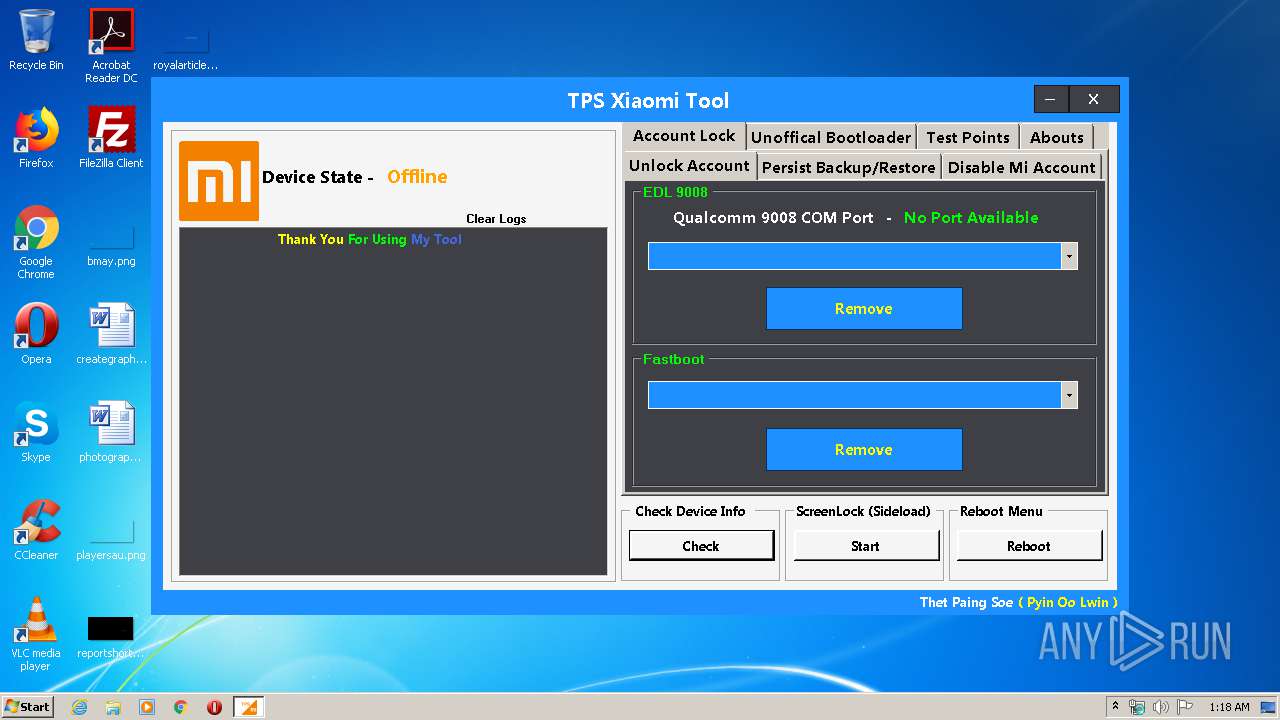
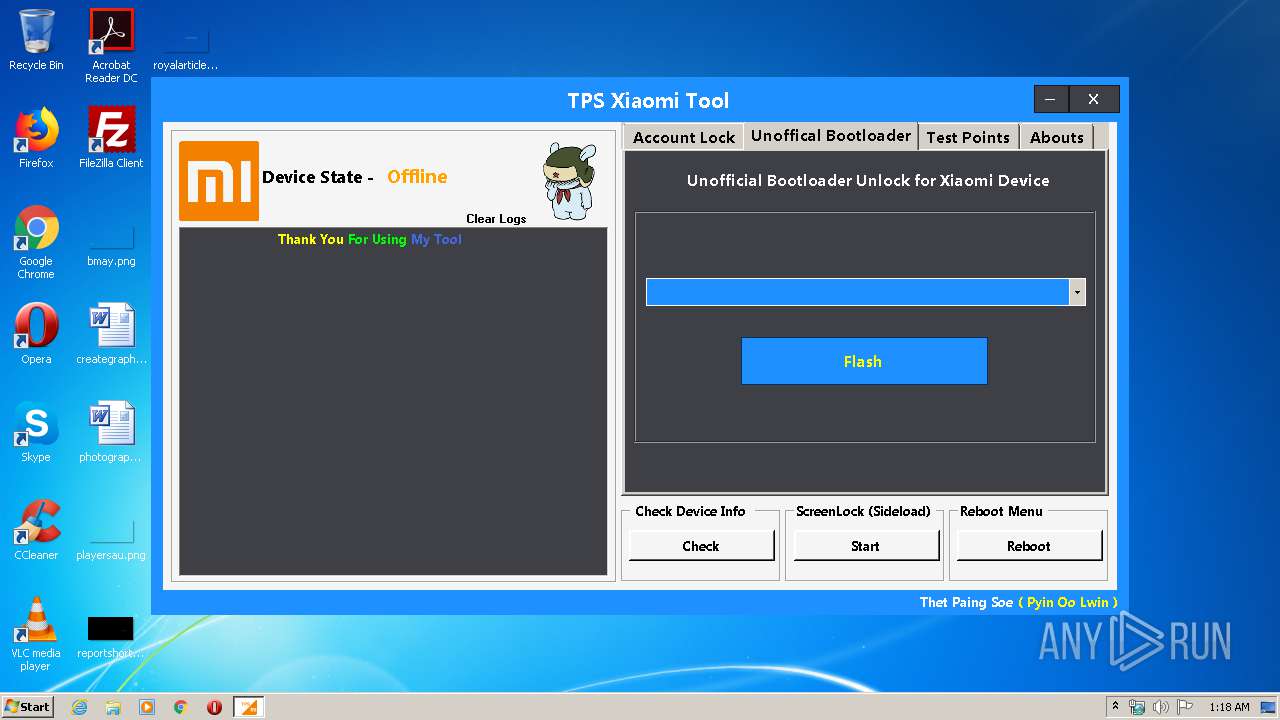
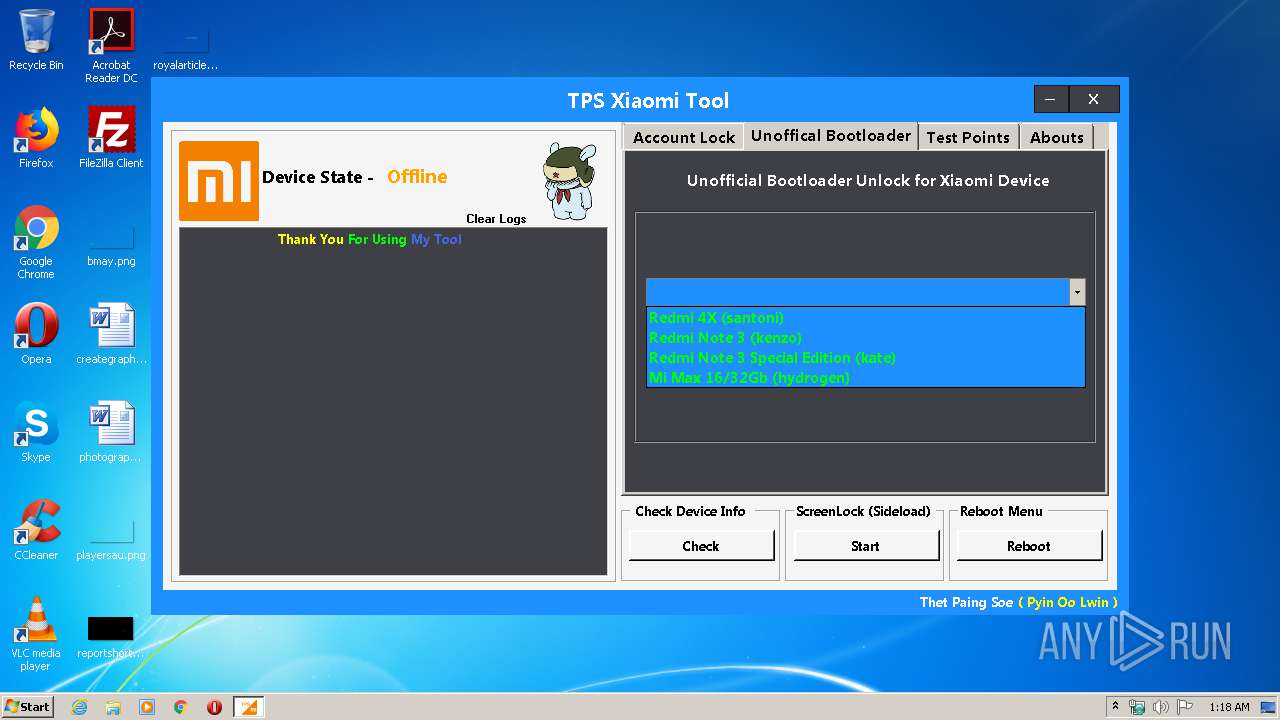
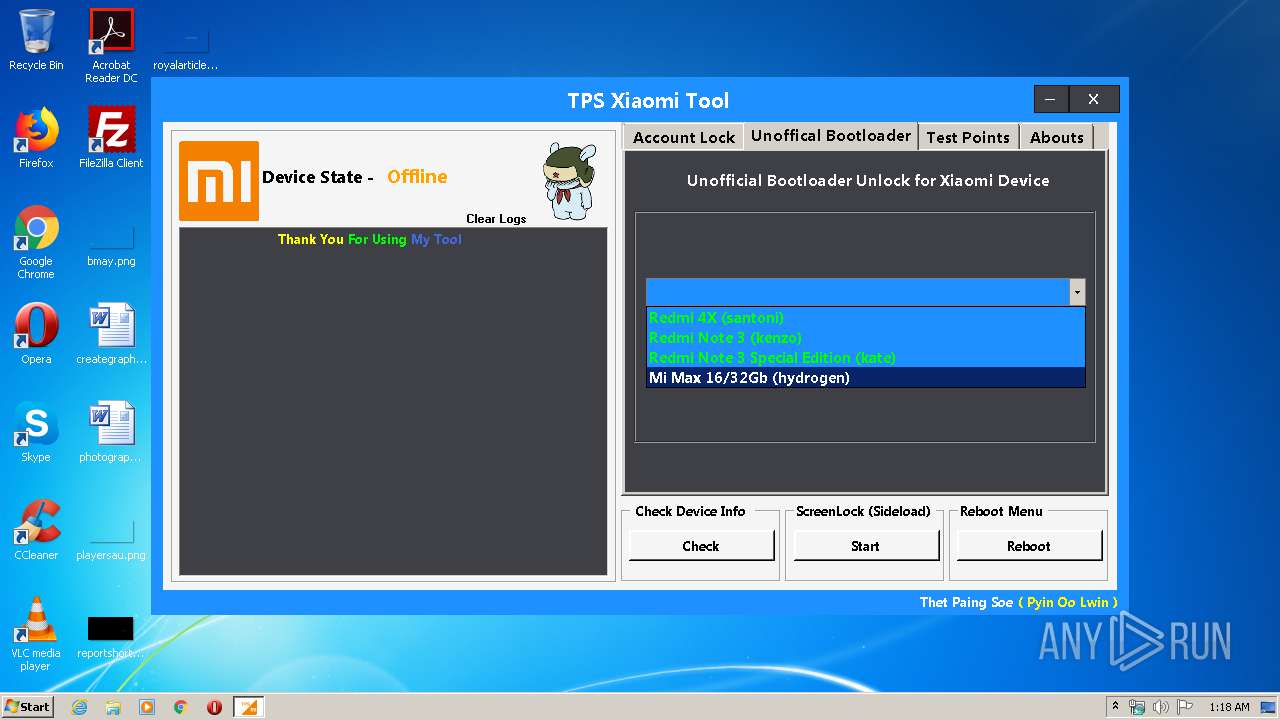
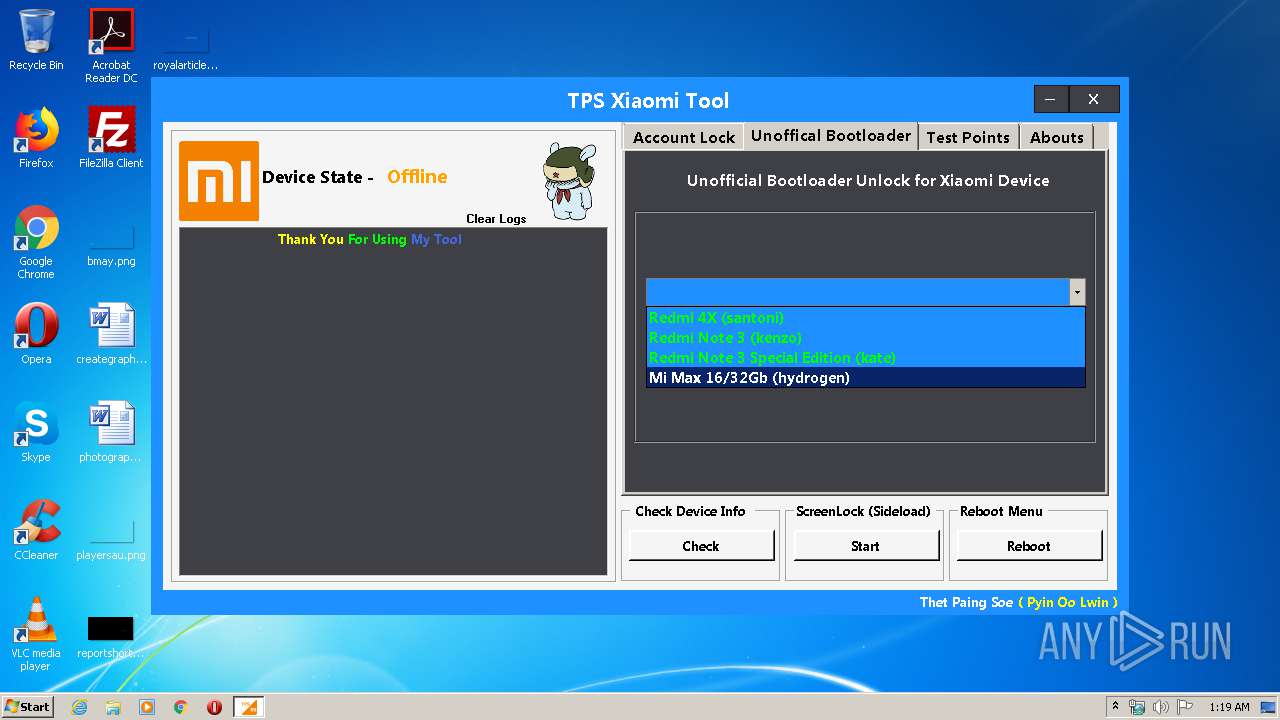
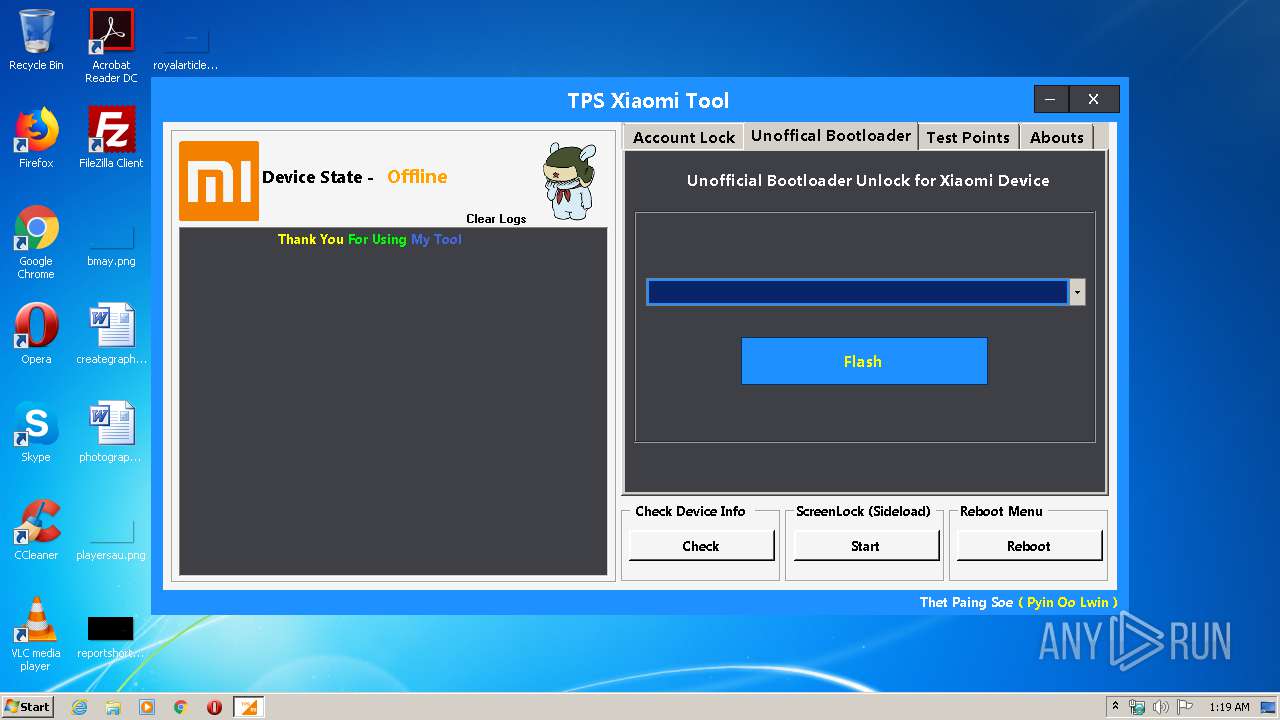
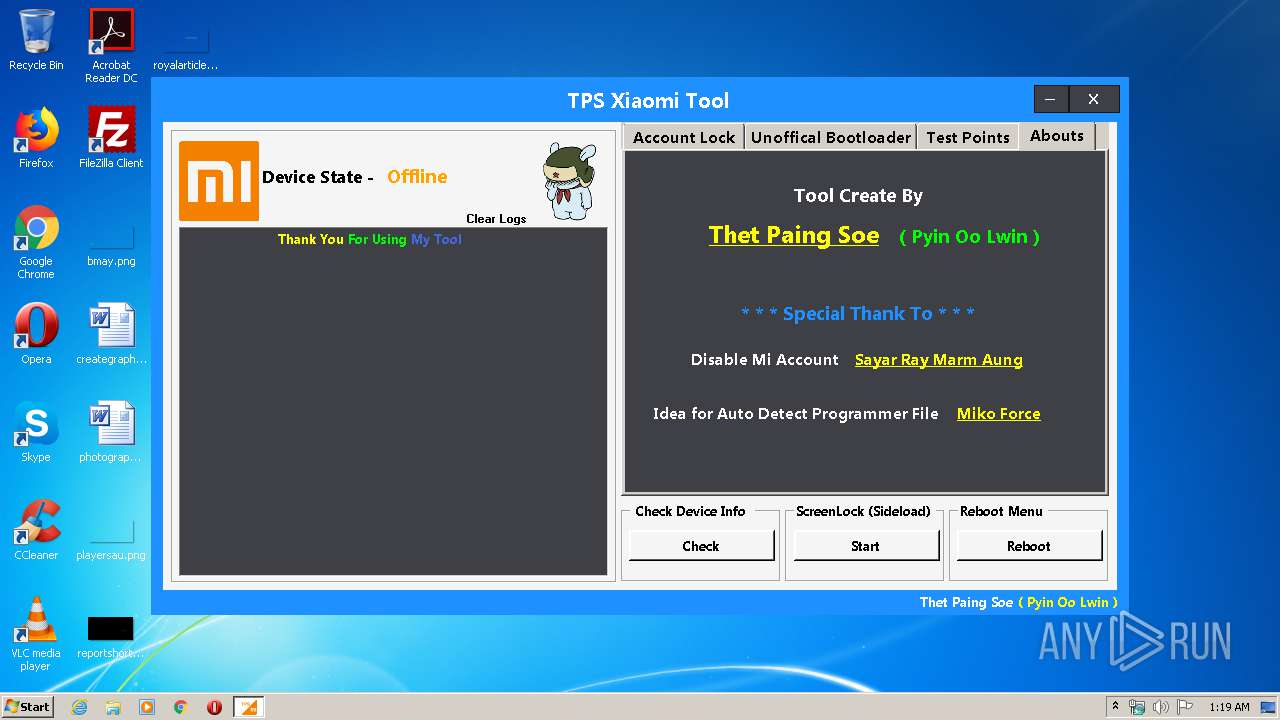
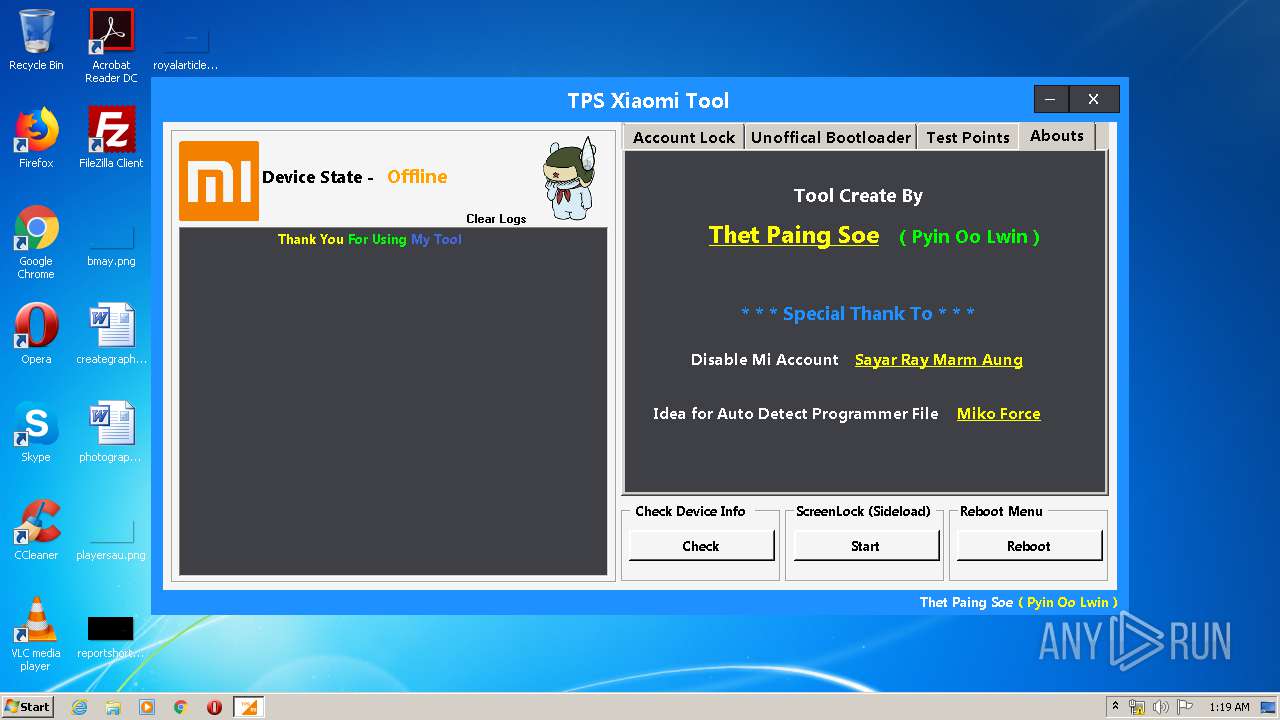
| File name: | TPS Xiaomi Tool.exe |
| Full analysis: | https://app.any.run/tasks/724d7d95-0949-4dab-b075-952d7b3dea60 |
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2020, 00:18:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 71B52678AFBE02F88BC172032EE076A3 |
| SHA1: | DC07501DDA620A780073A5B2085D4690E204FBA6 |
| SHA256: | 74FEADC84784D0DBA6681C4D4ECA3F4D61C9DEF81CE92DC1D344F98FEBB17AA6 |
| SSDEEP: | 196608:/c7Tq+c2LP/hFT93CCoiduA6oERhH0/2EqGijx:U7Tq+jVSdAwU6x |
MALICIOUS
Application was dropped or rewritten from another process
- adb.exe (PID: 2340)
- adb.exe (PID: 2440)
- emmcdl.exe (PID: 2412)
- fastboot.exe (PID: 3944)
- adb.exe (PID: 1296)
- Xiaomi Tool.exe (PID: 1400)
- fastboot.exe (PID: 2492)
- adb.exe (PID: 3352)
- emmcdl.exe (PID: 440)
- fastboot.exe (PID: 3196)
- adb.exe (PID: 1760)
- fastboot.exe (PID: 3240)
- adb.exe (PID: 3916)
- adb.exe (PID: 1848)
- adb.exe (PID: 3012)
- emmcdl.exe (PID: 2484)
- fastboot.exe (PID: 3384)
- emmcdl.exe (PID: 1340)
- emmcdl.exe (PID: 2628)
- adb.exe (PID: 2064)
- fastboot.exe (PID: 3296)
- adb.exe (PID: 3600)
- adb.exe (PID: 304)
- emmcdl.exe (PID: 3092)
- fastboot.exe (PID: 3372)
- emmcdl.exe (PID: 3800)
- fastboot.exe (PID: 3664)
- adb.exe (PID: 2708)
- fastboot.exe (PID: 3044)
- adb.exe (PID: 3588)
- emmcdl.exe (PID: 2712)
- fastboot.exe (PID: 3596)
- fastboot.exe (PID: 2248)
- adb.exe (PID: 2752)
- emmcdl.exe (PID: 3144)
- emmcdl.exe (PID: 3240)
- adb.exe (PID: 3004)
- fastboot.exe (PID: 2948)
- fastboot.exe (PID: 1464)
- emmcdl.exe (PID: 1840)
- fastboot.exe (PID: 2636)
- adb.exe (PID: 3876)
- adb.exe (PID: 3708)
- emmcdl.exe (PID: 1604)
- fastboot.exe (PID: 2064)
- adb.exe (PID: 3928)
- adb.exe (PID: 2488)
- fastboot.exe (PID: 3360)
- emmcdl.exe (PID: 2124)
- emmcdl.exe (PID: 2096)
- emmcdl.exe (PID: 3776)
- fastboot.exe (PID: 3748)
- adb.exe (PID: 3972)
- emmcdl.exe (PID: 3872)
- fastboot.exe (PID: 1296)
- emmcdl.exe (PID: 3016)
- fastboot.exe (PID: 2376)
- adb.exe (PID: 2968)
- emmcdl.exe (PID: 3976)
- emmcdl.exe (PID: 3760)
- adb.exe (PID: 2556)
- fastboot.exe (PID: 3744)
- adb.exe (PID: 2452)
- emmcdl.exe (PID: 2316)
- fastboot.exe (PID: 2780)
- emmcdl.exe (PID: 1876)
- adb.exe (PID: 4068)
- emmcdl.exe (PID: 3472)
- fastboot.exe (PID: 2776)
- adb.exe (PID: 4092)
- fastboot.exe (PID: 1544)
- emmcdl.exe (PID: 4000)
- fastboot.exe (PID: 3188)
- fastboot.exe (PID: 2800)
- emmcdl.exe (PID: 2456)
- fastboot.exe (PID: 480)
- emmcdl.exe (PID: 3704)
- adb.exe (PID: 1780)
- adb.exe (PID: 3588)
- emmcdl.exe (PID: 1784)
- fastboot.exe (PID: 2592)
- adb.exe (PID: 3992)
- adb.exe (PID: 1748)
- emmcdl.exe (PID: 2828)
- fastboot.exe (PID: 3196)
- emmcdl.exe (PID: 3372)
- adb.exe (PID: 4068)
- adb.exe (PID: 2956)
- fastboot.exe (PID: 3276)
- adb.exe (PID: 2248)
- fastboot.exe (PID: 2012)
- adb.exe (PID: 2752)
- fastboot.exe (PID: 3556)
- emmcdl.exe (PID: 2928)
- adb.exe (PID: 3816)
- adb.exe (PID: 2104)
- fastboot.exe (PID: 1812)
- emmcdl.exe (PID: 3160)
- fastboot.exe (PID: 968)
- emmcdl.exe (PID: 3464)
- adb.exe (PID: 2244)
- adb.exe (PID: 1428)
- fastboot.exe (PID: 2908)
- emmcdl.exe (PID: 1920)
- adb.exe (PID: 1844)
- fastboot.exe (PID: 3148)
- emmcdl.exe (PID: 1444)
- fastboot.exe (PID: 2500)
- emmcdl.exe (PID: 3596)
- adb.exe (PID: 3852)
- emmcdl.exe (PID: 3460)
- fastboot.exe (PID: 1008)
- emmcdl.exe (PID: 2900)
- adb.exe (PID: 2252)
- fastboot.exe (PID: 1464)
- emmcdl.exe (PID: 2368)
- adb.exe (PID: 3736)
- fastboot.exe (PID: 2432)
- emmcdl.exe (PID: 564)
- adb.exe (PID: 1708)
- fastboot.exe (PID: 1564)
- adb.exe (PID: 536)
- emmcdl.exe (PID: 3028)
- fastboot.exe (PID: 3052)
- emmcdl.exe (PID: 2296)
- adb.exe (PID: 3380)
- fastboot.exe (PID: 2732)
- emmcdl.exe (PID: 1252)
- adb.exe (PID: 1536)
- adb.exe (PID: 1084)
- emmcdl.exe (PID: 1388)
- emmcdl.exe (PID: 3720)
- adb.exe (PID: 3448)
- fastboot.exe (PID: 2636)
- fastboot.exe (PID: 3188)
- emmcdl.exe (PID: 2120)
- emmcdl.exe (PID: 956)
- adb.exe (PID: 404)
- fastboot.exe (PID: 2964)
- fastboot.exe (PID: 3704)
- emmcdl.exe (PID: 3912)
Loads dropped or rewritten executable
- fastboot.exe (PID: 3944)
- fastboot.exe (PID: 2492)
- adb.exe (PID: 2340)
- adb.exe (PID: 2440)
- adb.exe (PID: 1296)
- adb.exe (PID: 1848)
- fastboot.exe (PID: 3240)
- adb.exe (PID: 3352)
- adb.exe (PID: 1760)
- fastboot.exe (PID: 2636)
- adb.exe (PID: 3916)
- fastboot.exe (PID: 3384)
- adb.exe (PID: 3012)
- adb.exe (PID: 2064)
- adb.exe (PID: 3600)
- fastboot.exe (PID: 3372)
- adb.exe (PID: 304)
- fastboot.exe (PID: 3664)
- fastboot.exe (PID: 3296)
- adb.exe (PID: 2708)
- adb.exe (PID: 2752)
- adb.exe (PID: 3588)
- fastboot.exe (PID: 3596)
- fastboot.exe (PID: 2248)
- fastboot.exe (PID: 3044)
- adb.exe (PID: 3004)
- fastboot.exe (PID: 2948)
- adb.exe (PID: 3876)
- fastboot.exe (PID: 2064)
- adb.exe (PID: 3708)
- adb.exe (PID: 3928)
- fastboot.exe (PID: 3360)
- fastboot.exe (PID: 3196)
- adb.exe (PID: 2488)
- fastboot.exe (PID: 3748)
- adb.exe (PID: 3972)
- fastboot.exe (PID: 2376)
- adb.exe (PID: 2968)
- fastboot.exe (PID: 1296)
- adb.exe (PID: 2556)
- fastboot.exe (PID: 3744)
- adb.exe (PID: 2452)
- fastboot.exe (PID: 2780)
- adb.exe (PID: 4068)
- fastboot.exe (PID: 2776)
- adb.exe (PID: 4092)
- fastboot.exe (PID: 1544)
- fastboot.exe (PID: 3188)
- adb.exe (PID: 1748)
- fastboot.exe (PID: 2800)
- adb.exe (PID: 3588)
- fastboot.exe (PID: 480)
- fastboot.exe (PID: 1464)
- adb.exe (PID: 1780)
- adb.exe (PID: 3992)
- fastboot.exe (PID: 2592)
- fastboot.exe (PID: 3196)
- adb.exe (PID: 4068)
- adb.exe (PID: 2956)
- fastboot.exe (PID: 3276)
- fastboot.exe (PID: 2012)
- adb.exe (PID: 2752)
- fastboot.exe (PID: 3556)
- adb.exe (PID: 3816)
- fastboot.exe (PID: 1812)
- adb.exe (PID: 2104)
- fastboot.exe (PID: 968)
- adb.exe (PID: 2248)
- adb.exe (PID: 2244)
- fastboot.exe (PID: 2908)
- adb.exe (PID: 1428)
- fastboot.exe (PID: 3148)
- fastboot.exe (PID: 2500)
- fastboot.exe (PID: 1008)
- adb.exe (PID: 3852)
- fastboot.exe (PID: 1464)
- adb.exe (PID: 2252)
- adb.exe (PID: 3736)
- fastboot.exe (PID: 2432)
- fastboot.exe (PID: 1564)
- fastboot.exe (PID: 3052)
- adb.exe (PID: 536)
- fastboot.exe (PID: 2732)
- adb.exe (PID: 3380)
- adb.exe (PID: 1536)
- adb.exe (PID: 1708)
- fastboot.exe (PID: 2964)
- adb.exe (PID: 1084)
- fastboot.exe (PID: 2636)
- adb.exe (PID: 3448)
- fastboot.exe (PID: 3188)
- adb.exe (PID: 404)
- adb.exe (PID: 1844)
SUSPICIOUS
Executable content was dropped or overwritten
- TPS Xiaomi Tool.exe (PID: 3224)
Application launched itself
- adb.exe (PID: 2340)
- adb.exe (PID: 3352)
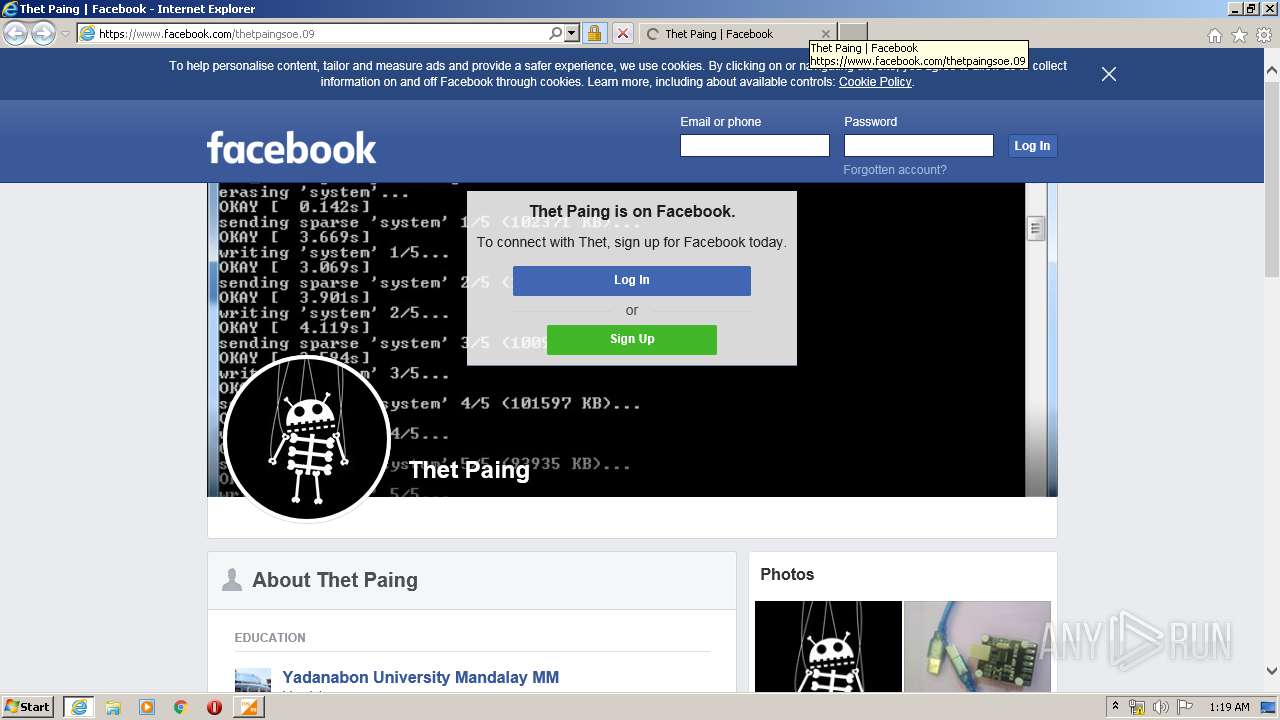
Starts Internet Explorer
- Xiaomi Tool.exe (PID: 1400)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3760)
Reads Internet Cache Settings
- iexplore.exe (PID: 3760)
- iexplore.exe (PID: 3980)
Application launched itself
- iexplore.exe (PID: 3760)
Reads internet explorer settings
- iexplore.exe (PID: 3980)
Dropped object may contain TOR URL's
- iexplore.exe (PID: 3980)
Reads settings of System Certificates
- iexplore.exe (PID: 3980)
- iexplore.exe (PID: 3760)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3760)
Changes settings of System certificates
- iexplore.exe (PID: 3760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:02:03 20:38:25+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 169984 |
| InitializedDataSize: | 784384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e64b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Feb-2016 19:38:25 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 03-Feb-2016 19:38:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00029604 | 0x00029800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.7094 |
.rdata | 0x0002B000 | 0x000058A3 | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.09421 |
.data | 0x00031000 | 0x00021608 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.58964 |
.rsrc | 0x00053000 | 0x000B8544 | 0x000B8600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.58497 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 1.9858 | 270376 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 2.15448 | 67624 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 2.31235 | 38056 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 2.50636 | 16936 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 2.7127 | 9640 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.15447 | 494 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
324
Monitored processes
145
Malicious processes
6
Suspicious processes
89
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "bin\adb.exe" devices | C:\Users\admin\AppData\Local\Temp\RarSFX0\bin\adb.exe | Xiaomi Tool.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 404 | "bin\adb.exe" devices | C:\Users\admin\AppData\Local\Temp\RarSFX0\bin\adb.exe | Xiaomi Tool.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 440 | "bin\emmcdl.exe" -l | C:\Users\admin\AppData\Local\Temp\RarSFX0\bin\emmcdl.exe | — | Xiaomi Tool.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 480 | "bin\fastboot.exe" devices | C:\Users\admin\AppData\Local\Temp\RarSFX0\bin\fastboot.exe | — | Xiaomi Tool.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 536 | "bin\adb.exe" devices | C:\Users\admin\AppData\Local\Temp\RarSFX0\bin\adb.exe | Xiaomi Tool.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 564 | "bin\emmcdl.exe" -l | C:\Users\admin\AppData\Local\Temp\RarSFX0\bin\emmcdl.exe | — | Xiaomi Tool.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 956 | "bin\emmcdl.exe" -l | C:\Users\admin\AppData\Local\Temp\RarSFX0\bin\emmcdl.exe | — | Xiaomi Tool.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 968 | "bin\fastboot.exe" devices | C:\Users\admin\AppData\Local\Temp\RarSFX0\bin\fastboot.exe | — | Xiaomi Tool.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1008 | "bin\fastboot.exe" devices | C:\Users\admin\AppData\Local\Temp\RarSFX0\bin\fastboot.exe | — | Xiaomi Tool.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1084 | "bin\adb.exe" devices | C:\Users\admin\AppData\Local\Temp\RarSFX0\bin\adb.exe | Xiaomi Tool.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 042
Read events
1 164
Write events
607
Delete events
271
Modification events
| (PID) Process: | (3224) TPS Xiaomi Tool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3224) TPS Xiaomi Tool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1400) Xiaomi Tool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000EE67F9C99730D601 | |||
| (PID) Process: | (3760) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3689971736 | |||
| (PID) Process: | (3760) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30814359 | |||
| (PID) Process: | (3760) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3760) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3760) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3760) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3760) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
7
Suspicious files
16
Text files
120
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | TPS Xiaomi Tool.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\prog\prog_emmc_firehose_8992_ddr.mbn | binary | |
MD5:D0AB72BF8C0E501E2EC493C20BC8FD06 | SHA256:E4B1C94C7FD74196BCC86E650865EB919B77CAD83B0F128F0352B0B747297CCC | |||
| 3224 | TPS Xiaomi Tool.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\prog\prog_ufs_firehose_8996_ddr.elf | o | |
MD5:35565A86464A35FDCE4A192D6CECAABF | SHA256:74097D3BE3CA0A28A38FACA668704190993AFCF8FE1EC73A44EBC19DE0585F2B | |||
| 3224 | TPS Xiaomi Tool.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\prog\prog_emmc_firehose_8976_ddr.mbn | o | |
MD5:8391F1D9FC965F0F5B3954BCC8955398 | SHA256:A95B538AD6838BC3DD47CD5BDD54D901EF063561EB1E902A34FC3B0A19D0DF3F | |||
| 3224 | TPS Xiaomi Tool.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\prog\prog_emmc_firehose_8974.mbn | binary | |
MD5:74F11B10B33C1988494B947C64A006B8 | SHA256:964B5C486B200AA6462733A682F9CEAD3EBFAD555CE2FF3622FEA8B279B006EE | |||
| 3224 | TPS Xiaomi Tool.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\prog\prog_emmc_firehose_8953_ddr.mbn | o | |
MD5:7432B18B3DE13A4006CD18456926DA4A | SHA256:9F4F747E6B34AD4367C8D2A16939FDAC98EF1F99135C0EE3C804E764B3290926 | |||
| 3224 | TPS Xiaomi Tool.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\prog\prog_emmc_firehose_8953.mbn | o | |
MD5:328B4F0F88F79CF718318FDCE7A05223 | SHA256:106DA54E2B265E89A9A8990FBA09F2B5DD31827908620A54A955FD13B3AE146A | |||
| 3224 | TPS Xiaomi Tool.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\prog\prog_emmc_firehose_8917_ddr.mbn | o | |
MD5:0C9D056A3B7EBE489CB9277BD2943902 | SHA256:8FE42241E7710A29D2723DEBDB2D6C8AC44432FF3EDFABA3BF45F4EEF25AA3A8 | |||
| 3224 | TPS Xiaomi Tool.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\prog\prog_ufs_firehose_8996.elf | o | |
MD5:03622174F2483AC36702C260A640D5BD | SHA256:4DF0F3BA55CEDDBC119C8B5F12BCC2AAEE4D204517CB29FDACF6F14B6390BFA7 | |||
| 3224 | TPS Xiaomi Tool.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\prog\prog_emmc_firehose_8994_lite.mbn | binary | |
MD5:6F0A28E0C69F312D5F16F653C62D1E30 | SHA256:3D35069A713D0A2B54BB661A68AAB69E380F8A72FB195129C7E262F0132A2CA8 | |||
| 3224 | TPS Xiaomi Tool.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\TestPoints\Aries | image | |
MD5:694EE2CA1A5C5FD25EC9789B1B63DD41 | SHA256:5E50F6A0B0AF61BDF787DA9747C86A320FD84453CC08573FF088E720F6613AAB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
40
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3980 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAlYH7M%2B8vLc4AsLWUhBAKk%3D | US | der | 471 b | whitelisted |
3980 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA6O%2BBjVXZc2rpJ%2B516RAgc%3D | US | der | 471 b | whitelisted |
3980 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAlYH7M%2B8vLc4AsLWUhBAKk%3D | US | der | 471 b | whitelisted |
3980 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA6O%2BBjVXZc2rpJ%2B516RAgc%3D | US | der | 471 b | whitelisted |
3980 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3980 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3760 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3980 | iexplore.exe | 157.240.20.35:443 | facebook.com | Facebook, Inc. | US | whitelisted |
3980 | iexplore.exe | 157.240.20.19:443 | static.xx.fbcdn.net | Facebook, Inc. | US | whitelisted |
3980 | iexplore.exe | 157.240.1.23:443 | scontent-lht6-1.xx.fbcdn.net | Facebook, Inc. | US | whitelisted |
3760 | iexplore.exe | 204.79.197.200:80 | www.facebook.com | Microsoft Corporation | US | whitelisted |
3980 | iexplore.exe | 157.240.221.16:443 | scontent-lhr8-1.xx.fbcdn.net | — | US | unknown |
— | — | 157.240.20.19:443 | static.xx.fbcdn.net | Facebook, Inc. | US | whitelisted |
3980 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.facebook.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
static.xx.fbcdn.net |
| whitelisted |
scontent-lht6-1.xx.fbcdn.net |
| whitelisted |
scontent-lhr8-1.xx.fbcdn.net |
| whitelisted |
external-lht6-1.xx.fbcdn.net |
| whitelisted |
facebook.com |
| whitelisted |
fbcdn.net |
| whitelisted |