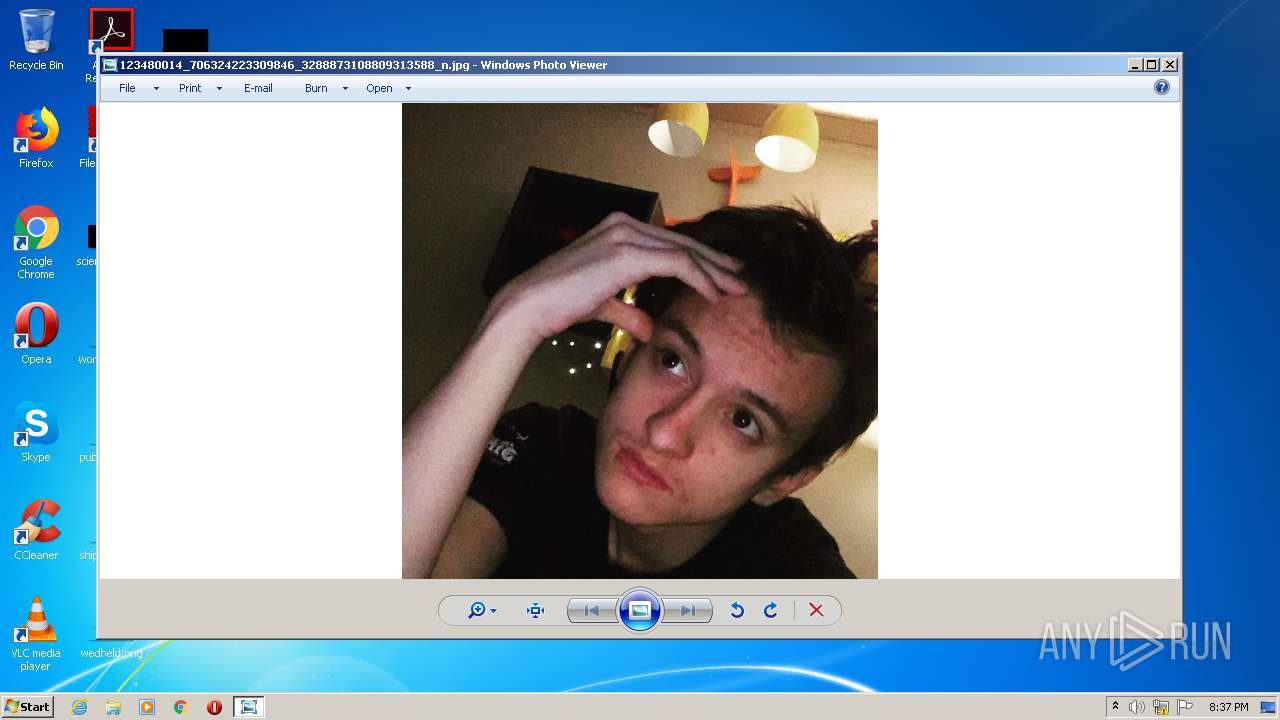
| File name: | 123480014_706324223309846_3288873108809313588_n.jpg |
| Full analysis: | https://app.any.run/tasks/99dc1e48-f69b-42e9-afc7-2b8e4cd25d6f |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 20:37:21 |
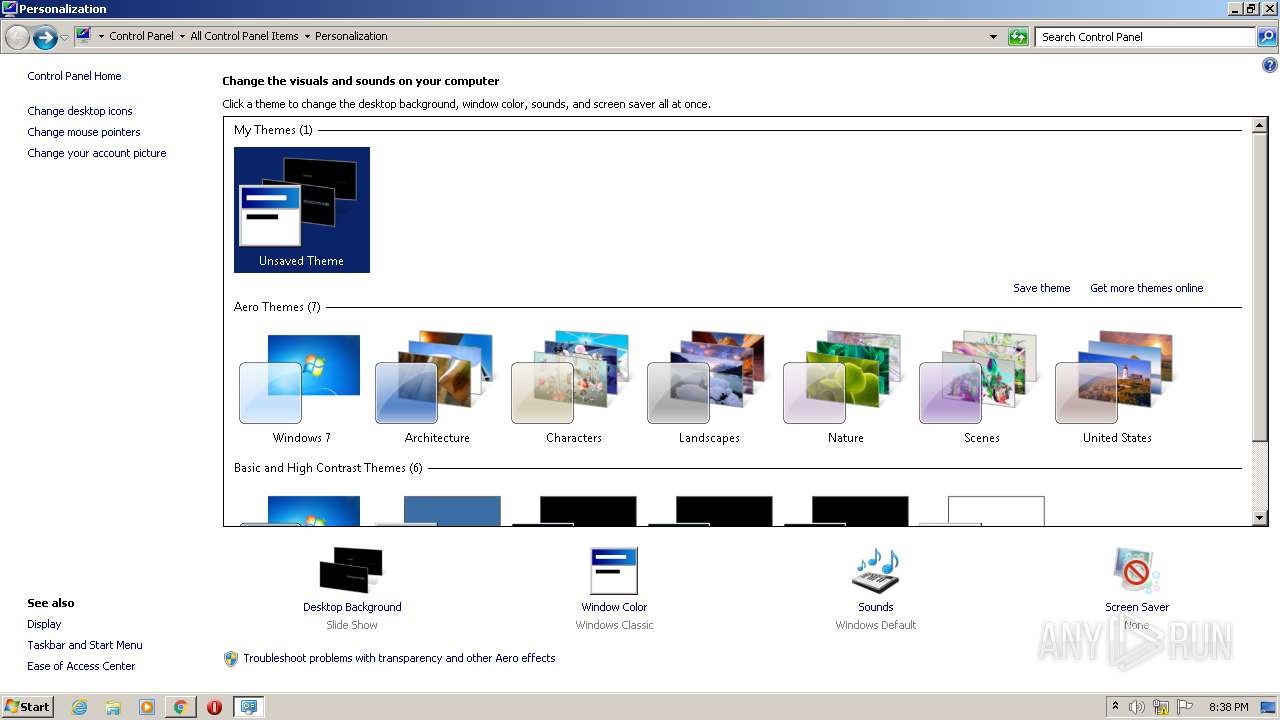
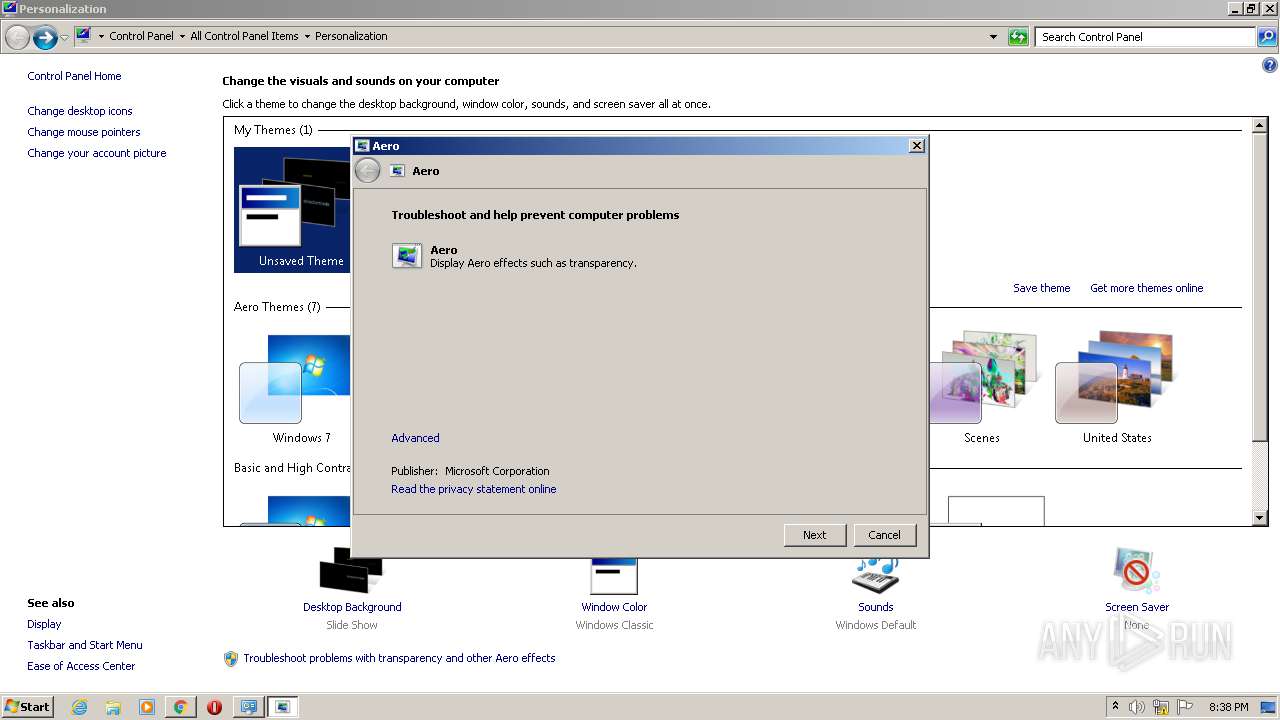
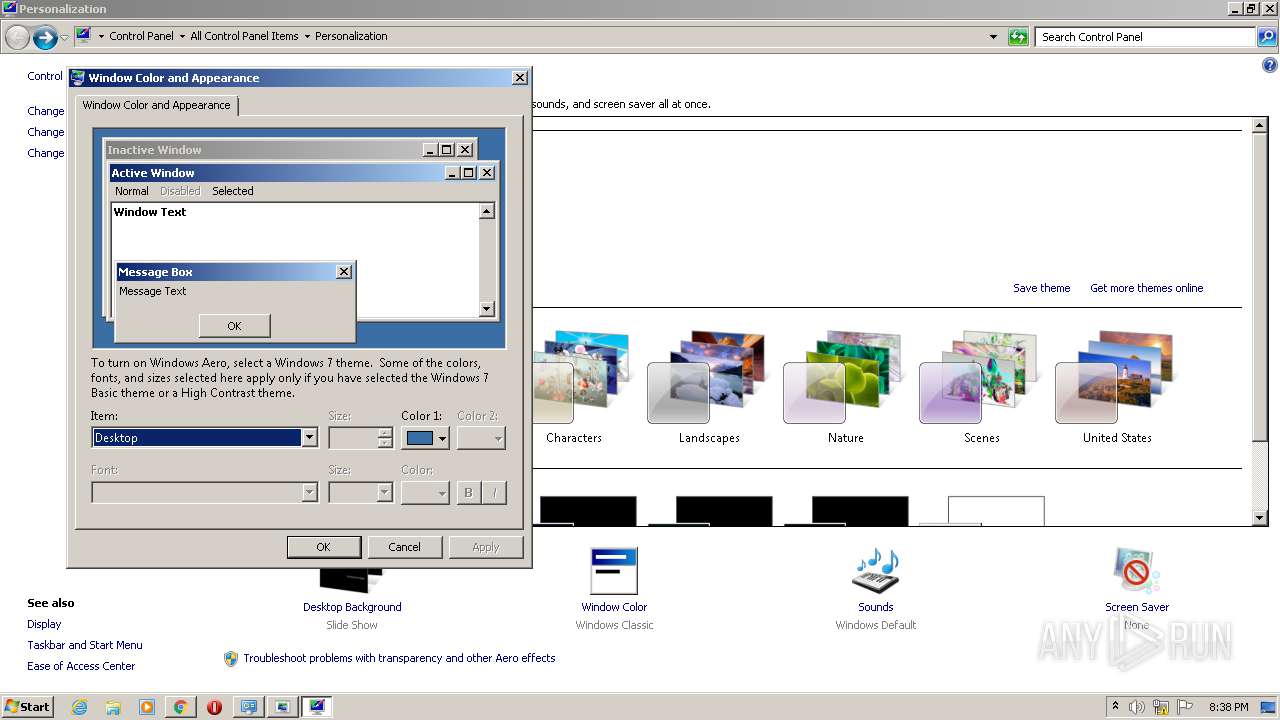
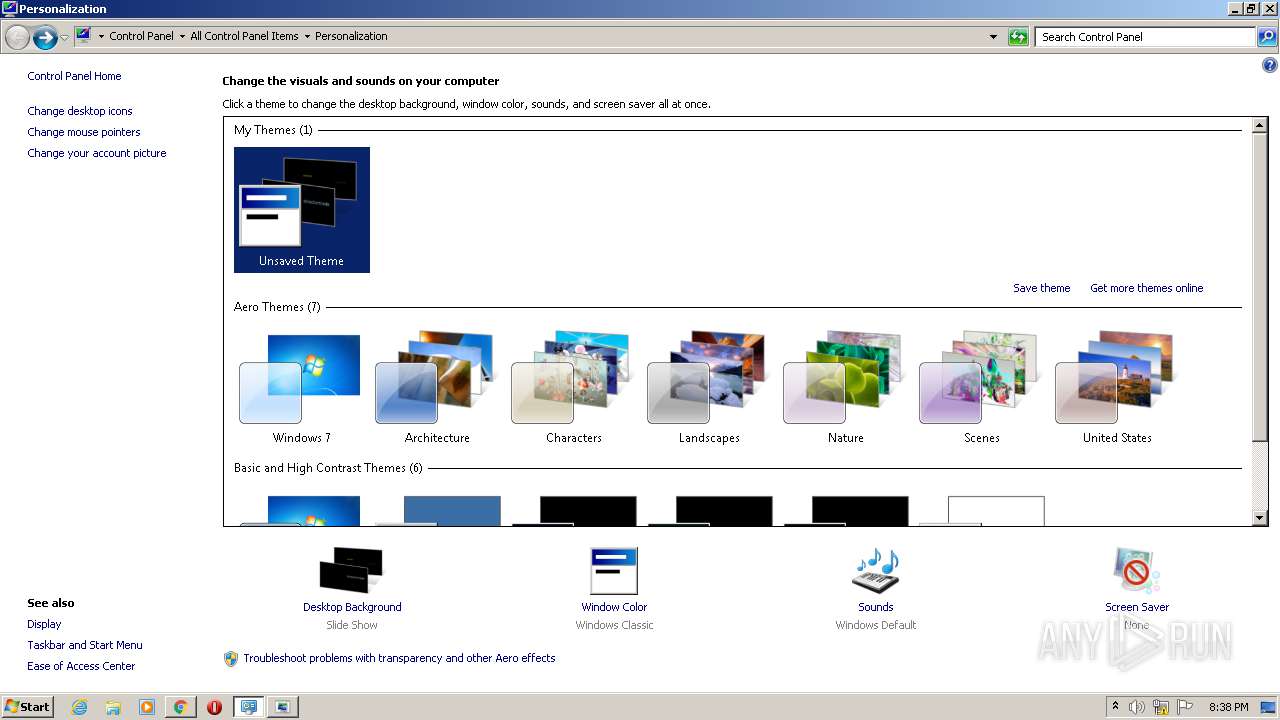
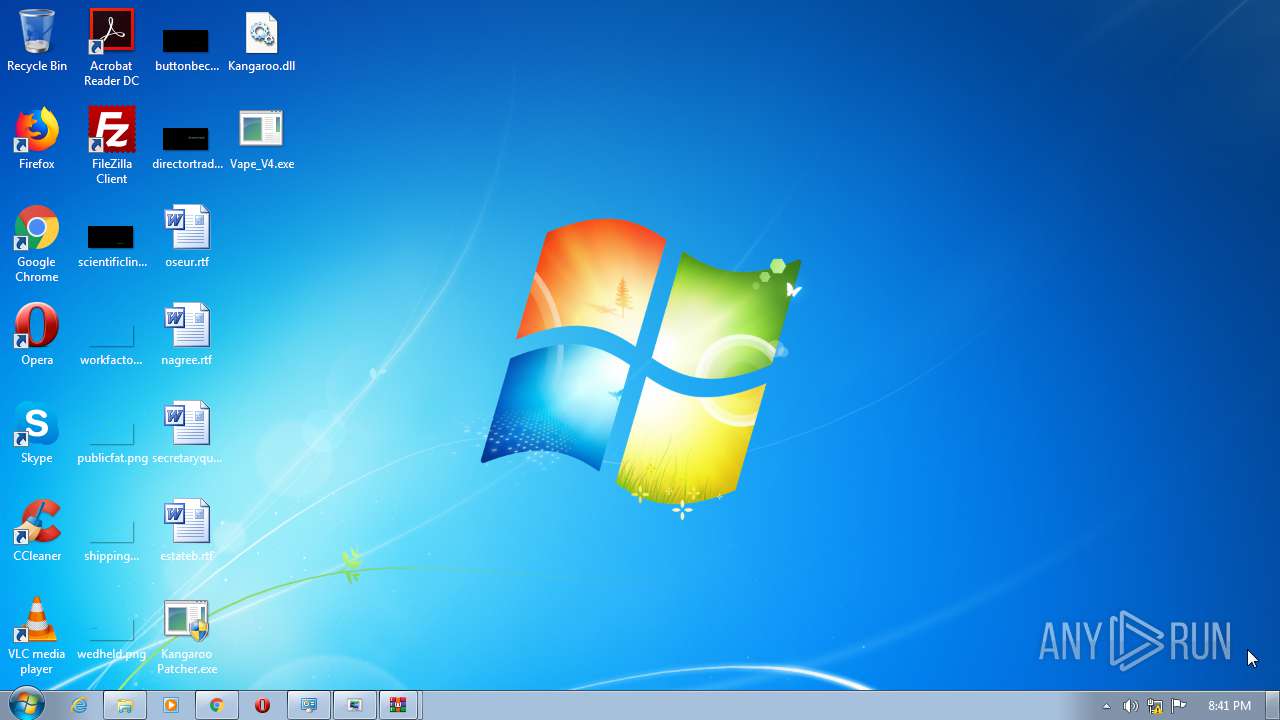
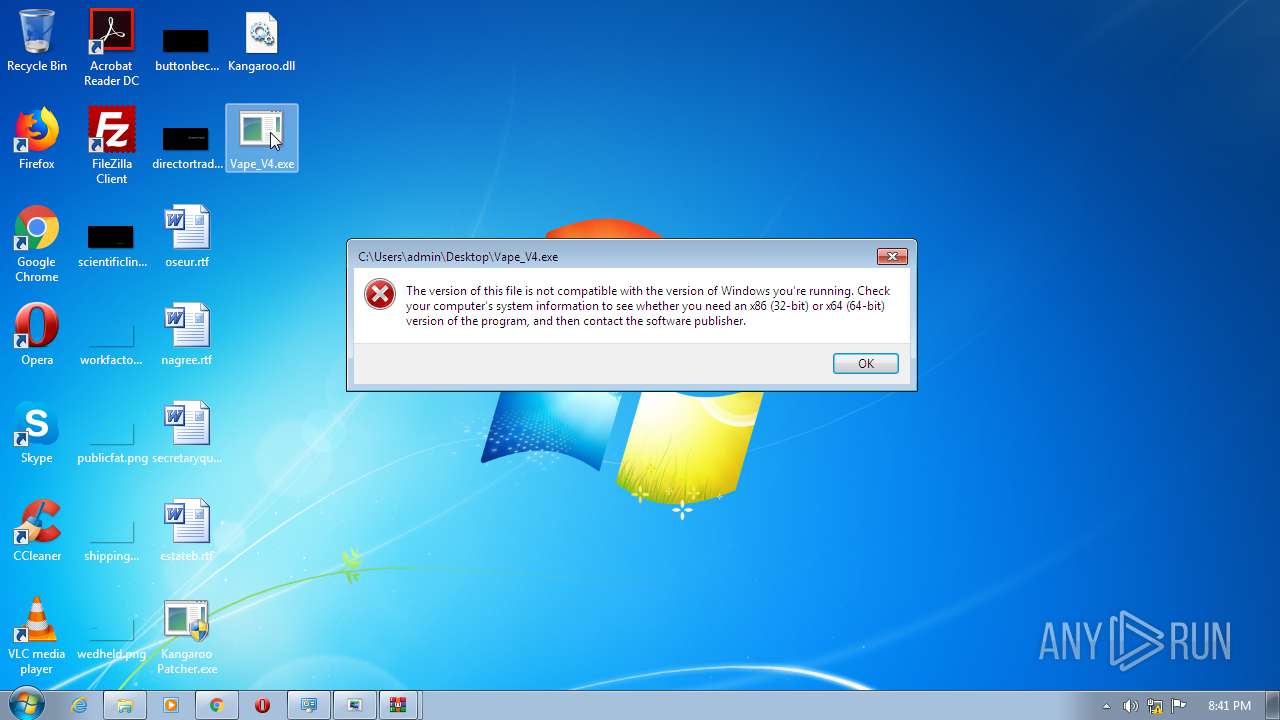
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | image/jpeg |
| File info: | JPEG image data, JFIF standard 1.01, aspect ratio, density 72x72, segment length 16, progressive, precision 8, 719x719, frames 3 |
| MD5: | 5A183E04E696D2CAE4EE77B734DE26F1 |
| SHA1: | D0BEF1A4720E6E3870E4D791BA0E571EC72D4D68 |
| SHA256: | 74D12974247F85250F3DE8CD1FB85BAD758CFE713235DAEF70AC1BB1E4D2A030 |
| SSDEEP: | 768:qSSclXqX94aucUG6uWvNP+en8fVnM+WkTRKxW79xNNkL6EeHsKSXYiwllti:zaucU1uWvNafVMXkGW79fXEeMGiclk |
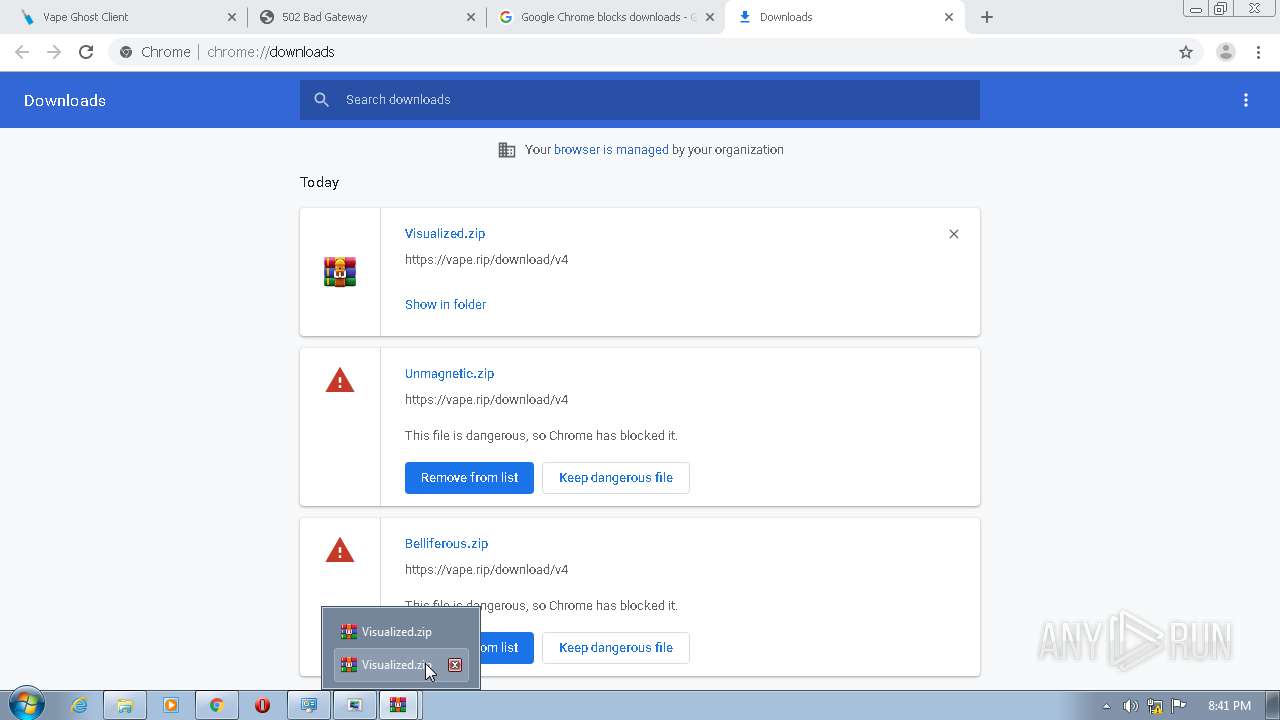
MALICIOUS
Drops executable file immediately after starts
- msdt.exe (PID: 3476)
- msdt.exe (PID: 4080)
Starts Visual C# compiler
- sdiagnhost.exe (PID: 120)
SUSPICIOUS
Drops a file that was compiled in debug mode
- msdt.exe (PID: 3476)
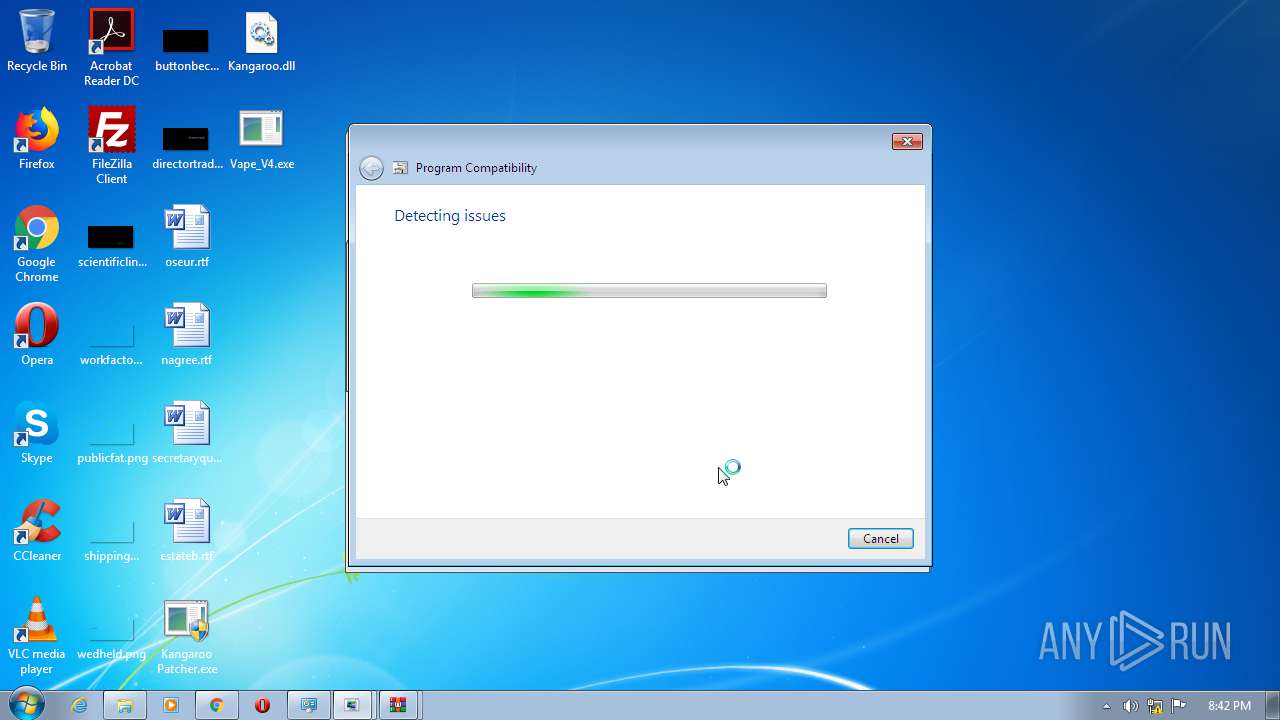
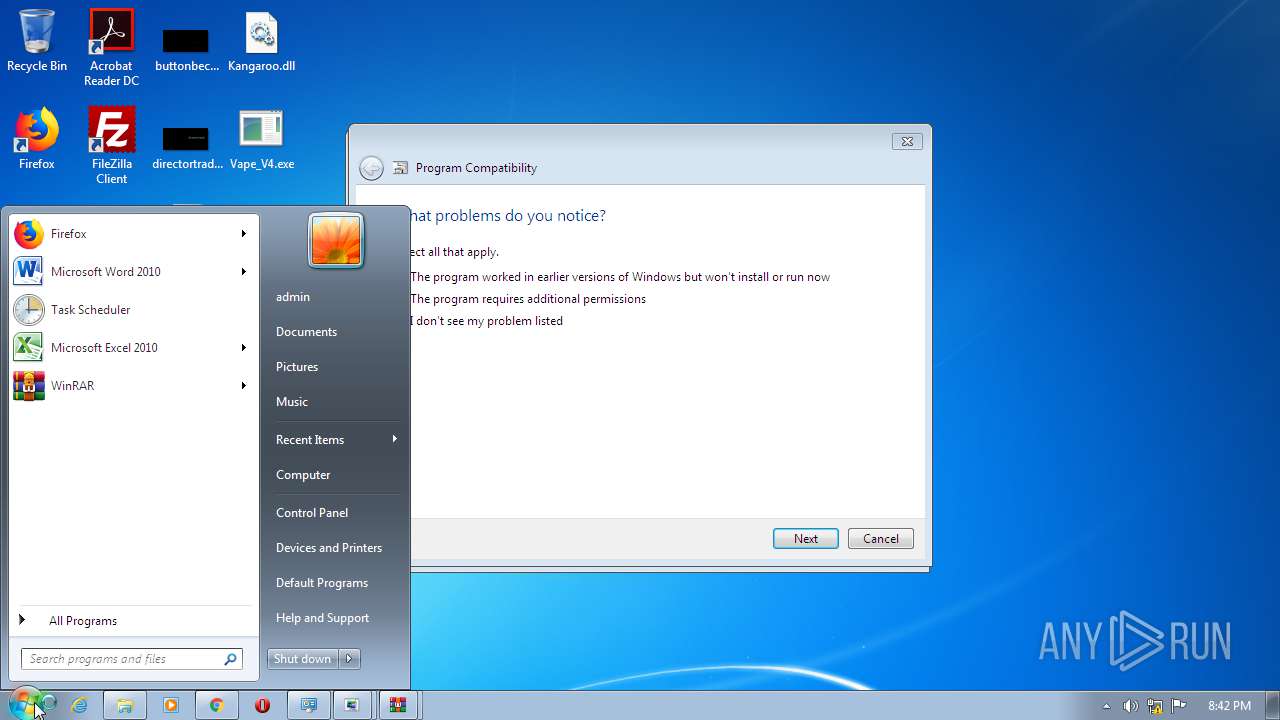
Application launched itself
- msdt.exe (PID: 3312)
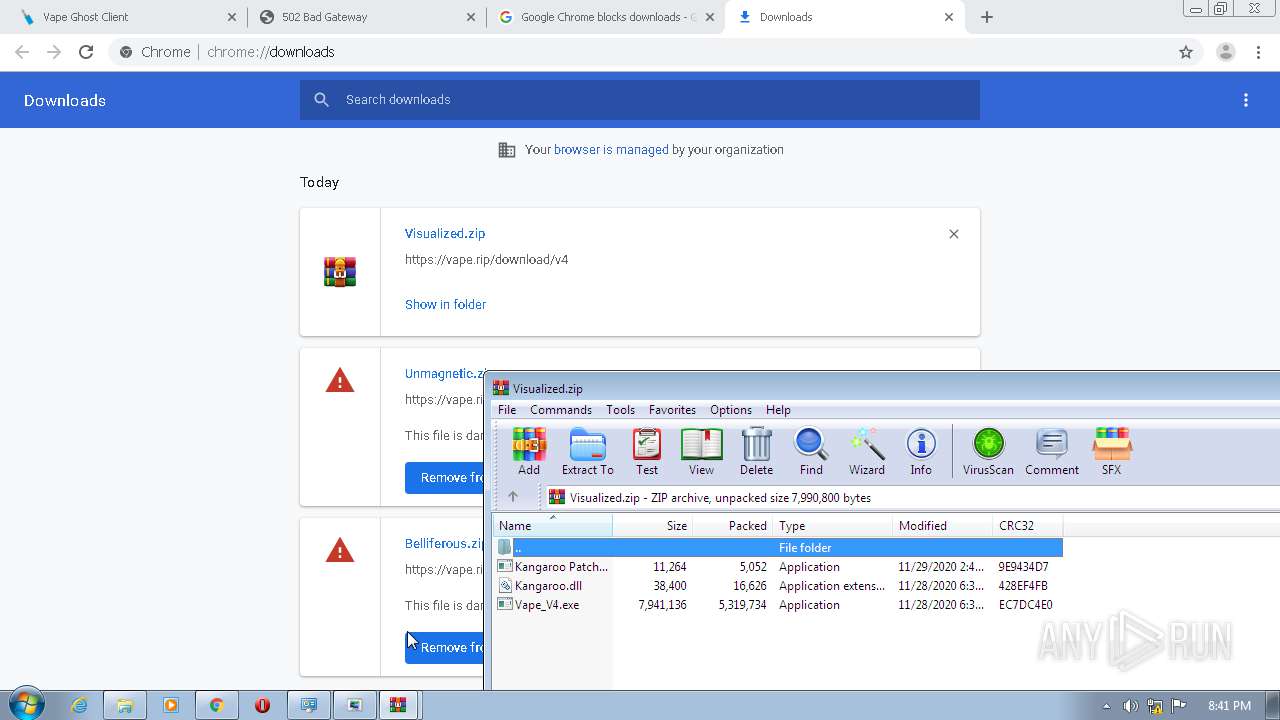
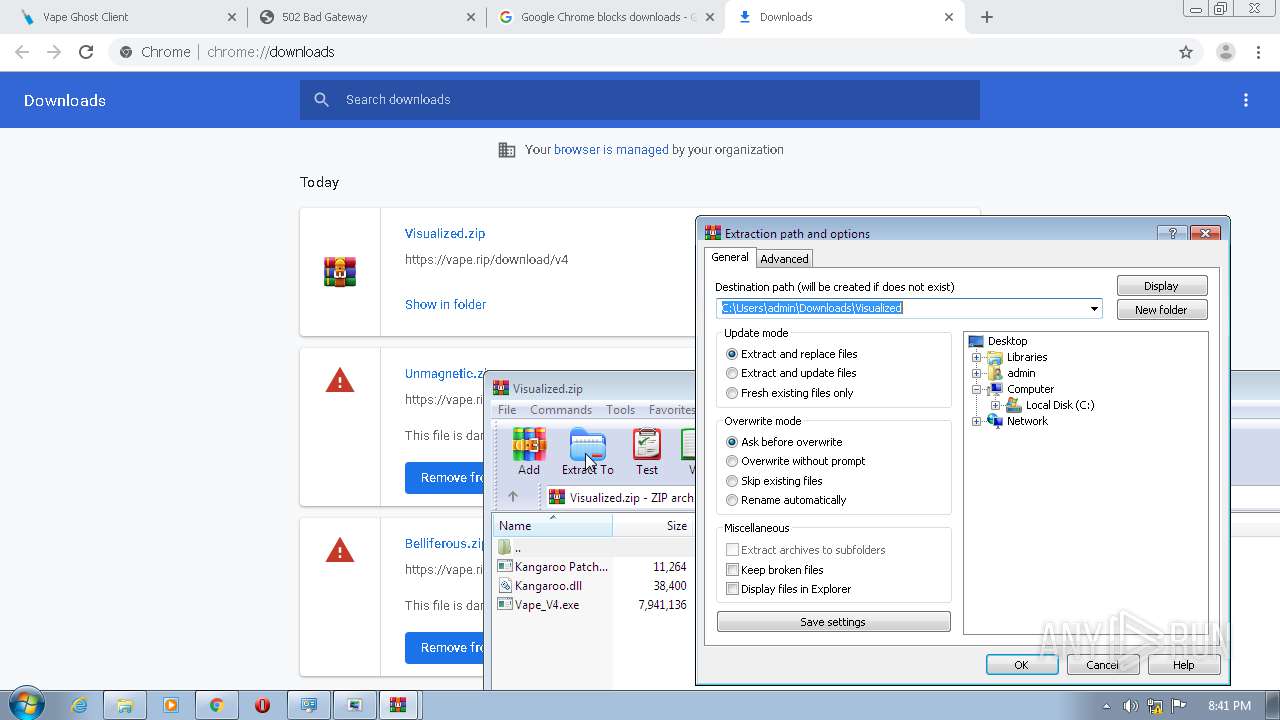
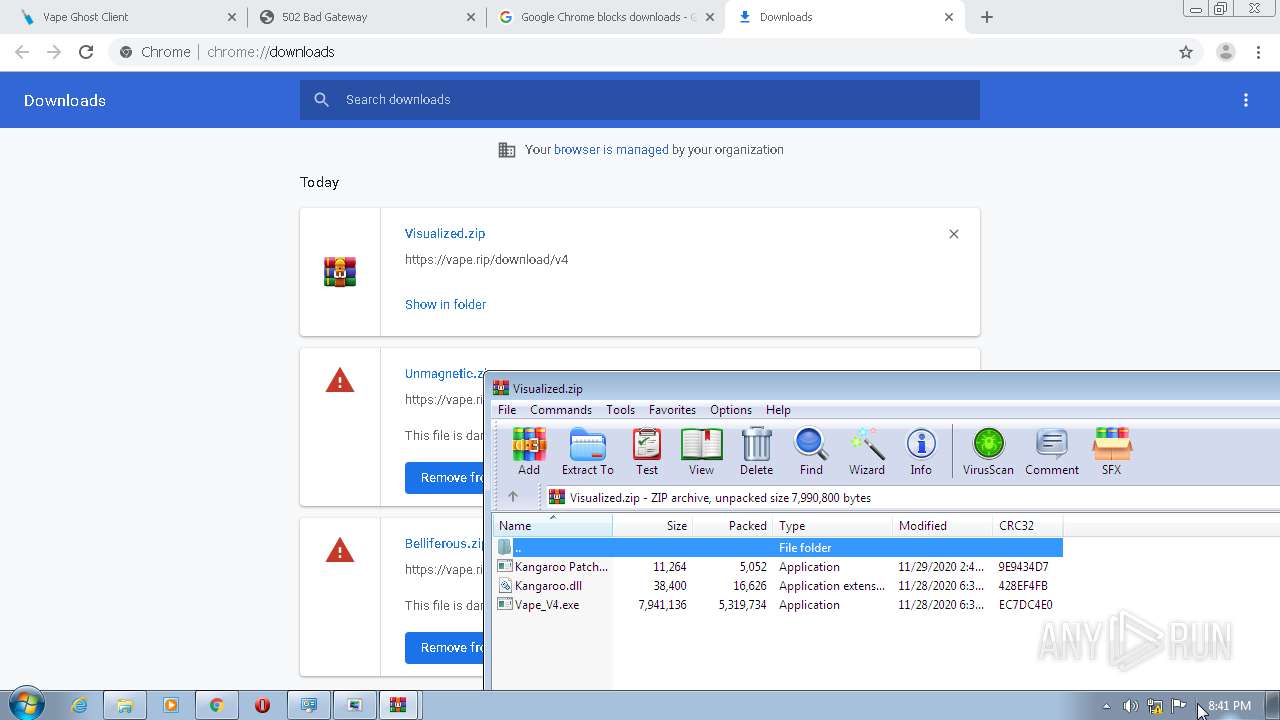
Executable content was dropped or overwritten
- msdt.exe (PID: 3476)
- WinRAR.exe (PID: 2872)
- msdt.exe (PID: 4080)
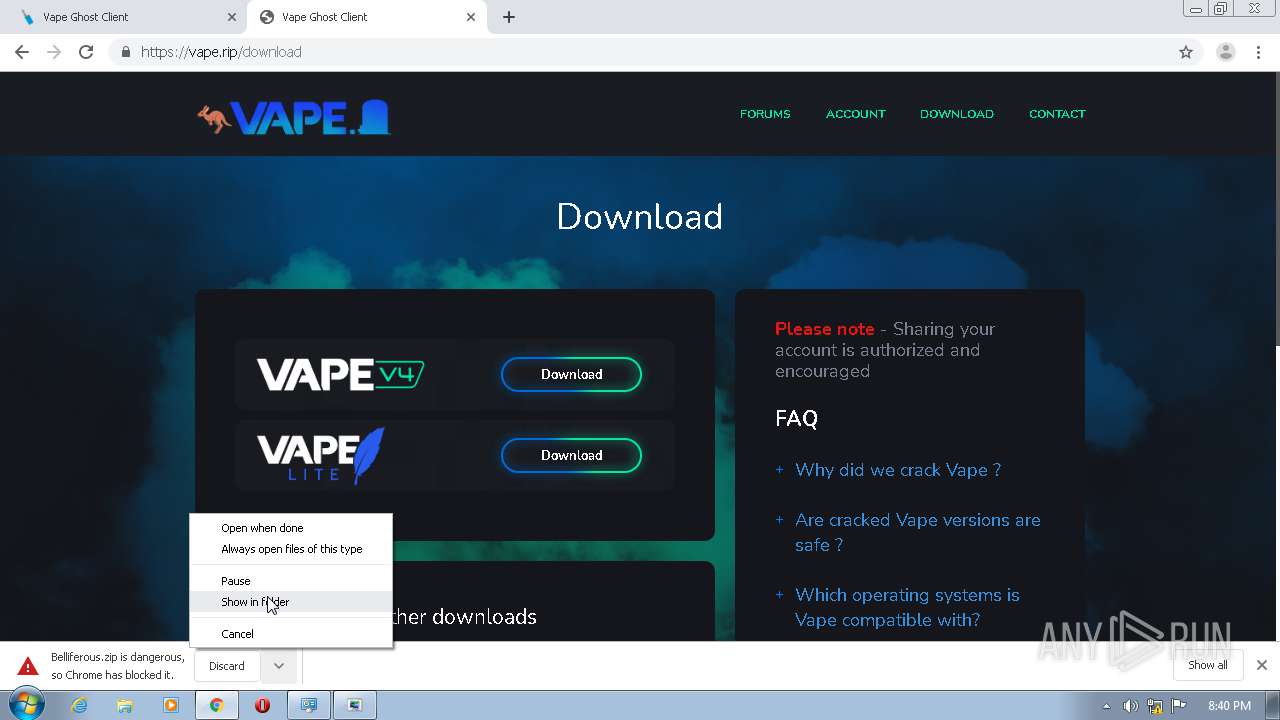
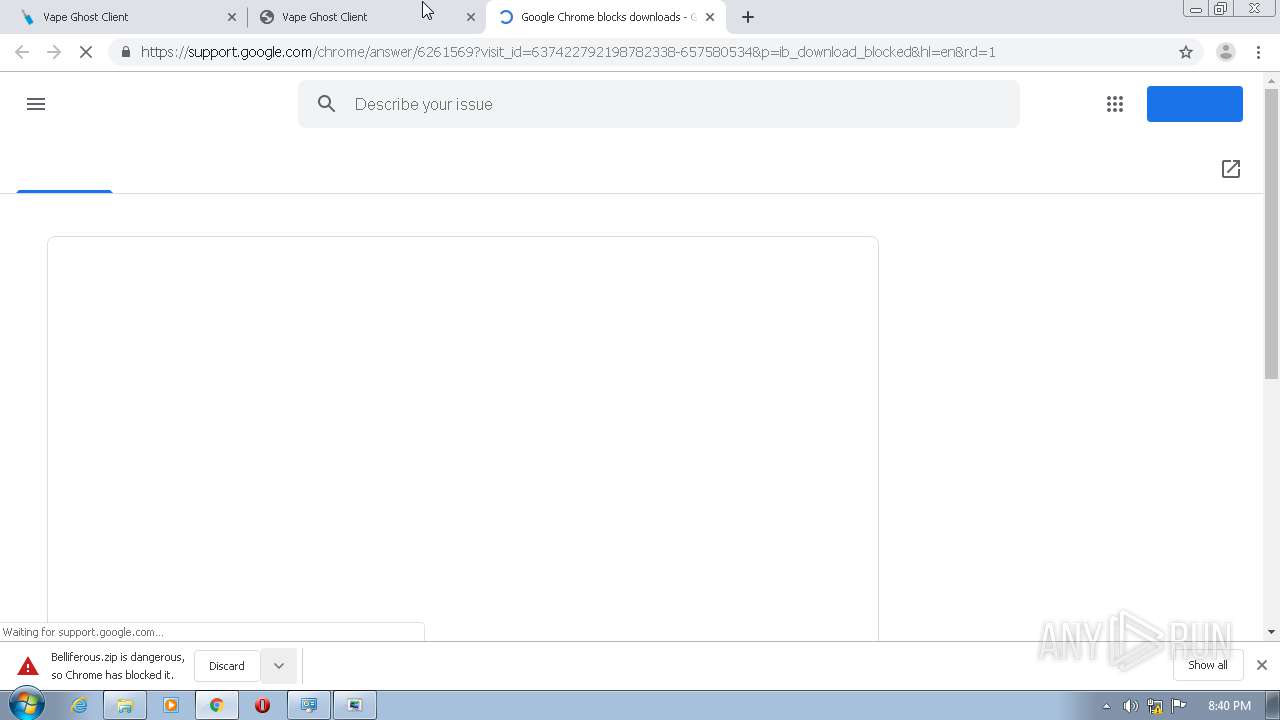
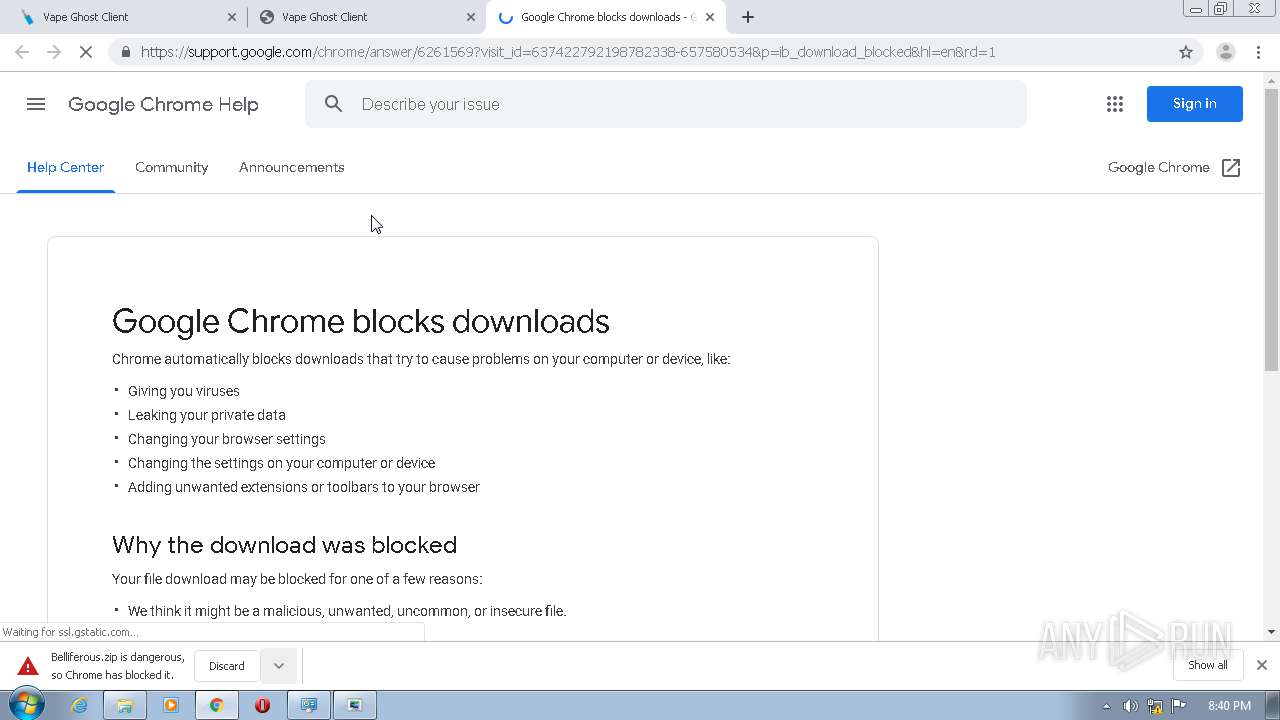
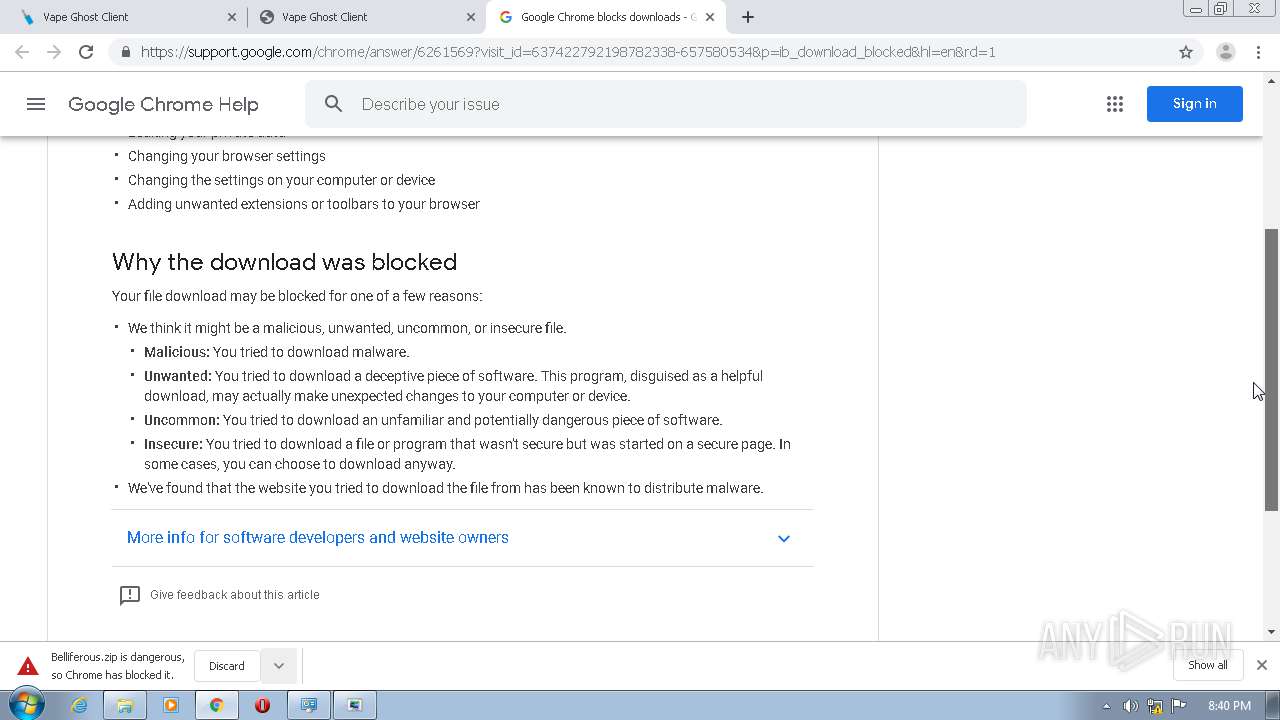
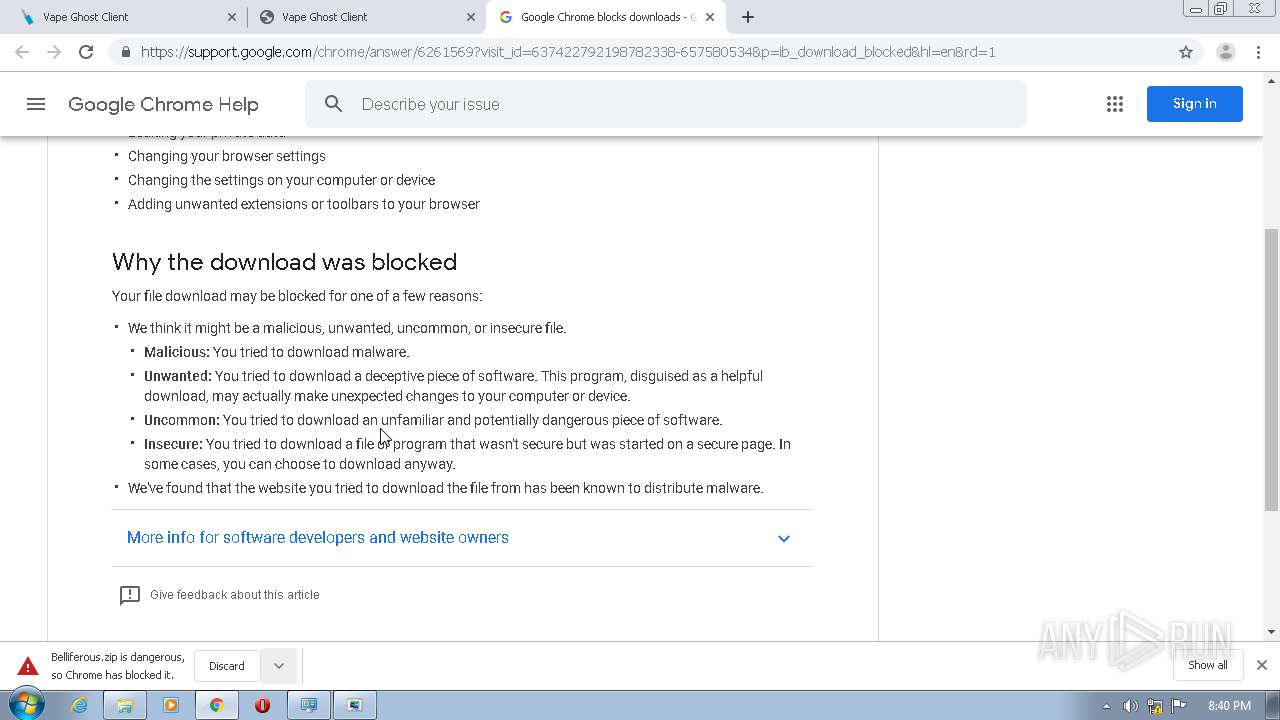
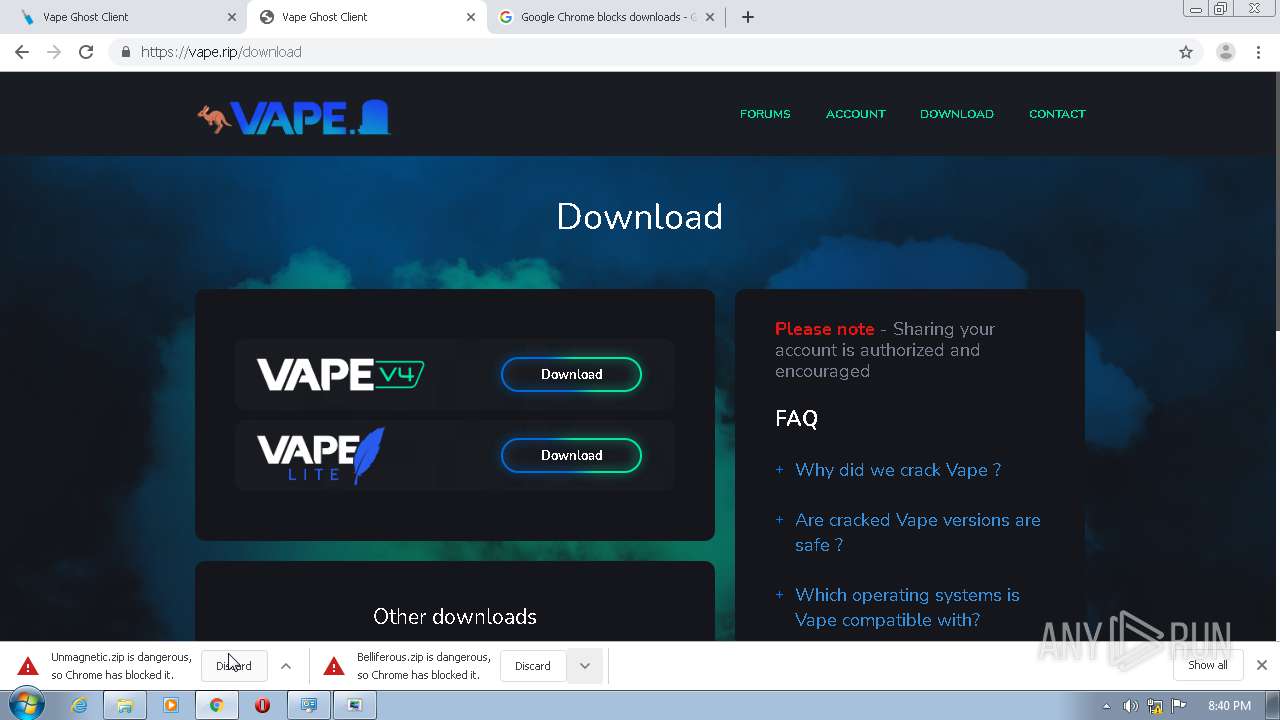
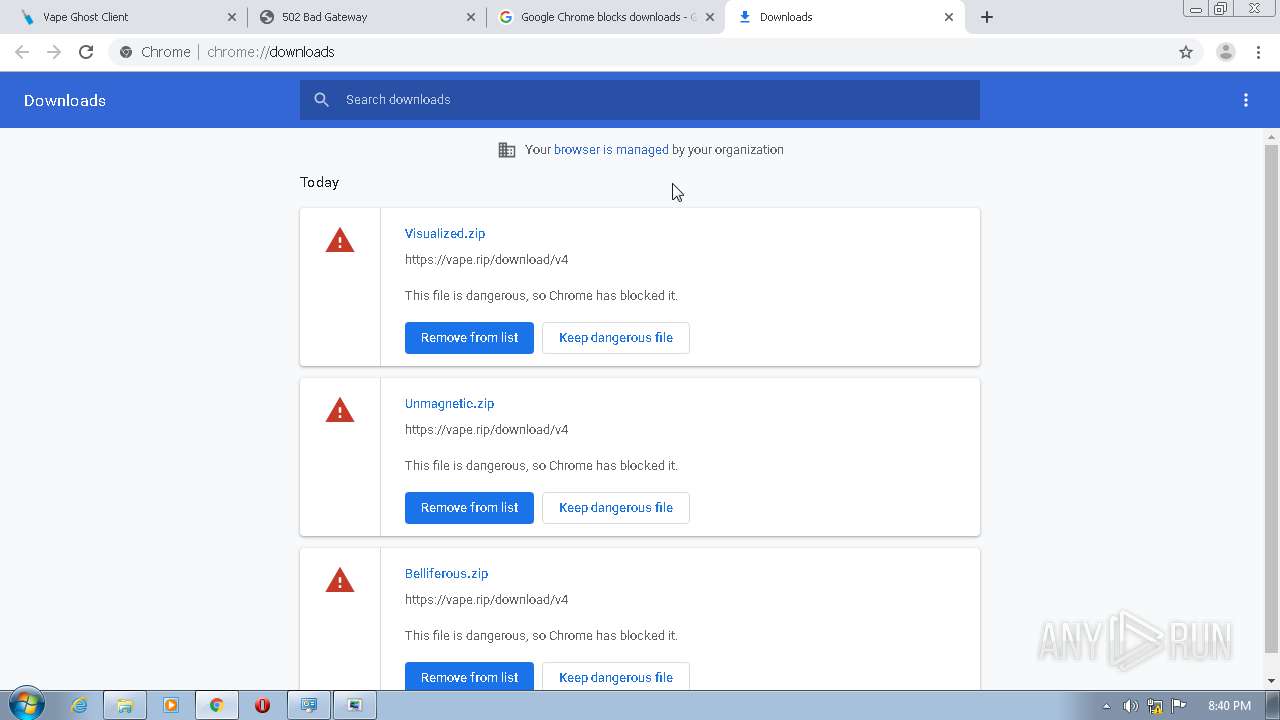
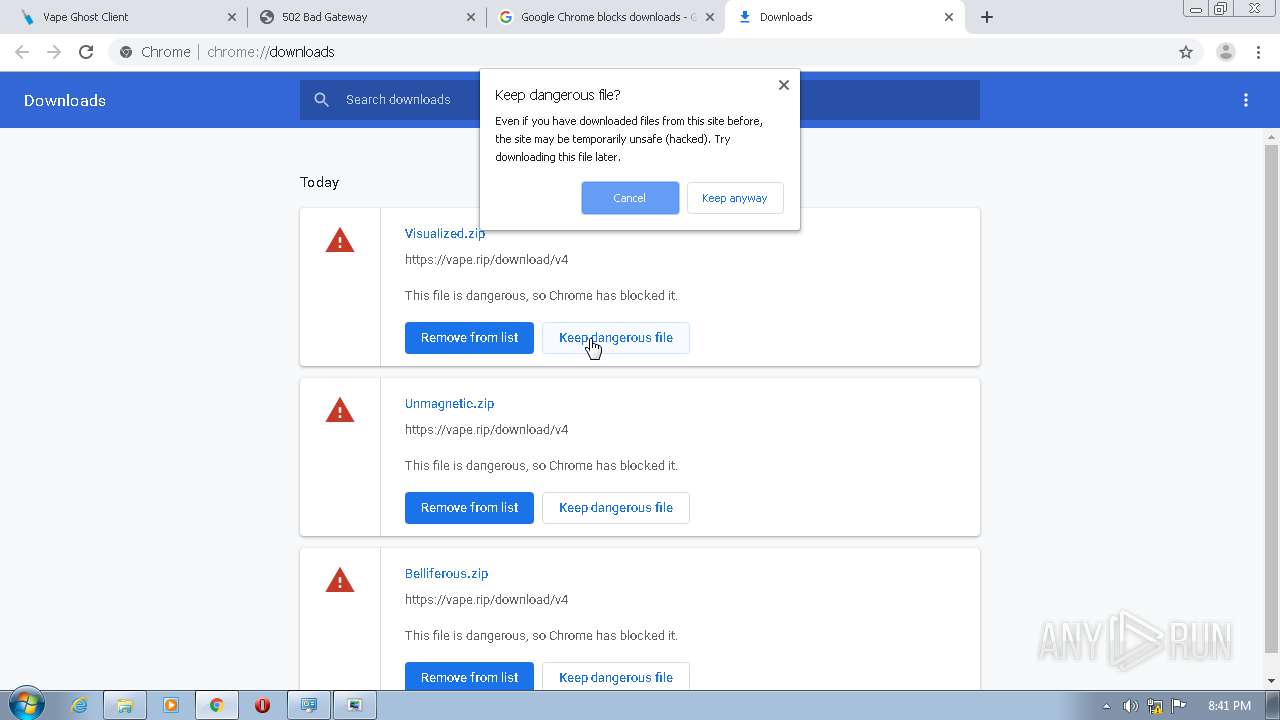
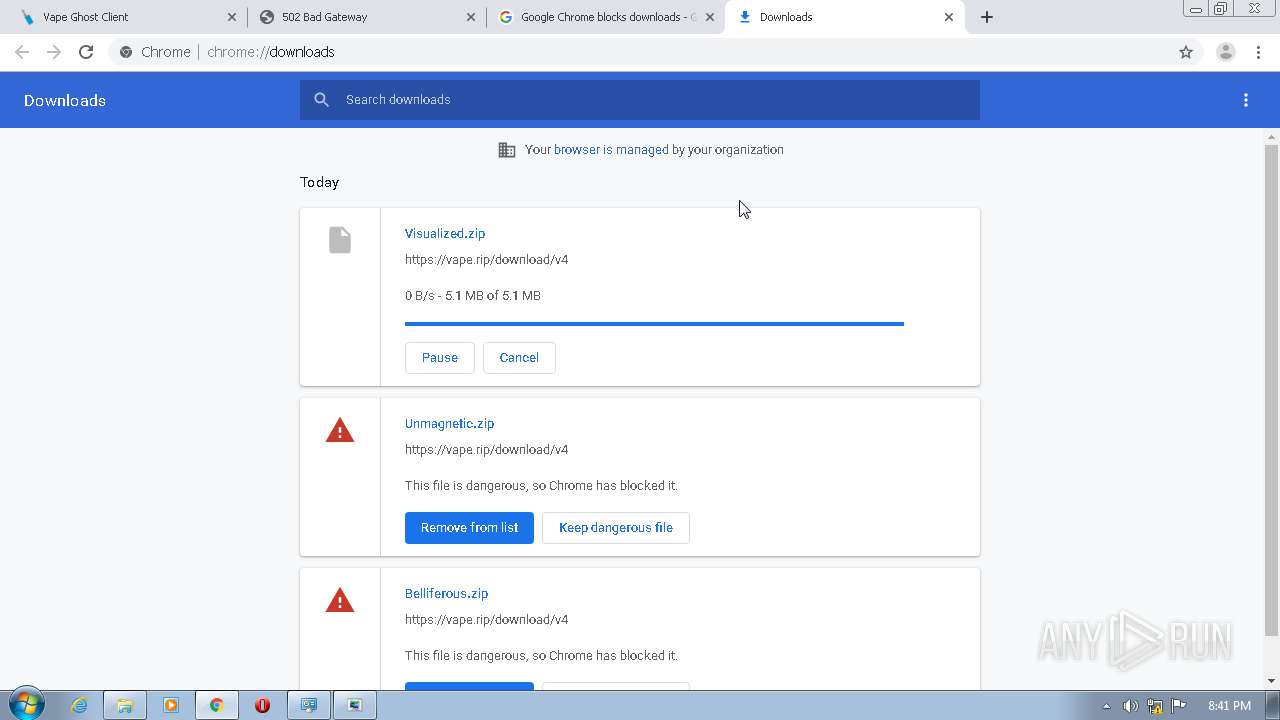
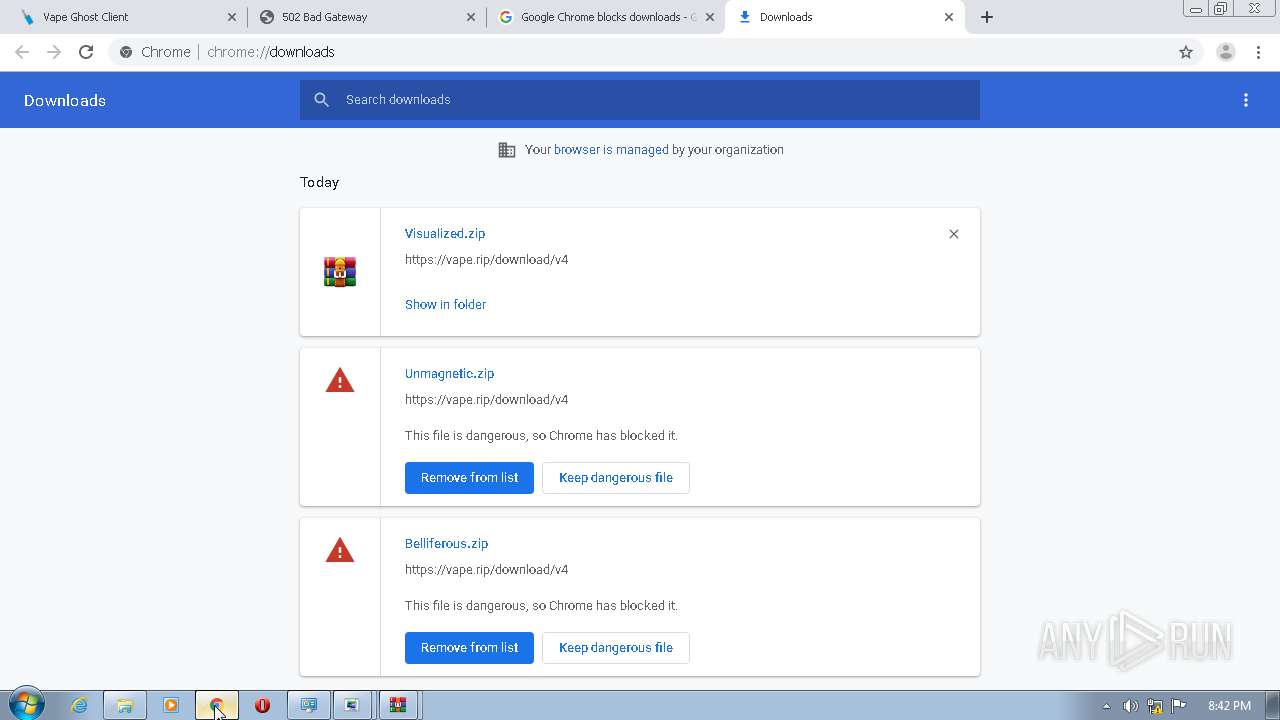
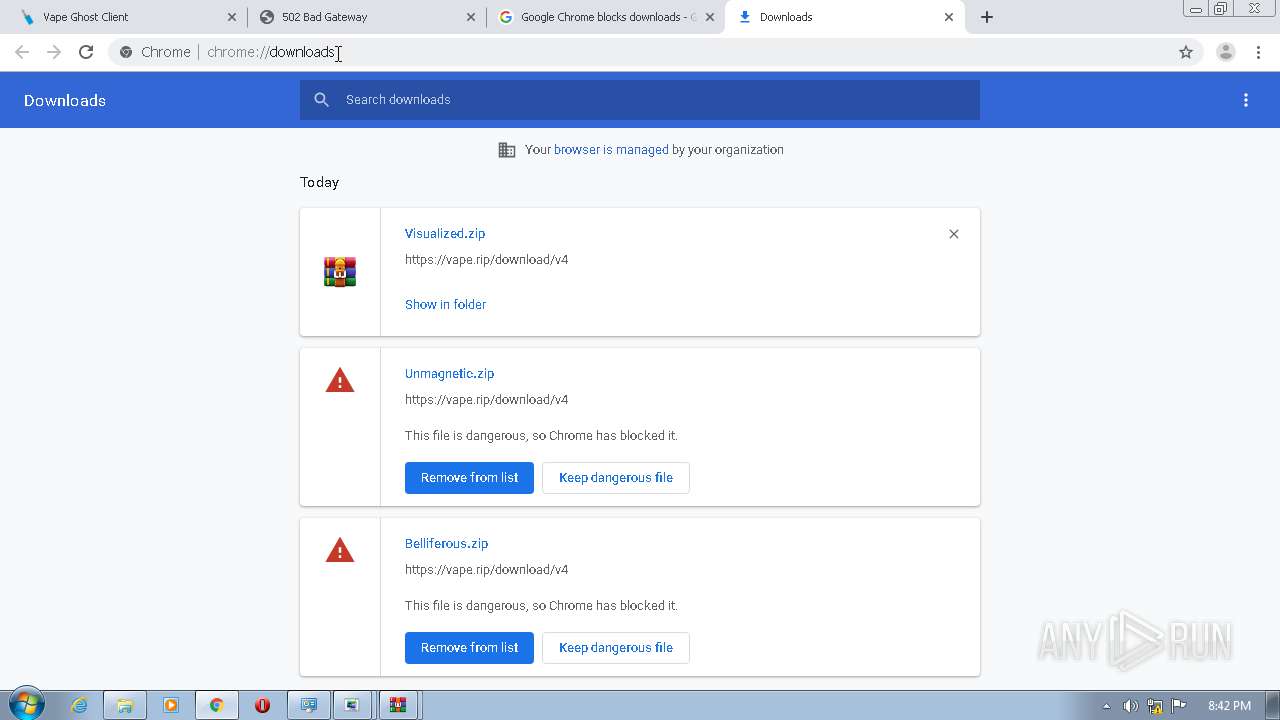
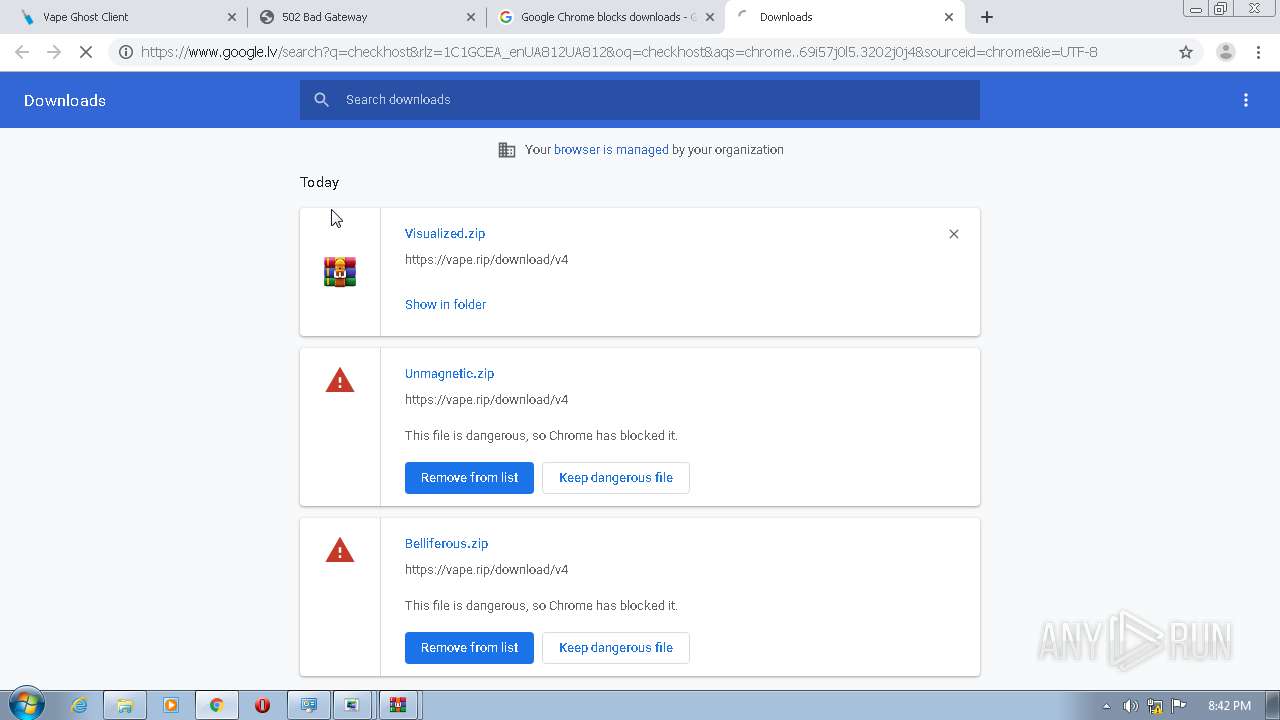
Modifies files in Chrome extension folder
- chrome.exe (PID: 3104)
Drops a file with too old compile date
- msdt.exe (PID: 3476)
- msdt.exe (PID: 4080)
Creates files in the Windows directory
- msdt.exe (PID: 3476)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2872)
Uses RUNDLL32.EXE to load library
- control.exe (PID: 928)
- control.exe (PID: 3948)
Executed via COM
- sdiagnhost.exe (PID: 120)
INFO
Reads the hosts file
- chrome.exe (PID: 2384)
- chrome.exe (PID: 3104)
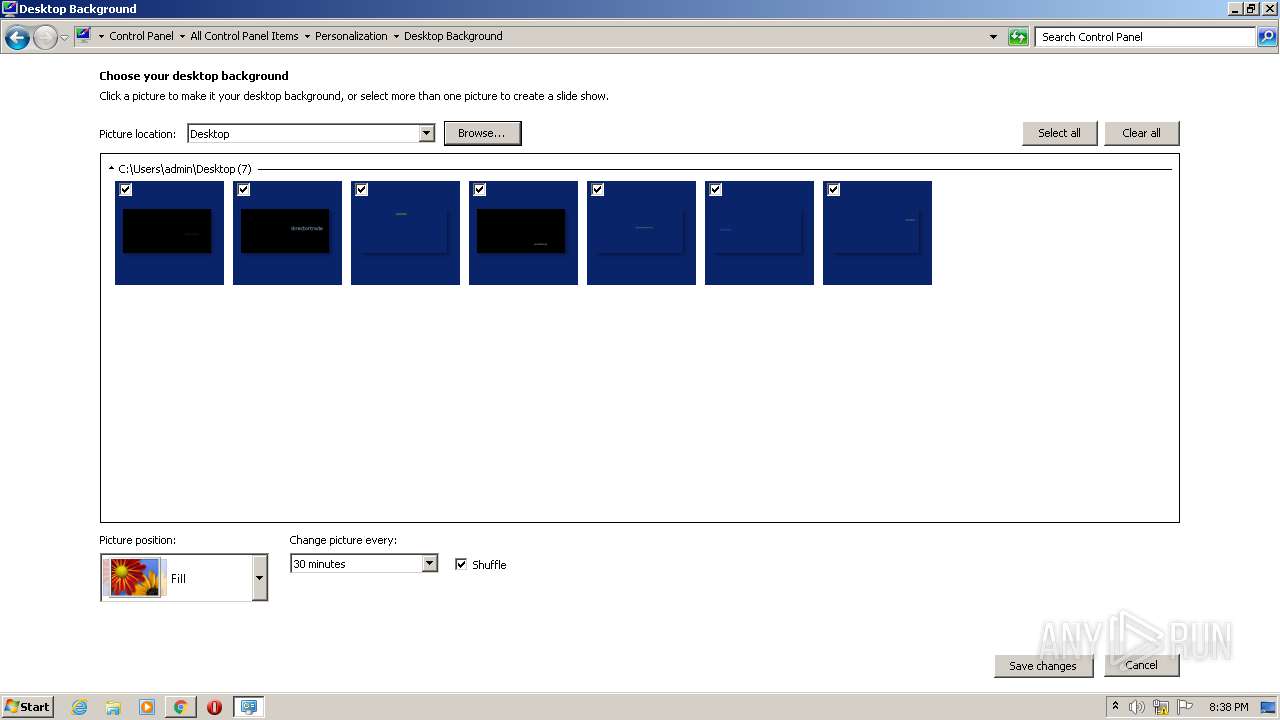
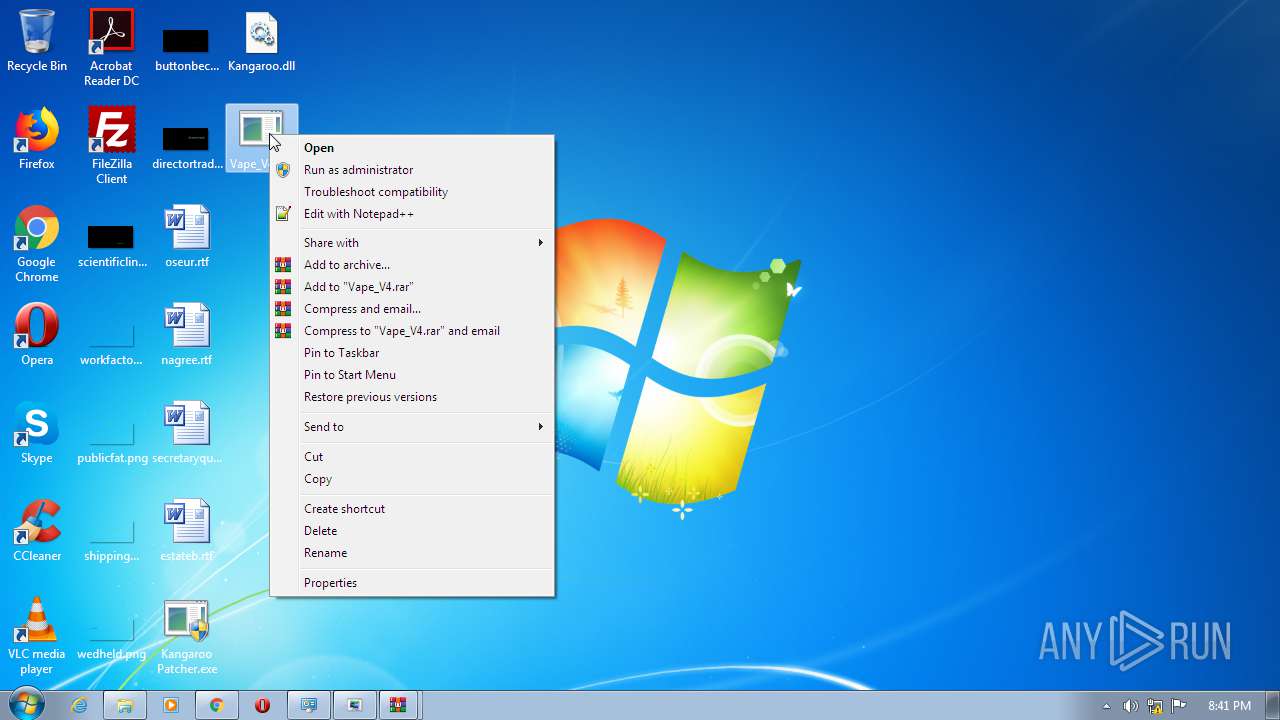
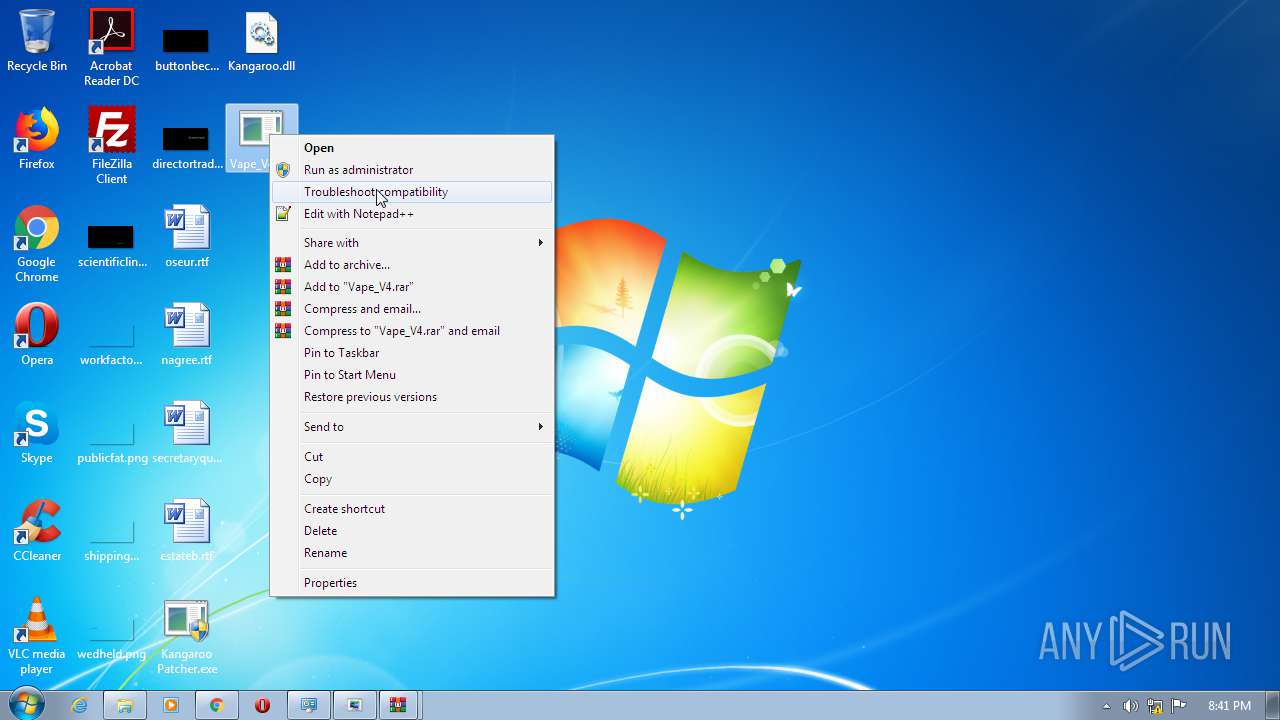
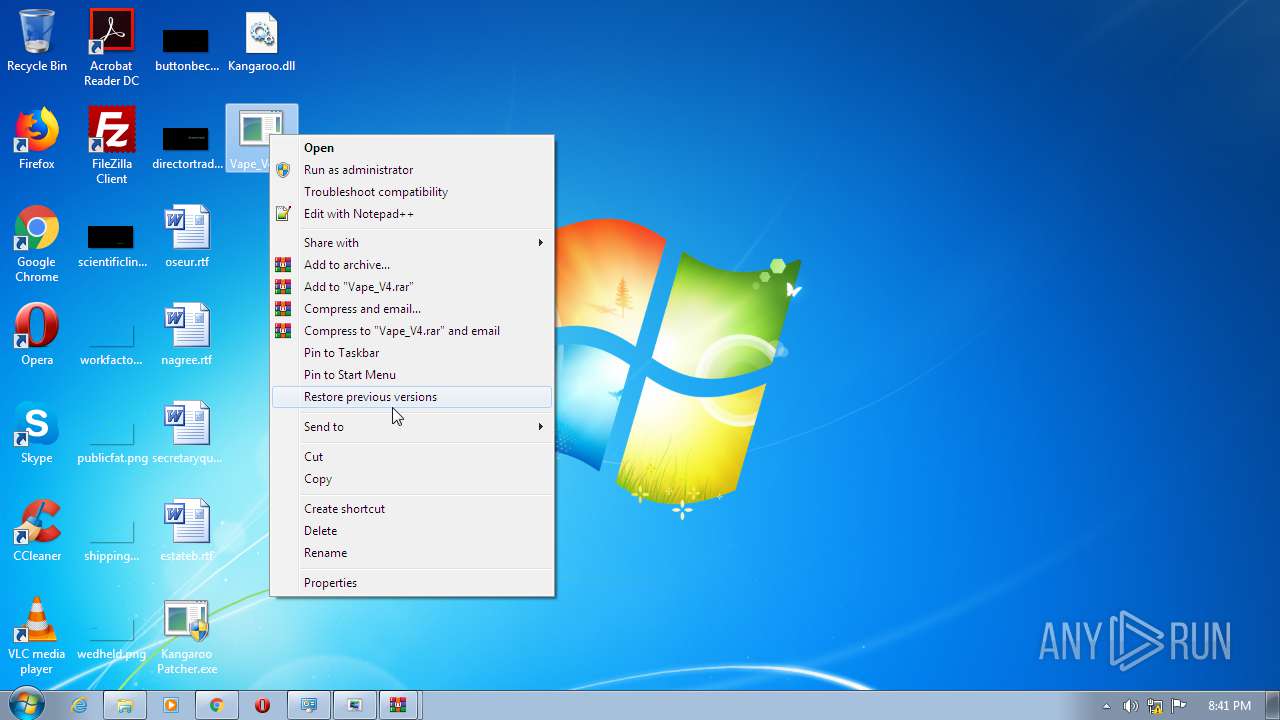
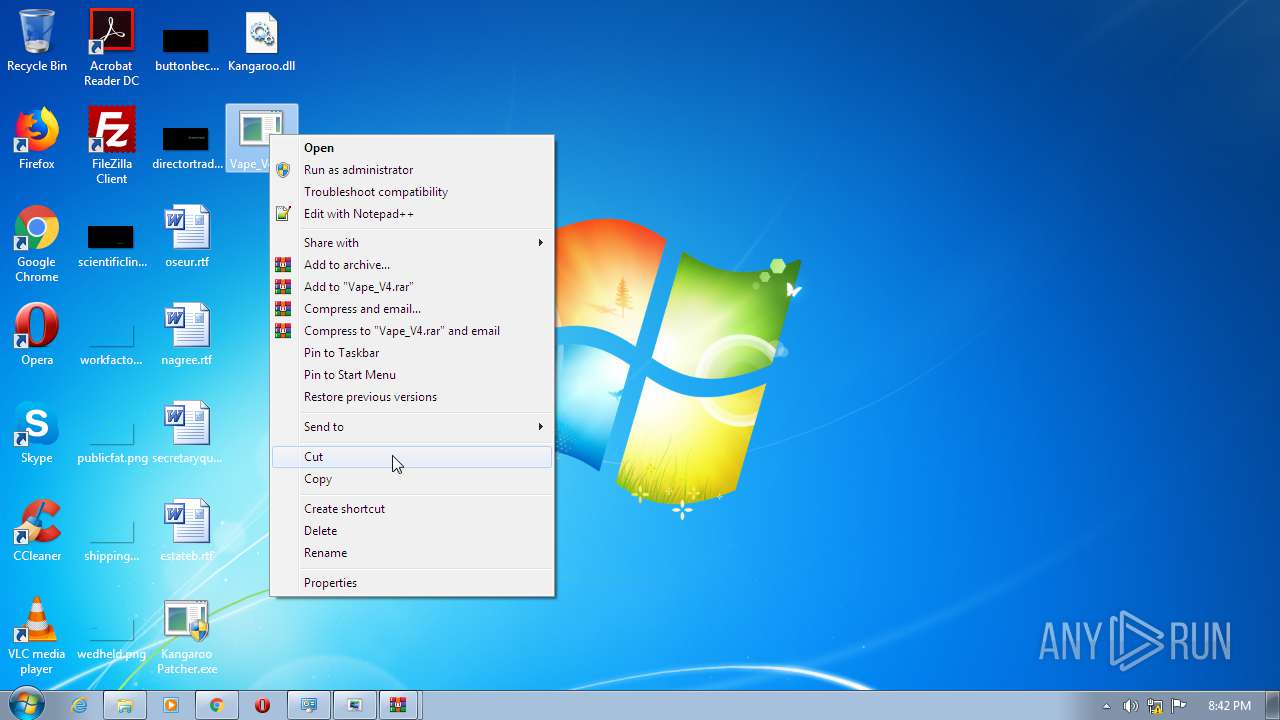
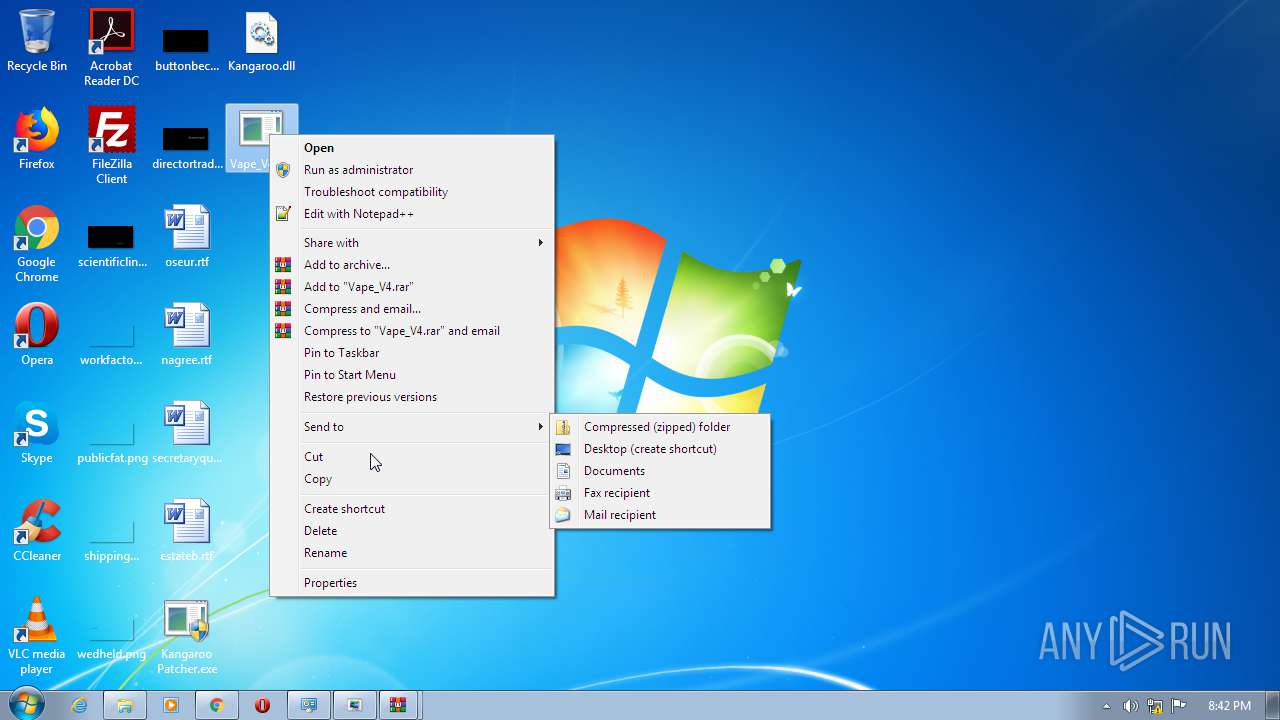
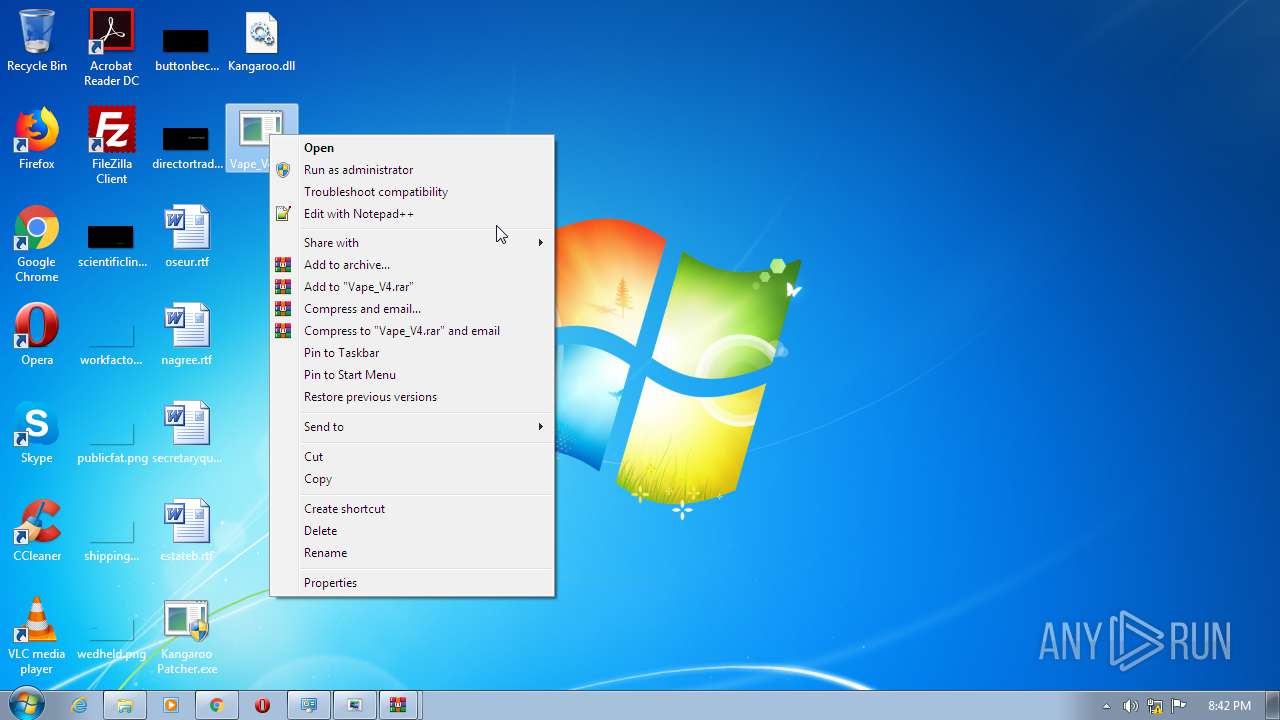
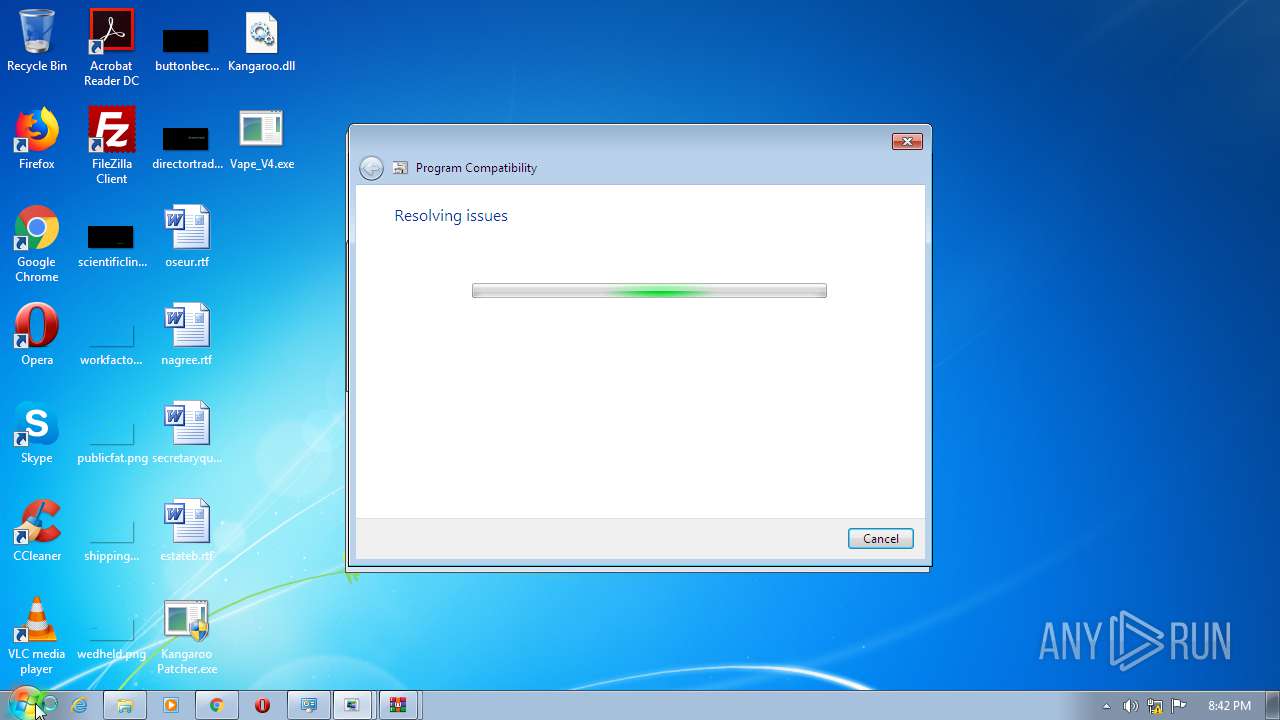
Manual execution by user
- control.exe (PID: 928)
- chrome.exe (PID: 3104)
- control.exe (PID: 3948)
- msdt.exe (PID: 3312)
- rundll32.exe (PID: 3004)
- pcwrun.exe (PID: 1596)
Reads settings of System Certificates
- chrome.exe (PID: 2384)
Application launched itself
- chrome.exe (PID: 3104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jpg | | | JFIF JPEG bitmap (50) |
|---|---|---|
| .jpg | | | JPEG bitmap (37.4) |
| .mp3 | | | MP3 audio (12.4) |
EXIF
JFIF
| JFIFVersion: | 1.01 |
|---|---|
| ResolutionUnit: | None |
| XResolution: | 72 |
| YResolution: | 72 |
IPTC
| OriginalTransmissionReference: | kSRIr_V-HjYlpOkCVc5u |
|---|
Composite
| ImageSize: | 719x719 |
|---|---|
| Megapixels: | 0.517 |
Total processes
118
Monitored processes
70
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,8654579456847533860,9502642248352165761,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6407645576774909130 --mojo-platform-channel-handle=1080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,8654579456847533860,9502642248352165761,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5866407553894636236 --mojo-platform-channel-handle=4228 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 444 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES8CF4.tmp" "c:\Users\admin\AppData\Local\Temp\CSC8CF3.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,8654579456847533860,9502642248352165761,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15904495862152232239 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,8654579456847533860,9502642248352165761,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5837345916862420562 --mojo-platform-channel-handle=2440 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,8654579456847533860,9502642248352165761,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17051829803453980831 --mojo-platform-channel-handle=3340 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
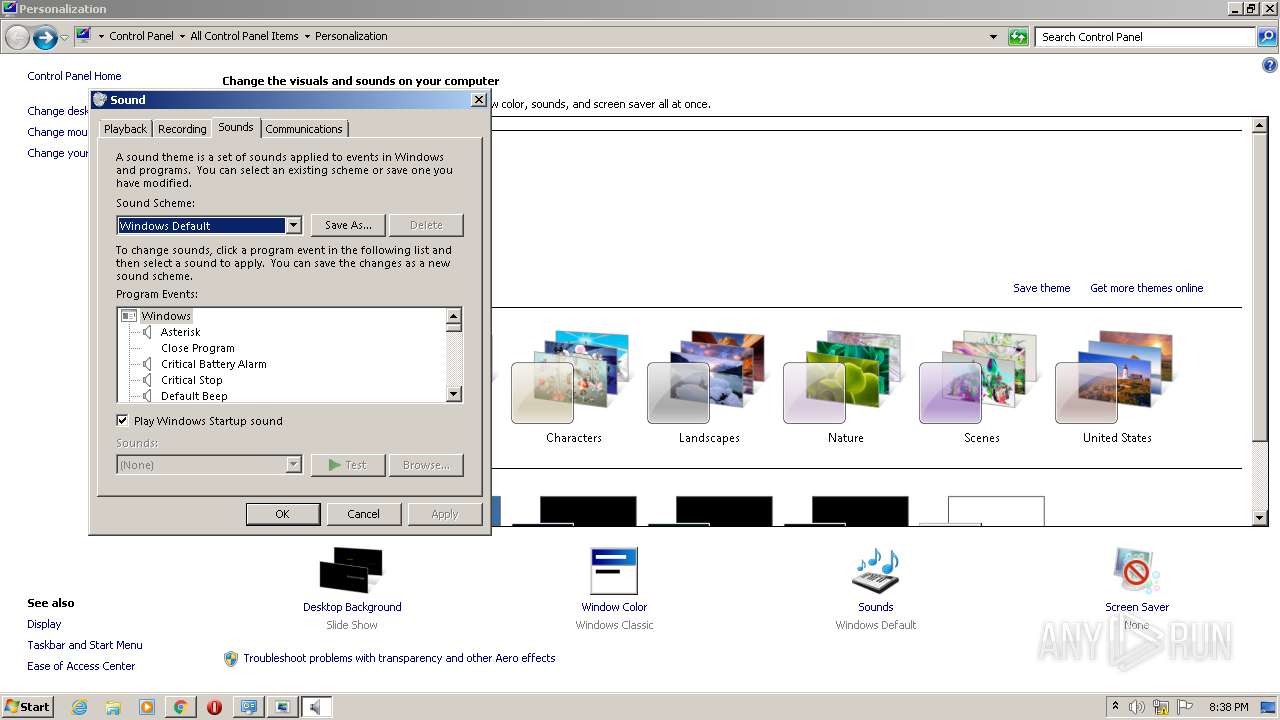
| 928 | "C:\Windows\System32\control.exe" /name Microsoft.Sound /page 2 | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,8654579456847533860,9502642248352165761,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11410822332025244691 --renderer-client-id=50 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,8654579456847533860,9502642248352165761,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17952034450970608361 --mojo-platform-channel-handle=1140 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 663
Read events
2 268
Write events
390
Delete events
5
Modification events
| (PID) Process: | (2236) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: rundll32.exe | |||
| (PID) Process: | (2236) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3104-13251155871940750 |
Value: 259 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
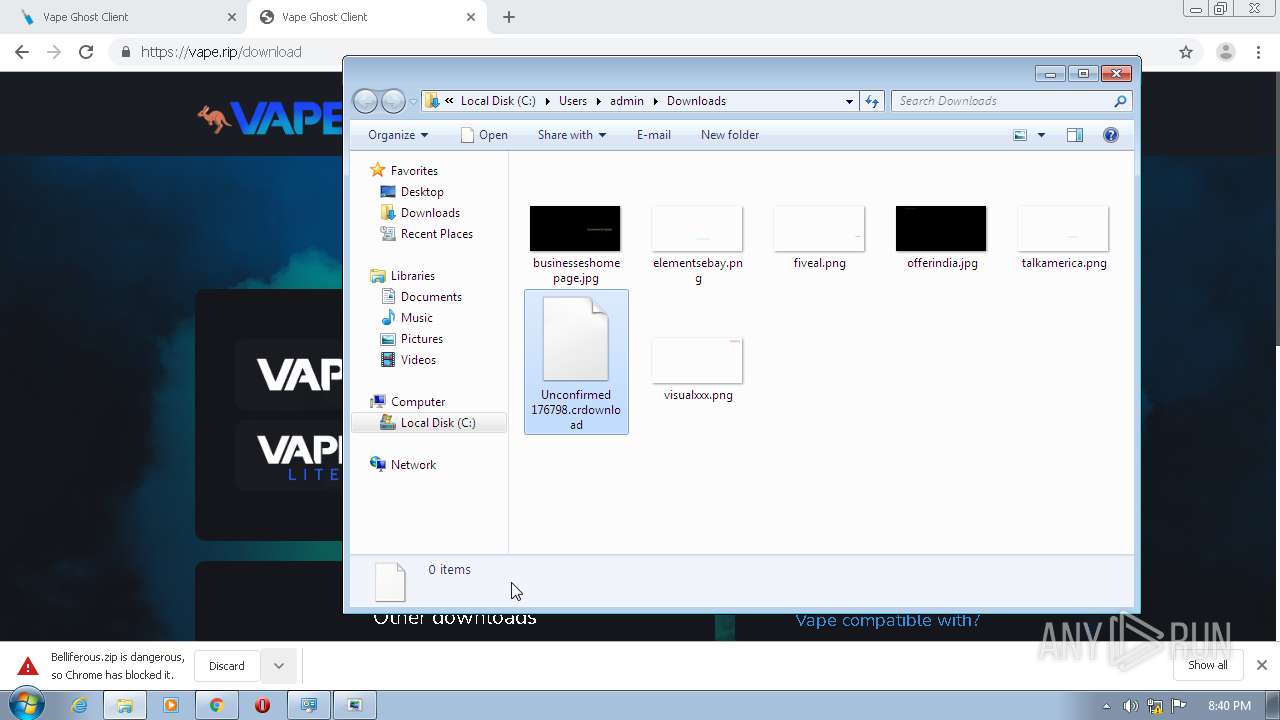
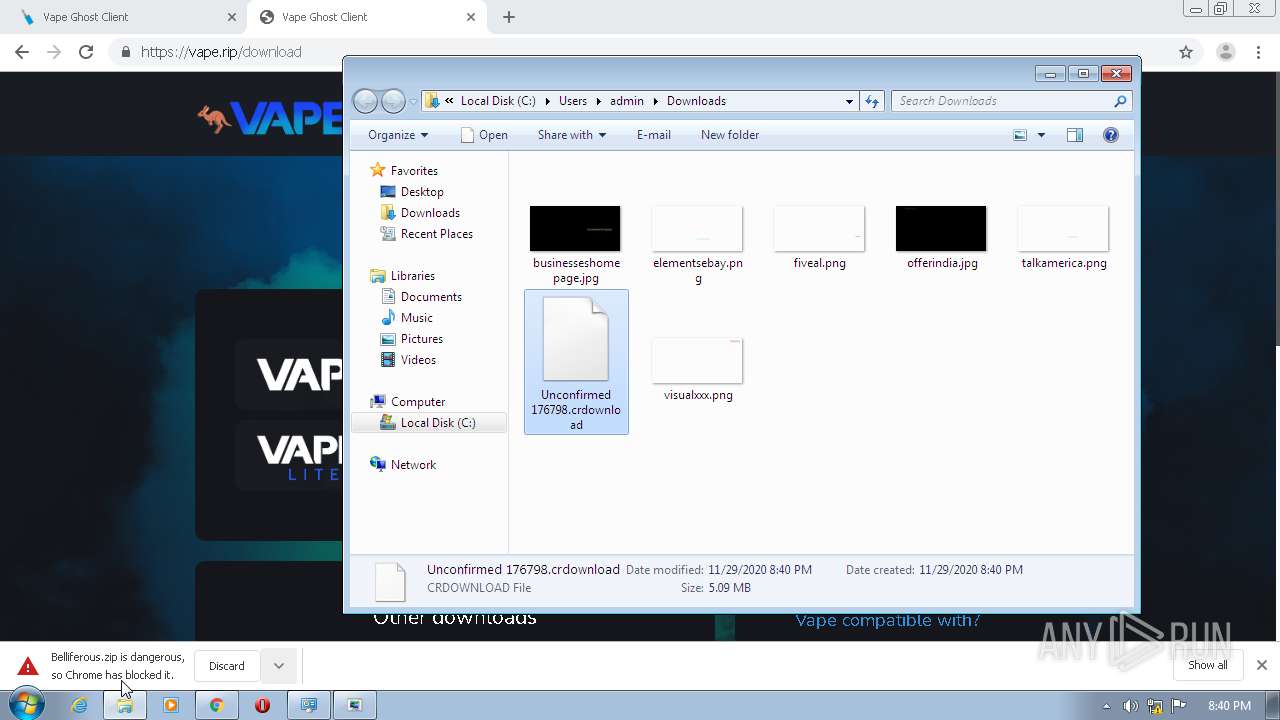
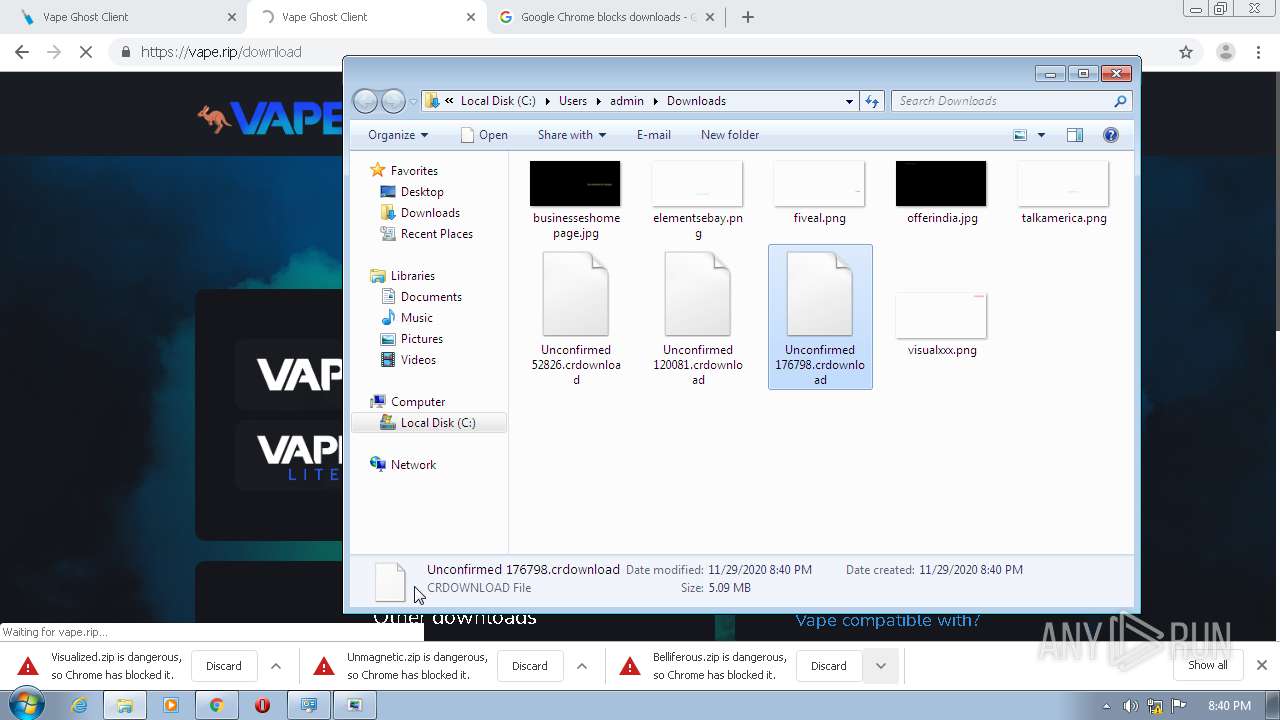
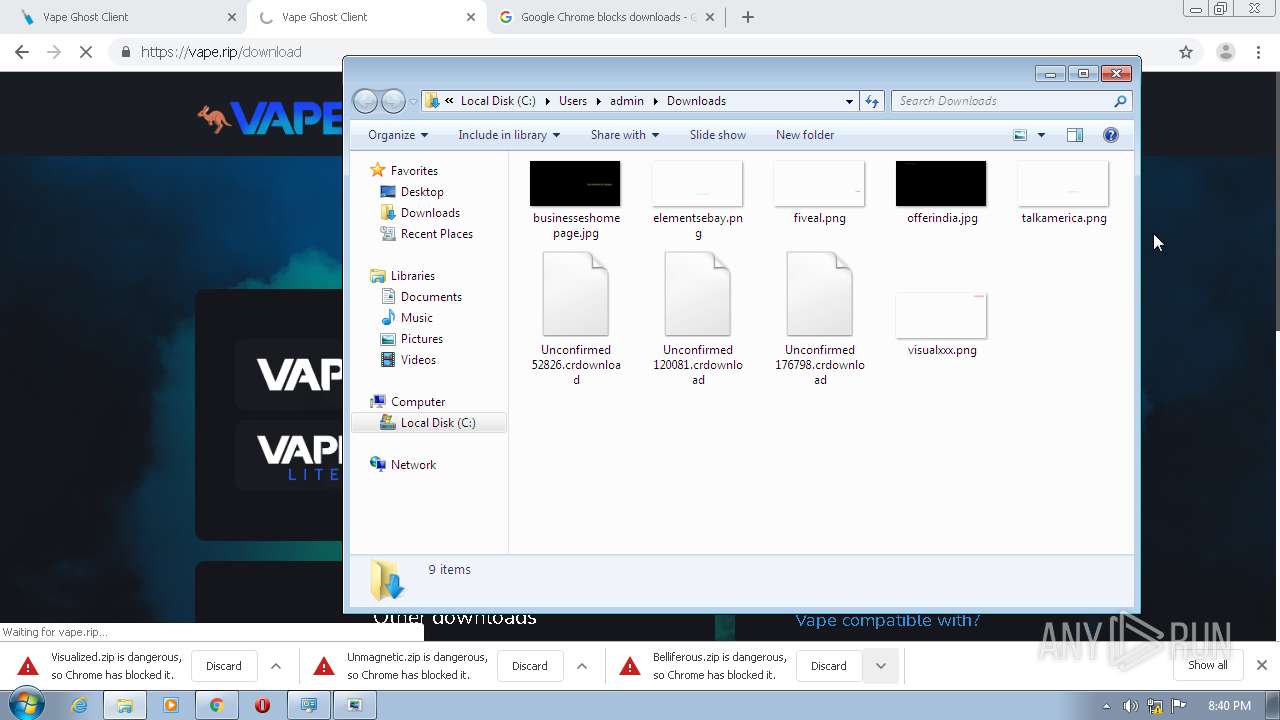
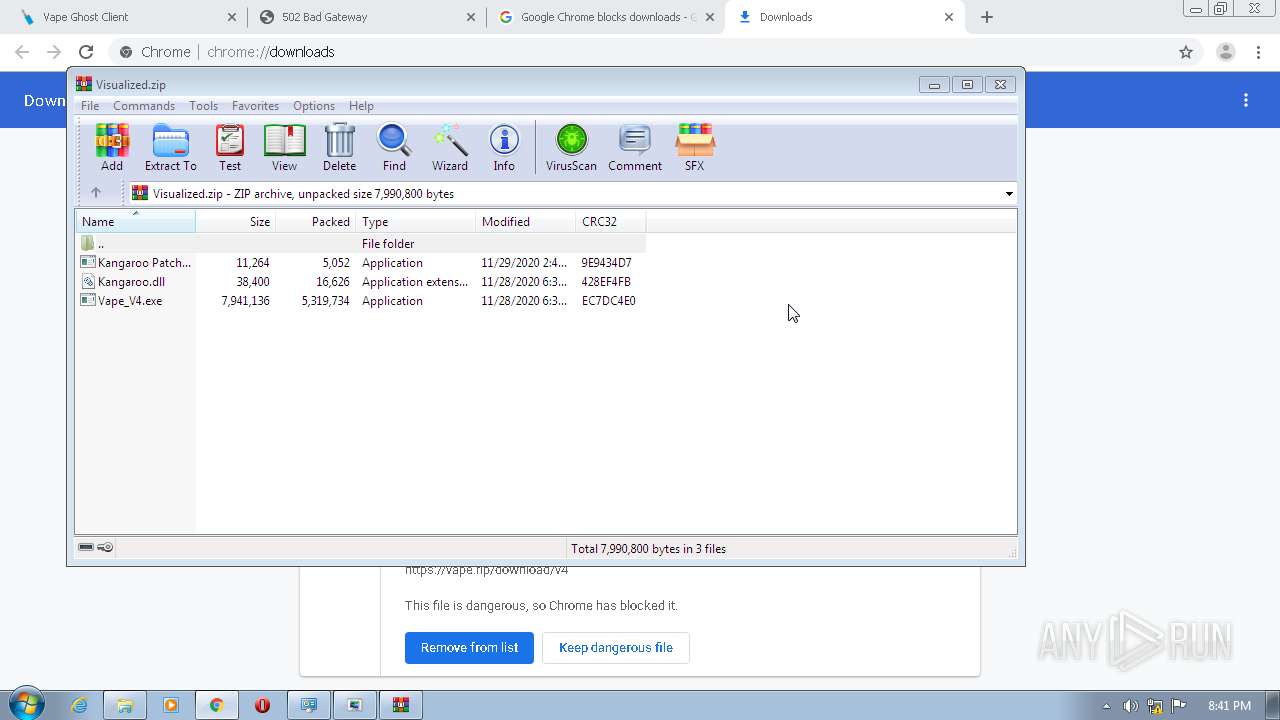
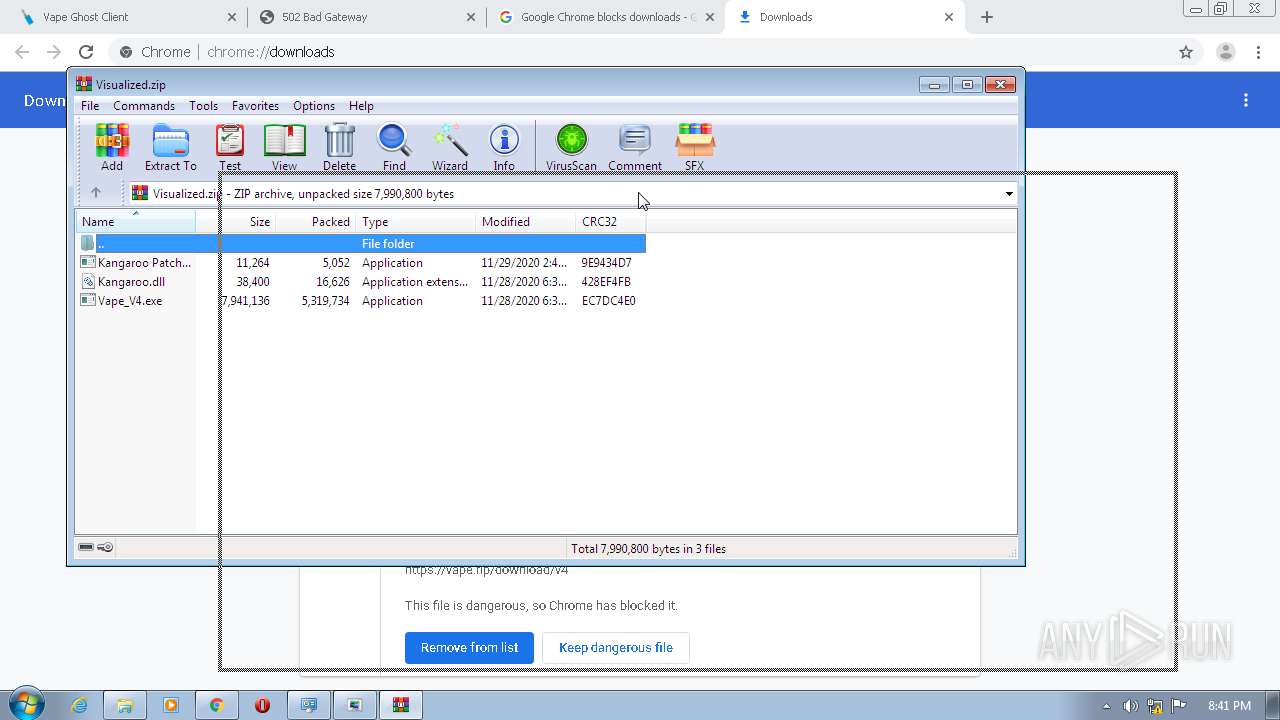
Executable files
9
Suspicious files
99
Text files
403
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC406A0-C20.pma | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c2391772-52a7-4b80-8756-986bd3e47cda.tmp | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF12a61b.TMP | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12a531.TMP | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF12a5ed.TMP | text | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF12a81f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
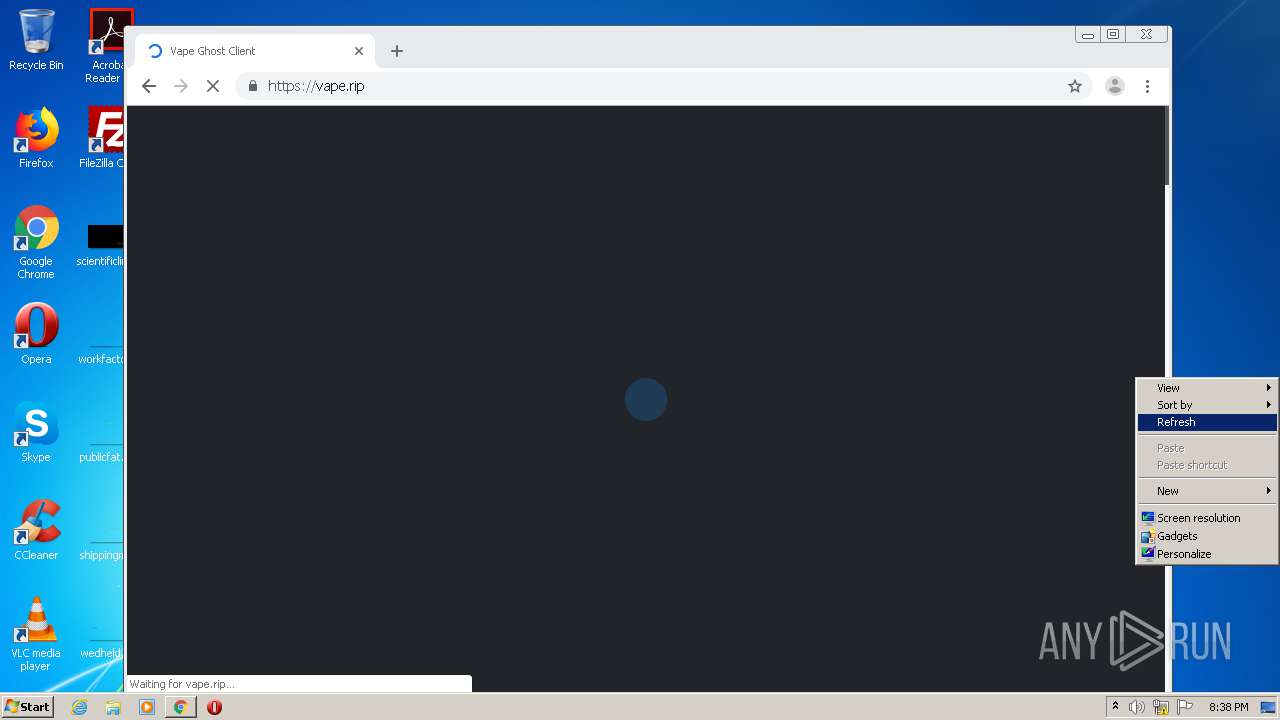
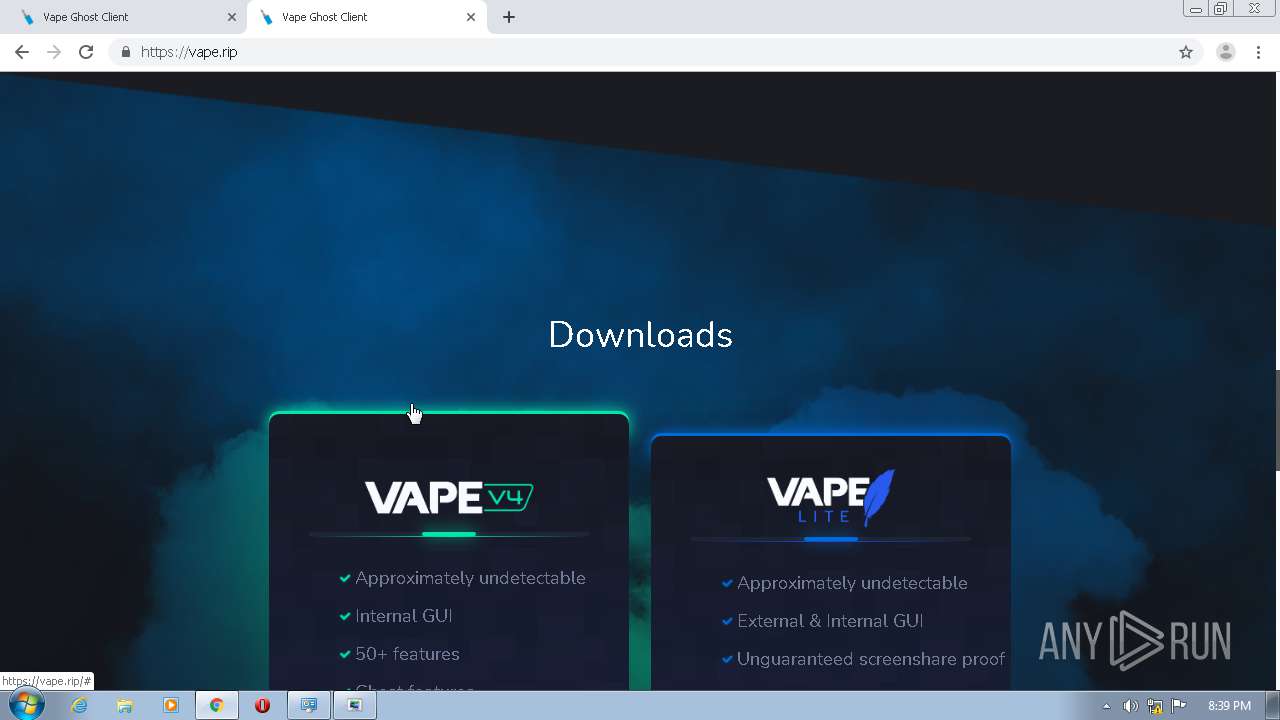
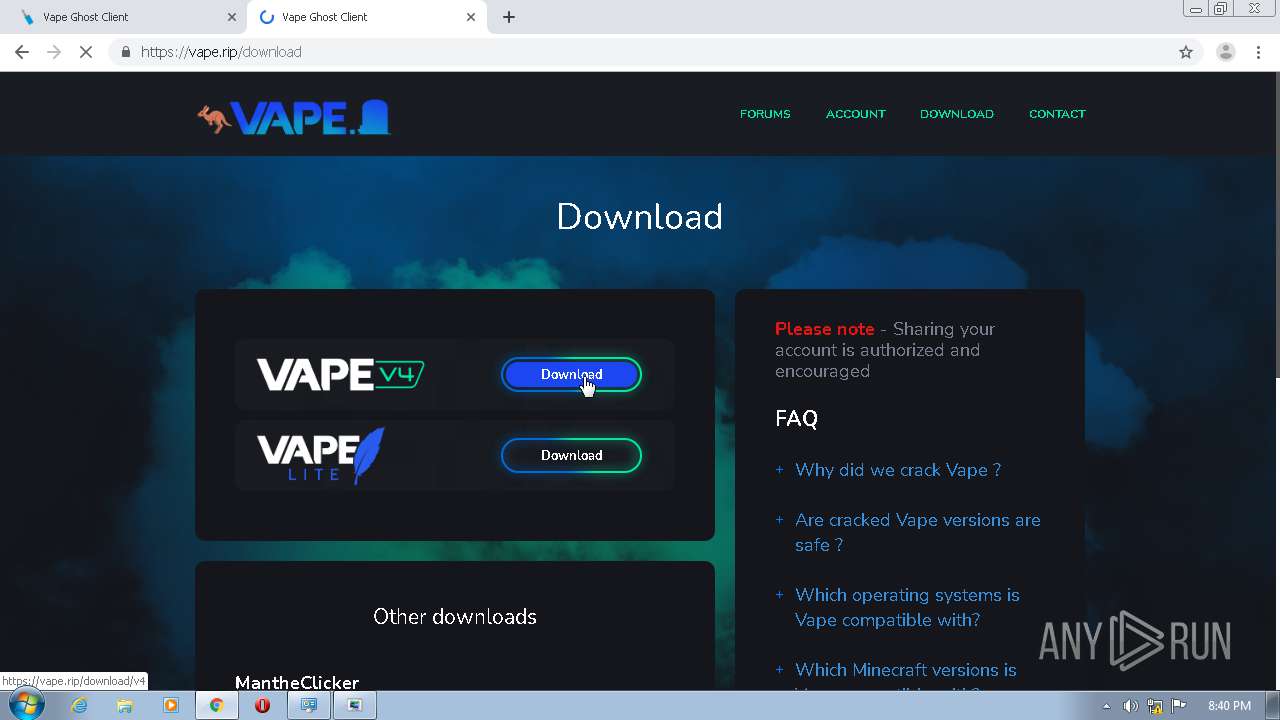
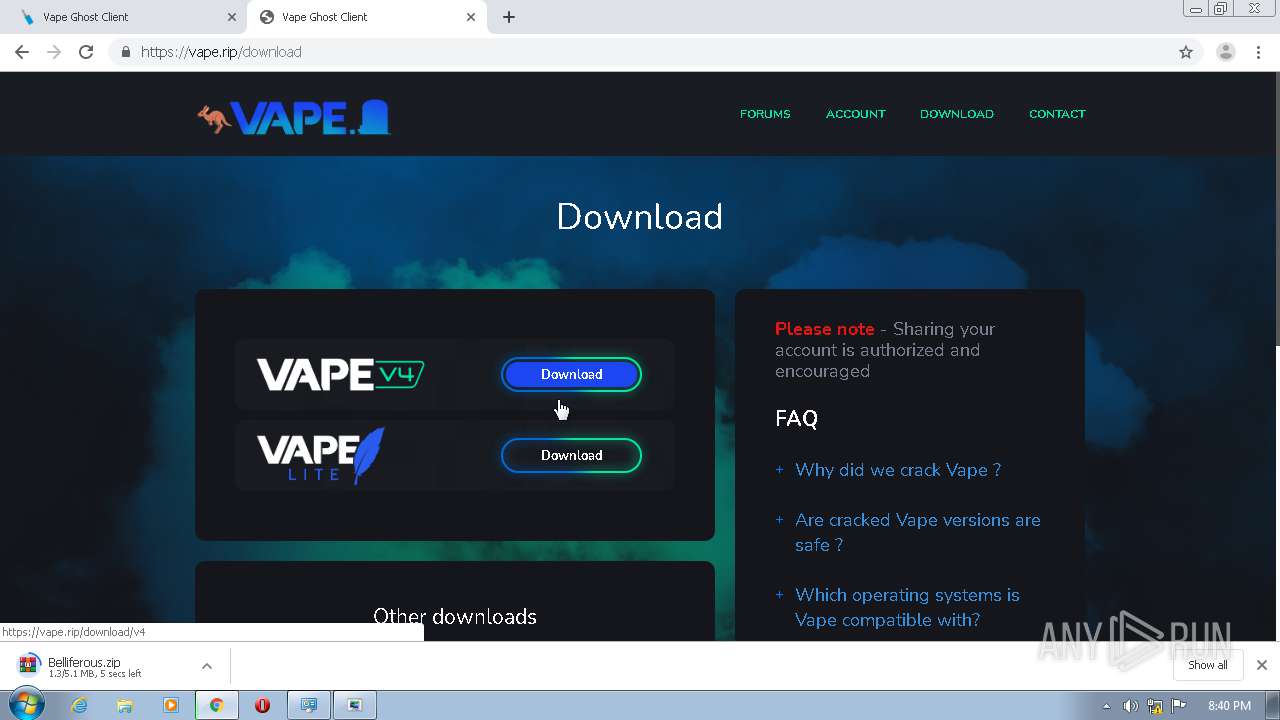
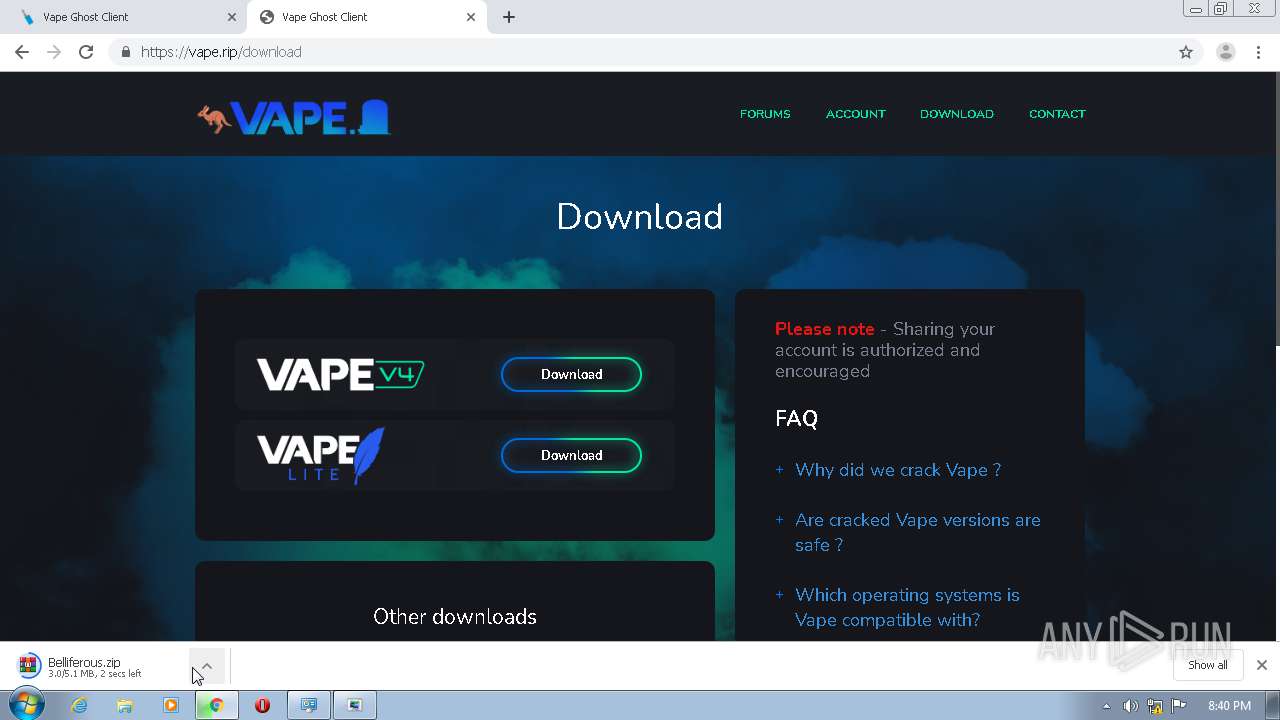
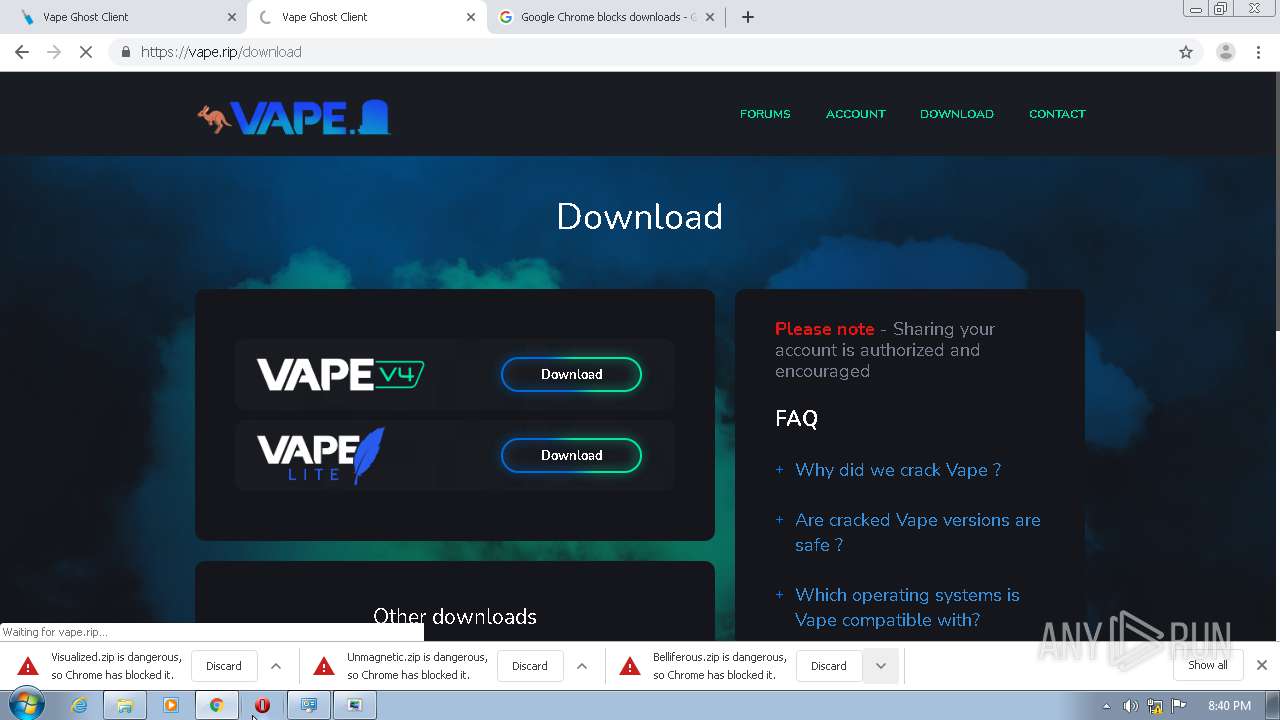
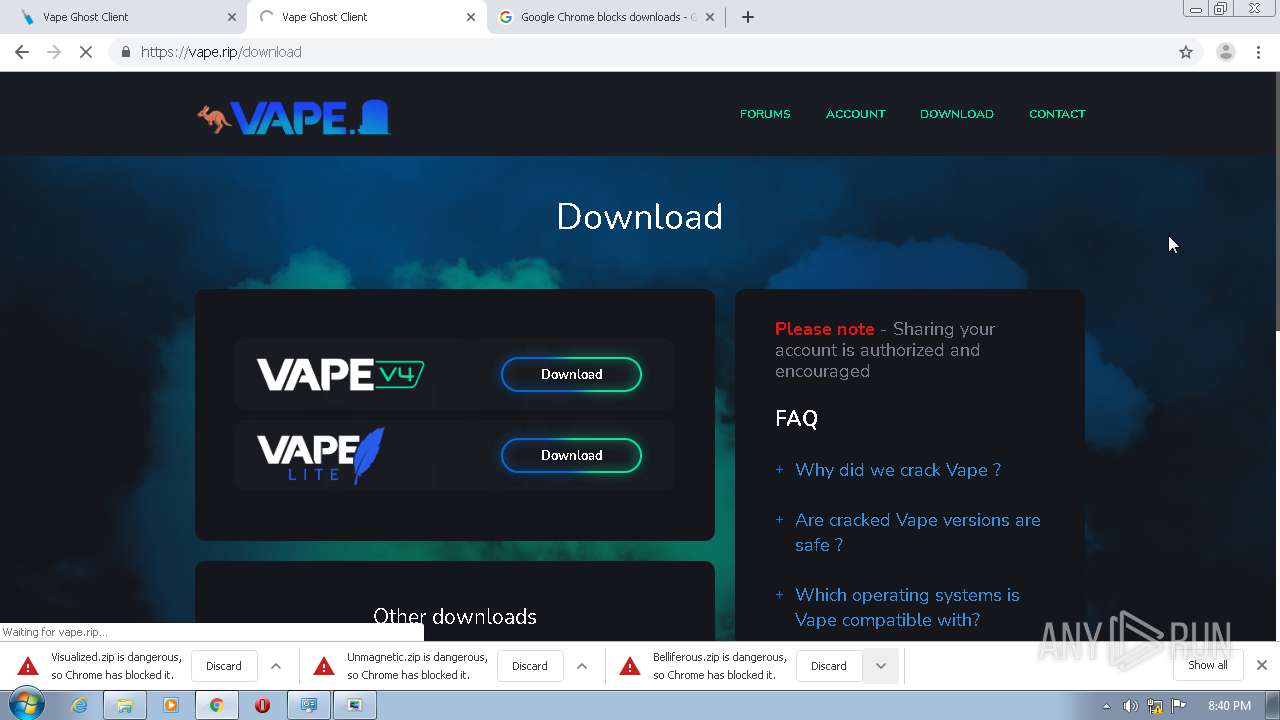
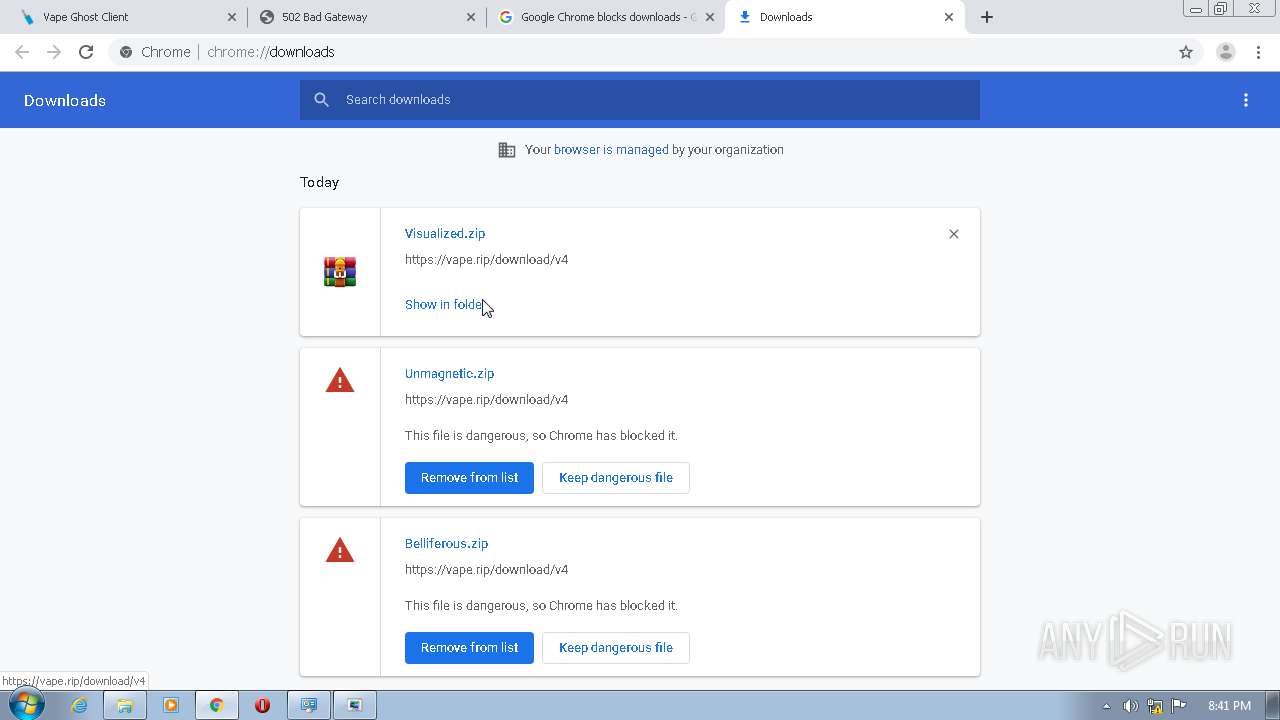
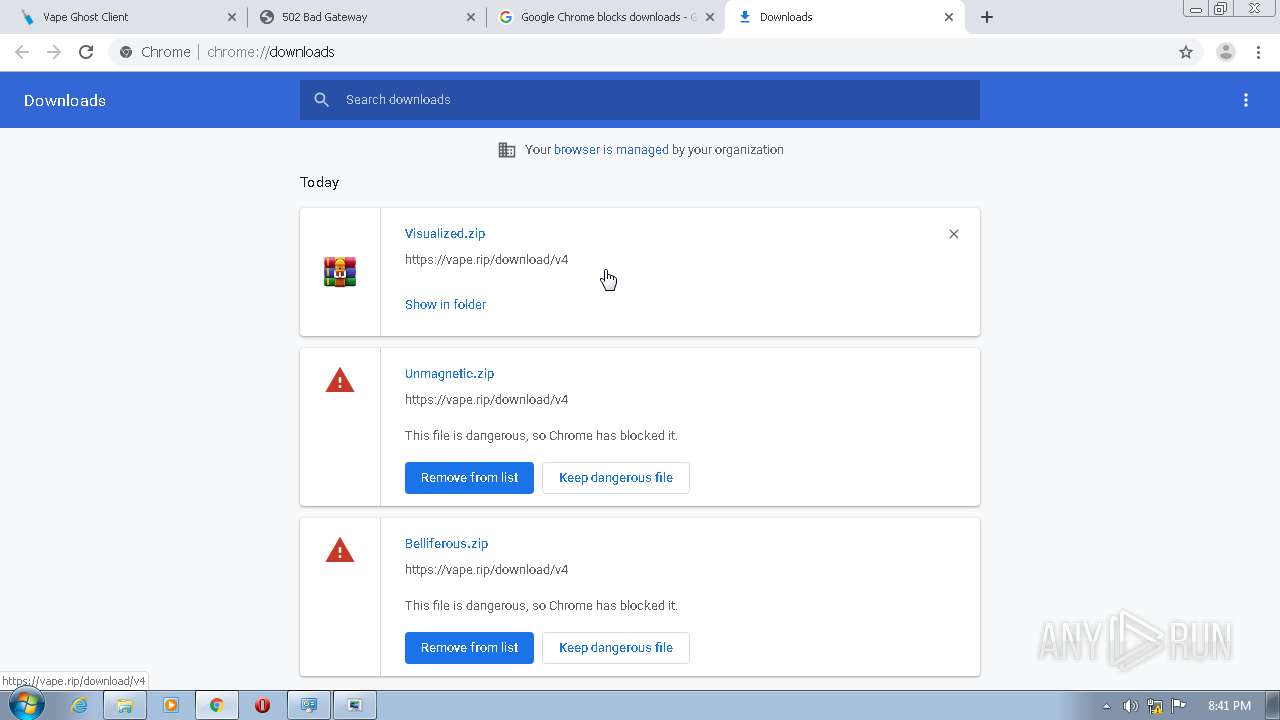
HTTP(S) requests
6
TCP/UDP connections
62
DNS requests
31
Threats
0
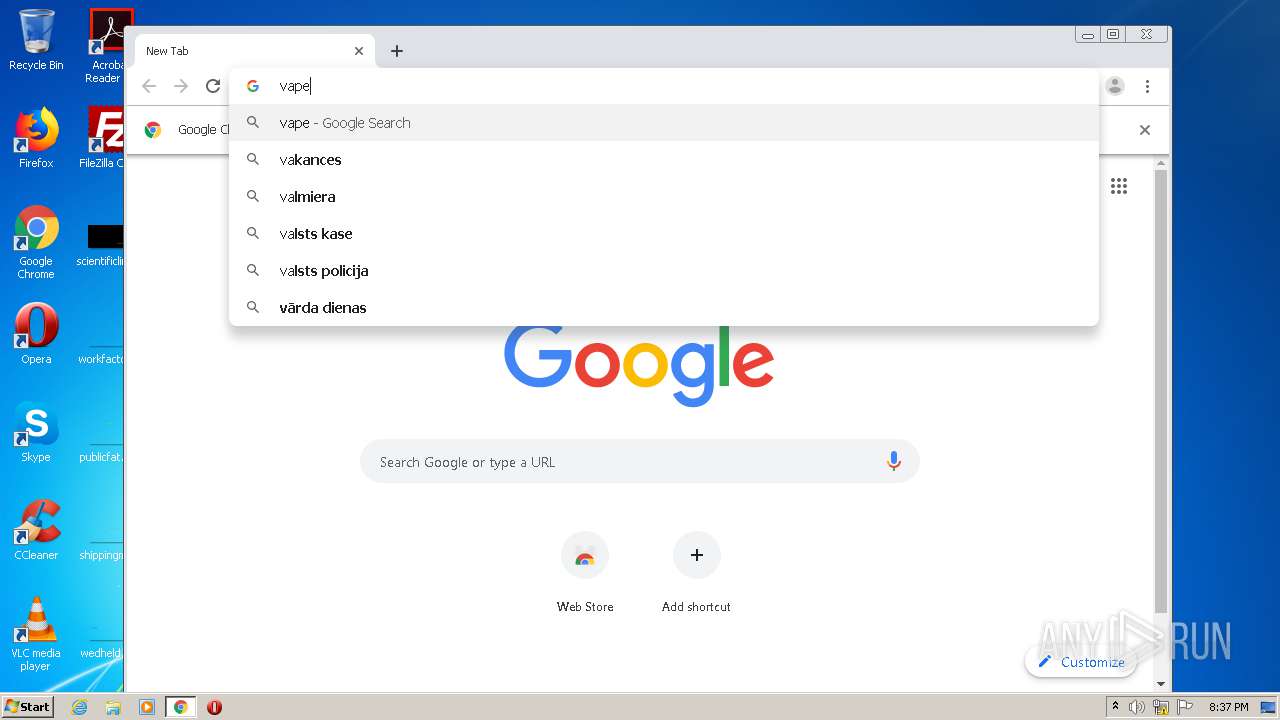
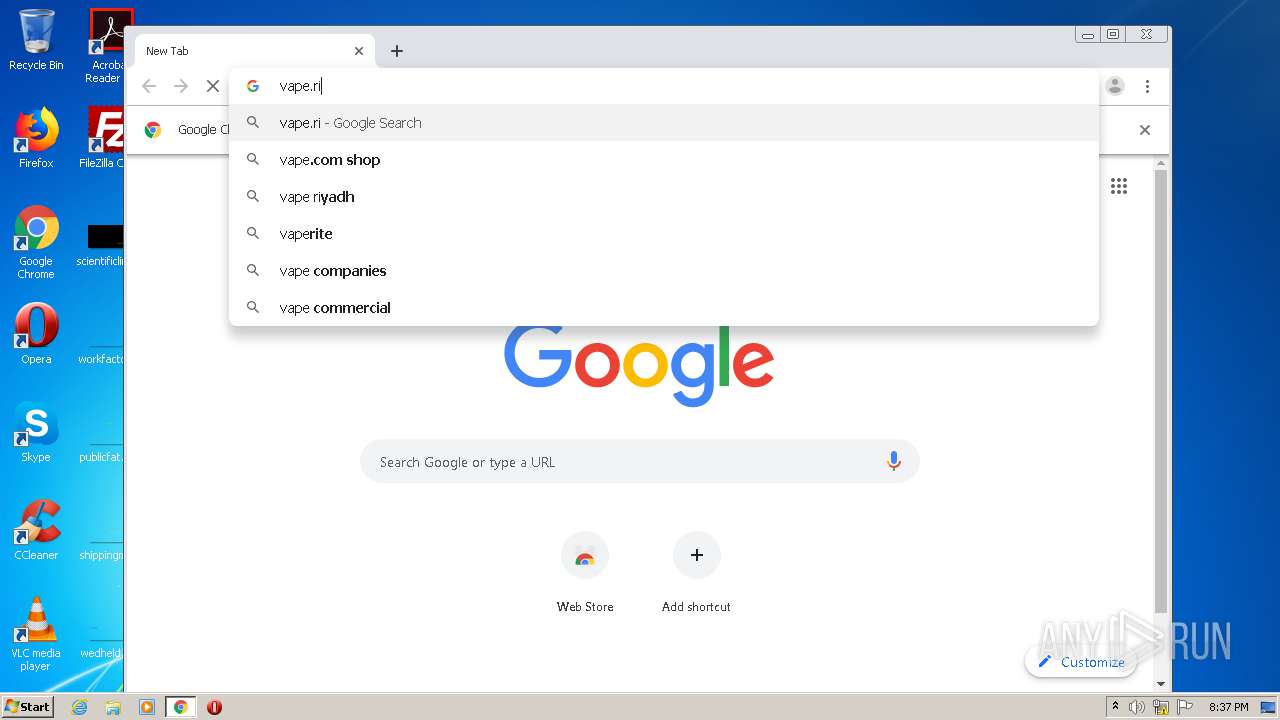
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
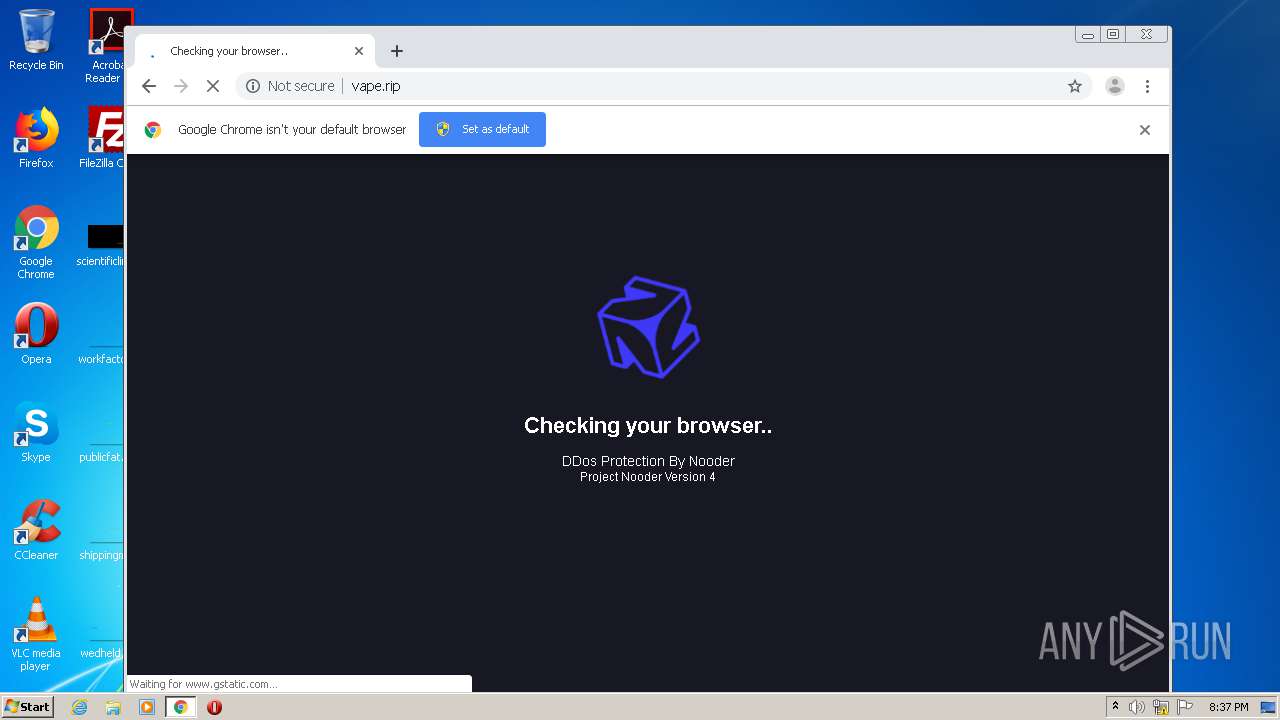
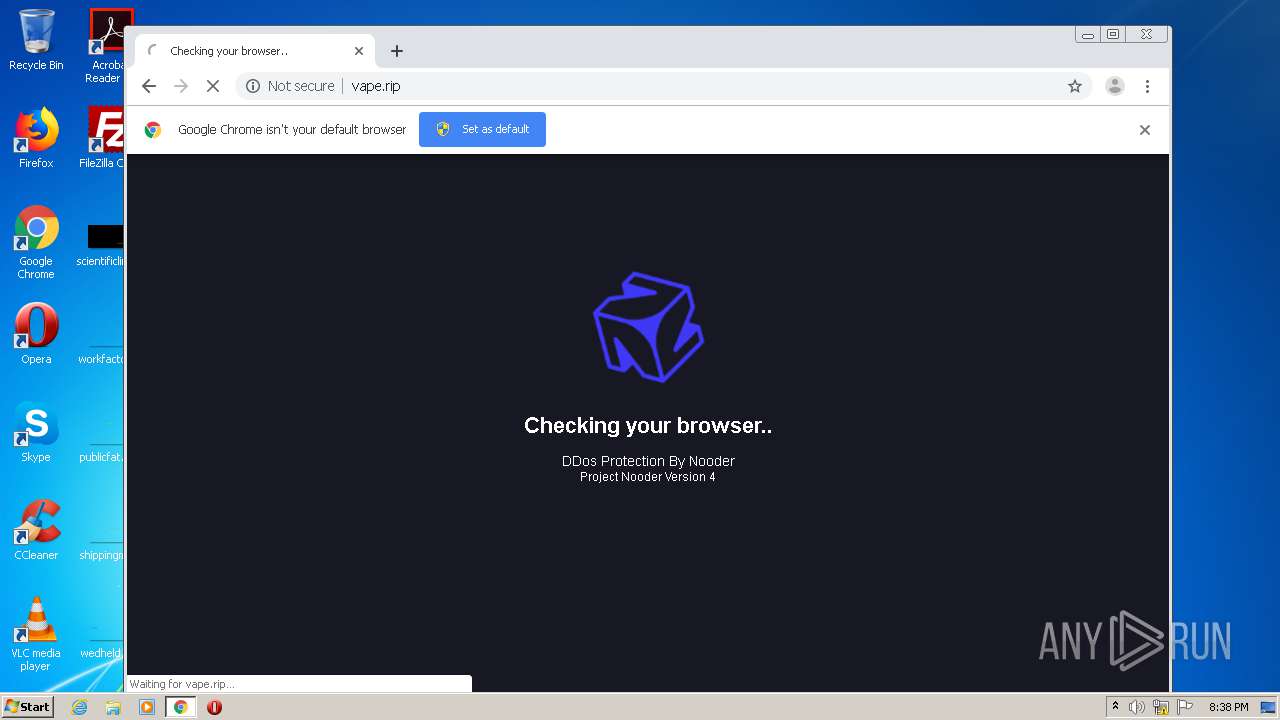
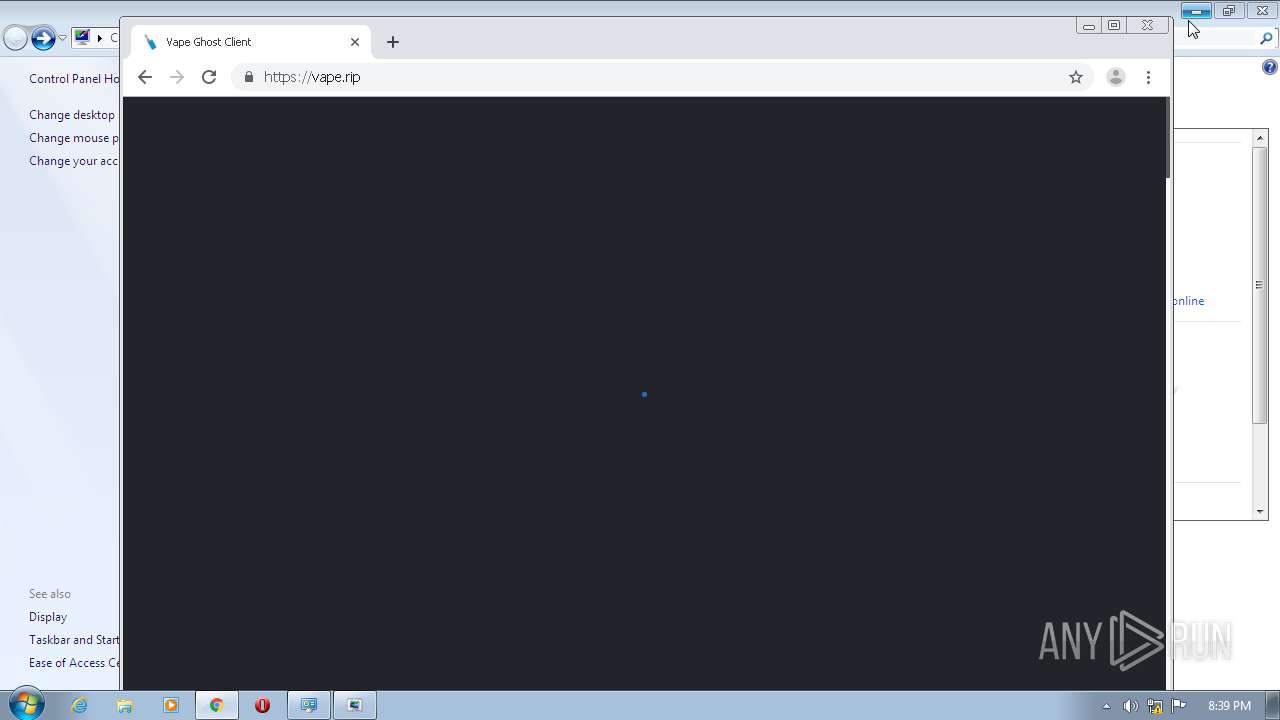
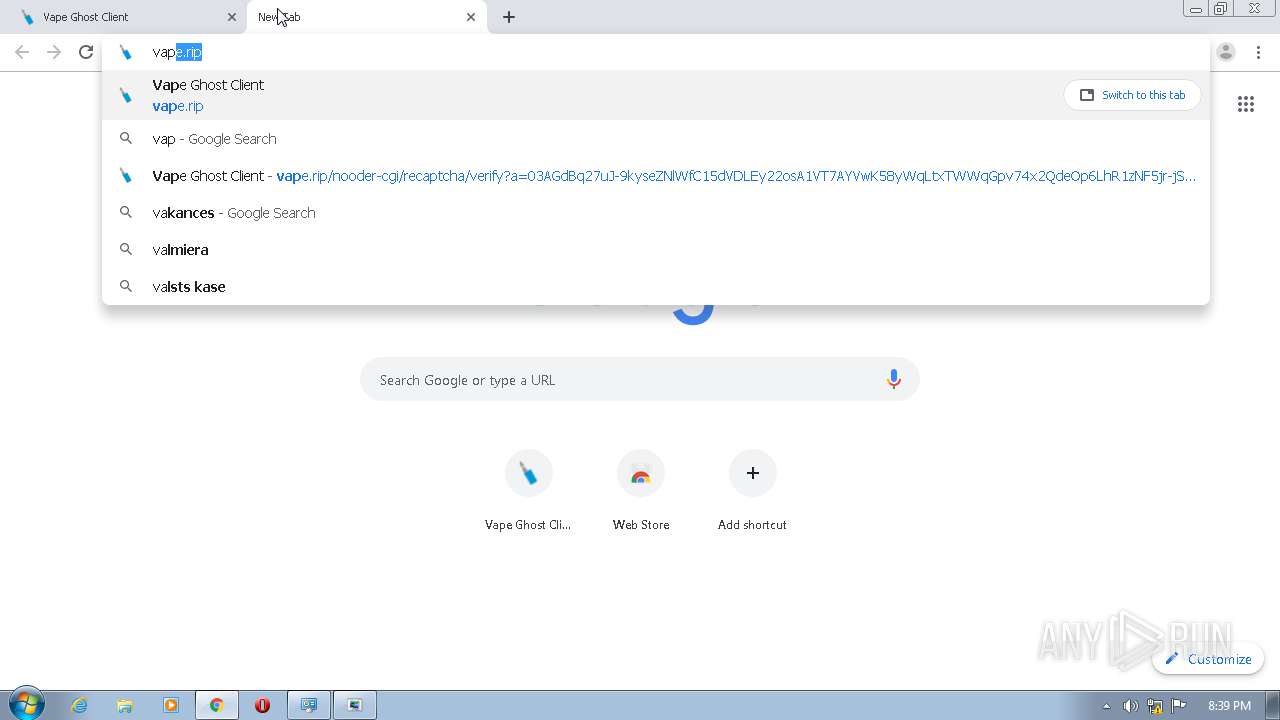
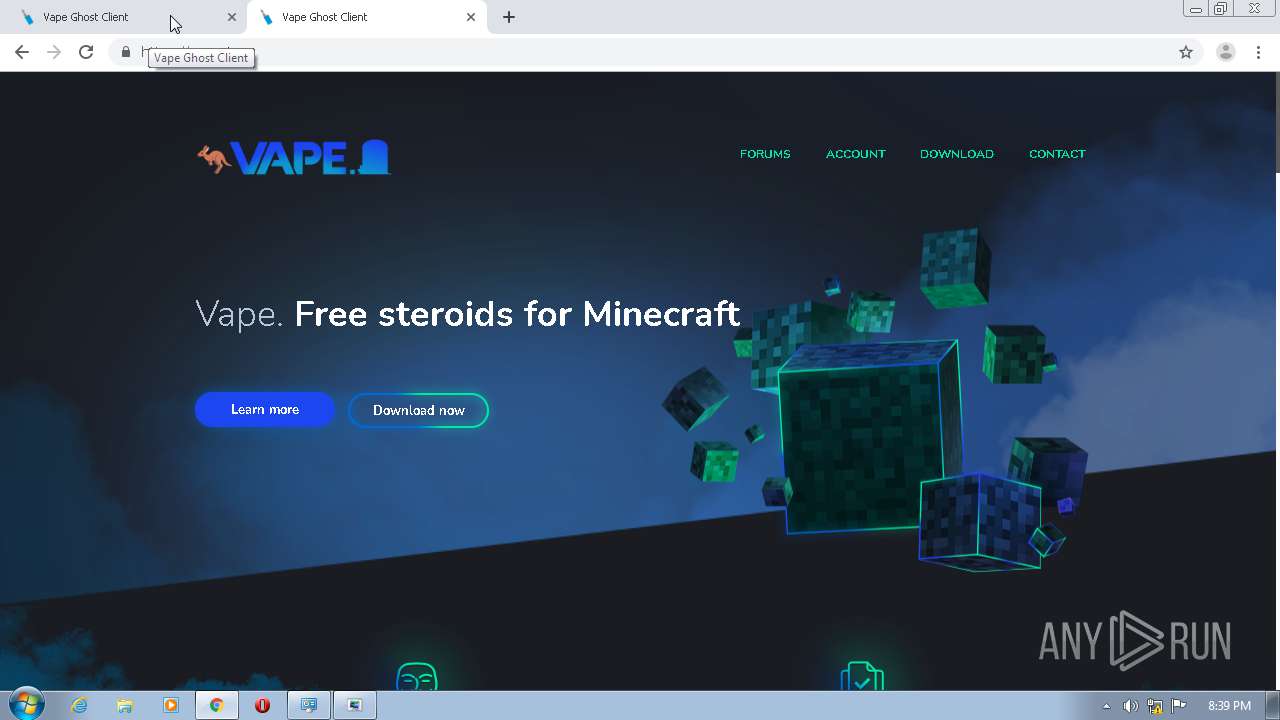
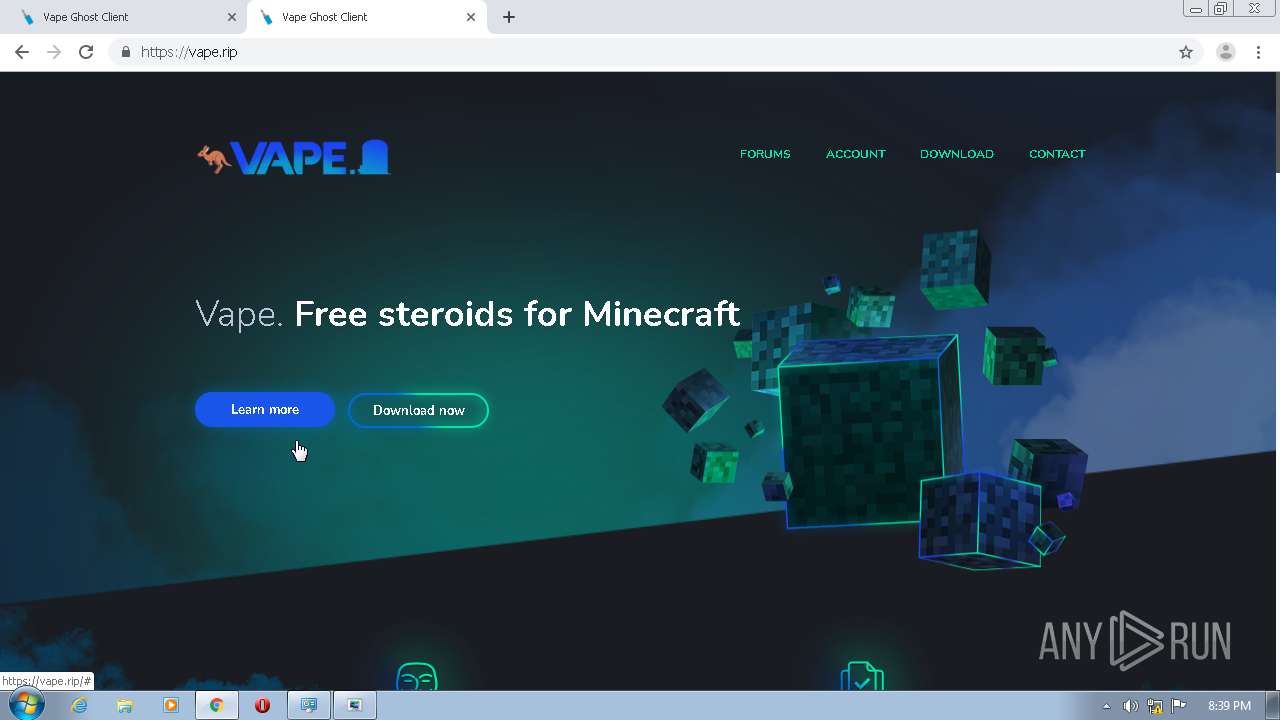
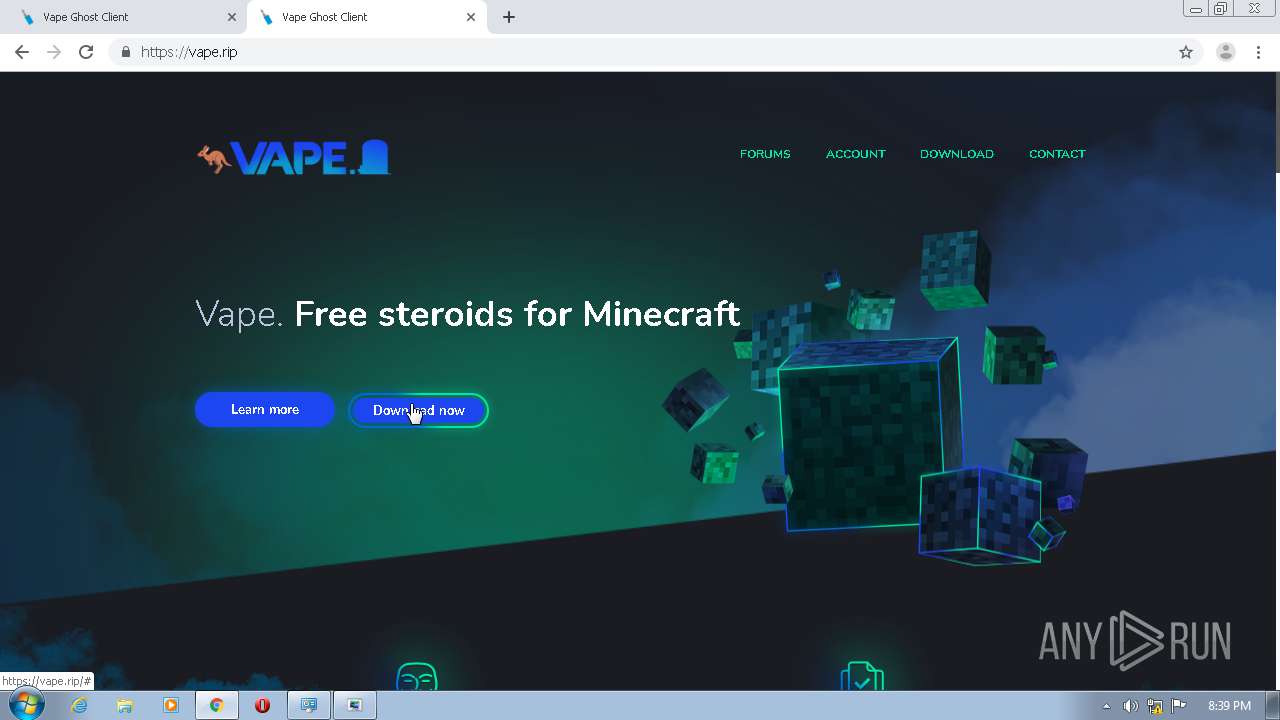
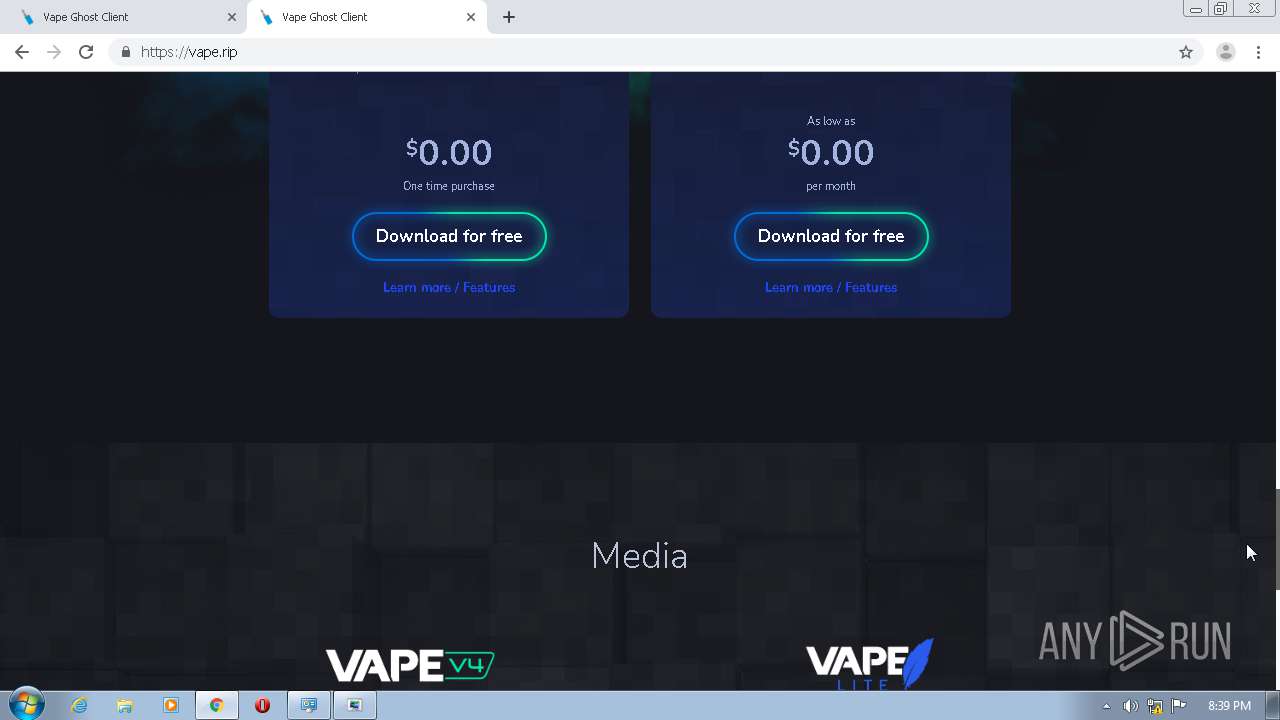
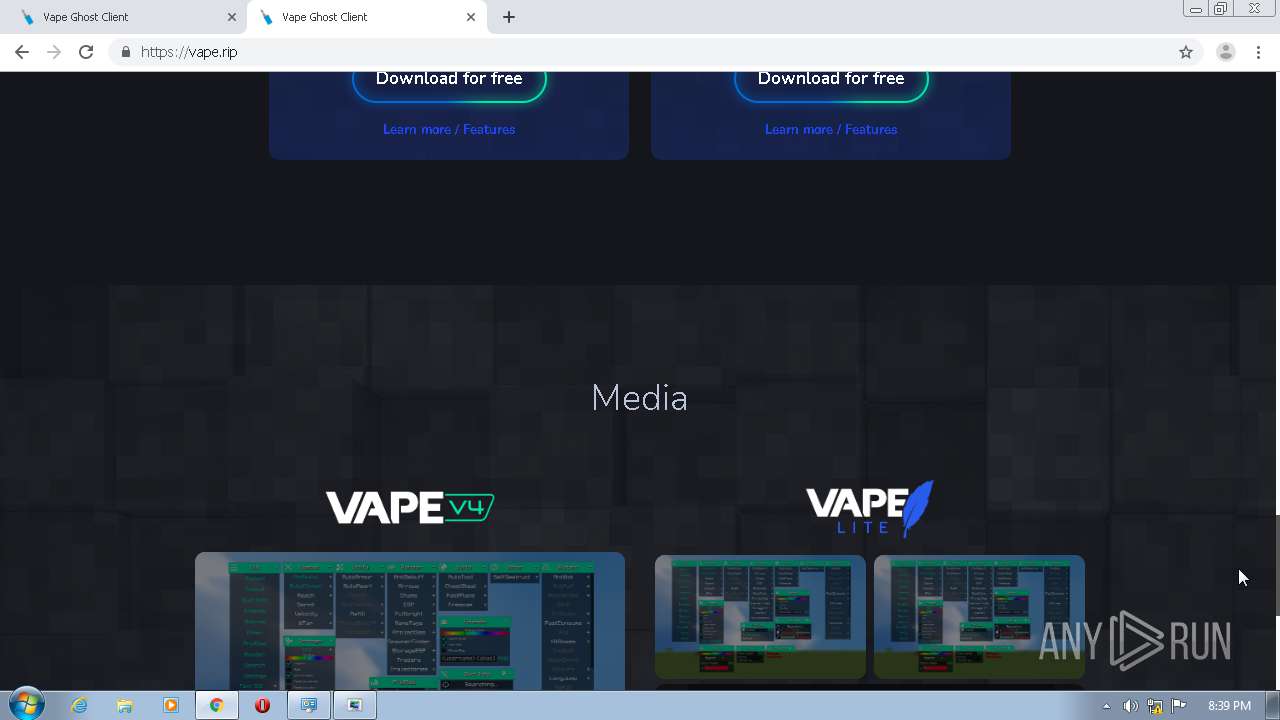
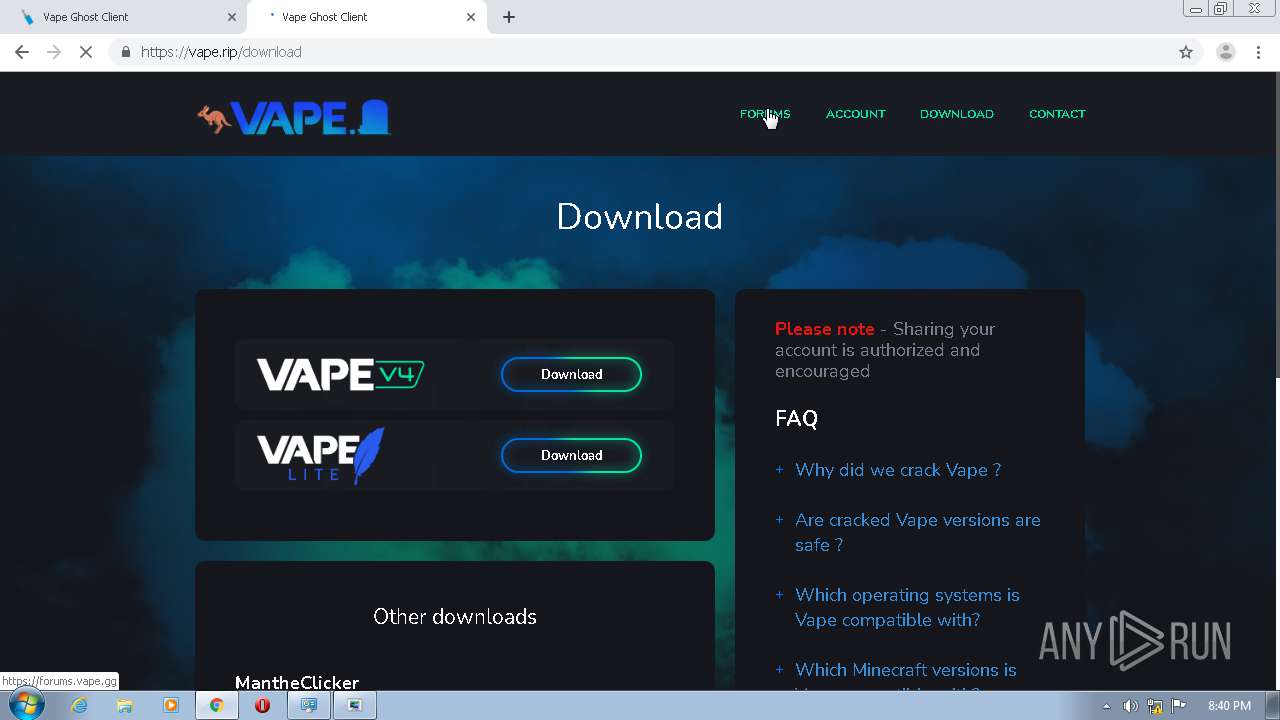
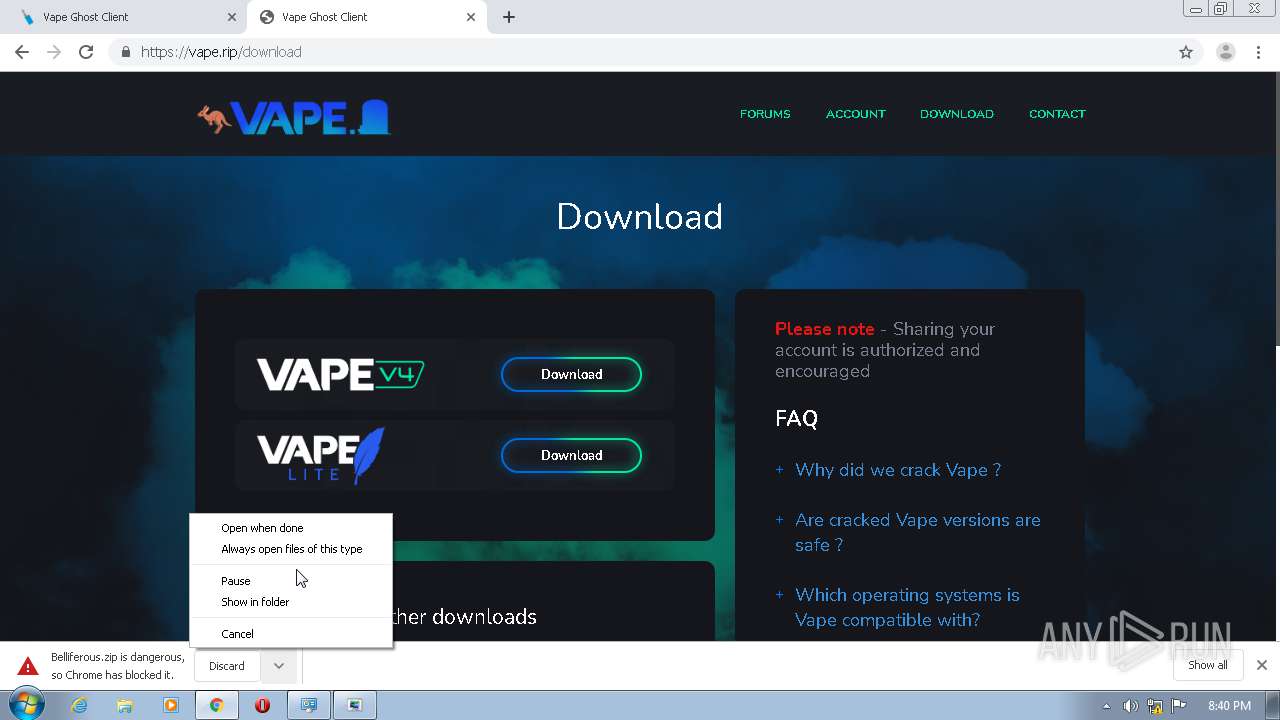
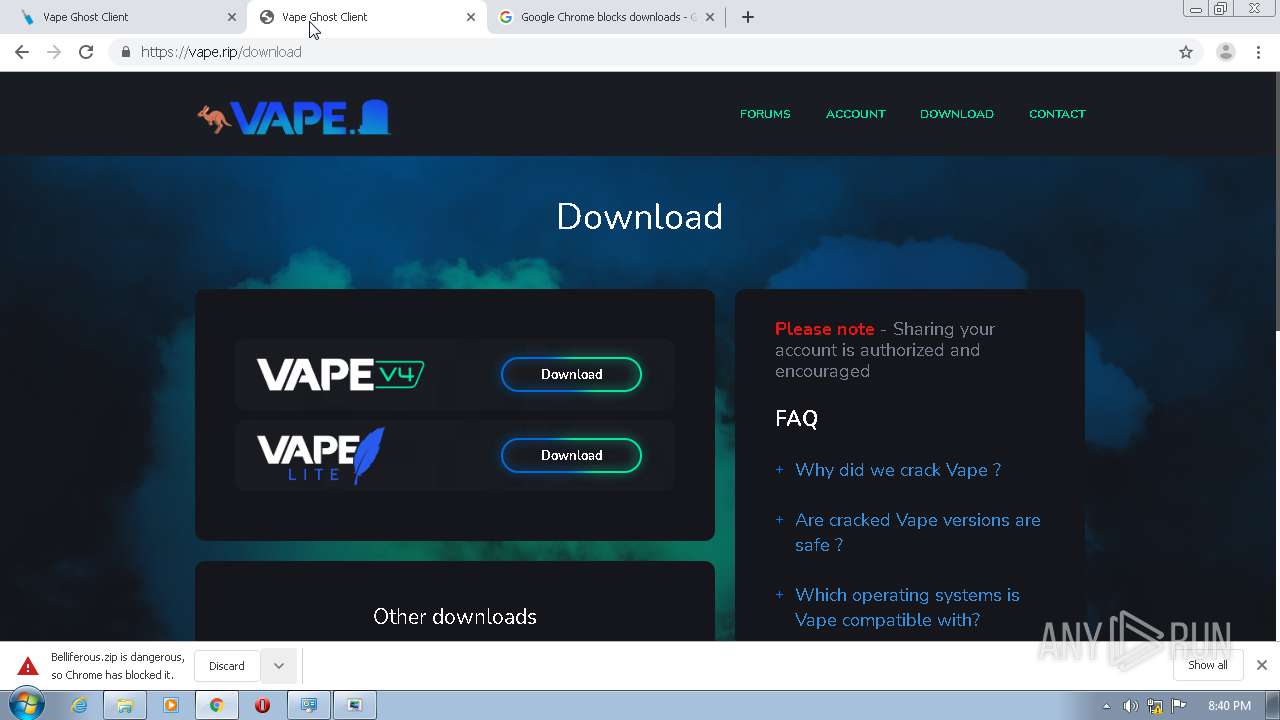
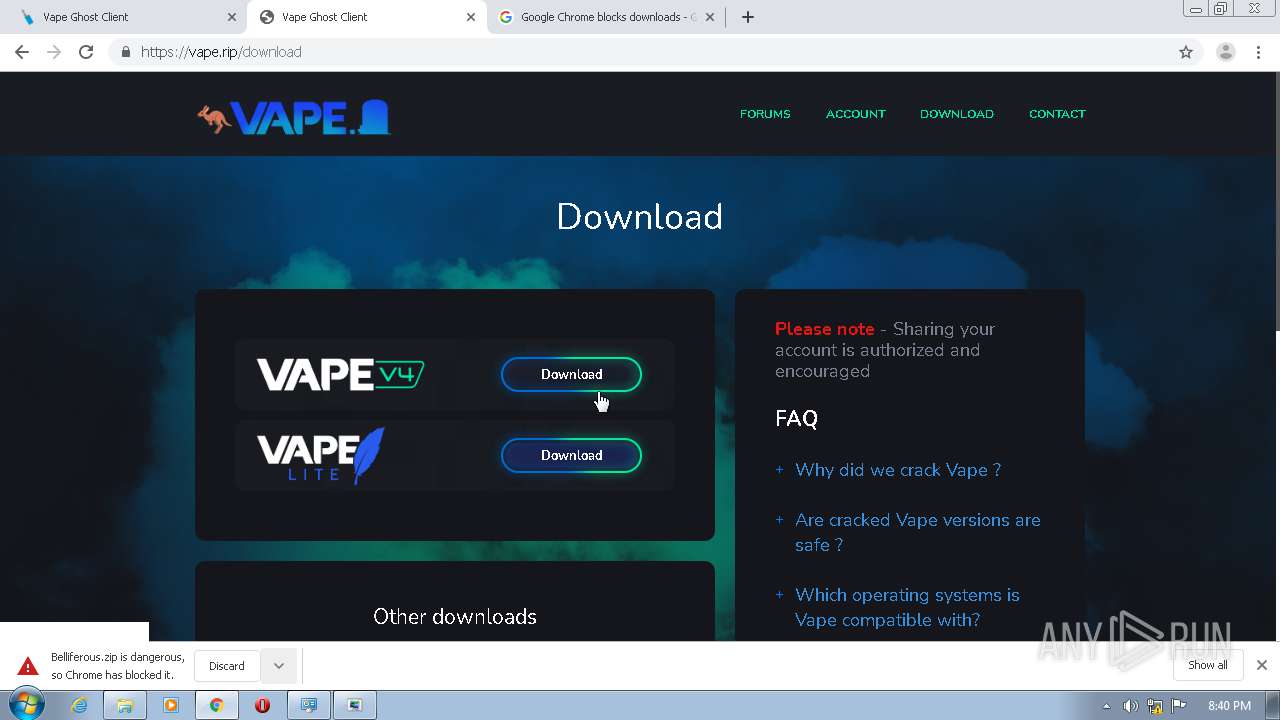
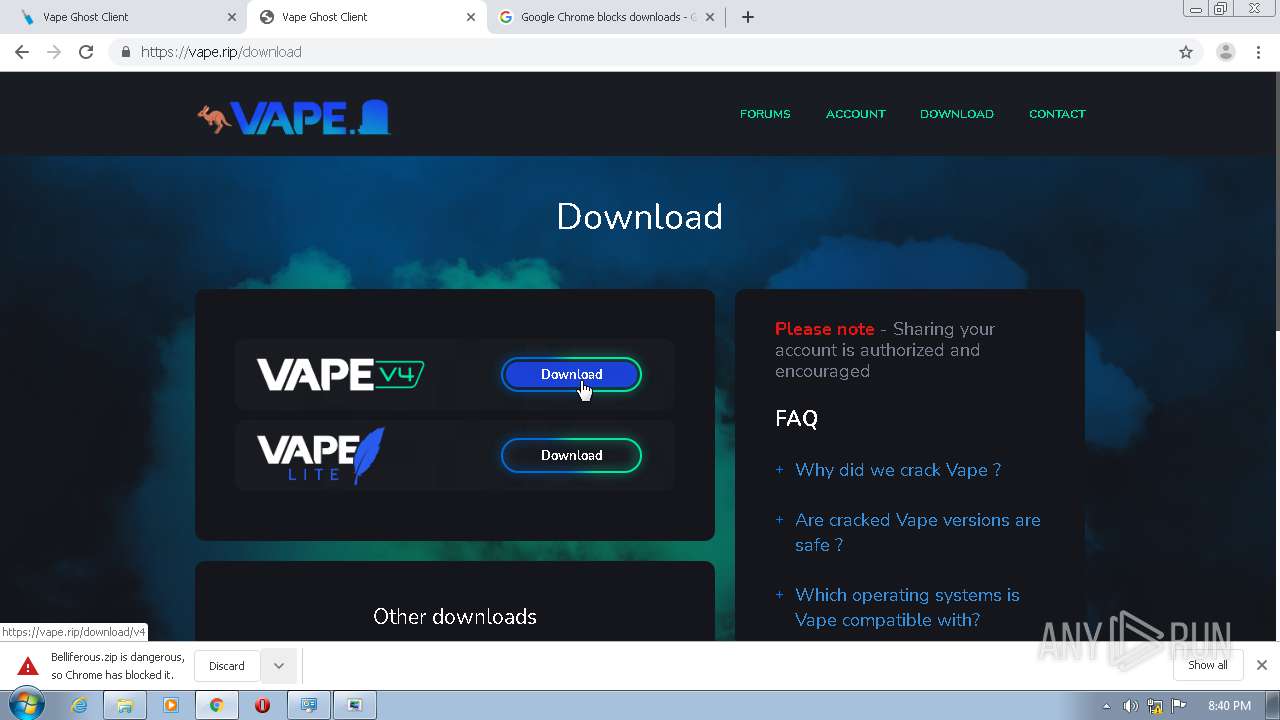
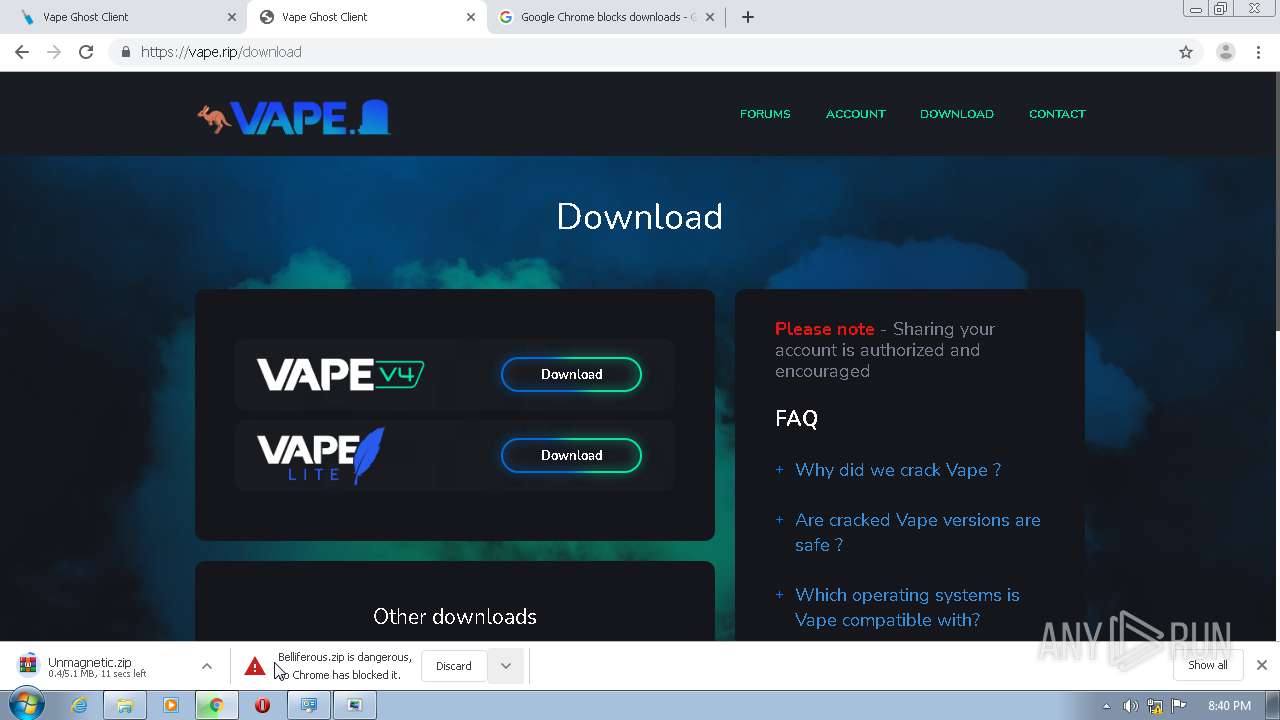
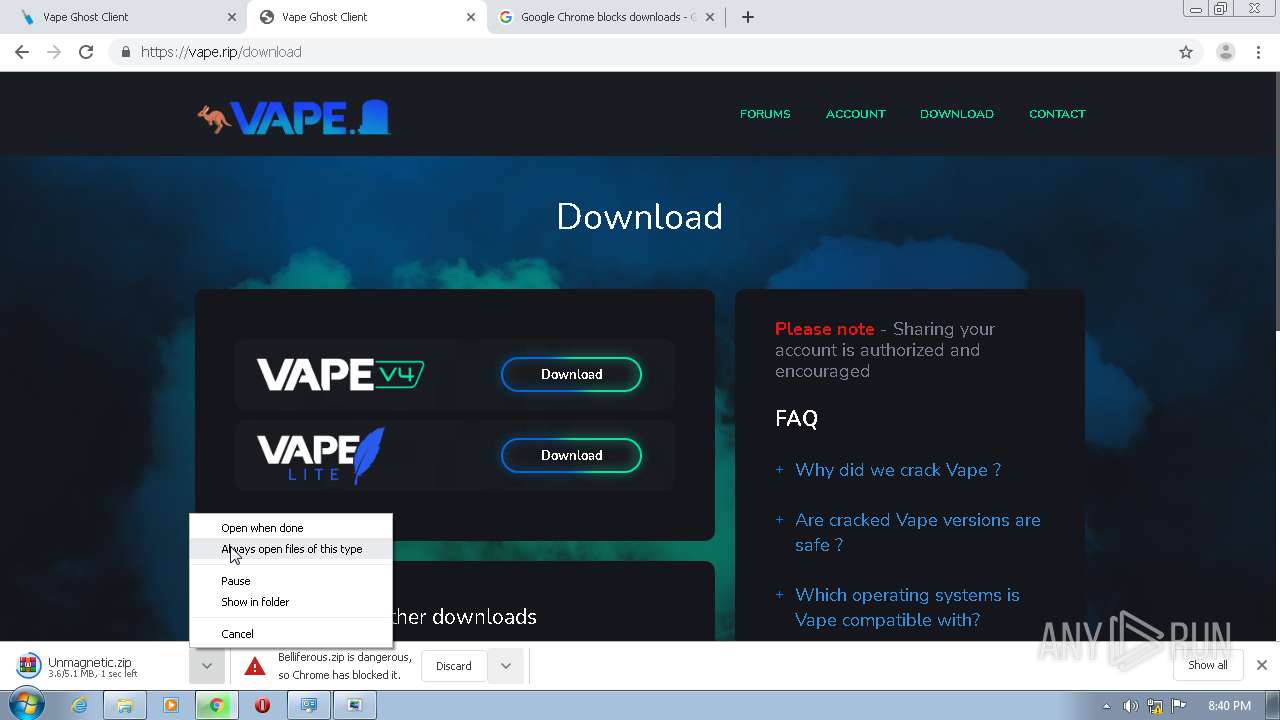
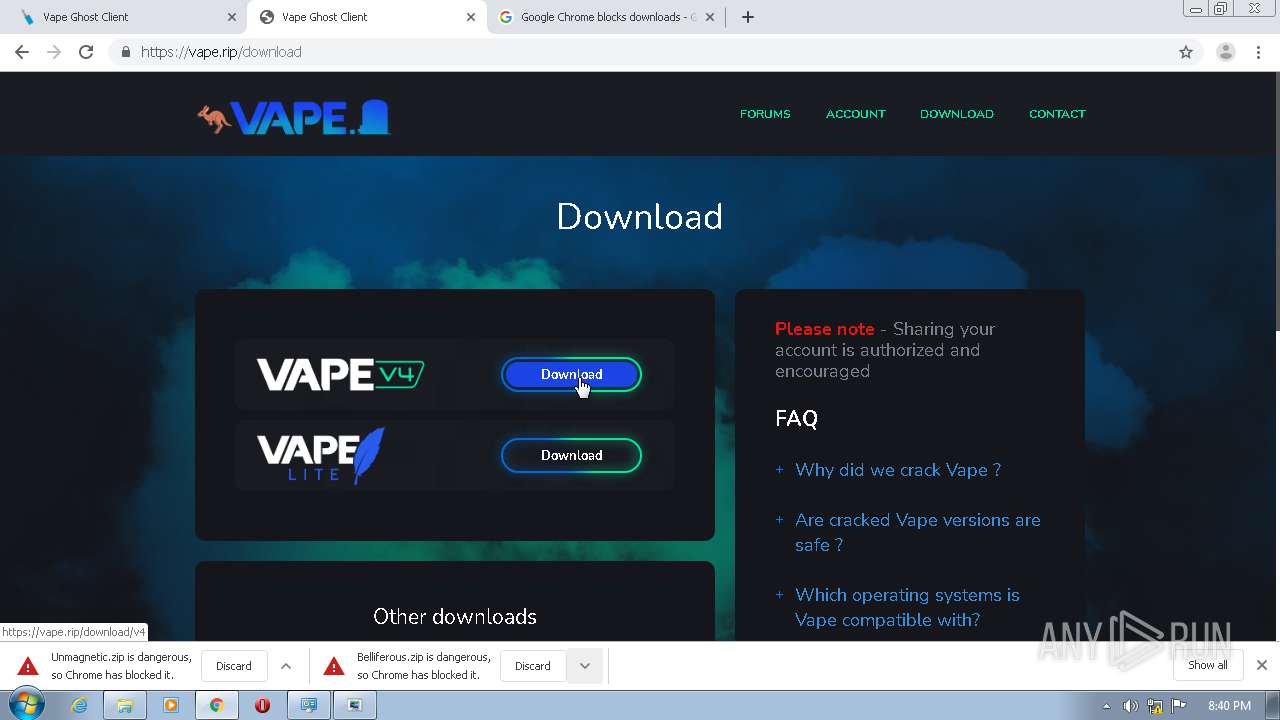
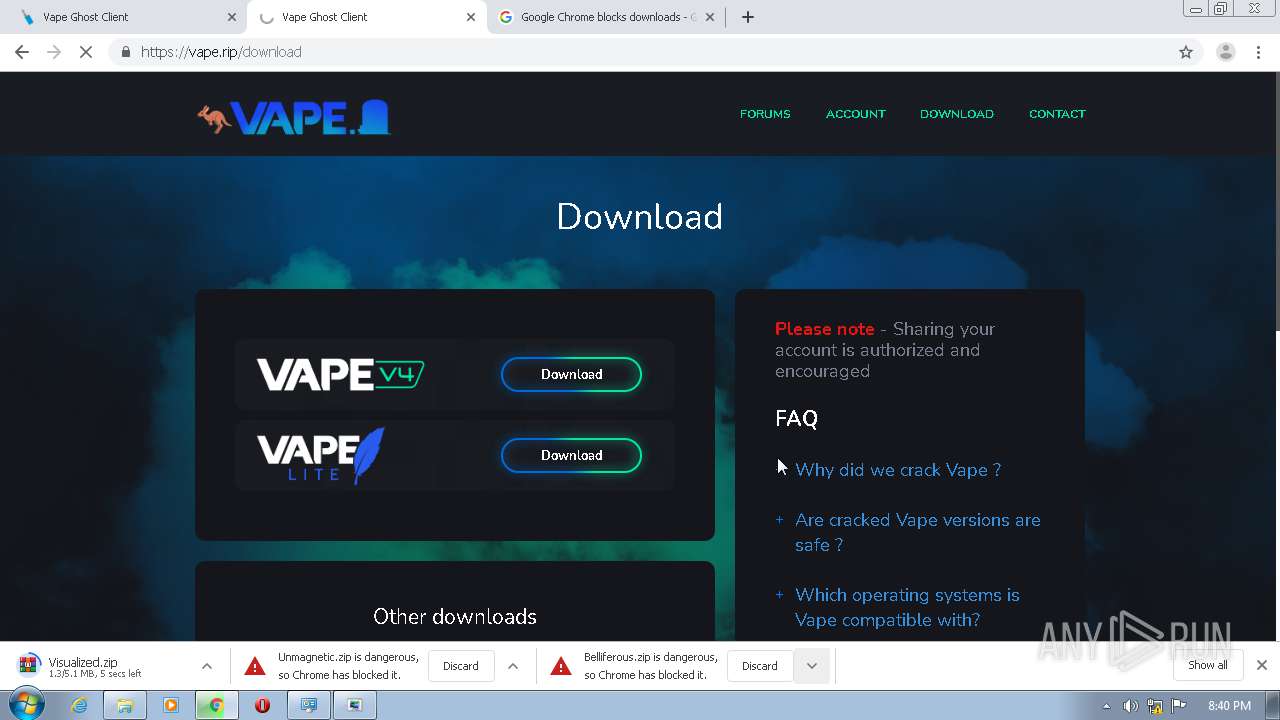
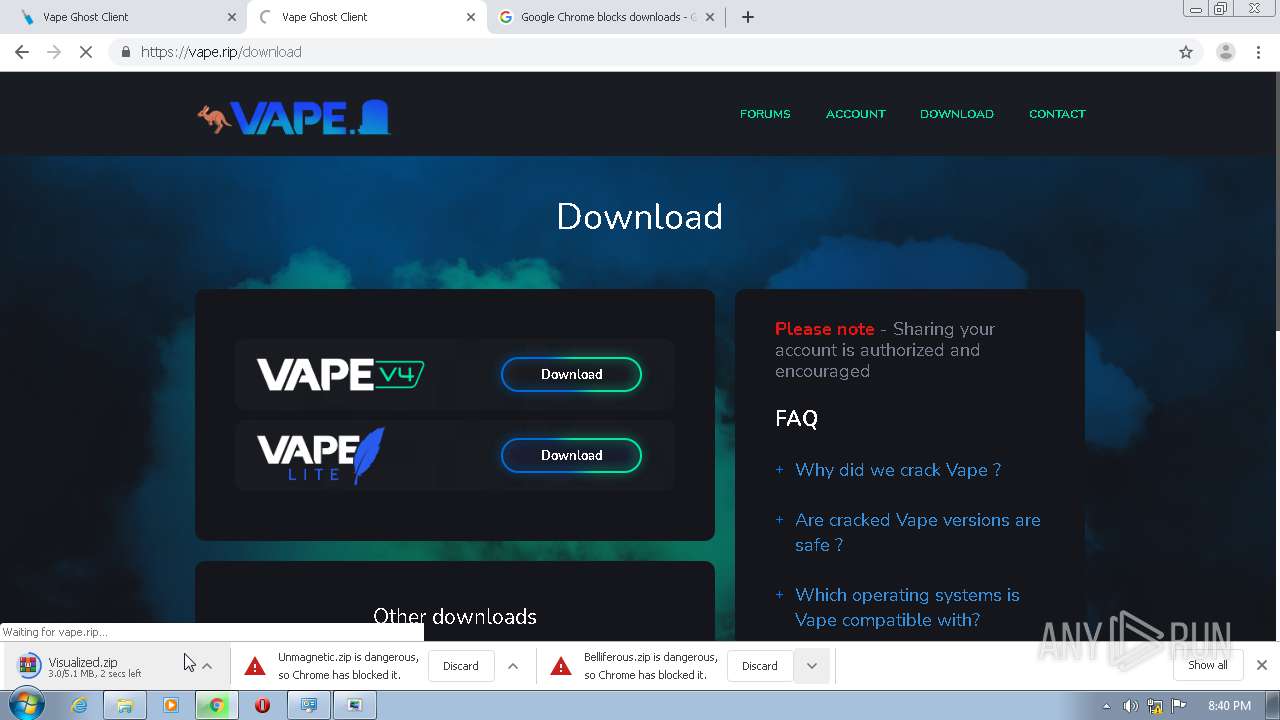
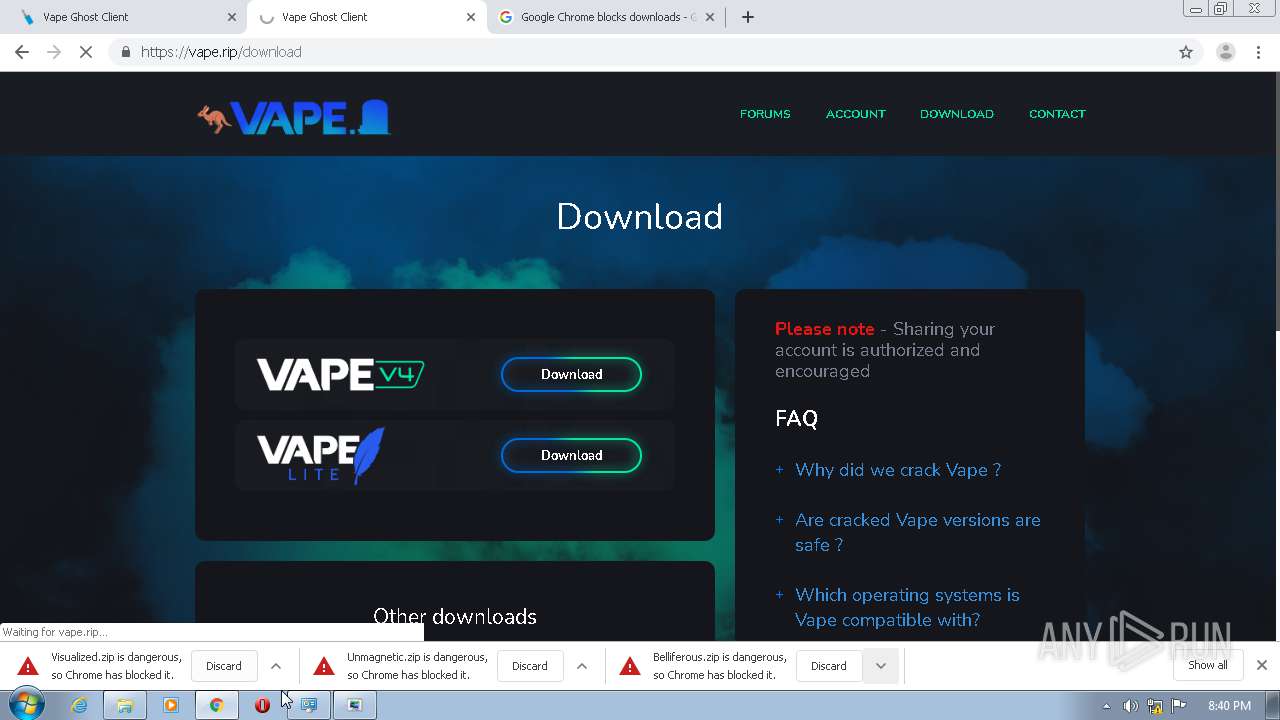
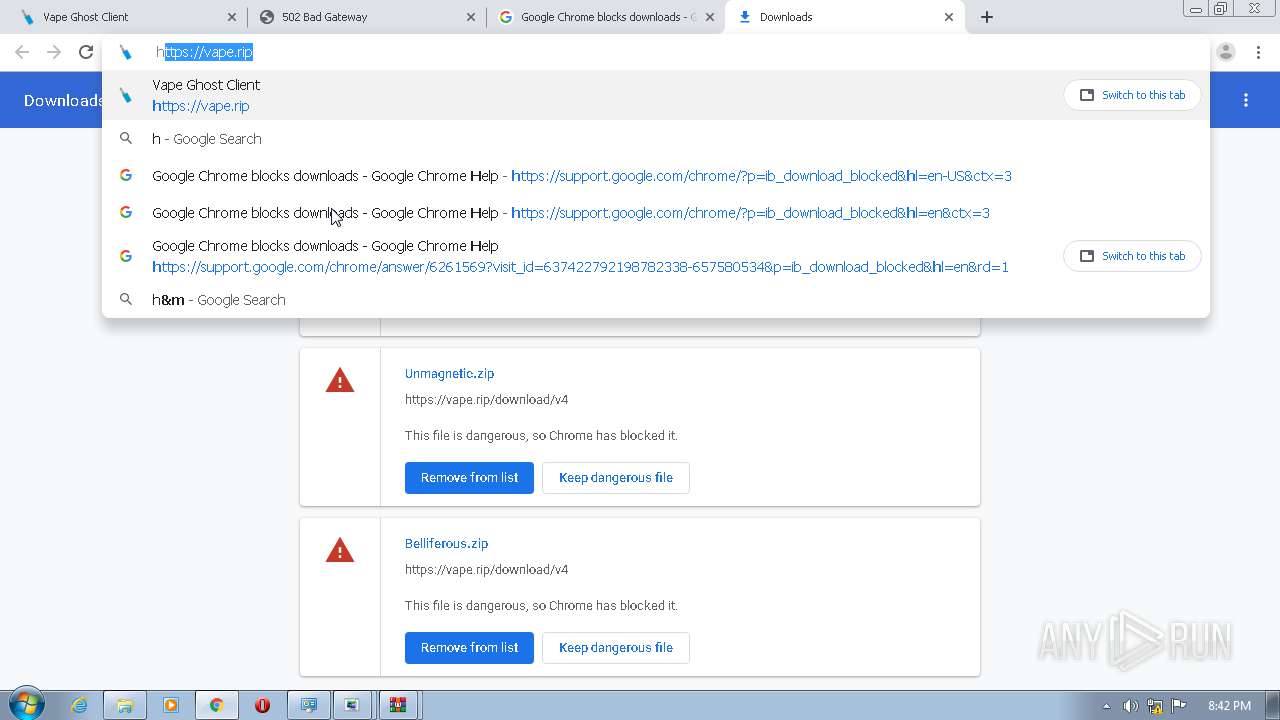
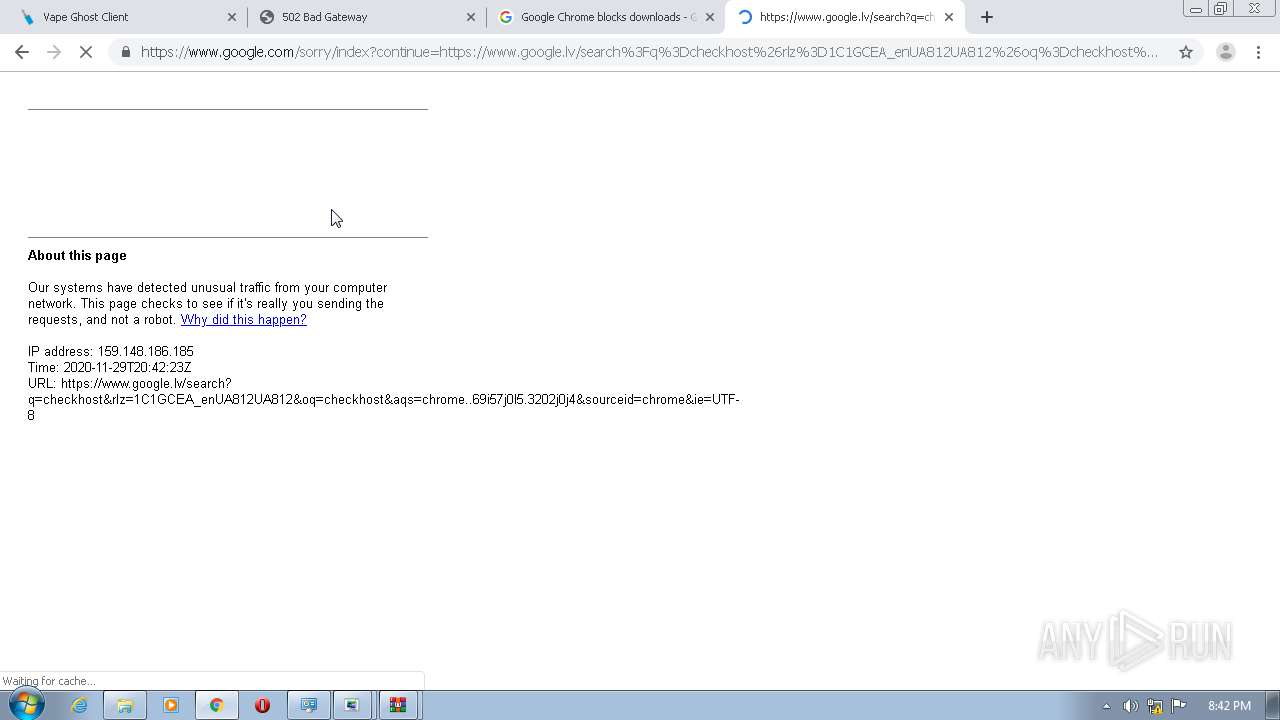
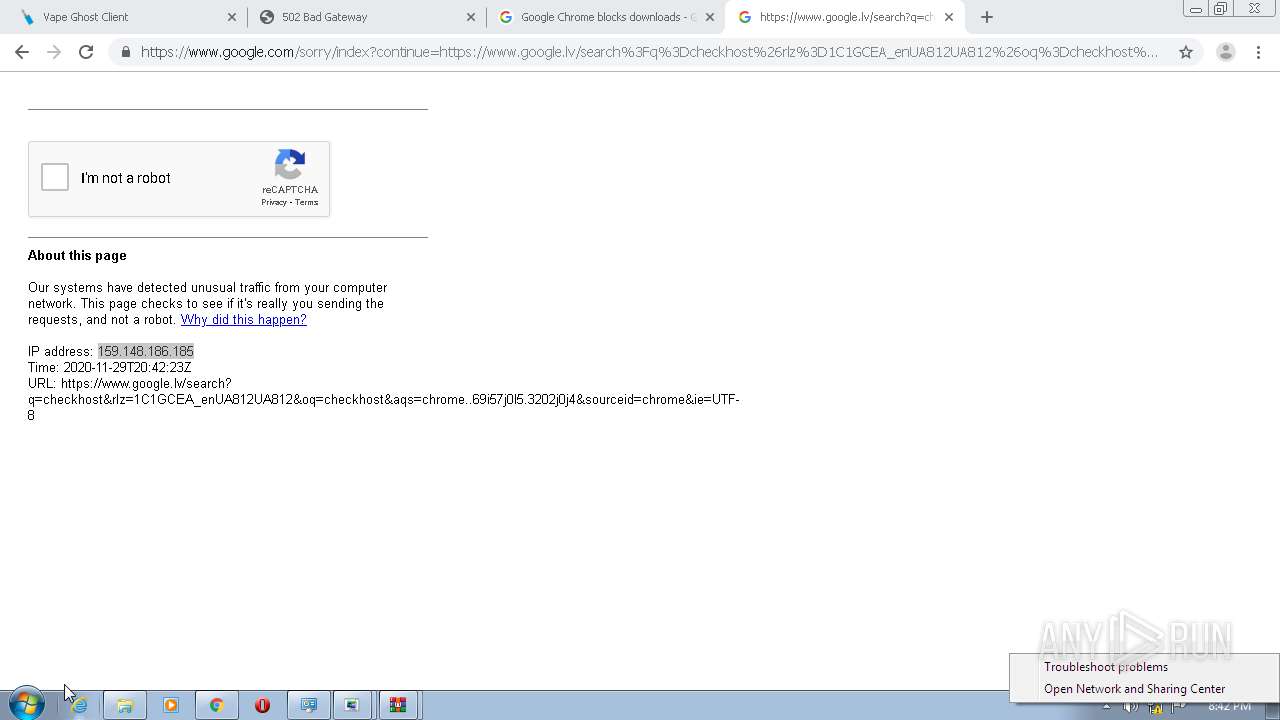
2384 | chrome.exe | GET | — | 45.138.200.4:80 | http://vape.rip/nooder-cgi/recaptcha/check.js | unknown | — | — | malicious |
2384 | chrome.exe | GET | 302 | 45.138.200.4:80 | http://vape.rip/ | unknown | text | 21 b | malicious |
2384 | chrome.exe | GET | 302 | 45.138.200.4:80 | http://vape.rip/ | unknown | text | 21 b | malicious |
2384 | chrome.exe | GET | 200 | 45.138.200.4:80 | http://vape.rip/ | unknown | html | 2.06 Kb | malicious |
2384 | chrome.exe | GET | 307 | 45.138.200.4:80 | http://vape.rip/nooder-cgi/recaptcha/verify?a=03AGdBq27uJ-9kyseZNlWfC15dVDLEy22osA1VT7AYVwK58yWqLtxTWWqGpv74x2QdeOp6LhR1zNF5jr-jS80fqRaMVeHJRiolAYsmyDkwwsjFJ_cGF9w_W7fhYdpFllezXLw5k7_dLrPlt5UvIuRiYpuR5CiQ48yQiOPfTPX1pJZw1YCWb-aCDtLqiXHcS6Ngh8dKgetnIuhC3zmUe-WBR3HLOASw7PZJhEmWbcFE4zq466wT0KFmwGvr_Vp16vzGpY6Ru7zh5qA2bpJkSBSadwdZHZOl0TIoVRMA5Y3lu7sqyuzcV8q_IXerEwoaDEonZECFB0RU2TCRCz1EffwTEdV0JVxHug329TrtPp4QLmrllGyu4AhAcfjj4dhz4hZZ7iO_Jv7YLEqIrTlaKEySi7WeeEoBrjcpIccaVaA8TvRvsGf_D2n7R_piRrMVF-xYrlAGQd3lJBKSrhUOhzmDdjKIF9v0YDHMXQ | unknown | text | 11 b | malicious |
2384 | chrome.exe | GET | 403 | 45.138.200.4:80 | http://vape.rip/favicon.ico | unknown | text | 3 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2384 | chrome.exe | 172.217.12.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2384 | chrome.exe | 142.250.74.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2384 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2384 | chrome.exe | 172.217.6.206:443 | apis.google.com | Google Inc. | US | whitelisted |
2384 | chrome.exe | 172.217.23.110:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2384 | chrome.exe | 172.217.21.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2384 | chrome.exe | 172.217.21.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2384 | chrome.exe | 45.138.200.4:80 | vape.rip | — | — | suspicious |
2384 | chrome.exe | 216.58.207.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2384 | chrome.exe | 151.101.12.193:443 | i.imgur.com | Fastly | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|