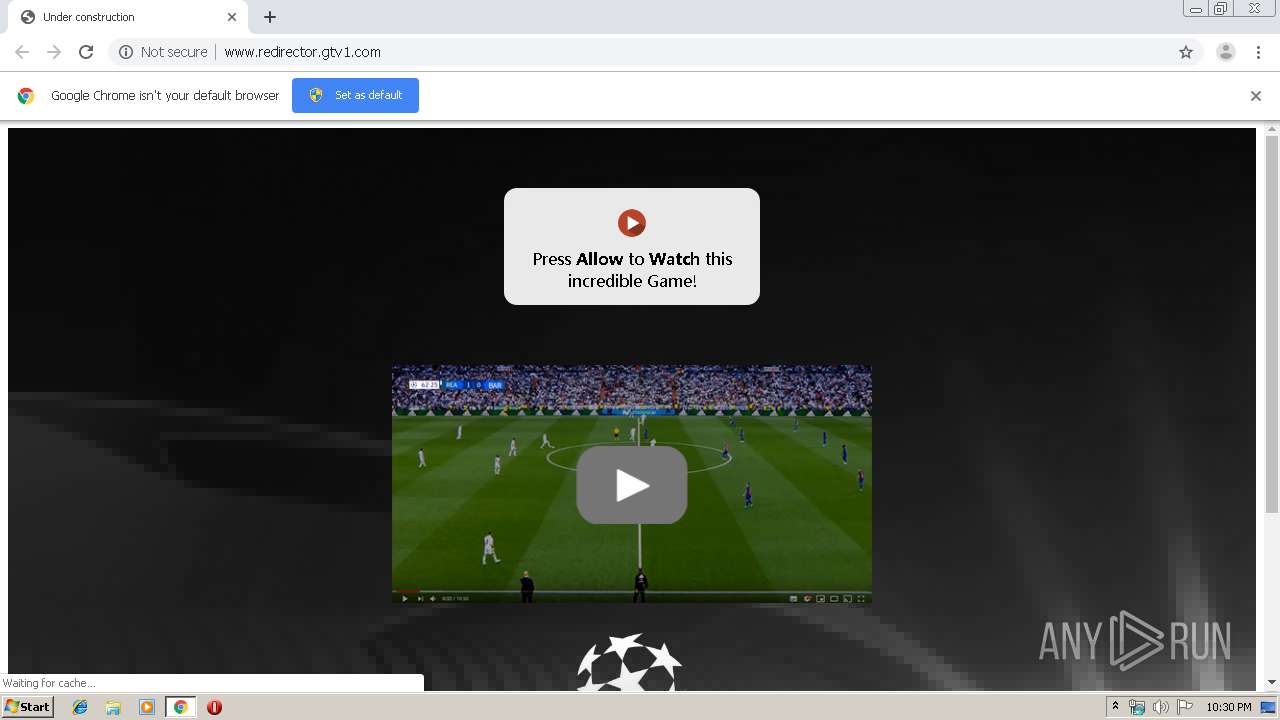
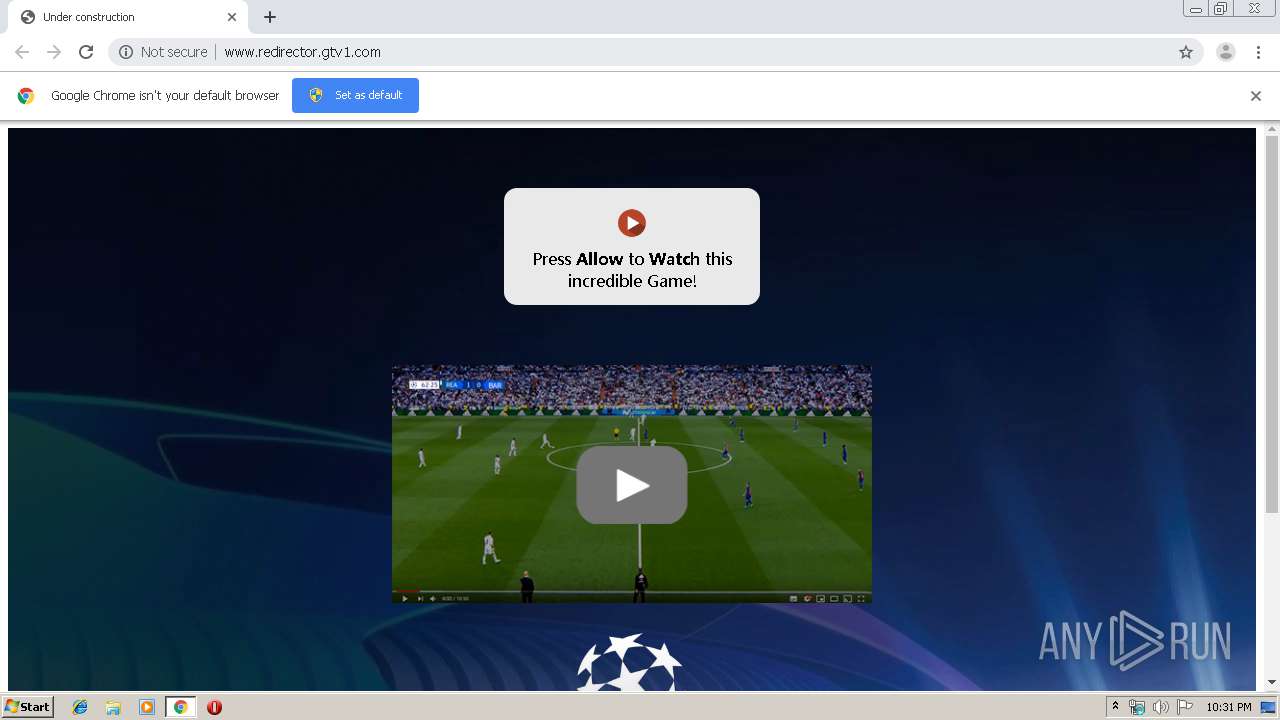
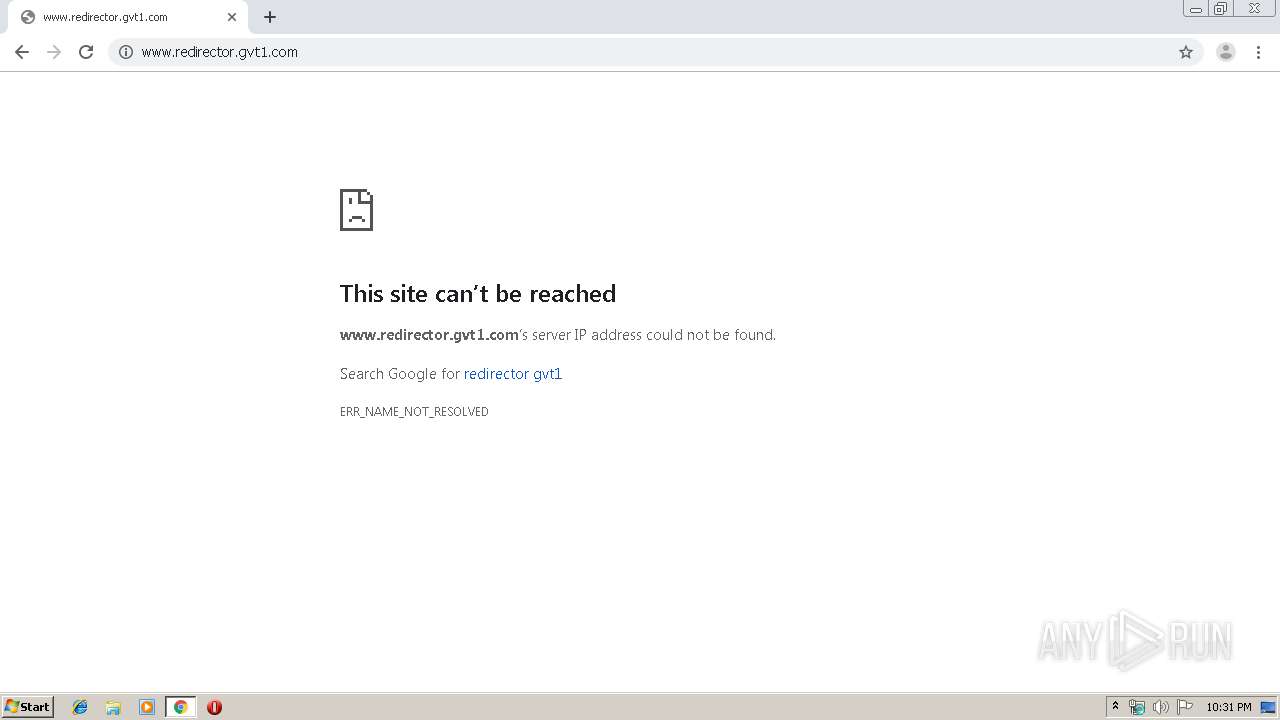
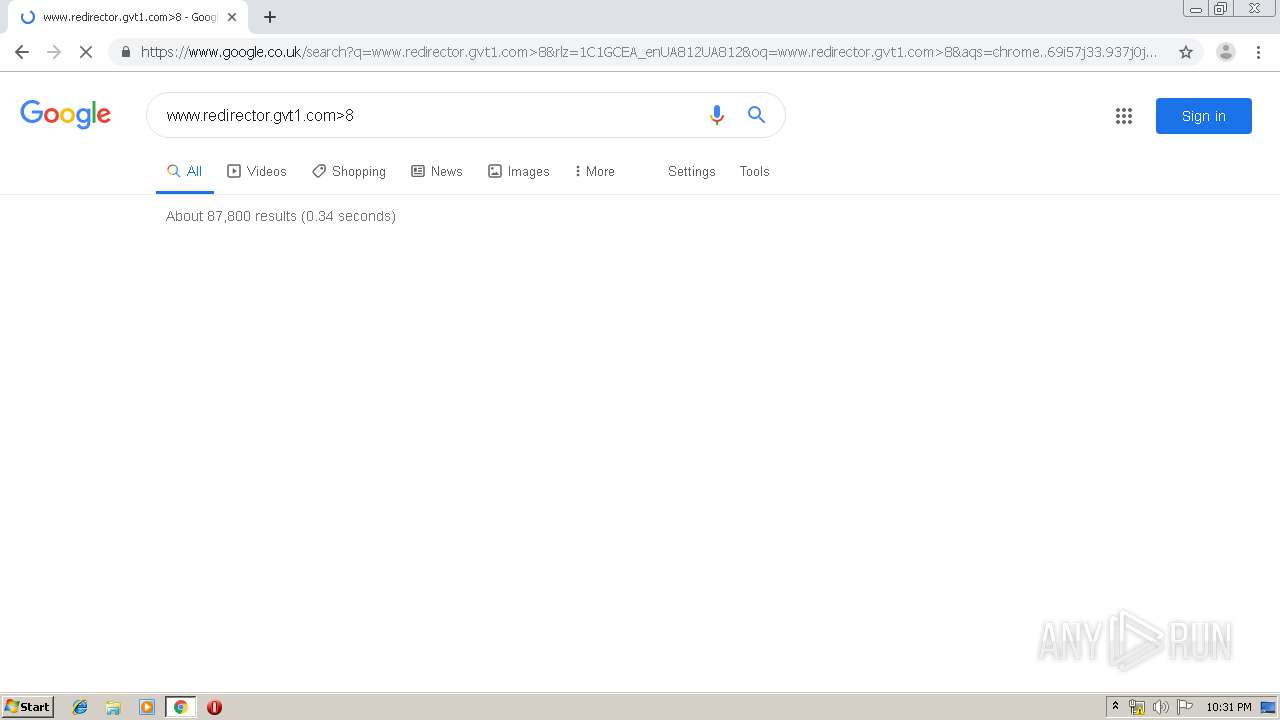
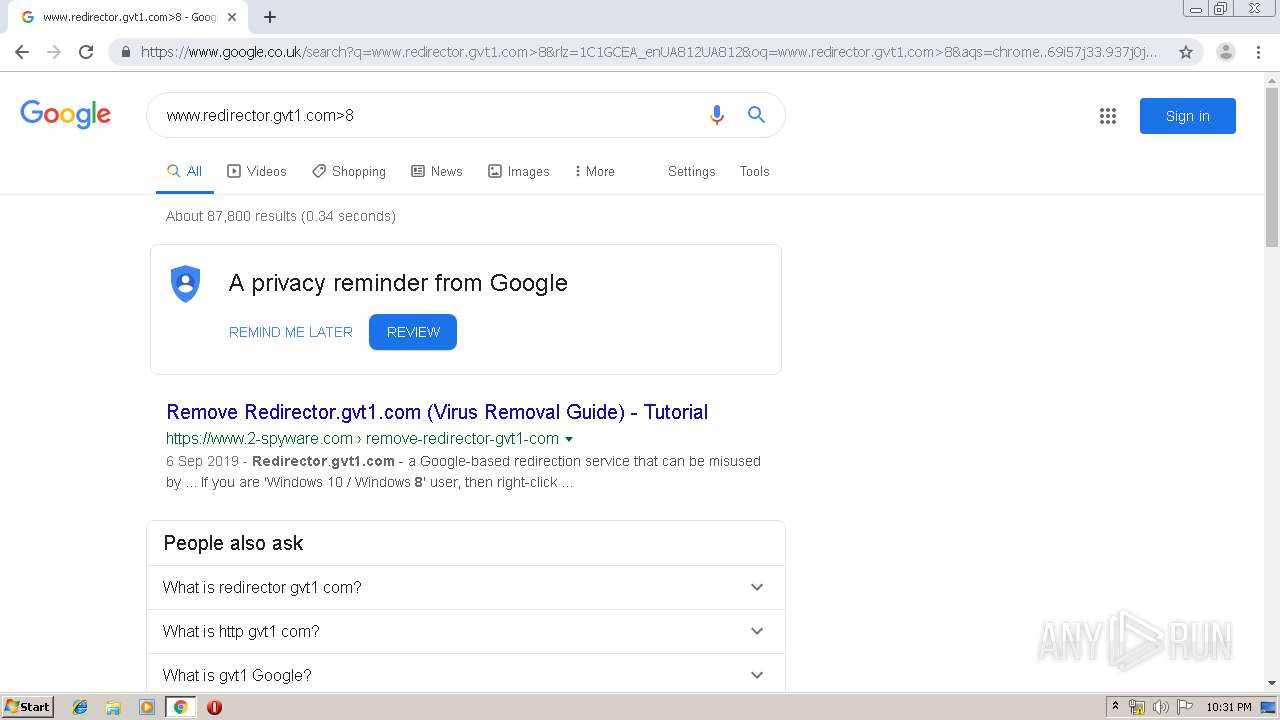
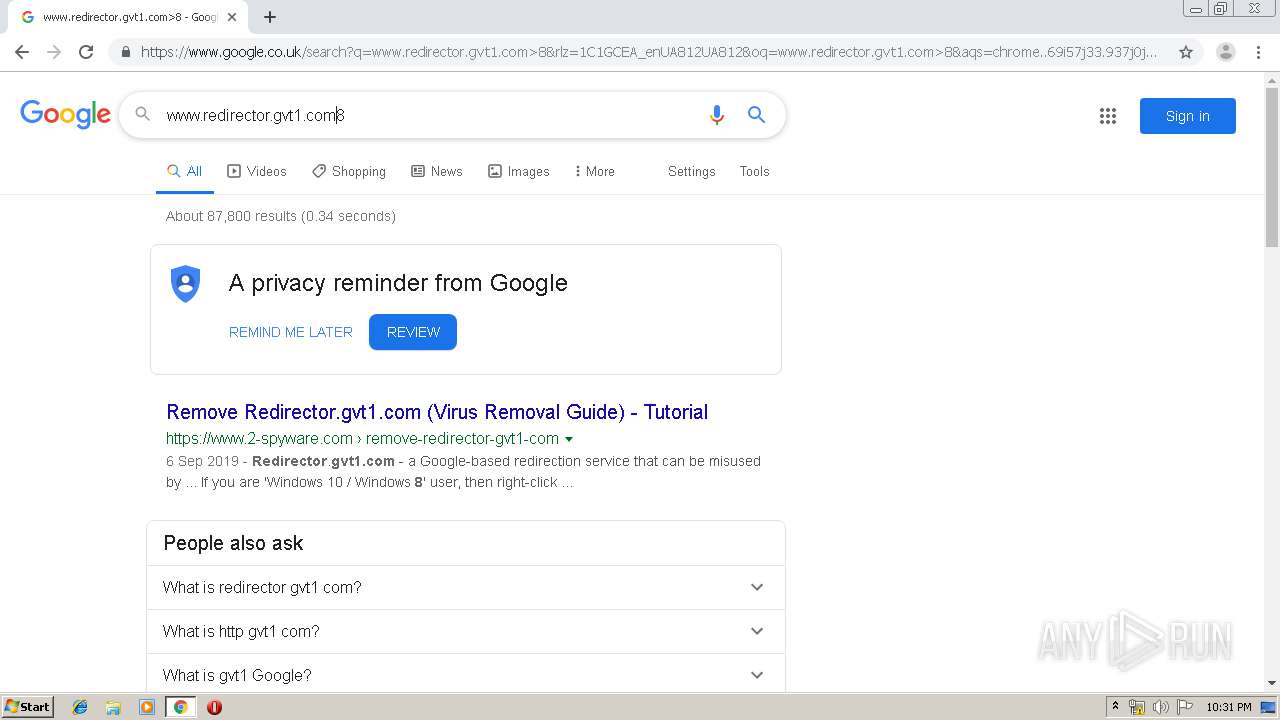
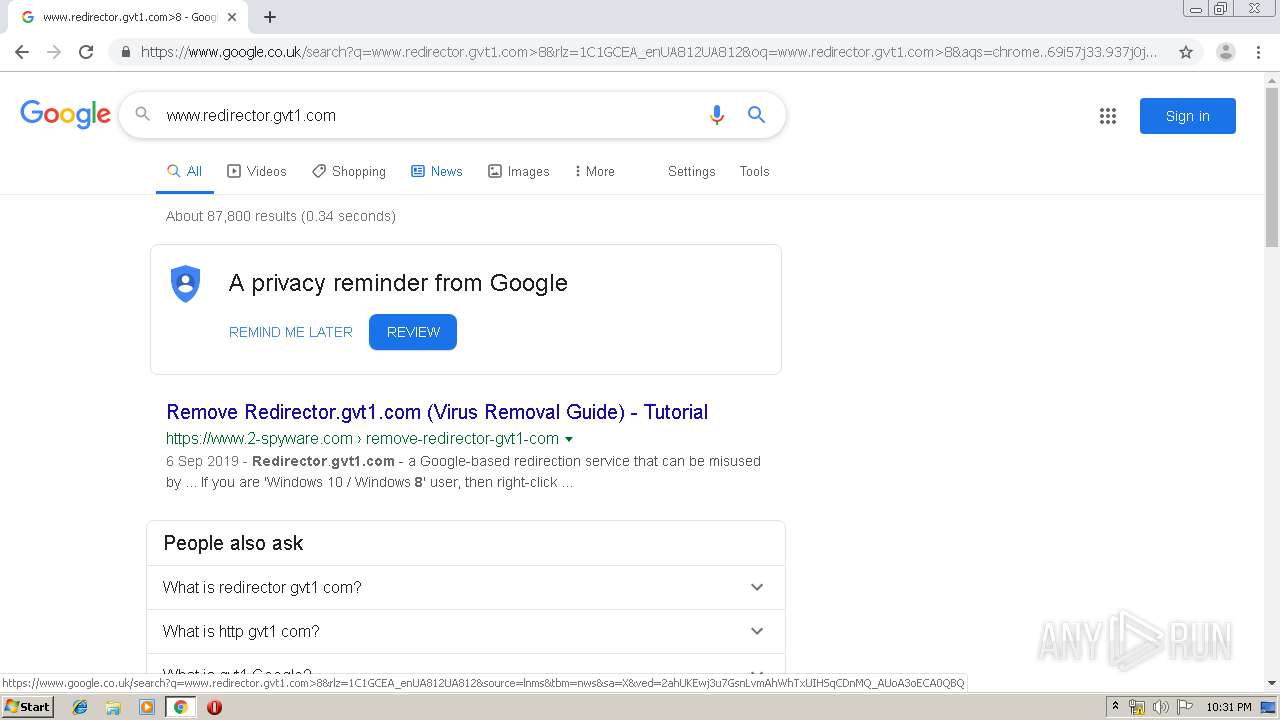
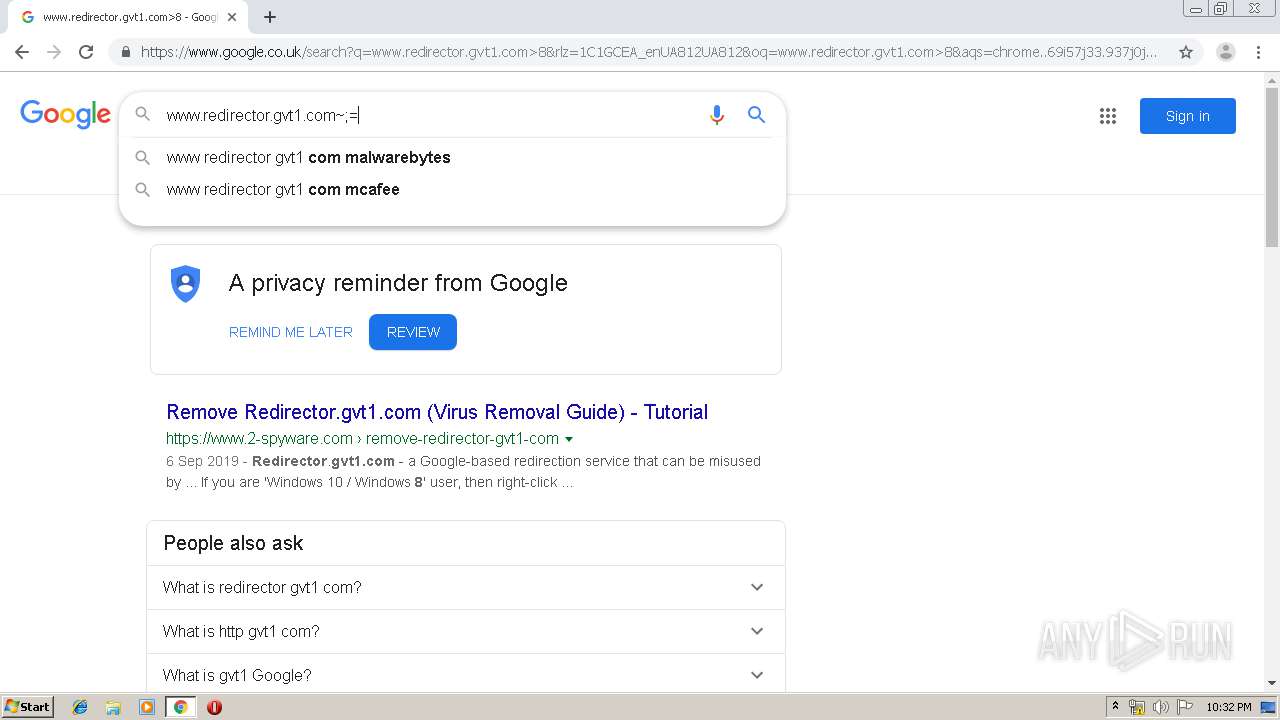
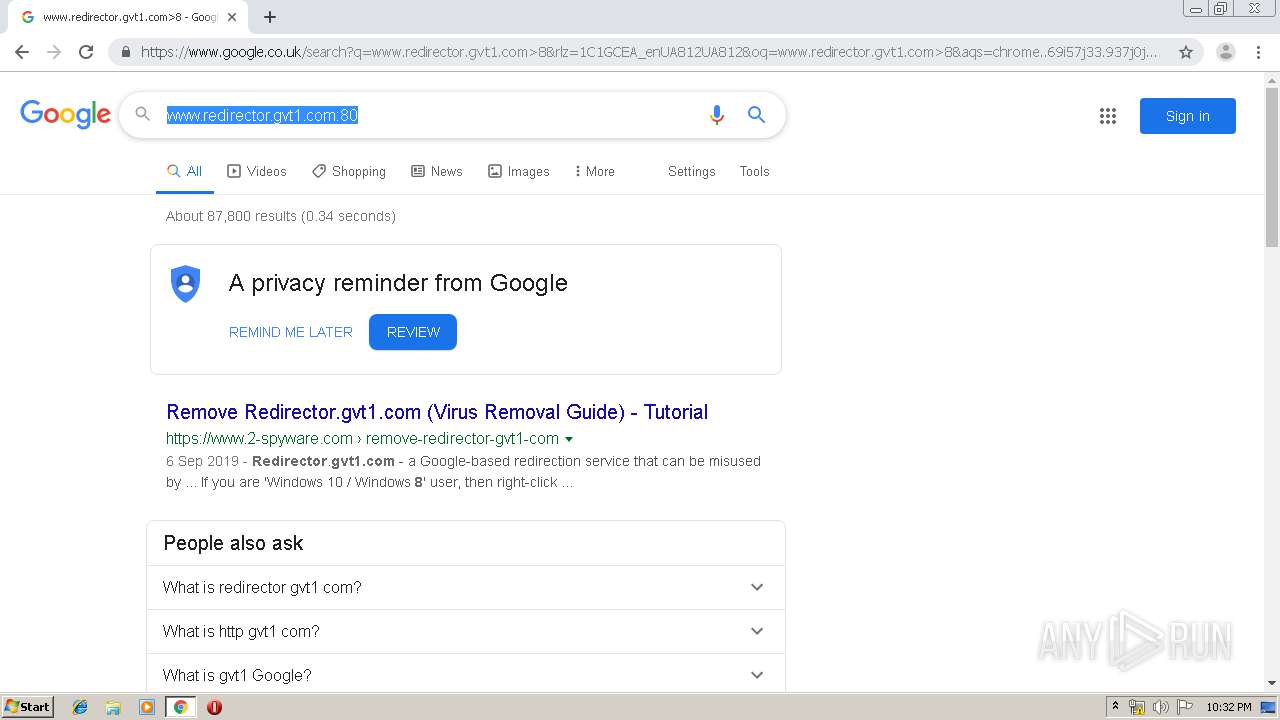
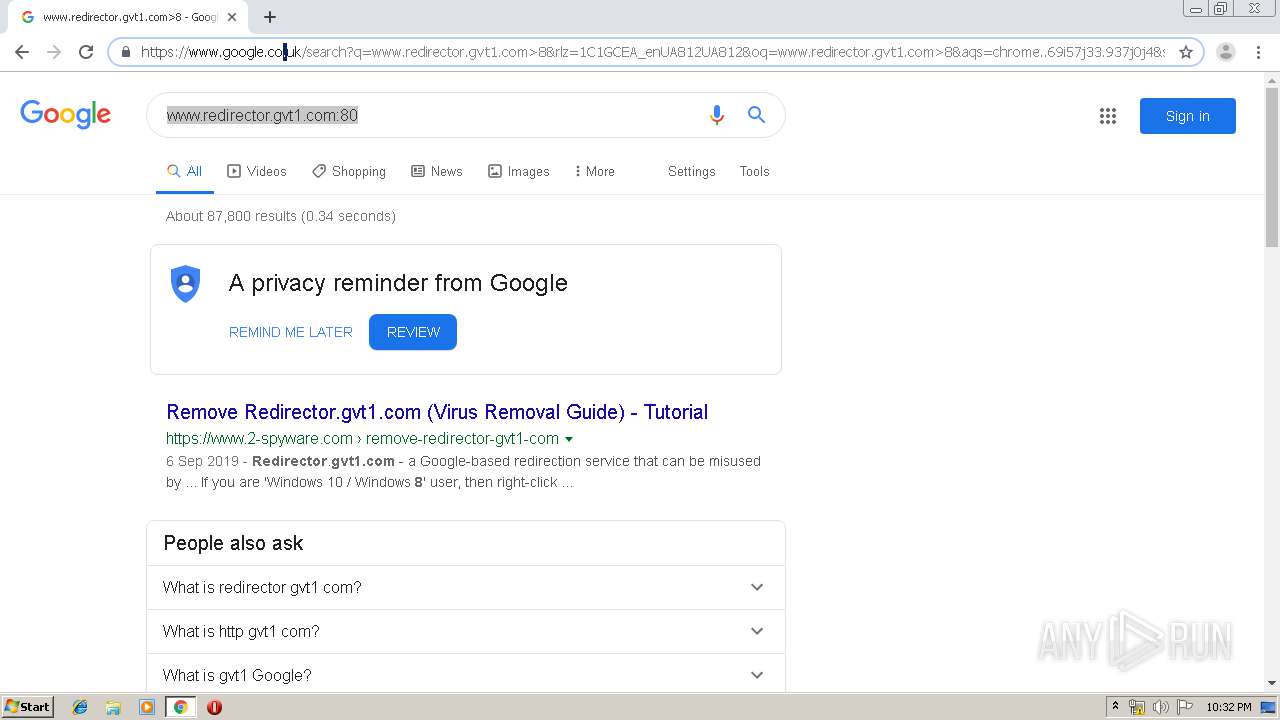
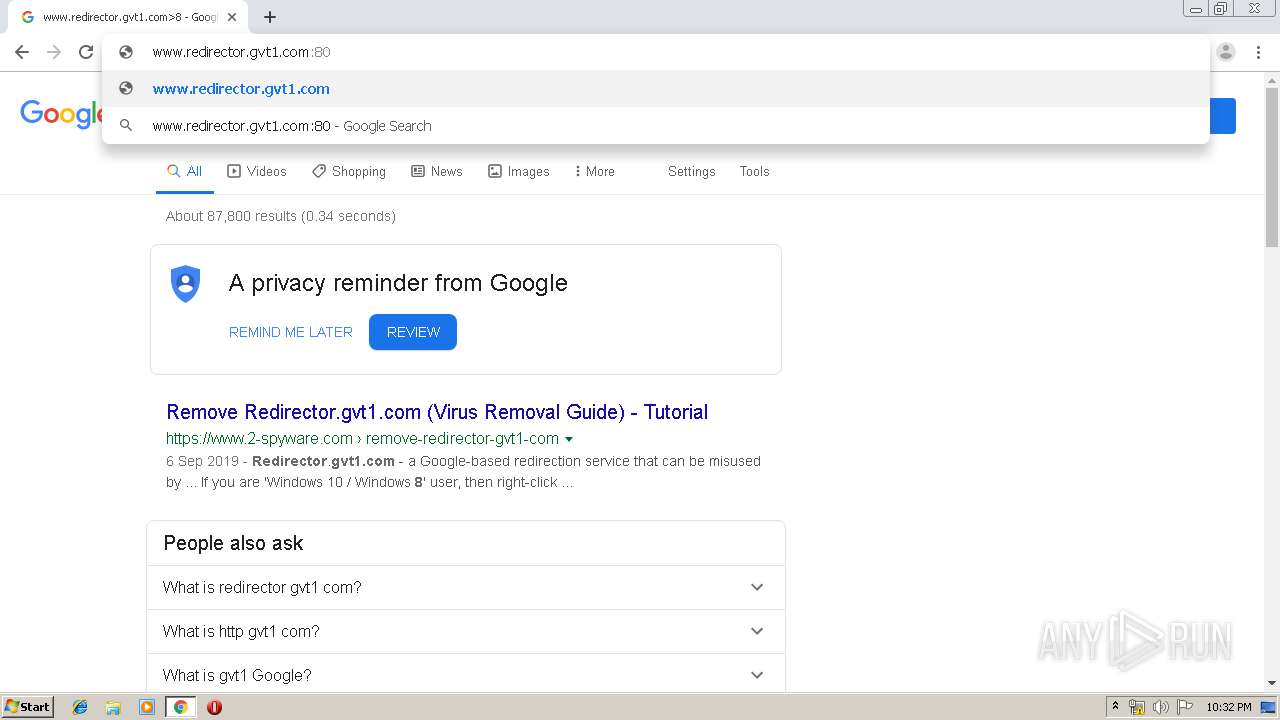
| URL: | http://www.redirector.gtv1.com:80 |
| Full analysis: | https://app.any.run/tasks/a26f02dc-67a9-4d6d-9a17-fb28219768a0 |
| Verdict: | Malicious activity |
| Analysis date: | December 16, 2019, 22:30:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B50C4082D863DE31B370FCA18664BE10 |
| SHA1: | D210BD548D35D232BE10107336E35C4B51DFCBBB |
| SHA256: | 74713FAEA0CDF29E70CC66B38591E543D3C756DE91177C0F0471A586367EDF12 |
| SSDEEP: | 3:N1KJS4Q8niIfX:Cc4QaiiX |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1552)
INFO
Reads the hosts file
- chrome.exe (PID: 1552)
- chrome.exe (PID: 1908)
Application launched itself
- chrome.exe (PID: 1552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
44
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13302427272277733659 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8011920907949209903 --mojo-platform-channel-handle=3752 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1324 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1802172822572357619 --mojo-platform-channel-handle=4364 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12658134391235232676 --mojo-platform-channel-handle=4184 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15631984942747979558 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3776 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8843848481616180811 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.redirector.gtv1.com:80" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11062206471915120877 --mojo-platform-channel-handle=3792 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9479845404696322454 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4388 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
634
Read events
518
Write events
111
Delete events
5
Modification events
| (PID) Process: | (1552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (496) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1552-13221009023237625 |
Value: 259 | |||
| (PID) Process: | (1552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1552) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
43
Text files
261
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3d4a5a25-386e-41ed-8330-e37fdf5e5e08.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39992d.TMP | text | |
MD5:— | SHA256:— | |||
| 1552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39994c.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
51
DNS requests
42
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1908 | chrome.exe | GET | 302 | 72.52.179.175:80 | http://dsnextgen.com/?domainname=ttrader.mydomain.com&a_id=127039 | US | — | — | malicious |
1908 | chrome.exe | GET | — | 91.195.240.136:80 | http://ww1.dsnextgen.com/ | DE | — | — | malicious |
1908 | chrome.exe | GET | — | 91.195.240.136:80 | http://ww1.dsnextgen.com/ | DE | — | — | malicious |
1908 | chrome.exe | GET | — | 52.28.12.46:80 | http://cletrogen-daution.com/redirect?target=BASE64aHR0cHM6Ly9mcmVlLnV1bWVpanUuY29tLz91dG1fbWVkaXVtPWVlODk5MmE1NWRkMTYyMGNmYmRmMmIzZTNkYTM1OTAxODNmMjhmOTEmdXRtX2NhbXBhaWduPVB1c2hWTSZjaWQ9d2oxZXNqMGlyYmRkam1ocmhuczhjYXZz&ts=1576535430802&hash=7GGUZ6BVSgNd26mibeE5nLd5hdwotS6yoGmTLlocGUA&rm=DJ | DE | — | — | suspicious |
1908 | chrome.exe | GET | 200 | 3.226.8.132:80 | http://usd.nethaneel-has.com/zcvisitor/a9fcc1b2-2053-11ea-827e-12afff3d9613?campaignid=d9edea60-1cf3-11ea-99c4-12f2f4d45bc1 | US | html | 1012 b | whitelisted |
1908 | chrome.exe | GET | 302 | 91.195.240.136:80 | http://ww1.dsnextgen.com/search/redirect.php?f=http%3A%2F%2Fusd.nethaneel-has.com%2Fzcvisitor%2Fa9fcc1b2-2053-11ea-827e-12afff3d9613%3Fcampaignid%3Dd9edea60-1cf3-11ea-99c4-12f2f4d45bc1&v=ZDZjMjliNjg5YjkwMjI2NDM2OTAyYWM4YmJkNTU3ZTQJMQl3dzEuZHNuZXh0Z2VuLmNvbTVkZjgwNTg1NDI3ZTc2LjMyNjMzMTY0CXd3MS5kc25leHRnZW4uY29tNWRmODA1ODU0MjgwZDYuMjA4NDk4MjgJMTU3NjUzNTQyOQlhZF8zMV8w&l=NwllNWUzNDRkYzZiODM5Y2VmZTUzNDY5MDhmZTVjMTUyNQkwCTEzCTAJYTQ5MDQzZGI3OWRmZjA5OWU4ODBhMmM5ZjBhODhhMGIJMzM1ODI1MDg2CWRzbmV4dGdlbgkxMTAxCTMxCTQJMwkxNTc2NTM1NDI5CTAuMDAwNTYJTgkwCTAJMAkxMjA1CTk4MjAwODY5CTE4NS40My4xMTAuMjQ5 | DE | compressed | 2.81 Kb | malicious |
1908 | chrome.exe | GET | 200 | 52.28.12.46:80 | http://cletrogen-daution.com/zp-redirect?target=https%3A%2F%2Ffree.uumeiju.com%2F%3Futm_medium%3Dee8992a55dd1620cfbdf2b3e3da3590183f28f91%26utm_campaign%3DPushVM%26cid%3Dwj1esj0irbddjmhrhns8cavs&caid=472d0791-256b-4a83-b3b8-028e7a26e3f2&zpid=a9fcc1b2-2053-11ea-827e-12afff3d9613&cid=wj1esj0irbddjmhrhns8cavs&rt=DJ | DE | html | 880 b | suspicious |
1908 | chrome.exe | GET | 302 | 91.195.240.136:80 | http://ww1.dsnextgen.com/search/tcerider.php?f=http%3A%2F%2Fusd.nethaneel-has.com%2Fzcvisitor%2Fa9fcc1b2-2053-11ea-827e-12afff3d9613%3Fcampaignid%3Dd9edea60-1cf3-11ea-99c4-12f2f4d45bc1&v=ZDZjMjliNjg5YjkwMjI2NDM2OTAyYWM4YmJkNTU3ZTQJMQl3dzEuZHNuZXh0Z2VuLmNvbTVkZjgwNTg1NDI3ZTc2LjMyNjMzMTY0CXd3MS5kc25leHRnZW4uY29tNWRmODA1ODU0MjgwZDYuMjA4NDk4MjgJMTU3NjUzNTQyOQlhZF8zMV8w&l=NwllNWUzNDRkYzZiODM5Y2VmZTUzNDY5MDhmZTVjMTUyNQkwCTEzCTAJYTQ5MDQzZGI3OWRmZjA5OWU4ODBhMmM5ZjBhODhhMGIJMzM1ODI1MDg2CWRzbmV4dGdlbgkxMTAxCTMxCTQJMwkxNTc2NTM1NDI5CTAuMDAwNTYJTgkwCTAJMAkxMjA1CTk4MjAwODY5CTE4NS40My4xMTAuMjQ5 | DE | html | 469 b | malicious |
1908 | chrome.exe | GET | 200 | 66.96.163.136:80 | http://ttrader.mydomain.com/welcome.php | US | html | 1.67 Kb | malicious |
1908 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1908 | chrome.exe | 66.96.149.1:80 | www.redirector.gtv1.com | The Endurance International Group, Inc. | US | malicious |
1908 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1908 | chrome.exe | 72.52.179.175:80 | dsnextgen.com | Liquid Web, L.L.C | US | malicious |
1908 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
1908 | chrome.exe | 66.96.163.136:80 | ttrader.mydomain.com | The Endurance International Group, Inc. | US | malicious |
1908 | chrome.exe | 91.195.240.136:80 | ww1.dsnextgen.com | SEDO GmbH | DE | malicious |
1908 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
1908 | chrome.exe | 205.234.175.175:80 | img.sedoparking.com | CacheNetworks, Inc. | US | suspicious |
1908 | chrome.exe | 172.217.16.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
1908 | chrome.exe | 3.226.8.132:80 | usd.nethaneel-has.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.redirector.gtv1.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ttrader.mydomain.com |
| malicious |
dsnextgen.com |
| malicious |
ww1.dsnextgen.com |
| malicious |
www.google.com |
| malicious |
img.sedoparking.com |
| whitelisted |
clients2.google.com |
| whitelisted |
usd.nethaneel-has.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1908 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |