| File name: | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe |
| Full analysis: | https://app.any.run/tasks/a8aa73a1-add9-44ea-bf02-2050ba7027e9 |
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2024, 17:26:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | F2D84CD8DDEE28EE85B223BB65E24492 |
| SHA1: | 8FD9E40E64D0D43A329BA2B43406ECAA35AD455E |
| SHA256: | 7457B690797DB097D1BB68ABEB3A4D89C3125EFB259D775E21847E3D3680C33F |
| SSDEEP: | 12288:pA5zlwP7ck4LbsfRSIVIitfMQeB5z4RYa5lH:pA5zlwPgkUbsfRSMIitfLeB58H5lH |
MALICIOUS
Drops the executable file immediately after the start
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
Unusual connection from system programs
- rundll32.exe (PID: 3244)
SUSPICIOUS
The process creates files with name similar to system file names
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
Executable content was dropped or overwritten
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
Reads the Internet Settings
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
- rundll32.exe (PID: 3244)
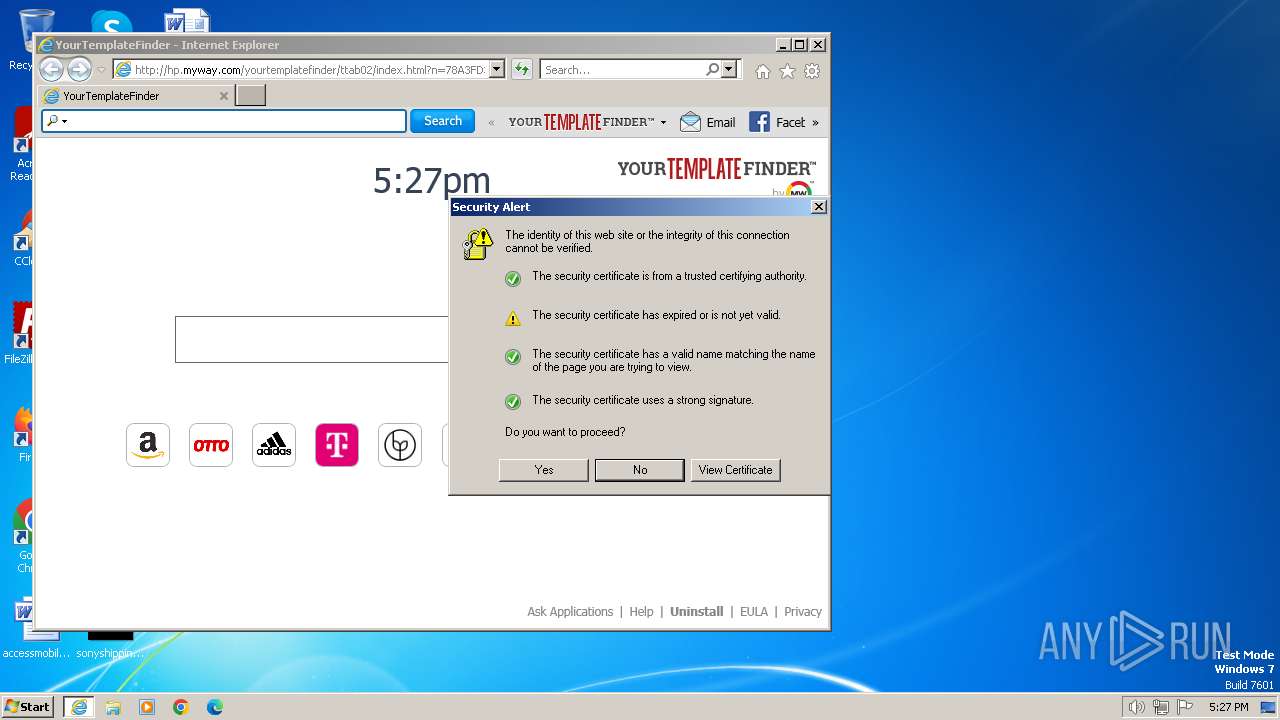
Reads settings of System Certificates
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
- rundll32.exe (PID: 3244)
Checks Windows Trust Settings
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
Reads security settings of Internet Explorer
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
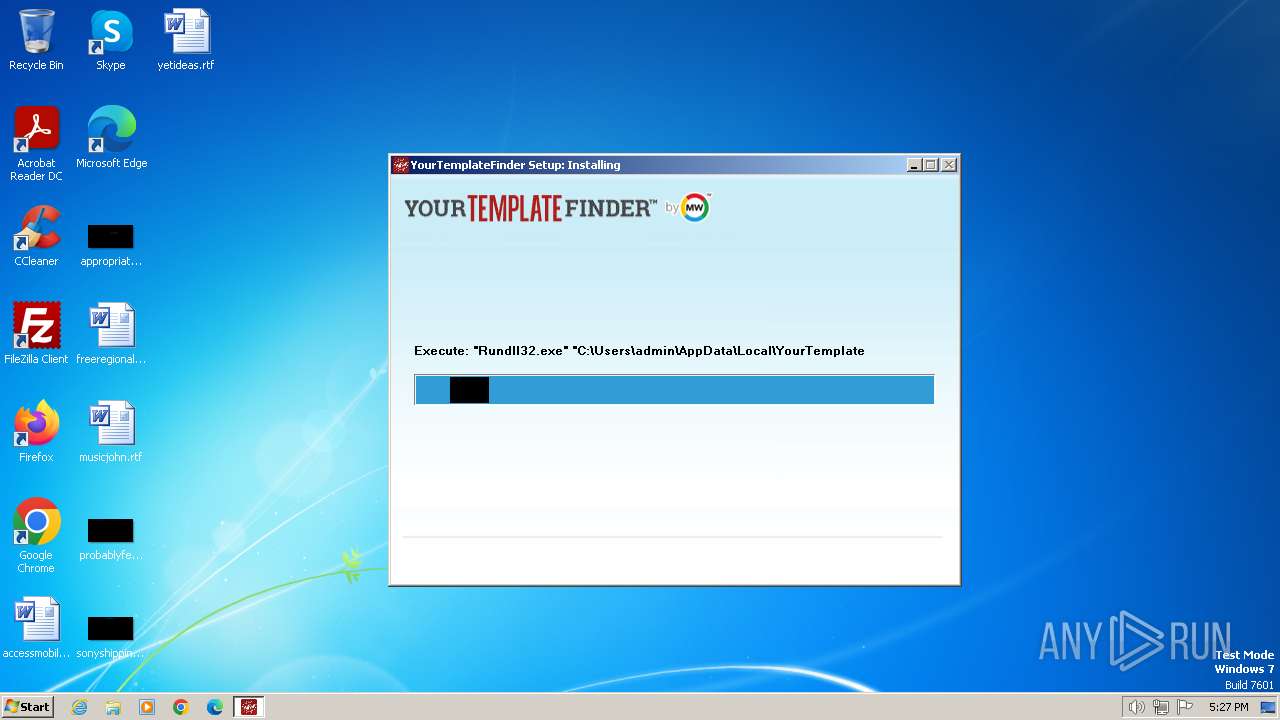
Uses RUNDLL32.EXE to load library
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
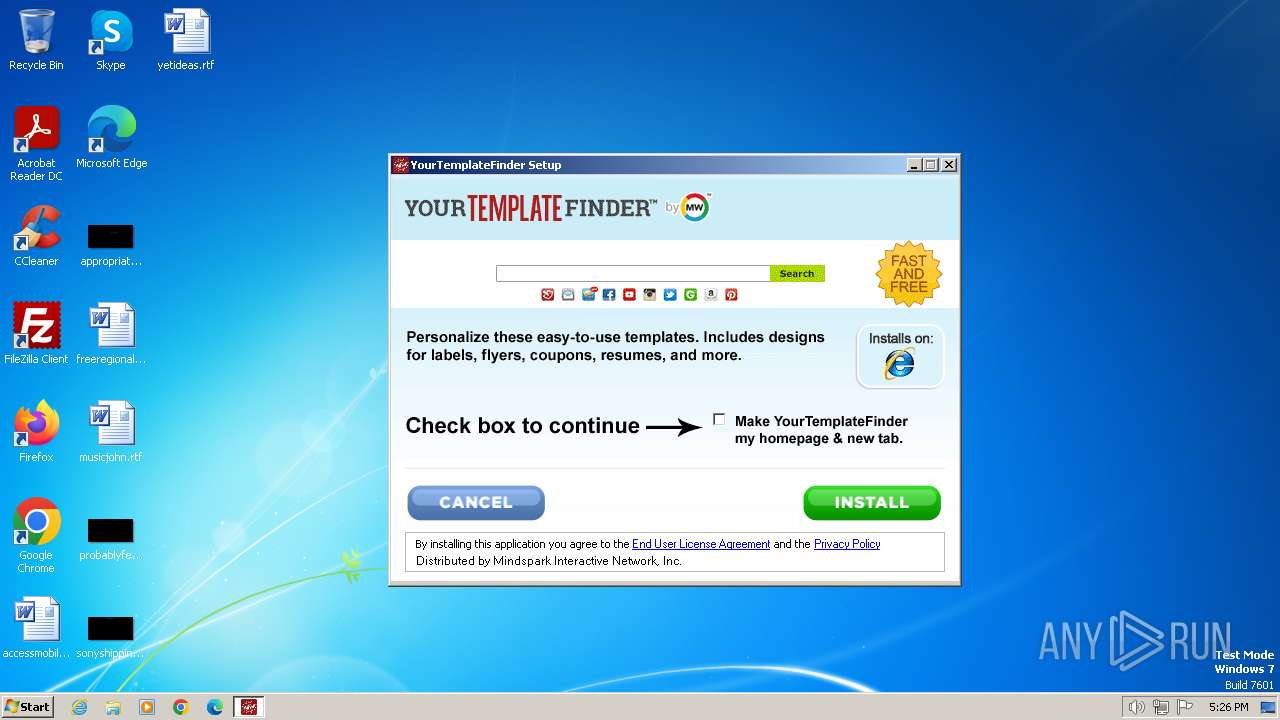
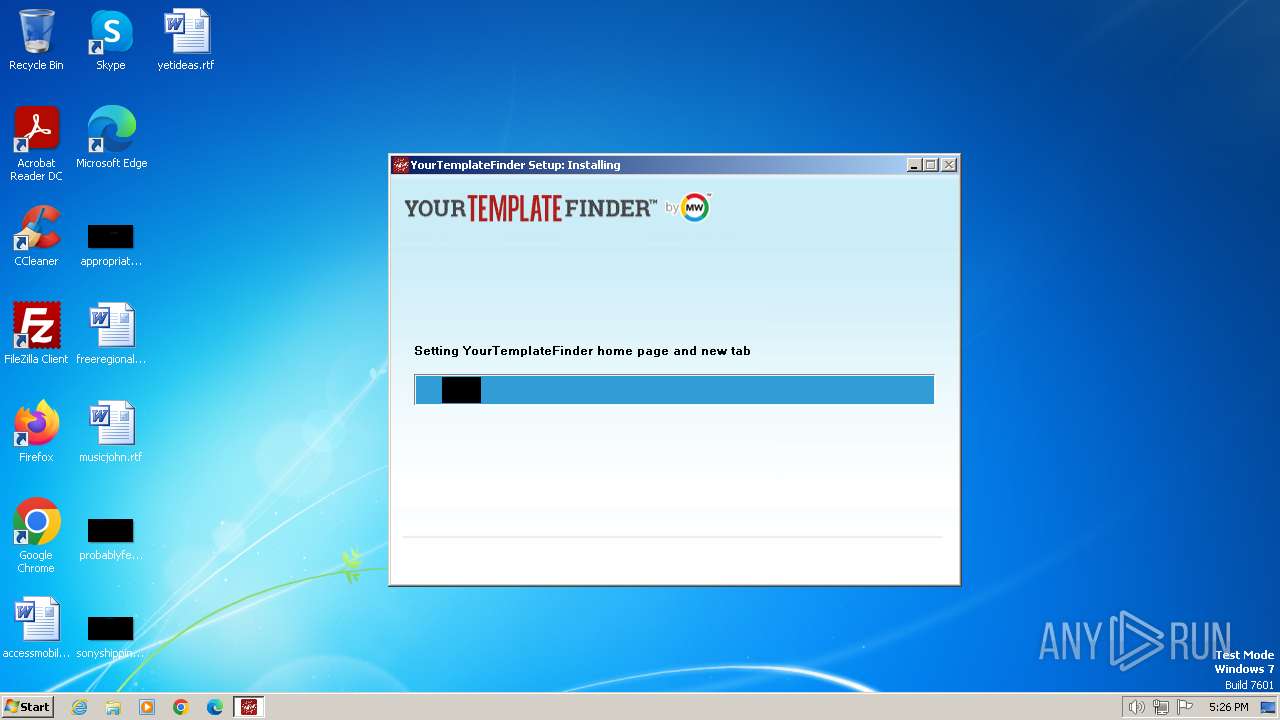
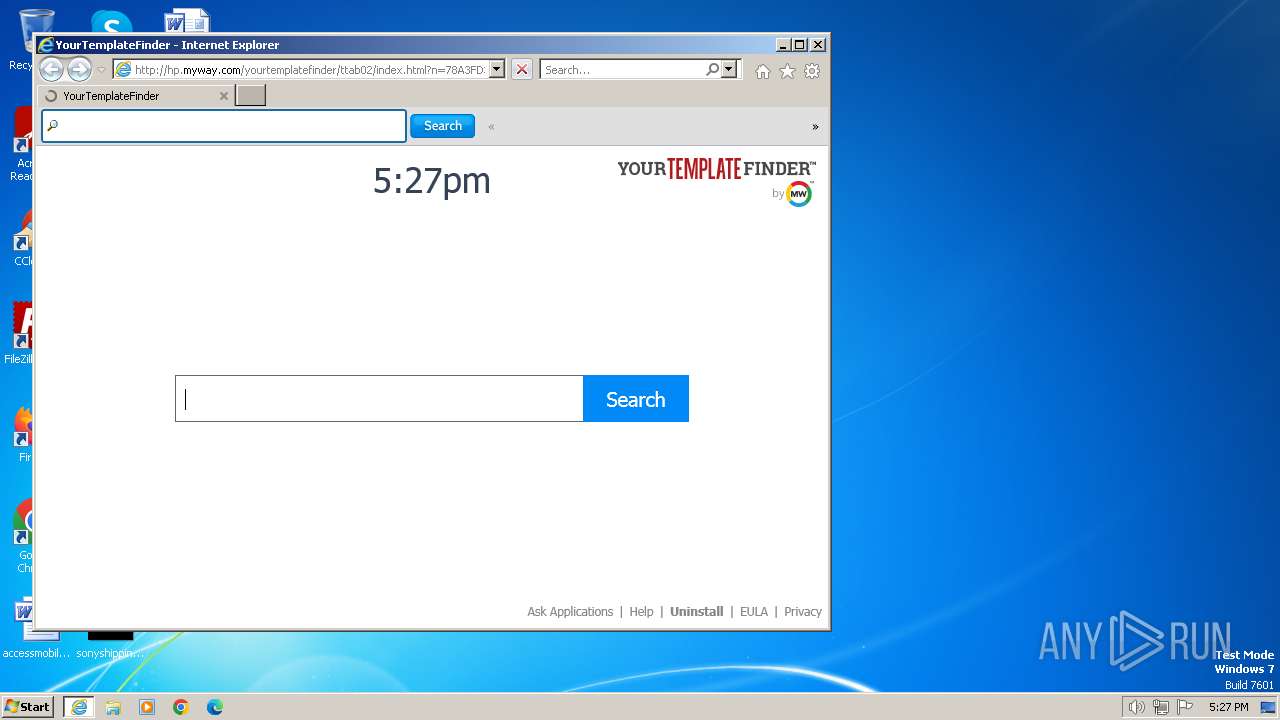
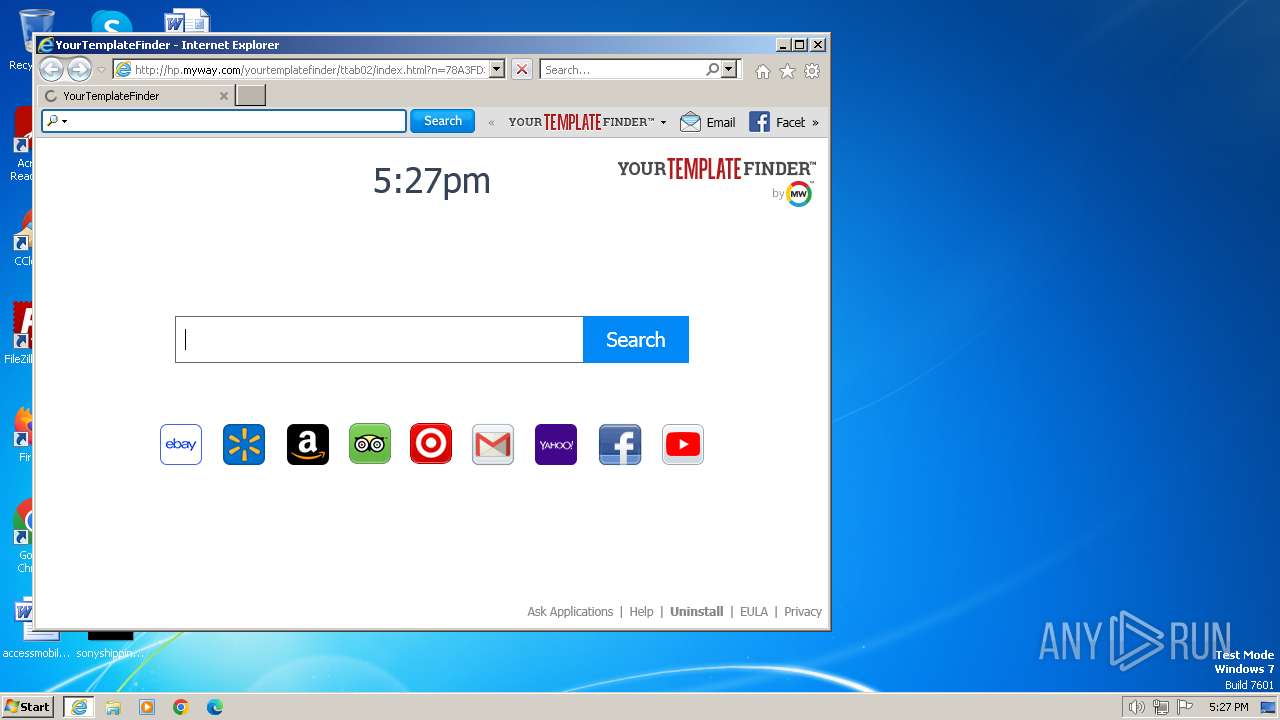
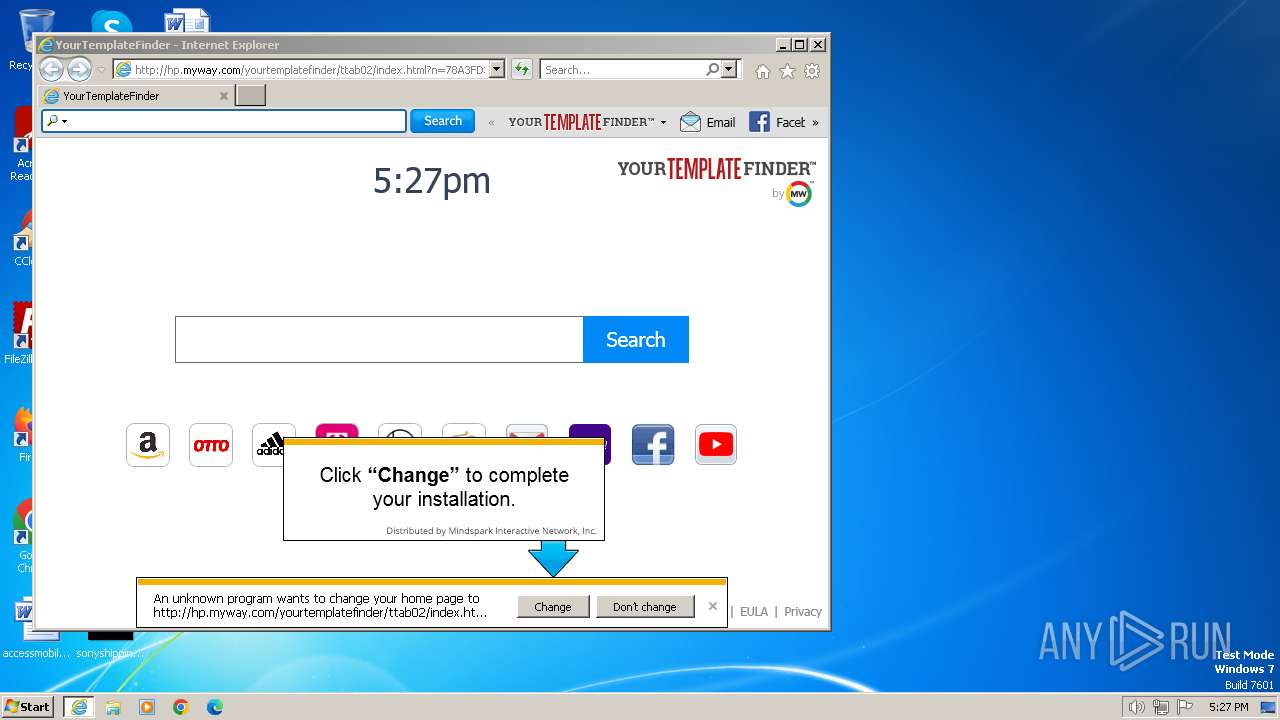
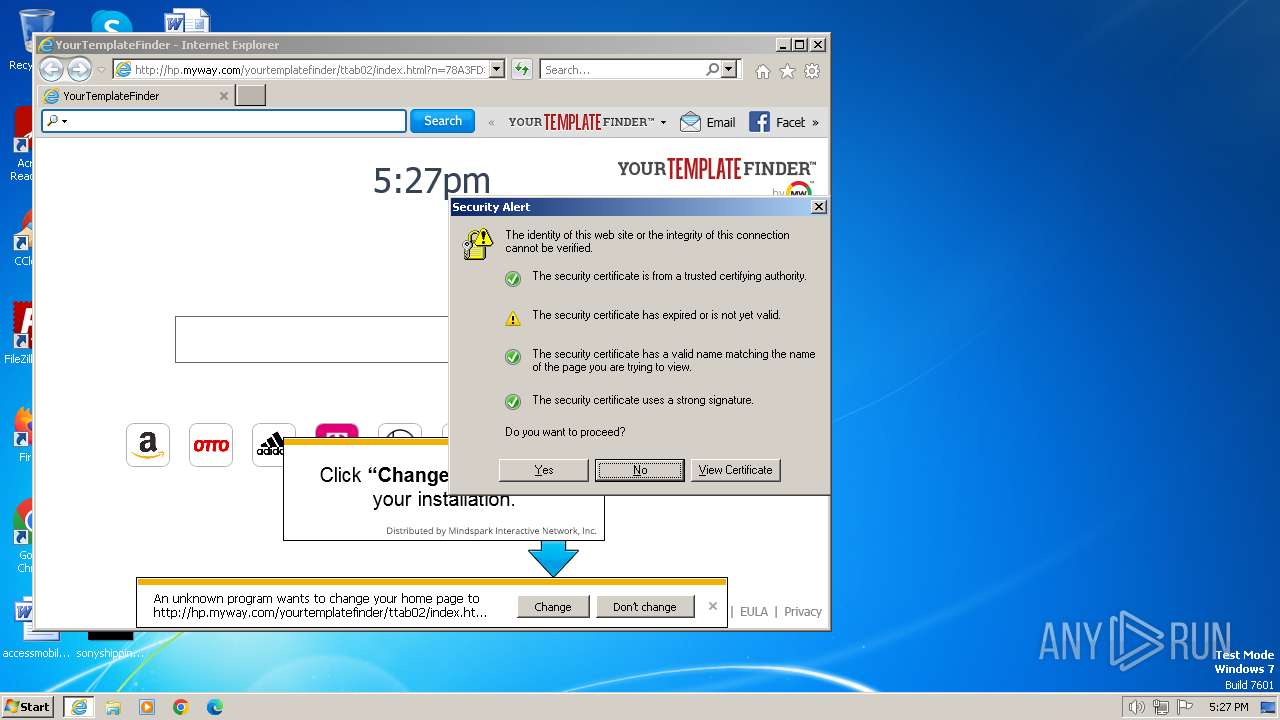
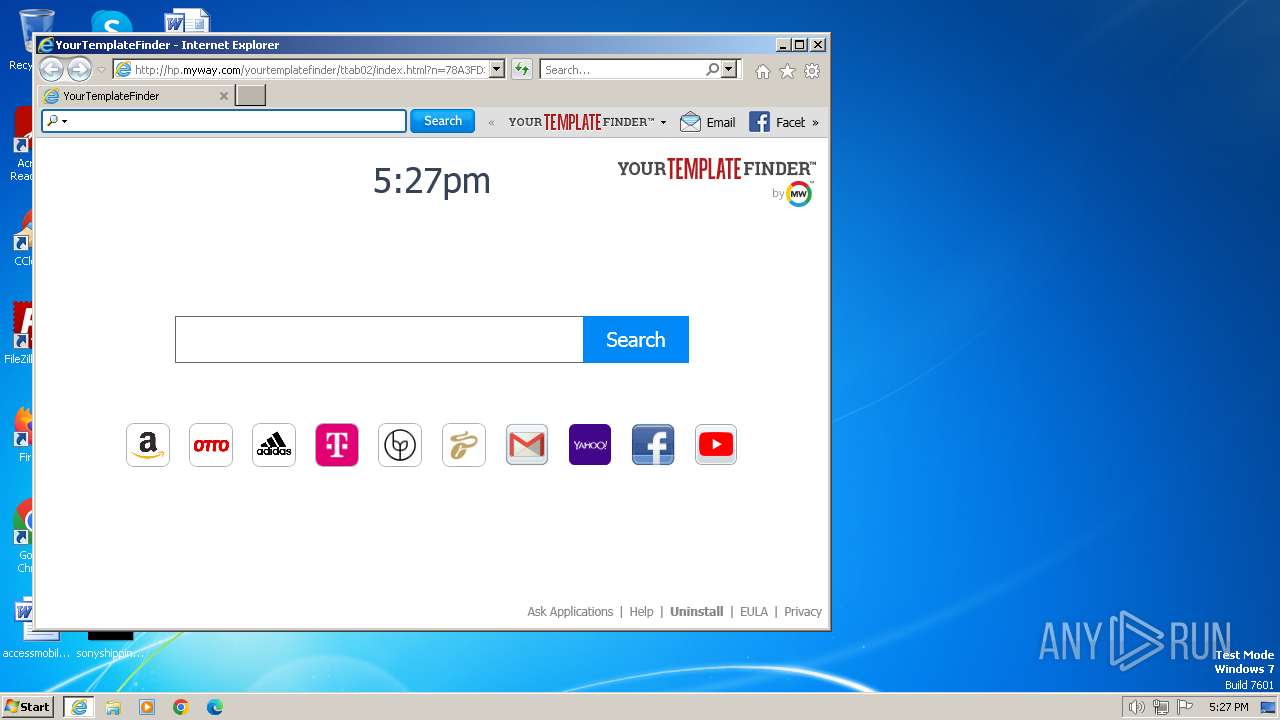
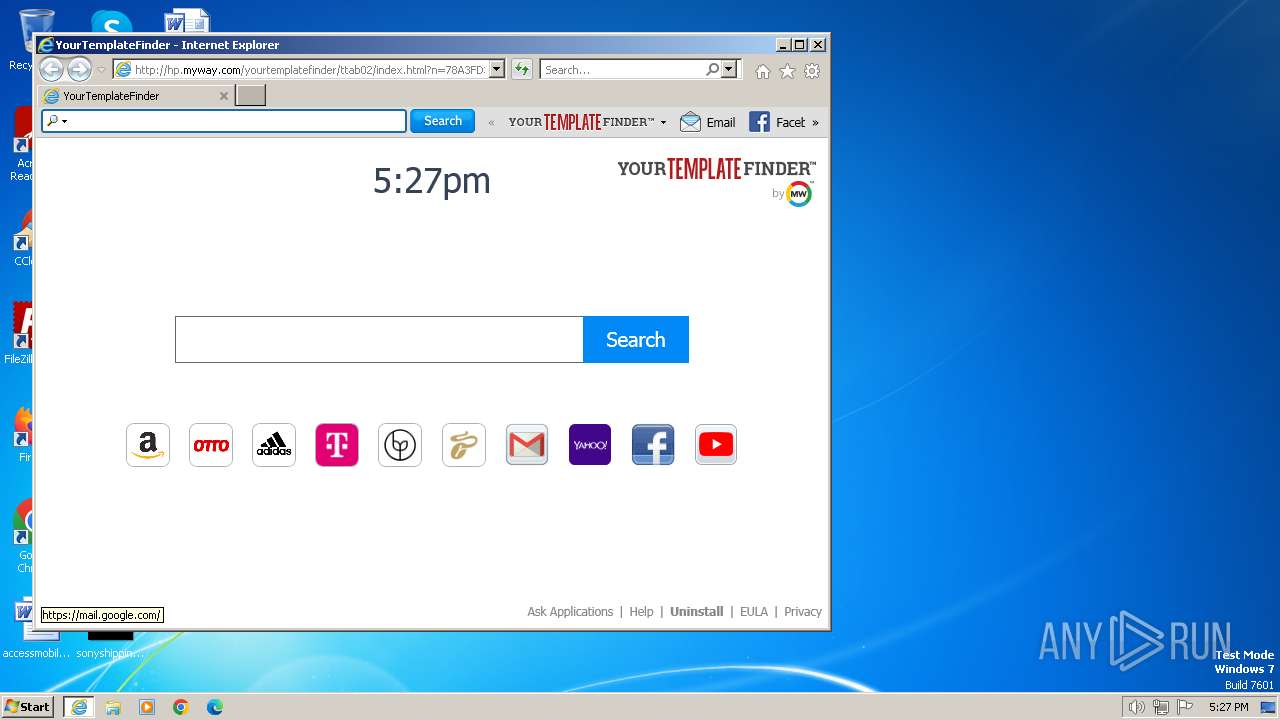
Changes the Home page of Internet Explorer
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
Changes the title of the Internet Explorer window
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
- iexplore.exe (PID: 2508)
Malware-specific behavior (creating "System.dll" in Temp)
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
INFO
Reads the computer name
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
Checks supported languages
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
Checks proxy server information
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
- rundll32.exe (PID: 3244)
Create files in a temporary directory
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
Reads the machine GUID from the registry
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
Creates files or folders in the user directory
- YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe (PID: 1392)
Application launched itself
- iexplore.exe (PID: 2508)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 3244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:25 06:01:44+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3229 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.7.1.3000 |
| ProductVersionNumber: | 2.7.1.3000 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | http://www.mindspark.com |
| CompanyName: | Mindspark Interactive Network, Inc. |
| FileDescription: | YourTemplateFinder Setup |
| FileVersion: | 2.7.1.3000 |
| InternalName: | YourTemplateFinder |
| LegalCopyright: | © 2015 Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| LegalTrademarks: | ® & ™ Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| ProductName: | YourTemplateFinder |
| ProductVersion: | 2.7.1.3000 |
Total processes
43
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1392 | "C:\Users\admin\AppData\Local\Temp\YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe" | C:\Users\admin\AppData\Local\Temp\YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | explorer.exe | ||||||||||||
User: admin Company: Mindspark Interactive Network, Inc. Integrity Level: MEDIUM Description: YourTemplateFinder Setup Exit code: 0 Version: 2.7.1.3000 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2508 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3244 | "Rundll32.exe" "C:\Users\admin\AppData\Local\YourTemplateFinderTooltab\TooltabExtension.dll",A -hp=http://hp.myway.com/yourtemplatefinder/ttab02/index.html -ua="(Windows NT 6.1; Win32; MSIE 11.0; Build 7601; SP 1)" -ul=https://anx.mindspark.com/anx.gif?anxa=%251&anxe=%252&anxt=AA43CC06-1D56-463D-8CF1-BA4C1A98DA7E&anxtv=2.7.1.3000&anxp=^BNF^mni000^TTAB02&anxsi=&anxv=%253&anxd=2024-01-31&anxr=%254 -hu=SHOW | C:\Windows\System32\rundll32.exe | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
27 937
Read events
27 767
Write events
160
Delete events
10
Modification events
| (PID) Process: | (1392) YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1392) YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1392) YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1392) YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1392) YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1392) YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1392) YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1392) YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1392) YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1392) YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | Start Page |
Value: about:blank | |||
Executable files
3
Suspicious files
45
Text files
36
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | C:\Users\admin\AppData\Local\Temp\nst336A.tmp\cancel_blue_1473358017200.bmp | image | |
MD5:C20F972BB1E321BCF007A11D1433496C | SHA256:DDEB1A235C5FBB989FADF287A627736894F62406C0258B2A8B73379ADA7A6775 | |||
| 1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | C:\Users\admin\AppData\Local\Temp\nst336A.tmp\nsDialogs.dll | executable | |
MD5:B9A5A272154FC0DD652EF9C59C5D63A0 | SHA256:D84D810B8F8819F4A34D5E033B72951EADDA1BBB5ED0B8C76874B6C25001CAA9 | |||
| 1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | C:\Users\admin\AppData\Local\Temp\nst336A.tmp\YourTemplateFinder_msi_bg-copy_1501857870041.bmp | image | |
MD5:98E8AE48A448CEB300834709580DF9AF | SHA256:CD89FBA61ABCF16DBAF7B2D5BE655B2B3F950867B612BF72CE1913206E708E46 | |||
| 1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:936124355EAA90B7274D26600CD1A3BD | SHA256:42AEE70D9BE9BCEE149DEBDCADB8F97586AFFDA6E369EAC062829859ECED9201 | |||
| 1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | C:\Users\admin\AppData\Local\Temp\nst336A.tmp\System.dll | executable | |
MD5:7399323923E3946FE9140132AC388132 | SHA256:5A1C20A3E2E2EB182976977669F2C5D9F3104477E98F74D69D2434E79B92FDC3 | |||
| 1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_45E3C223BCF135987E4038FB6B0DBA13 | binary | |
MD5:037AE8164352CA91E80AD33054D1906D | SHA256:07C018EB07002663D5248DAA8A65EAF587955E3DB45735E7E3AC9CB13D7D664E | |||
| 1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:AF5BBE48F933610B97F6429A4836485C | SHA256:F552794D7DB2AE0CD5BF05FADCFE96CC7F2F2B393DC6C6AC2B3711CA4B7FA99D | |||
| 1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_45E3C223BCF135987E4038FB6B0DBA13 | binary | |
MD5:B5D964B4EF0E9520A54852C8AC46443C | SHA256:ABD26F5CED8EB64BAD587122BDD620568D85D71A5A4C243E7A77BB2656D795FF | |||
| 1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:21A9BB4D828C51D3FACF2B10475C24F4 | SHA256:7A9A3F480DE913B5F6C2CE912164B325BCD6DAF6B274A6A3379A61EE46D9CC39 | |||
| 1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BFF0A61018050FB8C0C9B509A000BFFA_FFFF1B0233B3B20E85FAC14DE9C32C4A | binary | |
MD5:3CBC2029C9463D95573CF4263040011E | SHA256:F21394C6719A672CC45CD3ABE961634EAD32EDE8668B5A25A9044789DFAF70C1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
70
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2496 | iexplore.exe | GET | 200 | 23.206.21.59:80 | http://hp.myway.com/api/weather-service/lookup?uuid=AA43CC06-1D56-463D-8CF1-BA4C1A98DA7E&placeId=2601546&address=Mitte%2C%20Berlin%2C%20Germany | unknown | binary | 1.41 Kb | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | GET | 304 | 2.19.126.137:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7eb116b7cc29db82 | unknown | — | — | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | unknown | binary | 724 b | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/s/gts1d4/eQ2pKzFRzms/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEBrkojmzJx8VEEeg2WSex98%3D | unknown | binary | 5 b | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/s/gts1d4/eQ2pKzFRzms/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEBrkojmzJx8VEEeg2WSex98%3D | unknown | binary | 5 b | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | GET | 200 | 2.19.126.137:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?598436b6df23f990 | unknown | compressed | 65.2 Kb | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | GET | 200 | 142.250.74.195:80 | http://crls.pki.goog/gts1d4/kA4WW9mzpzY.crl | unknown | binary | 192 Kb | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | GET | 200 | 2.19.105.18:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | GET | 200 | 2.16.202.115:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQ8U6hGFKedZ8a0t%2BCc4tk5Aw%3D%3D | unknown | binary | 503 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | 34.120.232.229:443 | anx.mindspark.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | 2.19.126.137:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | 142.250.185.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | 142.250.74.195:80 | crls.pki.goog | GOOGLE | US | whitelisted |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | 35.201.91.40:443 | dp.tb.ask.com | GOOGLE | US | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | 2.19.105.18:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
1392 | YourTemplateFinder.06ecbca39b444a91a4f4bca45f211b66.exe | 2.16.202.115:80 | r3.o.lencr.org | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anx.mindspark.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
crls.pki.goog |
| whitelisted |
dp.tb.ask.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
hp.myway.com |
| whitelisted |
ak.staticimgfarm.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |