| File name: | OfficeSetup.exe |
| Full analysis: | https://app.any.run/tasks/1acab24e-23b8-496a-baa6-3d2b9922973c |
| Verdict: | Malicious activity |
| Analysis date: | September 12, 2020, 10:49:49 |
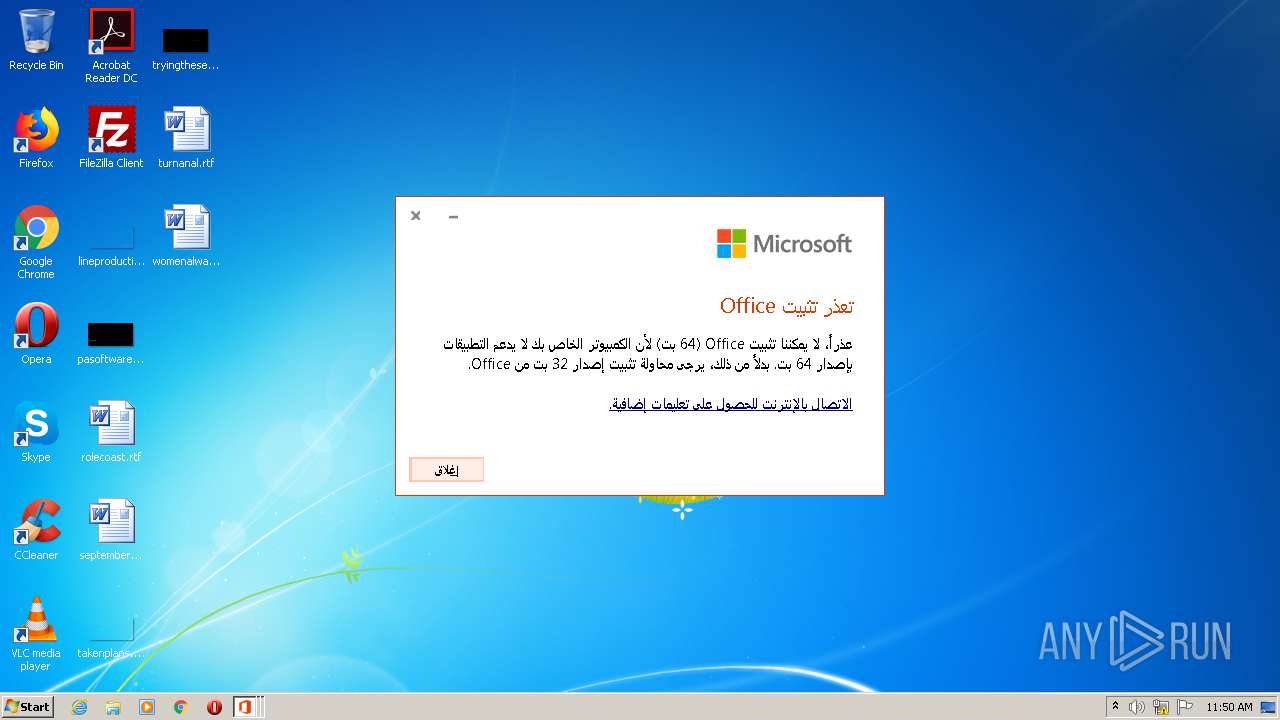
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5959C2255EC01E3E17A124085840BA4B |
| SHA1: | 6F02AEA521EA5A5C5B1FE2CF932C526868FAEABA |
| SHA256: | 74116B61C6108CE59A82941C67A708321C4BED8733203D7B864D848699D0A2F1 |
| SSDEEP: | 98304:iSVzKvzDXOZZAep0Xmpk0sSGeUrdzE2x0uqRcwY2h115c:BSvX0dnmtpzfW |
MALICIOUS
Changes settings of System certificates
- OfficeSetup.exe (PID: 824)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 540)
- powershell.exe (PID: 3688)
Executes PowerShell scripts
- OfficeSetup.exe (PID: 824)
Reads Internet Cache Settings
- OfficeSetup.exe (PID: 2908)
- OfficeSetup.exe (PID: 824)
Application launched itself
- OfficeSetup.exe (PID: 2908)
Adds / modifies Windows certificates
- OfficeSetup.exe (PID: 824)
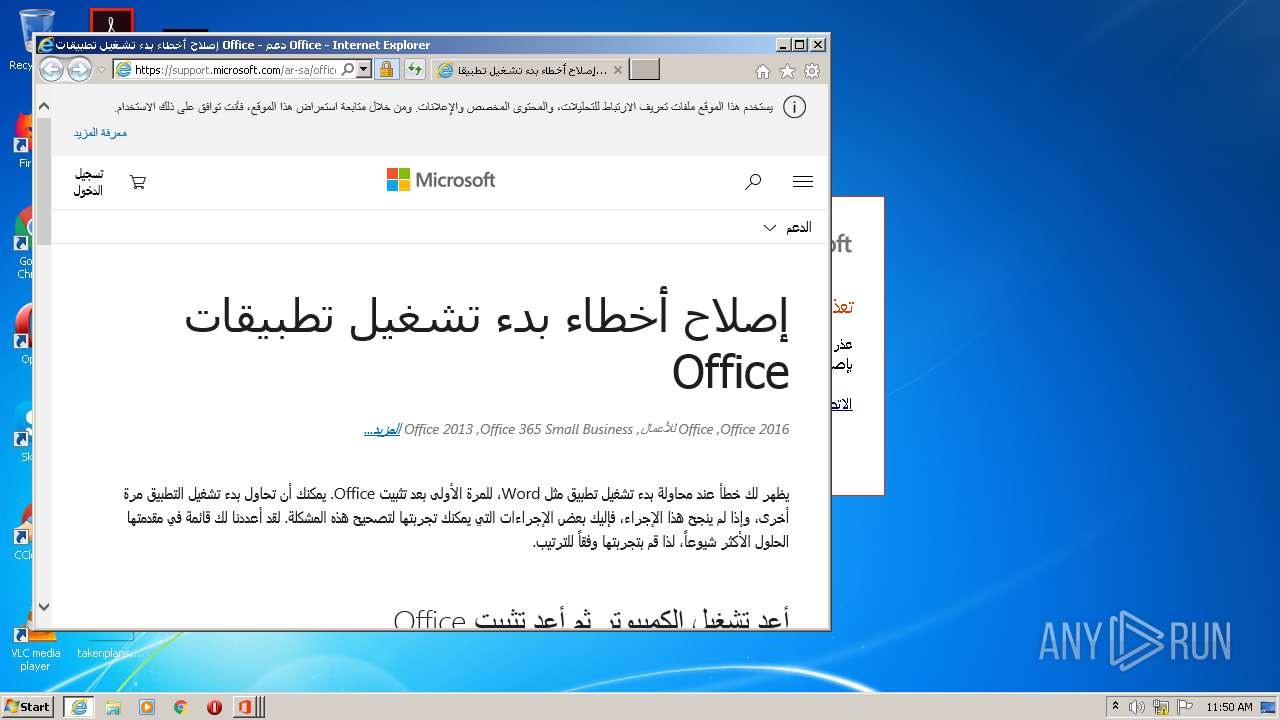
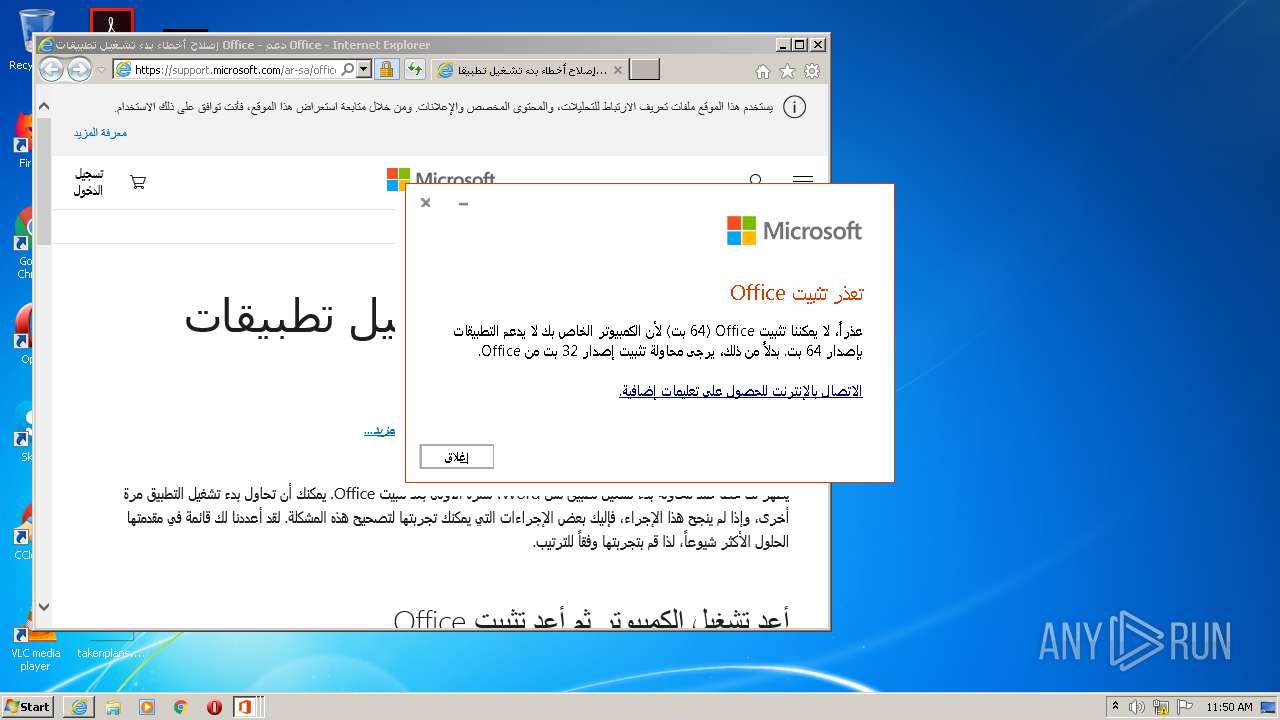
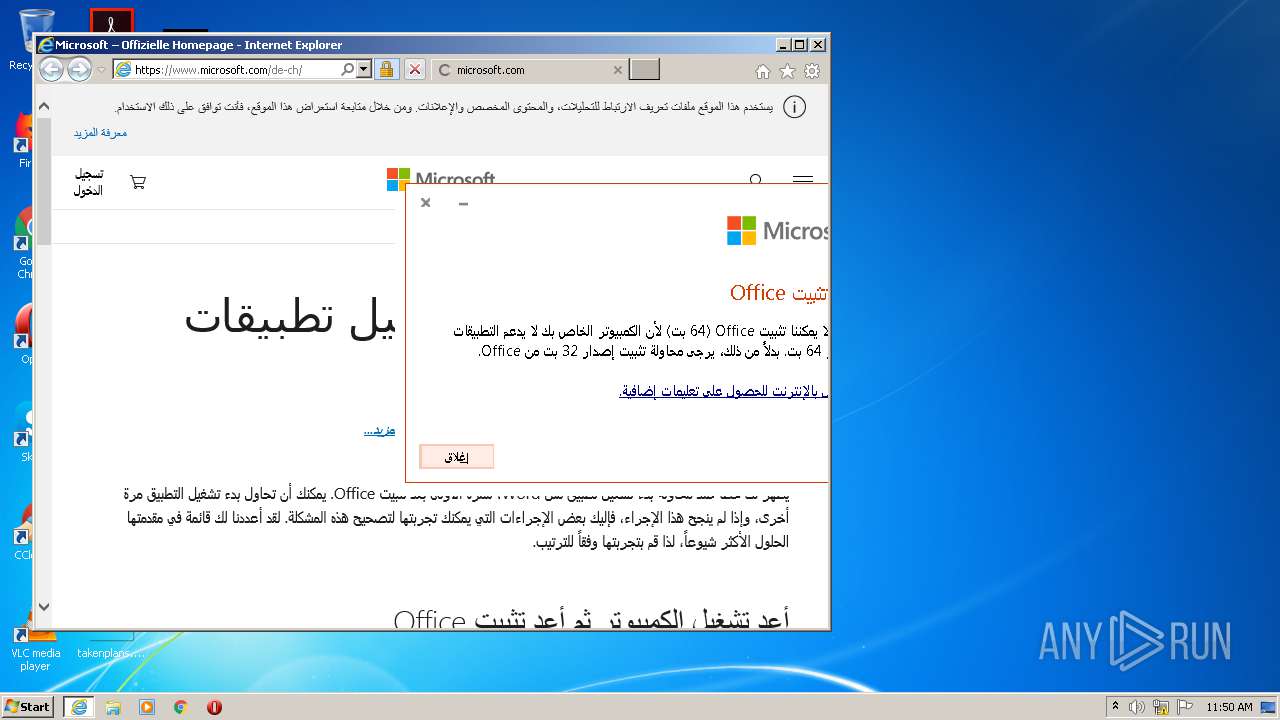
Starts Internet Explorer
- OfficeSetup.exe (PID: 824)
INFO
Reads Microsoft Office registry keys
- OfficeSetup.exe (PID: 824)
Reads settings of System Certificates
- OfficeSetup.exe (PID: 824)
- iexplore.exe (PID: 2984)
- iexplore.exe (PID: 3332)
Reads Internet Cache Settings
- iexplore.exe (PID: 3332)
- iexplore.exe (PID: 2984)
Application launched itself
- iexplore.exe (PID: 3332)
Changes internet zones settings
- iexplore.exe (PID: 3332)
Creates files in the user directory
- iexplore.exe (PID: 2984)
Reads internet explorer settings
- iexplore.exe (PID: 2984)
Changes settings of System certificates
- iexplore.exe (PID: 2984)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2984)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:05:08 17:00:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 2979328 |
| InitializedDataSize: | 2360832 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25960d |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.0.12730.20270 |
| ProductVersionNumber: | 16.0.12730.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
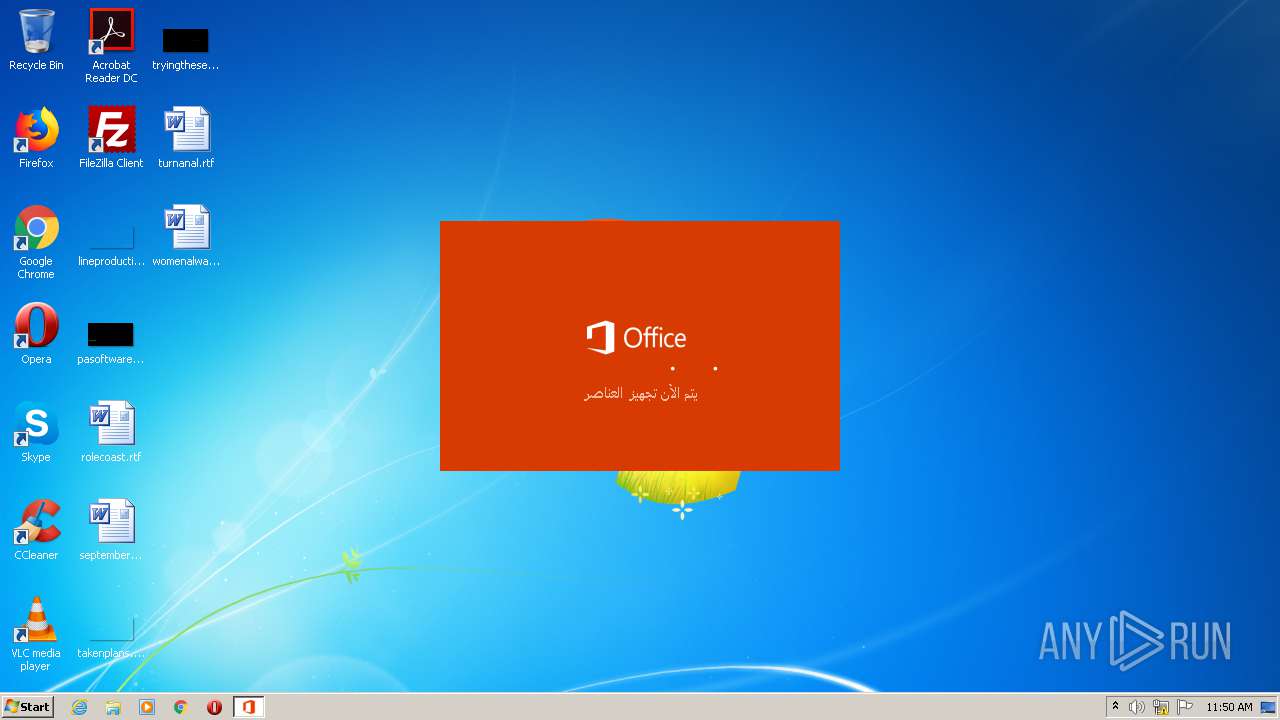
| FileDescription: | Microsoft Office |
| FileVersion: | 16.0.12730.20270 |
| InternalName: | Bootstrapper.exe |
| LegalTrademarks1: | Microsoft® is a registered trademark of Microsoft Corporation. |
| LegalTrademarks2: | Windows® is a registered trademark of Microsoft Corporation. |
| OriginalFileName: | Bootstrapper.exe |
| ProductName: | Microsoft Office |
| ProductVersion: | 16.0.12730.20270 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-May-2020 15:00:46 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Office |
| FileVersion: | 16.0.12730.20270 |
| InternalName: | Bootstrapper.exe |
| LegalTrademarks1: | Microsoft® is a registered trademark of Microsoft Corporation. |
| LegalTrademarks2: | Windows® is a registered trademark of Microsoft Corporation. |
| OriginalFilename: | Bootstrapper.exe |
| ProductName: | Microsoft Office |
| ProductVersion: | 16.0.12730.20270 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 08-May-2020 15:00:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x002D7581 | 0x002D7600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66148 |
.rdata | 0x002D9000 | 0x0014FB20 | 0x0014FC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.70615 |
.data | 0x00429000 | 0x00023B60 | 0x00015800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.10985 |
.rsrc | 0x0044D000 | 0x00095000 | 0x00094A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.52142 |
.reloc | 0x004E2000 | 0x00046750 | 0x00046800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.47872 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33138 | 1809 | Latin 1 / Western European | Arabic - Saudi Arabia | RT_MANIFEST |
2 | 1.96082 | 9640 | Latin 1 / Western European | Arabic - Saudi Arabia | RT_ICON |
3 | 2.20562 | 4264 | Latin 1 / Western European | Arabic - Saudi Arabia | RT_ICON |
4 | 2.87138 | 1128 | Latin 1 / Western European | Arabic - Saudi Arabia | RT_ICON |
188 | 2.78173 | 186 | Latin 1 / Western European | Arabic - Saudi Arabia | RT_STRING |
376 | 3.6437 | 1728 | Latin 1 / Western European | Arabic - Saudi Arabia | RT_STRING |
377 | 3.93776 | 2094 | Latin 1 / Western European | Arabic - Saudi Arabia | RT_STRING |
378 | 3.78478 | 1860 | Latin 1 / Western European | Arabic - Saudi Arabia | RT_STRING |
379 | 3.84953 | 842 | Latin 1 / Western European | Arabic - Saudi Arabia | RT_STRING |
380 | 3.96458 | 1026 | Latin 1 / Western European | Arabic - Saudi Arabia | RT_STRING |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SETUPAPI.dll |
WINTRUST.dll |
WS2_32.dll |
api-ms-win-core-winrt-string-l1-1-0.dll (delay-loaded) |
gdiplus.dll |
Total processes
45
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile "$package = Get-AppxPackage Microsoft.Office.Desktop -allUsers; if (!$package) { $Error.Add(\"Package is not installed\")}; if ($error.Count -eq 0) { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch' -InputObject '1' -Encoding ascii; } else { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch' -InputObject '0' -Encoding ascii; Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateError.scratch' -InputObject $error -Encoding ascii;} " | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | OfficeSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 824 | "C:\Users\admin\AppData\Local\Temp\OfficeSetup.exe" ELEVATED sid=S-1-5-21-1302019708-1500728564-335382590-1000 | C:\Users\admin\AppData\Local\Temp\OfficeSetup.exe | OfficeSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office Exit code: 1603 Version: 16.0.12730.20270 Modules
| |||||||||||||||
| 2908 | "C:\Users\admin\AppData\Local\Temp\OfficeSetup.exe" | C:\Users\admin\AppData\Local\Temp\OfficeSetup.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Exit code: 1603 Version: 16.0.12730.20270 Modules
| |||||||||||||||
| 2984 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3332 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Internet Explorer\iexplore.exe" https://officeredir.microsoft.com/r/rlidOfficeWebHelp?p1=OCSAC2RClickToRun&ver=16&clid=1025&helpid=%2211-BOOTSTRAPPER_PREREQ-odtBitnessCheck%22&app=webview | C:\Program Files\Internet Explorer\iexplore.exe | OfficeSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3688 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile "$package = Get-AppxPackage Microsoft.Office.Desktop -allUsers; if (!$package) { $Error.Add(\"Package is not installed\")}; if ($error.Count -eq 0) { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch' -InputObject '1' -Encoding ascii; } else { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch' -InputObject '0' -Encoding ascii; Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateError.scratch' -InputObject $error -Encoding ascii;} " | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | OfficeSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 135
Read events
1 806
Write events
328
Delete events
1
Modification events
| (PID) Process: | (2908) OfficeSetup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2908) OfficeSetup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2908) OfficeSetup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (2908) OfficeSetup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (2908) OfficeSetup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (2908) OfficeSetup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (2908) OfficeSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | UIFallbackLanguages |
Value: x-none | |||
| (PID) Process: | (2908) OfficeSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | HelpLanguageTag |
Value: en-US | |||
| (PID) Process: | (2908) OfficeSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | PreferredEditingLanguage |
Value: en-US | |||
| (PID) Process: | (2908) OfficeSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | PreviousPreferredEditingLanguage |
Value: en-US | |||
Executable files
0
Suspicious files
61
Text files
65
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 540 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6TKGDEUAJQPR44JSBZGR.temp | — | |
MD5:— | SHA256:— | |||
| 3688 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SFPK5I60H1UMJOHEQIJQ.temp | — | |
MD5:— | SHA256:— | |||
| 3688 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch | — | |
MD5:— | SHA256:— | |||
| 3688 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Office.ValidateError.scratch | — | |
MD5:— | SHA256:— | |||
| 824 | OfficeSetup.exe | C:\Users\admin\AppData\Local\Temp\Cab11.tmp | — | |
MD5:— | SHA256:— | |||
| 824 | OfficeSetup.exe | C:\Users\admin\AppData\Local\Temp\Tar12.tmp | — | |
MD5:— | SHA256:— | |||
| 824 | OfficeSetup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R9A739D92-246D-482D-B966-7CE111F162C2OfficeC2RF8837721-D17A-4C54-9000-E759D99D18D1\v64.hash | — | |
MD5:— | SHA256:— | |||
| 824 | OfficeSetup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R9A739D92-246D-482D-B966-7CE111F162C2OfficeC2RF8837721-D17A-4C54-9000-E759D99D18D1\VersionDescriptor.xml | — | |
MD5:— | SHA256:— | |||
| 824 | OfficeSetup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R9A739D92-246D-482D-B966-7CE111F162C2\v64.hash | — | |
MD5:— | SHA256:— | |||
| 824 | OfficeSetup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R9A739D92-246D-482D-B966-7CE111F162C2\VersionDescriptor.xml | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
63
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 2.17.46.200:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.12527.21104.cab | unknown | — | — | whitelisted |
824 | OfficeSetup.exe | HEAD | 301 | 104.108.144.60:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.12527.21104.cab | US | — | — | whitelisted |
824 | OfficeSetup.exe | HEAD | 200 | 2.17.46.200:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.12527.21104.cab | unknown | — | — | whitelisted |
824 | OfficeSetup.exe | HEAD | 301 | 104.108.144.60:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.12527.21104.cab | US | — | — | whitelisted |
— | — | HEAD | 301 | 104.108.144.60:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.12527.21104.cab | US | — | — | whitelisted |
— | — | HEAD | 301 | 104.108.144.60:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.12527.21104.cab | US | — | — | whitelisted |
824 | OfficeSetup.exe | HEAD | 200 | 2.17.46.200:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.12527.21104.cab | unknown | — | — | whitelisted |
— | — | GET | 301 | 104.108.144.60:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.12527.21104.cab | US | — | — | whitelisted |
824 | OfficeSetup.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_2010-07-06.crl | unknown | der | 557 b | whitelisted |
— | — | GET | 301 | 104.108.144.60:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.12527.21104.cab | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 52.109.88.6:443 | officeredir.microsoft.com | Microsoft Corporation | NL | whitelisted |
824 | OfficeSetup.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
2984 | iexplore.exe | 52.109.88.6:443 | officeredir.microsoft.com | Microsoft Corporation | NL | whitelisted |
2984 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2984 | iexplore.exe | 104.108.144.117:443 | support.microsoft.com | TOT Public Company Limited | US | malicious |
2984 | iexplore.exe | 2.16.186.27:443 | statics-marketingsites-neu-ms-com.akamaized.net | Akamai International B.V. | — | whitelisted |
2984 | iexplore.exe | 104.111.245.158:443 | support.office.com | Akamai International B.V. | NL | whitelisted |
2984 | iexplore.exe | 2.16.186.40:443 | img-prod-cms-rt-microsoft-com.akamaized.net | Akamai International B.V. | — | whitelisted |
2984 | iexplore.exe | 152.199.19.160:443 | az725175.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2908 | OfficeSetup.exe | 52.113.194.132:443 | ecs.office.com | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ecs.office.com |
| whitelisted |
mrodevicemgr.officeapps.live.com |
| whitelisted |
officecdn.microsoft.com |
| whitelisted |
officecdn.microsoft.com.edgesuite.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |
officeredir.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
support.office.com |
| whitelisted |
support.microsoft.com |
| malicious |
www.microsoft.com |
| whitelisted |