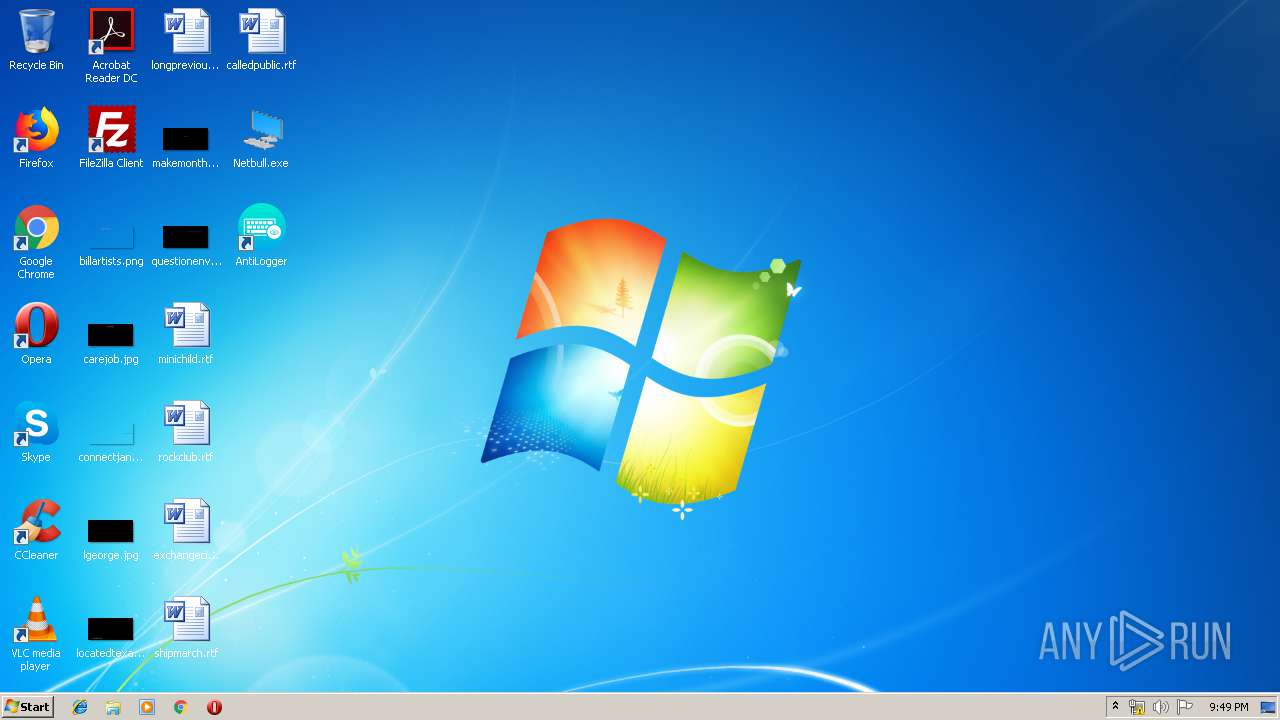
| File name: | Netbull.exe |
| Full analysis: | https://app.any.run/tasks/d189ee6e-c7e3-42fb-afab-e05034673a6c |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 21:47:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 28602BA664770C545FE59C28FA64D207 |
| SHA1: | 824168027BC2D4C46892C042FF3B4F8E62DFA080 |
| SHA256: | 7559D9262637D1E610F24BD694D8333A95A15DF687599A128055AA03025DF4DC |
| SSDEEP: | 6144:Wa6rm3jPz4m78UknzfVLr97rBp+4xdtBIF0tlOQOQbqJ+NJk1bznjAb1ytk2C:WmTEmgUQl97rBp+QtWWaQOQbqJm60YA |
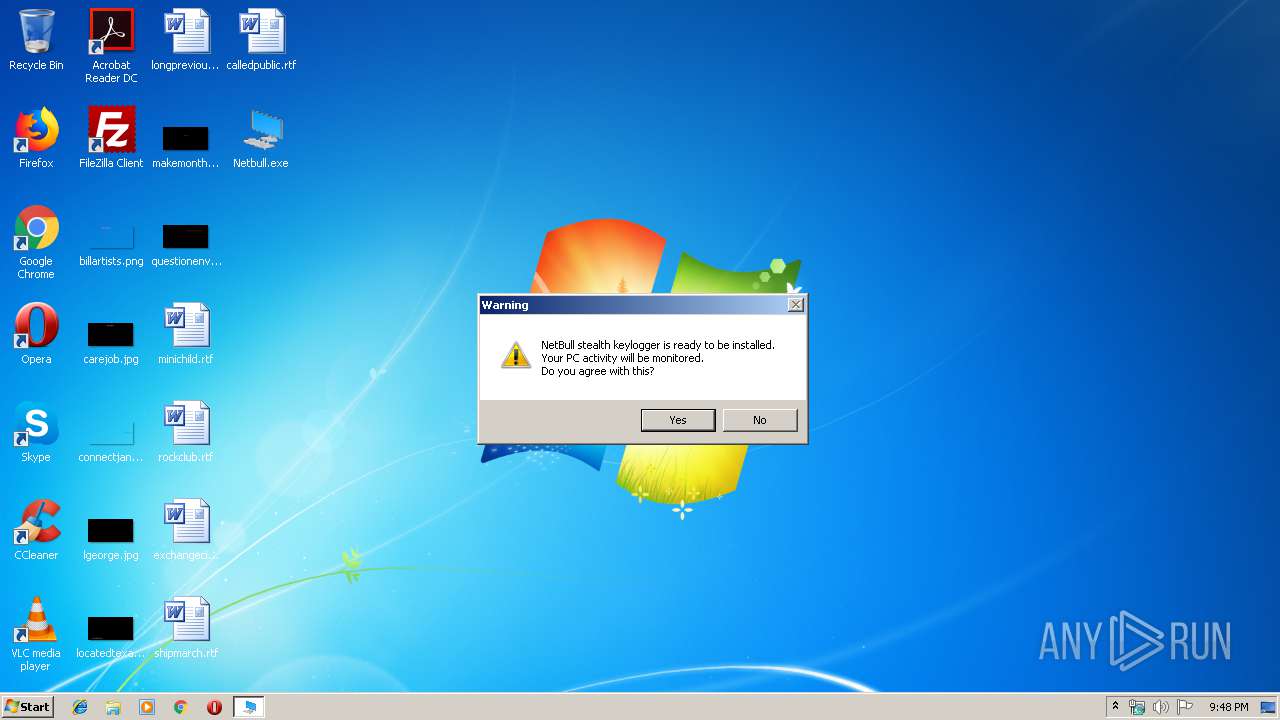
MALICIOUS
Changes the autorun value in the registry
- svchost.exe (PID: 4028)
Uses SVCHOST.EXE for hidden code execution
- Netbull.exe (PID: 2152)
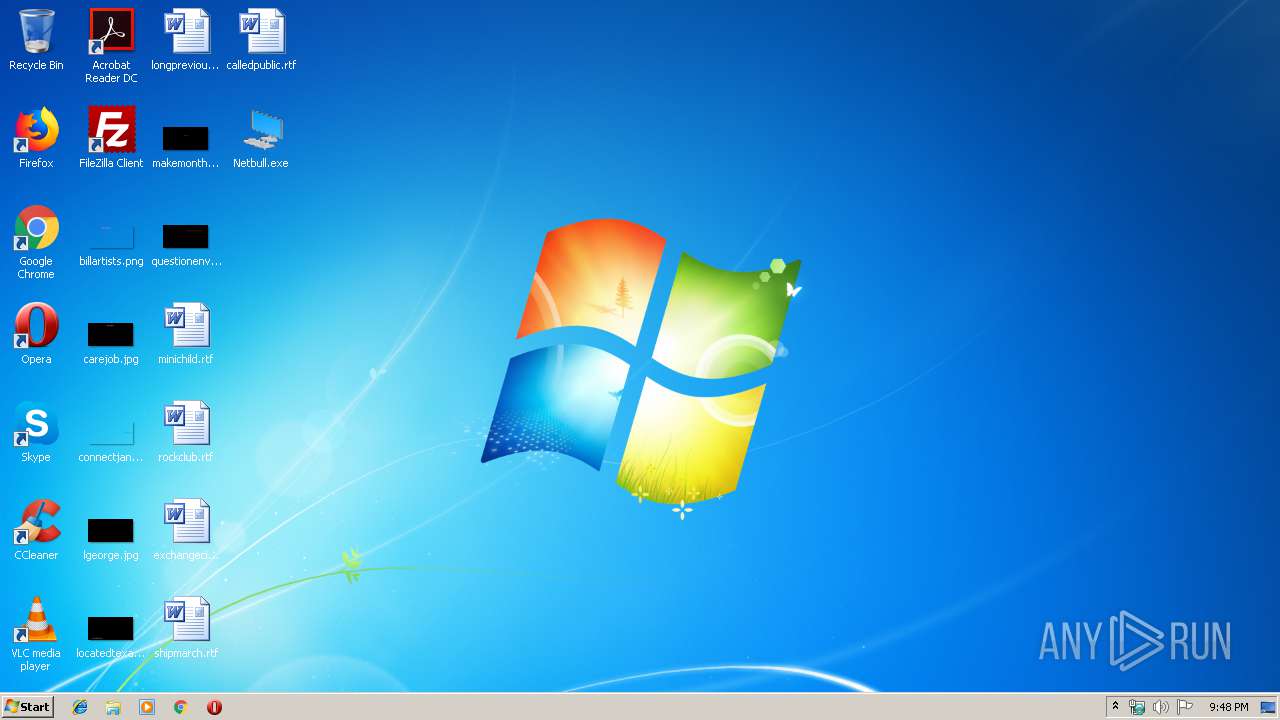
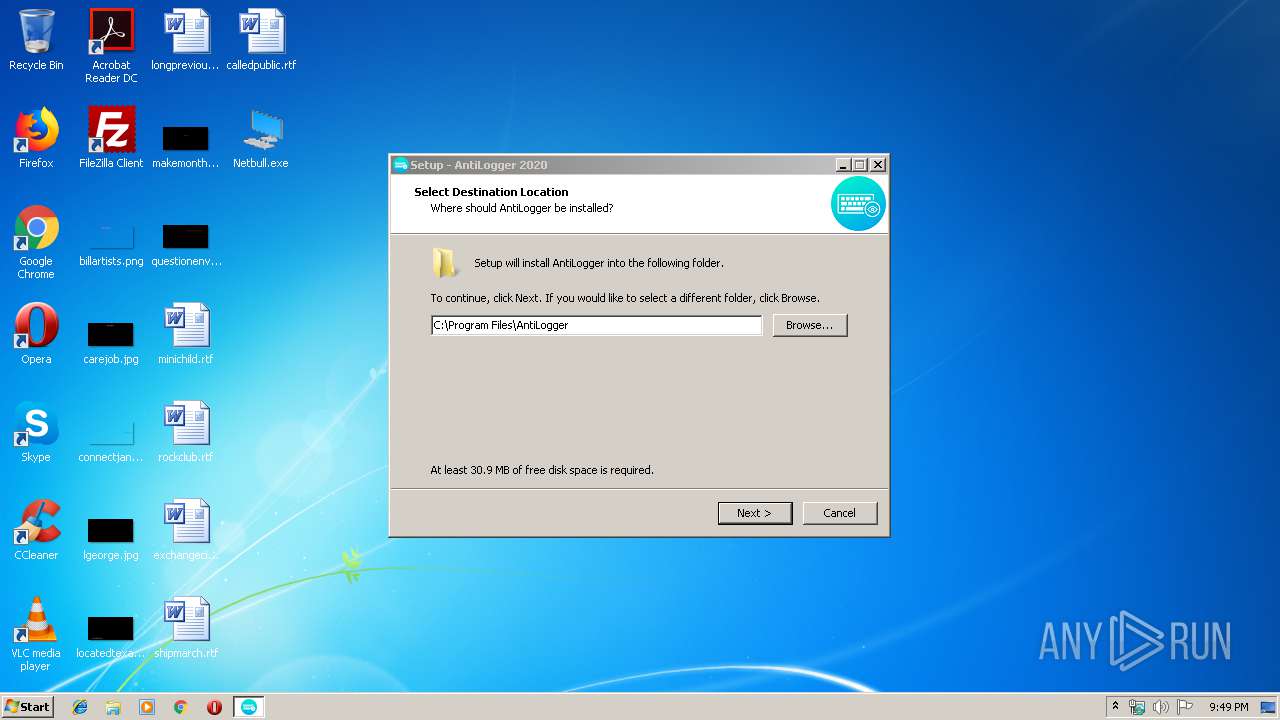
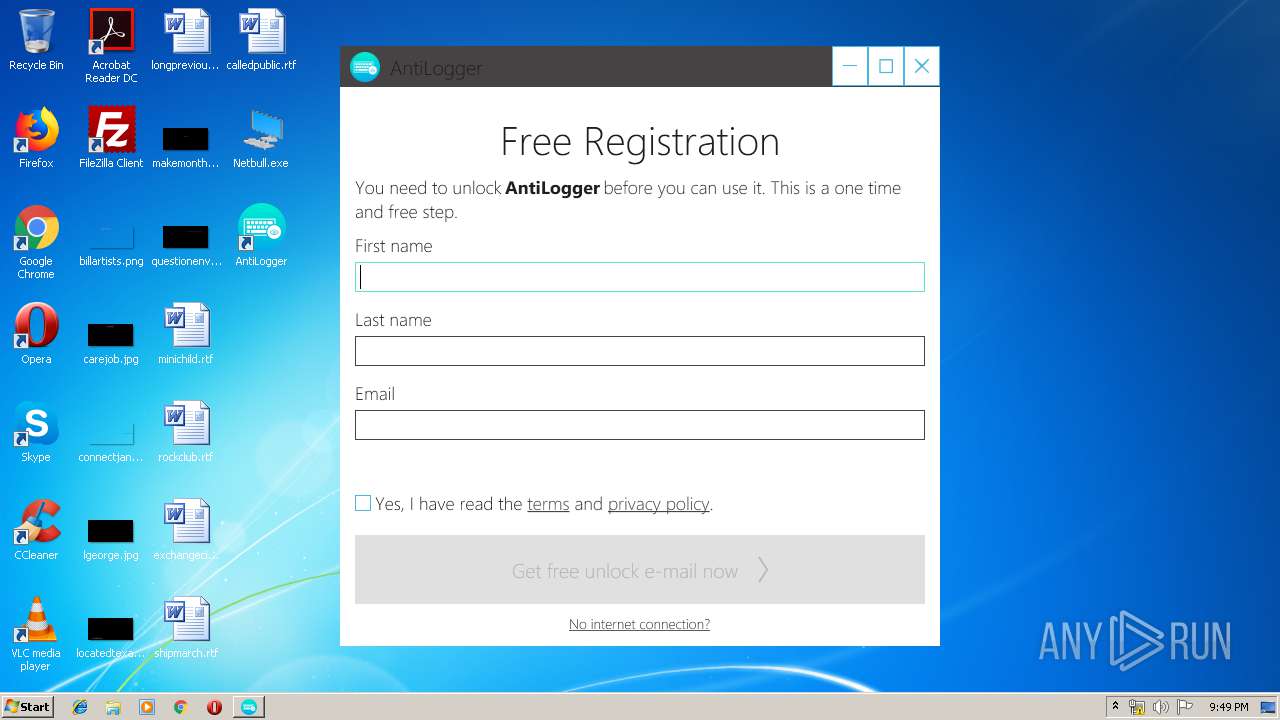
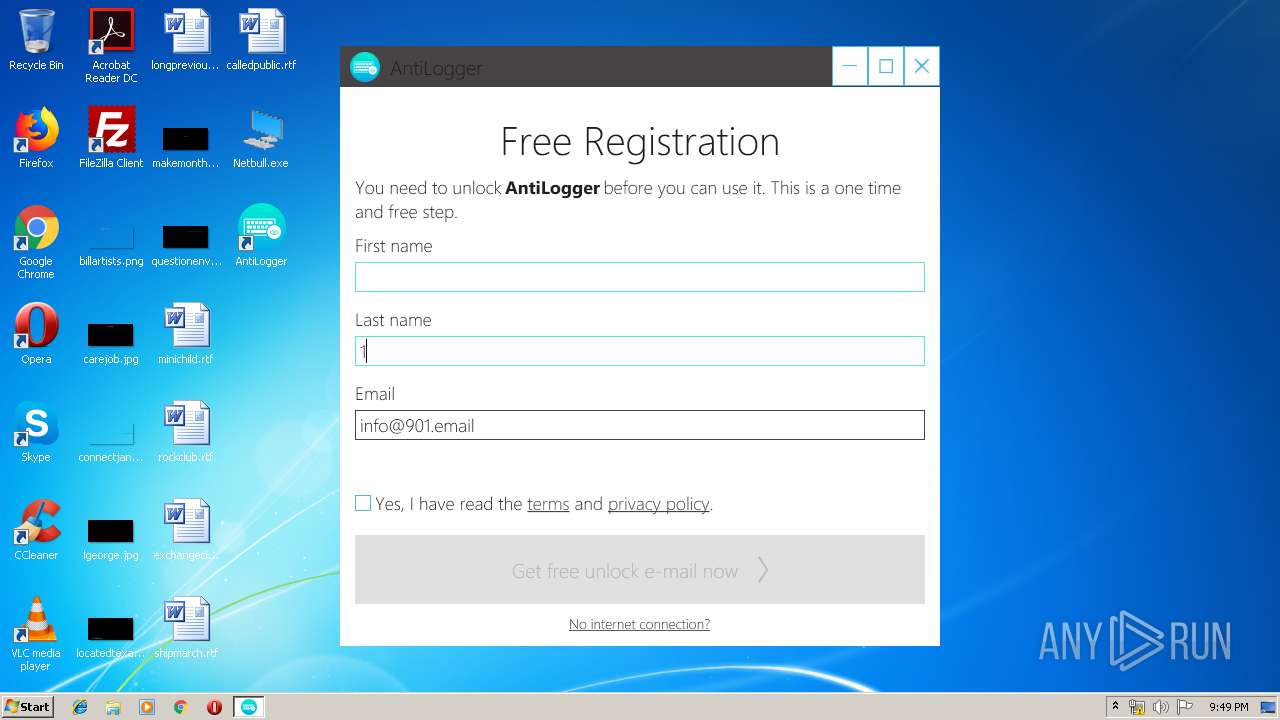
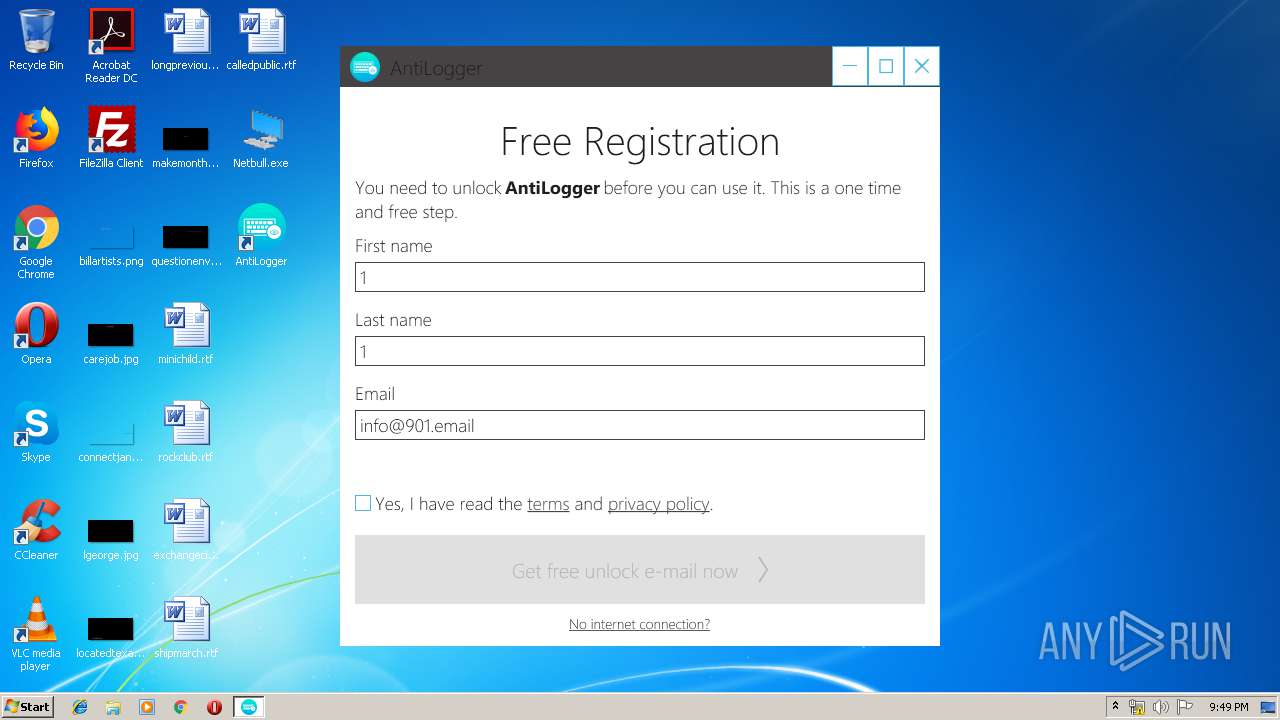
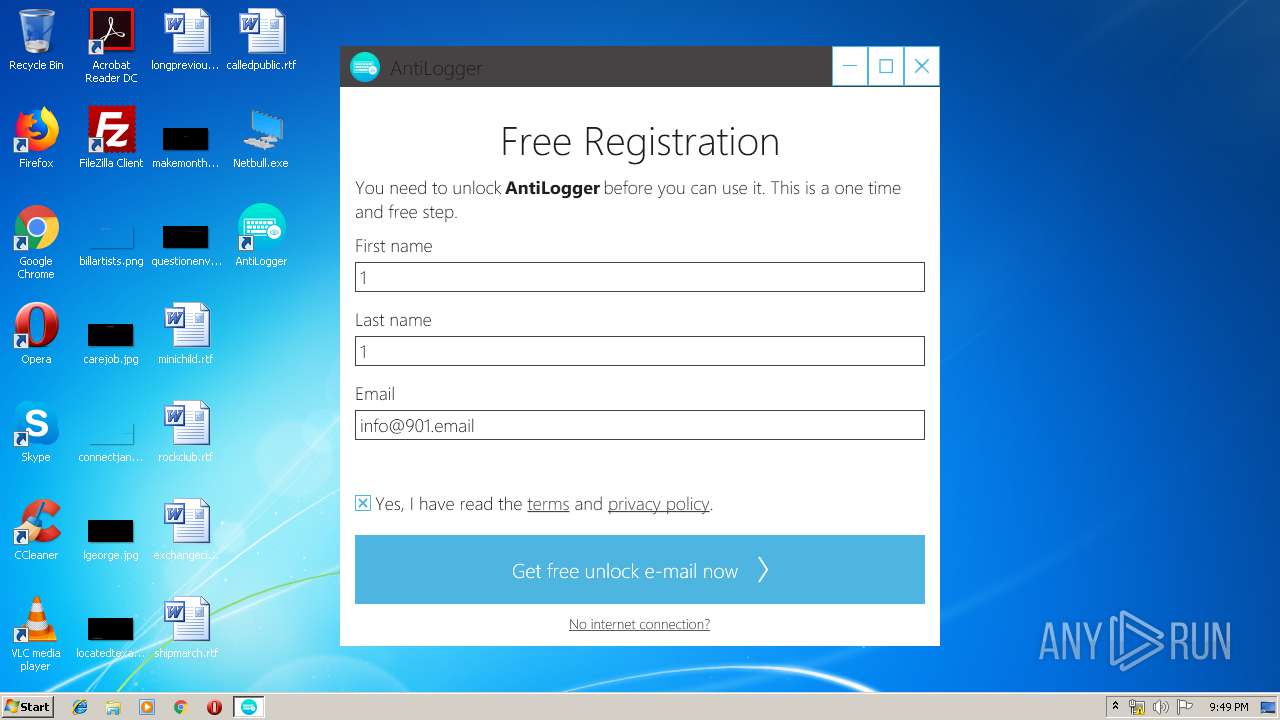
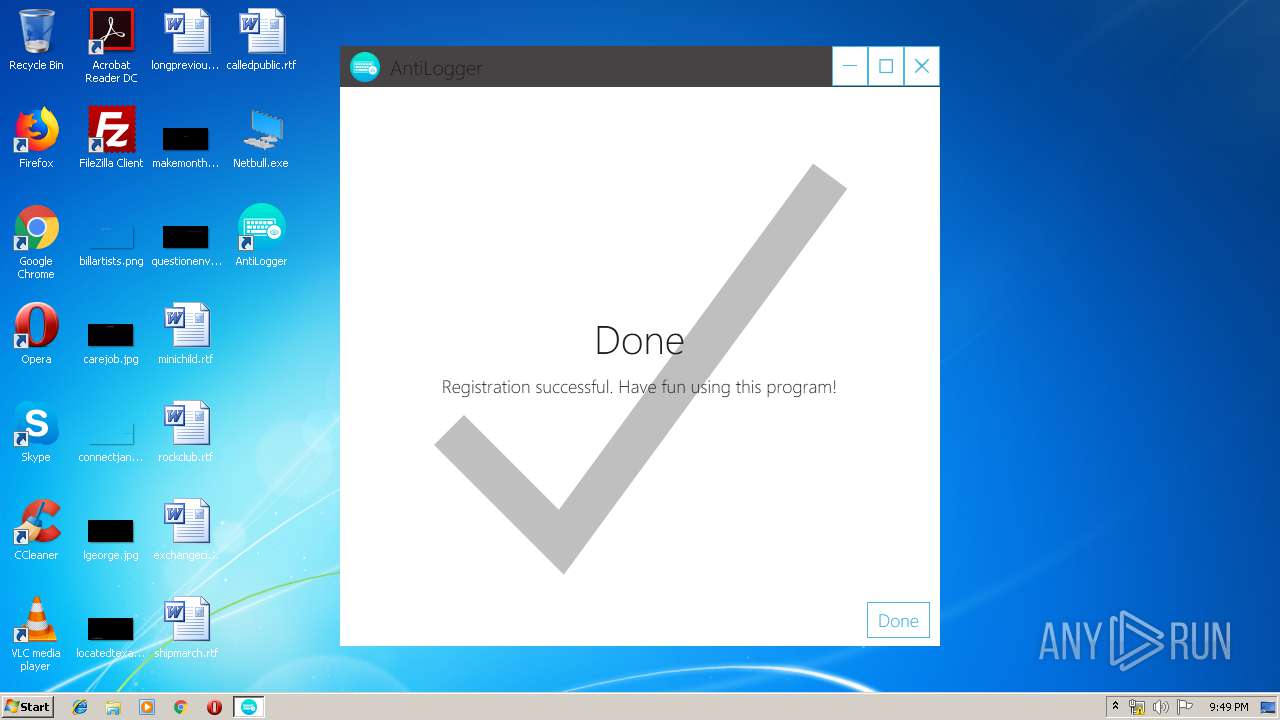
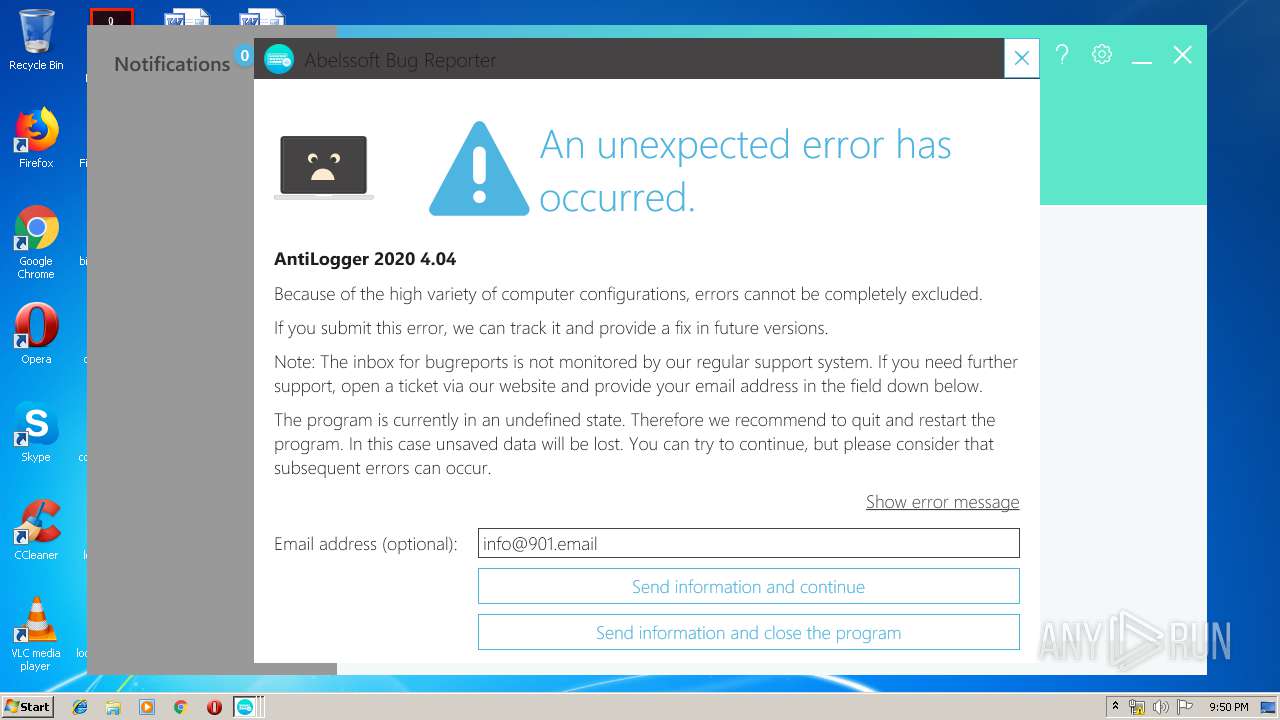
Application was dropped or rewritten from another process
- antilogger[1].exe (PID: 820)
- AntiLogger.exe (PID: 2836)
- antilogger[1].exe (PID: 1796)
- AntiLogger.exe (PID: 2212)
- AbLauncher.exe (PID: 1536)
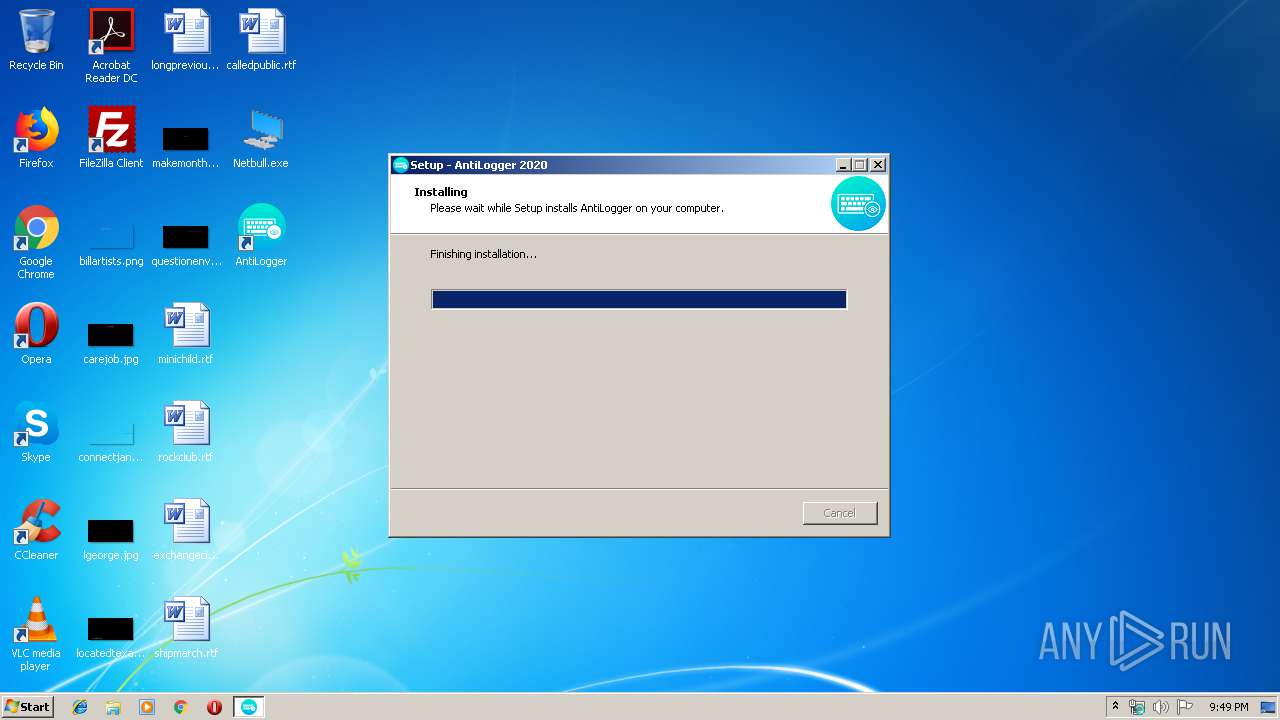
Loads dropped or rewritten executable
- AntiLogger.exe (PID: 2836)
- AbLauncher.exe (PID: 1536)
- AntiLogger.exe (PID: 2212)
Changes settings of System certificates
- AntiLogger.exe (PID: 2836)
Loads the Task Scheduler COM API
- AntiLogger.exe (PID: 2836)
- AntiLogger.exe (PID: 2212)
SUSPICIOUS
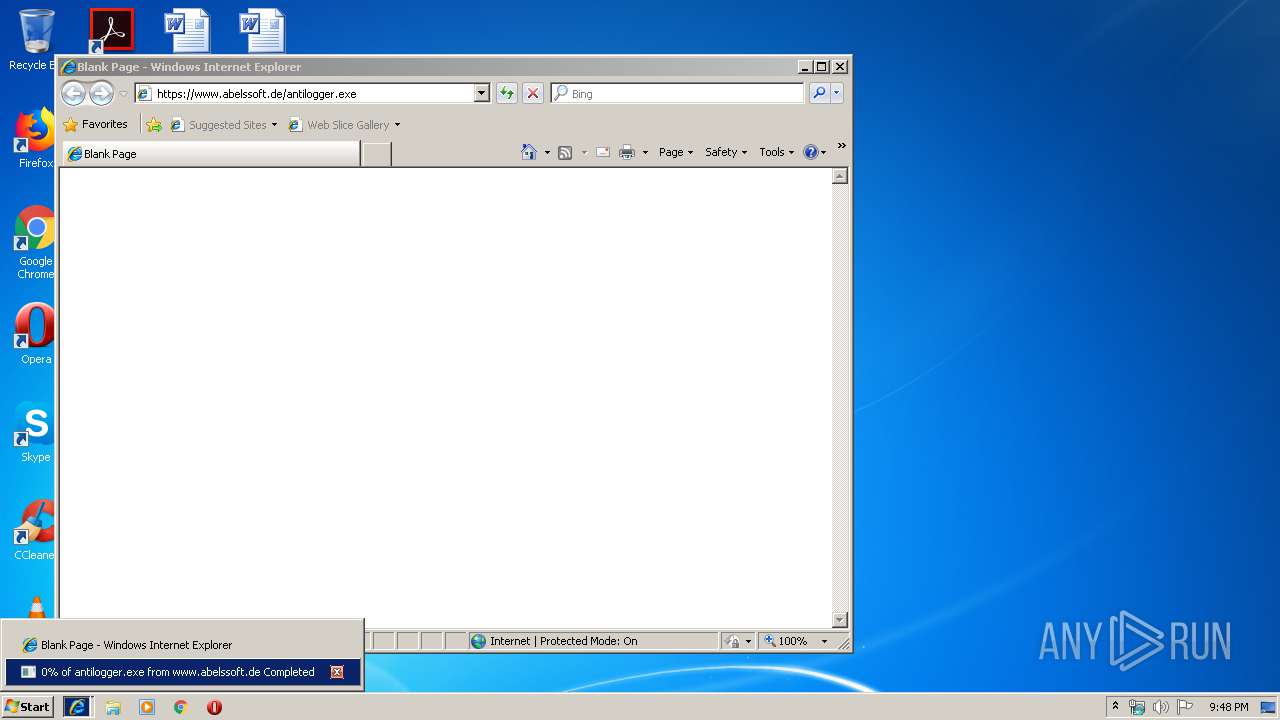
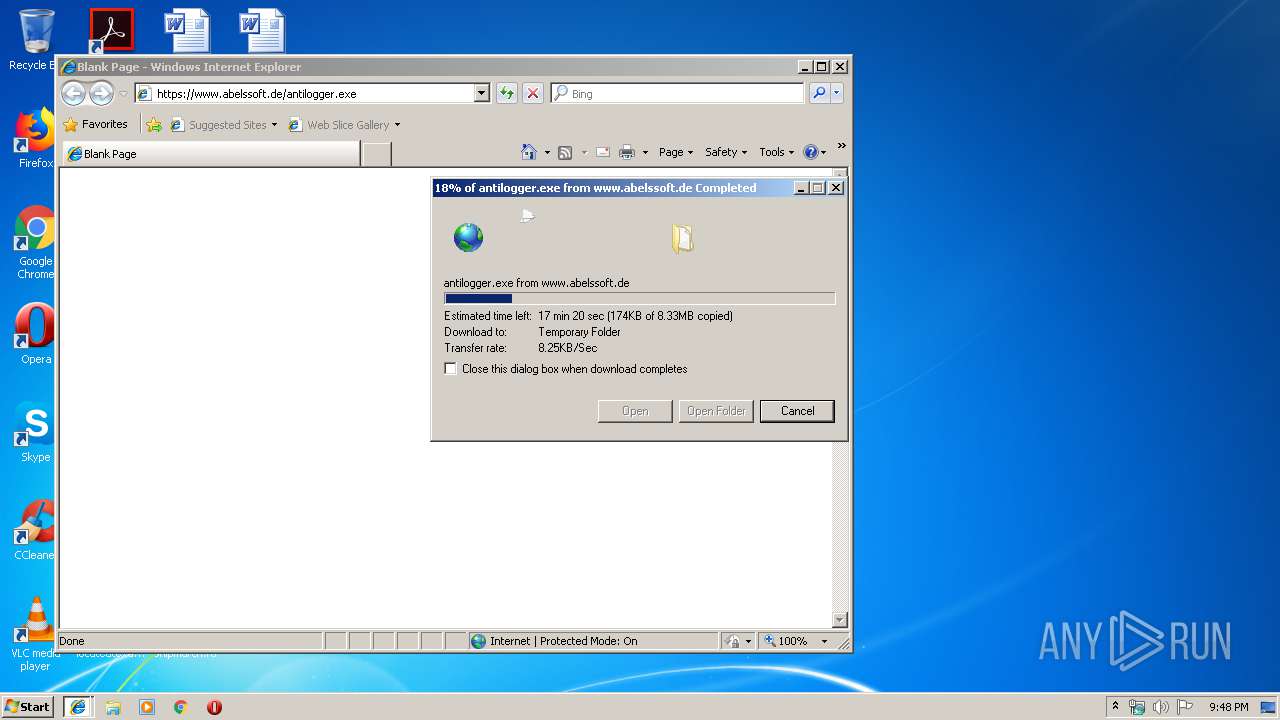
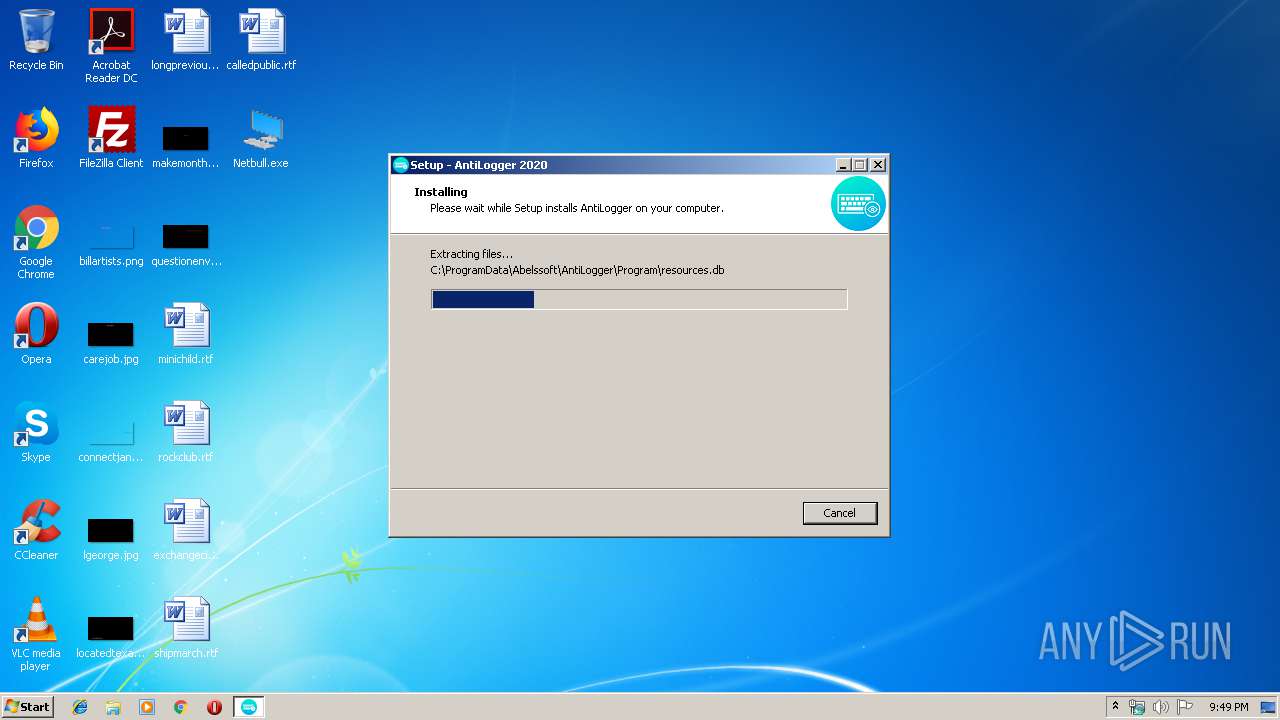
Executable content was dropped or overwritten
- svchost.exe (PID: 4028)
- iexplore.exe (PID: 2784)
- antilogger[1].exe (PID: 1796)
- iexplore.exe (PID: 4032)
- Netbull.exe (PID: 2152)
- antilogger[1].exe (PID: 820)
- antilogger[1].tmp (PID: 2956)
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 4028)
Reads Windows owner or organization settings
- antilogger[1].tmp (PID: 2956)
Reads the Windows organization settings
- antilogger[1].tmp (PID: 2956)
Creates files in the Windows directory
- antilogger[1].tmp (PID: 2956)
Reads Environment values
- AntiLogger.exe (PID: 2212)
- AntiLogger.exe (PID: 2836)
Creates files in the program directory
- AntiLogger.exe (PID: 2212)
Adds / modifies Windows certificates
- AntiLogger.exe (PID: 2836)
Searches for installed software
- AntiLogger.exe (PID: 2836)
- AntiLogger.exe (PID: 2212)
INFO
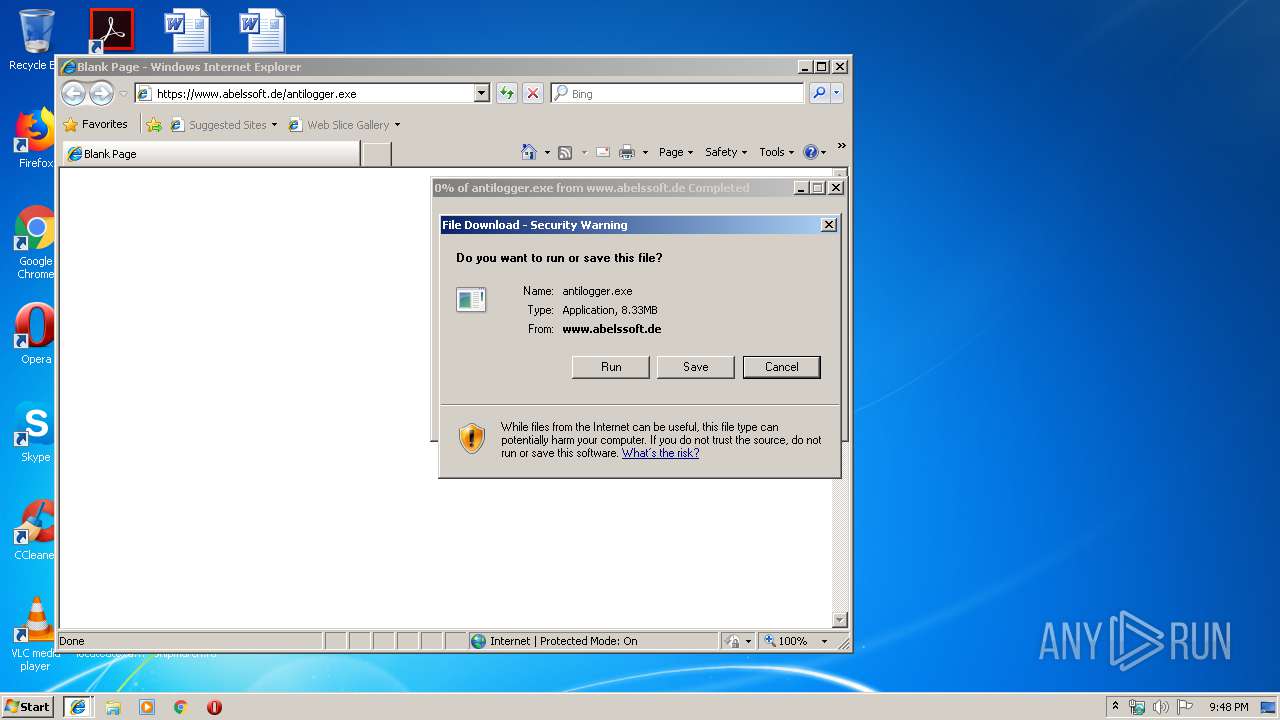
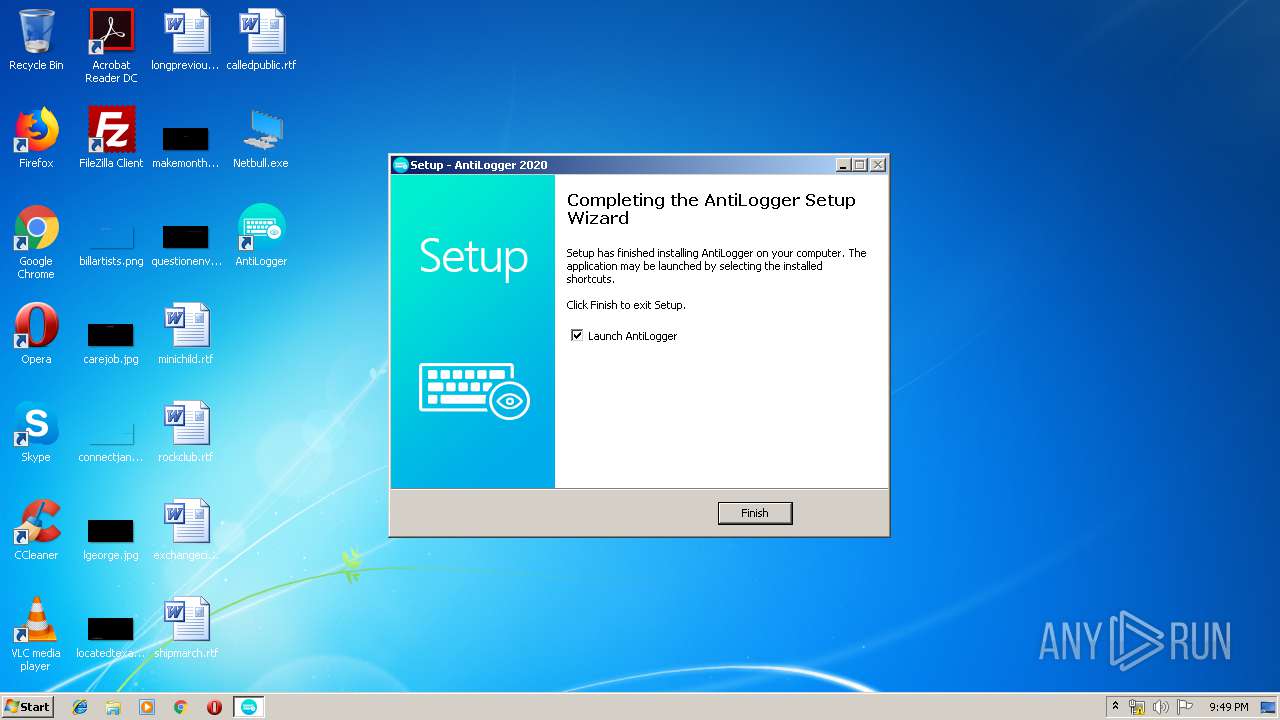
Manual execution by user
- iexplore.exe (PID: 2784)
- iexplore.exe (PID: 1768)
Changes internet zones settings
- iexplore.exe (PID: 1768)
- iexplore.exe (PID: 2784)
Reads Internet Cache Settings
- iexplore.exe (PID: 2140)
- iexplore.exe (PID: 4032)
- iexplore.exe (PID: 2784)
Reads internet explorer settings
- iexplore.exe (PID: 2140)
- iexplore.exe (PID: 4032)
Application launched itself
- iexplore.exe (PID: 1768)
Creates files in the user directory
- iexplore.exe (PID: 2784)
- iexplore.exe (PID: 4032)
Application was dropped or rewritten from another process
- closeapp.exe (PID: 3688)
- antilogger[1].tmp (PID: 2956)
- antilogger[1].tmp (PID: 2928)
Creates a software uninstall entry
- antilogger[1].tmp (PID: 2956)
Reads settings of System Certificates
- AntiLogger.exe (PID: 2836)
- AntiLogger.exe (PID: 2212)
Loads dropped or rewritten executable
- antilogger[1].tmp (PID: 2956)
Creates files in the program directory
- antilogger[1].tmp (PID: 2956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (38.2) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (37.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.2) |
| .exe | | | Win32 Executable (generic) (6.3) |
| .exe | | | Win16/32 Executable Delphi generic (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 28160 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x79d0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00006CB8 | 0x00006E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51771 |
DATA | 0x00008000 | 0x00000830 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.21269 |
BSS | 0x00009000 | 0x00000A75 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000A000 | 0x0000087C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.11254 |
.tls | 0x0000B000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000C000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0000D000 | 0x00000754 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.41981 |
.rsrc | 0x0000E000 | 0x0000102C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.38169 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.563 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
2 | 3.03265 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
DVCLAL | 4 | 16 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 4.48265 | 104 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
MAINICON | 2.32824 | 34 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
advapi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
54
Monitored processes
14
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 820 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\antilogger[1].exe" /SPAWNWND=$202C6 /NOTIFYWND=$3018E | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\antilogger[1].exe | antilogger[1].tmp | ||||||||||||
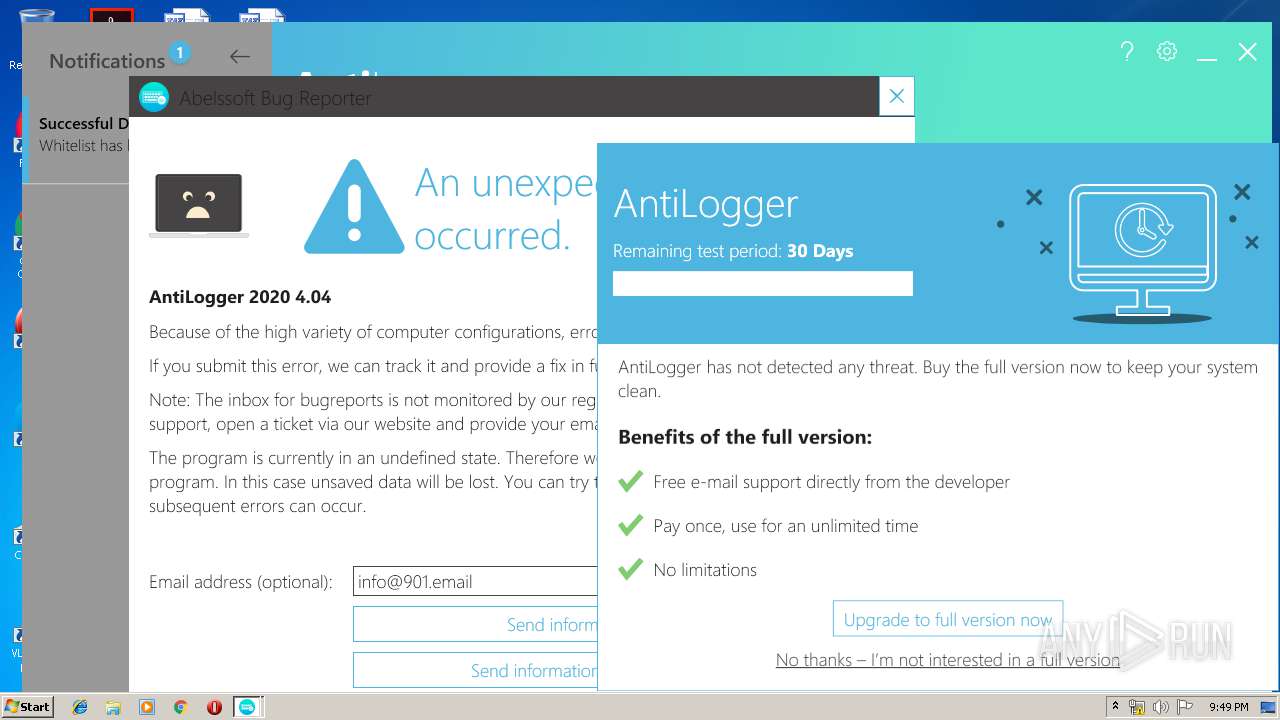
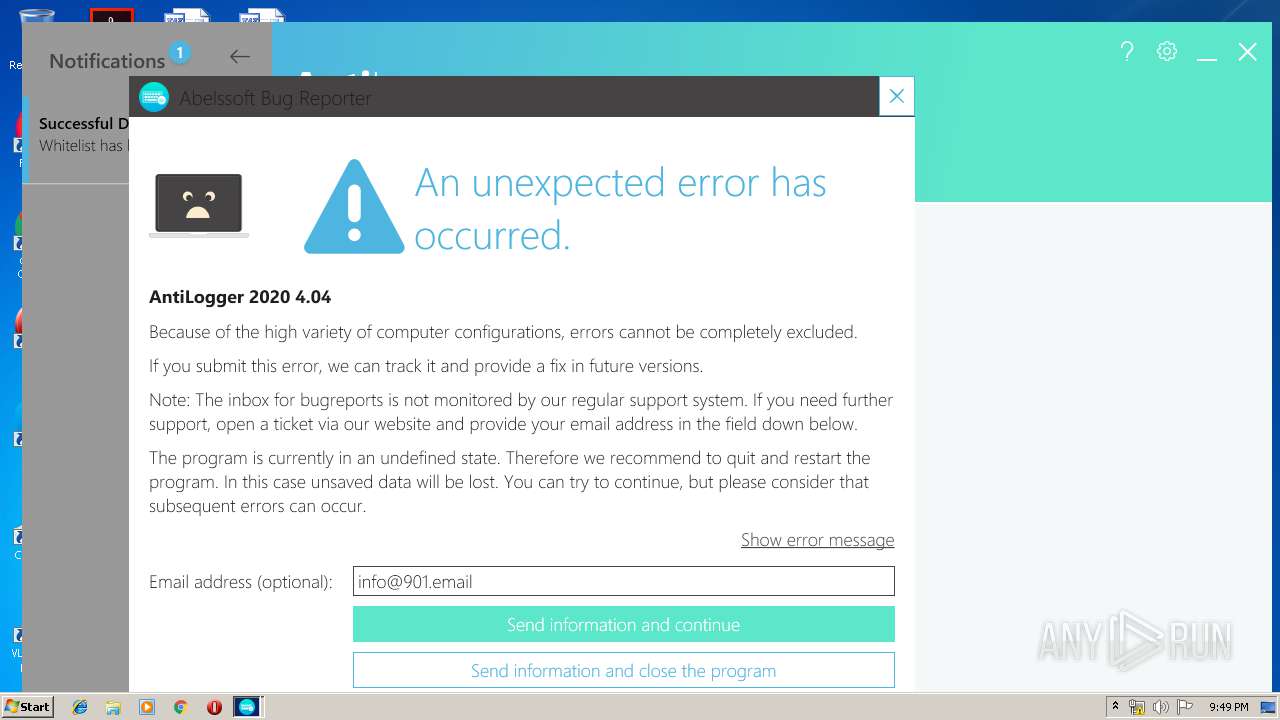
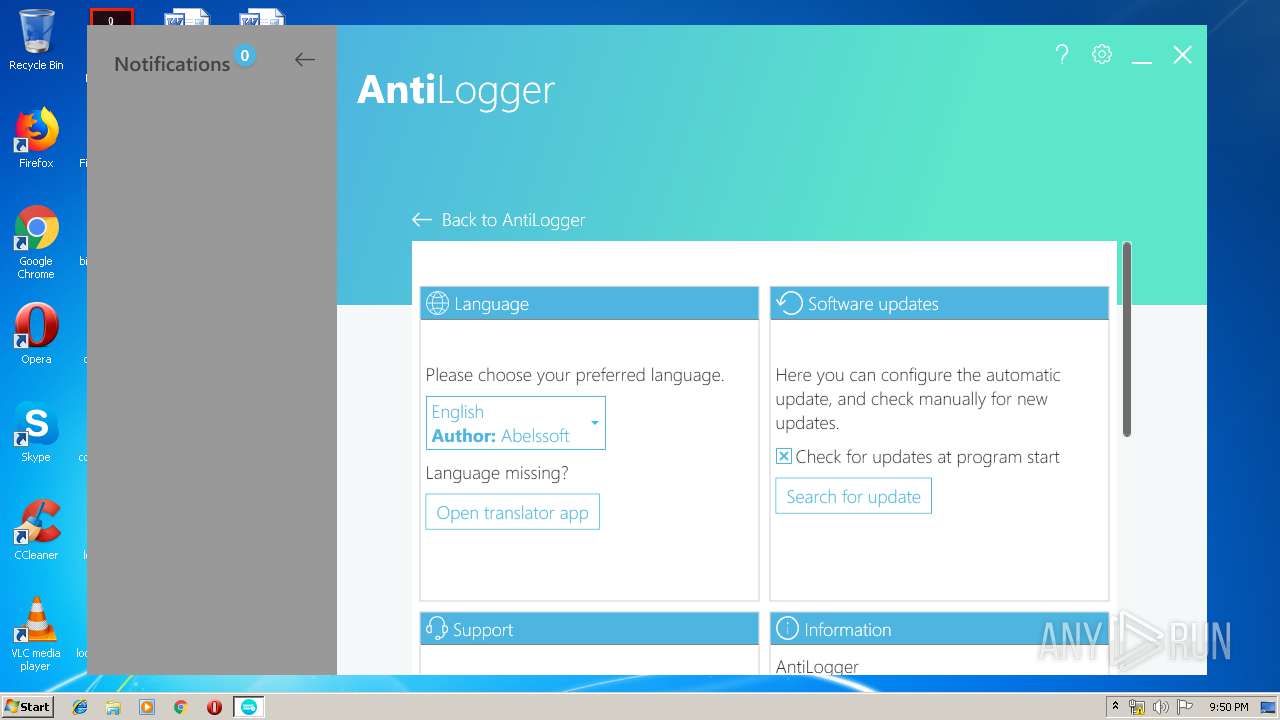
User: admin Company: Abelssoft Integrity Level: HIGH Description: AntiLogger 2020 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\AntiLogger\AbLauncher.exe" | C:\Program Files\AntiLogger\AbLauncher.exe | — | antilogger[1].tmp | |||||||||||
User: admin Integrity Level: HIGH Description: ConsoleApplication1 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1796 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\antilogger[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\antilogger[1].exe | iexplore.exe | ||||||||||||
User: admin Company: Abelssoft Integrity Level: MEDIUM Description: AntiLogger 2020 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1768 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | "C:\Users\admin\Desktop\Netbull.exe" | C:\Users\admin\Desktop\Netbull.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
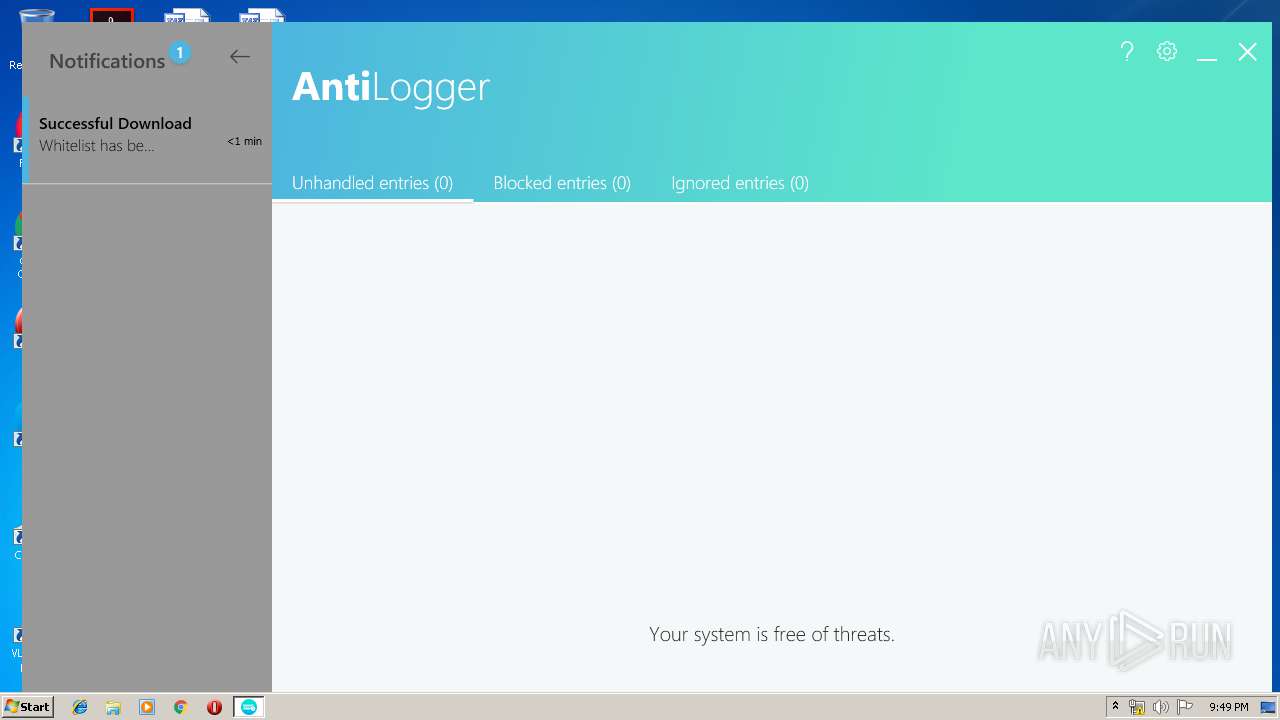
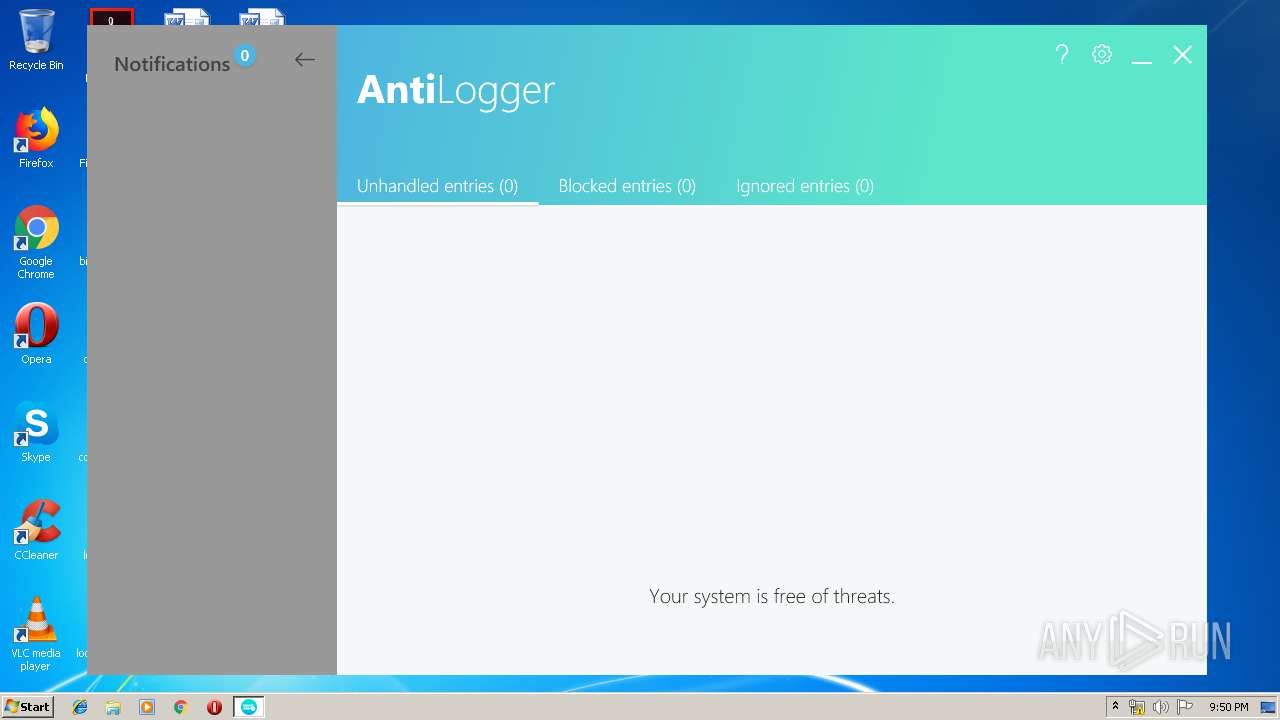
| 2212 | "C:\ProgramData\Abelssoft\AntiLogger\Program\AntiLogger.exe" | C:\ProgramData\Abelssoft\AntiLogger\Program\AntiLogger.exe | AbLauncher.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: AntiLogger Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2836 | "C:\ProgramData\Abelssoft\AntiLogger\Program\AntiLogger.exe" -install | C:\ProgramData\Abelssoft\AntiLogger\Program\AntiLogger.exe | antilogger[1].tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: AntiLogger Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2928 | "C:\Users\admin\AppData\Local\Temp\is-K4S26.tmp\antilogger[1].tmp" /SL5="$3018E,8308595,131584,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\antilogger[1].exe" | C:\Users\admin\AppData\Local\Temp\is-K4S26.tmp\antilogger[1].tmp | — | antilogger[1].exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
1 980
Read events
1 728
Write events
242
Delete events
10
Modification events
| (PID) Process: | (2152) Netbull.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\NL |
| Operation: | write | Name: | tr |
Value: CpJ6Zf2Z9A/YTVKXPKBGJyjCjlFJ0EbL4/T2QwekYSdYIKPv4RjeC/lVBKDEDZBzYxfGwy7RnlIJp0I | |||
| (PID) Process: | (4028) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\NL |
| Operation: | write | Name: | M1 |
Value: 5 | |||
| (PID) Process: | (4028) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\NL |
| Operation: | write | Name: | NBT |
Value: CpJ6Zf2Z9A/YTVKXPKBGJyjCjlFJ0EbL4/T2QwekYSdYIKPv4RjeC/lVBKDEDZBzYxfGwy7RnlYLi3M | |||
| (PID) Process: | (4028) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows |
| Operation: | write | Name: | Load |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows\nb3trial.exe | |||
| (PID) Process: | (4028) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4028) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4028) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4028) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4028) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4028) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
67
Suspicious files
10
Text files
143
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4028 | svchost.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3799140.tmp | — | |
MD5:— | SHA256:— | |||
| 2784 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1768 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[2].ico | — | |
MD5:— | SHA256:— | |||
| 1768 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1768 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB26AE6B9301F48C5.TMP | — | |
MD5:— | SHA256:— | |||
| 1768 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{29643D7D-1872-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 1768 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF935B8D514BC9B5F.TMP | — | |
MD5:— | SHA256:— | |||
| 1768 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF249D8749FE3C0466.TMP | — | |
MD5:— | SHA256:— | |||
| 1768 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{29643D7B-1872-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2152 | Netbull.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\nb3trial.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
9
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1768 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2784 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2784 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1768 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
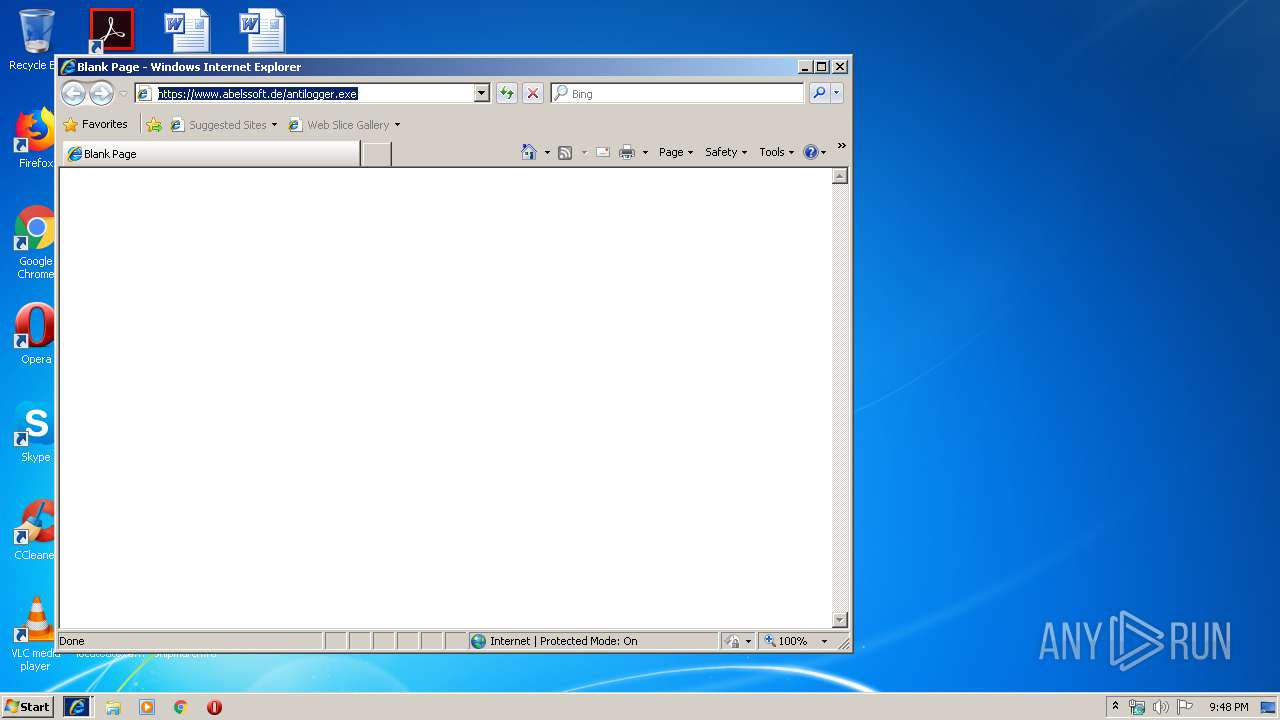
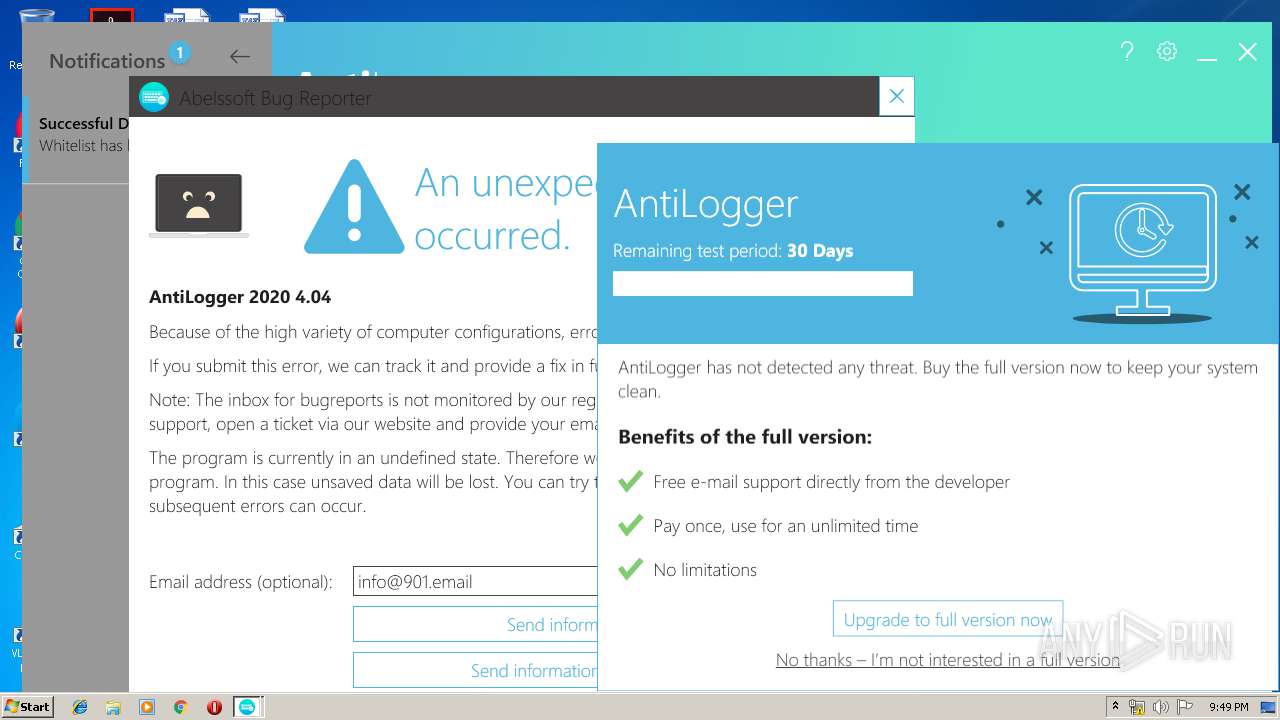
4032 | iexplore.exe | 104.26.1.177:443 | www.abelssoft.de | Cloudflare Inc | US | suspicious |
2836 | AntiLogger.exe | 104.26.3.173:443 | datahub.ascora.de | Cloudflare Inc | US | unknown |
2212 | AntiLogger.exe | 104.26.1.177:443 | www.abelssoft.de | Cloudflare Inc | US | suspicious |
2212 | AntiLogger.exe | 104.26.3.173:443 | datahub.ascora.de | Cloudflare Inc | US | unknown |
2212 | AntiLogger.exe | 104.26.0.177:443 | www.abelssoft.de | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.abelssoft.de |
| suspicious |
datahub.ascora.de |
| unknown |
key.abelssoft.de |
| suspicious |
abelssoft.de |
| whitelisted |
antilogger-api.abelssoft.de |
| suspicious |
api.abelssoft.de |
| suspicious |
Threats
Process | Message |
|---|---|
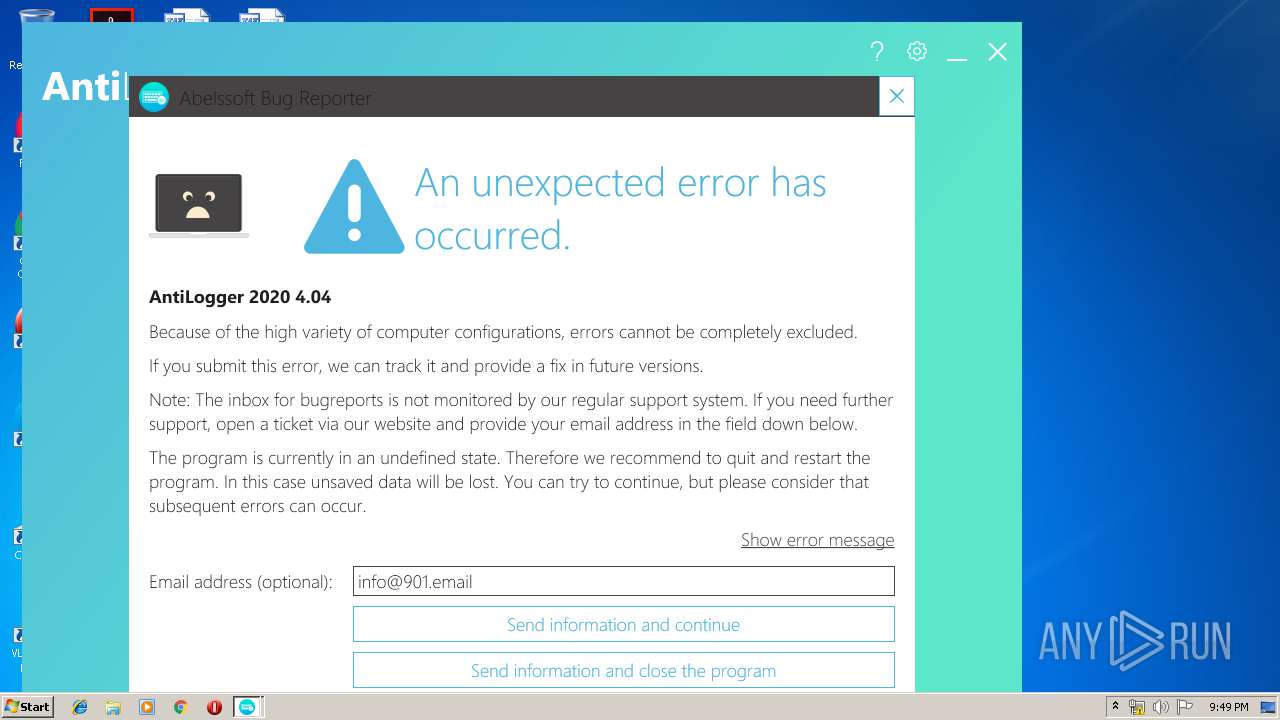
AntiLogger.exe | Log4Net: 2019-12-06 21:49:08,987 [INFO ] [Thread: 1] (AbDefault.AbstractApplication.InitializeLogger) - Logged-In User: USER-PC\admin
|
AntiLogger.exe | Log4Net: 2019-12-06 21:49:09,112 [INFO ] [Thread: 1] (AbDefault.AbstractApplication.InitializeLogger) - .NET Runtime: 4.0.30319.42000
|
AntiLogger.exe | Log4Net: 2019-12-06 21:49:09,112 [INFO ] [Thread: 1] (AbDefault.AbstractApplication.InitializeLogger) - Context-User: USER-PC\admin
|
AntiLogger.exe | Log4Net: 2019-12-06 21:49:09,112 [INFO ] [Thread: 1] (AbDefault.AbstractApplication.InitializeLogger) - Environment.Is64BitProcess: False
|
AntiLogger.exe | Log4Net: 2019-12-06 21:49:09,112 [INFO ] [Thread: 1] (AbDefault.AbstractApplication.InitializeLogger) - Environment.Is64BitOperatingSystem: False
|
AntiLogger.exe | Log4Net: 2019-12-06 21:49:09,143 [INFO ] [Thread: 1] (AbDefault.AbstractApplication.InitializeLogger) - OS: Microsoft Windows 7 Professional , 32-bit, Service Pack 1, Version 6.1.7601, Build 7601
|
AntiLogger.exe | Log4Net: 2019-12-06 21:49:09,158 [INFO ] [Thread: 1] (AbDefault.AbstractApplication.InitializeLogger) - AppInformation.Features.LiteRegistration: True
|
AntiLogger.exe | Log4Net: 2019-12-06 21:49:09,158 [INFO ] [Thread: 1] (AbDefault.AbstractApplication.InitializeLogger) - AppInformation.Features.TipScreen: False
|
AntiLogger.exe | Log4Net: 2019-12-06 21:49:09,158 [INFO ] [Thread: 1] (AbDefault.AbstractApplication.InitializeLogger) - AppInformation.AppId: 3
|
AntiLogger.exe | Log4Net: 2019-12-06 21:49:09,158 [INFO ] [Thread: 1] (AbDefault.AbstractApplication.InitializeLogger) - AppInformation.AppName: AntiLogger
|