| download: | pdfforgeExtension.exe |
| Full analysis: | https://app.any.run/tasks/f18fa230-7998-4265-a606-4c0f2cbb507b |
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2020, 20:00:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3B2E52BCEE1538F26F2688CCF3EB5740 |
| SHA1: | 51838F4BE589EFC63EEBB010103EA47EBDBD4BE9 |
| SHA256: | 753CBAE11A881B871E3295D65449954817061DB5DEC53DF7B379FEE9F21C33D1 |
| SSDEEP: | 98304:vnA5OLieju6bZfHHnwEwELln0WmAMaOA71pEmx3hqd/31wL+isCoE:fA50jBfHHnwETnyA35RpEM01whN |
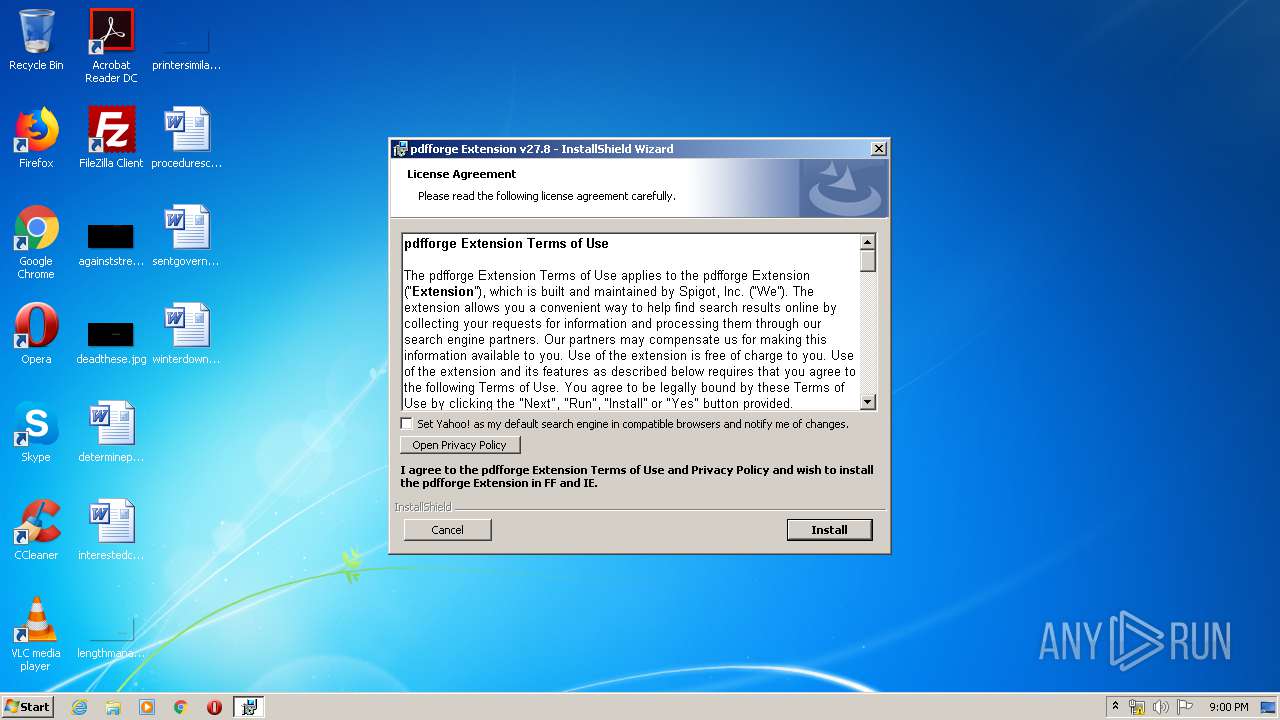
MALICIOUS
Actions looks like stealing of personal data
- MsiExec.exe (PID: 3704)
- PreferencesManager.exe (PID: 3156)
Application was dropped or rewritten from another process
- ApplicationUpdater.exe (PID: 2564)
- PreferencesManager.exe (PID: 3156)
Loads dropped or rewritten executable
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 2684)
- svchost.exe (PID: 864)
SUSPICIOUS
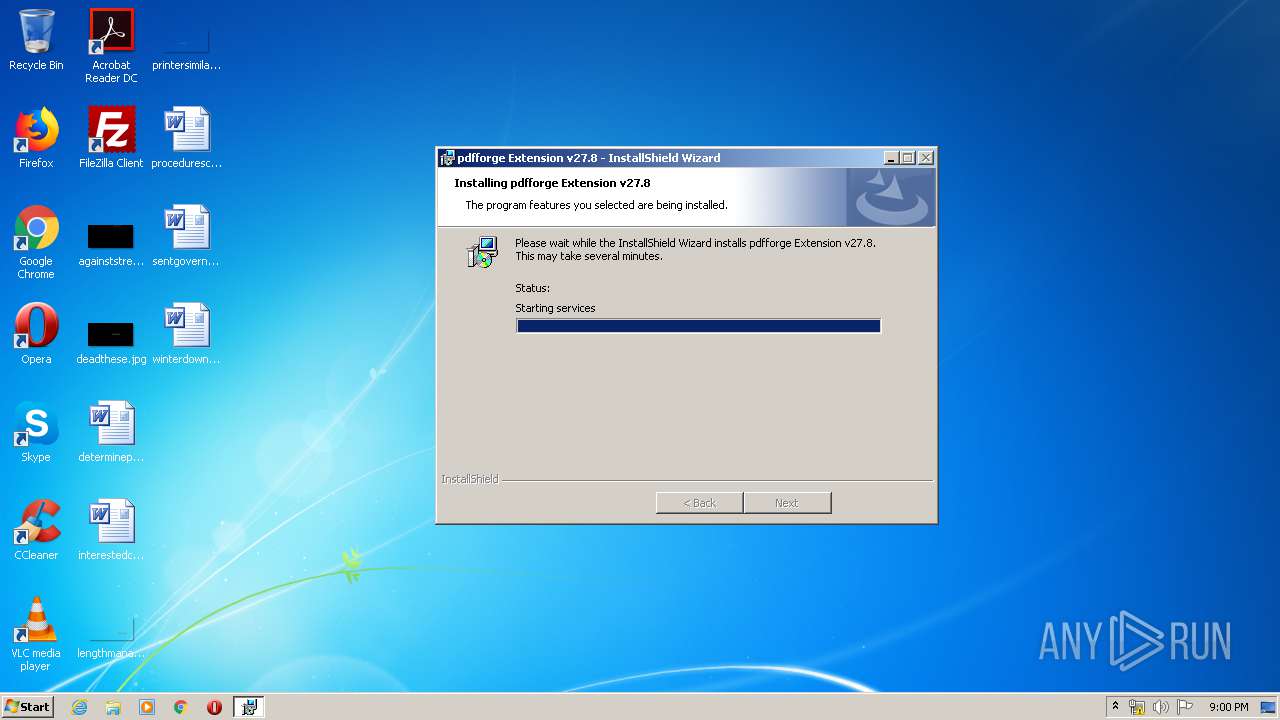
Executed as Windows Service
- ApplicationUpdater.exe (PID: 2564)
Reads Internet Cache Settings
- MsiExec.exe (PID: 3704)
- PreferencesManager.exe (PID: 3156)
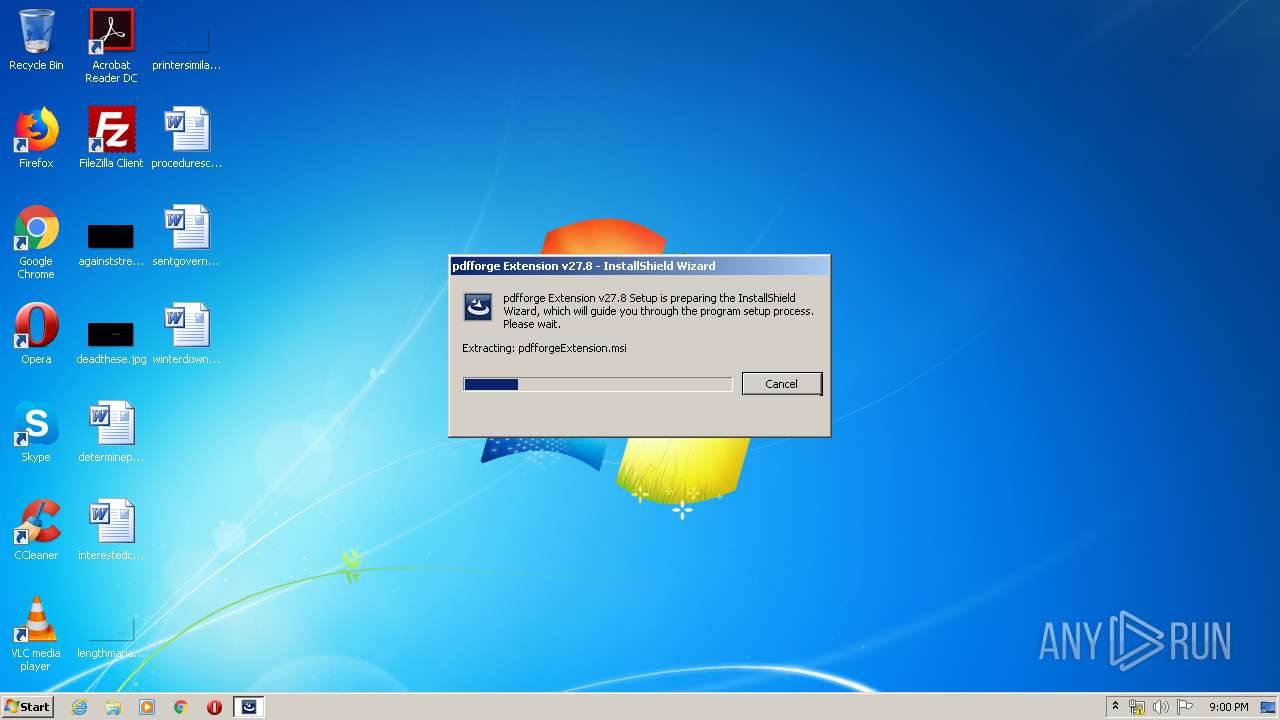
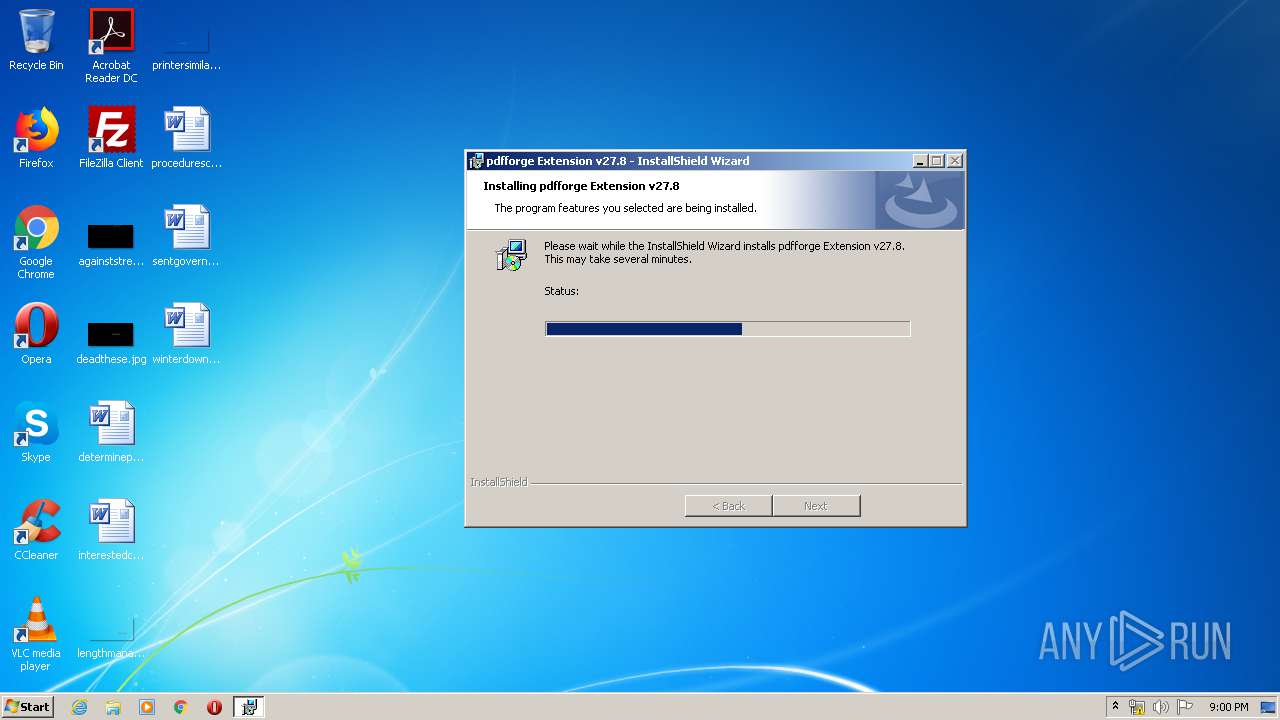
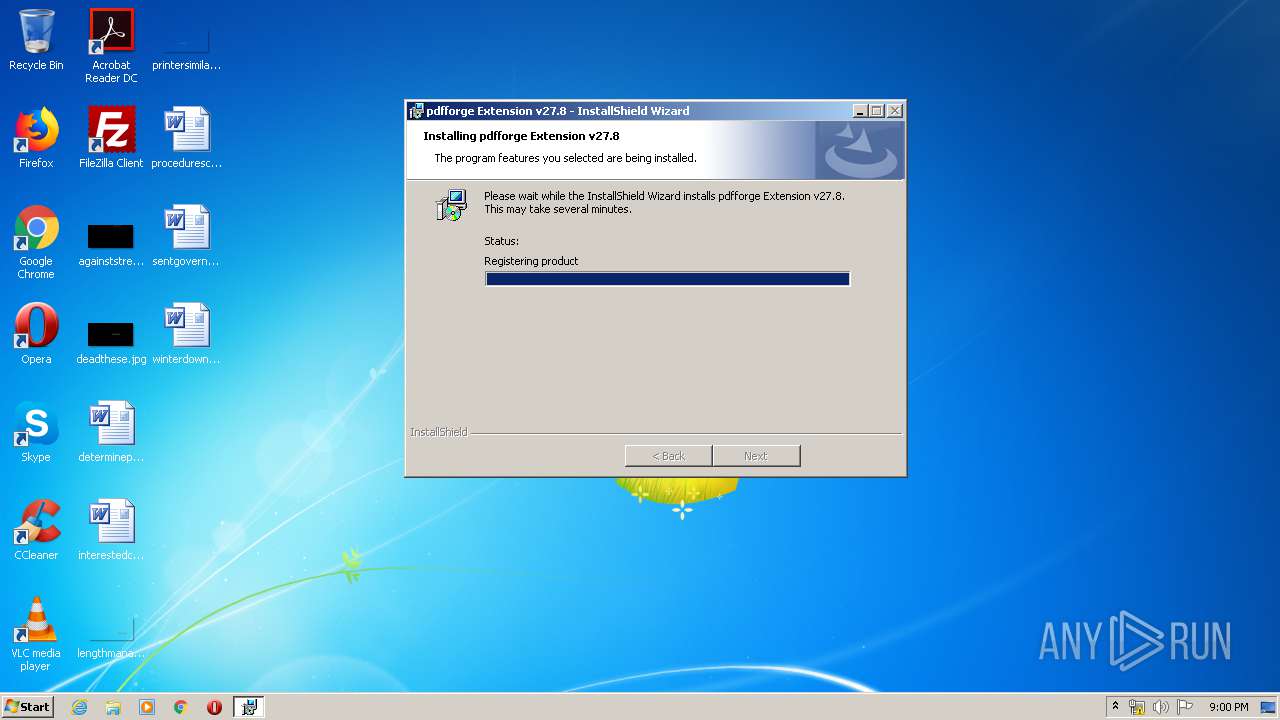
Starts Microsoft Installer
- pdfforgeExtension.exe (PID: 1188)
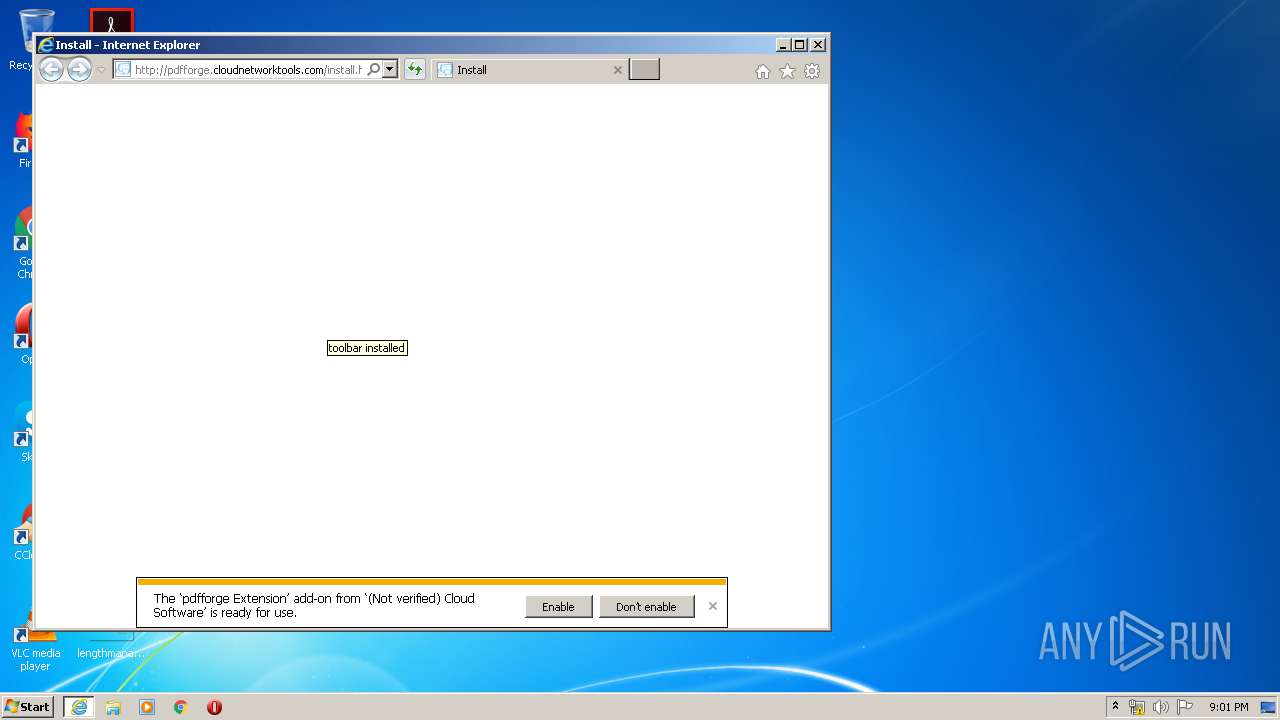
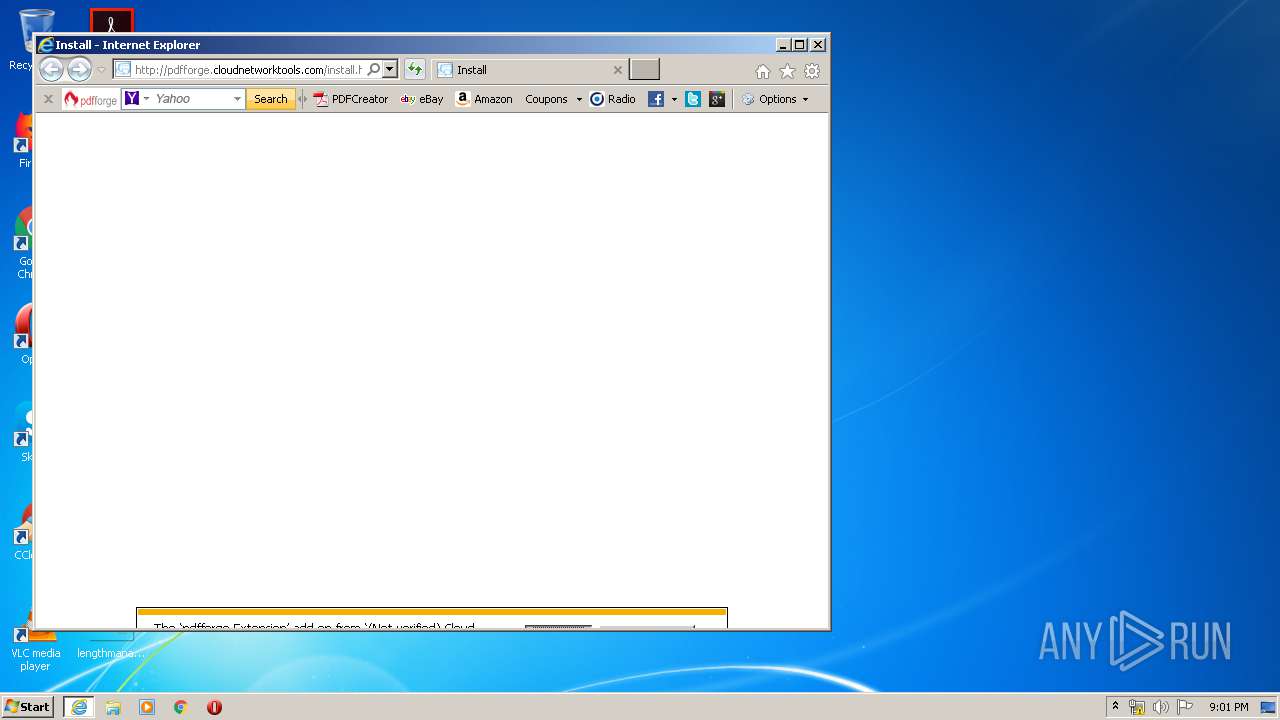
Starts Internet Explorer
- MsiExec.exe (PID: 1160)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3704)
- MsiExec.exe (PID: 2296)
- MsiExec.exe (PID: 1160)
Reads Internet Cache Settings
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 2684)
Changes internet zones settings
- iexplore.exe (PID: 2244)
Reads internet explorer settings
- iexplore.exe (PID: 2684)
Reads settings of System Certificates
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 2684)
Creates files in the user directory
- iexplore.exe (PID: 2684)
Changes settings of System certificates
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 2244)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 2684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:04:25 03:16:12+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 713728 |
| InitializedDataSize: | 498176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6aabb |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 27.8.0.0 |
| ProductVersionNumber: | 27.8.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | CloudSoftware |
| FileDescription: | Setup Launcher Unicode |
| FileVersion: | 27.8 |
| InternalName: | Setup |
| LegalCopyright: | Copyright © 2005-2017 CloudSoftware |
| OriginalFileName: | InstallShield Setup.exe |
| ProductName: | pdfforge Extension v27.8 |
| ProductVersion: | 27.8 |
| InternalBuildNumber: | 115289 |
| ISInternalVersion: | 19.0.160 |
| ISInternalDescription: | Setup Launcher Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Apr-2012 01:16:12 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | CloudSoftware |
| FileDescription: | Setup Launcher Unicode |
| FileVersion: | 27.8 |
| InternalName: | Setup |
| LegalCopyright: | Copyright © 2005-2017 CloudSoftware |
| OriginalFilename: | InstallShield Setup.exe |
| ProductName: | pdfforge Extension v27.8 |
| ProductVersion: | 27.8 |
| Internal Build Number: | 115289 |
| ISInternalVersion: | 19.0.160 |
| ISInternalDescription: | Setup Launcher Unicode |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 25-Apr-2012 01:16:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000AE20D | 0x000AE400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58831 |
.rdata | 0x000B0000 | 0x000291E0 | 0x00029200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.91329 |
.data | 0x000DA000 | 0x00008828 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.54163 |
.rsrc | 0x000E3000 | 0x0004DF10 | 0x0004E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.57484 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22609 | 1210 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.835 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.35696 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 6.14965 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 6.18448 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.85842 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.57777 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.81004 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 6.06596 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 3.22977 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
msi.dll (delay-loaded) |
Total processes
50
Monitored processes
11
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1160 | C:\Windows\system32\MsiExec.exe -Embedding D971A796DE38BB52328581A4DFDCC4C4 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1188 | "C:\Users\admin\AppData\Local\Temp\pdfforgeExtension.exe" | C:\Users\admin\AppData\Local\Temp\pdfforgeExtension.exe | explorer.exe | ||||||||||||
User: admin Company: CloudSoftware Integrity Level: HIGH Description: Setup Launcher Unicode Exit code: 0 Version: 27.8 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Internet Explorer\iexplore.exe" http://pdfforge.cloudnetworktools.com/install.html?cnid=589518&isn=2C504ED957A74D2E915796AFCA16C75F&code_ver=278&type=install&cid=90059c37132041a4b58d2b75a9850d2f | C:\Program Files\Internet Explorer\iexplore.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2256 | MSIEXEC.EXE /i "C:\Users\admin\AppData\Local\Temp\{C46B43A0-EEE9-4531-A829-32441B965D68}\pdfforgeExtension.msi" TRANSFORMS="C:\Users\admin\AppData\Local\Temp\{C46B43A0-EEE9-4531-A829-32441B965D68}\1033.MST" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp" SETUPEXENAME="pdfforgeExtension.exe" | C:\Windows\system32\MSIEXEC.EXE | — | pdfforgeExtension.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | C:\Windows\system32\MsiExec.exe -Embedding 9E2798A8F413D7A529475CCD79430317 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Application Updater\ApplicationUpdater.exe" | C:\Program Files\Application Updater\ApplicationUpdater.exe | services.exe | ||||||||||||
User: SYSTEM Company: CloudSoftware Integrity Level: SYSTEM Description: Application Updater Exit code: 0 Version: 27, 8, 0, 3 Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2244 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2760 | "C:\Users\admin\AppData\Local\Temp\pdfforgeExtension.exe" | C:\Users\admin\AppData\Local\Temp\pdfforgeExtension.exe | — | explorer.exe | |||||||||||
User: admin Company: CloudSoftware Integrity Level: MEDIUM Description: Setup Launcher Unicode Exit code: 3221226540 Version: 27.8 Modules
| |||||||||||||||
| 3156 | "C:\Program Files\Common Files\Spigot\Preferences Manager\PreferencesManager.exe" /reset 0 DFROMKIT | C:\Program Files\Common Files\Spigot\Preferences Manager\PreferencesManager.exe | msiexec.exe | ||||||||||||
User: admin Company: CloudSoftware Integrity Level: HIGH Description: Preferences Manager Exit code: 0 Version: 27, 8, 0, 3 Modules
| |||||||||||||||
Total events
2 901
Read events
952
Write events
1 941
Delete events
8
Modification events
| (PID) Process: | (864) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000680F607E6134D60160030000C40E0000E8030000010000000500000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (864) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000D098697E6134D60160030000C40E0000E8030000000000000500000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (864) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | PREPAREBACKUP (Enter) |
Value: 4000000000000000681D87856134D60160030000C40E0000E90300000100000005000000000000009B8C83DCFD2DC54BBABB51818CA3D59B0000000000000000 | |||
| (PID) Process: | (864) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | PREPAREBACKUP (Leave) |
Value: 40000000000000002A0993856134D60160030000C40E0000E90300000000000001000000000000009B8C83DCFD2DC54BBABB51818CA3D59B0000000000000000 | |||
| (PID) Process: | (864) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | VSS_WS_STABLE (SetCurrentState) |
Value: 40000000000000002A0993856134D60160030000C40E0000010000000100000001000000000000009B8C83DCFD2DC54BBABB51818CA3D59B0000000000000000 | |||
| (PID) Process: | (864) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | GETSTATE (Enter) |
Value: 400000000000000062A5AF856134D60160030000F00E0000F90300000100000001000000000000009B8C83DCFD2DC54BBABB51818CA3D59B0000000000000000 | |||
| (PID) Process: | (864) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | GETSTATE (Leave) |
Value: 4000000000000000BC07B2856134D60160030000F00E0000F90300000000000001000000000000009B8C83DCFD2DC54BBABB51818CA3D59B0000000000000000 | |||
| (PID) Process: | (864) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | PREPARESNAPSHOT (Enter) |
Value: 400000000000000010F2DC856134D60160030000F00E0000EA0300000100000001000000000000009B8C83DCFD2DC54BBABB51818CA3D59B0000000000000000 | |||
| (PID) Process: | (864) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | PREPARESNAPSHOT (Leave) |
Value: 4000000000000000F6DA26866134D60160030000F00E0000EA0300000000000001000000000000009B8C83DCFD2DC54BBABB51818CA3D59B0000000000000000 | |||
| (PID) Process: | (864) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | VSS_WS_WAITING_FOR_FREEZE (SetCurrentState) |
Value: 4000000000000000F6DA26866134D60160030000F00E0000020000000100000001000000000000009B8C83DCFD2DC54BBABB51818CA3D59B0000000000000000 | |||
Executable files
0
Suspicious files
10
Text files
36
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1188 | pdfforgeExtension.exe | C:\Users\admin\AppData\Local\Temp\~B3F6.tmp | — | |
MD5:— | SHA256:— | |||
| 1188 | pdfforgeExtension.exe | C:\Users\admin\AppData\Local\Temp\~B407.tmp | — | |
MD5:— | SHA256:— | |||
| 1188 | pdfforgeExtension.exe | C:\Users\admin\AppData\Local\Temp\{C46B43A0-EEE9-4531-A829-32441B965D68}\pdfforgeExtension.msi | — | |
MD5:— | SHA256:— | |||
| 2256 | MSIEXEC.EXE | C:\Users\admin\AppData\Local\Temp\MSIC934.tmp | — | |
MD5:— | SHA256:— | |||
| 2256 | MSIEXEC.EXE | C:\Users\admin\AppData\Local\Temp\MSIC9B2.tmp | — | |
MD5:— | SHA256:— | |||
| 2256 | MSIEXEC.EXE | C:\Users\admin\AppData\Local\Temp\MSIC9D2.tmp | — | |
MD5:— | SHA256:— | |||
| 2256 | MSIEXEC.EXE | C:\Users\admin\AppData\Local\Temp\MSIC9E3.tmp | — | |
MD5:— | SHA256:— | |||
| 3156 | PreferencesManager.exe | C:\Users\admin\AppData\Local\Temp\{358A642C-E634-473E-AC7C-2FD26E7FBBAA}\META-INF\mozilla.rsa | — | |
MD5:— | SHA256:— | |||
| 3156 | PreferencesManager.exe | C:\Users\admin\AppData\Local\Temp\{358A642C-E634-473E-AC7C-2FD26E7FBBAA}\privileged\multipreffer\api.js | — | |
MD5:— | SHA256:— | |||
| 3156 | PreferencesManager.exe | C:\Users\admin\AppData\Local\Temp\{358A642C-E634-473E-AC7C-2FD26E7FBBAA}\privileged\study\schema.json | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
21
DNS requests
8
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2684 | iexplore.exe | GET | — | 158.85.63.185:80 | http://pdfforge.cloudnetworktools.com/image/1/1/pdfforge/1231869545/pdfc_portal_logo.gif | US | — | — | malicious |
2684 | iexplore.exe | GET | — | 158.85.63.185:80 | http://pdfforge.cloudnetworktools.com/favicon.ico | US | — | — | malicious |
3156 | PreferencesManager.exe | POST | — | 158.85.63.185:80 | http://api.cloudnetworktools.com/cgi/api.cgi/589518/2C504ED957A74D2E915796AFCA16C75F/ping/10/73/ | US | — | — | malicious |
2684 | iexplore.exe | GET | 200 | 158.85.63.185:80 | http://pdfforge.cloudnetworktools.com/image/1/2/pdfforge/1261096968/pdfc_portal_tb.gif | US | image | 14.2 Kb | malicious |
2684 | iexplore.exe | GET | 302 | 158.85.63.185:80 | http://pdfforge.cloudnetworktools.com/install.html?cnid=589518&isn=2C504ED957A74D2E915796AFCA16C75F&code_ver=278&type=install&cid=90059c37132041a4b58d2b75a9850d2f | US | html | 371 b | malicious |
3156 | PreferencesManager.exe | POST | 200 | 158.85.63.185:80 | http://api.cloudnetworktools.com/cgi/api.cgi/589518/2C504ED957A74D2E915796AFCA16C75F/vloc/10 | US | text | 1.08 Kb | malicious |
2564 | ApplicationUpdater.exe | POST | 200 | 158.85.63.185:80 | http://www.cloudnetworktools.com/cgi/api.cgi/589518/2C504ED957A74D2E915796AFCA16C75F/vaus/14/ | US | text | 58 b | malicious |
2684 | iexplore.exe | POST | 200 | 158.85.63.185:80 | http://pdfforge.cloudnetworktools.com/cgi/api.cgi/589518/2C504ED957A74D2E915796AFCA16C75F/vloc/1 | US | text | 1.08 Kb | malicious |
2684 | iexplore.exe | GET | 200 | 158.85.63.185:80 | http://pdfforge.cloudnetworktools.com/install.html?rt=1&cnid=589518&isn=2C504ED957A74D2E915796AFCA16C75F&code_ver=278&type=install&cid=90059c37132041a4b58d2b75a9850d2f | US | html | 3.08 Kb | malicious |
2564 | ApplicationUpdater.exe | POST | 200 | 158.85.63.185:80 | http://www.cloudnetworktools.com/cgi/api.cgi/589518/2C504ED957A74D2E915796AFCA16C75F/ping/14/73/ | US | text | 58 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 158.85.63.185:80 | pdfforge.cloudnetworktools.com | SoftLayer Technologies Inc. | US | malicious |
2684 | iexplore.exe | 158.85.63.185:80 | pdfforge.cloudnetworktools.com | SoftLayer Technologies Inc. | US | malicious |
2564 | ApplicationUpdater.exe | 158.85.63.185:80 | pdfforge.cloudnetworktools.com | SoftLayer Technologies Inc. | US | malicious |
2684 | iexplore.exe | 172.217.22.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2684 | iexplore.exe | 172.217.18.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2244 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3704 | MsiExec.exe | 158.85.63.185:80 | pdfforge.cloudnetworktools.com | SoftLayer Technologies Inc. | US | malicious |
3156 | PreferencesManager.exe | 158.85.63.185:80 | pdfforge.cloudnetworktools.com | SoftLayer Technologies Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pdfforge.cloudnetworktools.com |
| malicious |
api.cloudnetworktools.com |
| malicious |
www.cloudnetworktools.com |
| malicious |
www.google-analytics.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3704 | MsiExec.exe | A Network Trojan was detected | ET MALWARE W32/Toolbar.WIDGI User-Agent (WidgiToolbar-) |
3704 | MsiExec.exe | A Network Trojan was detected | MALWARE [PTsecurity] WebToolbar.Win32.Spigot.gen HTTP POST |
3156 | PreferencesManager.exe | A Network Trojan was detected | ET MALWARE W32/Toolbar.WIDGI User-Agent (WidgiToolbar-) |
3156 | PreferencesManager.exe | A Network Trojan was detected | MALWARE [PTsecurity] WebToolbar.Win32.Spigot.gen HTTP POST |
3156 | PreferencesManager.exe | A Network Trojan was detected | ET MALWARE W32/Toolbar.WIDGI User-Agent (WidgiToolbar-) |
3156 | PreferencesManager.exe | A Network Trojan was detected | MALWARE [PTsecurity] WebToolbar.Win32.Spigot.gen HTTP POST |
2564 | ApplicationUpdater.exe | A Network Trojan was detected | ET MALWARE W32/Toolbar.WIDGI User-Agent (WidgiToolbar-) |
2564 | ApplicationUpdater.exe | A Network Trojan was detected | MALWARE [PTsecurity] WebToolbar.Win32.Spigot.gen HTTP POST |
2564 | ApplicationUpdater.exe | A Network Trojan was detected | ET MALWARE W32/Toolbar.WIDGI User-Agent (WidgiToolbar-) |
2564 | ApplicationUpdater.exe | A Network Trojan was detected | MALWARE [PTsecurity] WebToolbar.Win32.Spigot.gen HTTP POST |
7 ETPRO signatures available at the full report