| File name: | BBB.ps1 |
| Full analysis: | https://app.any.run/tasks/466c7cb6-b3e5-4d41-bc2b-389583da7f93 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2022, 09:34:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | B6B16106C3F141C87742FAA016CDA878 |
| SHA1: | 1B3F33DC0FC50C0E582F508821D531A8E6A2F9D2 |
| SHA256: | 7445338FF74C31EC410C7E98193BE7EA4E230E83673699D93BACBAC6113E9416 |
| SSDEEP: | 3072:e6dE2yerMJB3MkG/nv5FAust3oHsPVWvpiSs9jkrZh70ciIKT5BV:e6daePkwnEgsPcRiSs9jkt2/IKT5BV |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- powershell.exe (PID: 3720)
- powershell.exe (PID: 2424)
PowerShell script executed
- powershell.exe (PID: 3720)
- powershell.exe (PID: 2424)
Creates files in the user directory
- powershell.exe (PID: 3720)
- powershell.exe (PID: 2424)
Reads the date of Windows installation
- powershell.exe (PID: 3720)
- powershell.exe (PID: 2424)
Reads the computer name
- powershell.exe (PID: 3720)
- powershell.exe (PID: 2424)
Creates files in the program directory
- powershell.exe (PID: 3720)
Executable content was dropped or overwritten
- powershell.exe (PID: 3720)
INFO
Checks Windows Trust Settings
- powershell.exe (PID: 3720)
- powershell.exe (PID: 2424)
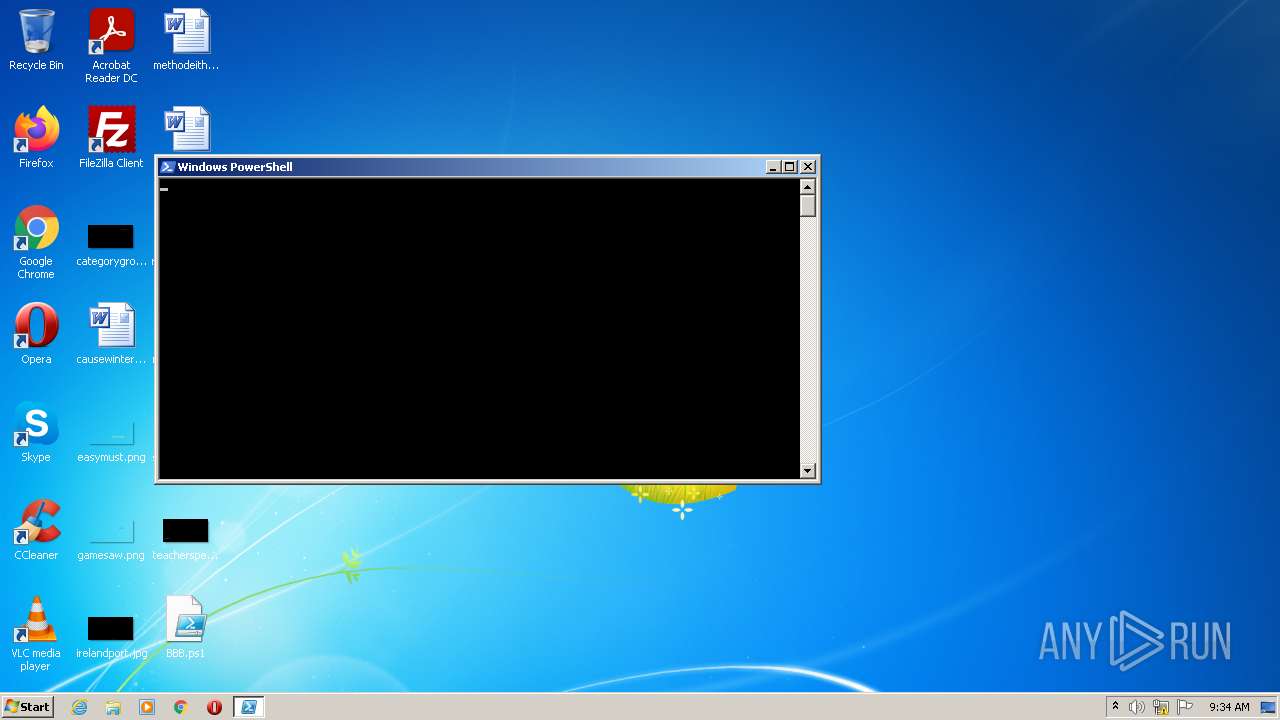
Manual execution by user
- powershell.exe (PID: 2424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2424 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\BBB.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3720 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\BBB.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
2 723
Read events
2 599
Write events
124
Delete events
0
Modification events
| (PID) Process: | (3720) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3720) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3720) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3720) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3720) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2424) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2424) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2424) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2424) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2424) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
10
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3720 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3720 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12c74f.TMP | binary | |
MD5:— | SHA256:— | |||
| 2424 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12f3af.TMP | binary | |
MD5:— | SHA256:— | |||
| 2424 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3720 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ALAN1XAX6X25XKDEUL15.temp | binary | |
MD5:— | SHA256:— | |||
| 3720 | powershell.exe | C:\Users\admin\AppData\Local\Temp\2duxc1qd.bay.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3720 | powershell.exe | C:\Programdata\AAA.exe | executable | |
MD5:1EB3EE5060AFC5E13727F37F41303653 | SHA256:646DA59078F6247B5004A351BAA2E90F7D4BD2502826B7286E4747BCB6814601 | |||
| 3720 | powershell.exe | C:\Users\admin\AppData\Local\Temp\0q3pw0yf.gx1.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3720 | powershell.exe | C:\Programdata\S02.ps1 | text | |
MD5:EBB5975C09105FD692537B5AB793838C | SHA256:F10507288EF55EDCCE685206B64D152A76A3B6DBF36CEC06073AE9E204704D3A | |||
| 2424 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\T3S76SSGKF8KZ1G8Q2OU.temp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report