| File name: | 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f |
| Full analysis: | https://app.any.run/tasks/0e49f643-ee03-4a99-9c52-f49eb63f5f66 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 20:44:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | E9C0BEFBE98043F4A4179491187E8635 |
| SHA1: | F58EA4E73E9FB40DC450CEE931FDEF8170F728C9 |
| SHA256: | 74F00395B788009ACF25E23CE1859E6AB6190ED10FF7E7519B2947261406714F |
| SSDEEP: | 49152:O7f0tu7IfpNZvOXyfrkNfVImhQSWwudyq4sWKxEtfis9:Cf0t+IcX4rkNfeSQVy6La |
MALICIOUS
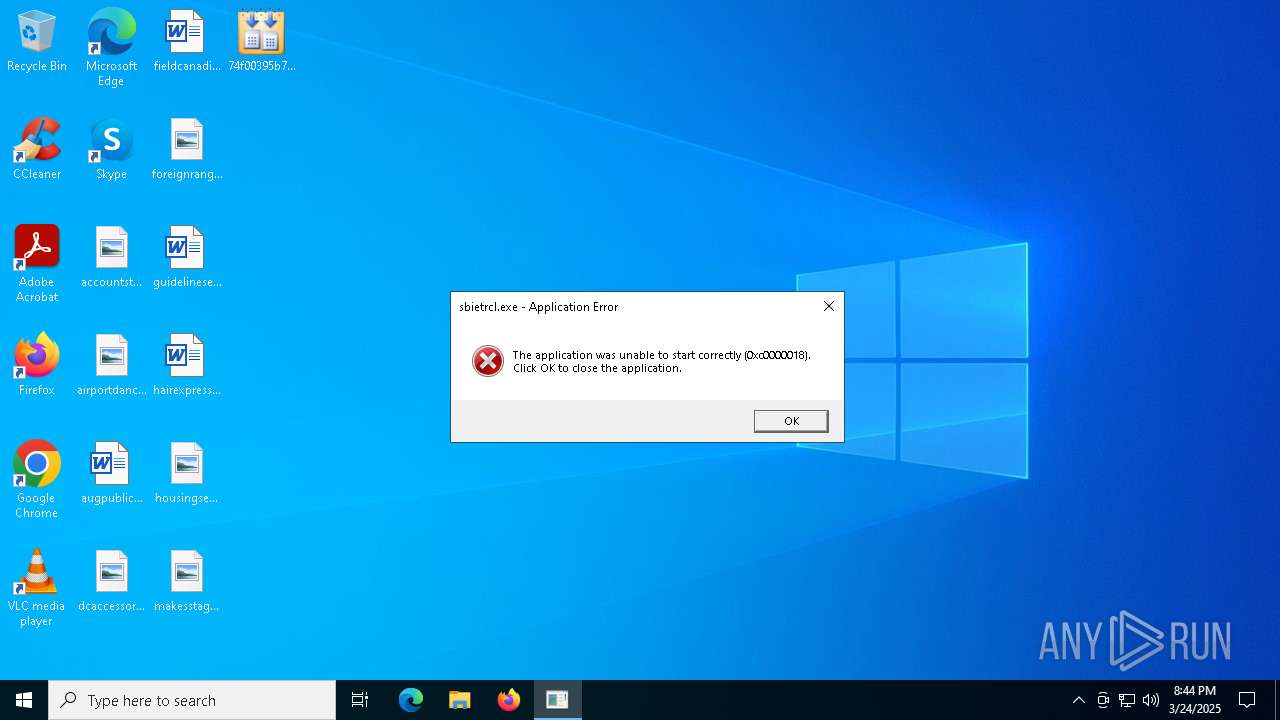
Executing a file with an untrusted certificate
- 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe (PID: 7368)
- sbietrcl.exe (PID: 7868)
- sbietrcl.exe (PID: 7940)
Changes the autorun value in the registry
- 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe (PID: 7368)
SUSPICIOUS
Executable content was dropped or overwritten
- 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe (PID: 7368)
Reads security settings of Internet Explorer
- 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe (PID: 7368)
- sbietrcl.exe (PID: 7868)
Process drops legitimate windows executable
- 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe (PID: 7368)
Application launched itself
- sbietrcl.exe (PID: 7868)
INFO
Reads the machine GUID from the registry
- 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe (PID: 7368)
- sbietrcl.exe (PID: 7868)
Creates files or folders in the user directory
- 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe (PID: 7368)
- sbietrcl.exe (PID: 7868)
The sample compiled with english language support
- 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe (PID: 7368)
Checks supported languages
- 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe (PID: 7368)
- sbietrcl.exe (PID: 7868)
Reads the software policy settings
- 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe (PID: 7368)
- sbietrcl.exe (PID: 7868)
- slui.exe (PID: 6816)
Create files in a temporary directory
- 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe (PID: 7368)
Reads the computer name
- sbietrcl.exe (PID: 7868)
Process checks computer location settings
- 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe (PID: 7368)
Checks proxy server information
- sbietrcl.exe (PID: 7868)
- slui.exe (PID: 6816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:03:26 23:56:46+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 705024 |
| InitializedDataSize: | 71680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xae0fe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 14.59.101.2 |
| ProductVersionNumber: | 14.59.101.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Amd K8 |
| CompanyName: | Company & Sons |
| FileDescription: | AMD Processor |
| FileVersion: | 14.59.101.2 |
| InternalName: | AMD Processor.exe |
| LegalCopyright: | Copyright © 2002-2017 by Company & Sons |
| OriginalFileName: | AMD Processor.exe |
| ProductName: | AMD Processor |
| ProductVersion: | 14.59.101.2 |
| AssemblyVersion: | 14.59.101.2 |
Total processes
133
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6816 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7368 | "C:\Users\admin\Desktop\74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe" | C:\Users\admin\Desktop\74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe | explorer.exe | ||||||||||||
User: admin Company: Company & Sons Integrity Level: MEDIUM Description: AMD Processor Exit code: 4294967295 Version: 14.59.101.2 Modules
| |||||||||||||||
| 7868 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\sbietrcl.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\sbietrcl.exe | 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe | ||||||||||||
User: admin Company: Company & Sons Integrity Level: MEDIUM Description: AMD Processor Exit code: 0 Version: 14.59.101.2 Modules
| |||||||||||||||
| 7940 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\sbietrcl.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\sbietrcl.exe | — | sbietrcl.exe | |||||||||||
User: admin Company: Company & Sons Integrity Level: MEDIUM Description: AMD Processor Exit code: 3221225496 Version: 14.59.101.2 Modules
| |||||||||||||||
Total events
10 175
Read events
10 174
Write events
1
Delete events
0
Modification events
| (PID) Process: | (7368) 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Application |
Value: C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\sbietrcl.exe | |||
Executable files
4
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7868 | sbietrcl.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C0018BB1B5834735BFA60CD063B31956 | binary | |
MD5:909250D0473FAFA87F53FDD42CA2EF29 | SHA256:EA770A1A2082FD87A51F4AFF44EEDB07B12B09C86A626A5E4BDB77B277886E9A | |||
| 7368 | 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\sbietrcl.exe | executable | |
MD5:E9C0BEFBE98043F4A4179491187E8635 | SHA256:74F00395B788009ACF25E23CE1859E6AB6190ED10FF7E7519B2947261406714F | |||
| 7368 | 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe | C:\Users\admin\AppData\Local\Temp\mscorsvw1.exe | executable | |
MD5:BA428E7084F97B488865397D11059748 | SHA256:3E824F0D325FD32F8100DDF6B506AD6250BE48286AC20726DCB23A9CEDF3E4C1 | |||
| 7368 | 74f00395b788009acf25e23ce1859e6ab6190ed10ff7e7519b2947261406714f.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\sbietrcl_signed.exe | executable | |
MD5:9460DEC0FB82B8EA30FAFD8E64E4F214 | SHA256:B78254EC1C4249714A4D012D6B9B8BCD40D2386026F20862F64C13FD8F439D8D | |||
| 7868 | sbietrcl.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:3B5E0BD6640456A749D9155E6C135727 | SHA256:C362A3D2B661C6066A02FC169FAAA1976C2F6160DA5837C7E68B7E0F67B794ED | |||
| 7868 | sbietrcl.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:F9FE439AF6D196E16DEF05A6E7A71289 | SHA256:4692C5FF0AAC4C62CBF827AC13A33316C801B40924220543D60C0F730BCDE61E | |||
| 7868 | sbietrcl.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C0018BB1B5834735BFA60CD063B31956 | binary | |
MD5:1EA27366E034EB9447A33CE639C01489 | SHA256:788D210EF206A4D11B6B506BF52124EE03FCA4E8A9389FAD43772202A7E29452 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
57
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 104.124.11.58:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7868 | sbietrcl.exe | GET | 200 | 104.124.11.58:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7868 | sbietrcl.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
8116 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.32.68:443 | https://login.live.com/RST2.srf | unknown | xml | 1.35 Kb | whitelisted |
— | — | POST | 400 | 20.190.160.4:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | GET | 200 | 20.199.58.43:443 | https://arc.msn.com/v3/Delivery/Placement?pubid=da63df93-3dbc-42ae-a505-b34988683ac7&pid=88000045&adm=2&w=1&h=1&wpx=1&hpx=1&fmt=json&cltp=app&dim=le&rafb=0&nct=1&pm=1&cfmt=text,image,poly&sft=jpeg,png,gif&topt=1&poptin=0&localid=w:AC7699B0-48EA-FD22-C8DC-06A02098A0F0&ctry=US&time=20250324T204450Z&lc=en-US&pl=en-US&idtp=mid&uid=9115d6d1-9f4e-4053-9297-2a8c833b3912&aid=00000000-0000-0000-0000-000000000000&ua=WindowsShellClient%2F9.0.40929.0%20%28Windows%29&asid=02c977d6103d4445a9faadd89a9e3c93&ctmode=MultiSession&arch=x64&betaedgever=0.0.0.0&canedgever=0.0.0.0&cdm=1&cdmver=10.0.19041.3636&currsel=137271744000000000&devedgever=0.0.0.0&devfam=Windows.Desktop&devform=Unknown&devosver=10.0.19045.4046&disphorzres=1280&dispsize=15.3&dispvertres=720&fosver=16299&isu=0&lo=3967964&metered=false&nettype=ethernet&npid=sc-88000045&oemName=DELL&oemid=DELL&ossku=Professional&prevosver=15063&smBiosDm=DELL&stabedgever=122.0.2365.59&tl=2&tsu=1358493&waasBldFlt=1&waasCfgExp=1&waasCfgSet=1&waasRetail=1&waasRing=&svoffered=2 | unknown | binary | 2.95 Kb | whitelisted |
— | — | POST | 200 | 20.190.160.66:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 104.124.11.58:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6544 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7432 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7868 | sbietrcl.exe | 104.124.11.58:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |