| File name: | Netbull.exe |
| Full analysis: | https://app.any.run/tasks/392ad23c-05de-499e-b8a7-96f4a66c8e9b |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 20:57:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 28602BA664770C545FE59C28FA64D207 |
| SHA1: | 824168027BC2D4C46892C042FF3B4F8E62DFA080 |
| SHA256: | 7559D9262637D1E610F24BD694D8333A95A15DF687599A128055AA03025DF4DC |
| SSDEEP: | 6144:Wa6rm3jPz4m78UknzfVLr97rBp+4xdtBIF0tlOQOQbqJ+NJk1bznjAb1ytk2C:WmTEmgUQl97rBp+QtWWaQOQbqJm60YA |
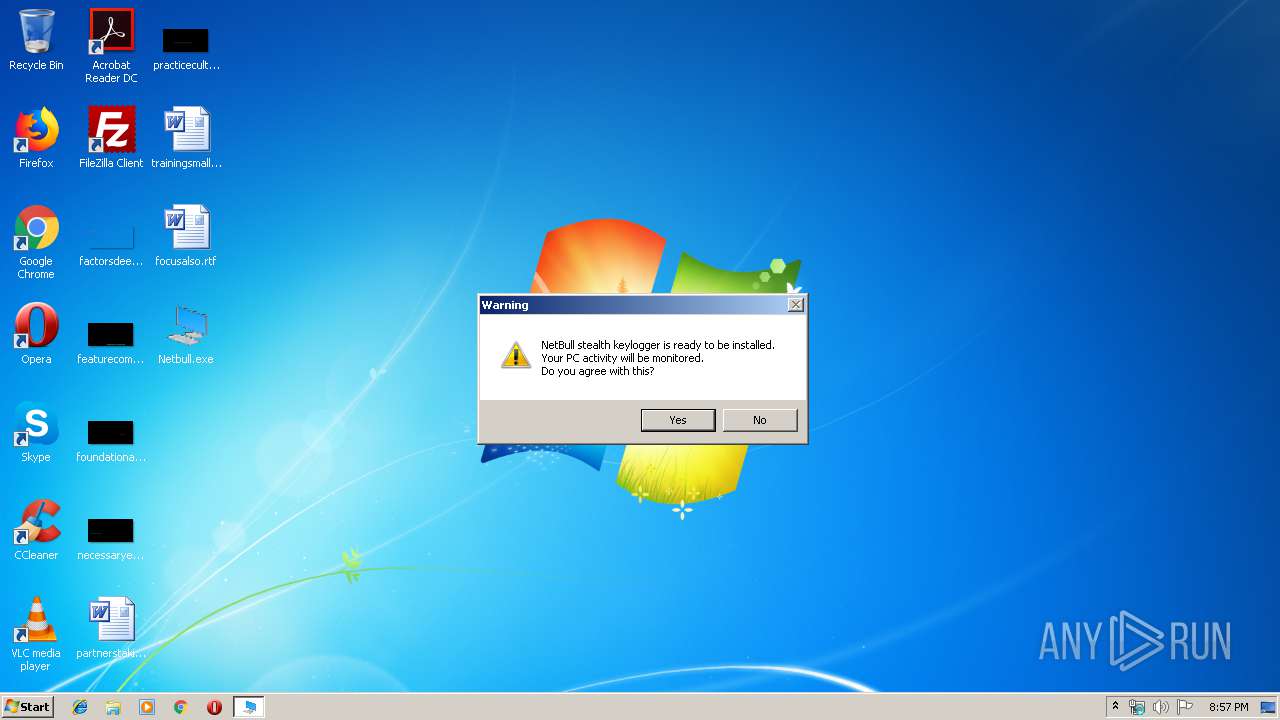
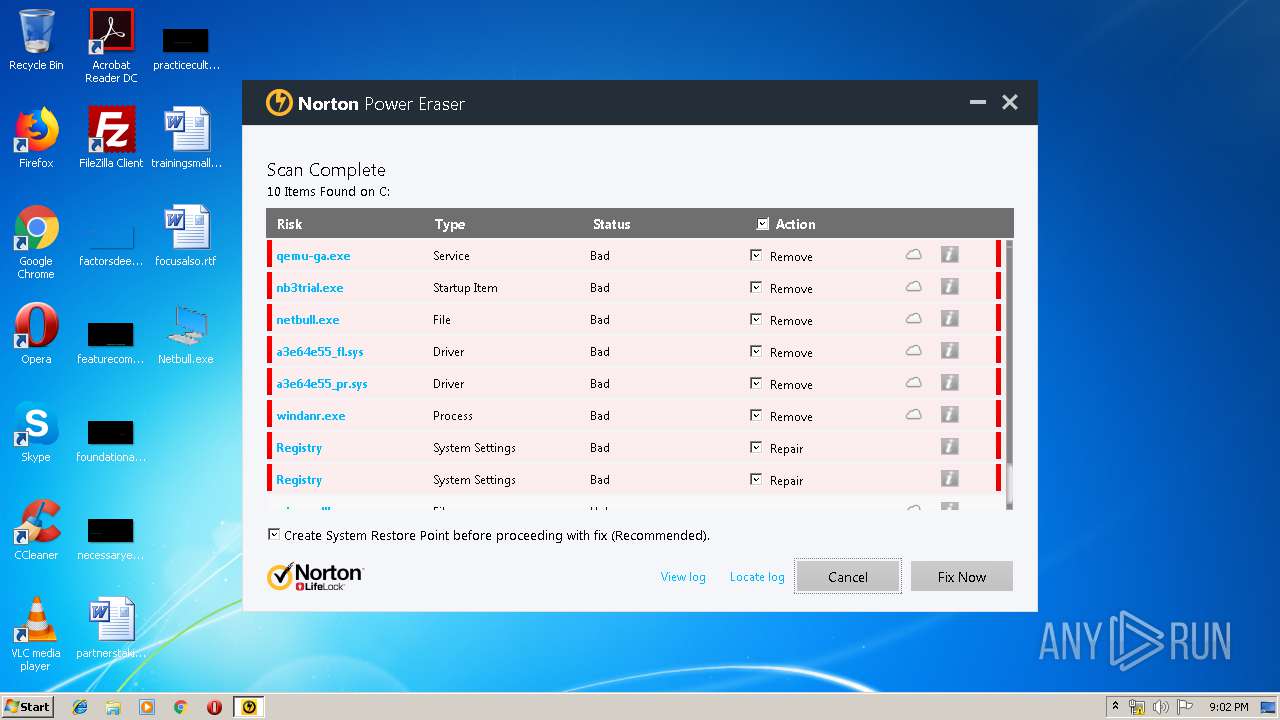
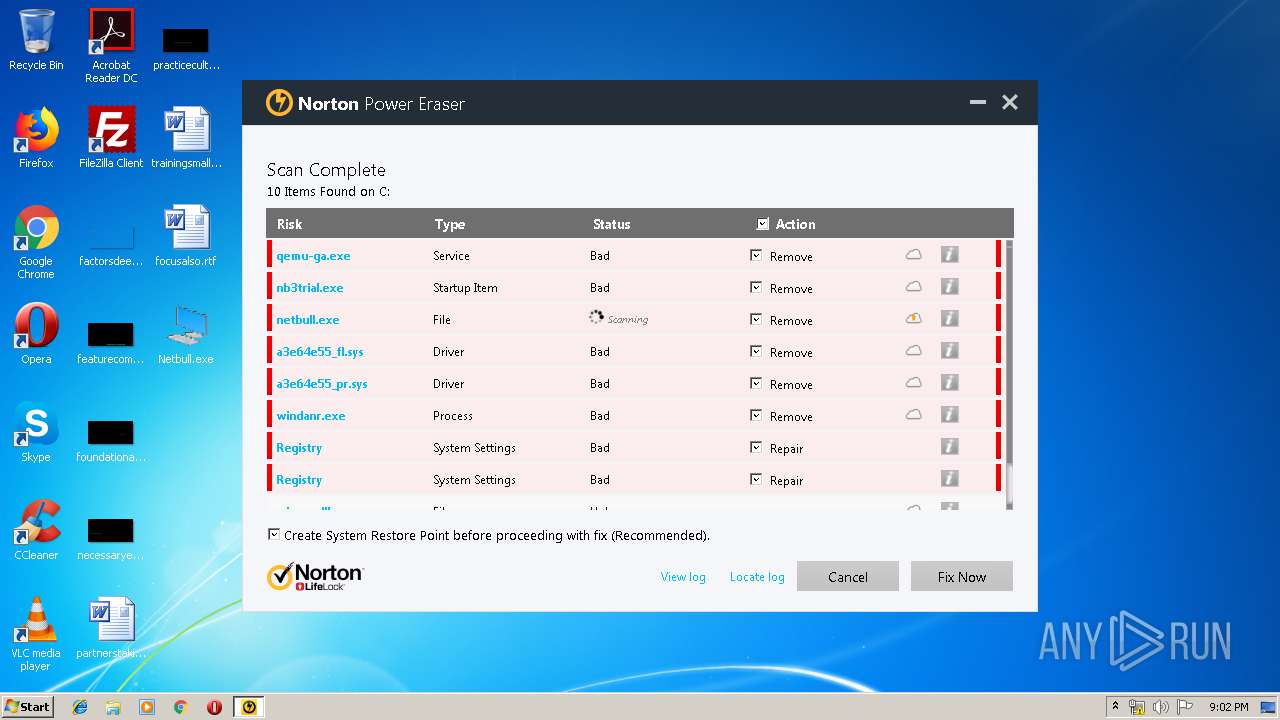
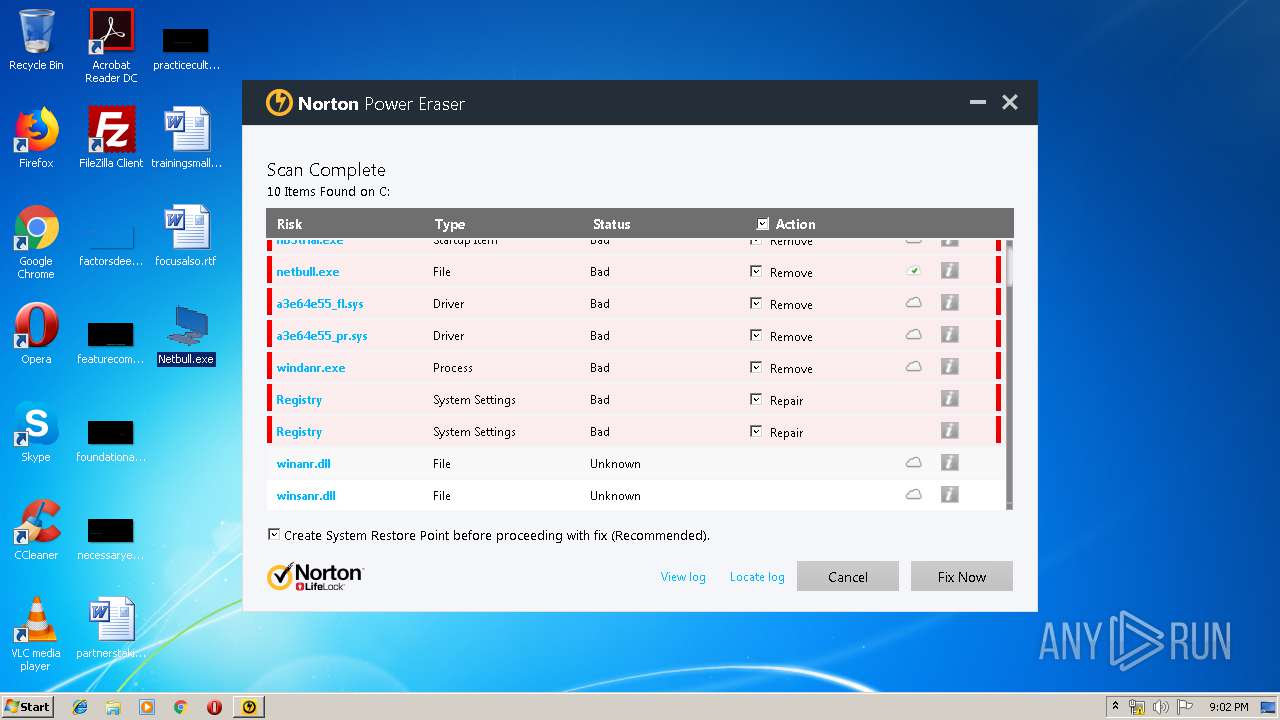
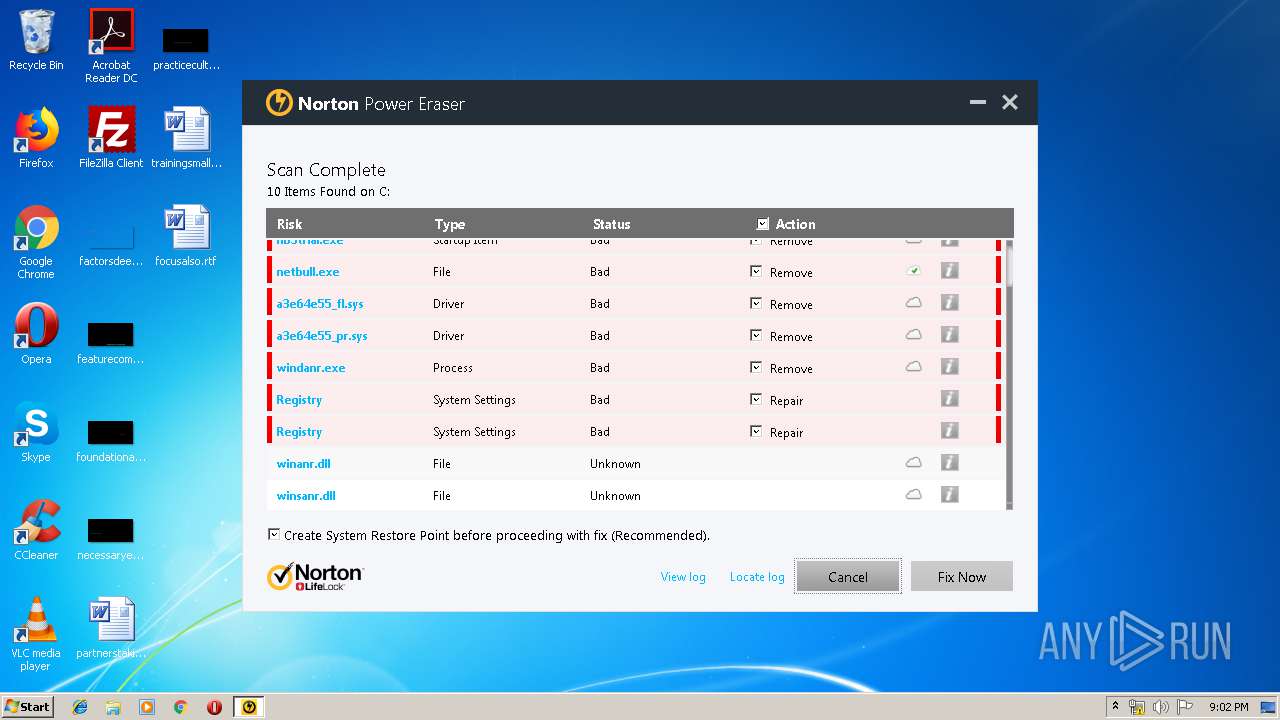
MALICIOUS
Changes the autorun value in the registry
- svchost.exe (PID: 3892)
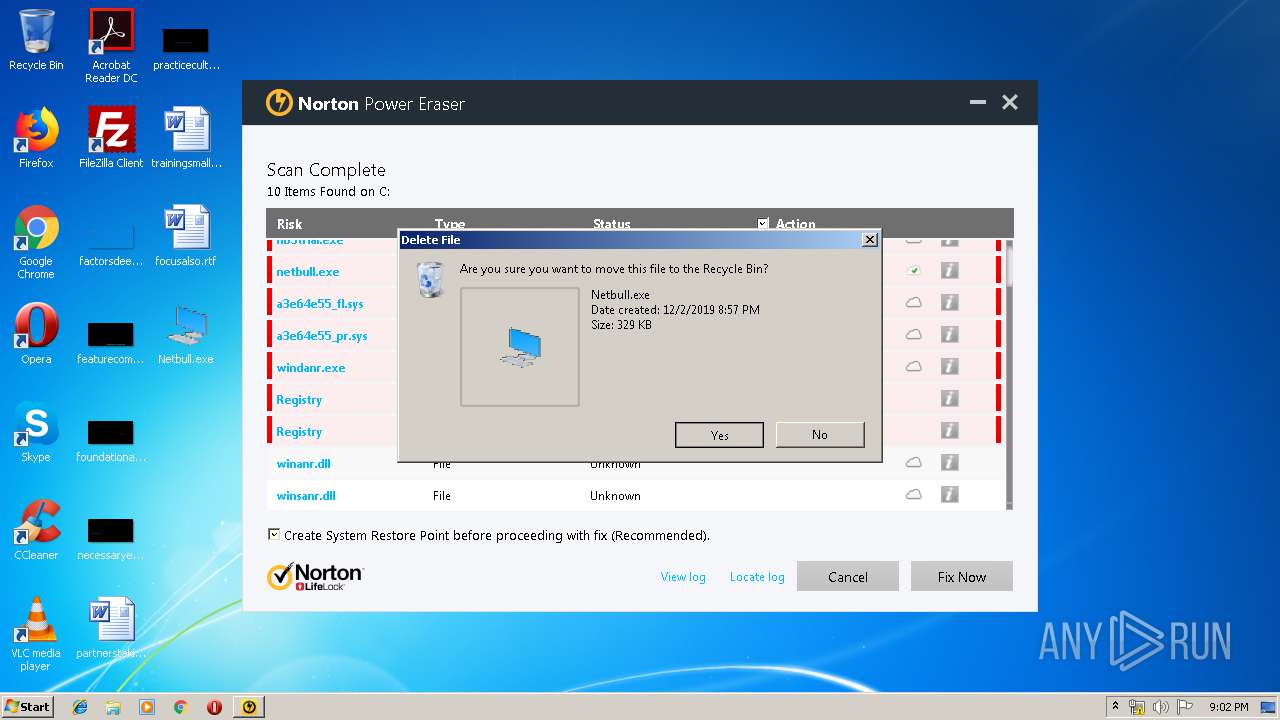
Application was dropped or rewritten from another process
- NPE[1].exe (PID: 3980)
- NPE[1].exe (PID: 3012)
Changes settings of System certificates
- NPE[1].exe (PID: 3012)
Uses SVCHOST.EXE for hidden code execution
- Netbull.exe (PID: 964)
SUSPICIOUS
Executable content was dropped or overwritten
- Netbull.exe (PID: 964)
- NPE[1].exe (PID: 3012)
- iexplore.exe (PID: 3312)
- iexplore.exe (PID: 2180)
- svchost.exe (PID: 3892)
Creates files in the program directory
- NPE[1].exe (PID: 3012)
Removes files from Windows directory
- NPE[1].exe (PID: 3012)
Creates files in the driver directory
- NPE[1].exe (PID: 3012)
Creates files in the Windows directory
- NPE[1].exe (PID: 3012)
Adds / modifies Windows certificates
- NPE[1].exe (PID: 3012)
Reads Internet Cache Settings
- NPE[1].exe (PID: 3012)
Searches for installed software
- NPE[1].exe (PID: 3012)
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 3892)
INFO
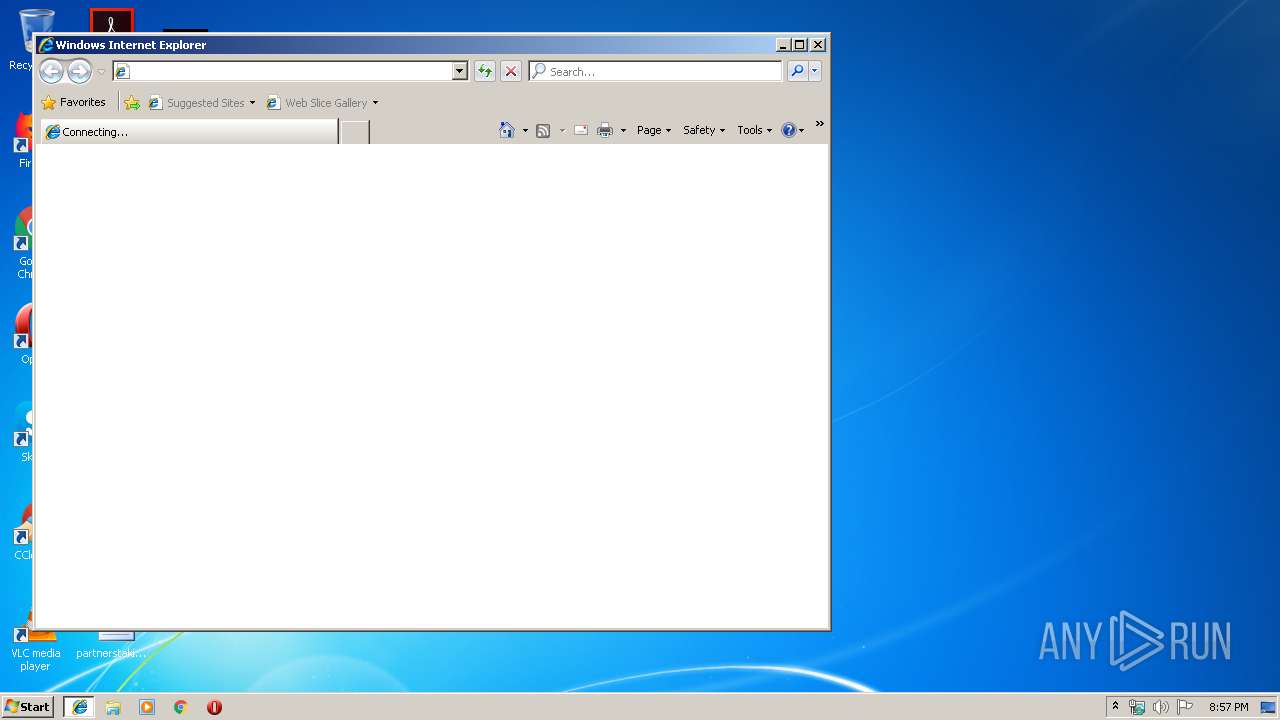
Reads internet explorer settings
- iexplore.exe (PID: 3312)
Reads Internet Cache Settings
- iexplore.exe (PID: 3312)
- iexplore.exe (PID: 2180)
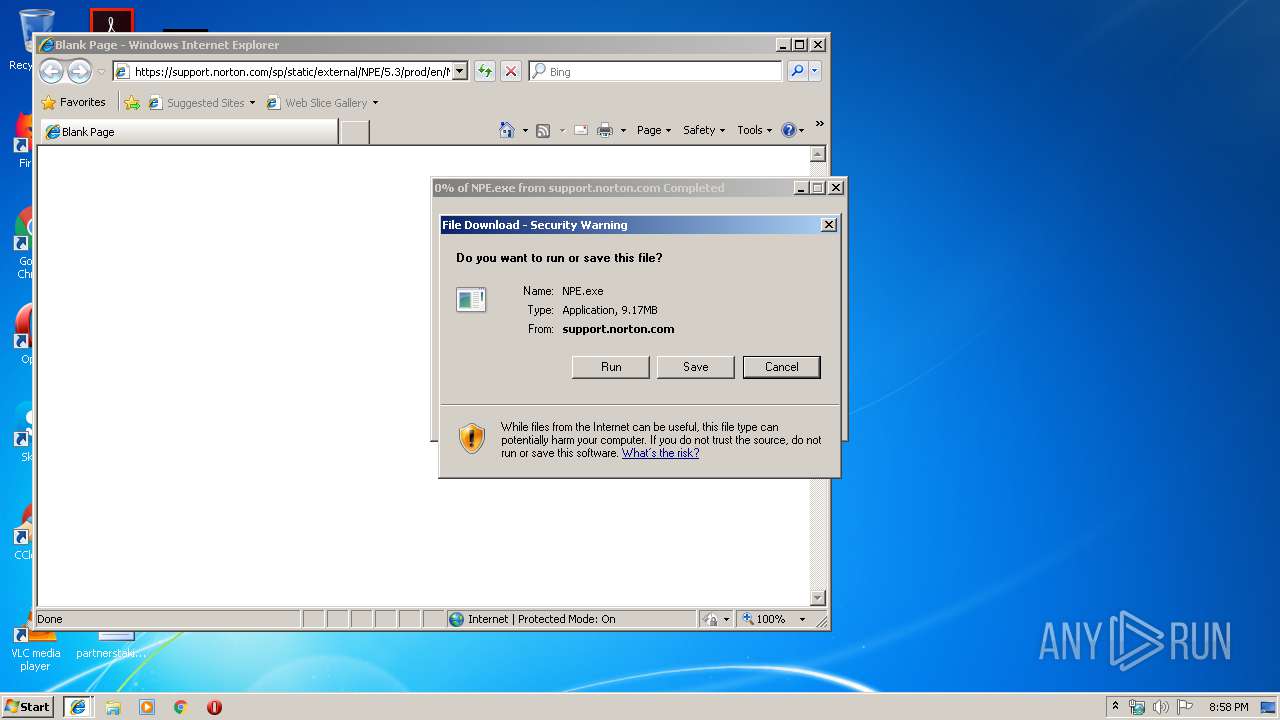
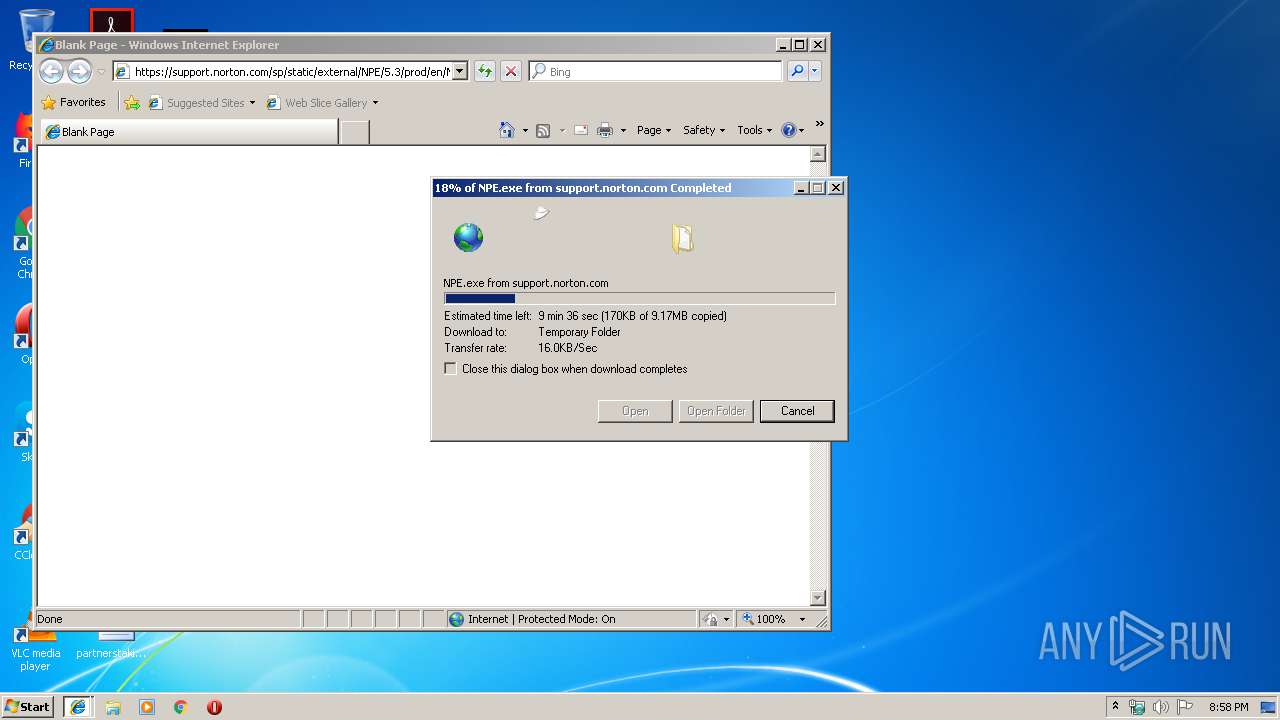
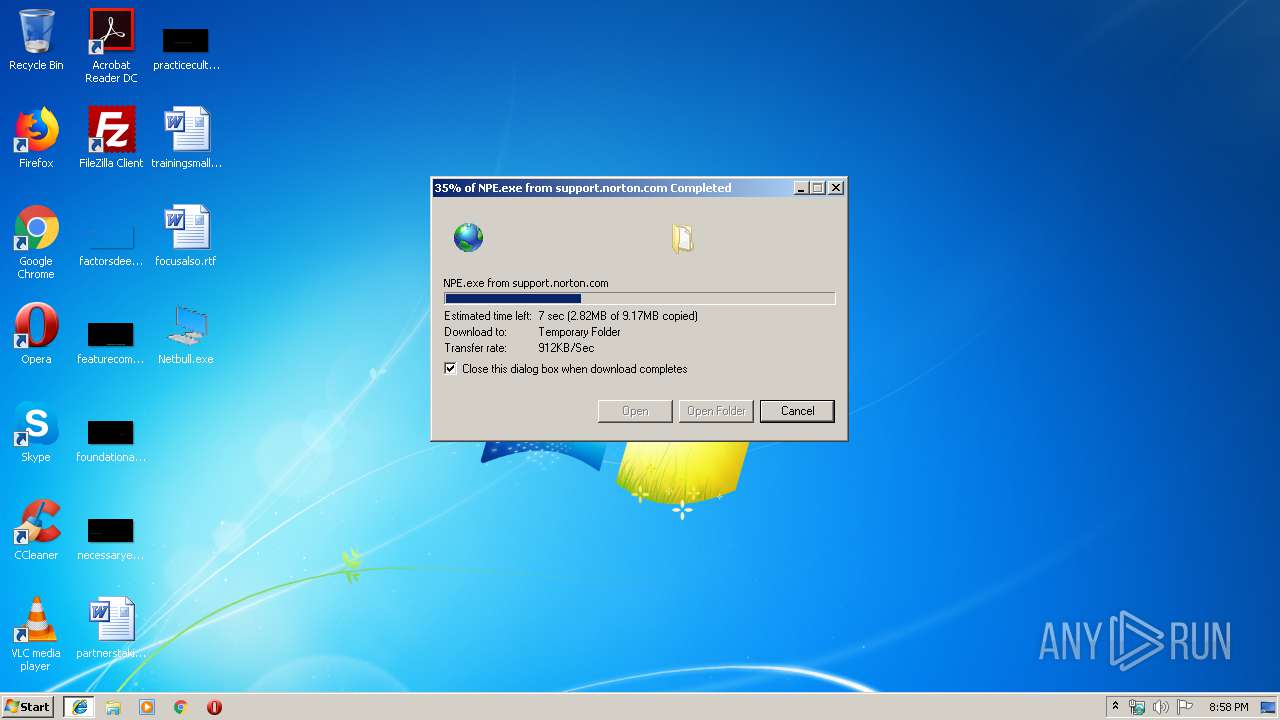
Manual execution by user
- iexplore.exe (PID: 2180)
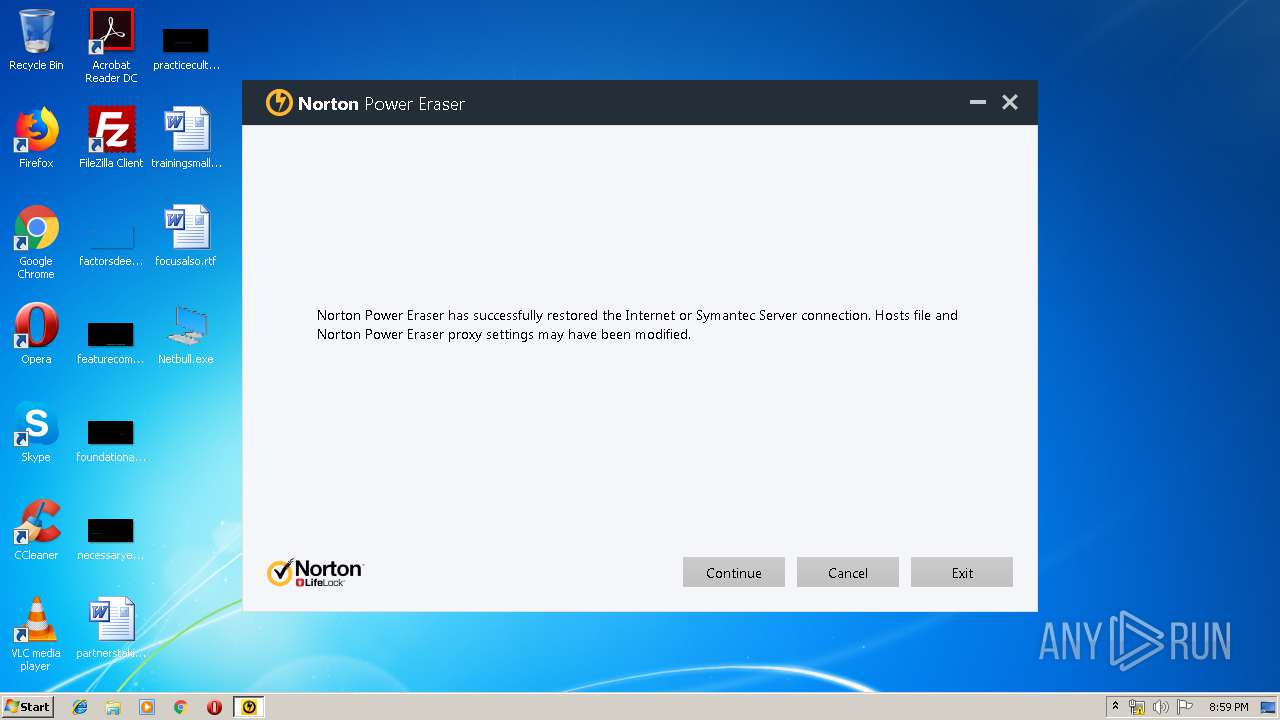
Reads the hosts file
- NPE[1].exe (PID: 3012)
Dropped object may contain Bitcoin addresses
- NPE[1].exe (PID: 3012)
Changes internet zones settings
- iexplore.exe (PID: 2180)
Application launched itself
- iexplore.exe (PID: 2180)
Reads settings of System Certificates
- NPE[1].exe (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (38.2) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (37.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.2) |
| .exe | | | Win32 Executable (generic) (6.3) |
| .exe | | | Win16/32 Executable Delphi generic (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 28160 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x79d0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00006CB8 | 0x00006E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51771 |
DATA | 0x00008000 | 0x00000830 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.21269 |
BSS | 0x00009000 | 0x00000A75 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000A000 | 0x0000087C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.11254 |
.tls | 0x0000B000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000C000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0000D000 | 0x00000754 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.41981 |
.rsrc | 0x0000E000 | 0x0000102C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.38169 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.563 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
2 | 3.03265 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
DVCLAL | 4 | 16 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 4.48265 | 104 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
MAINICON | 2.32824 | 34 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
advapi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
43
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 964 | "C:\Users\admin\Desktop\Netbull.exe" | C:\Users\admin\Desktop\Netbull.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
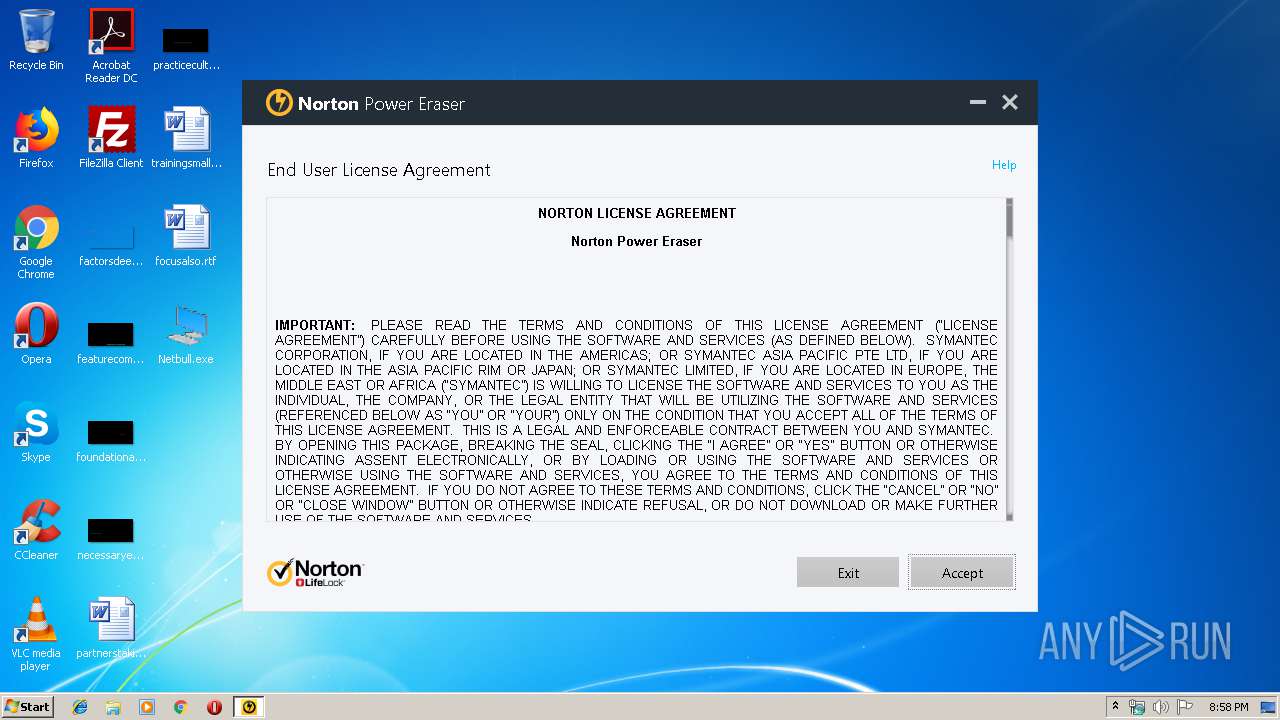
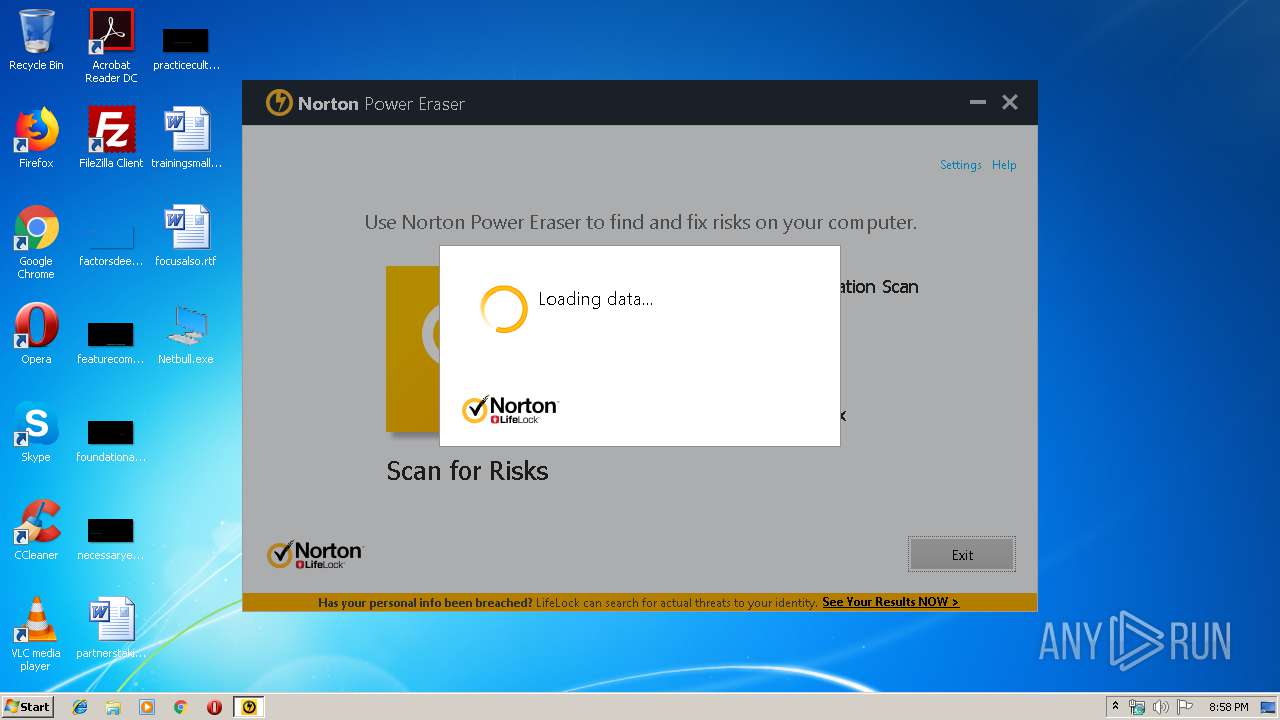
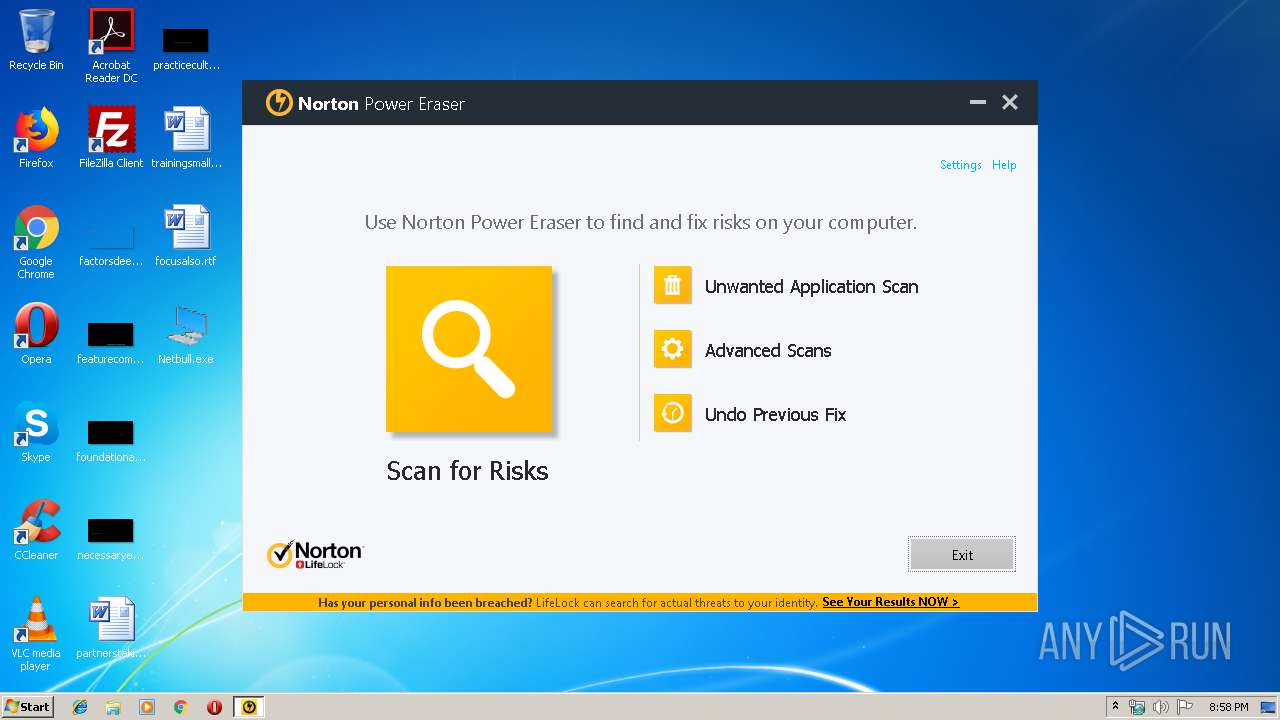
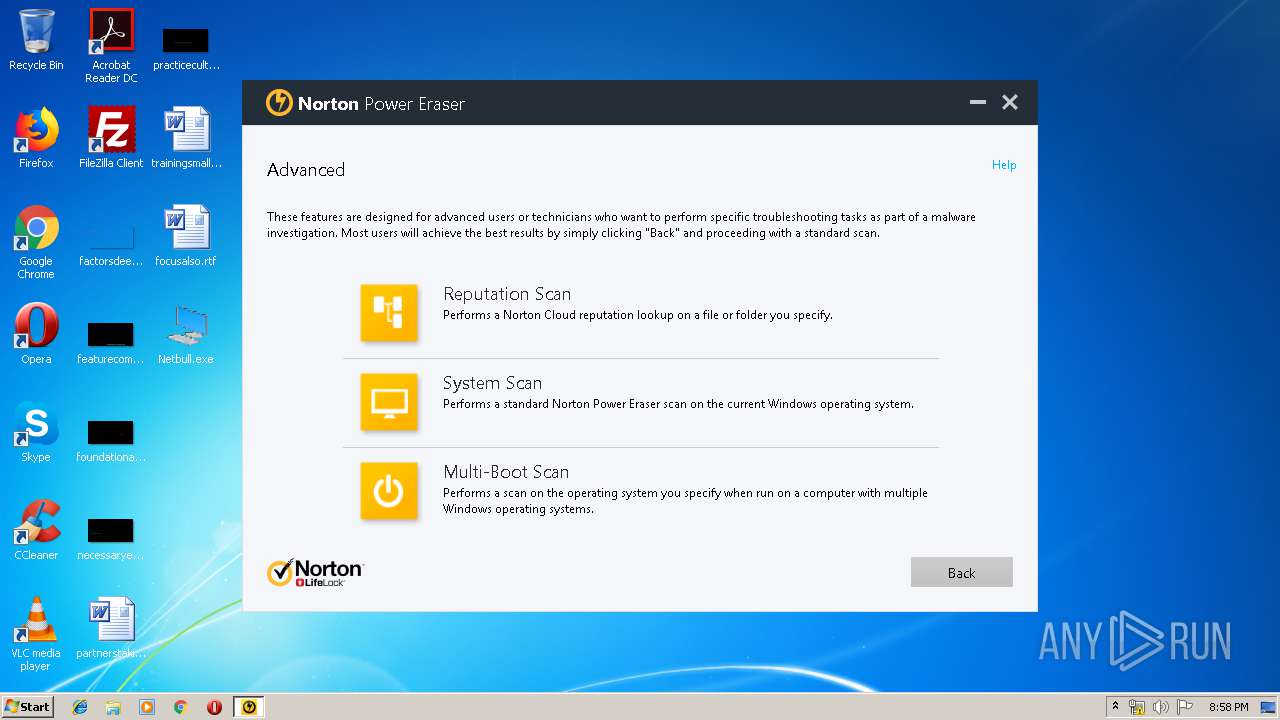
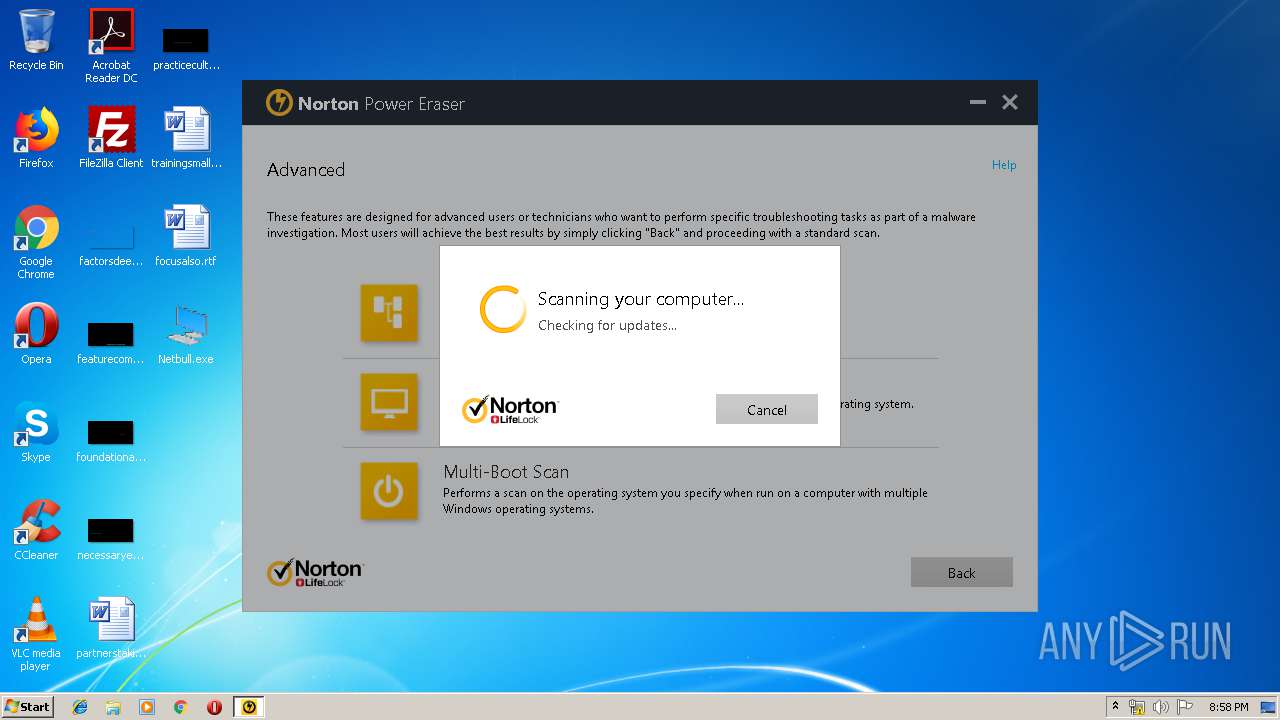
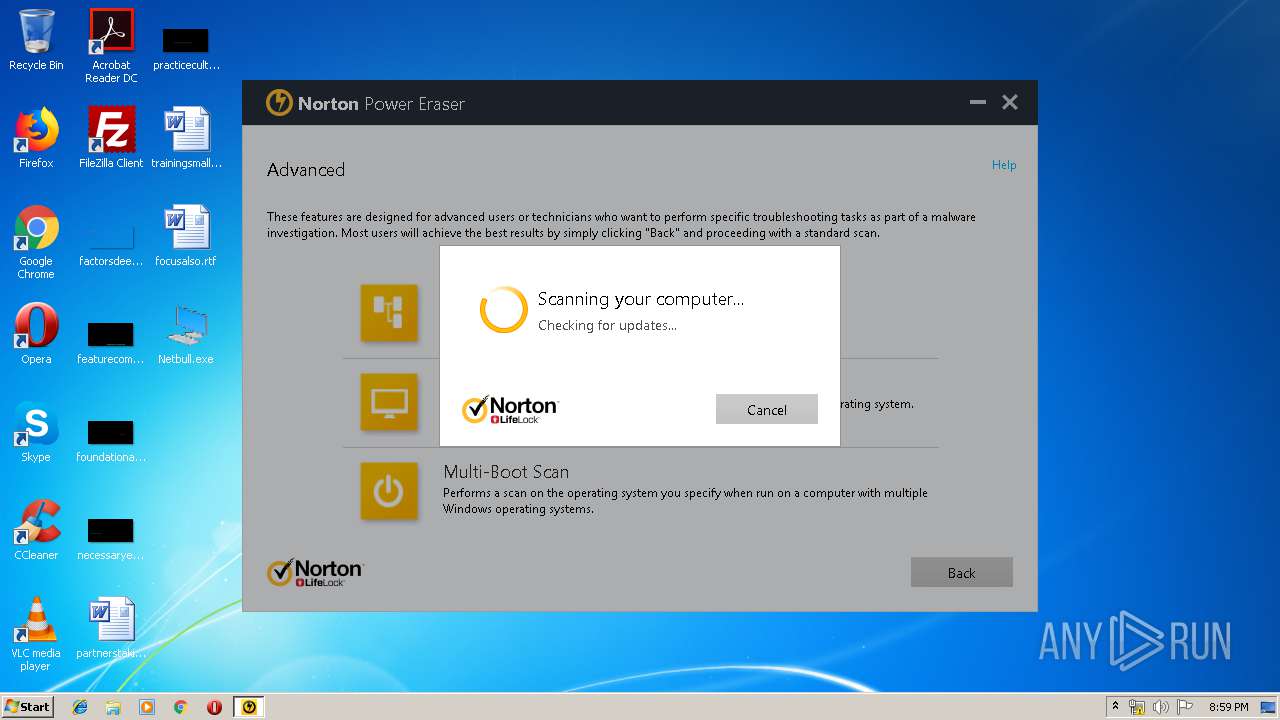
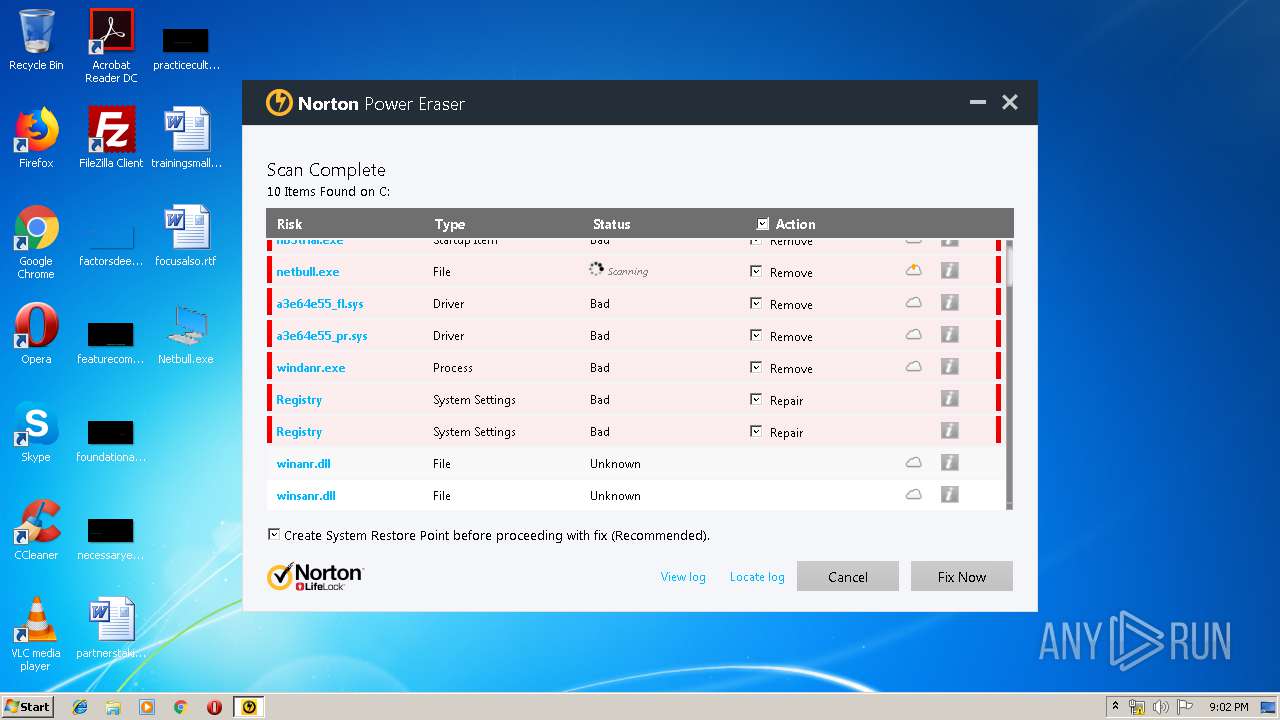
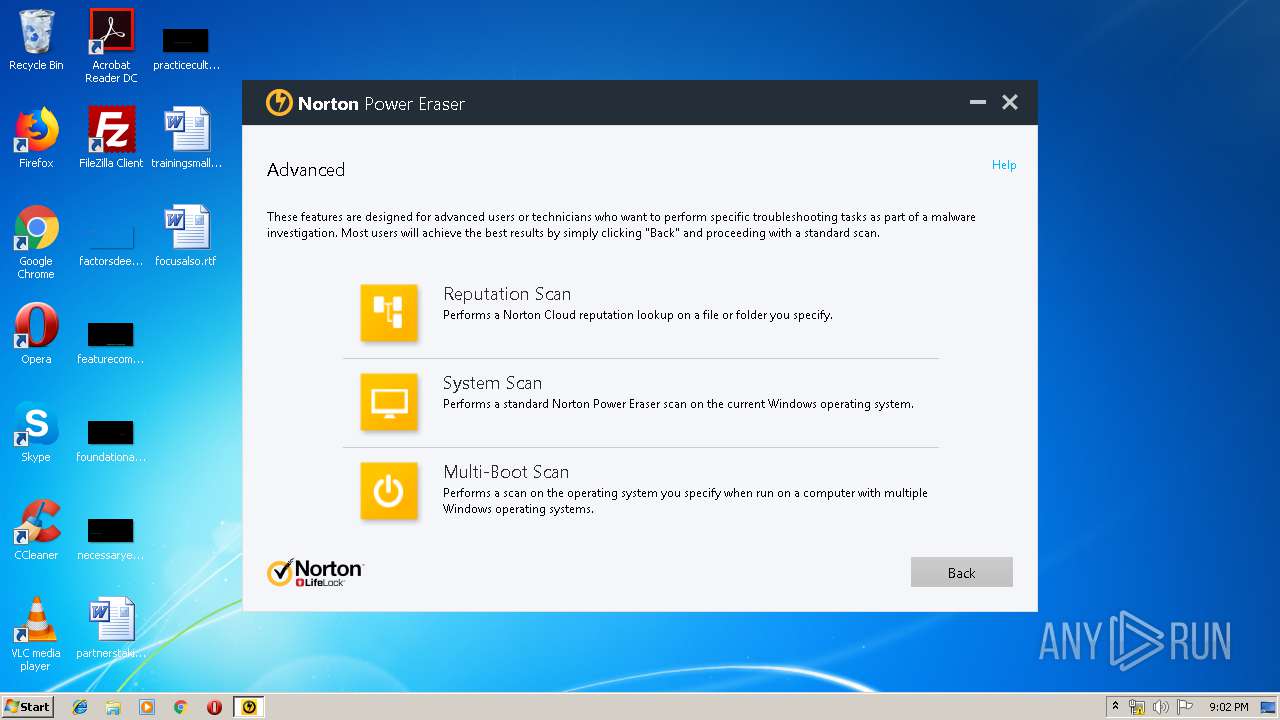
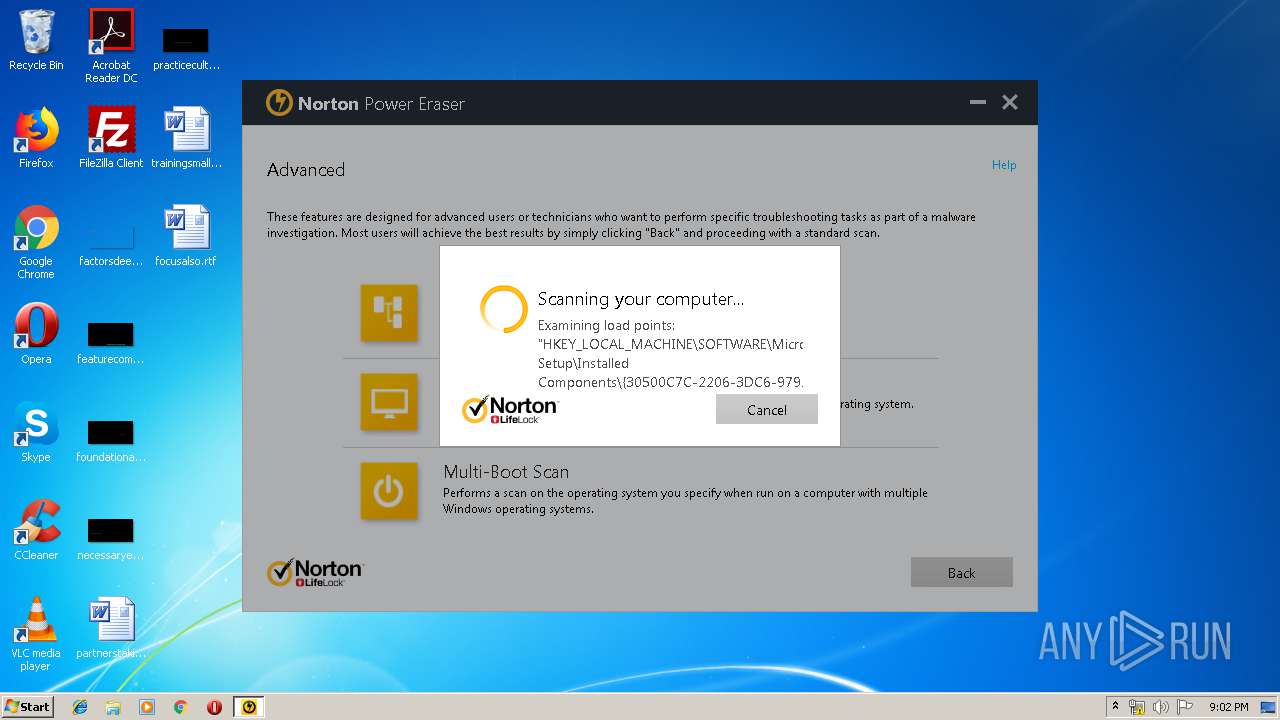
| 3012 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\NPE[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\NPE[1].exe | iexplore.exe | ||||||||||||
User: admin Company: Symantec Corporation Integrity Level: HIGH Description: Norton Power Eraser Exit code: 0 Version: 5.3.0.47 Modules
| |||||||||||||||
| 3312 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2180 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3892 | svchost.exe | C:\Windows\system32\svchost.exe | Netbull.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3980 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\NPE[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\NPE[1].exe | — | iexplore.exe | |||||||||||
User: admin Company: Symantec Corporation Integrity Level: MEDIUM Description: Norton Power Eraser Exit code: 3221226540 Version: 5.3.0.47 Modules
| |||||||||||||||
Total events
2 410
Read events
2 197
Write events
209
Delete events
4
Modification events
| (PID) Process: | (964) Netbull.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\NL |
| Operation: | write | Name: | tr |
Value: CpJ6Zf2Z9A/YTVKXPKBGJyjCjlFJ0EbL4/T2QwekYSdYIKPv4RjeC/lVBKDEDZBzYxfGwy7RnlIJp0I | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {6A680F43-1546-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
Executable files
6
Suspicious files
12
Text files
20
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3892 | svchost.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3799812.tmp | — | |
MD5:— | SHA256:— | |||
| 2180 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2180 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF292EA161FCCF38E3.TMP | — | |
MD5:— | SHA256:— | |||
| 2180 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{6A680F45-1546-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2180 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFDA3AB8CAD3E5C4A6.TMP | — | |
MD5:— | SHA256:— | |||
| 3012 | NPE[1].exe | C:\Users\admin\AppData\Local\NPE\ErrMgmt\SQCLIENT.dat.log | — | |
MD5:— | SHA256:— | |||
| 3312 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2180 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6B266C466D216C06.TMP | — | |
MD5:— | SHA256:— | |||
| 2180 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{6A680F43-1546-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
54
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3012 | NPE[1].exe | GET | — | 152.195.132.112:80 | http://definitions.symantec.com/defs/dm/smrdat.7z | US | — | — | malicious |
3012 | NPE[1].exe | GET | 200 | 152.195.132.112:80 | http://definitions.symantec.com/defs/dm/smrscd.7z | US | compressed | 6.37 Kb | malicious |
3012 | NPE[1].exe | GET | 200 | 152.195.132.112:80 | http://definitions.symantec.com/defs/dm/smrscd.7z | US | compressed | 6.37 Kb | malicious |
3012 | NPE[1].exe | GET | 200 | 152.195.132.112:80 | http://definitions.symantec.com/defs/dm/smrscd.7z | US | compressed | 6.37 Kb | malicious |
3012 | NPE[1].exe | GET | 200 | 152.195.132.112:80 | http://definitions.symantec.com/defs/dm/smrdat.7z | US | compressed | 282 Kb | malicious |
3012 | NPE[1].exe | GET | 200 | 152.195.132.112:80 | http://definitions.symantec.com/defs/dm/smrdat.7z | US | compressed | 282 Kb | malicious |
3012 | NPE[1].exe | GET | 200 | 152.195.132.112:80 | http://definitions.symantec.com/defs/dm/smrdat.7z | US | compressed | 282 Kb | malicious |
3012 | NPE[1].exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2180 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3012 | NPE[1].exe | 2.20.188.10:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3012 | NPE[1].exe | 40.121.151.238:443 | tool-avpg.crsi.symantec.com | Microsoft Corporation | US | unknown |
3012 | NPE[1].exe | 208.67.222.222:53 | — | OpenDNS, LLC | US | malicious |
3012 | NPE[1].exe | 91.199.212.52:80 | crt.comodoca.com | Comodo CA Ltd | GB | suspicious |
3312 | iexplore.exe | 2.20.20.197:443 | support.norton.com | Akamai International B.V. | — | whitelisted |
3012 | NPE[1].exe | 152.195.132.112:80 | definitions.symantec.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3012 | NPE[1].exe | 8.8.4.4:53 | — | Google Inc. | US | whitelisted |
3012 | NPE[1].exe | 40.118.201.45:443 | stats.norton.com | Microsoft Corporation | US | malicious |
3012 | NPE[1].exe | 2.20.20.197:443 | support.norton.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
support.norton.com |
| whitelisted |
definitions.symantec.com |
| malicious |
stats.qalabs.symantec.com |
| unknown |
stats.norton.com |
| unknown |
supporttool-shasta-rrs.symantec.com |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
crt.comodoca.com |
| whitelisted |
tool-avpg.crsi.symantec.com |
| unknown |
deepscan.norton.com |
| unknown |