| File name: | asfasf.exe |
| Full analysis: | https://app.any.run/tasks/def8bc27-d729-4c23-bde7-800dbb719340 |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2021, 15:57:38 |
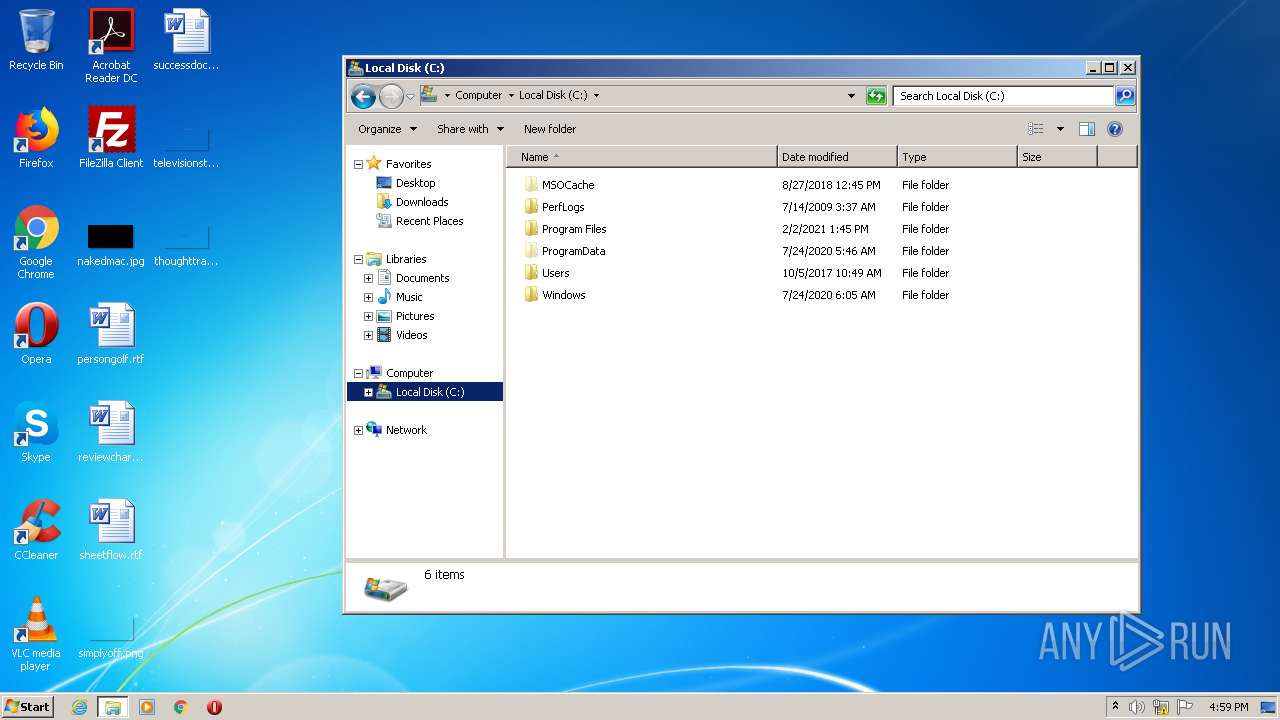
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | F6939EEE26352EC547AD7385CC11063B |
| SHA1: | 47F5A8429ABEA80B565D4D8C9A881FA702037137 |
| SHA256: | 74EB821765FCE8AD980AF31D19514F335EE2EFE2C383719A3EE5E03A38D790FB |
| SSDEEP: | 49152:Z4sPPY1FjcvOgC1H1b2CwwKslmfaVPEK73avw7d7zV3G7ItZxB:jGnH+NWPZLavG3cI3 |
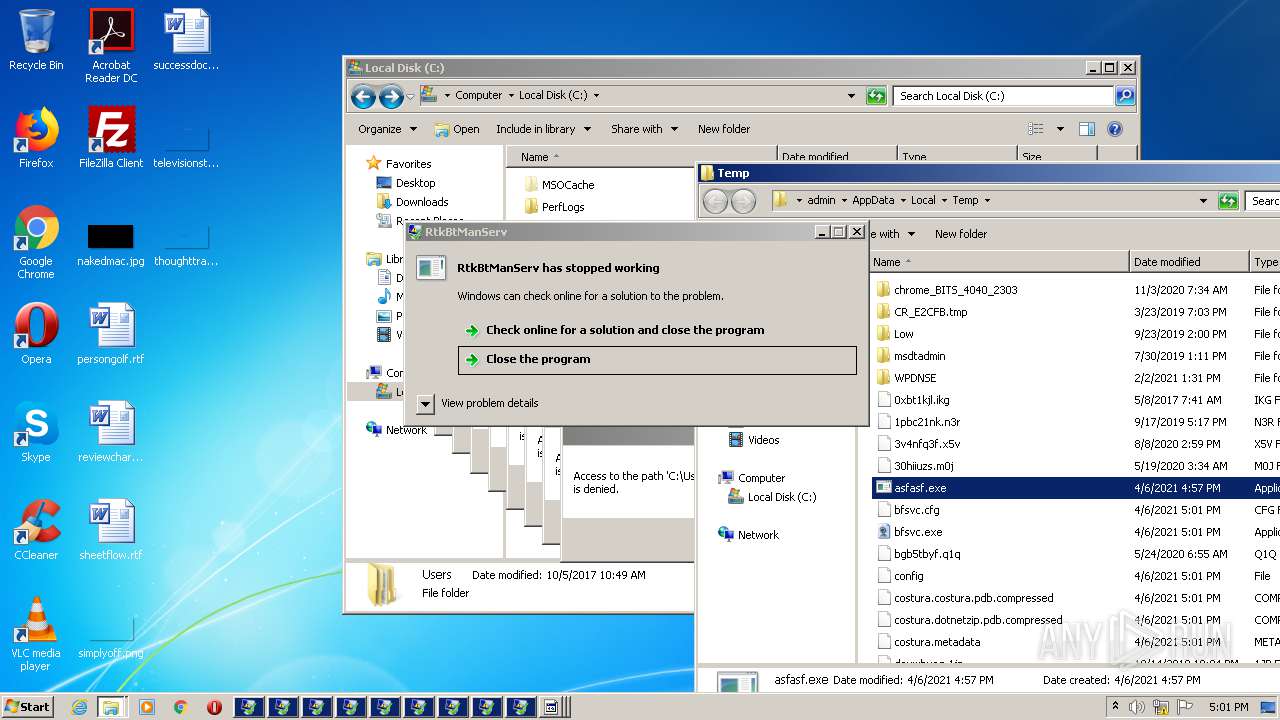
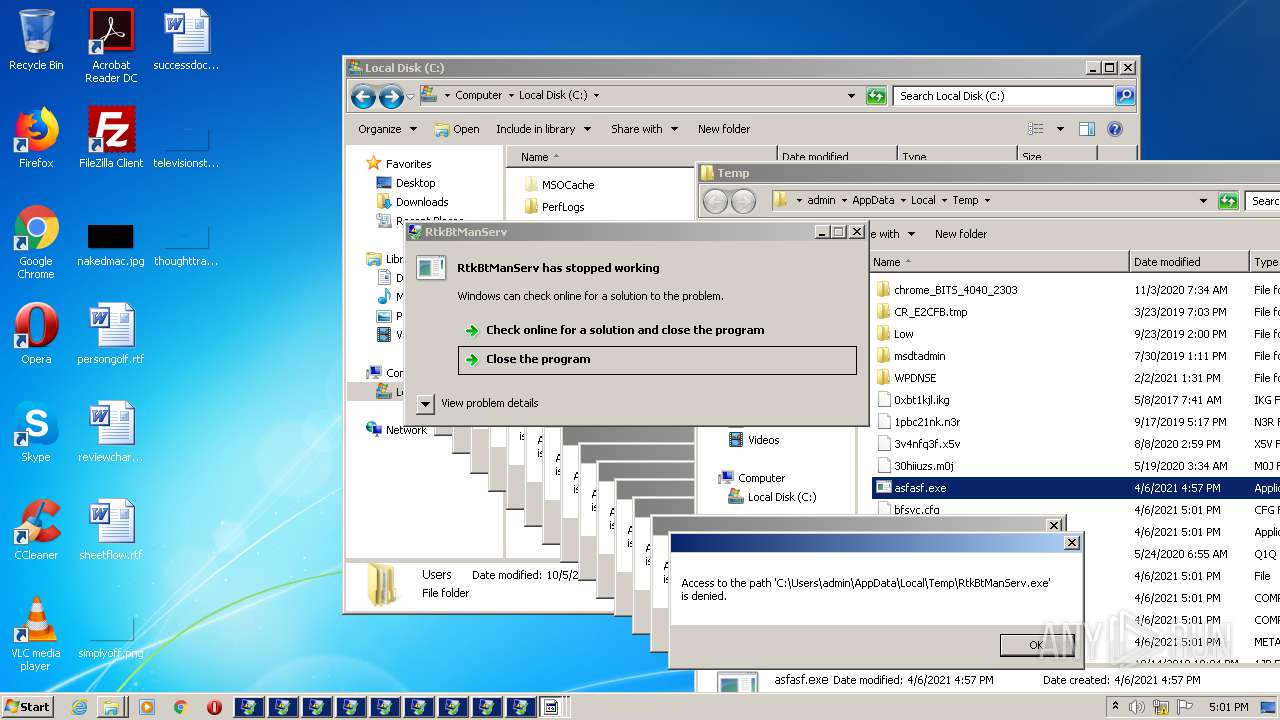
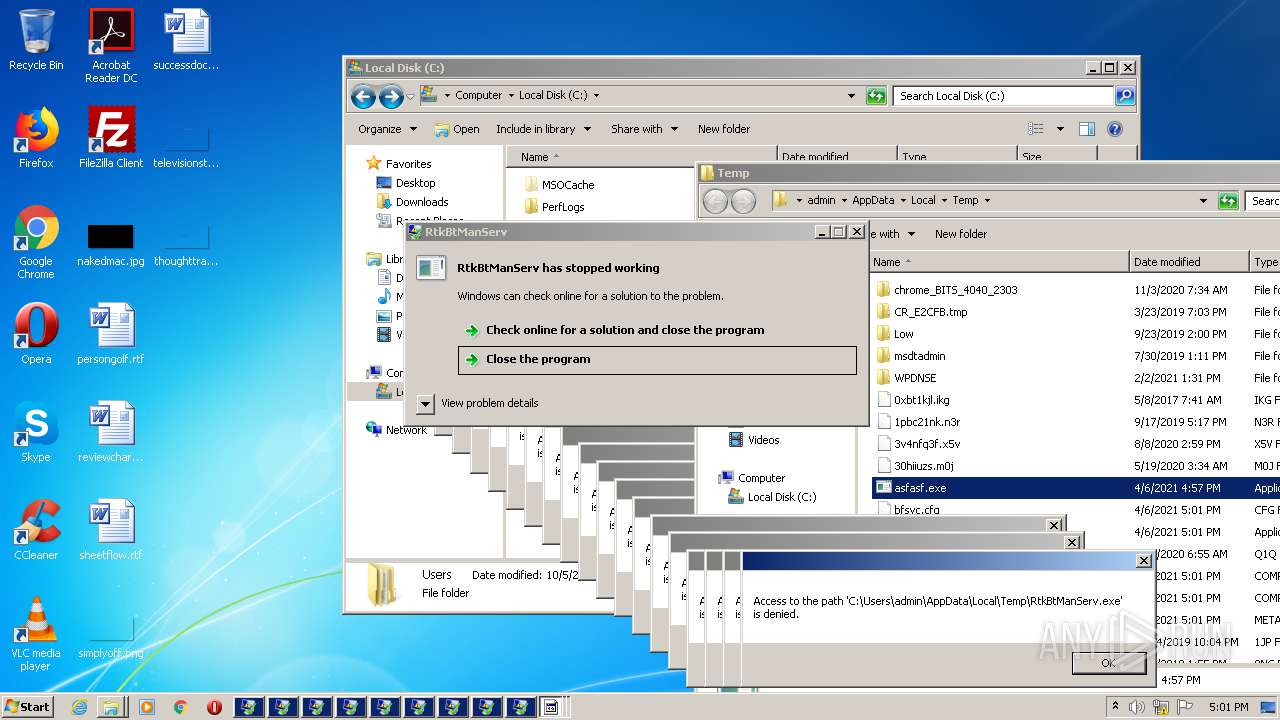
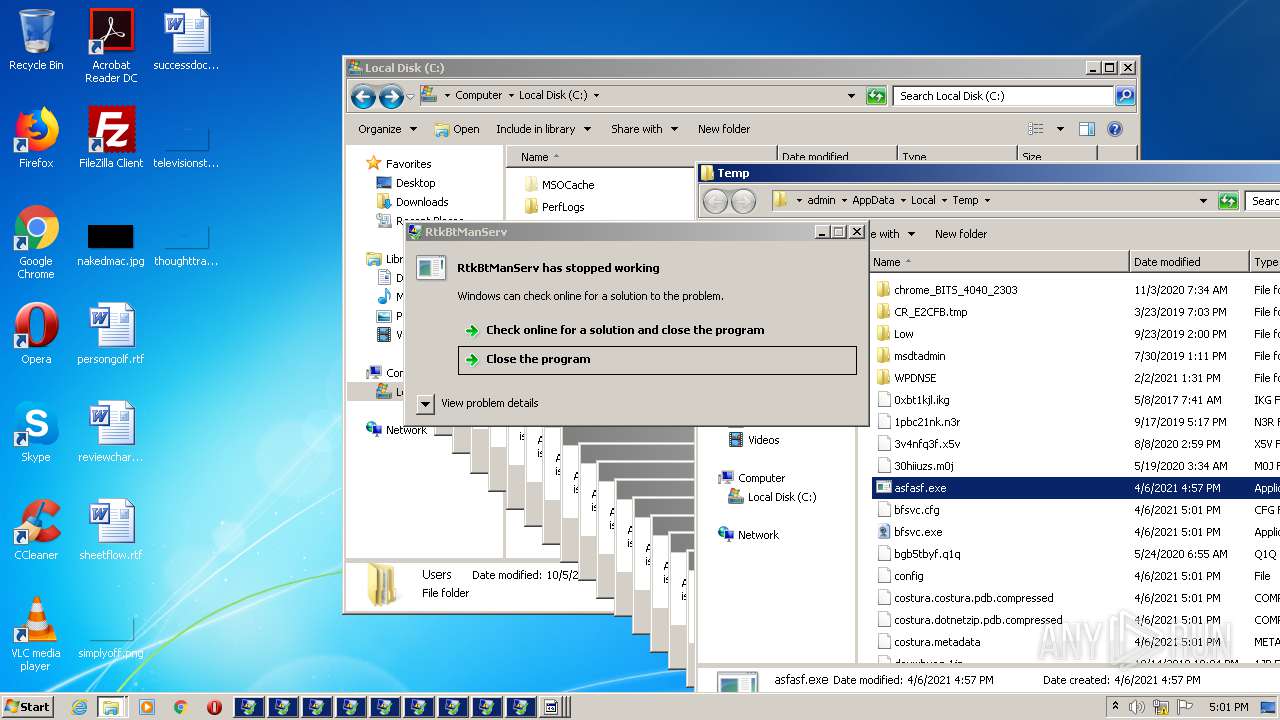
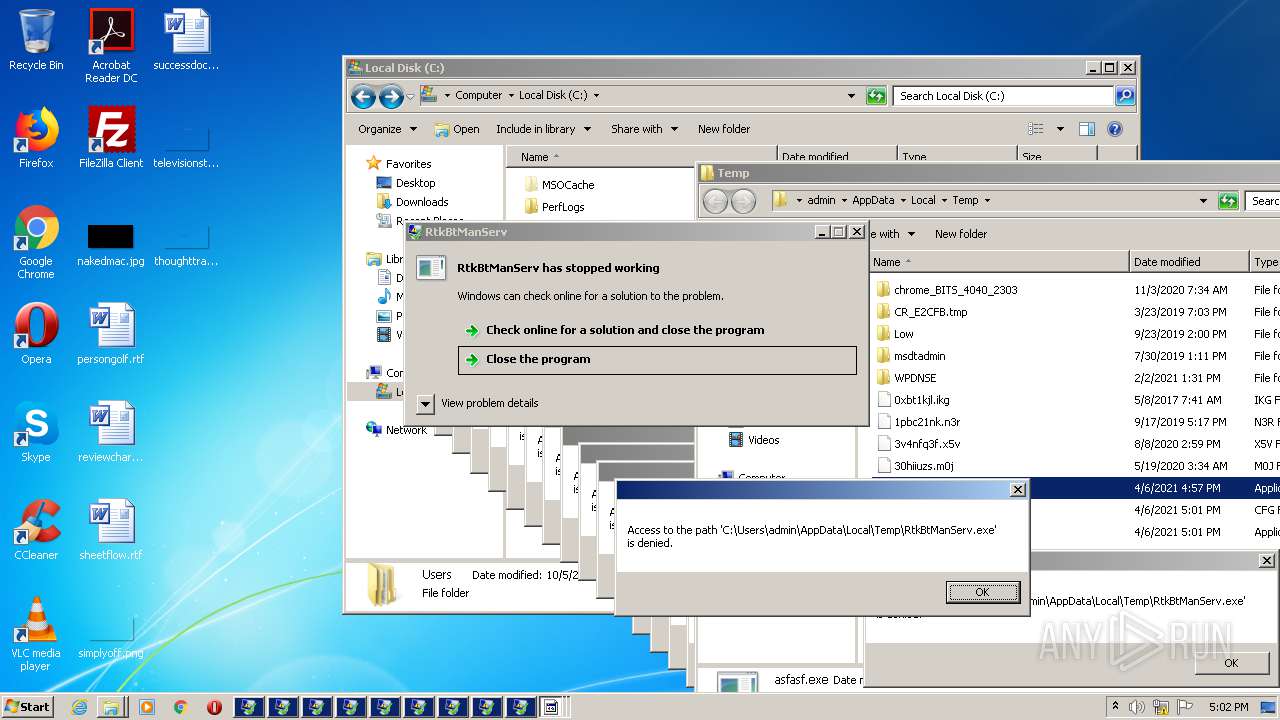
MALICIOUS
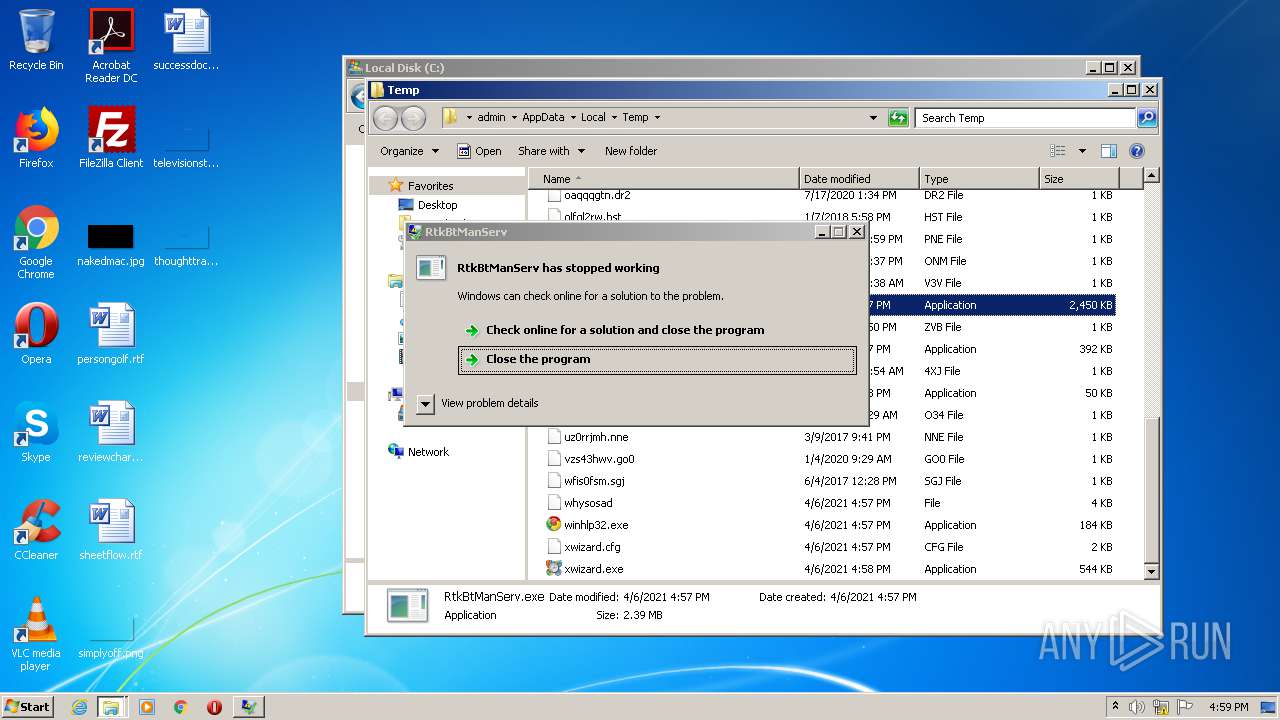
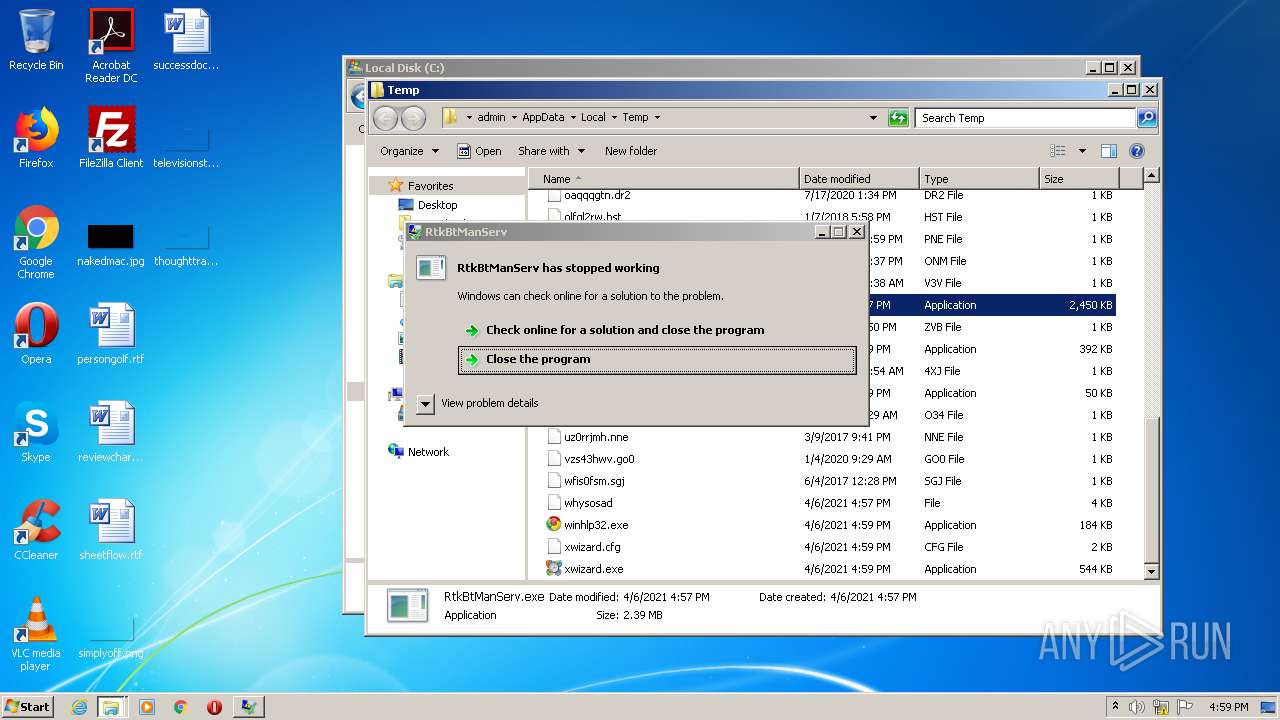
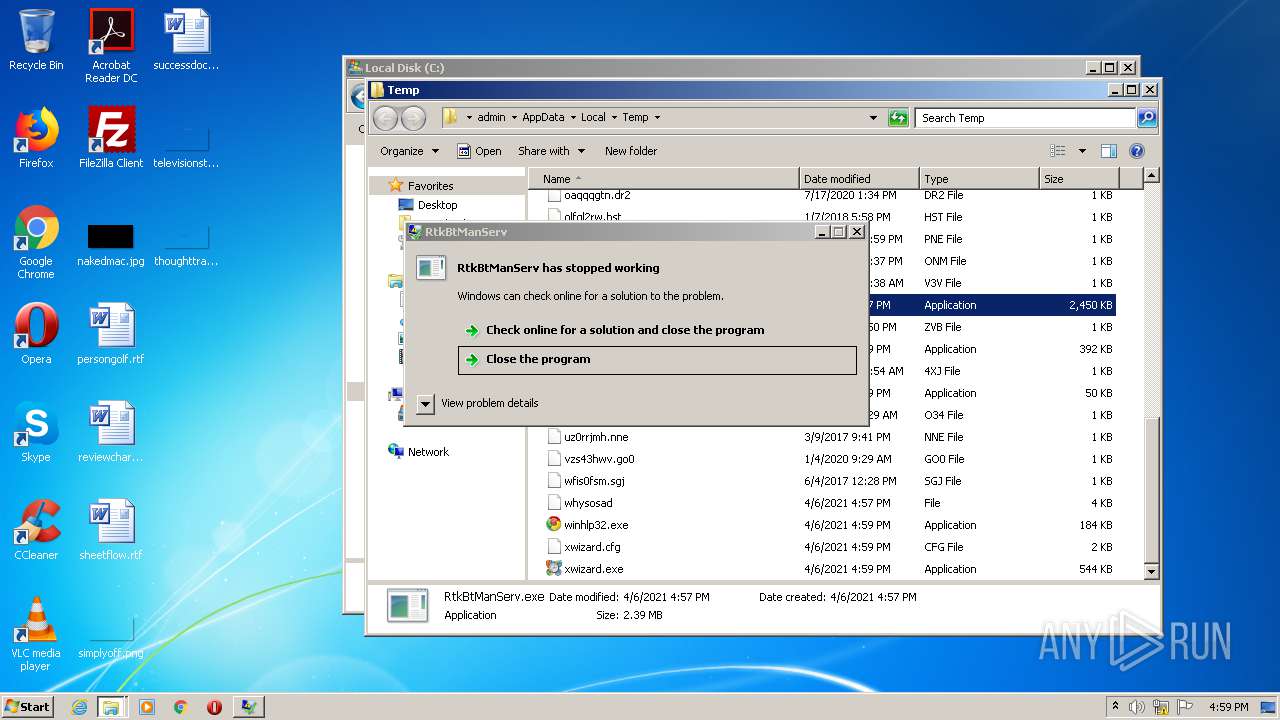
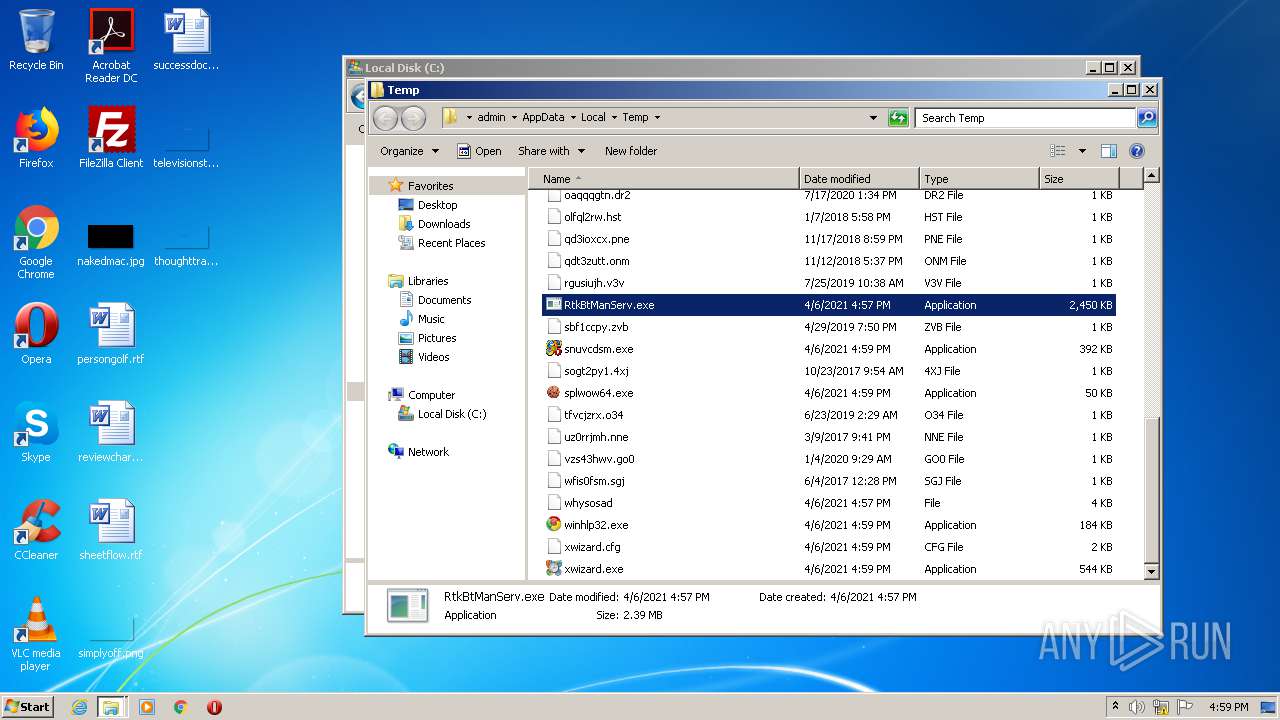
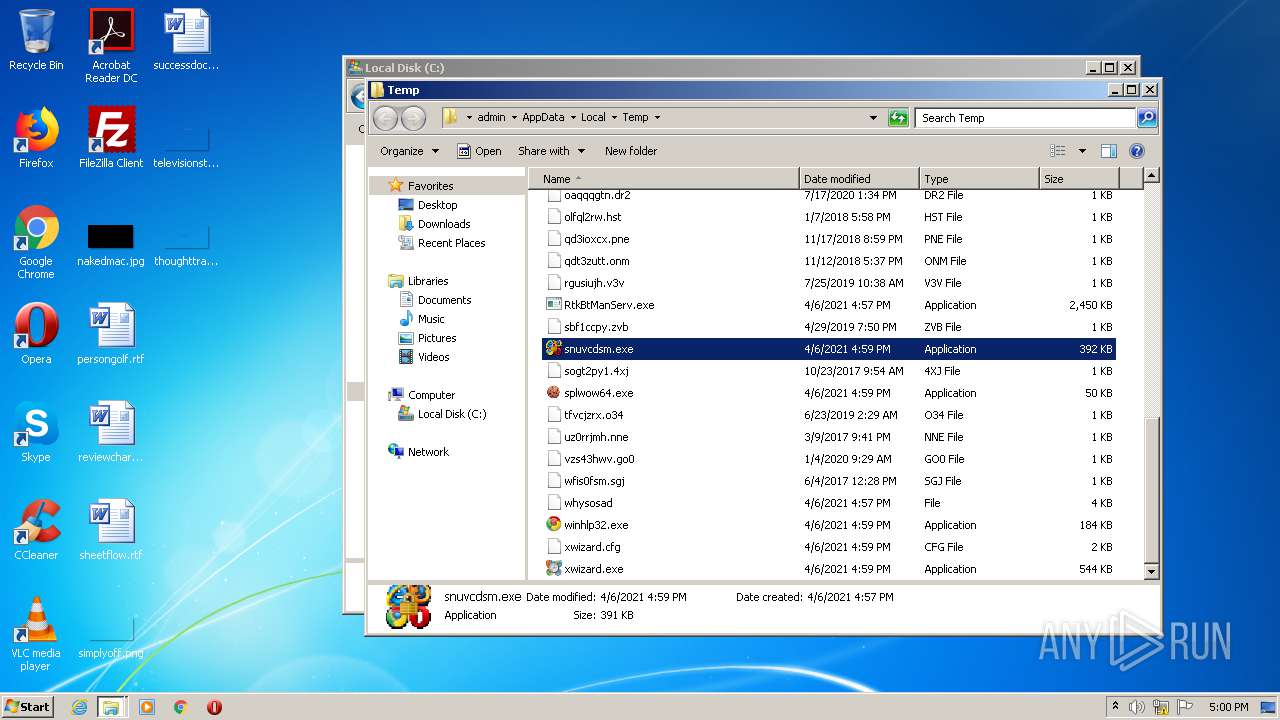
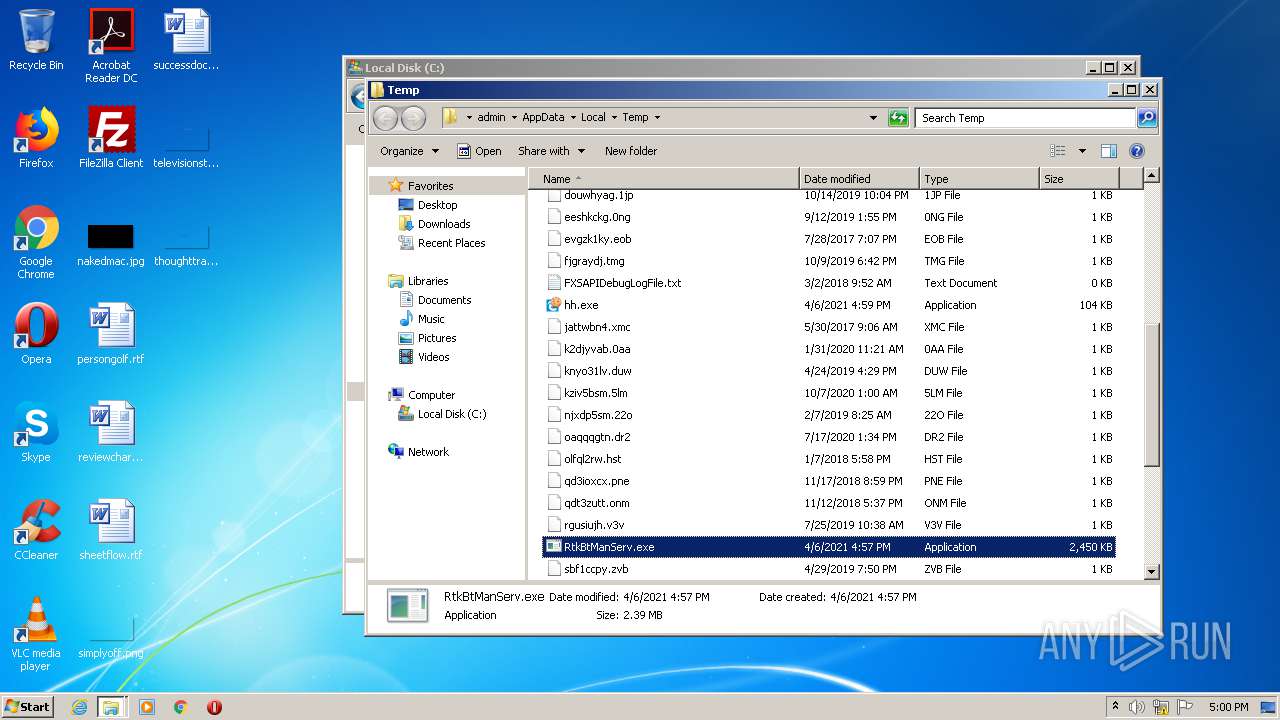
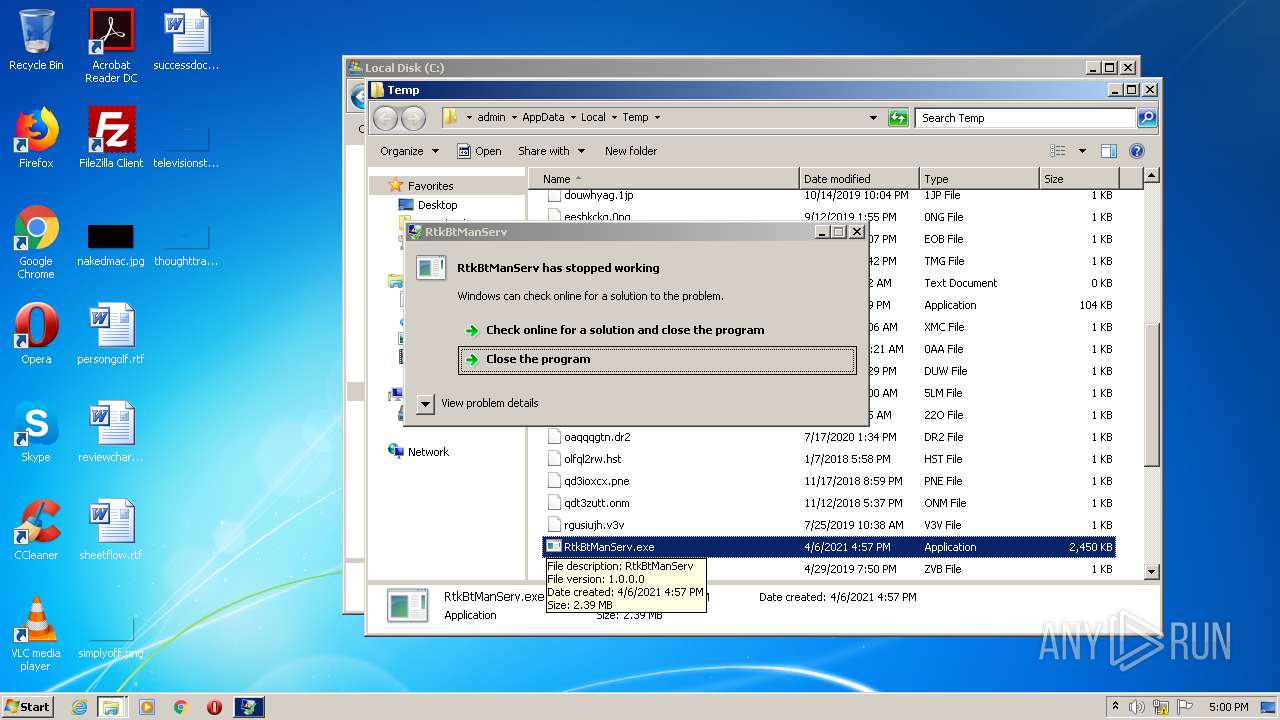
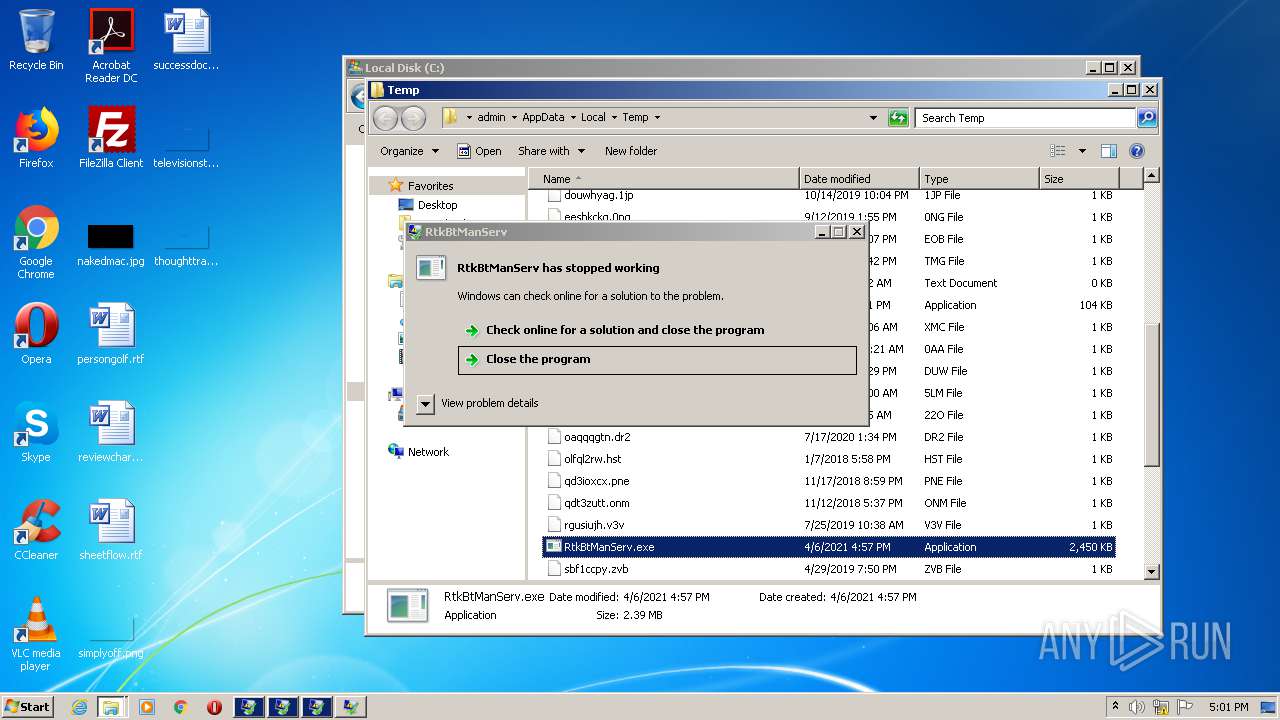
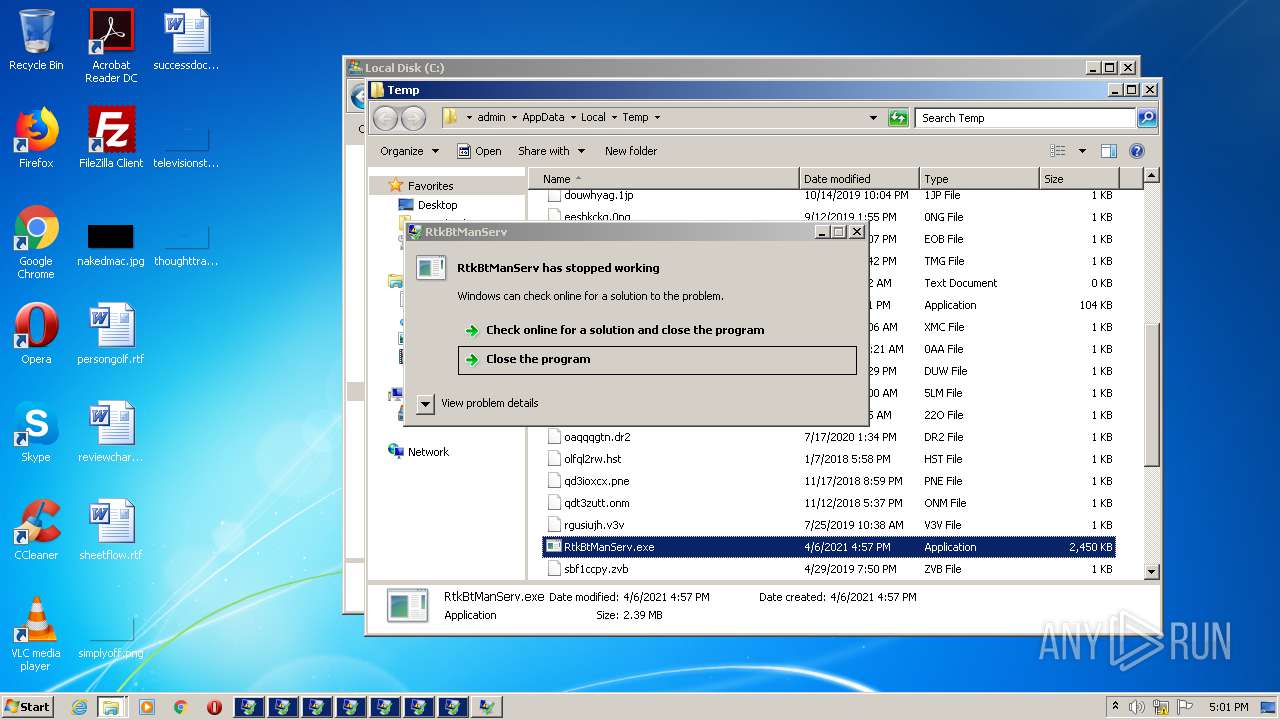
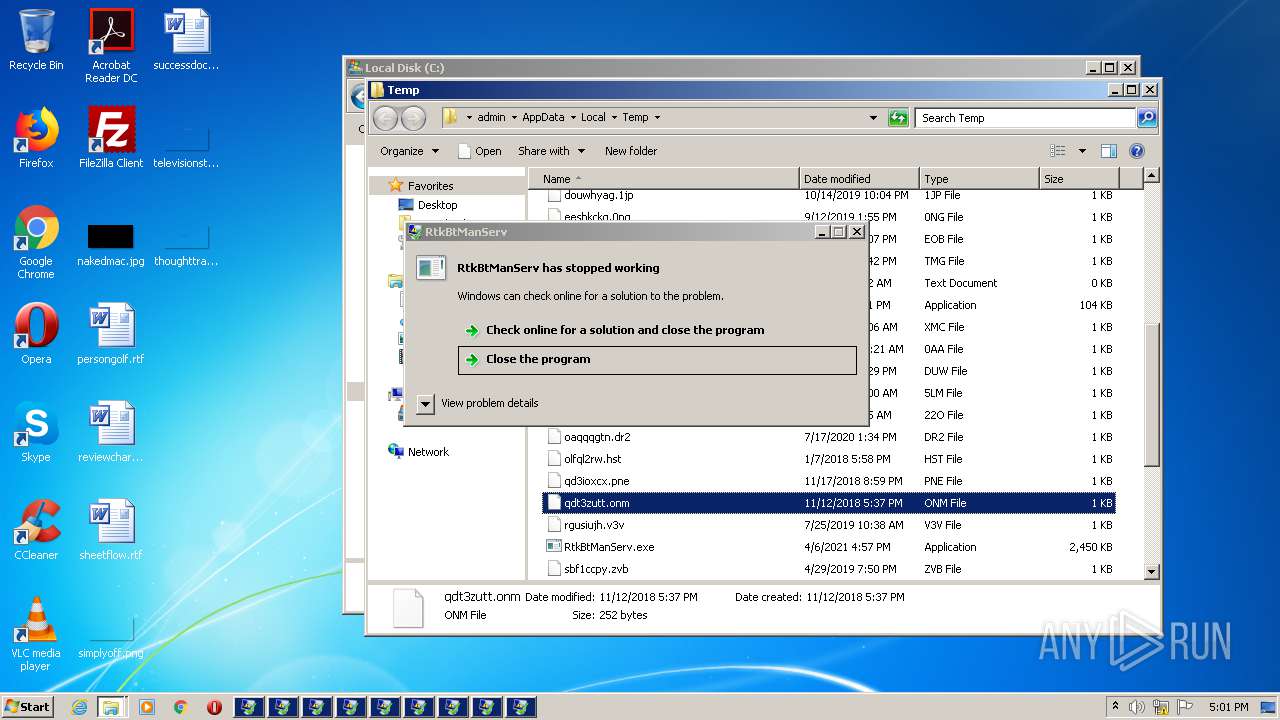
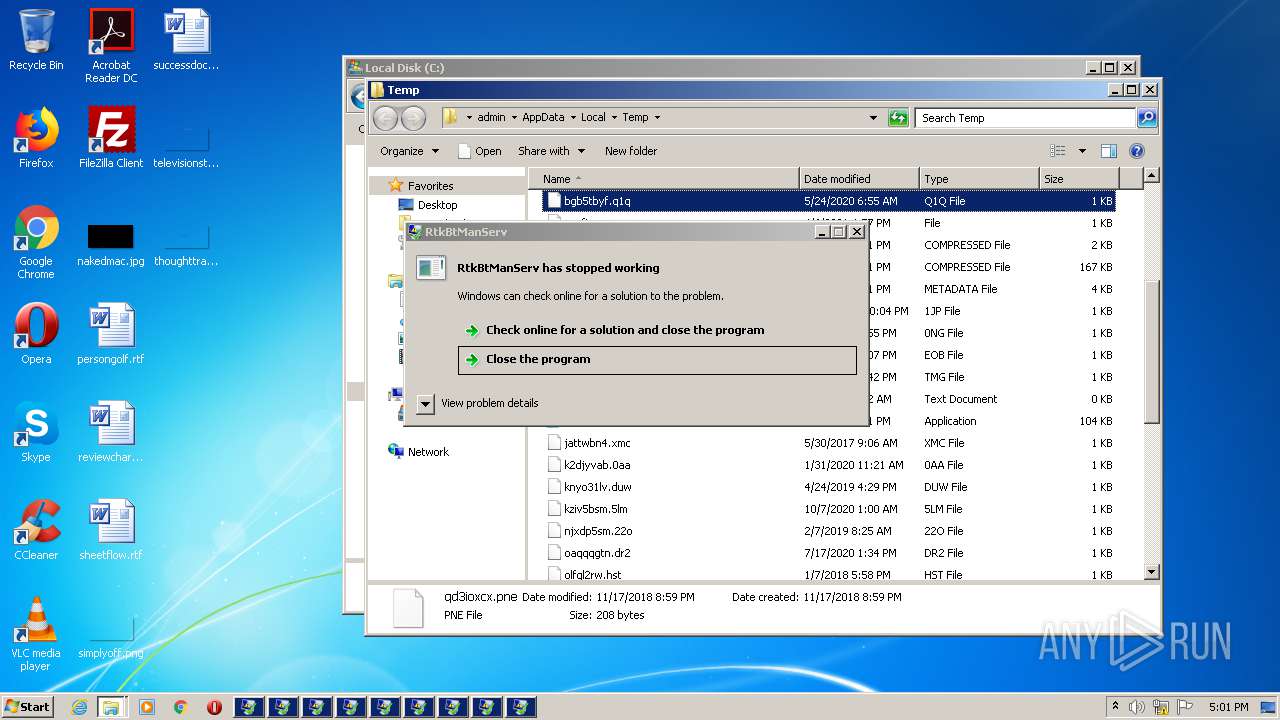
Application was dropped or rewritten from another process
- RtkBtManServ.exe (PID: 4084)
- RtkBtManServ.exe (PID: 1280)
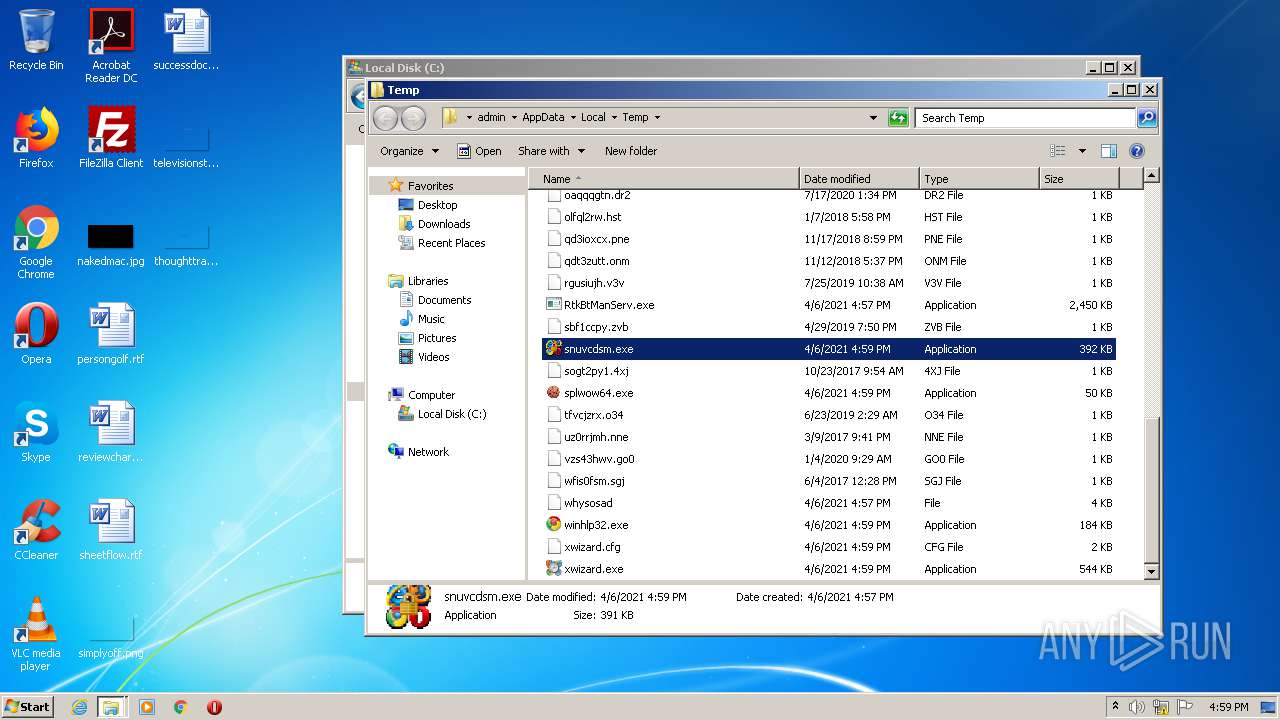
- snuvcdsm.exe (PID: 1112)
- RtkBtManServ.exe (PID: 4088)
- RtkBtManServ.exe (PID: 2756)
- RtkBtManServ.exe (PID: 3456)
- RtkBtManServ.exe (PID: 1916)
- RtkBtManServ.exe (PID: 3528)
- RtkBtManServ.exe (PID: 2212)
- RtkBtManServ.exe (PID: 2644)
- RtkBtManServ.exe (PID: 2928)
- RtkBtManServ.exe (PID: 3852)
- RtkBtManServ.exe (PID: 2592)
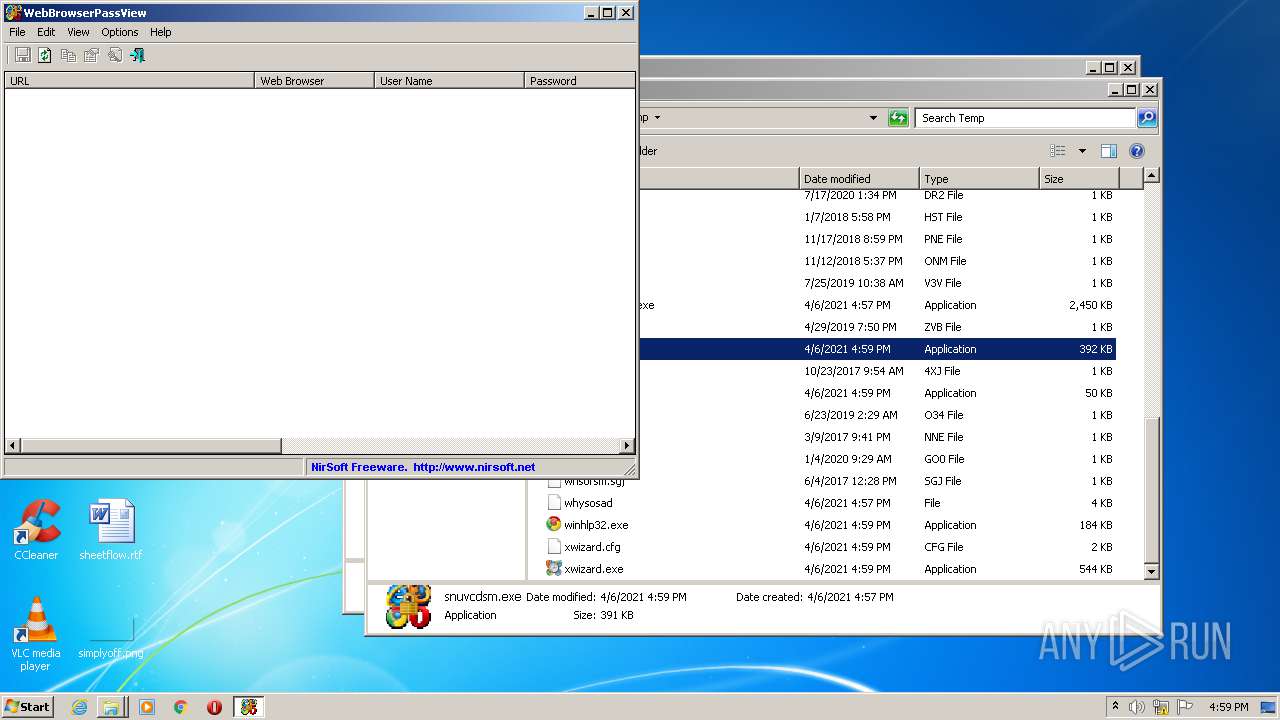
Actions looks like stealing of personal data
- snuvcdsm.exe (PID: 1112)
Steals credentials from Web Browsers
- snuvcdsm.exe (PID: 1112)
SUSPICIOUS
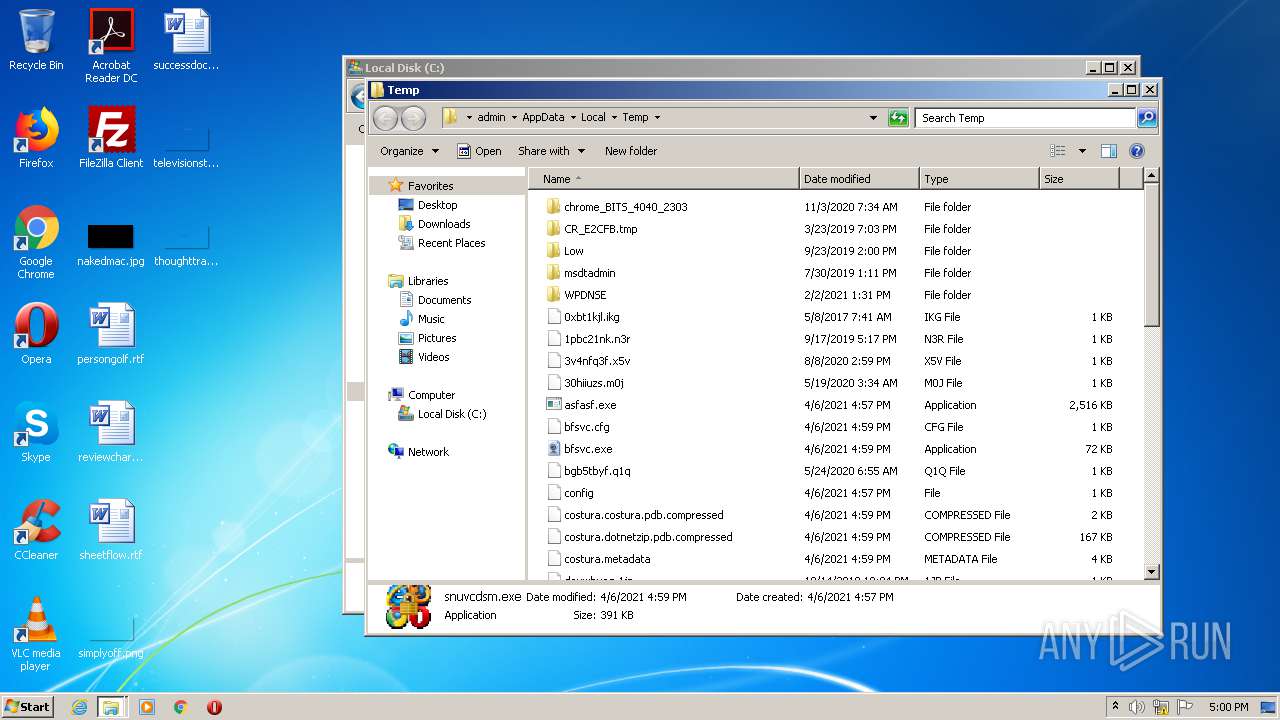
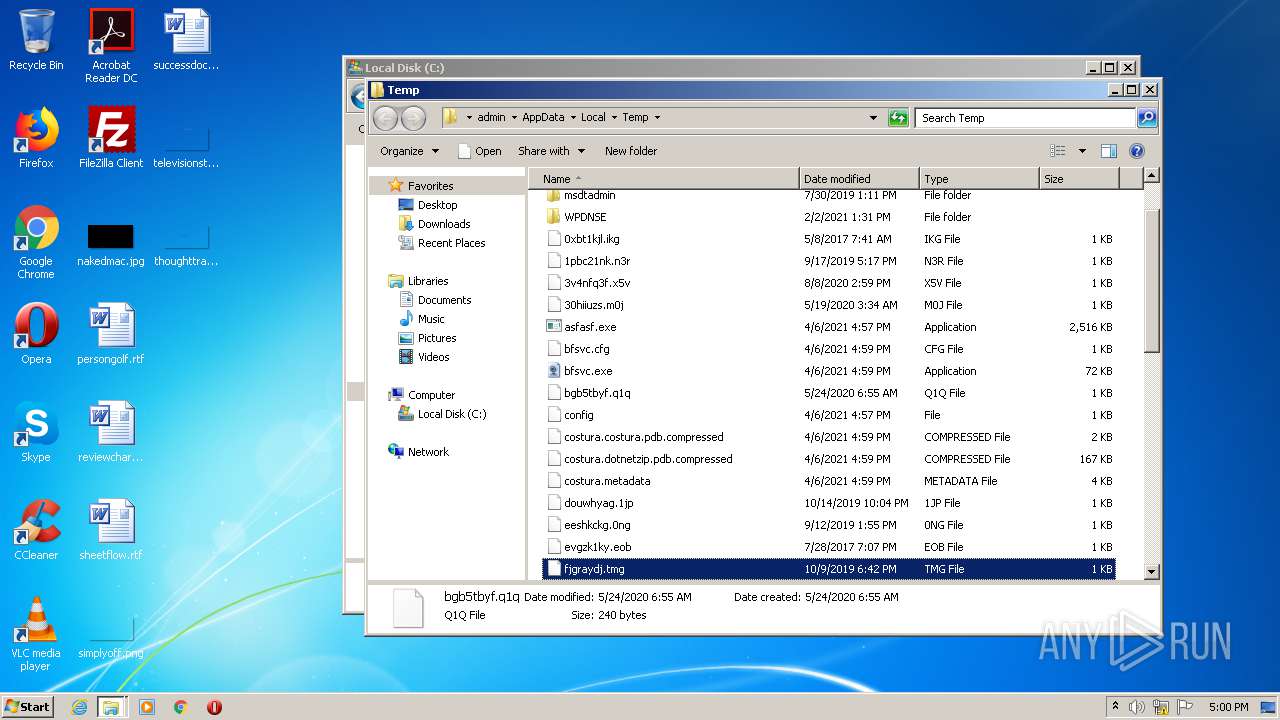
Executable content was dropped or overwritten
- asfasf.exe (PID: 3440)
- RtkBtManServ.exe (PID: 4084)
- RtkBtManServ.exe (PID: 1280)
- RtkBtManServ.exe (PID: 2756)
- RtkBtManServ.exe (PID: 3456)
- RtkBtManServ.exe (PID: 4088)
- RtkBtManServ.exe (PID: 1916)
- RtkBtManServ.exe (PID: 2212)
- RtkBtManServ.exe (PID: 3528)
- RtkBtManServ.exe (PID: 2928)
- RtkBtManServ.exe (PID: 2644)
- RtkBtManServ.exe (PID: 2592)
- RtkBtManServ.exe (PID: 3852)
Drops a file with a compile date too recent
- asfasf.exe (PID: 3440)
Drops a file that was compiled in debug mode
- RtkBtManServ.exe (PID: 4084)
- RtkBtManServ.exe (PID: 1280)
- RtkBtManServ.exe (PID: 4088)
- RtkBtManServ.exe (PID: 2756)
- RtkBtManServ.exe (PID: 3456)
- RtkBtManServ.exe (PID: 1916)
- RtkBtManServ.exe (PID: 3528)
- RtkBtManServ.exe (PID: 2212)
- RtkBtManServ.exe (PID: 2644)
- RtkBtManServ.exe (PID: 2928)
- RtkBtManServ.exe (PID: 2592)
- RtkBtManServ.exe (PID: 3852)
INFO
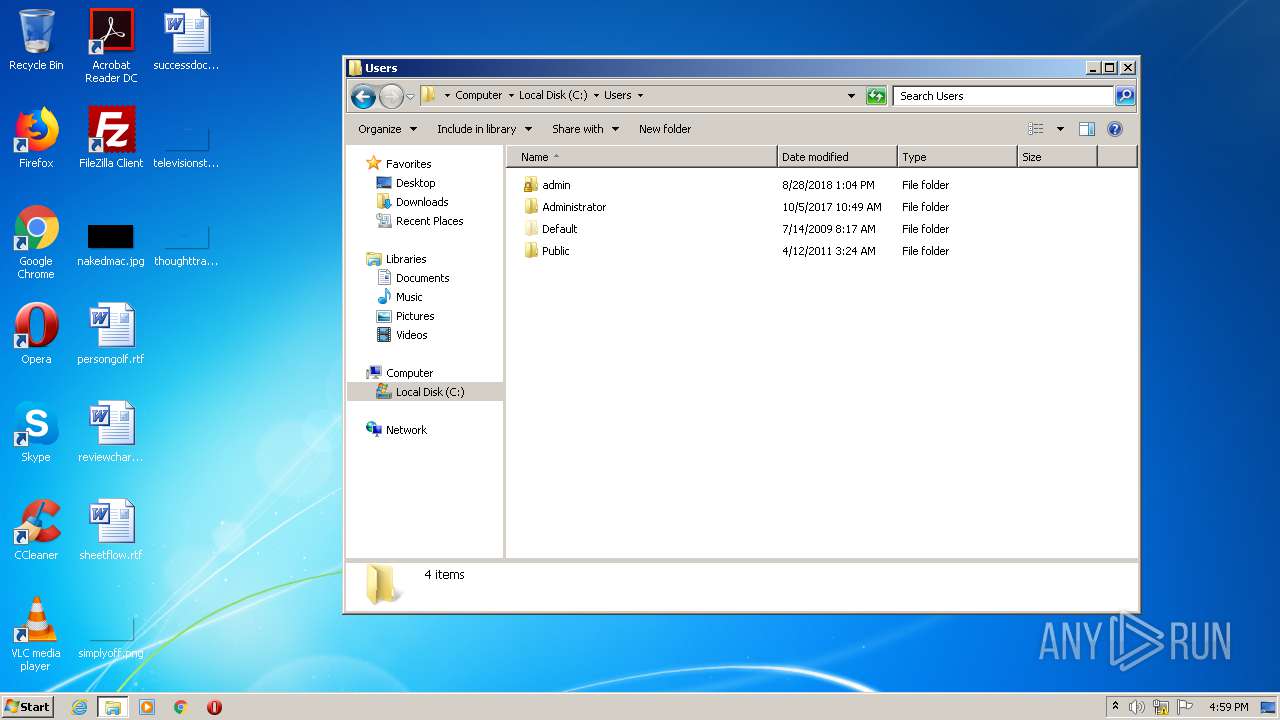
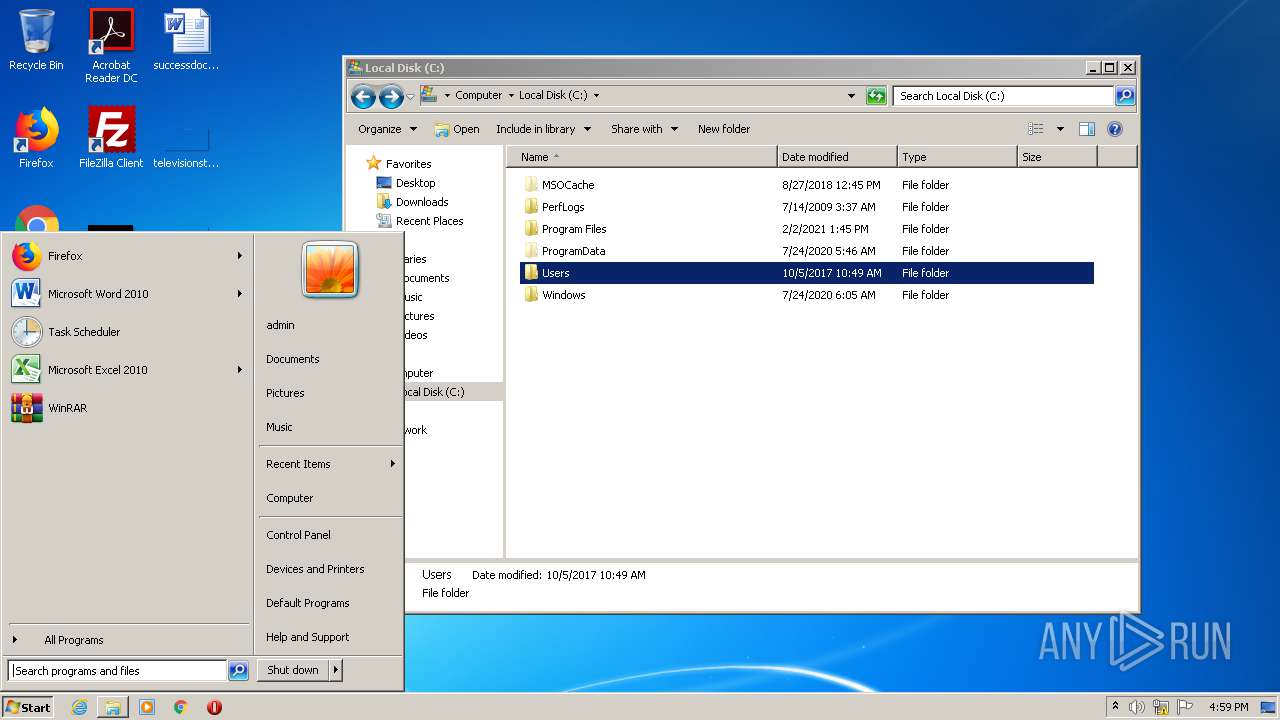
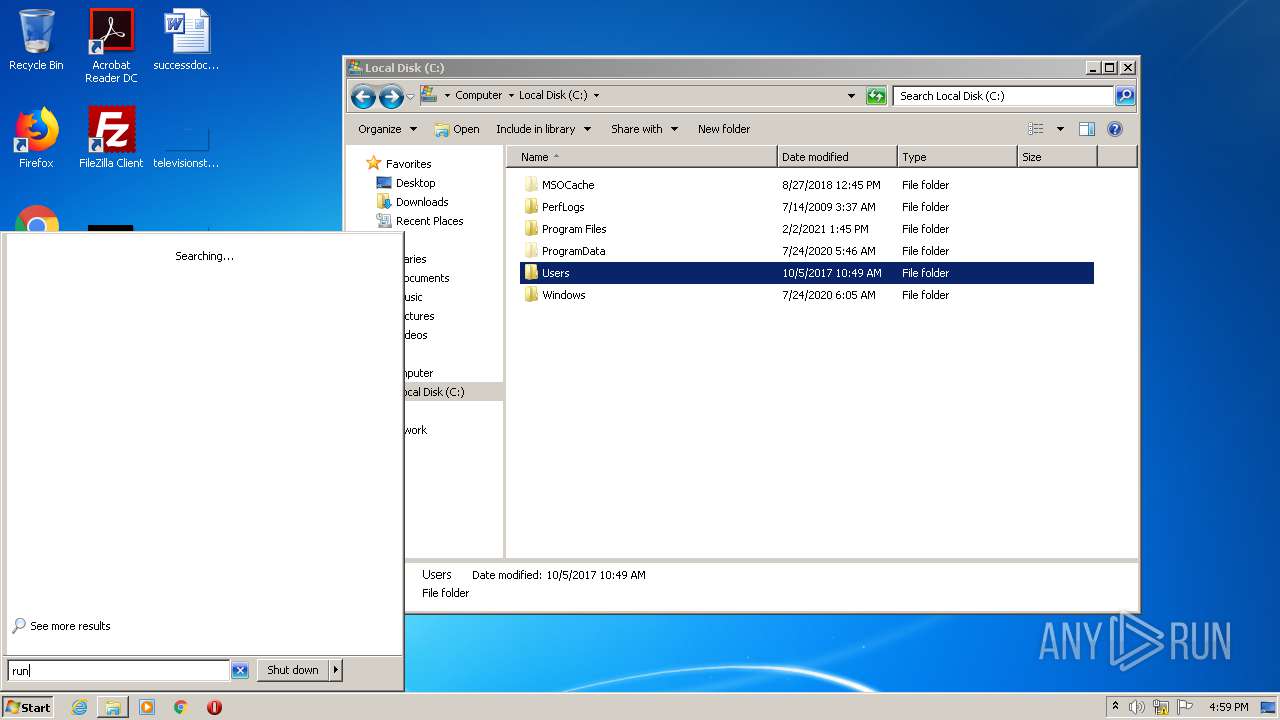
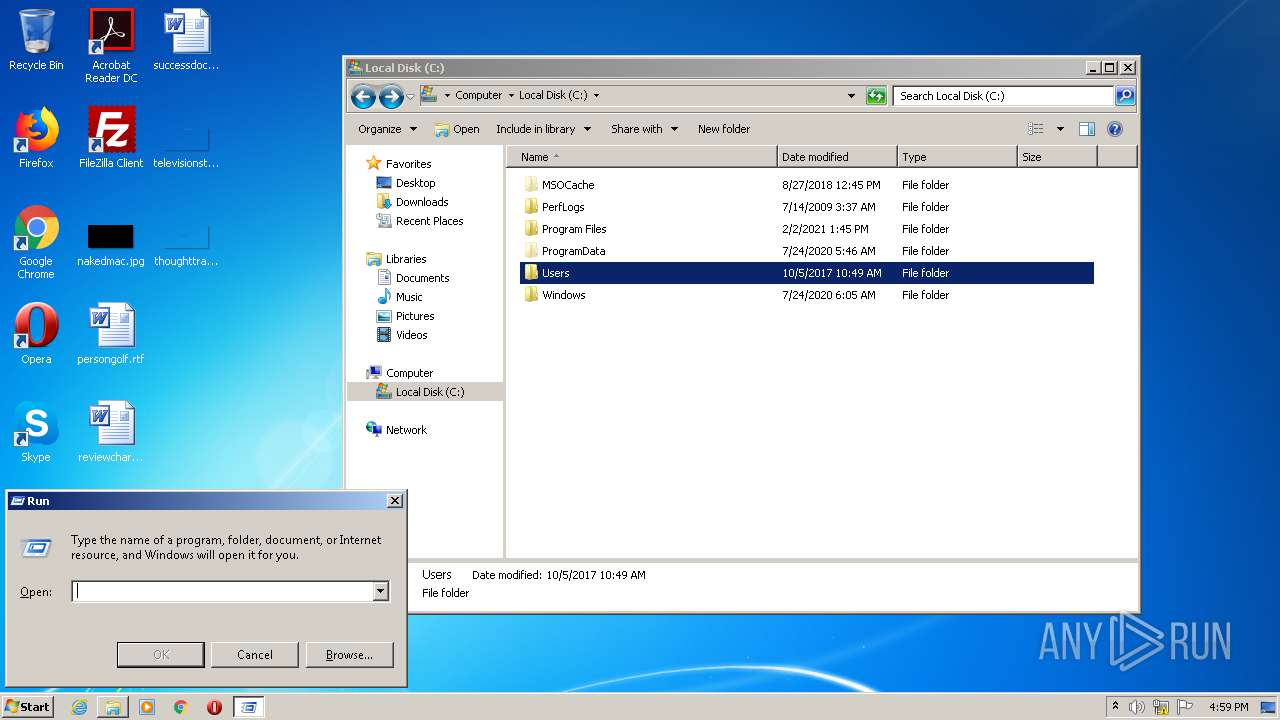
Manual execution by user
- explorer.exe (PID: 4048)
- snuvcdsm.exe (PID: 1112)
- RtkBtManServ.exe (PID: 4088)
- RtkBtManServ.exe (PID: 2592)
- RtkBtManServ.exe (PID: 1280)
- RtkBtManServ.exe (PID: 3456)
- RtkBtManServ.exe (PID: 2756)
- RtkBtManServ.exe (PID: 1916)
- RtkBtManServ.exe (PID: 3528)
- RtkBtManServ.exe (PID: 2212)
- RtkBtManServ.exe (PID: 2644)
- RtkBtManServ.exe (PID: 2928)
- RtkBtManServ.exe (PID: 3852)
- asfasf.exe (PID: 3300)
- asfasf.exe (PID: 2400)
- asfasf.exe (PID: 3412)
- asfasf.exe (PID: 336)
- asfasf.exe (PID: 2556)
- asfasf.exe (PID: 2860)
- asfasf.exe (PID: 1736)
- asfasf.exe (PID: 1844)
- asfasf.exe (PID: 3544)
- asfasf.exe (PID: 4032)
- asfasf.exe (PID: 3260)
- asfasf.exe (PID: 2808)
- asfasf.exe (PID: 2492)
- asfasf.exe (PID: 2304)
- asfasf.exe (PID: 2948)
- asfasf.exe (PID: 2728)
- asfasf.exe (PID: 2504)
- asfasf.exe (PID: 3216)
- asfasf.exe (PID: 1492)
- asfasf.exe (PID: 2344)
- asfasf.exe (PID: 3480)
- asfasf.exe (PID: 3752)
- asfasf.exe (PID: 4092)
- asfasf.exe (PID: 3516)
- asfasf.exe (PID: 2408)
- asfasf.exe (PID: 2168)
- asfasf.exe (PID: 3308)
- asfasf.exe (PID: 1748)
- asfasf.exe (PID: 2148)
- asfasf.exe (PID: 3912)
- asfasf.exe (PID: 2136)
- asfasf.exe (PID: 1316)
- asfasf.exe (PID: 2656)
- asfasf.exe (PID: 4060)
- asfasf.exe (PID: 2788)
- asfasf.exe (PID: 2636)
- asfasf.exe (PID: 2376)
- asfasf.exe (PID: 2284)
- asfasf.exe (PID: 1432)
- asfasf.exe (PID: 1864)
- asfasf.exe (PID: 3644)
- asfasf.exe (PID: 3924)
- asfasf.exe (PID: 2140)
- asfasf.exe (PID: 2724)
- asfasf.exe (PID: 3588)
- asfasf.exe (PID: 2124)
- asfasf.exe (PID: 1324)
- asfasf.exe (PID: 5512)
- asfasf.exe (PID: 4004)
- asfasf.exe (PID: 4724)
- asfasf.exe (PID: 5788)
- asfasf.exe (PID: 3304)
- asfasf.exe (PID: 5412)
- asfasf.exe (PID: 4112)
- asfasf.exe (PID: 5160)
- asfasf.exe (PID: 5416)
- asfasf.exe (PID: 5528)
- asfasf.exe (PID: 4460)
- asfasf.exe (PID: 5976)
- asfasf.exe (PID: 4680)
- asfasf.exe (PID: 4700)
- asfasf.exe (PID: 4728)
- asfasf.exe (PID: 5040)
- asfasf.exe (PID: 6124)
- asfasf.exe (PID: 5596)
- asfasf.exe (PID: 4656)
- asfasf.exe (PID: 1436)
- asfasf.exe (PID: 4456)
- asfasf.exe (PID: 4840)
- asfasf.exe (PID: 5060)
- asfasf.exe (PID: 5296)
- asfasf.exe (PID: 4968)
- asfasf.exe (PID: 6112)
- asfasf.exe (PID: 5208)
- asfasf.exe (PID: 4884)
- asfasf.exe (PID: 5028)
- asfasf.exe (PID: 4444)
- asfasf.exe (PID: 5352)
- asfasf.exe (PID: 4160)
- asfasf.exe (PID: 5820)
- asfasf.exe (PID: 4320)
- asfasf.exe (PID: 5640)
- asfasf.exe (PID: 5228)
- asfasf.exe (PID: 4296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:04:06 17:54:29+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 2564608 |
| InitializedDataSize: | 10240 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27a00a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | Obfuscated Name.exe |
| LegalCopyright: | |
| OriginalFileName: | Obfuscated Name.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2021 15:54:29 |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Obfuscated Name.exe |
| LegalCopyright: | - |
| OriginalFilename: | Obfuscated Name.exe |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Apr-2021 15:54:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
P;\x0e\x1c\x1dXg;d\x1f | 0x00002000 | 0x00001F64 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97614 |
.text | 0x00004000 | 0x00271E58 | 0x00272000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.97943 |
.rsrc | 0x00276000 | 0x000004F0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.77917 |
.reloc | 0x00278000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
0x0027A000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.682132 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
156
Monitored processes
99
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
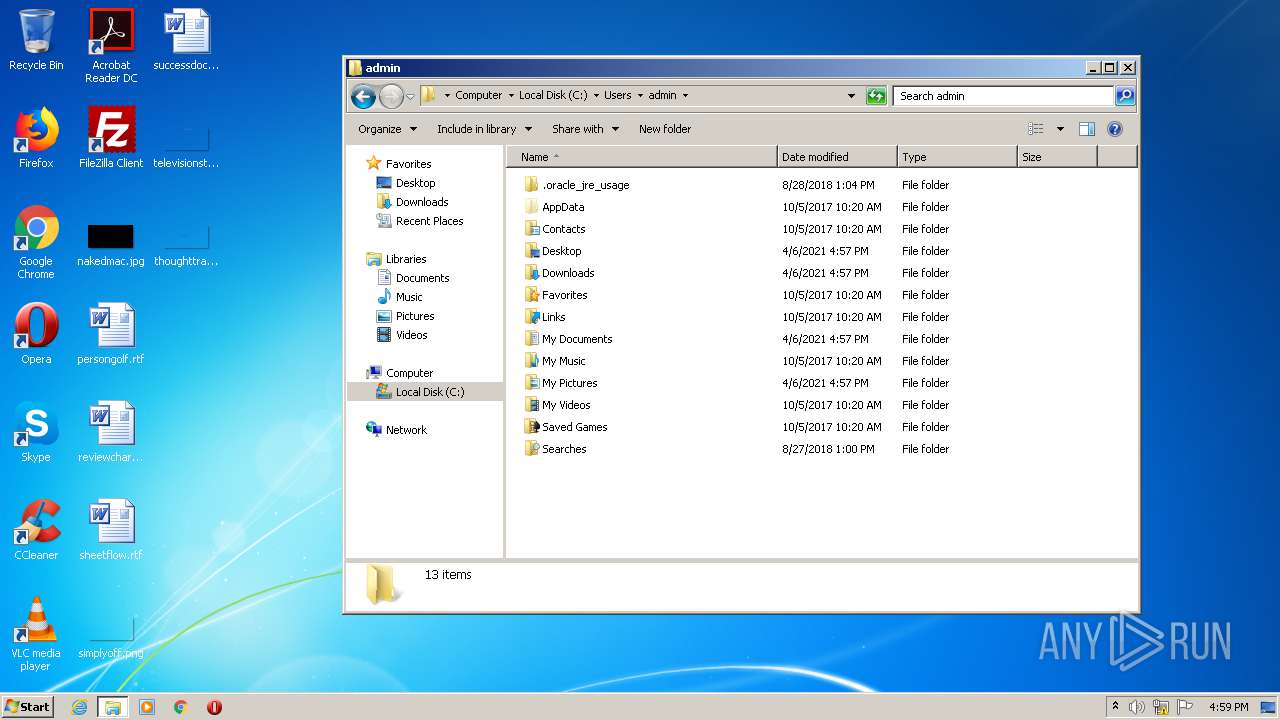
| 336 | "C:\Users\admin\AppData\Local\Temp\asfasf.exe" | C:\Users\admin\AppData\Local\Temp\asfasf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1112 | "C:\Users\admin\AppData\Local\Temp\snuvcdsm.exe" | C:\Users\admin\AppData\Local\Temp\snuvcdsm.exe | explorer.exe | ||||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: Web Browser Password Viewer Exit code: 0 Version: 2.06 Modules
| |||||||||||||||
| 1280 | "C:\Users\admin\AppData\Local\Temp\RtkBtManServ.exe" | C:\Users\admin\AppData\Local\Temp\RtkBtManServ.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RtkBtManServ Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1316 | "C:\Users\admin\AppData\Local\Temp\asfasf.exe" | C:\Users\admin\AppData\Local\Temp\asfasf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\AppData\Local\Temp\asfasf.exe" | C:\Users\admin\AppData\Local\Temp\asfasf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1432 | "C:\Users\admin\AppData\Local\Temp\asfasf.exe" | C:\Users\admin\AppData\Local\Temp\asfasf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1436 | "C:\Users\admin\AppData\Local\Temp\asfasf.exe" | C:\Users\admin\AppData\Local\Temp\asfasf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1492 | "C:\Users\admin\AppData\Local\Temp\asfasf.exe" | C:\Users\admin\AppData\Local\Temp\asfasf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1736 | "C:\Users\admin\AppData\Local\Temp\asfasf.exe" | C:\Users\admin\AppData\Local\Temp\asfasf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1748 | "C:\Users\admin\AppData\Local\Temp\asfasf.exe" | C:\Users\admin\AppData\Local\Temp\asfasf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
553
Read events
537
Write events
16
Delete events
0
Modification events
| (PID) Process: | (3440) asfasf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3440) asfasf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4084) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4084) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4084) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4084) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4084) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4084) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (4084) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4084) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
73
Suspicious files
24
Text files
218
Unknown types
0
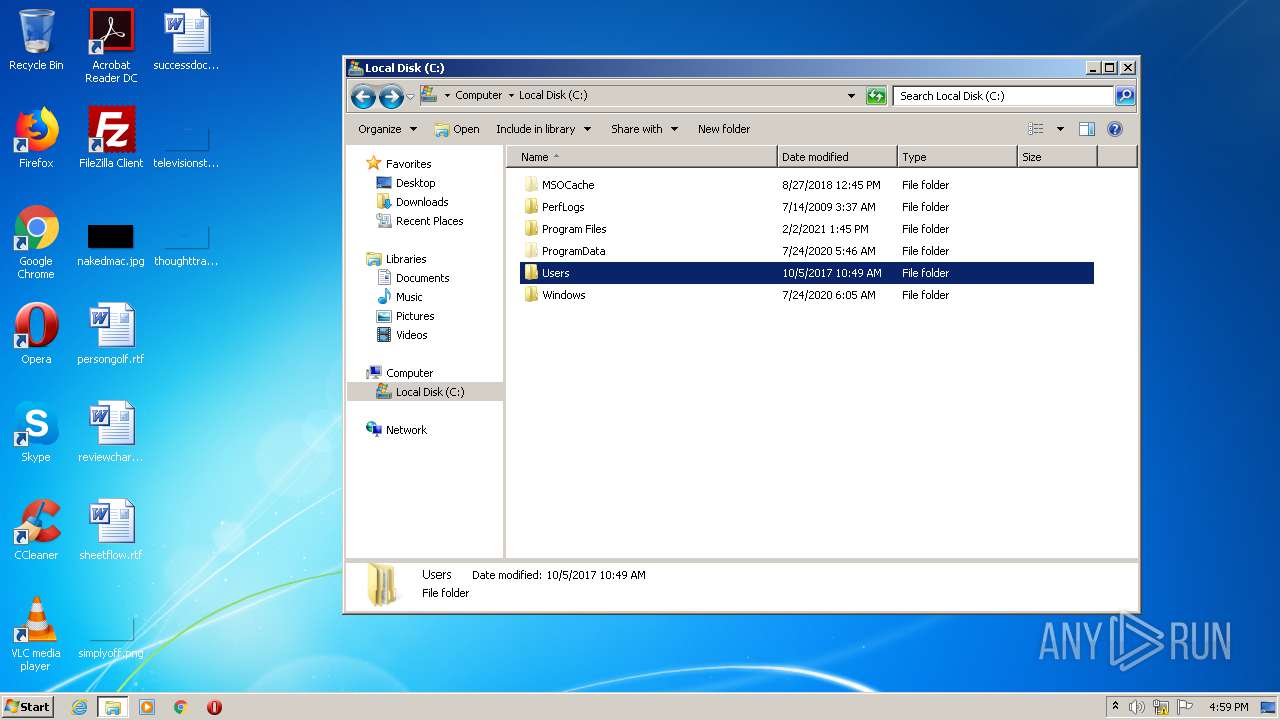
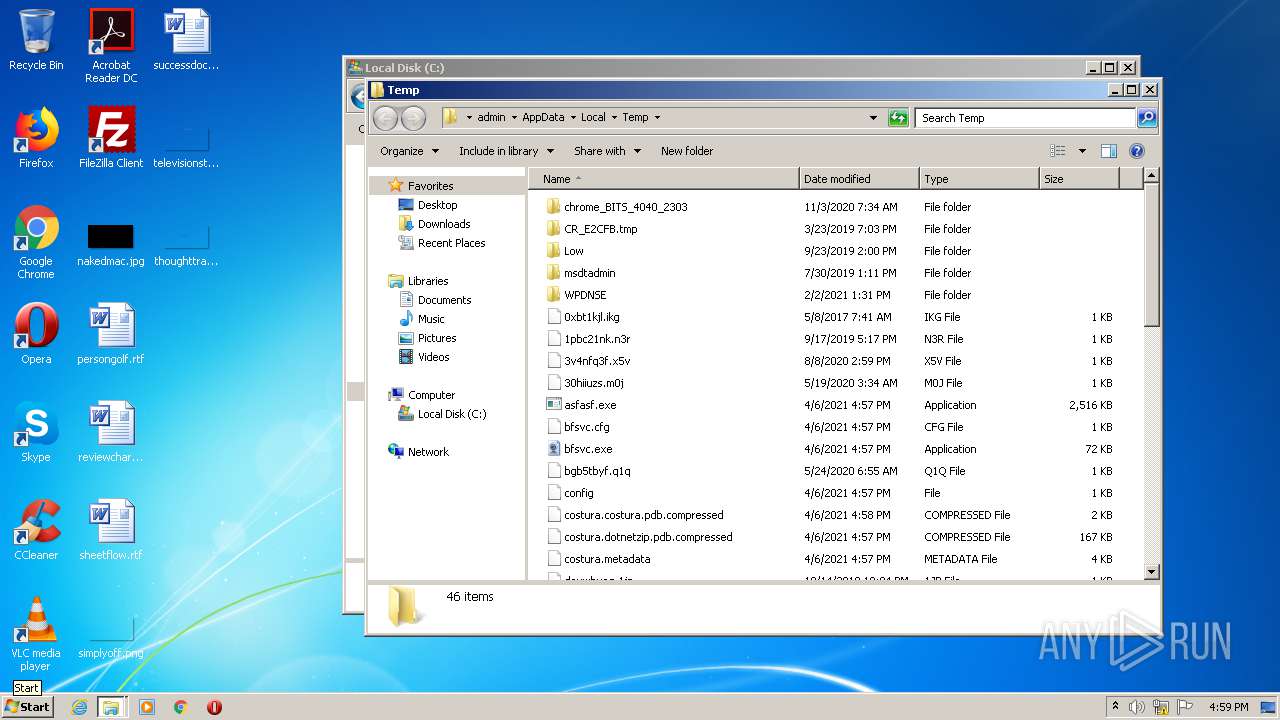
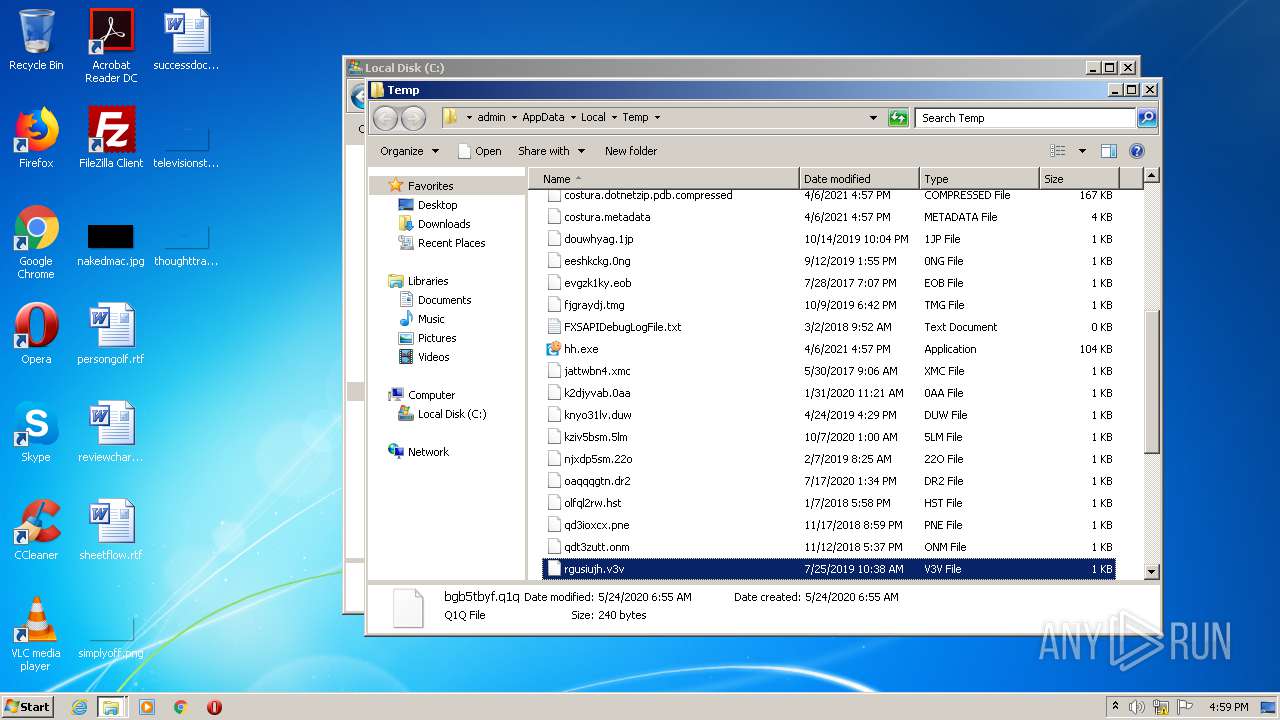
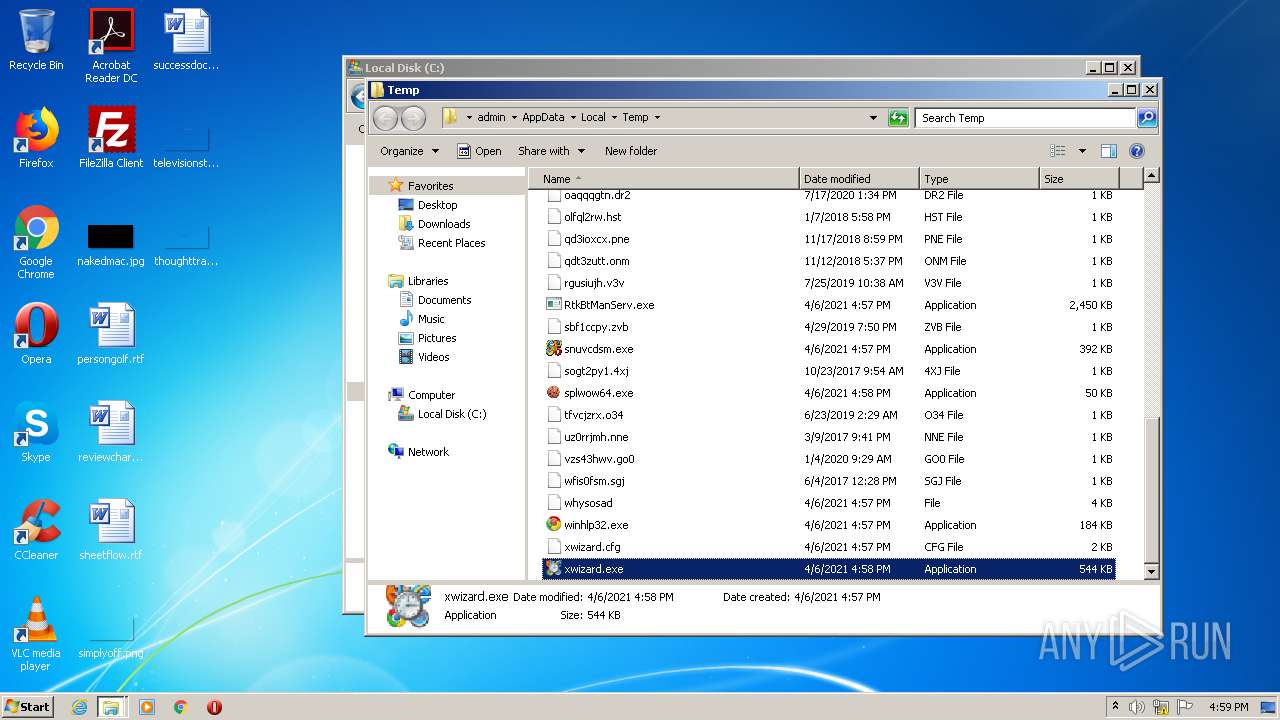
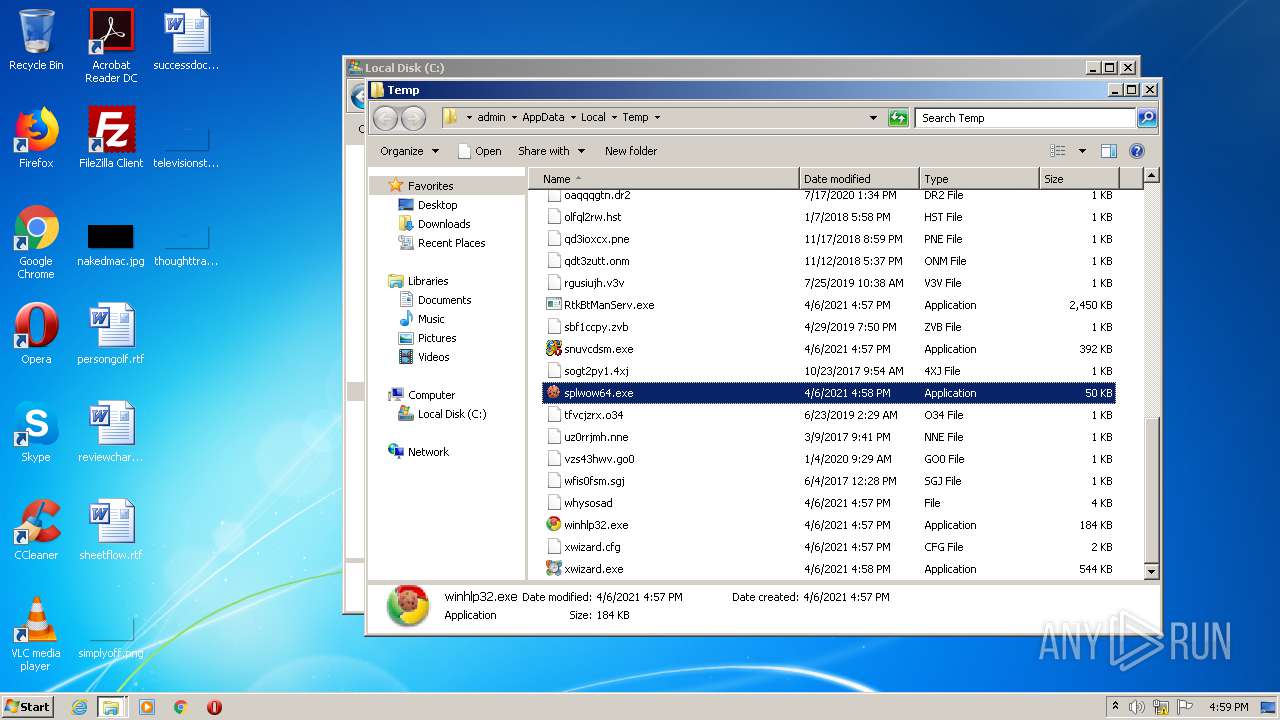
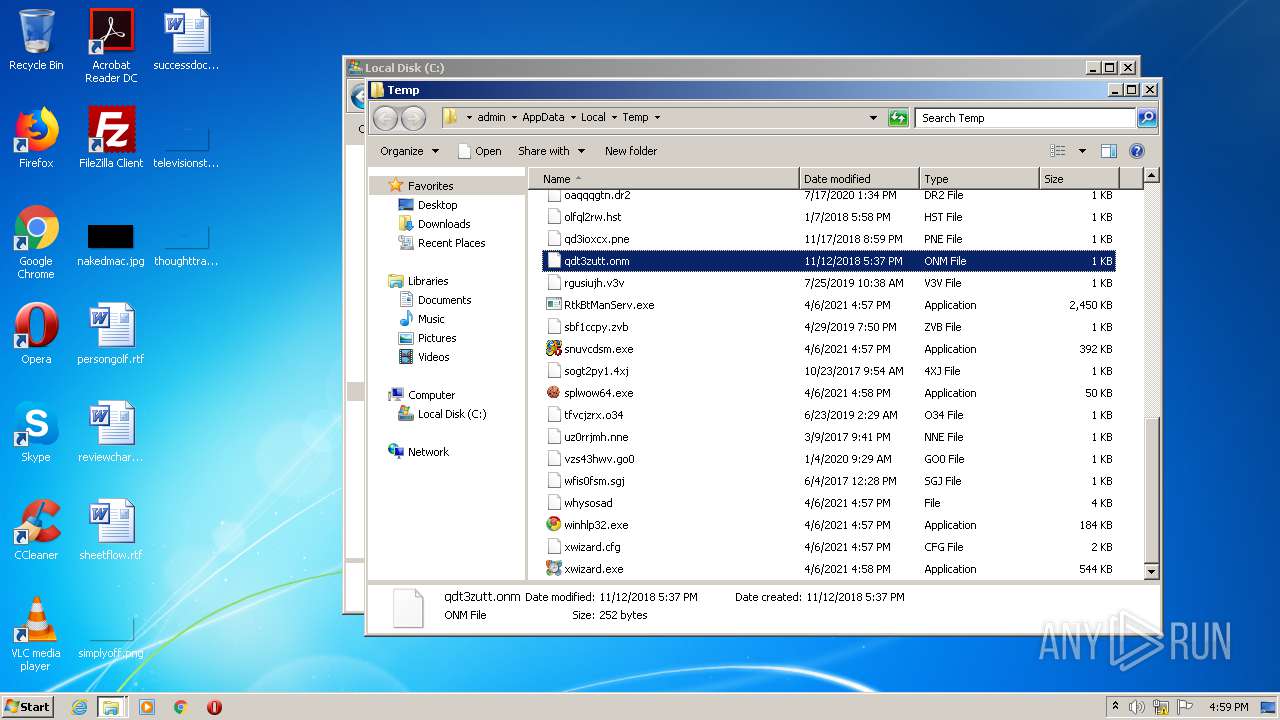
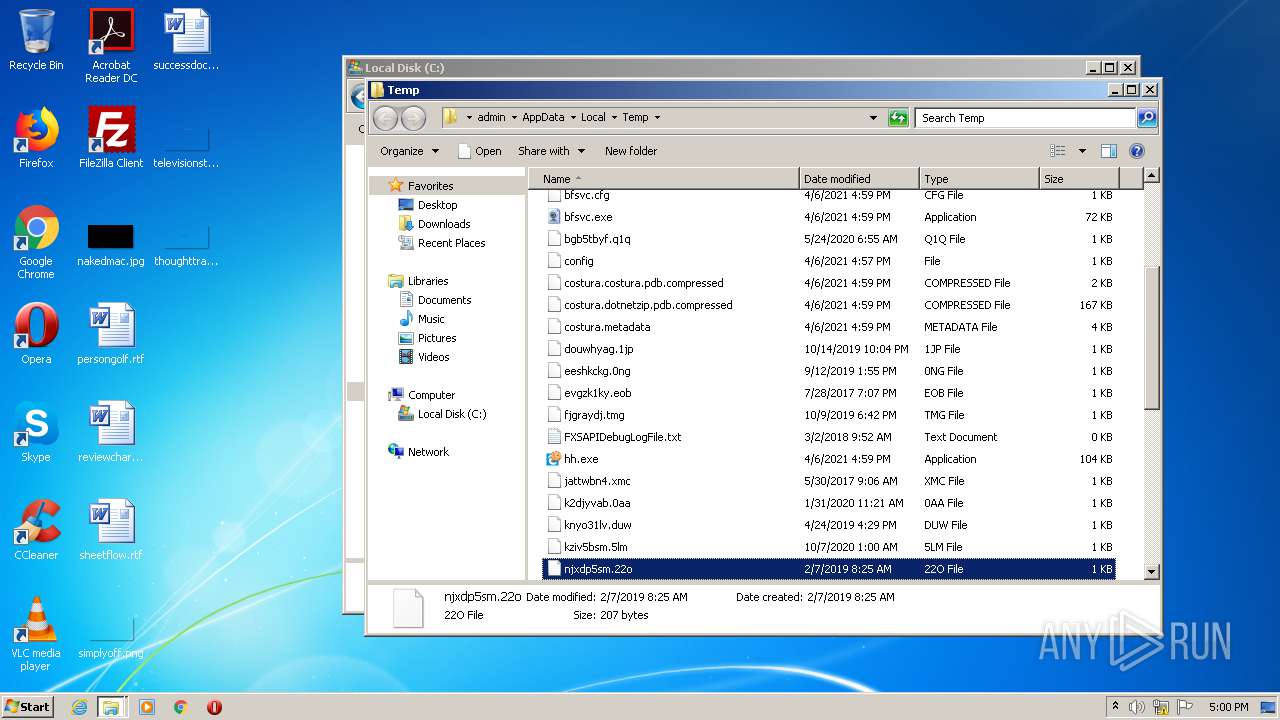
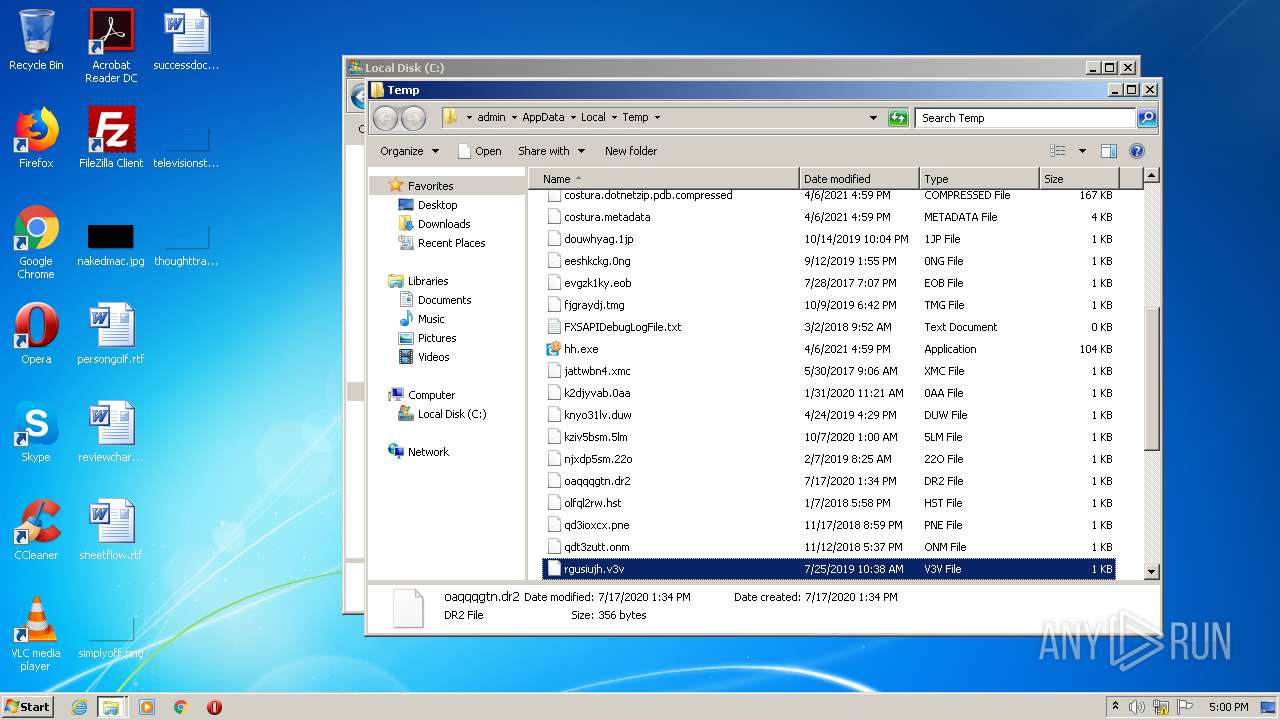
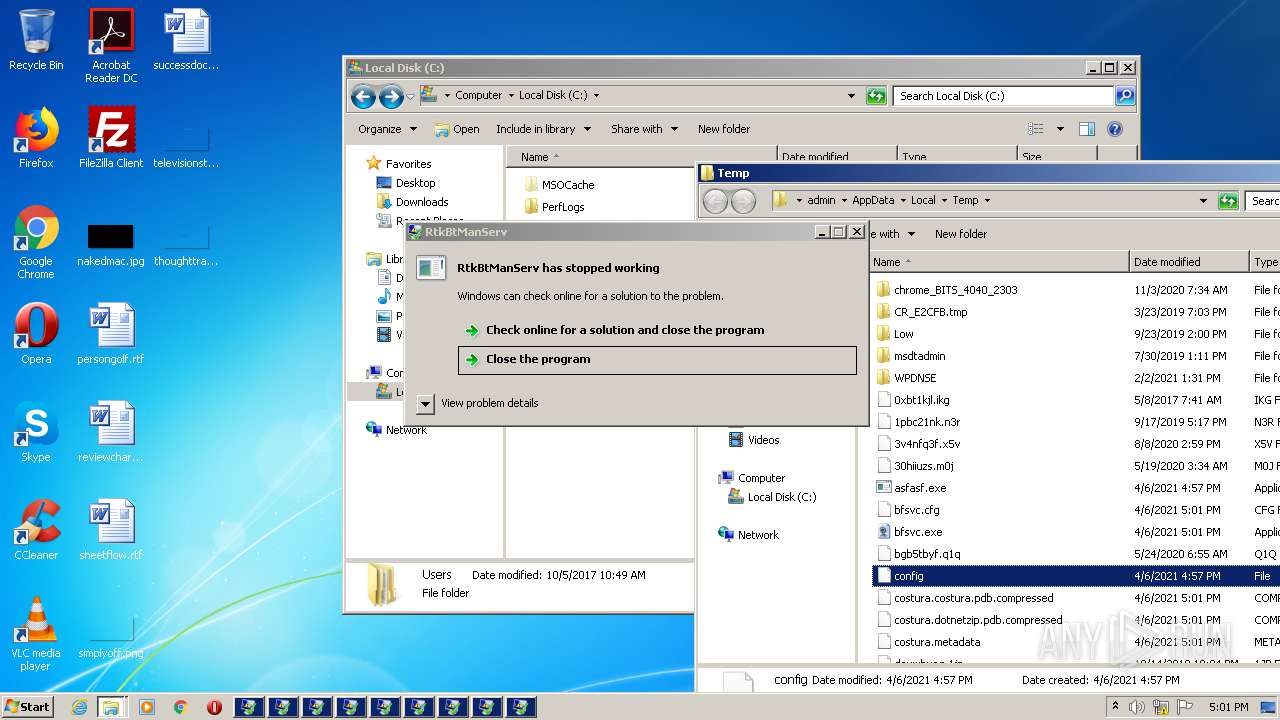
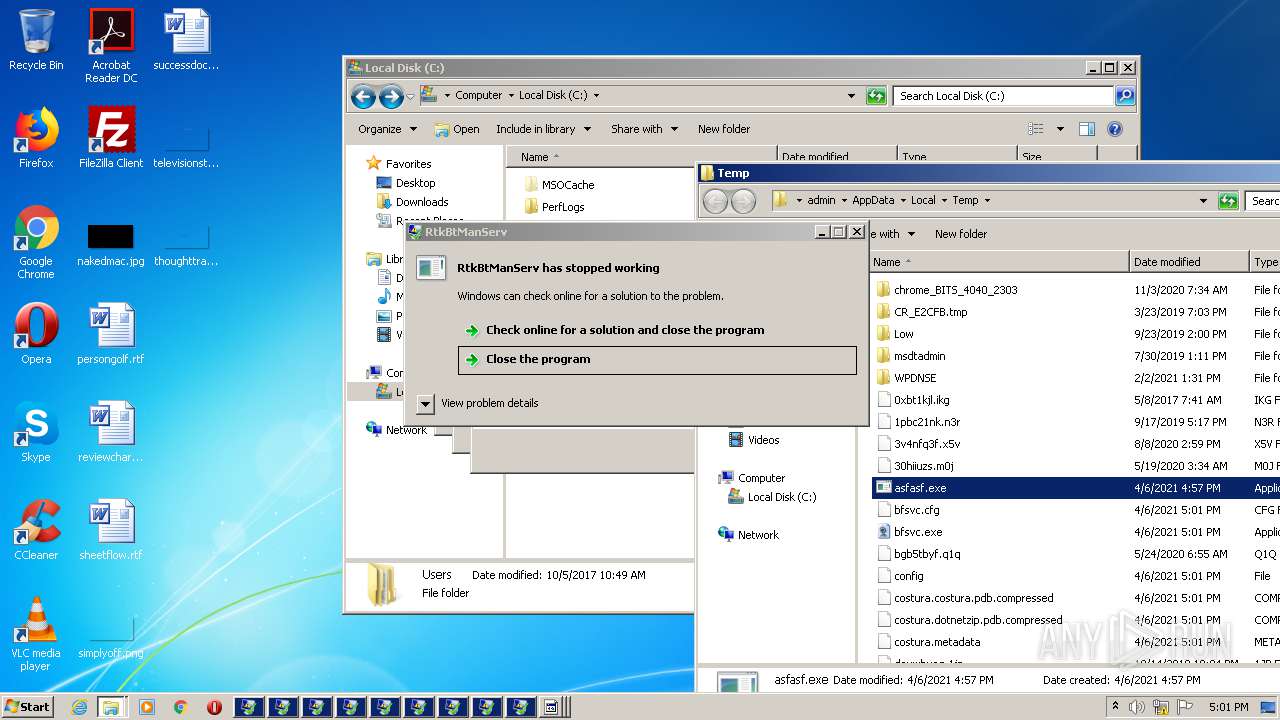
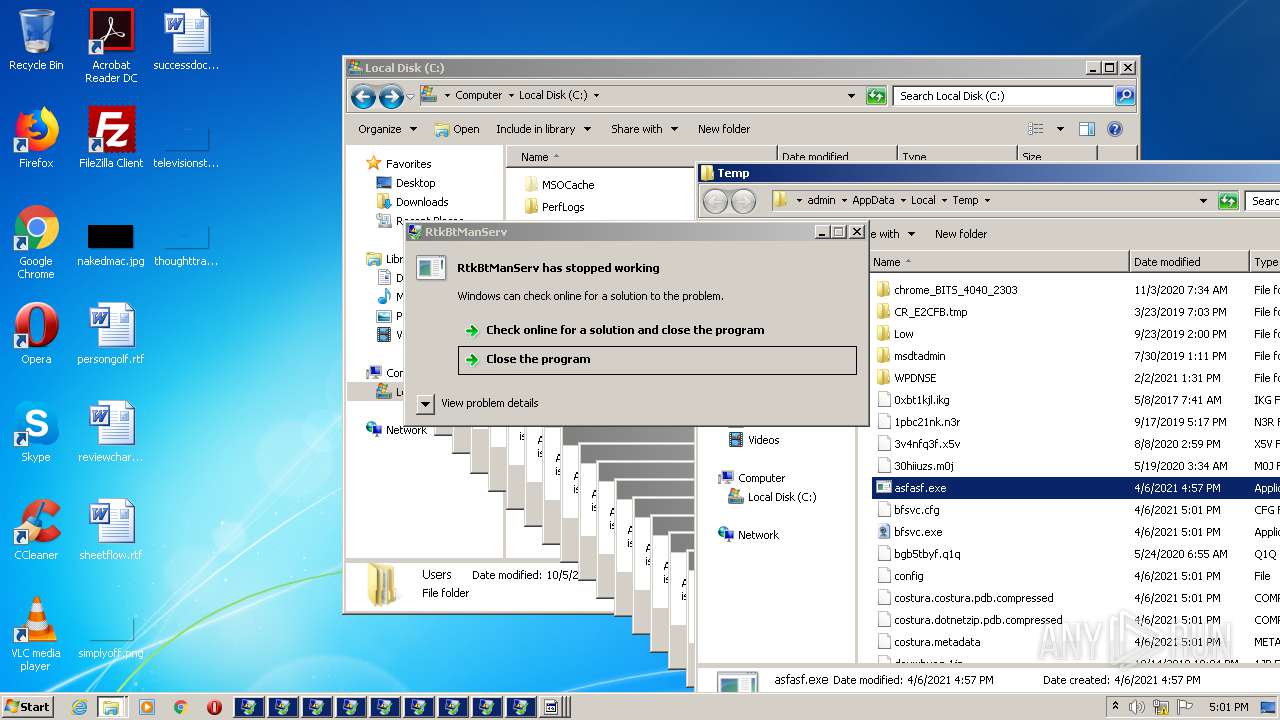
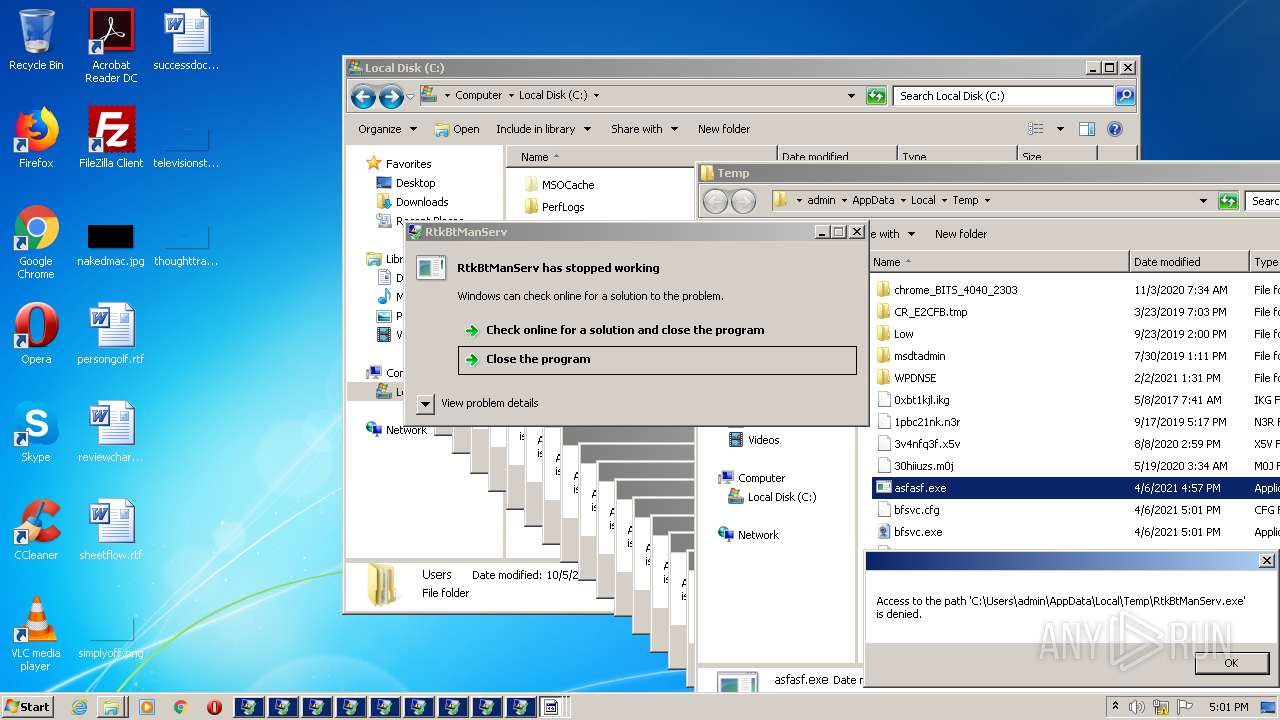
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
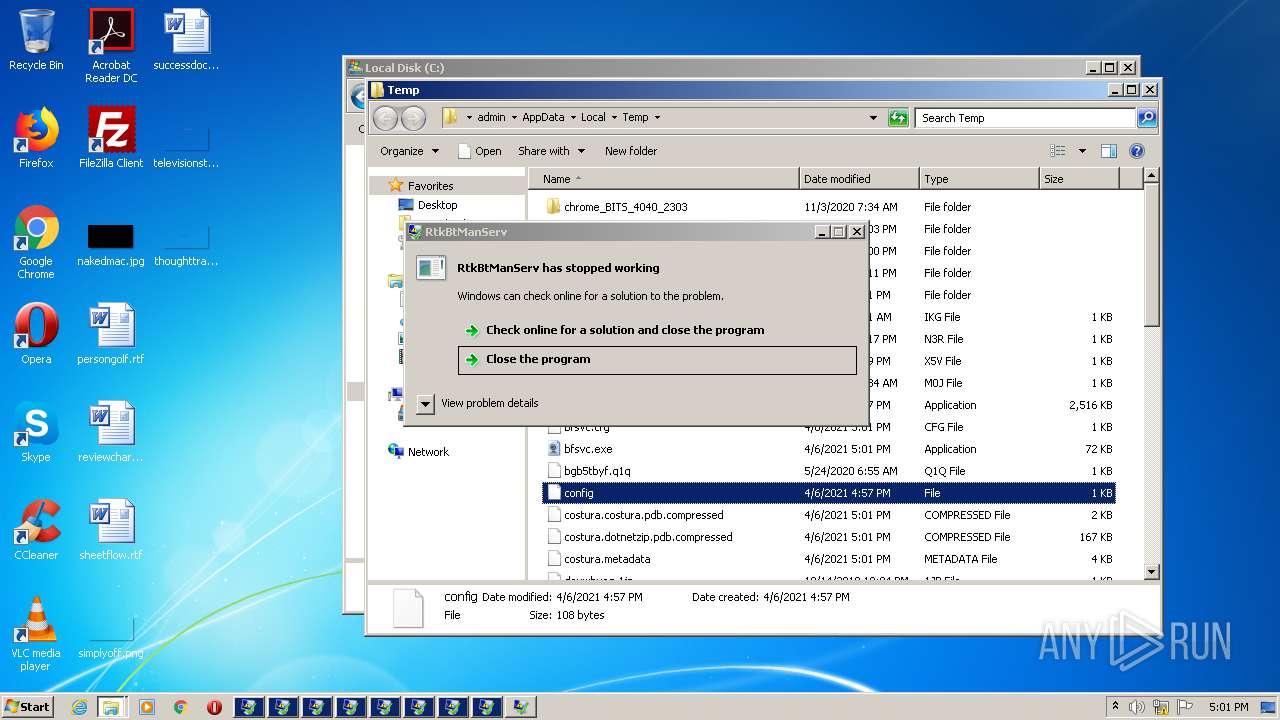
| 3440 | asfasf.exe | C:\Users\admin\AppData\Local\Temp\config | text | |
MD5:1BA367D0F9AAC0F650E65AB7401776C0 | SHA256:68C4EC552C98F3B5A4744E4EEFADD6364DC8075C2E718B7BCBFC76625AA60D03 | |||
| 3440 | asfasf.exe | C:\Users\admin\AppData\Local\Temp\RtkBtManServ.exe | executable | |
MD5:— | SHA256:— | |||
| 4084 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\bfsvc.cfg | text | |
MD5:— | SHA256:— | |||
| 4084 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\hh.exe | executable | |
MD5:4D4C98ECA32B14AEB074DB34CD0881E4 | SHA256:4182172A01BDFC08C5CF7E8652F7D9D81858345A770E2B6B507840E4C1C7764F | |||
| 2592 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\costura.metadata | text | |
MD5:— | SHA256:— | |||
| 4084 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\xwizard.exe | executable | |
MD5:DF991217F1CFADD9ACFA56F878DA5EE7 | SHA256:DEB1246347CE88E8CDD63A233A64BC2090B839F2D933A3097A2FD8FD913C4112 | |||
| 2592 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\bfsvc.cfg | text | |
MD5:— | SHA256:— | |||
| 4084 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\costura.dotnetzip.pdb.compressed | binary | |
MD5:74D98C2F5DF1ABC721DB40D7A8760EF9 | SHA256:2E4A99ACCFEBE28E54AB148B95E7012EC9CF72A5DE1CB3AB5BC7969EBF41BCE6 | |||
| 4084 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\winhlp32.exe | executable | |
MD5:A776E68F497C996788B406A3DC5089EB | SHA256:071E26DDF5323DD9ED6671BCDE89DF73D78BAC2336070E6CB9E3E4B93BDE78D1 | |||
| 2592 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\snuvcdsm.exe | executable | |
MD5:053778713819BEAB3DF309DF472787CD | SHA256:F999357A17E672E87FBED66D14BA2BEBD6FB04E058A1AAE0F0FDC49A797F58FE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4084 | RtkBtManServ.exe | 172.67.212.52:443 | itroublvehacker.cf | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
itroublvehacker.cf |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .cf Domain |
4084 | RtkBtManServ.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.cf) in TLS SNI |