| File name: | iCal-201909.ics |
| Full analysis: | https://app.any.run/tasks/4e9b225e-e6eb-457d-a70f-f05c6b1e00a7 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 13:08:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | text/calendar |
| File info: | vCalendar calendar file |
| MD5: | 49590A81EAF5C6B0F4ACDC49F3DB71CC |
| SHA1: | 0A391019121AEBB176C4B9A71DAA5C7528F43942 |
| SHA256: | 748960BD01CF29AF07365102EDE453A6561EB4184DBD265019C228FD77CBF3B8 |
| SSDEEP: | 96:EpfMgraKWPCqZY4ahPkgs1Soa7MFuiYA6NDLgv5iMJ:WXraKWPRZors1Uxr4fJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads internet explorer settings
- OUTLOOK.EXE (PID: 2796)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2796)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2796)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2108)
- OUTLOOK.EXE (PID: 2796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ics/vcs | | | iCalendar - vCalendar (100) |
|---|
EXIF
VCard
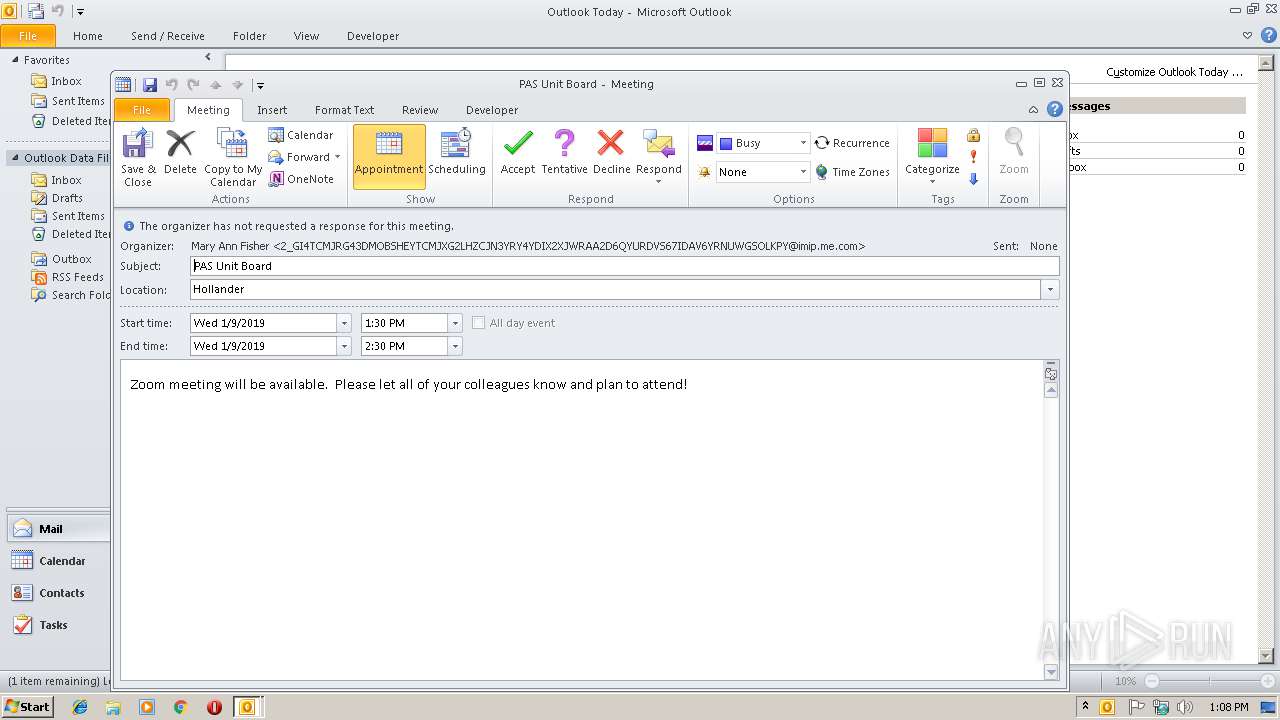
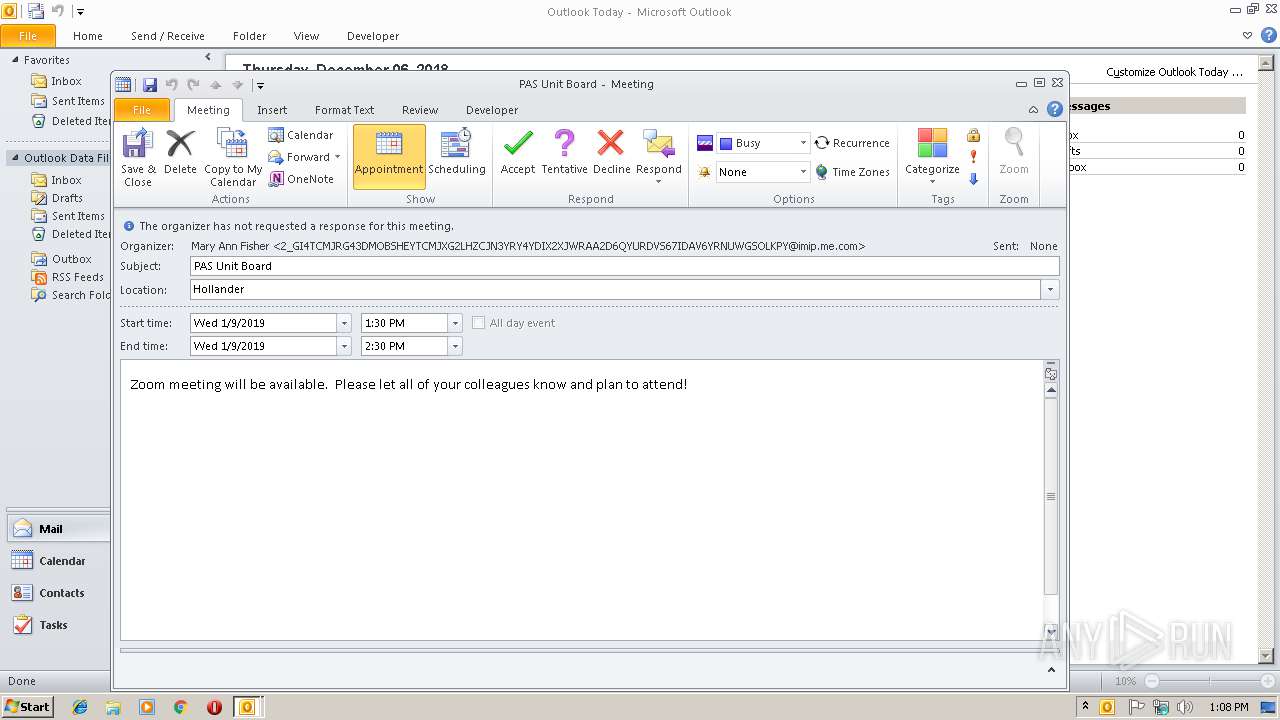
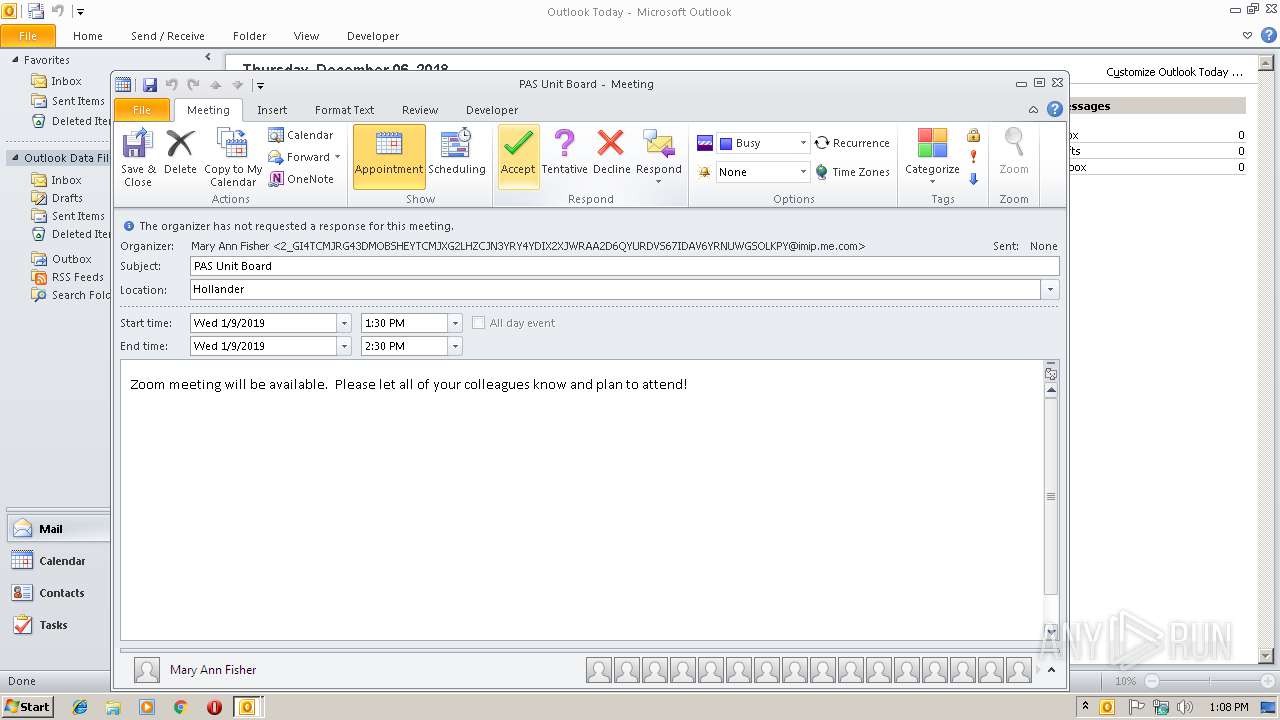
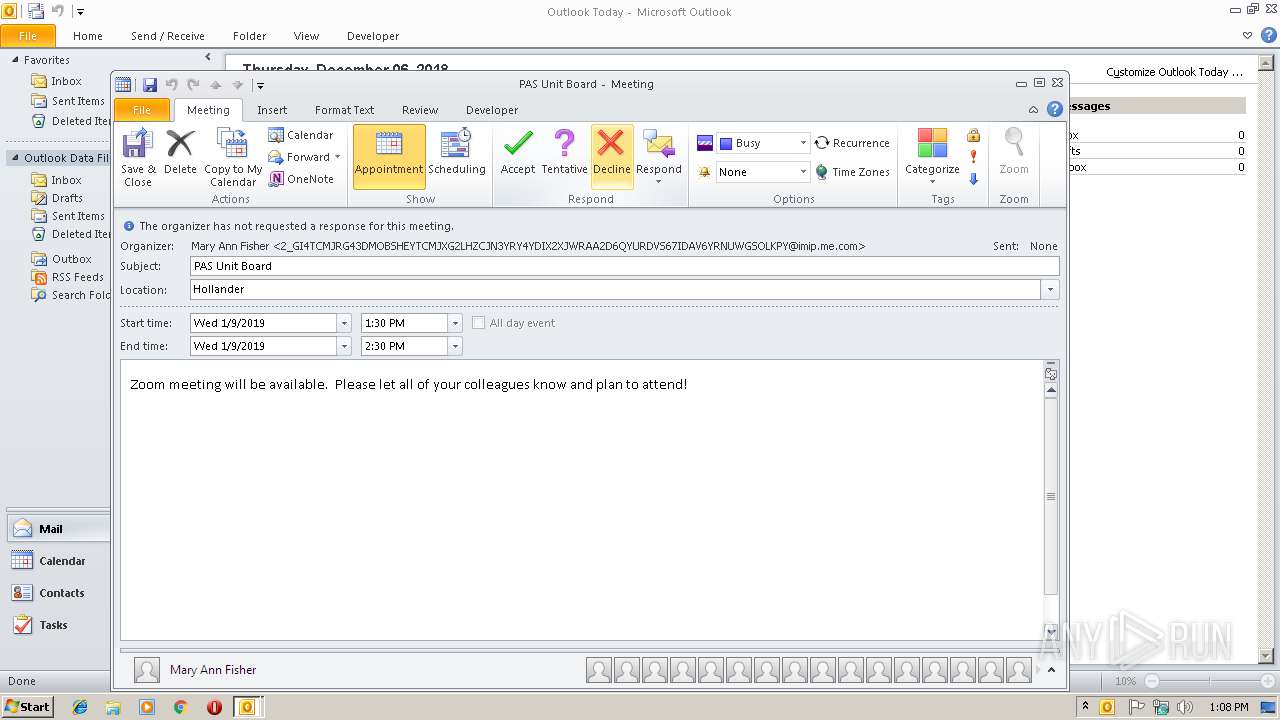
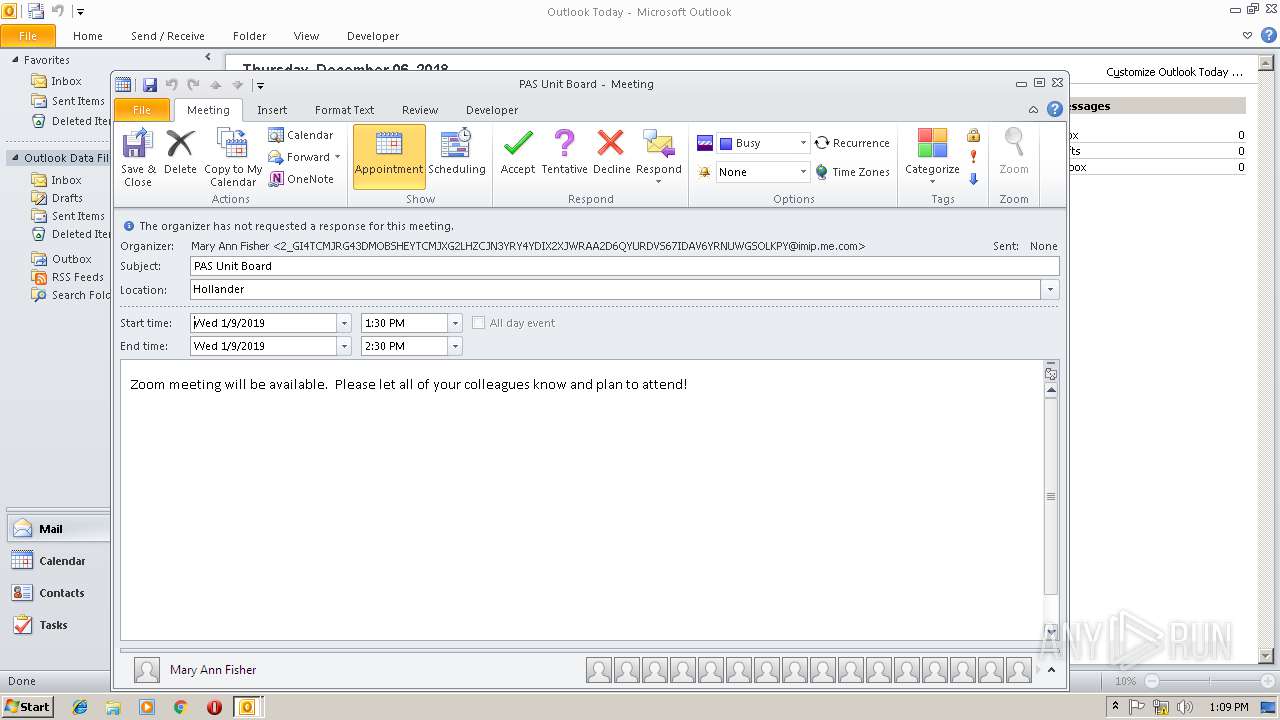
| Software: | -//CALENDARSERVER.ORG//NONSGML Version 1//EN |
|---|---|
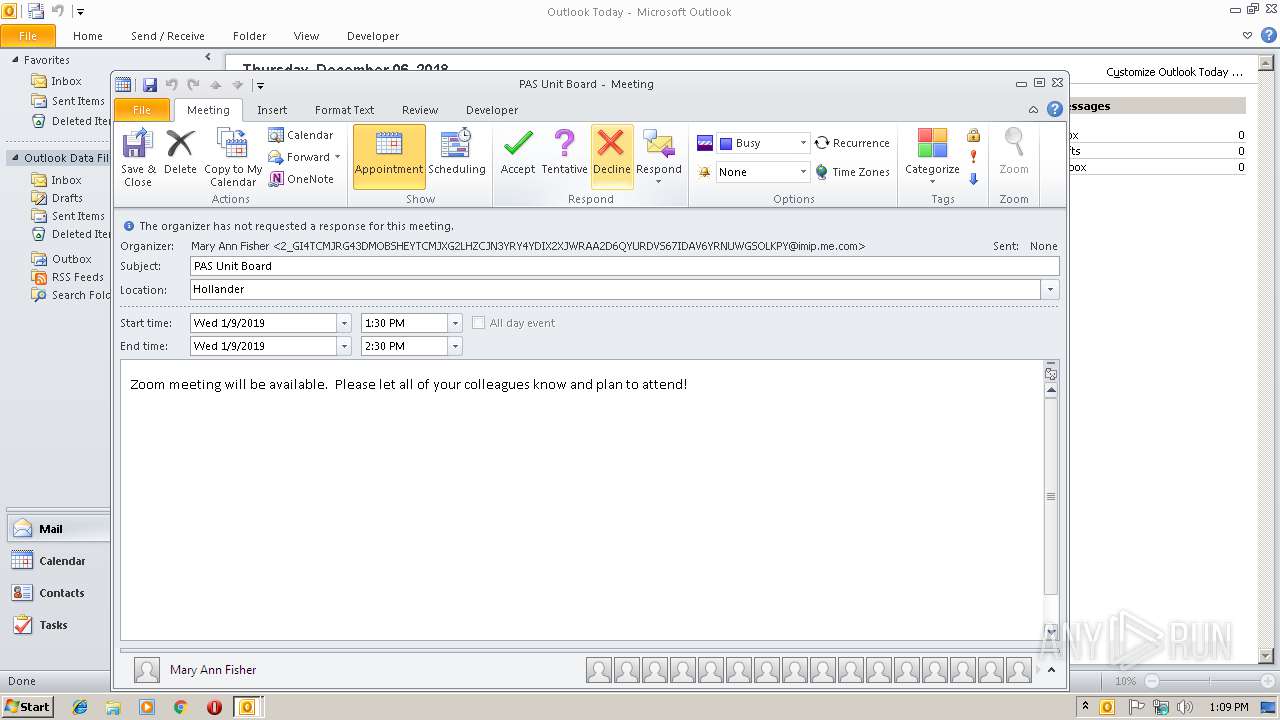
| VCalendarVersion: | 2 |
| Attendee: | mailto:delores.word-gaines@vumc.org |
| DateCreated: | 2018:12:06 00:37:01Z |
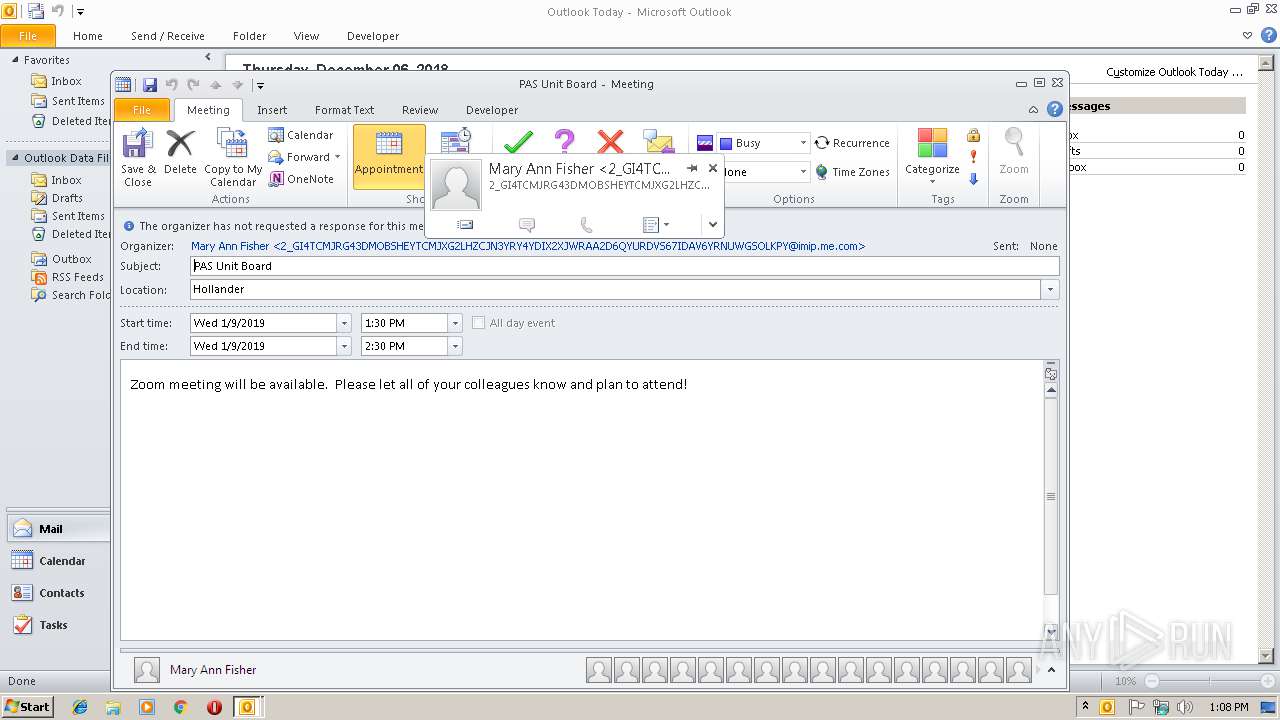
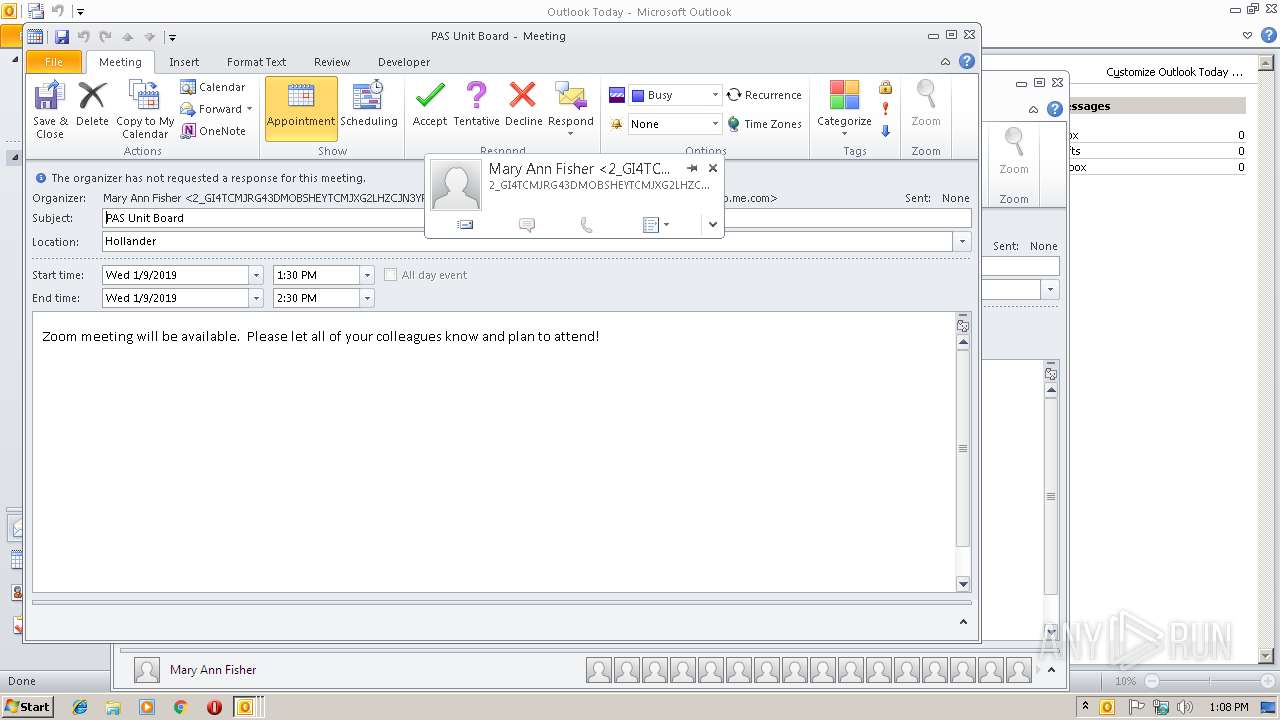
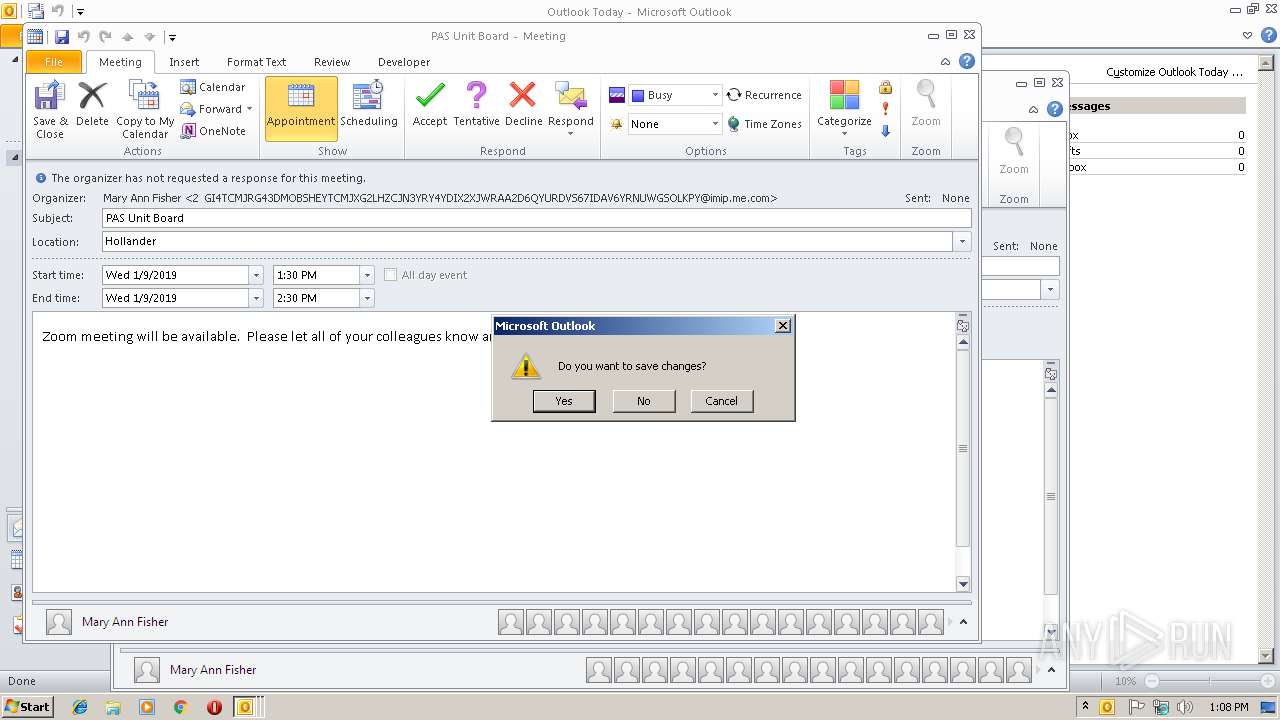
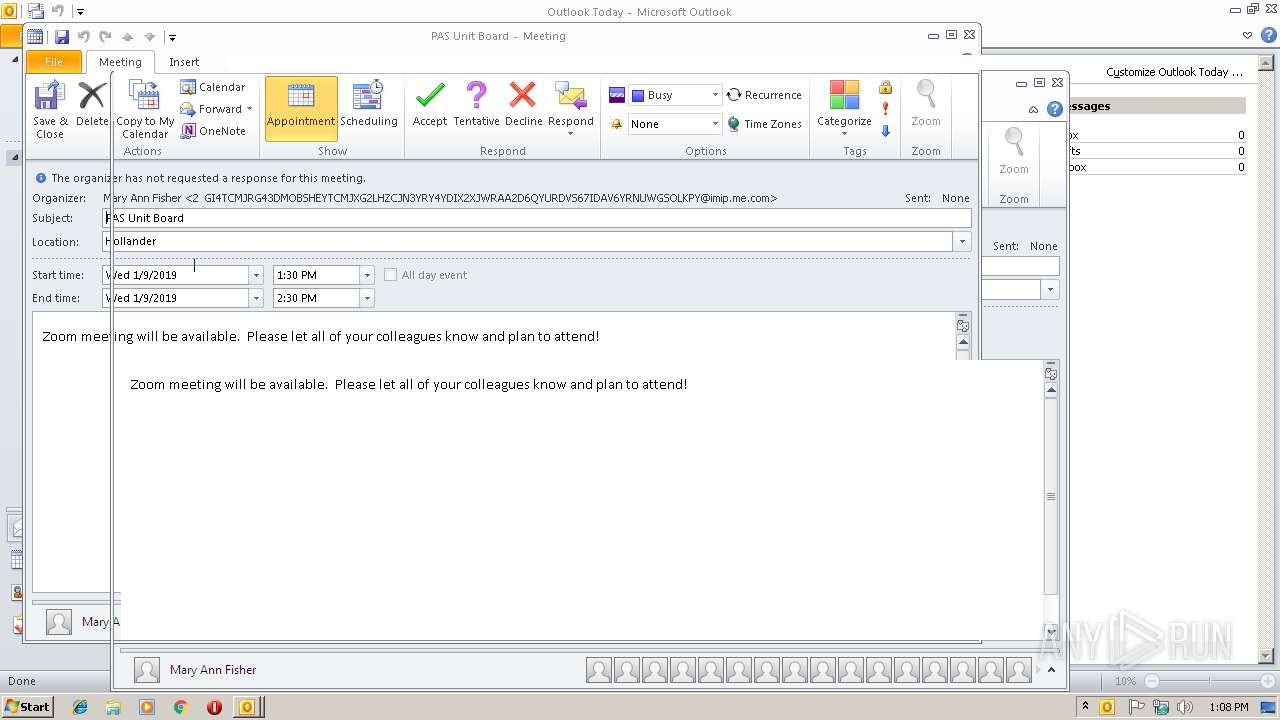
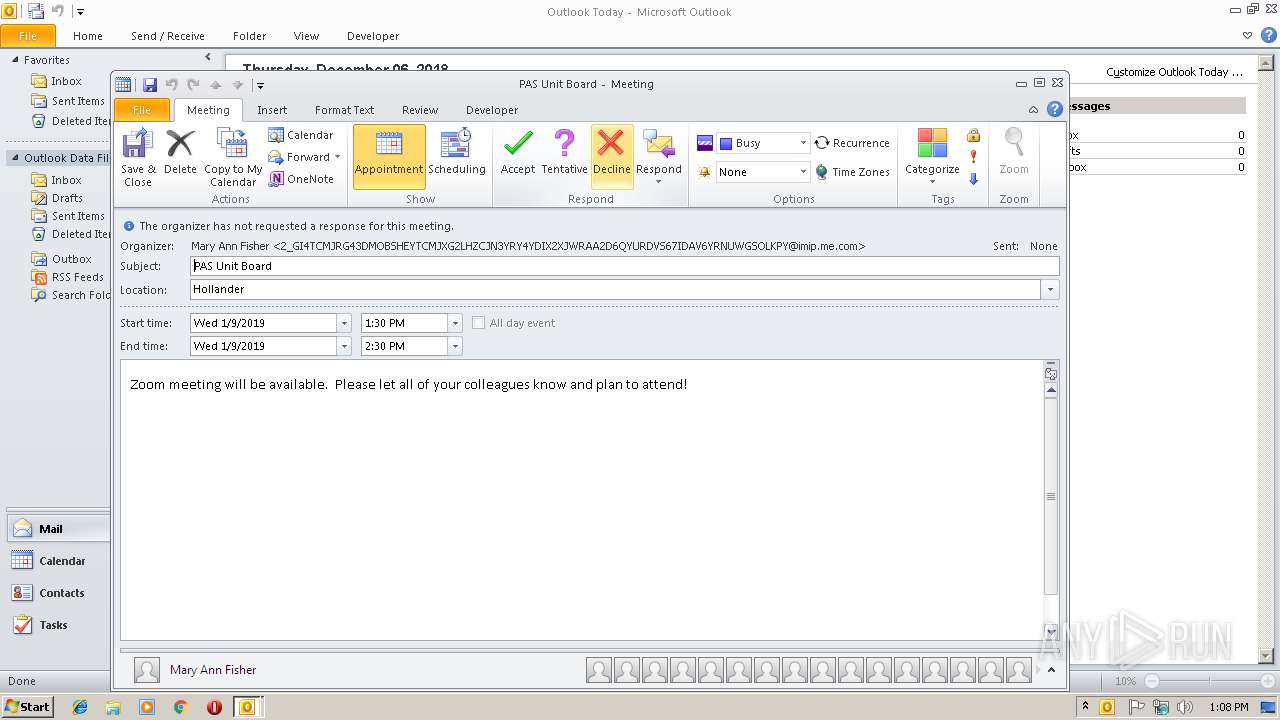
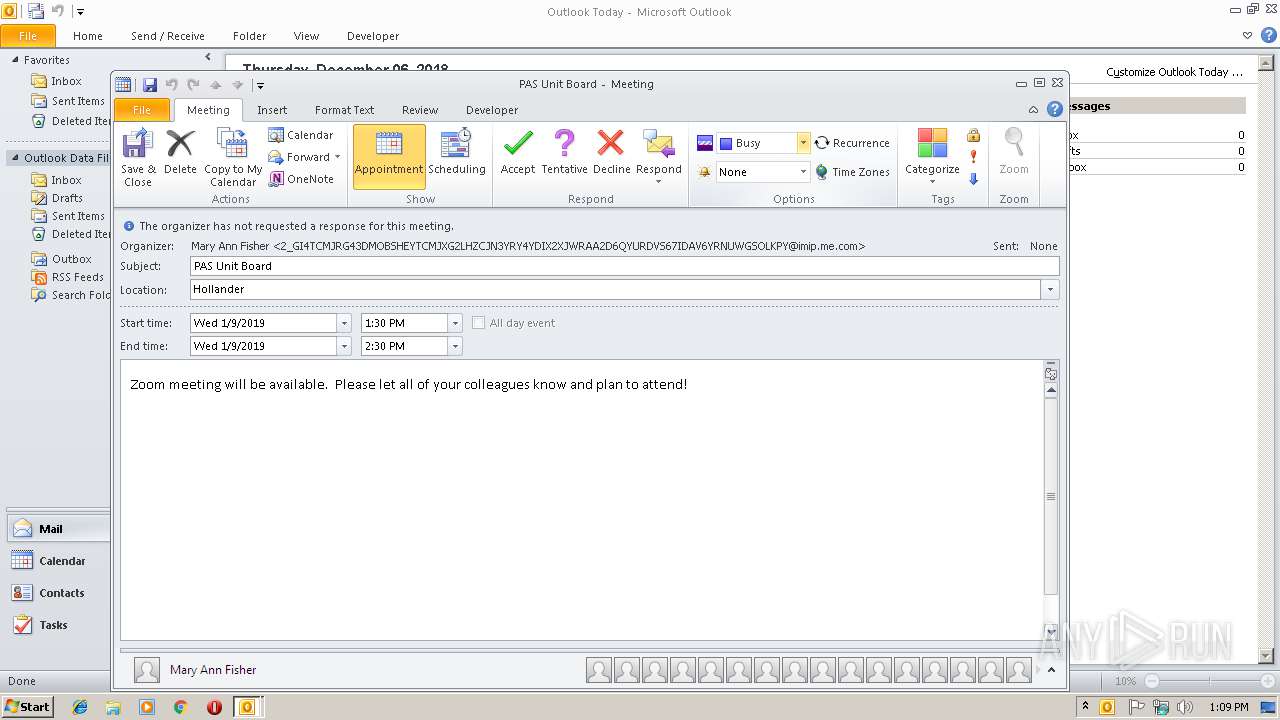
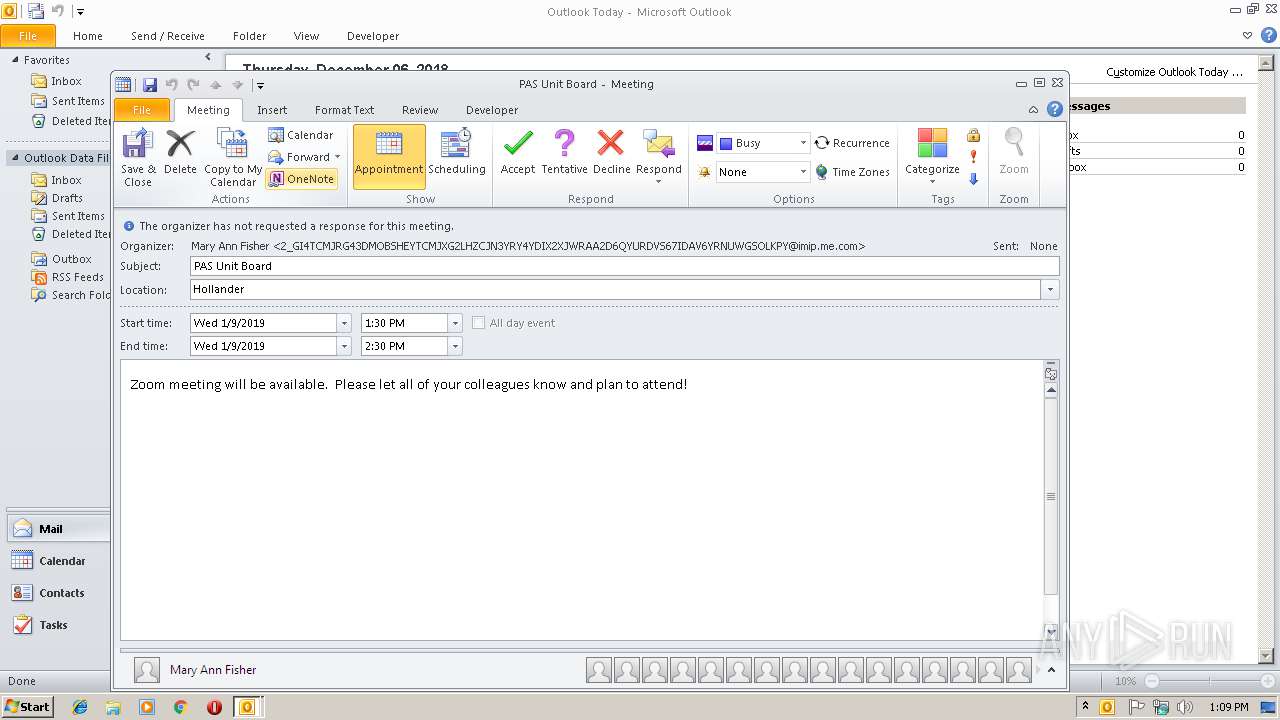
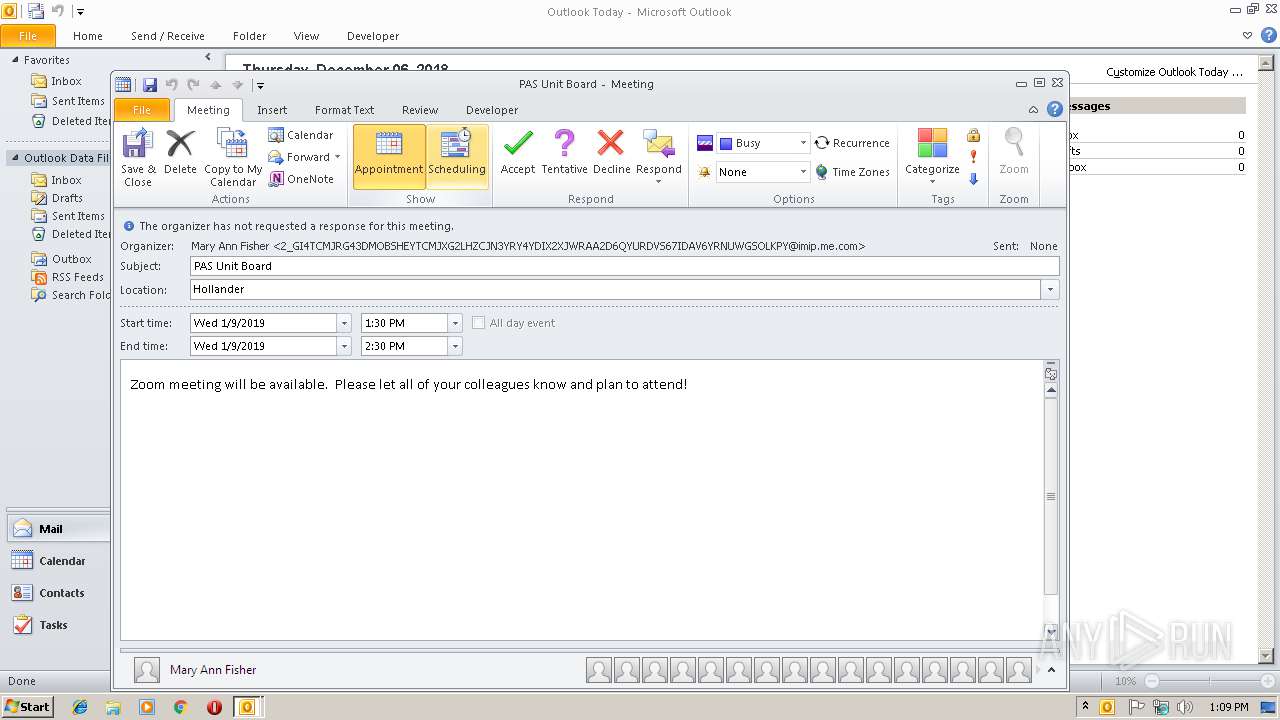
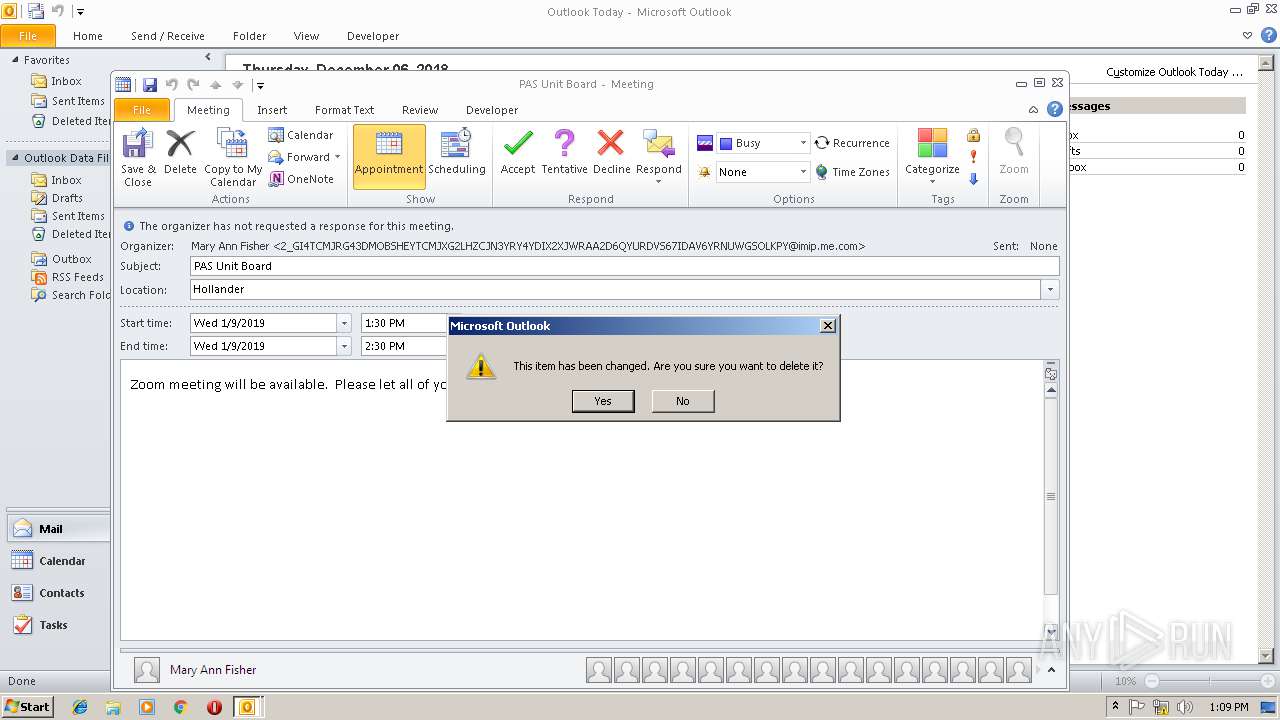
| Description: | Zoom meeting will be available. Please let all of your colleagues know and plan to attend! |
| DateTimeEnd: | 2019:01:09 08:30:00 |
| DateTimeEndTimezoneID: | America/Chicago |
| DateTimeStamp: | 2018:12:06 00:37:08Z |
| DateTimeStart: | 2019:01:09 07:30:00 |
| DateTimeStartTimezoneID: | America/Chicago |
| ModifyDate: | 2018:12:06 00:37:01Z |
| Location: | Hollander |
| Organizer: | mailto:2_GI4TCMJRG43DMOBSHEYTCMJXG2LHZCJN3YRY4YDIX2XJWRAA2D6QYURDVS67IDAV6YRNUWGSOLKPY@imip.me.com |
| SequenceNumber: | - |
| Summary: | PAS Unit Board |
| UID: | 5111AF95-A84A-42D0-9F4C-60EBB74C364B |
| URL: | - |
Total processes
32
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2108 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /ical "C:\Users\admin\AppData\Local\Temp\iCal-201909.ics" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
1 594
Read events
1 123
Write events
433
Delete events
38
Modification events
| (PID) Process: | (2796) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2796) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2796) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | `%$ |
Value: 60252400EC0A0000010000000000000000000000 | |||
| (PID) Process: | (2796) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: EC0A000022EAA5CB648DD40100000000 | |||
| (PID) Process: | (2796) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2796) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219808800 | |||
| (PID) Process: | (2796) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2796) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2796) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2796) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1300627477 | |||
Executable files
0
Suspicious files
0
Text files
26
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2796 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9551.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2796 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFF15E74BA820FE5F6.TMP | — | |
MD5:— | SHA256:— | |||
| 2796 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF94A4CFD637FAB8BC.TMP | — | |
MD5:— | SHA256:— | |||
| 2108 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRD70D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2796 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF3EA4E9F9A27C8A63.TMP | — | |
MD5:— | SHA256:— | |||
| 2796 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF55542B452D905C82.TMP | — | |
MD5:— | SHA256:— | |||
| 2796 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018120620181207\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2796 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2796 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\mso99B7.tmp | html | |
MD5:A8934077843220A8E31367C7BBE15E6C | SHA256:A2DB0201D36F07F3F99D1ADF8B8EAFB9CF9BB803D024FCC9327B77AF56346861 | |||
| 2796 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_38DB349F50855E4EAEC40C7A7F4FB1D8.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2796 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2796 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |