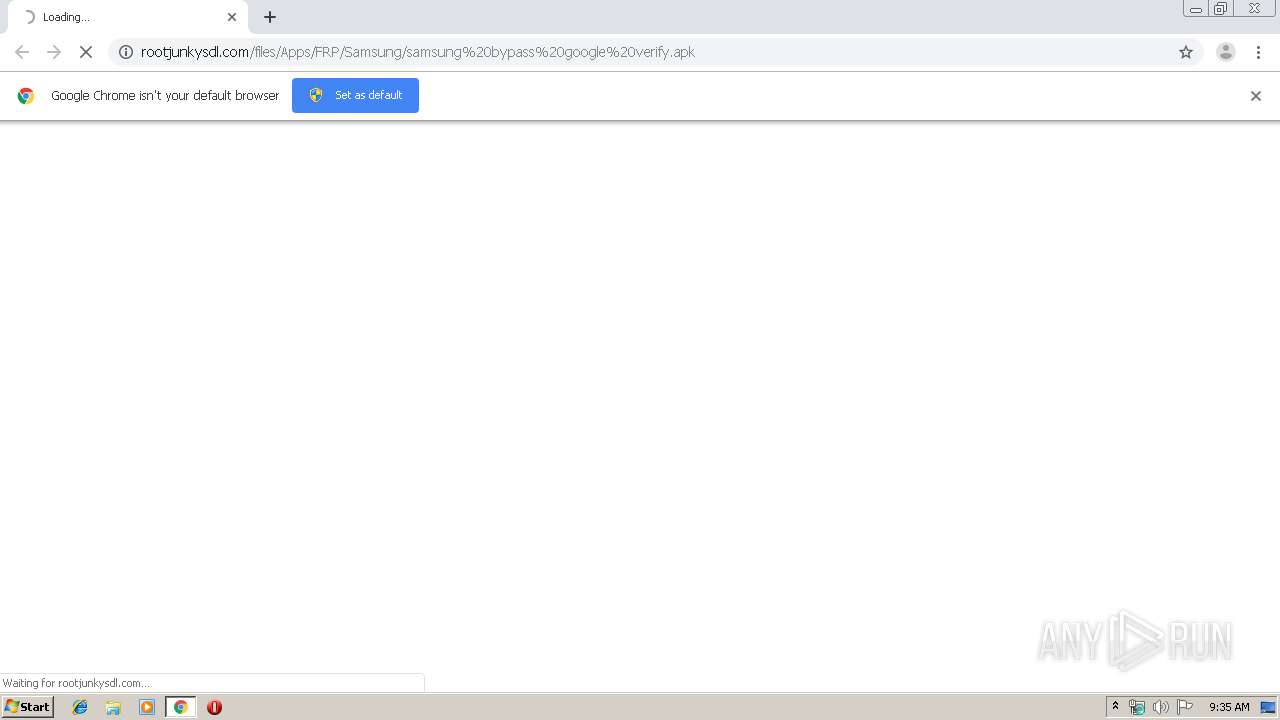
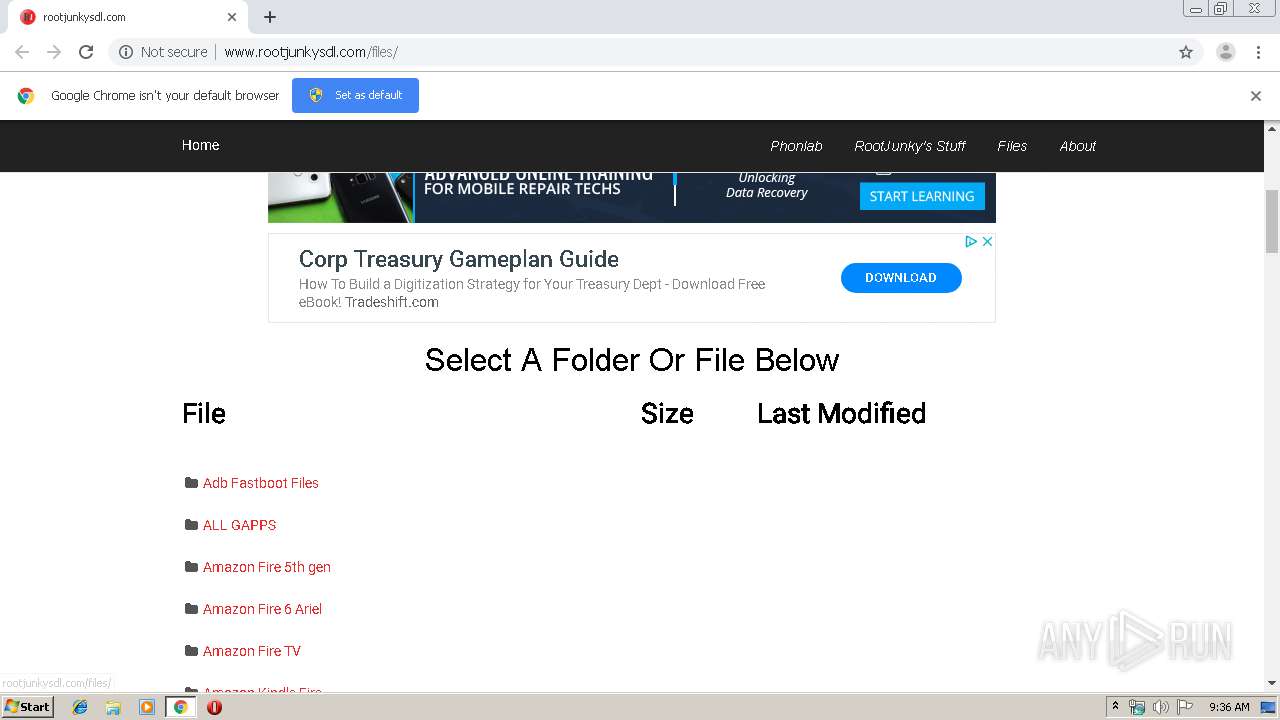
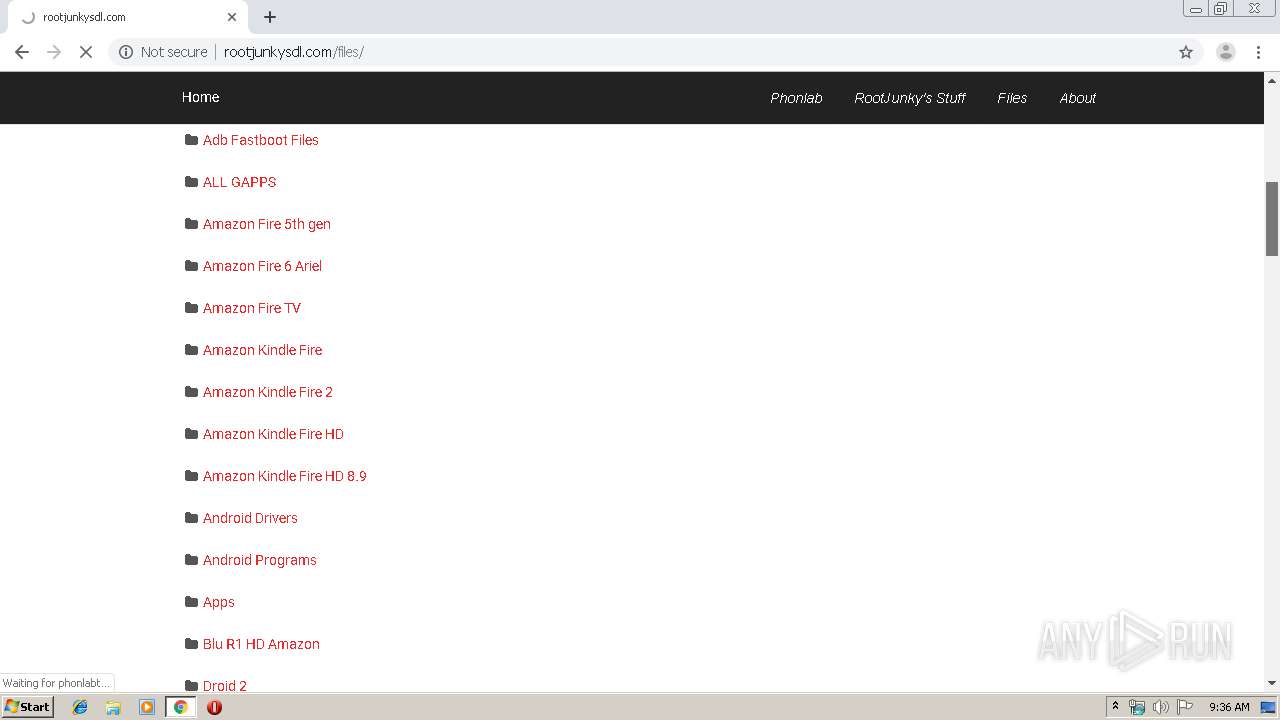
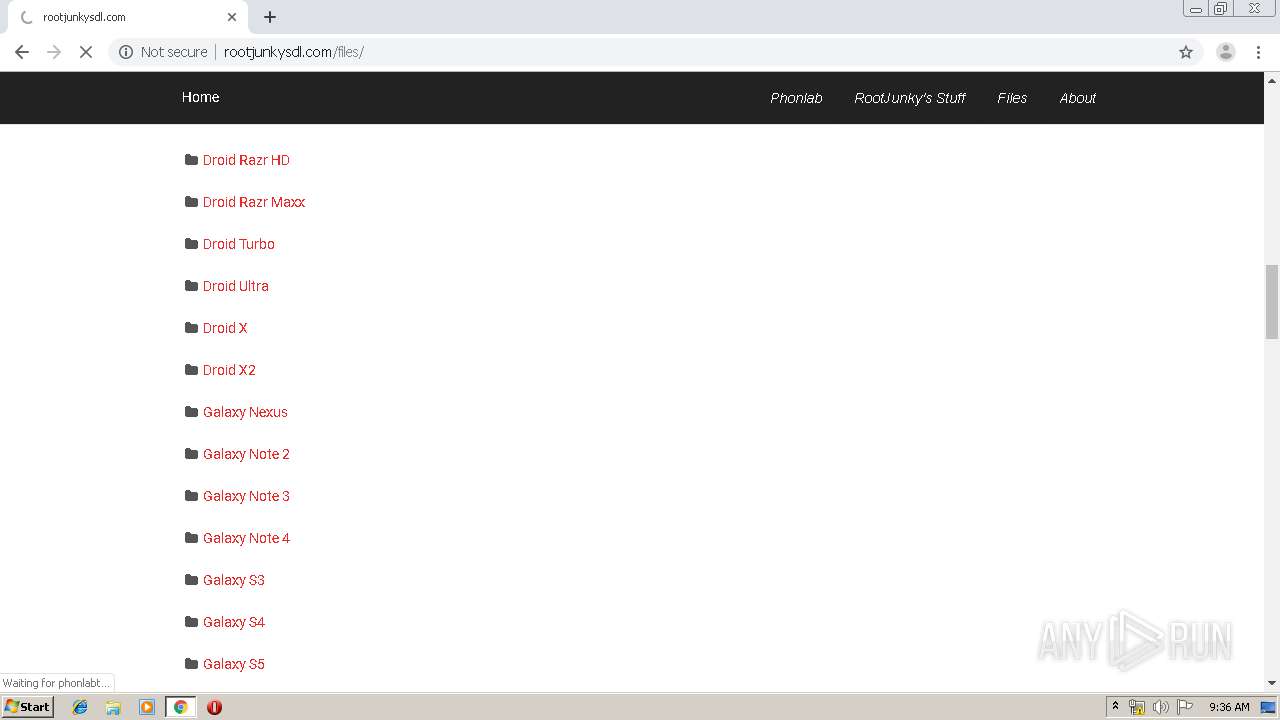
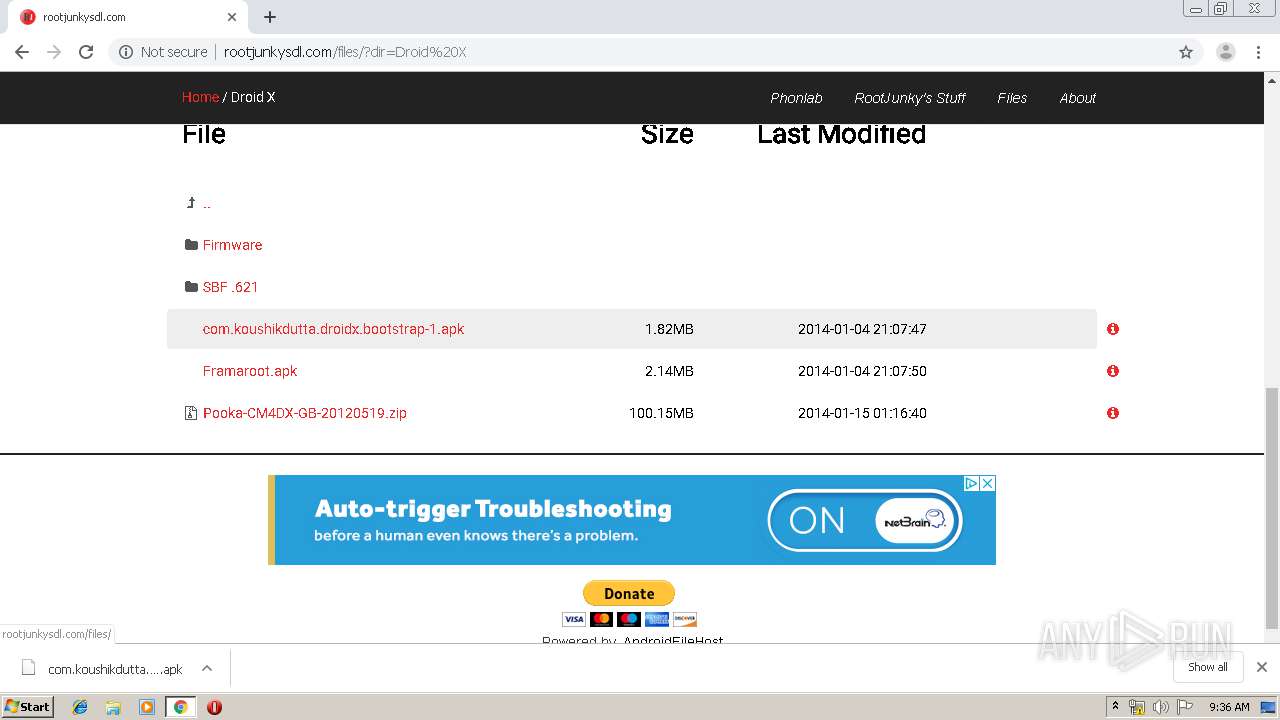
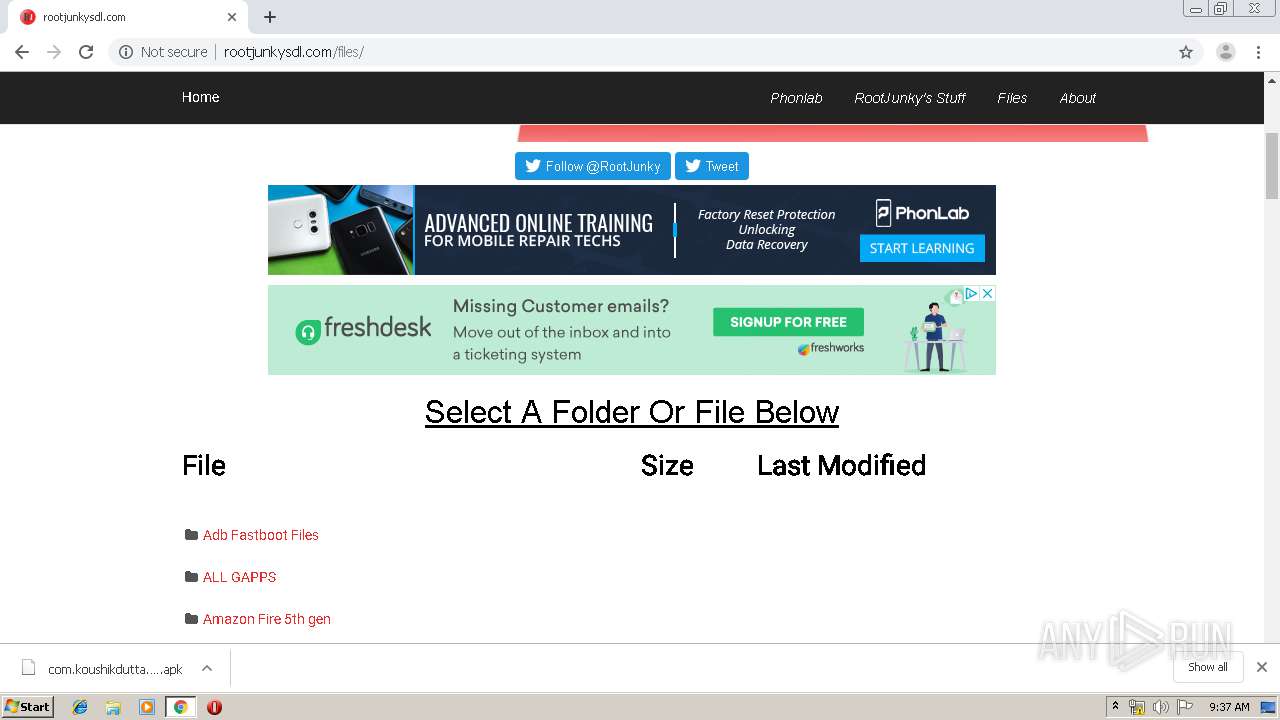
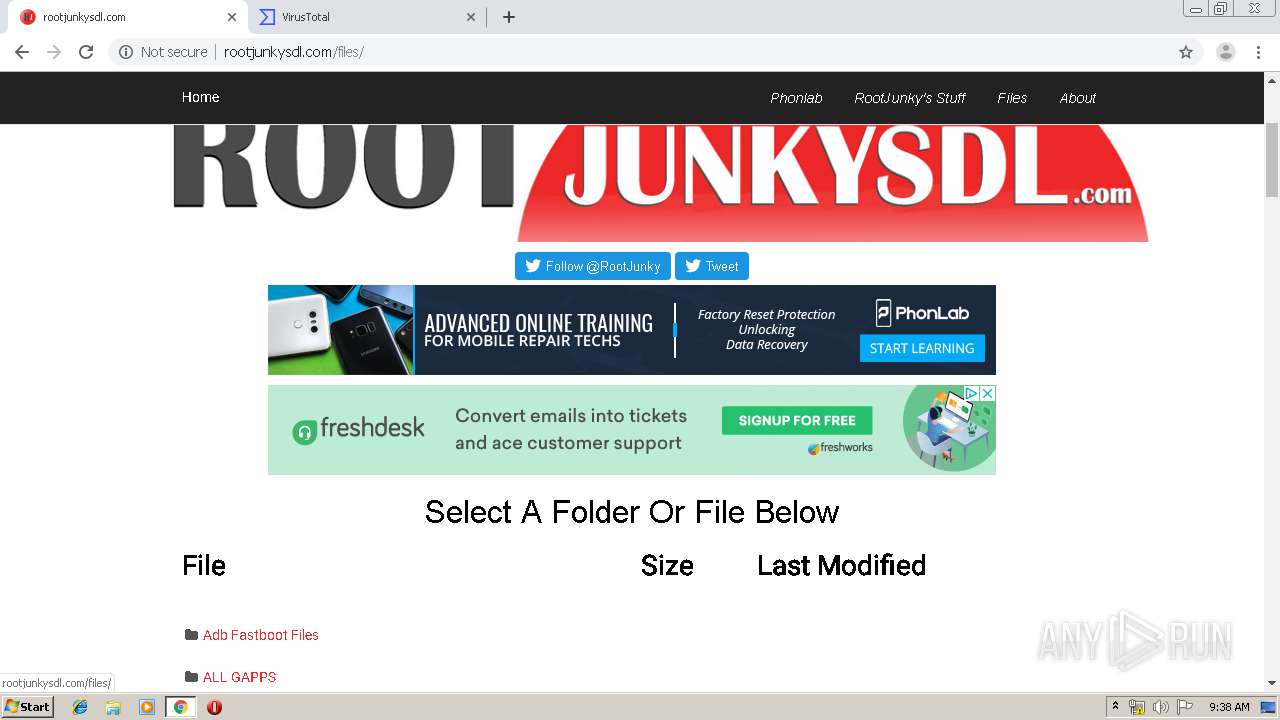
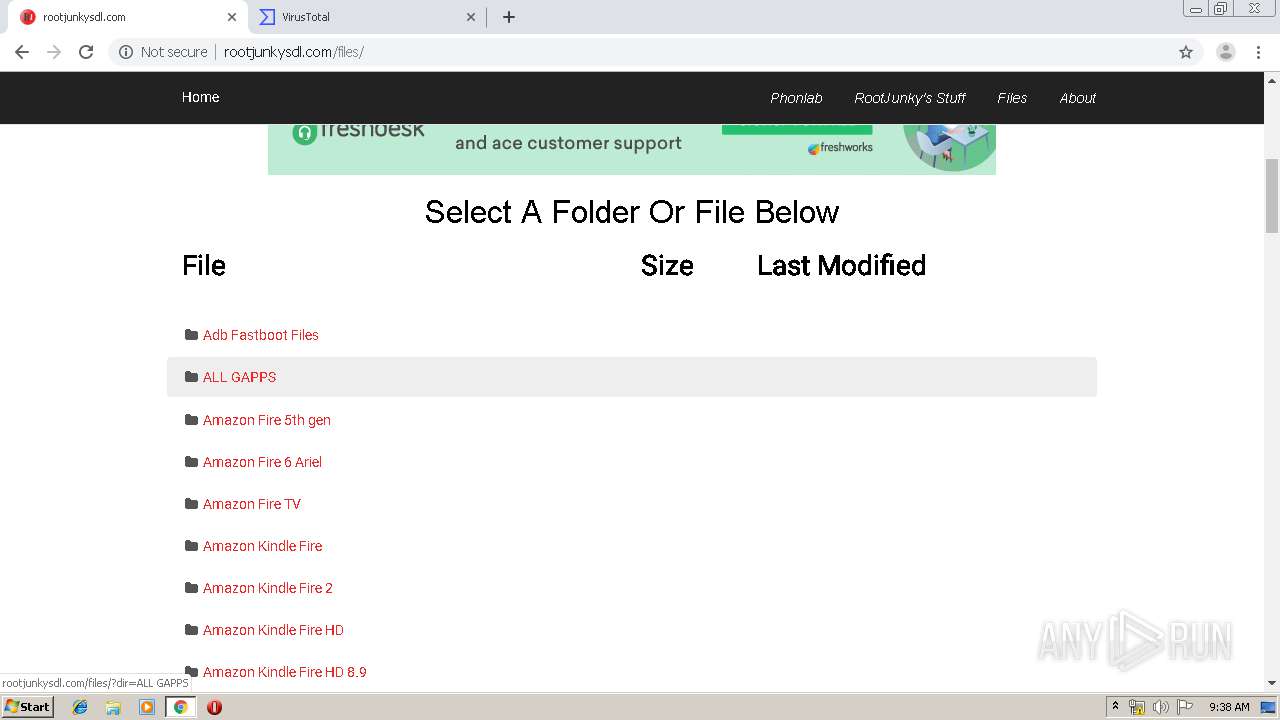
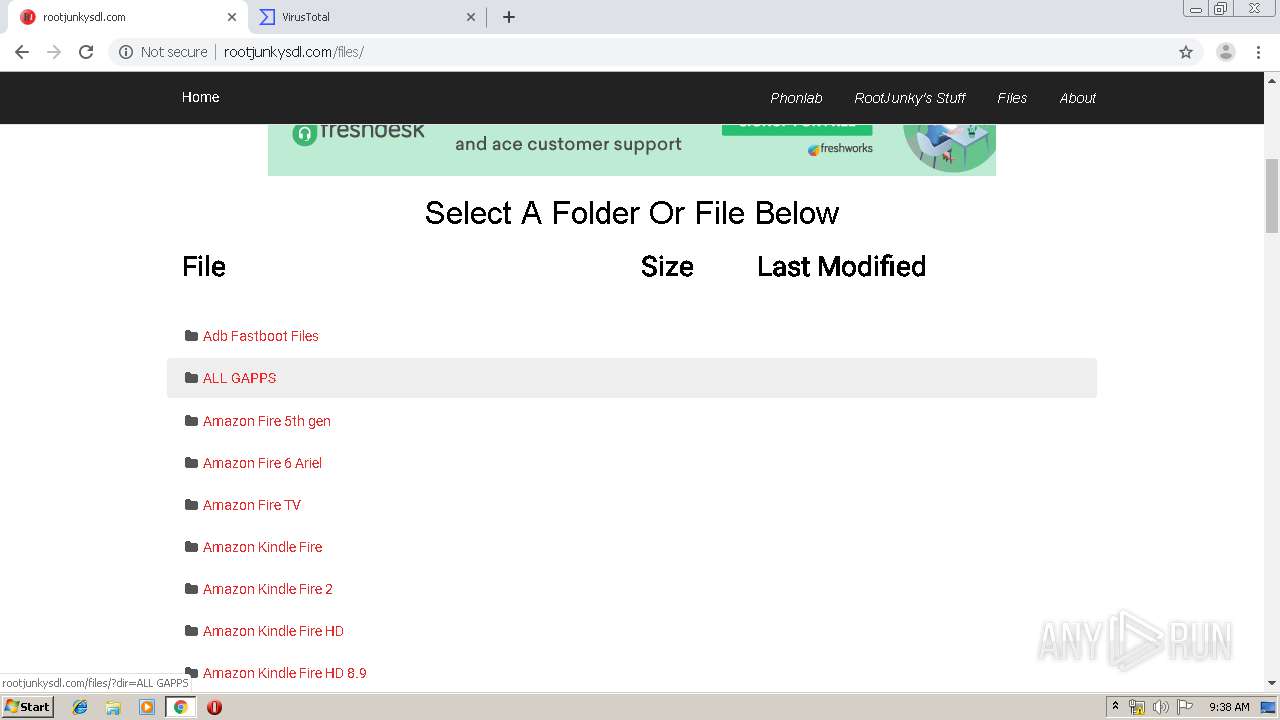
| URL: | http://rootjunkysdl.com/files/Apps/FRP/Samsung/samsung%20bypass%20google%20verify.apk |
| Full analysis: | https://app.any.run/tasks/9eaba539-0544-4436-9ba6-93c13d71e6a4 |
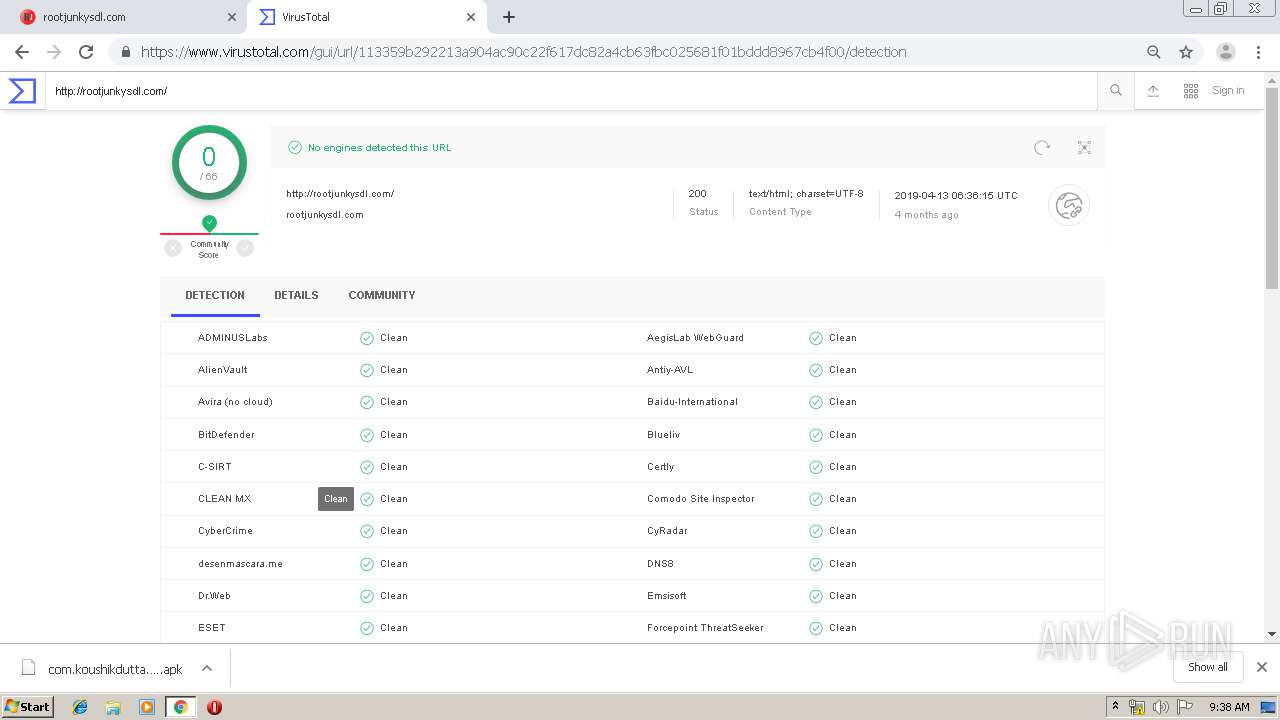
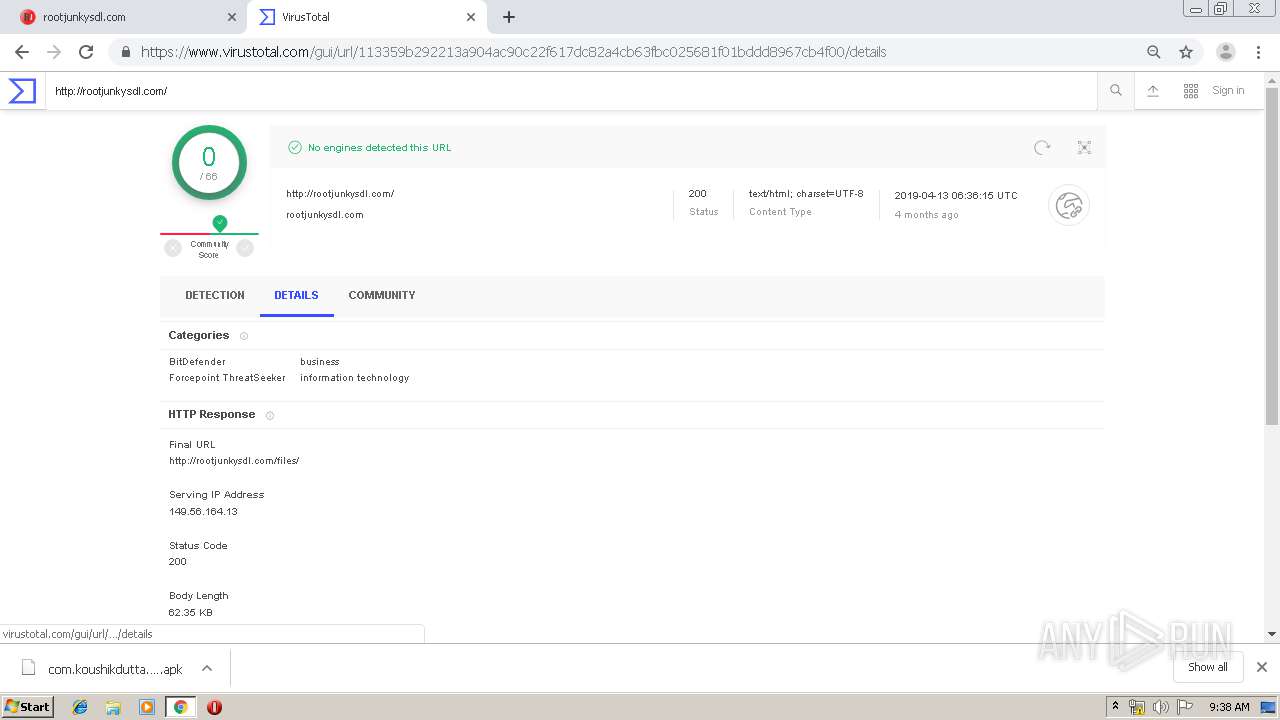
| Verdict: | No threats detected |
| Analysis date: | August 22, 2019, 08:35:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 67F1D73511C61B3F96B26BBF61196A38 |
| SHA1: | 1C4D16E83B5B85CA1910C9E73AF2198F97EEB0DE |
| SHA256: | 74A4B788F1C564FA4B8F255C4E7ACD996789F3F757004714541A91A3E59506DB |
| SSDEEP: | 3:N1KM/QLOcUd3D0KiBK2hmfXaeAXoK3lFLALf:CMCi3aBthm3K7ALf |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3512)
INFO
Application launched itself
- chrome.exe (PID: 3512)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3512)
Reads Internet Cache Settings
- chrome.exe (PID: 3512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
58
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9842723499123115067 --renderer-client-id=55 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3612 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17517493145555731529 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3596 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17929608813418297516 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4139073764958244759 --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12706456602543377798 --mojo-platform-channel-handle=2932 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fdea9d0,0x6fdea9e0,0x6fdea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17791960364954521719 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3090265067538304202 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1536273739106879700 --renderer-client-id=53 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2396 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3574355998853788573,11180175248895247365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5520984692906052604 --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
986
Read events
872
Write events
110
Delete events
4
Modification events
| (PID) Process: | (3512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3512-13210936537630875 |
Value: 259 | |||
| (PID) Process: | (3512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3512) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
5
Suspicious files
326
Text files
298
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\467e78da-4c18-4849-ad48-fa54b7076990.tmp | — | |
MD5:— | SHA256:— | |||
| 3512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:C4D6CBB269C626168A5D6D0D8CCE6C30 | SHA256:B62CDBB758278A0C2E50593357390119441D8DE09428EB29027F3DFD1332E348 | |||
| 3512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169b79.TMP | text | |
MD5:DC32343F45B01764B6267AD36548102A | SHA256:A250F5AD57D4BD58AAE92810D50278E3BE2DBF869F126A3A3519691BCDFC2075 | |||
| 3512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:213AE3DA120D7862D60B5763B6C9D466 | SHA256:5736534D6EE654C1BF1A8E79E73330AF58F622E8657285330D2C7189A55604F4 | |||
| 3512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:911B244E4A362B56F2478647D2D61A40 | SHA256:3A5AEC1EA537D8841E604D0AA4CD5F9241C805A3D4EB4E372CFB7EEB3678A361 | |||
| 3512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:454106CCF080F3E3795C229FC73350D4 | SHA256:9974DC611BE9E20BDFA7B8D939CB913AD23859DEA5F52EBB8D10CEAD9AB5B4FA | |||
| 3512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169be7.TMP | text | |
MD5:A519780ED0A2F4336DB4F5651D79C369 | SHA256:DA5B71BD0075B55757BF757BF5F4D4A1DCBCF0762CDA5B31B28680963E068C75 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
144
DNS requests
80
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
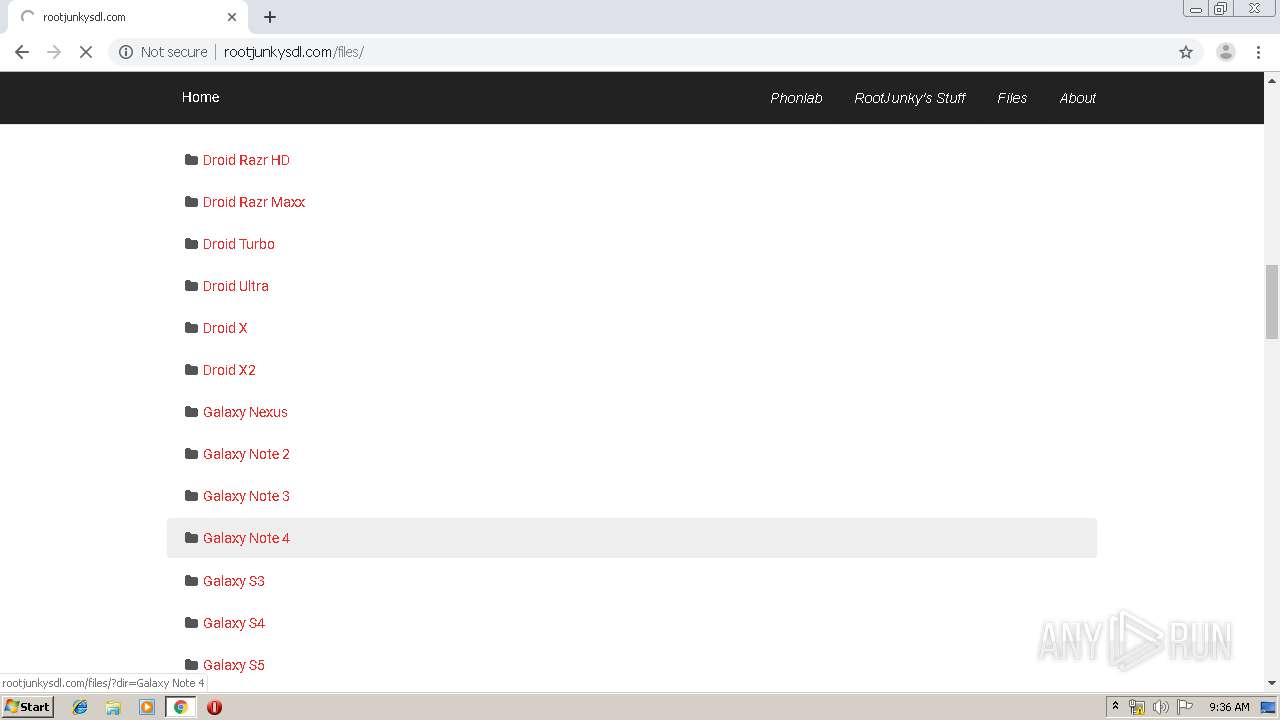
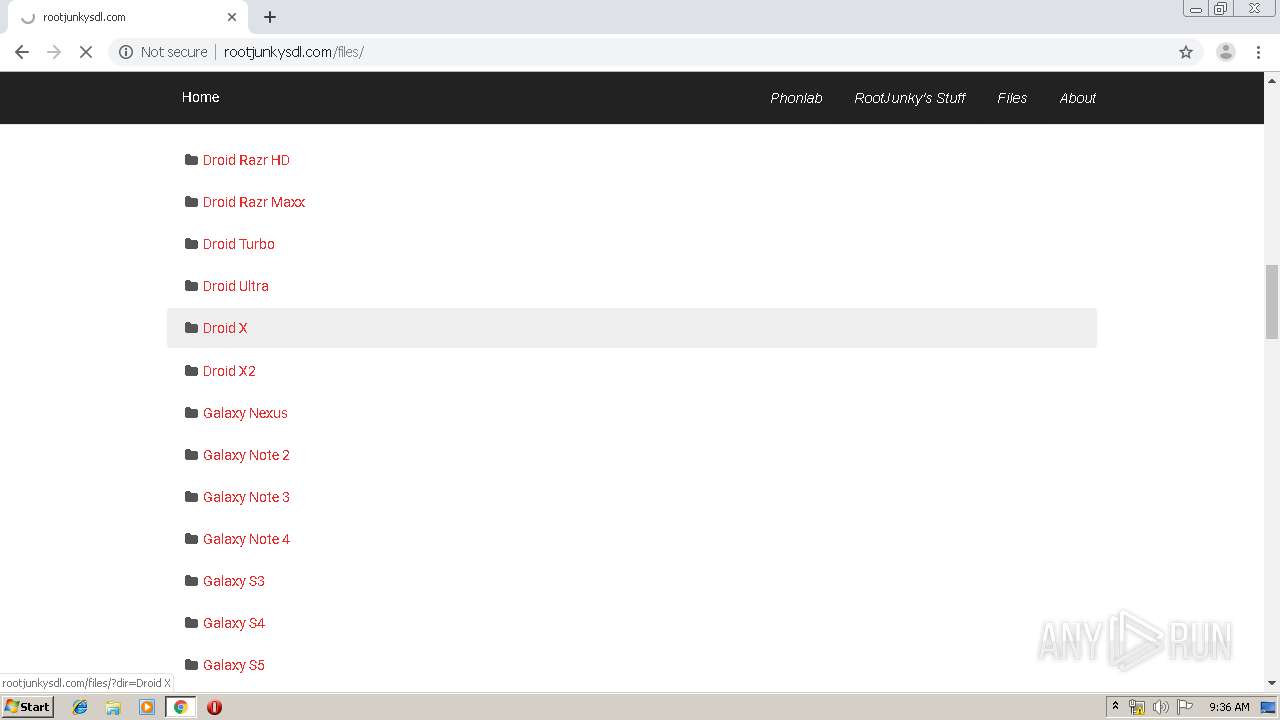
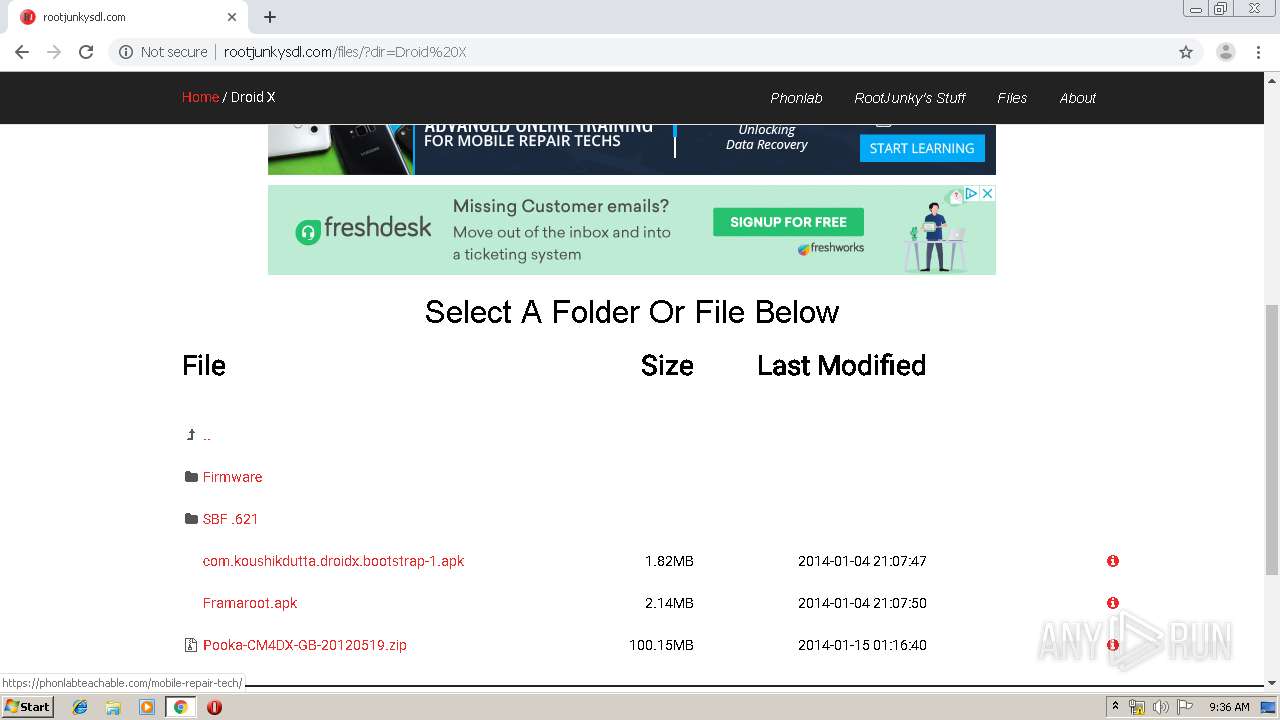
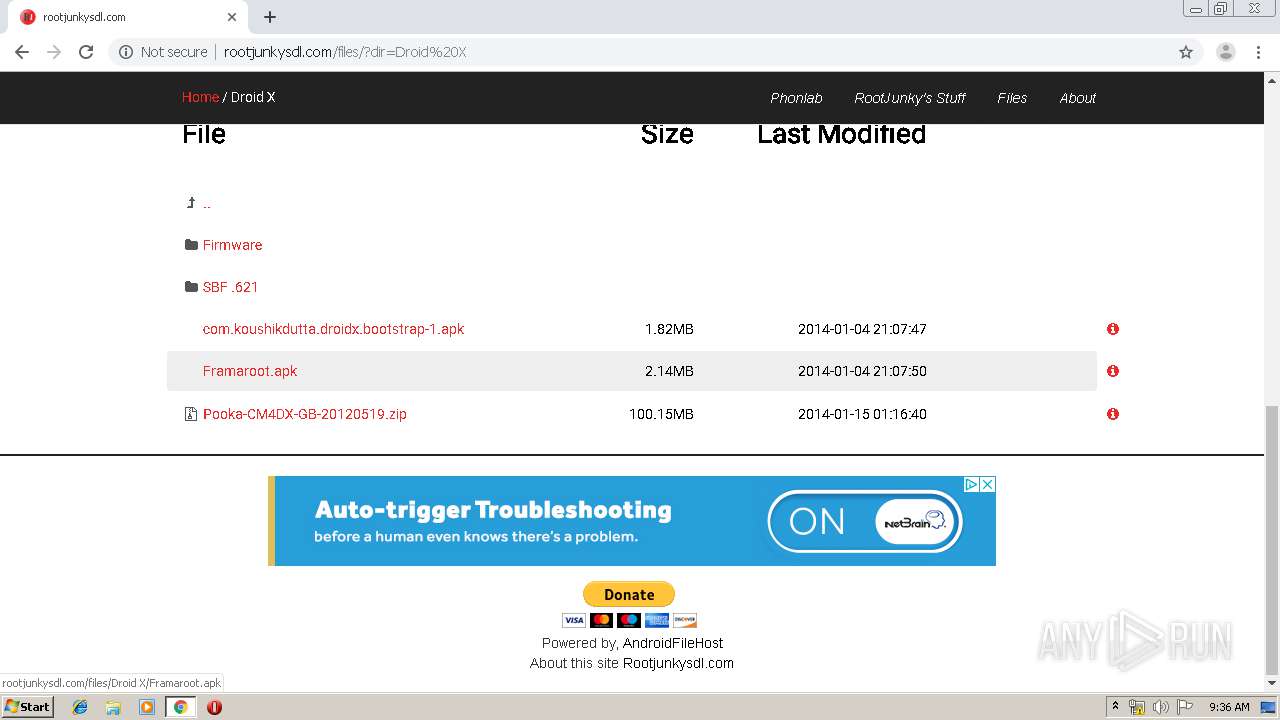
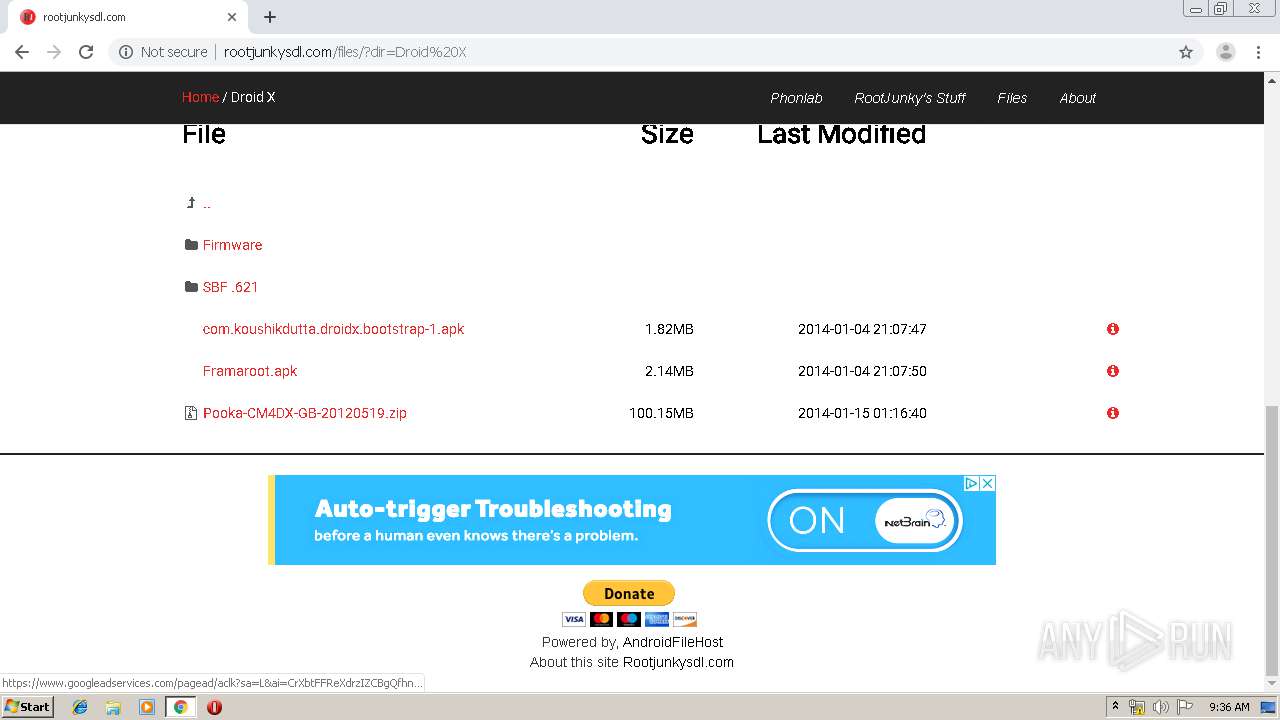
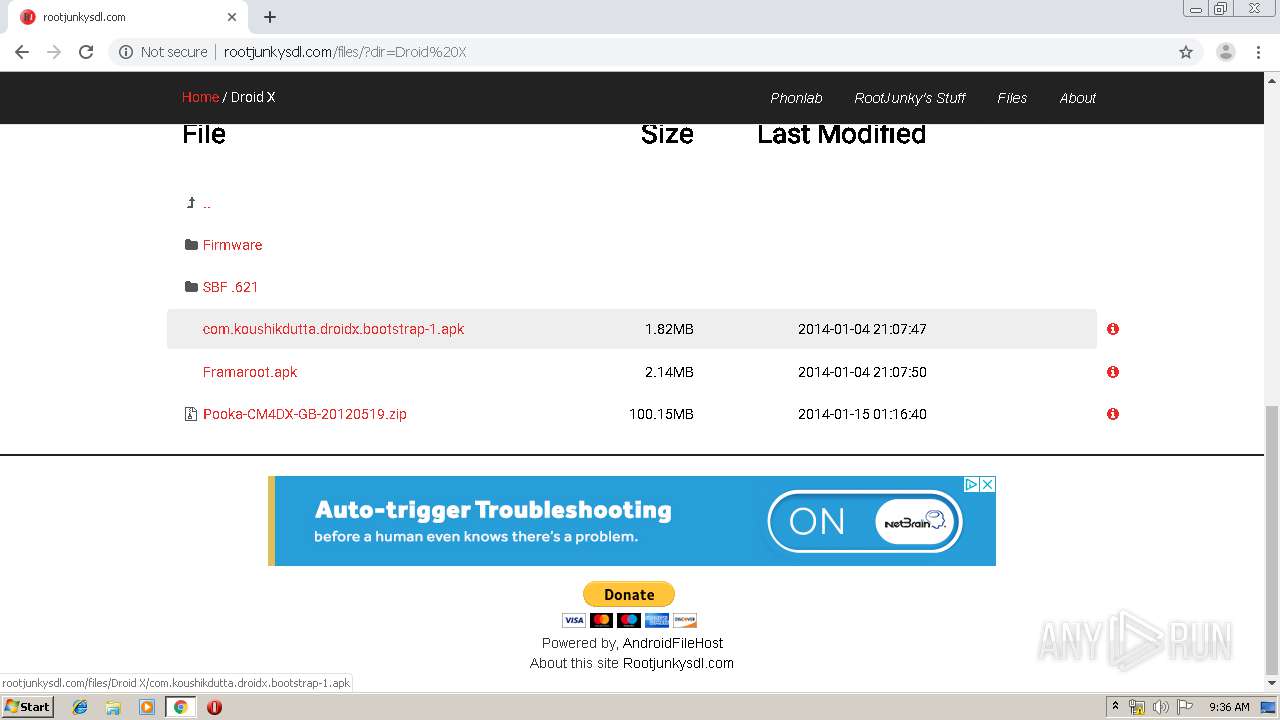
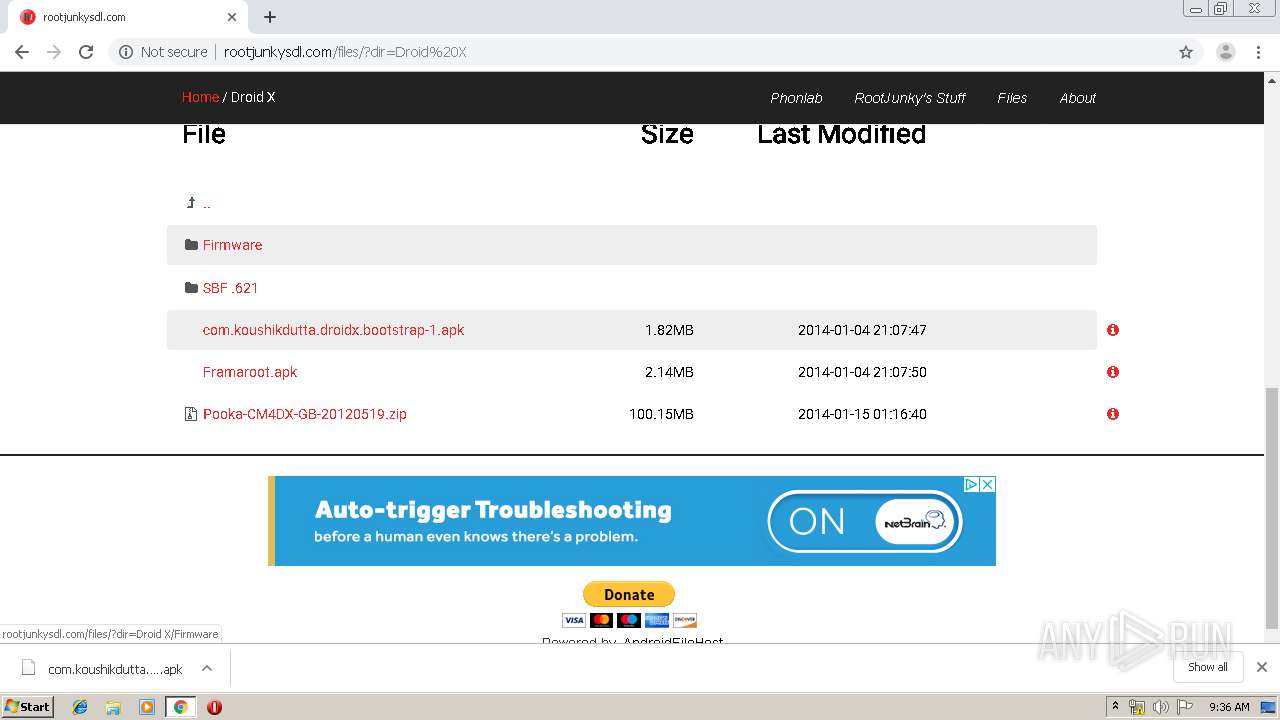
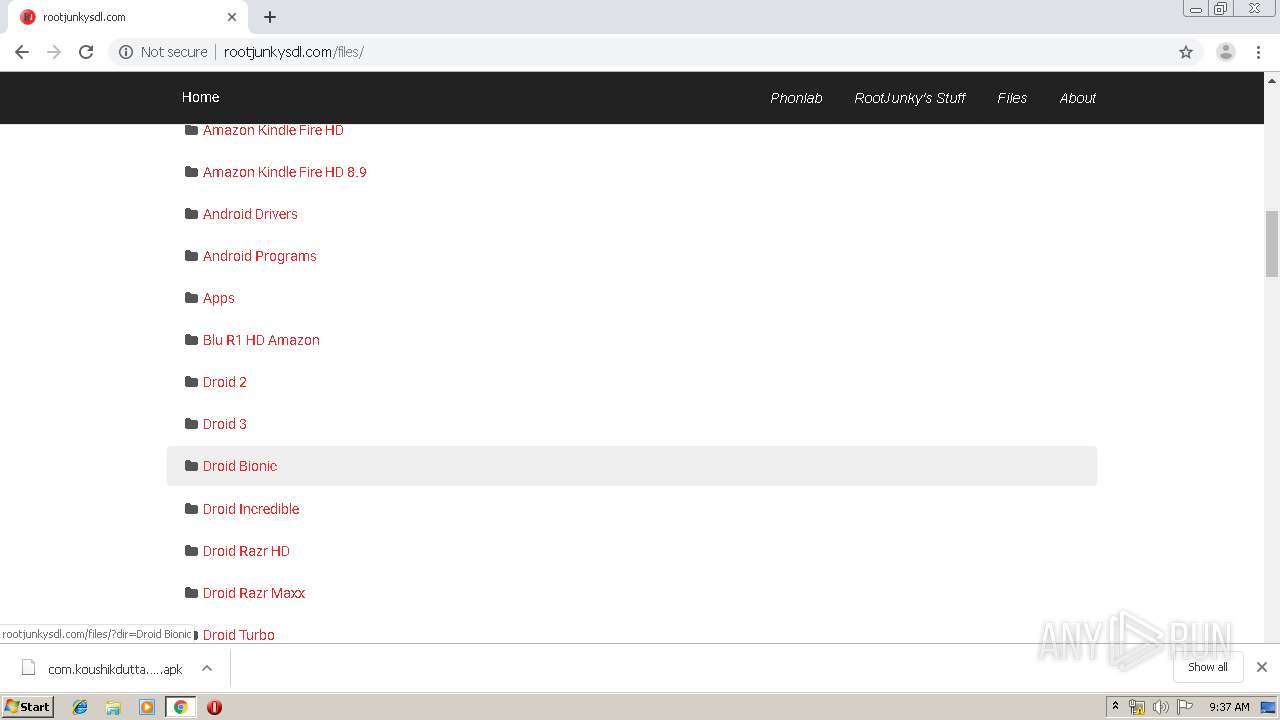
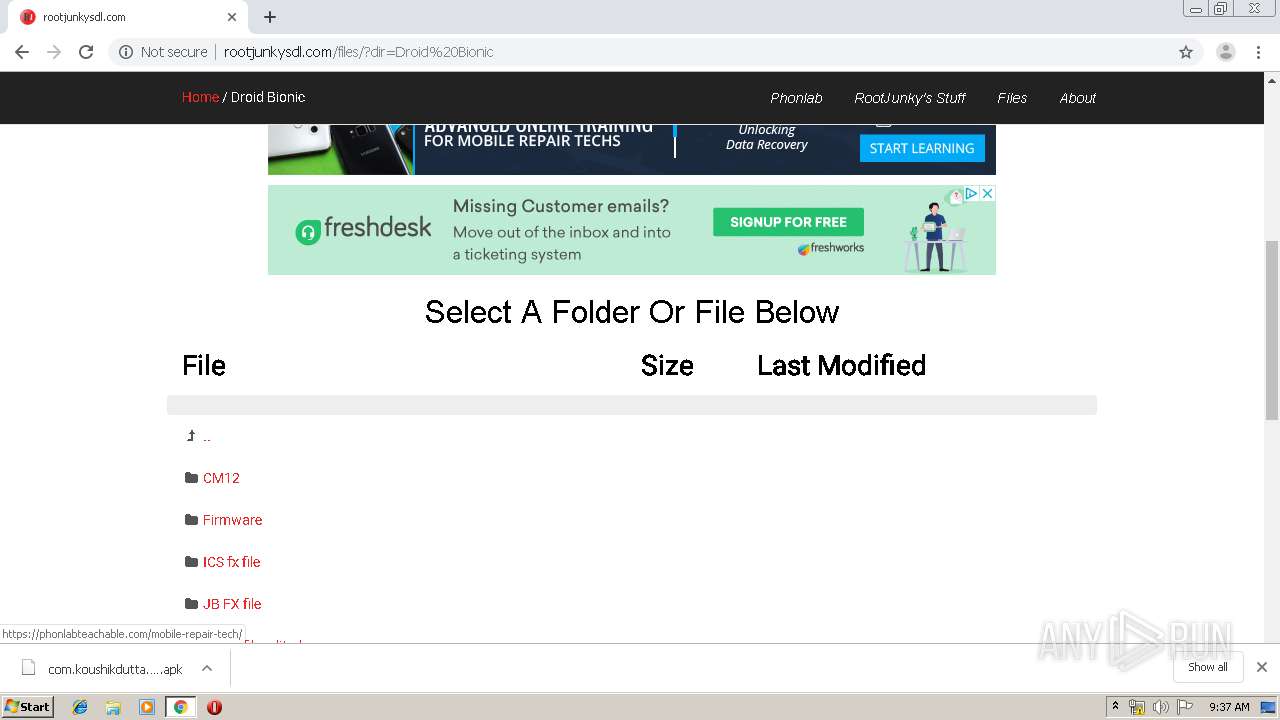
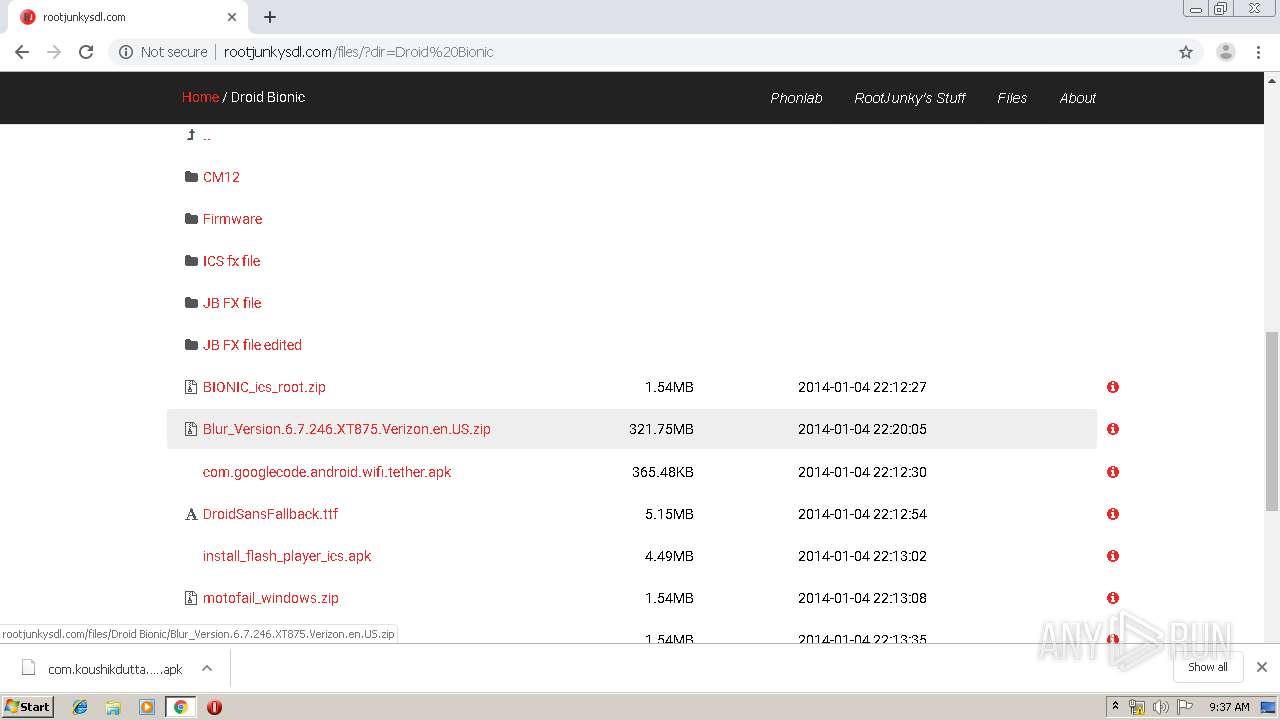
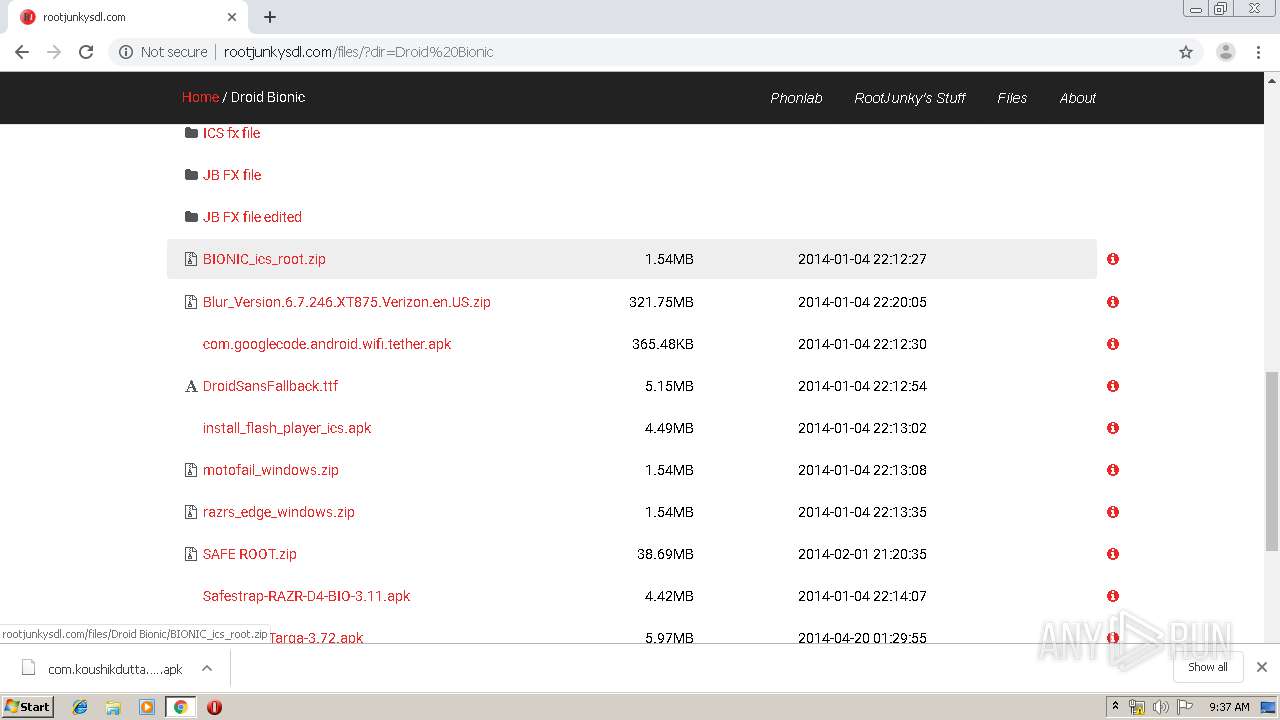
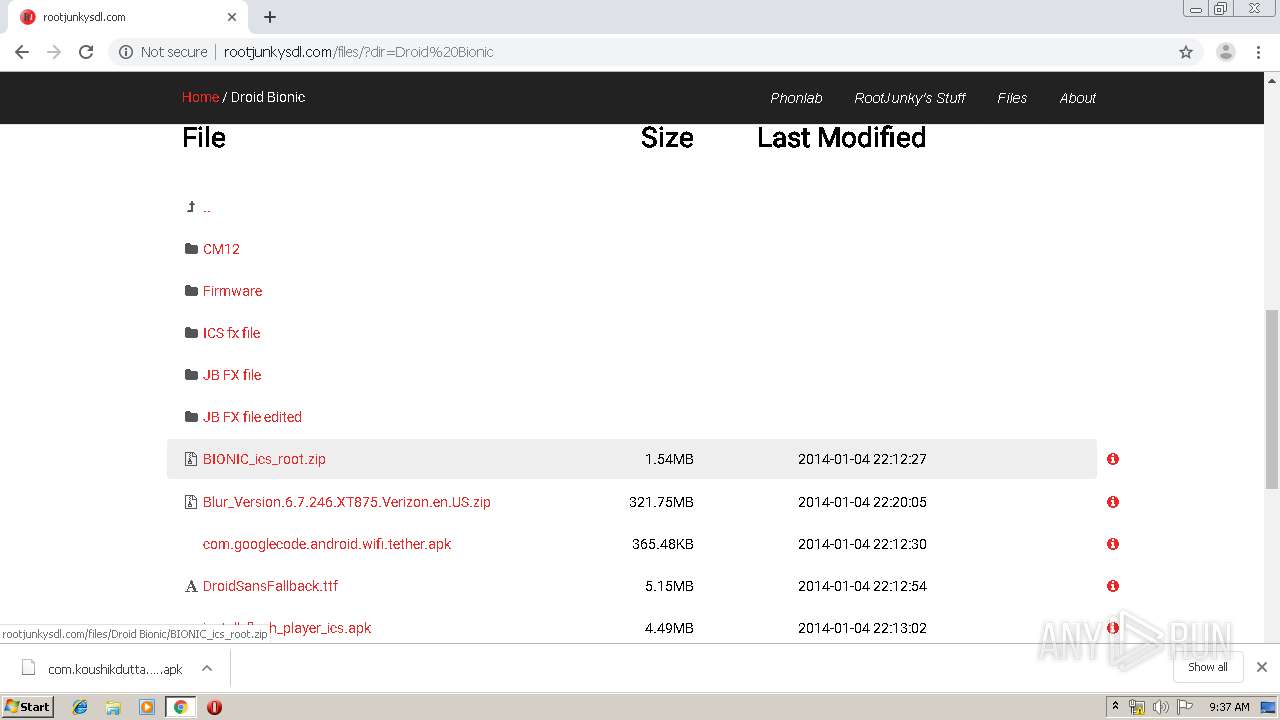
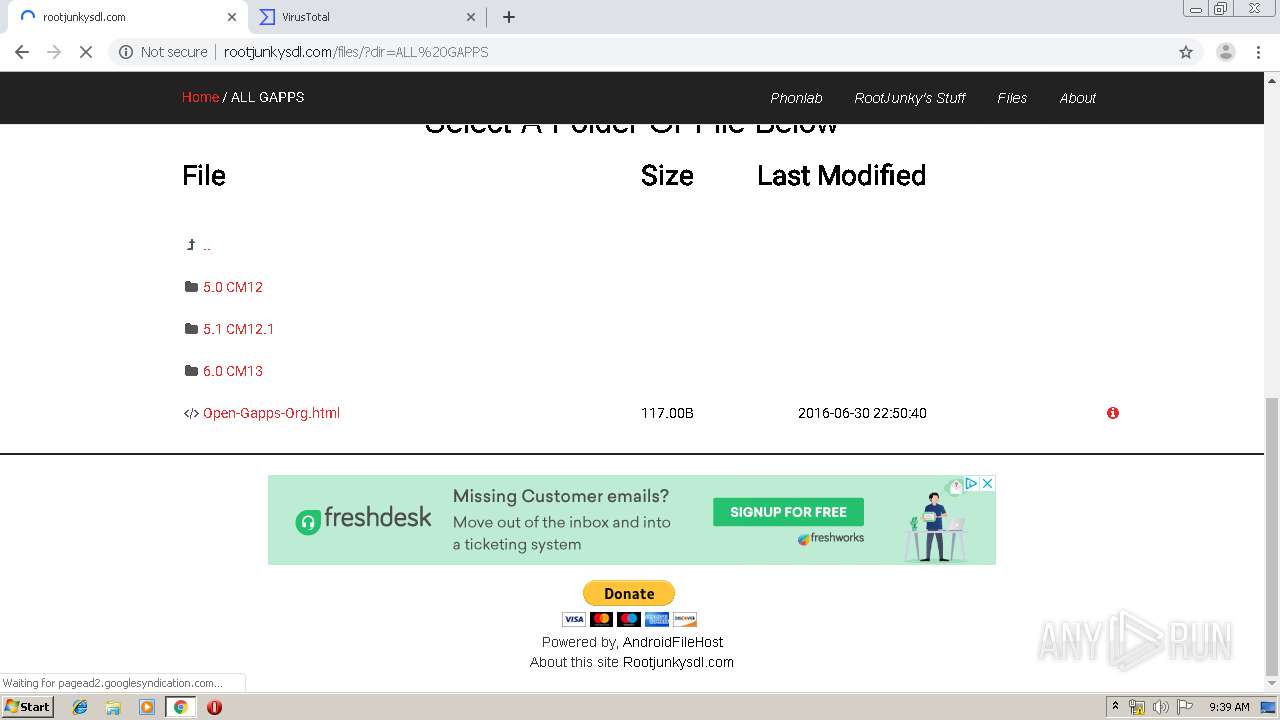
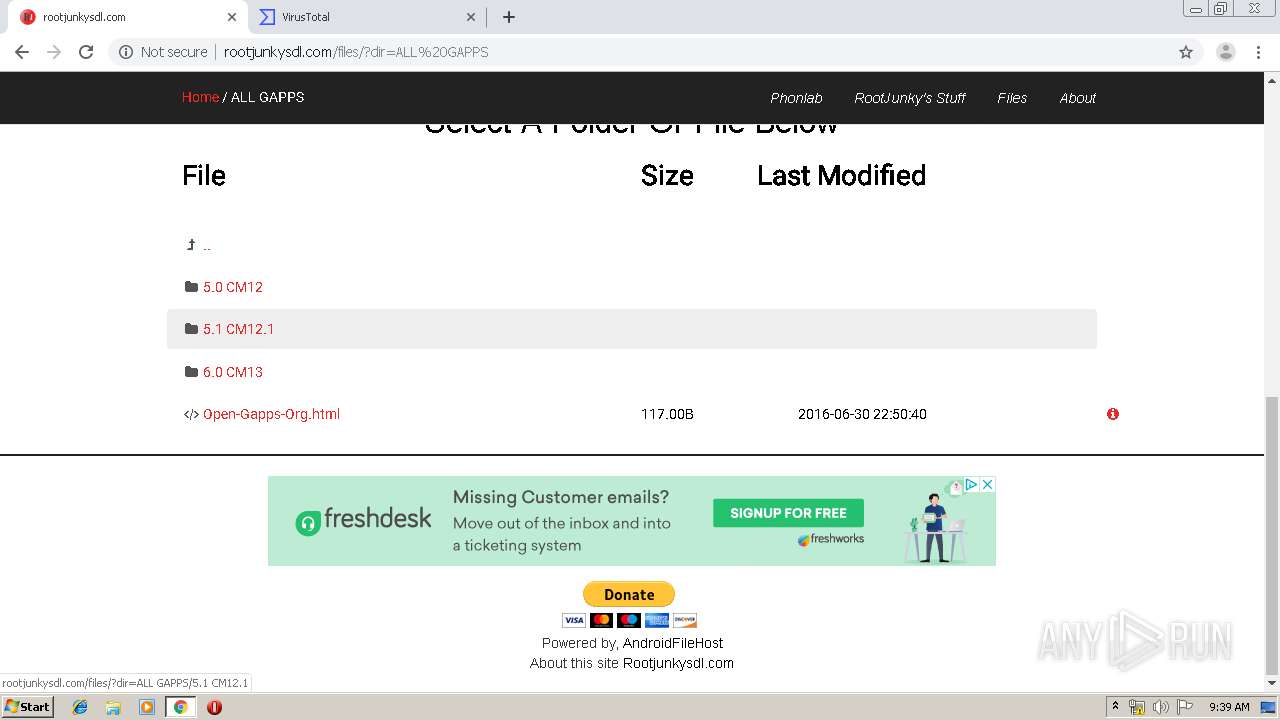
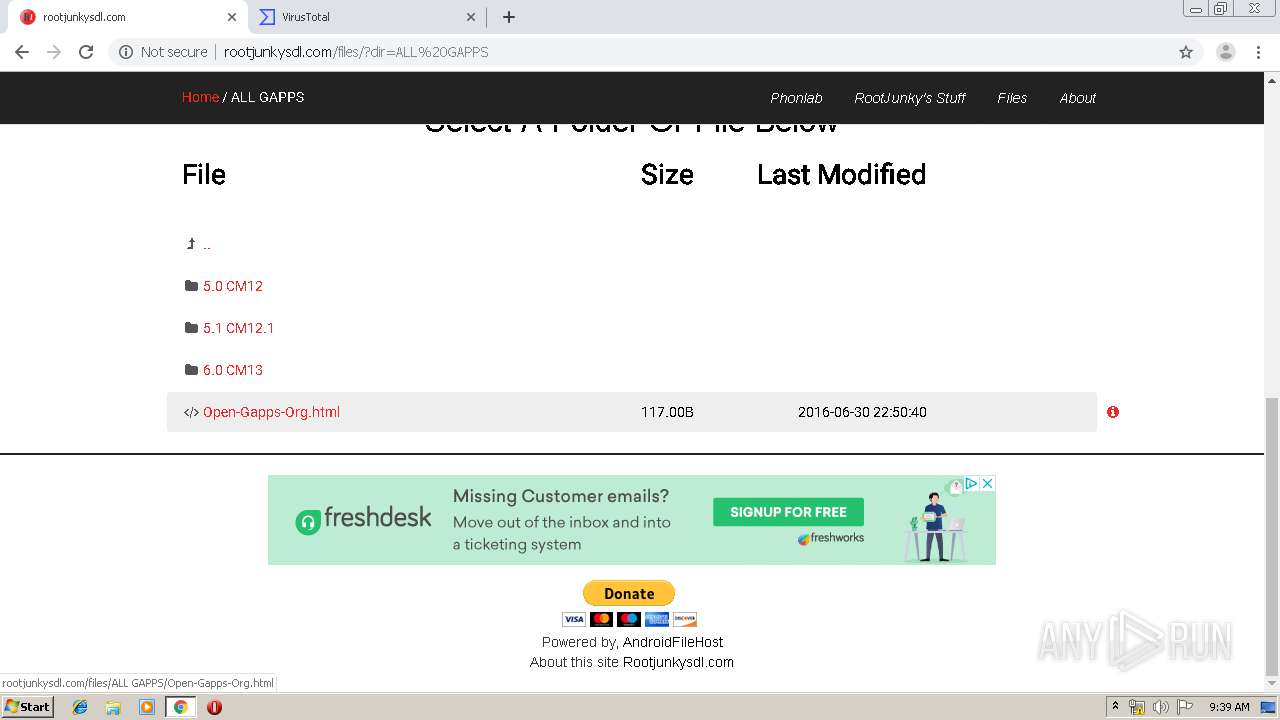
2828 | chrome.exe | GET | — | 149.56.164.13:80 | http://www.rootjunkysdl.com/files/resources/themes/bootstrap/css/style.css | CA | — | — | whitelisted |
2828 | chrome.exe | GET | 200 | 209.197.3.15:80 | http://maxcdn.bootstrapcdn.com/font-awesome/4.3.0/css/font-awesome.min.css | US | text | 5.31 Kb | whitelisted |
2828 | chrome.exe | GET | 200 | 216.58.207.74:80 | http://fonts.googleapis.com/css?family=Roboto | US | text | 510 b | whitelisted |
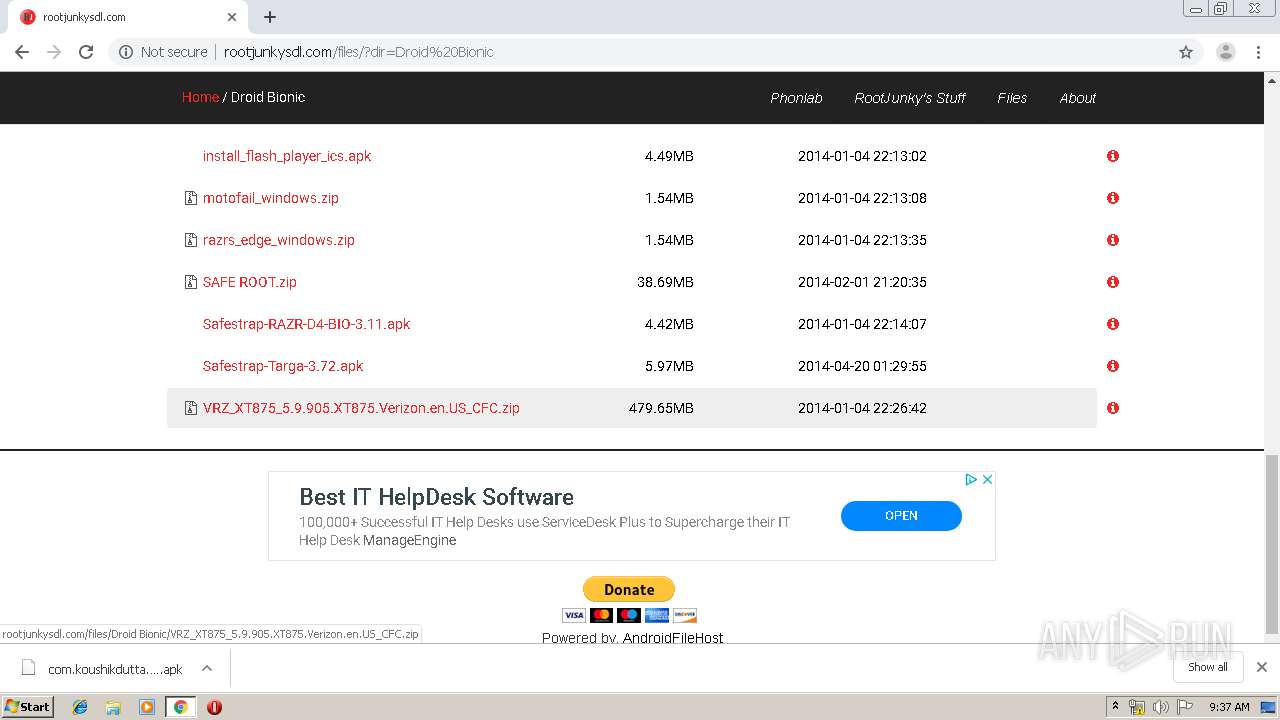
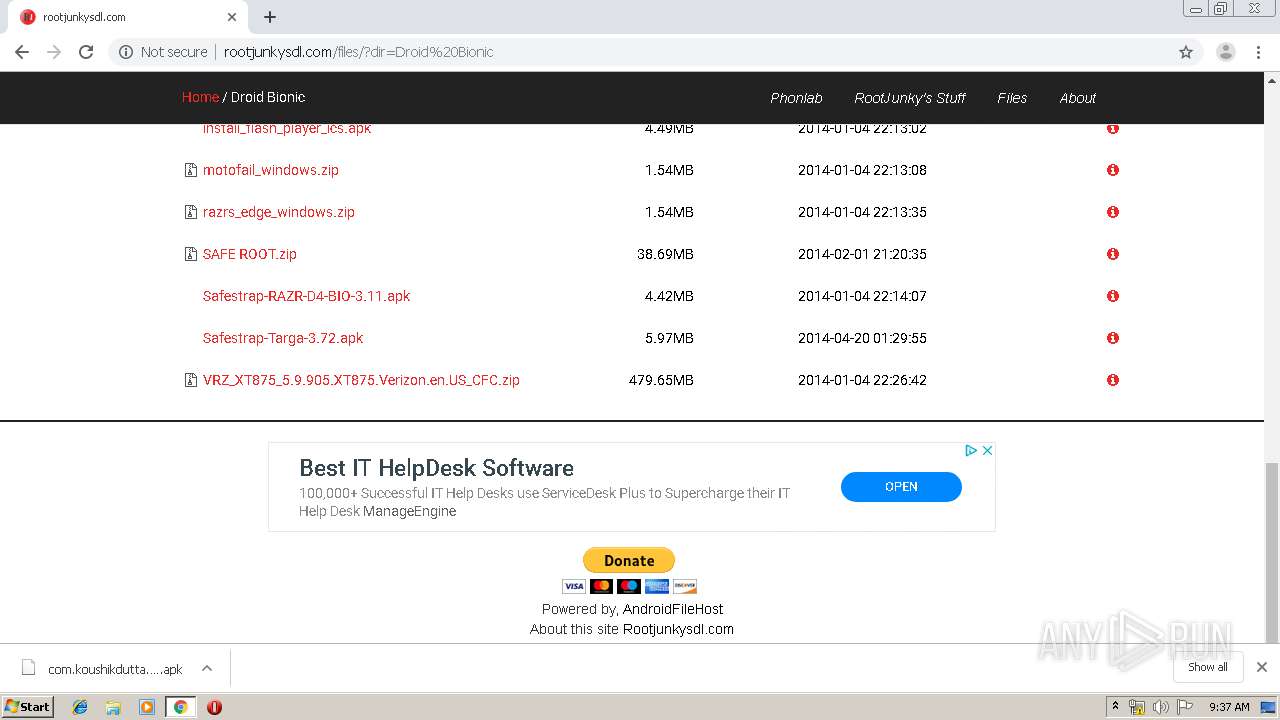
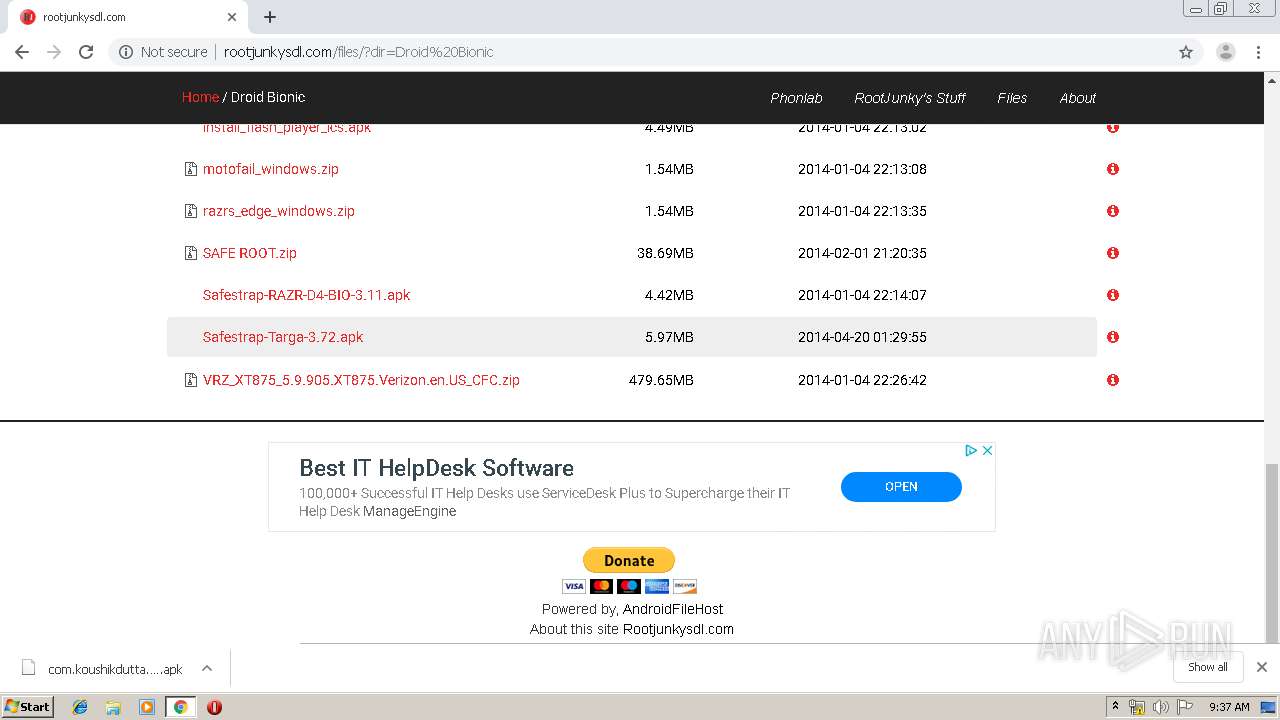
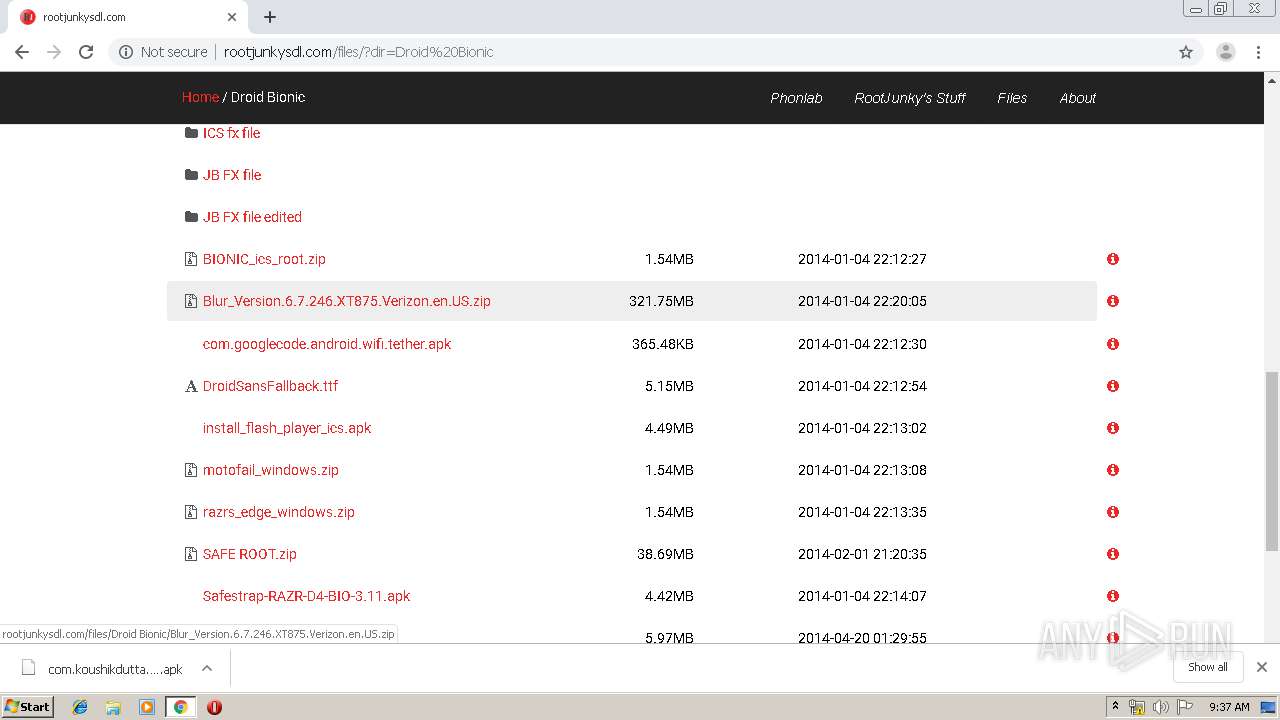
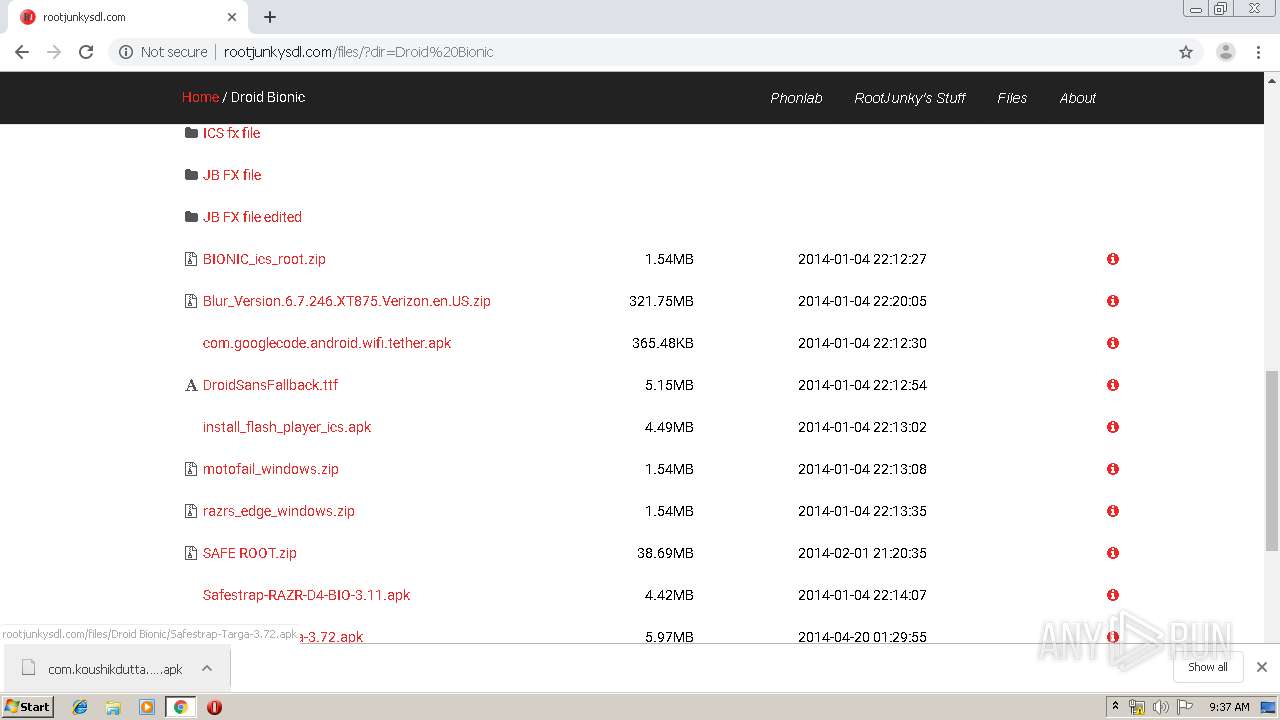
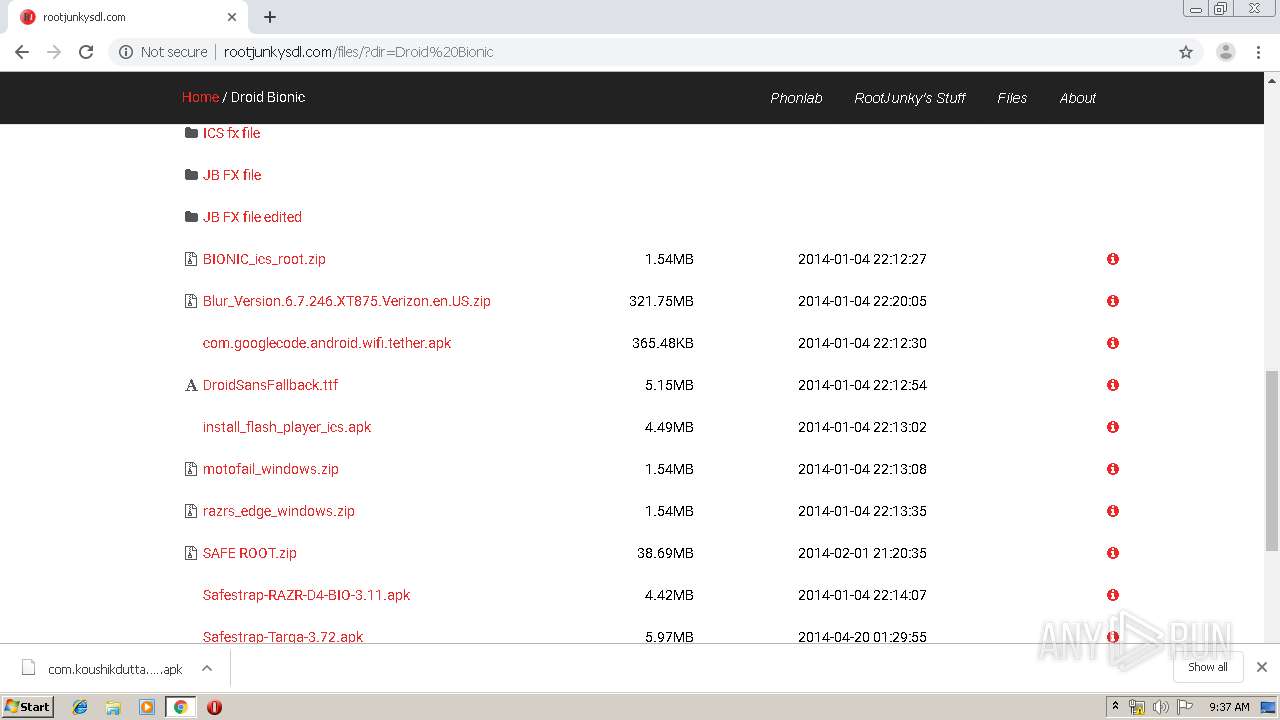
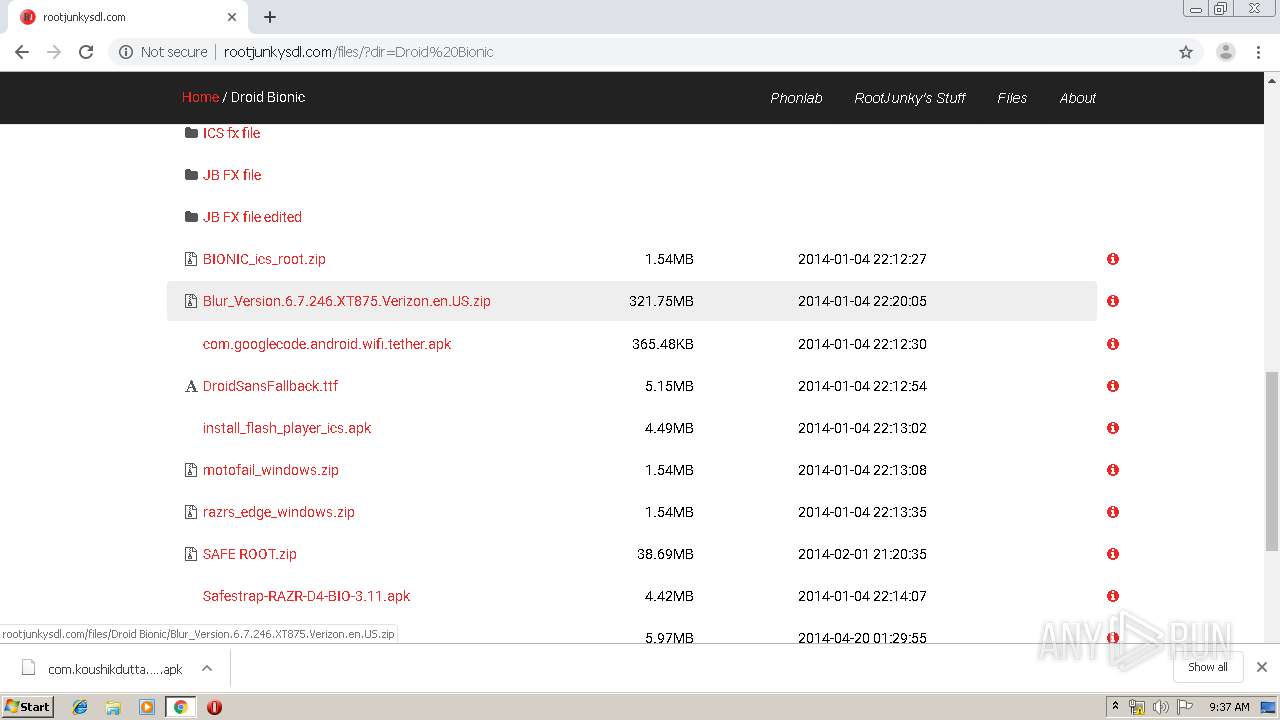
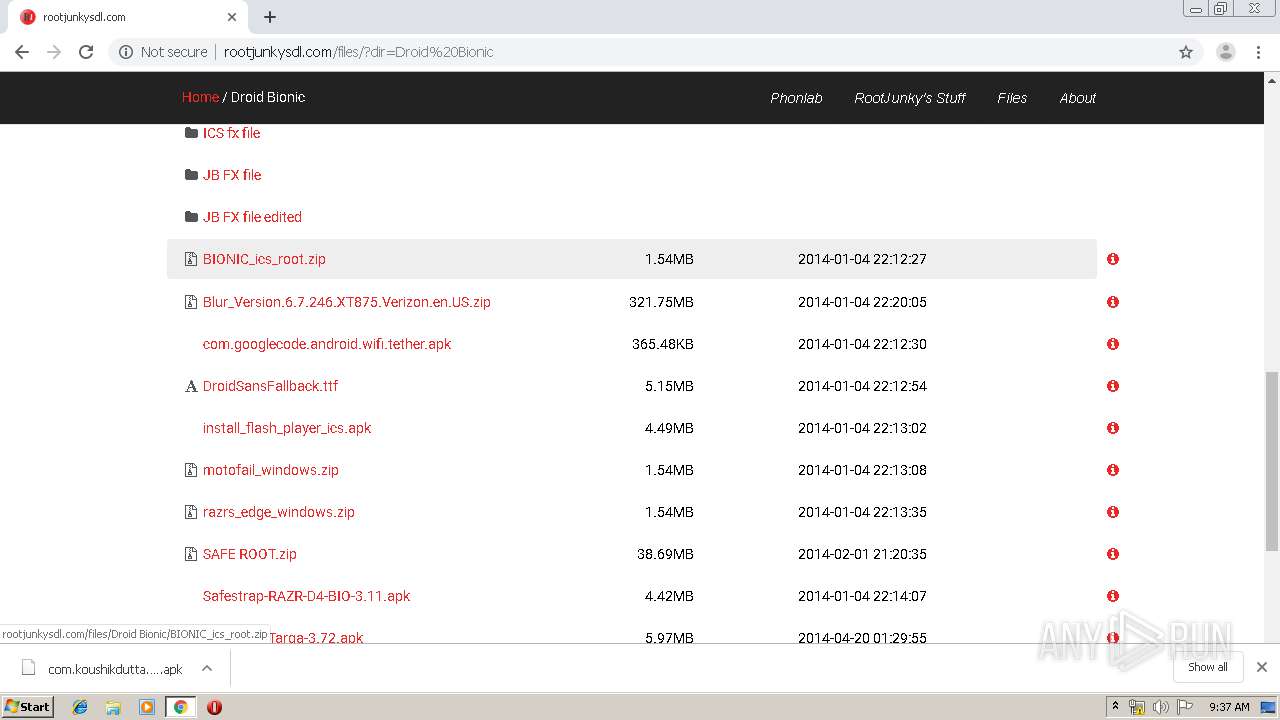
2828 | chrome.exe | GET | 302 | 149.56.164.13:80 | http://rootjunkysdl.com/files/Apps/FRP/Samsung/samsung%20bypass%20google%20verify.apk | CA | html | 218 b | whitelisted |
2828 | chrome.exe | GET | 200 | 216.58.207.74:80 | http://fonts.googleapis.com/css?family=Cutive+Mono | US | text | 369 b | whitelisted |
2828 | chrome.exe | GET | 200 | 209.197.3.15:80 | http://maxcdn.bootstrapcdn.com/bootstrap/3.3.4/js/bootstrap.min.js | US | text | 9.31 Kb | whitelisted |
2828 | chrome.exe | GET | 200 | 149.56.164.13:80 | http://www.rootjunkysdl.com/files/resources/themes/bootstrap/js/directorylister.js | CA | text | 1.77 Kb | whitelisted |
2828 | chrome.exe | GET | 200 | 216.58.207.66:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 34.1 Kb | whitelisted |
2828 | chrome.exe | GET | 200 | 149.56.164.13:80 | http://www.rootjunkysdl.com/files/resources/themes/bootstrap/img/728x90.png | CA | image | 63.4 Kb | whitelisted |
2828 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertTransitionRSARoot.crl | US | der | 521 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2828 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
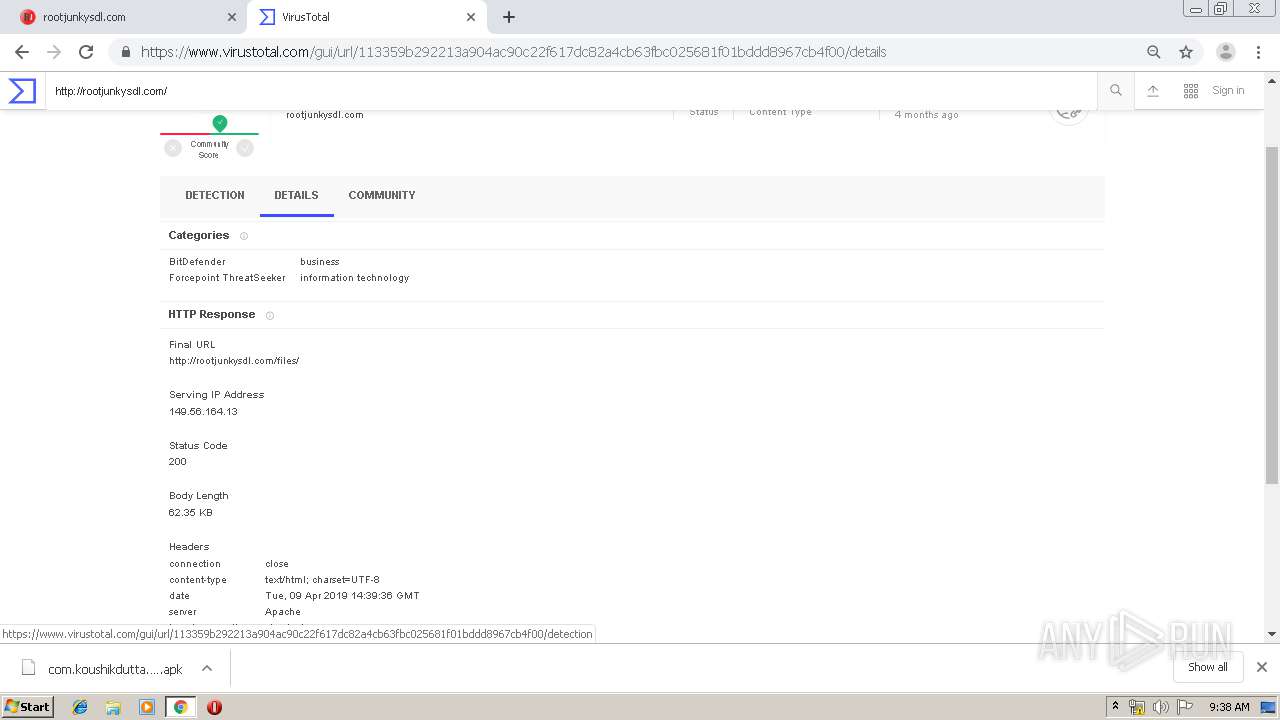
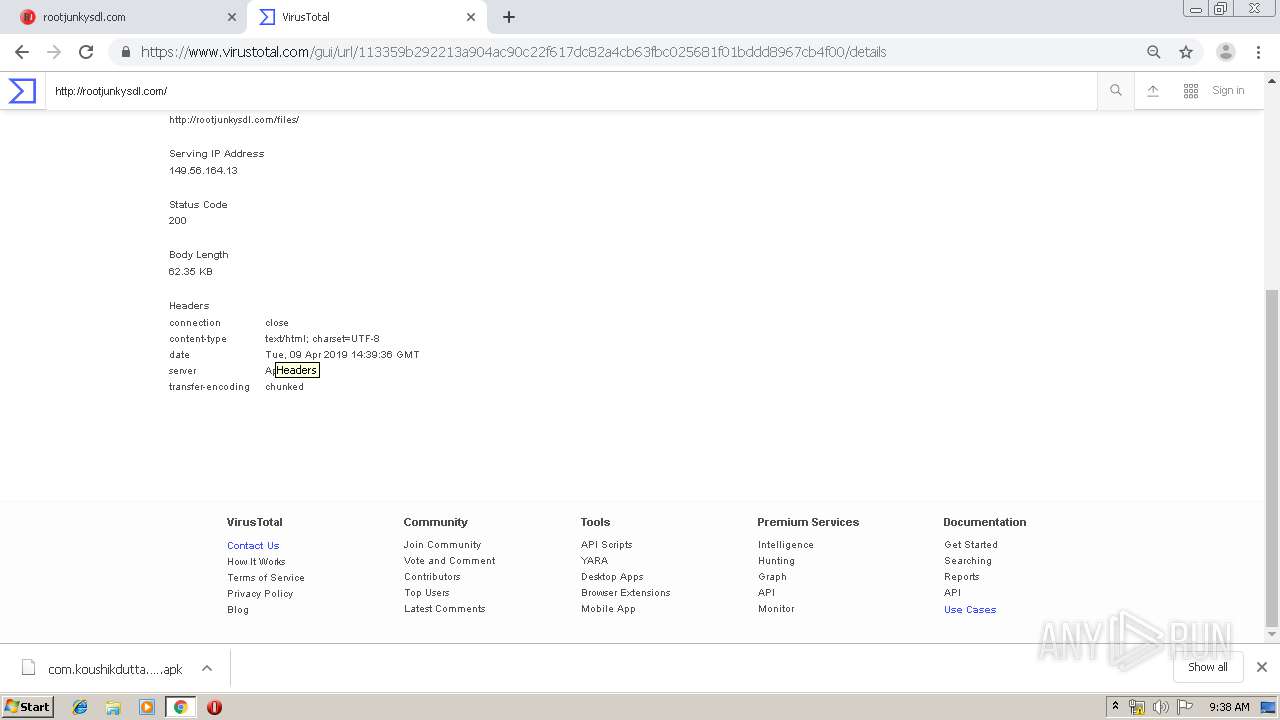
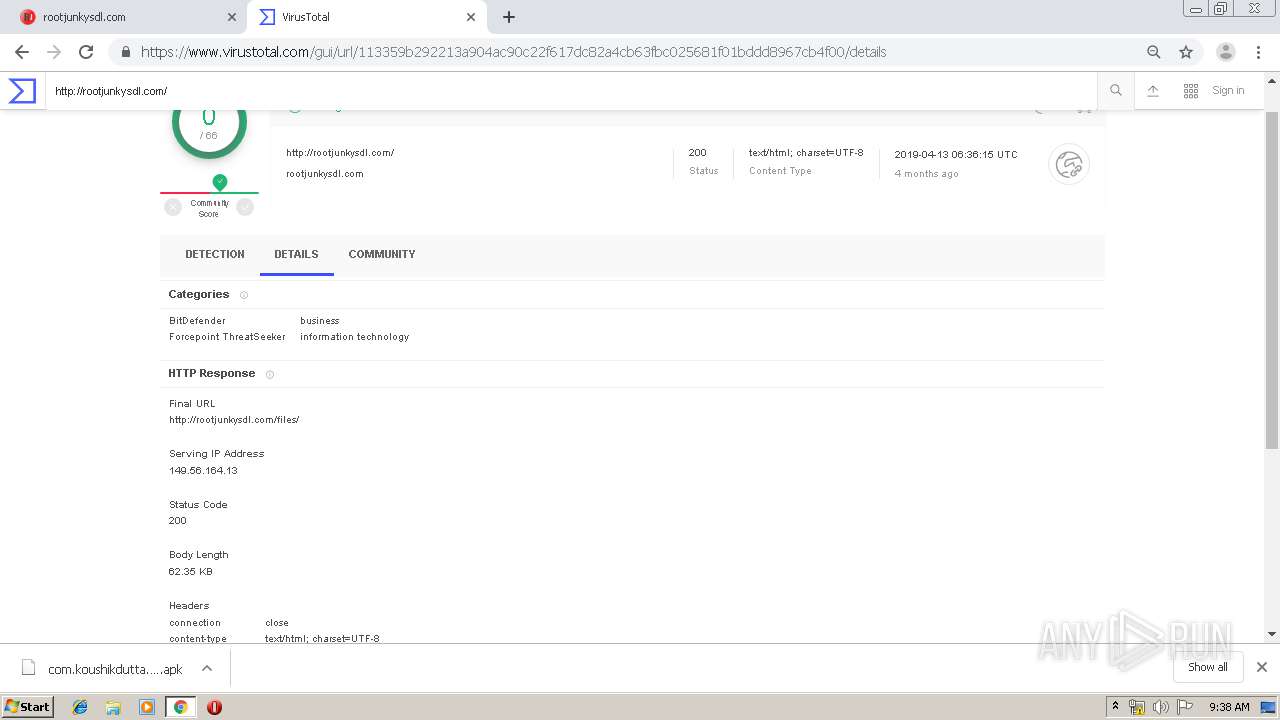
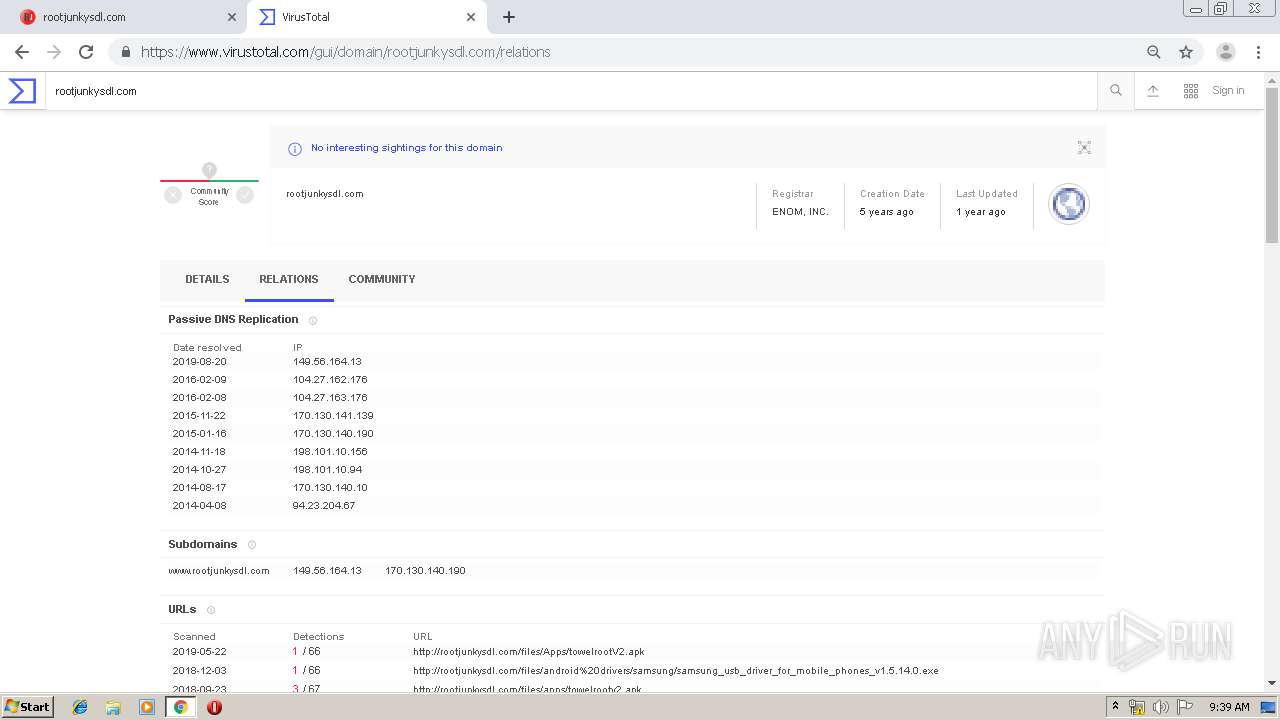
2828 | chrome.exe | 149.56.164.13:80 | rootjunkysdl.com | OVH SAS | CA | unknown |
2828 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2828 | chrome.exe | 209.197.3.15:80 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2828 | chrome.exe | 216.58.207.74:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2828 | chrome.exe | 172.217.21.238:443 | apis.google.com | Google Inc. | US | whitelisted |
2828 | chrome.exe | 172.217.22.10:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2828 | chrome.exe | 172.217.22.35:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2828 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2828 | chrome.exe | 216.58.207.66:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
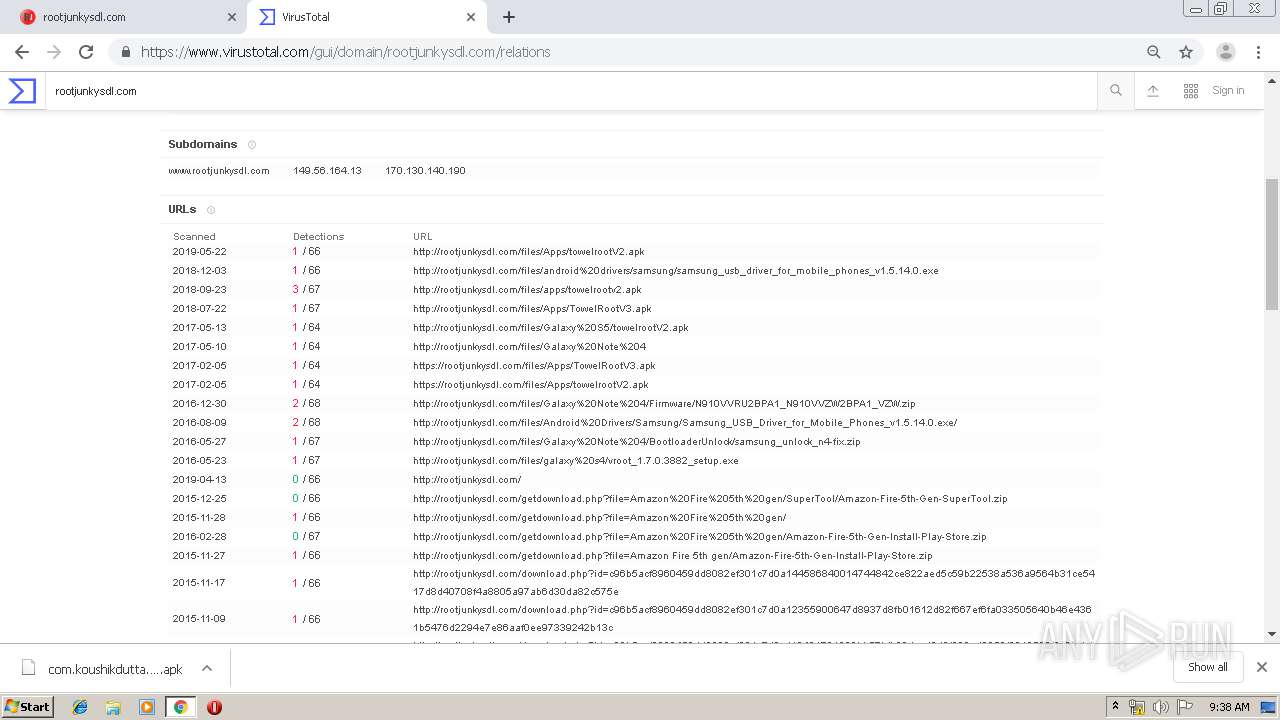
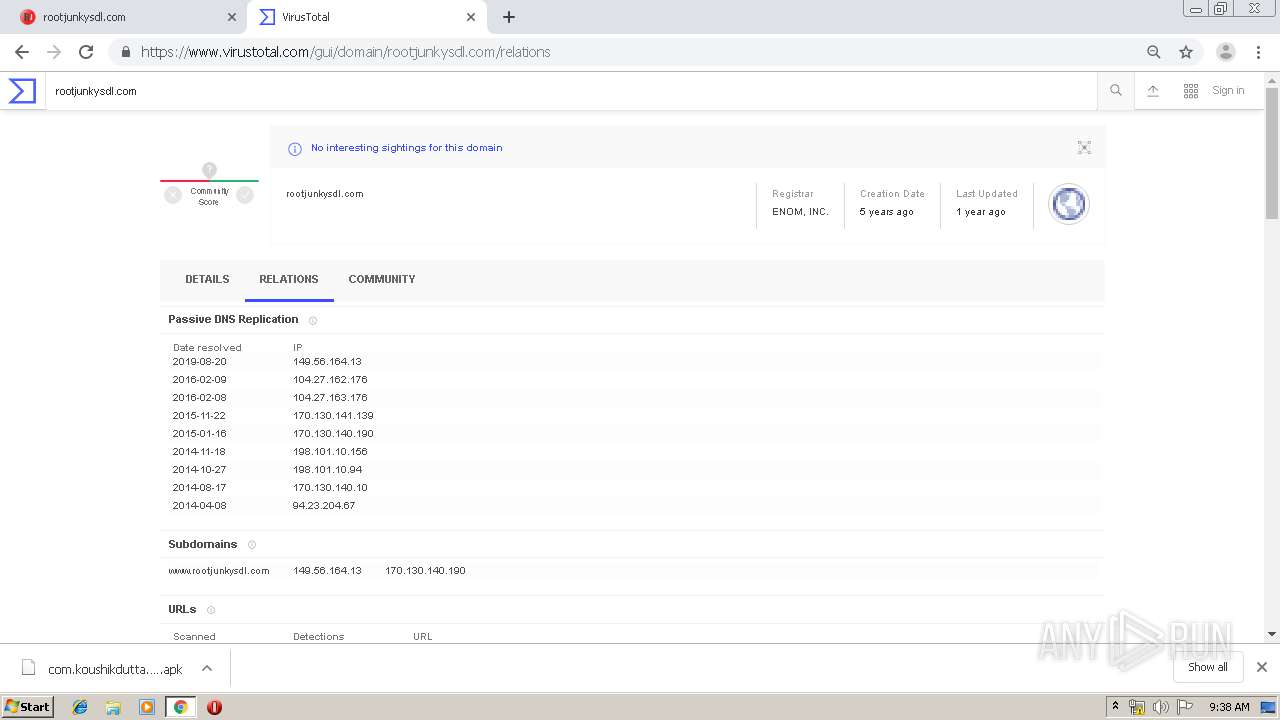
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
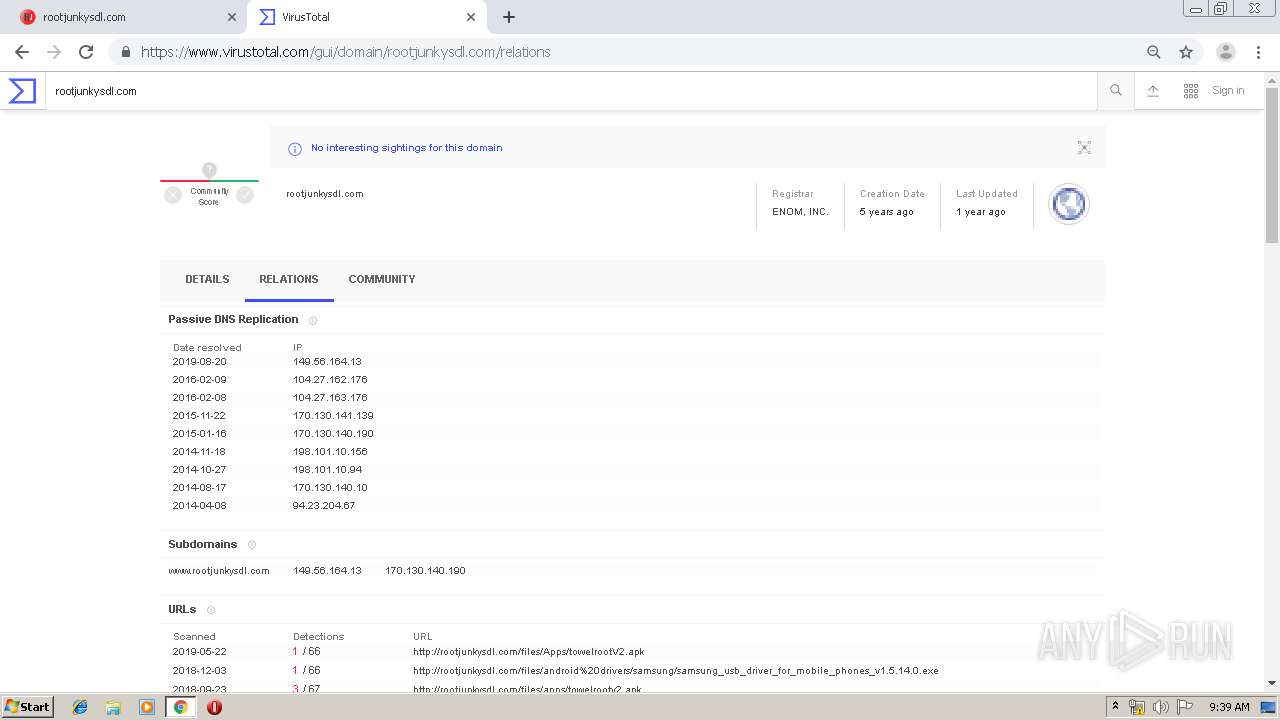
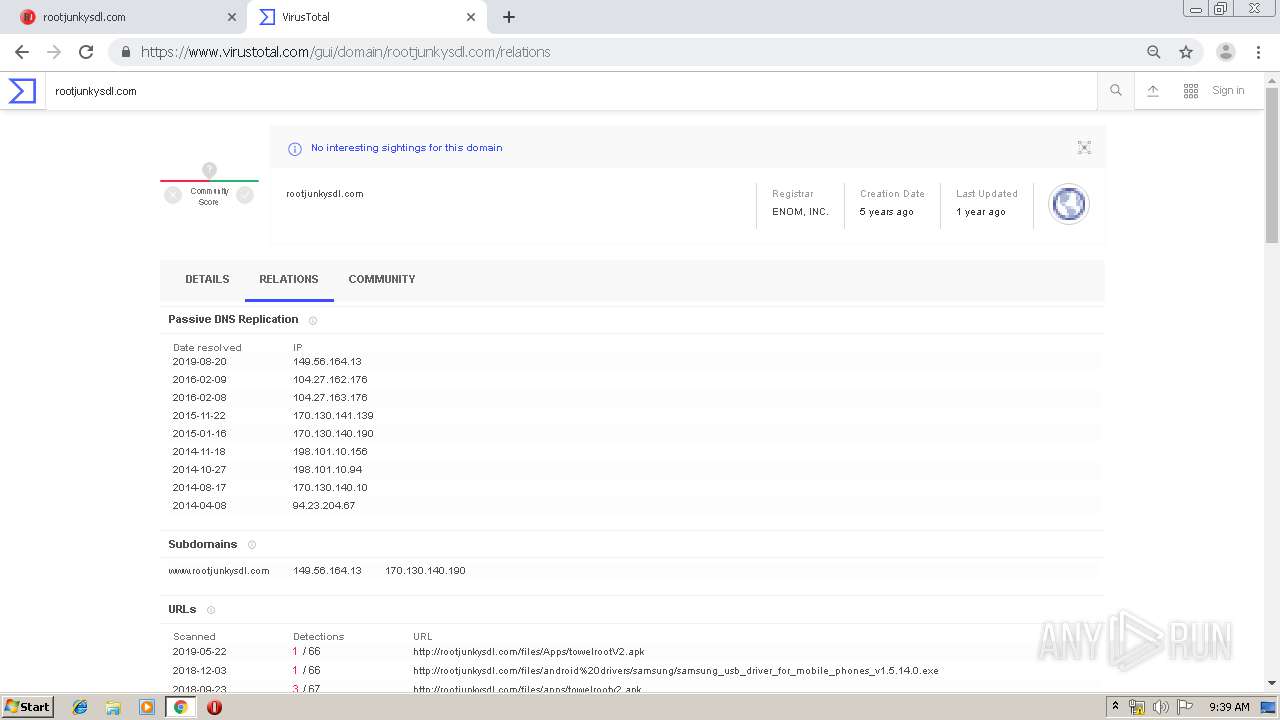
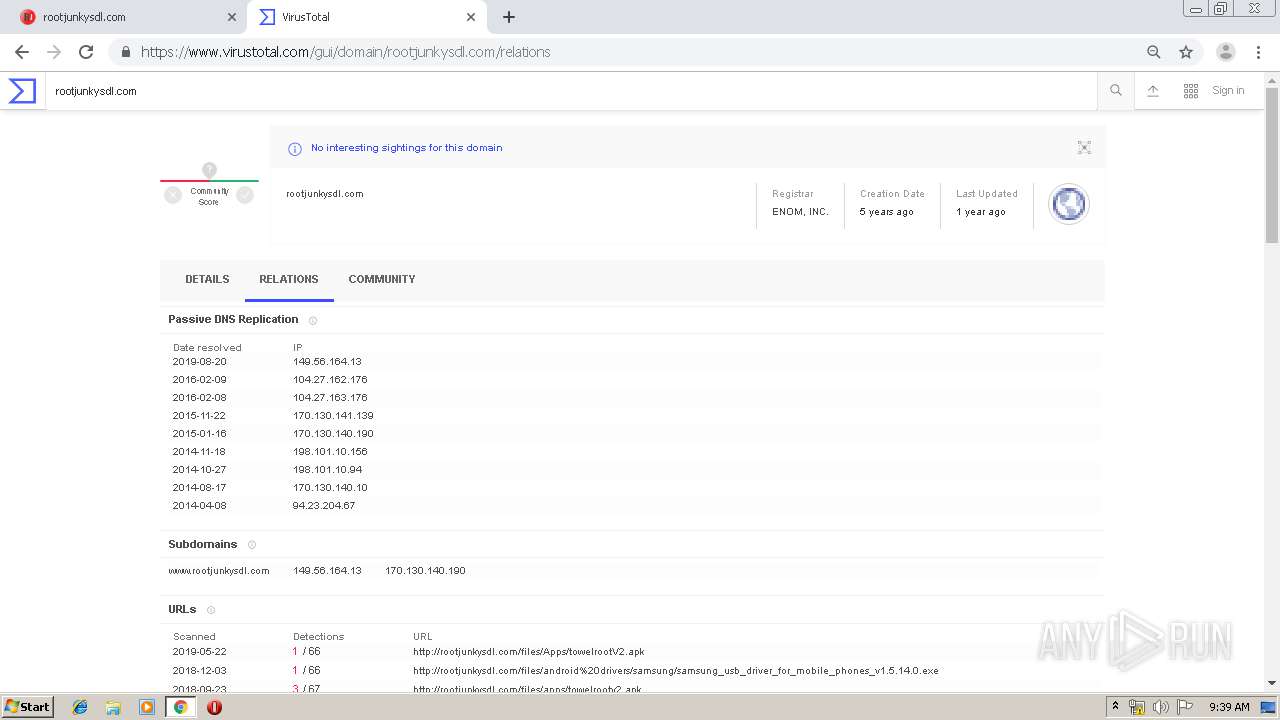
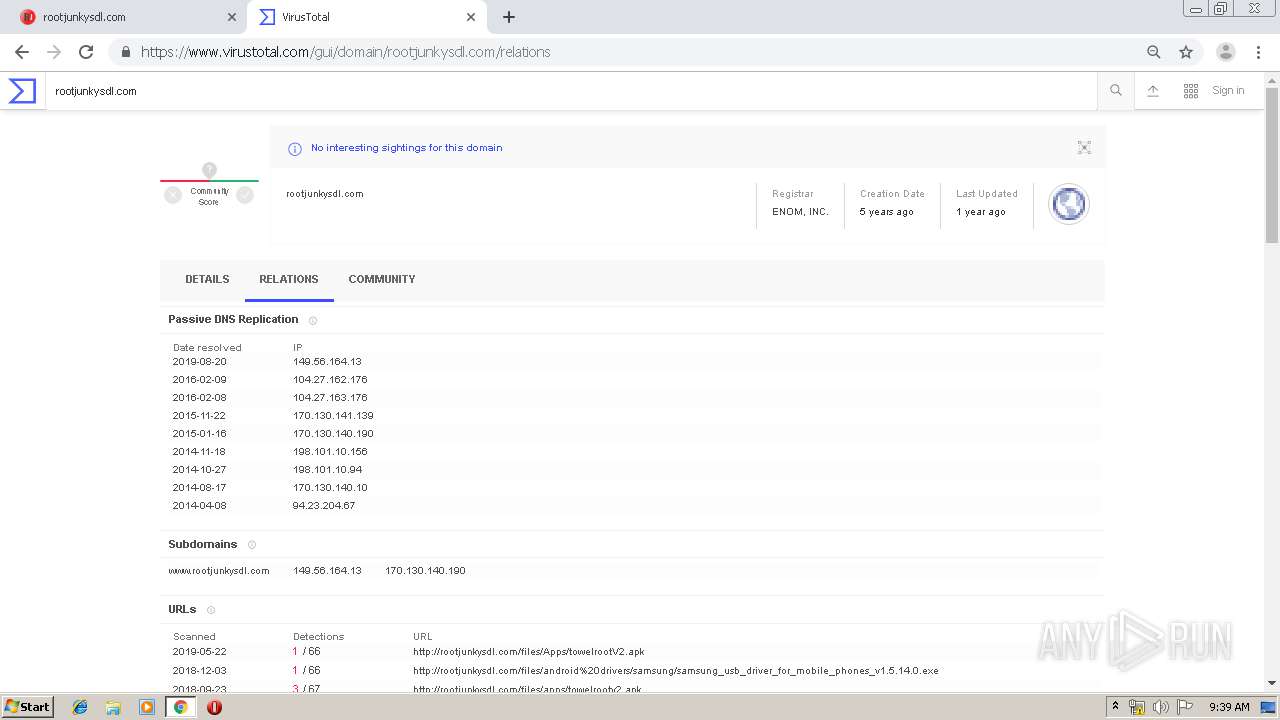
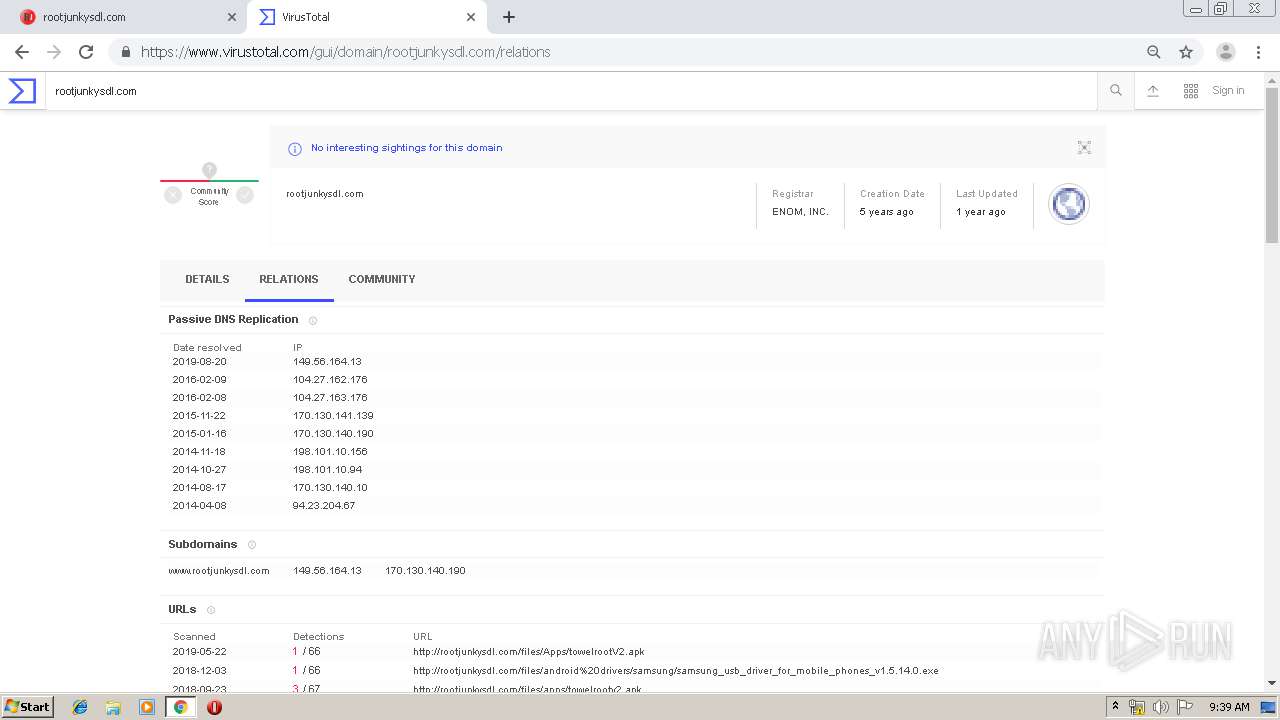
rootjunkysdl.com |
| whitelisted |
accounts.google.com |
| shared |
www.rootjunkysdl.com |
| unknown |
maxcdn.bootstrapcdn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |