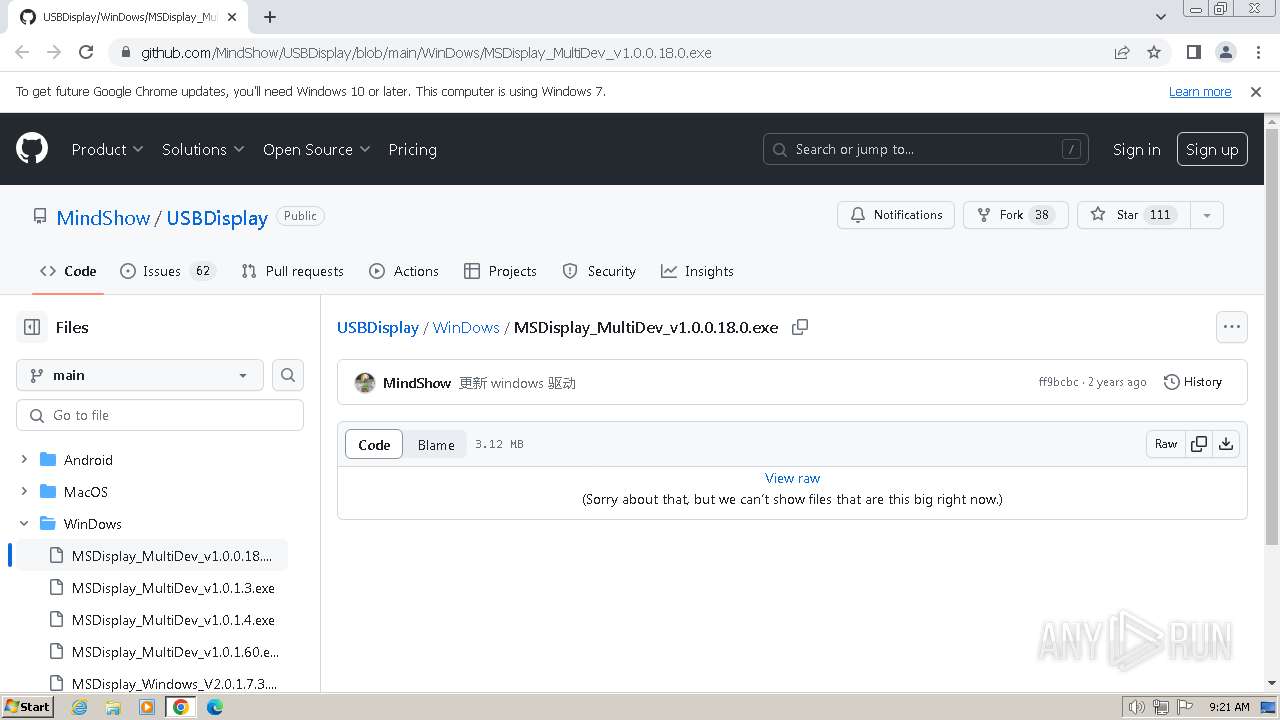
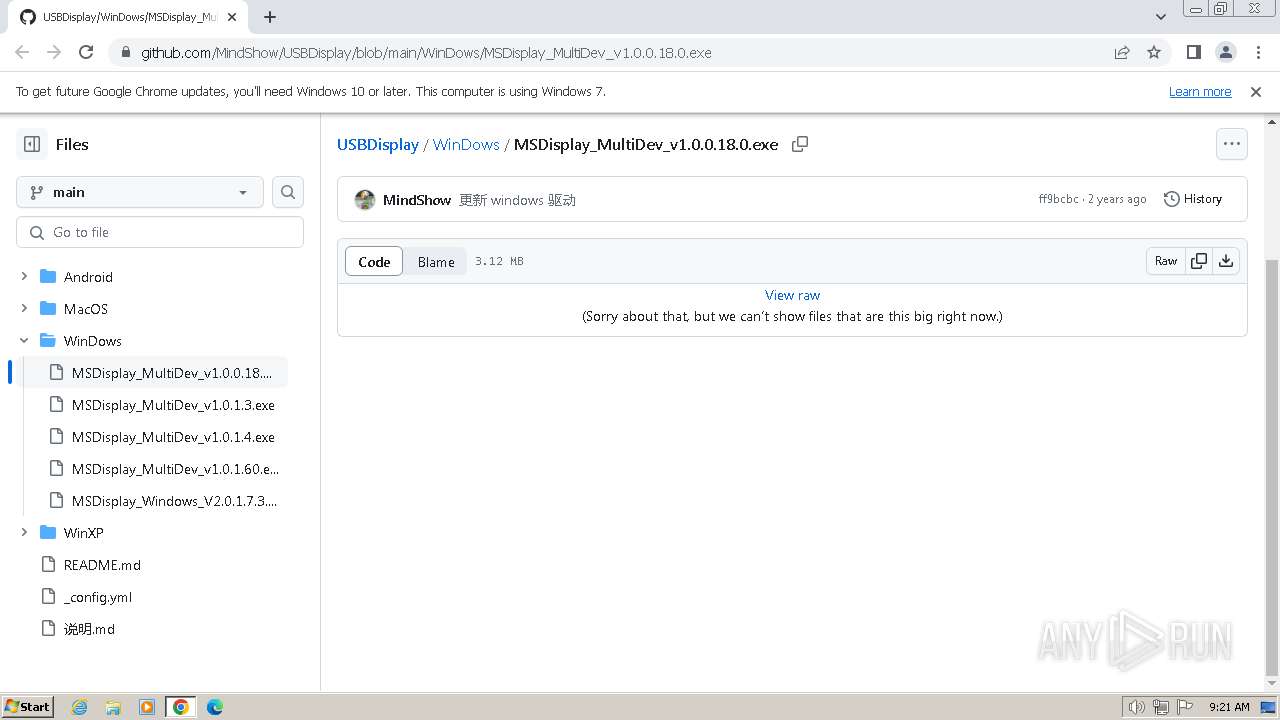
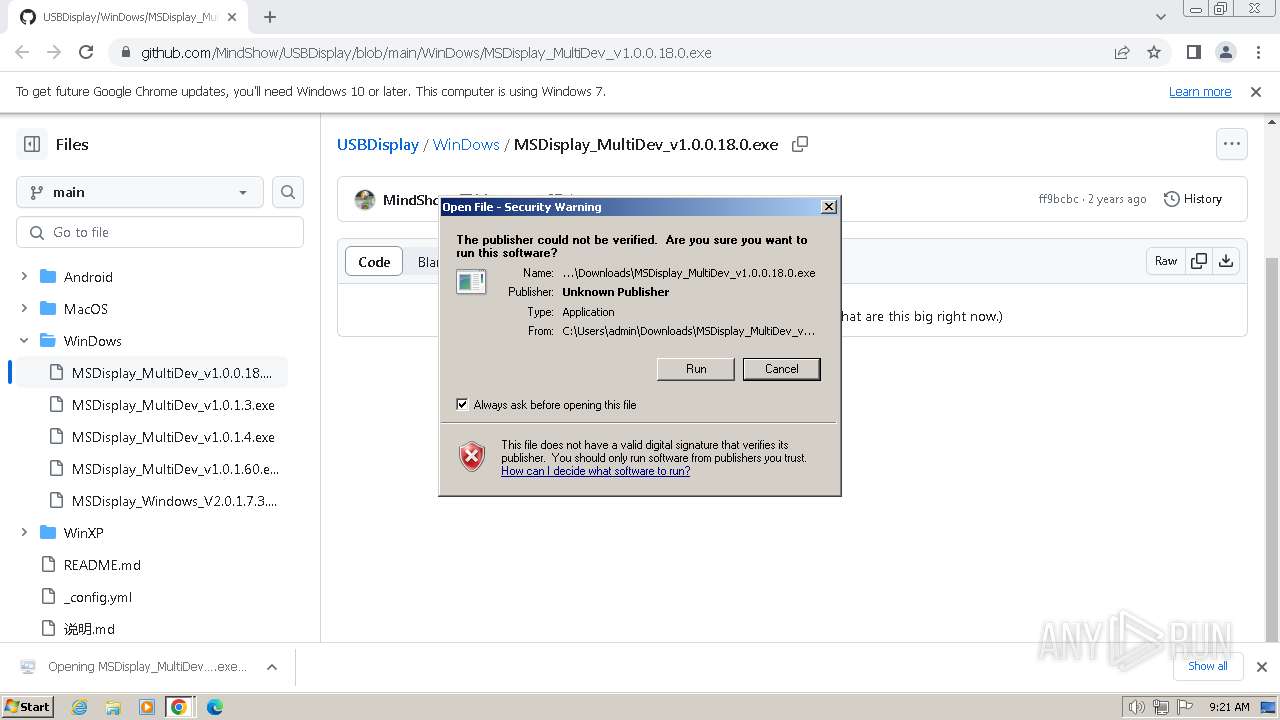
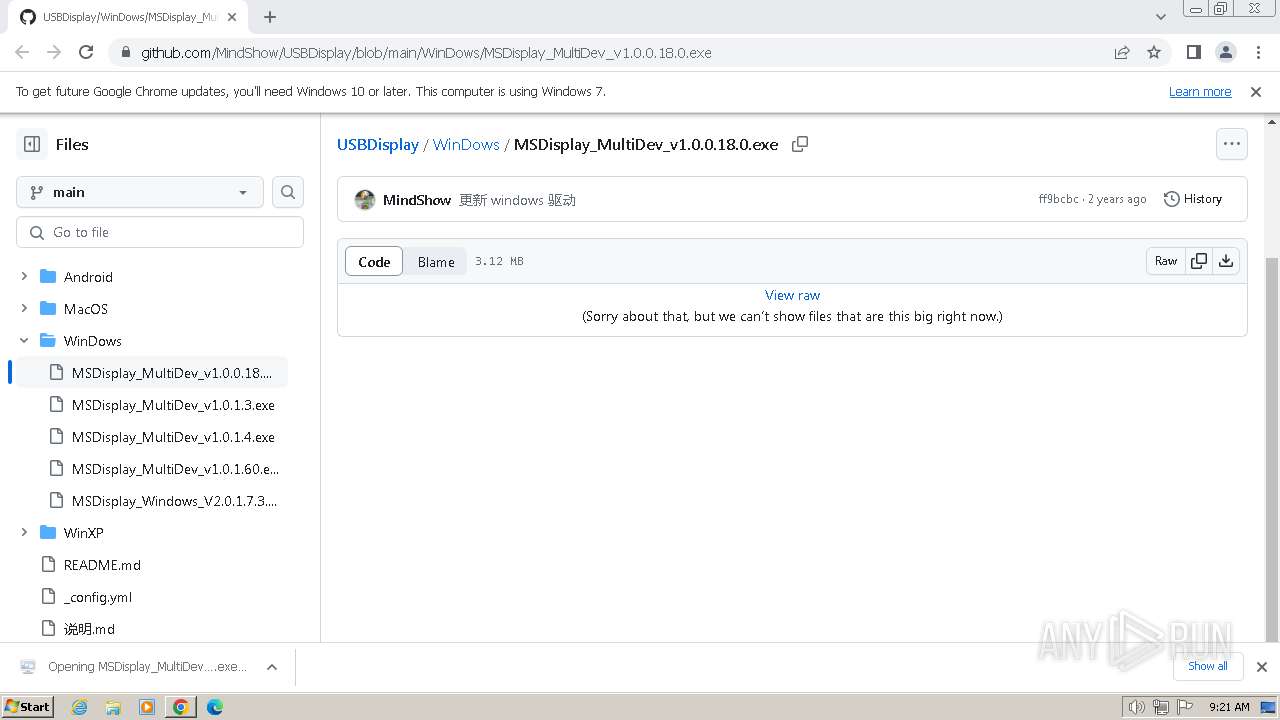
| URL: | https://github.com/MindShow/USBDisplay/blob/main/WinDows/MSDisplay_MultiDev_v1.0.0.18.0.exe |
| Full analysis: | https://app.any.run/tasks/9933da7b-2e2e-4307-bece-023ef77eb0f6 |
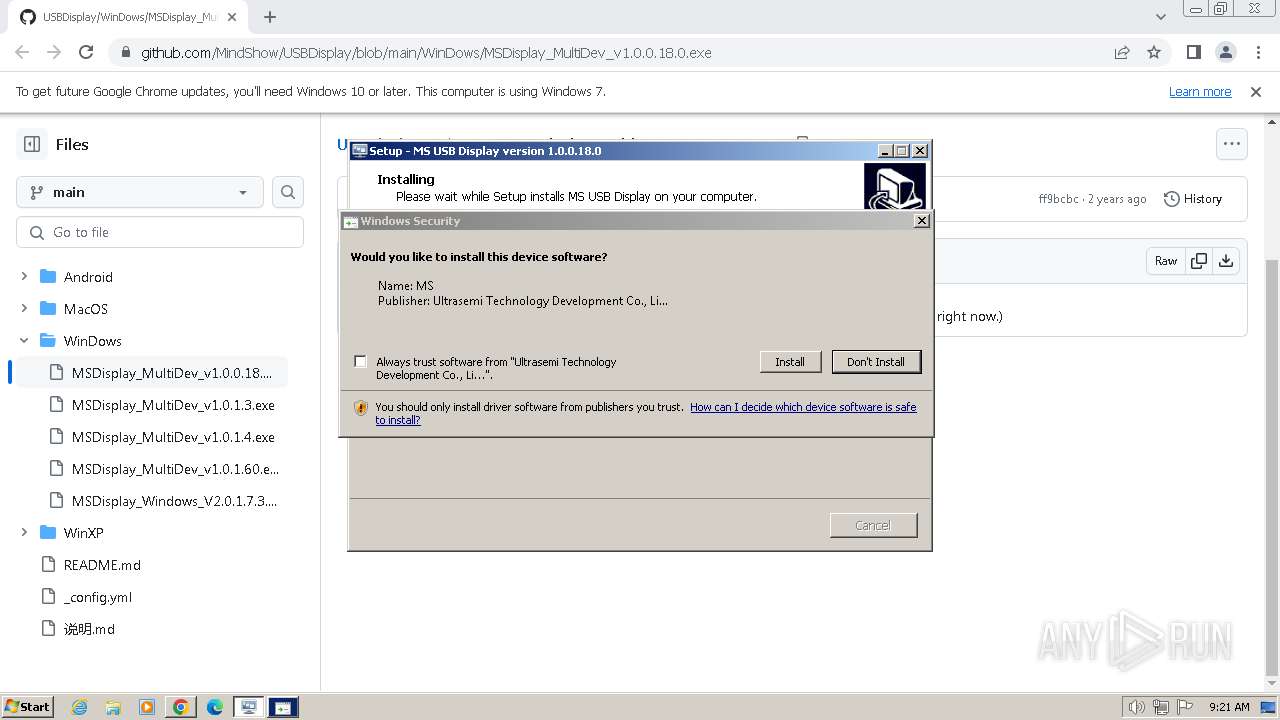
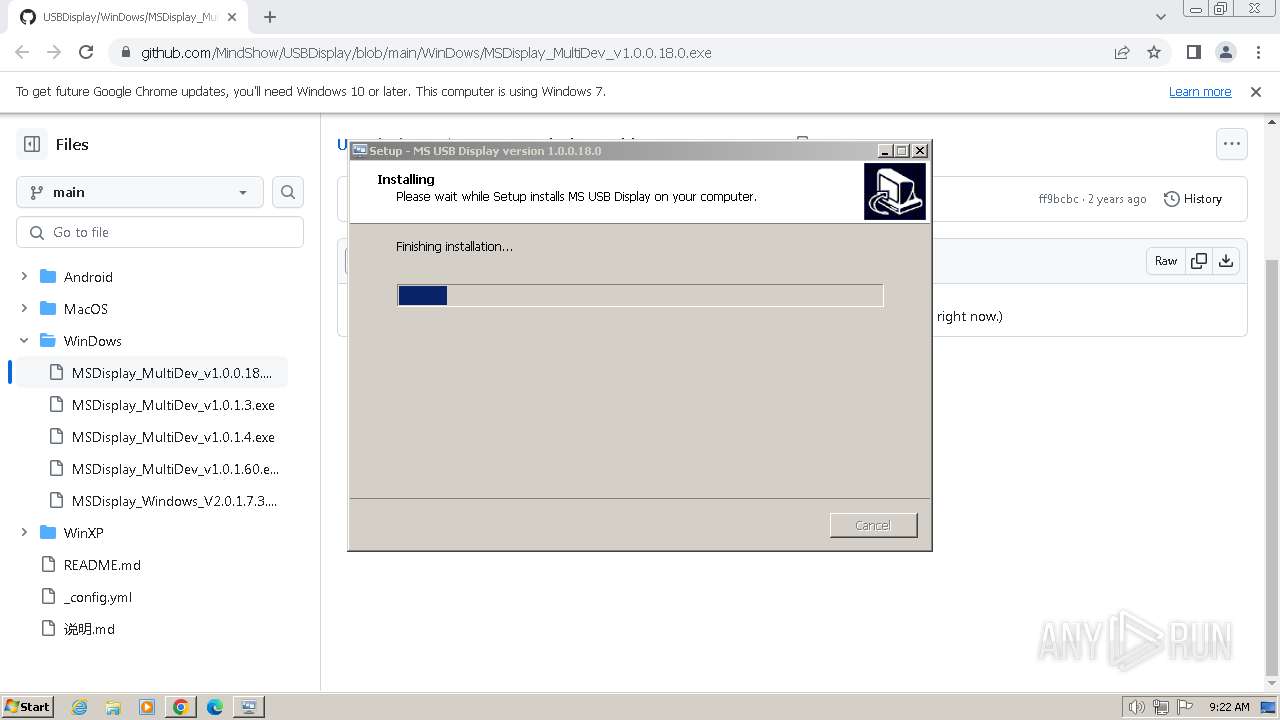
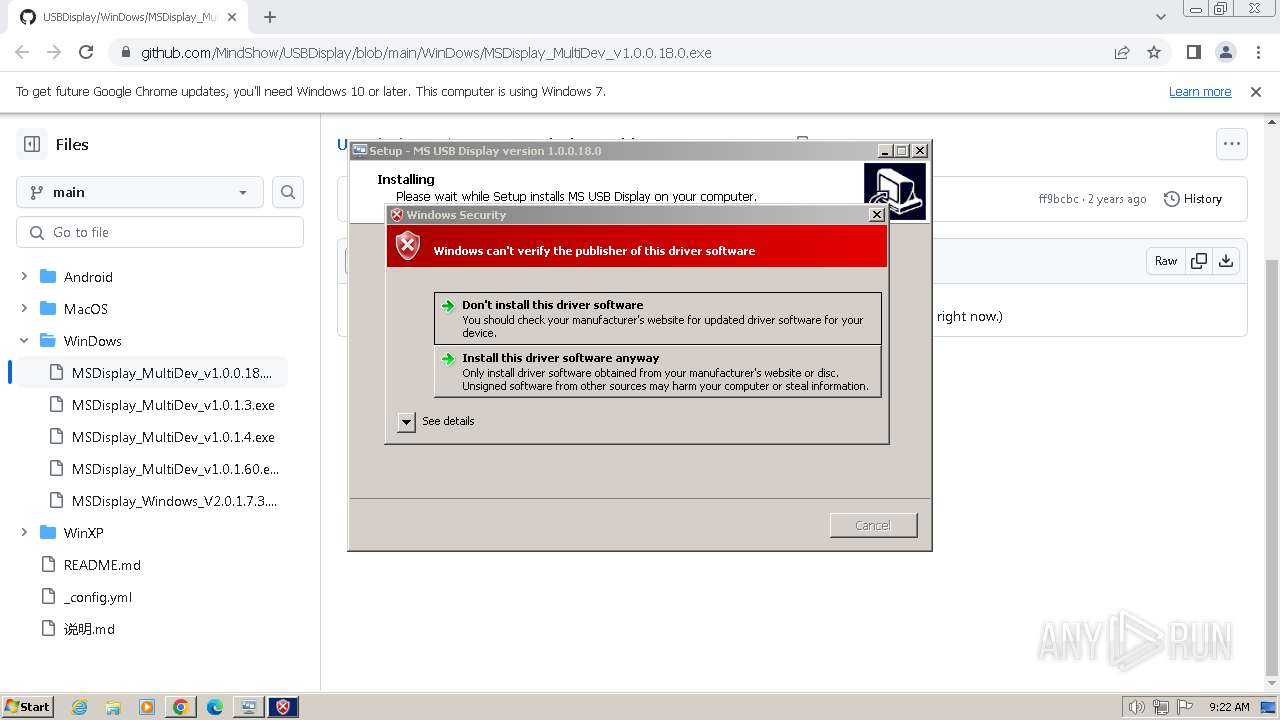
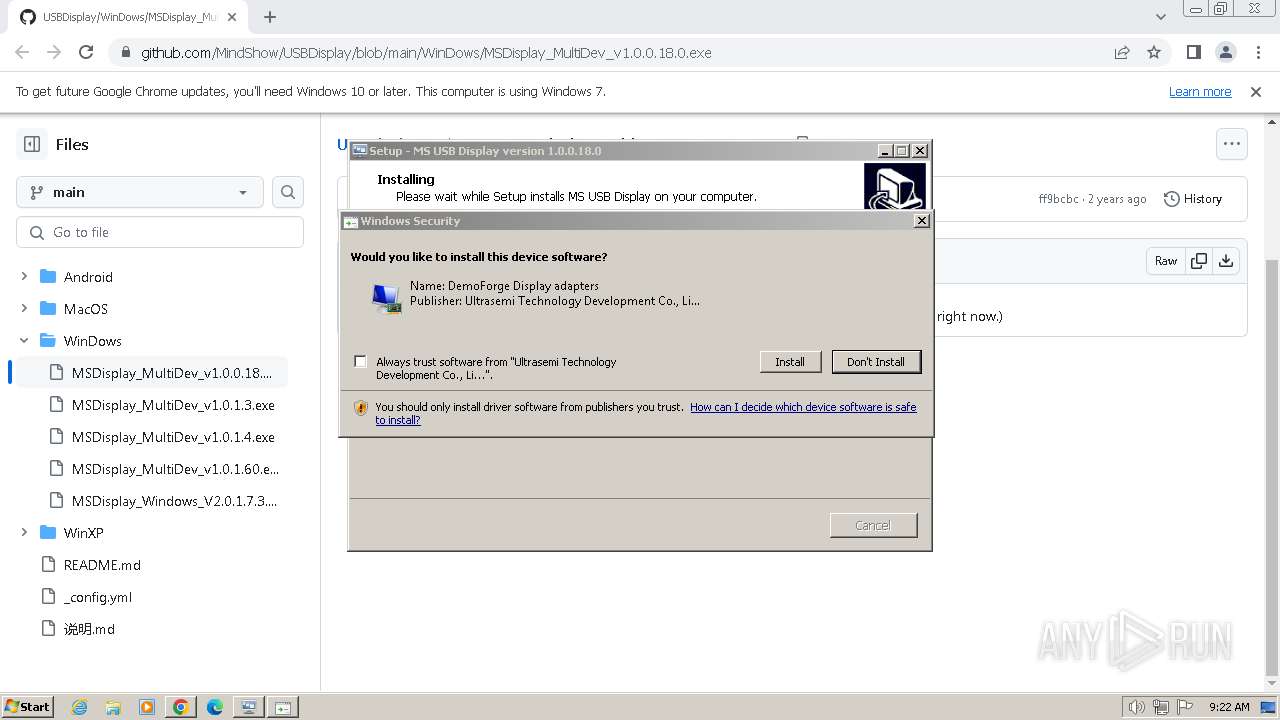
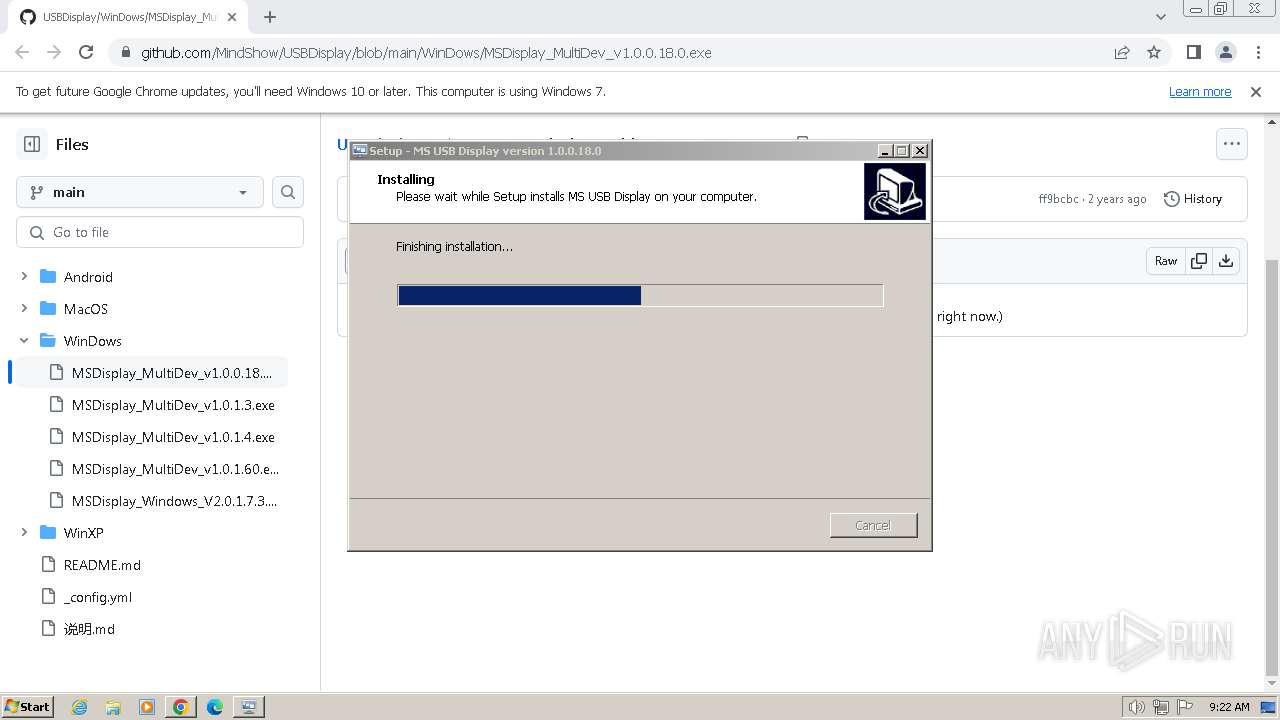
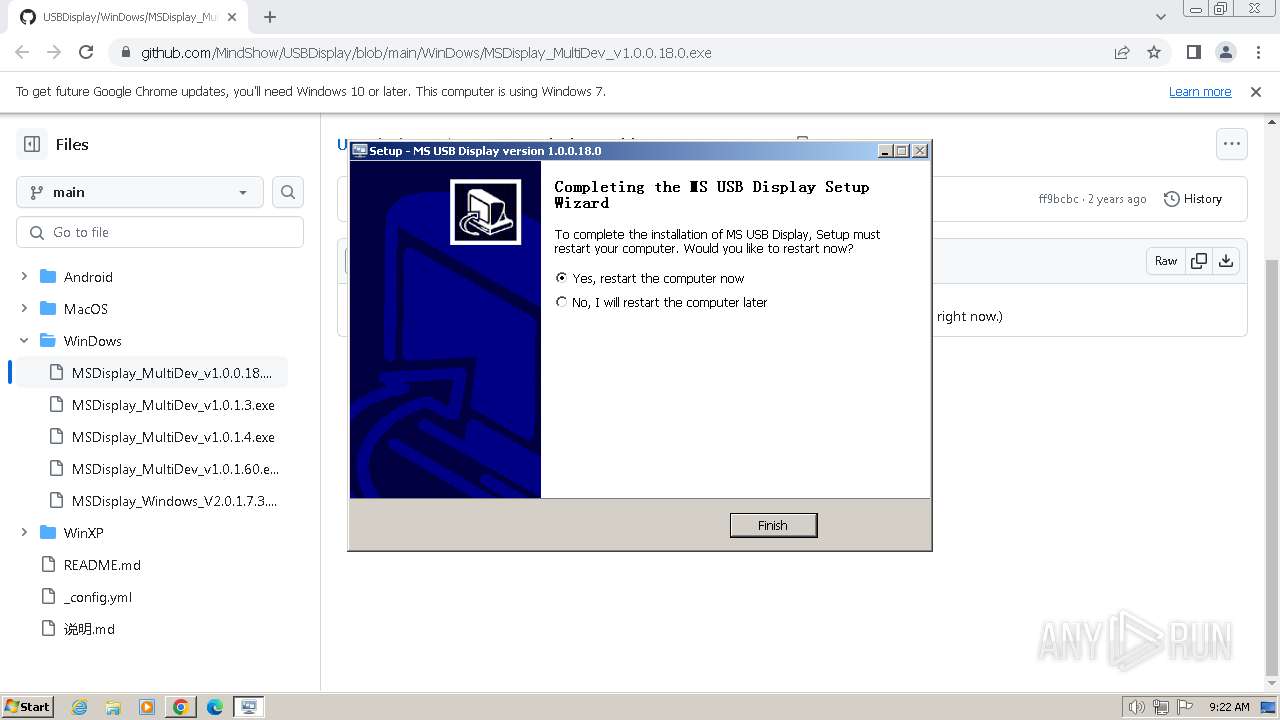
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2024, 09:21:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3BB9D1D315E0B60F274D4F0AB16ED783 |
| SHA1: | 70E10878D5F267B01F09B2D7F4AD5775E4322176 |
| SHA256: | 746F3717603A7AB152004CB227A83A71B200CB8E1AAFB89D385672B28F613E31 |
| SSDEEP: | 3:N8tEddANKuAa6Ec47IERdK9b616bRPbiVLACn:2u3Asa614MsdK9bE6bZb2Jn |
MALICIOUS
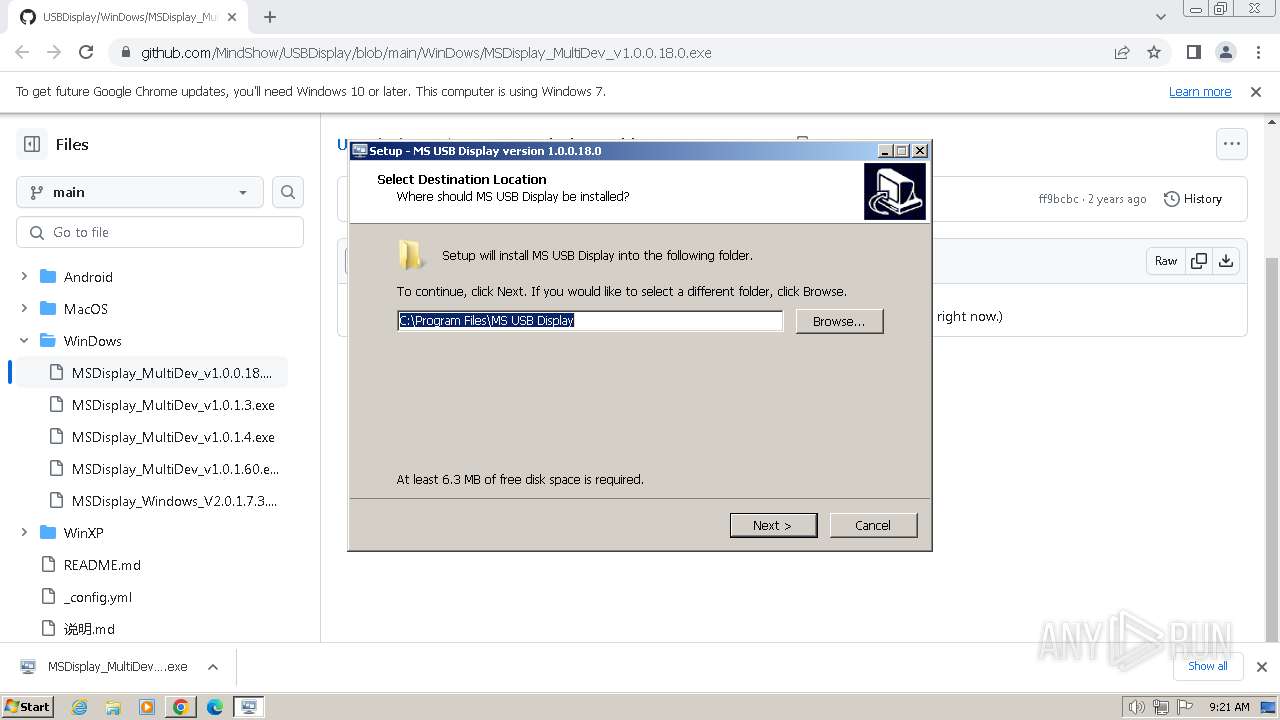
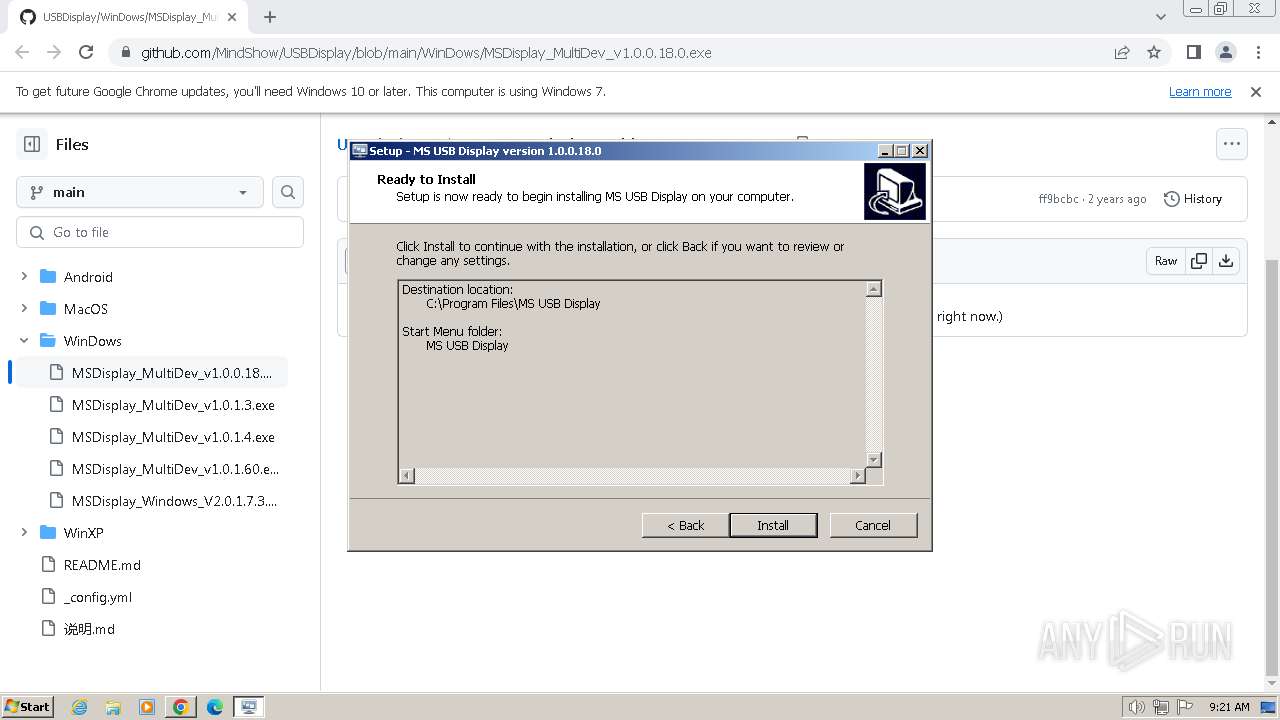
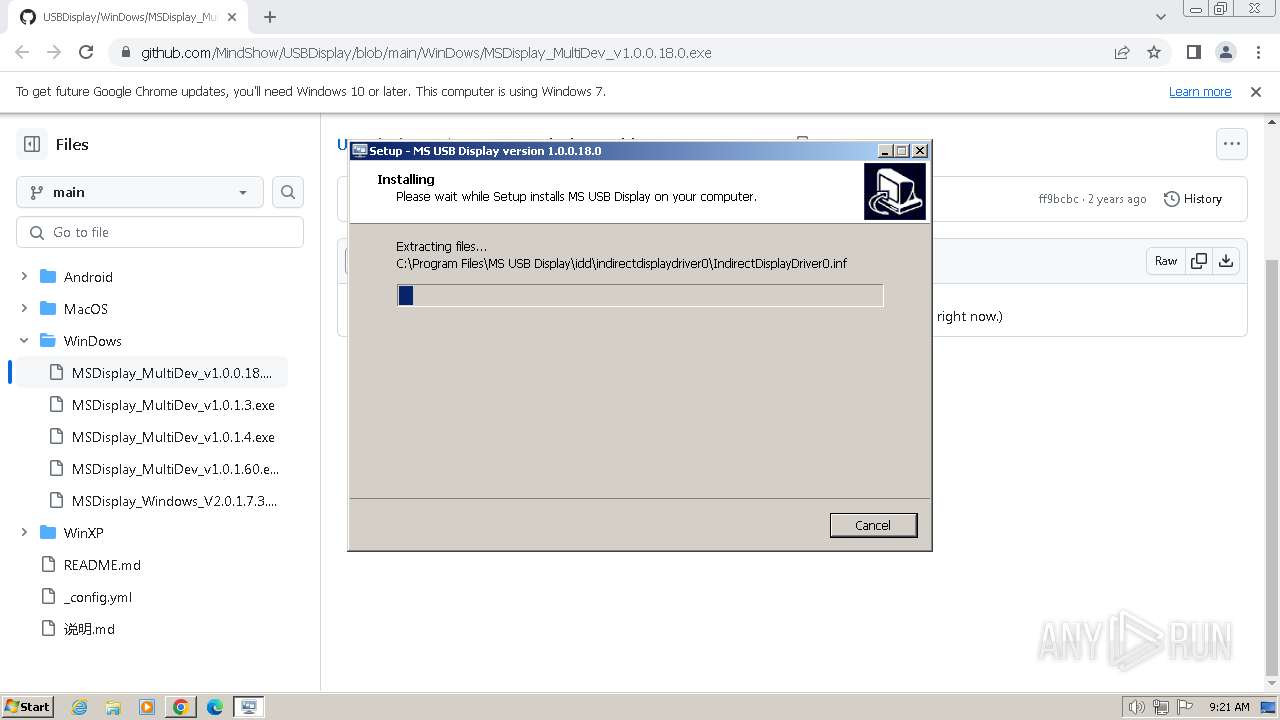
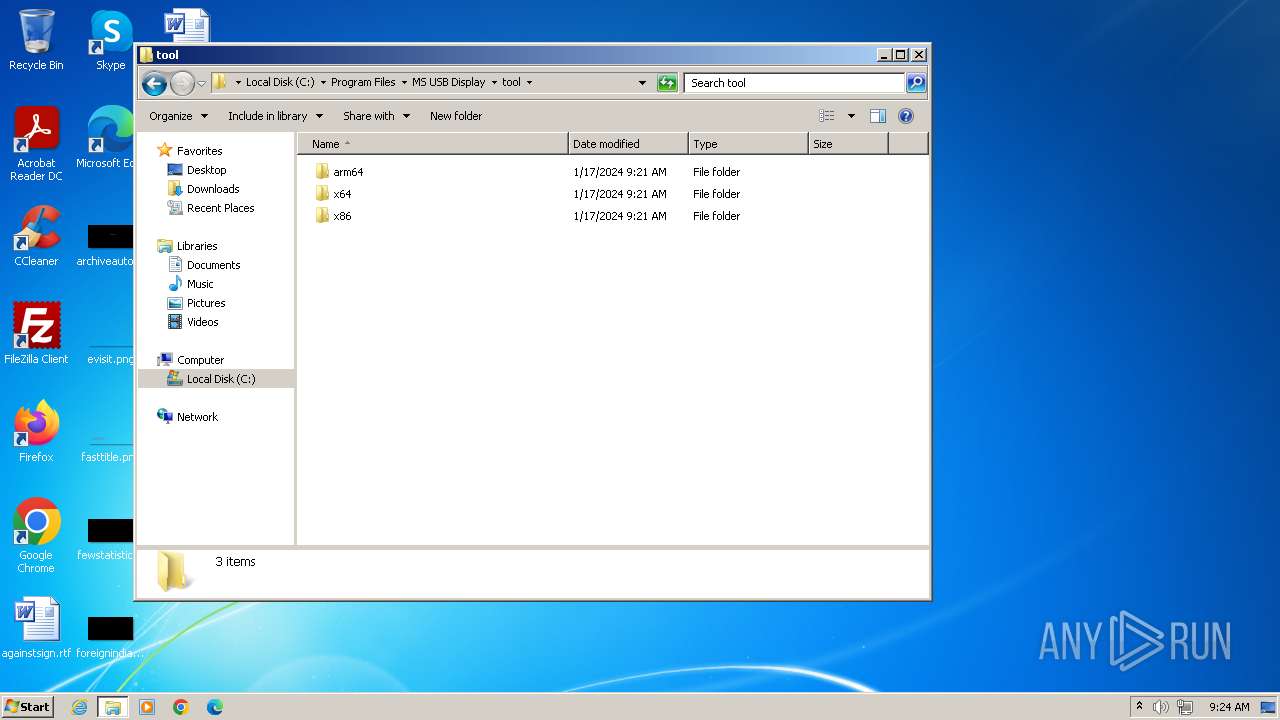
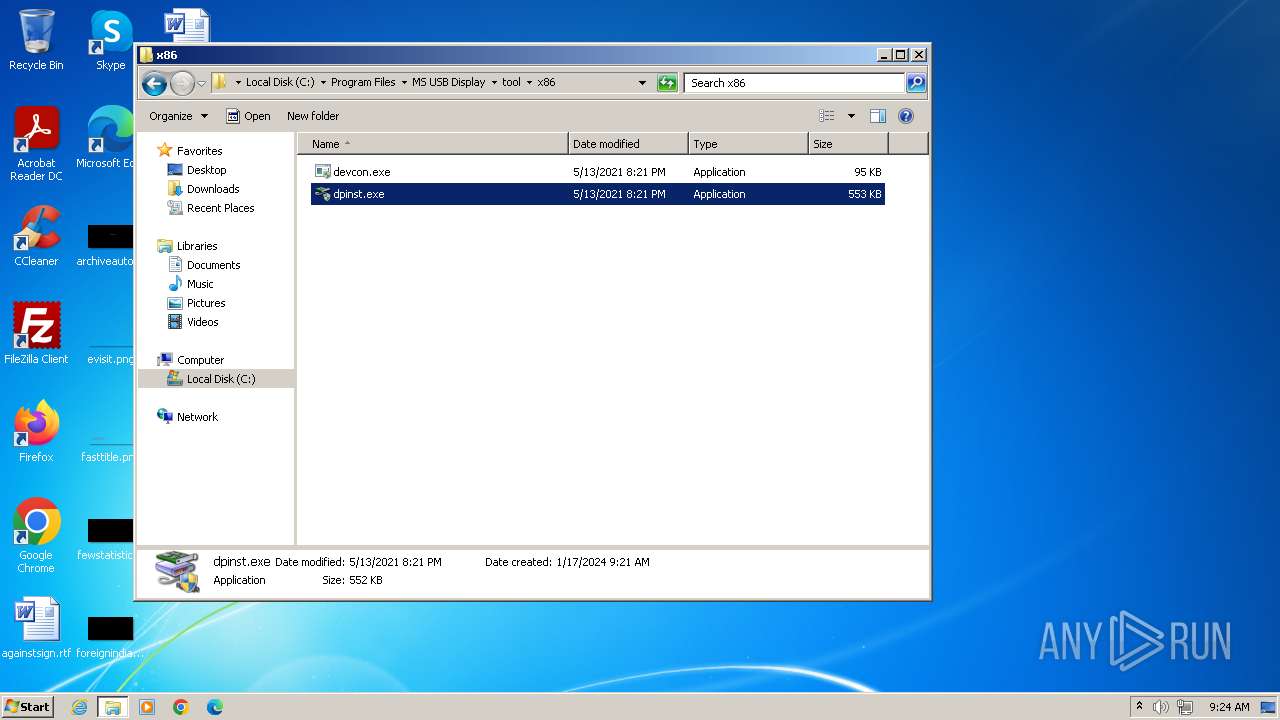
Drops the executable file immediately after the start
- MSDisplay_MultiDev_v1.0.0.18.0.exe (PID: 2972)
- devcon.exe (PID: 2796)
- MSDisplay_MultiDev_v1.0.0.18.0.exe (PID: 2508)
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2820)
- drvinst.exe (PID: 2676)
- devcon.exe (PID: 2104)
- drvinst.exe (PID: 3492)
- drvinst.exe (PID: 1020)
- devcon.exe (PID: 1984)
- drvinst.exe (PID: 1376)
- drvinst.exe (PID: 3076)
Creates a writable file in the system directory
- drvinst.exe (PID: 2676)
- drvinst.exe (PID: 3492)
- drvinst.exe (PID: 1020)
- drvinst.exe (PID: 1376)
- drvinst.exe (PID: 3076)
SUSPICIOUS
Executable content was dropped or overwritten
- MSDisplay_MultiDev_v1.0.0.18.0.exe (PID: 2508)
- MSDisplay_MultiDev_v1.0.0.18.0.exe (PID: 2972)
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2820)
- devcon.exe (PID: 2796)
- drvinst.exe (PID: 2676)
- devcon.exe (PID: 2104)
- drvinst.exe (PID: 1020)
- drvinst.exe (PID: 1376)
- devcon.exe (PID: 1984)
- drvinst.exe (PID: 3492)
- drvinst.exe (PID: 3076)
Reads the Windows owner or organization settings
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2820)
Process drops legitimate windows executable
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2820)
Drops a system driver (possible attempt to evade defenses)
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2820)
- drvinst.exe (PID: 2676)
- devcon.exe (PID: 2796)
- devcon.exe (PID: 2104)
- drvinst.exe (PID: 3492)
- drvinst.exe (PID: 1376)
- devcon.exe (PID: 1984)
- drvinst.exe (PID: 1020)
- drvinst.exe (PID: 3076)
The process drops C-runtime libraries
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2820)
Creates files in the driver directory
- drvinst.exe (PID: 2676)
- drvinst.exe (PID: 3492)
- drvinst.exe (PID: 1020)
- drvinst.exe (PID: 1376)
- drvinst.exe (PID: 3076)
Reads security settings of Internet Explorer
- devcon.exe (PID: 2104)
- devcon.exe (PID: 1984)
Executes as Windows Service
- VSSVC.exe (PID: 3104)
Checks Windows Trust Settings
- drvinst.exe (PID: 2676)
- devcon.exe (PID: 2104)
- drvinst.exe (PID: 1020)
- drvinst.exe (PID: 3492)
- devcon.exe (PID: 1984)
- drvinst.exe (PID: 1376)
- drvinst.exe (PID: 3076)
Reads settings of System Certificates
- rundll32.exe (PID: 2664)
- devcon.exe (PID: 2104)
- devcon.exe (PID: 1984)
- rundll32.exe (PID: 2928)
- sipnotify.exe (PID: 1512)
Reads the Internet Settings
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2820)
- sipnotify.exe (PID: 1512)
Application launched itself
- WinUsbDisplay.exe (PID: 2016)
The process executes via Task Scheduler
- sipnotify.exe (PID: 1512)
- ctfmon.exe (PID: 1636)
INFO
Manual execution by a user
- wmpnscfg.exe (PID: 1768)
- IMEKLMG.EXE (PID: 1164)
- WinUsbDisplay.exe (PID: 1400)
- wmpnscfg.exe (PID: 2468)
- explorer.exe (PID: 2280)
- wmpnscfg.exe (PID: 2424)
- IMEKLMG.EXE (PID: 128)
Application launched itself
- chrome.exe (PID: 2040)
Drops the executable file immediately after the start
- chrome.exe (PID: 2040)
The process uses the downloaded file
- chrome.exe (PID: 1860)
- chrome.exe (PID: 2040)
Executable content was dropped or overwritten
- chrome.exe (PID: 2040)
Reads the computer name
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2372)
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2820)
- wmpnscfg.exe (PID: 1768)
- devcon.exe (PID: 2796)
- drvinst.exe (PID: 2676)
- drvinst.exe (PID: 3492)
- drvinst.exe (PID: 1020)
- devcon.exe (PID: 1984)
- drvinst.exe (PID: 1376)
- devcon.exe (PID: 2104)
- drvinst.exe (PID: 3076)
- devcon.exe (PID: 2876)
- WinUsbDisplay.exe (PID: 2016)
- IMEKLMG.EXE (PID: 128)
- IMEKLMG.EXE (PID: 1164)
- WinUsbDisplay.exe (PID: 1400)
- wmpnscfg.exe (PID: 2424)
- wmpnscfg.exe (PID: 2468)
- MSDisplay_MultiDev_v1.0.0.18.0.exe (PID: 2508)
Create files in a temporary directory
- MSDisplay_MultiDev_v1.0.0.18.0.exe (PID: 2508)
- MSDisplay_MultiDev_v1.0.0.18.0.exe (PID: 2972)
- devcon.exe (PID: 2796)
- devcon.exe (PID: 2104)
- devcon.exe (PID: 1984)
Checks supported languages
- MSDisplay_MultiDev_v1.0.0.18.0.exe (PID: 2508)
- MSDisplay_MultiDev_v1.0.0.18.0.exe (PID: 2972)
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2372)
- wmpnscfg.exe (PID: 1768)
- devcon.exe (PID: 2796)
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2820)
- drvinst.exe (PID: 2676)
- devcon.exe (PID: 2104)
- drvinst.exe (PID: 3492)
- drvinst.exe (PID: 1020)
- devcon.exe (PID: 1984)
- drvinst.exe (PID: 1376)
- drvinst.exe (PID: 3076)
- devcon.exe (PID: 2876)
- WinUsbDisplay.exe (PID: 2016)
- IMEKLMG.EXE (PID: 1164)
- WinUsbDisplay.exe (PID: 1400)
- IMEKLMG.EXE (PID: 128)
- wmpnscfg.exe (PID: 2424)
- wmpnscfg.exe (PID: 2468)
- WinUsbDisplay.exe (PID: 3220)
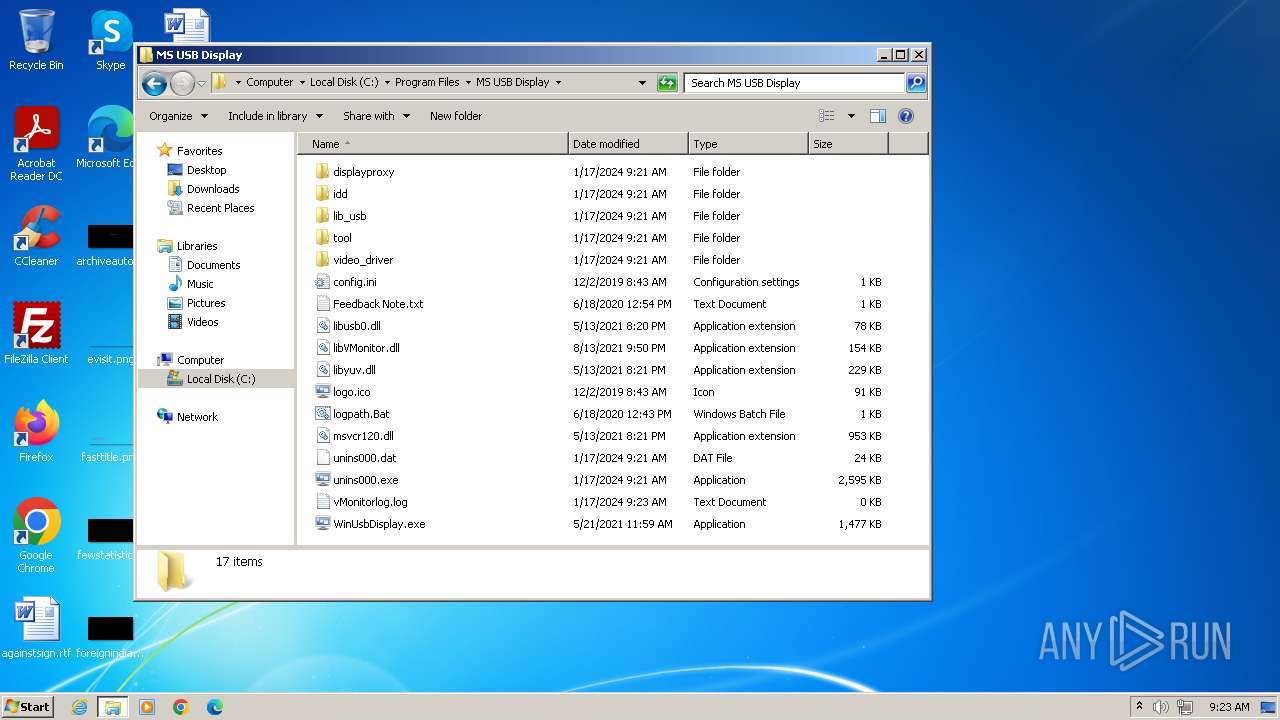
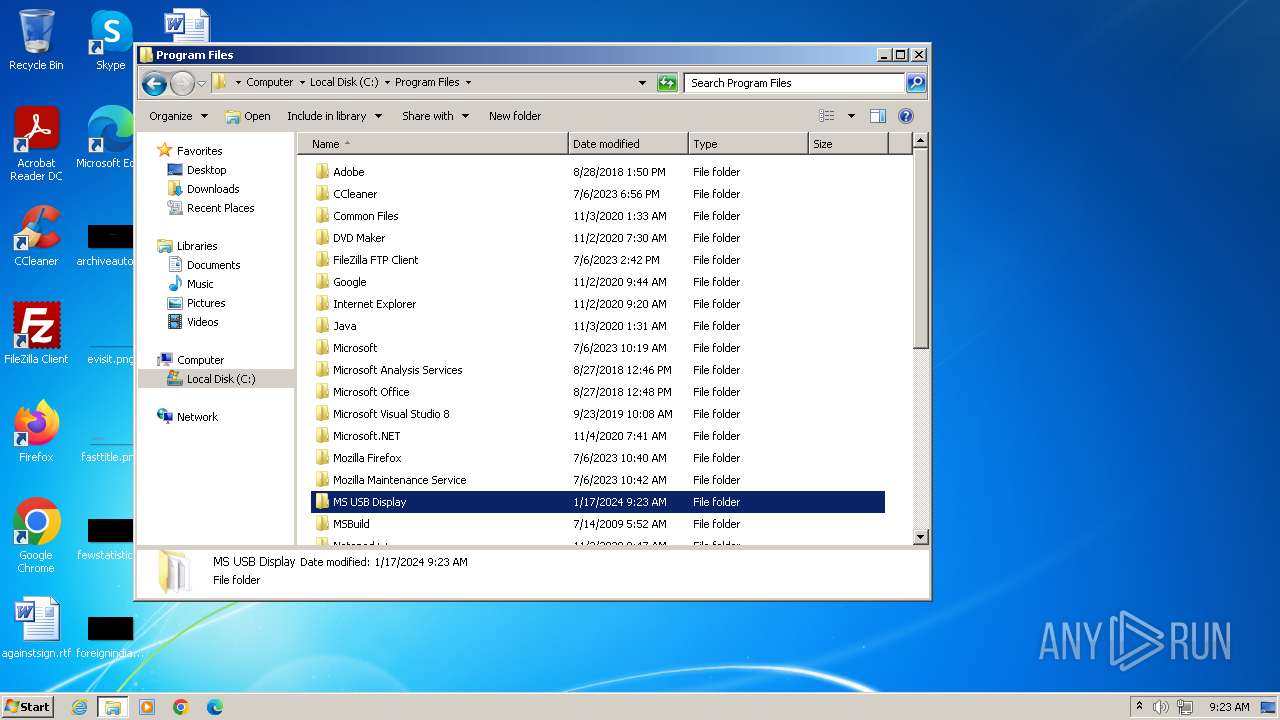
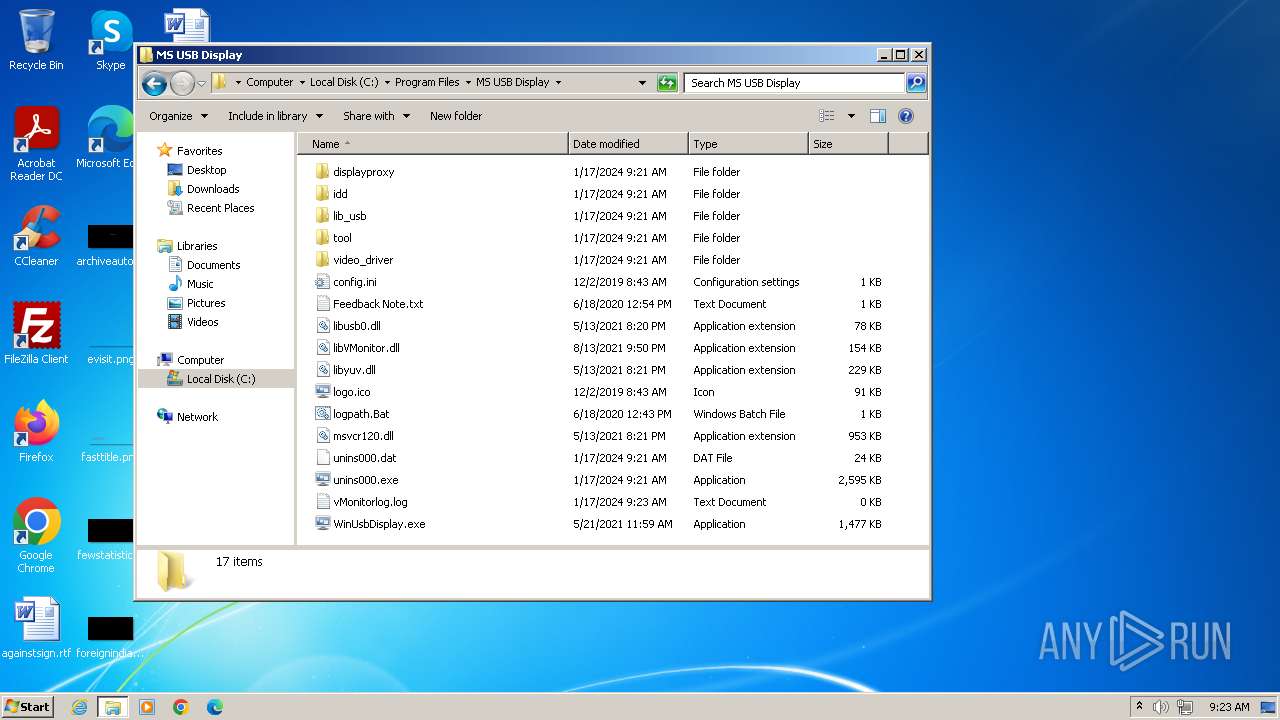
Creates files in the program directory
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2820)
- WinUsbDisplay.exe (PID: 2016)
Creates files or folders in the user directory
- MSDisplay_MultiDev_v1.0.0.18.0.tmp (PID: 2820)
- WinUsbDisplay.exe (PID: 2016)
Reads the machine GUID from the registry
- devcon.exe (PID: 2796)
- drvinst.exe (PID: 2676)
- devcon.exe (PID: 2104)
- drvinst.exe (PID: 3492)
- drvinst.exe (PID: 1020)
- devcon.exe (PID: 1984)
- drvinst.exe (PID: 1376)
- drvinst.exe (PID: 3076)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 2664)
- rundll32.exe (PID: 2928)
- sipnotify.exe (PID: 1512)
Adds/modifies Windows certificates
- drvinst.exe (PID: 2676)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 1164)
- IMEKLMG.EXE (PID: 128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
137
Monitored processes
46
Malicious processes
15
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1812 --field-trial-handle=1144,i,1013283864133590013,9274797999949499544,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1048 --field-trial-handle=1144,i,1013283864133590013,9274797999949499544,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1272 --field-trial-handle=1144,i,1013283864133590013,9274797999949499544,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3572 --field-trial-handle=1144,i,1013283864133590013,9274797999949499544,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3228 --field-trial-handle=1144,i,1013283864133590013,9274797999949499544,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1020 | DrvInst.exe "2" "211" "ROOT\SYSTEM\0001" "C:\Windows\INF\oem4.inf" "displayproxykmd.inf:MNF.NTx86:Display_Inst:15.47.24.217:root\ultrasemidisplayproxy" "62141fc7f" "0000055C" "000005F0" "000005F8" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1496 --field-trial-handle=1144,i,1013283864133590013,9274797999949499544,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 1376 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{4f5b4dd4-4f07-1fa3-1485-8e6fe8a21628}\dfmirage.inf" "0" "670102fe7" "00000600" "WinSta0\Default" "0000055C" "208" "c:\program files\ms usb display\video_driver" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
46 362
Read events
45 794
Write events
560
Delete events
8
Modification events
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
105
Suspicious files
169
Text files
52
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFdfccf.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFdffbd.TMP | text | |
MD5:F5B58F0B08202C8D6DE12514994A84BF | SHA256:F5BA8809B6A3920A11CF31E7F6A1DEC46EF4F4339D6158967CCB1405409D1241 | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:65239F35CB63C76EA1F59EF64F7AAFF4 | SHA256:252EF82CC03FDE4BEF13CF81CD1AC5CE45854212D1A7359035E7A5D6BEDBE229 | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:4E2B7997F4C3647F8D1ADA88339BBBA5 | SHA256:C33226C460208AA10537A23CB5128FD887DCBAA335C7DC8BFFBE08A607CCFDF5 | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe04fd.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2c79e64b-b619-4cd5-a310-5adb2adcea44.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RFe16b0.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
44
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 9.98 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 173 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 5.23 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 168 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 9.83 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 10.0 Kb | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k6wsb2nosvgtb5tlblnxh52bjm_3014/jflookgnkcckhobaglndicnbbgbonegd_3014_all_oxdfroi5hvcpldbydznavsndea.crx3 | unknown | binary | 65.8 Kb | unknown |
1512 | sipnotify.exe | HEAD | 200 | 23.197.138.118:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133499570082500000 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 81.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2040 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
532 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | unknown |
532 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
532 | chrome.exe | 142.250.187.170:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
532 | chrome.exe | 185.199.108.154:443 | github.githubassets.com | FASTLY | US | unknown |
532 | chrome.exe | 185.199.108.133:443 | avatars.githubusercontent.com | FASTLY | US | unknown |
532 | chrome.exe | 142.251.140.42:443 | content-autofill.googleapis.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
github.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
collector.github.com |
| whitelisted |
api.github.com |
| whitelisted |