| File name: | da7d0a85032774c72239a3f6d64430b7 |
| Full analysis: | https://app.any.run/tasks/2847b98e-1532-4c15-b901-dc732fbf5968 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 07:54:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DA7D0A85032774C72239A3F6D64430B7 |
| SHA1: | DA508EC59861E5A0CDBF479F3197A9311B7B7DA8 |
| SHA256: | 7432D9DDBC3C25F69AA99B89908735360FA108F00532BB50871EB2965FF11BB0 |
| SSDEEP: | 24576:MVJrJ3YpLtsXGx9Q8zQ/+kCsg+T3yKqTbG39zf:MJoUXGx9i/w0jyd+f |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- da7d0a85032774c72239a3f6d64430b7.exe (PID: 2976)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:08:07 07:07:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 688128 |
| InitializedDataSize: | 512000 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x873c9 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
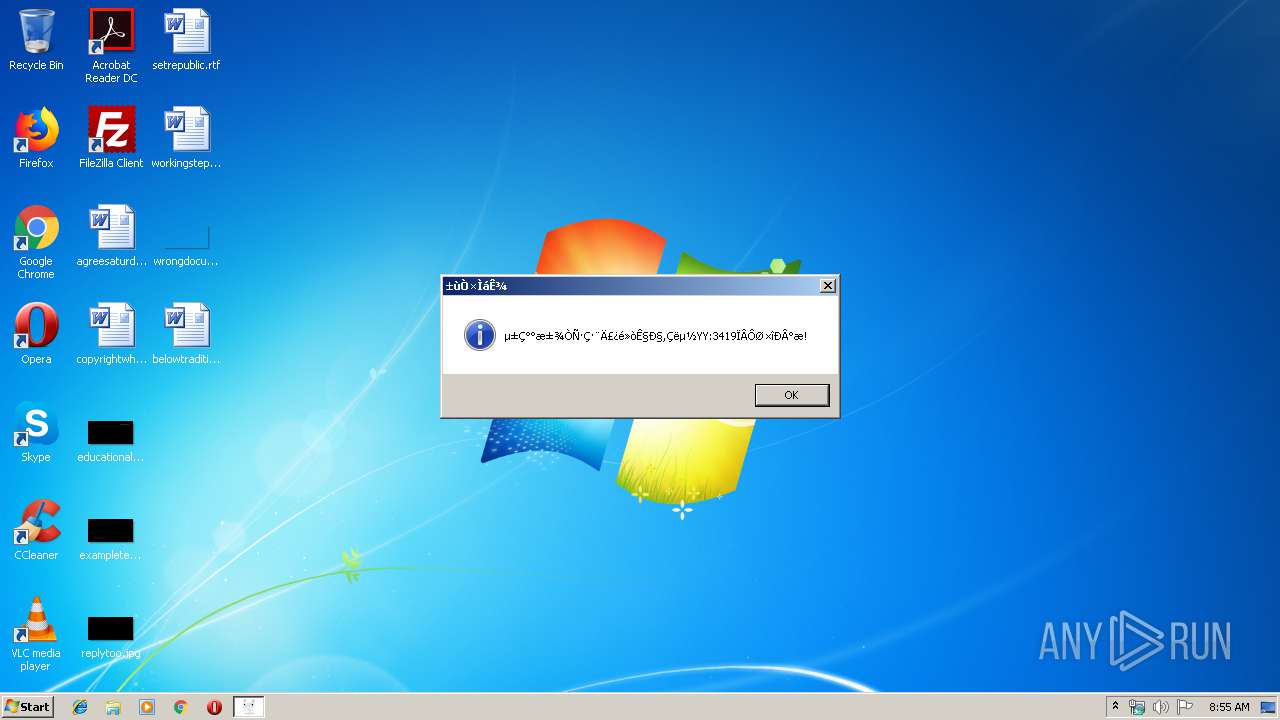
| FileDescription: | YY:3419源吉制作 |
| ProductName: | YY:3419源吉制作 |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | 源吉 |
| LegalCopyright: | CF冰易网游创建空白名生成器 |
| Comments: | YY:3419源吉制作 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Aug-2015 05:07:44 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| FileDescription: | YY:3419源吉制作 |
| ProductName: | YY:3419源吉制作 |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | 源吉 |
| LegalCopyright: | CF冰易网游创建空白名生成器 |
| Comments: | YY:3419源吉制作 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 07-Aug-2015 05:07:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000A8000 | 0x000A8000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.51837 |
.rdata | 0x000A9000 | 0x00018000 | 0x00018000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.43367 |
.data | 0x000C1000 | 0x0005A000 | 0x0005A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.64896 |
.rsrc | 0x0011B000 | 0x0000AB5C | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.09506 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07446 | 461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 4.14558 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.74274 | 180 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
5 | 2.37095 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
6 | 2.42931 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
127 | 1.4183 | 12 | Latin 1 / Western European | Chinese - PRC | RT_MENU |
150 | 3.06278 | 152 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
286 | 3.5561 | 378 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
554 | 3.78697 | 250 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
Imports
ADVAPI32.dll |
AVIFIL32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVFW32.dll |
OLEAUT32.dll |
RASAPI32.dll |
SHELL32.dll |
USER32.dll |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2976 | "C:\Users\admin\AppData\Local\Temp\da7d0a85032774c72239a3f6d64430b7.exe" | C:\Users\admin\AppData\Local\Temp\da7d0a85032774c72239a3f6d64430b7.exe | explorer.exe | ||||||||||||
User: admin Company: 源吉 Integrity Level: MEDIUM Description: YY:3419源吉制作 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
40
Read events
21
Write events
19
Delete events
0
Modification events
| (PID) Process: | (2976) da7d0a85032774c72239a3f6d64430b7.exe | Key: | HKEY_CURRENT_USER\Software\Super-EC\½ûÖ¹Öظ´ÔËÐÐ |
| Operation: | write | Name: | |
Value: 0 | |||
| (PID) Process: | (2976) da7d0a85032774c72239a3f6d64430b7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\da7d0a85032774c72239a3f6d64430b7_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2976) da7d0a85032774c72239a3f6d64430b7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\da7d0a85032774c72239a3f6d64430b7_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2976) da7d0a85032774c72239a3f6d64430b7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\da7d0a85032774c72239a3f6d64430b7_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2976) da7d0a85032774c72239a3f6d64430b7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\da7d0a85032774c72239a3f6d64430b7_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2976) da7d0a85032774c72239a3f6d64430b7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\da7d0a85032774c72239a3f6d64430b7_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2976) da7d0a85032774c72239a3f6d64430b7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\da7d0a85032774c72239a3f6d64430b7_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2976) da7d0a85032774c72239a3f6d64430b7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\da7d0a85032774c72239a3f6d64430b7_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2976) da7d0a85032774c72239a3f6d64430b7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\da7d0a85032774c72239a3f6d64430b7_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2976) da7d0a85032774c72239a3f6d64430b7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\da7d0a85032774c72239a3f6d64430b7_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | da7d0a85032774c72239a3f6d64430b7.exe | C:\Users\admin\AppData\Local\Temp\EC72.tmp | — | |
MD5:— | SHA256:— | |||
| 2976 | da7d0a85032774c72239a3f6d64430b7.exe | C:\Users\admin\AppData\Local\Temp\EC73.tmp | — | |
MD5:— | SHA256:— | |||
| 2976 | da7d0a85032774c72239a3f6d64430b7.exe | C:\Users\admin\AppData\Local\Temp\EC83.tmp | — | |
MD5:— | SHA256:— | |||
| 2976 | da7d0a85032774c72239a3f6d64430b7.exe | C:\Users\admin\AppData\Local\Temp\da7d0a85032774c72239a3f6d64430b7.exe{3C8D4BFC-6BD7-46c3-AF71-C8F2354A765F} | — | |
MD5:— | SHA256:— | |||
| 2976 | da7d0a85032774c72239a3f6d64430b7.exe | C:\Users\admin\AppData\Local\Temp\RCXECA4.tmp | — | |
MD5:— | SHA256:— | |||
| 2976 | da7d0a85032774c72239a3f6d64430b7.exe | C:\Users\admin\AppData\Local\Temp\da7d0a85032774c72239a3f6d64430b7.exe | executable | |
MD5:— | SHA256:— | |||
| 2976 | da7d0a85032774c72239a3f6d64430b7.exe | C:\Users\admin\AppData\Local\Temp\_@ECA3.tmp | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2976 | da7d0a85032774c72239a3f6d64430b7.exe | GET | — | 123.58.180.39:80 | http://cfyuanji.blog.163.com/blog/static/21795512620156505533625/ | CN | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2976 | da7d0a85032774c72239a3f6d64430b7.exe | 123.58.180.39:80 | cfyuanji.blog.163.com | Guangzhou NetEase Computer System Co., Ltd. | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cfyuanji.blog.163.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2976 | da7d0a85032774c72239a3f6d64430b7.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
2976 | da7d0a85032774c72239a3f6d64430b7.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spyware.OnlineGames |