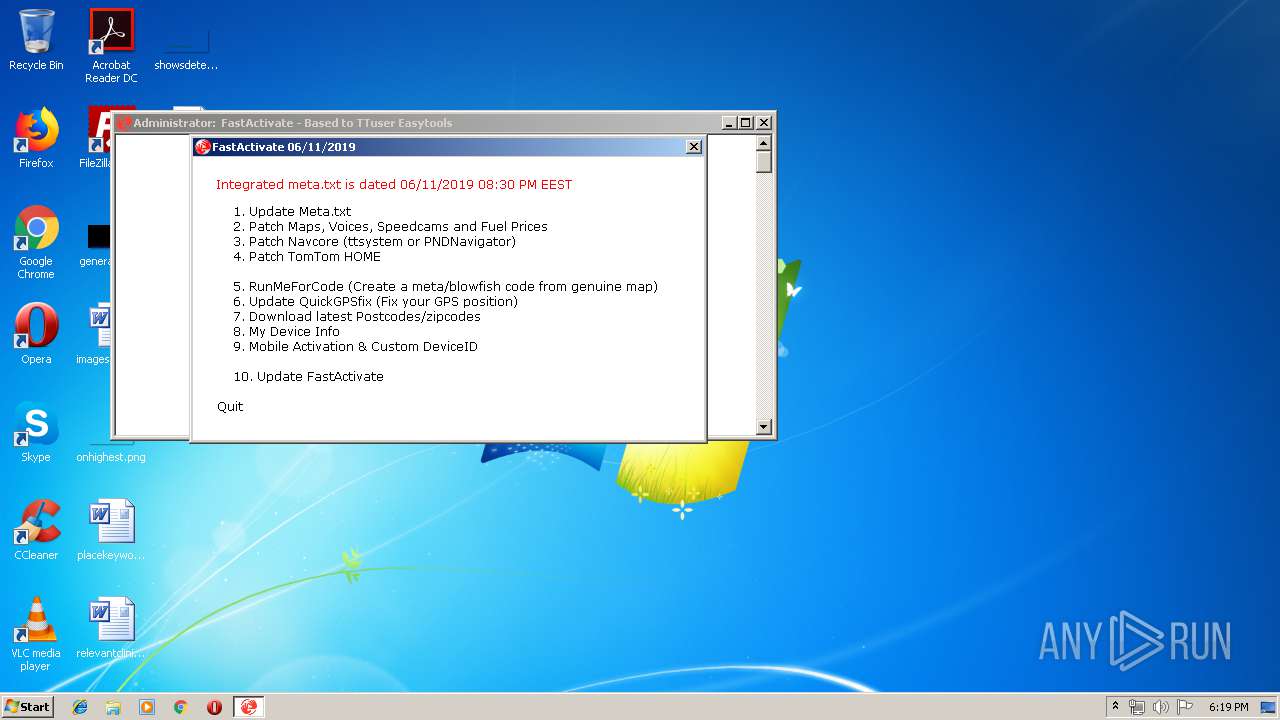
| File name: | FastActivate.exe |
| Full analysis: | https://app.any.run/tasks/a1b55e12-e702-4a47-92b7-2b175a4950f6 |
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2019, 17:18:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable, MZ for MS-DOS |
| MD5: | C8C7100C0620D3BBA7198B9B9BC1F04D |
| SHA1: | ED21957154473273E25A696B61A231F1BEC7297A |
| SHA256: | 7413A356A0C64F0ED2FF8F1CE8E53A1C957981CE5568602C83C80ADDDB4D728A |
| SSDEEP: | 49152:b8DXbKj7vHDBy2NZ1IBmQpcl00eGJvpmJsE4biv4To+2hkOGR:b8fuHDM25IBmkaJeamJTv4To0 |
MALICIOUS
Detects Cygwin installation
- UnRAR.exe (PID: 1580)
Application was dropped or rewritten from another process
- Wselect.exe (PID: 2872)
- UnRAR.exe (PID: 1580)
SUSPICIOUS
Executable content was dropped or overwritten
- FastActivate.exe (PID: 3304)
- UnRAR.exe (PID: 1580)
- cmd.exe (PID: 2184)
Starts CMD.EXE for commands execution
- FastActivate.exe (PID: 3304)
- cmd.exe (PID: 2184)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2184)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 1536)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3144)
Application launched itself
- cmd.exe (PID: 2184)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2184)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:03:25 14:17:51+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 33792 |
| InitializedDataSize: | 2991616 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e61e7 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 11.6.2019.2230 |
| ProductVersionNumber: | 11.6.2019.2230 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | GPSUrl |
| FileDescription: | Activate Maps,Voices, Speedcams & Fuel prices. Patch Navcore & HOME. Check current meta code. Update QuickGPSfix |
| FileVersion: | 11,06,2019,2230 |
| ProductName: | FastActivate |
| InternalName: | FastActivate |
| ProductVersion: | 11,06,2019,2230 |
| LegalCopyright: | GPSUrl |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 25-Mar-2011 13:17:51 |
| Detected languages: |
|
| CompanyName: | GPSUrl |
| FileDescription: | Activate Maps,Voices, Speedcams & Fuel prices. Patch Navcore & HOME. Check current meta code. Update QuickGPSfix |
| FileVersion: | 11,06,2019,2230 |
| ProductName: | FastActivate |
| InternalName: | FastActivate |
| ProductVersion: | 11,06,2019,2230 |
| LegalCopyright: | GPSUrl |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0040 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0002 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0xB400 |
| OEM information: | 0xCD09 |
| Address of NE header: | 0x00000040 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Mar-2011 13:17:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.MPRESS1 | 0x00001000 | 0x002E5000 | 0x00299400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99993 |
.MPRESS2Q\x0d | 0x002E6000 | 0x00000D51 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.85501 |
.rsrc | 0x002E7000 | 0x00011F8C | 0x00012000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.7314 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09999 | 668 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.24404 | 304 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.95616 | 240 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.25082 | 176 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.91163 | 1640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.32087 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.41931 | 488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 3.098 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 2.76479 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 2.2624 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.DLL |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
Total processes
60
Monitored processes
23
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | find /v /i "a" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | taskkill /f /im tt8_keygen2.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | WMIC LOGICALDISK GET Name,Size,FreeSpace | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1536 | C:\Windows\system32\cmd.exe /c "WMIC LOGICALDISK GET Name,Size,FreeSpace | find /i "C:"" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1580 | "C:\Users\admin\AppData\Local\Temp\ED18.tmp\unrar" e -o+ "C:\Users\admin\AppData\Local\Temp\ED18.tmp\ADDS.rar" "C:\Users\admin\AppData\Local\Temp\ED18.tmp" | C:\Users\admin\AppData\Local\Temp\ED18.tmp\UnRAR.exe | cmd.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Command line RAR Exit code: 0 Version: 5.71.0 Modules
| |||||||||||||||
| 1784 | find /v /i "c" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | taskkill /f /im wget.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | cmd /c ""C:\Users\admin\AppData\Local\Temp\ED18.tmp\FastActivate.BAT" C:\Users\admin\AppData\Local\Temp\" | C:\Windows\system32\cmd.exe | FastActivate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2416 | C:\Windows\system32\cmd.exe /c mountvol |find /i ":\" |find /v /i "a"|find /v /i "c"|find /v /i "b"|find /v /i "D" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2580 | mountvol | C:\Windows\system32\mountvol.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Mount Volume Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
89
Read events
89
Write events
0
Delete events
0
Modification events
Executable files
16
Suspicious files
2
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3304 | FastActivate.exe | C:\Users\admin\AppData\Local\Temp\ED18.tmp\ADDS.rar | compressed | |
MD5:— | SHA256:— | |||
| 1580 | UnRAR.exe | C:\Users\admin\AppData\Local\Temp\ED18.tmp\Wbusy.exe | — | |
MD5:— | SHA256:— | |||
| 1580 | UnRAR.exe | C:\Users\admin\AppData\Local\Temp\ED18.tmp\wget.exe | — | |
MD5:— | SHA256:— | |||
| 3304 | FastActivate.exe | C:\Users\admin\AppData\Local\Temp\ED18.tmp\FastActivate.BAT | text | |
MD5:— | SHA256:— | |||
| 1580 | UnRAR.exe | C:\Users\admin\AppData\Local\Temp\ED18.tmp\7z.dll | executable | |
MD5:72491C7B87A7C2DD350B727444F13BB4 | SHA256:34AD9BB80FE8BF28171E671228EB5B64A55CAA388C31CB8C0DF77C0136735891 | |||
| 1580 | UnRAR.exe | C:\Users\admin\AppData\Local\Temp\ED18.tmp\FastActivate-Updater.exe | executable | |
MD5:— | SHA256:— | |||
| 1580 | UnRAR.exe | C:\Users\admin\AppData\Local\Temp\ED18.tmp\meta1.txt | text | |
MD5:— | SHA256:— | |||
| 1580 | UnRAR.exe | C:\Users\admin\AppData\Local\Temp\ED18.tmp\zipmenu.txt | text | |
MD5:— | SHA256:— | |||
| 1580 | UnRAR.exe | C:\Users\admin\AppData\Local\Temp\ED18.tmp\tt8_keygen2.exe | executable | |
MD5:565872A244FC5A1AB899DC0C60A70A8B | SHA256:51E359E84D7FA1FC3A4A07E19C0DB236A12CDBF305815CF3163AC7452B282C8B | |||
| 1580 | UnRAR.exe | C:\Users\admin\AppData\Local\Temp\ED18.tmp\Menu.txt | text | |
MD5:7A3D5966ACF04F2B61261D84E14A0538 | SHA256:C5827BBA544B9D37B748C880C6663FB8E00A20A2F8A53ABE770A07837AD68FB3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report