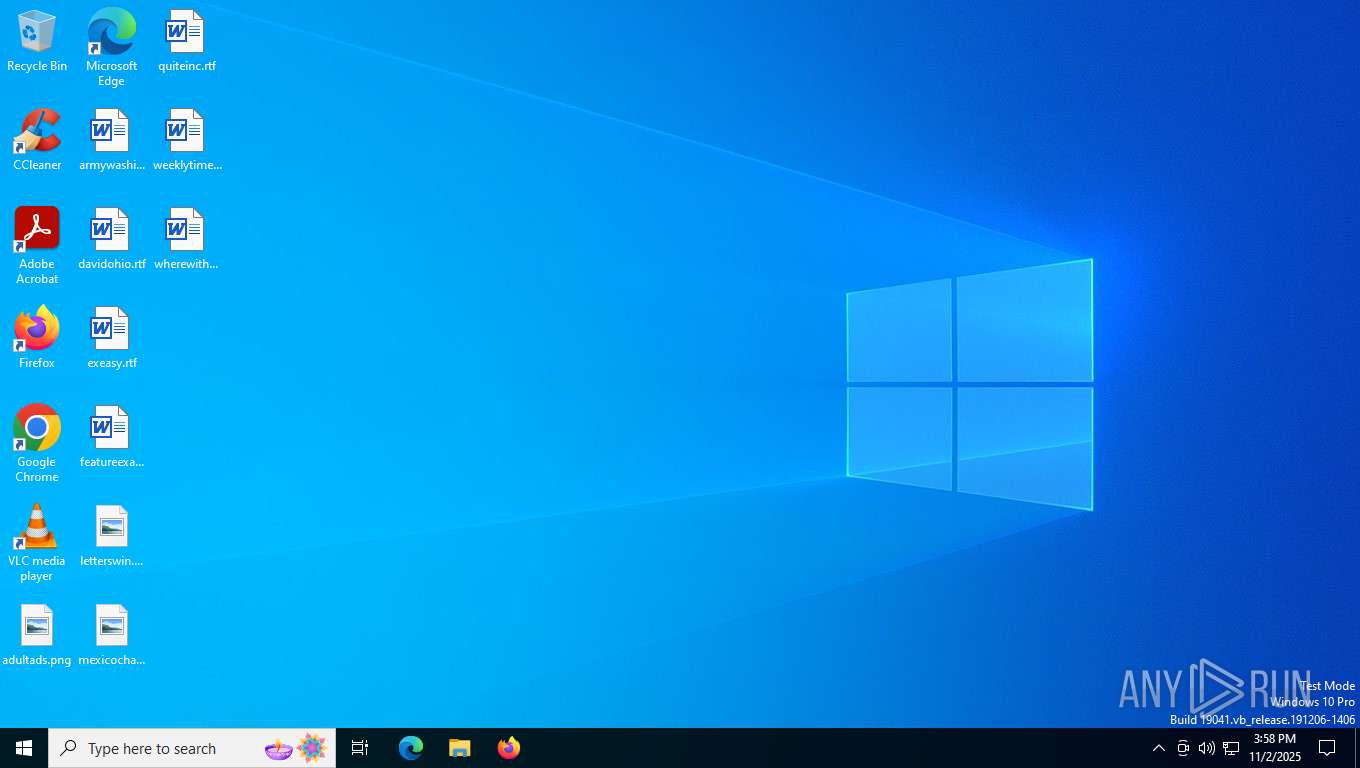
| File name: | Volcano_Executor.exe |
| Full analysis: | https://app.any.run/tasks/b9eeb58d-f4ad-43d3-8057-e2eb3754c59d |
| Verdict: | Malicious activity |
| Analysis date: | November 02, 2025, 15:58:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 8E1413E66B8F444073ED90B1356ED47D |
| SHA1: | 4690E601BE70BFCAB87251ABF9EB84B0CC0A62E7 |
| SHA256: | 751B3F4CA0DB12BCA8B7FE426A9F4D9E294B06256BF60F0B755E971D4E743A3F |
| SSDEEP: | 98304:UK0l+uXCTQ+I4UleSsq9Dku/pV06LVQV7KWV7Fbz5dlQq14WiEDPkohJN/Oujn+N:UTXaD7bZIaP5/6 |
MALICIOUS
GENERIC has been found (auto)
- Volcano_Executor.exe (PID: 7608)
Changes the autorun value in the registry
- Client.exe (PID: 7960)
- VolcanoCrashHandler.exe (PID: 7860)
SUSPICIOUS
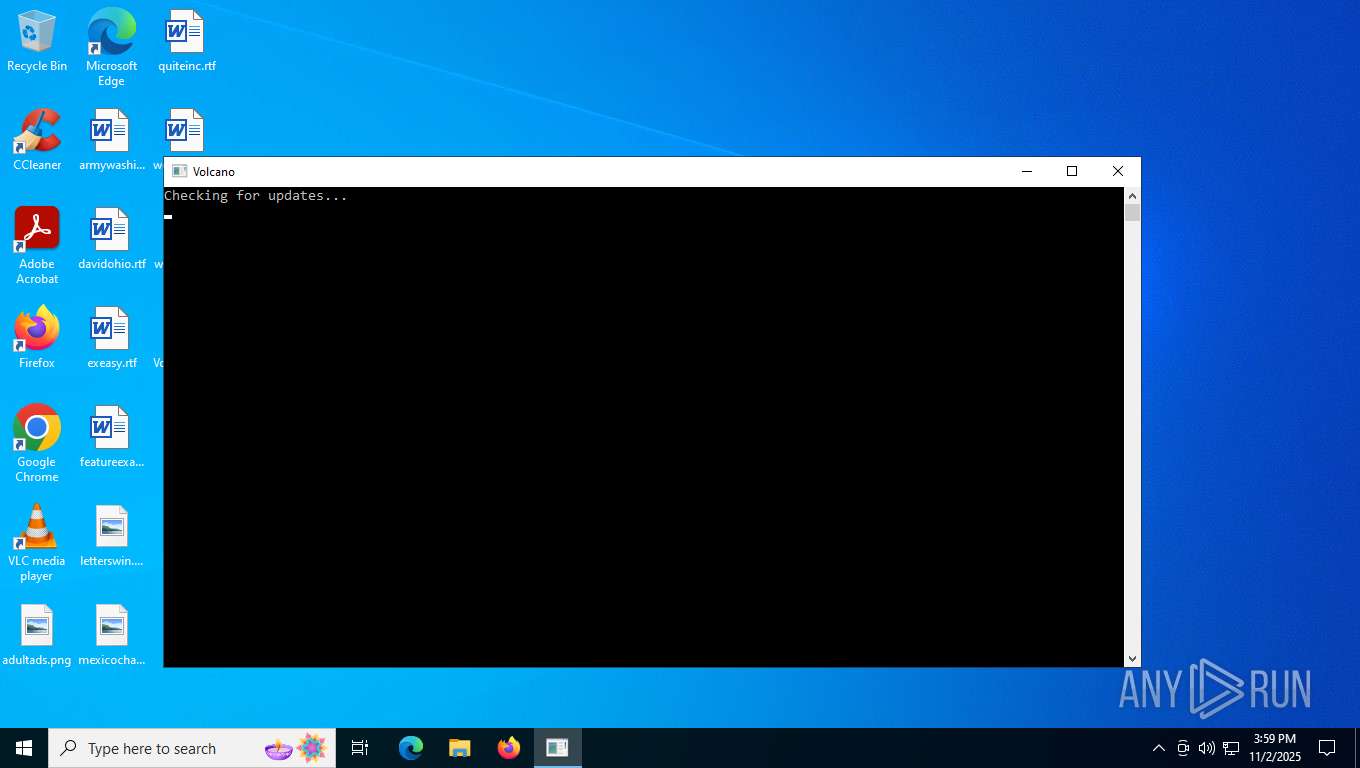
Reads the date of Windows installation
- Volcano_Executor.exe (PID: 7608)
- VolcanoUpdater.exe (PID: 7820)
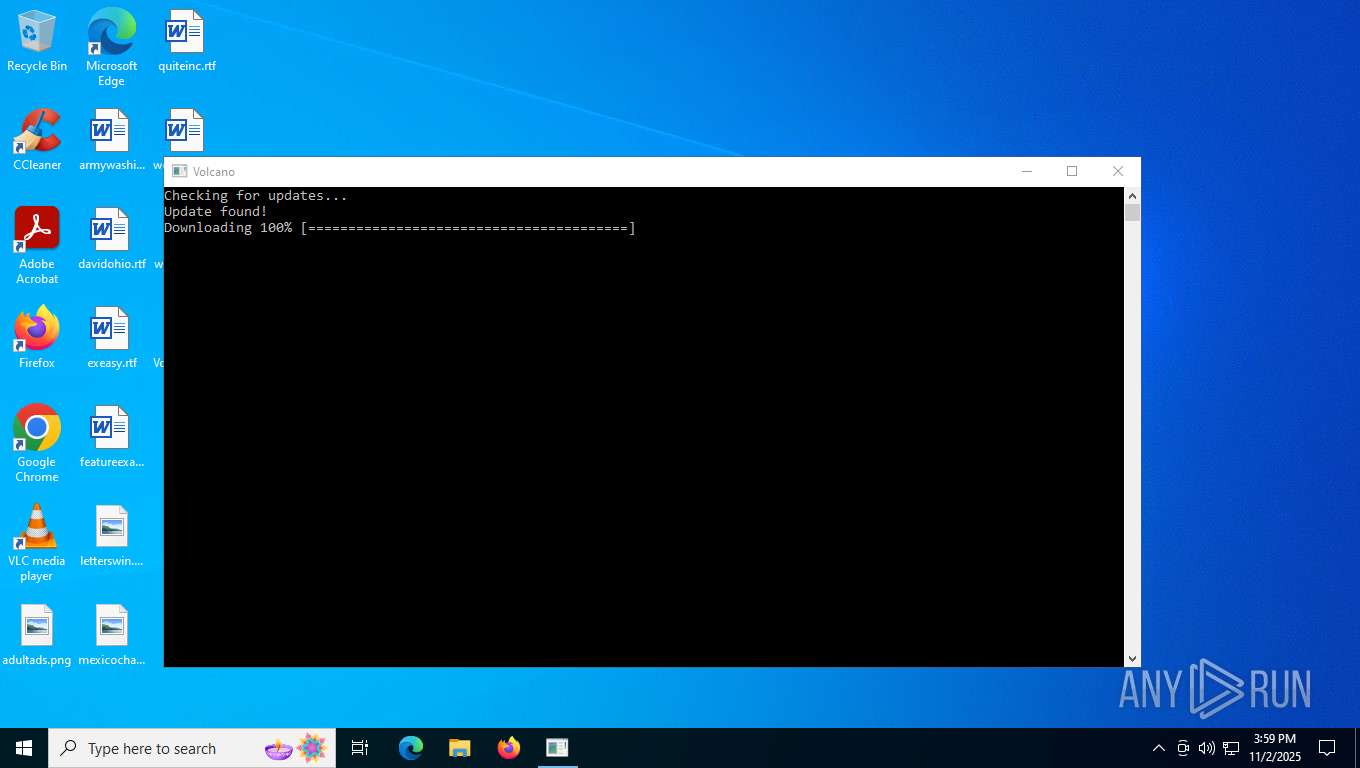
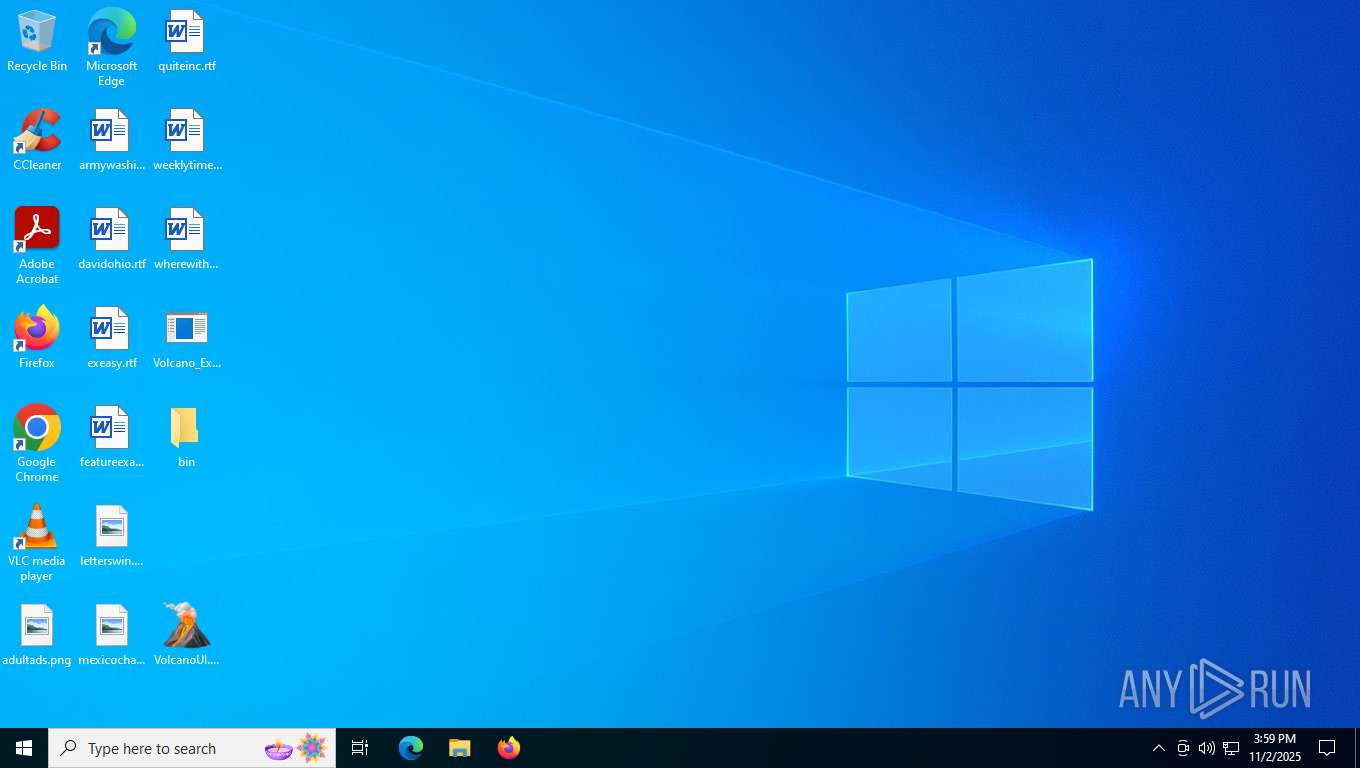
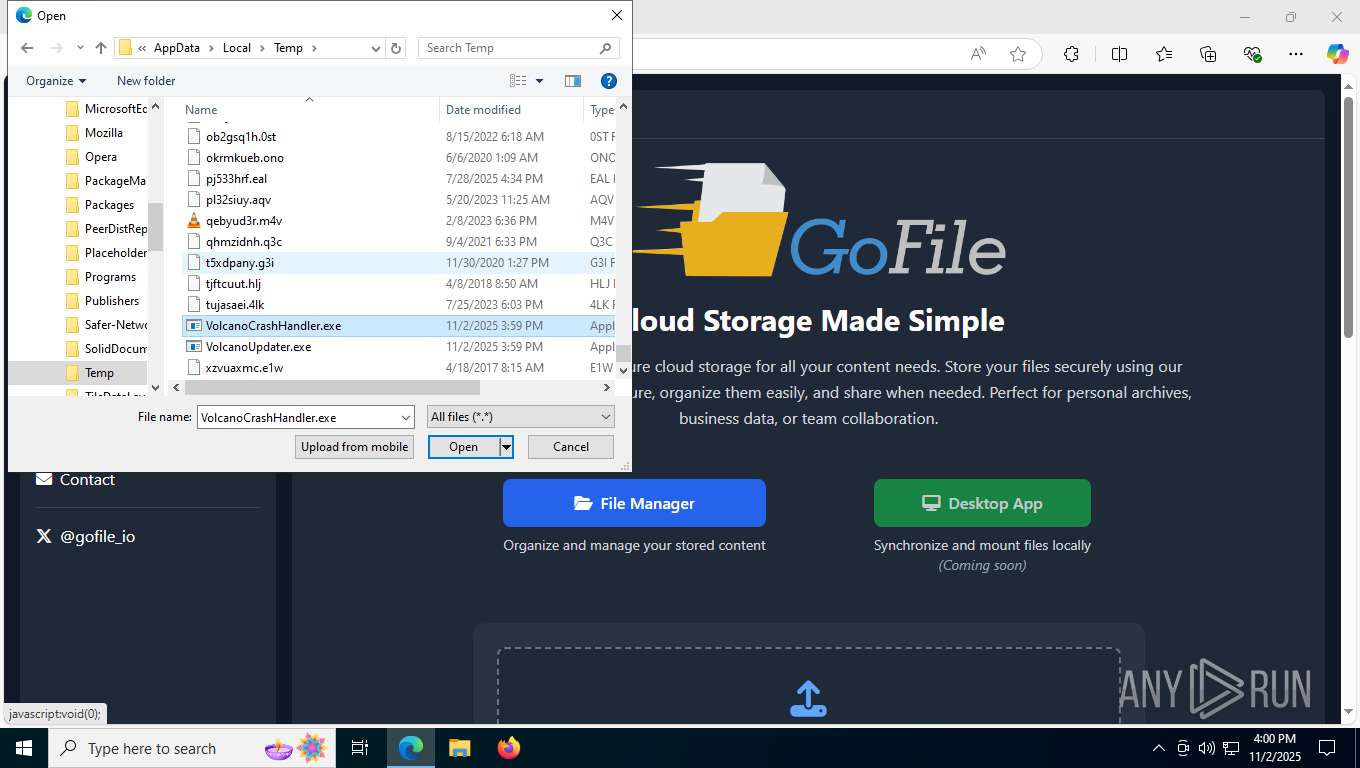
Executable content was dropped or overwritten
- Volcano_Executor.exe (PID: 7608)
- VolcanoUpdater.exe (PID: 7820)
- VolcanoCrashHandler.exe (PID: 7860)
- VolcanoUI.exe (PID: 8048)
Reads security settings of Internet Explorer
- Volcano_Executor.exe (PID: 7608)
- VolcanoUpdater.exe (PID: 7820)
Reads the BIOS version
- VolcanoUpdater.exe (PID: 7820)
- VolcanoUI.exe (PID: 8048)
Starts itself from another location
- VolcanoCrashHandler.exe (PID: 7860)
There is functionality for taking screenshot (YARA)
- Client.exe (PID: 7960)
Connects to unusual port
- Client.exe (PID: 7960)
Found regular expressions for crypto-addresses (YARA)
- Client.exe (PID: 7960)
Process drops legitimate windows executable
- VolcanoUI.exe (PID: 8048)
INFO
Reads the computer name
- Volcano_Executor.exe (PID: 7608)
- VolcanoCrashHandler.exe (PID: 7860)
- Client.exe (PID: 7960)
- VolcanoUpdater.exe (PID: 7820)
- VolcanoUI.exe (PID: 8048)
- identity_helper.exe (PID: 7544)
Checks supported languages
- Volcano_Executor.exe (PID: 7608)
- VolcanoCrashHandler.exe (PID: 7860)
- VolcanoUpdater.exe (PID: 7820)
- Client.exe (PID: 7960)
- identity_helper.exe (PID: 7544)
- VolcanoUI.exe (PID: 8048)
Reads the machine GUID from the registry
- Volcano_Executor.exe (PID: 7608)
- VolcanoCrashHandler.exe (PID: 7860)
- Client.exe (PID: 7960)
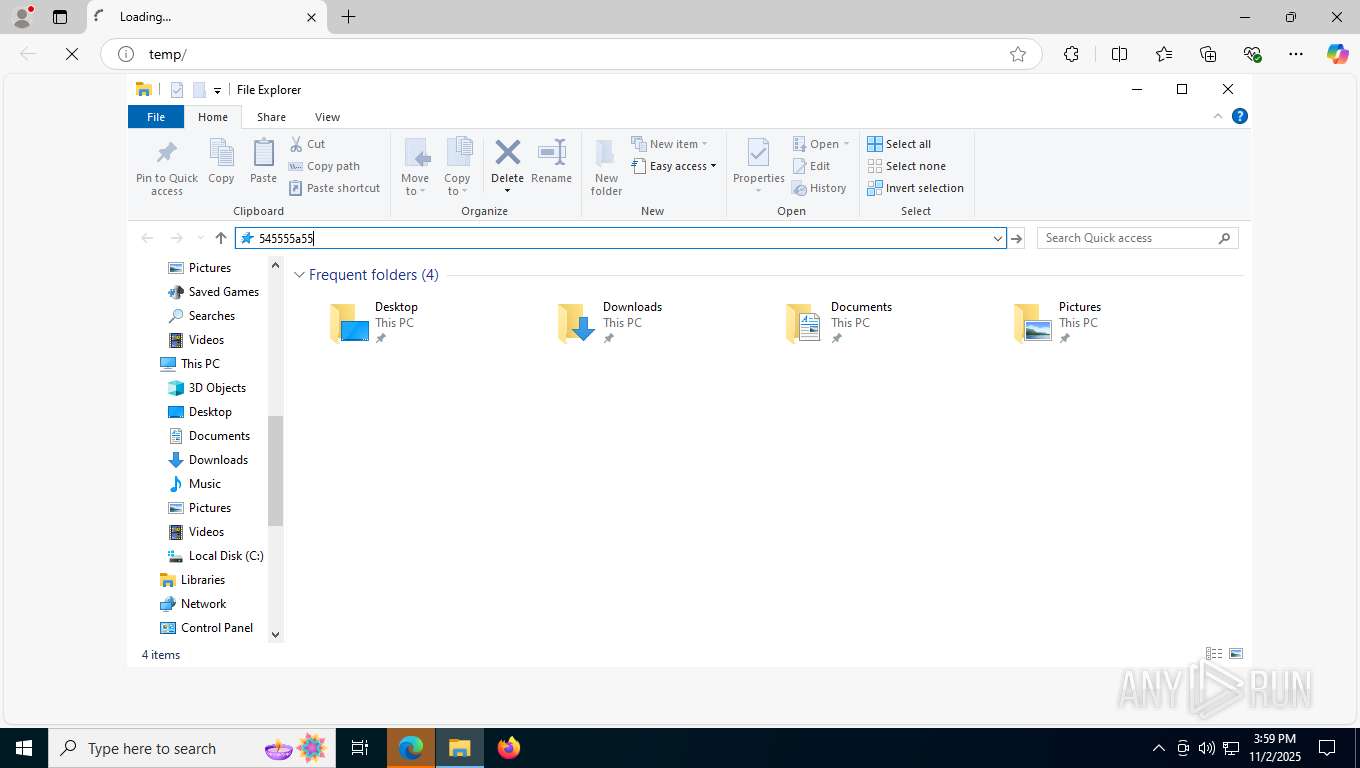
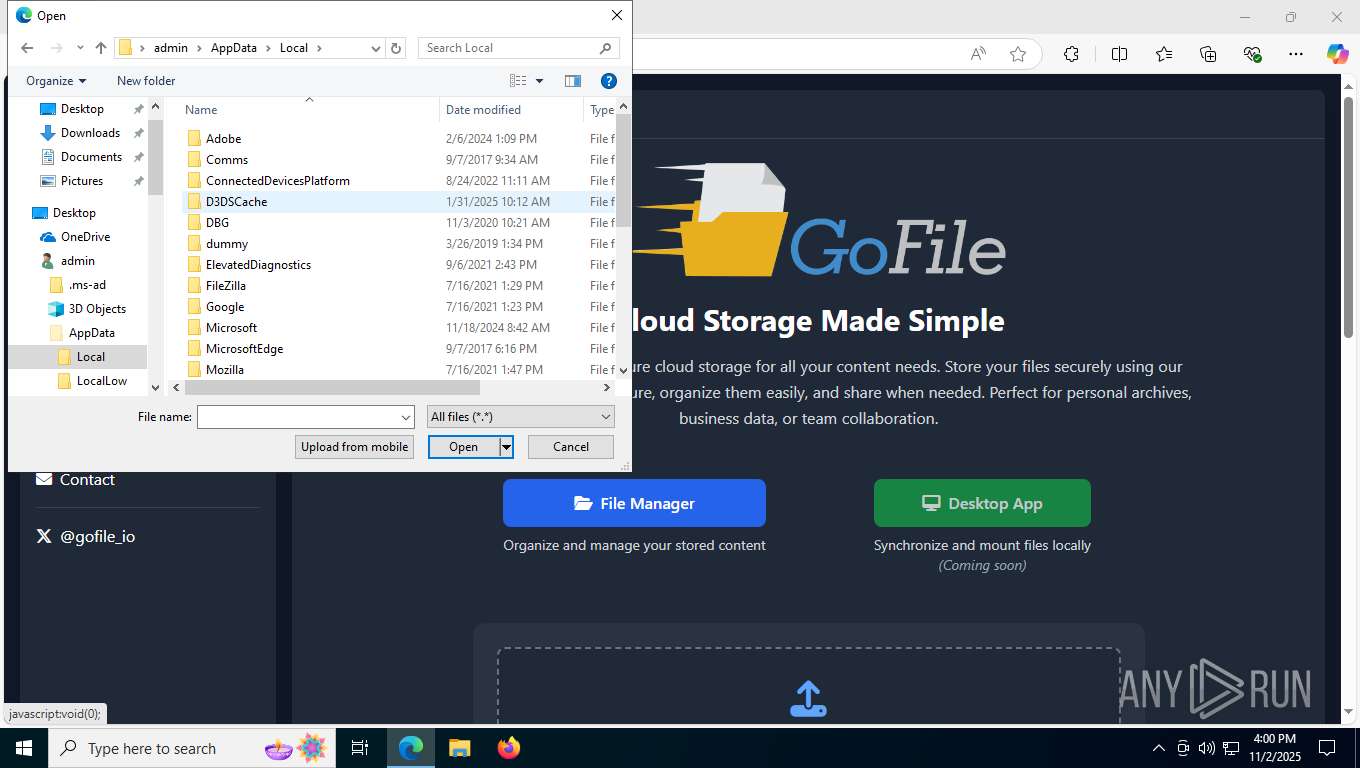
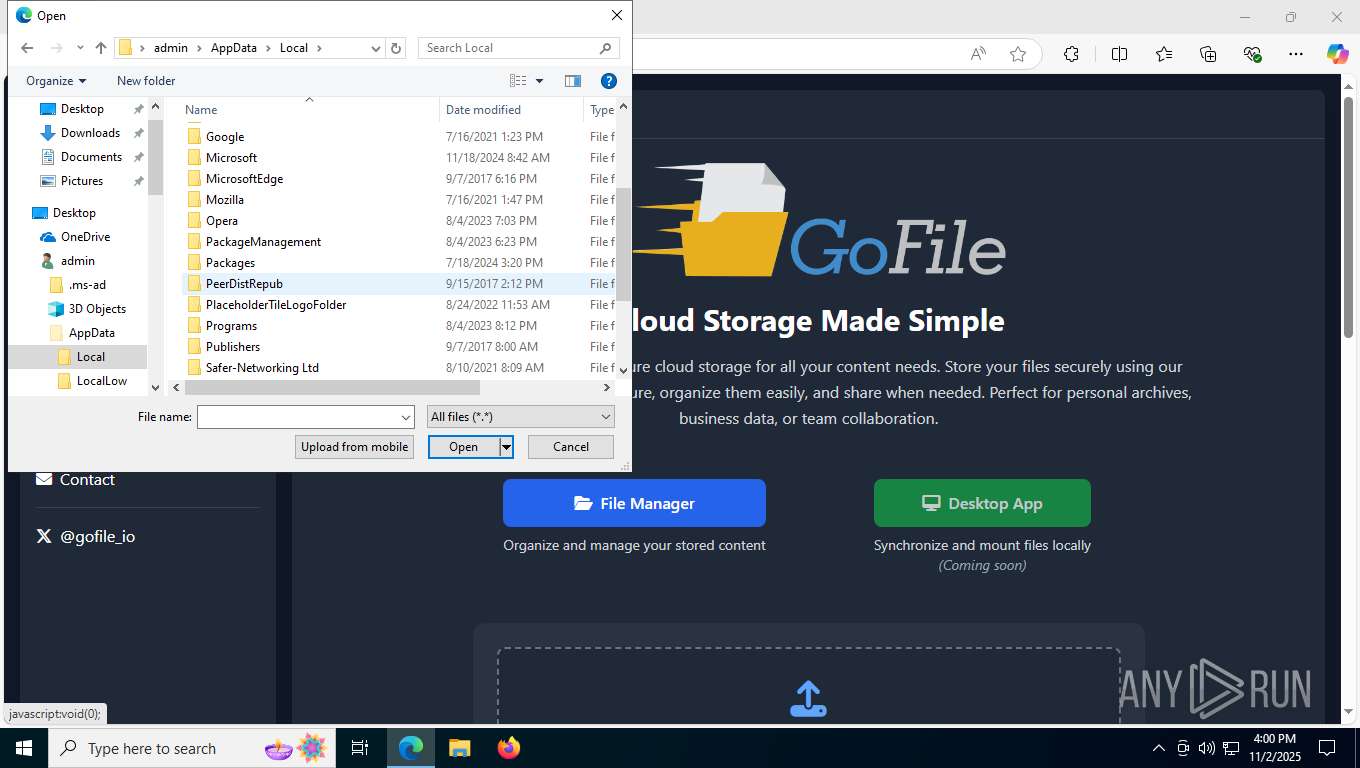
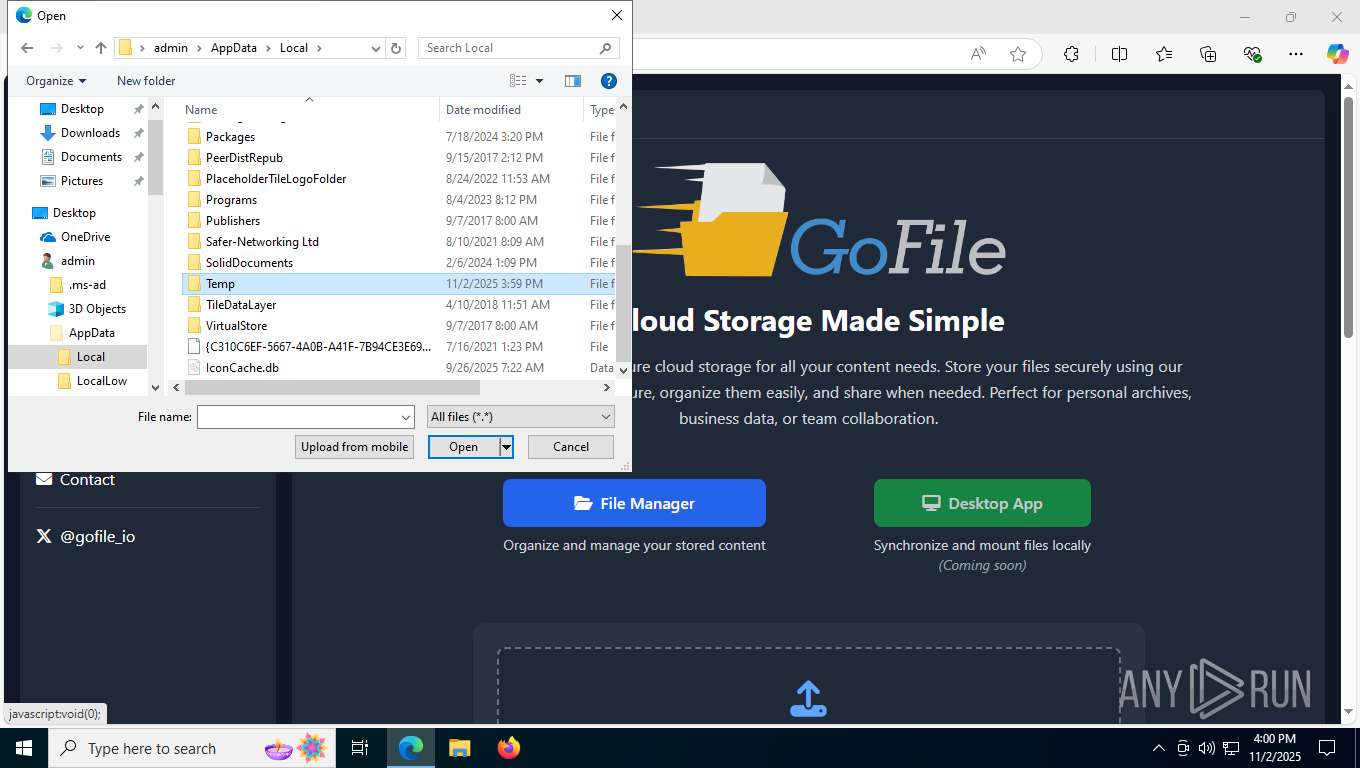
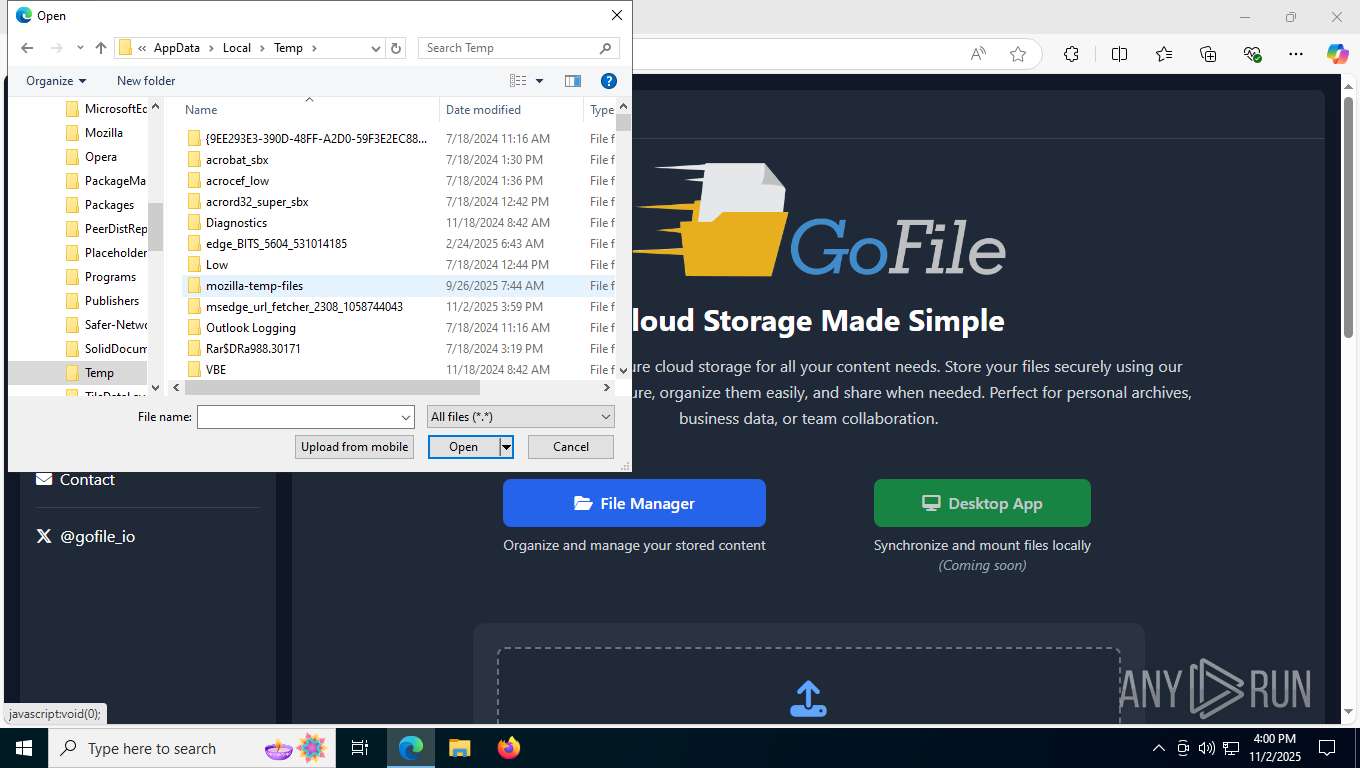
Create files in a temporary directory
- Volcano_Executor.exe (PID: 7608)
Process checks computer location settings
- Volcano_Executor.exe (PID: 7608)
- VolcanoUpdater.exe (PID: 7820)
Reads Environment values
- VolcanoCrashHandler.exe (PID: 7860)
- Client.exe (PID: 7960)
- identity_helper.exe (PID: 7544)
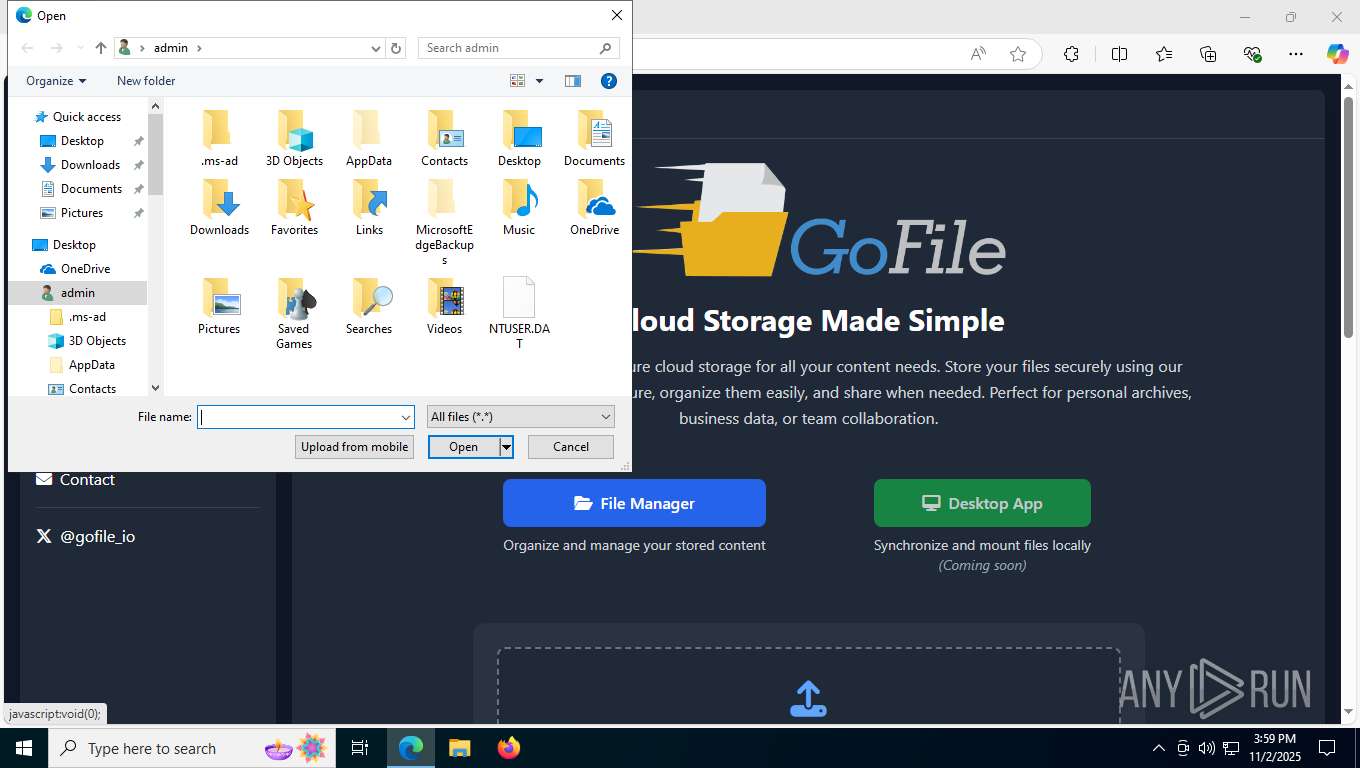
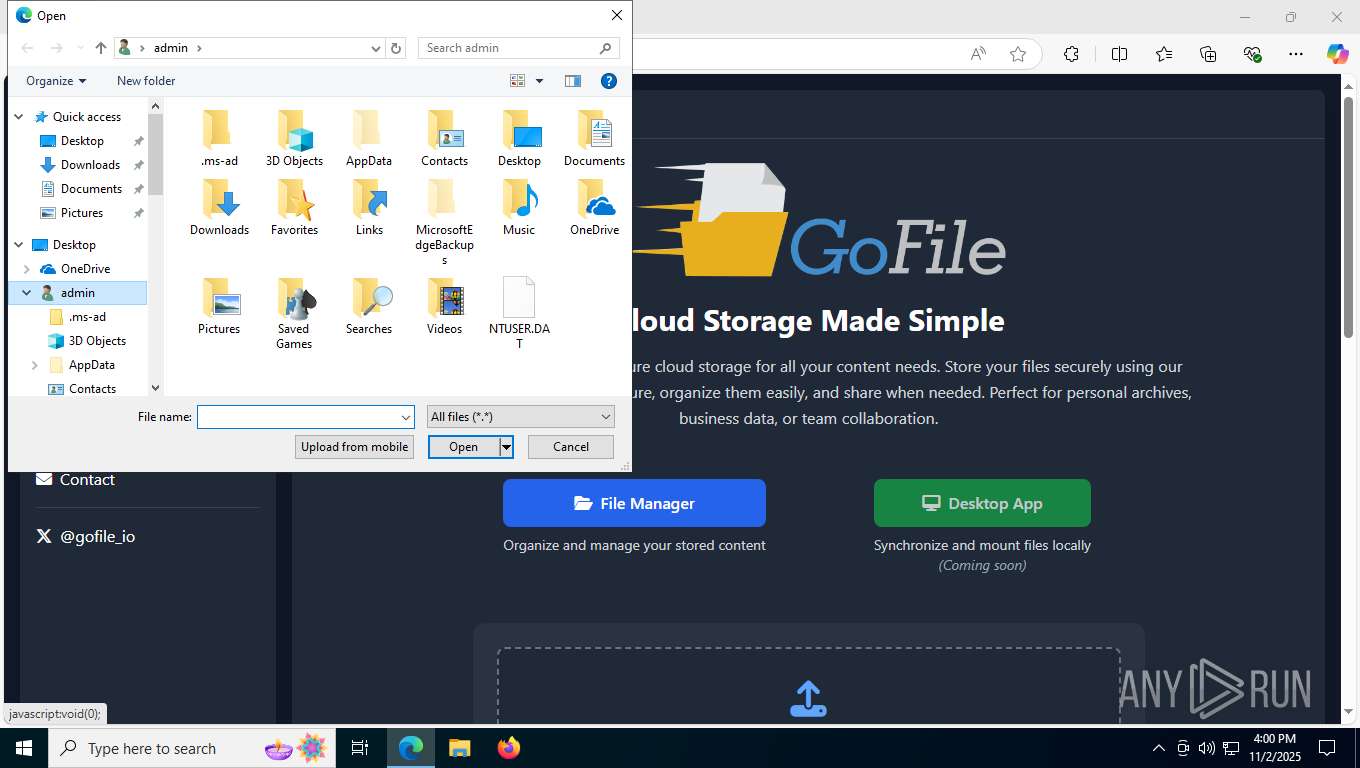
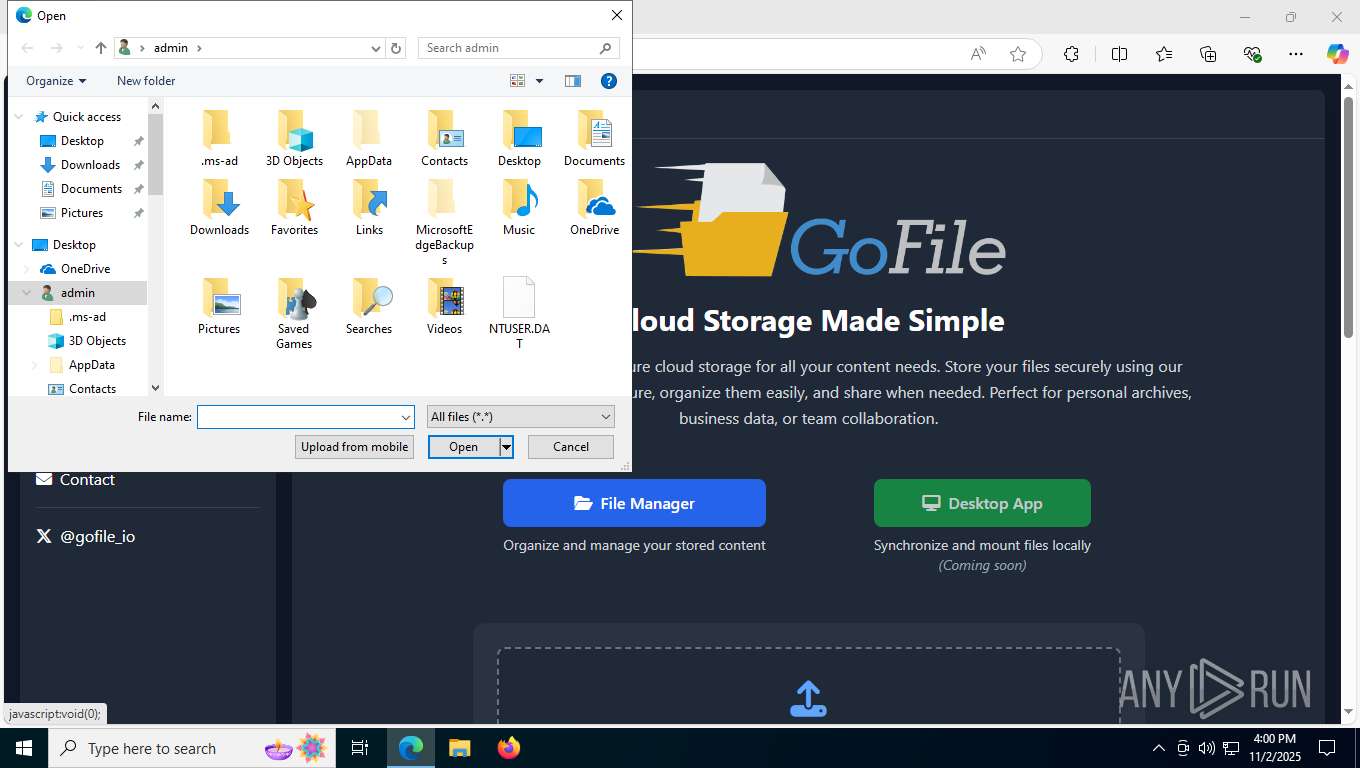
Creates files or folders in the user directory
- VolcanoCrashHandler.exe (PID: 7860)
Launching a file from a Registry key
- VolcanoCrashHandler.exe (PID: 7860)
- Client.exe (PID: 7960)
The sample compiled with english language support
- VolcanoUI.exe (PID: 8048)
Manual execution by a user
- msedge.exe (PID: 2308)
Application launched itself
- msedge.exe (PID: 2308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:11:02 02:24:12+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 5306880 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x51194e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | Volcano_Executor.exe |
| LegalCopyright: | |
| OriginalFileName: | Volcano_Executor.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
183
Monitored processes
35
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 224 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5900,i,15462513327911913303,11715174726206955599,262144 --variations-seed-version --mojo-platform-channel-handle=6008 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 988 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=20 --always-read-main-dll --field-trial-handle=5592,i,15462513327911913303,11715174726206955599,262144 --variations-seed-version --mojo-platform-channel-handle=6984 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=11 --always-read-main-dll --field-trial-handle=5148,i,15462513327911913303,11715174726206955599,262144 --variations-seed-version --mojo-platform-channel-handle=5704 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2276 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2308 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument http://temp/ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2312 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=10 --always-read-main-dll --field-trial-handle=5712,i,15462513327911913303,11715174726206955599,262144 --variations-seed-version --mojo-platform-channel-handle=5444 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2412 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7fff783af208,0x7fff783af214,0x7fff783af220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=9 --always-read-main-dll --field-trial-handle=4648,i,15462513327911913303,11715174726206955599,262144 --variations-seed-version --mojo-platform-channel-handle=4000 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4596 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5684,i,15462513327911913303,11715174726206955599,262144 --variations-seed-version --mojo-platform-channel-handle=5660 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4756 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1464,i,15462513327911913303,11715174726206955599,262144 --variations-seed-version --mojo-platform-channel-handle=6632 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
3 347
Read events
3 345
Write events
2
Delete events
0
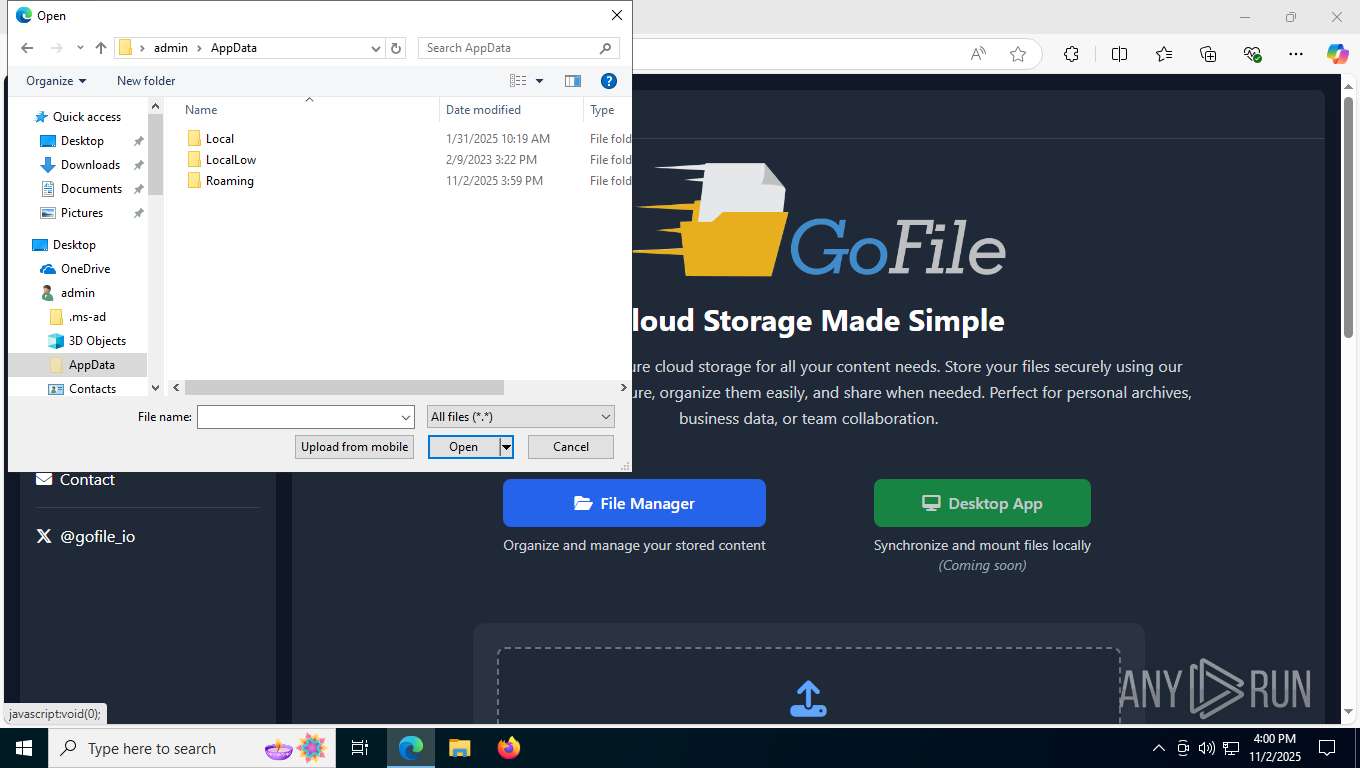
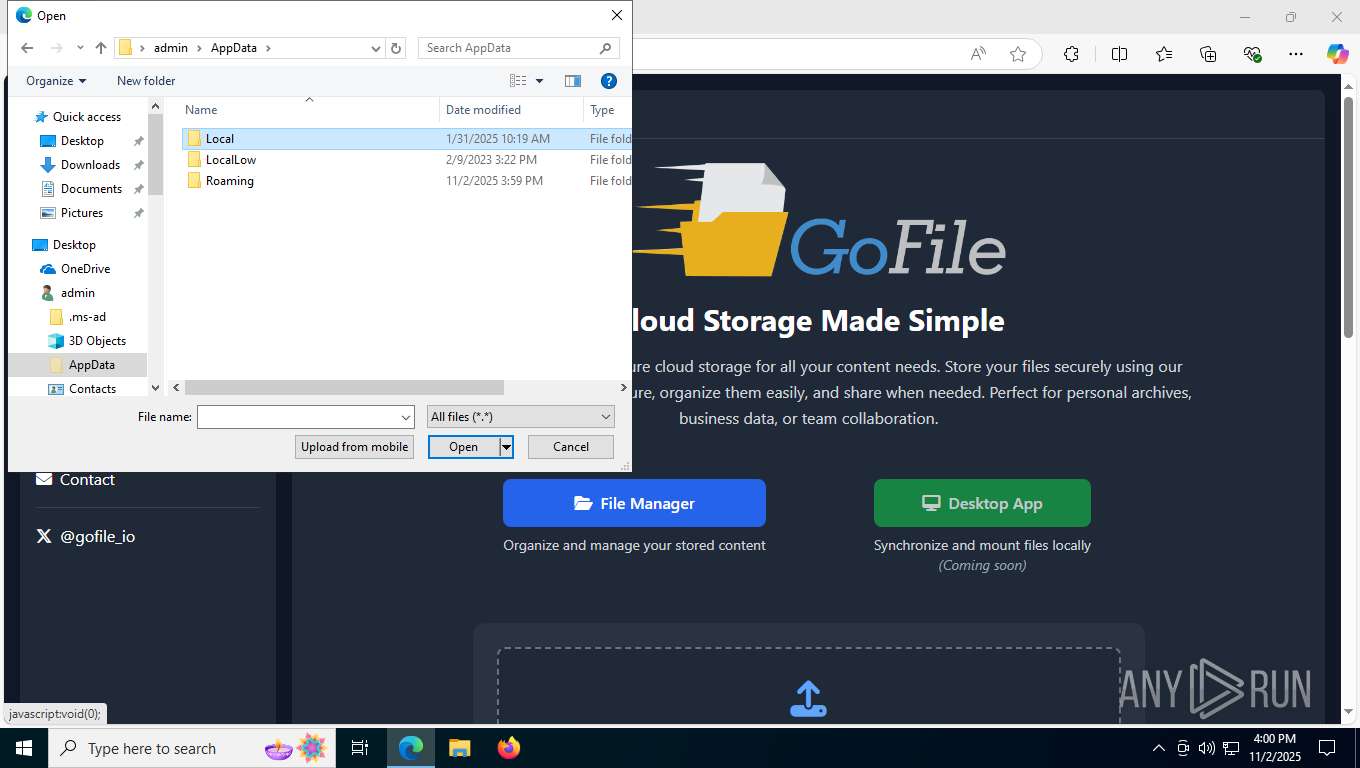
Modification events
| (PID) Process: | (7860) VolcanoCrashHandler.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftDefender |
Value: "C:\Users\admin\AppData\Roaming\SubDir\Client.exe" | |||
| (PID) Process: | (7960) Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftDefender |
Value: "C:\Users\admin\AppData\Roaming\SubDir\Client.exe" | |||
Executable files
14
Suspicious files
213
Text files
44
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF16db13.TMP | — | |
MD5:— | SHA256:— | |||
| 2308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF16db13.TMP | — | |
MD5:— | SHA256:— | |||
| 2308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF16db13.TMP | — | |
MD5:— | SHA256:— | |||
| 2308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF16db22.TMP | — | |
MD5:— | SHA256:— | |||
| 2308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF16db22.TMP | — | |
MD5:— | SHA256:— | |||
| 2308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
85
DNS requests
80
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
816 | lsass.exe | GET | 200 | 142.250.186.99:80 | http://c.pki.goog/r/r4.crl | US | binary | 530 b | whitelisted |
816 | lsass.exe | GET | 200 | 142.250.186.99:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
6836 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7456 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | whitelisted |
7456 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | DE | binary | 813 b | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 95.101.78.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7928 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:-zX8WsGFQroPIpPJg0yz3gpAZ7CZqHPmA6wptVYKfJw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 101 b | whitelisted |
7456 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | DE | binary | 401 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2116 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6836 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7088 | SearchApp.exe | 184.86.251.21:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7820 | VolcanoUpdater.exe | 104.21.56.14:443 | file.volcano.wtf | CLOUDFLARENET | — | unknown |
816 | lsass.exe | 142.250.186.99:80 | c.pki.goog | GOOGLE | US | whitelisted |
7960 | Client.exe | 147.185.221.16:7181 | side-char.gl.at.ply.gg | PLAYIT-GG | US | malicious |
8048 | VolcanoUI.exe | 104.21.56.14:443 | file.volcano.wtf | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
file.volcano.wtf |
| unknown |
c.pki.goog |
| whitelisted |
side-char.gl.at.ply.gg |
| unknown |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2276 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2276 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |
2276 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
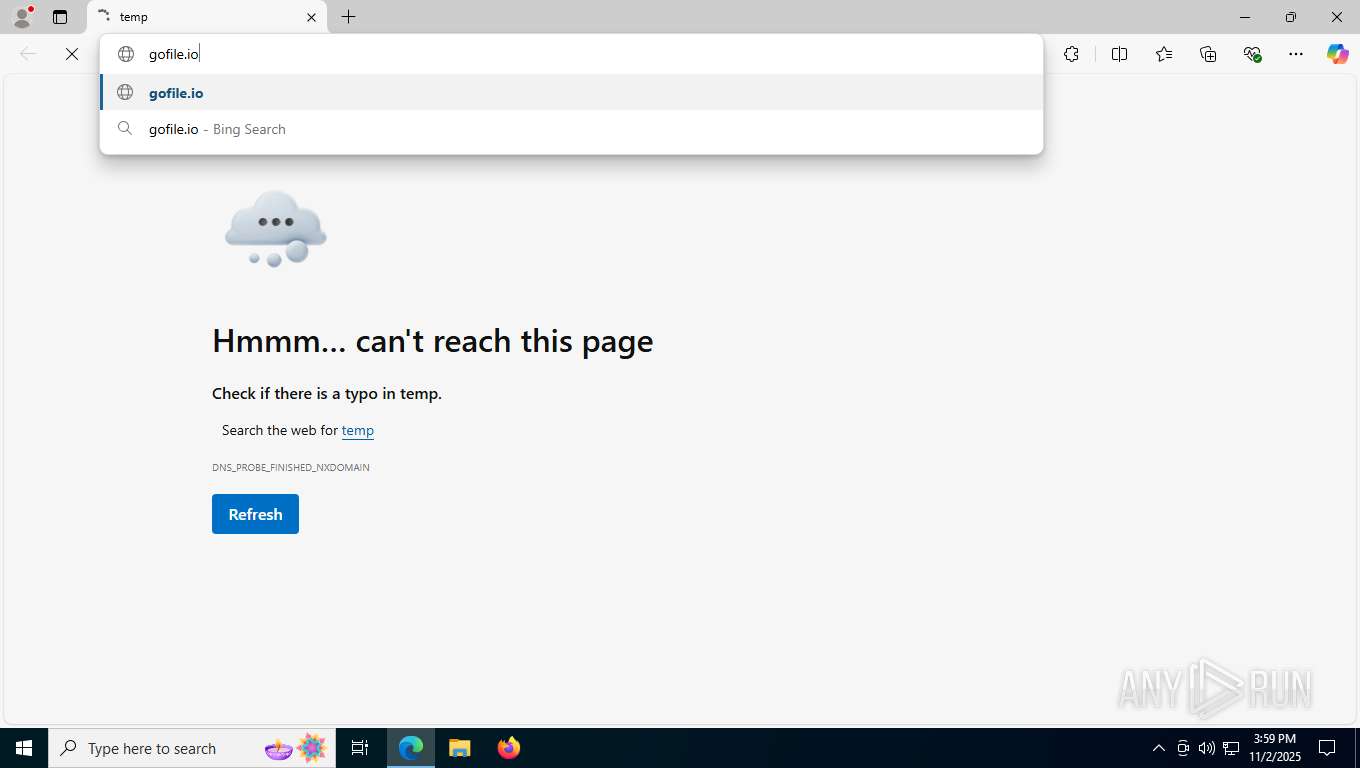
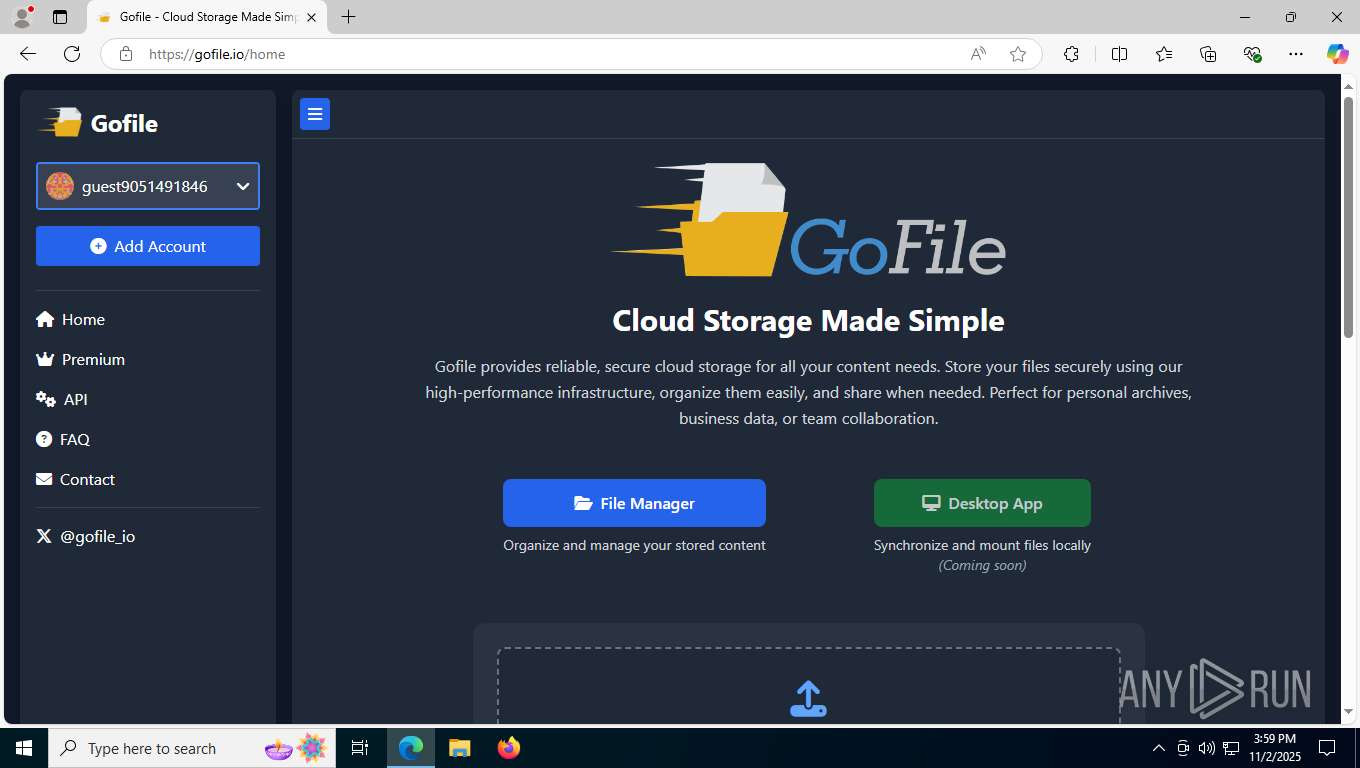
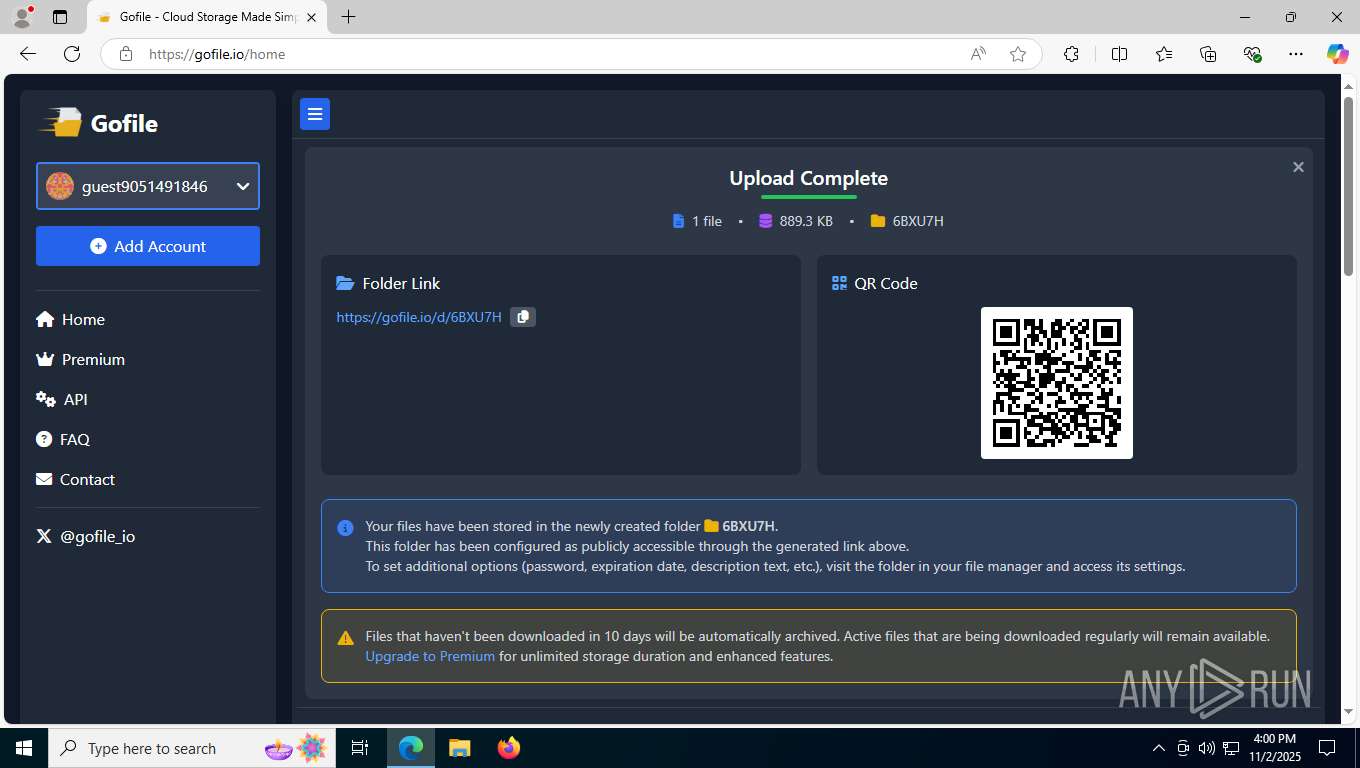
7928 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7928 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7928 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7928 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7928 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7928 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
Process | Message |
|---|---|
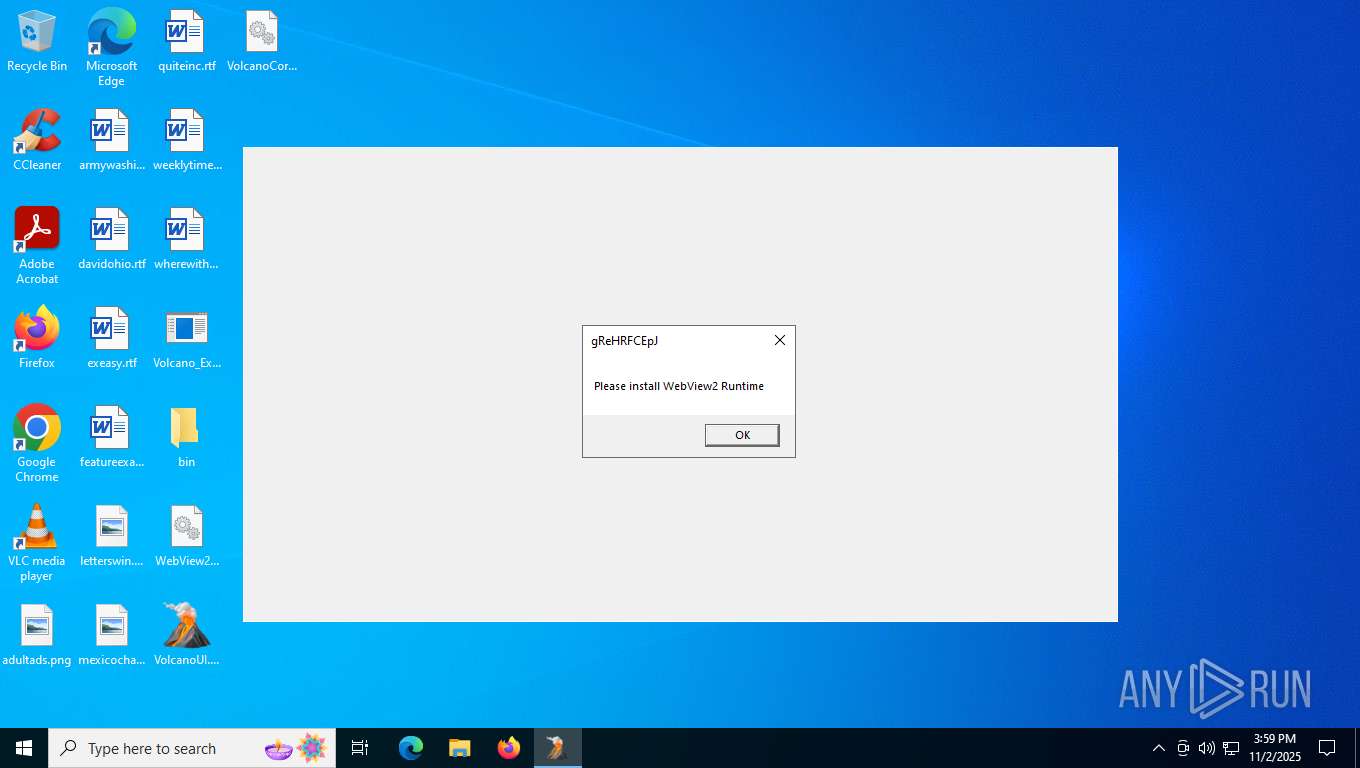
VolcanoUI.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
VolcanoUI.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|