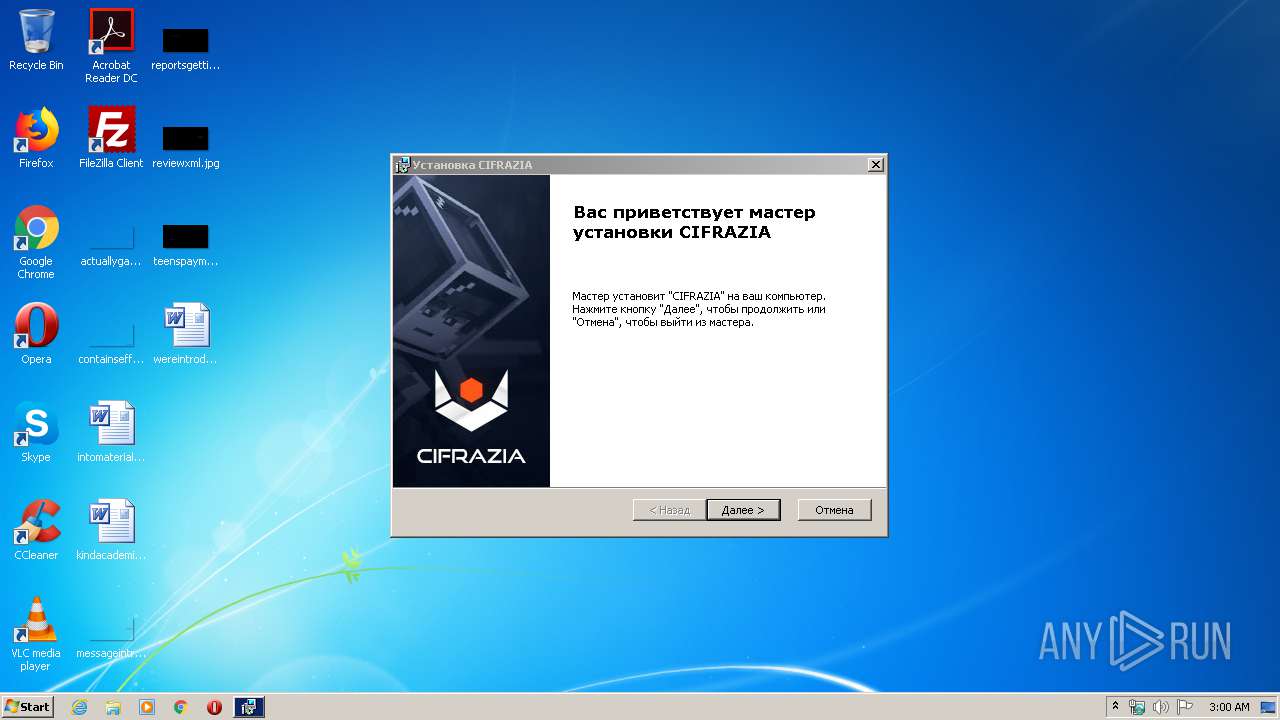
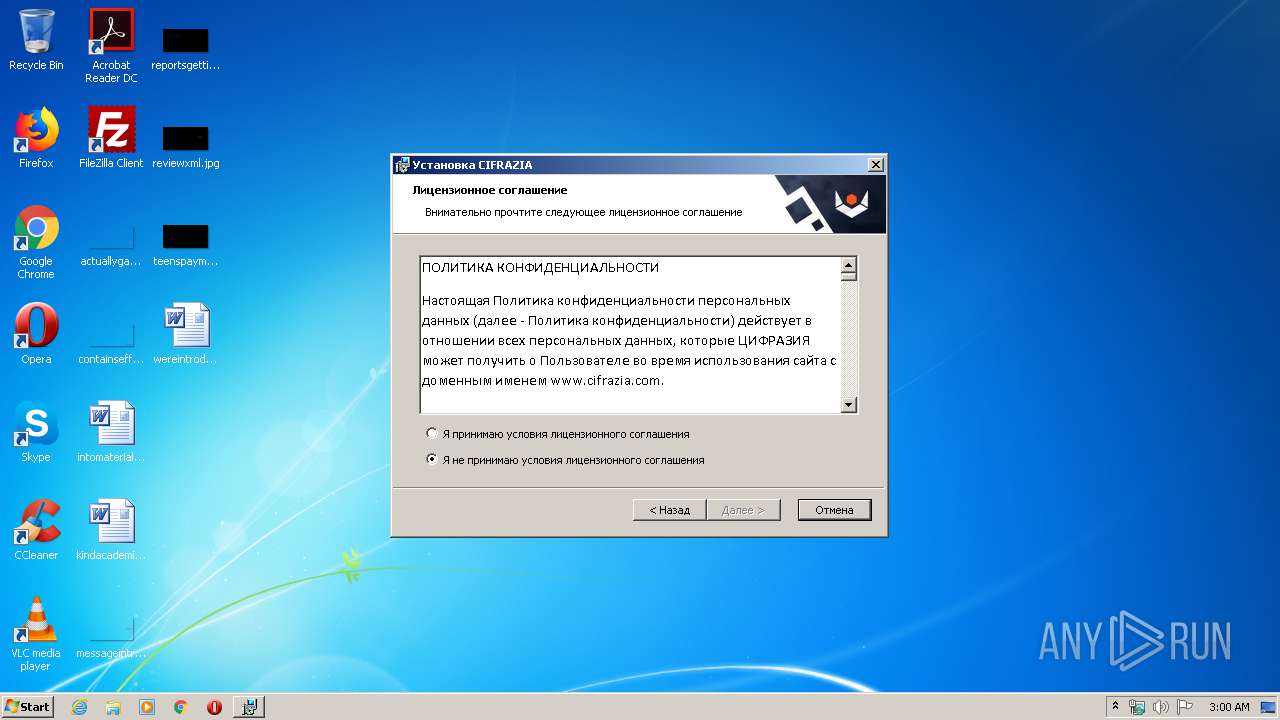
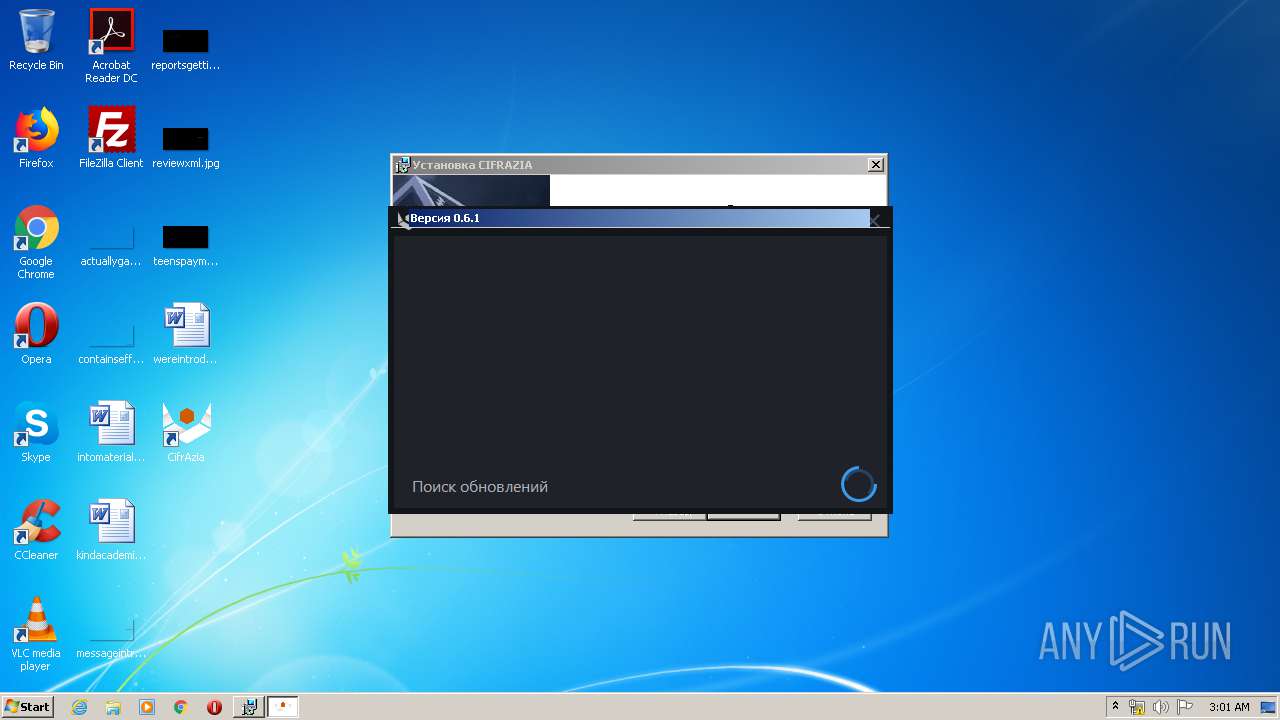
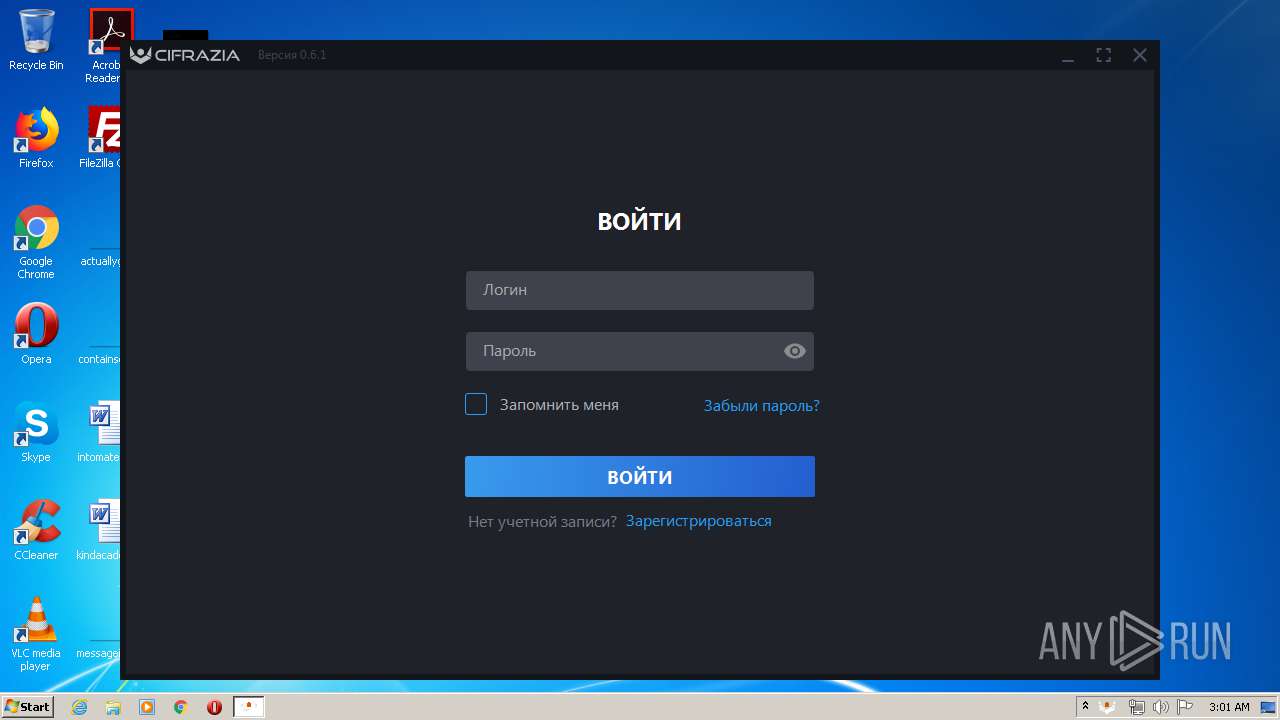
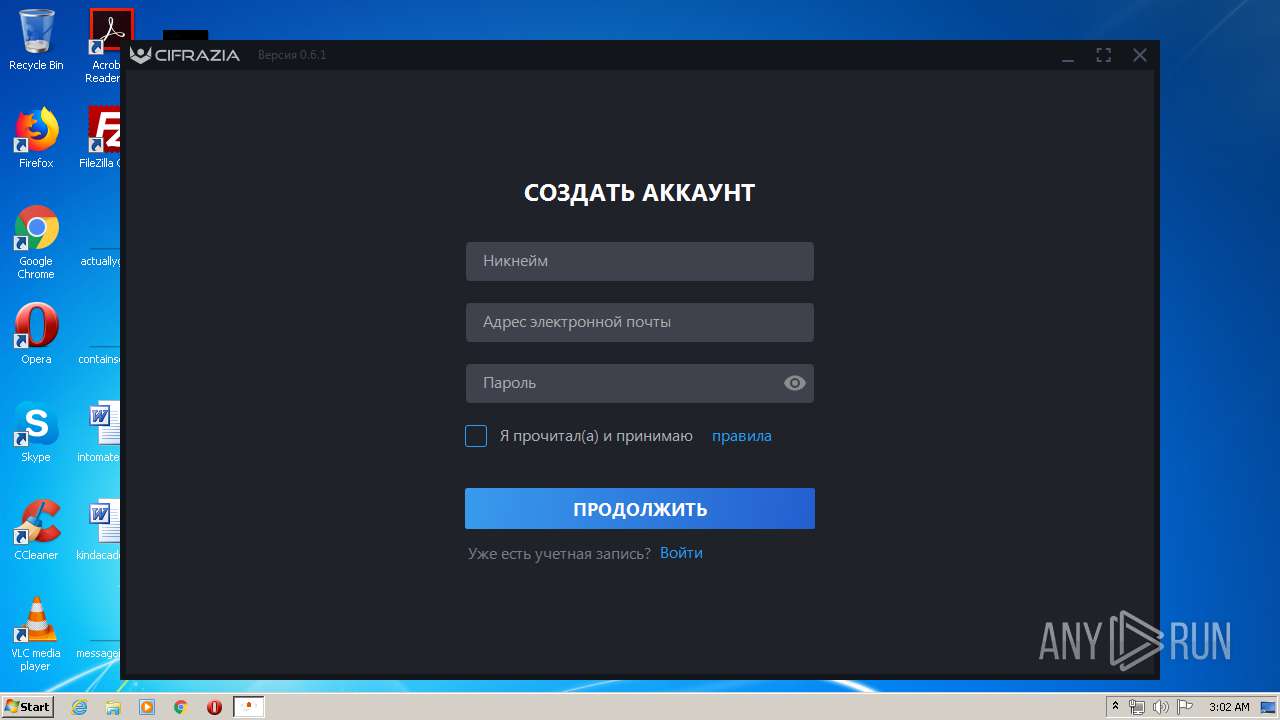
| File name: | Cifrazia.Installer.exe |
| Full analysis: | https://app.any.run/tasks/1fba5f2c-1032-4041-af12-3d540fae2ec9 |
| Verdict: | Malicious activity |
| Analysis date: | May 05, 2020, 02:00:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DA3795094DD576E67F03124B25384EB6 |
| SHA1: | 4EE5B28A3A827454448987EA6767359B008F4029 |
| SHA256: | 74F90C482174B31680CC869650F724DF69ED0ADC429B1548D478D1B19C6EFEDC |
| SSDEEP: | 393216:dB4h5YlTdVYAuQ0o/JM1f1KpjJCxSwbcoK39+yfO:z4hsT82y1fcpVo6+yfO |
MALICIOUS
Application was dropped or rewritten from another process
- CifrAzia.exe (PID: 3636)
Loads the Task Scheduler DLL interface
- Cifrazia.Installer.exe (PID: 2536)
SUSPICIOUS
Executed as Windows Service
- vssvc.exe (PID: 2612)
Creates files in the user directory
- Cifrazia.Installer.exe (PID: 2536)
- msiexec.exe (PID: 3100)
- CifrAzia.exe (PID: 3636)
Executable content was dropped or overwritten
- Cifrazia.Installer.exe (PID: 2536)
- msiexec.exe (PID: 1708)
- msiexec.exe (PID: 3100)
Starts Microsoft Installer
- Cifrazia.Installer.exe (PID: 2536)
Modifies the open verb of a shell class
- msiexec.exe (PID: 3100)
INFO
Application launched itself
- msiexec.exe (PID: 3100)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3452)
- MsiExec.exe (PID: 2932)
- MsiExec.exe (PID: 1756)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2612)
Searches for installed software
- msiexec.exe (PID: 3100)
Creates files in the program directory
- msiexec.exe (PID: 3100)
Creates a software uninstall entry
- msiexec.exe (PID: 3100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (18) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (2.9) |
| .exe | | | Generic Win/DOS Executable (1.3) |
| .exe | | | DOS Executable Generic (1.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:04:27 15:06:19+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.25 |
| CodeSize: | 1515008 |
| InitializedDataSize: | 849408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1205cc |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.100 |
| ProductVersionNumber: | 0.0.0.100 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Unicode |
| CompanyName: | CIFRAZIA |
| FileDescription: | CIFRAZIA Installer |
| FileVersion: | 0.0.0.100 |
| InternalName: | Cifrazia_Setup |
| LegalCopyright: | Copyright (C) 2020 CIFRAZIA |
| OriginalFileName: | Cifrazia_Setup.exe |
| ProductName: | CIFRAZIA |
| ProductVersion: | 0.0.0.100 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2020 13:06:19 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | CIFRAZIA |
| FileDescription: | CIFRAZIA Installer |
| FileVersion: | 0.0.0.100 |
| InternalName: | Cifrazia_Setup |
| LegalCopyright: | Copyright (C) 2020 CIFRAZIA |
| OriginalFileName: | Cifrazia_Setup.exe |
| ProductName: | CIFRAZIA |
| ProductVersion: | 0.0.0.100 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Apr-2020 13:06:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00171D3F | 0x00171E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45128 |
.rdata | 0x00173000 | 0x0005D87C | 0x0005DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.61049 |
.data | 0x001D1000 | 0x00006CF0 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.05514 |
.rsrc | 0x001D8000 | 0x00052FB8 | 0x00053000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.17959 |
.reloc | 0x0022B000 | 0x00019664 | 0x00019800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55644 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.221 | 1915 | Latin 1 / Western European | Russian - Russia | RT_MANIFEST |
2 | 3.1591 | 9640 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 3.46873 | 4264 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 3.54157 | 2440 | Latin 1 / Western European | Russian - Russia | RT_ICON |
5 | 4.01317 | 1128 | Latin 1 / Western European | Russian - Russia | RT_ICON |
9 | 3.96518 | 1114 | Latin 1 / Western European | Russian - Russia | RT_STRING |
10 | 4.22341 | 2032 | Latin 1 / Western European | Russian - Russia | RT_STRING |
11 | 3.82278 | 840 | Latin 1 / Western European | Russian - Russia | RT_STRING |
12 | 3.80147 | 1438 | Latin 1 / Western European | Russian - Russia | RT_STRING |
13 | 3.91416 | 850 | Latin 1 / Western European | Russian - Russia | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
49
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1708 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\CIFRAZIA\CIFRAZIA 0.0.0.100\install\Cifrazia_Installer.msi" AI_SETUPEXEPATH=C:\Users\admin\AppData\Local\Temp\Cifrazia.Installer.exe SETUPEXEDIR=C:\Users\admin\AppData\Local\Temp\ EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1588633105 " ALLUSERS="1" | C:\Windows\system32\msiexec.exe | Cifrazia.Installer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1756 | C:\Windows\system32\MsiExec.exe -Embedding 5EA072514919F4D0C081E1BB57F303AD | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2536 | "C:\Users\admin\AppData\Local\Temp\Cifrazia.Installer.exe" | C:\Users\admin\AppData\Local\Temp\Cifrazia.Installer.exe | explorer.exe | ||||||||||||
User: admin Company: CIFRAZIA Integrity Level: MEDIUM Description: CIFRAZIA Installer Exit code: 0 Version: 0.0.0.100 Modules
| |||||||||||||||
| 2612 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | C:\Windows\system32\MsiExec.exe -Embedding 05D4C05E5922B227244276127D462EEC C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3100 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3452 | C:\Windows\system32\MsiExec.exe -Embedding 4E81862047EF711B29D729DFC9A42417 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3636 | "C:\Users\admin\AppData\Roaming\Cifrazia\CifrAzia.exe" | C:\Users\admin\AppData\Roaming\Cifrazia\CifrAzia.exe | MsiExec.exe | ||||||||||||
User: admin Company: CIFRAZIA Integrity Level: MEDIUM Description: CifrAzia Exit code: 0 Version: 0.0.0.100 Modules
| |||||||||||||||
Total events
1 463
Read events
1 143
Write events
308
Delete events
12
Modification events
| (PID) Process: | (2536) Cifrazia.Installer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1708) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3100) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000EE6A29078122D6011C0C0000D00E0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3100) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000EE6A29078122D6011C0C0000D00E0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2612) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000582B8B078122D601340A0000400D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2612) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000582B8B078122D601340A0000DC0F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2612) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000582B8B078122D601340A0000E00F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2612) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000582B8B078122D601340A00007C0B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3100) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 34 | |||
| (PID) Process: | (3100) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000E27A7A078122D6011C0C0000D00E0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
7
Suspicious files
5
Text files
12
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2536 | Cifrazia.Installer.exe | C:\Users\admin\AppData\Roaming\CIFRAZIA\CIFRAZIA 0.0.0.100\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 2536 | Cifrazia.Installer.exe | C:\Users\admin\AppData\Local\Temp\MSIF787.tmp | — | |
MD5:— | SHA256:— | |||
| 1708 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIF9BA.tmp | — | |
MD5:— | SHA256:— | |||
| 1708 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIFA57.tmp | — | |
MD5:— | SHA256:— | |||
| 1708 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIFA68.tmp | — | |
MD5:— | SHA256:— | |||
| 1708 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIFAA7.tmp | — | |
MD5:— | SHA256:— | |||
| 3100 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3100 | msiexec.exe | C:\Windows\Installer\MSI695D.tmp | — | |
MD5:— | SHA256:— | |||
| 3100 | msiexec.exe | C:\Windows\Installer\MSI69CB.tmp | — | |
MD5:— | SHA256:— | |||
| 3100 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF30F367273F00977A.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3636 | CifrAzia.exe | 95.217.57.238:9090 | — | Hetzner Online GmbH | DE | unknown |