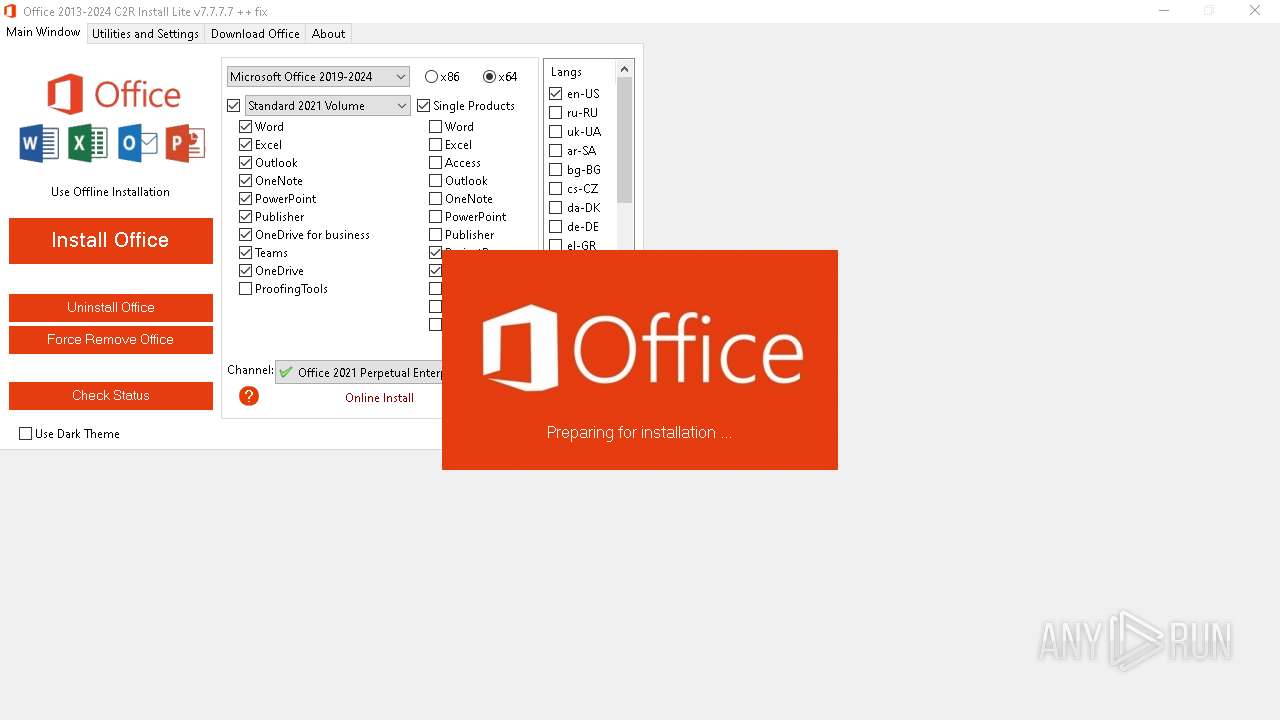
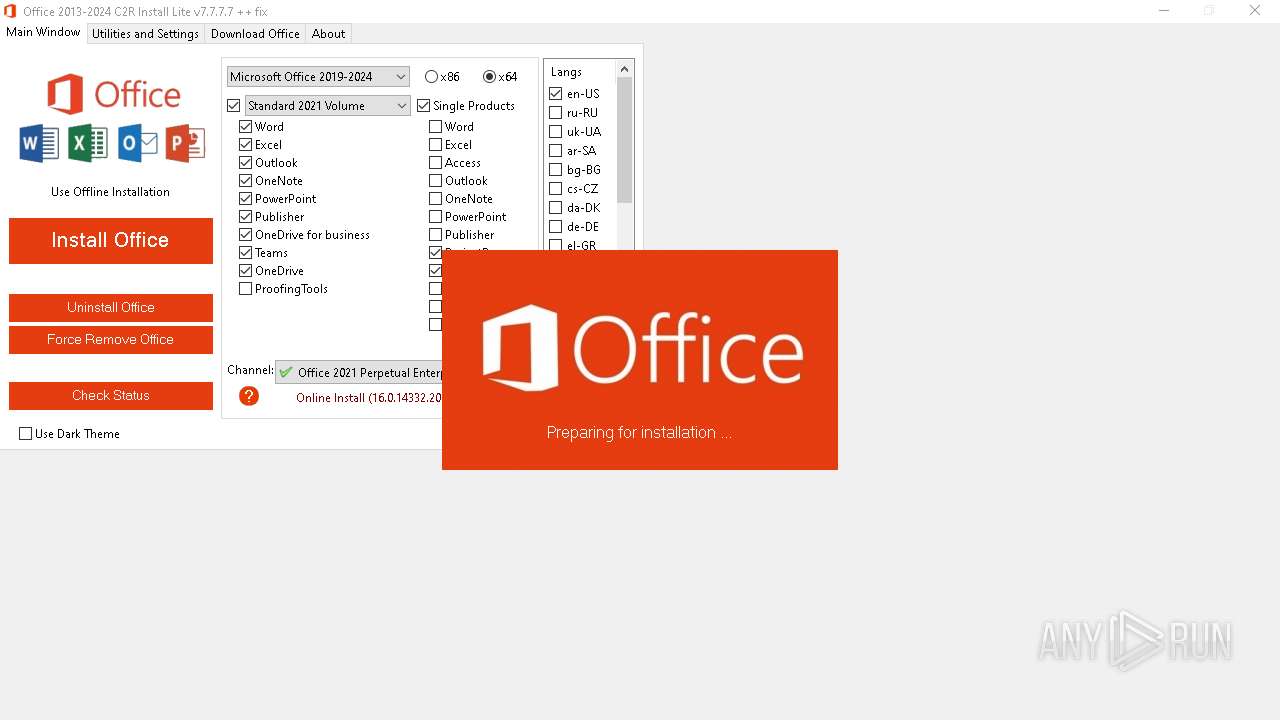
| File name: | OInstallLite.exe |
| Full analysis: | https://app.any.run/tasks/f7d37b51-3ba7-4837-b2bd-fee0ab13456c |
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2024, 13:30:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BF4C0F9C8B84E9AA7E2F050684D76255 |
| SHA1: | EAB1B806EFCD32E2133FAEEC6E29C5BB9B1AB1CA |
| SHA256: | 7469711490EDF0A55F04DBEEA9CC43E59D34985909336978307A0D4FB36E8827 |
| SSDEEP: | 98304:l+l4pdOdytpPOhQUjbXMCmXBFI4dgoj/HdHYjt6jLQJeEGjoIeN7BUOHZe952Uh/:m7 |
MALICIOUS
Uses WMIC.EXE to add exclusions to the Windows Defender
- cmd.exe (PID: 6180)
- cmd.exe (PID: 4092)
SUSPICIOUS
Uses REG/REGEDIT.EXE to modify registry
- OInstallLite.exe (PID: 1104)
Starts CMD.EXE for commands execution
- OInstallLite.exe (PID: 1104)
The process drops C-runtime libraries
- files.dat (PID: 5768)
- expand.exe (PID: 236)
Process drops legitimate windows executable
- files.dat (PID: 5768)
- expand.exe (PID: 236)
Executable content was dropped or overwritten
- OInstallLite.exe (PID: 1104)
- expand.exe (PID: 236)
- files.dat (PID: 5768)
Drops the executable file immediately after the start
- OInstallLite.exe (PID: 1104)
- expand.exe (PID: 236)
- files.dat (PID: 5768)
Found strings related to reading or modifying Windows Defender settings
- OInstallLite.exe (PID: 1104)
Starts POWERSHELL.EXE for commands execution
- OInstallLite.exe (PID: 1104)
Probably download files using WebClient
- OInstallLite.exe (PID: 1104)
The process bypasses the loading of PowerShell profile settings
- OInstallLite.exe (PID: 1104)
Starts SC.EXE for service management
- cmd.exe (PID: 2584)
Uses TASKKILL.EXE to kill process
- OInstallLite.exe (PID: 1104)
Unpacks CAB file
- expand.exe (PID: 236)
- expand.exe (PID: 3812)
Reads security settings of Internet Explorer
- OInstallLite.exe (PID: 1104)
Reads the date of Windows installation
- OInstallLite.exe (PID: 1104)
Starts application with an unusual extension
- cmd.exe (PID: 2580)
Drops 7-zip archiver for unpacking
- OInstallLite.exe (PID: 1104)
INFO
Reads Environment values
- OInstallLite.exe (PID: 1104)
Checks supported languages
- OInstallLite.exe (PID: 1104)
- expand.exe (PID: 236)
- expand.exe (PID: 3812)
- OfficeClickToRun.exe (PID: 5124)
- OfficeClickToRun.exe (PID: 1480)
- files.dat (PID: 5768)
Reads the computer name
- OInstallLite.exe (PID: 1104)
- OfficeClickToRun.exe (PID: 5124)
- OfficeClickToRun.exe (PID: 1480)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6328)
- WMIC.exe (PID: 4252)
Reads Microsoft Office registry keys
- OInstallLite.exe (PID: 1104)
- OfficeClickToRun.exe (PID: 5124)
- OfficeClickToRun.exe (PID: 1480)
Disables trace logs
- powershell.exe (PID: 5504)
- powershell.exe (PID: 1964)
- powershell.exe (PID: 6480)
Checks proxy server information
- powershell.exe (PID: 5504)
- powershell.exe (PID: 1964)
- powershell.exe (PID: 6480)
- OfficeClickToRun.exe (PID: 5124)
- OfficeClickToRun.exe (PID: 1480)
Create files in a temporary directory
- OInstallLite.exe (PID: 1104)
- OfficeClickToRun.exe (PID: 5124)
Creates files in the program directory
- OInstallLite.exe (PID: 1104)
- expand.exe (PID: 3812)
- expand.exe (PID: 236)
- OfficeClickToRun.exe (PID: 1480)
Reads the machine GUID from the registry
- expand.exe (PID: 3812)
- expand.exe (PID: 236)
- OfficeClickToRun.exe (PID: 1480)
The process uses the downloaded file
- OInstallLite.exe (PID: 1104)
Process checks computer location settings
- OInstallLite.exe (PID: 1104)
Executes as Windows Service
- OfficeClickToRun.exe (PID: 1480)
Creates files or folders in the user directory
- OfficeClickToRun.exe (PID: 5124)
Reads the software policy settings
- OfficeClickToRun.exe (PID: 1480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.3) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.1) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:05 07:18:30+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 1056256 |
| InitializedDataSize: | 10825728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.7.7.7 |
| ProductVersionNumber: | 7.7.7.7 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| ProductName: | Office 2013-2024 C2R Install Lite |
| FileDescription: | Office 2013-2024 C2R Install Lite |
Total processes
174
Monitored processes
48
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | "expand" i640.cab -F:* "C:\Program Files\Common Files\Microsoft Shared\ClickToRun" | C:\Windows\SysWOW64\expand.exe | OInstallLite.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 5.00 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 320 | "taskkill.exe" /t /f /IM IntegratedOffice.exe | C:\Windows\SysWOW64\taskkill.exe | — | OInstallLite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1104 | "C:\Users\admin\Desktop\OInstallLite.exe" | C:\Users\admin\Desktop\OInstallLite.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Office 2013-2024 C2R Install Lite Modules
| |||||||||||||||
| 1184 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1480 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe" /service | C:\Program Files\Common Files\microsoft shared\ClickToRun\OfficeClickToRun.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Office Click-to-Run (SxS) Version: 16.0.14332.20761 Modules
| |||||||||||||||
| 1920 | "C:\WINDOWS\Sysnative\reg.exe" add "HKLM\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /v KeyManagementServicePort /t REG_SZ /d 1688 /f | C:\Windows\System32\reg.exe | — | OInstallLite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1964 | "powershell" -command "& { (New-Object Net.WebClient).DownloadFile('http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/i640.cab', 'C:\Users\admin\AppData\Local\Temp\over623743\i640.cab') }" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | OInstallLite.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
39 376
Read events
39 111
Write events
137
Delete events
128
Modification events
| (PID) Process: | (4980) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (5504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
228
Suspicious files
54
Text files
61
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1964 | powershell.exe | C:\Users\admin\AppData\Local\Temp\over623743\i640.cab | — | |
MD5:— | SHA256:— | |||
| 5768 | files.dat | C:\Users\admin\Desktop\files\x64\cleanospp.exe | executable | |
MD5:D3467CB7B83B654C2D05407DC7BA2360 | SHA256:EDF85F4E2EF1A427B34265A22F261D664EC78DE90C3B5DA4174EF28558C8522A | |||
| 1104 | OInstallLite.exe | C:\Users\admin\Desktop\files\files.dat | executable | |
MD5:BB5569B15D68C10B7FF2D96B45825120 | SHA256:4E3B13B56BEC0E41778E6506430282BBBD75CCAA600FD4B645CE37DD95B44C8E | |||
| 1104 | OInstallLite.exe | C:\Users\admin\Desktop\files\Configure.xml | text | |
MD5:46C7CEAD7726B1530BB4C096A648137E | SHA256:BF9CA6C946B42346C8E4B5B1EDCEAA9385069F680F53BEA30C9B16529C39EA8B | |||
| 5768 | files.dat | C:\Users\admin\Desktop\files\x86\cleanospp.exe | executable | |
MD5:98821A7A5737D656633D10A3AFB724BD | SHA256:04BA4487F95290E0B0557B44300C18F637FBAF0872EE96E3111013B8A1539F25 | |||
| 5504 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:4CBE867E20C39C1F29365AE220A0E809 | SHA256:F032DB17B9A93A9596D6139D2550E160D8A72F3626FFCDE7E27F2BD4E709FBDB | |||
| 5504 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5poxp4wn.n5j.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1104 | OInstallLite.exe | C:\Users\admin\AppData\Local\Temp\newui.reg | text | |
MD5:7FB2BDA7CA25568909EAB0B872416ADA | SHA256:92DC5F009E30E42D18B80FDCCE0E029DF6D56E387EB38E16C5585A9C5A0B41A7 | |||
| 5504 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ver.txt | text | |
MD5:6A0AF9B9B7EE97F1644A96C32AEE8BAB | SHA256:1D6D457E7D1360485BC3942BE219F3CEC4ACD5423DF3801A567542DB357D2DDA | |||
| 5504 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4xphzill.da1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
45
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1964 | powershell.exe | GET | 200 | 23.48.23.164:80 | http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/i640.cab | unknown | — | — | whitelisted |
6480 | powershell.exe | GET | 200 | 152.199.21.175:80 | http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/i641033.cab | unknown | — | — | whitelisted |
3504 | svchost.exe | GET | 206 | 152.199.21.175:80 | http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s640.cab | unknown | — | — | whitelisted |
3504 | svchost.exe | GET | 206 | 152.199.21.175:80 | http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s640.cab | unknown | — | — | whitelisted |
3504 | svchost.exe | GET | 206 | 152.199.21.175:80 | http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s640.cab | unknown | — | — | whitelisted |
3504 | svchost.exe | GET | 206 | 152.199.21.175:80 | http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s640.cab | unknown | — | — | whitelisted |
3504 | svchost.exe | GET | 206 | 152.199.21.175:80 | http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s640.cab | unknown | — | — | whitelisted |
3504 | svchost.exe | GET | 206 | 152.199.21.175:80 | http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s640.cab | unknown | — | — | whitelisted |
3504 | svchost.exe | GET | 206 | 152.199.21.175:80 | http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s641036.cab | unknown | — | — | whitelisted |
3504 | svchost.exe | GET | 206 | 152.199.21.175:80 | http://officecdn.microsoft.com/pr/5030841d-c919-4594-8d2d-84ae4f96e58e/Office/Data/16.0.14332.20763/s641036.cab | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6052 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6160 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4324 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5504 | powershell.exe | 52.109.89.117:443 | mrodevicemgr.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1964 | powershell.exe | 23.48.23.164:80 | officecdn.microsoft.com | Akamai International B.V. | DE | whitelisted |
6480 | powershell.exe | 152.199.21.175:80 | officecdn.microsoft.com | EDGECAST | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
mrodevicemgr.officeapps.live.com |
| whitelisted |
officecdn.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
geo.prod.do.dsp.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
geover.prod.do.dsp.mp.microsoft.com |
| whitelisted |