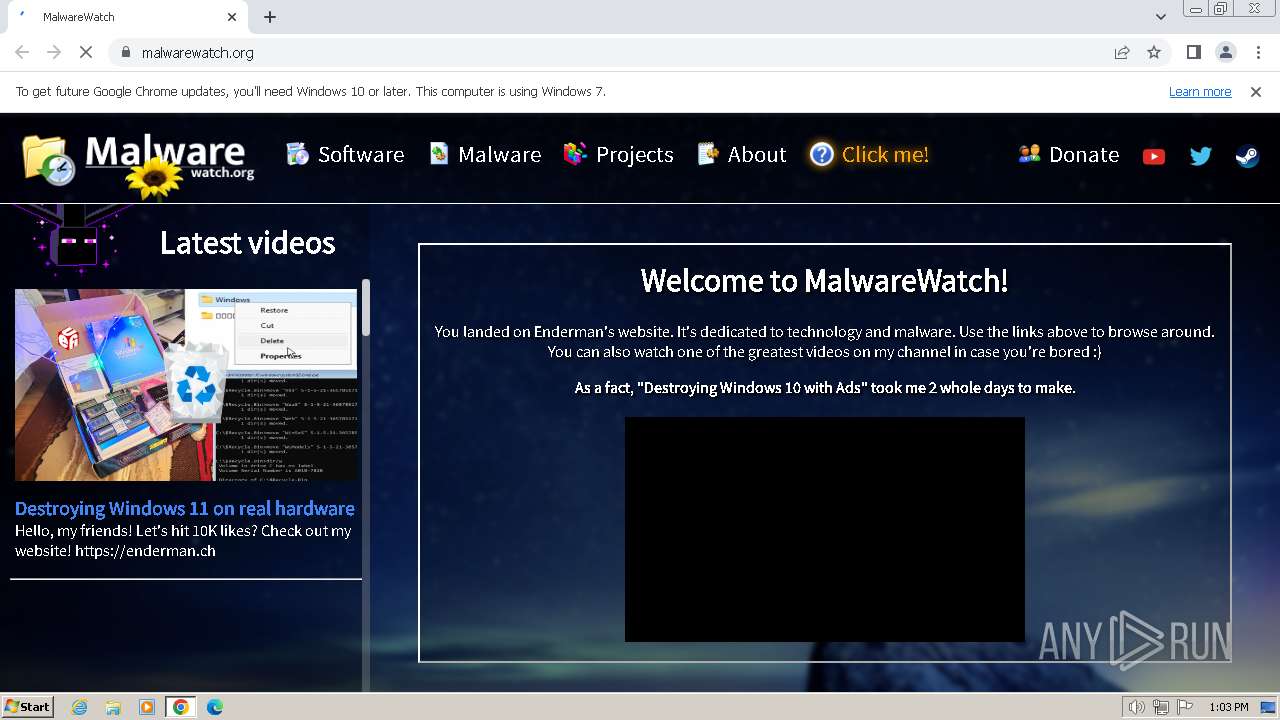
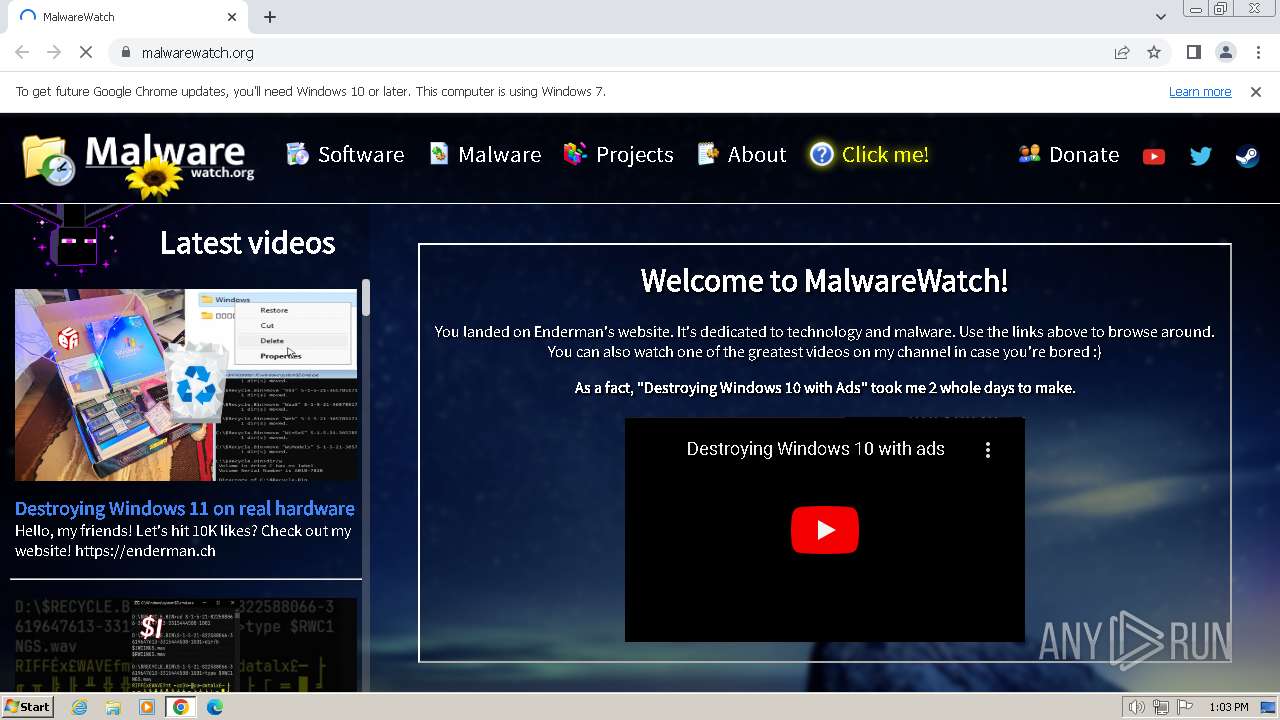
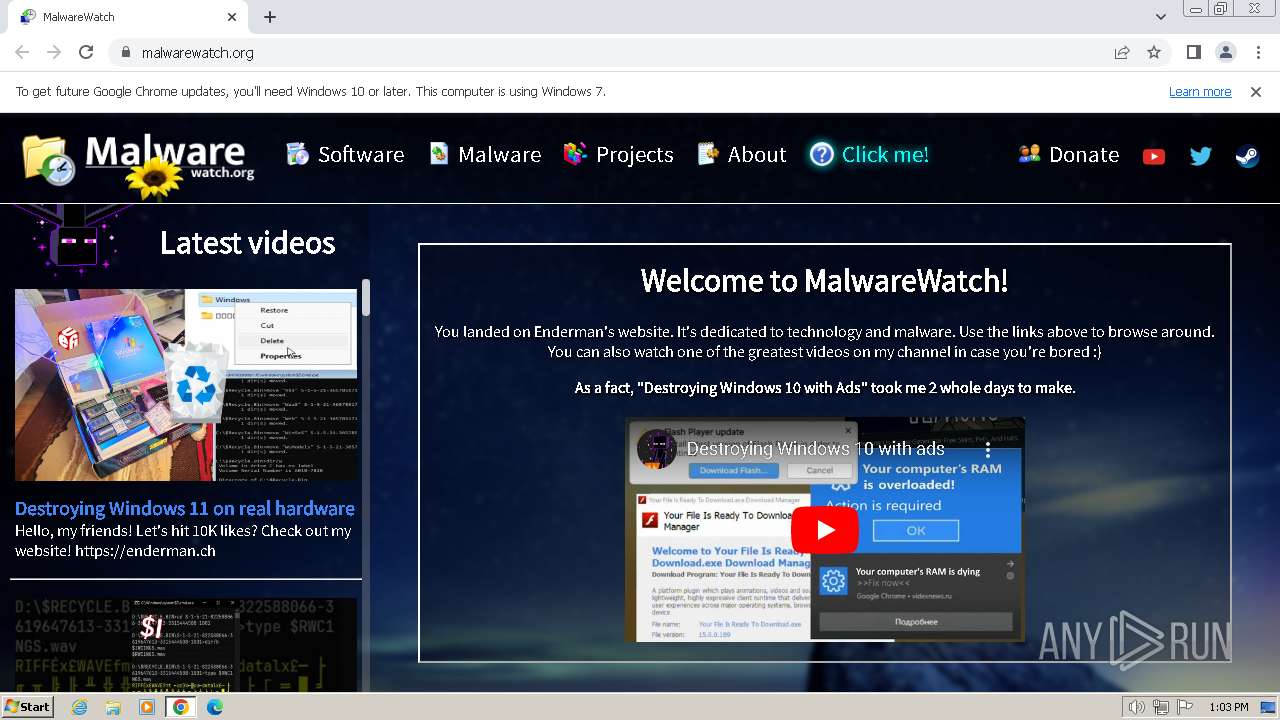
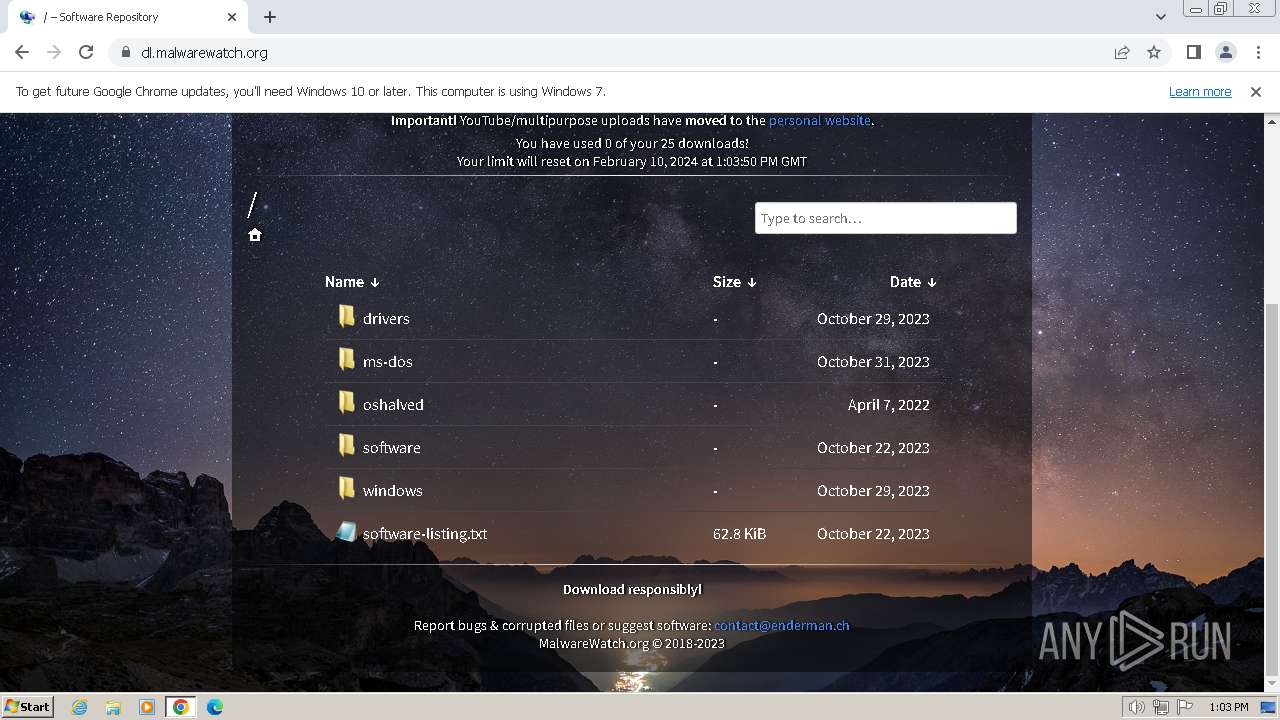
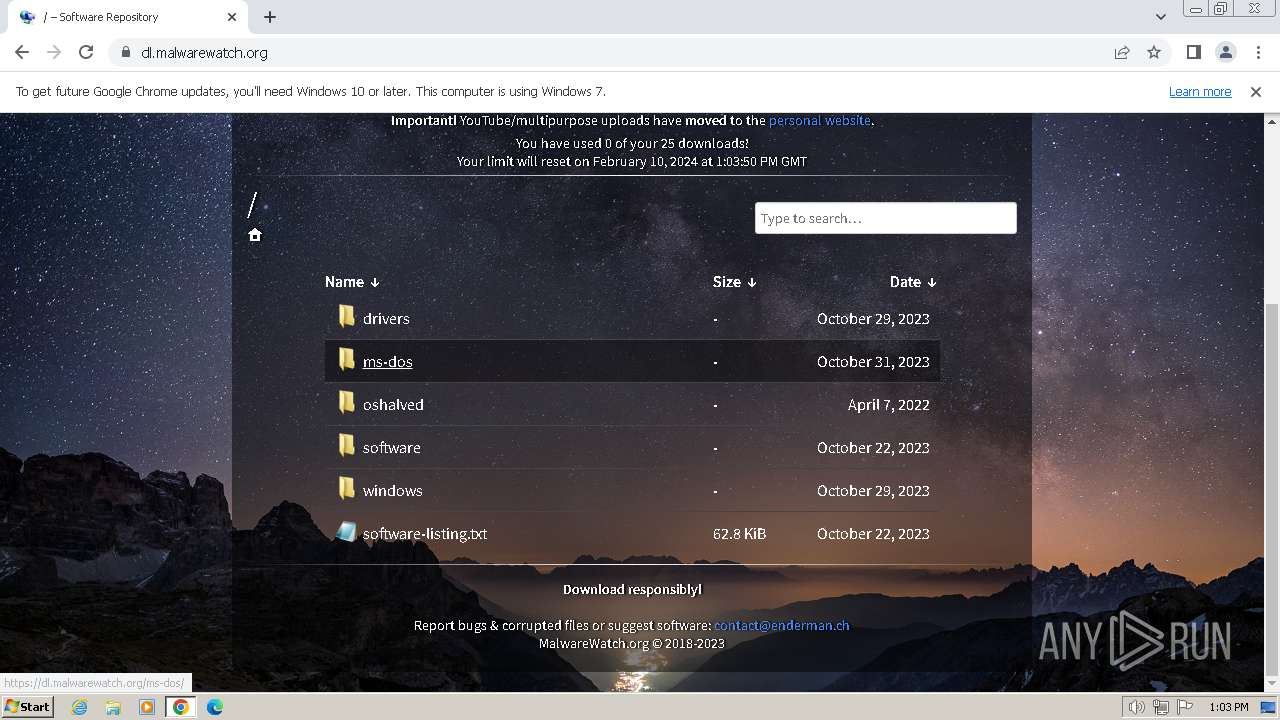
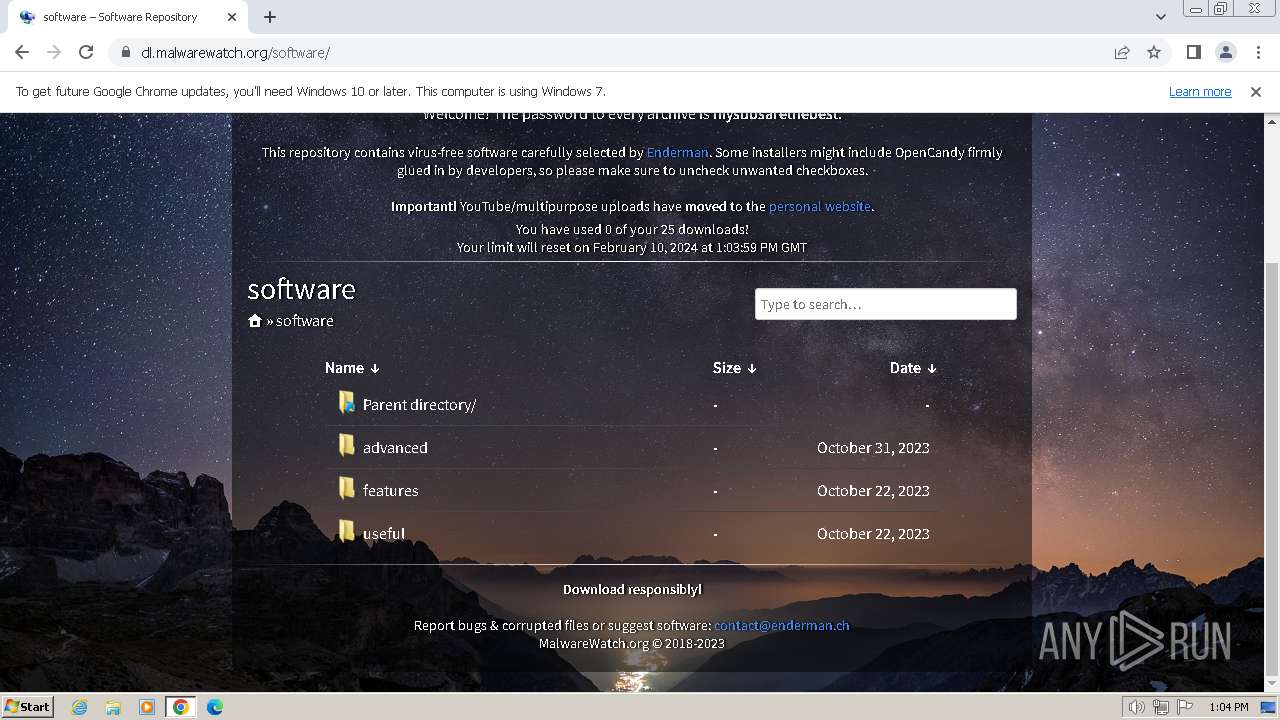
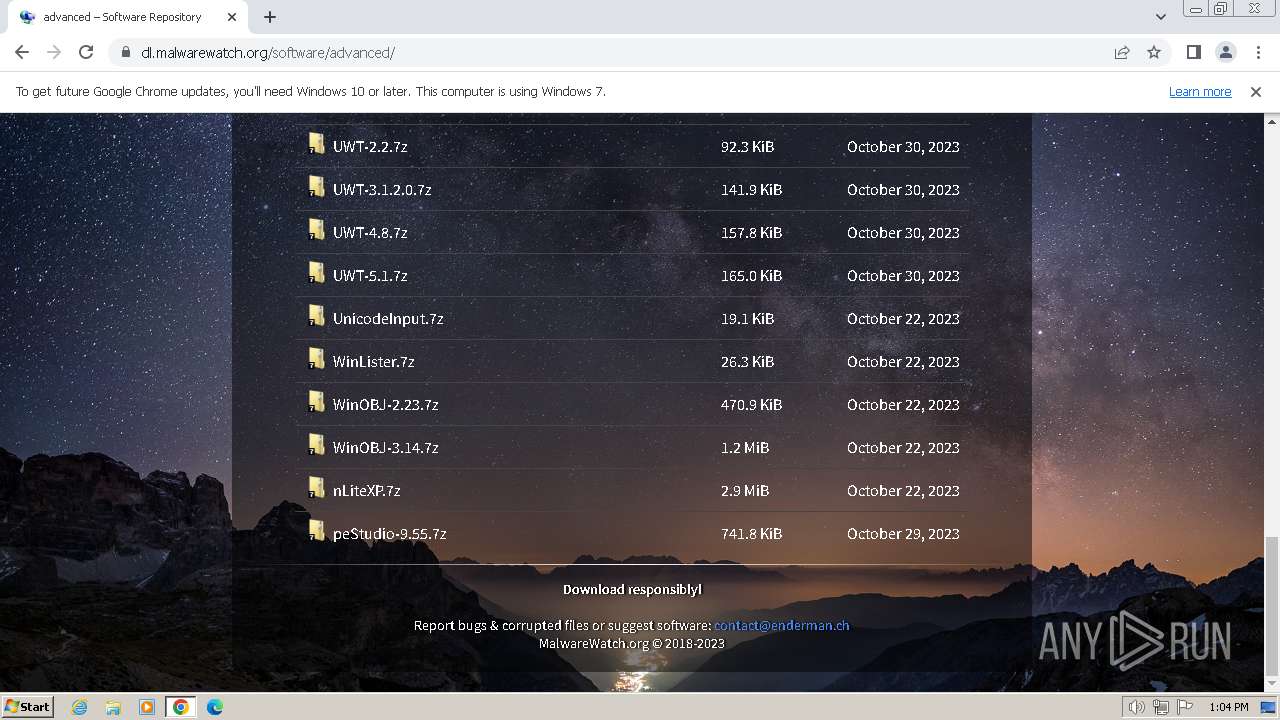
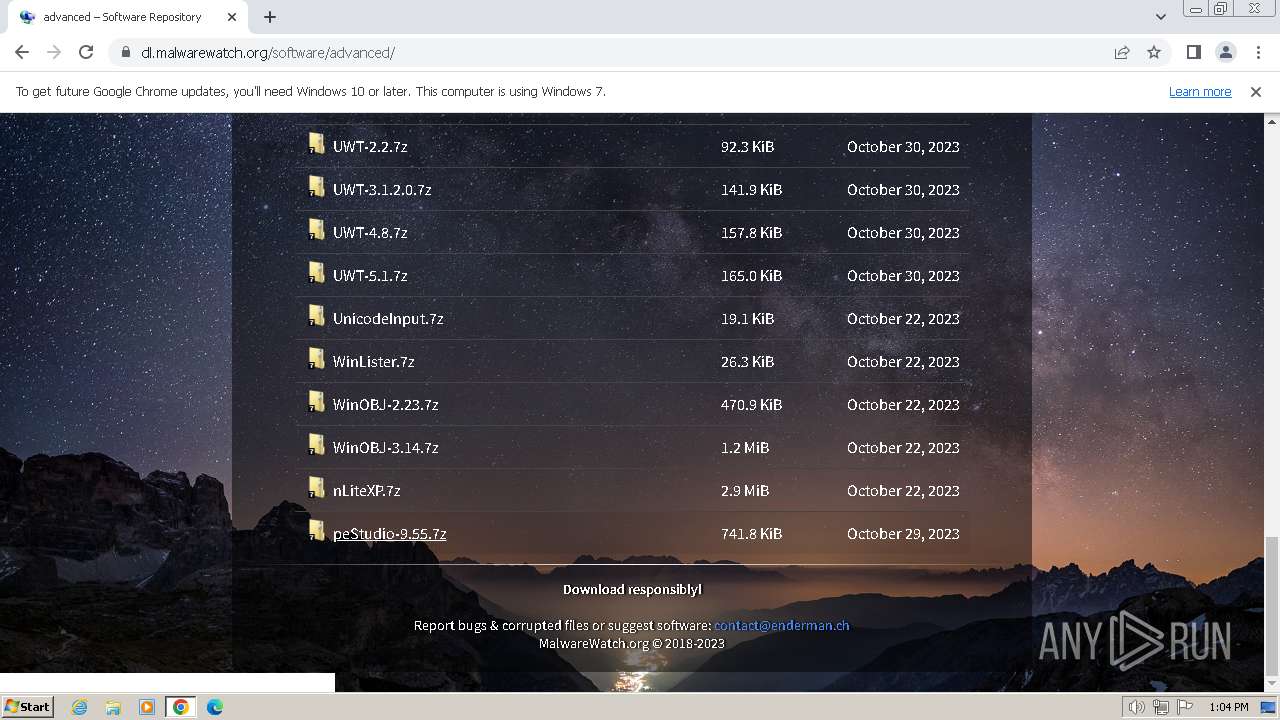
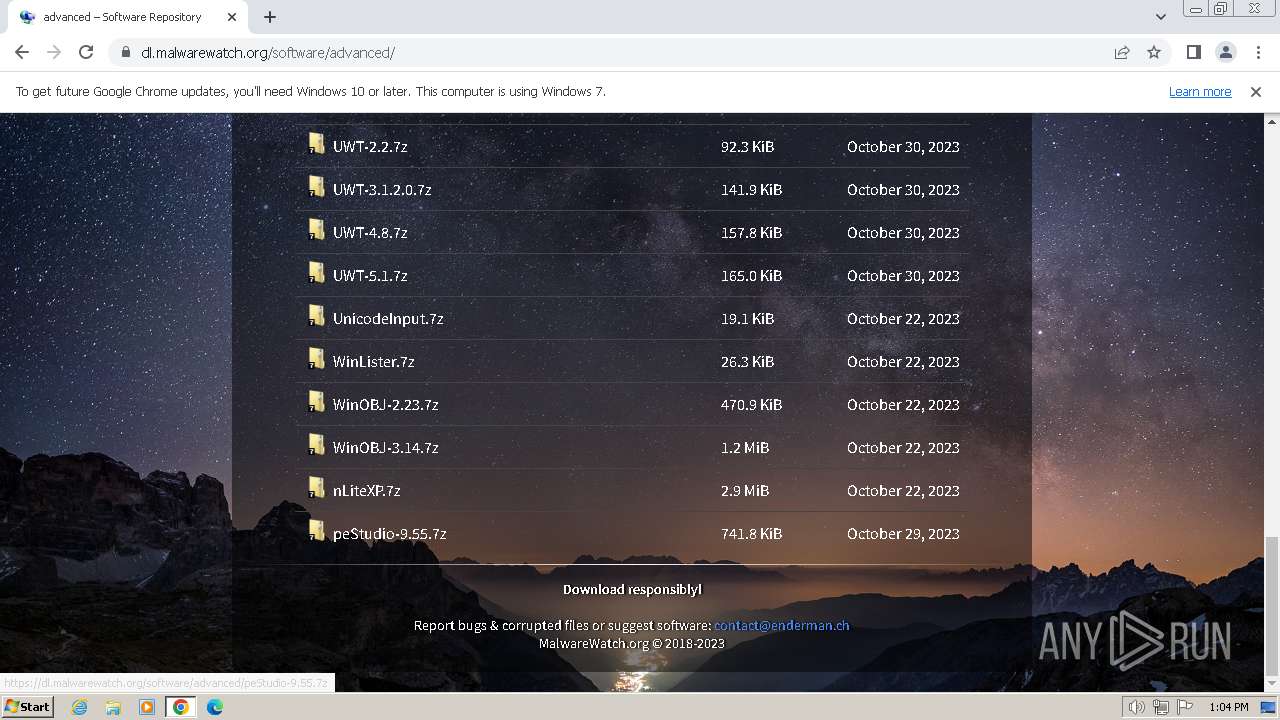
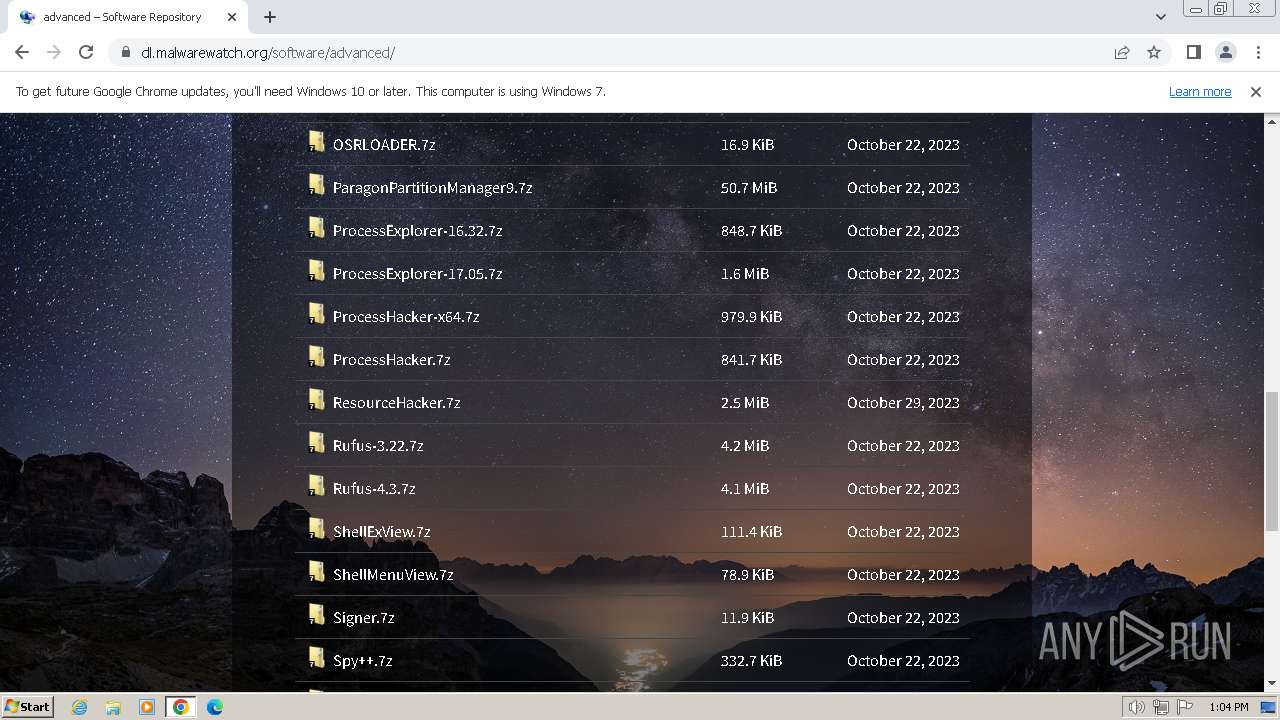
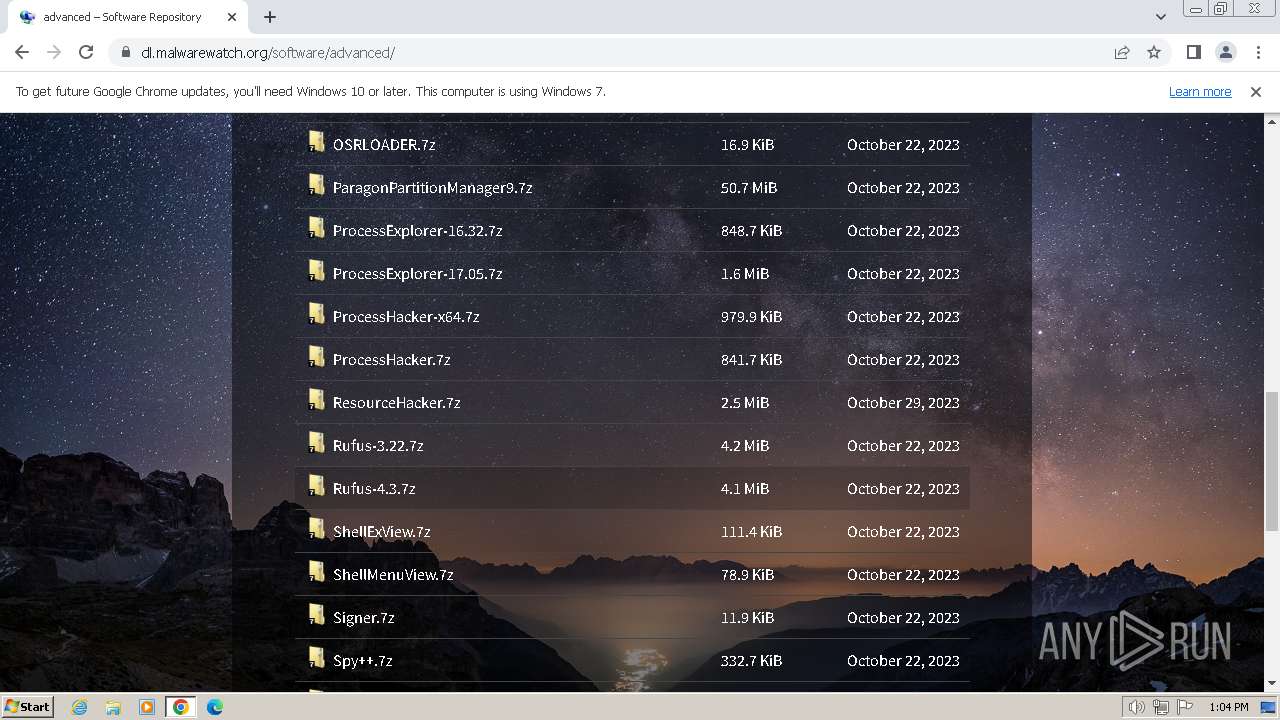
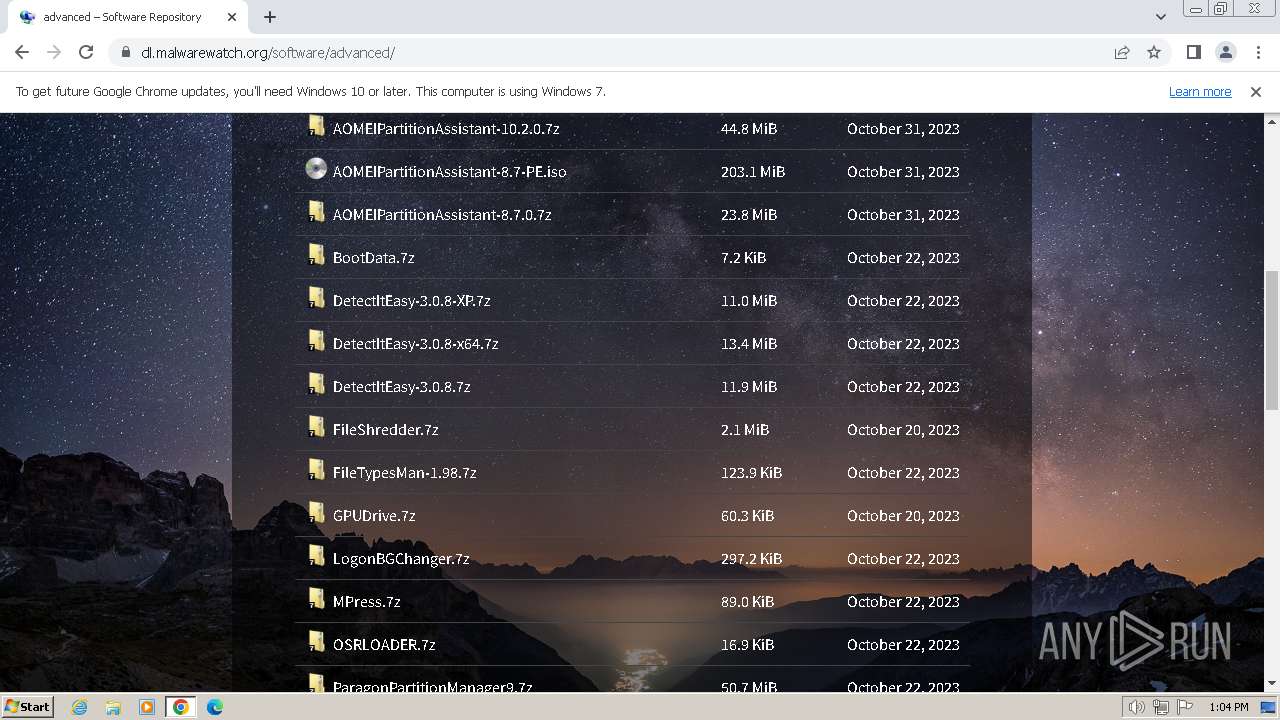
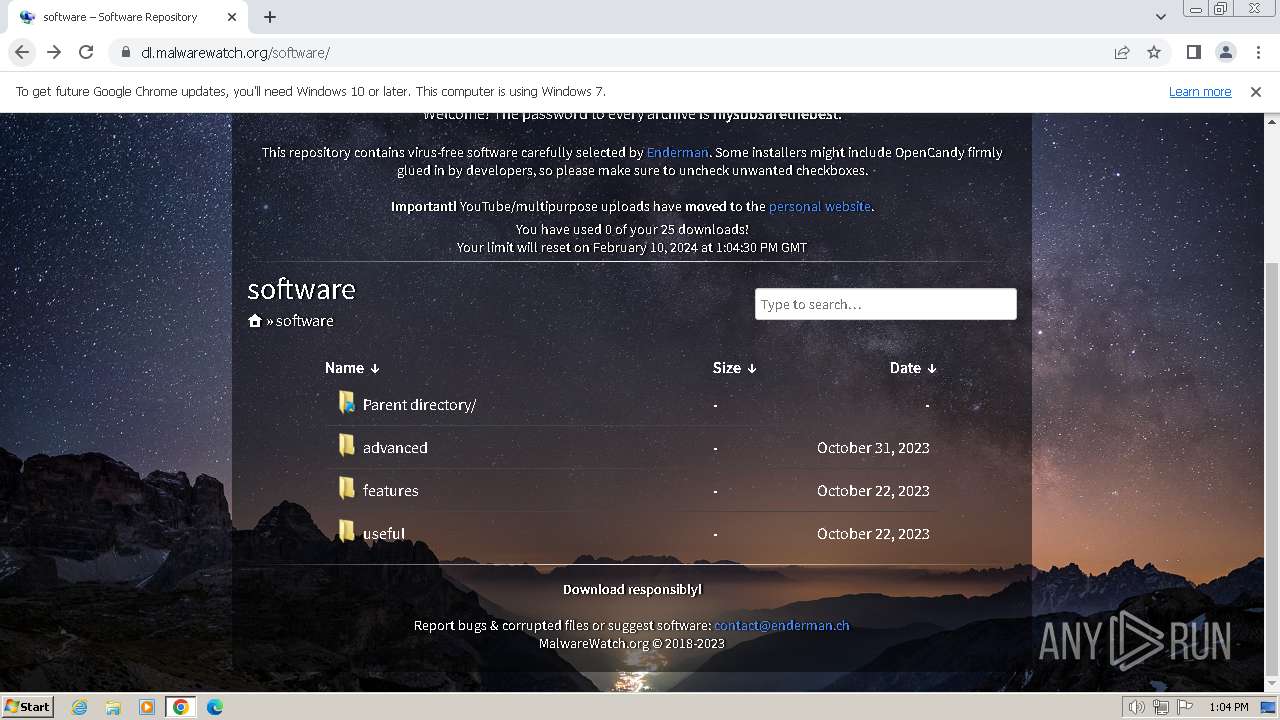
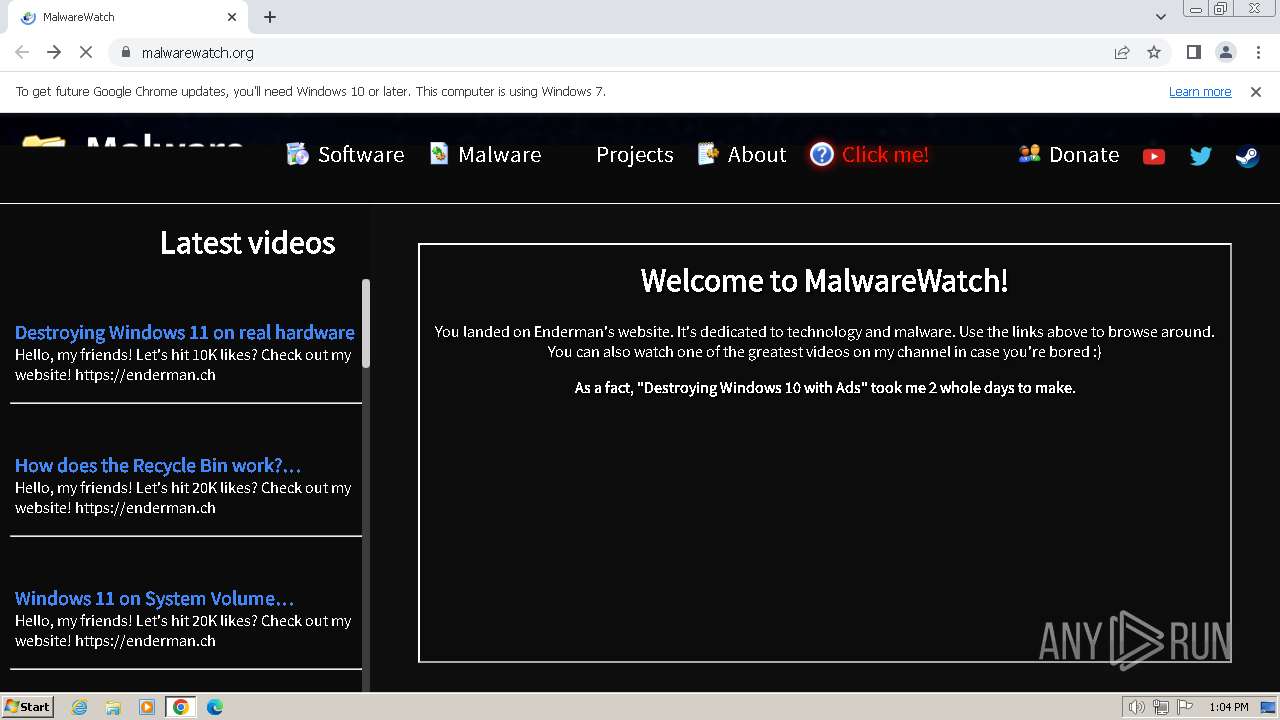
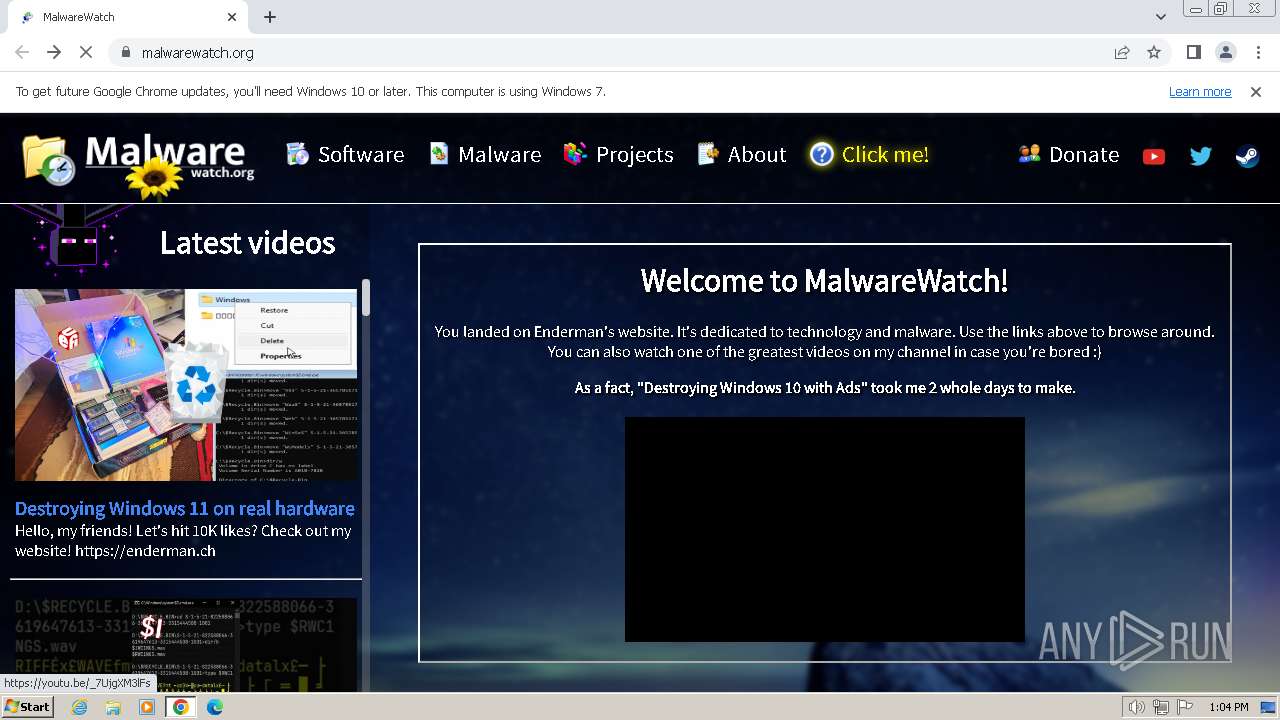
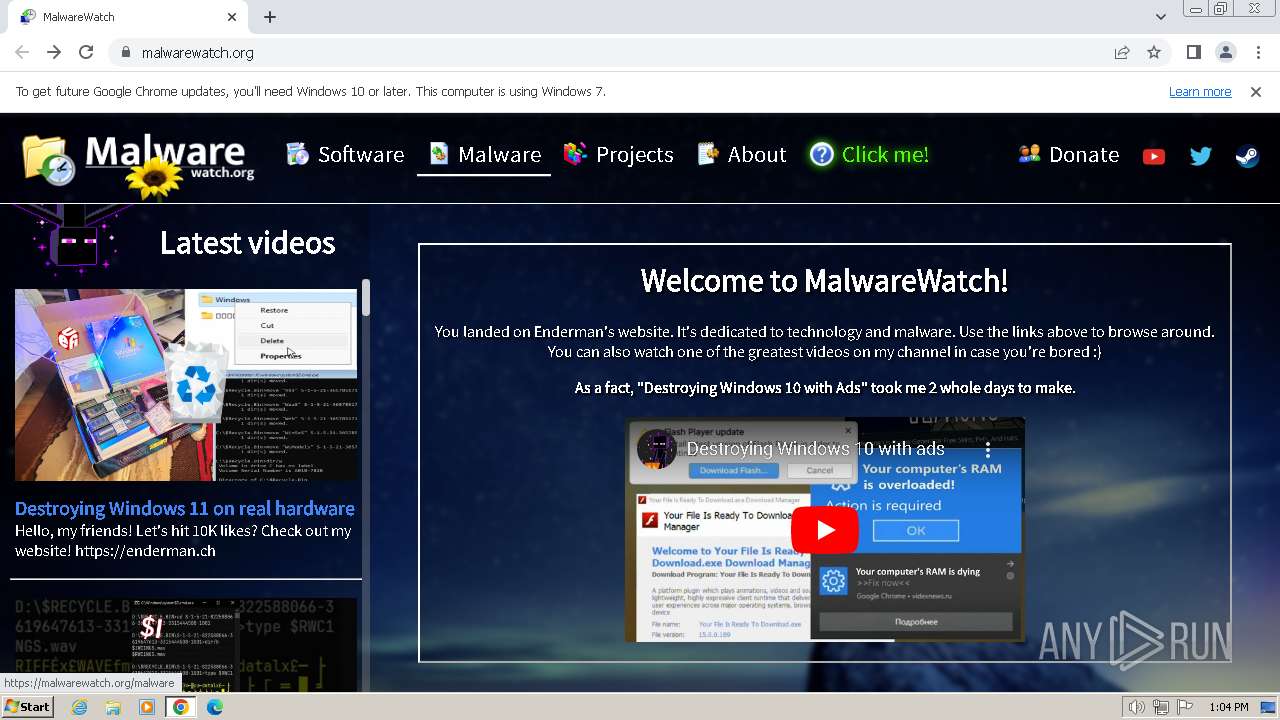
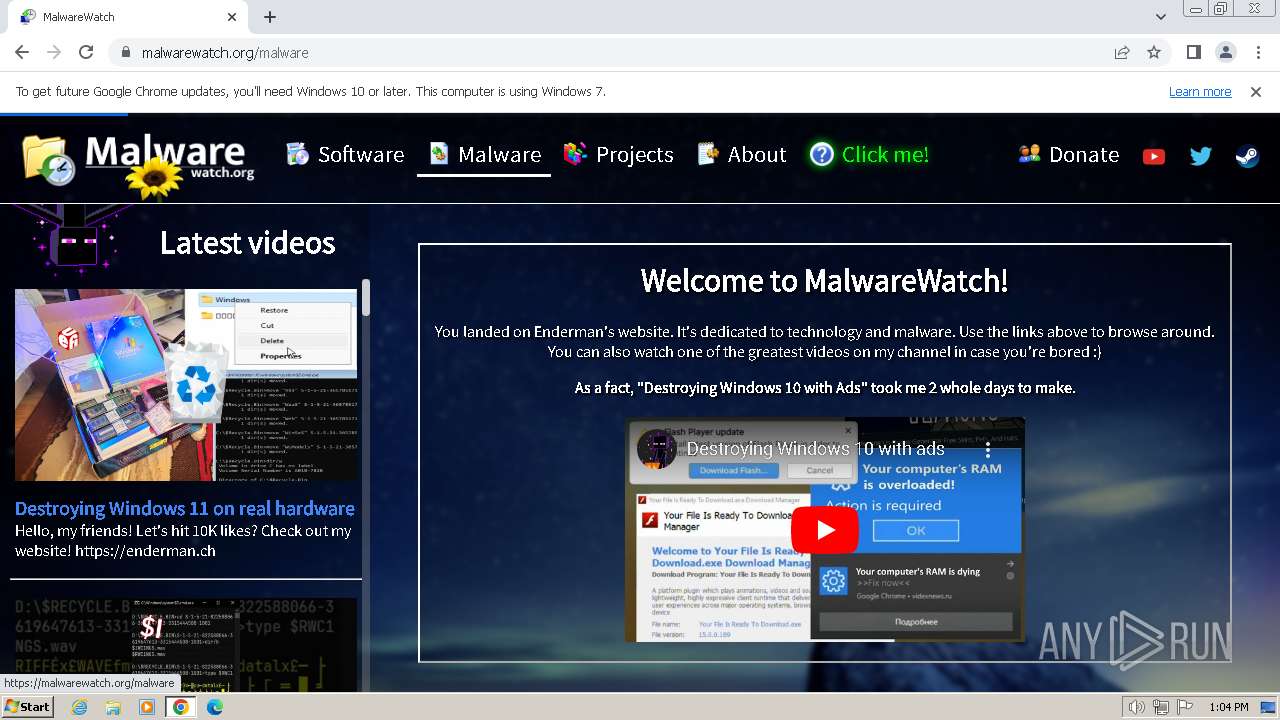
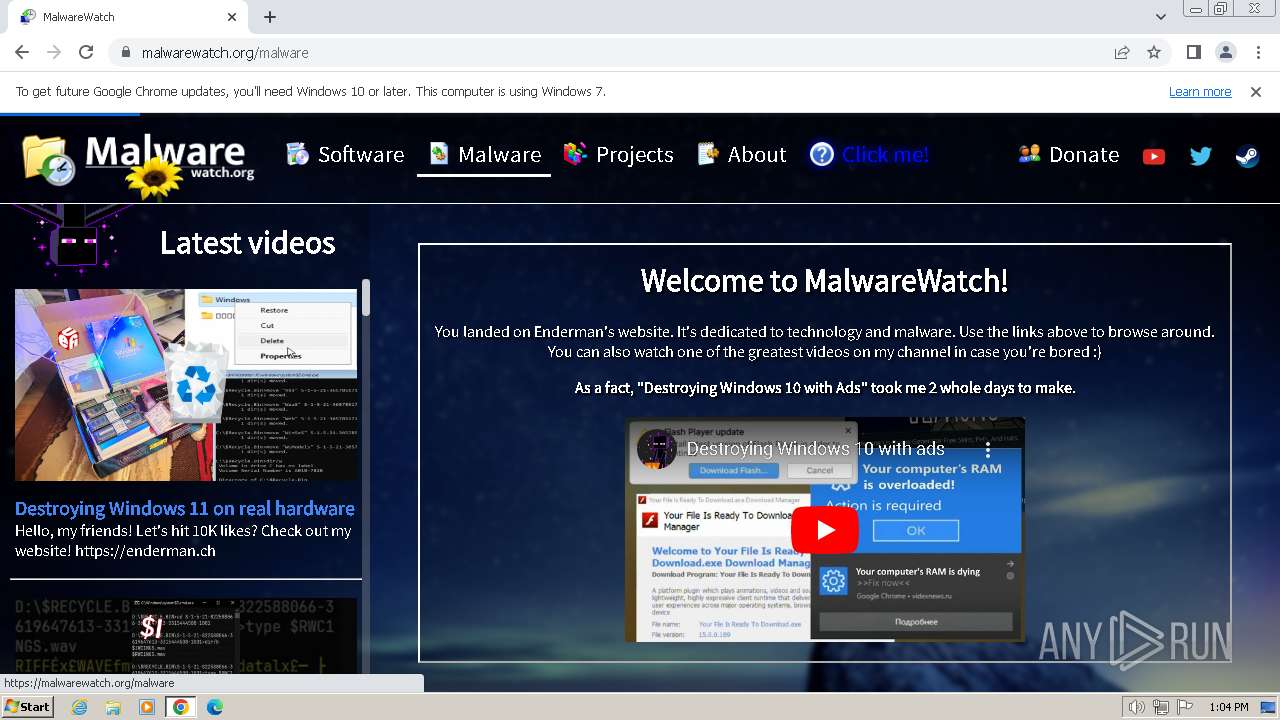
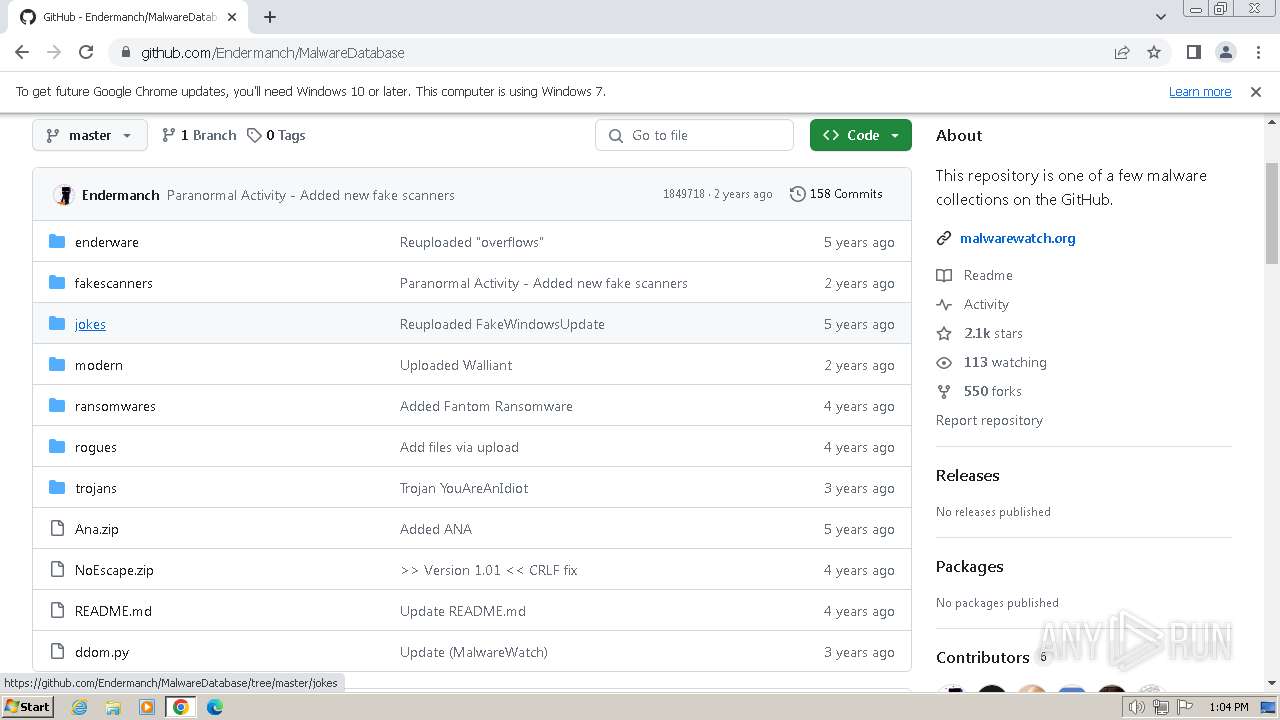
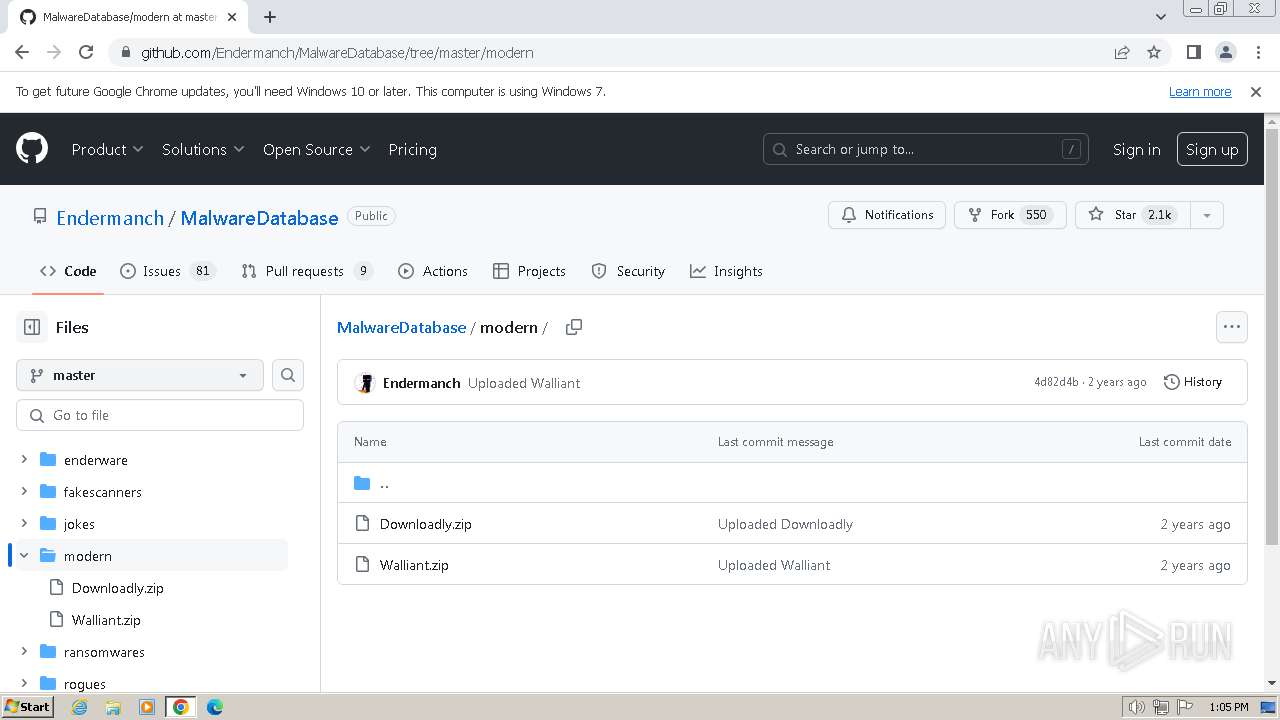
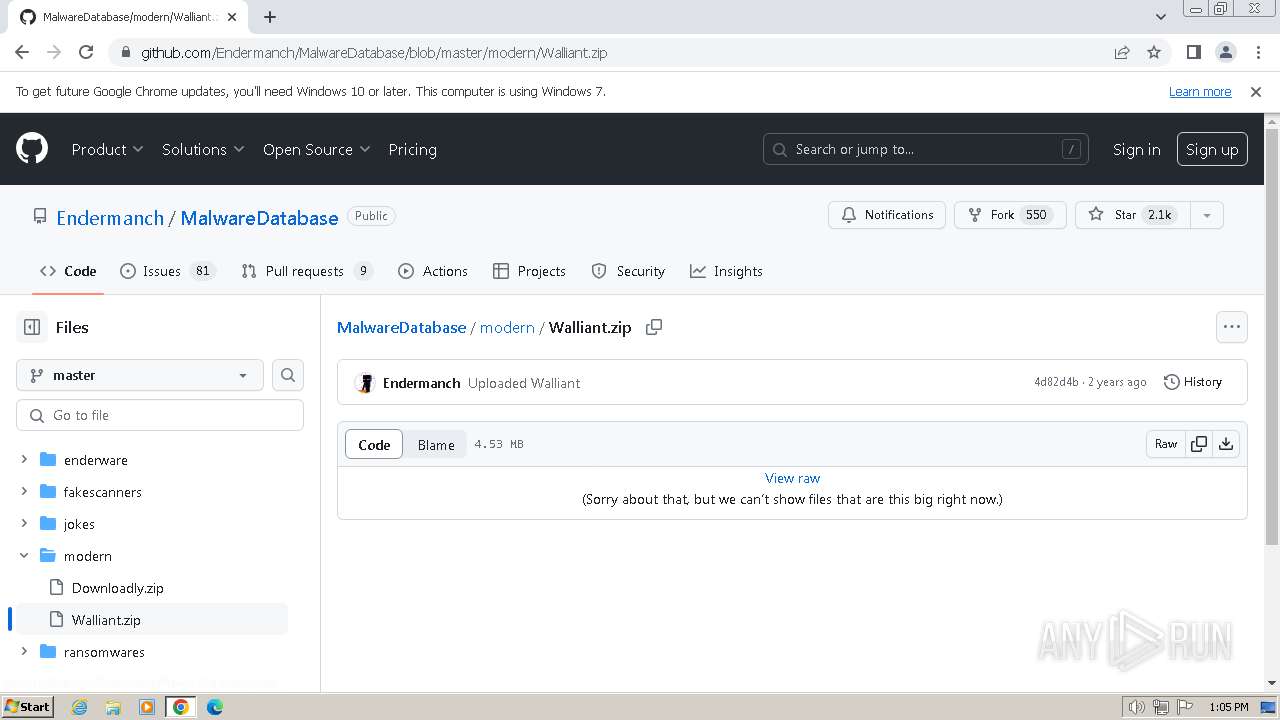
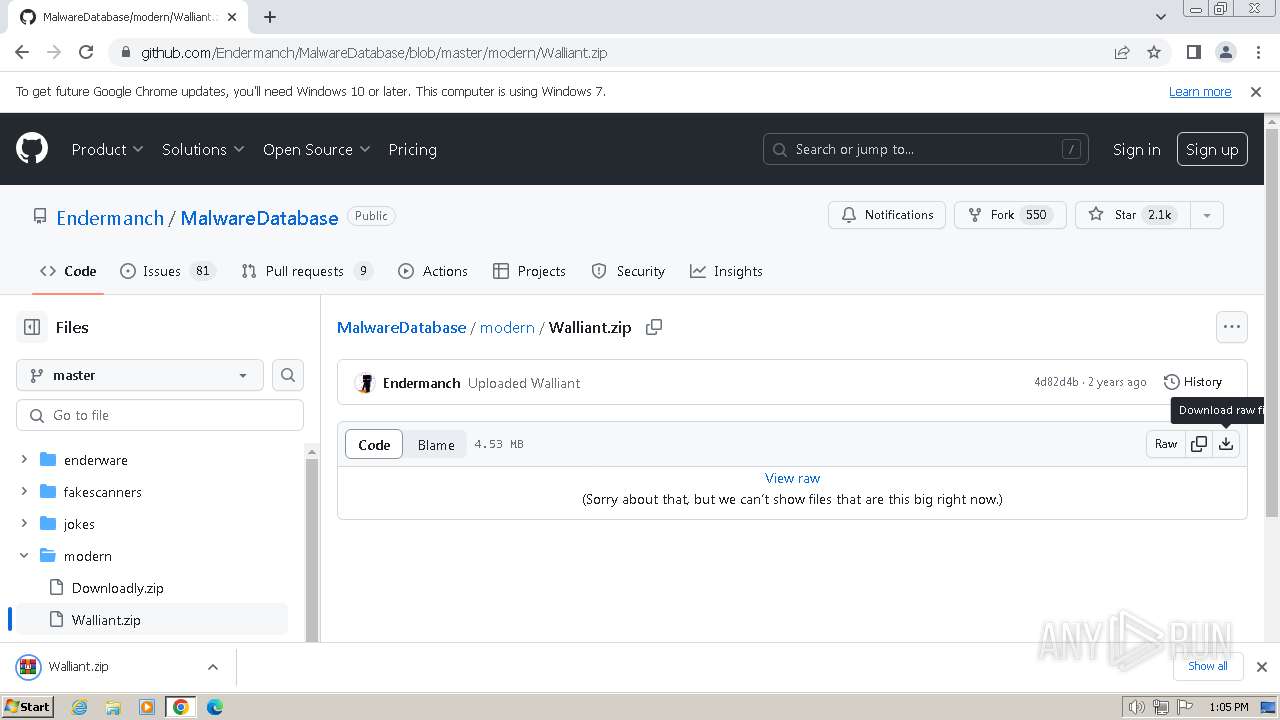
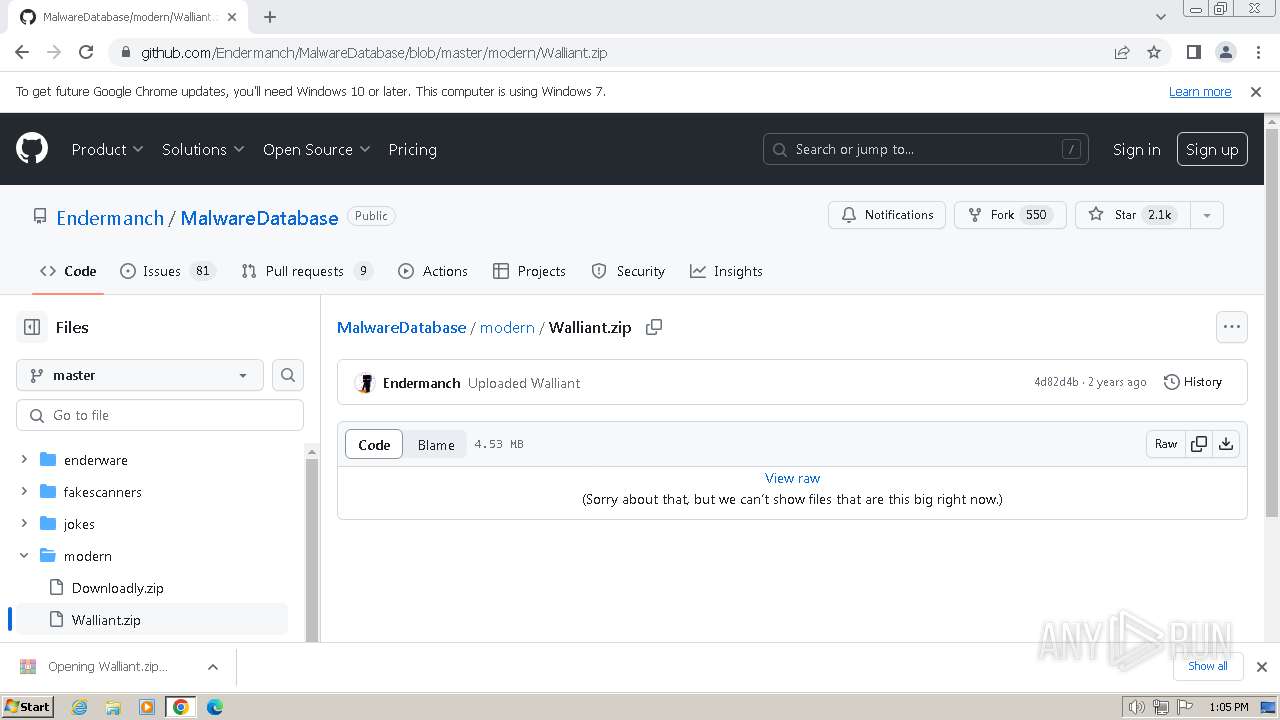
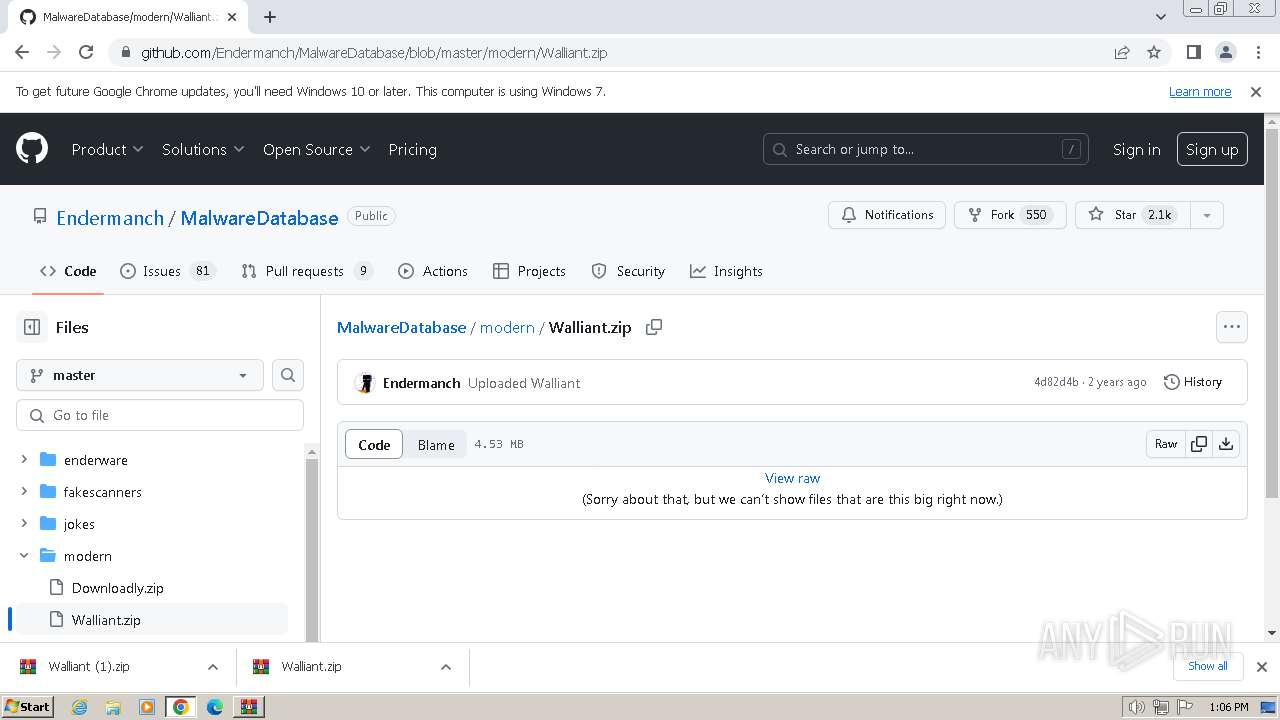
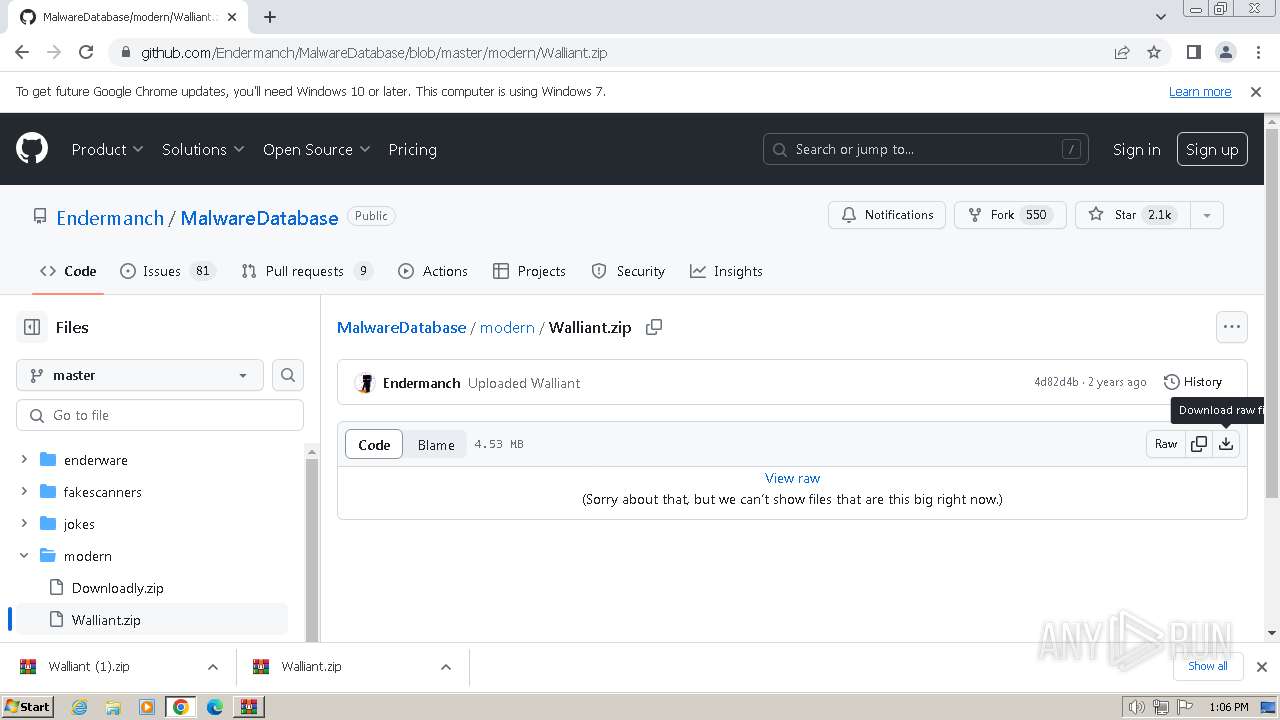
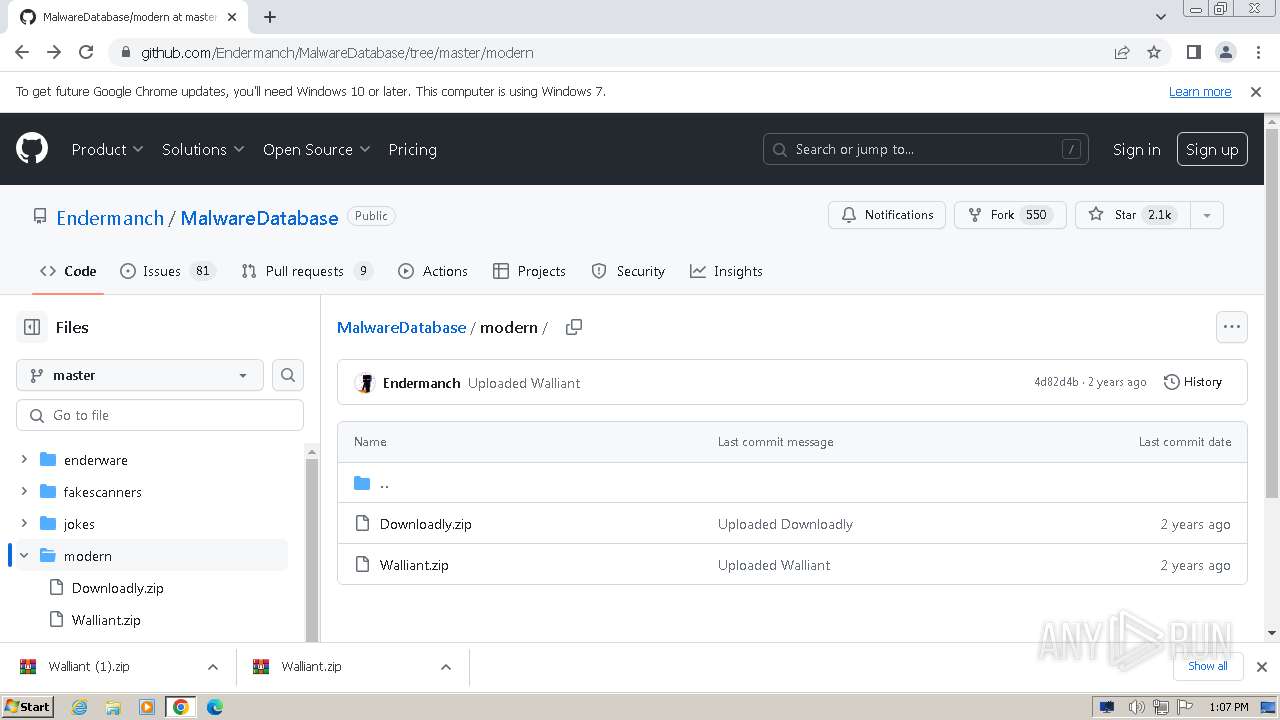
| URL: | malwarewatch.org |
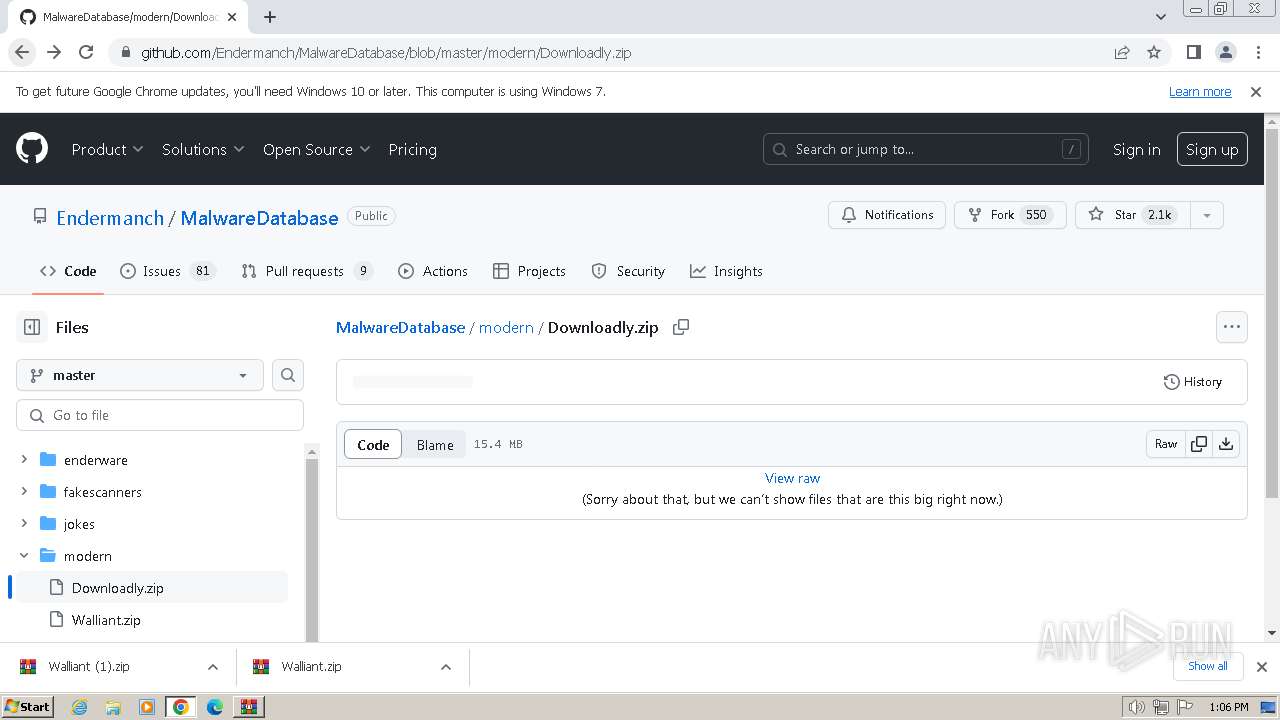
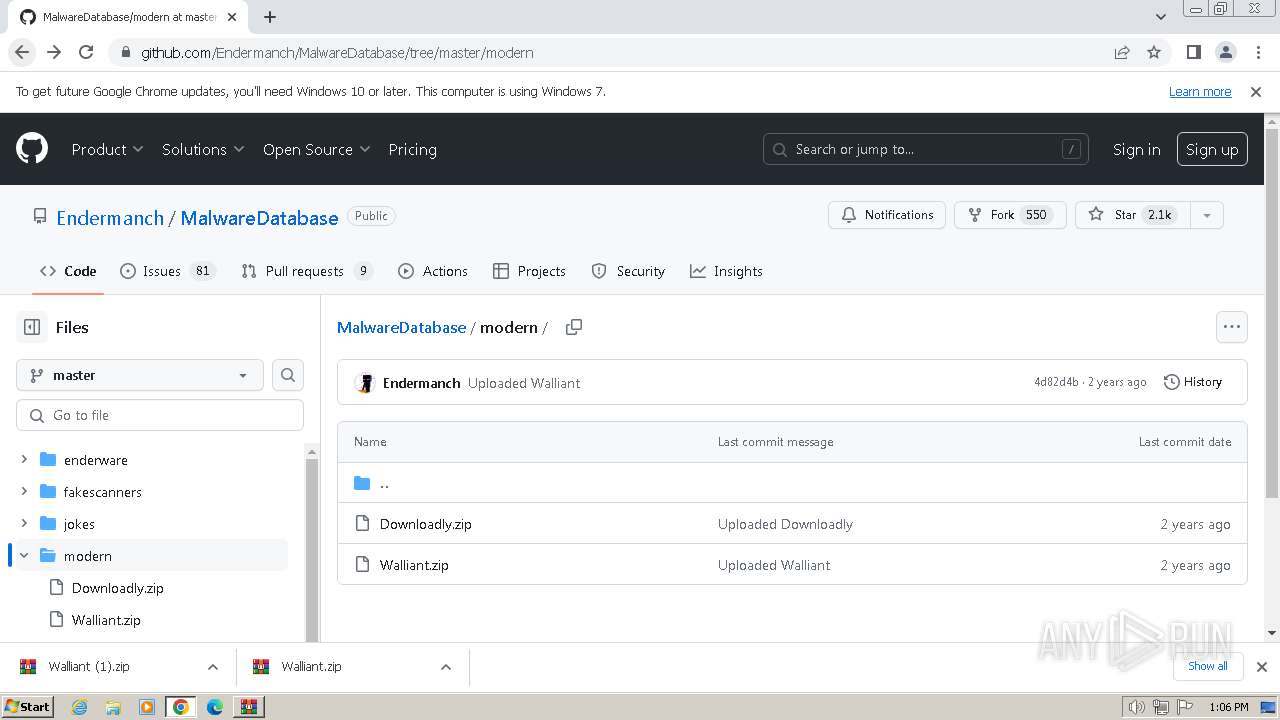
| Full analysis: | https://app.any.run/tasks/14e34631-d122-46d8-a3f3-db99358e6358 |
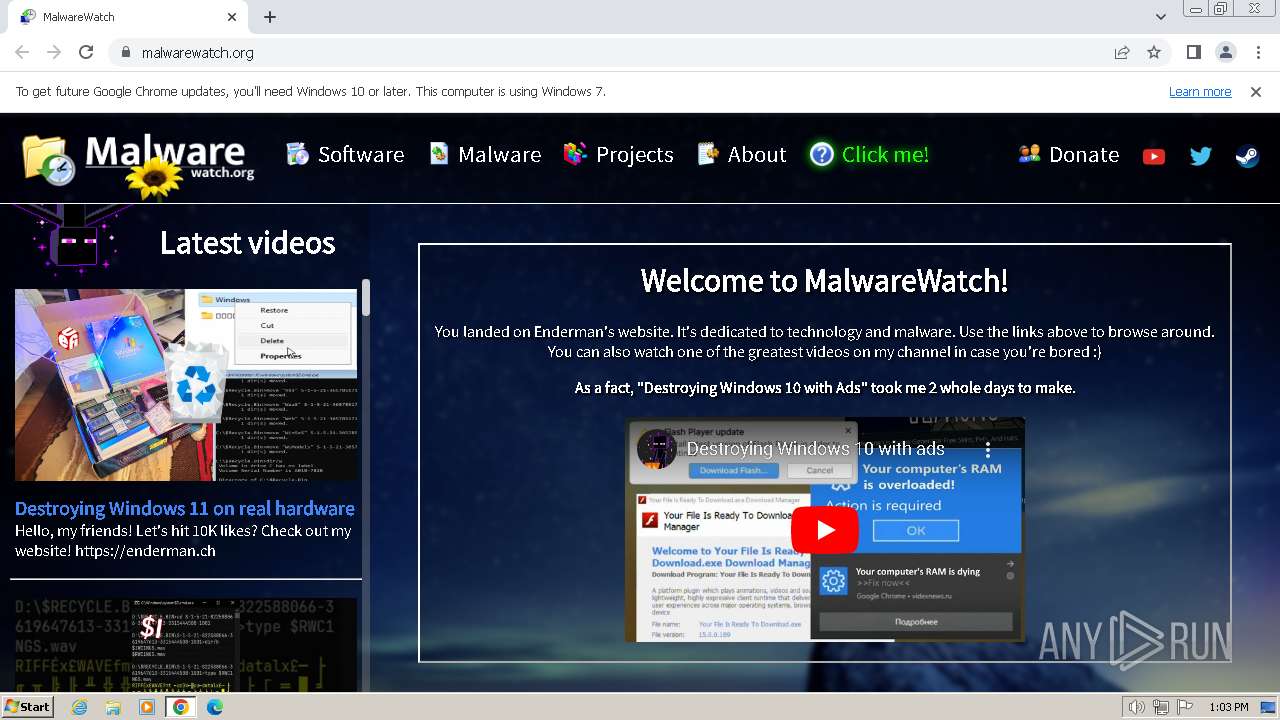
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2024, 13:03:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 12C0EEC13DDBEBFDA3B6E37BCE7A3A14 |
| SHA1: | A409911DB94F419276109E194BAD8A96F6066631 |
| SHA256: | 7566935D309A53867953F0B94B6B60151F93140EE8B30F3CFDCAF57220C22D82 |
| SSDEEP: | 3:5c+0gNn:EY |
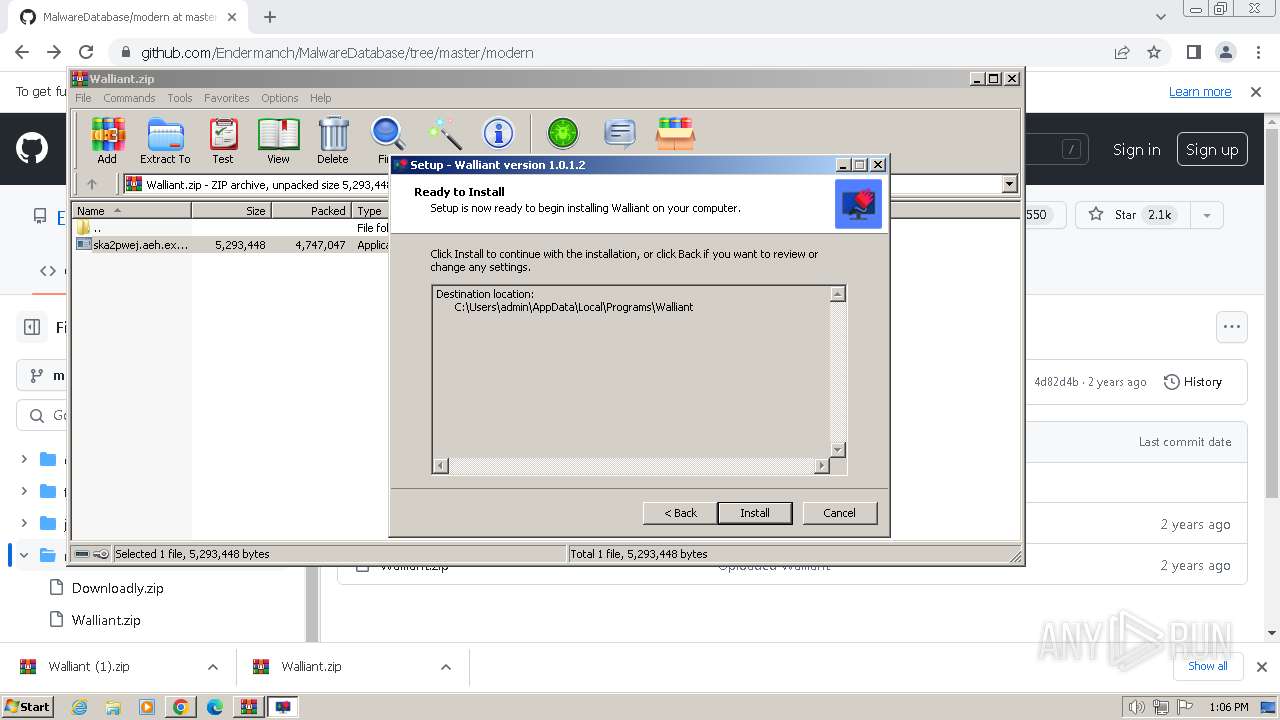
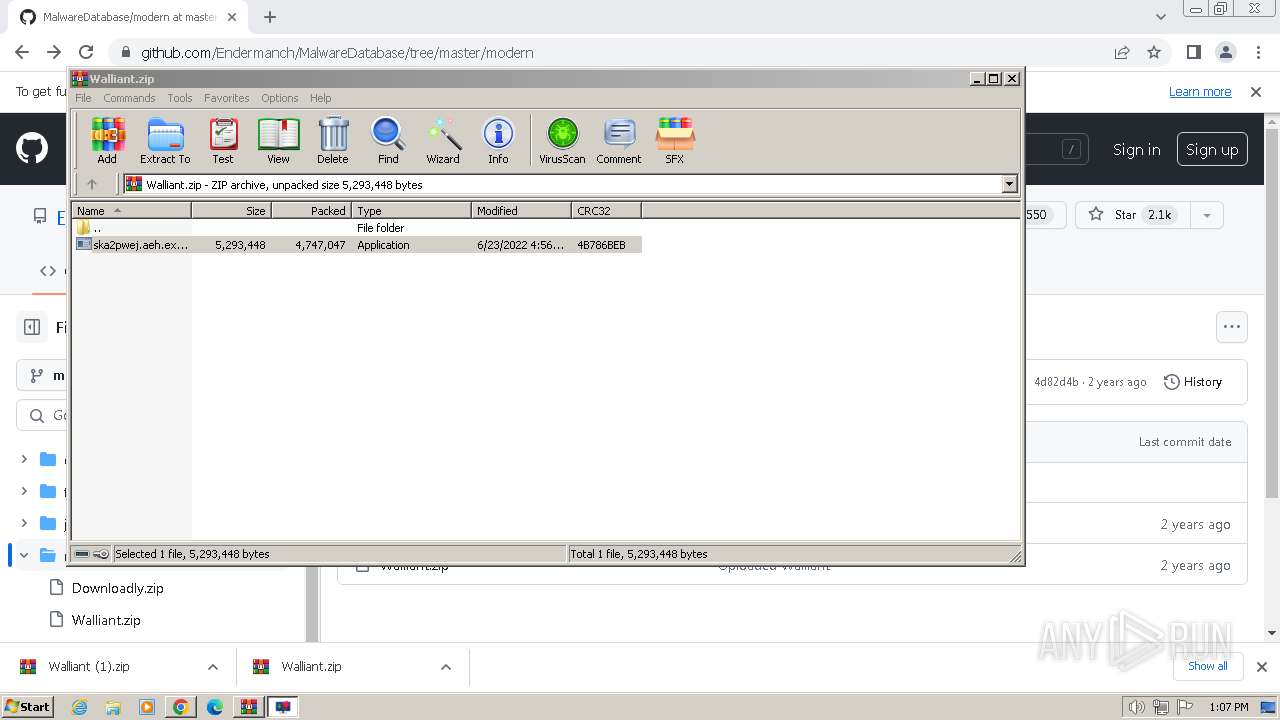
MALICIOUS
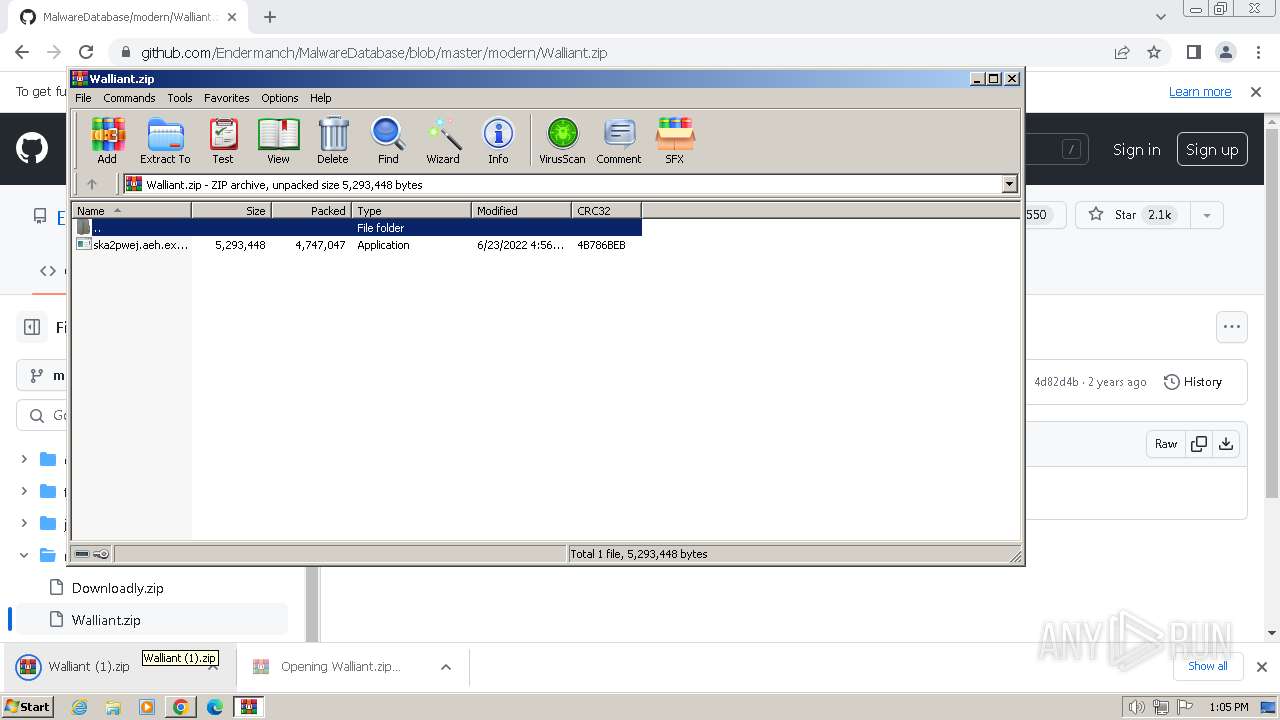
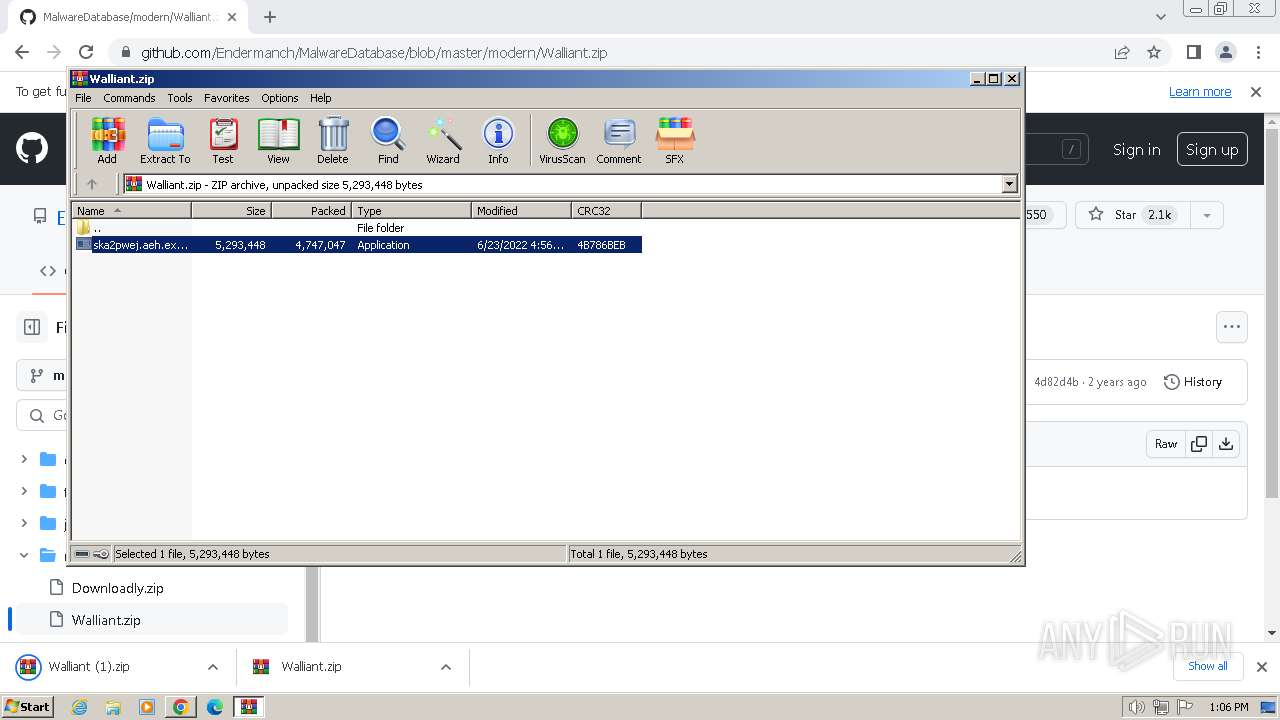
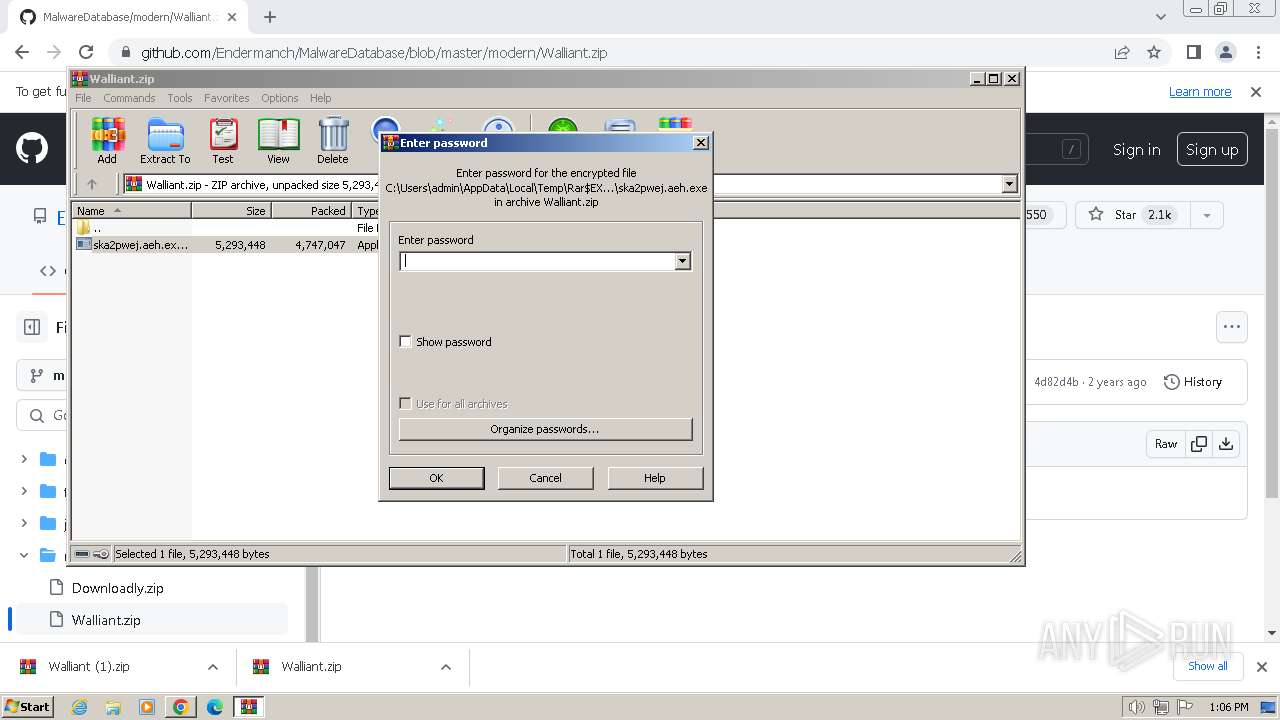
Drops the executable file immediately after the start
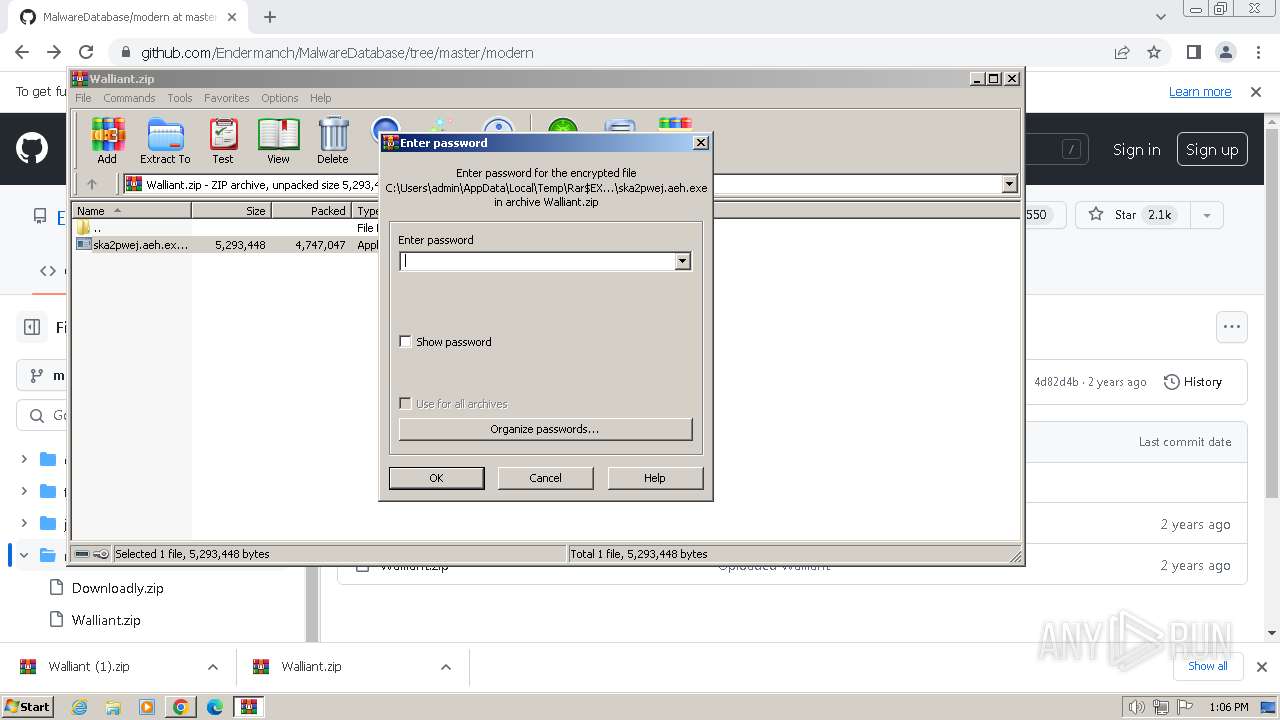
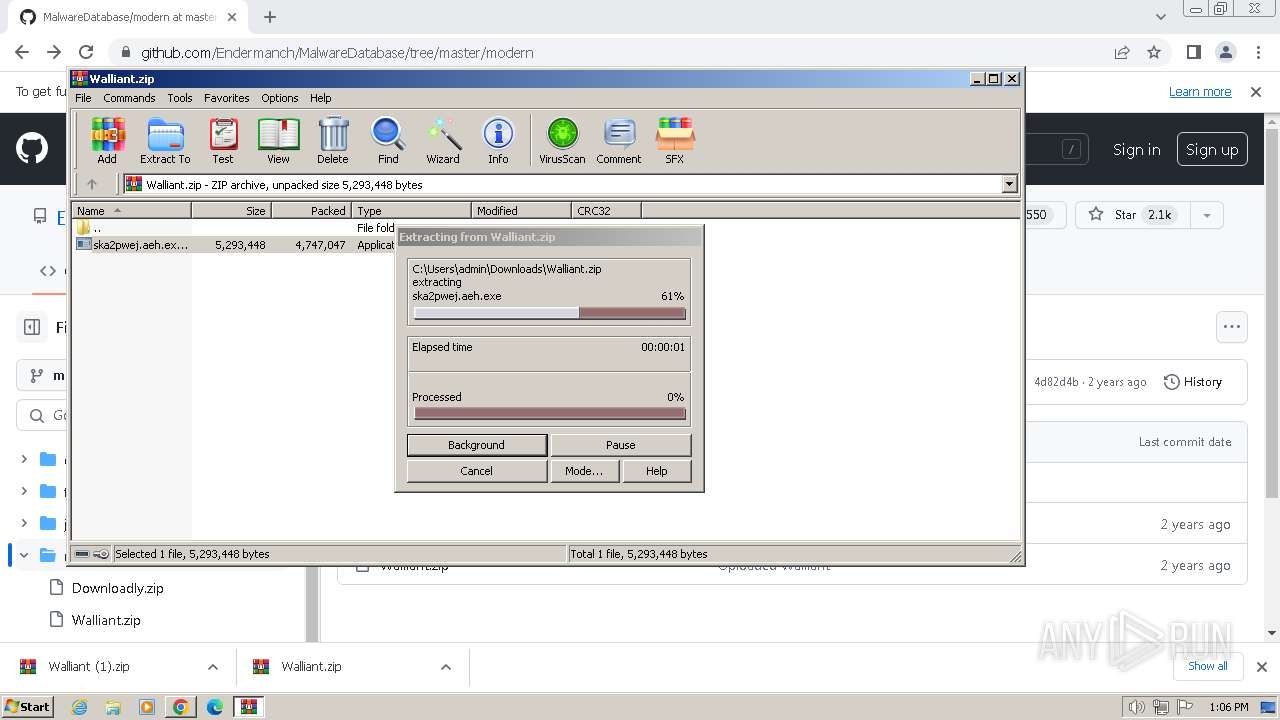
- ska2pwej.aeh.exe (PID: 3912)
- ska2pwej.aeh.tmp (PID: 3308)
Changes the autorun value in the registry
- ska2pwej.aeh.tmp (PID: 3308)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3412)
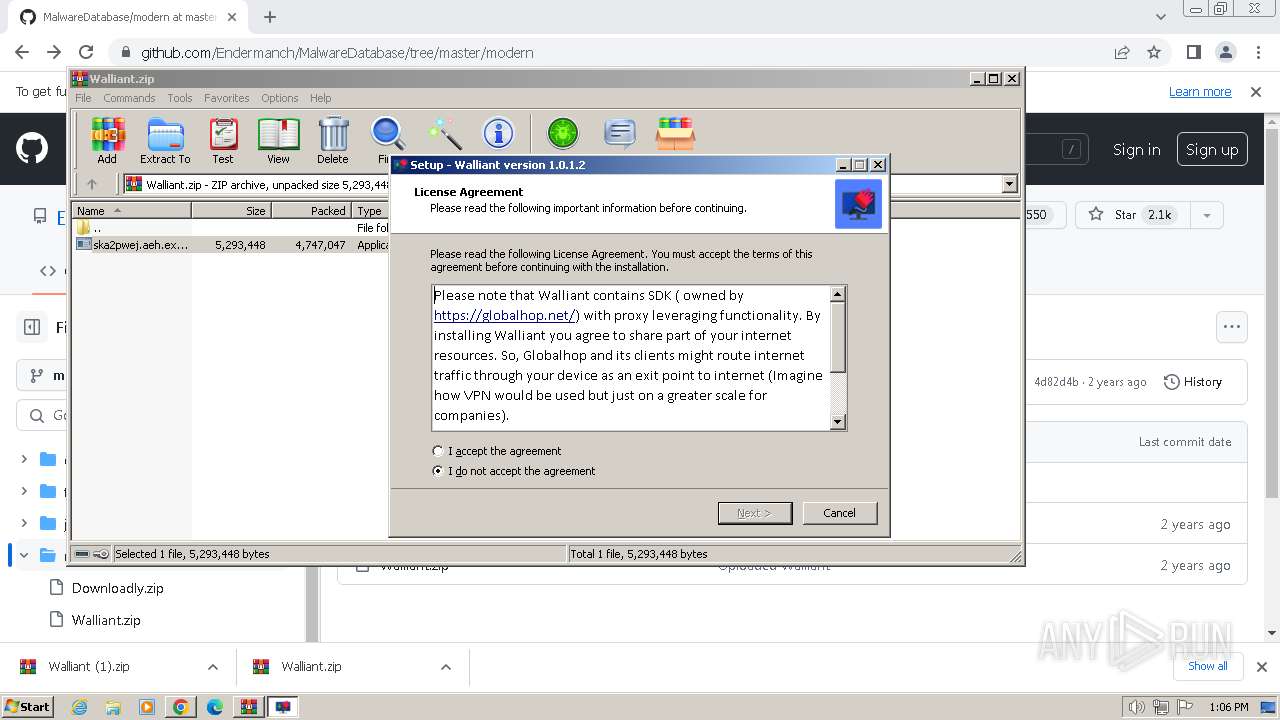
- walliant.exe (PID: 2820)
- walliant.exe (PID: 4024)
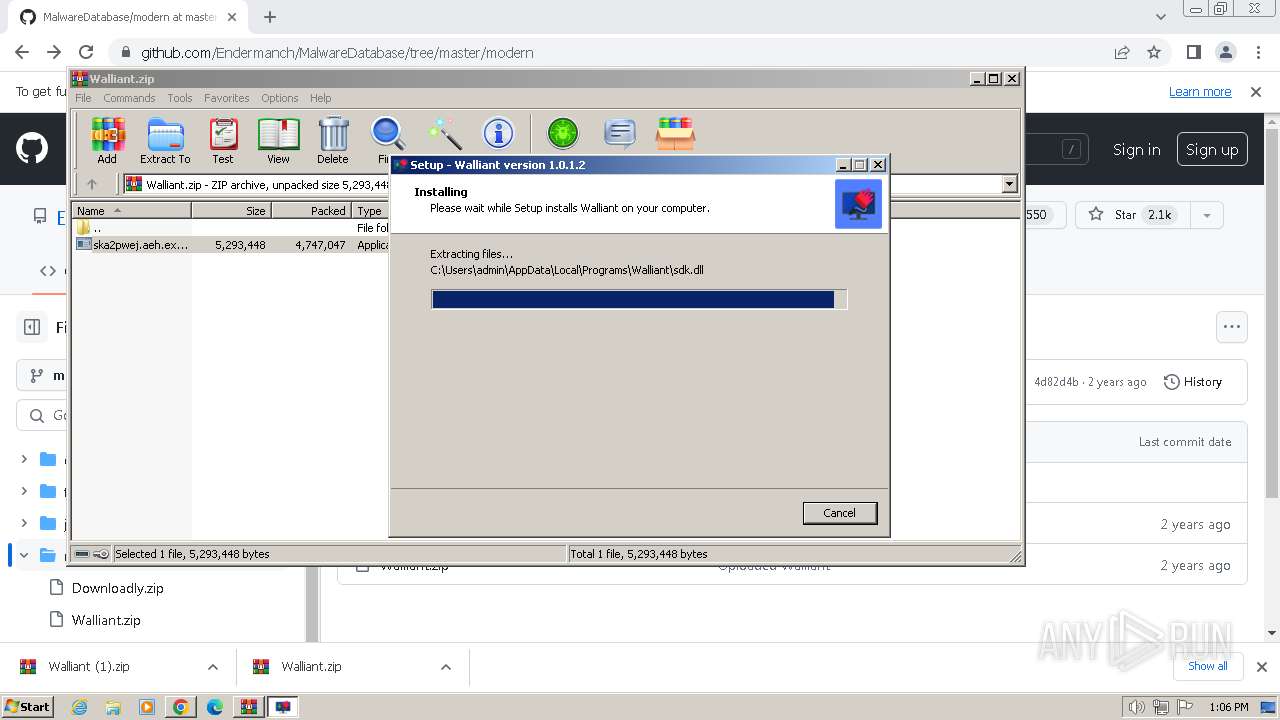
Executable content was dropped or overwritten
- ska2pwej.aeh.exe (PID: 3912)
- ska2pwej.aeh.tmp (PID: 3308)
Reads the Windows owner or organization settings
- ska2pwej.aeh.tmp (PID: 3308)
Reads settings of System Certificates
- ska2pwej.aeh.tmp (PID: 3308)
- walliant.exe (PID: 2820)
- walliant.exe (PID: 4024)
Process drops legitimate windows executable
- ska2pwej.aeh.tmp (PID: 3308)
Checks Windows Trust Settings
- walliant.exe (PID: 2820)
- walliant.exe (PID: 4024)
Reads the Internet Settings
- walliant.exe (PID: 2820)
Reads Internet Explorer settings
- walliant.exe (PID: 2820)
Checks for external IP
- walliant.exe (PID: 2820)
Connects to unusual port
- walliant.exe (PID: 2820)
Reads Microsoft Outlook installation path
- walliant.exe (PID: 2820)
INFO
The process uses the downloaded file
- chrome.exe (PID: 2796)
- chrome.exe (PID: 3860)
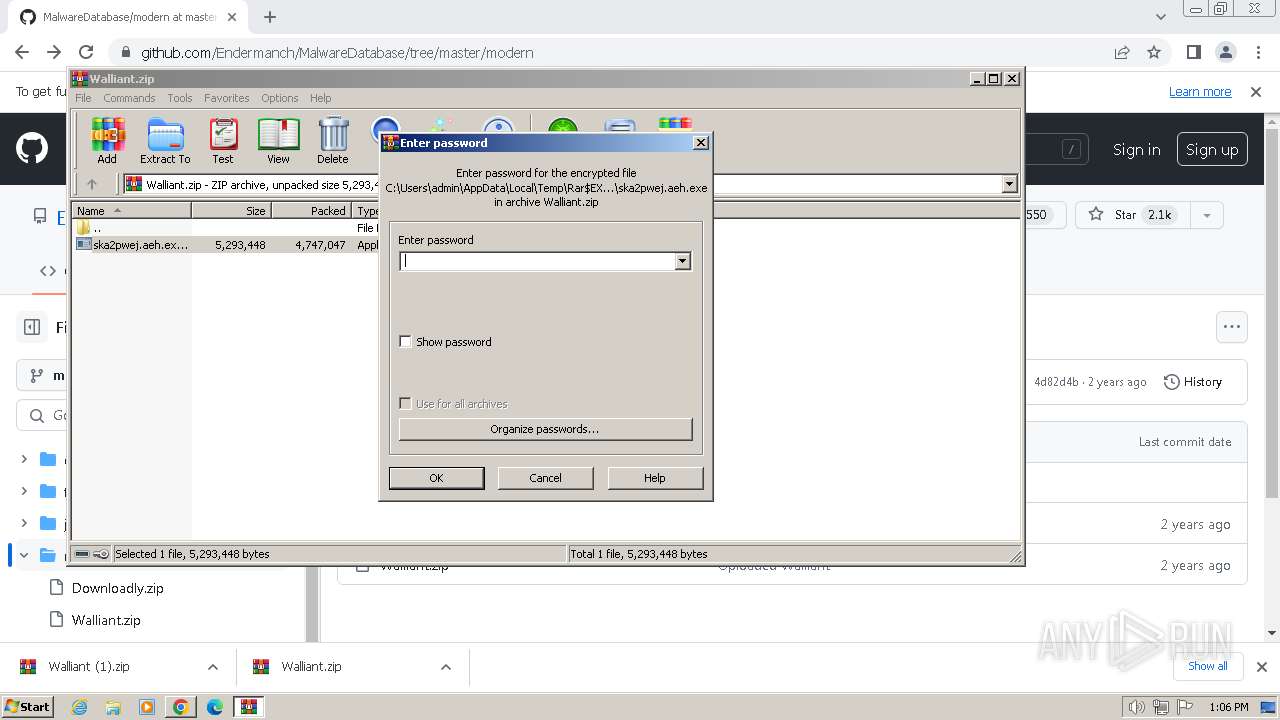
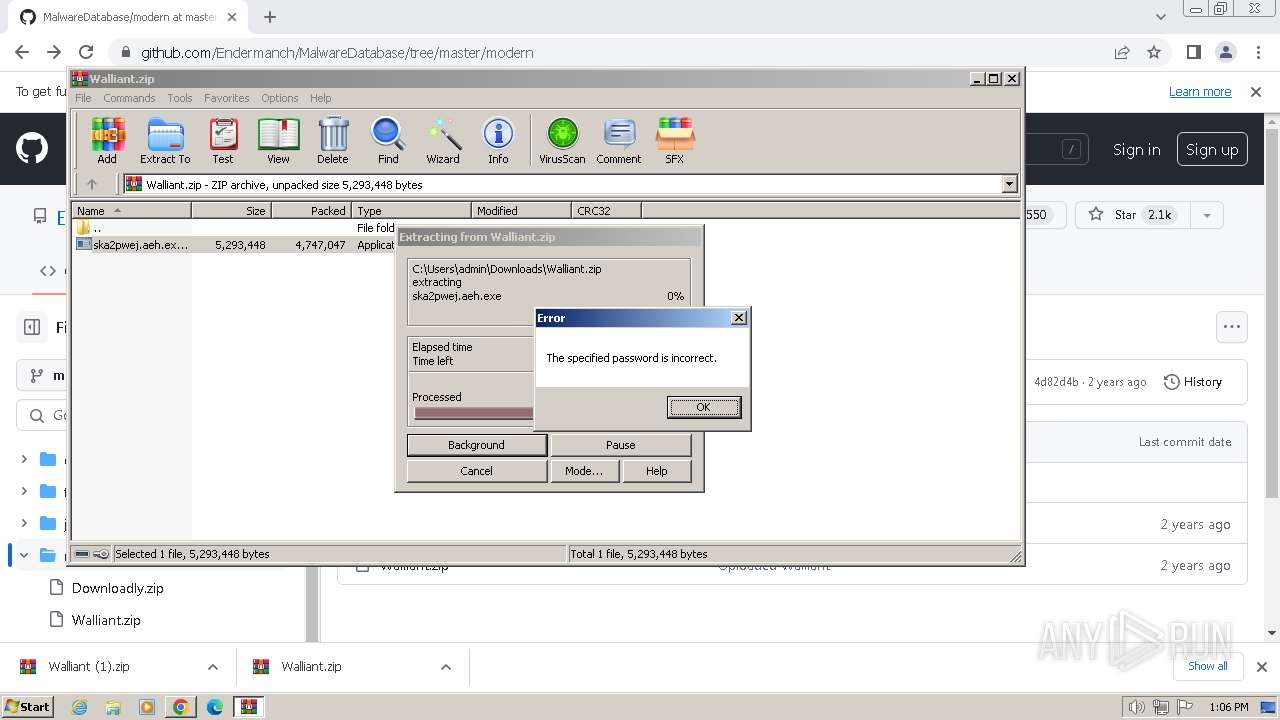
- WinRAR.exe (PID: 3412)
Checks supported languages
- wmpnscfg.exe (PID: 3988)
- ska2pwej.aeh.exe (PID: 3912)
- ska2pwej.aeh.tmp (PID: 3308)
- walliant.exe (PID: 2820)
- walliant.exe (PID: 4024)
Reads the computer name
- wmpnscfg.exe (PID: 3988)
- ska2pwej.aeh.tmp (PID: 3308)
- walliant.exe (PID: 2820)
- walliant.exe (PID: 4024)
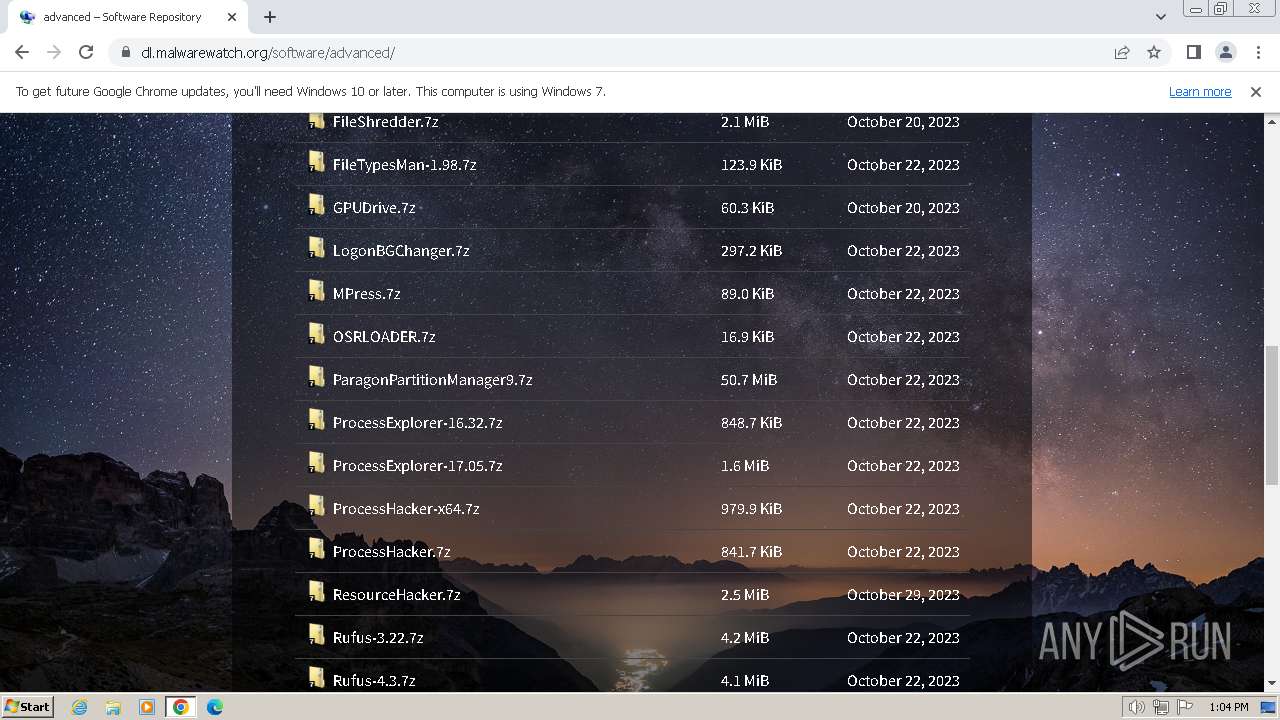
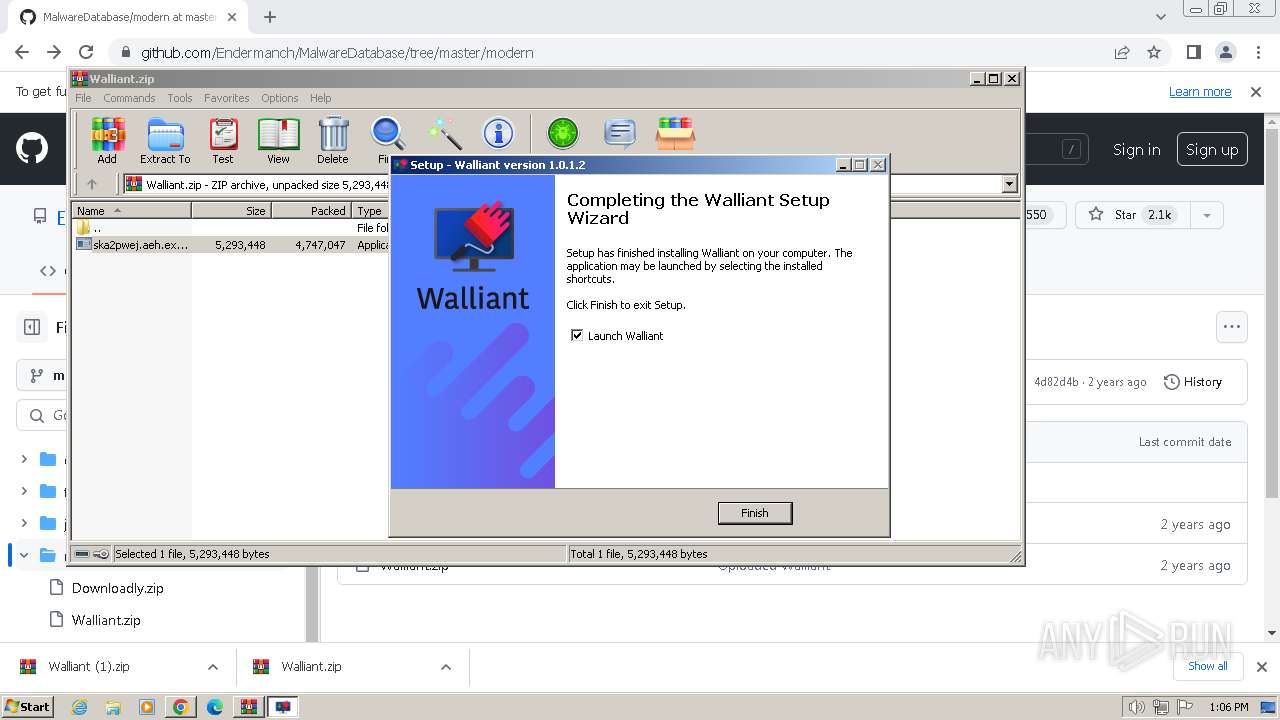
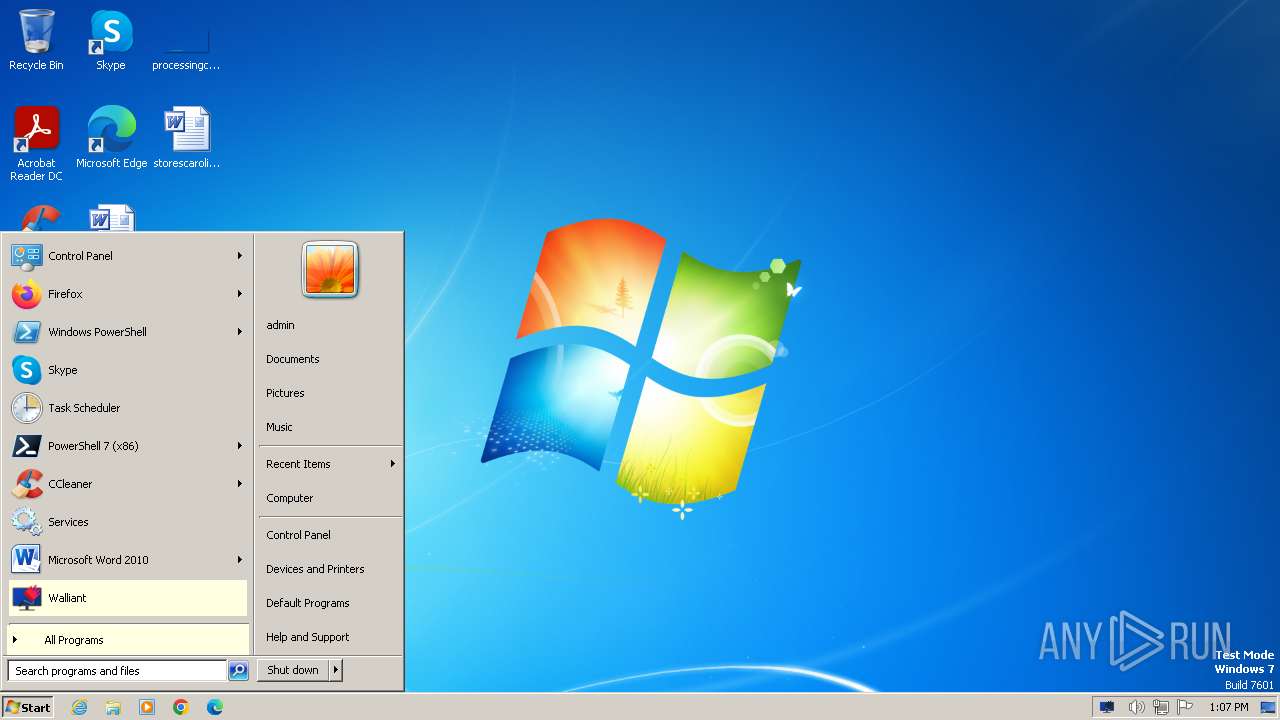
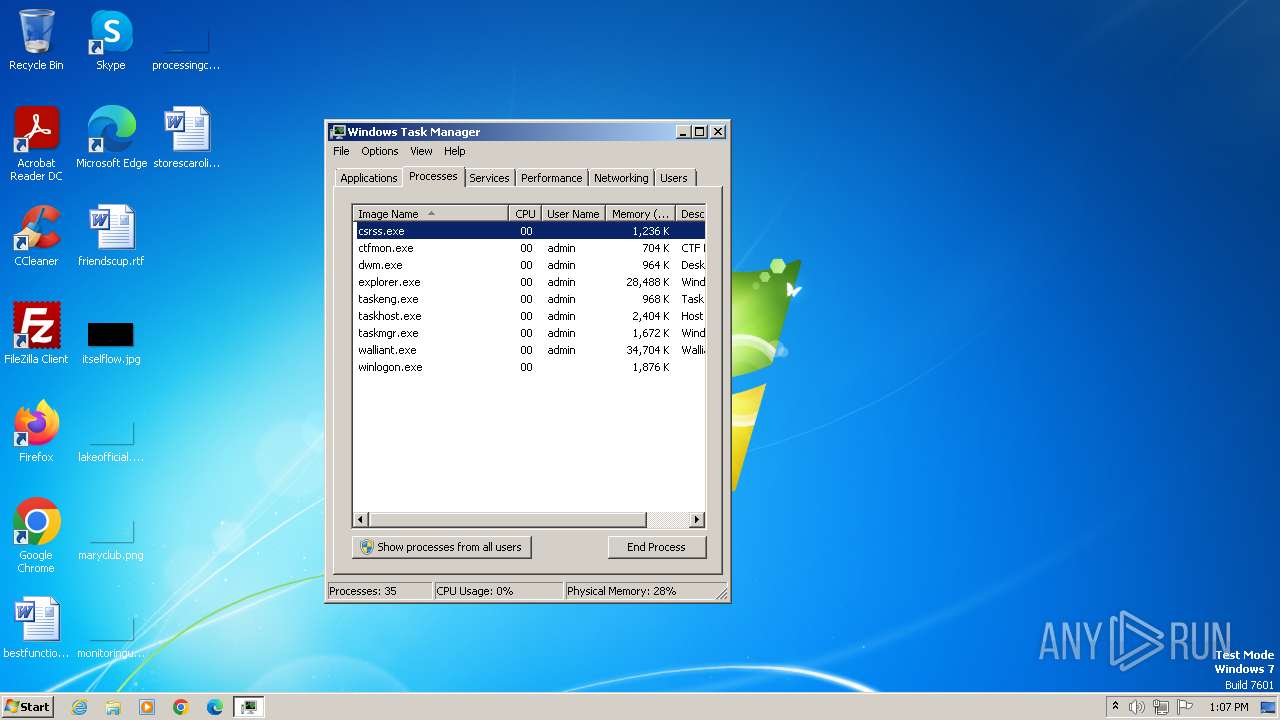
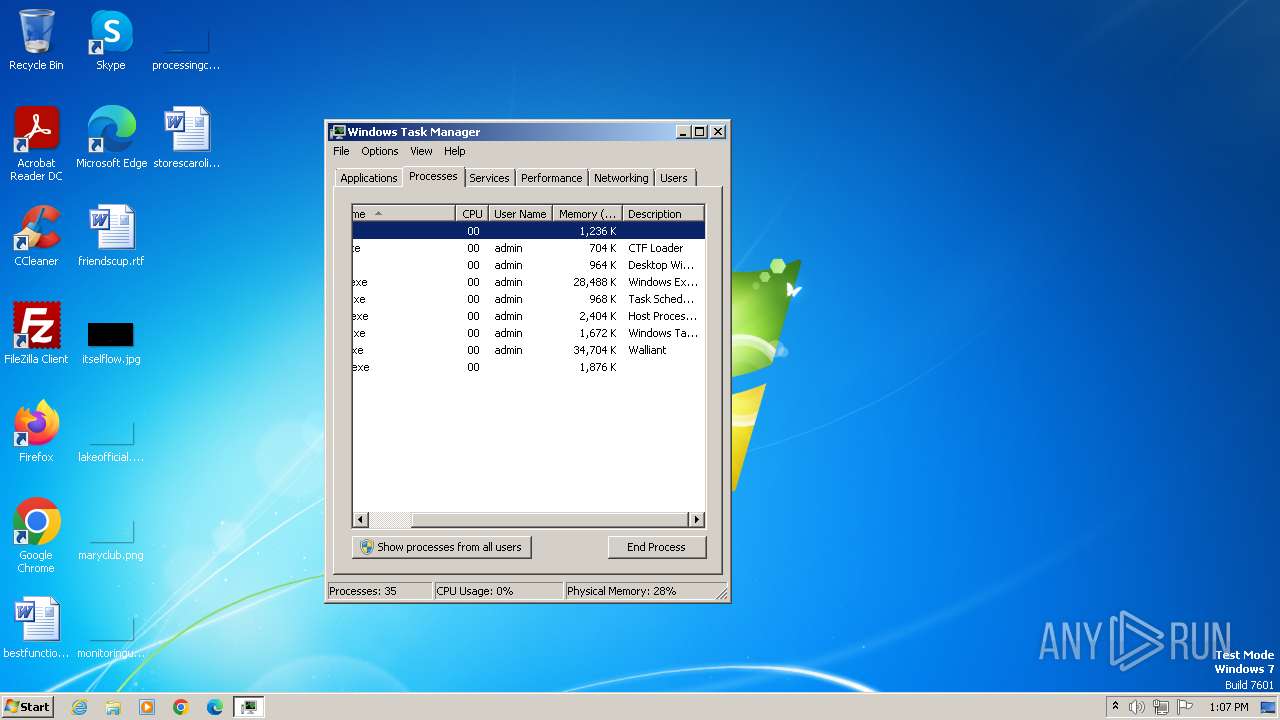
Manual execution by a user
- wmpnscfg.exe (PID: 3988)
- walliant.exe (PID: 4024)
- taskmgr.exe (PID: 1036)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3412)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3412)
Application launched itself
- chrome.exe (PID: 1384)
Create files in a temporary directory
- ska2pwej.aeh.exe (PID: 3912)
- walliant.exe (PID: 2820)
Reads the machine GUID from the registry
- ska2pwej.aeh.tmp (PID: 3308)
- walliant.exe (PID: 2820)
- walliant.exe (PID: 4024)
Reads the software policy settings
- ska2pwej.aeh.tmp (PID: 3308)
- walliant.exe (PID: 2820)
- walliant.exe (PID: 4024)
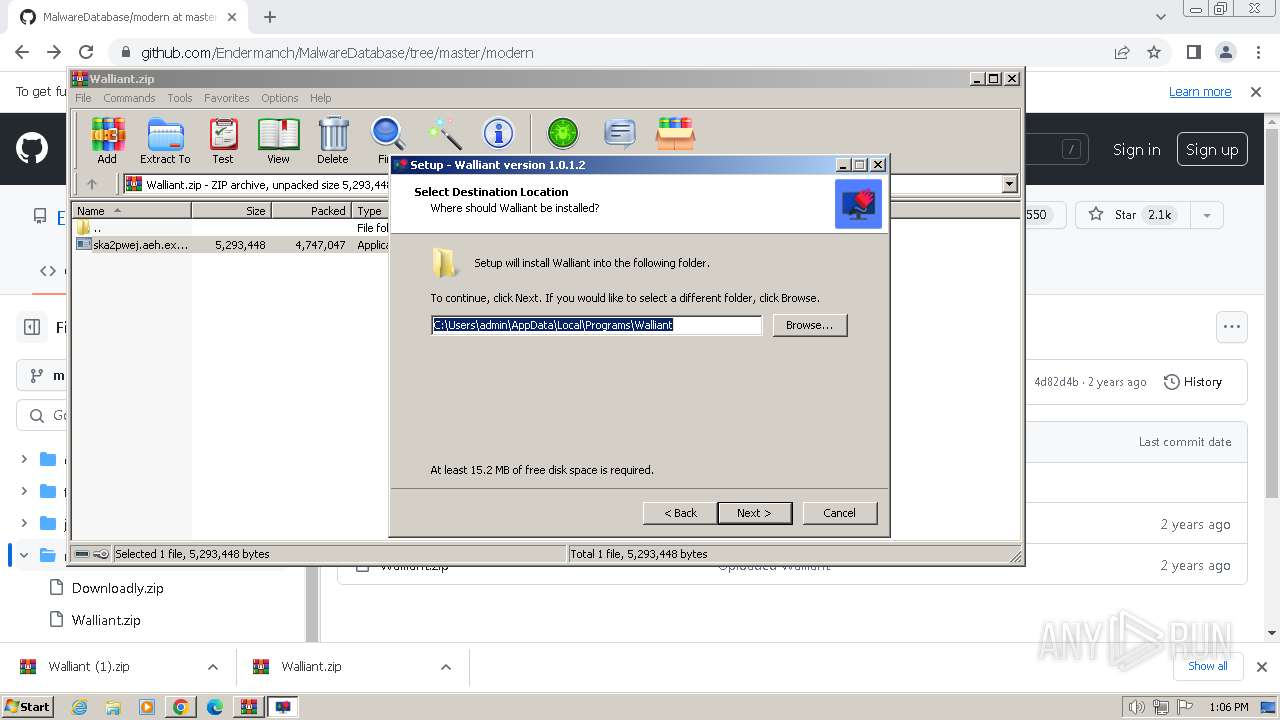
Creates files or folders in the user directory
- ska2pwej.aeh.tmp (PID: 3308)
- walliant.exe (PID: 2820)
Creates a software uninstall entry
- ska2pwej.aeh.tmp (PID: 3308)
Reads Environment values
- walliant.exe (PID: 2820)
Reads product name
- walliant.exe (PID: 2820)
Checks proxy server information
- walliant.exe (PID: 2820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
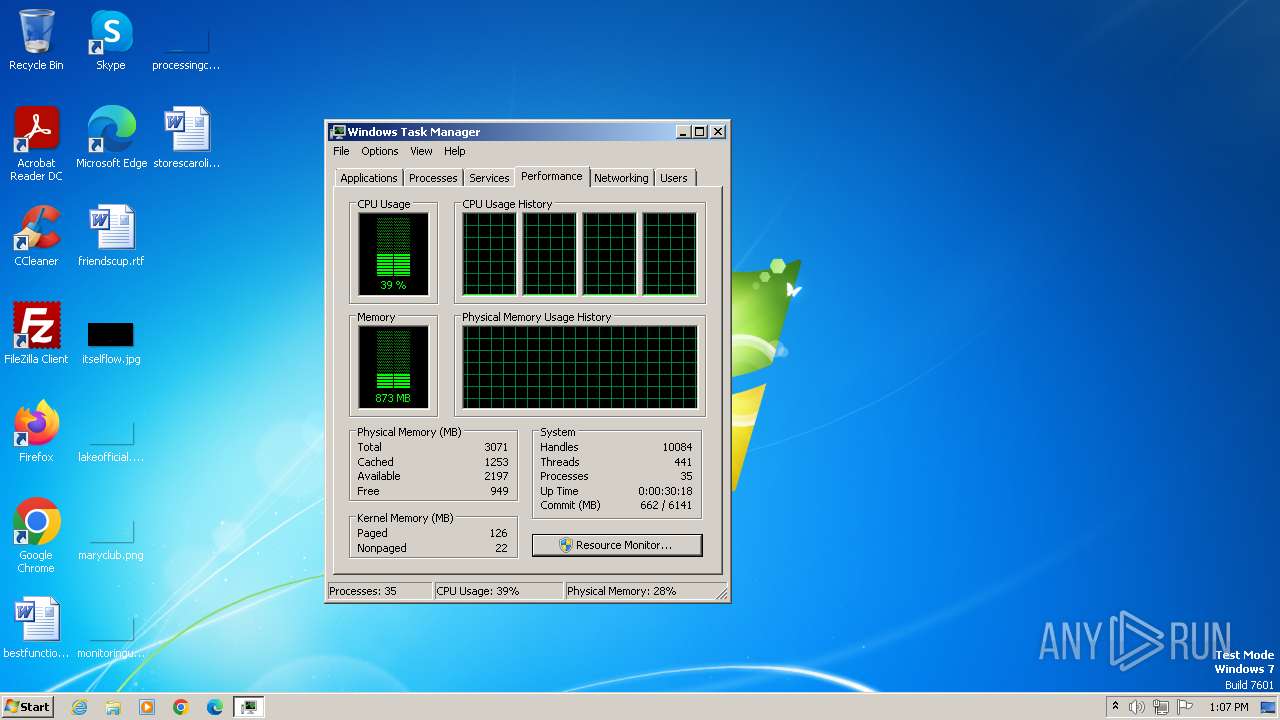
Total processes
70
Monitored processes
30
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=2560 --field-trial-handle=1156,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --mojo-platform-channel-handle=3172 --field-trial-handle=1156,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=2936 --field-trial-handle=1156,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1036 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=2016 --field-trial-handle=1156,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1332 --field-trial-handle=1156,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "malwarewatch.org" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1232 --field-trial-handle=1156,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=1340 --field-trial-handle=1156,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3620 --field-trial-handle=1156,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
31 479
Read events
31 225
Write events
235
Delete events
19
Modification events
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
19
Suspicious files
91
Text files
42
Unknown types
67
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f165.TMP | — | |
MD5:— | SHA256:— | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF17f30a.TMP | text | |
MD5:F5B58F0B08202C8D6DE12514994A84BF | SHA256:F5BA8809B6A3920A11CF31E7F6A1DEC46EF4F4339D6158967CCB1405409D1241 | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17f155.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17f4b0.TMP | — | |
MD5:— | SHA256:— | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17f155.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
104
DNS requests
101
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
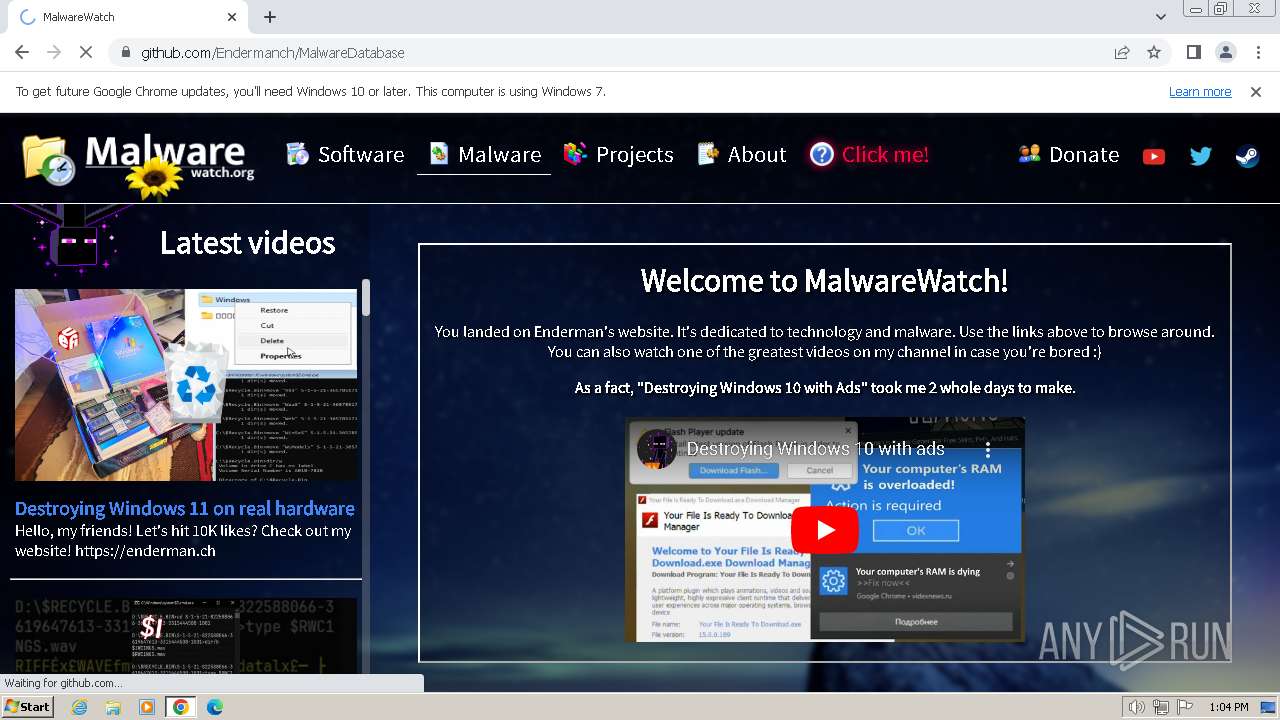
2752 | chrome.exe | GET | 301 | 188.114.96.3:80 | http://malwarewatch.org/ | unknown | — | — | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 3.07 Kb | unknown |
2820 | walliant.exe | GET | 200 | 178.79.208.1:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?4e8bb94d52841687 | unknown | compressed | 65.2 Kb | unknown |
2820 | walliant.exe | GET | 200 | 104.18.114.97:80 | http://ipv4.icanhazip.com:80/ | unknown | text | 13 b | unknown |
2820 | walliant.exe | POST | 200 | 101.32.104.41:80 | http://sgshort.wechat.com/mmtls/1da82c25 | unknown | binary | 33.6 Kb | unknown |
2820 | walliant.exe | POST | 200 | 101.32.104.41:80 | http://sgshort.wechat.com/mmtls/1da82c25 | unknown | binary | 33.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2752 | chrome.exe | 142.251.168.84:443 | accounts.google.com | GOOGLE | US | unknown |
1384 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2752 | chrome.exe | 188.114.96.3:80 | malwarewatch.org | CLOUDFLARENET | NL | unknown |
2752 | chrome.exe | 188.114.96.3:443 | malwarewatch.org | CLOUDFLARENET | NL | unknown |
2752 | chrome.exe | 104.16.123.175:443 | unpkg.com | CLOUDFLARENET | — | shared |
2752 | chrome.exe | 172.64.207.38:443 | use.fontawesome.com | CLOUDFLARENET | US | unknown |
2752 | chrome.exe | 142.250.184.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
malwarewatch.org |
| whitelisted |
accounts.google.com |
| shared |
unpkg.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
use.fontawesome.com |
| whitelisted |
www.youtube.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
i.ytimg.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
static.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2752 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
2752 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2820 | walliant.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
2820 | walliant.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] Received IP address from server as result of HTTP request |