| File name: | unsafe3 |
| Full analysis: | https://app.any.run/tasks/0a09690b-5efd-43d5-b60b-c3ca2a4e6f22 |
| Verdict: | Malicious activity |
| Analysis date: | October 08, 2018, 04:41:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 27601D095E5B3761D9289584415A73CC |
| SHA1: | 9570F23B5ABE2EF46A23DED17ADB2FB6C203A201 |
| SHA256: | 749F5E042B317DC4E989C174D92936EF83D9D4FBF4C190F0E5B759B858B15CF4 |
| SSDEEP: | 12288:REqmA0wfzInoQJUi1KHvQtzDNfo1arLaLRvs+Jkp/eH:RHmSyo+Ui13zZCI7+up/eH |
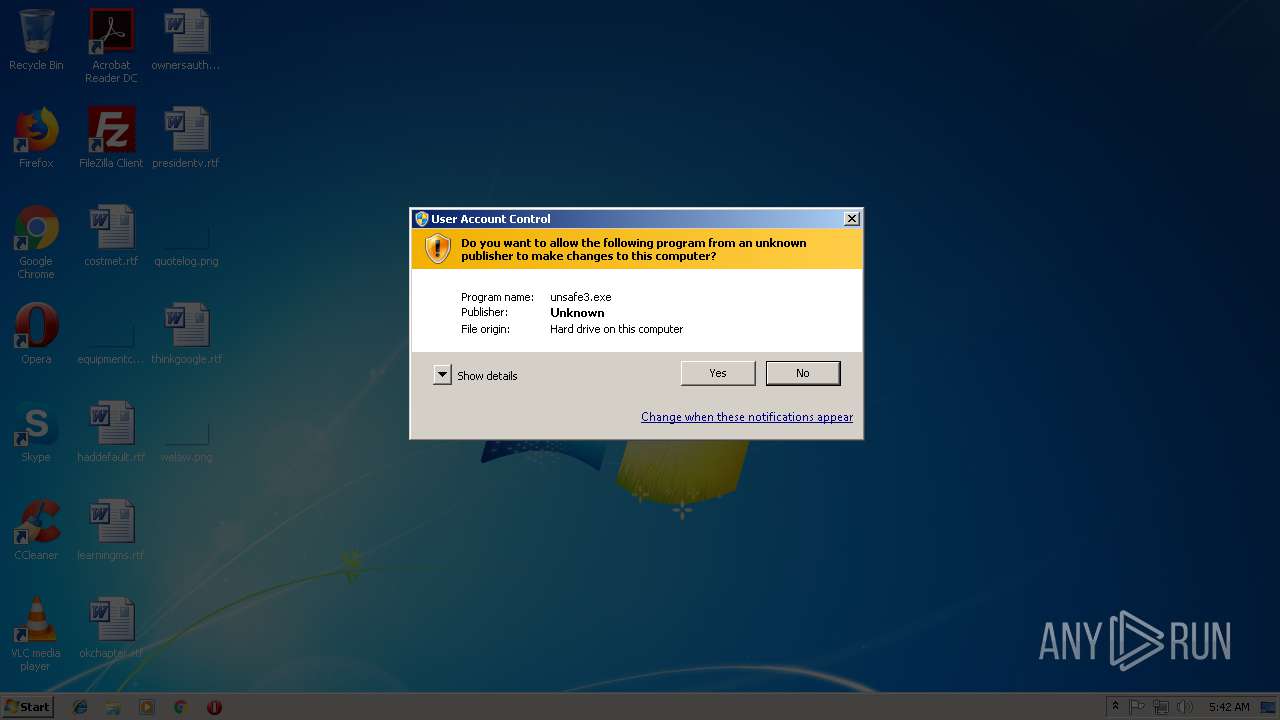
MALICIOUS
Application was dropped or rewritten from another process
- WombatStarter.exe (PID: 3704)
- HPWombatSrv.exe (PID: 3088)
- WombatStarter.exe (PID: 3844)
Loads dropped or rewritten executable
- unsafe3.exe (PID: 1840)
SUSPICIOUS
Executable content was dropped or overwritten
- unsafe3.exe (PID: 1840)
Creates files in the program directory
- unsafe3.exe (PID: 1840)
- HPWombatSrv.exe (PID: 3088)
Creates files in the user directory
- unsafe3.exe (PID: 1840)
- HPWombatSrv.exe (PID: 3088)
Creates a software uninstall entry
- unsafe3.exe (PID: 1840)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x39e3 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 41.457.890.11 |
| ProductVersionNumber: | 41.457.890.11 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Why did you come with the wintry air? |
| CompanyName: | When the faint note dies in the robin's throat |
| FileDescription: | What a strange, strange season to choose to come |
| FileVersion: | 41.457.890.11 |
| InternalName: | When the heavens are blind and the earth is dumb |
| LegalCopyright: | And the gables drip and the white flakes float? |
| ProductName: | Why did you come when the trees were bare? |
| ProductVersion: | 41.457.890.11 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:59 |
| Detected languages: |
|
| Comments: | Why did you come with the wintry air? |
| CompanyName: | When the faint note dies in the robin's throat |
| FileDescription: | What a strange, strange season to choose to come |
| FileVersion: | 41.457.890.11 |
| InternalName: | When the heavens are blind and the earth is dumb |
| LegalCopyright: | And the gables drip and the white flakes float? |
| ProductName: | Why did you come when the trees were bare? |
| ProductVersion: | 41.457.890.11 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006F10 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49788 |
.rdata | 0x00008000 | 0x00002A92 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39389 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47278 |
.ndata | 0x00073000 | 0x00081000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000F4000 | 0x00000F68 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.34039 |
.reloc | 0x000F5000 | 0x00000F8A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.18767 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21712 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
40
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1840 | "C:\Users\admin\AppData\Local\Temp\unsafe3.exe" | C:\Users\admin\AppData\Local\Temp\unsafe3.exe | explorer.exe | ||||||||||||
User: admin Company: When the faint note dies in the robin's throat Integrity Level: HIGH Description: What a strange, strange season to choose to come Exit code: 0 Version: 41.457.890.11 Modules
| |||||||||||||||
| 3088 | "C:\Program Files\HPWombat\HPWombatSrv.exe" | C:\Program Files\HPWombat\HPWombatSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: sijyanpoz ouhcequv Integrity Level: SYSTEM Description: akyite iihtahbeo Aroit POIWRIEHF Exit code: 0 Version: 7.13.107.2177 Modules
| |||||||||||||||
| 3144 | "C:\Users\admin\AppData\Local\Temp\unsafe3.exe" | C:\Users\admin\AppData\Local\Temp\unsafe3.exe | — | explorer.exe | |||||||||||
User: admin Company: When the faint note dies in the robin's throat Integrity Level: MEDIUM Description: What a strange, strange season to choose to come Exit code: 3221226540 Version: 41.457.890.11 Modules
| |||||||||||||||
| 3704 | "C:\Program Files\HPWombat\WombatStarter.exe" "write_patch_str_to_reg" "C:\Users\admin\AppData\Local\Temp\unsafe3.exe" "HKLM" Software\HPWombat "jeromu" | C:\Program Files\HPWombat\WombatStarter.exe | — | unsafe3.exe | |||||||||||
User: admin Company: Eoniijh Integrity Level: HIGH Description: Lremyyle Eemcimxeva Exit code: 0 Version: 10.4.9.22251 Modules
| |||||||||||||||
| 3844 | "C:\Program Files\HPWombat\WombatStarter.exe" "install_and_start_srv" "C:\Users\admin\AppData\Local\Temp\unsafe3.exe" | C:\Program Files\HPWombat\WombatStarter.exe | — | unsafe3.exe | |||||||||||
User: admin Company: Eoniijh Integrity Level: HIGH Description: Lremyyle Eemcimxeva Exit code: 0 Version: 10.4.9.22251 Modules
| |||||||||||||||
Total events
575
Read events
526
Write events
49
Delete events
0
Modification events
| (PID) Process: | (1840) unsafe3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\HPWombat\Components |
| Operation: | write | Name: | Main |
Value: 1 | |||
| (PID) Process: | (1840) unsafe3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HPWombat |
| Operation: | write | Name: | DisplayName |
Value: HPWombat | |||
| (PID) Process: | (1840) unsafe3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HPWombat |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\HPWombat\uninstaller.exe | |||
| (PID) Process: | (3088) HPWombatSrv.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3088) HPWombatSrv.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @"%windir%\System32\ie4uinit.exe",-732 |
Value: Finds and displays information and Web sites on the Internet. | |||
| (PID) Process: | (3088) HPWombatSrv.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @"%windir%\System32\ie4uinit.exe",-738 |
Value: Start Internet Explorer without ActiveX controls or browser extensions. | |||
| (PID) Process: | (3088) HPWombatSrv.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @"%systemroot%\system32\windowspowershell\v1.0\powershell.exe",-111 |
Value: Performs object-based (command-line) functions | |||
| (PID) Process: | (3704) WombatStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\HPWombat |
| Operation: | write | Name: | jeromu |
Value: eyAicmV3cml0ZV90aW1lb3V0X21pbiIgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDUsICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICJ1cmwiICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgIDogICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICJodHRwOi8vYW1wYWNrZW56dS5ydS8iICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICB9 | |||
| (PID) Process: | (1840) unsafe3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\unsafe3_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1840) unsafe3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\unsafe3_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
5
Suspicious files
0
Text files
5
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | HPWombatSrv.exe | C:\Program Files\HPWombat\1.lnk | — | |
MD5:— | SHA256:— | |||
| 3088 | HPWombatSrv.exe | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\User Pinned\TaskBar\Internet Explorer.lnk | — | |
MD5:— | SHA256:— | |||
| 3088 | HPWombatSrv.exe | C:\Users\Administrator\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\User Pinned\TaskBar\Internet Explorer.lnk | — | |
MD5:— | SHA256:— | |||
| 1840 | unsafe3.exe | C:\Users\admin\AppData\Local\Temp\nsv3EB0.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | HPWombatSrv.exe | C:\Users\Administrator\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\User Pinned\TaskBar\Intеrnеt Ехрlоrеr.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3088 | HPWombatSrv.exe | C:\Users\Public\Desktop\Firеfох.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3088 | HPWombatSrv.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Intеrnеt Ехрlоrеr.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3088 | HPWombatSrv.exe | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\User Pinned\TaskBar\Intеrnеt Ехрlоrеr.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3088 | HPWombatSrv.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Accessories\System Tools\Intеrnеt Ехрlоrеr (Nо Аdd-оns).lnk | lnk | |
MD5:— | SHA256:— | |||
| 1840 | unsafe3.exe | C:\Program Files\HPWombat\Resources\Icons\Browsers\3.ico | image | |
MD5:7303CD6483F7342CE33E0EDFA413102E | SHA256:48C0167F89407E9E3CD9BEB207AC4AED90BE7603536F160046C2E0C9C04499E5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
giffki.ru |
| malicious |