| File name: | Rec.exe |
| Full analysis: | https://app.any.run/tasks/ef695b66-4168-4aec-a767-ae08755bdc1a |
| Verdict: | Malicious activity |
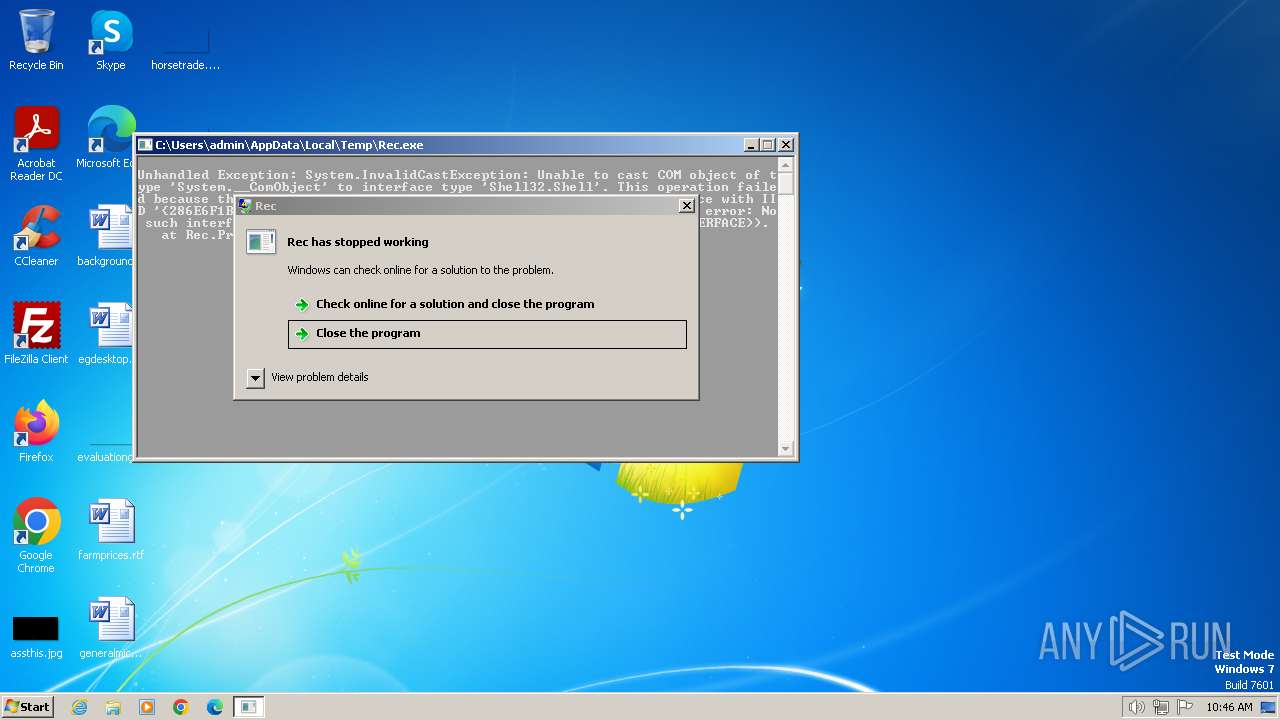
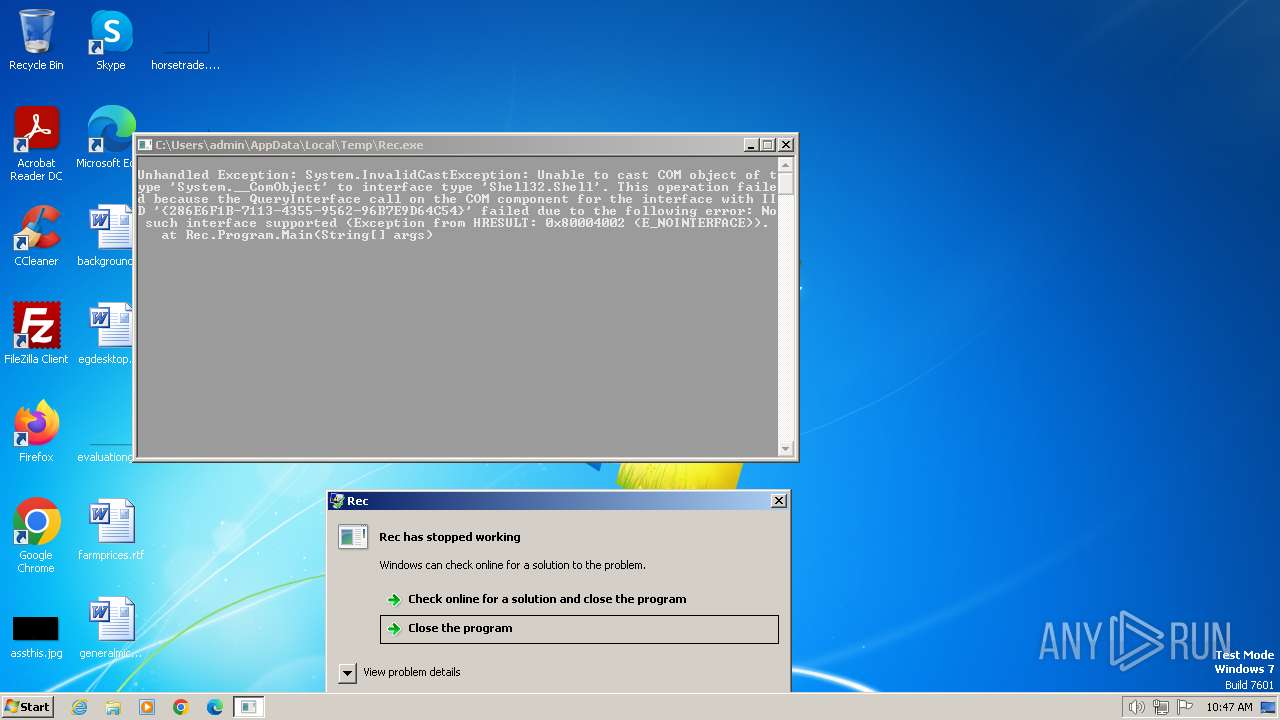
| Analysis date: | March 14, 2024, 10:46:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | CFD46308C4B161BE5490C29970BDAFD0 |
| SHA1: | 9911521DFBC740C32B1BED9097E8715B80501C4B |
| SHA256: | 751C159CF43393943B74AC2E1BC12940EF3FA3A987FBC166FEBD2A0D4ED83312 |
| SSDEEP: | 192:Jsw7S9kR8QY6fnpIiuQ7ovXnh8C5+uWN1hqSxwdrV/kwj2BEPDQoOy:JA6fpMvXnh8C56h2rVs/0QoO |
MALICIOUS
Drops the executable file immediately after the start
- Rec.exe (PID: 3668)
SUSPICIOUS
Process drops legitimate windows executable
- msdt.exe (PID: 2756)
Reads settings of System Certificates
- msdt.exe (PID: 2756)
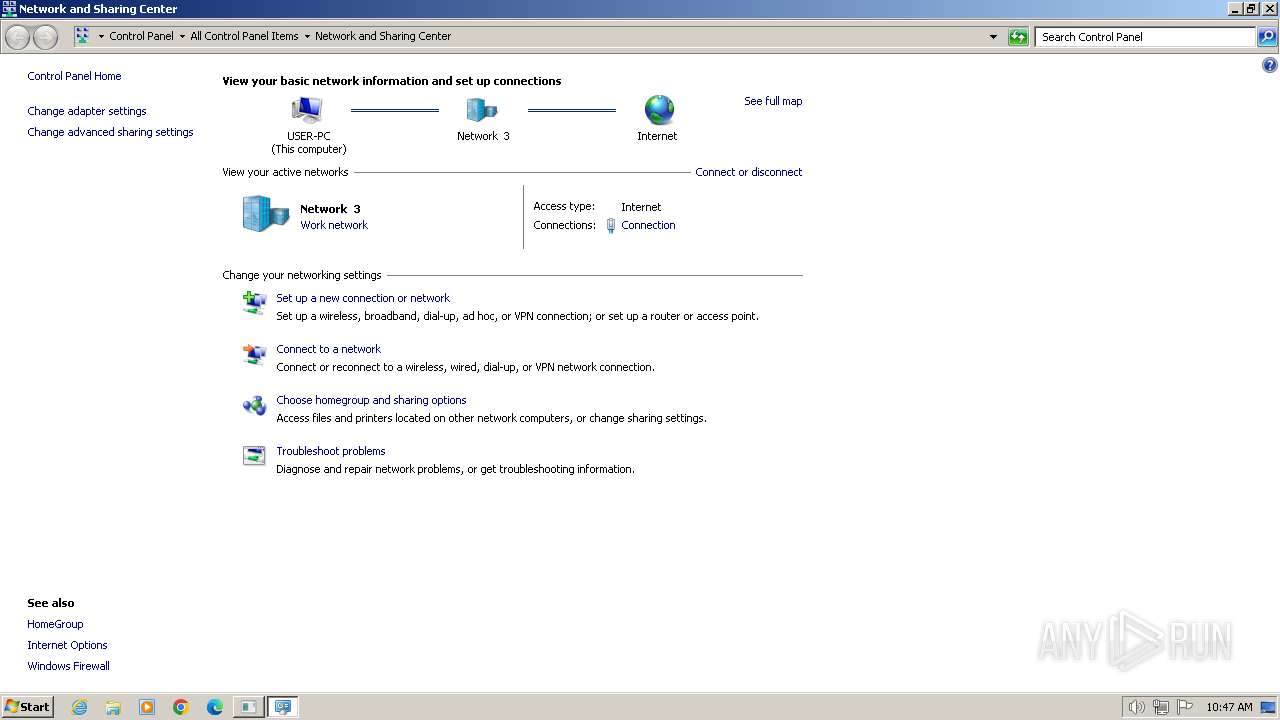
Reads the Internet Settings
- sdiagnhost.exe (PID: 696)
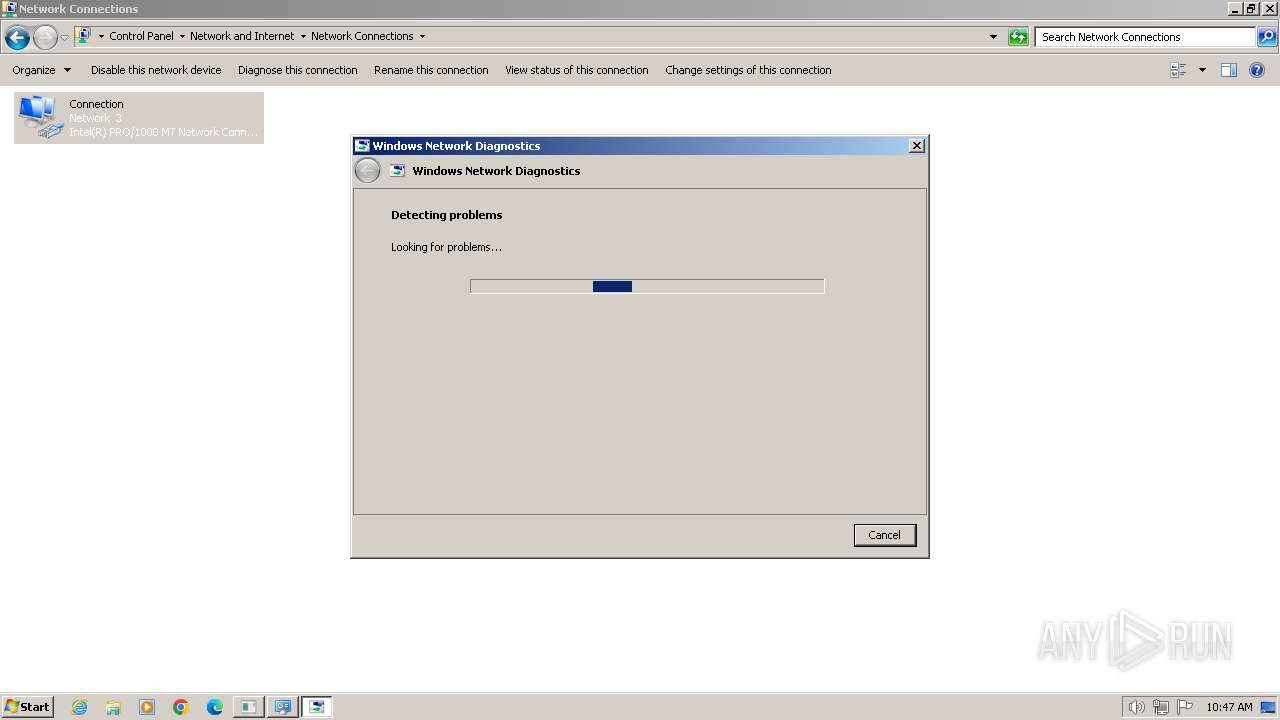
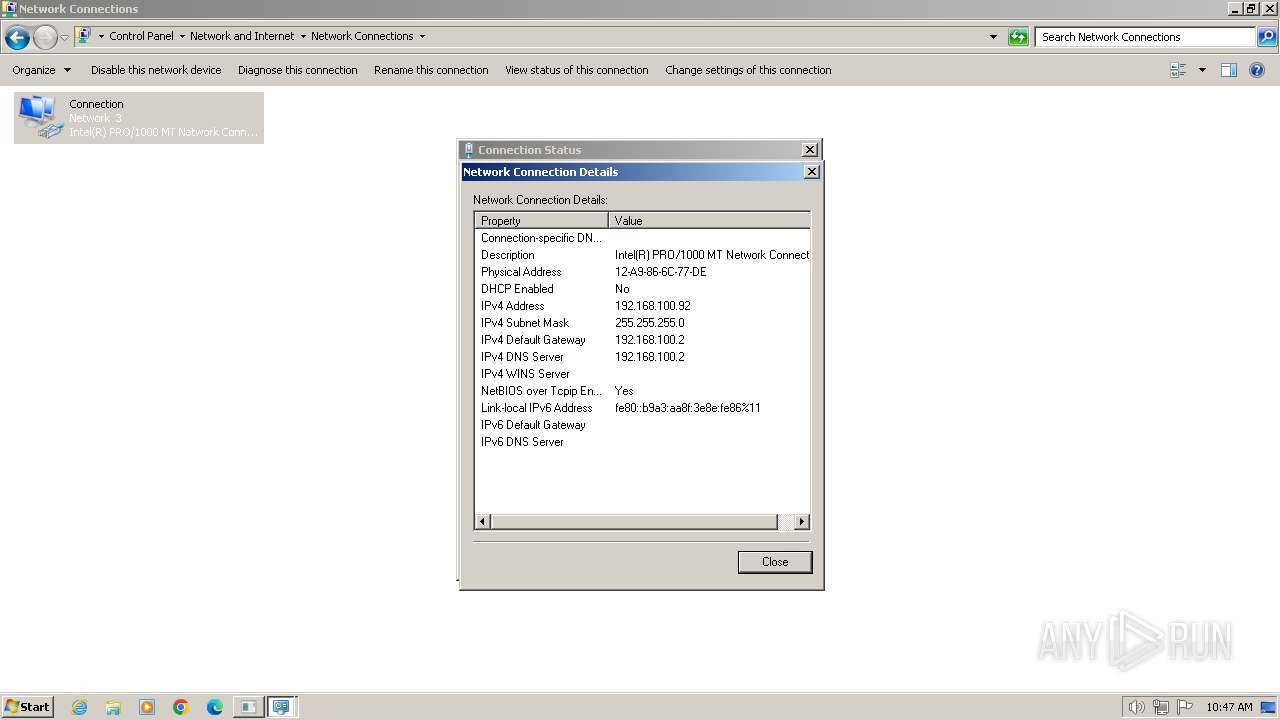
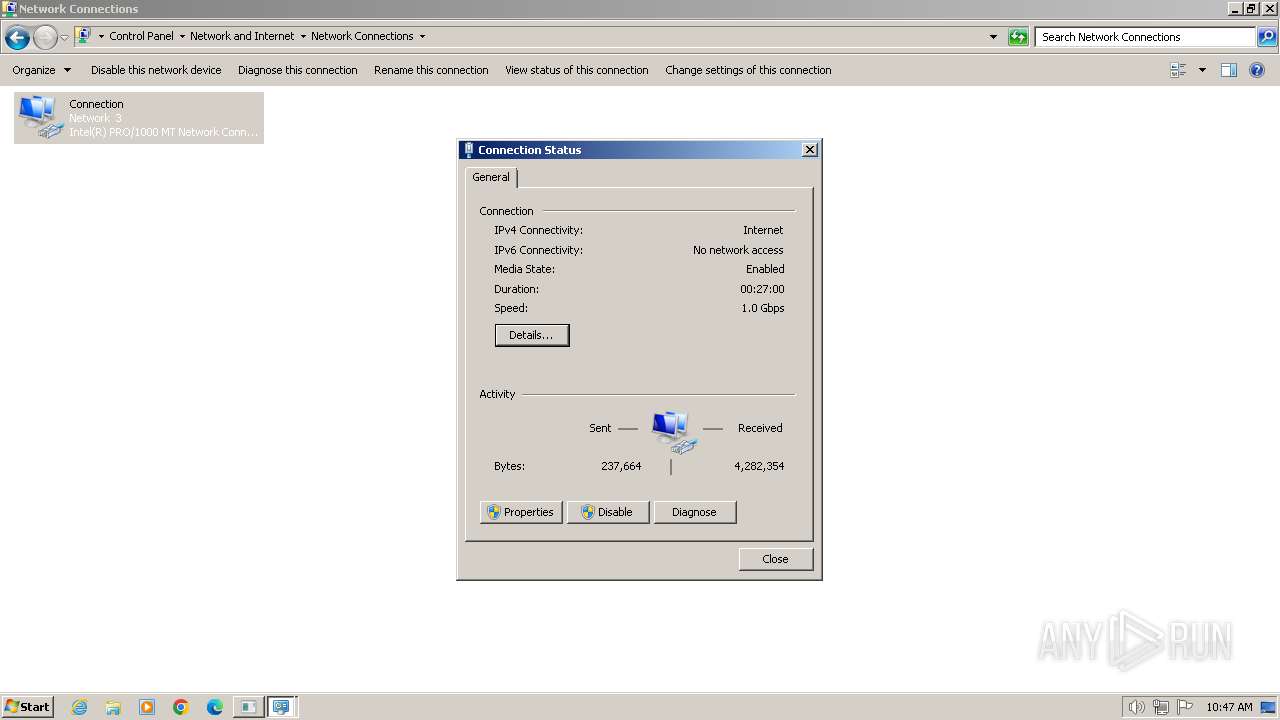
Process uses IPCONFIG to discover network configuration
- sdiagnhost.exe (PID: 696)
Uses ROUTE.EXE to obtain the routing table information
- sdiagnhost.exe (PID: 696)
INFO
Checks supported languages
- Rec.exe (PID: 3668)
Reads the computer name
- Rec.exe (PID: 3668)
Reads the machine GUID from the registry
- Rec.exe (PID: 3668)
Reads security settings of Internet Explorer
- msdt.exe (PID: 2756)
- sdiagnhost.exe (PID: 696)
Manual execution by a user
- msdt.exe (PID: 2756)
Reads the software policy settings
- msdt.exe (PID: 2756)
Create files in a temporary directory
- msdt.exe (PID: 2756)
- sdiagnhost.exe (PID: 696)
- makecab.exe (PID: 2060)
Drops the executable file immediately after the start
- msdt.exe (PID: 2756)
Creates files or folders in the user directory
- msdt.exe (PID: 2756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2056:02:08 02:42:34+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 7168 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3b52 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Rec |
| FileVersion: | 1.0.0.0 |
| InternalName: | Rec.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | Rec.exe |
| ProductName: | Rec |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
51
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
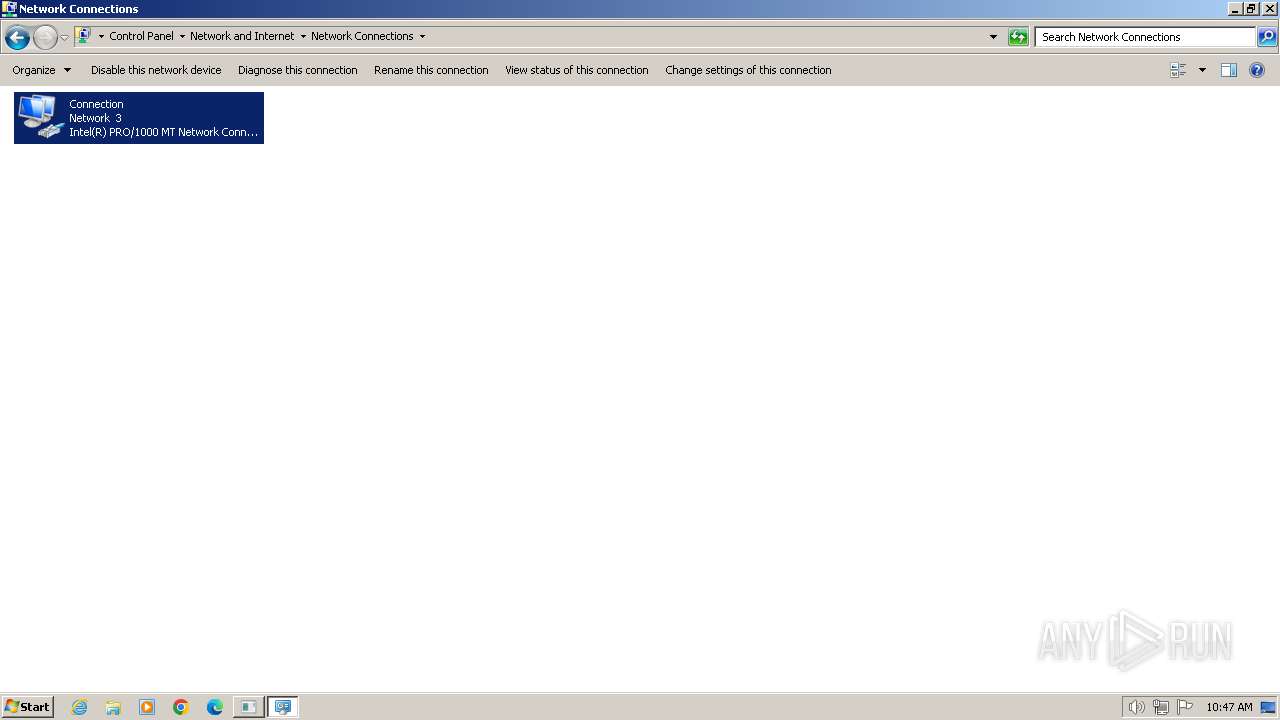
| 696 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2060 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\System32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2576 | C:\Windows\system32\DllHost.exe /Processid:{7007ACD1-3202-11D1-AAD2-00805FC1270E} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | C:\Windows\system32\DllHost.exe /Processid:{7007ACD1-3202-11D1-AAD2-00805FC1270E} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2756 | -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDF9BFC.tmp -ep NetworkDiagnosticsGenericNetConnection | C:\Windows\System32\msdt.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3072 | "C:\Windows\system32\ROUTE.EXE" print | C:\Windows\System32\ROUTE.EXE | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3668 | "C:\Users\admin\AppData\Local\Temp\Rec.exe" | C:\Users\admin\AppData\Local\Temp\Rec.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Rec Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3912 | "C:\Windows\system32\ipconfig.exe" /all | C:\Windows\System32\ipconfig.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 285
Read events
7 239
Write events
45
Delete events
1
Modification events
| (PID) Process: | (2692) dllhost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2692) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Network\NetCfgLockHolder |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2756) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (696) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (696) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (696) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (696) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2756) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\Windows Error Reporting\Debug |
| Operation: | write | Name: | StoreLocation |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_Microsoft Window_bd5996727e9ea1acda90841fa2c99a88df4fb9d6_cab_0adca4e6 | |||
| (PID) Process: | (2576) dllhost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
34
Text files
28
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2756 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ba88af3-af49-4185-be67-5c285bb00929\InteractiveRes.ps1 | text | |
MD5:25B8543DBF571F040118423BC3C7A75E | SHA256:D78E6291D6F27AC6FEBDCF0A4D5A34521E7F033AF8875E026DF21BA7513AB64A | |||
| 2756 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ba88af3-af49-4185-be67-5c285bb00929\UtilitySetConstants.ps1 | text | |
MD5:0C75AE5E75C3E181D13768909C8240BA | SHA256:DE5C231C645D3AE1E13694284997721509F5DE64EE5C96C966CDFDA9E294DB3F | |||
| 2756 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ba88af3-af49-4185-be67-5c285bb00929\NetworkDiagnosticsVerify.ps1 | text | |
MD5:C0BB6343BD0F6F9B46B33E4B66106953 | SHA256:EB9BC61668A93759D0127A11CDFC03E924100D69C7E6457FEAA89330474C90C3 | |||
| 2756 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ba88af3-af49-4185-be67-5c285bb00929\HTInteractiveRes.ps1 | text | |
MD5:C25ED2111C6EE9299E6D9BF51012F2F5 | SHA256:8E326EE0475208D4C943D885035058FAD7146BBA02B66305F7C9F31F6A57E81B | |||
| 2756 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ba88af3-af49-4185-be67-5c285bb00929\DiagPackage.dll | executable | |
MD5:2433E09C08C21455000F7E36D7653759 | SHA256:EA9400E719FB15CD82D5DAB4B7D8E3870BB375BBE11BB95B0D957A84FEE2891C | |||
| 2756 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ba88af3-af49-4185-be67-5c285bb00929\NetworkDiagnosticsTroubleshoot.ps1 | text | |
MD5:1D192CE36953DBB7DC7EE0D04C57AD8D | SHA256:935A231924AE5D4A017B0C99D4A5F3904EF280CEA4B3F727D365283E26E8A756 | |||
| 2756 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ba88af3-af49-4185-be67-5c285bb00929\NetworkDiagnosticsResolve.ps1 | text | |
MD5:A7B957F221C643580184665BE57E6AC8 | SHA256:8582EF50174CB74233F196F193E04C0CCBBEE2AED5CE50964CBB95822C218E7F | |||
| 2756 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ba88af3-af49-4185-be67-5c285bb00929\StartDPSService.ps1 | text | |
MD5:A660422059D953C6D681B53A6977100E | SHA256:D19677234127C38A52AEC23686775A8EB3F4E3A406F4A11804D97602D6C31813 | |||
| 2756 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ba88af3-af49-4185-be67-5c285bb00929\UtilityFirewall.ps1 | text | |
MD5:B004AFC224E9216115EC3B0BF5D43BA2 | SHA256:31B97632CA31D1BB21917A07757B2FF415DBB6A4E7DD7B533ECC52431ACF65B5 | |||
| 2756 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ba88af3-af49-4185-be67-5c285bb00929\DiagPackage.diagpkg | xml | |
MD5:C9FB87FA3460FAE6D5D599236CFD77E2 | SHA256:CDE728C08A4E50A02FCFF35C90EE2B3B33AB24C8B858F180B6A67BFA94DEF35F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
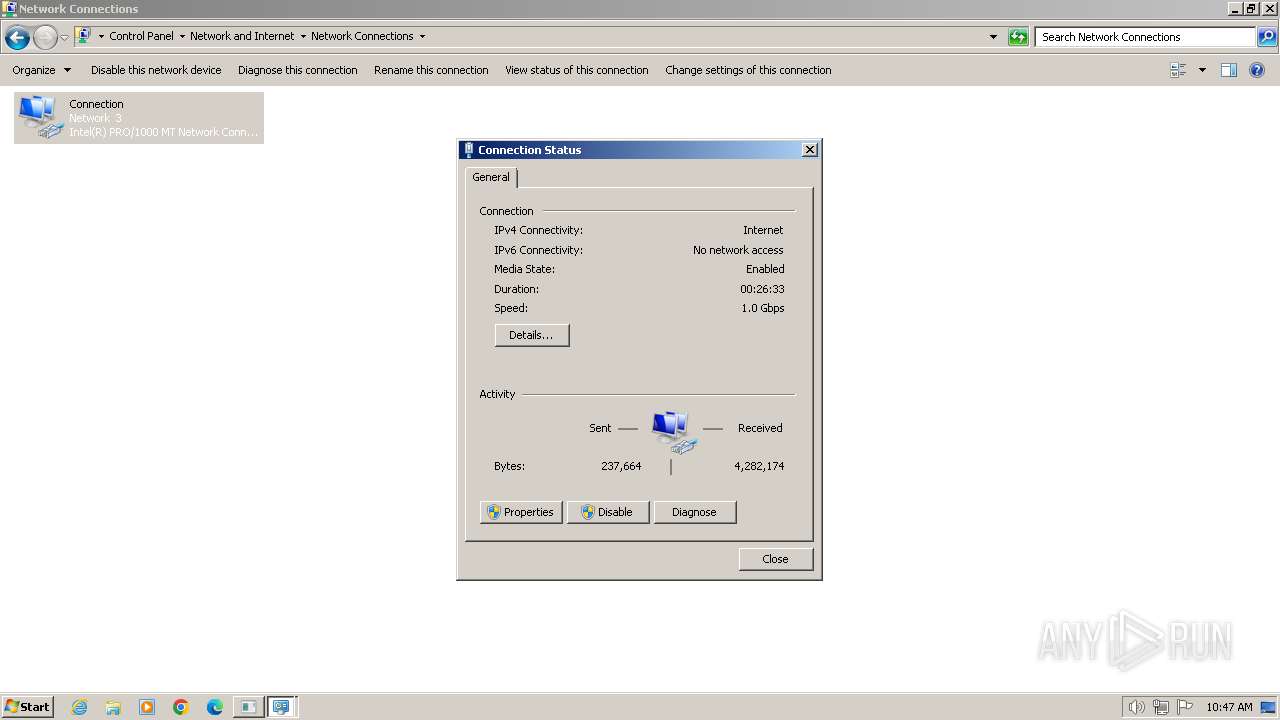
HTTP(S) requests
0
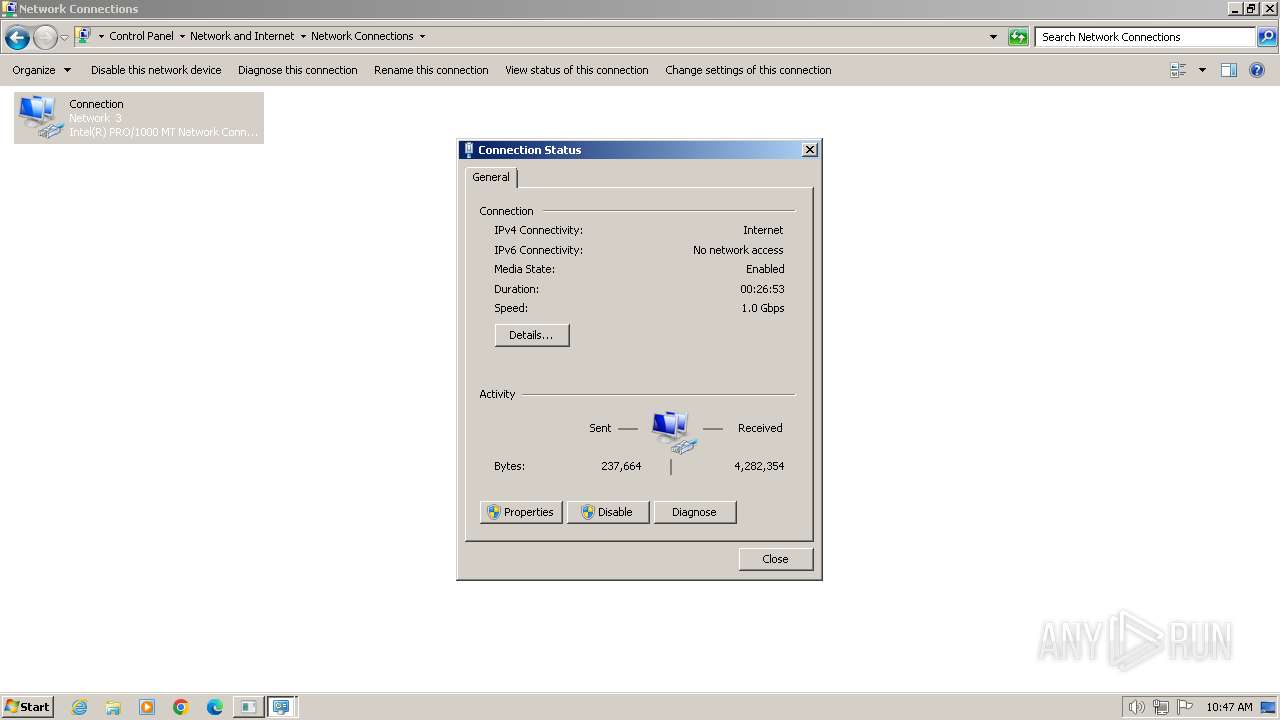
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |