| File name: | 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee |
| Full analysis: | https://app.any.run/tasks/6c905947-14c5-46de-9968-99ce0f75353c |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 16:09:43 |
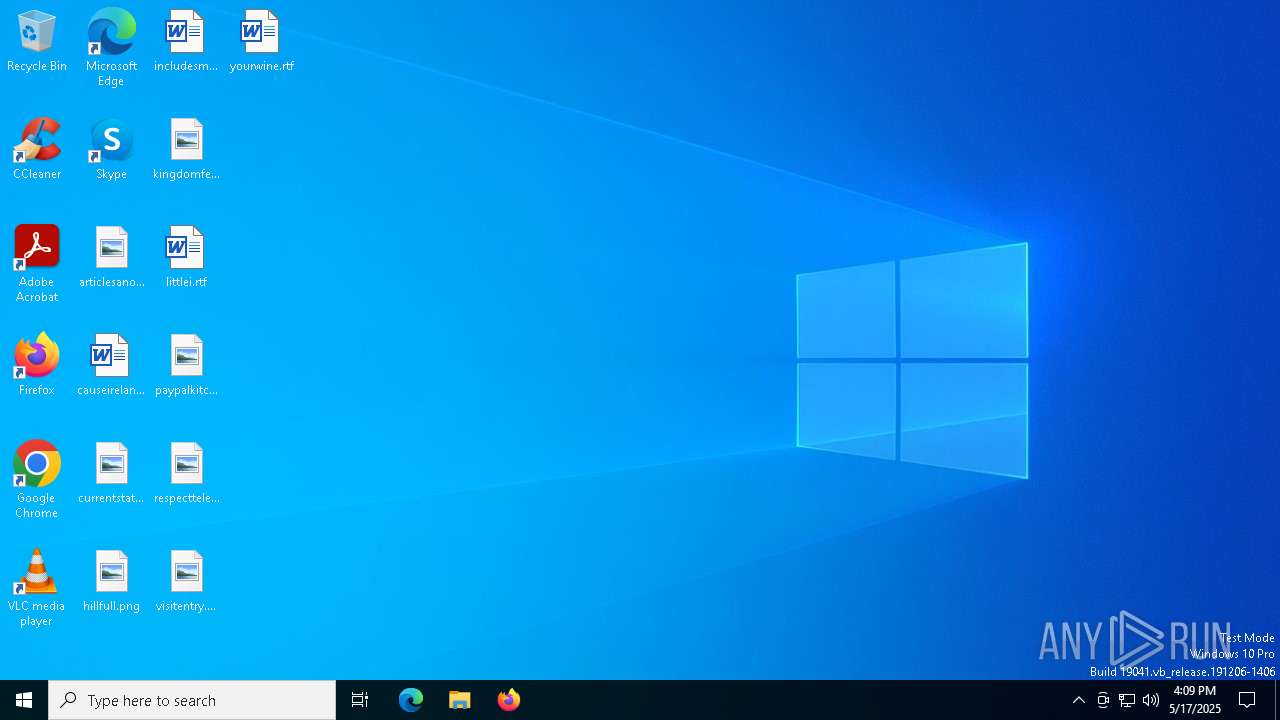
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 4BF7B176EA685BC7DC8D791FA3EA2536 |
| SHA1: | 23E98604FED95306635A290C485EEEA3E4F659A5 |
| SHA256: | 752A8C947C96E2067E4BFE6EC163668EBF61AFA59C8A0400C8B6E03F53D4230E |
| SSDEEP: | 98304:1gV1JooL6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6E6n:1 |
MALICIOUS
Changes the autorun value in the registry
- 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe (PID: 7560)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe (PID: 7560)
Reads security settings of Internet Explorer
- 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe (PID: 7560)
Executes application which crashes
- 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe (PID: 7560)
- zgxopshw.exe (PID: 7728)
- zgxopshw.exe (PID: 7964)
Detected use of alternative data streams (AltDS)
- svchost.exe (PID: 7808)
- svchost.exe (PID: 7984)
INFO
Reads the computer name
- 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe (PID: 7560)
- zgxopshw.exe (PID: 7728)
- zgxopshw.exe (PID: 7964)
Create files in a temporary directory
- 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe (PID: 7560)
Process checks computer location settings
- 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe (PID: 7560)
Checks supported languages
- zgxopshw.exe (PID: 7728)
- 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe (PID: 7560)
- zgxopshw.exe (PID: 7964)
Auto-launch of the file from Registry key
- 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe (PID: 7560)
Manual execution by a user
- zgxopshw.exe (PID: 7964)
Checks proxy server information
- slui.exe (PID: 6108)
Reads the software policy settings
- slui.exe (PID: 6108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:01:11 10:20:13+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 140800 |
| InitializedDataSize: | 34230272 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14e9c |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 90.0.0.0 |
| ProductVersionNumber: | 24.0.0.0 |
| FileFlagsMask: | 0x790c |
| FileFlags: | (none) |
| FileOS: | Unknown (0x60484) |
| ObjectFileType: | Unknown (53) |
| FileSubtype: | - |
Total processes
139
Monitored processes
11
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6108 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7560 | "C:\Users\admin\Desktop\2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe" | C:\Users\admin\Desktop\2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 7608 | "C:\Windows\System32\wusa.exe" | C:\Windows\SysWOW64\wusa.exe | — | 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7704 | "C:\WINDOWS\SysWOW64\wusa.exe" | C:\Windows\SysWOW64\wusa.exe | 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7728 | "C:\Users\admin\zgxopshw.exe" /d"C:\Users\admin\Desktop\2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe" /e5E0D02100000007F | C:\Users\admin\zgxopshw.exe | 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 7808 | svchost.exe | C:\Windows\SysWOW64\svchost.exe | — | zgxopshw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 3221225501 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7856 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7560 -s 1300 | C:\Windows\SysWOW64\WerFault.exe | — | 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7876 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7728 -s 568 | C:\Windows\SysWOW64\WerFault.exe | — | zgxopshw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7964 | "C:\Users\admin\zgxopshw.exe" | C:\Users\admin\zgxopshw.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 7984 | svchost.exe | C:\Windows\SysWOW64\svchost.exe | — | zgxopshw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 3221225501 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 250
Read events
5 245
Write events
3
Delete events
2
Modification events
| (PID) Process: | (7560) 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | nvalhmzh |
Value: "C:\Users\admin\zgxopshw.exe" | |||
| (PID) Process: | (7808) svchost.exe | Key: | HKEY_CURRENT_USER\Control Panel\Buses |
| Operation: | write | Name: | Config0 |
Value: 008D703E5358363D24EDB47D450DD49D084297DCE82E72BAA491EBFFE422031DADC43DBDDCCC945D24EDB47D470DD49D024195DAF71261ADC06D04FDA6E22673BBC9154961CDA56B16DC864B733AEDA4644490BDB67D20E8975F02CFF6BD54758DF21D5904FCA26D14DD87447139E69D084295D9E13F4BB4C06D05CEC4E82C7E81DD00626DA3F23224E7C2183630EDA9444995C9E1705EBCCA4D05CEE4BF642CDC8D450F3EFDAC6717DFBE1E796EE4AD541DC48CE06D75E0945E04CEF3BE6758C4DB150042FDAC6C62DB81487138E1A85118CCFFA43871BB995D07CDF7BB612CD5A72B5C7CF0A46D14DD844D743CDDC20655C98DB47D24ED945D04F49BEE2C20D49F307B42FFD11F2DB2D005793DE6D9226BC6FBB7444BAECD5004CF80CB1229D7957D6260A4A96D16A9F23B764BE7943B4F8480B47F509BE25900C9CDD2276DD99D4679428BA61F1CE7C6183030E4AE541ECC8CB57D1DAD955004CEF4B9642FD2997D4D36F0A46D14DD844D743DDDED5710C48DB47D24ED945D3D8DF0B0642FA0EB3209328E9E2F4199894D773DE7DC5018B2B4F47C29ED975D07C485BB1614949F490D37FDA76465DBF674343EE9AD566BB5FFB47D24D4D45909CDF6BD662DD69D463776A8E06013DB8C4F024E97A46D5DC580B47F529CE65D04CDCDFD6620D39B4C0F428ED66D2D9D8740743DE4AD541DC4848D3D20E0935A01CBF3CE6158EEDD185A77F79E5D | |||
| (PID) Process: | (7808) svchost.exe | Key: | HKEY_CURRENT_USER\Control Panel\Buses |
| Operation: | delete value | Name: | Config1 |
Value: | |||
| (PID) Process: | (7984) svchost.exe | Key: | HKEY_CURRENT_USER\Control Panel\Buses |
| Operation: | write | Name: | Config0 |
Value: 008D443F5358363D24EDB47D450DD49D084297DCE82E72BAA491EBFFE422031D135574C2DCCC945D24EDB47D470DD49D024195DAF71261ADC06D04FDA6E22673BBC9154961CDA56B16DC864B733AEDA4644490BDB67D20E8975F02CFF6BD54758DF21D5904FCA26D14DD87447139E69D084295D9E13F4BB4C06D05CEC4E82C7E81DD00626DA3F23224E7C2183630EDA9444995C9E1705EBCCA4D05CEE4BF642CDC8D450F3EFDAC6717DFBE1E796EE4AD541DC48CE06D75E0945F06BBF3BE6758C4DB150042FDAC6C62DB81487138E1A85118CCFFA43871BB995D06CF82BB612CD5A72B5C7CF0A46D14DD844D743CDDC20655C98DB47D24ED945D04F49BEE2C20D49F467942FED71B2DB2D005793DE6AF206BC7F9B3444BAECD5004CFF6C91228D5EE7D6260A4A96D16DFF03B7749E3943B4F8480B47F2699E25806C5CDD2276DD99D460F408BA76467E7C6183030E4AF566BCC8CB57D1DAD955004CFF7BD642FD2997D4D36F0A46D14DD844D743DDDED5710C48DB47D24ED945D3D8DF0B0642FD6E9320831FD9E2F4199894D763F92DC5018B2B4F47C29ED965F72C485BB1614949F490D36FFD26465DBF674343EE9AD5618C385B47D24D4D45909CDF6BD662DD69D463776A8E06013DB8C4F024E97A46D5DC580B47F21EA9C5D04CDCDFD6620D39B4C0F428ED66D2D9D8740743FE6D92269CC858D3D20E0935A01CBF3CE6158EEDD185A77F79E5D | |||
| (PID) Process: | (7984) svchost.exe | Key: | HKEY_CURRENT_USER\Control Panel\Buses |
| Operation: | delete value | Name: | Config1 |
Value: | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7560 | 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe | C:\Users\admin\AppData\Local\Temp\zlndpgvs.exe | executable | |
MD5:532B599E8FBC51E33E10F720D447442D | SHA256:0BBC54E974098E26E06ED8CA551B64960B0792279F24B31A81AF014EB10B98E9 | |||
| 7560 | 2025-05-17_4bf7b176ea685bc7dc8d791fa3ea2536_amadey_elex_gcleaner_rhadamanthys_smoke-loader_tofsee.exe | C:\Users\admin\zgxopshw.exe | executable | |
MD5:2BBF5C948287FD8F1778157C9D890AEA | SHA256:D5F84D0148E900FE5445A38CC6BDBCF5BF657DE9B84A85E76A3E7EAE5C486396 | |||
| 7808 | svchost.exe | C:\Users\admin:.repos | binary | |
MD5:B6C2CA2A23729961449EAC286C88C8F5 | SHA256:01F7A9E3843972783C340CDABAA7295BB87422BAF6885ADD667C8BDC5CF0DB75 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
41
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4784 | RUXIMICS.exe | GET | 200 | 23.216.77.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4784 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8168 | SIHClient.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
8168 | SIHClient.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
8168 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
8168 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8168 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
8168 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
8168 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4784 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4784 | RUXIMICS.exe | 23.216.77.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4784 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
8168 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8168 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
login.live.com |
| whitelisted |