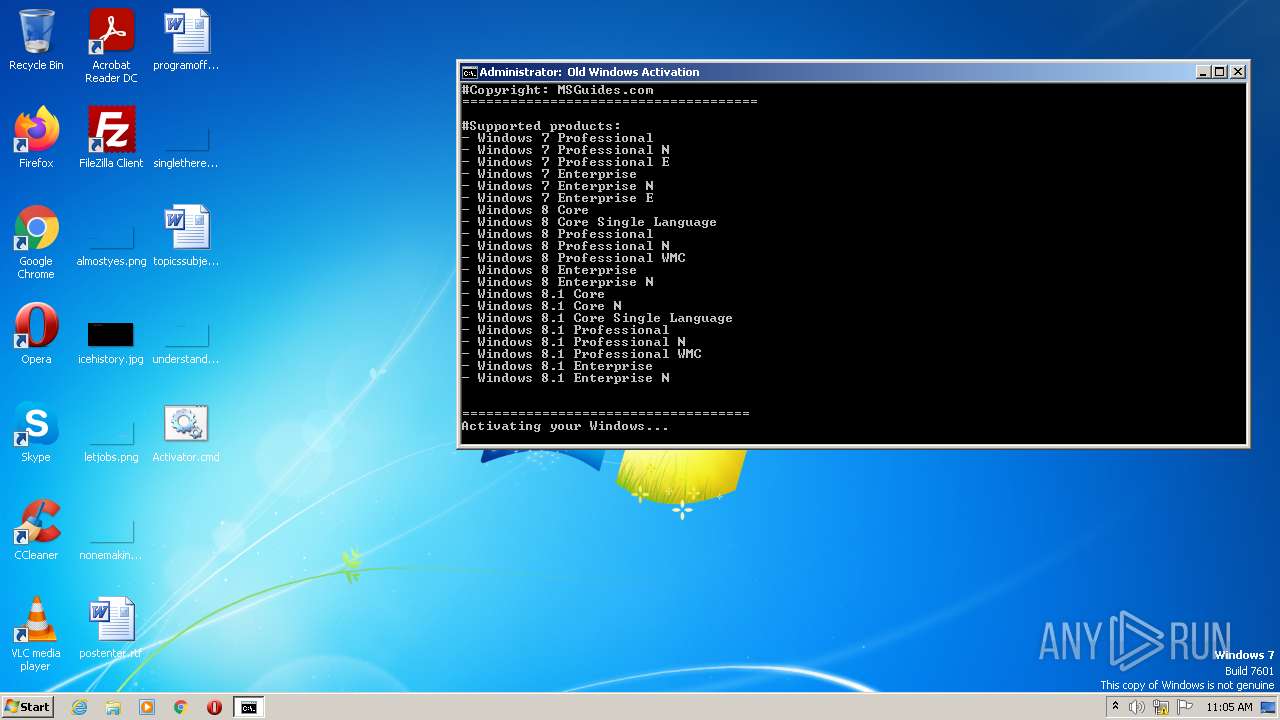
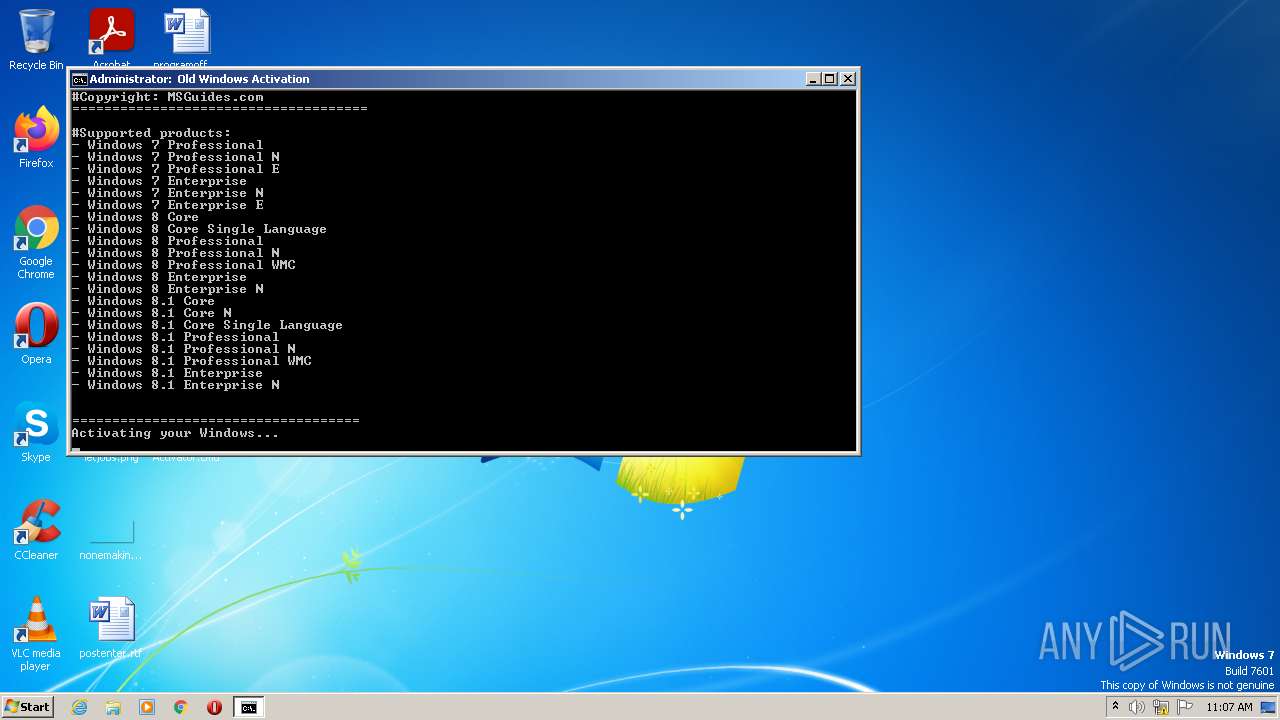
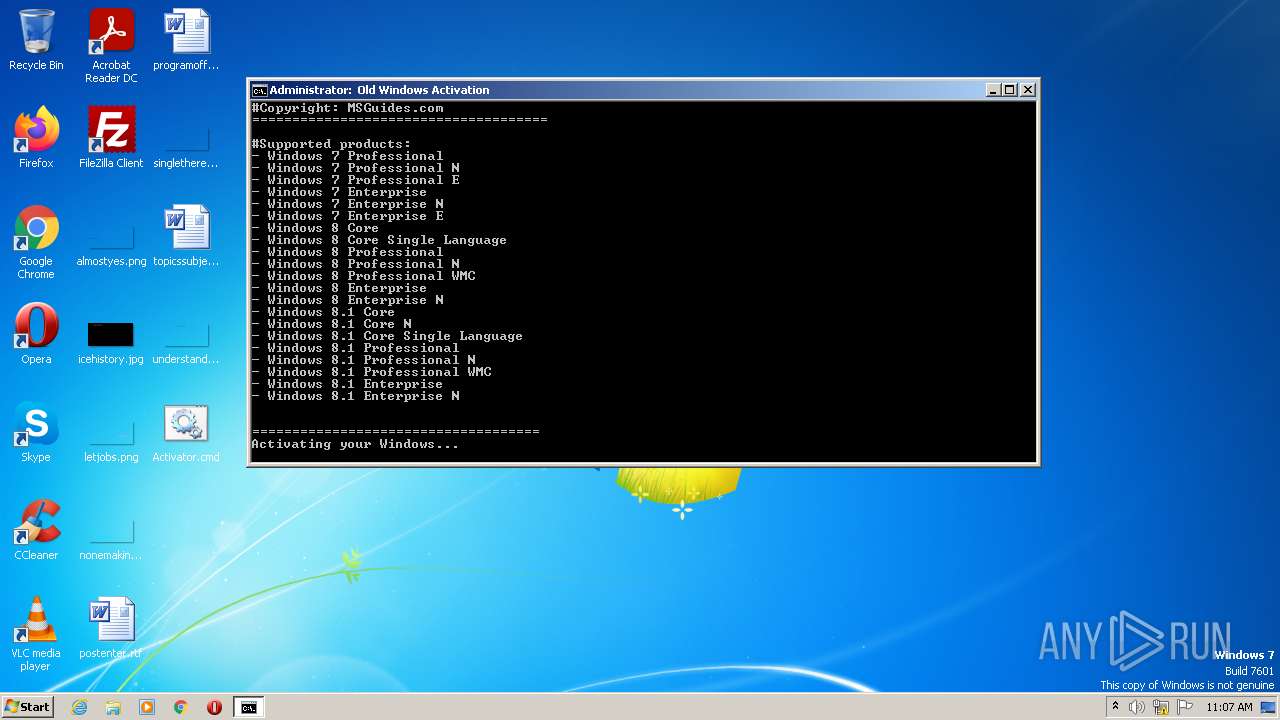
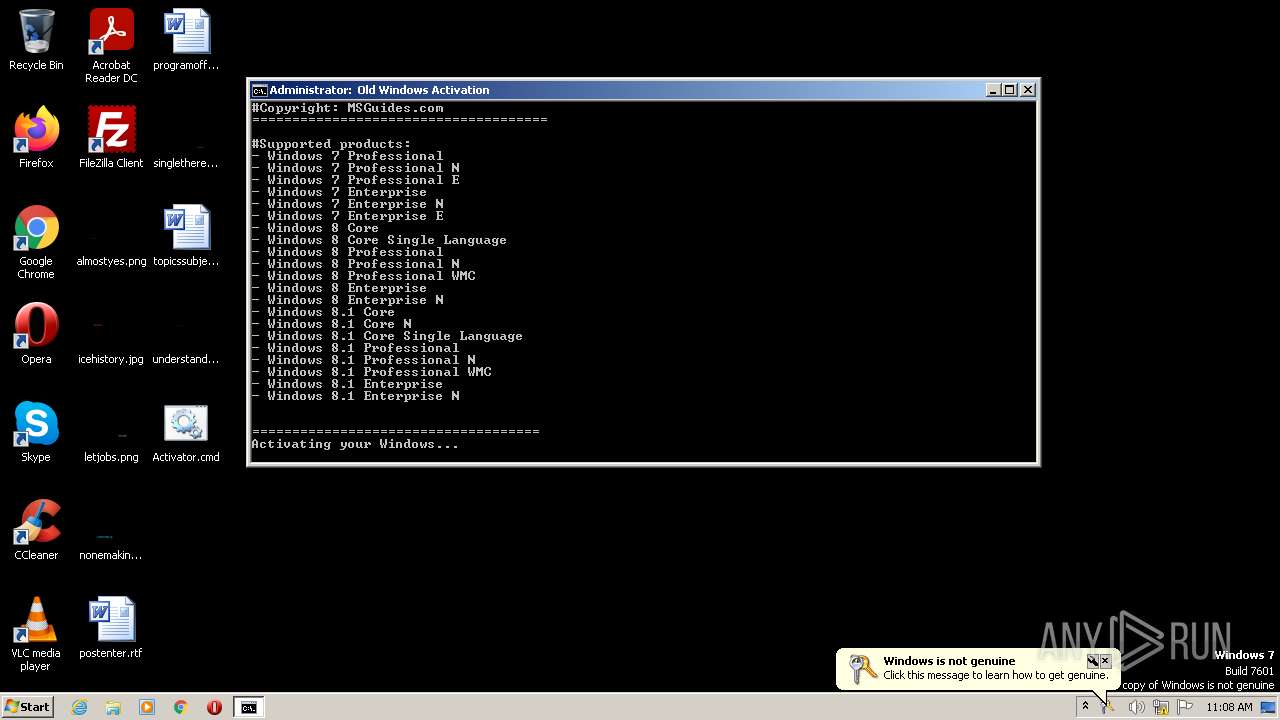
| File name: | Activator.cmd |
| Full analysis: | https://app.any.run/tasks/7fae8776-d4ae-45d0-9147-fd5e2328b36c |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 10:03:57 |
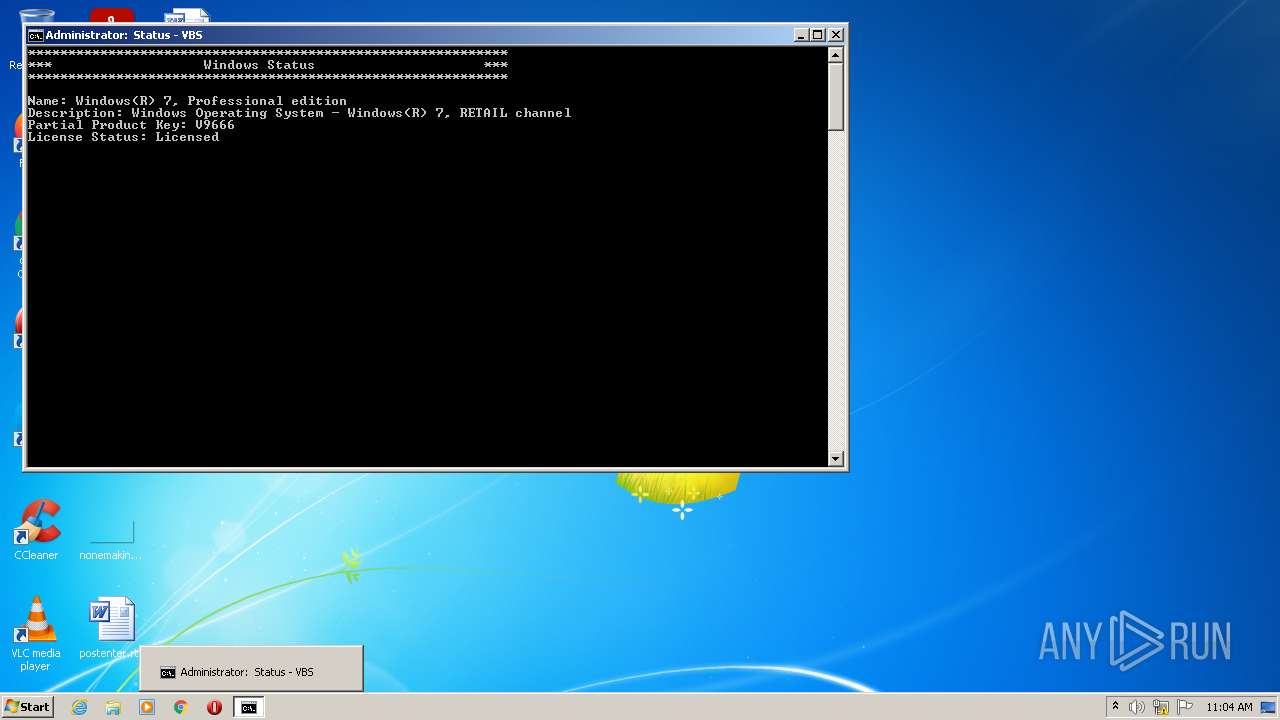
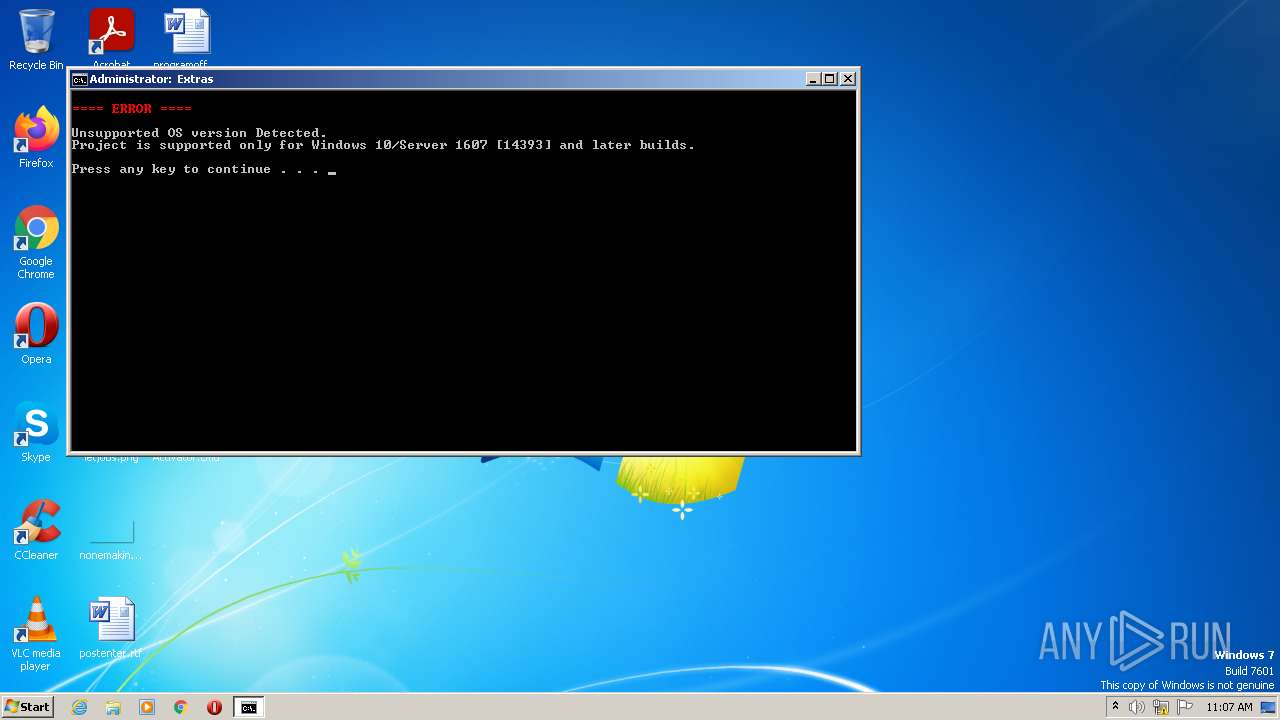
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 40FA4448A78F5AC2CD035CA172FDF30C |
| SHA1: | 0EABEFD14F50F9F0FFD2BF077F5EC3A3637D2C6E |
| SHA256: | 755AD56525460AB71725B77797922BE622A3EA8AAFCBC49C489BDFE11A4852C4 |
| SSDEEP: | 49152:XMLDN/hZw3m99EkHDu5xnAHItDatbEANPpxU/:SEm8kHS56oEy |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2820)
- cmd.exe (PID: 2984)
SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 3396)
- cmd.exe (PID: 3488)
- cmd.exe (PID: 3404)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 2176)
- cmd.exe (PID: 3084)
- cmd.exe (PID: 2972)
- cscript.exe (PID: 1736)
- mode.com (PID: 1128)
- mode.com (PID: 2776)
- cmd.exe (PID: 644)
- powershell.exe (PID: 2908)
- cscript.exe (PID: 3724)
- cmd.exe (PID: 3144)
- cscript.exe (PID: 3820)
- cmd.exe (PID: 1124)
- cmd.exe (PID: 3460)
- cscript.exe (PID: 3440)
- mode.com (PID: 2832)
- cscript.exe (PID: 2252)
- mode.com (PID: 3596)
- cscript.exe (PID: 3592)
- cscript.exe (PID: 1972)
- cmd.exe (PID: 1740)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 3720)
- cscript.exe (PID: 1852)
- cmd.exe (PID: 372)
- cmd.exe (PID: 2680)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 3148)
- cmd.exe (PID: 2948)
- cscript.exe (PID: 2004)
- cmd.exe (PID: 2984)
- cscript.exe (PID: 2124)
- mode.com (PID: 1368)
- mode.com (PID: 2872)
- mode.com (PID: 3160)
- cmd.exe (PID: 1204)
- powershell.exe (PID: 848)
- WMIC.exe (PID: 2968)
- WMIC.exe (PID: 2936)
- cmd.exe (PID: 3104)
- cmd.exe (PID: 4064)
- WMIC.exe (PID: 3684)
- WMIC.exe (PID: 3056)
- WMIC.exe (PID: 3652)
- WMIC.exe (PID: 1692)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 2508)
- cmd.exe (PID: 2624)
- WMIC.exe (PID: 3748)
- cmd.exe (PID: 3056)
- cmd.exe (PID: 2124)
- cmd.exe (PID: 3840)
- mode.com (PID: 3476)
- mode.com (PID: 4088)
- mode.com (PID: 1828)
- WMIC.exe (PID: 2188)
- cmd.exe (PID: 1808)
- WMIC.exe (PID: 1040)
- cmd.exe (PID: 3648)
- cmd.exe (PID: 2928)
- powershell.exe (PID: 3708)
- powershell.exe (PID: 4068)
- powershell.exe (PID: 3896)
- cmd.exe (PID: 2176)
- cmd.exe (PID: 3336)
- mode.com (PID: 1124)
- mode.com (PID: 3780)
- cscript.exe (PID: 348)
- cscript.exe (PID: 3384)
- cscript.exe (PID: 2700)
- mode.com (PID: 3892)
- mode.com (PID: 3364)
- cscript.exe (PID: 4008)
- cscript.exe (PID: 1636)
- cscript.exe (PID: 3048)
- cscript.exe (PID: 2284)
- cscript.exe (PID: 3740)
- cscript.exe (PID: 3888)
- cscript.exe (PID: 2804)
- cscript.exe (PID: 2792)
- cscript.exe (PID: 3376)
- cscript.exe (PID: 780)
- cscript.exe (PID: 2732)
- cscript.exe (PID: 1124)
- cscript.exe (PID: 3648)
- cscript.exe (PID: 892)
- cscript.exe (PID: 2348)
- cscript.exe (PID: 2428)
- cscript.exe (PID: 2604)
- cscript.exe (PID: 3348)
- cscript.exe (PID: 1620)
- cscript.exe (PID: 3360)
- cscript.exe (PID: 3404)
- cscript.exe (PID: 944)
- cscript.exe (PID: 2108)
- cscript.exe (PID: 3696)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2948)
- cmd.exe (PID: 2820)
- cscript.exe (PID: 1736)
- cmd.exe (PID: 372)
- cscript.exe (PID: 2004)
- cmd.exe (PID: 2984)
Reads the computer name
- cscript.exe (PID: 1736)
- powershell.exe (PID: 2908)
- cscript.exe (PID: 3724)
- cscript.exe (PID: 3820)
- cscript.exe (PID: 3440)
- cscript.exe (PID: 2252)
- cscript.exe (PID: 3592)
- cscript.exe (PID: 2124)
- cscript.exe (PID: 1972)
- cscript.exe (PID: 1852)
- cscript.exe (PID: 2004)
- powershell.exe (PID: 848)
- WMIC.exe (PID: 2968)
- WMIC.exe (PID: 3684)
- WMIC.exe (PID: 3056)
- WMIC.exe (PID: 2936)
- WMIC.exe (PID: 3748)
- WMIC.exe (PID: 3652)
- WMIC.exe (PID: 1692)
- WMIC.exe (PID: 1040)
- WMIC.exe (PID: 2188)
- powershell.exe (PID: 3708)
- powershell.exe (PID: 4068)
- powershell.exe (PID: 3896)
- cscript.exe (PID: 348)
- cscript.exe (PID: 2700)
- cscript.exe (PID: 3384)
- cscript.exe (PID: 4008)
- cscript.exe (PID: 3740)
- cscript.exe (PID: 3048)
- cscript.exe (PID: 2284)
- cscript.exe (PID: 1636)
- cscript.exe (PID: 2732)
- cscript.exe (PID: 2804)
- cscript.exe (PID: 2792)
- cscript.exe (PID: 3376)
- cscript.exe (PID: 780)
- cscript.exe (PID: 3888)
- cscript.exe (PID: 1124)
- cscript.exe (PID: 892)
- cscript.exe (PID: 2428)
- cscript.exe (PID: 3648)
- cscript.exe (PID: 3348)
- cscript.exe (PID: 1620)
- cscript.exe (PID: 3360)
- cscript.exe (PID: 3404)
- cscript.exe (PID: 2348)
- cscript.exe (PID: 2604)
- cscript.exe (PID: 944)
- cscript.exe (PID: 3696)
- cscript.exe (PID: 2108)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2948)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 3144)
- cmd.exe (PID: 1124)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 372)
- cmd.exe (PID: 2984)
Application launched itself
- cmd.exe (PID: 2948)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 372)
- cmd.exe (PID: 2984)
Executes scripts
- cmd.exe (PID: 2948)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 372)
- cmd.exe (PID: 2984)
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 2984)
Creates files in the Windows directory
- cmd.exe (PID: 2820)
- cmd.exe (PID: 2984)
Removes files from Windows directory
- cmd.exe (PID: 2820)
- cmd.exe (PID: 2984)
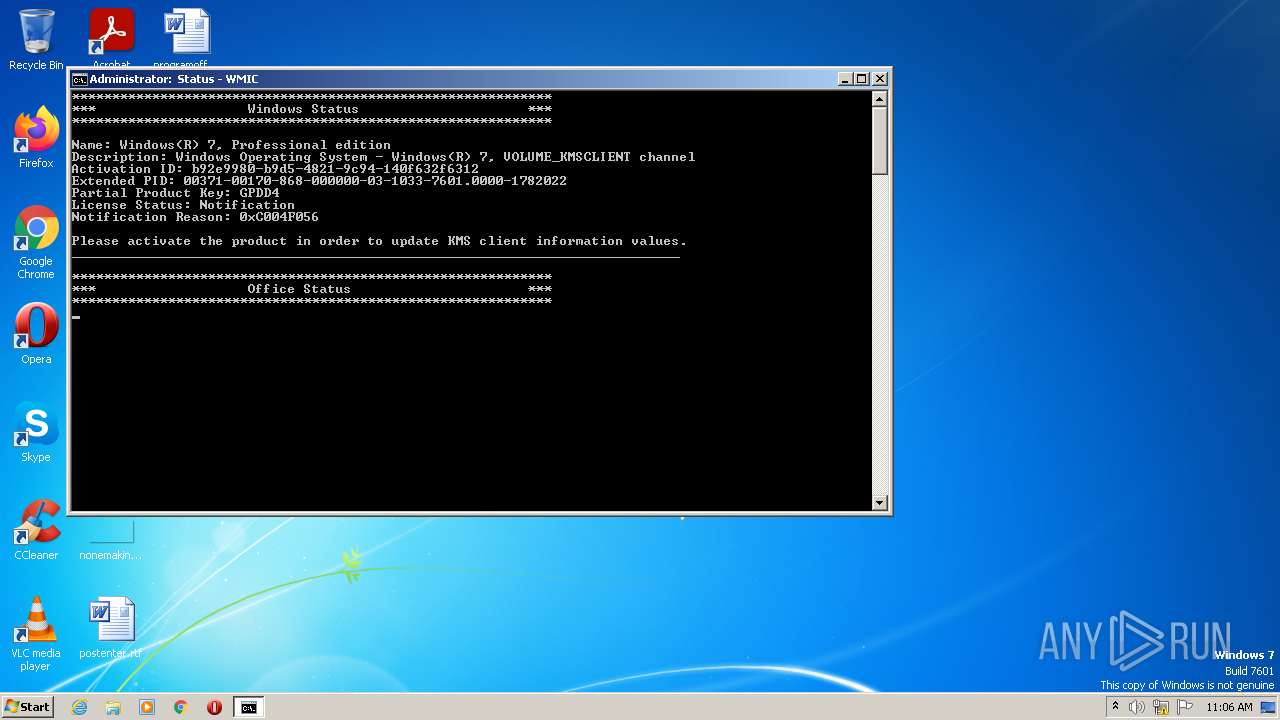
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 3104)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 2624)
- cmd.exe (PID: 3056)
- cmd.exe (PID: 2124)
- cmd.exe (PID: 1808)
Executed via COM
- slui.exe (PID: 3248)
INFO
Checks supported languages
- findstr.exe (PID: 3676)
- reg.exe (PID: 3740)
- reg.exe (PID: 2108)
- findstr.exe (PID: 1736)
- choice.exe (PID: 3504)
- findstr.exe (PID: 3116)
- reg.exe (PID: 3188)
- reg.exe (PID: 600)
- reg.exe (PID: 3612)
- reg.exe (PID: 2124)
- reg.exe (PID: 1580)
- reg.exe (PID: 572)
- choice.exe (PID: 3060)
- findstr.exe (PID: 1584)
- choice.exe (PID: 2972)
- findstr.exe (PID: 3628)
- reg.exe (PID: 580)
- findstr.exe (PID: 3500)
- reg.exe (PID: 3548)
- choice.exe (PID: 948)
- choice.exe (PID: 2104)
- findstr.exe (PID: 3520)
- findstr.exe (PID: 3076)
- findstr.exe (PID: 2920)
- findstr.exe (PID: 3240)
- findstr.exe (PID: 1120)
- findstr.exe (PID: 3432)
- findstr.exe (PID: 2828)
- findstr.exe (PID: 2380)
- findstr.exe (PID: 3252)
- choice.exe (PID: 284)
- findstr.exe (PID: 3576)
- choice.exe (PID: 528)
- findstr.exe (PID: 3144)
- reg.exe (PID: 3424)
- choice.exe (PID: 3572)
- findstr.exe (PID: 2428)
- choice.exe (PID: 2932)
- findstr.exe (PID: 2284)
- choice.exe (PID: 2772)
- choice.exe (PID: 2988)
- slui.exe (PID: 3248)
- find.exe (PID: 2708)
Checks Windows Trust Settings
- cscript.exe (PID: 1736)
- powershell.exe (PID: 2908)
- cscript.exe (PID: 3724)
- cscript.exe (PID: 3820)
- cscript.exe (PID: 3592)
- cscript.exe (PID: 2252)
- cscript.exe (PID: 2124)
- cscript.exe (PID: 3440)
- cscript.exe (PID: 1852)
- cscript.exe (PID: 1972)
- cscript.exe (PID: 2004)
- powershell.exe (PID: 848)
- powershell.exe (PID: 3708)
- powershell.exe (PID: 3896)
- powershell.exe (PID: 4068)
- cscript.exe (PID: 348)
- cscript.exe (PID: 3384)
- cscript.exe (PID: 4008)
- cscript.exe (PID: 1636)
- cscript.exe (PID: 3740)
- cscript.exe (PID: 3048)
- cscript.exe (PID: 2700)
- cscript.exe (PID: 2284)
- cscript.exe (PID: 780)
- cscript.exe (PID: 3888)
- cscript.exe (PID: 2804)
- cscript.exe (PID: 2732)
- cscript.exe (PID: 3376)
- cscript.exe (PID: 1124)
- cscript.exe (PID: 3648)
- cscript.exe (PID: 892)
- cscript.exe (PID: 2792)
- cscript.exe (PID: 2428)
- cscript.exe (PID: 1620)
- cscript.exe (PID: 3348)
- cscript.exe (PID: 3404)
- cscript.exe (PID: 3360)
- cscript.exe (PID: 2348)
- cscript.exe (PID: 2604)
- cscript.exe (PID: 3696)
- cscript.exe (PID: 2108)
- cscript.exe (PID: 944)
Reads Microsoft Office registry keys
- reg.exe (PID: 3612)
Manual execution by user
- cmd.exe (PID: 372)
Reads the computer name
- slui.exe (PID: 3248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
192
Monitored processes
142
Malicious processes
6
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
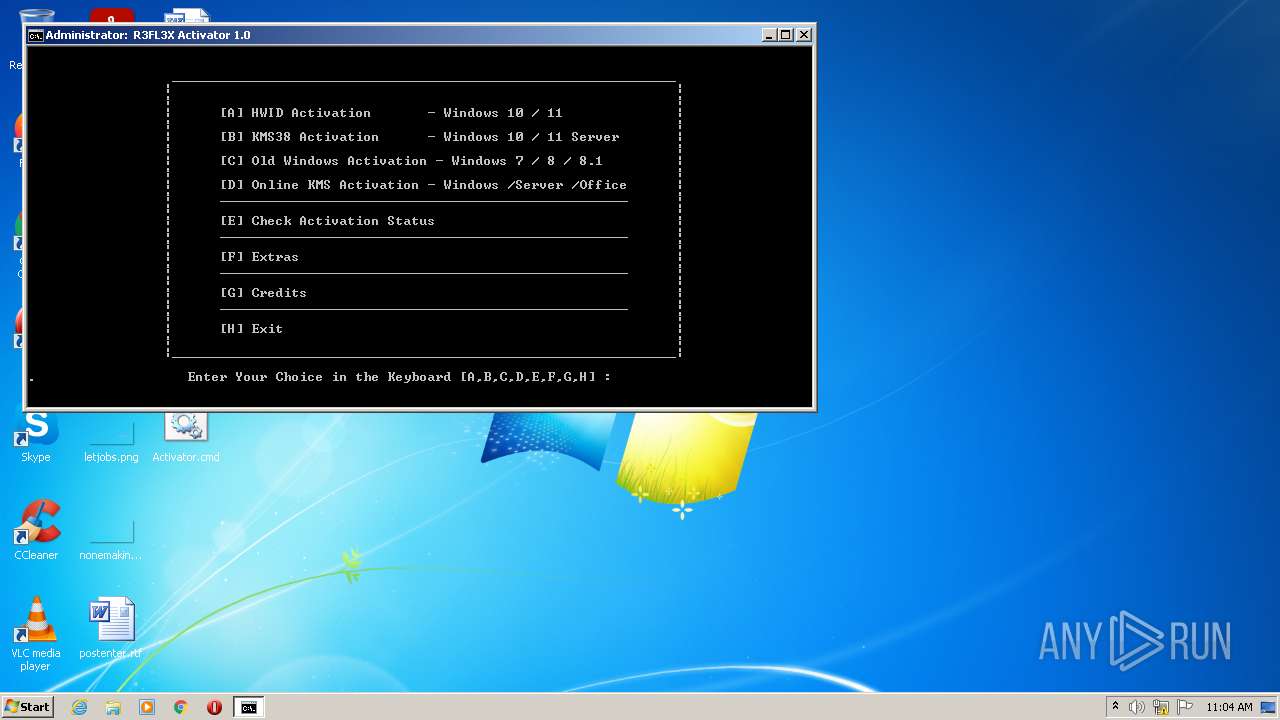
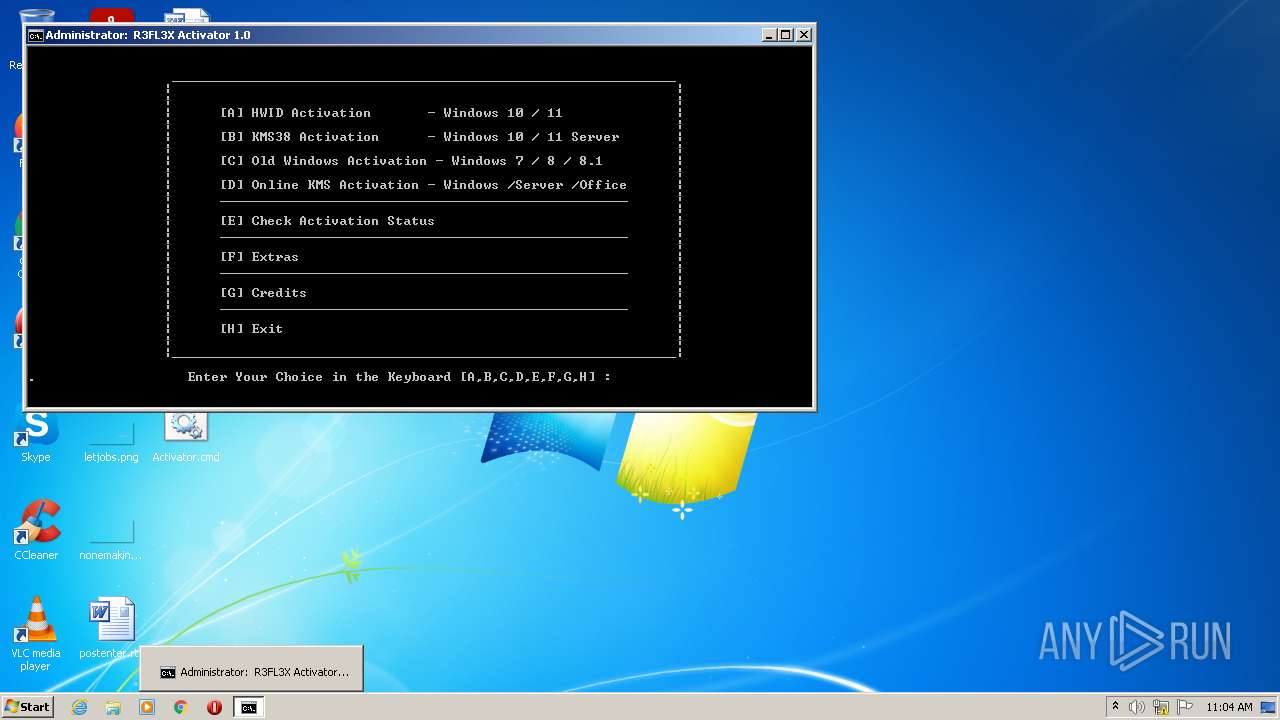
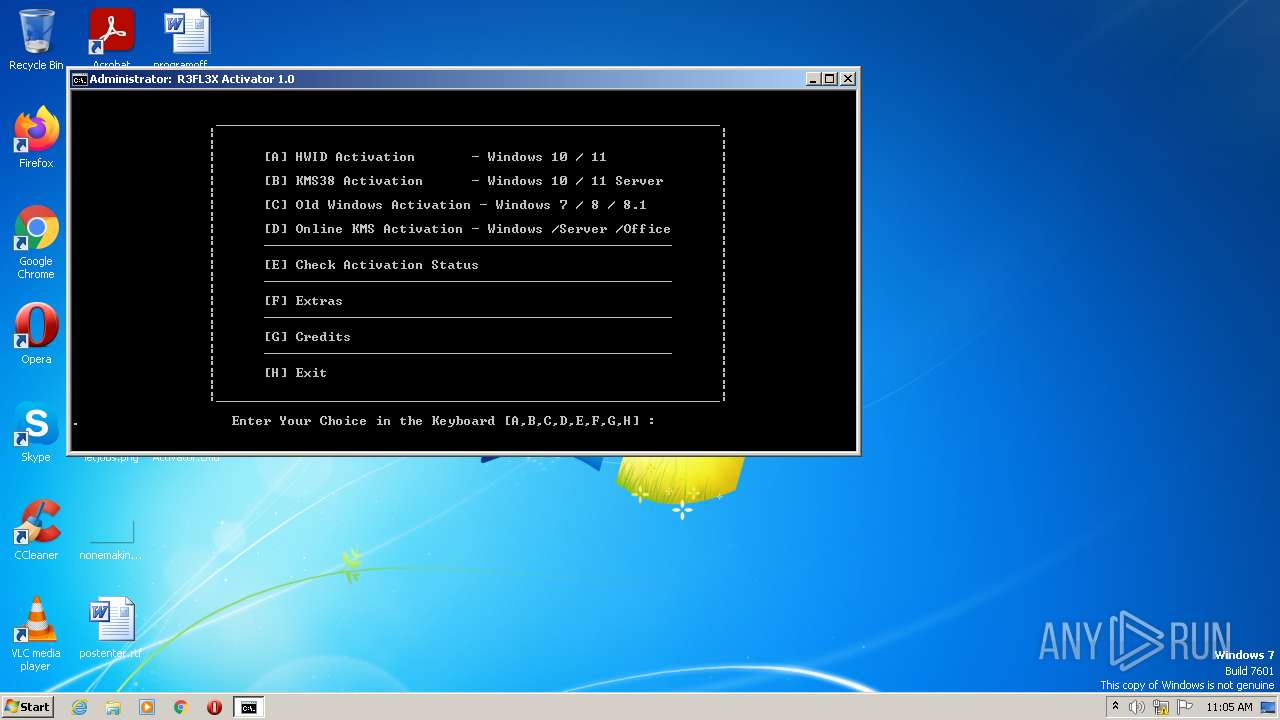
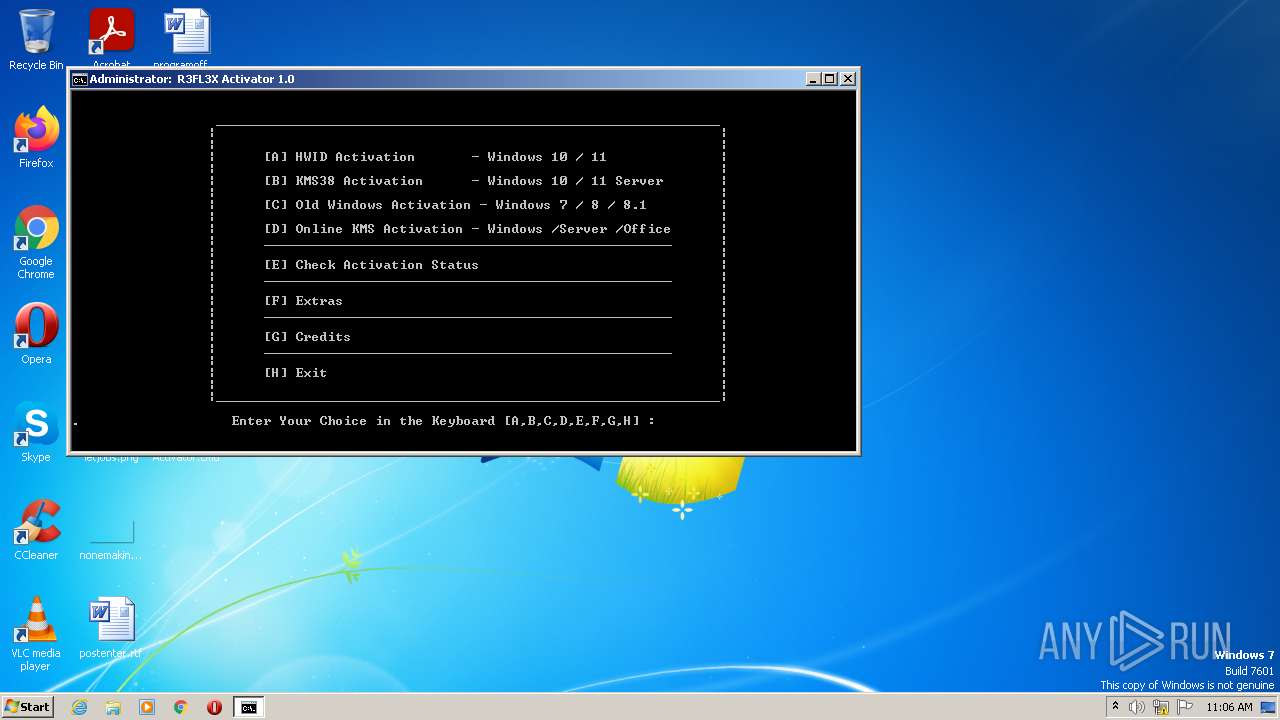
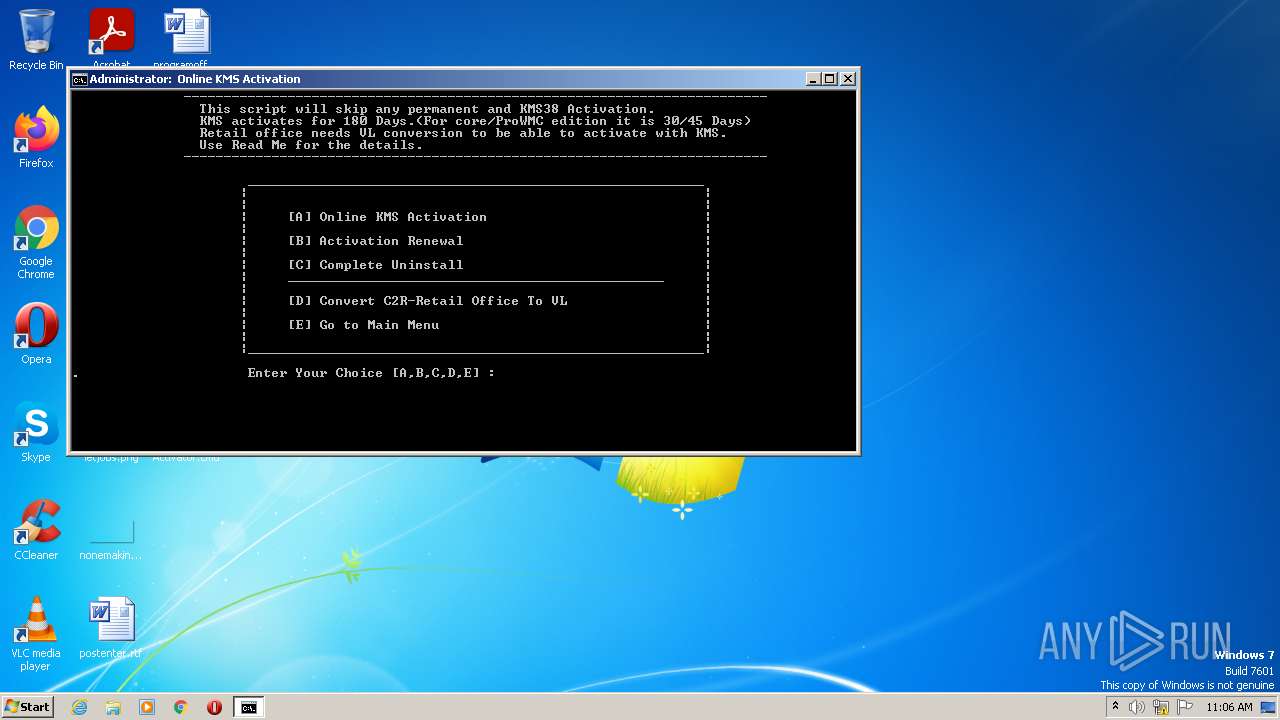
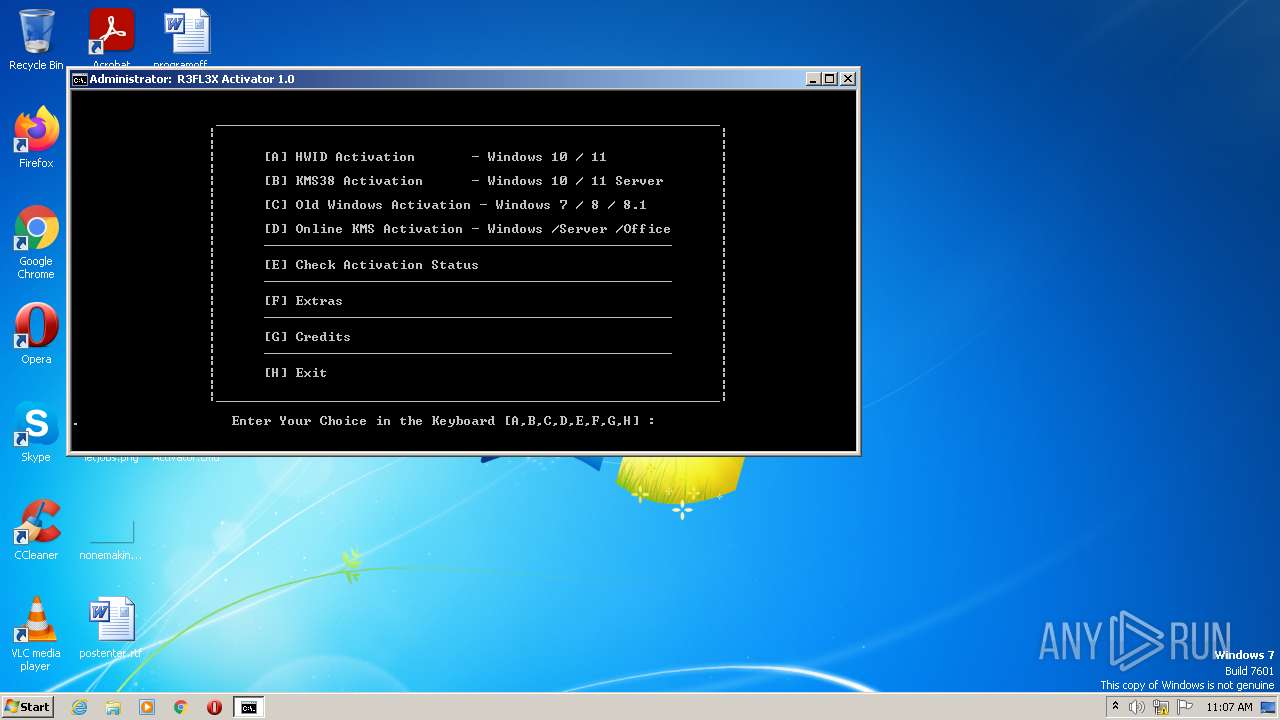
| 284 | choice /C:ABCDEFGH /N /M ". Enter Your Choice in the Keyboard [A,B,C,D,E,F,G,H] : " | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
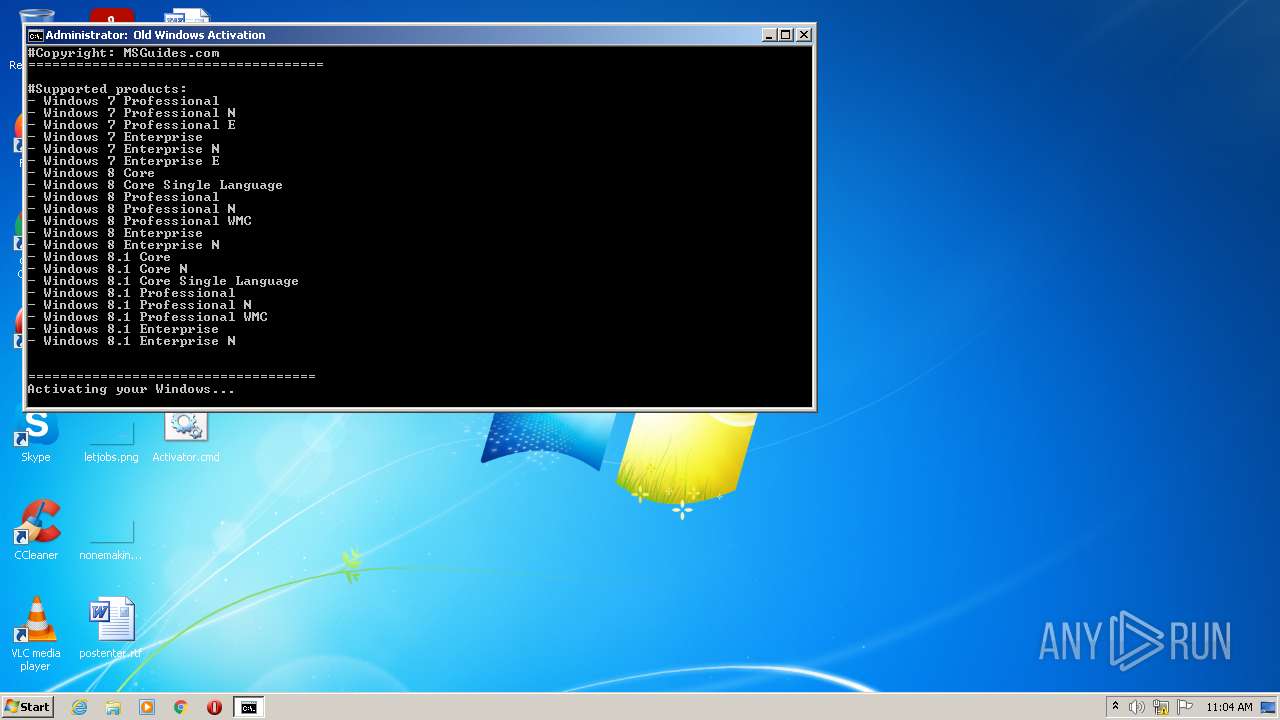
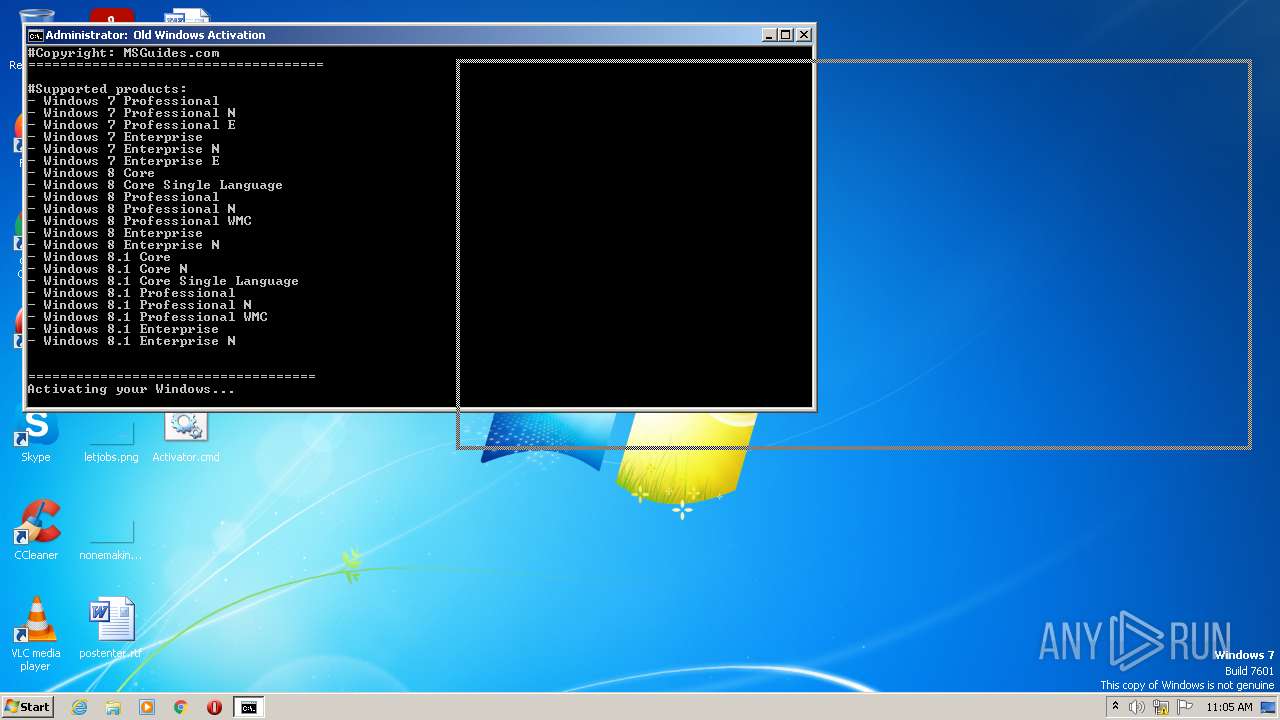
| 348 | cscript //nologo c:\windows\system32\slmgr.vbs /ipk FJ82H-XT6CR-J8D7P-XQJJ2-GPDD4 | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 372 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Activator.cmd" " | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 528 | choice /C:ABCDEFGH /N /M ". Enter Your Choice in the Keyboard [A,B,C,D,E,F,G,H] : " | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | reg query HKLM\SOFTWARE\Microsoft\Office\14.0\ClickToRun /v InstallPath | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 580 | reg query HKU\S-1-5-19 | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 600 | reg query HKLM\SOFTWARE\Microsoft\Office\15.0\Common\InstallRoot /v Path | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 644 | C:\Windows\system32\cmd.exe /c findstr/nbrc:":STATEVBStxt:\[" /c:":STATEVBStxt:\]" "C:\Users\admin\Desktop\Activator.cmd" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 780 | cscript //nologo c:\windows\system32\slmgr.vbs /ipk XCVCF-2NXM9-723PB-MHCB7-2RYQQ | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 3221549136 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 848 | powershell -NoProfile -command "&{$H=get-host;$W=$H.ui.rawui;$B=$W.buffersize;$B.width=100;$B.height=200;$W.buffersize=$B;}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
7 760
Read events
7 742
Write events
18
Delete events
0
Modification events
| (PID) Process: | (1736) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1736) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1736) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1736) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2004) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2004) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2004) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2004) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3248) slui.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\Activation |
| Operation: | write | Name: | LastAction |
Value: B212CA1803000000 | |||
| (PID) Process: | (3248) slui.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\Activation |
| Operation: | write | Name: | ActionId |
Value: 58 | |||
Executable files
0
Suspicious files
10
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
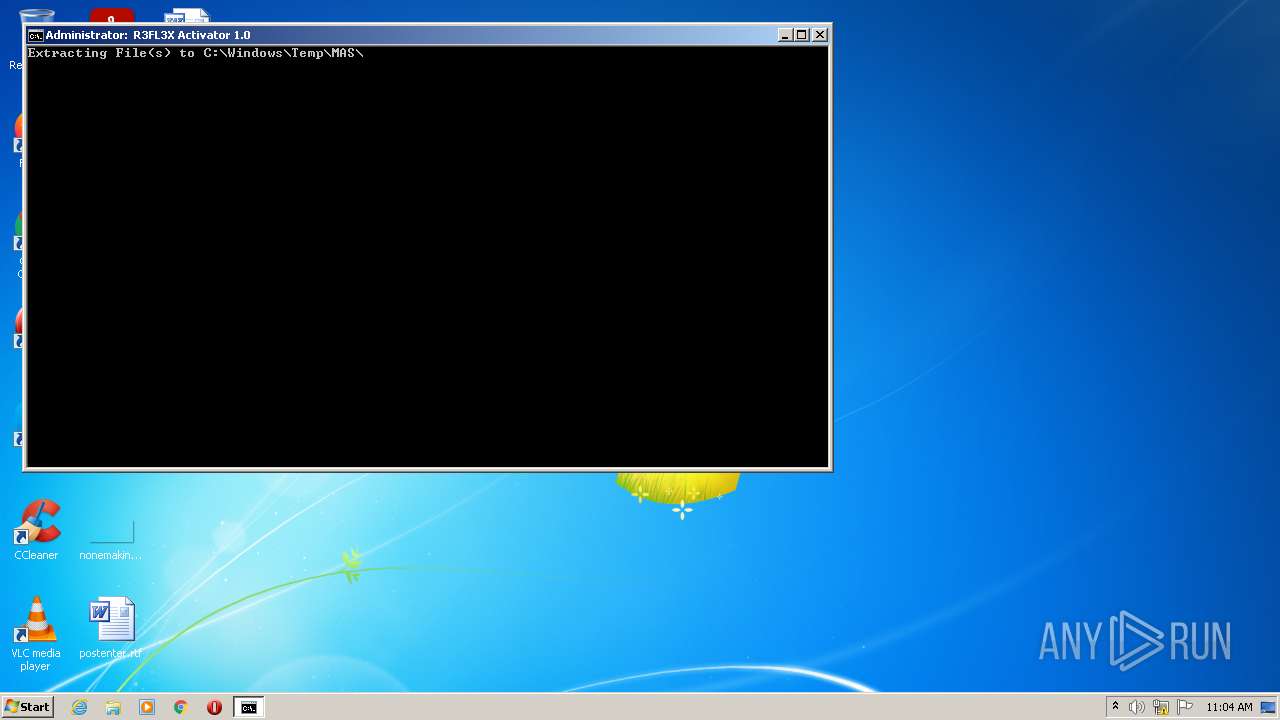
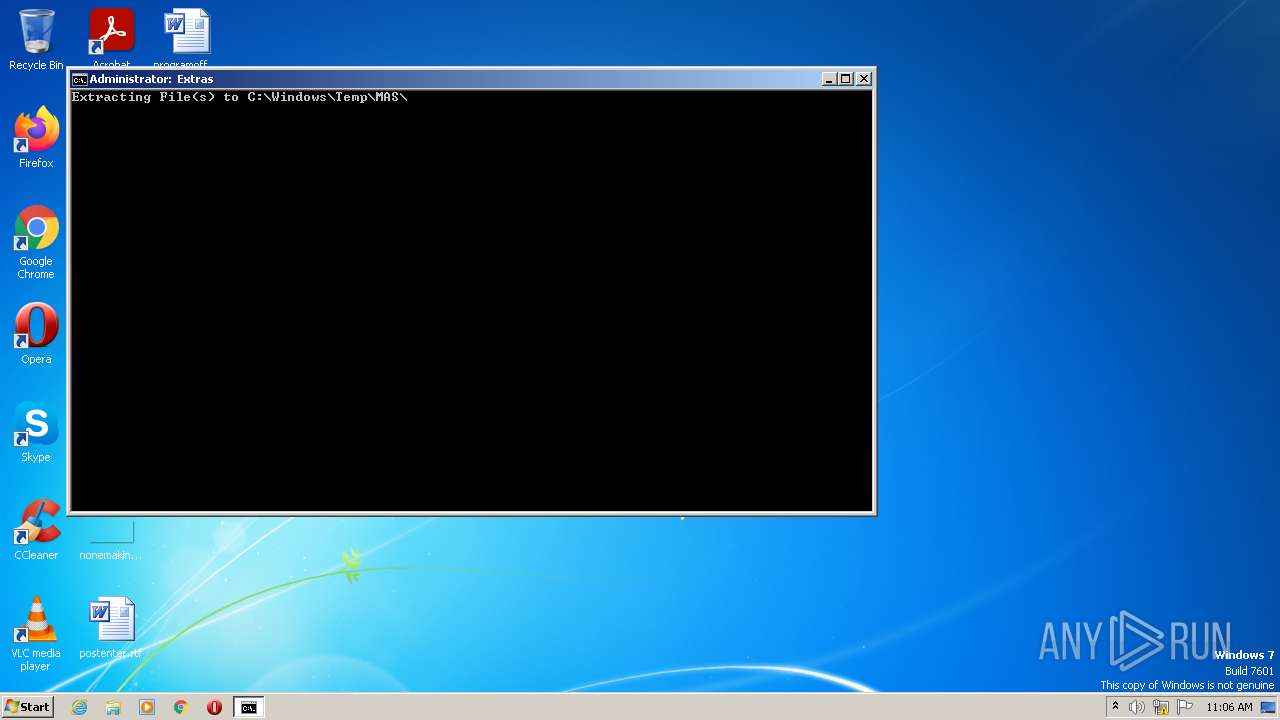
| 2984 | cmd.exe | C:\Windows\Temp\MAS\Check-Activation-Status-Alternative.cmd | text | |
MD5:— | SHA256:— | |||
| 2908 | powershell.exe | C:\Users\admin\AppData\Local\Temp\5zfzksm1.ucr.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2908 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2984 | cmd.exe | C:\Windows\Temp\MAS\Online_KMS_Activation.cmd | text | |
MD5:— | SHA256:— | |||
| 2948 | cmd.exe | C:\Users\admin\AppData\Local\Temp\elev.vbs | text | |
MD5:EFD88876976646C181001D1AFACFFF6E | SHA256:28DCB1CA4FA7B99BD64DC57F8E754A7DB595B4FE76258327241B53A052F3E73D | |||
| 372 | cmd.exe | C:\Users\admin\AppData\Local\Temp\elev.vbs | text | |
MD5:EFD88876976646C181001D1AFACFFF6E | SHA256:28DCB1CA4FA7B99BD64DC57F8E754A7DB595B4FE76258327241B53A052F3E73D | |||
| 2908 | powershell.exe | C:\Users\admin\AppData\Local\Temp\d4wtoftt.tho.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2820 | cmd.exe | C:\Windows\Temp\slmgr.vbs | text | |
MD5:38482A5013D8AB40DF0FB15EAE022C57 | SHA256:AC5C46B97345465A96E9AE1EDAFF44B191A39BF3D03DC1128090B8FFA92A16F8 | |||
| 848 | powershell.exe | C:\Users\admin\AppData\Local\Temp\whtu3hu3.lkl.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2820 | cmd.exe | C:\Users\admin\AppData\Local\Temp\==== ERROR ==== | text | |
MD5:DF66FA563A2FAFDB93CC559DEB0A38C4 | SHA256:3E39ED22DC63246937C4DBBF34CE4FB1CFE6B00DE7596B020CAD49AE50031351 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3232 | sppsvc.exe | 104.168.47.39:1688 | kms7.MSGuides.com | ColoCrossing | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kms7.MSGuides.com |
| unknown |