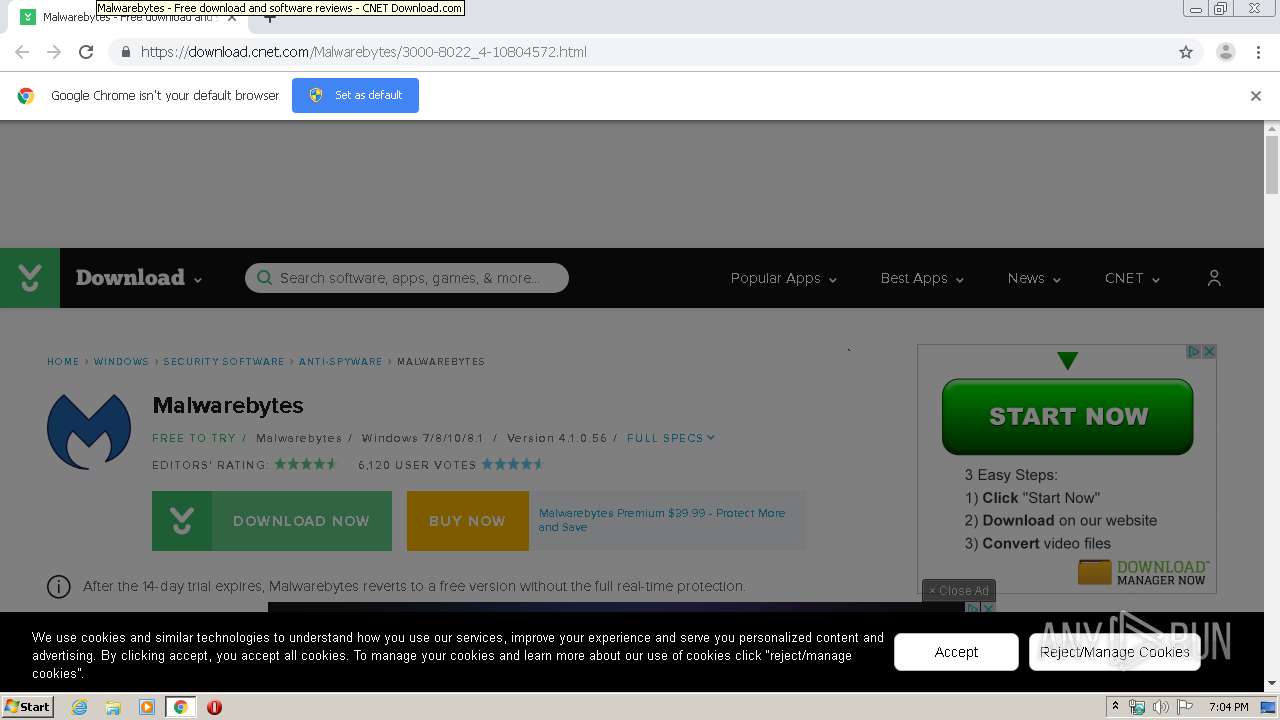
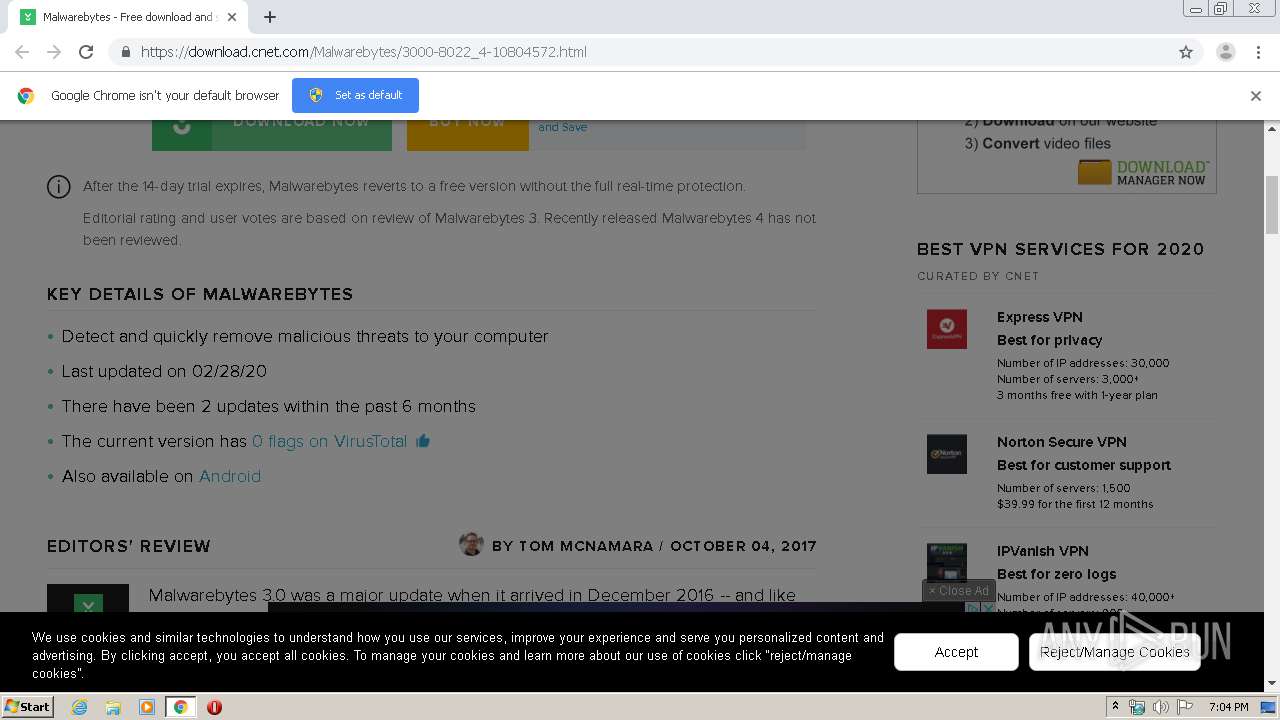
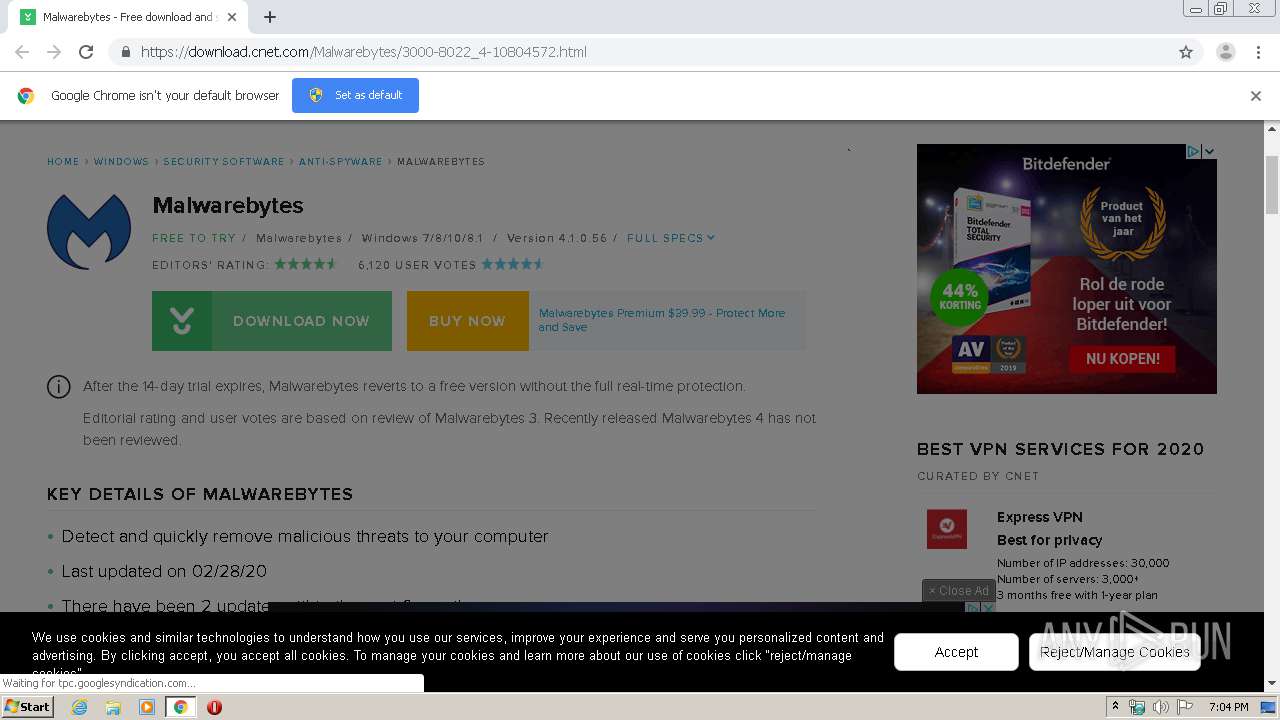
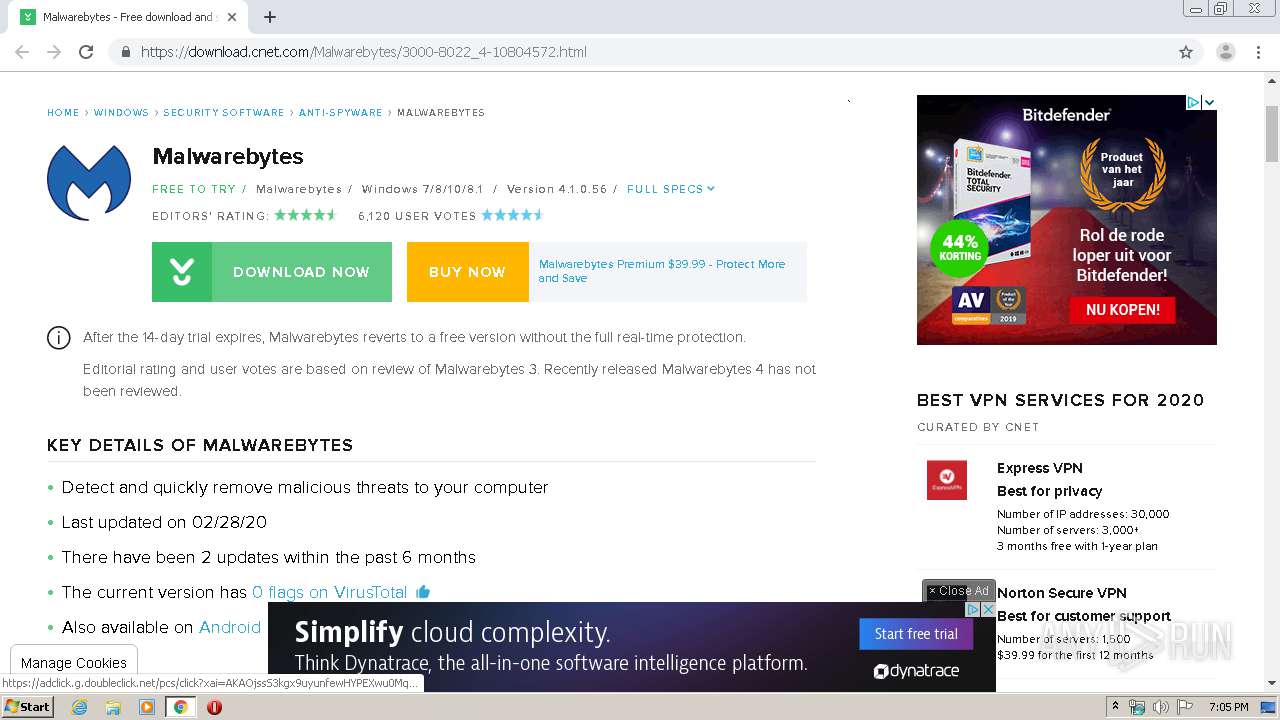
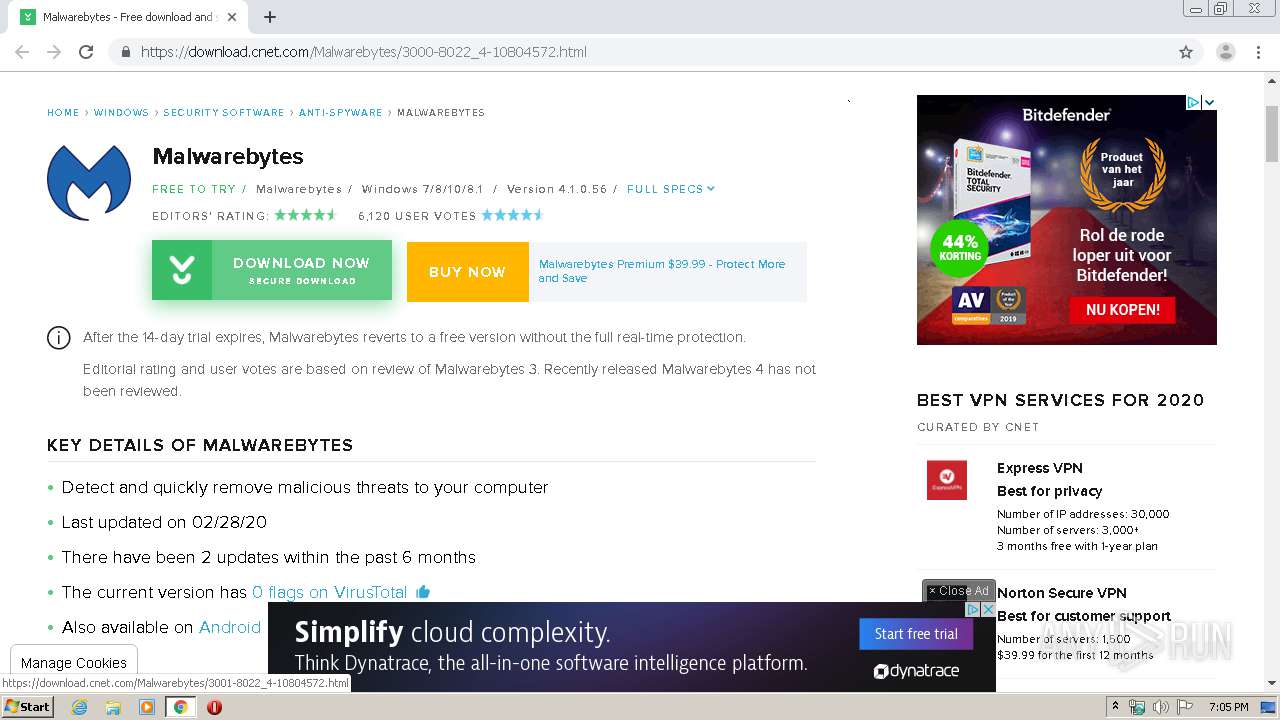
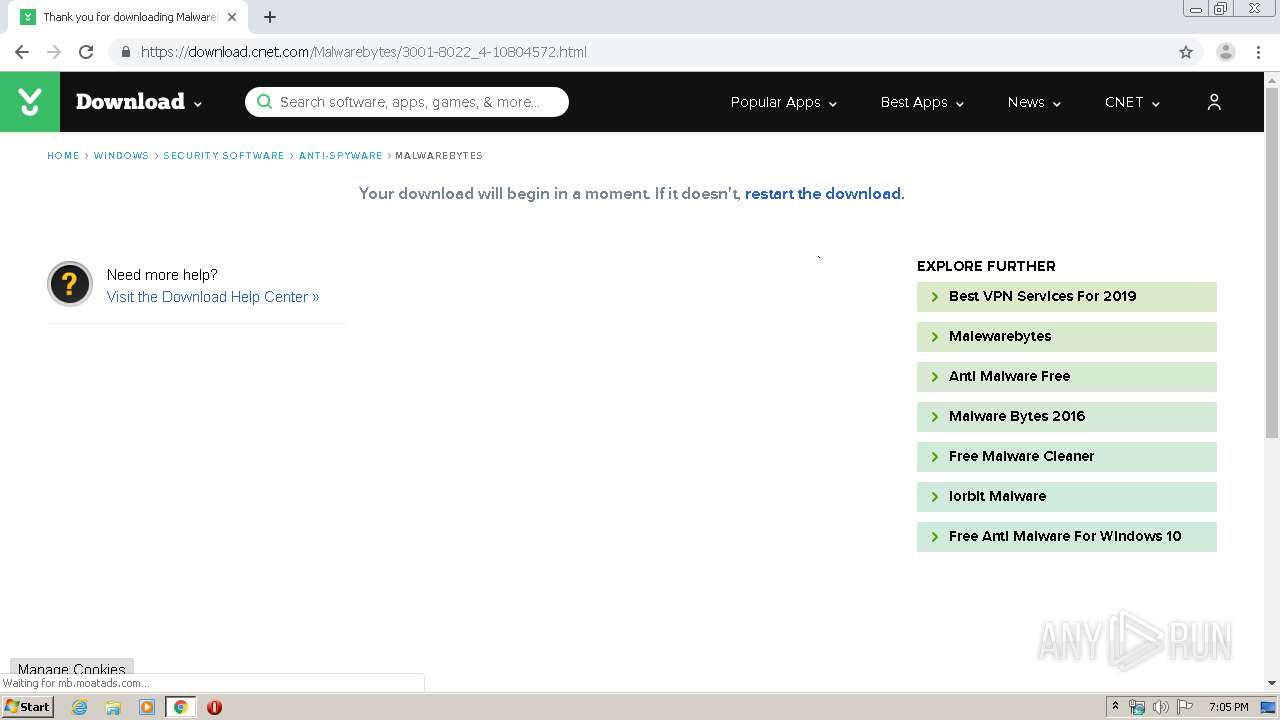
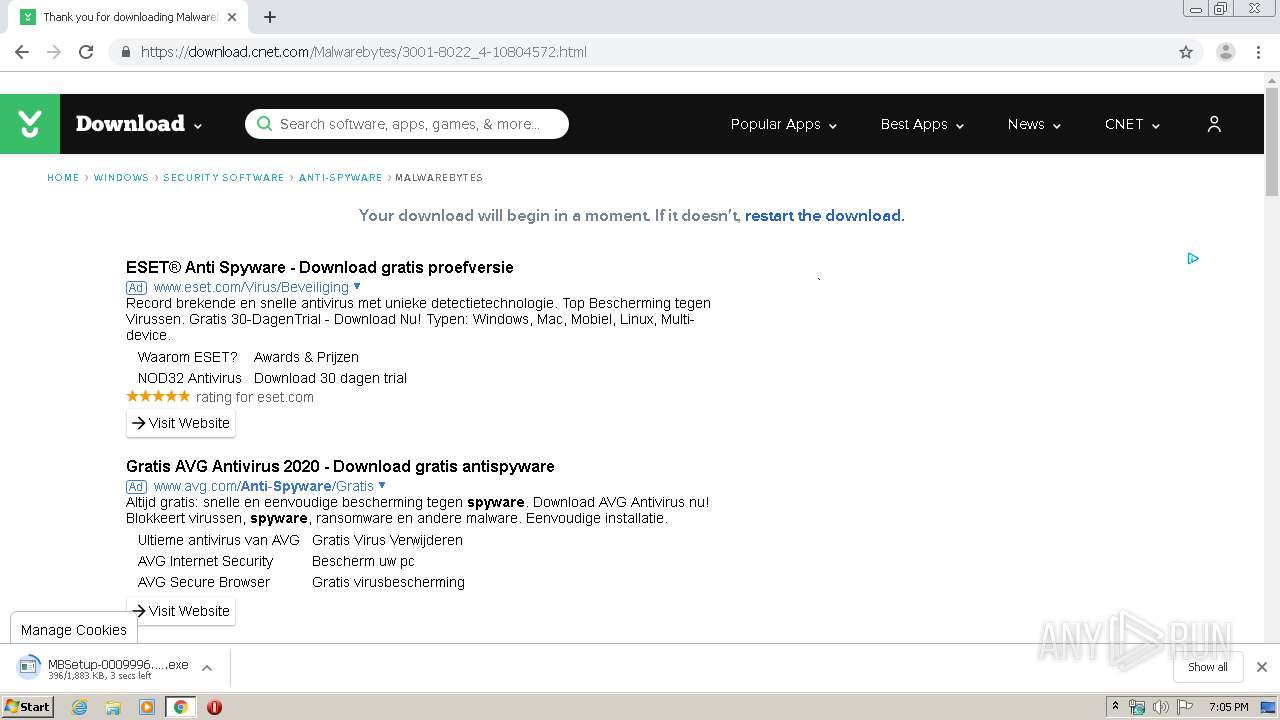
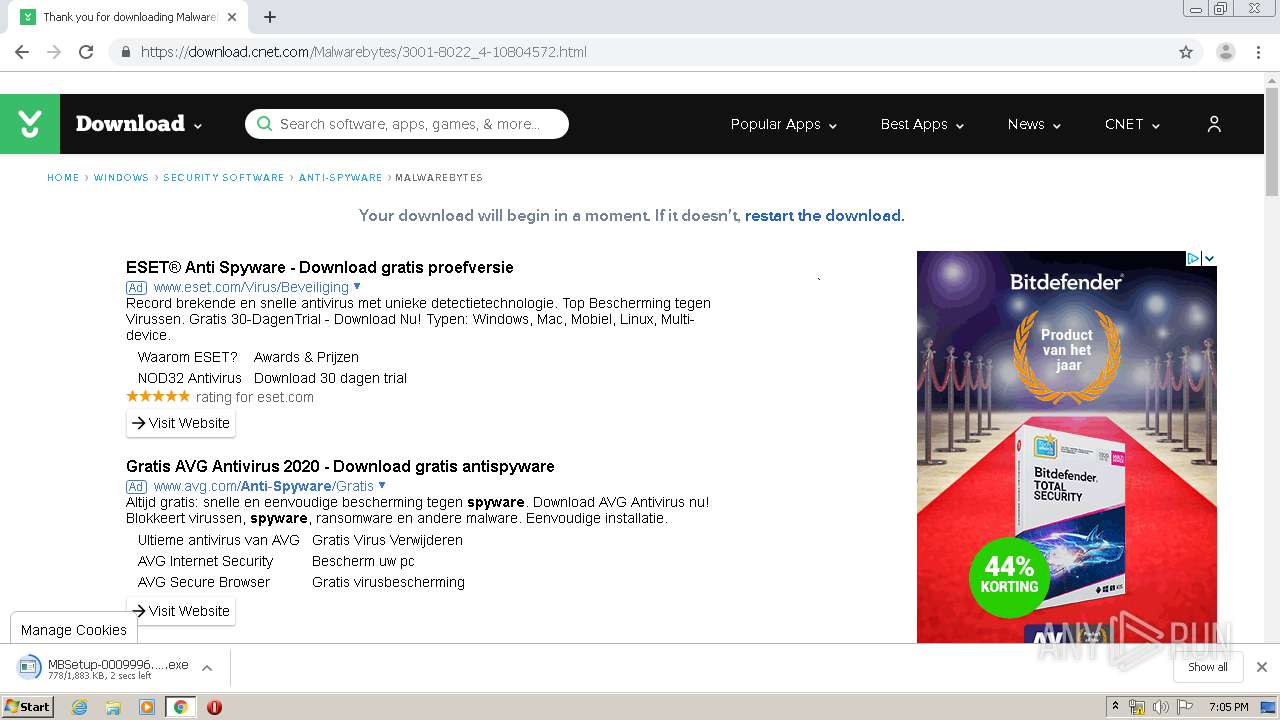
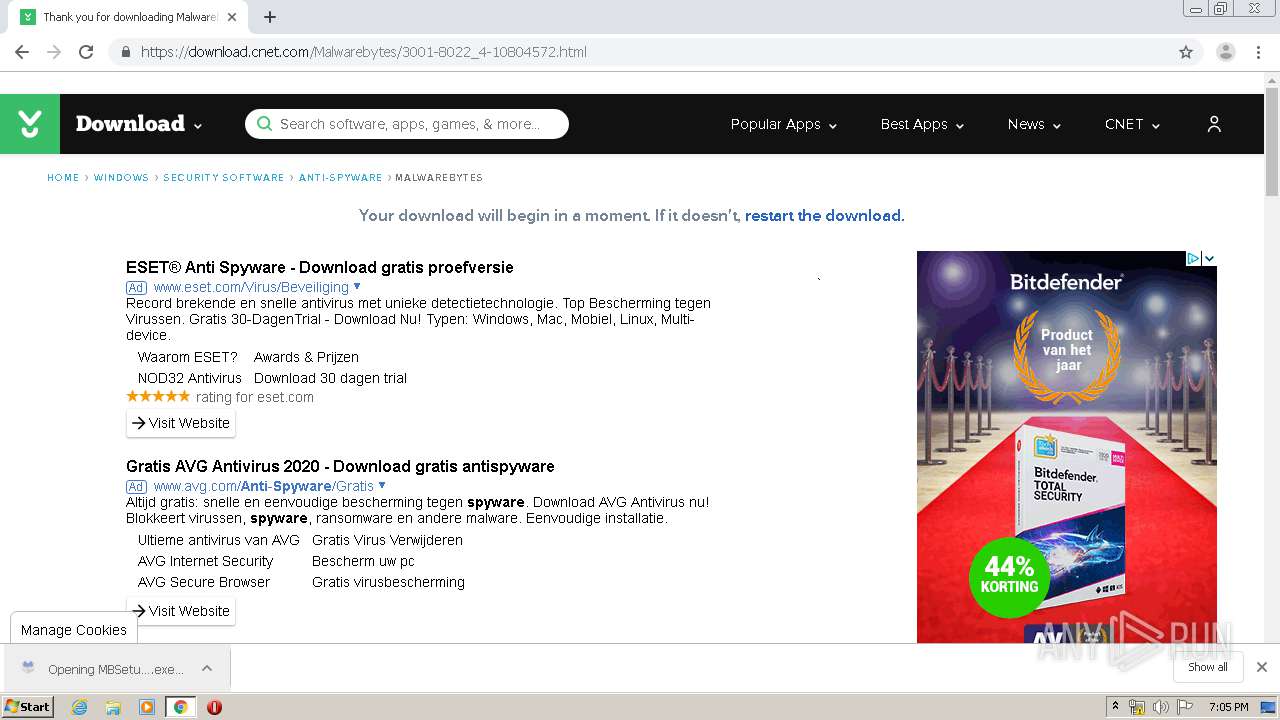
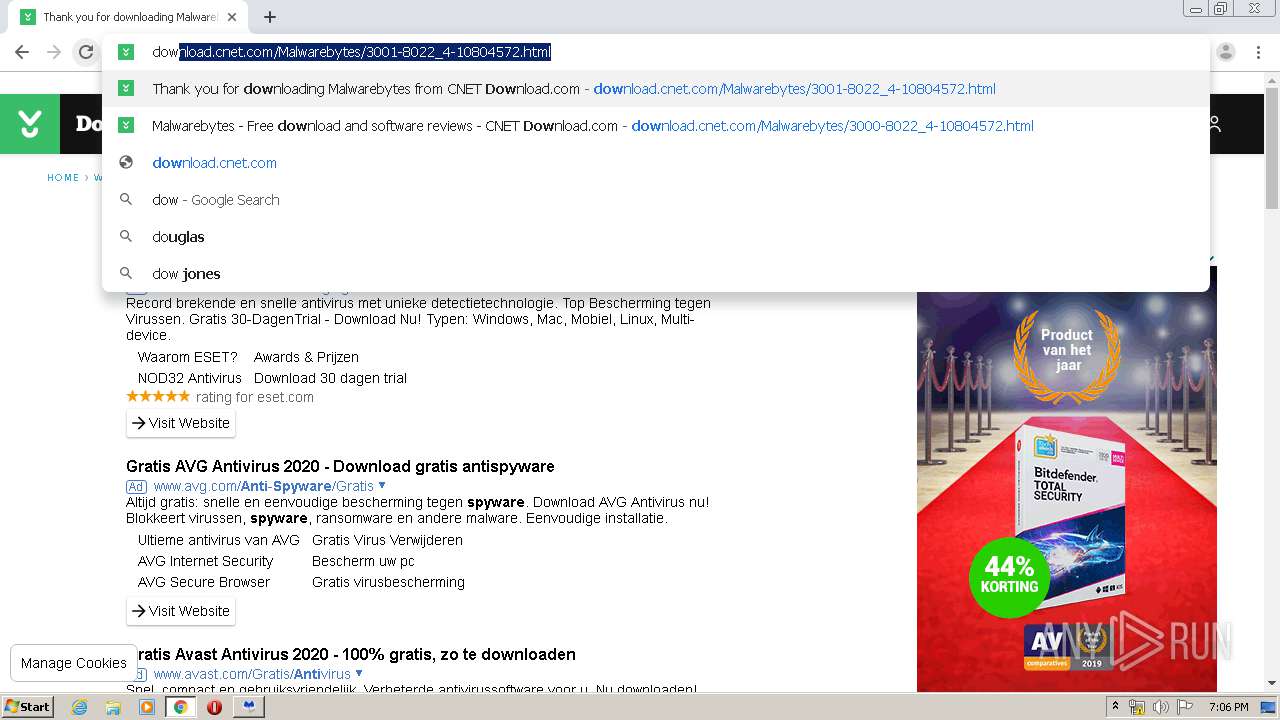
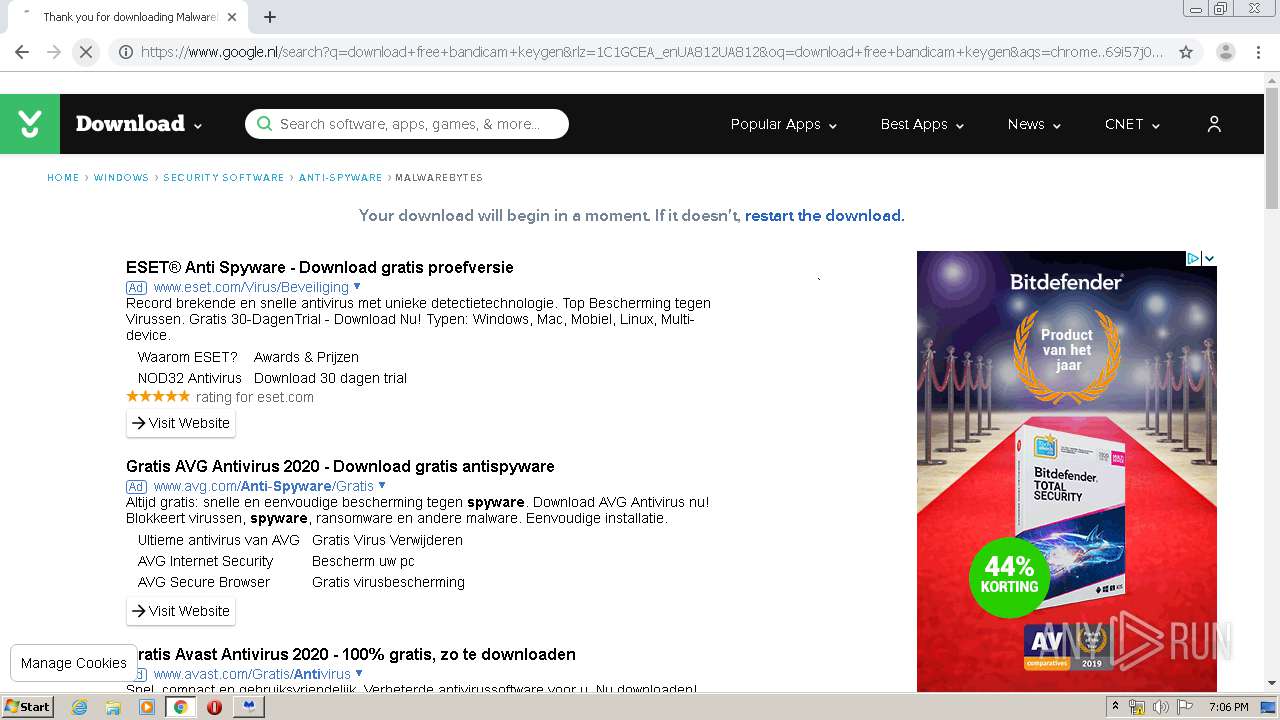
| URL: | https://download.cnet.com/Malwarebytes/3000-8022_4-10804572.html |
| Full analysis: | https://app.any.run/tasks/6e8030bf-b5de-4170-b722-d5712395b863 |
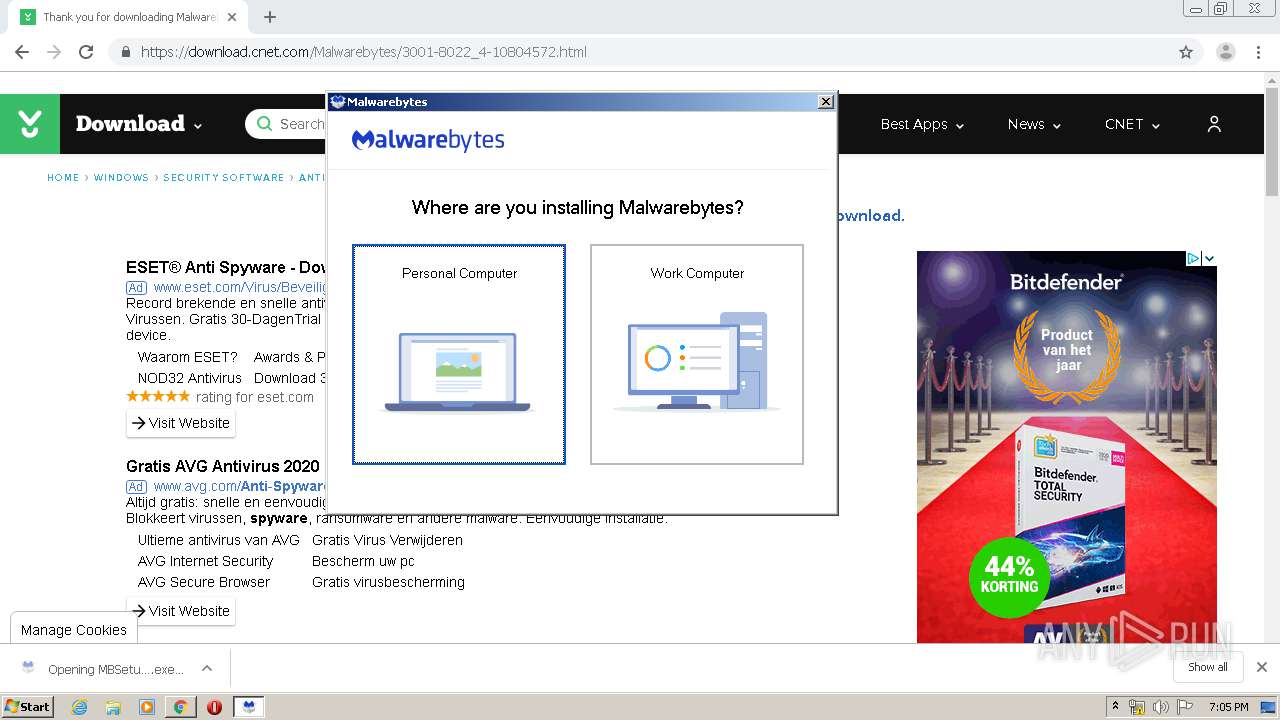
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2020, 18:03:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 90B0057570B23DF819670DB47D4FA550 |
| SHA1: | 8B420511C684571BEB8550DFEFFA4FDC3AE3ABCB |
| SHA256: | 751C50794FDDBF8D69A7463271F38DB8EE565C603420A830B79E95D03D5E10F8 |
| SSDEEP: | 3:N8SElbKU3JzfQaIUVdV2Ssn:2SKmUZRIUVXCn |
MALICIOUS
Application was dropped or rewritten from another process
- MBSetup-0009996.0009996-consumer.exe (PID: 3760)
- MBSetup-0009996.0009996-consumer.exe (PID: 3564)
- MBAMInstallerService.exe (PID: 3884)
- MBAMService.exe (PID: 2360)
- mbamtray.exe (PID: 2544)
- MBAMService.exe (PID: 2428)
- mbam.exe (PID: 2700)
- ig.exe (PID: 4000)
Loads dropped or rewritten executable
- MBAMInstallerService.exe (PID: 3884)
- MBAMService.exe (PID: 2428)
- mbamtray.exe (PID: 2544)
- mbam.exe (PID: 2700)
Changes settings of System certificates
- certutil.exe (PID: 1488)
- certutil.exe (PID: 2972)
- MBAMService.exe (PID: 2428)
- MBSetup-0009996.0009996-consumer.exe (PID: 3564)
Actions looks like stealing of personal data
- MBAMService.exe (PID: 2428)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2908)
Executable content was dropped or overwritten
- chrome.exe (PID: 2908)
- chrome.exe (PID: 3076)
- MBSetup-0009996.0009996-consumer.exe (PID: 3564)
- MBAMInstallerService.exe (PID: 3884)
- MBAMService.exe (PID: 2428)
Creates files in the program directory
- MBSetup-0009996.0009996-consumer.exe (PID: 3564)
- MBAMInstallerService.exe (PID: 3884)
- MBAMService.exe (PID: 2428)
Executed as Windows Service
- MBAMInstallerService.exe (PID: 3884)
- MBAMService.exe (PID: 2428)
Creates files in the Windows directory
- certutil.exe (PID: 1488)
- certutil.exe (PID: 2972)
- MBAMService.exe (PID: 2360)
- MBAMInstallerService.exe (PID: 3884)
- MBAMService.exe (PID: 2428)
Removes files from Windows directory
- certutil.exe (PID: 1488)
- certutil.exe (PID: 2972)
- MBAMService.exe (PID: 2428)
- MBAMInstallerService.exe (PID: 3884)
Creates files in the driver directory
- MBAMInstallerService.exe (PID: 3884)
- MBAMService.exe (PID: 2428)
Modifies the open verb of a shell class
- MBAMInstallerService.exe (PID: 3884)
Changes IE settings (feature browser emulation)
- MBAMInstallerService.exe (PID: 3884)
- MBAMService.exe (PID: 2428)
Creates COM task schedule object
- MBAMService.exe (PID: 2428)
Creates or modifies windows services
- MBAMService.exe (PID: 2428)
Reads Internet Cache Settings
- mbamtray.exe (PID: 2544)
- mbam.exe (PID: 2700)
Searches for installed software
- MBAMService.exe (PID: 2428)
Creates a software uninstall entry
- MBAMInstallerService.exe (PID: 3884)
Creates files in the user directory
- mbam.exe (PID: 2700)
Adds / modifies Windows certificates
- MBAMService.exe (PID: 2428)
- MBSetup-0009996.0009996-consumer.exe (PID: 3564)
INFO
Application launched itself
- chrome.exe (PID: 2908)
Reads the hosts file
- chrome.exe (PID: 3076)
- chrome.exe (PID: 2908)
Reads Internet Cache Settings
- chrome.exe (PID: 2908)
Reads settings of System Certificates
- chrome.exe (PID: 2908)
- MBSetup-0009996.0009996-consumer.exe (PID: 3564)
- chrome.exe (PID: 3076)
- MBAMService.exe (PID: 2428)
Dropped object may contain Bitcoin addresses
- MBAMInstallerService.exe (PID: 3884)
- MBAMService.exe (PID: 2428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
102
Monitored processes
57
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,11801231582748694948,581481455110937112,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11908595904718564131 --mojo-platform-channel-handle=4512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11801231582748694948,581481455110937112,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3042985898368560229 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11801231582748694948,581481455110937112,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17782415396737445288 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,11801231582748694948,581481455110937112,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=52645632738169410 --mojo-platform-channel-handle=4300 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,11801231582748694948,581481455110937112,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12213458253397689 --mojo-platform-channel-handle=1056 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1488 | certutil.exe -f -addstore root "C:\Windows\TEMP\MBInstallTemp\servicepkg\DigiCertEVRoot.crt" | C:\Windows\system32\certutil.exe | — | MBAMInstallerService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11801231582748694948,581481455110937112,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16569721221760561597 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11801231582748694948,581481455110937112,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11931096644561756066 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11801231582748694948,581481455110937112,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13067638458675098281 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11801231582748694948,581481455110937112,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=642756334595872852 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
5 032
Read events
2 303
Write events
2 717
Delete events
12
Modification events
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2908-13231015451271000 |
Value: 259 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
299
Suspicious files
385
Text files
1 315
Unknown types
83
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E90B51B-B5C.pma | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b2eb51bd-e2ef-4d60-b0a0-7bc29bd3b686.tmp | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa73af9.TMP | text | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa73c22.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
239
DNS requests
187
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3076 | chrome.exe | GET | 204 | 172.217.18.163:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
3076 | chrome.exe | GET | 204 | 172.217.18.163:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
2428 | MBAMService.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA%2BoSQYV1wCgviF2%2FcXsbb0%3D | US | der | 471 b | whitelisted |
3076 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
2428 | MBAMService.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertAssuredIDRootCA.crl | US | der | 592 b | whitelisted |
2428 | MBAMService.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertAssuredIDRootCA.crl | US | der | 592 b | whitelisted |
2428 | MBAMService.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSYagvY3tfizDNoybzVSPFZmSEm0wQUe2jOKarAF75JeuHlP9an90WPNTICEAii7E54oJ4XSxkuVTWYS1k%3D | US | der | 471 b | whitelisted |
3076 | chrome.exe | GET | 200 | 74.125.100.7:80 | http://r2---sn-5hnekn7l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=85.203.44.3&mm=28&mn=sn-5hnekn7l&ms=nvh&mt=1586541797&mv=m&mvi=1&pl=26&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3076 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
3076 | chrome.exe | GET | 200 | 74.125.8.155:80 | http://r5---sn-5hnednlr.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=85.203.44.3&mm=28&mn=sn-5hnednlr&ms=nvh&mt=1586541797&mv=m&mvi=4&pl=26&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3076 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3076 | chrome.exe | 104.111.226.134:443 | download.cnet.com | Akamai International B.V. | NL | unknown |
3076 | chrome.exe | 152.195.132.202:443 | cdn.cookielaw.org | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3076 | chrome.exe | 151.101.113.188:443 | production-cmp.isgprivacy.cbsi.com | Fastly | US | suspicious |
3076 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3076 | chrome.exe | 216.58.208.34:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
3076 | chrome.exe | 23.8.11.168:443 | c.go-mpulse.net | Akamai International B.V. | NL | whitelisted |
3076 | chrome.exe | 151.101.13.188:443 | dl2.cbsistatic.com | Fastly | US | malicious |
3076 | chrome.exe | 172.217.18.98:443 | adservice.google.com | Google Inc. | US | whitelisted |
3076 | chrome.exe | 172.217.23.98:443 | adservice.google.nl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.cnet.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cdn.cookielaw.org |
| whitelisted |
production-cmp.isgprivacy.cbsi.com |
| whitelisted |
dl1.cbsistatic.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
dl3.cbsistatic.com |
| unknown |
c.go-mpulse.net |
| whitelisted |
dl2.cbsistatic.com |
| unknown |
Threats
Process | Message |
|---|---|
mbamtray.exe | QAxBase::setControl: requested control {F36AD0D0-B5F0-4C69-AF08-603D177FEF0E} could not be instantiated
|
mbamtray.exe | Description:
|
mbamtray.exe | Code : -2147467259
|
mbamtray.exe | Source :
|
mbamtray.exe | Code : -2147467259
|
mbamtray.exe | Help :
|
mbamtray.exe | Connect to the exception(int,QString,QString,QString) signal to catch this exception
|
mbamtray.exe | qt.scenegraph.general: Loading backend software
|
mbamtray.exe | void __thiscall PageStatusMonitor::OnRequestFinished(class QNetworkReply *) "Page: https://links.malwarebytes.com/link/3x_cart?affiliate=0009996&uuid=&x-source=teams-trial&x-action=comparison_chart&x-token_secret=jgQTeomKKCX-ohzCvjCx3hwcIVtPY30kwsHoc_3VxIXPC5ThufEG_A8aL2BlAzhvmIhkdP9lEl05C-Hlskci2w==&ADDITIONAL_x-token_secret=jgQTeomKKCX-ohzCvjCx3hwcIVtPY30kwsHoc_3VxIXPC5ThufEG_A8aL2BlAzhvmIhkdP9lEl05C-Hlskci2w==&x-prodcode=MDAM-B&lang=en&version=4.1.0.56 received code: "
|
mbamtray.exe | "2020-04-10T19:06:27" void __thiscall TrayLicenseNotificationsModel::OnConfigUpdated(void) LicenseController has sent a config update notification!
|