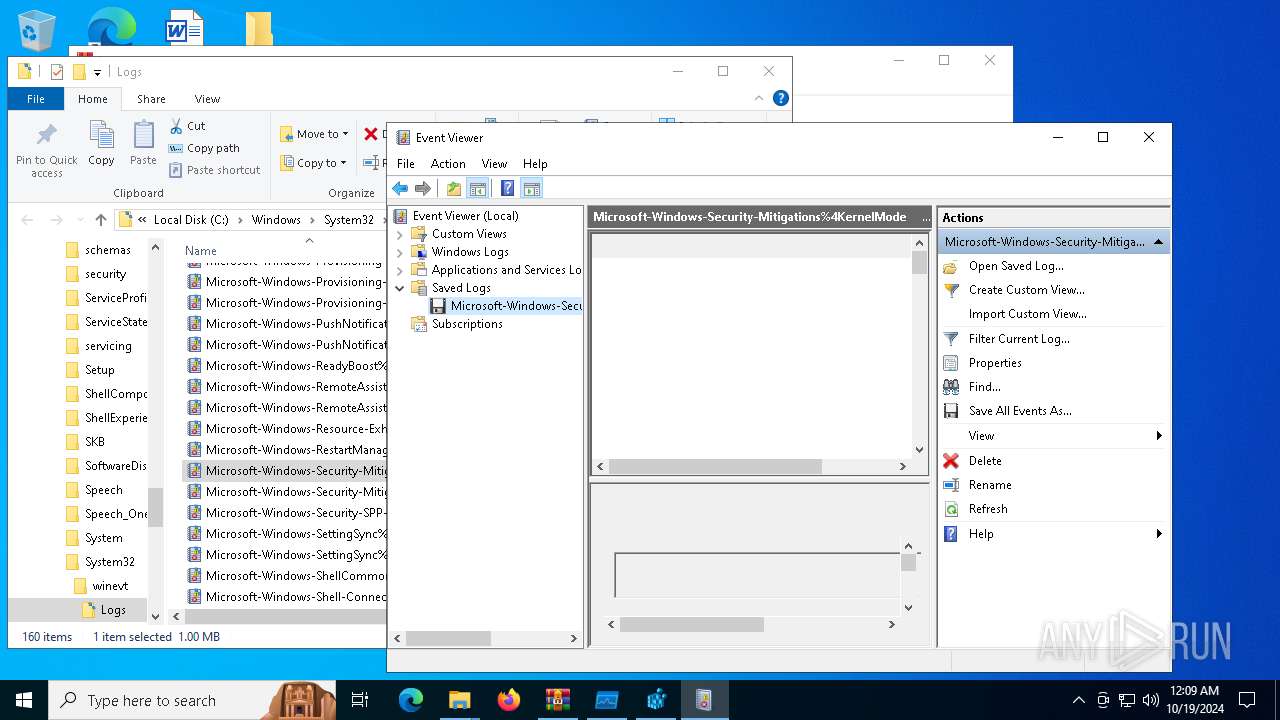
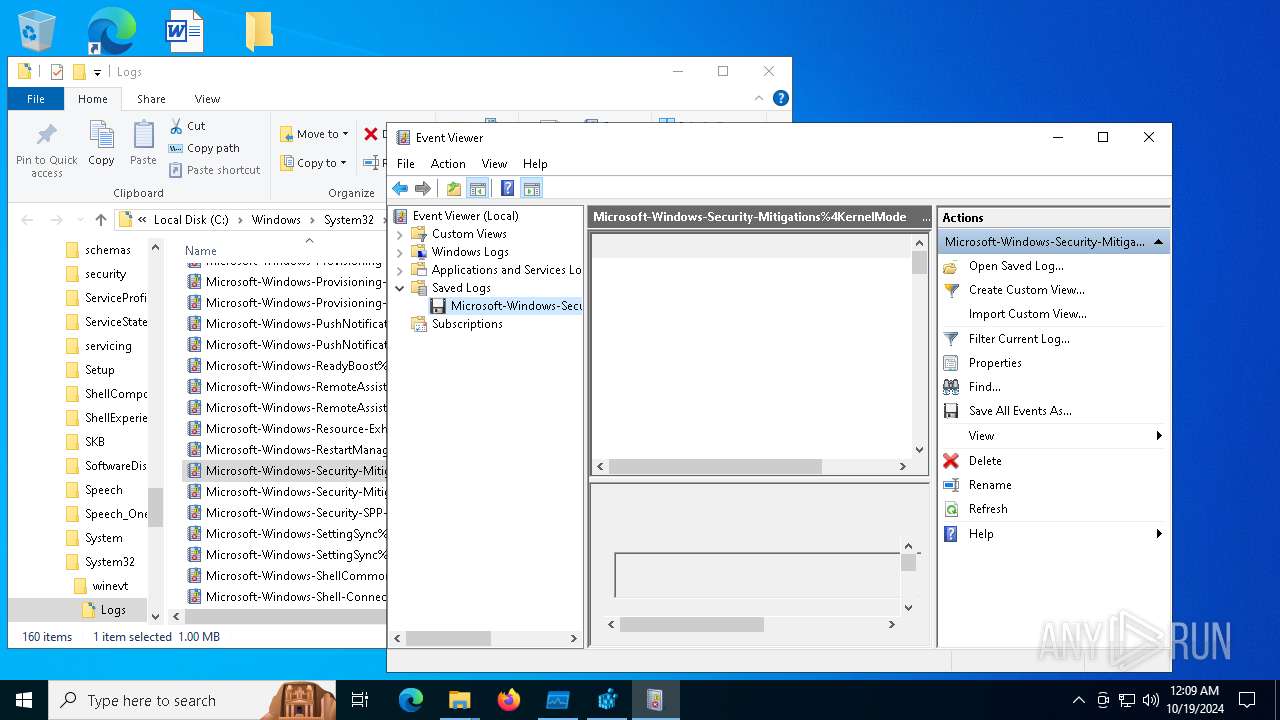
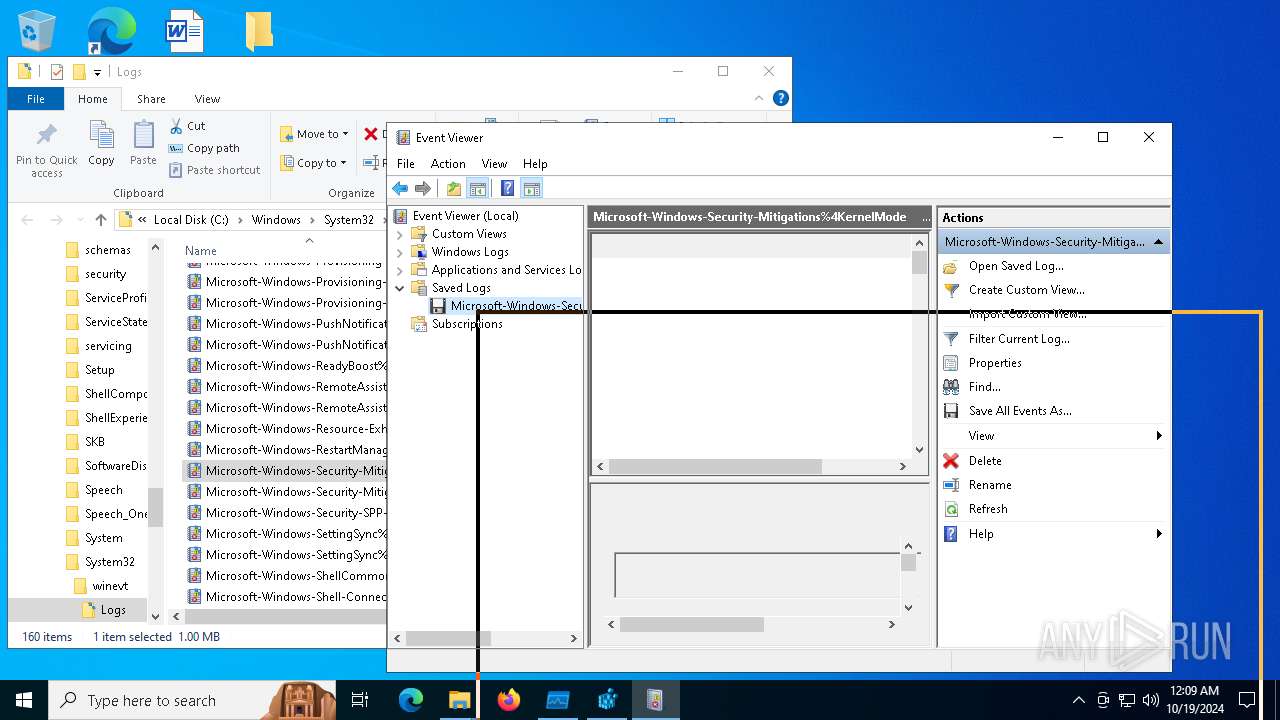
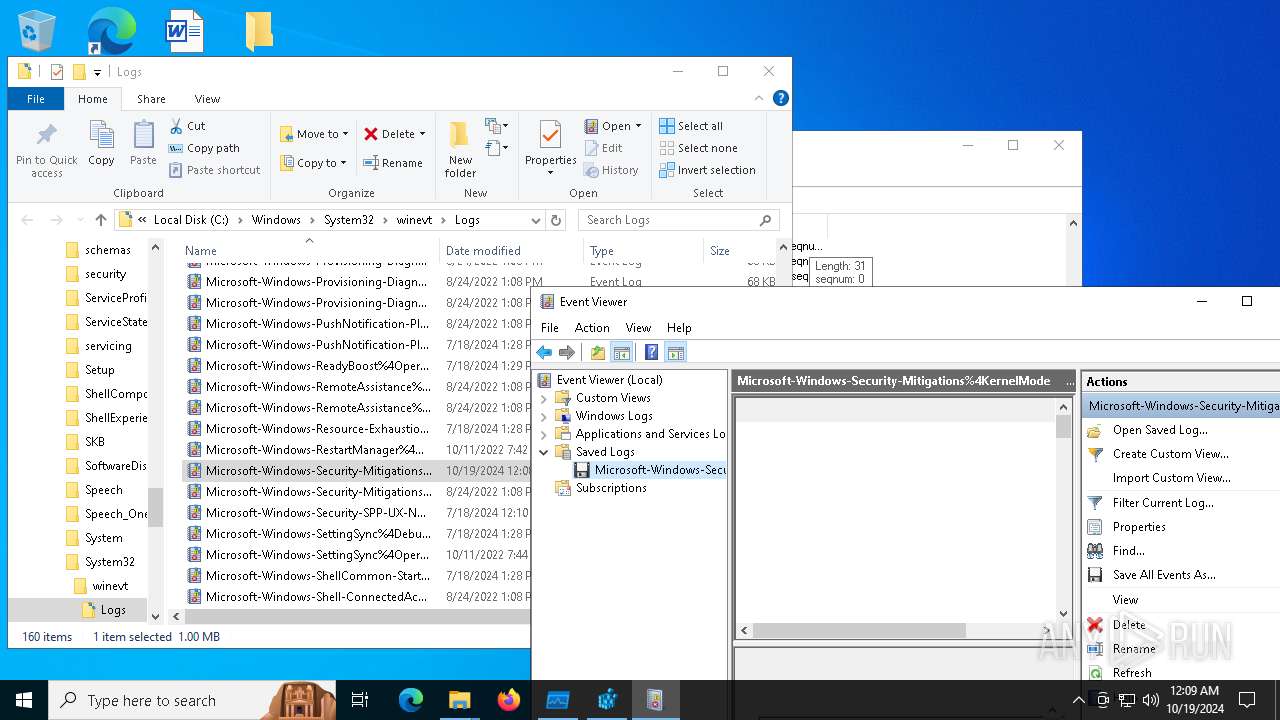
MALICIOUS
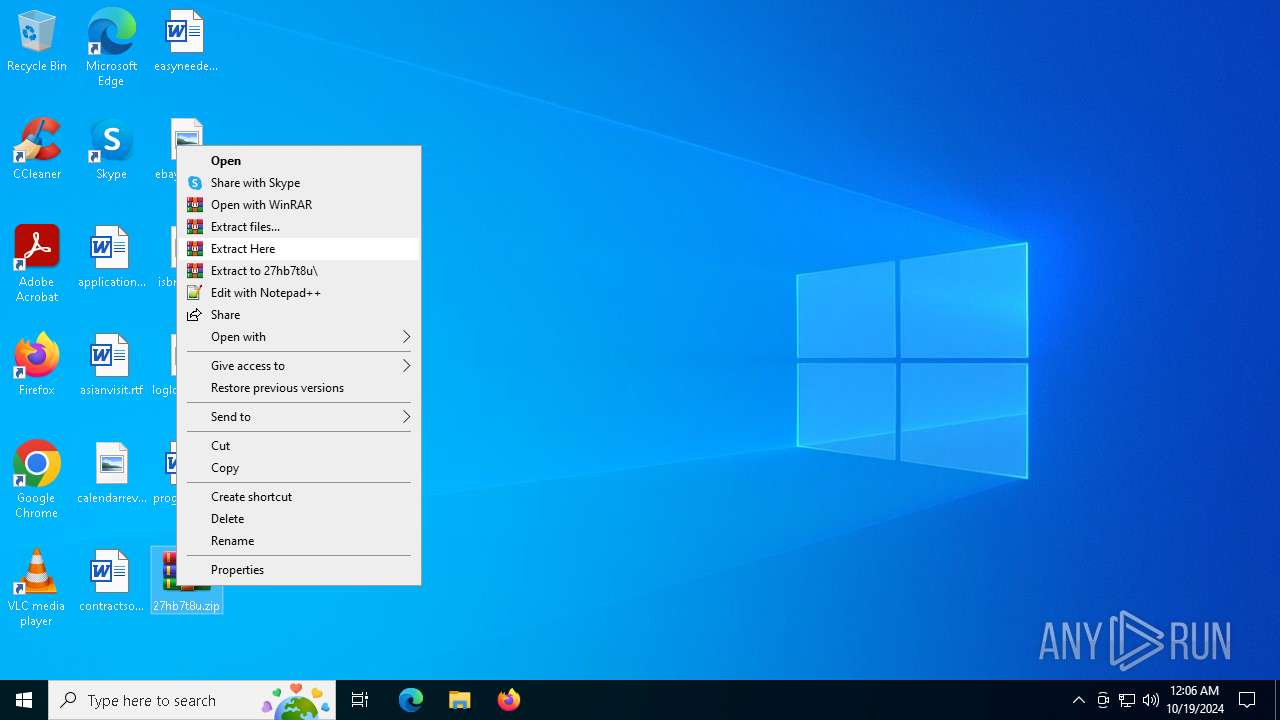
Generic archive extractor
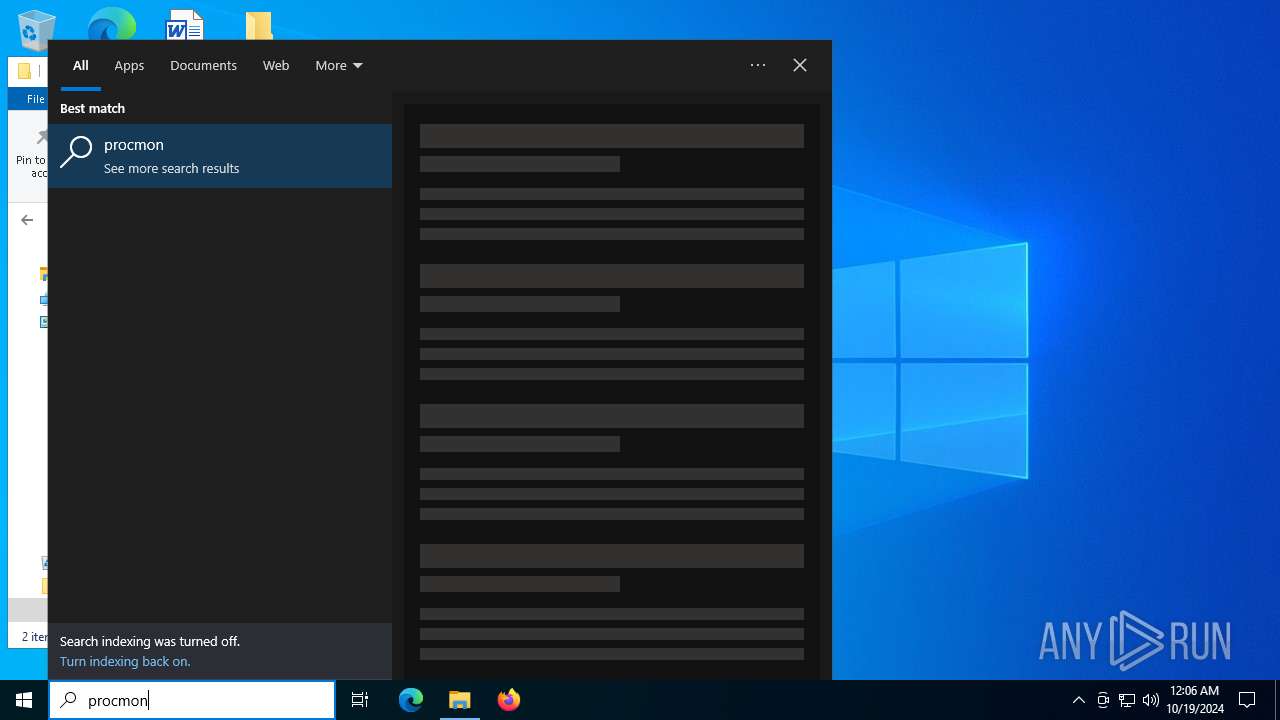
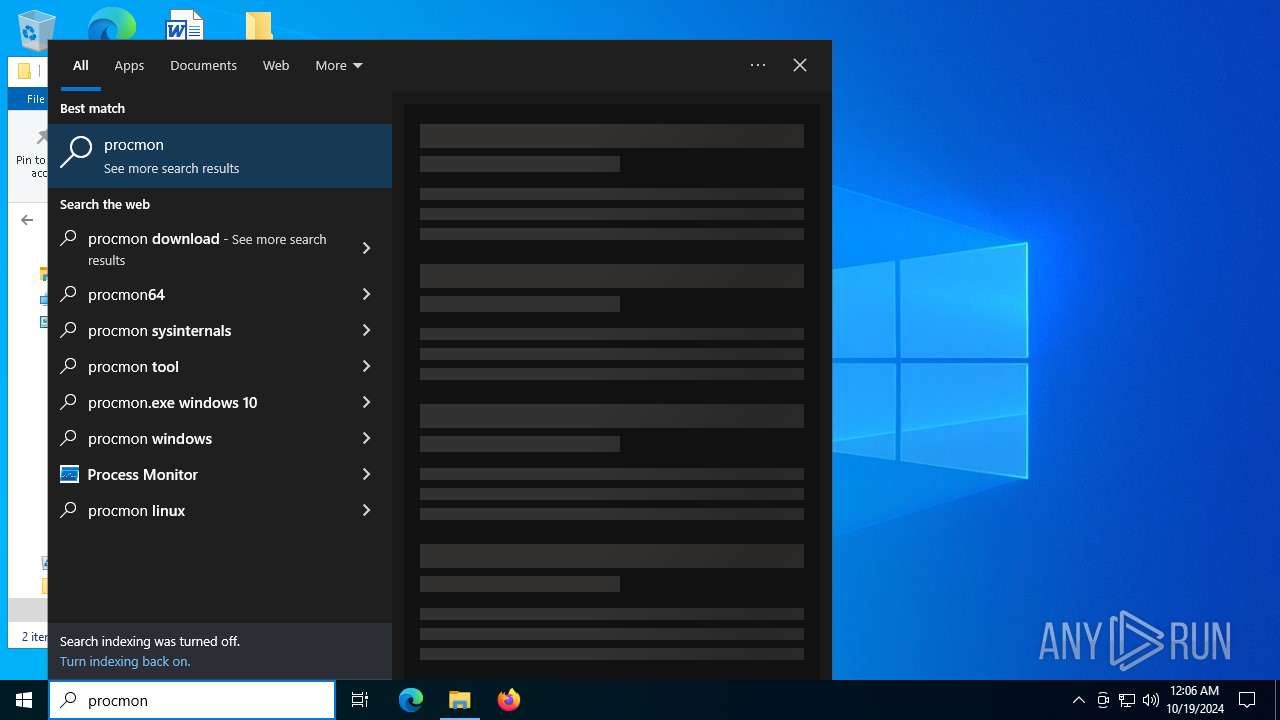
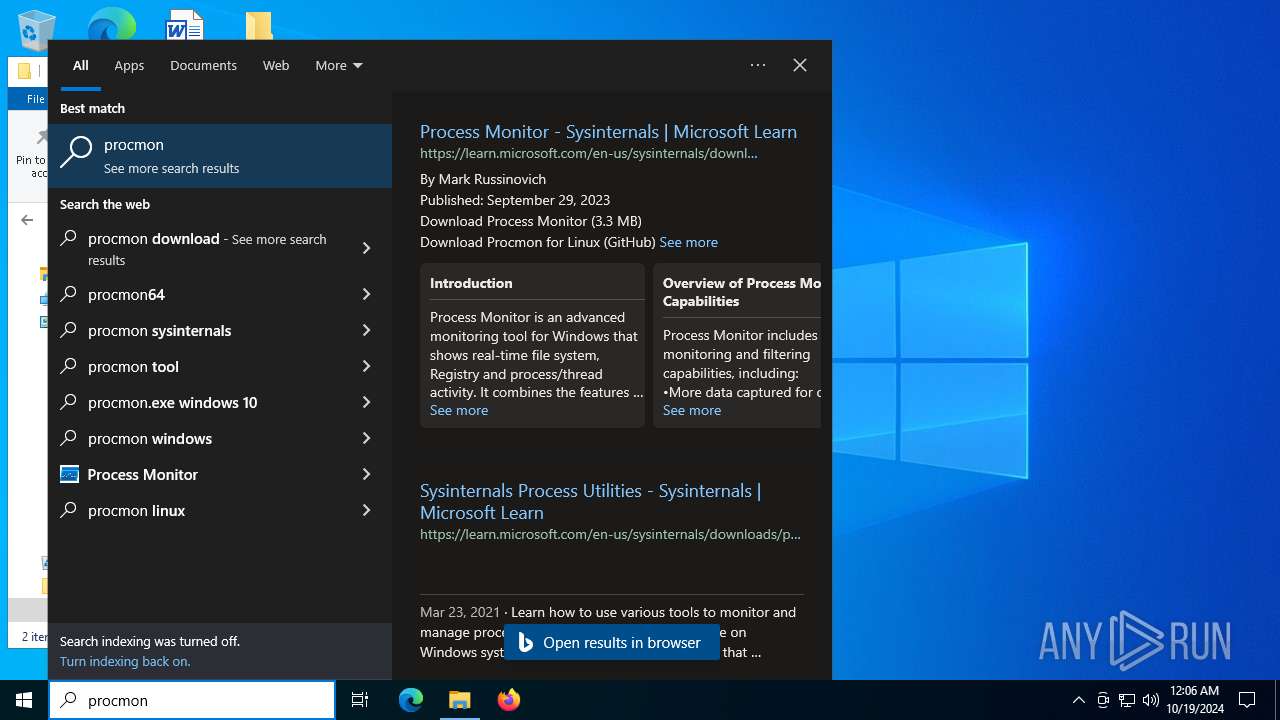
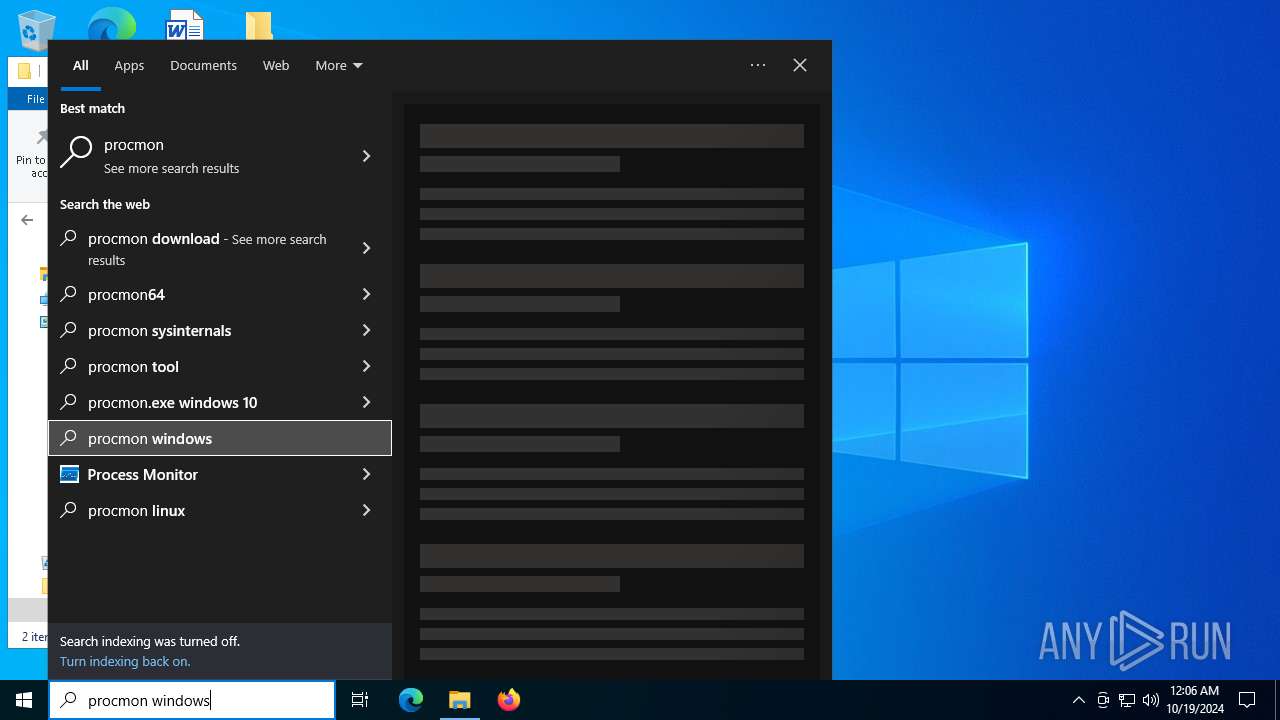
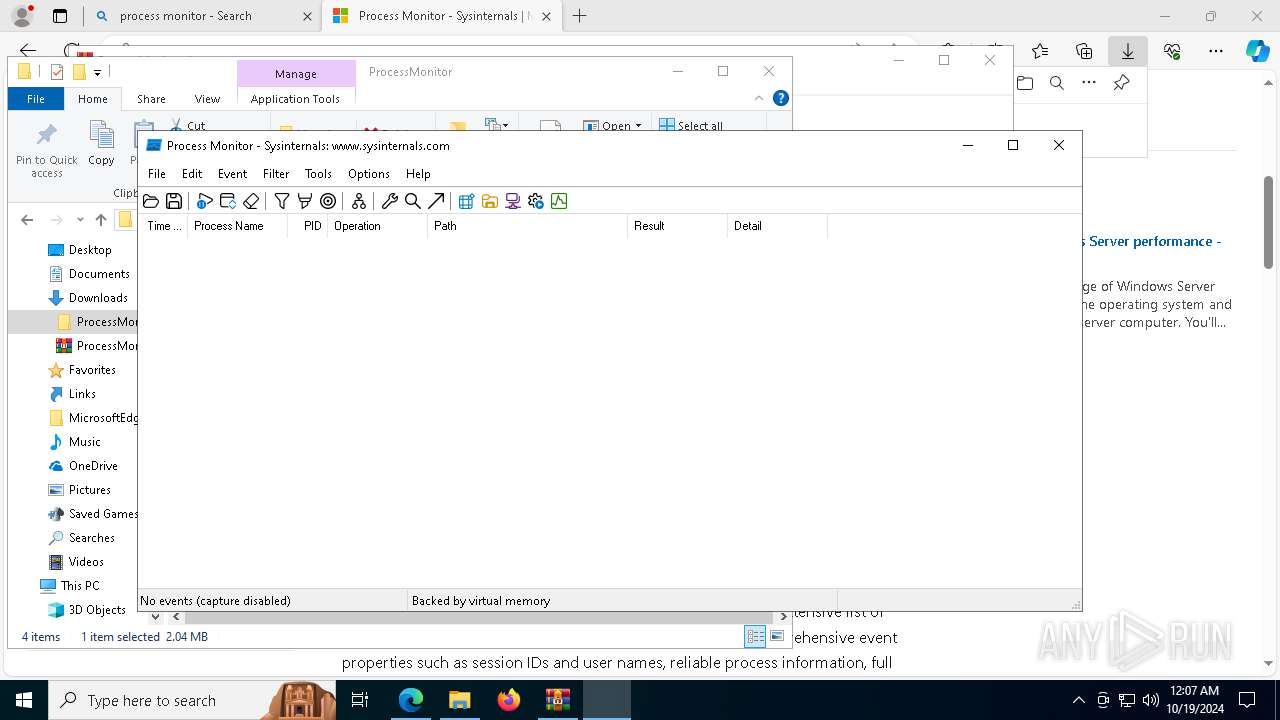
- WinRAR.exe (PID: 2432)
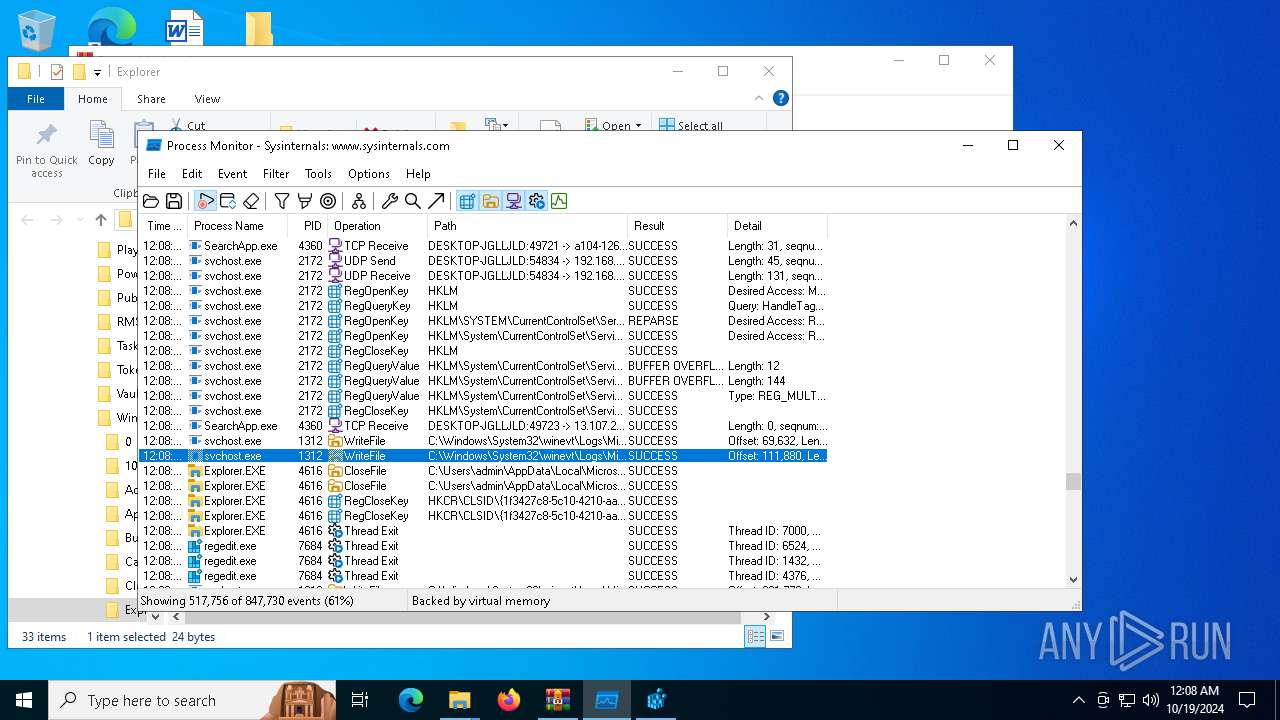
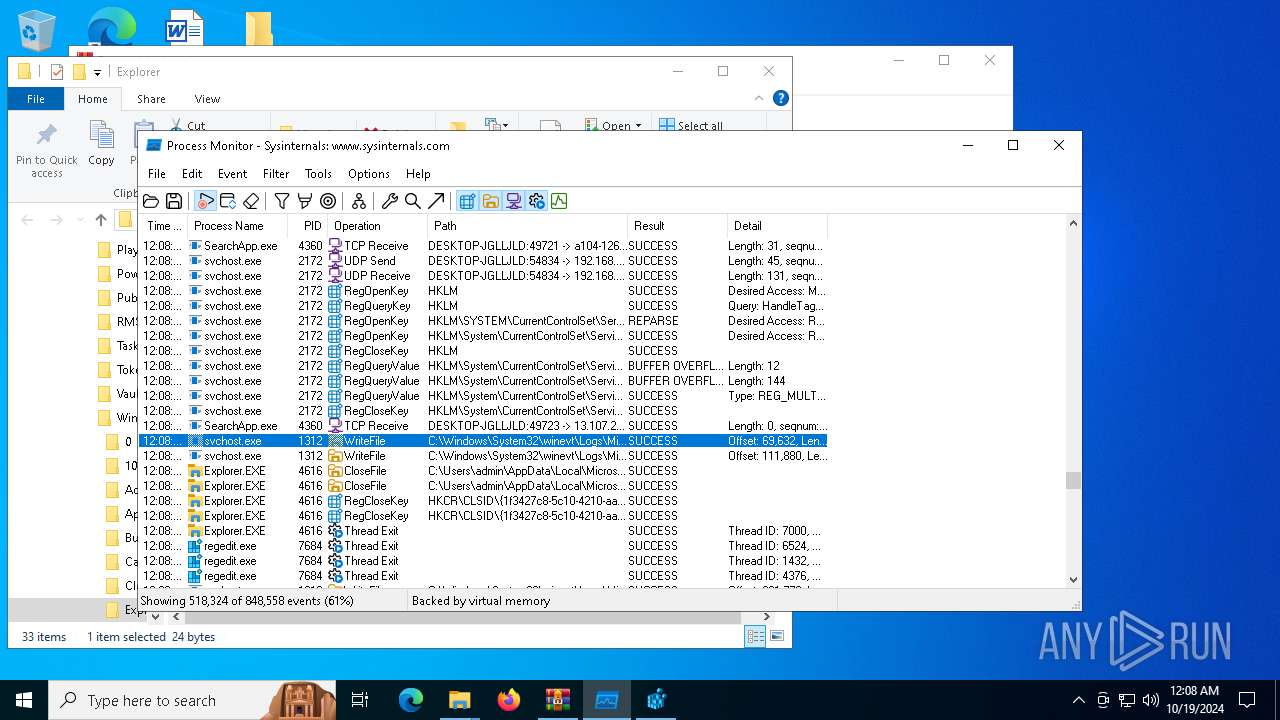
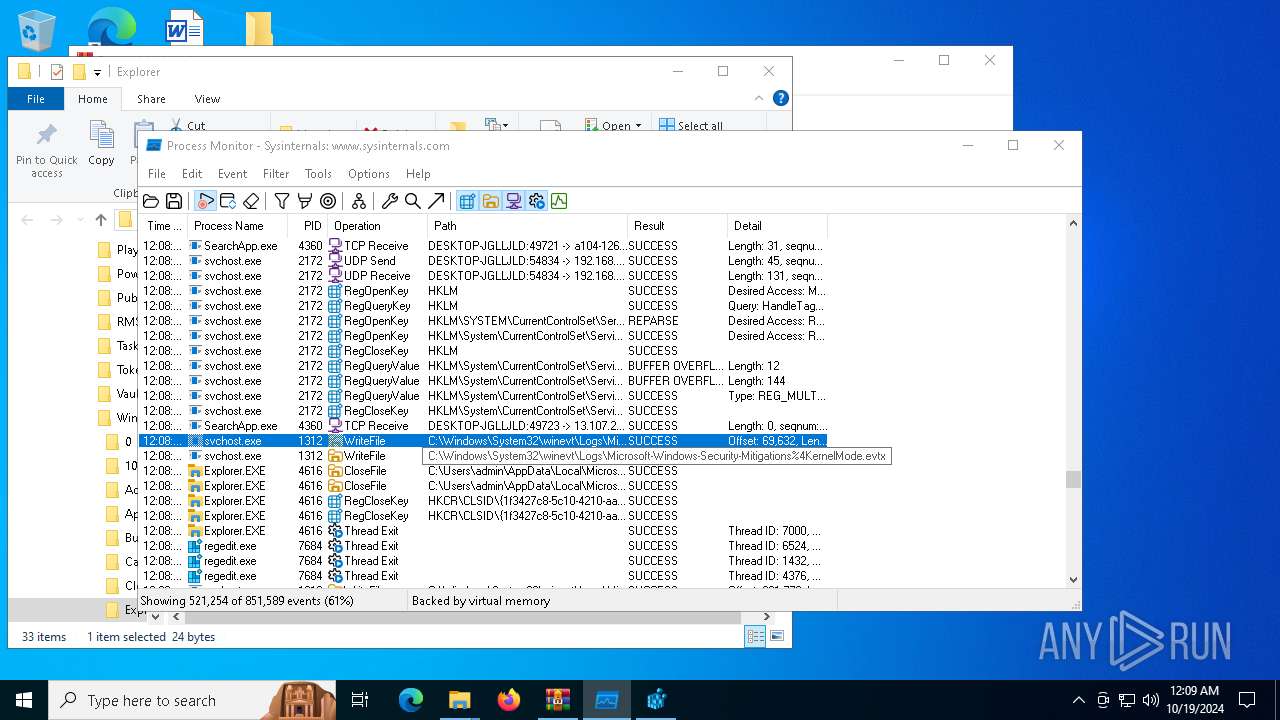
SUSPICIOUS
Application launched itself
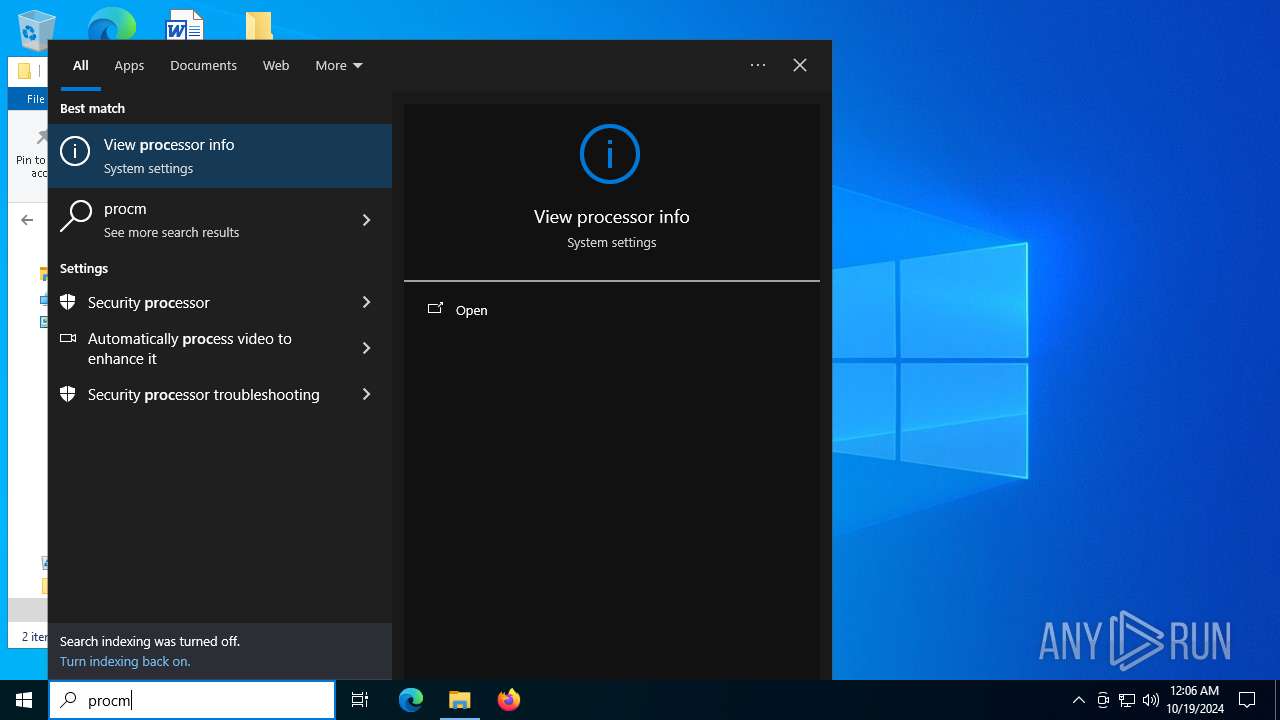
- Procmon64.exe (PID: 1168)
Executable content was dropped or overwritten
- Procmon64.exe (PID: 7080)
Drops a system driver (possible attempt to evade defenses)
- Procmon64.exe (PID: 7080)
INFO
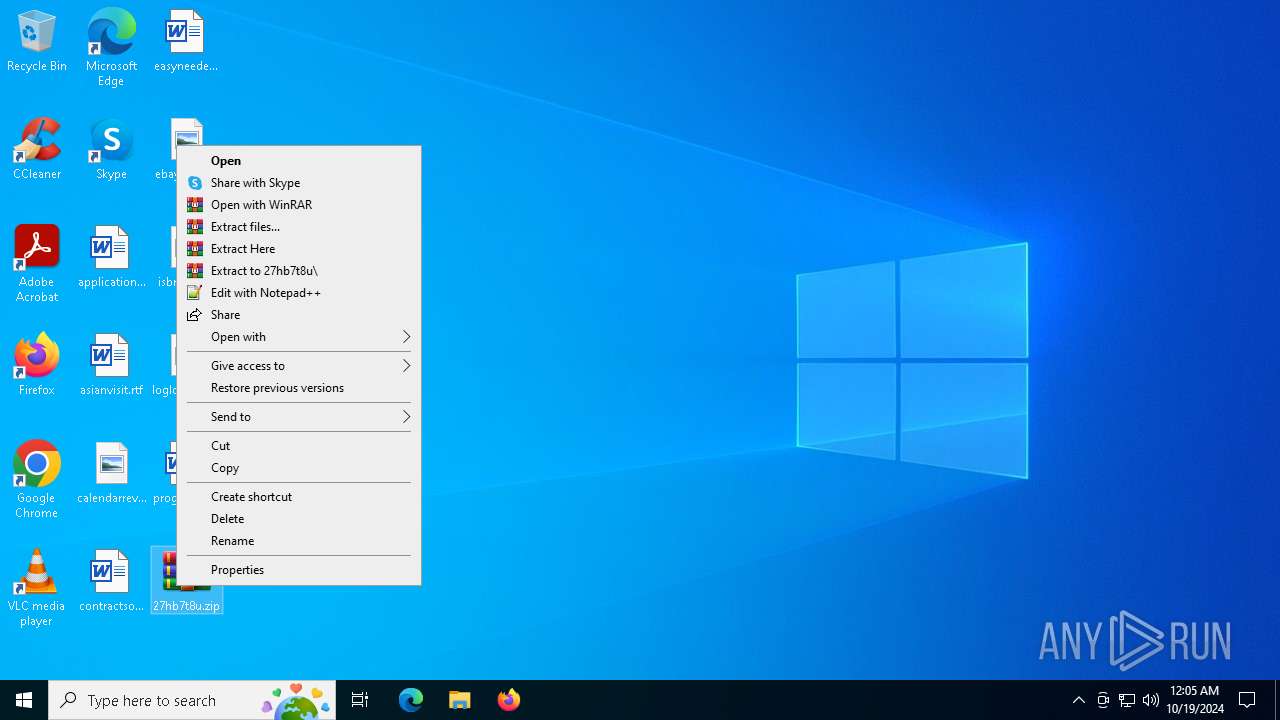
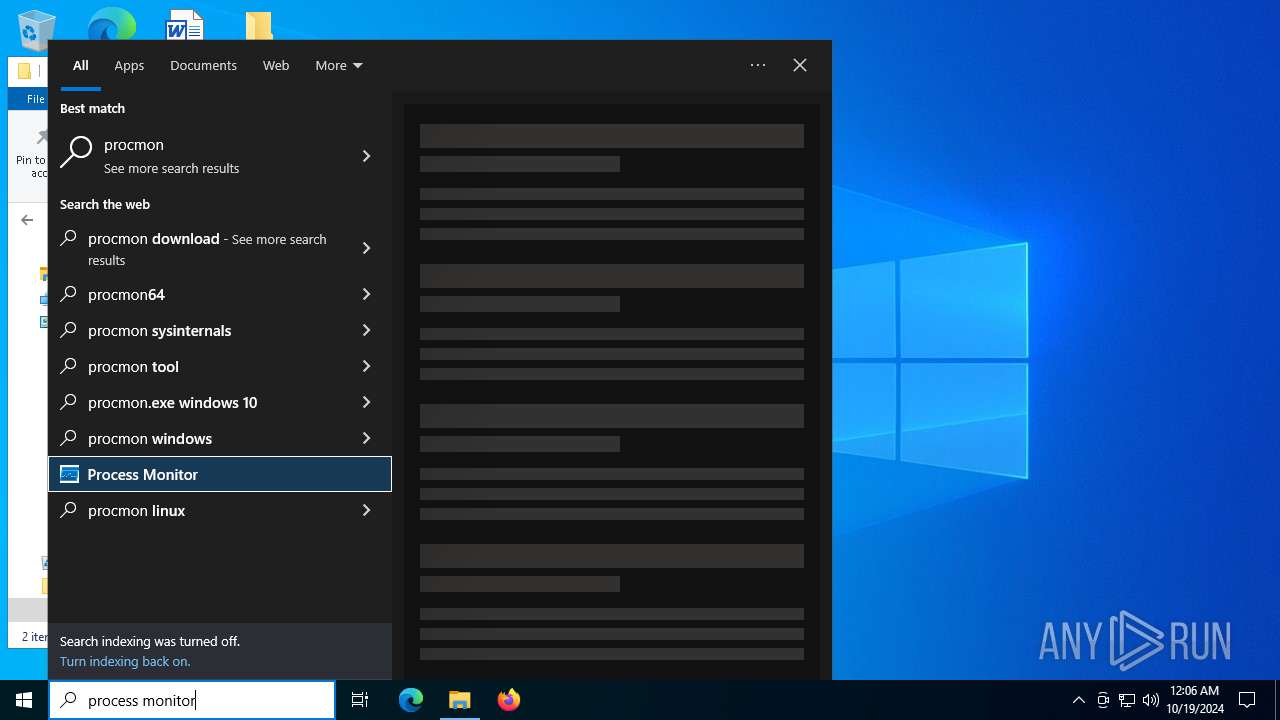
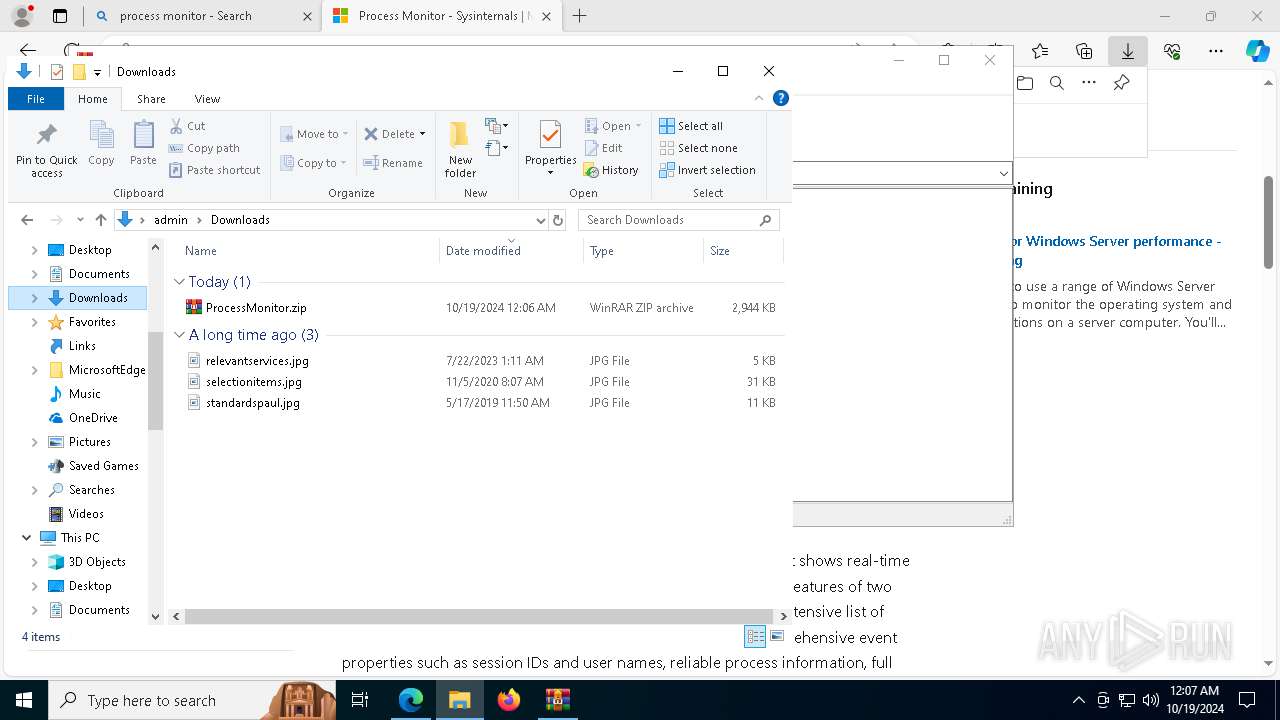
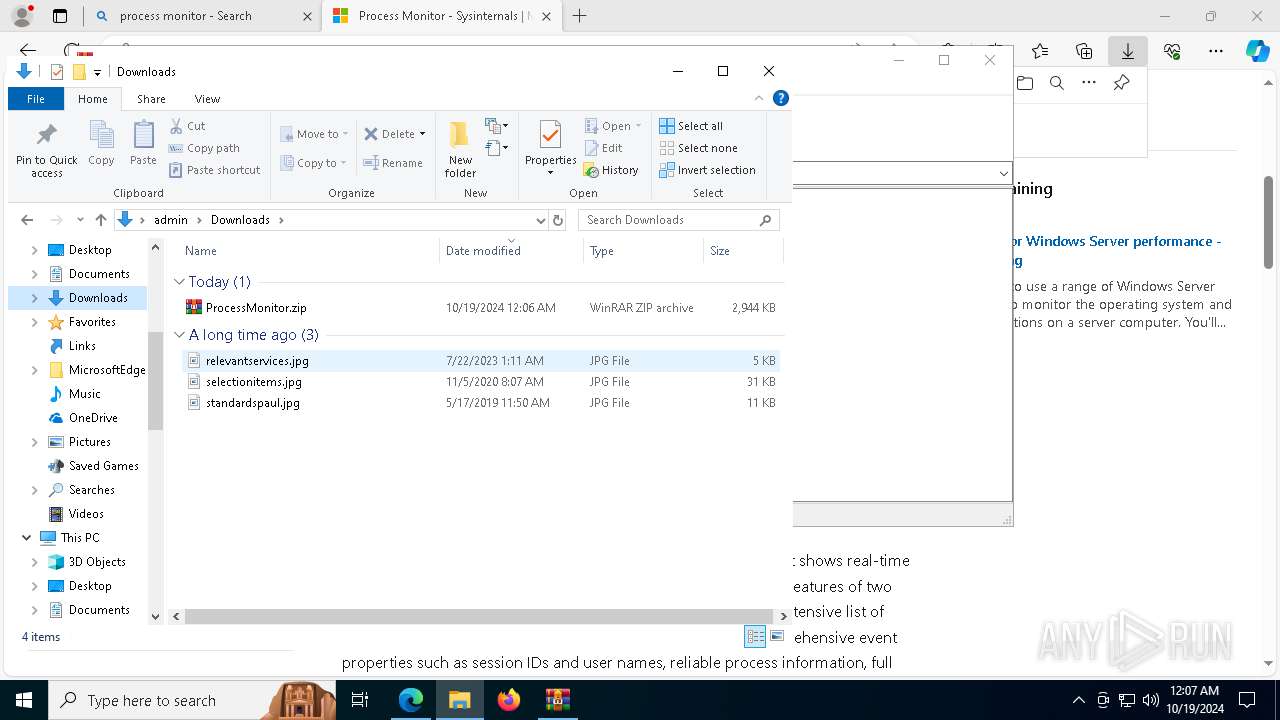
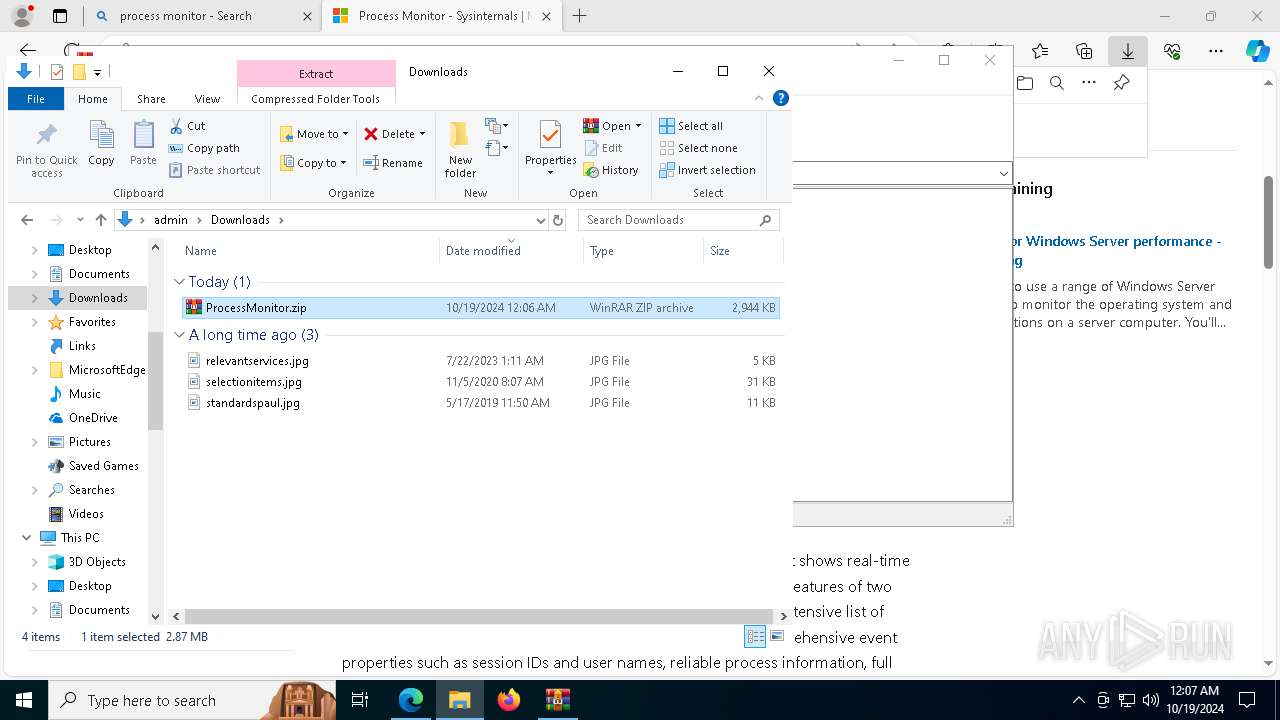
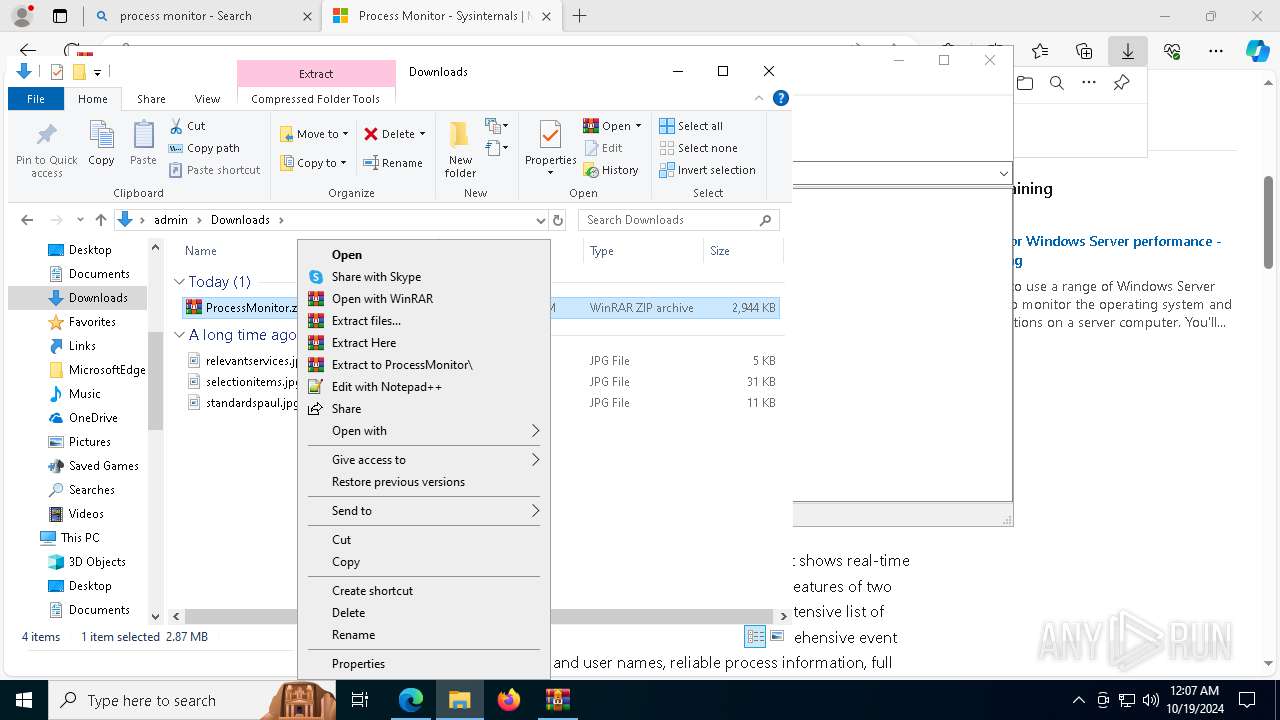
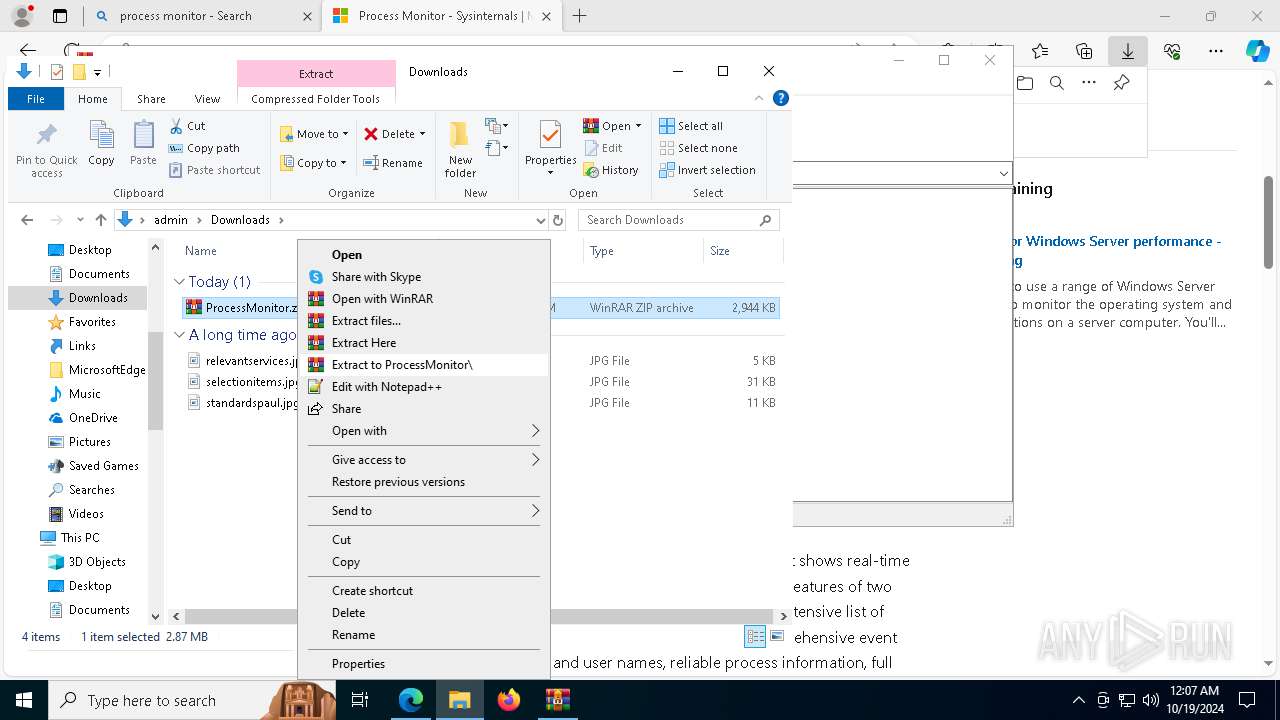
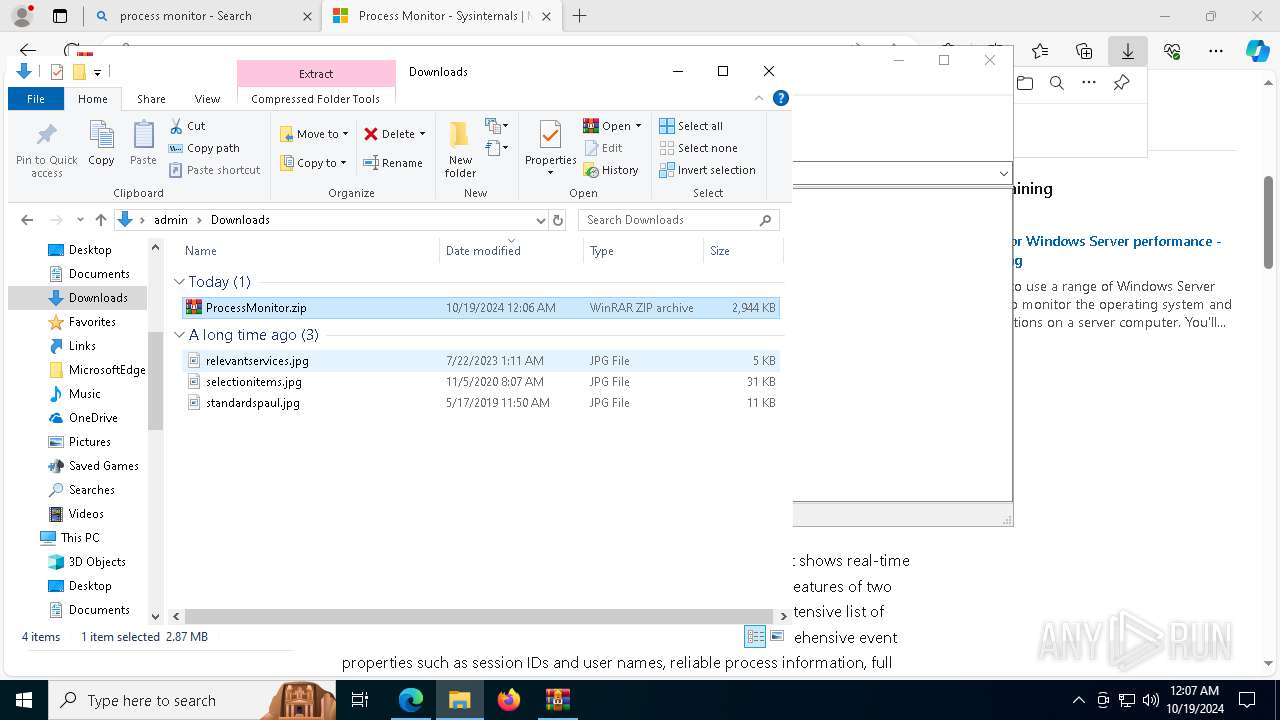
Manual execution by a user
- WinRAR.exe (PID: 6520)
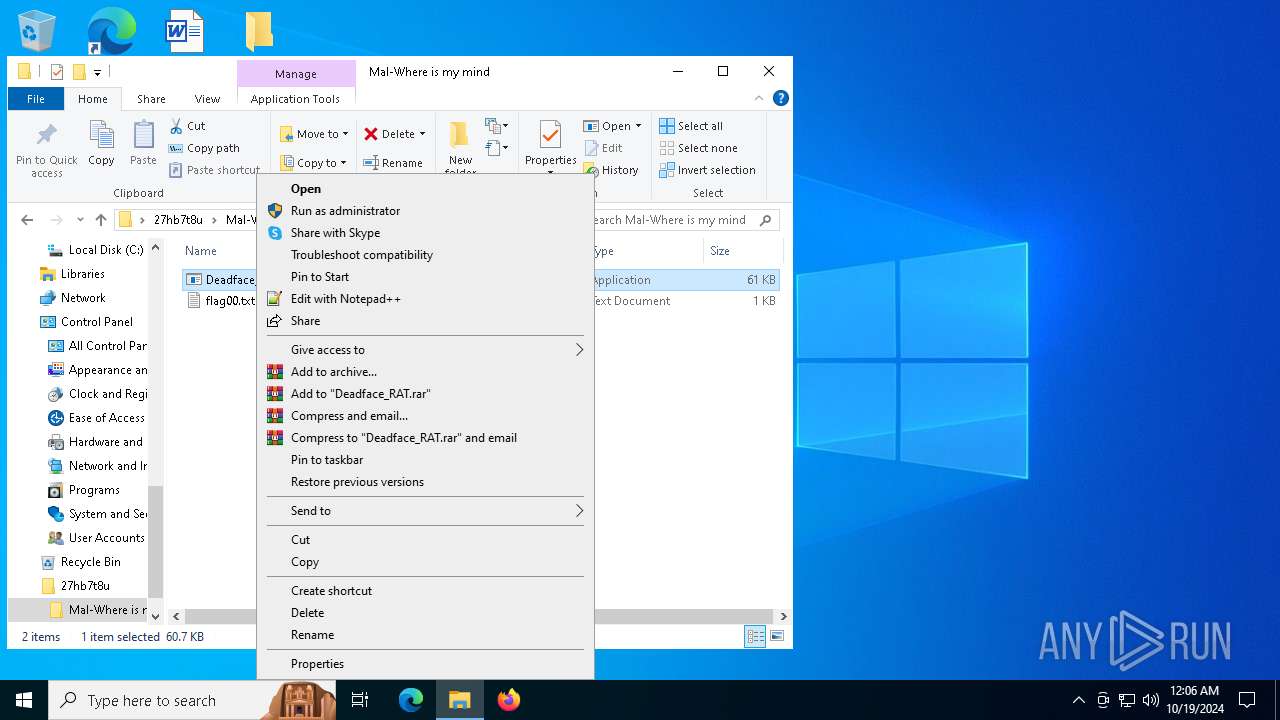
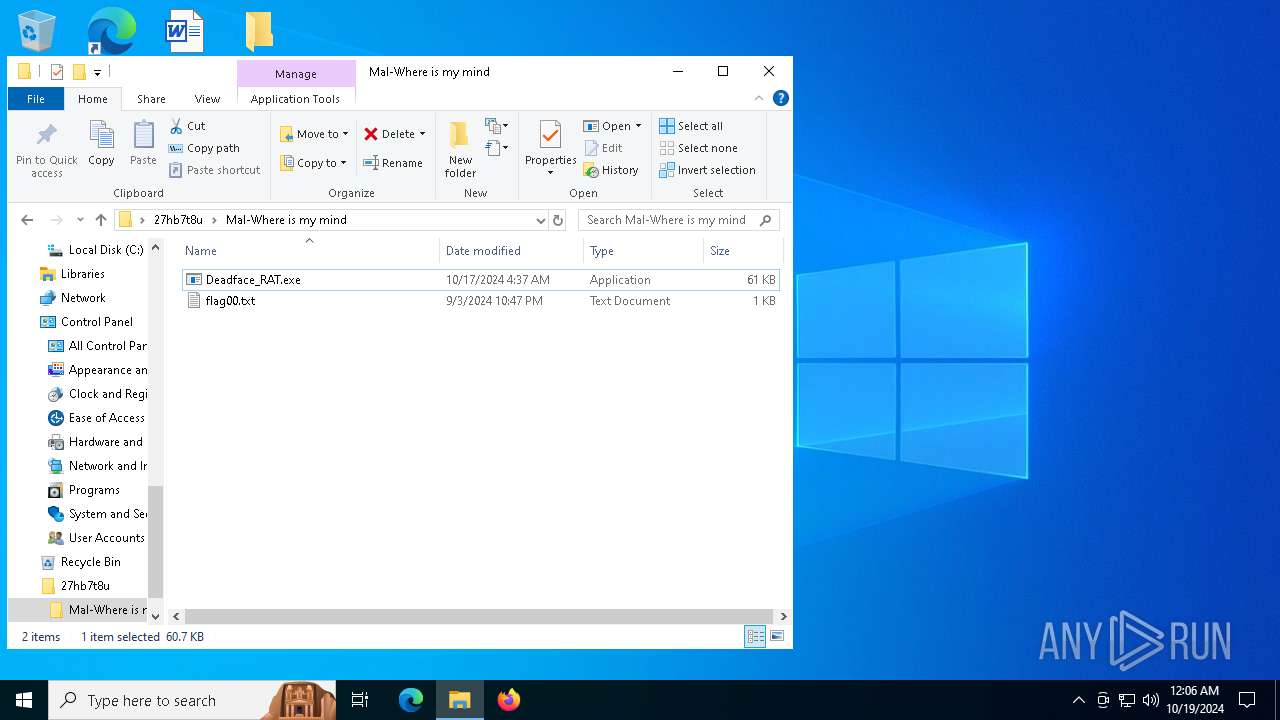
- Deadface_RAT.exe (PID: 4260)
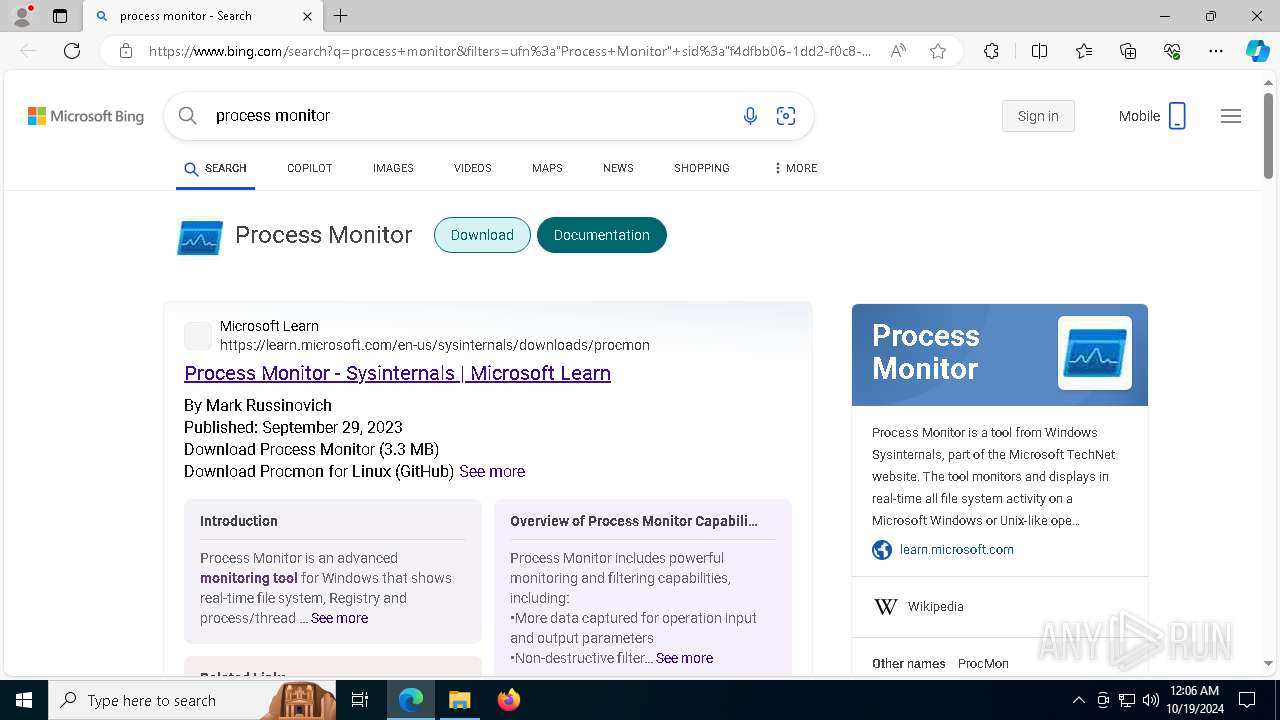
- Procmon64.exe (PID: 1168)
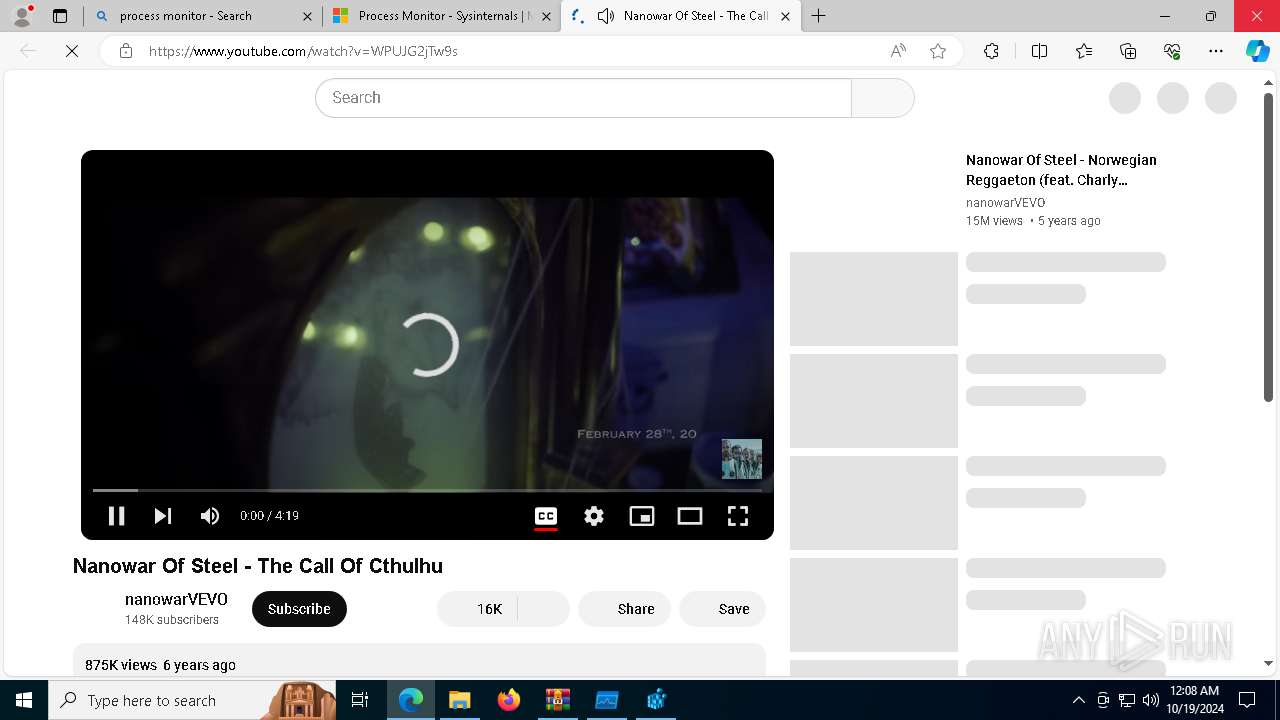
- msedge.exe (PID: 8052)
- WinRAR.exe (PID: 6324)
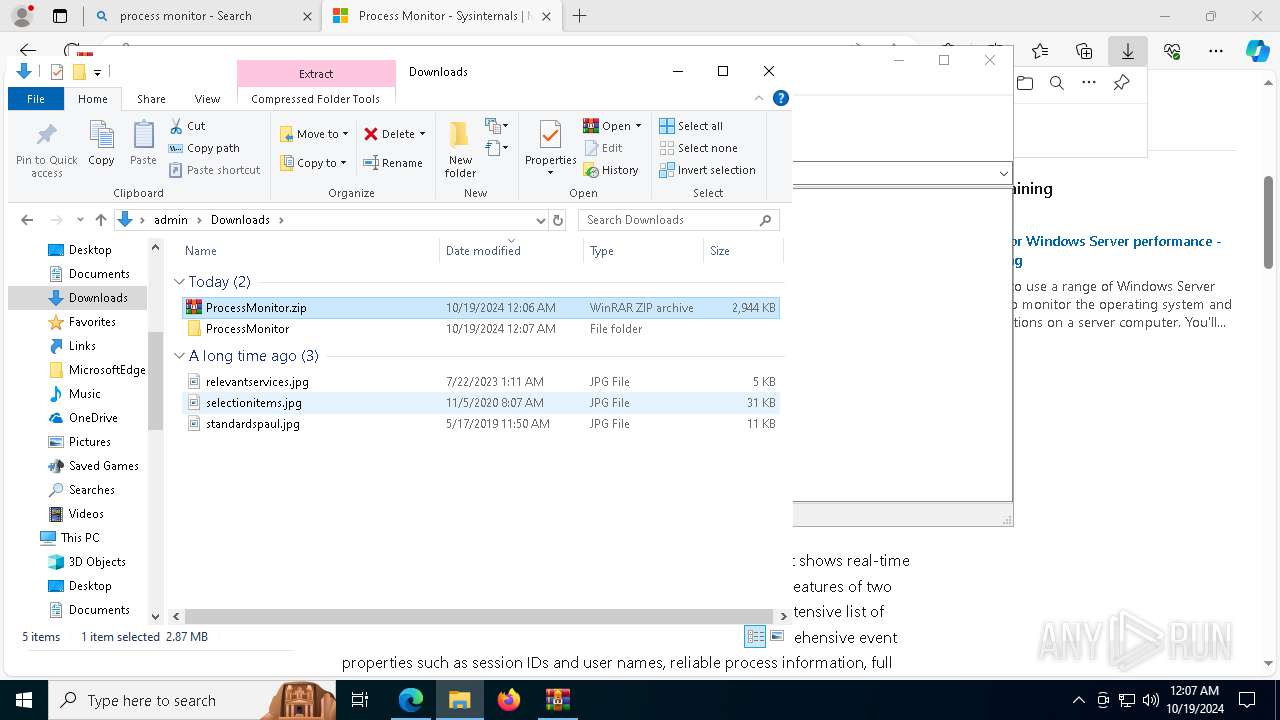
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6520)
- WinRAR.exe (PID: 6324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:10:16 23:38:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
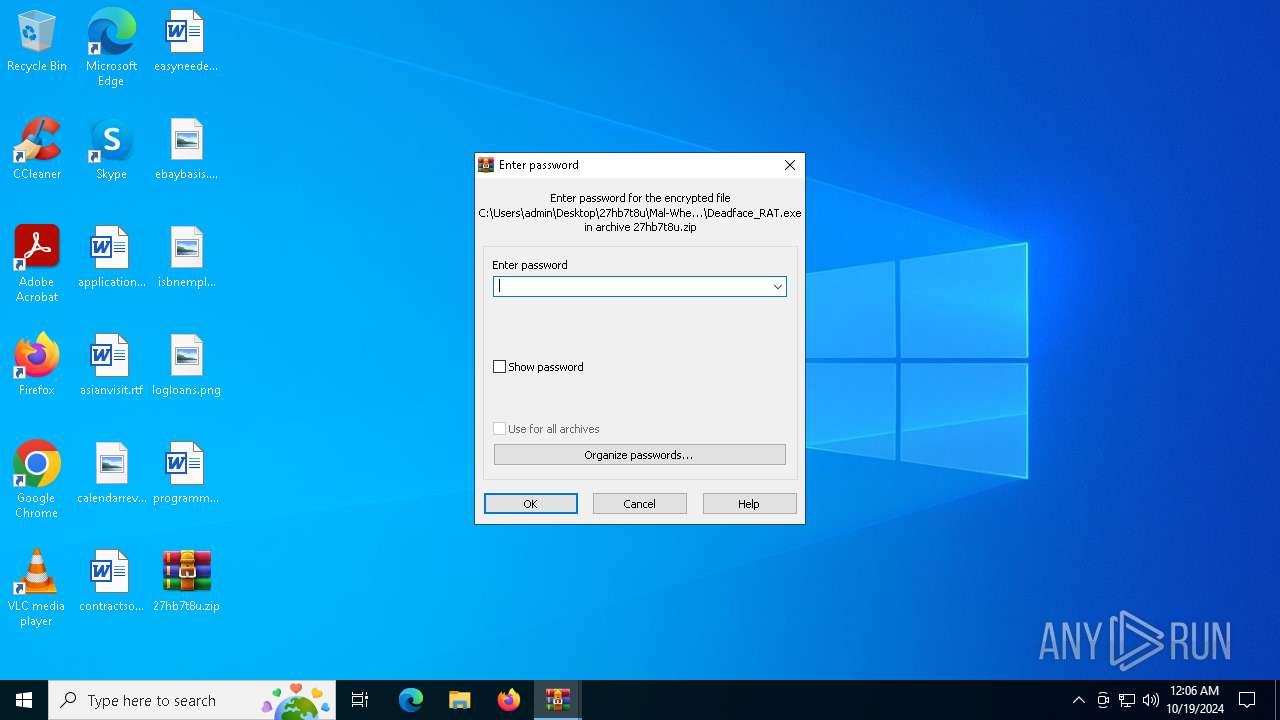
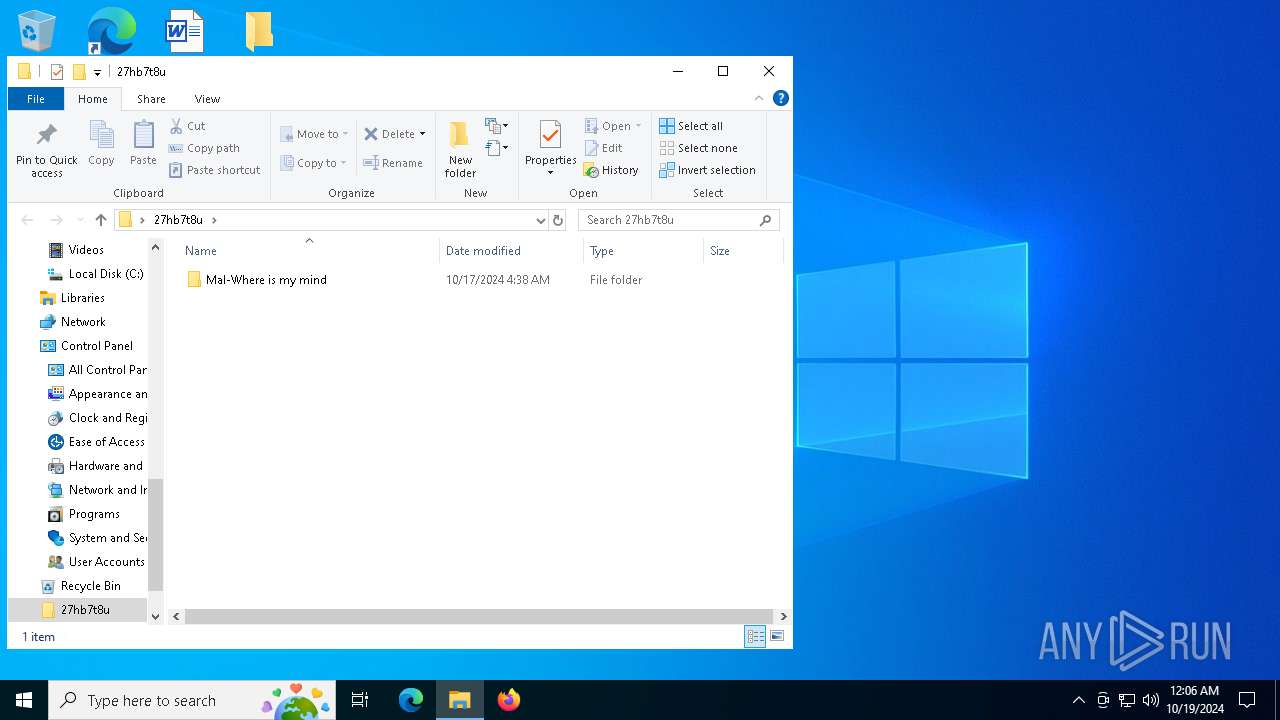
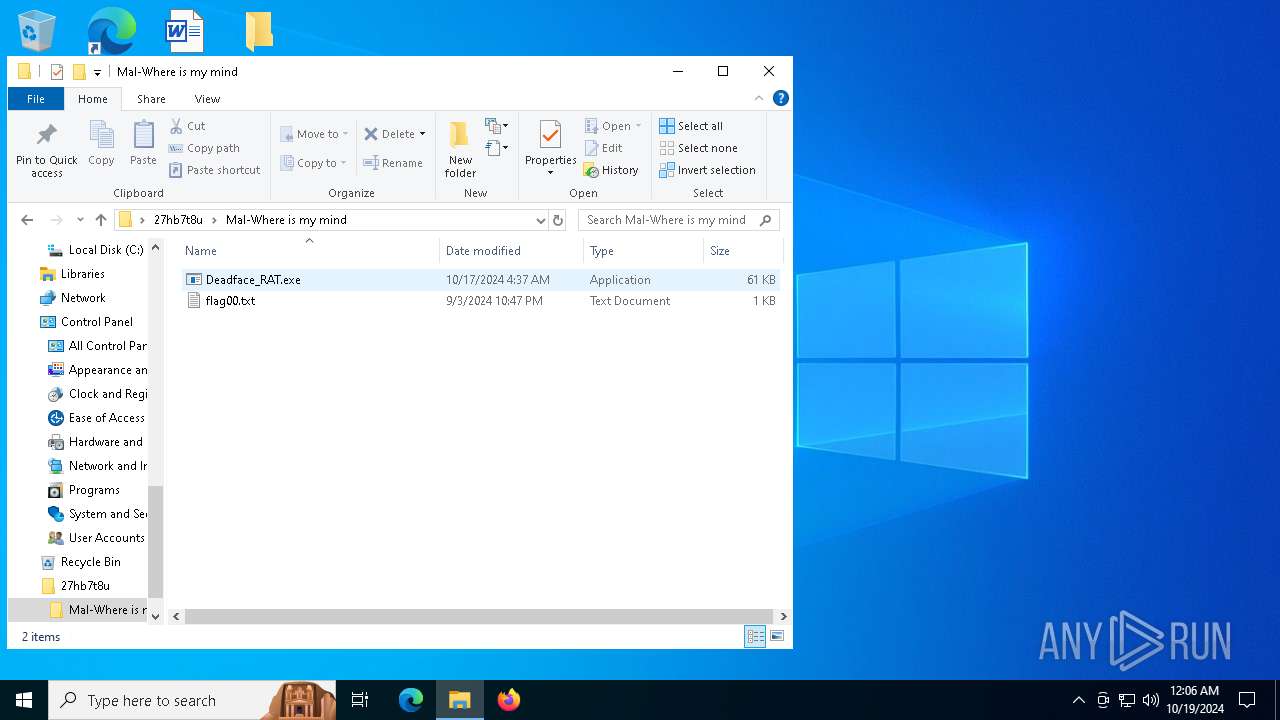
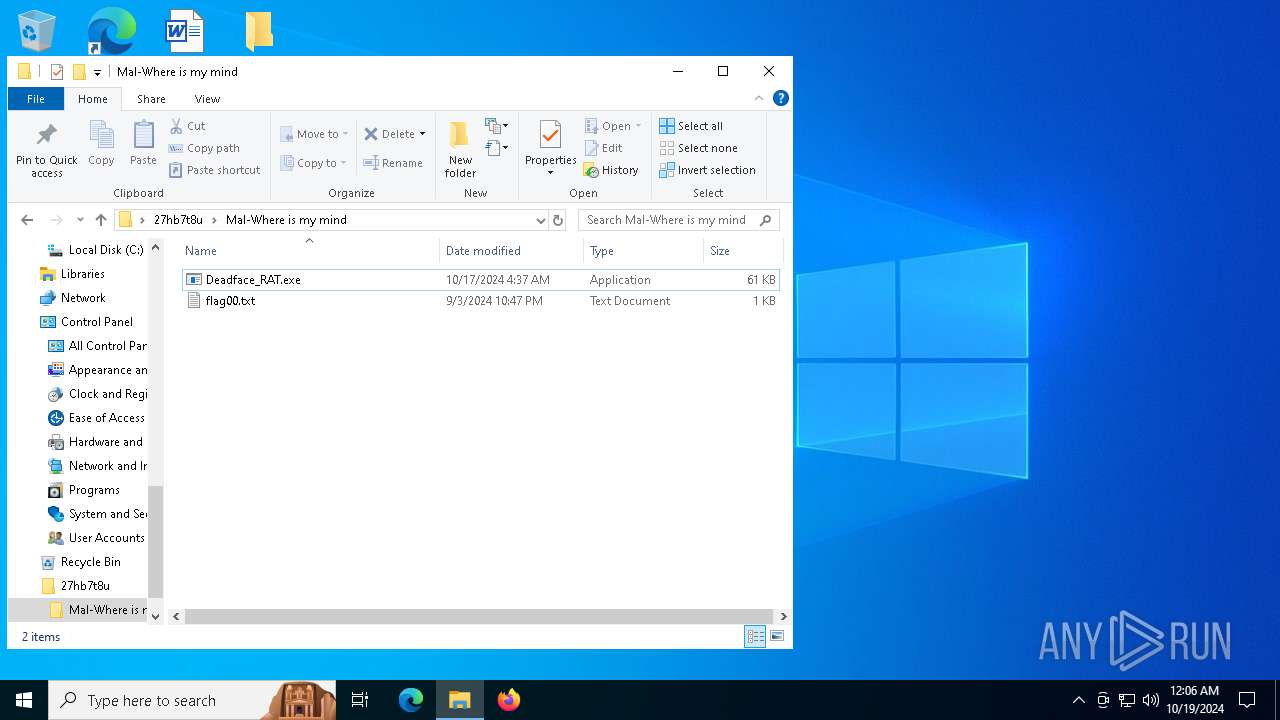
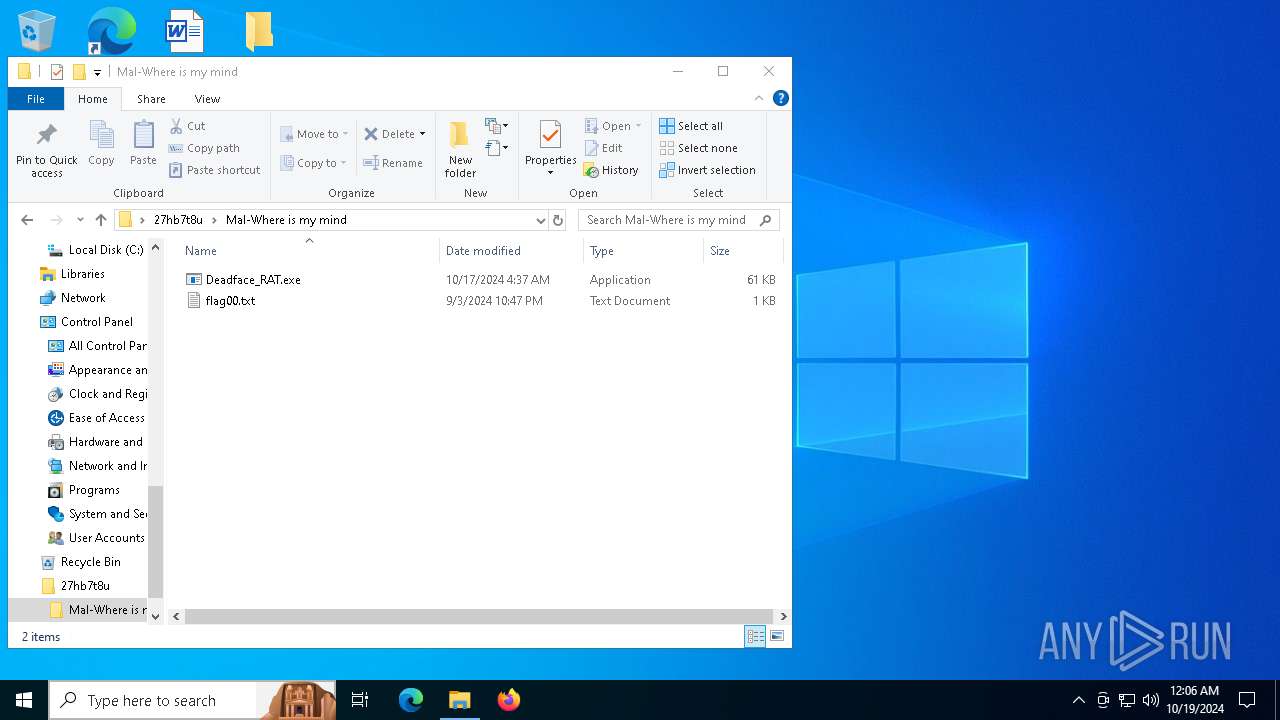
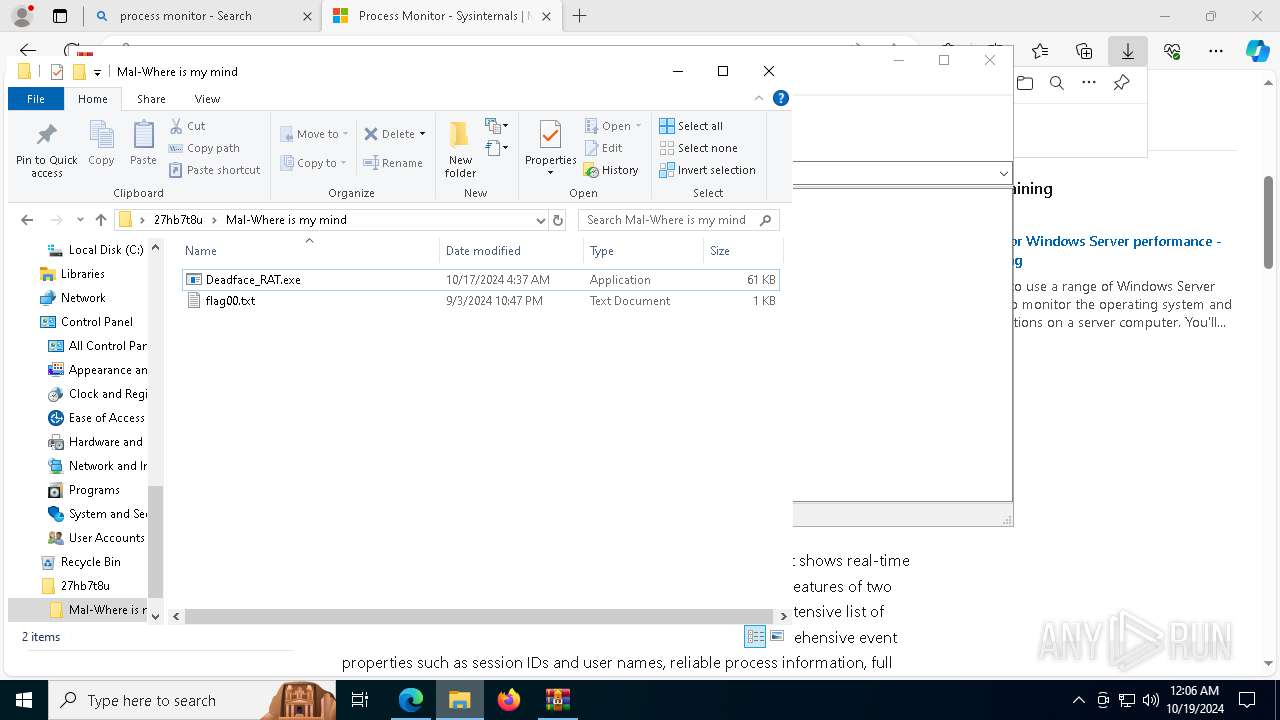
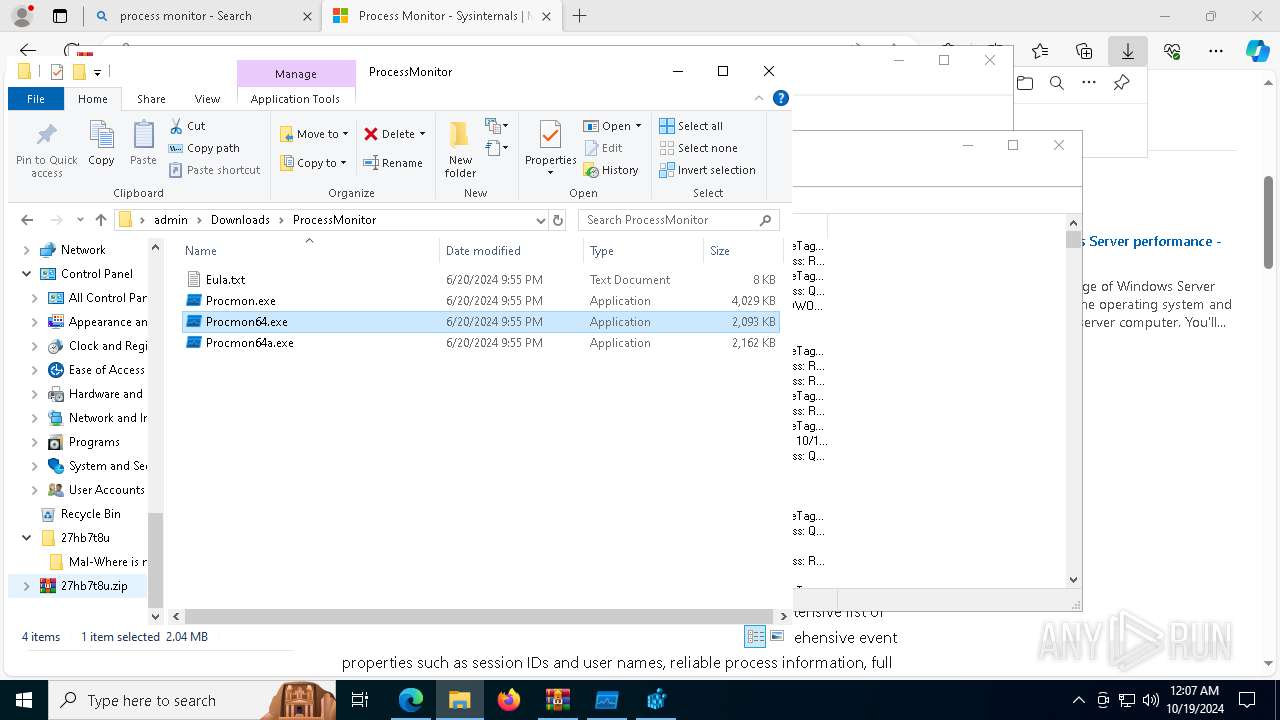
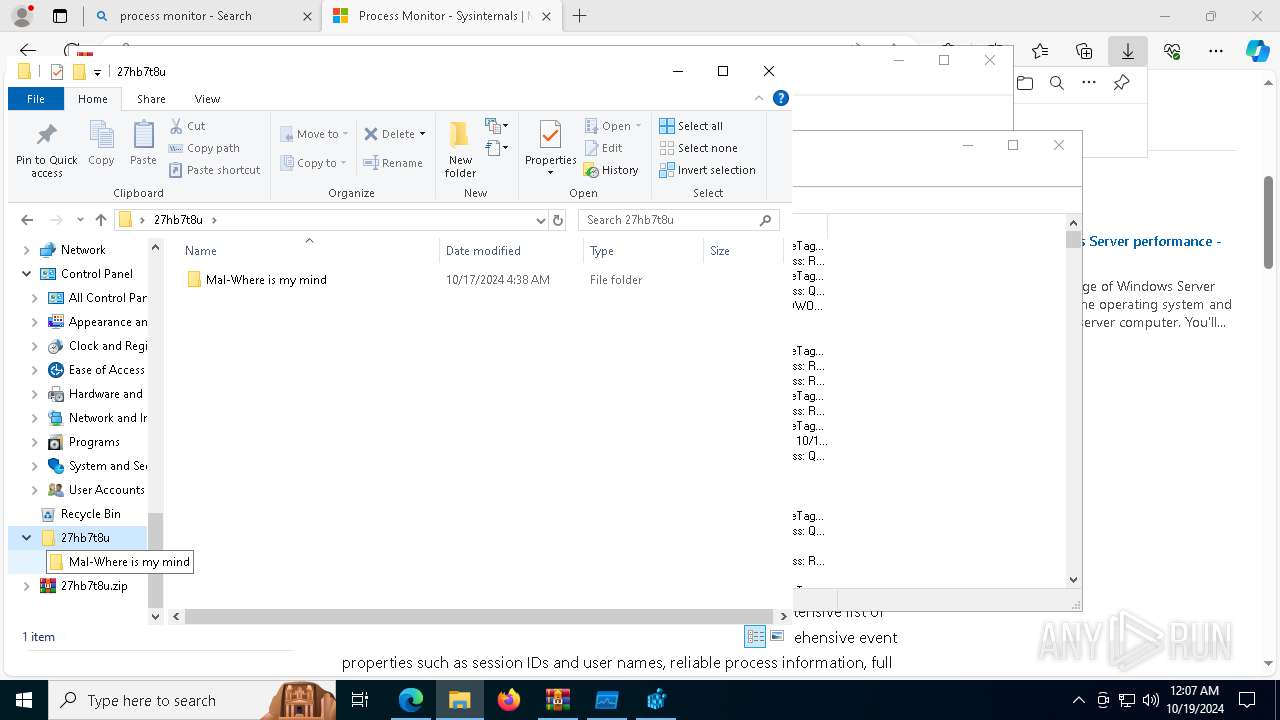
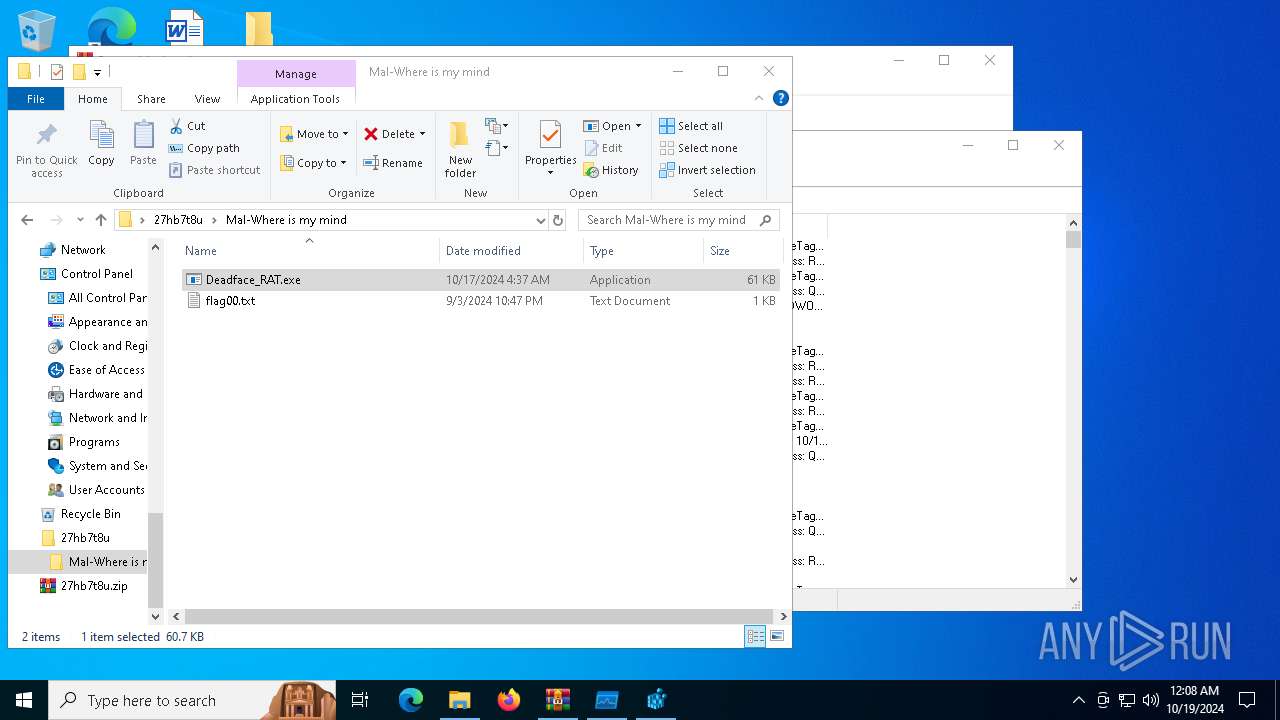
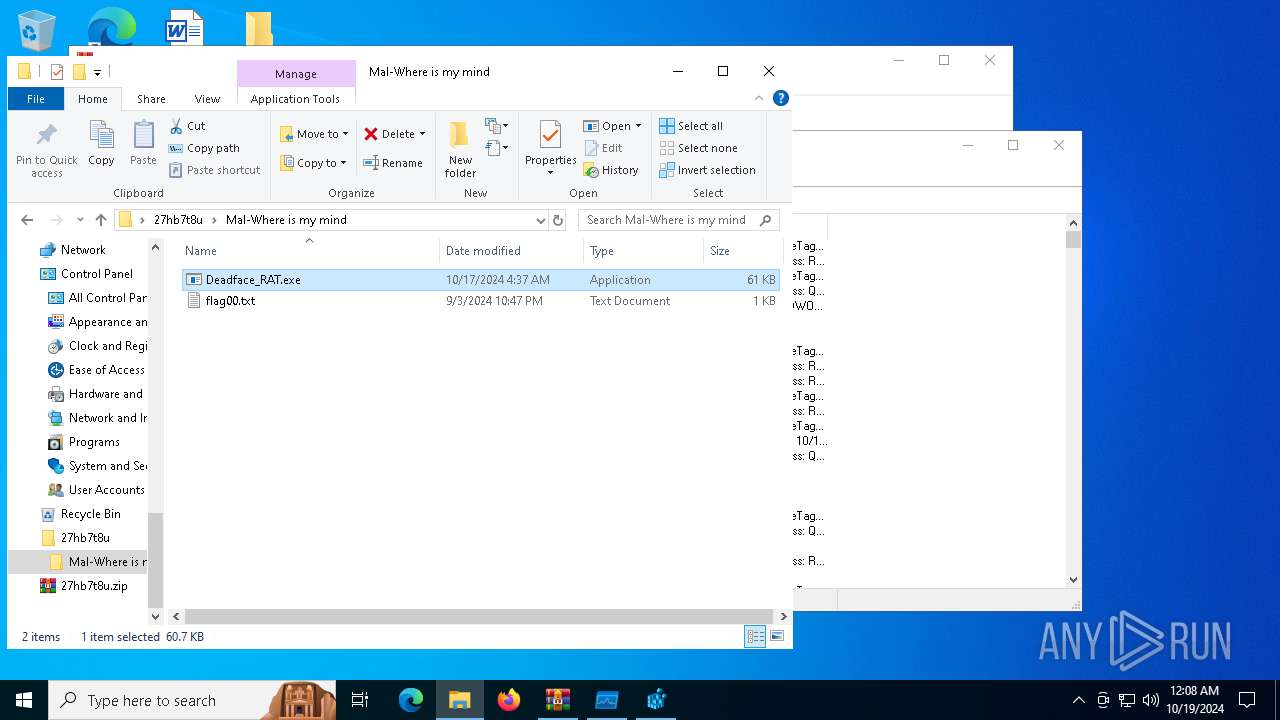
| ZipFileName: | Mal-Where is my mind/ |
Total processes
273
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
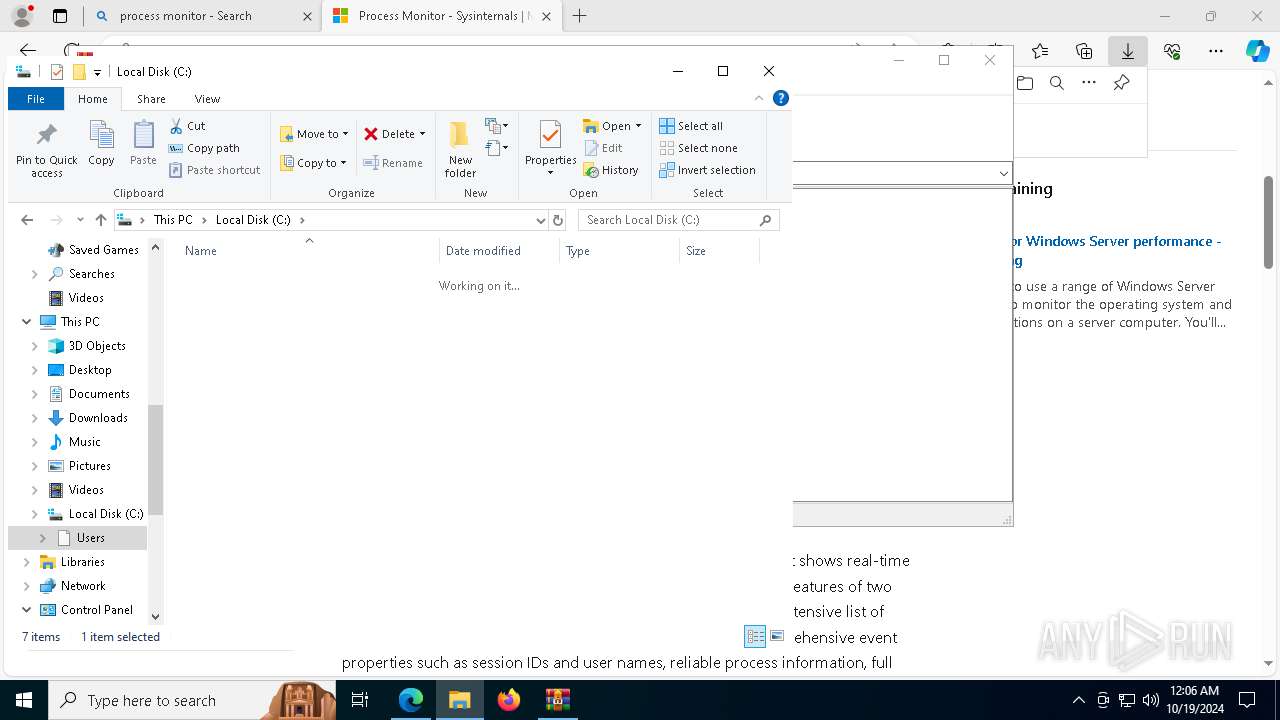
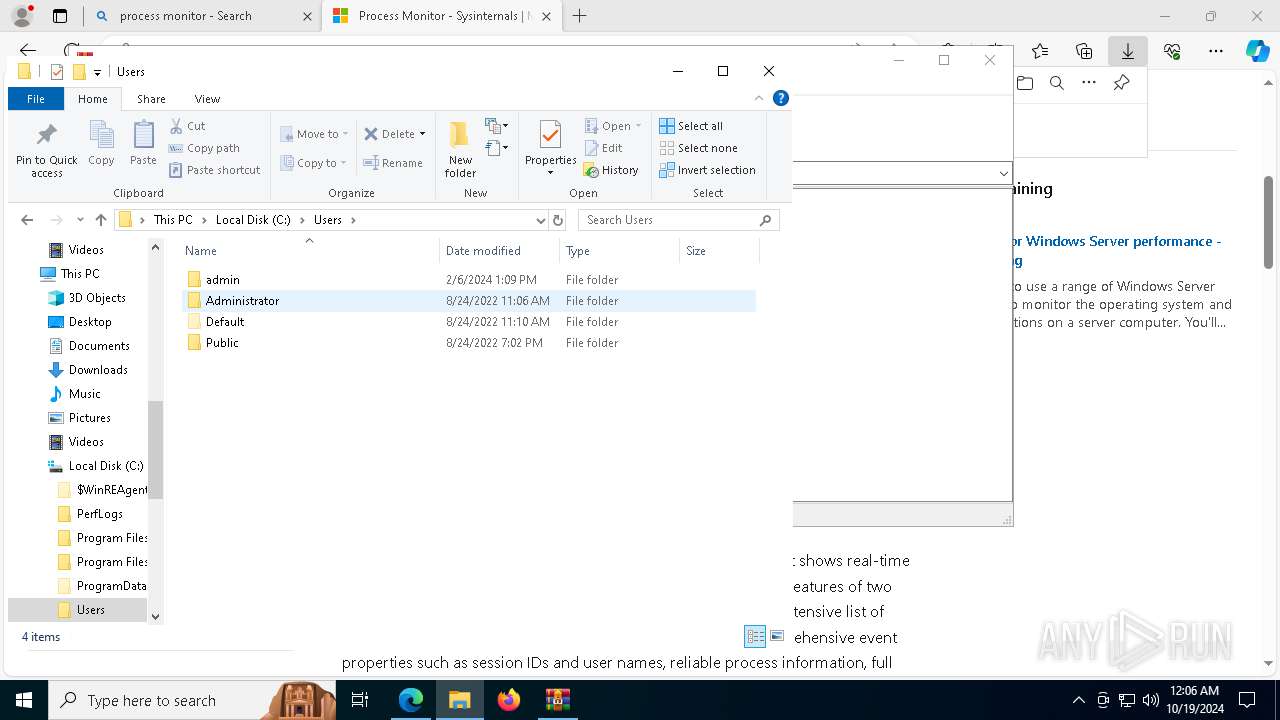
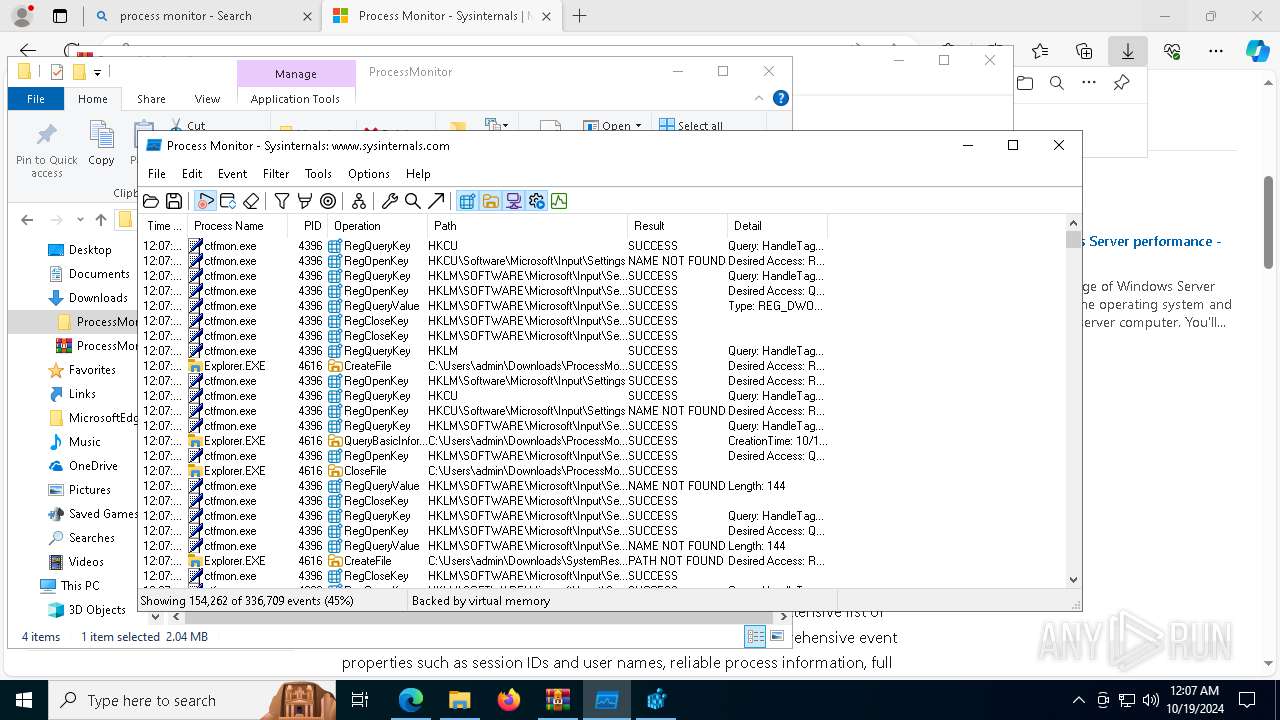
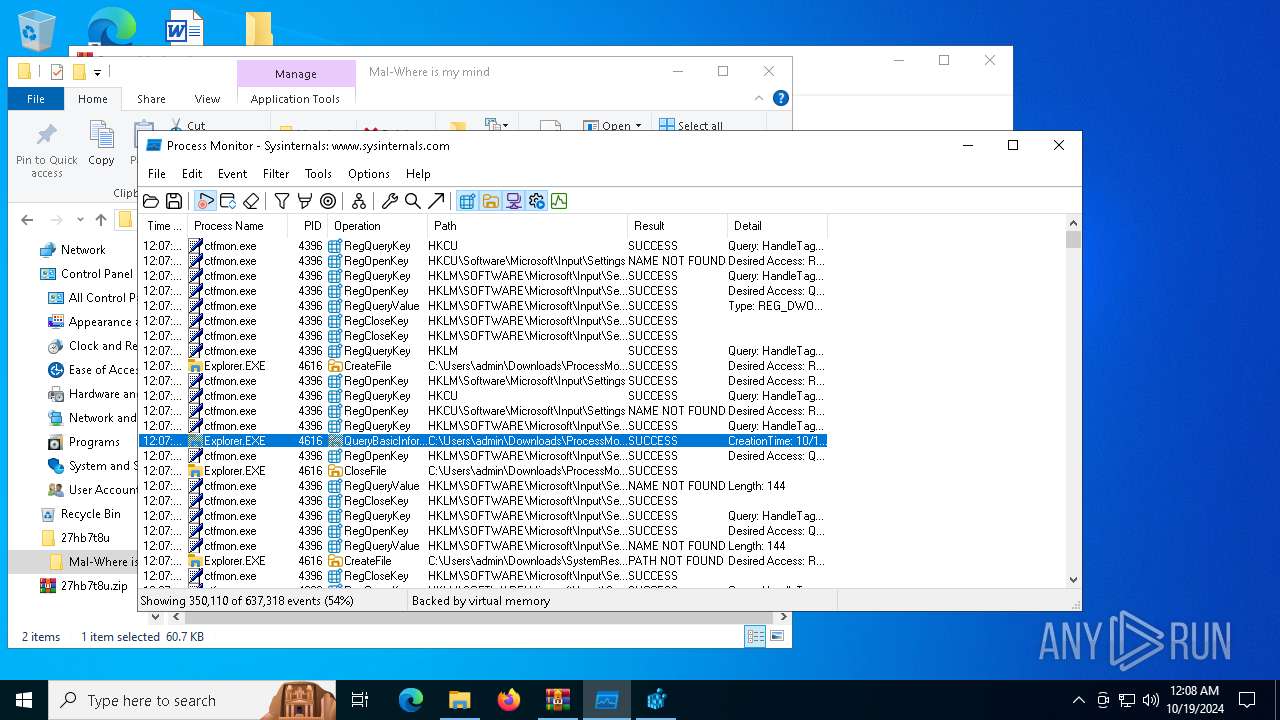
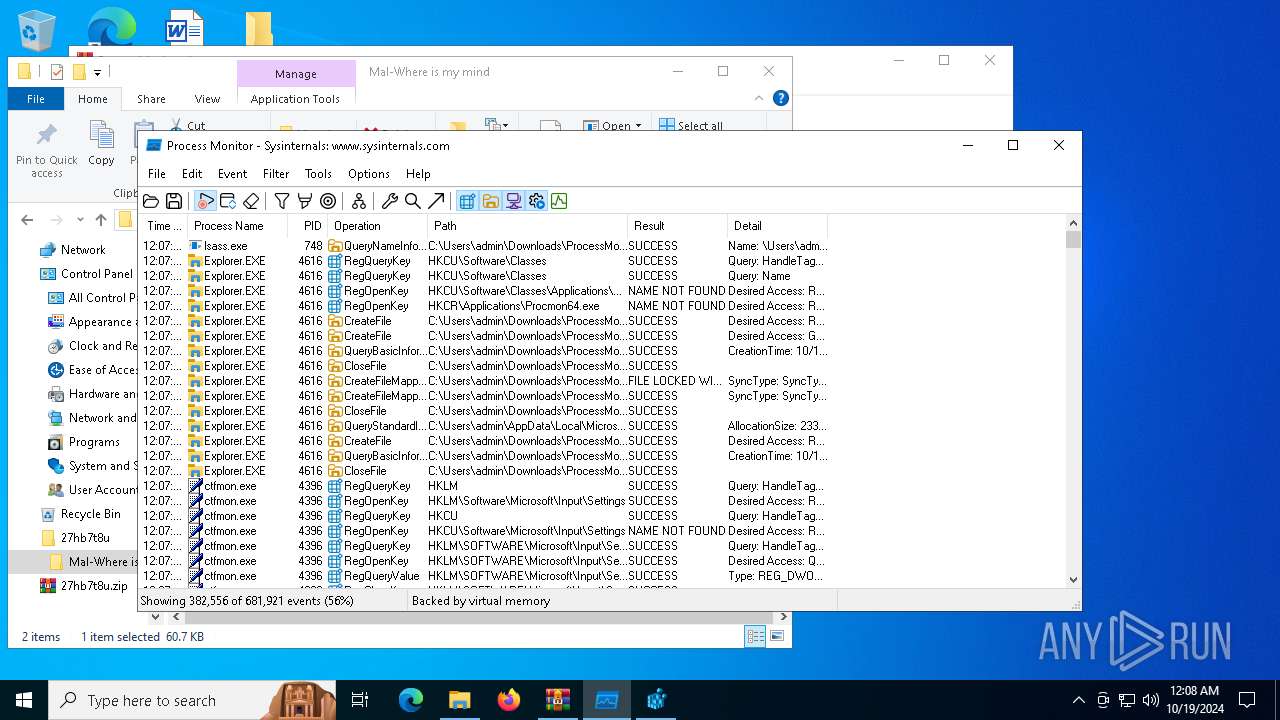
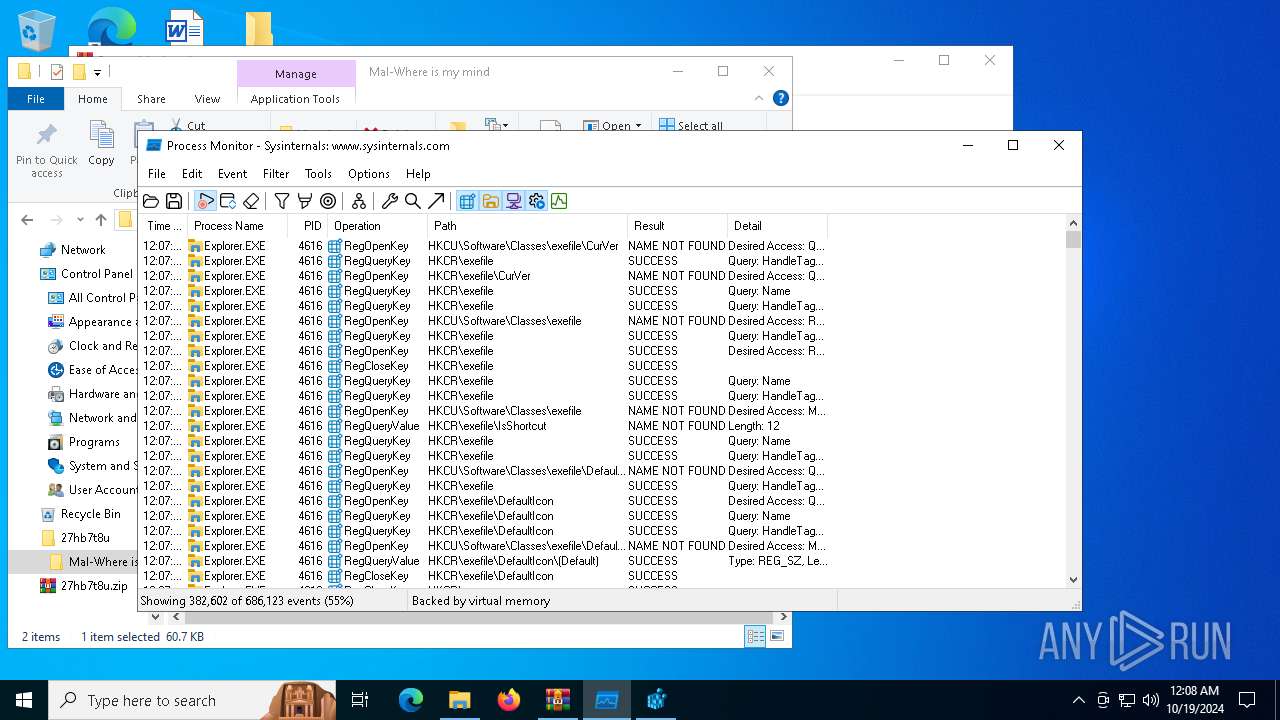
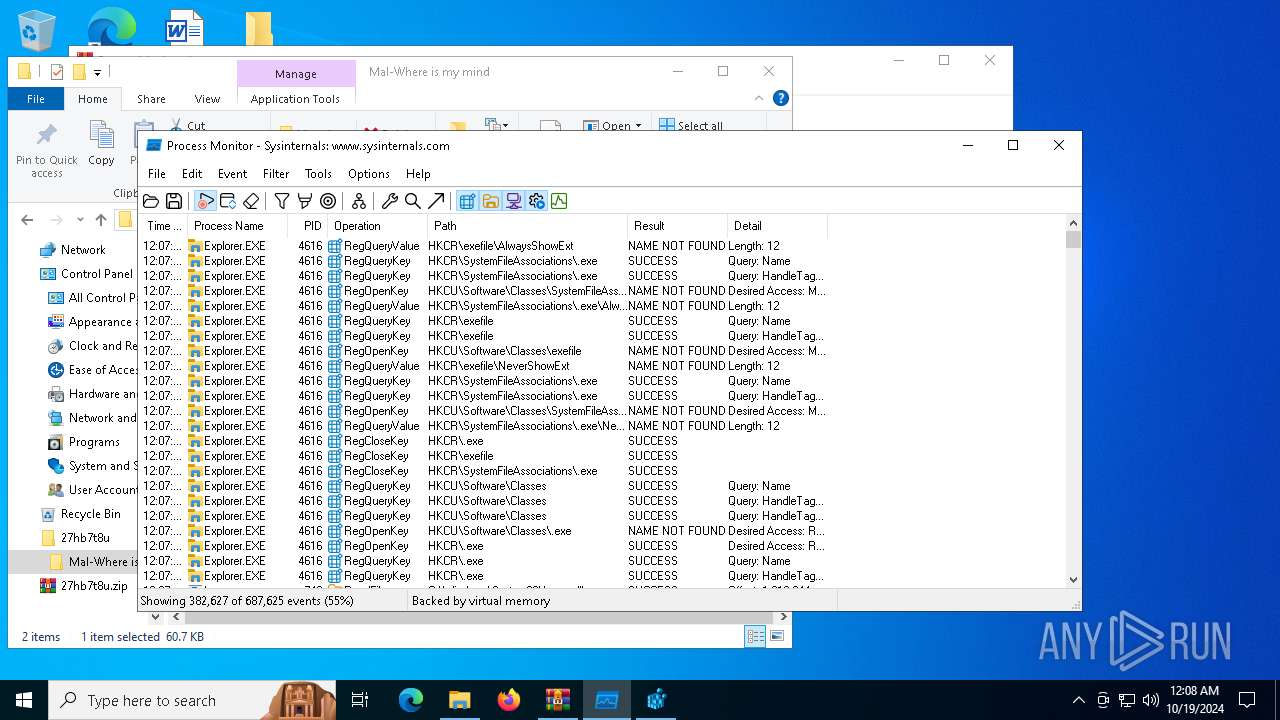
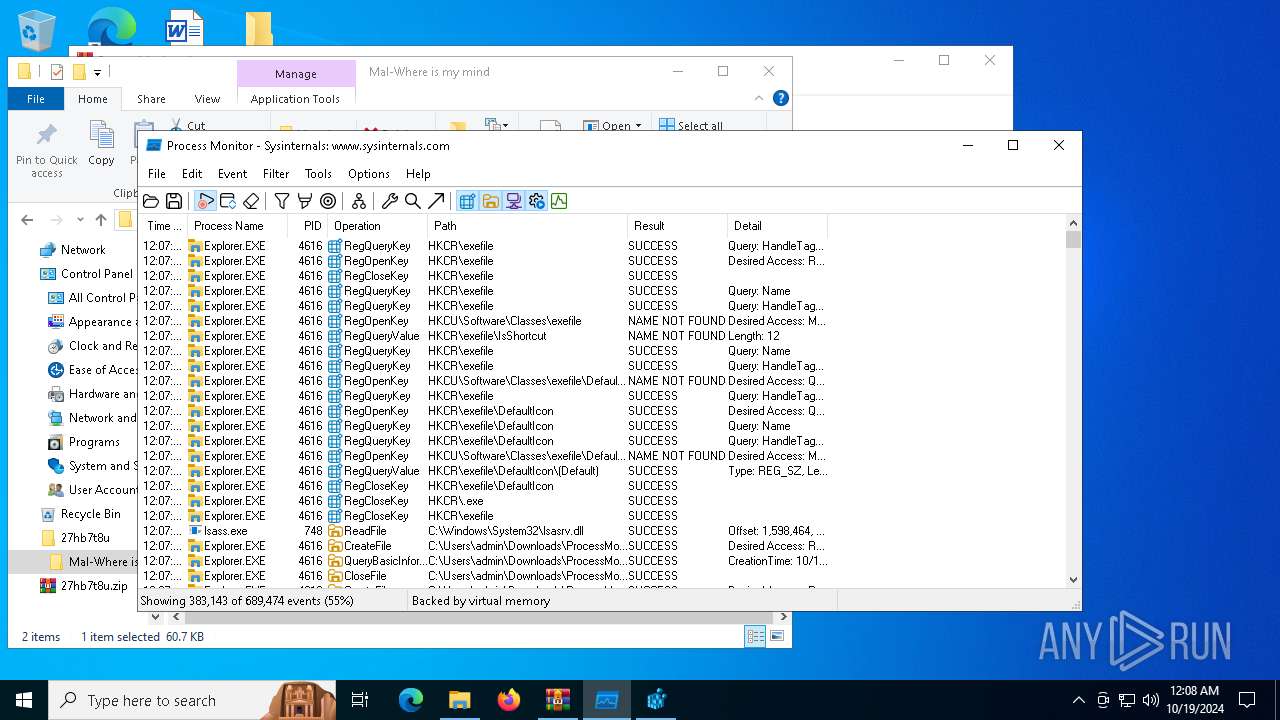
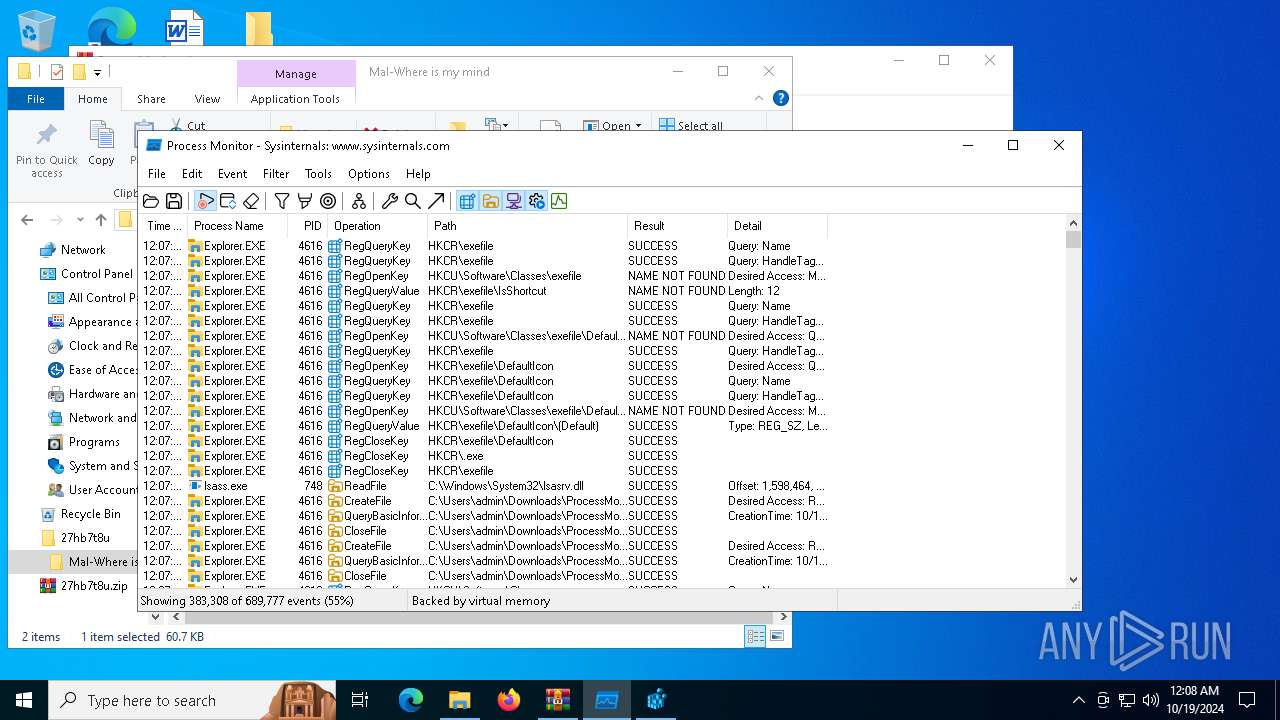
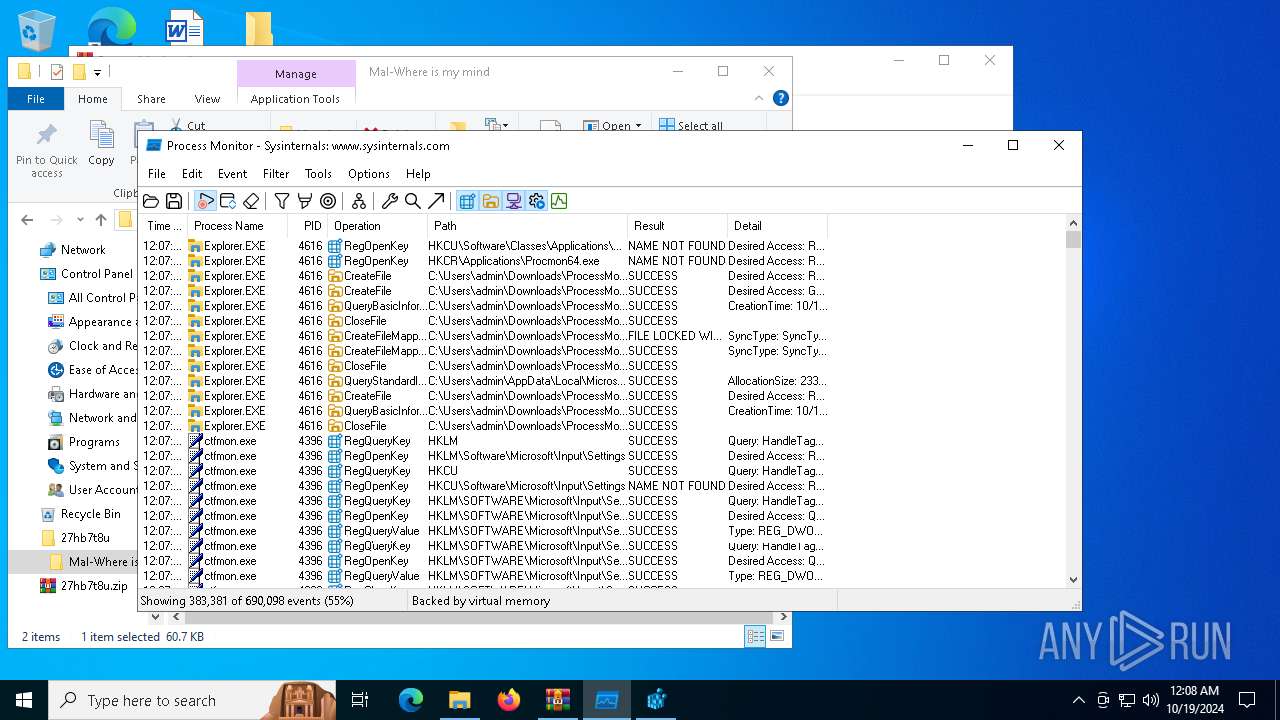
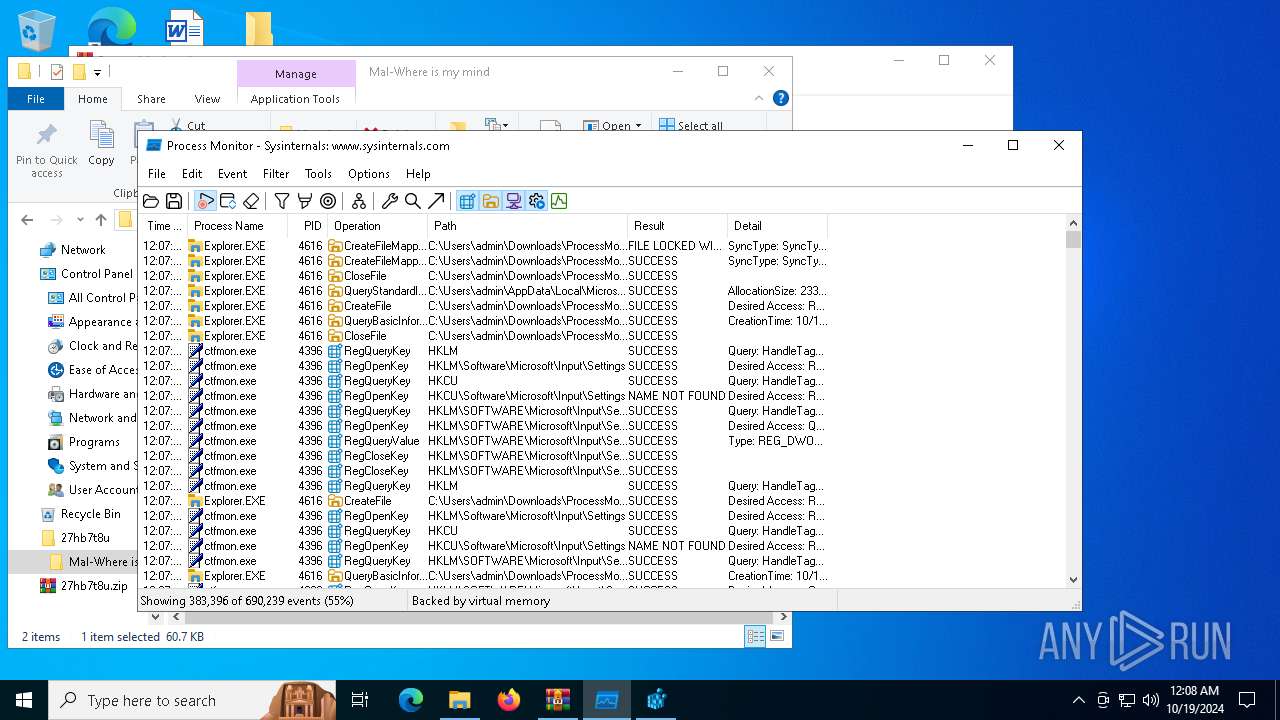
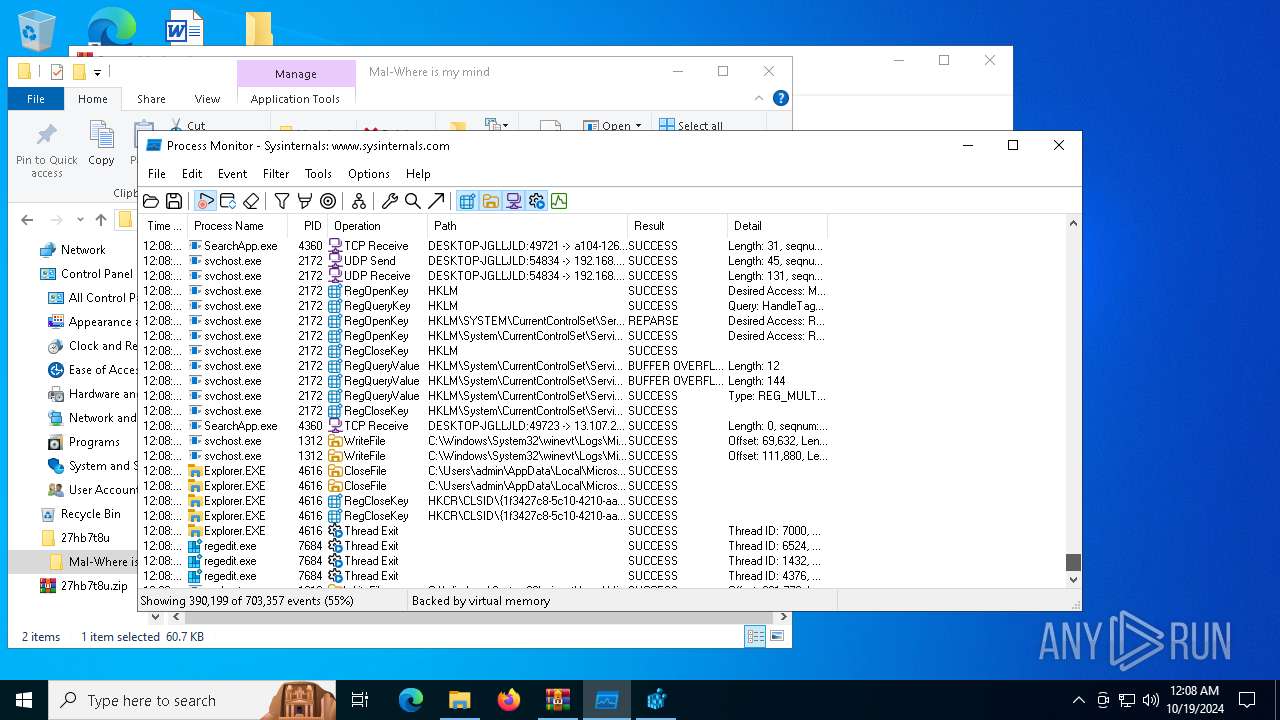
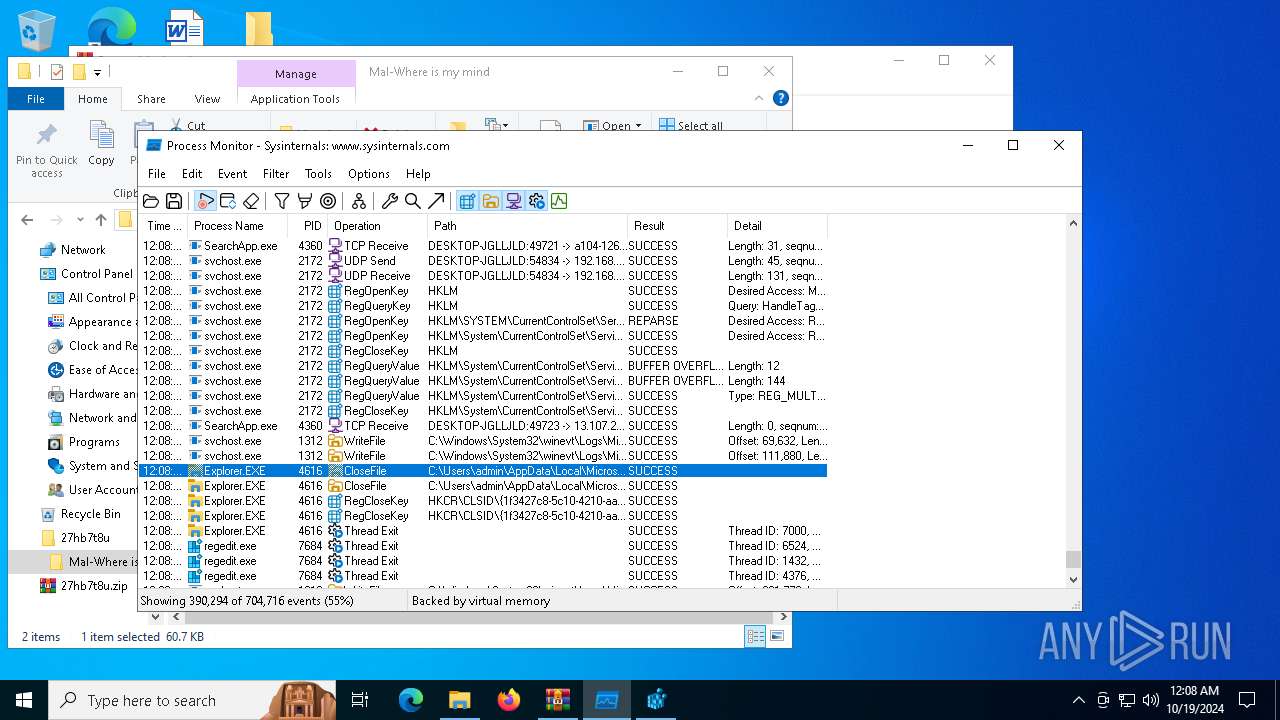
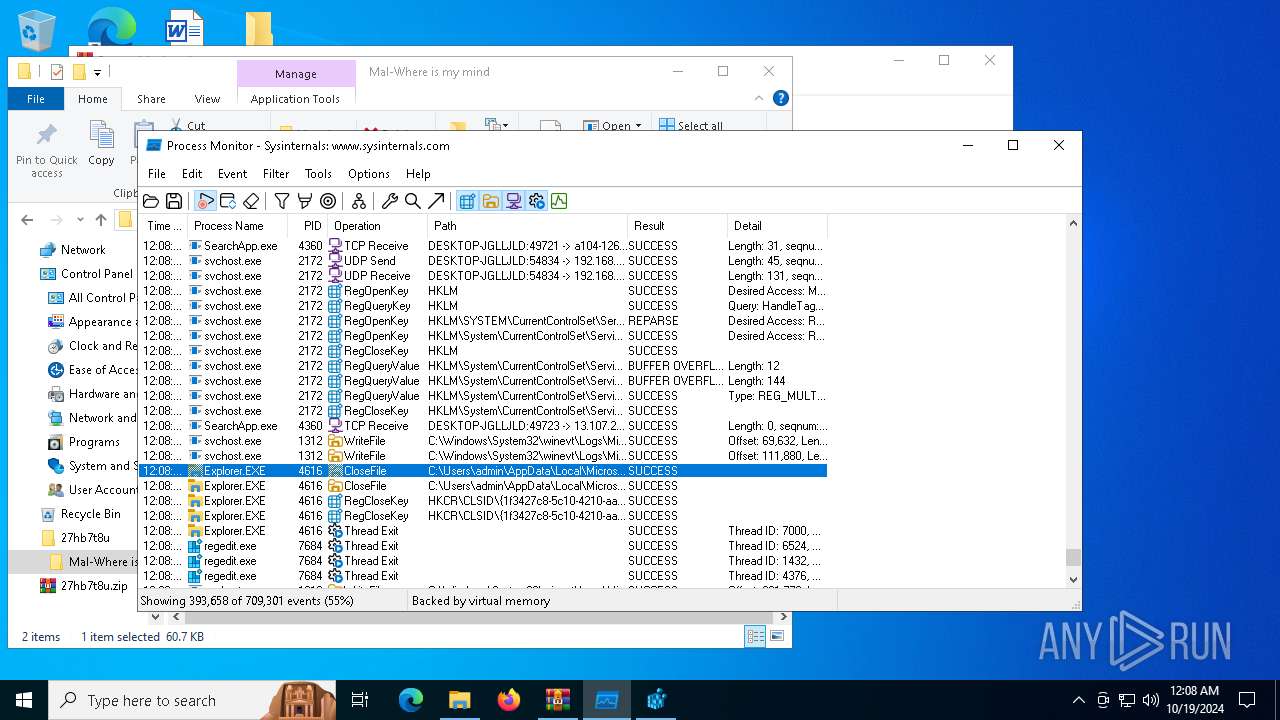
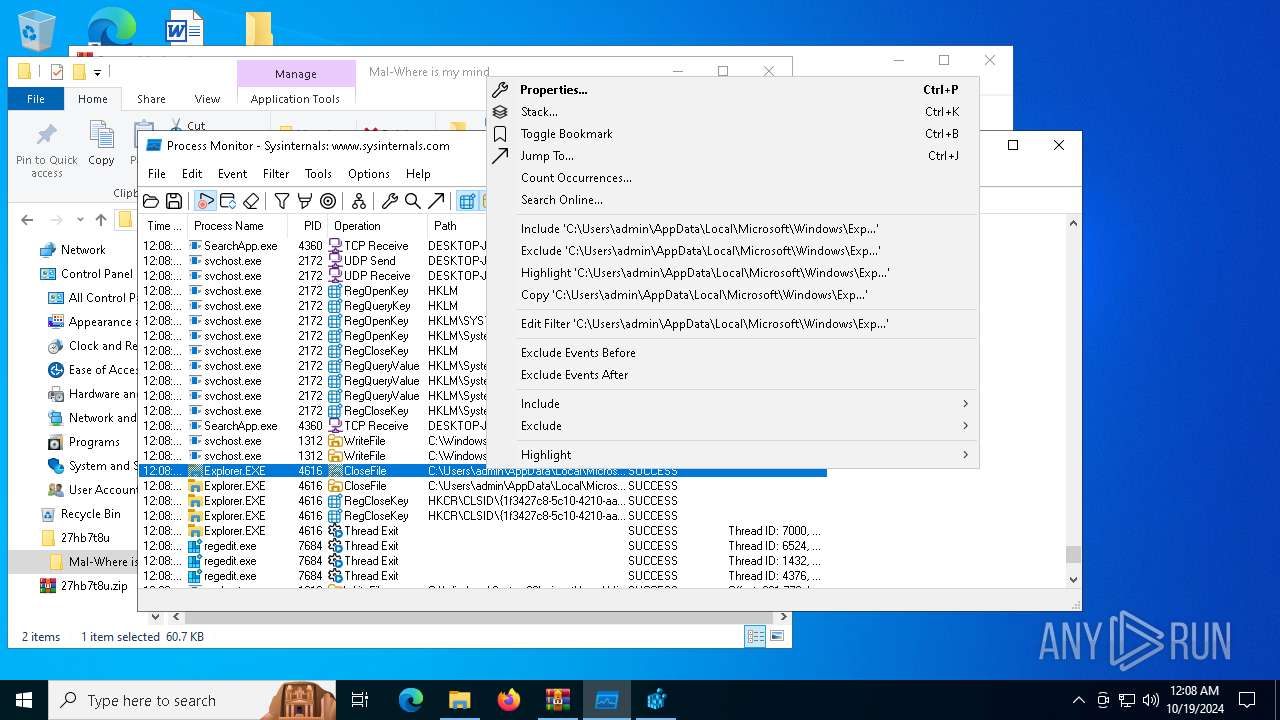
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
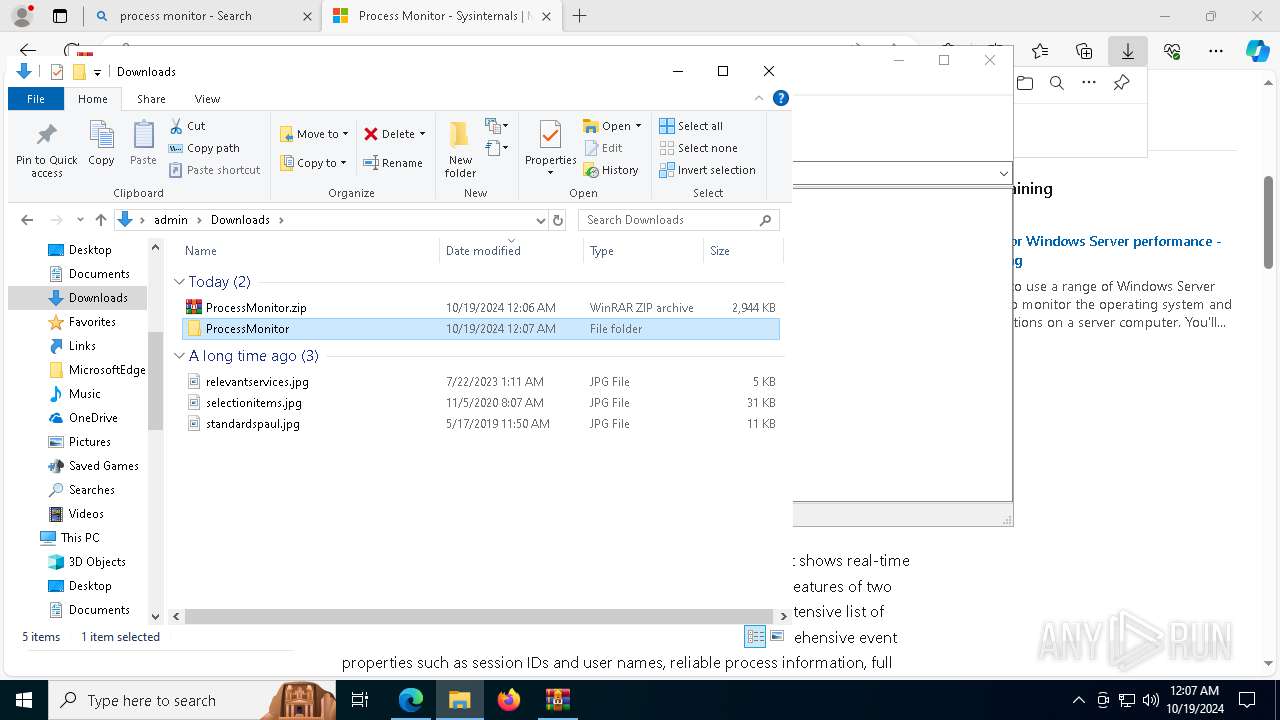
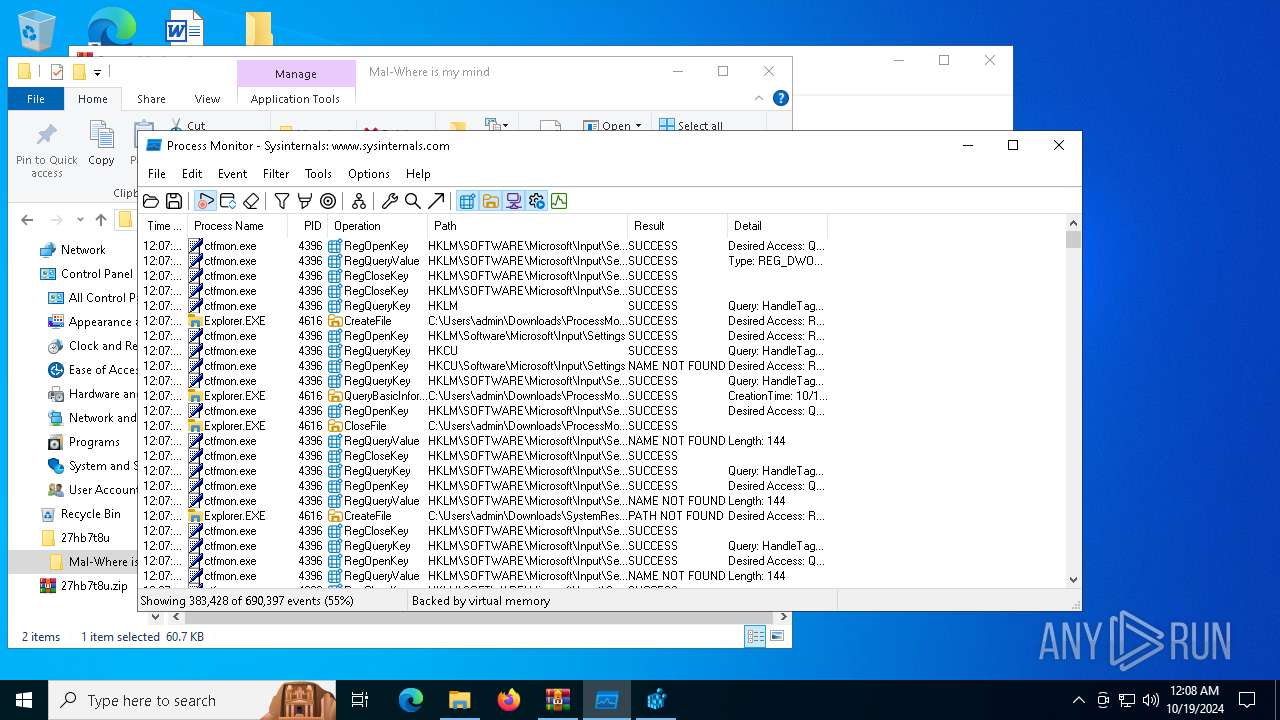
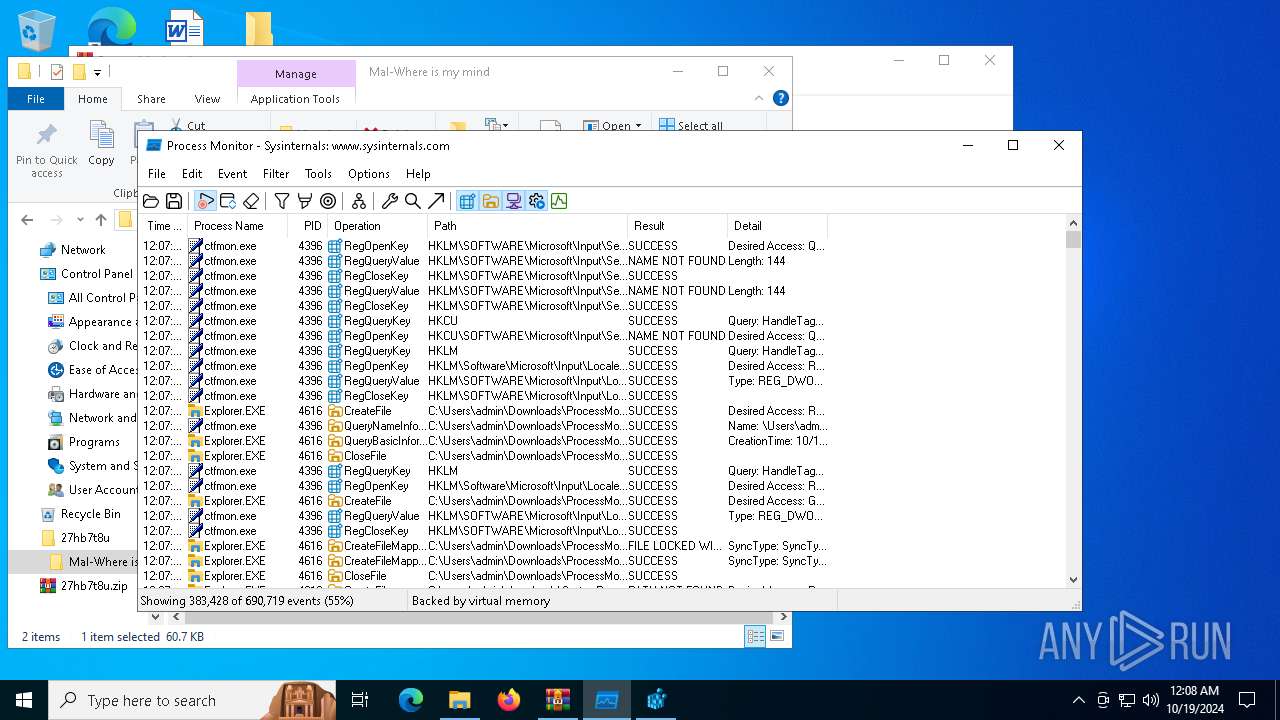
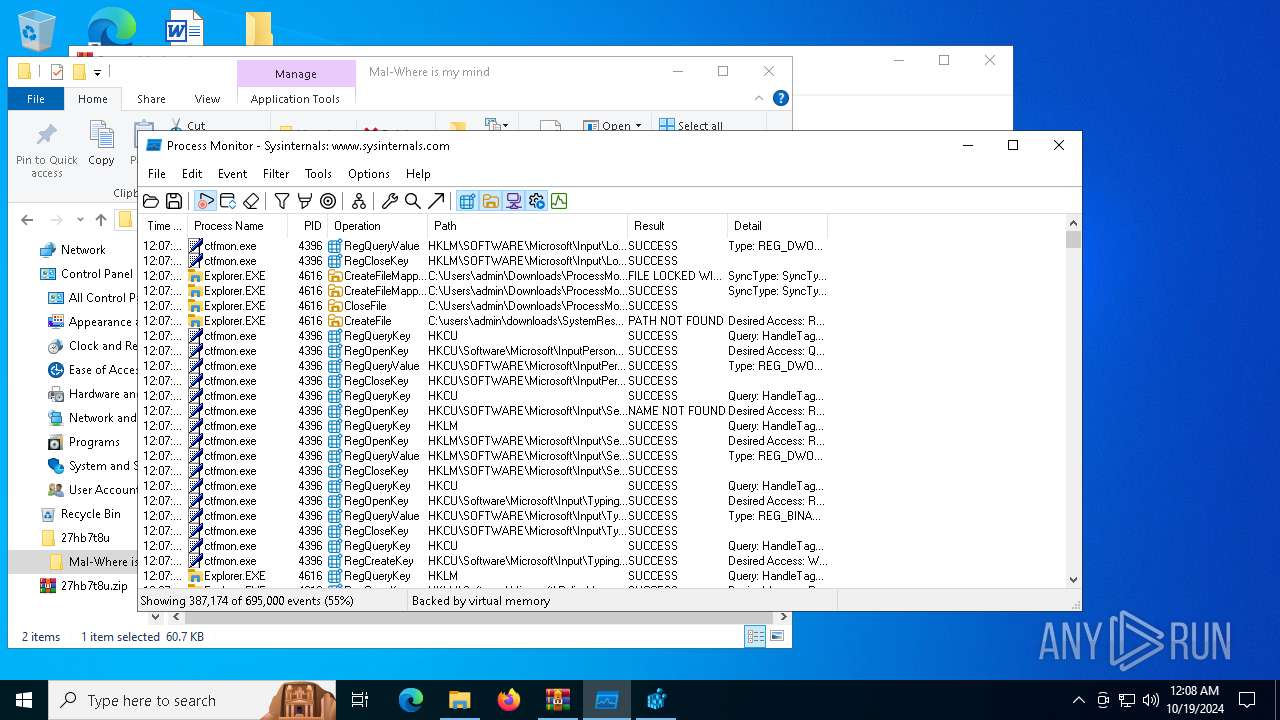
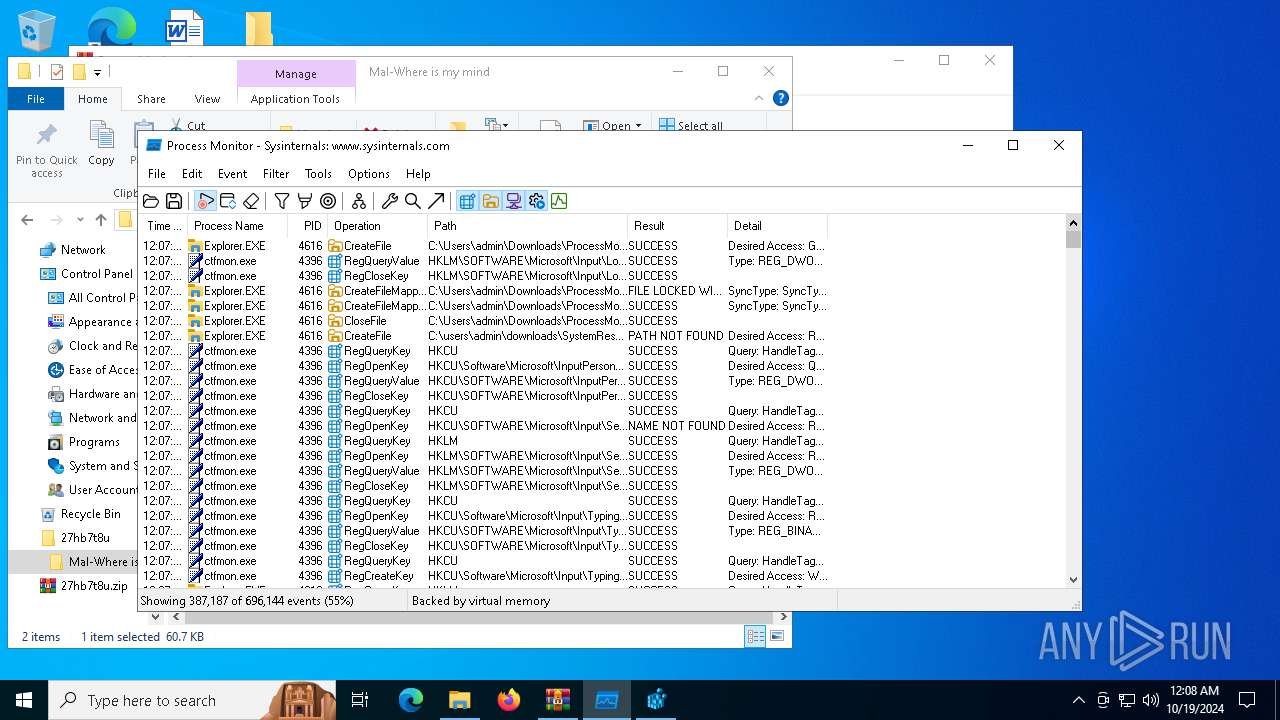
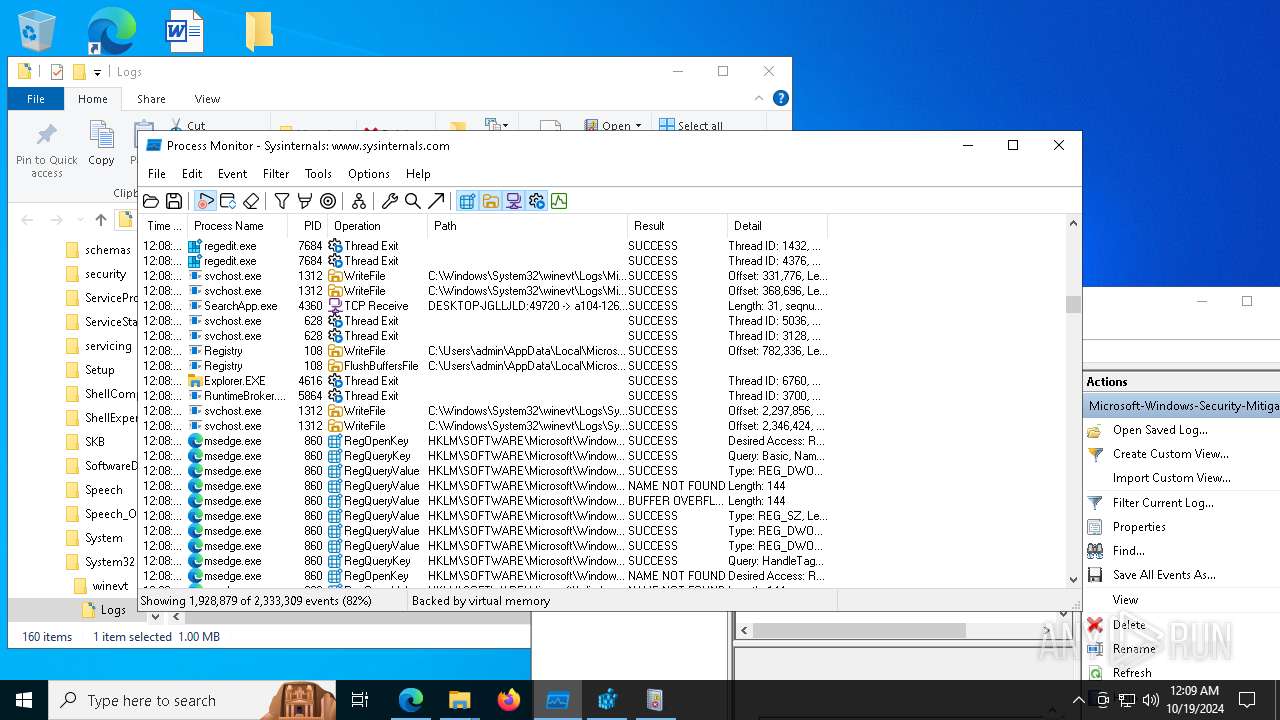
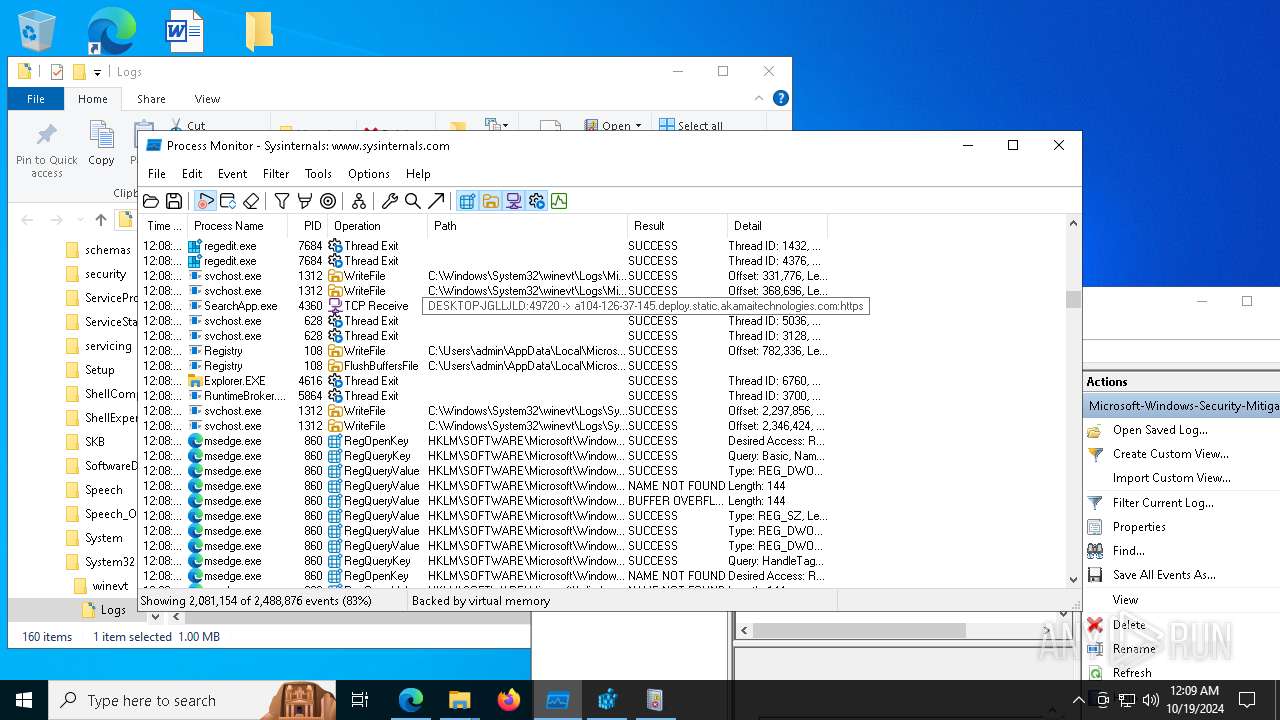
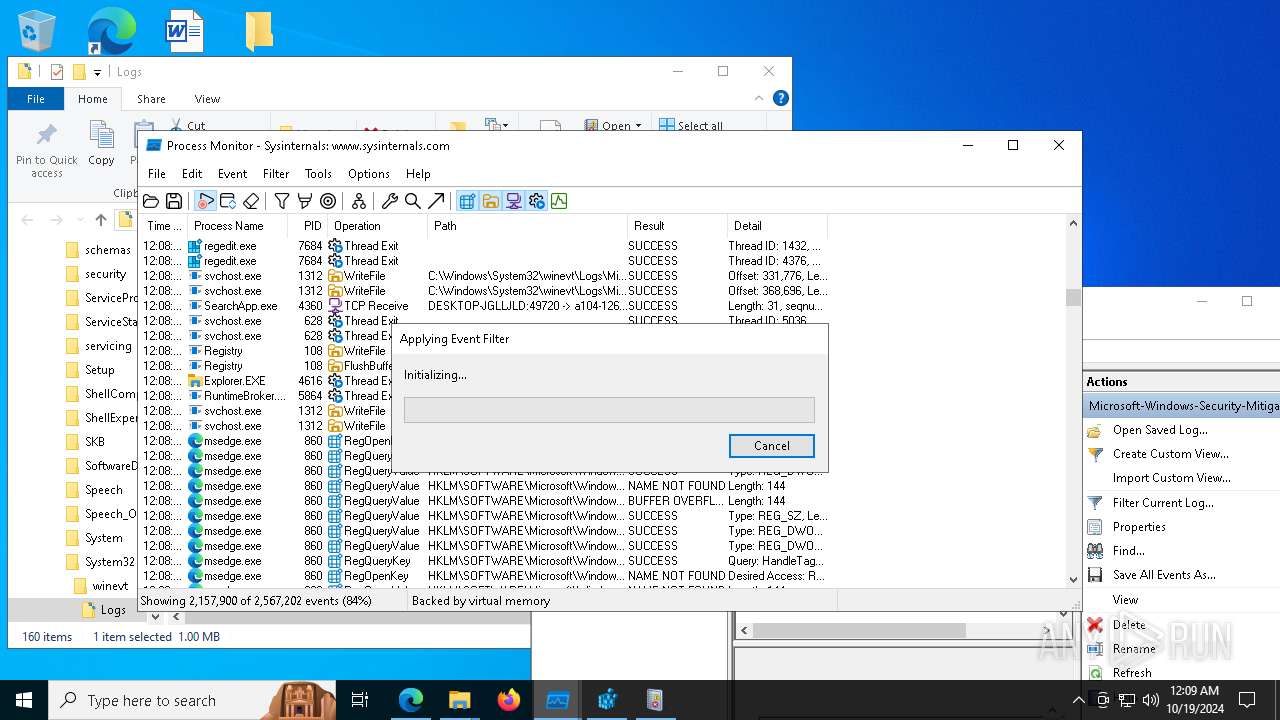
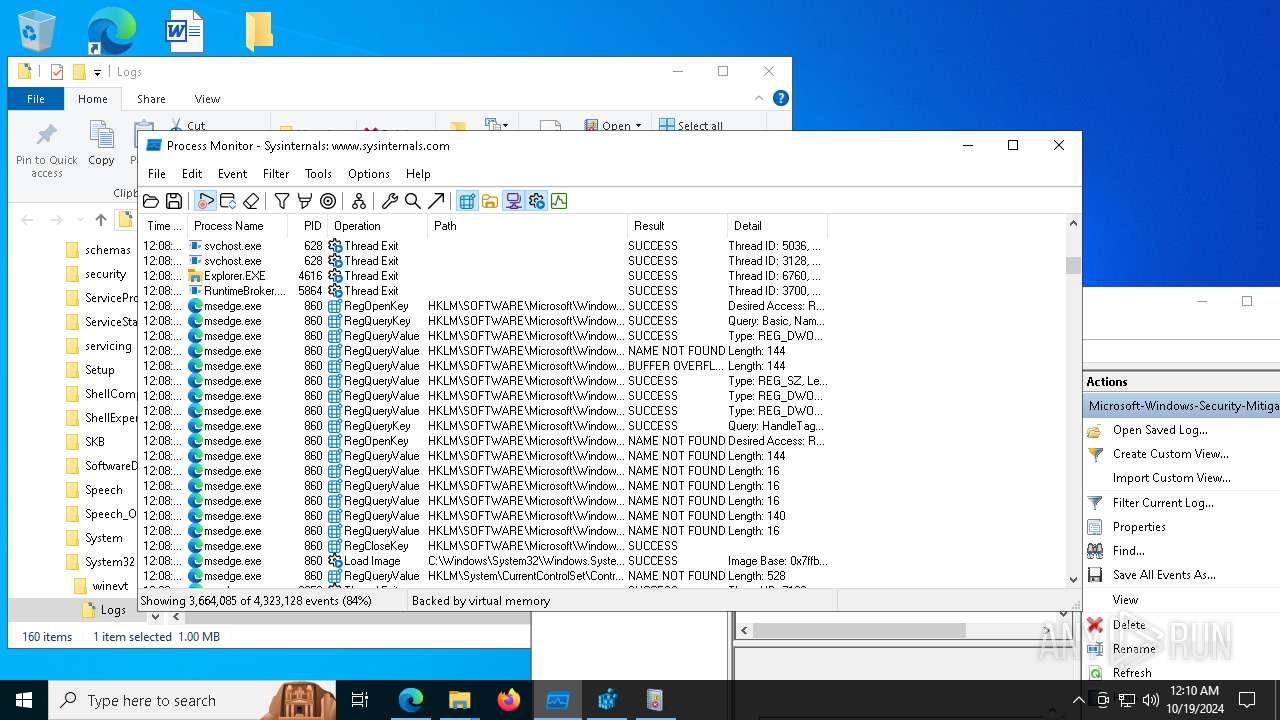
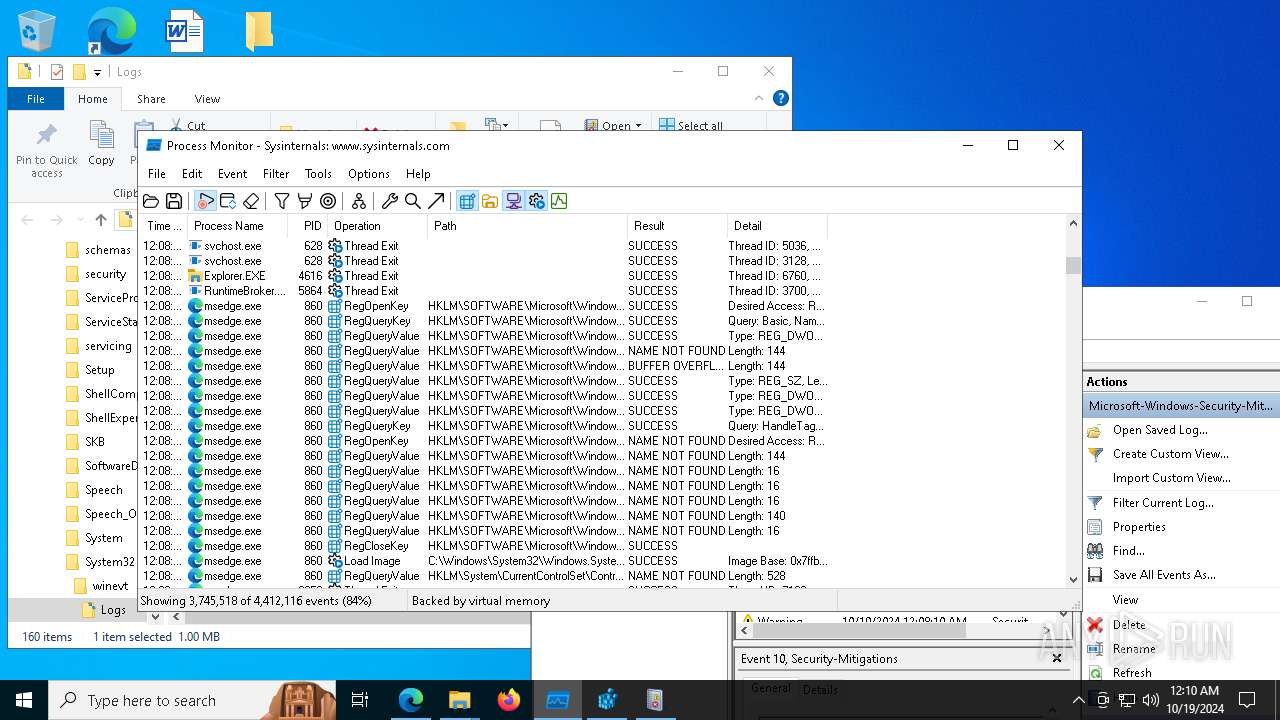
| 1168 | "C:\Users\admin\Downloads\ProcessMonitor\Procmon64.exe" | C:\Users\admin\Downloads\ProcessMonitor\Procmon64.exe | — | explorer.exe | |||||||||||
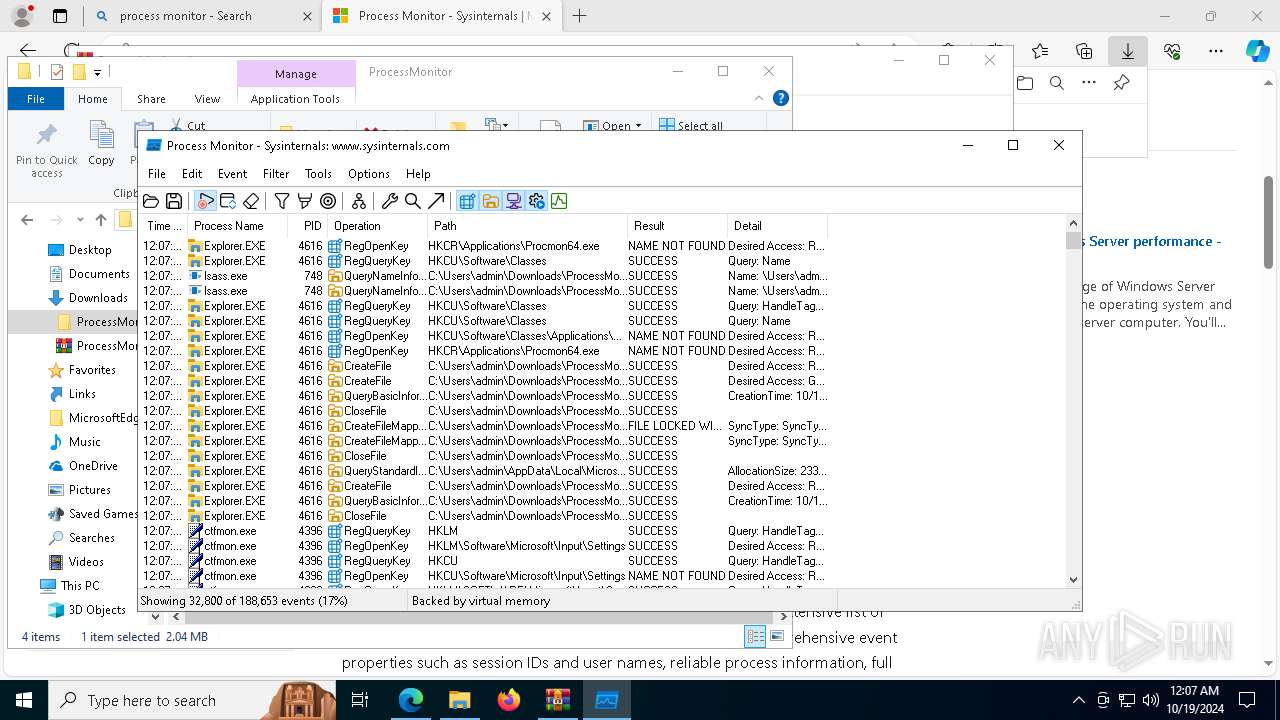
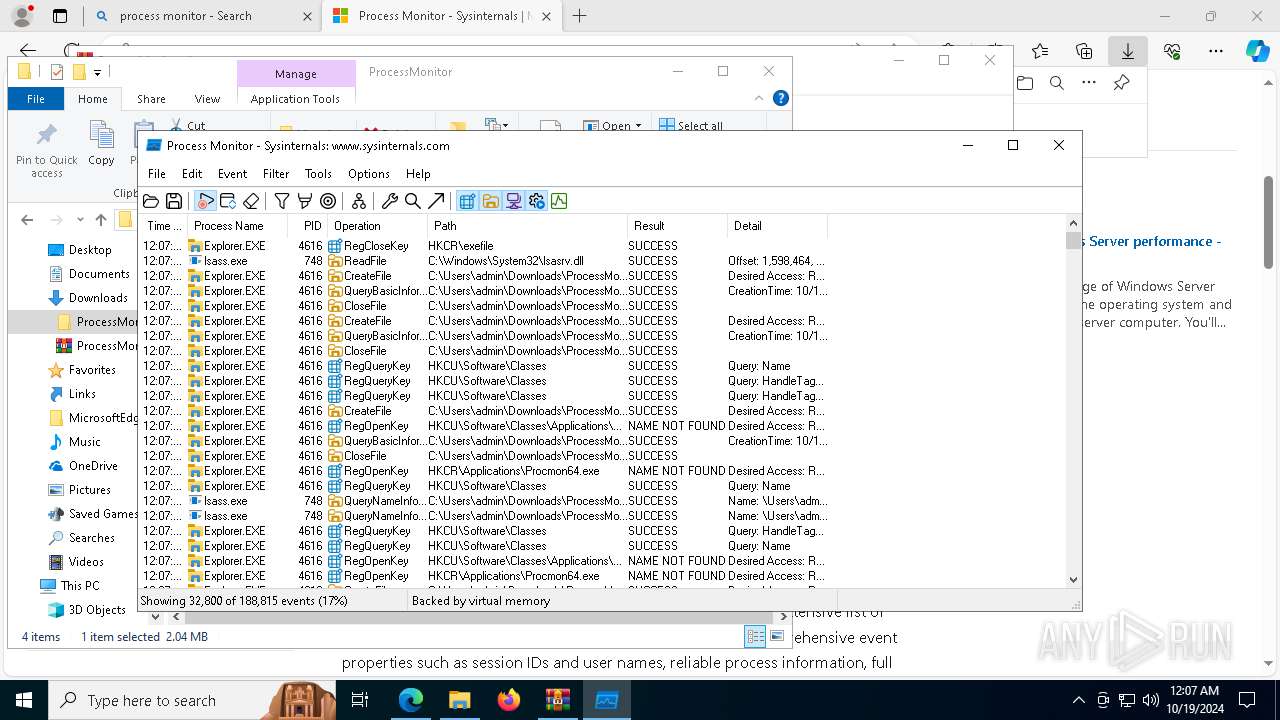
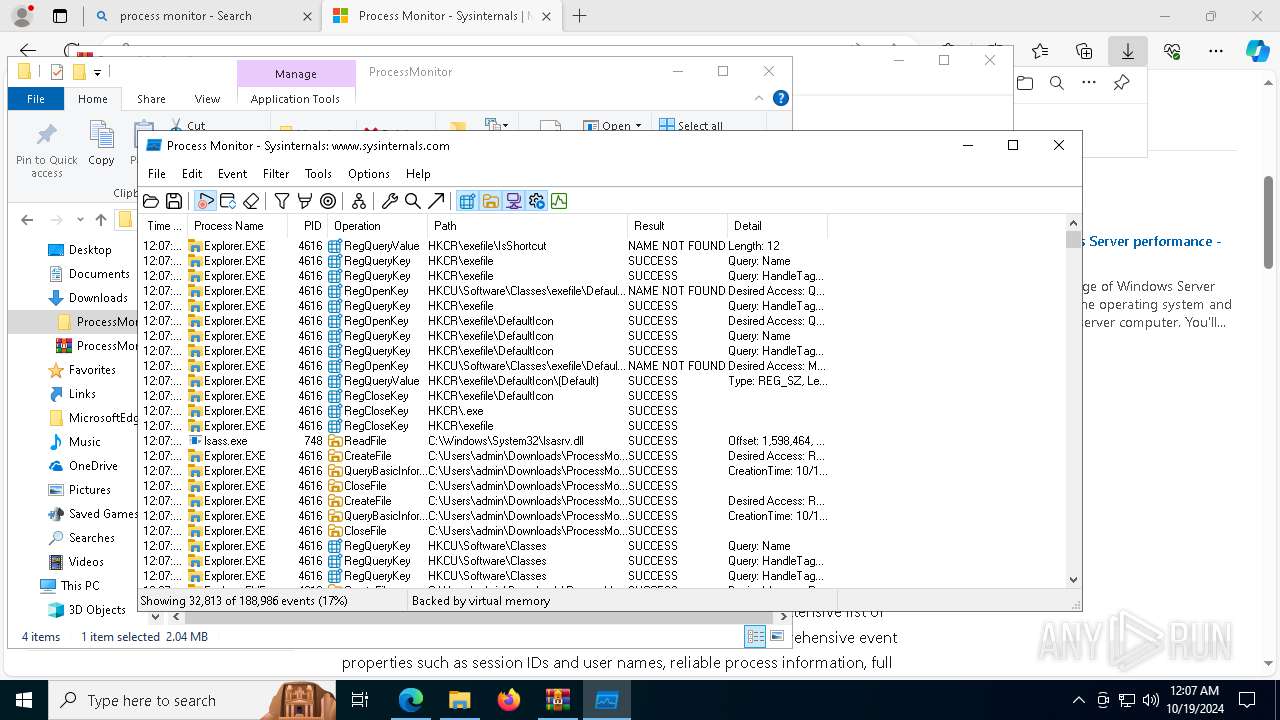
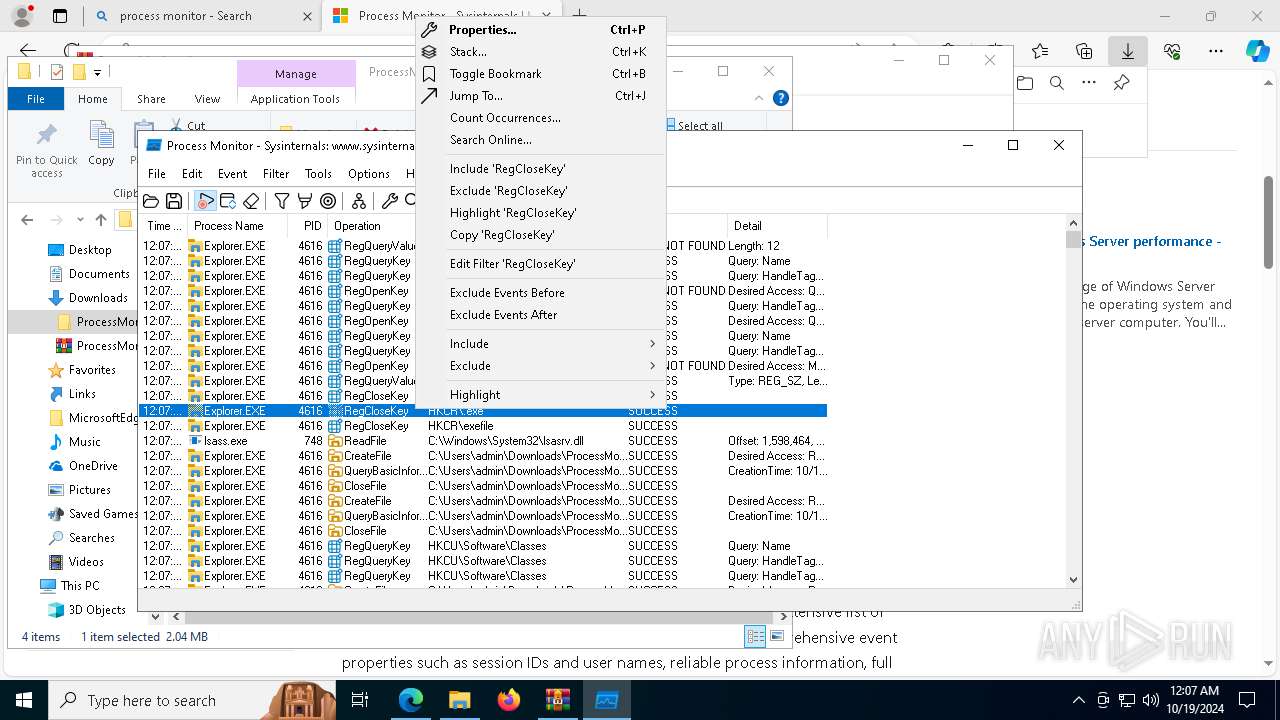
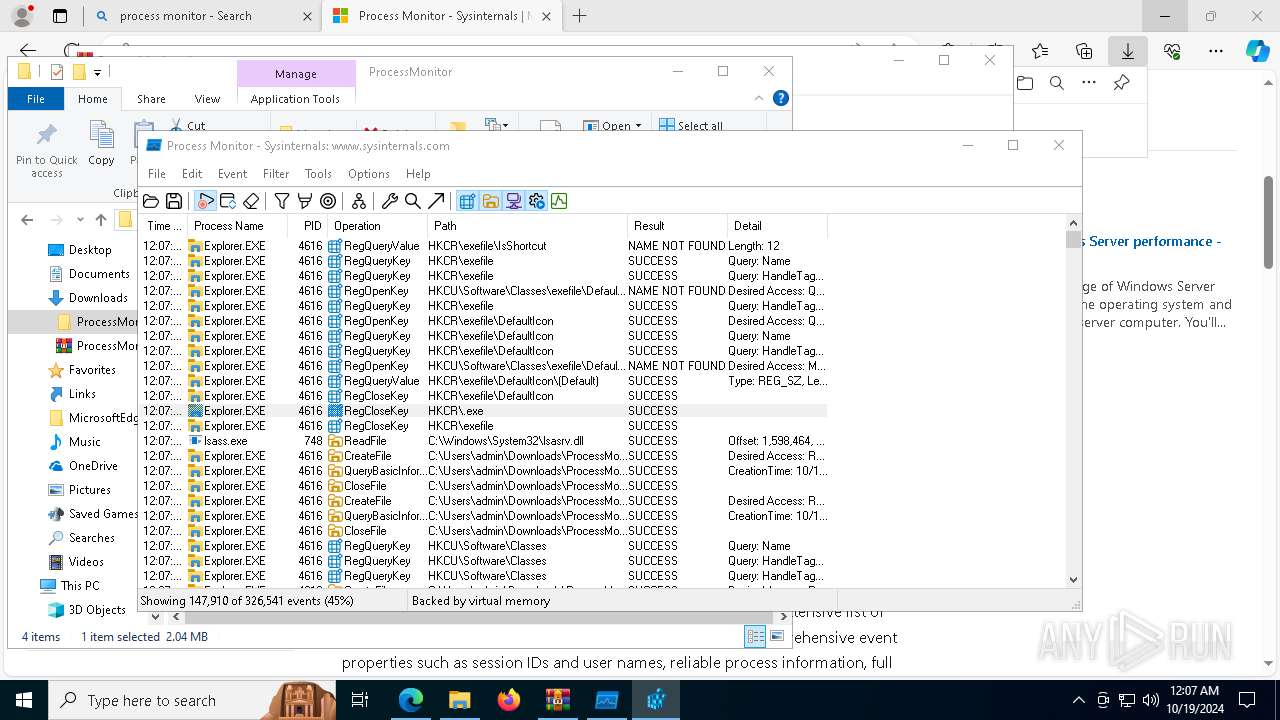
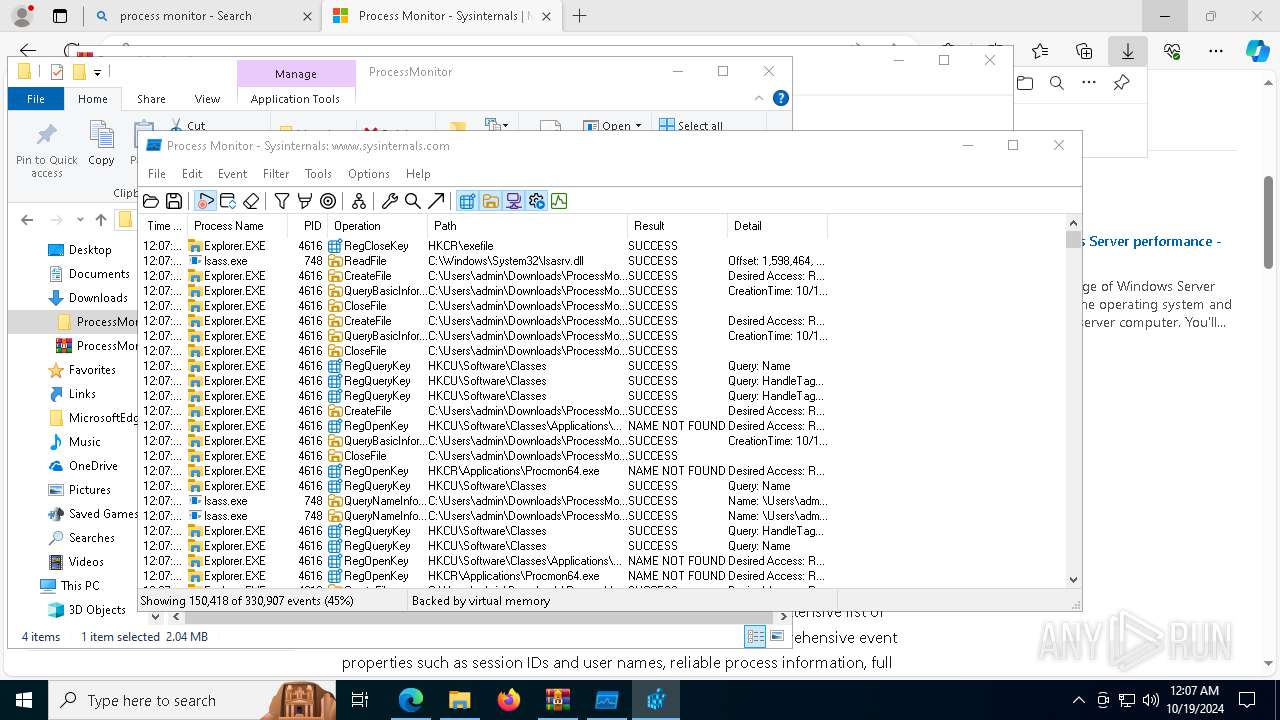
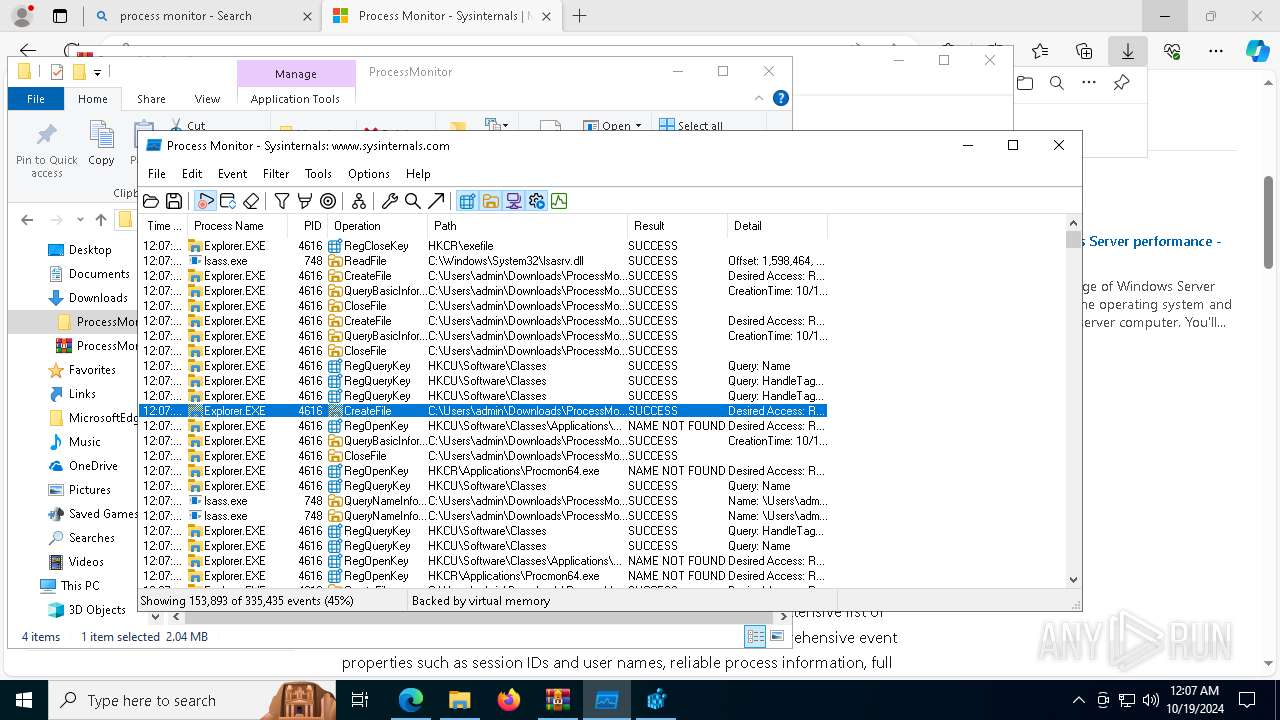
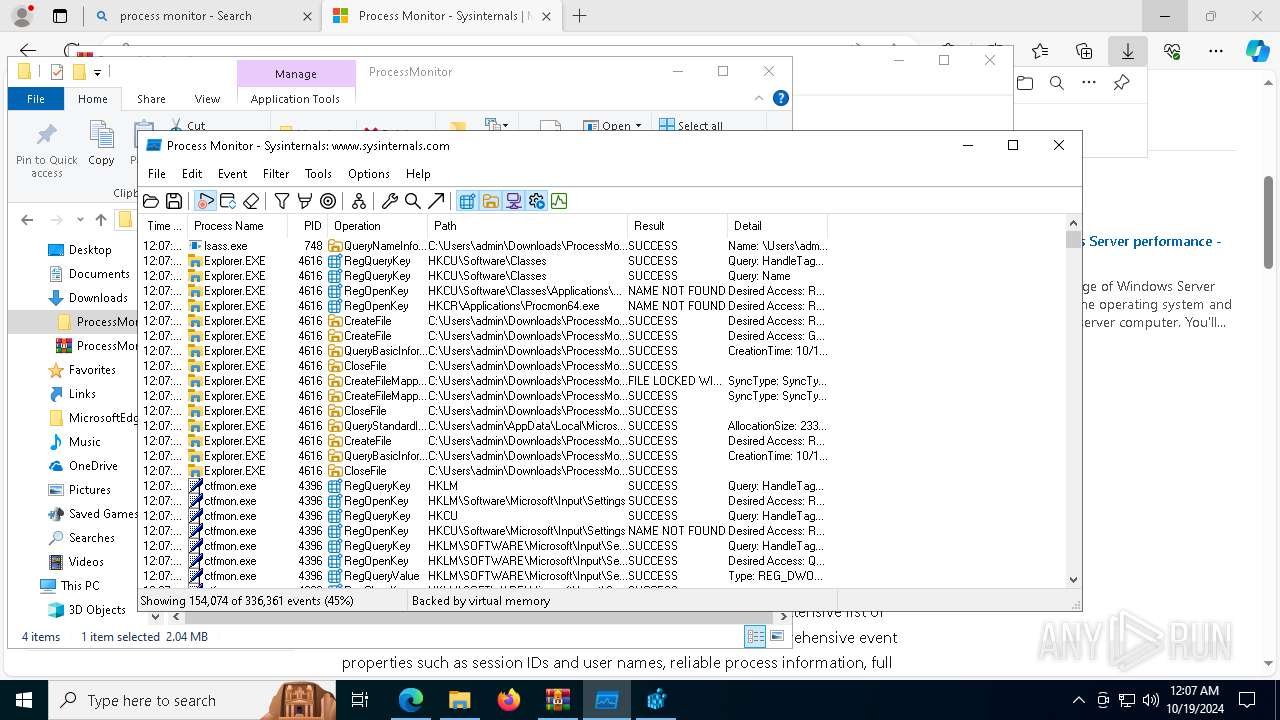
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Process Monitor Version: 4.01 Modules
| |||||||||||||||
| 2236 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) | |||||||||||||||
| 2432 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\27hb7t8u.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
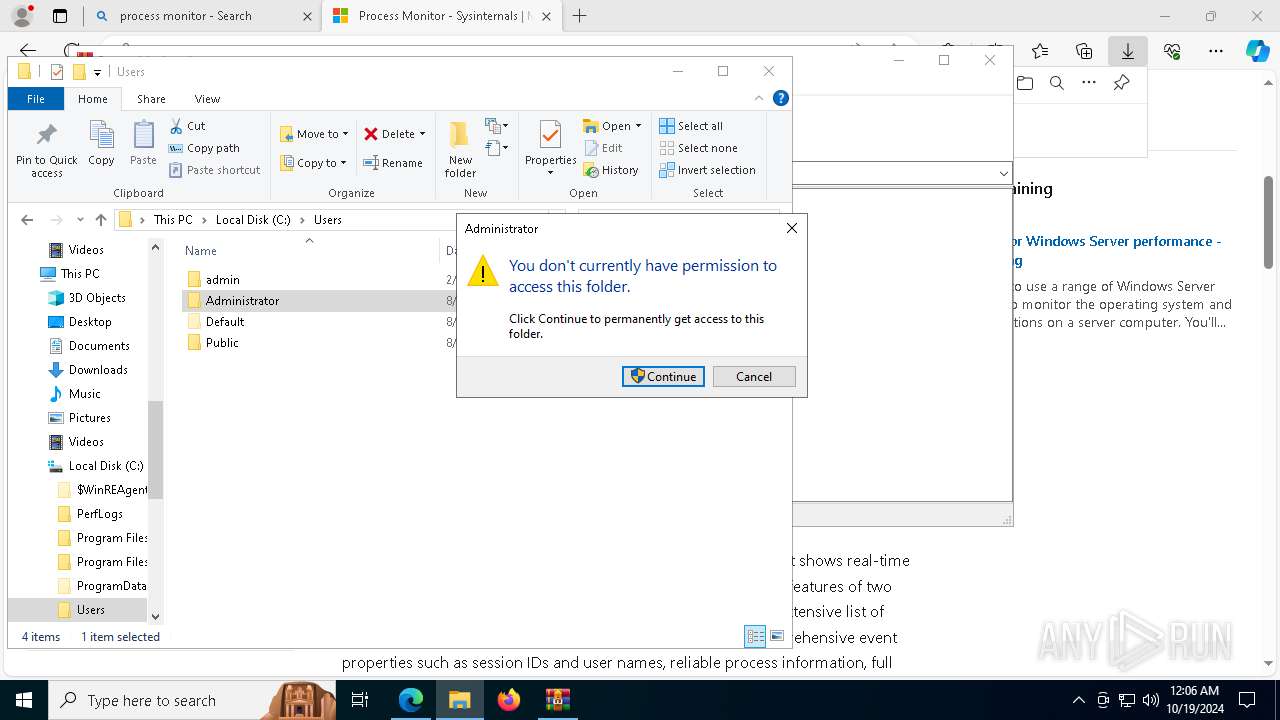
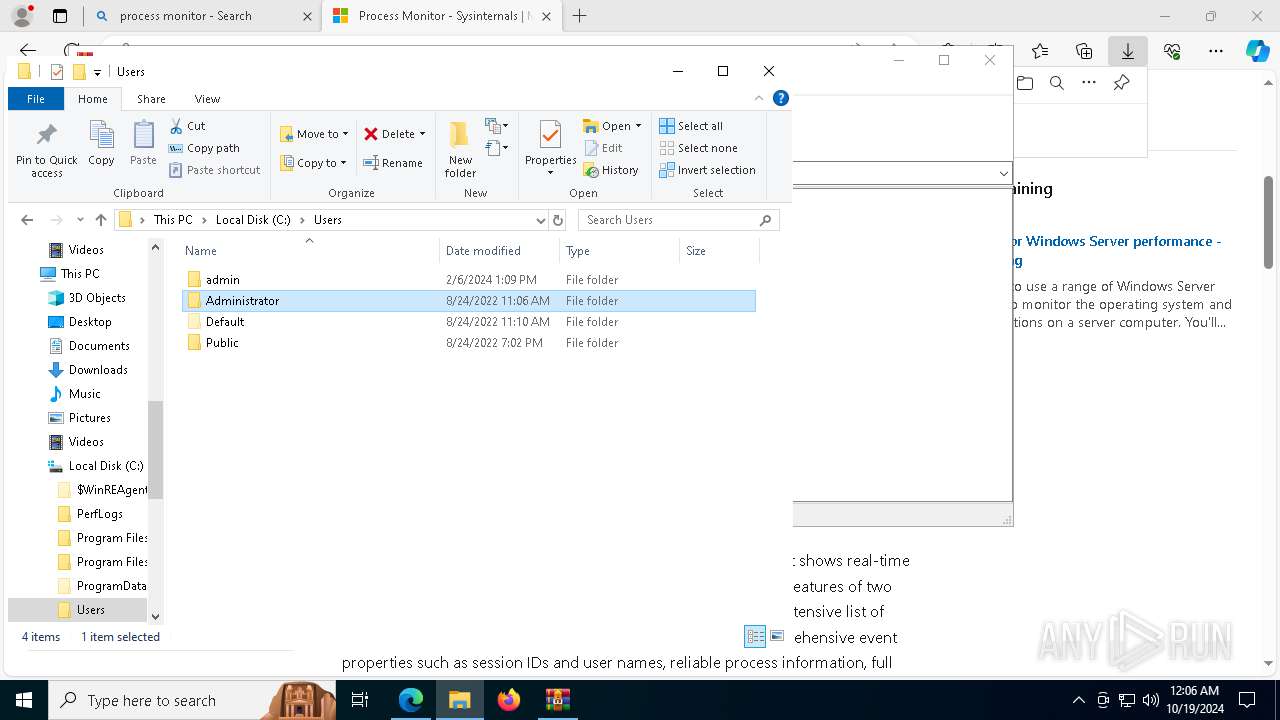
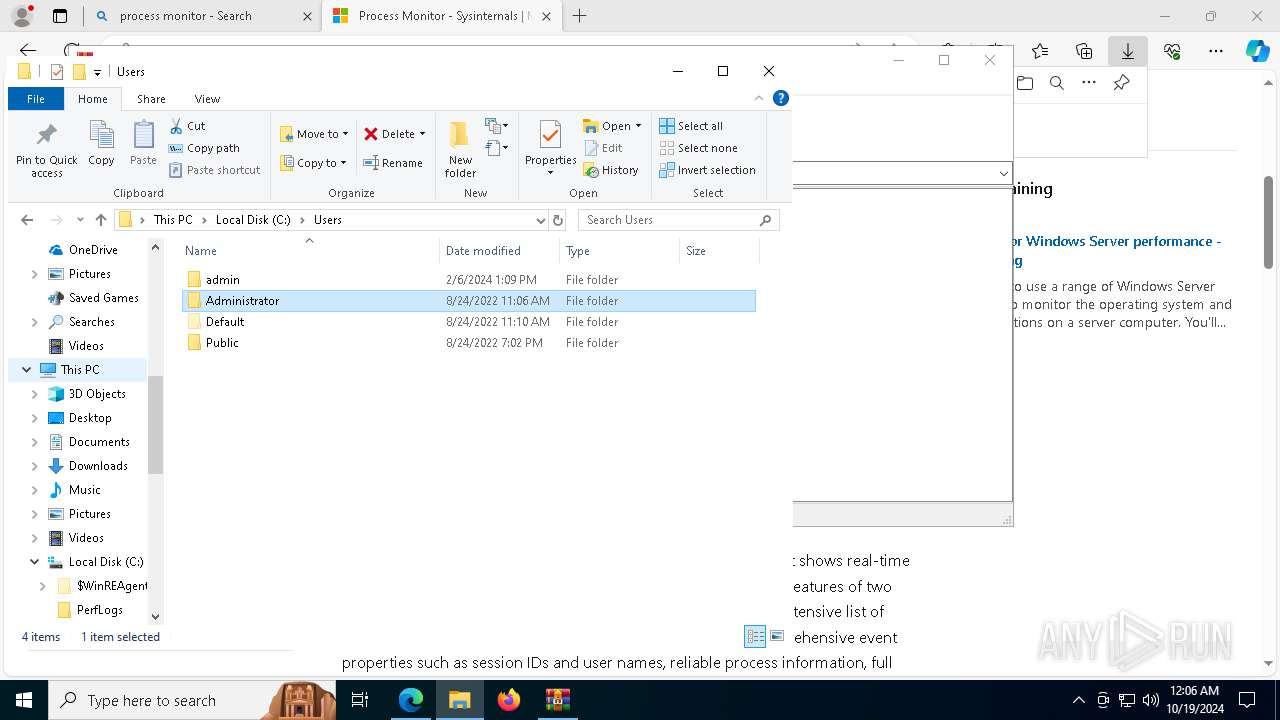
| 4260 | "C:\Users\admin\Desktop\27hb7t8u\Mal-Where is my mind\Deadface_RAT.exe" | C:\Users\admin\Desktop\27hb7t8u\Mal-Where is my mind\Deadface_RAT.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 | |||||||||||||||
| 4308 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6324 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\27hb7t8u.zip" C:\Users\admin\Desktop\27hb7t8u\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6520 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\ProcessMonitor.zip" C:\Users\admin\Downloads\ProcessMonitor\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6800 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) | |||||||||||||||
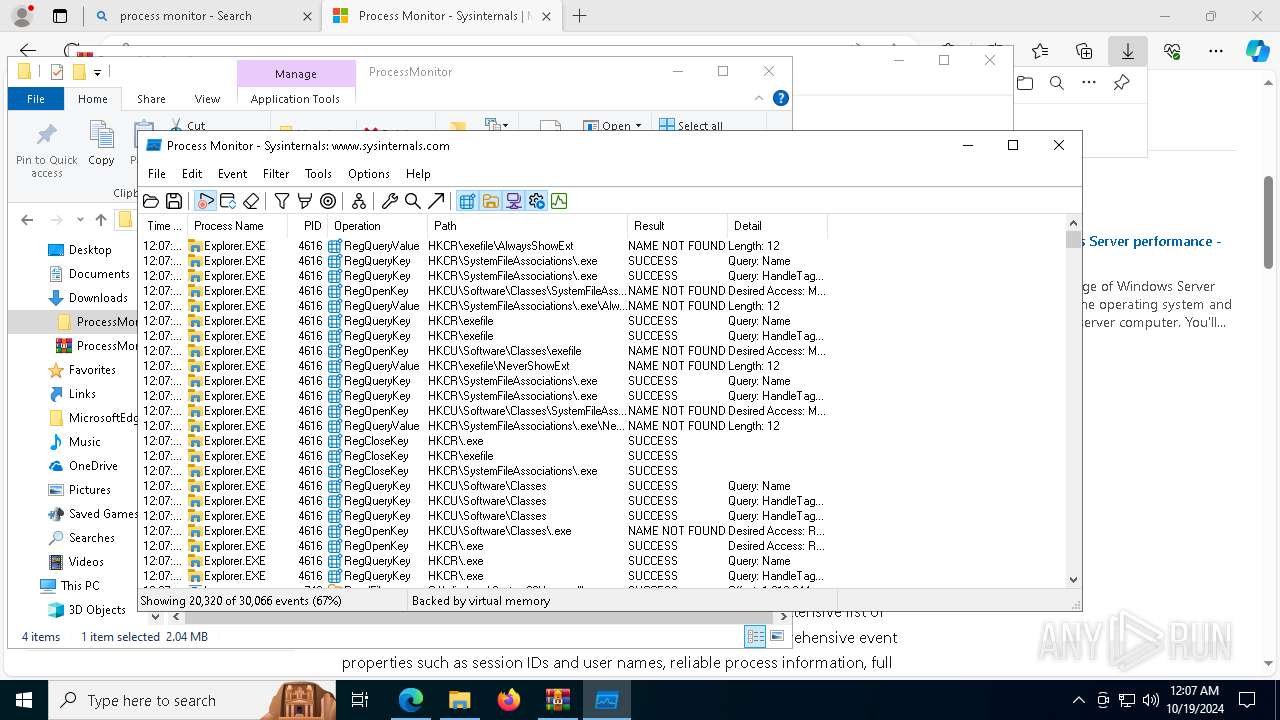
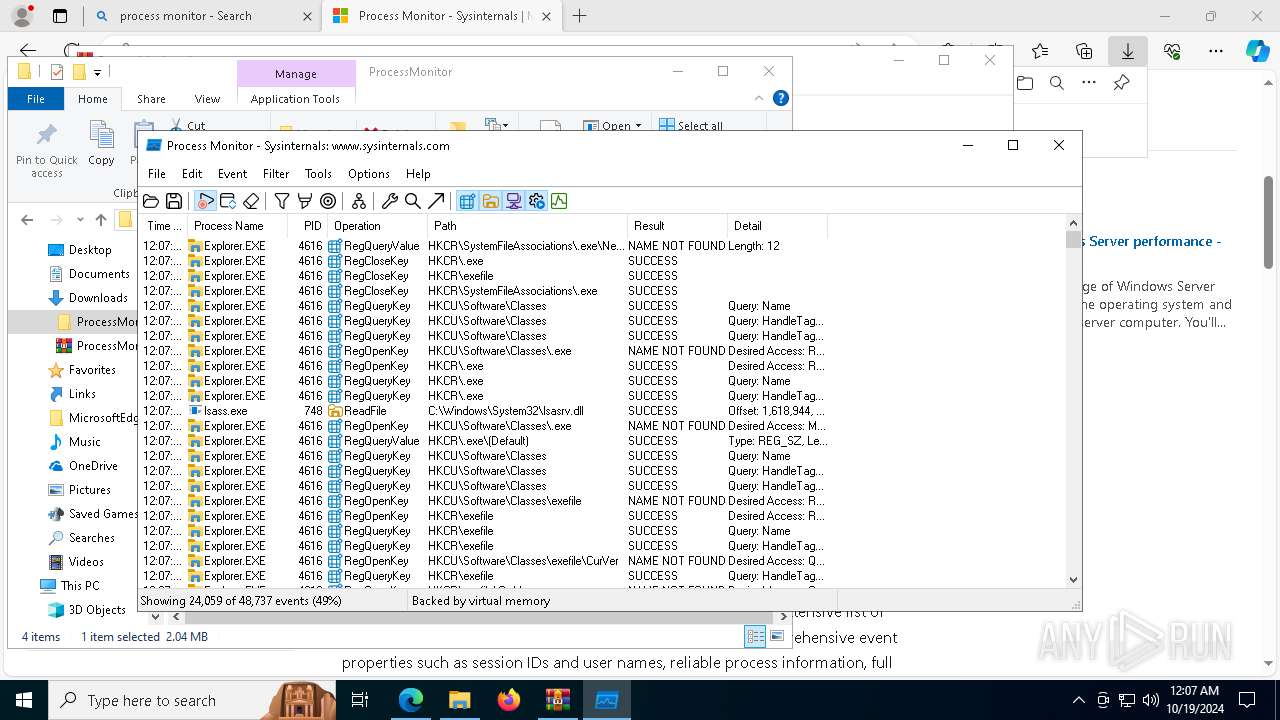
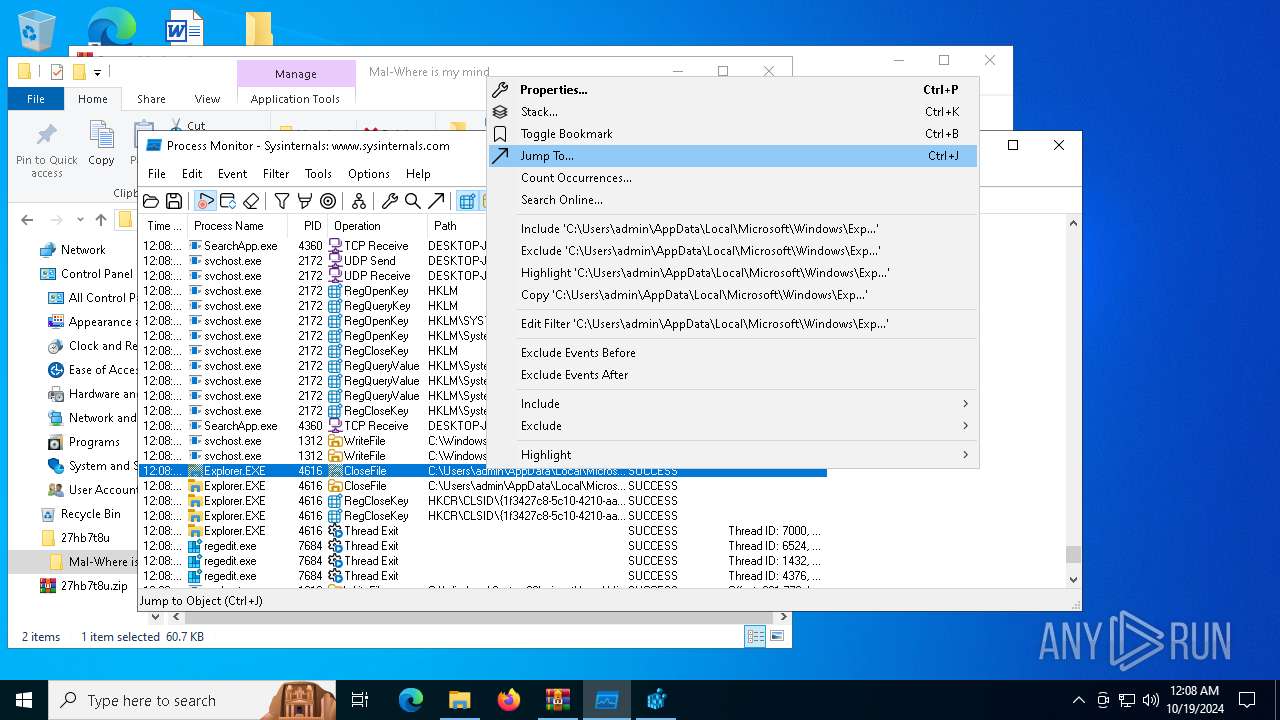
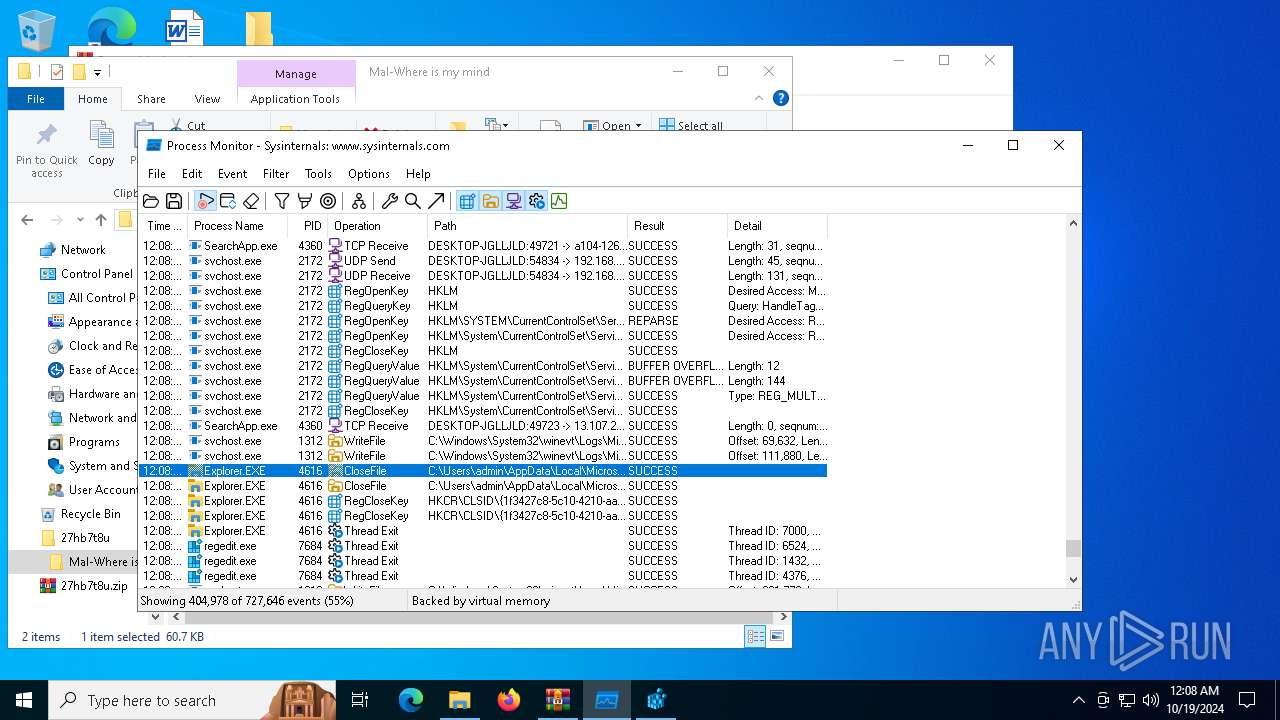
| 7080 | "C:\Users\admin\Downloads\ProcessMonitor\Procmon64.exe" | C:\Users\admin\Downloads\ProcessMonitor\Procmon64.exe | Procmon64.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Process Monitor Version: 4.01 Modules
| |||||||||||||||
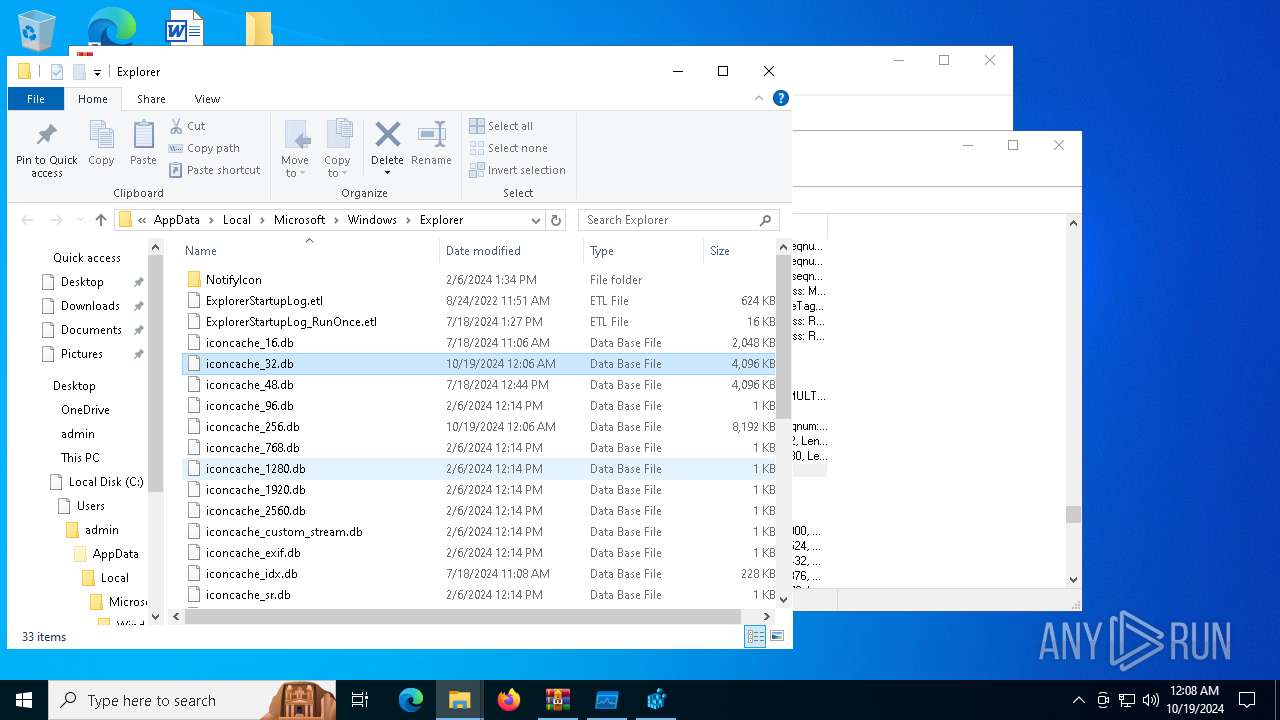
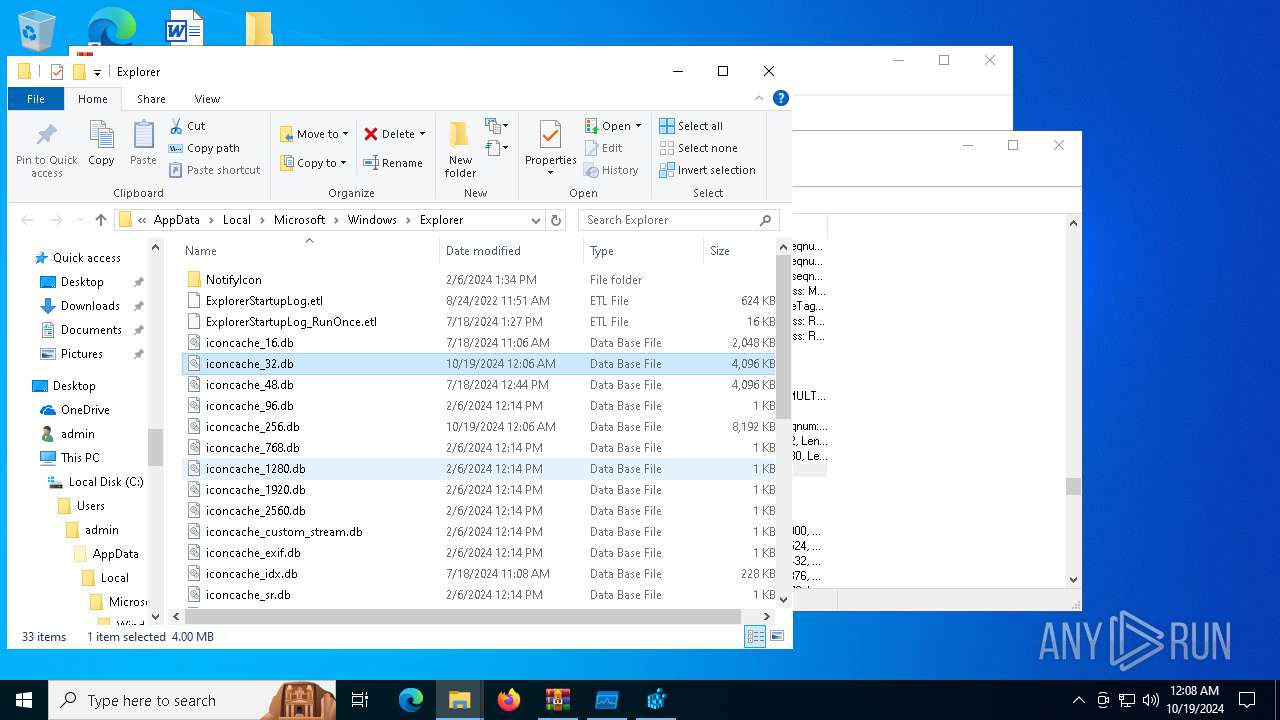
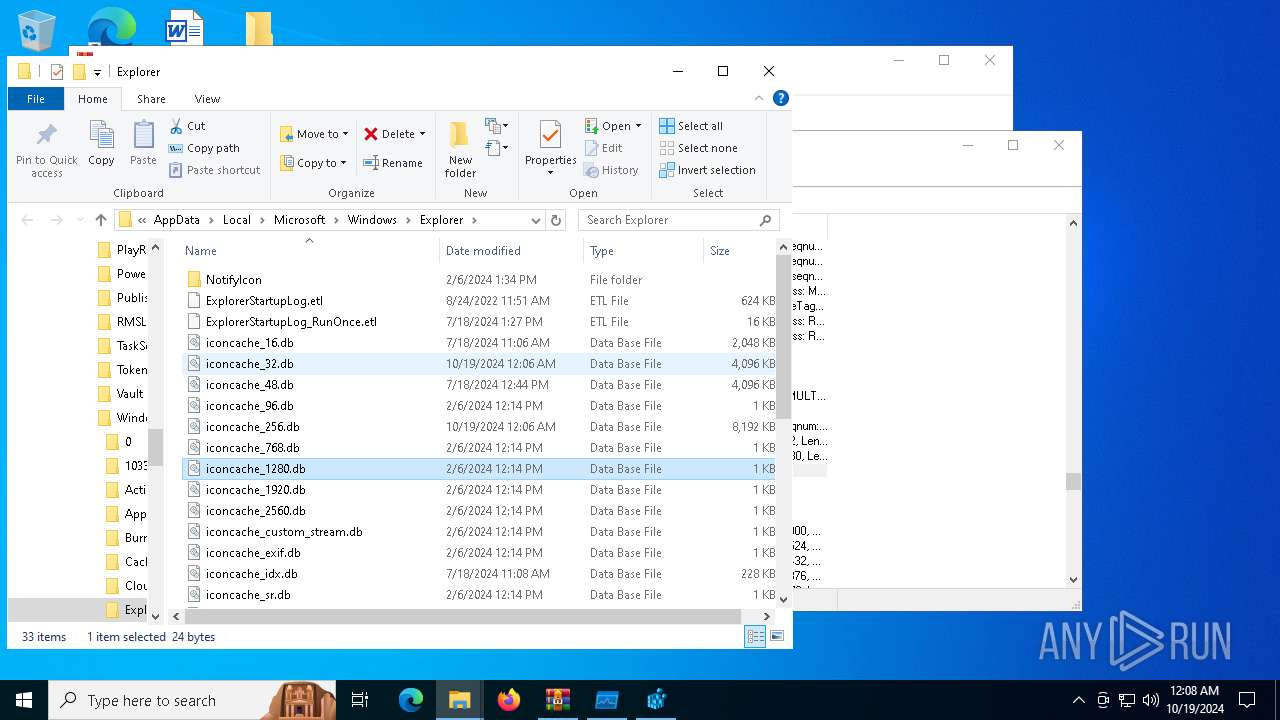
| 7256 | explorer /select,C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\iconcache_32.db | C:\Windows\explorer.exe | — | Procmon64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) | |||||||||||||||
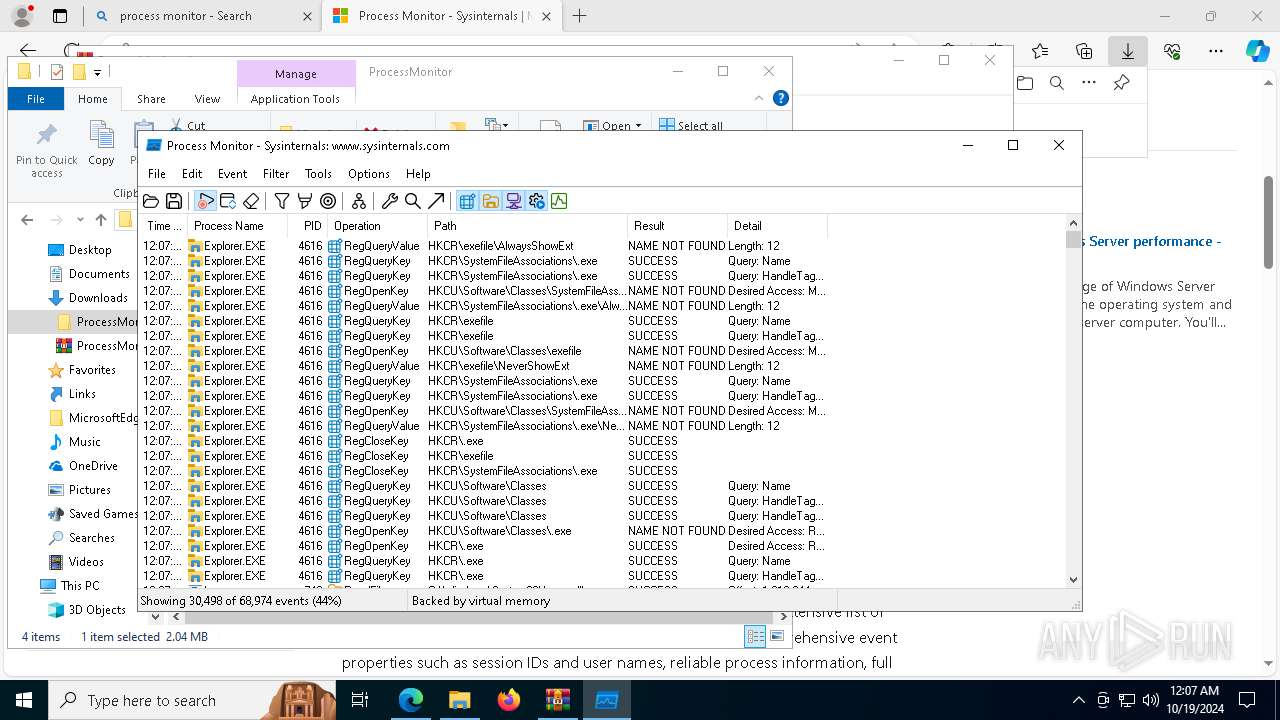
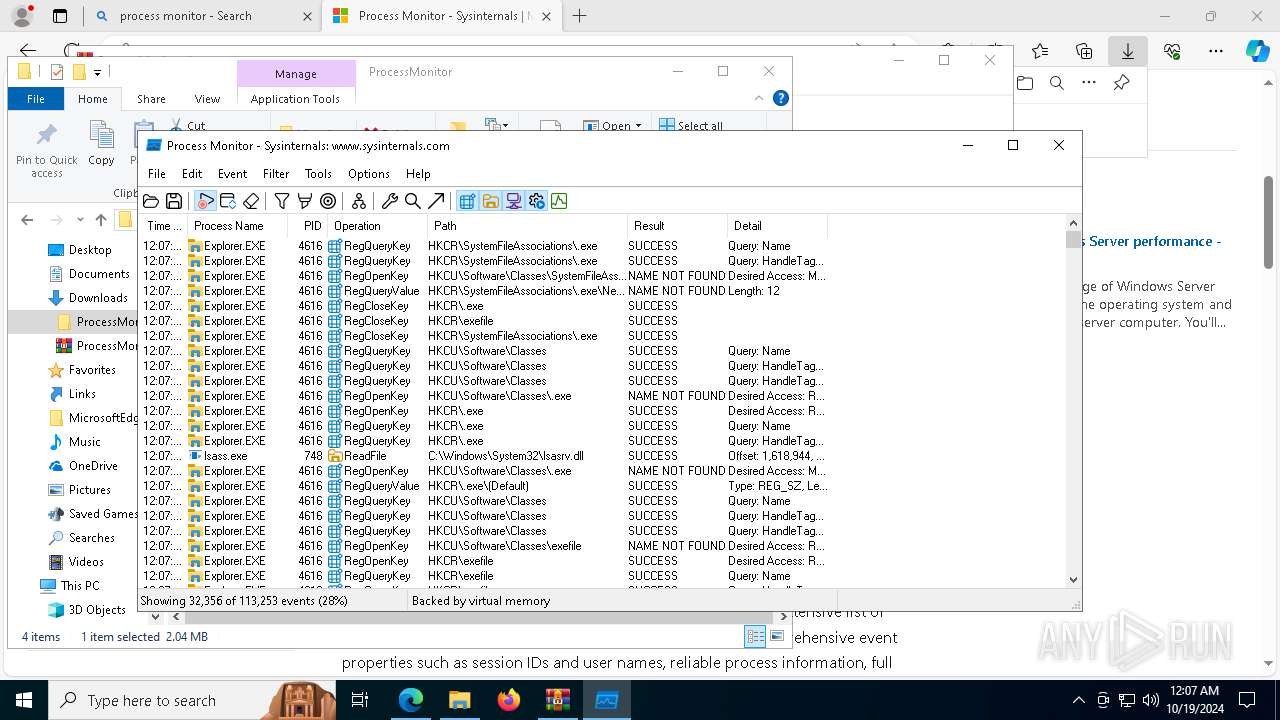
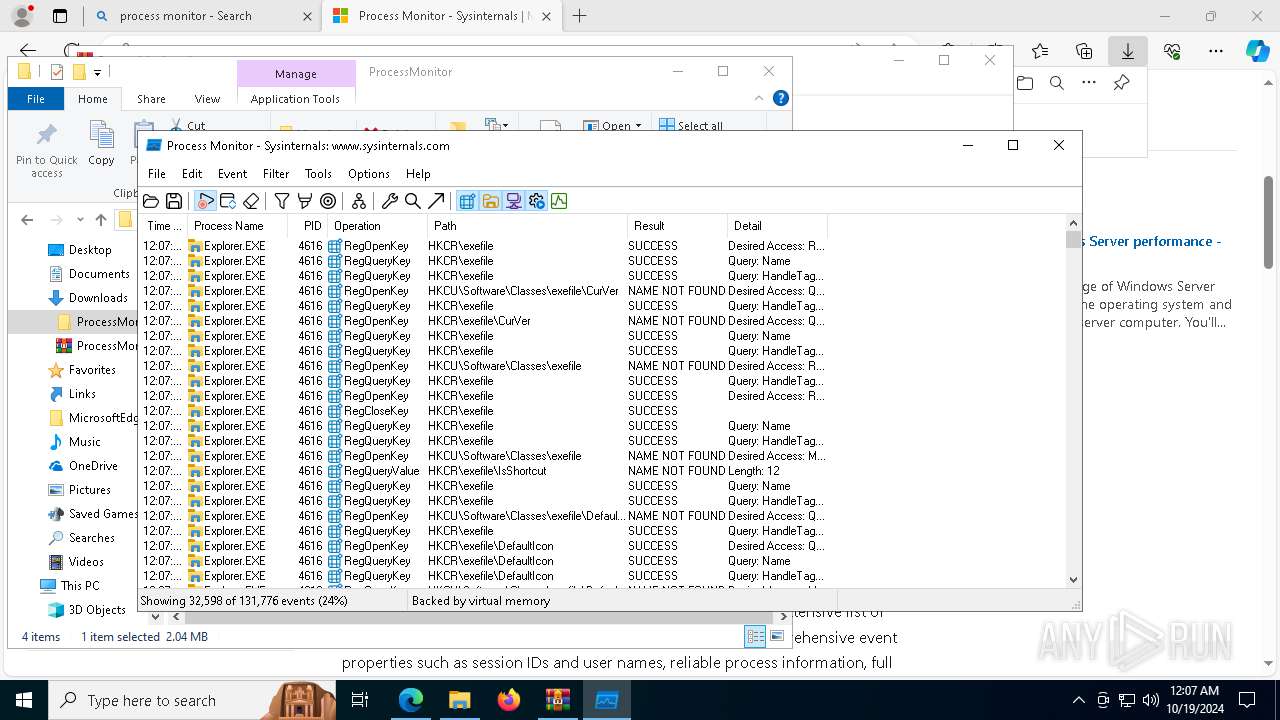
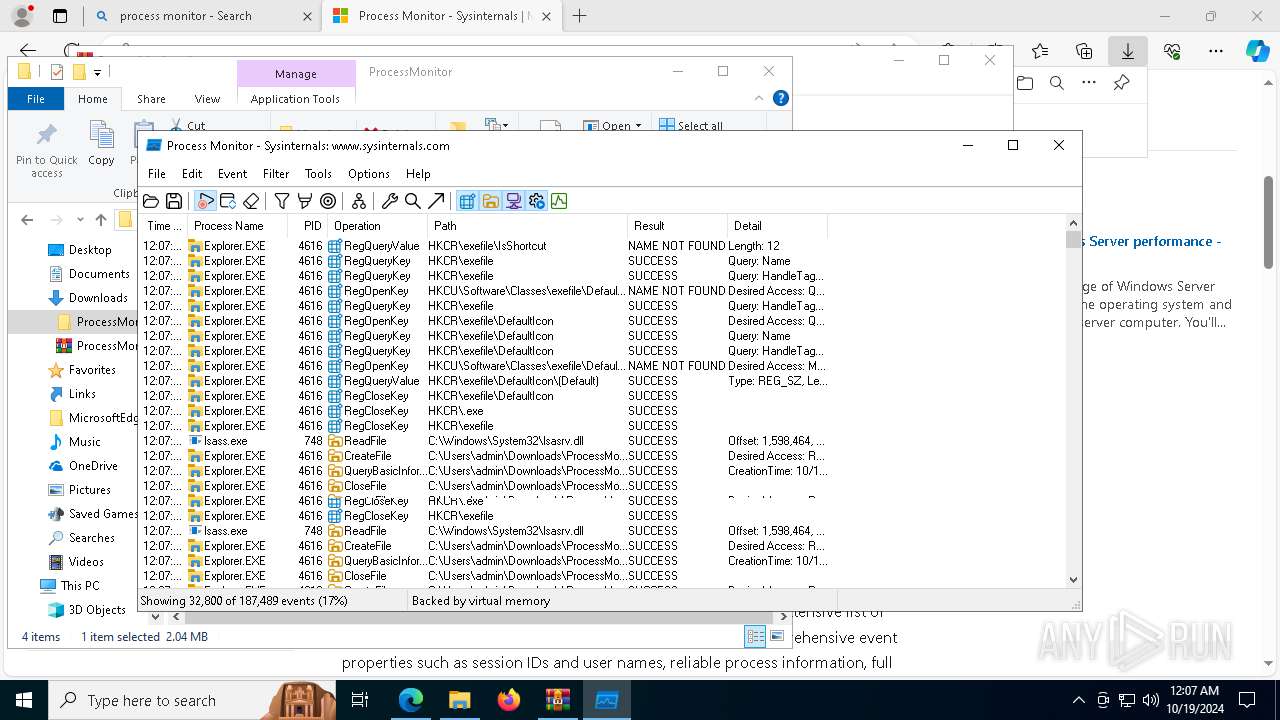
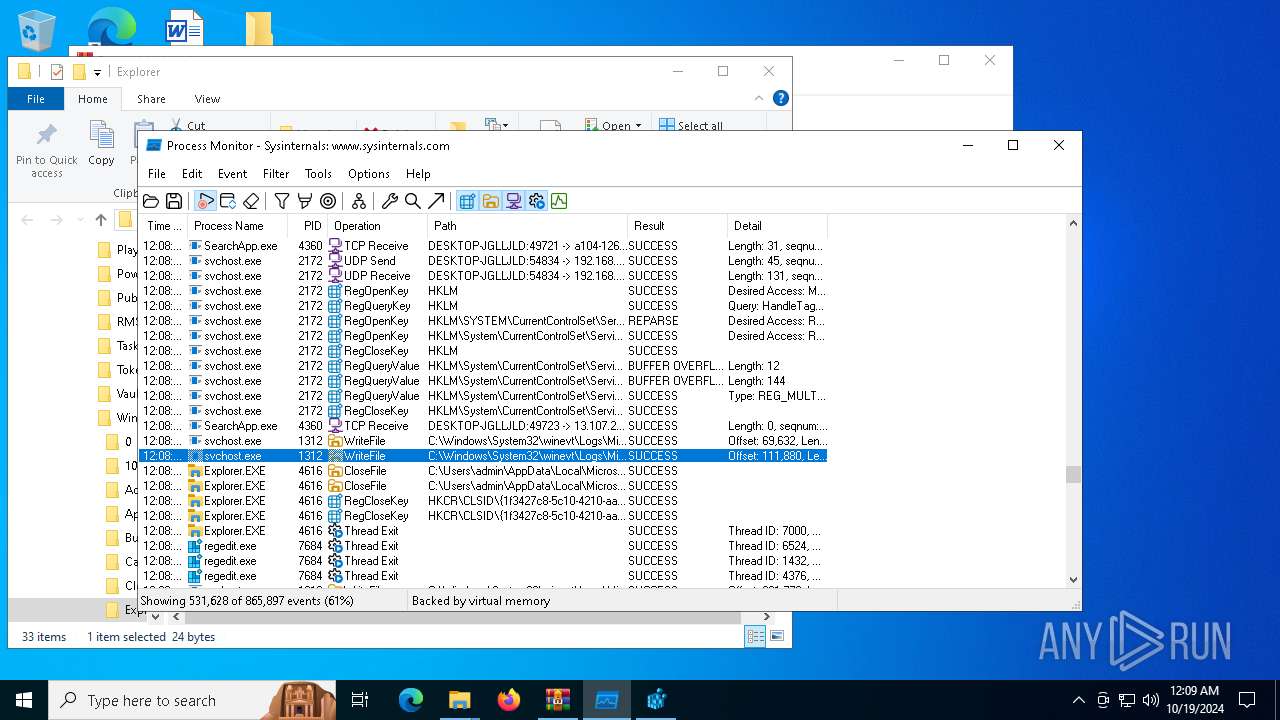
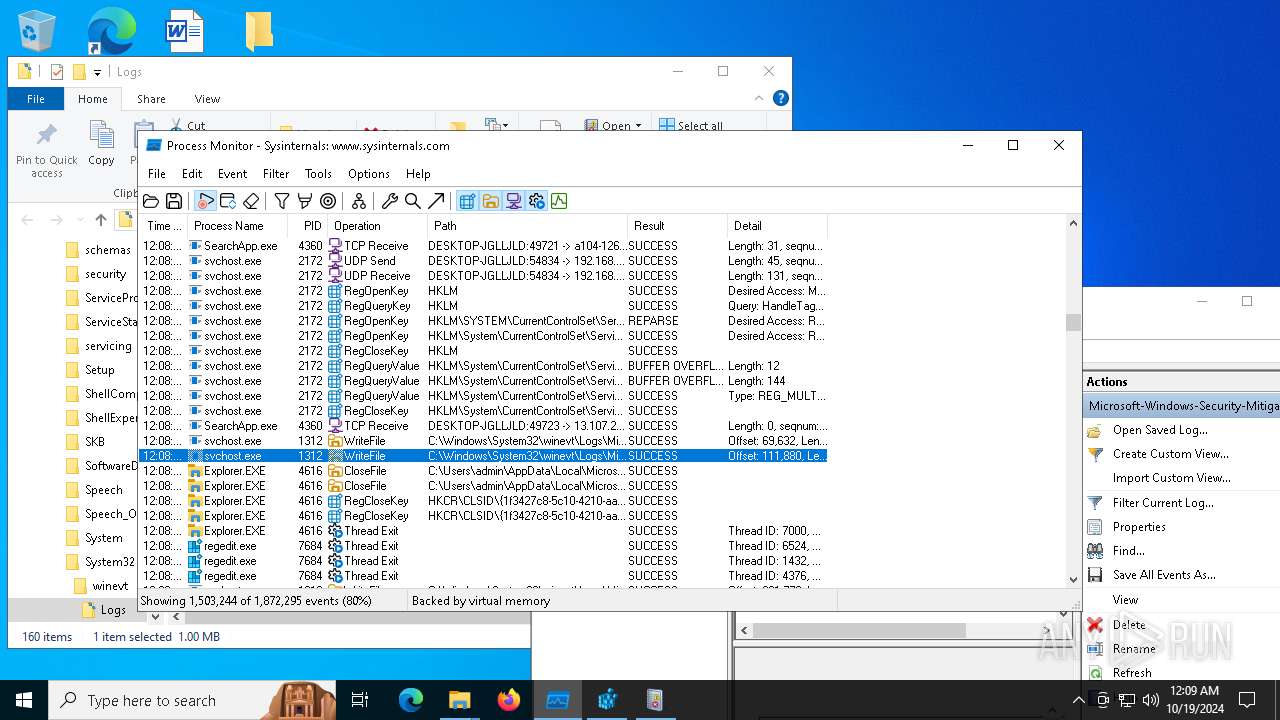
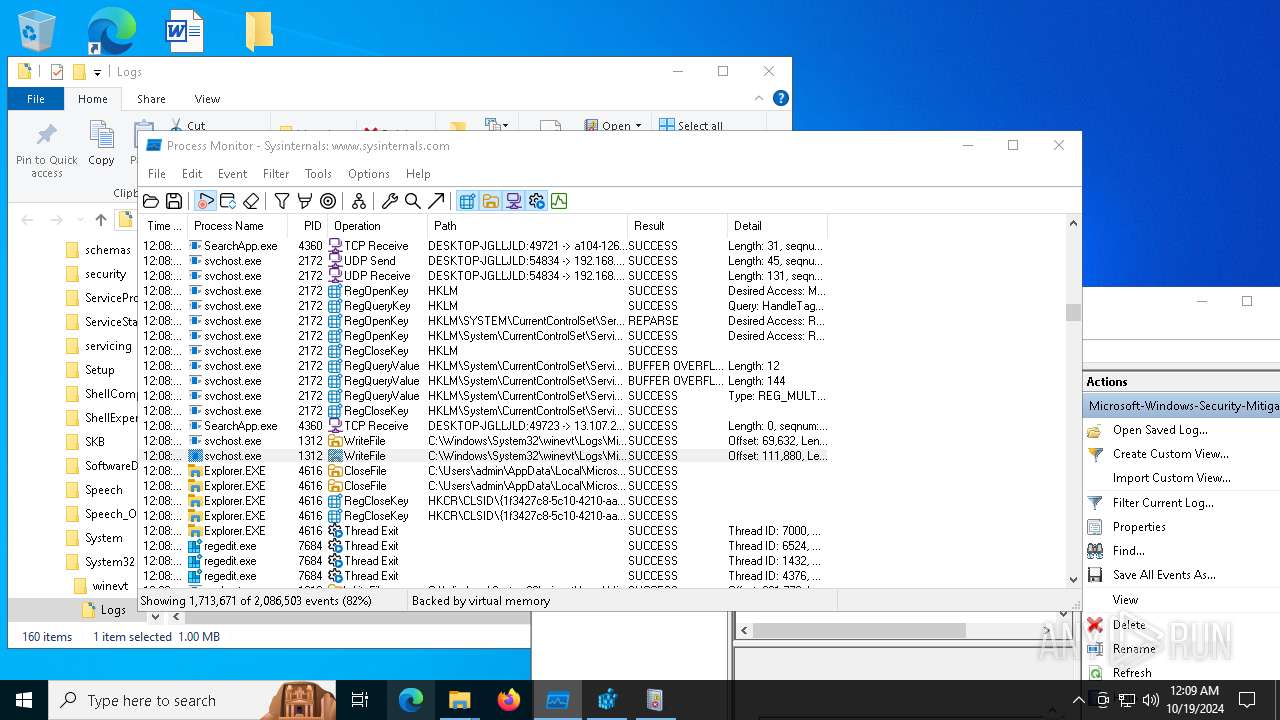
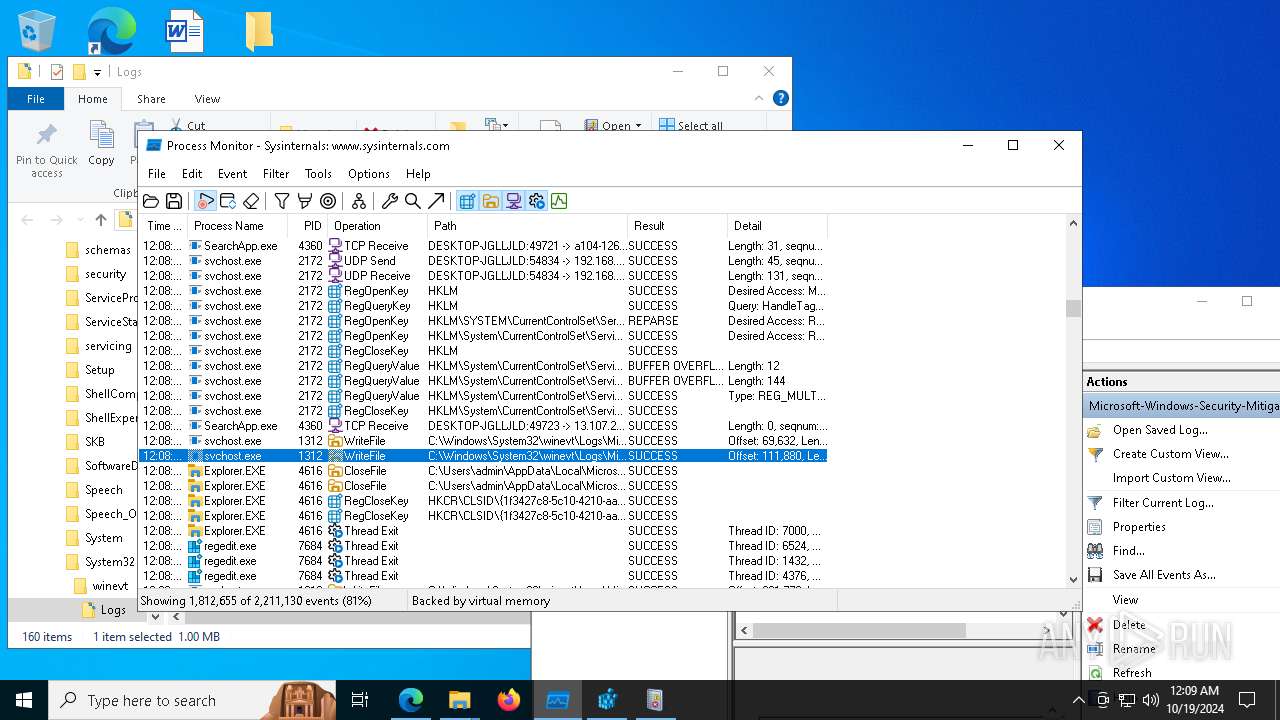
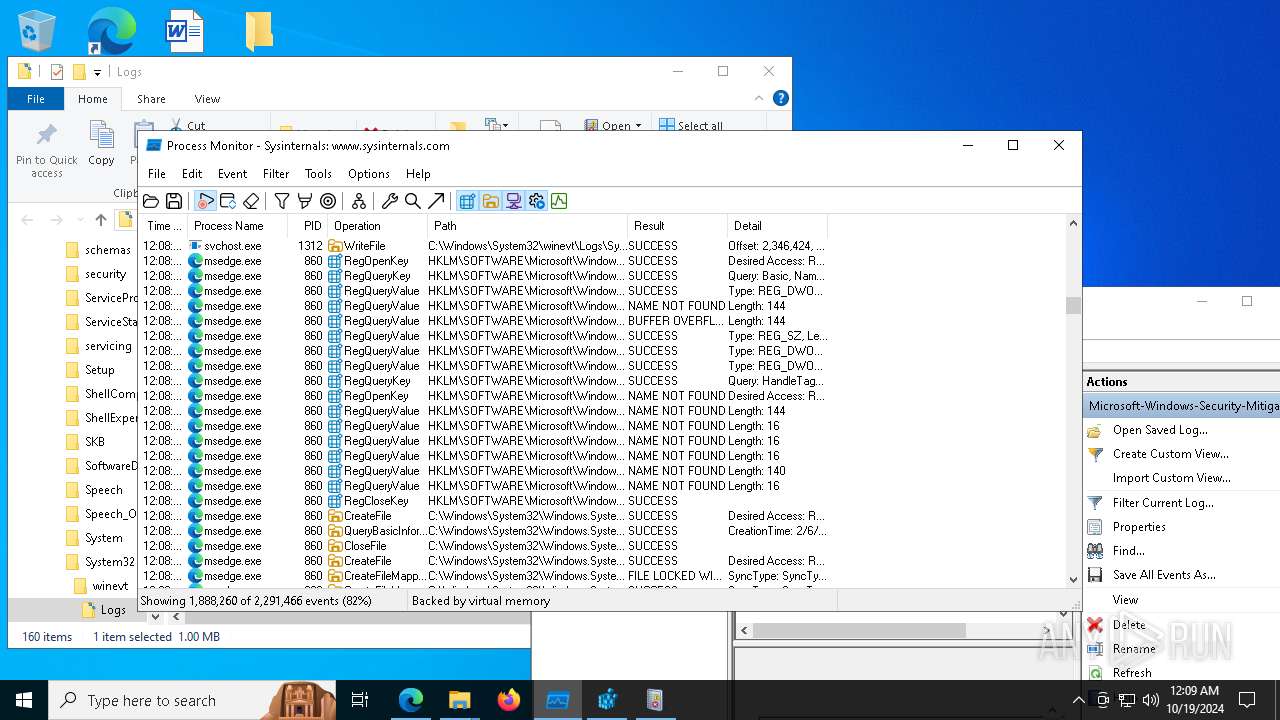
Total events
2 296
Read events
2 256
Write events
36
Delete events
4
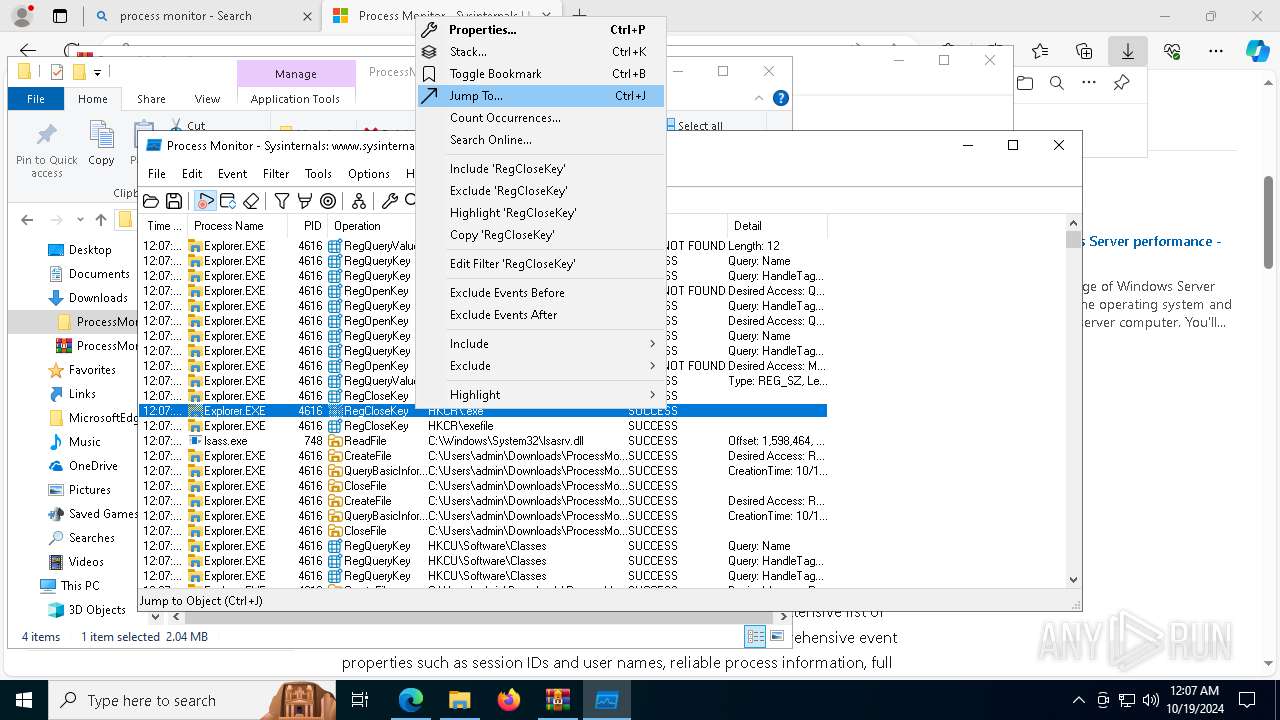
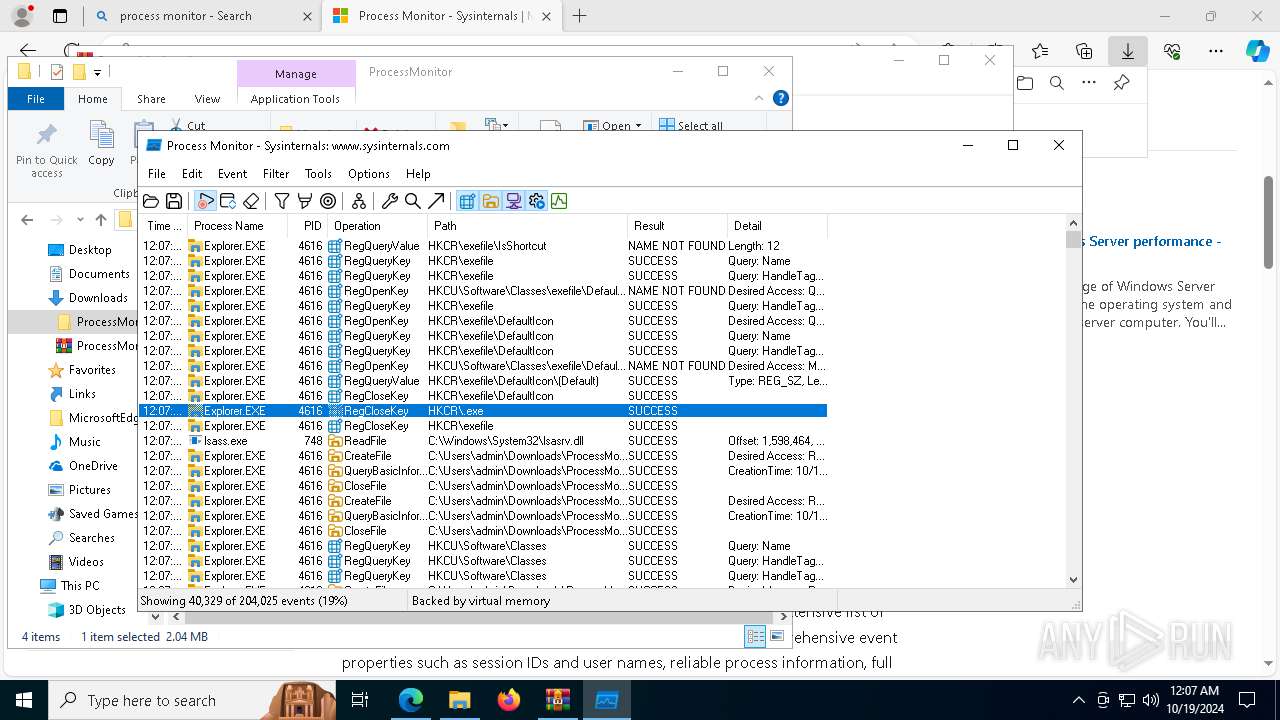
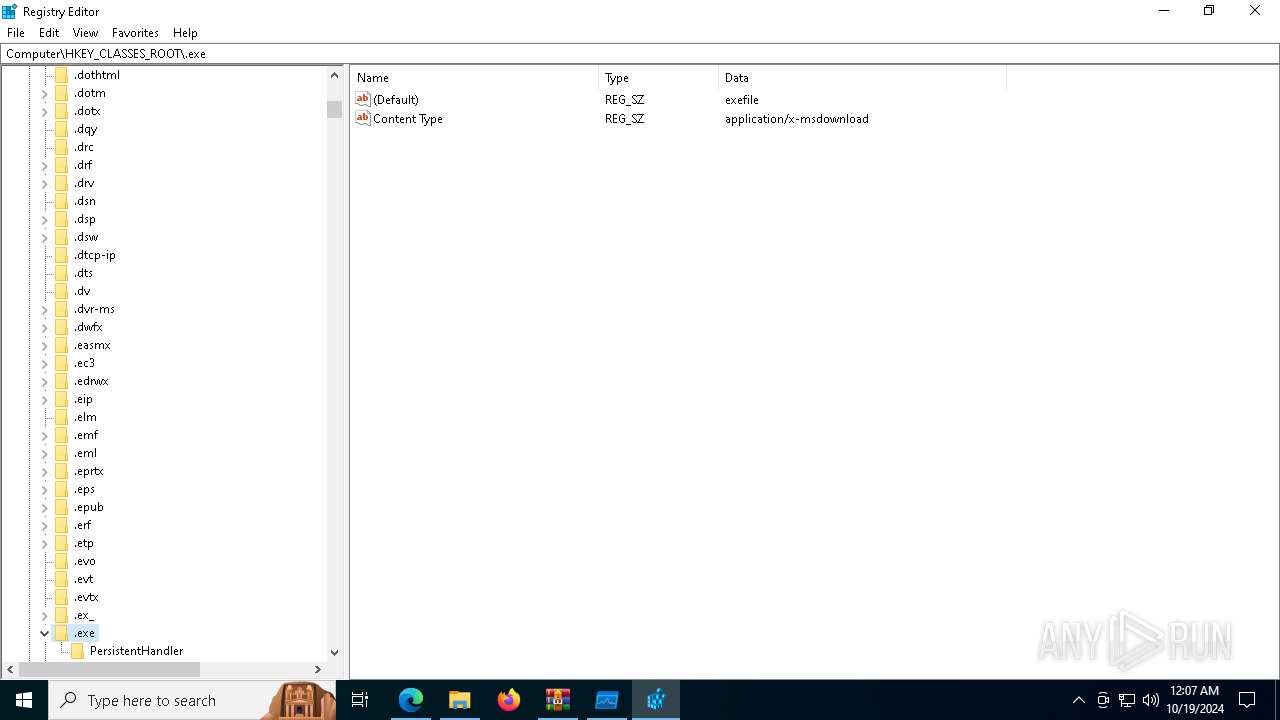
Modification events
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\27hb7t8u.zip | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
Executable files
5
Suspicious files
0
Text files
3
Unknown types
0
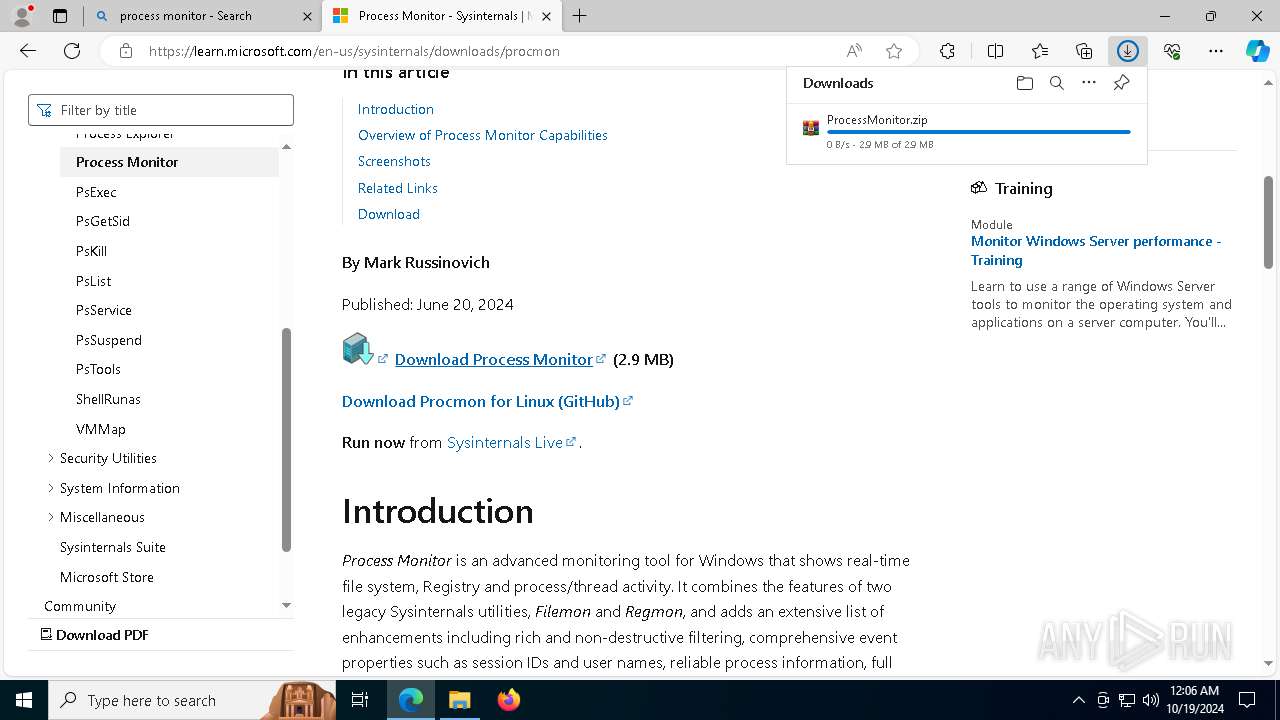
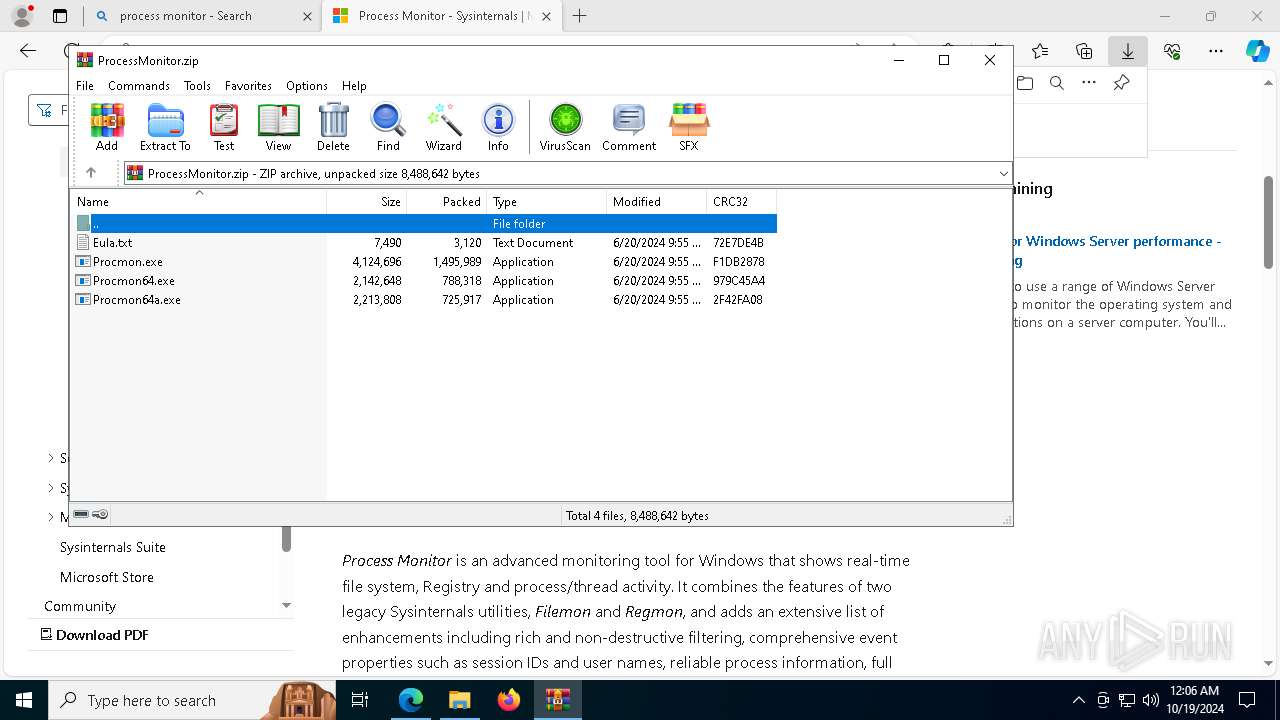
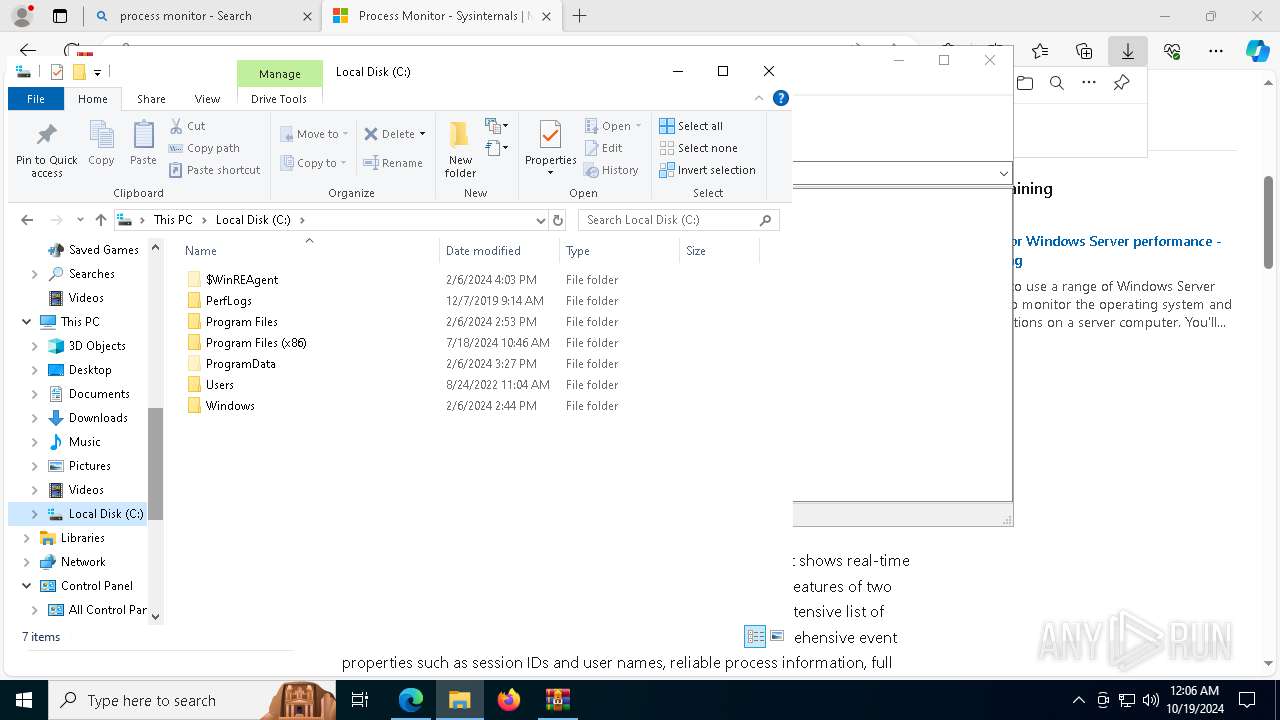
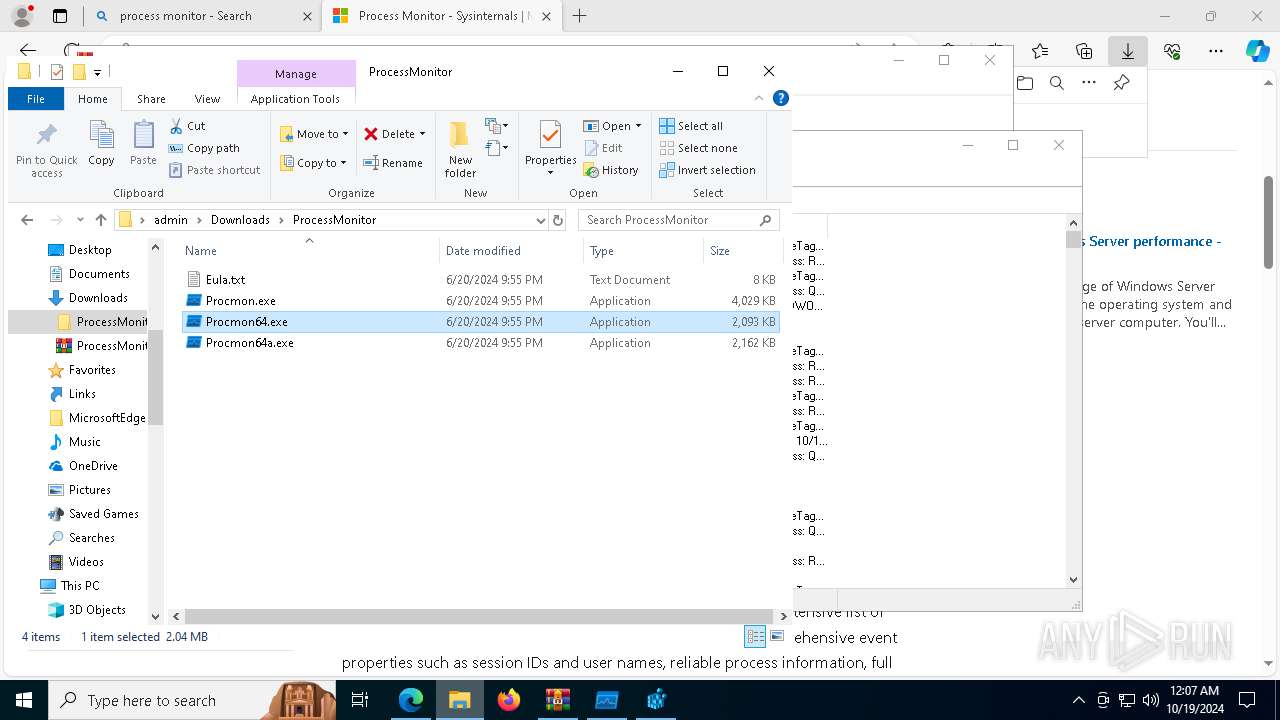
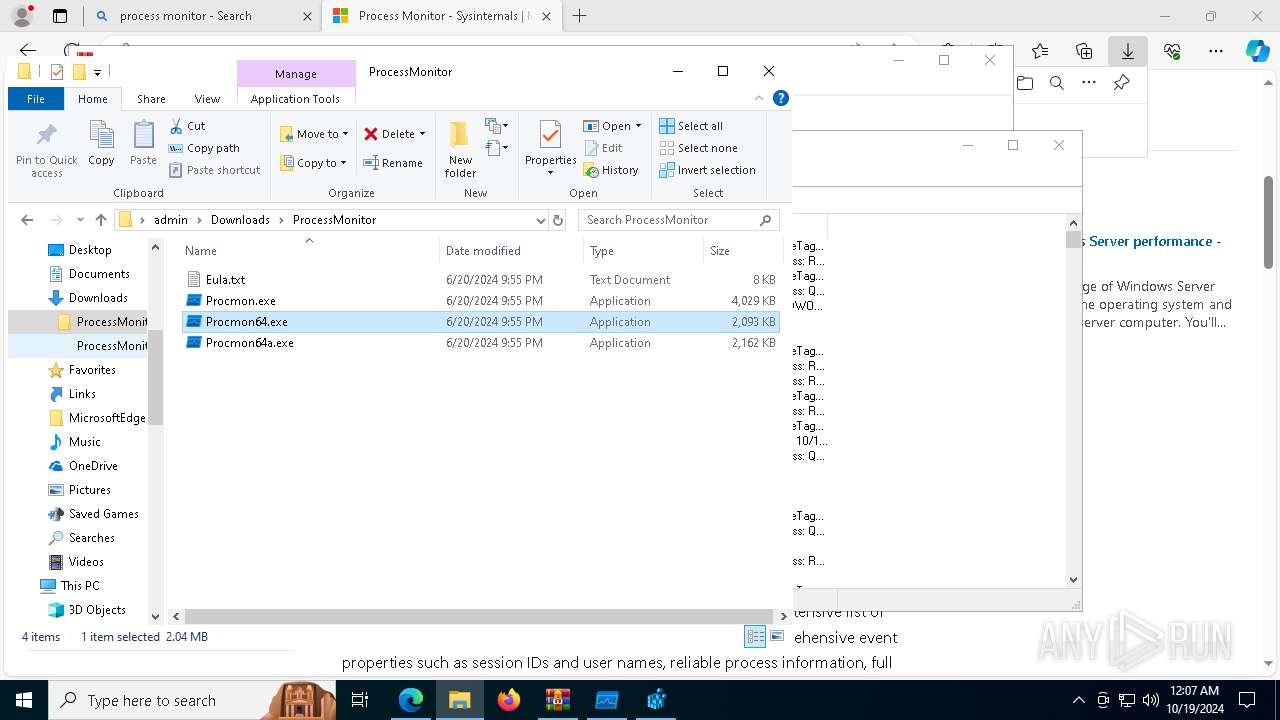
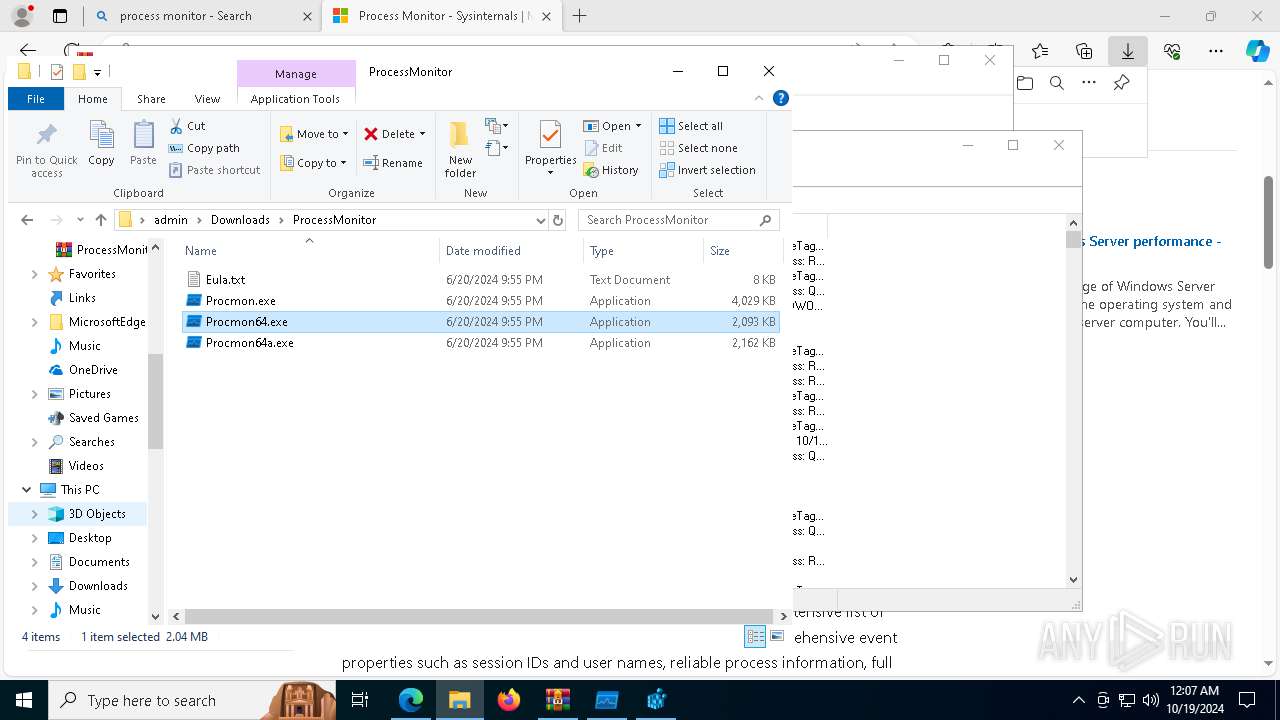
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
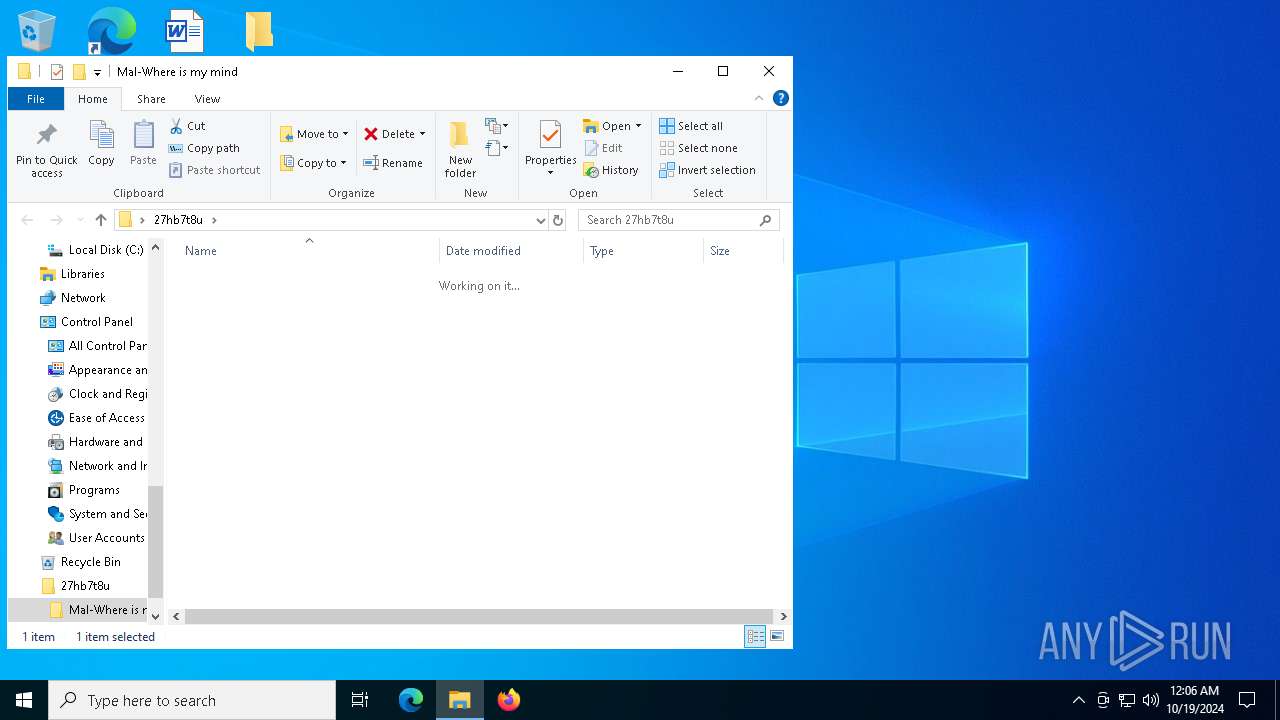
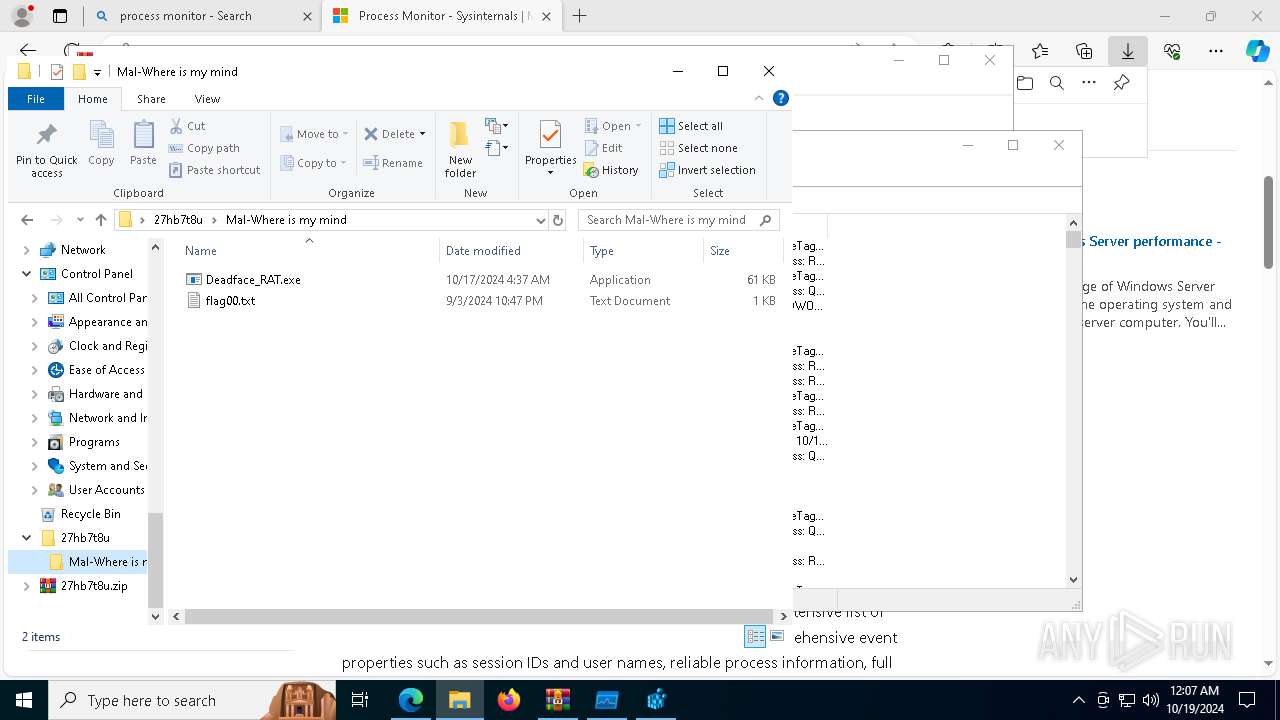
| 6324 | WinRAR.exe | C:\Users\admin\Desktop\27hb7t8u\Mal-Where is my mind\Deadface_RAT.exe | executable | |
MD5:C65302F51EAC936DD42BAFBD5567C2AC | SHA256:B314227559F298DCA1378B44298DEA11FC1EE9EEFFDA30818F6D0285DB0C2602 | |||
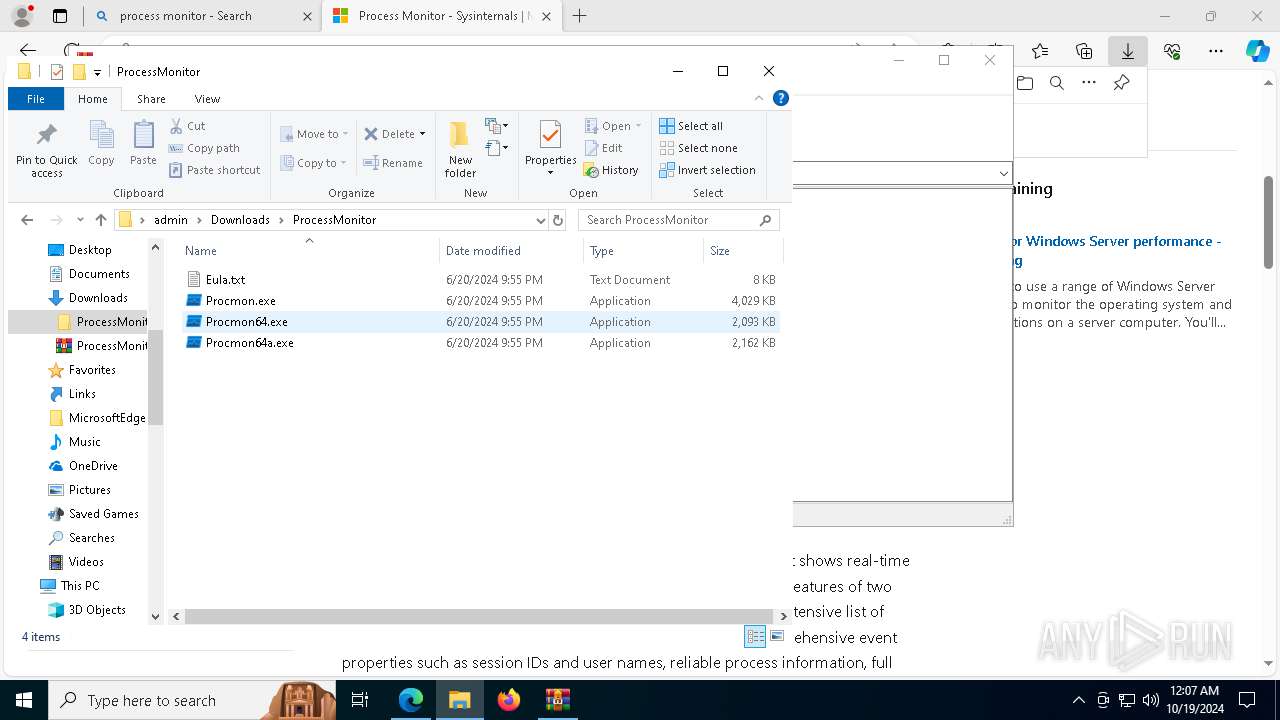
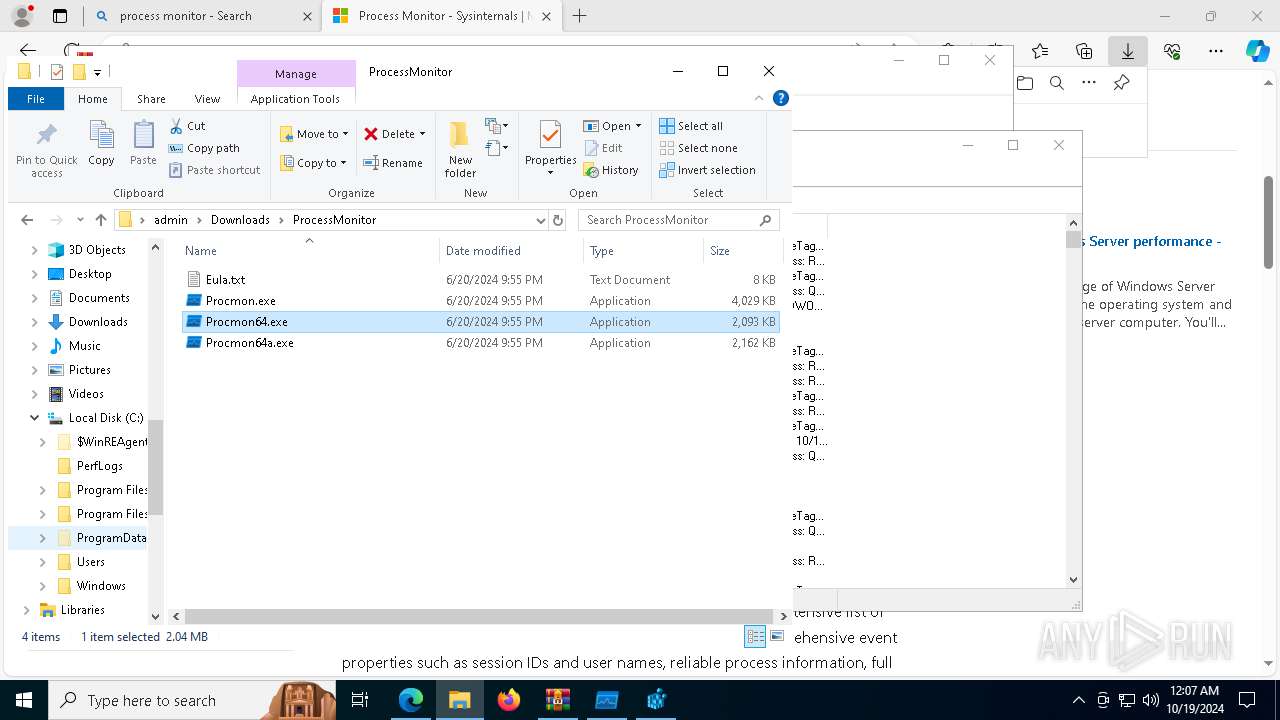
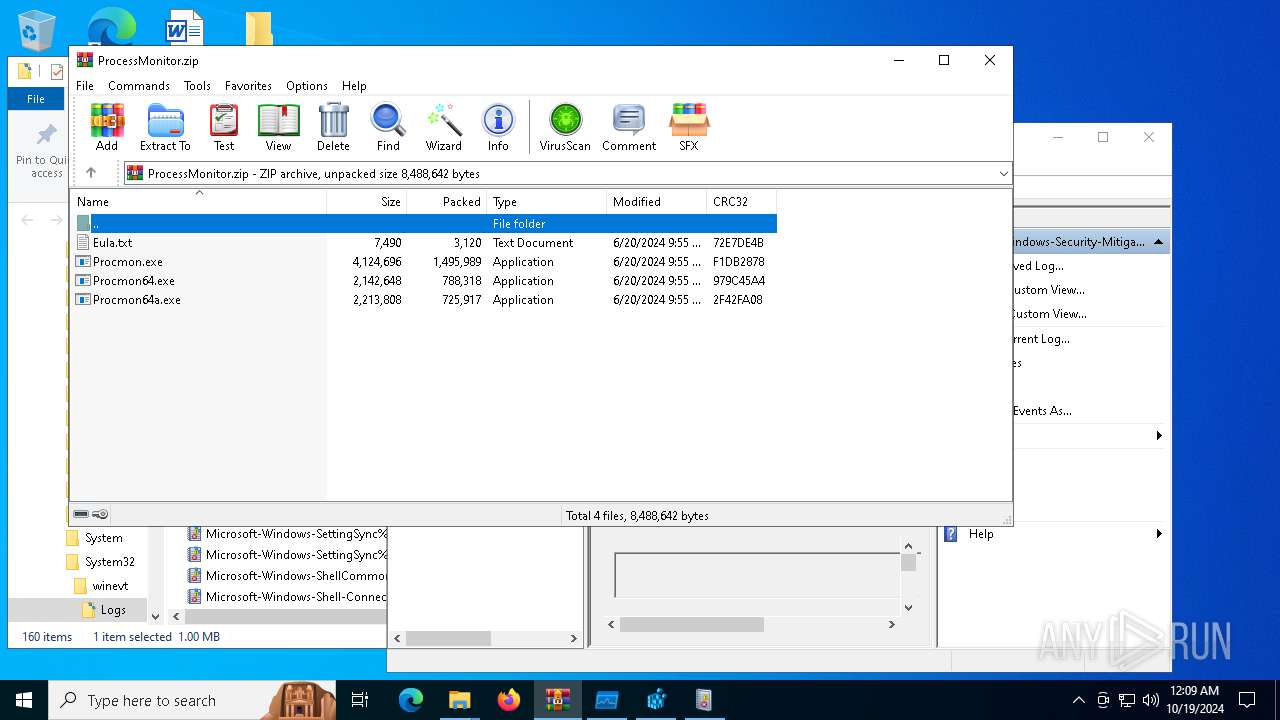
| 6520 | WinRAR.exe | C:\Users\admin\Downloads\ProcessMonitor\Eula.txt | text | |
MD5:8C24C4084CDC3B7E7F7A88444A012BFC | SHA256:8329BCBADC7F81539A4969CA13F0BE5B8EB7652B912324A1926FC9BFB6EC005A | |||
| 6520 | WinRAR.exe | C:\Users\admin\Downloads\ProcessMonitor\Procmon.exe | executable | |
MD5:C3E77B6959CC68BAEE9825C84DC41D9C | SHA256:3B7EA4318C3C1508701102CF966F650E04F28D29938F85D74EC0EC2528657B6E | |||
| 6520 | WinRAR.exe | C:\Users\admin\Downloads\ProcessMonitor\Procmon64.exe | executable | |
MD5:223B222CE387A7F446D49A1EE9B572BB | SHA256:3E15995894F38B2EEAD95F7FF714585471F34F3AF3D8F50A7F83344781502468 | |||
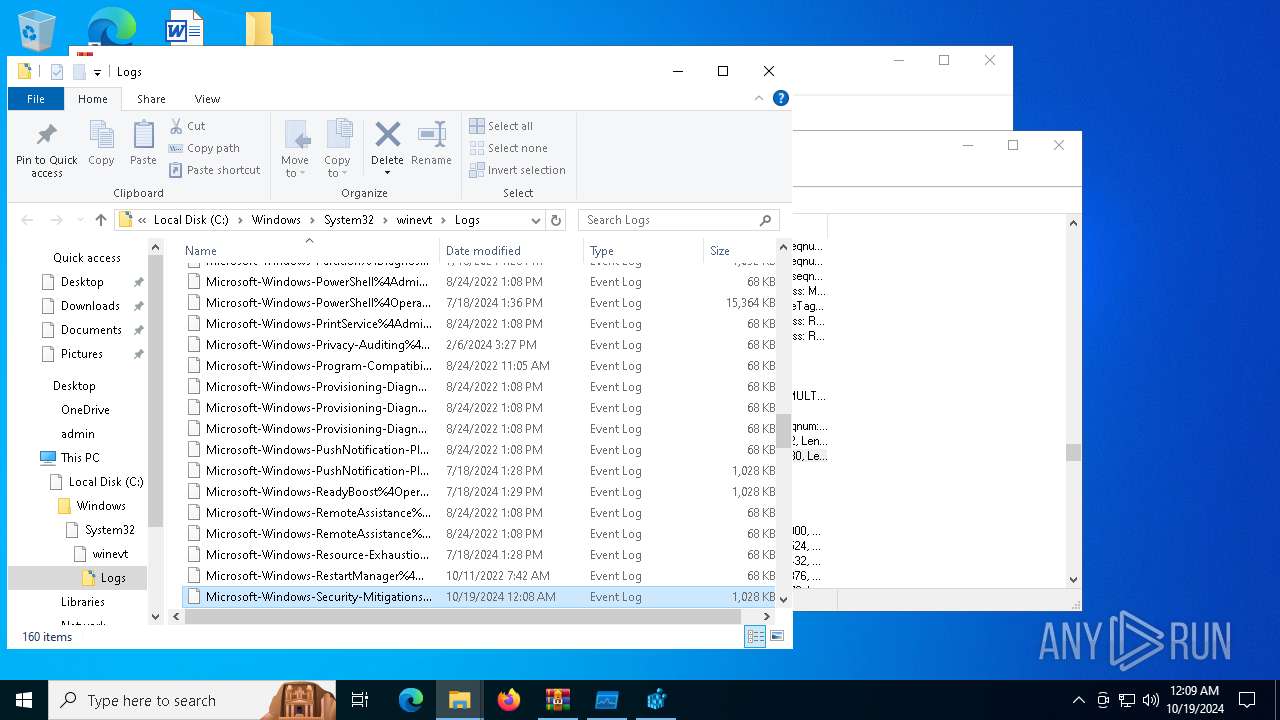
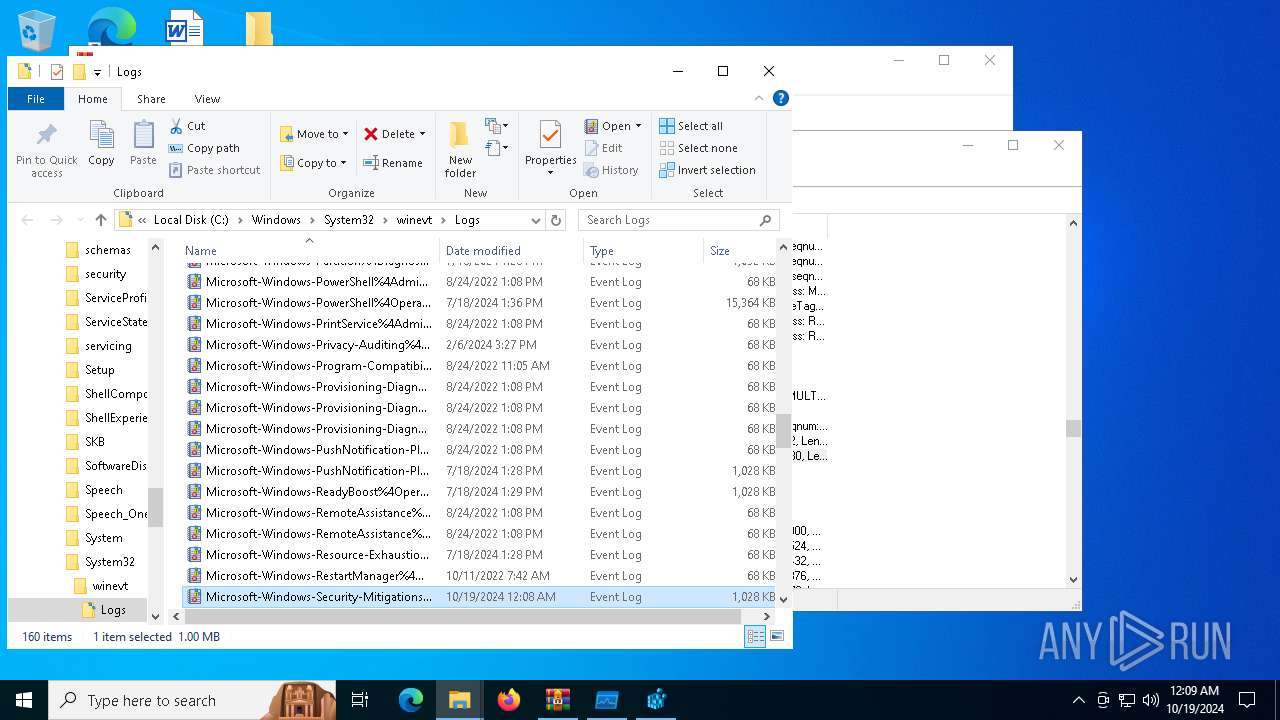
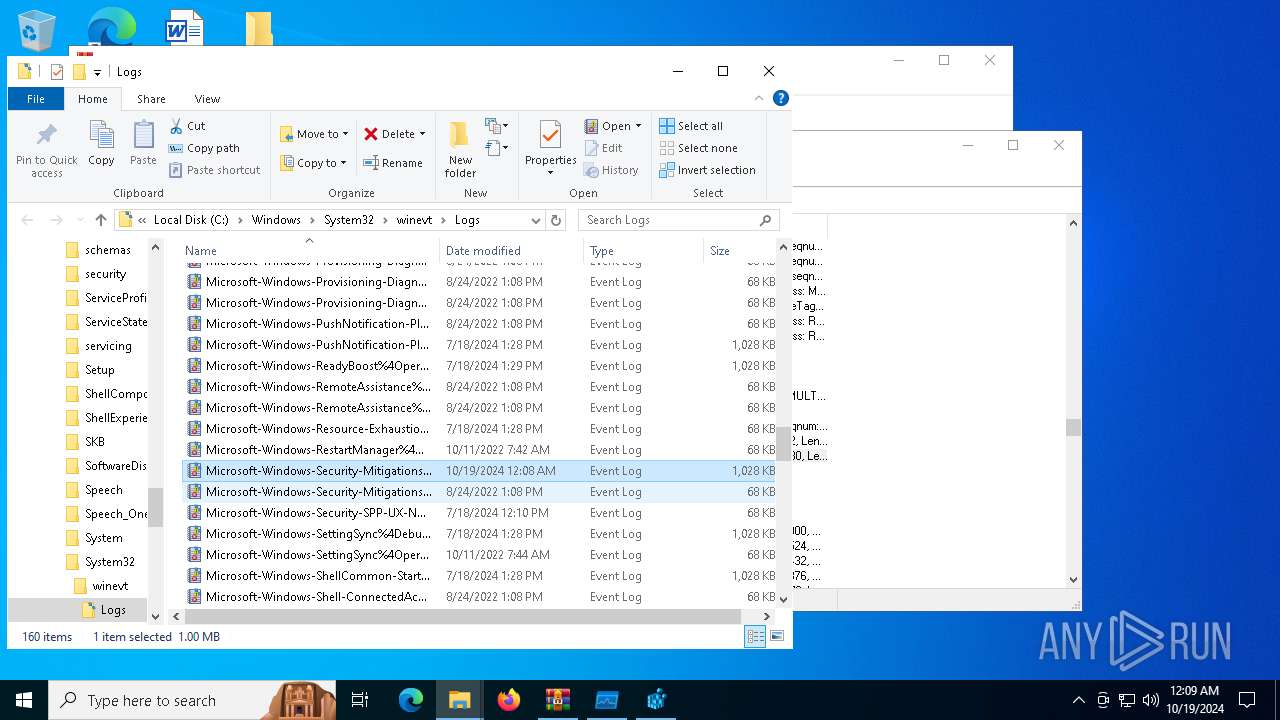
| 7080 | Procmon64.exe | C:\Windows\System32\drivers\PROCMON24.SYS | executable | |
MD5:03480D56A090F0CD397677251F747929 | SHA256:2A5A61BDA7B7B5D6E69B588FFBF625A1534D5A94F39801F6E0376774AA103DD9 | |||
| 6520 | WinRAR.exe | C:\Users\admin\Downloads\ProcessMonitor\Procmon64a.exe | executable | |
MD5:03A3A7C0F0534D7F56FB50D486FE8CEF | SHA256:36085927CA98B9B7D630EDEAD37671208E01978CA38974FB3FD435F42E709702 | |||
| 6324 | WinRAR.exe | C:\Users\admin\Desktop\27hb7t8u\Mal-Where is my mind\flag00.txt | text | |
MD5:BFE362640FB0C8DD7397906755A1193B | SHA256:1D2471336BC2418DB61AE0A13C9A91B21CD9D4F6AF6F4771B785AF7012CB1B22 | |||
| 4260 | Deadface_RAT.exe | C:\Users\admin\flag.txt | text | |
MD5:84ADBC5AB8D1BABF40E6CD53294BB0C4 | SHA256:D4BF5D1B8C132780805A3D968806D7AB1E9FACB014834A930DBA2642AE972D73 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
249
DNS requests
420
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4700 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3532 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/181d62d0-8e71-4ab0-b6f0-62f746749689?P1=1729775280&P2=404&P3=2&P4=ONpx%2frBwsdnOQ0klcCVjSXZ4v7yBzOvq8ZQMEeVw6rSG9bKoQVYHwNyV7GBwJiv%2bgm6%2boTswCcBsPq05iB%2bOaQ%3d%3d | unknown | — | — | whitelisted |
3532 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7088 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3396 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.145:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4700 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
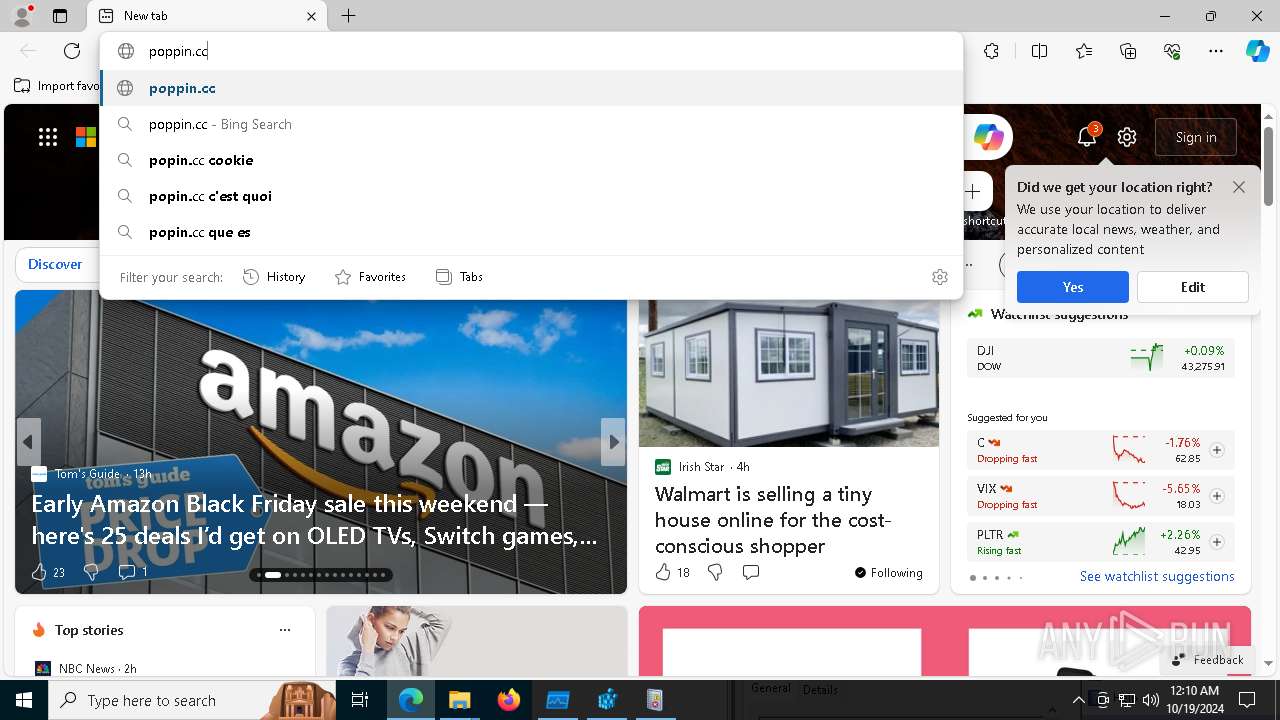
— | — | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
— | — | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |