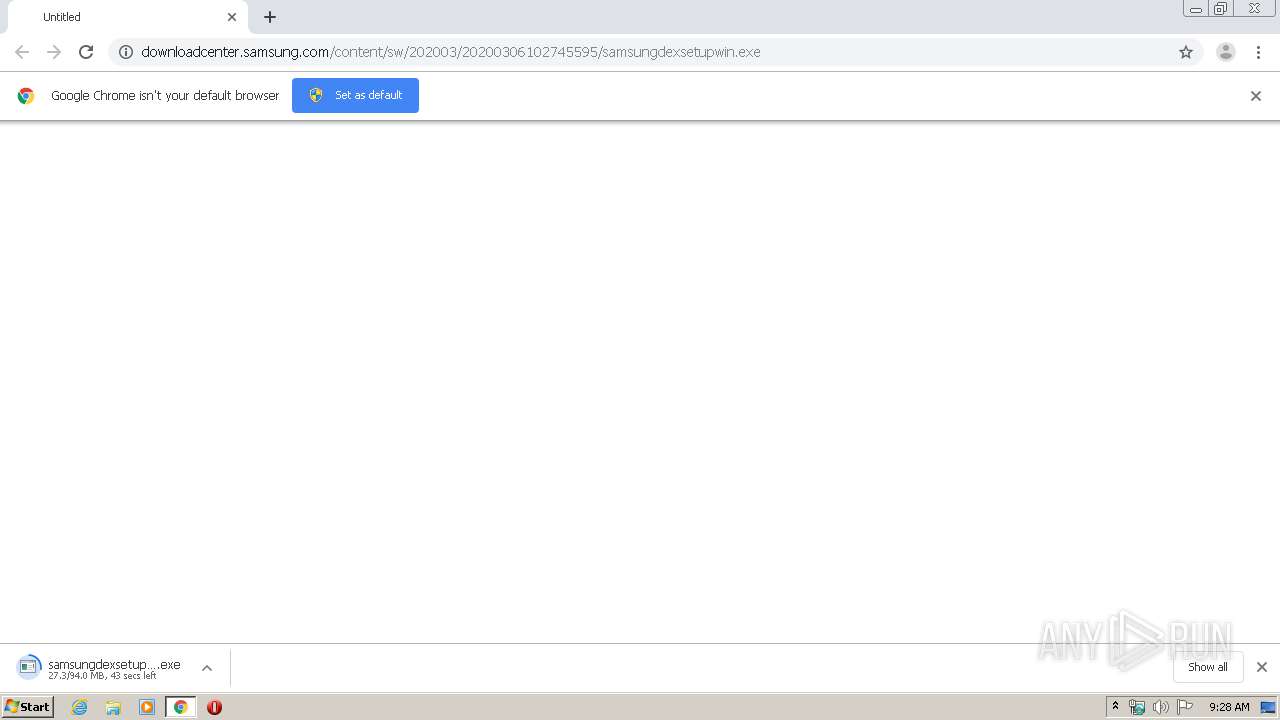
| URL: | http://downloadcenter.samsung.com/content/sw/202003/20200306102745595/samsungdexsetupwin.exe |
| Full analysis: | https://app.any.run/tasks/54e13e9a-b433-499b-97e1-c63ef4b17e80 |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2020, 09:28:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5E32FC69767C3AA2F874614B3B920E1C |
| SHA1: | 935413405339FFC9147076E48BF45188A6A91869 |
| SHA256: | 754FB25E14FC4FCD11BD978EA7999DD49DBEB5E1F63B5D21936B338141F3CC29 |
| SSDEEP: | 3:N1KaKEofXLWEidKL8sVKFX/WUO5UucPQ3du4A:Ca0WdQ9KVWUO/c0a |
MALICIOUS
Application was dropped or rewritten from another process
- samsungdexsetupwin.exe (PID: 3624)
- samsungdexsetupwin.exe (PID: 1084)
- SamsungDeXSetup_1.0.1.40_x86.exe (PID: 2272)
- vcredist_x86_vc2019.exe (PID: 748)
- VC_redist.x86.exe (PID: 3180)
- vcredist_x86_vc2019.exe (PID: 1792)
Changes the autorun value in the registry
- SamsungDeXSetup_1.0.1.40_x86.exe (PID: 2272)
- VC_redist.x86.exe (PID: 3180)
Loads dropped or rewritten executable
- samsungdexsetupwin.exe (PID: 3624)
- vcredist_x86_vc2019.exe (PID: 1792)
Changes settings of System certificates
- msiexec.exe (PID: 1440)
SUSPICIOUS
Executable content was dropped or overwritten
- samsungdexsetupwin.exe (PID: 1084)
- chrome.exe (PID: 2784)
- samsungdexsetupwin.exe (PID: 3624)
- SamsungDeXSetup_1.0.1.40_x86.exe (PID: 2272)
- vcredist_x86_vc2019.exe (PID: 748)
- vcredist_x86_vc2019.exe (PID: 1792)
- msiexec.exe (PID: 1440)
- VC_redist.x86.exe (PID: 3180)
Starts itself from another location
- samsungdexsetupwin.exe (PID: 3624)
- vcredist_x86_vc2019.exe (PID: 1792)
Executed as Windows Service
- vssvc.exe (PID: 2128)
Creates a software uninstall entry
- SamsungDeXSetup_1.0.1.40_x86.exe (PID: 2272)
- VC_redist.x86.exe (PID: 3180)
Creates files in the program directory
- SamsungDeXSetup_1.0.1.40_x86.exe (PID: 2272)
- VC_redist.x86.exe (PID: 3180)
Searches for installed software
- SamsungDeXSetup_1.0.1.40_x86.exe (PID: 2272)
- VC_redist.x86.exe (PID: 3180)
Creates files in the Windows directory
- vcredist_x86_vc2019.exe (PID: 1792)
- vcredist_x86_vc2019.exe (PID: 748)
Adds / modifies Windows certificates
- msiexec.exe (PID: 1440)
INFO
Application launched itself
- chrome.exe (PID: 2784)
Reads settings of System Certificates
- chrome.exe (PID: 2784)
- msiexec.exe (PID: 1440)
Reads the hosts file
- chrome.exe (PID: 2956)
- chrome.exe (PID: 2784)
Reads Internet Cache Settings
- chrome.exe (PID: 2784)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
19
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | "C:\ProgramData\Package Cache\AFA5BADCE64EE67290ADD24E0DC3D8210954AC6C\vcredist_x86_vc2019.exe" /install /quiet /norestart | C:\ProgramData\Package Cache\AFA5BADCE64EE67290ADD24E0DC3D8210954AC6C\vcredist_x86_vc2019.exe | SamsungDeXSetup_1.0.1.40_x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.24.28127 Exit code: 0 Version: 14.24.28127.4 Modules
| |||||||||||||||
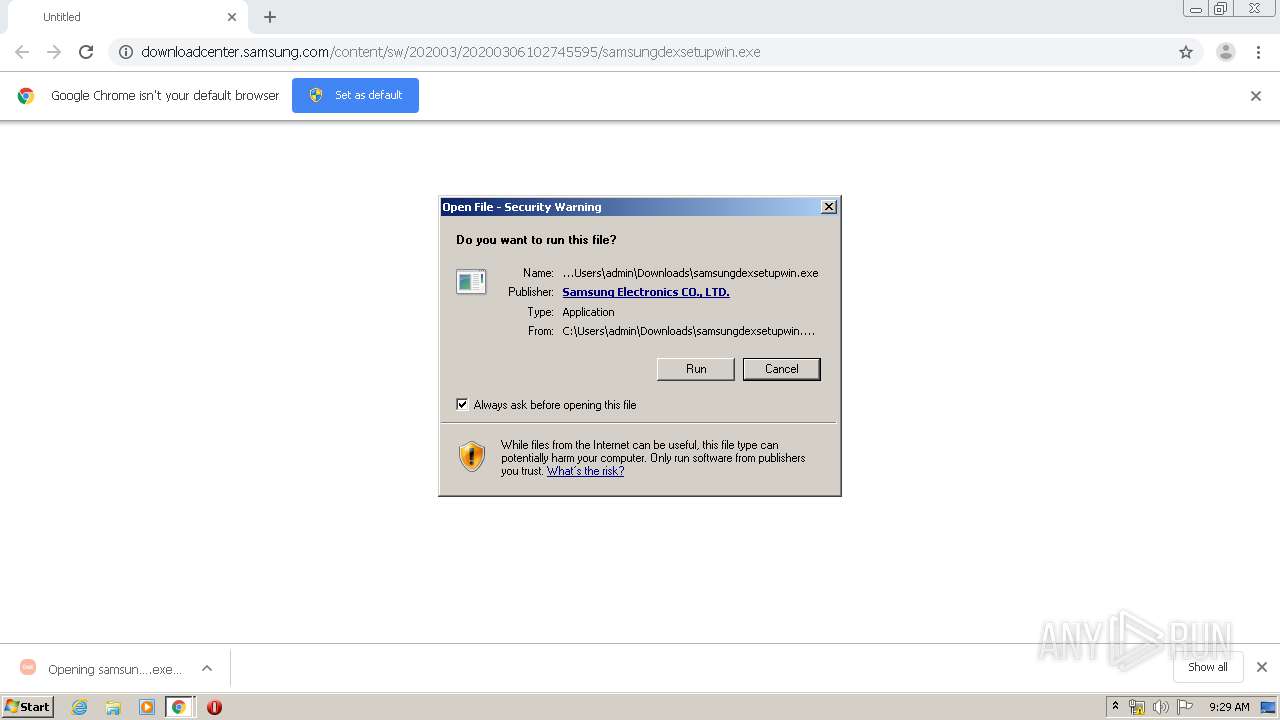
| 1084 | "C:\Users\admin\Downloads\samsungdexsetupwin.exe" | C:\Users\admin\Downloads\samsungdexsetupwin.exe | chrome.exe | ||||||||||||
User: admin Company: Samsung Electronics Co., Ltd. Integrity Level: MEDIUM Description: Samsung DeX Exit code: 0 Version: 1.0.1.40 Modules
| |||||||||||||||
| 1440 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1792 | "C:\Windows\Temp\{558E0B4E-0AEE-4B77-BB6E-AF6BDFE40968}\.cr\vcredist_x86_vc2019.exe" -burn.clean.room="C:\ProgramData\Package Cache\AFA5BADCE64EE67290ADD24E0DC3D8210954AC6C\vcredist_x86_vc2019.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 /install /quiet /norestart | C:\Windows\Temp\{558E0B4E-0AEE-4B77-BB6E-AF6BDFE40968}\.cr\vcredist_x86_vc2019.exe | vcredist_x86_vc2019.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.24.28127 Exit code: 0 Version: 14.24.28127.4 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,14334500486330115458,1680929877215465718,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13118418990114489869 --mojo-platform-channel-handle=3440 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2580 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2128 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | "C:\Users\admin\AppData\Local\Temp\{DF95DFD9-6C43-494E-BA51-AAACE39FB476}\.be\SamsungDeXSetup_1.0.1.40_x86.exe" -q -burn.elevated BurnPipe.{D64D3210-D0AA-4645-BD3D-76132D68D930} {B77E7FDB-6532-49A7-89C7-B0C2A3D0DFEA} 3624 | C:\Users\admin\AppData\Local\Temp\{DF95DFD9-6C43-494E-BA51-AAACE39FB476}\.be\SamsungDeXSetup_1.0.1.40_x86.exe | samsungdexsetupwin.exe | ||||||||||||
User: admin Company: Samsung Electronics Co., Ltd. Integrity Level: HIGH Description: Samsung DeX Exit code: 0 Version: 1.0.1.40 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,14334500486330115458,1680929877215465718,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11236204124139611732 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,14334500486330115458,1680929877215465718,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11897665936003815846 --mojo-platform-channel-handle=3004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 906
Read events
1 698
Write events
1 205
Delete events
3
Modification events
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2784-13228133306006125 |
Value: 259 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
53
Suspicious files
11
Text files
161
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E64BABA-AE0.pma | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6b7da929-633a-46f1-ae8d-dc5d0ad143d9.tmp | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66be1.TMP | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66d49.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
11
DNS requests
7
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2956 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2956 | chrome.exe | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2956 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2956 | chrome.exe | 172.217.18.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
2956 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
2956 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
2956 | chrome.exe | 23.210.248.84:80 | downloadcenter.samsung.com | Akamai International B.V. | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
downloadcenter.samsung.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2956 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
samsungdexsetupwin.exe | Pre-Device Connected : 0, Device Connected : 1, Hubs Connected: 0
|